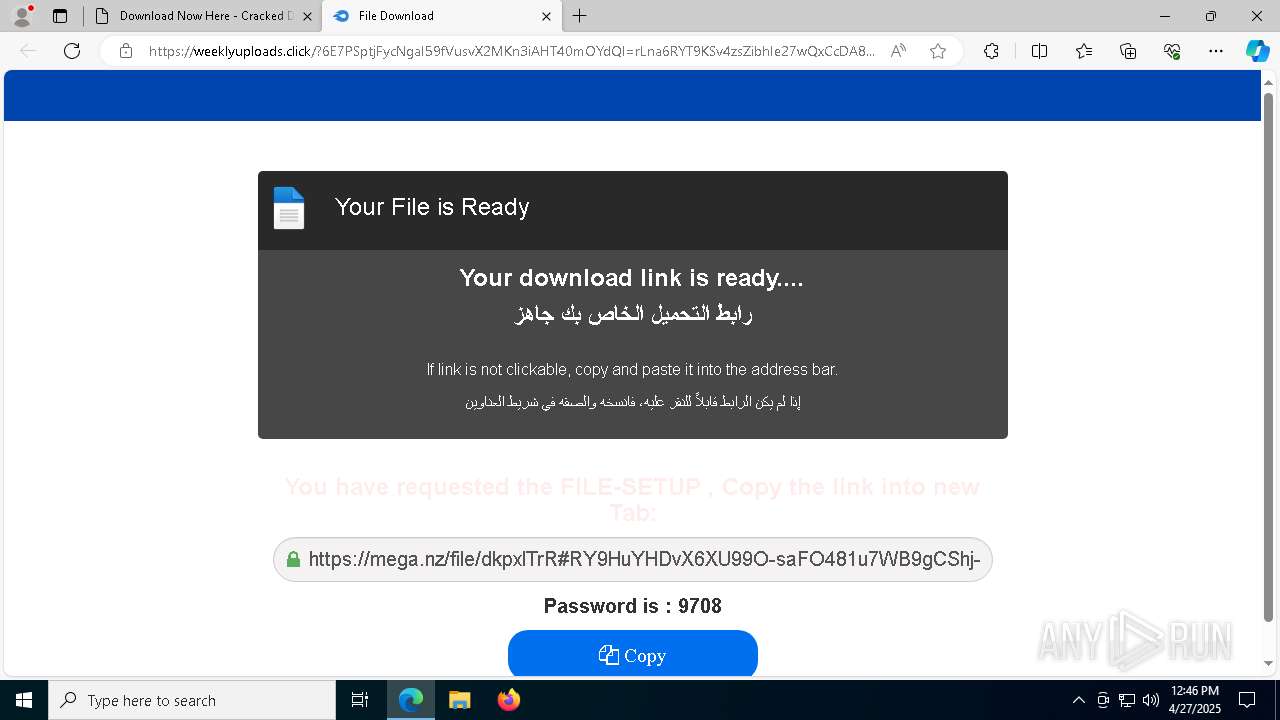
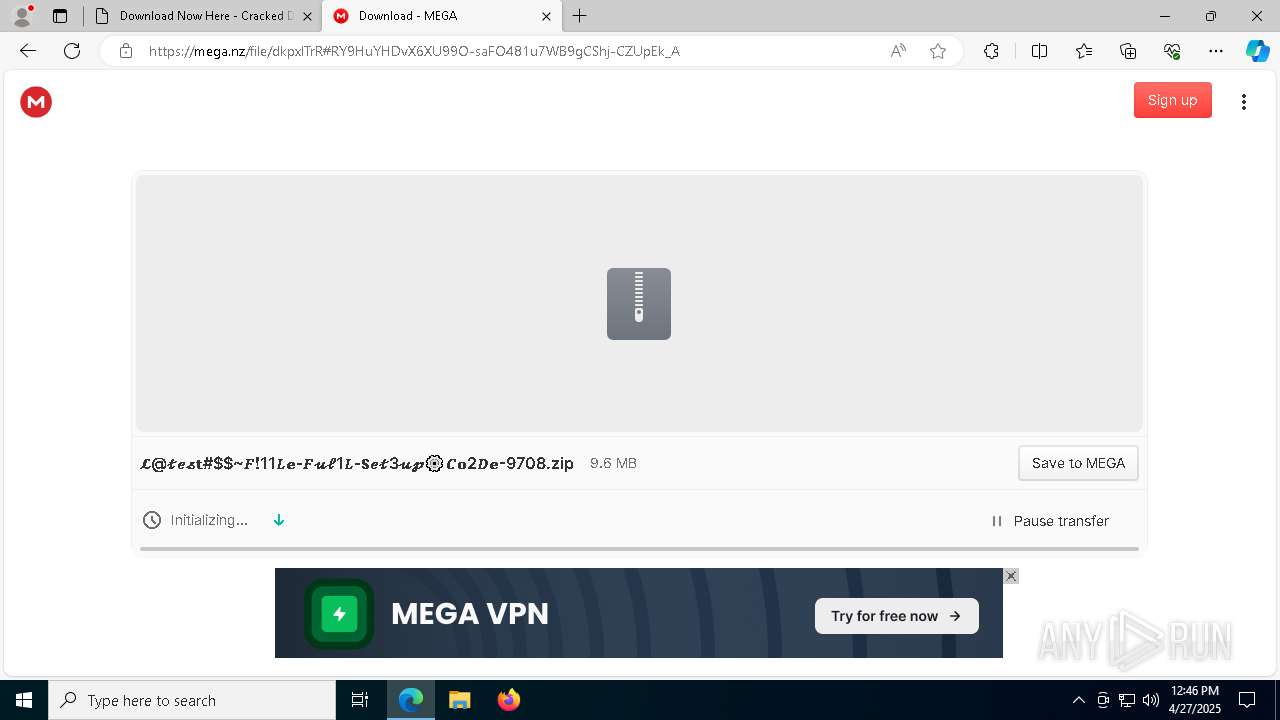
| URL: | https://bicfic.net/download-now-here/ |
| Full analysis: | https://app.any.run/tasks/258cb75e-3efd-4275-81c9-e41e8e14e455 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 27, 2025, 12:45:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
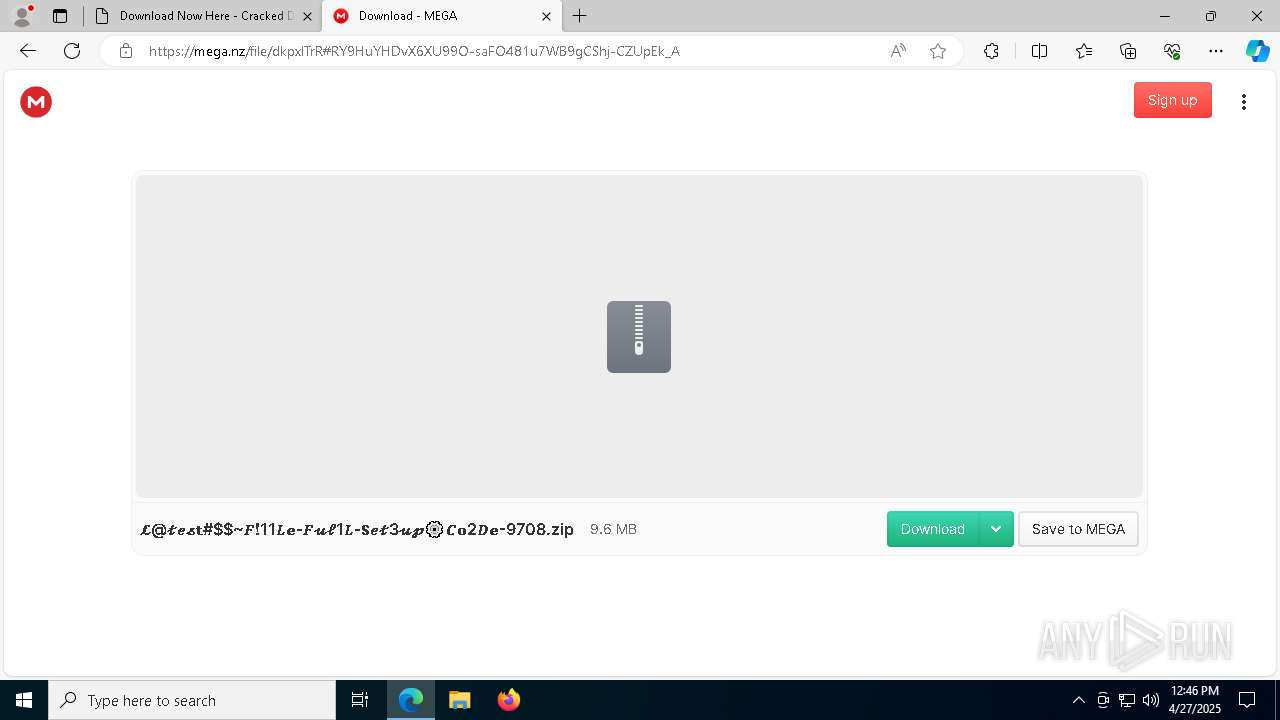
| MD5: | AB82FC09F814DDDDCC93E296D7D5328A |
| SHA1: | FF3BE881D3EEFCBB1C557D14F7C1F4B7D089CE38 |
| SHA256: | 50D1D34BEBF4051163B0FF0E4BB11FF496C6091FECA3B52FD3FB35E6BCB25F48 |
| SSDEEP: | 3:N8VLLAs8JLb:2VgJ |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7432)
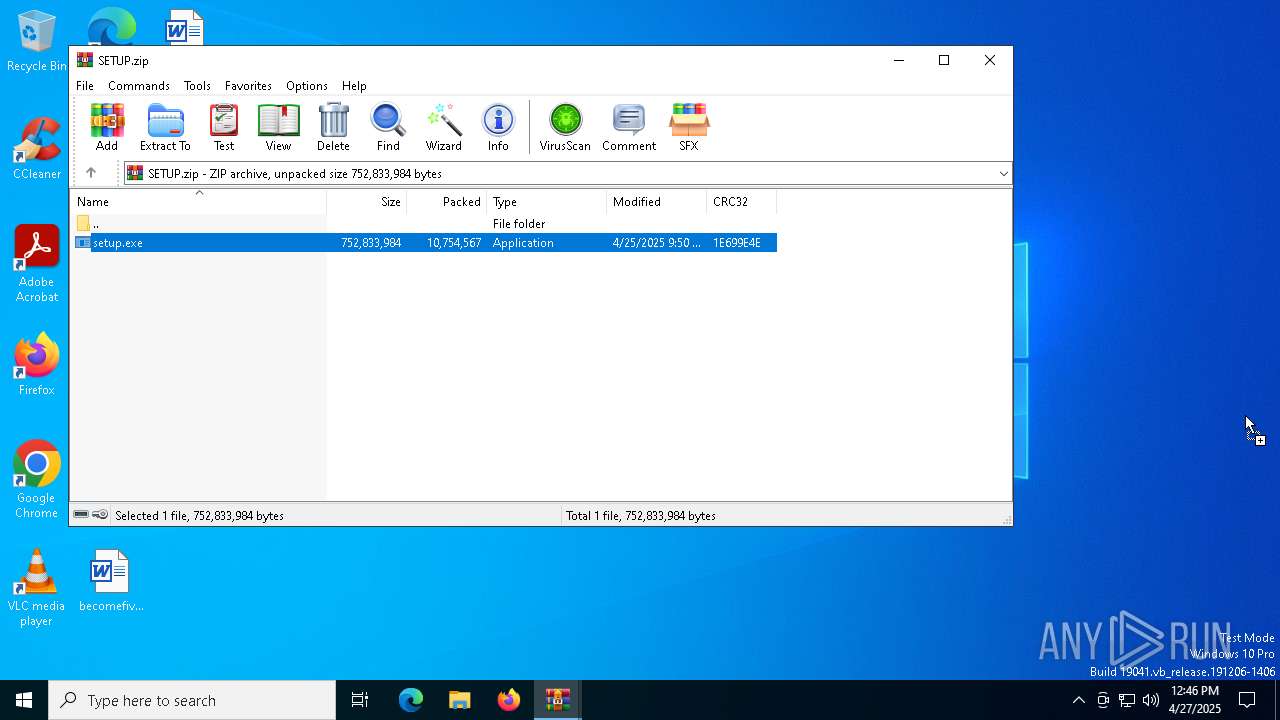
Executing a file with an untrusted certificate
- setup.exe (PID: 7596)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
LUMMA mutex has been found
- setup.exe (PID: 7596)
Actions looks like stealing of personal data
- setup.exe (PID: 7596)
Steals credentials from Web Browsers
- setup.exe (PID: 7596)
LUMMA has been detected (YARA)
- setup.exe (PID: 7596)
Changes the autorun value in the registry
- reg.exe (PID: 2980)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1116)
- WinRAR.exe (PID: 1128)
Application launched itself
- WinRAR.exe (PID: 1128)
- WinRAR.exe (PID: 1116)
Executable content was dropped or overwritten
- setup.exe (PID: 7596)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Multiple wallet extension IDs have been found
- setup.exe (PID: 7596)
Starts CMD.EXE for commands execution
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8004)
Connects to unusual port
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Searches for installed software
- setup.exe (PID: 7596)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Found regular expressions for crypto-addresses (YARA)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
INFO
Reads Environment values
- identity_helper.exe (PID: 1628)
- identity_helper.exe (PID: 4008)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7200)
Application launched itself
- msedge.exe (PID: 7200)
- msedge.exe (PID: 7252)
Checks supported languages
- identity_helper.exe (PID: 1628)
- identity_helper.exe (PID: 4008)
- setup.exe (PID: 7596)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Reads the computer name
- identity_helper.exe (PID: 4008)
- setup.exe (PID: 7596)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
- identity_helper.exe (PID: 1628)
Manual execution by a user
- setup.exe (PID: 7596)
Reads the software policy settings
- setup.exe (PID: 7596)
- slui.exe (PID: 5728)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Create files in a temporary directory
- setup.exe (PID: 7596)
The sample compiled with english language support
- setup.exe (PID: 7596)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
- msedge.exe (PID: 5452)
Creates files in the program directory
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Drops encrypted JS script (Microsoft Script Encoder)
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Reads the machine GUID from the registry
- 2W12DZ08M2XT58K8KGZGQHKZYFY.exe (PID: 7268)
Executable content was dropped or overwritten
- msedge.exe (PID: 5452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
80
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5360 --field-trial-handle=2444,i,3408334637988764726,6990178192498207955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2820 --field-trial-handle=2360,i,8414923693248377091,15617776652703935935,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5740 --field-trial-handle=2444,i,3408334637988764726,6990178192498207955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
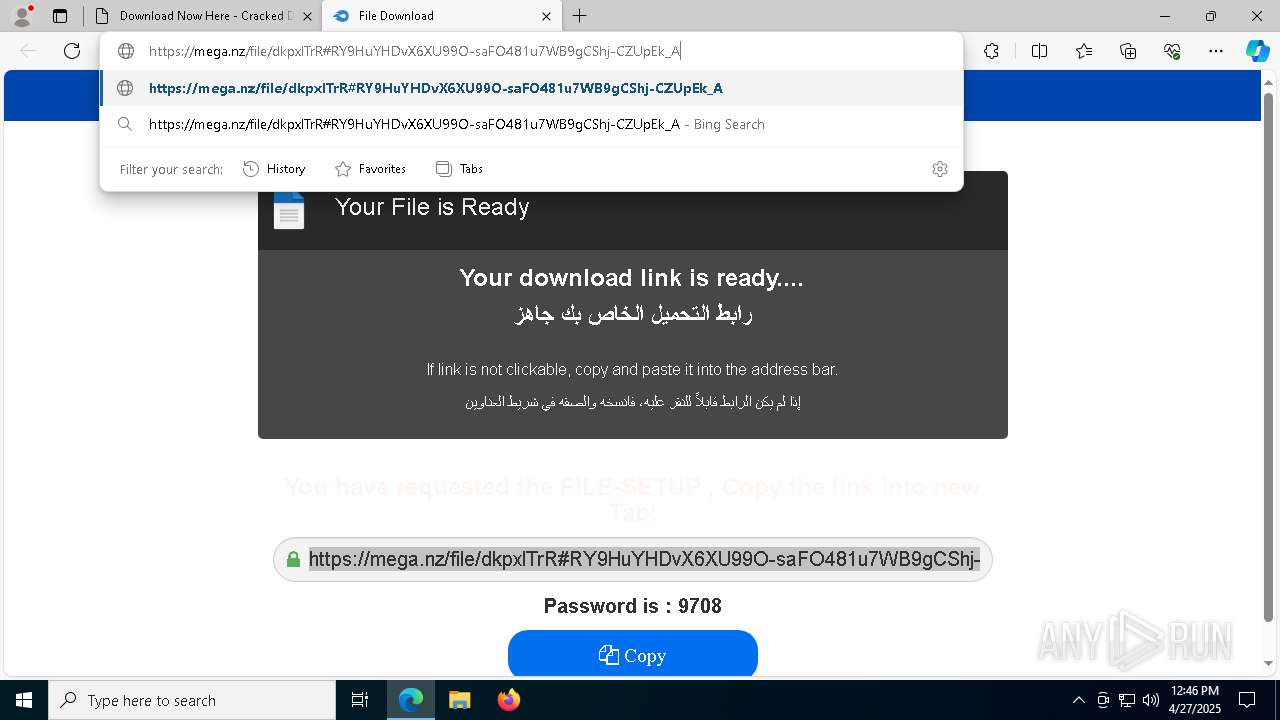
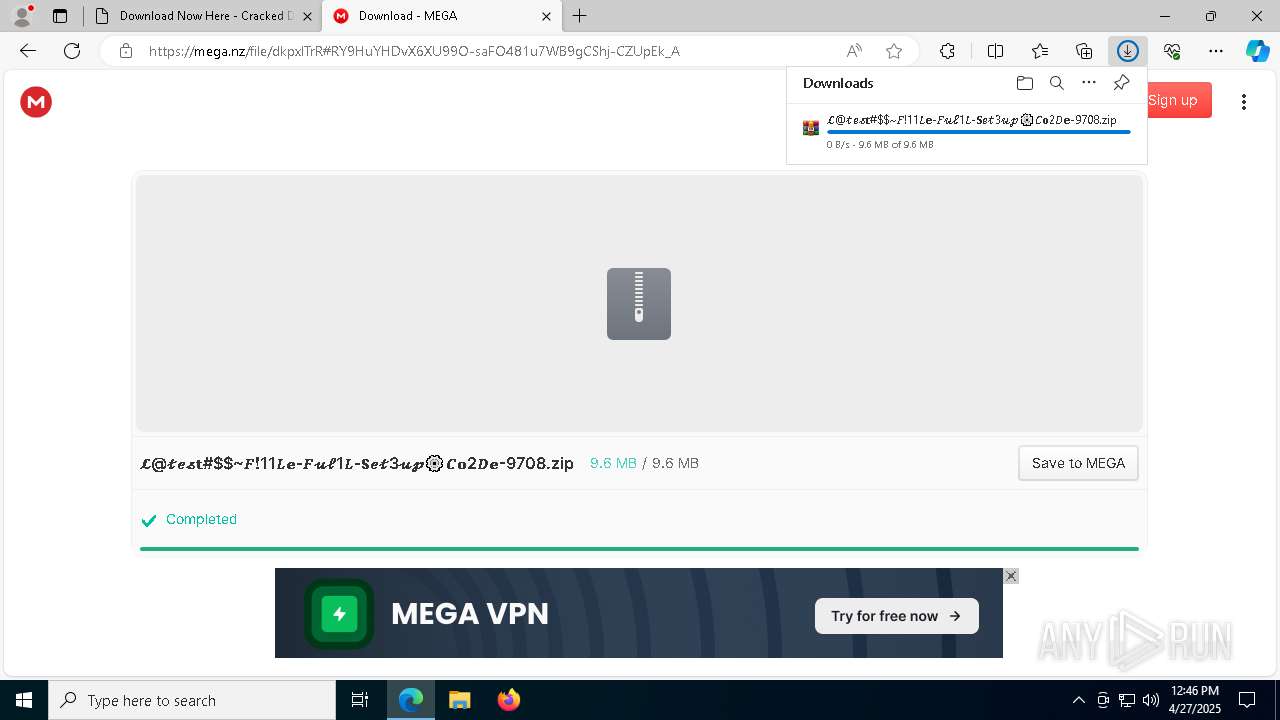
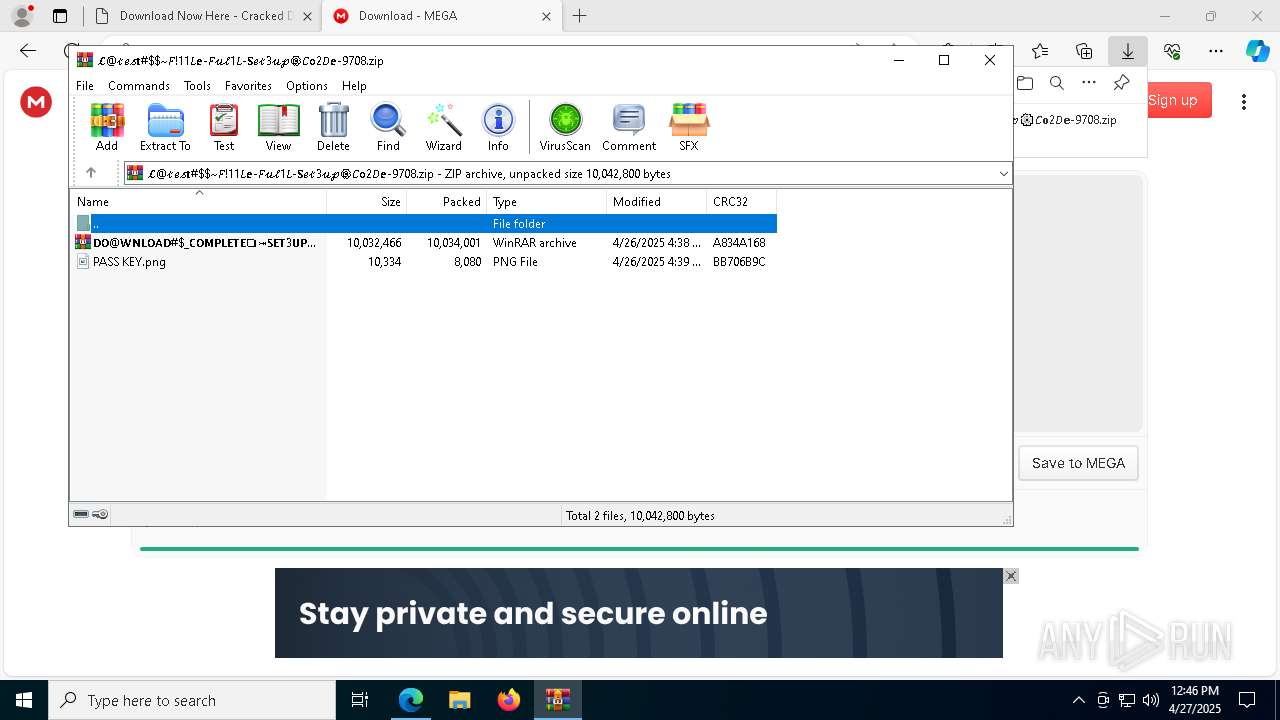
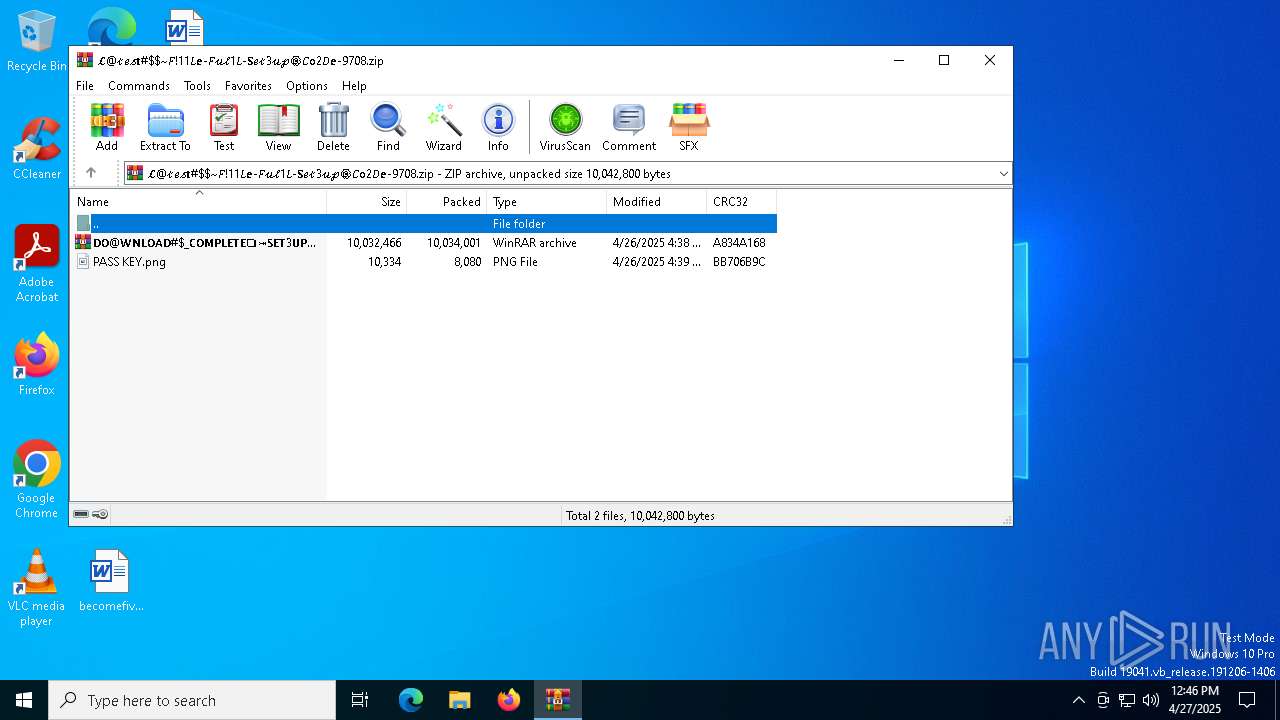
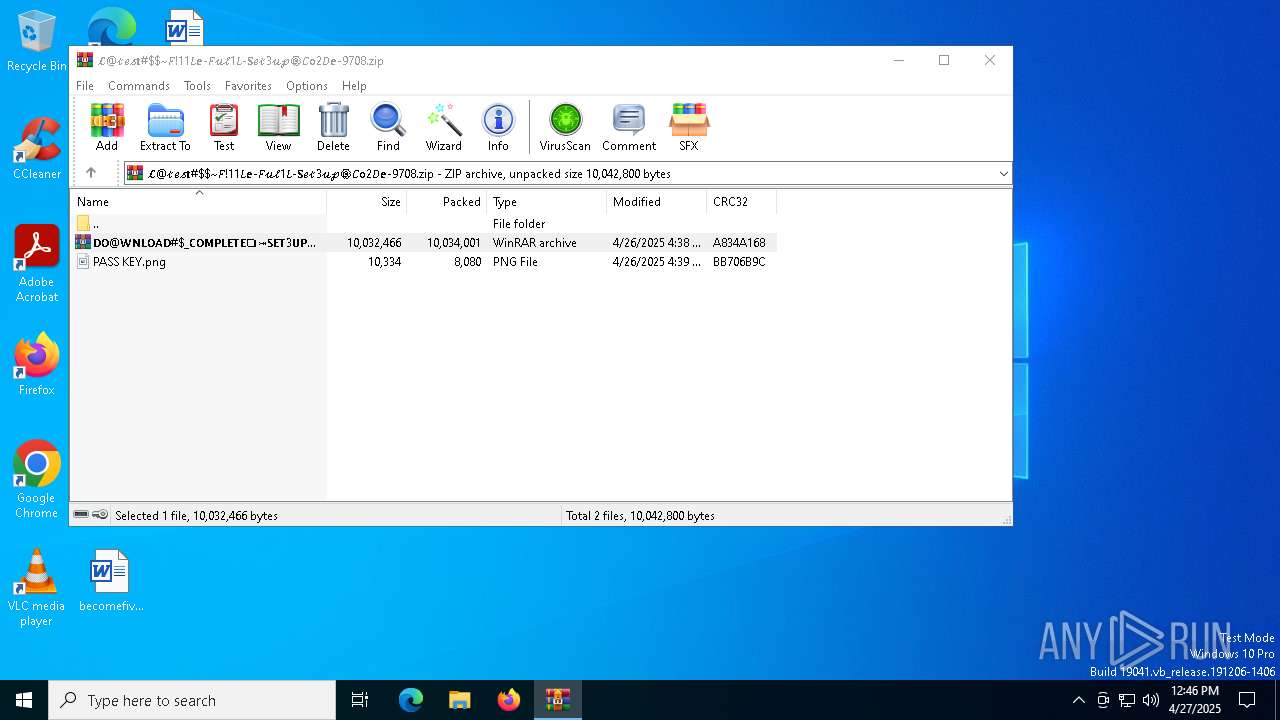
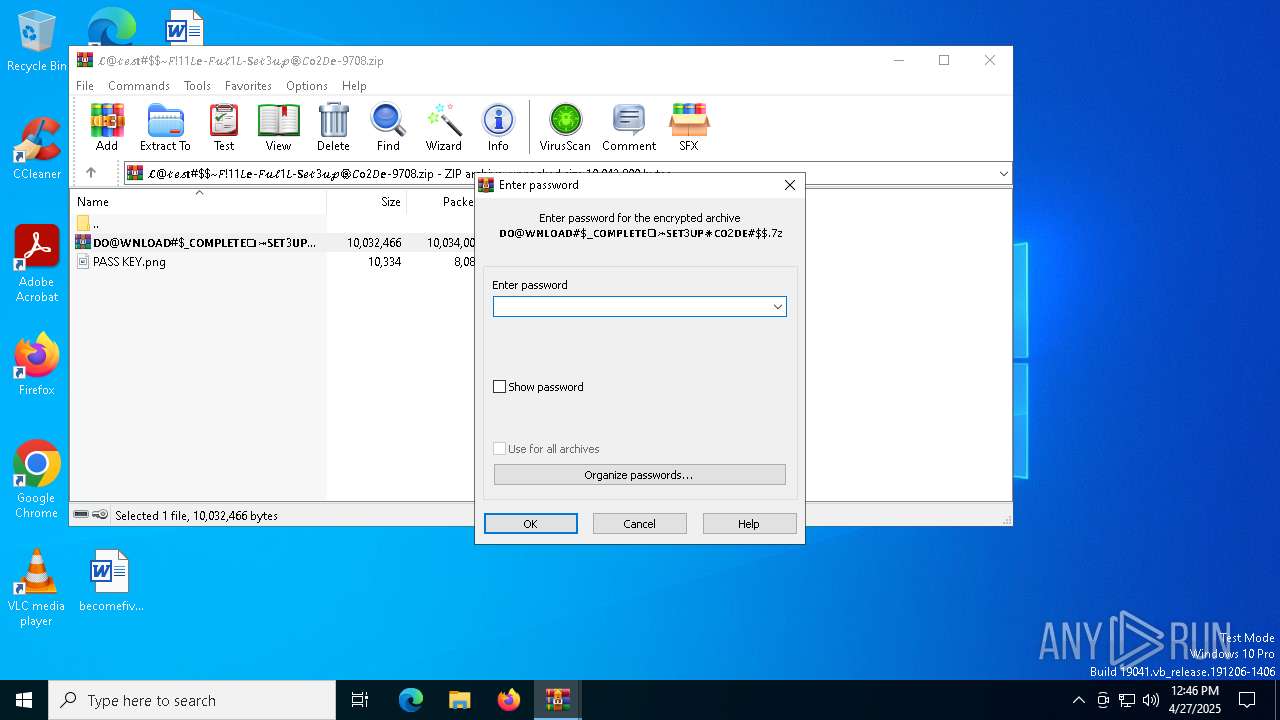
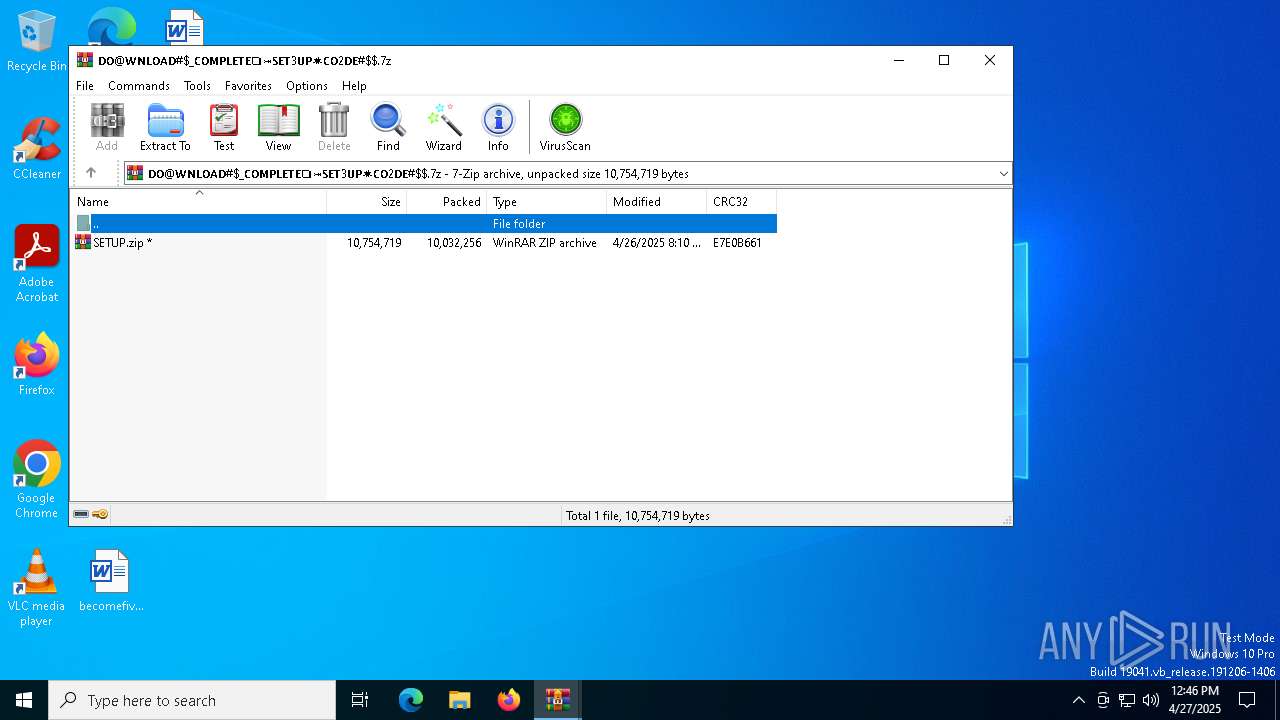
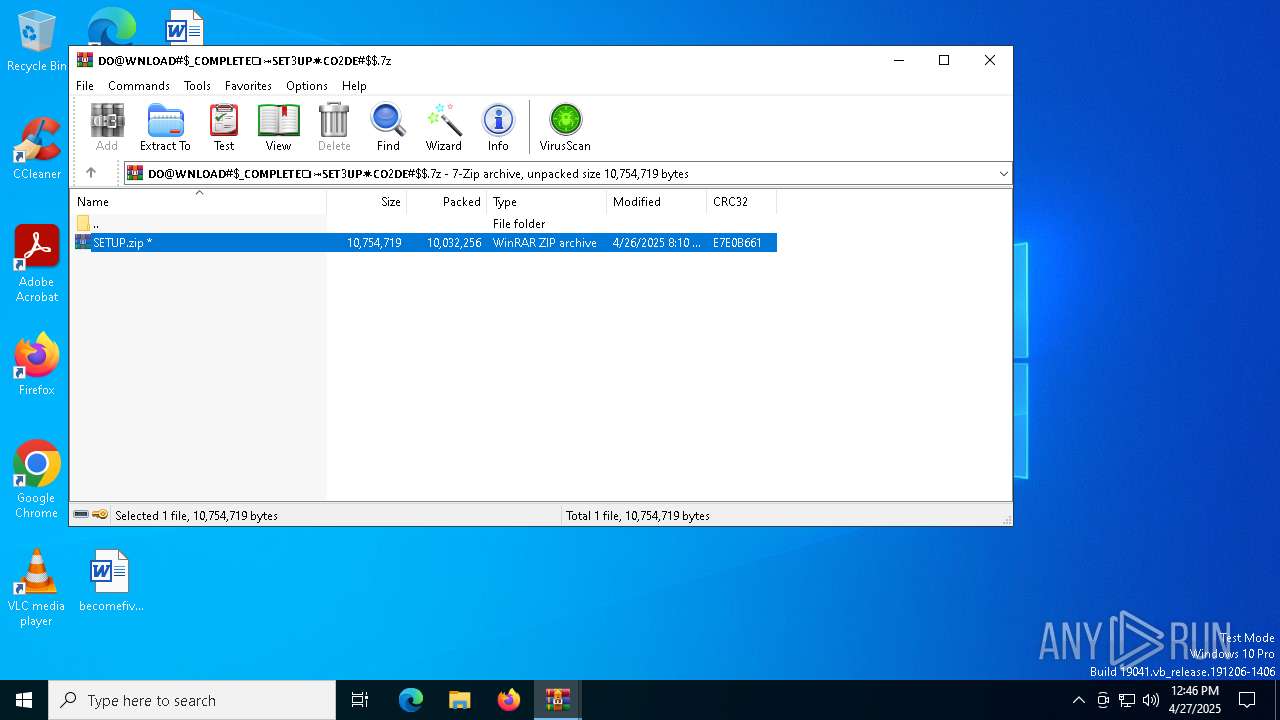
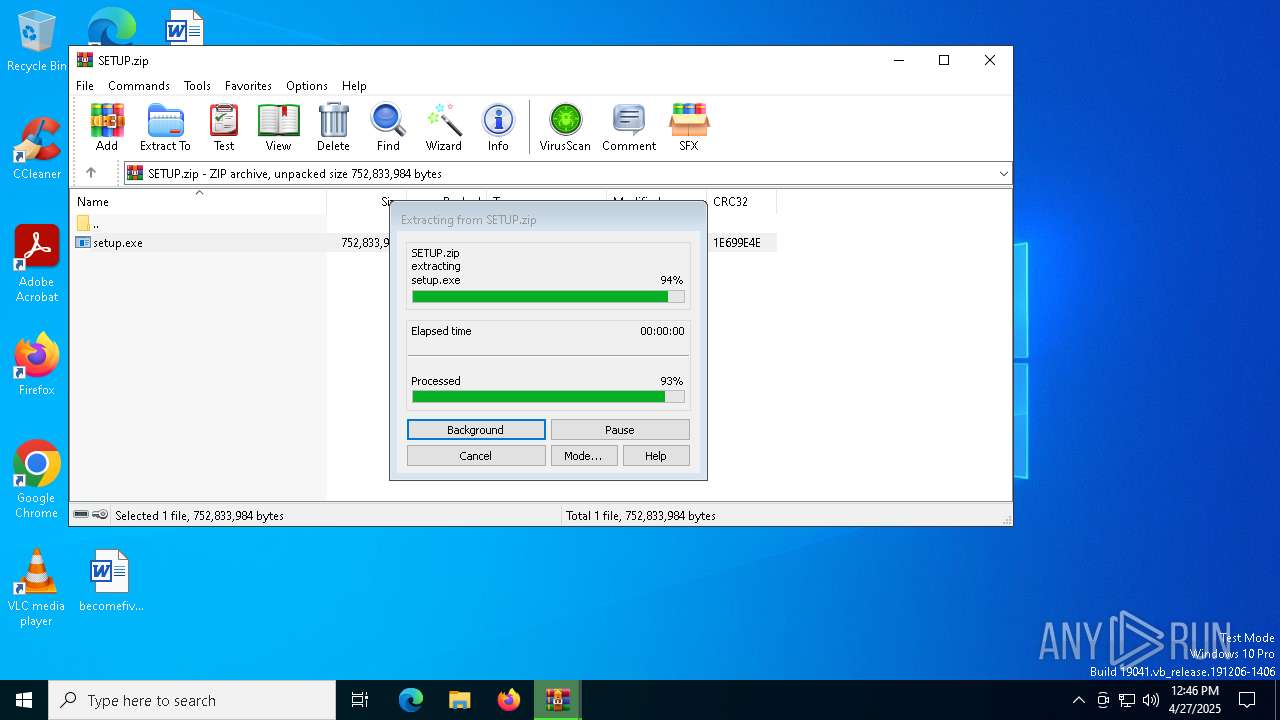
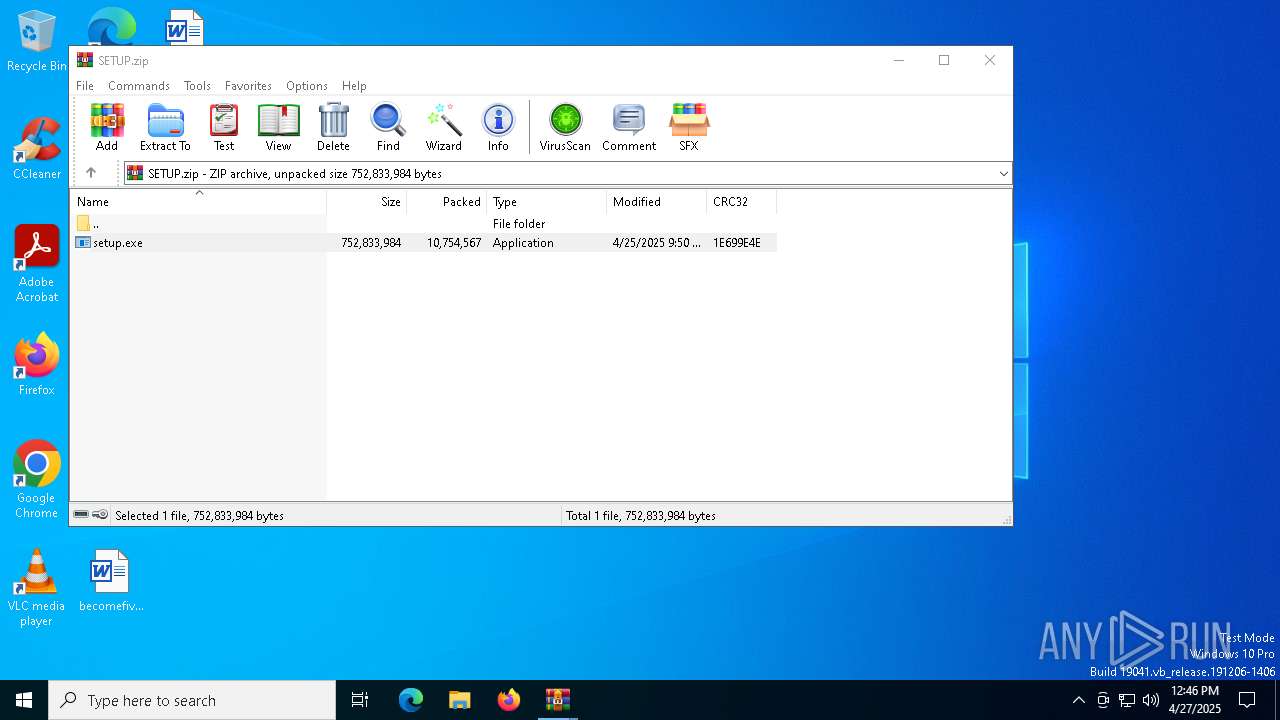
| 1116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\𝓛@𝓉𝑒𝓈𝐭#$~𝐹!11𝐿𝐞-𝐹𝓊𝓁1𝐿-𝐒𝑒𝓉3𝓊𝓅⚙️𝐶𝐨2𝐷𝐞-9708.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
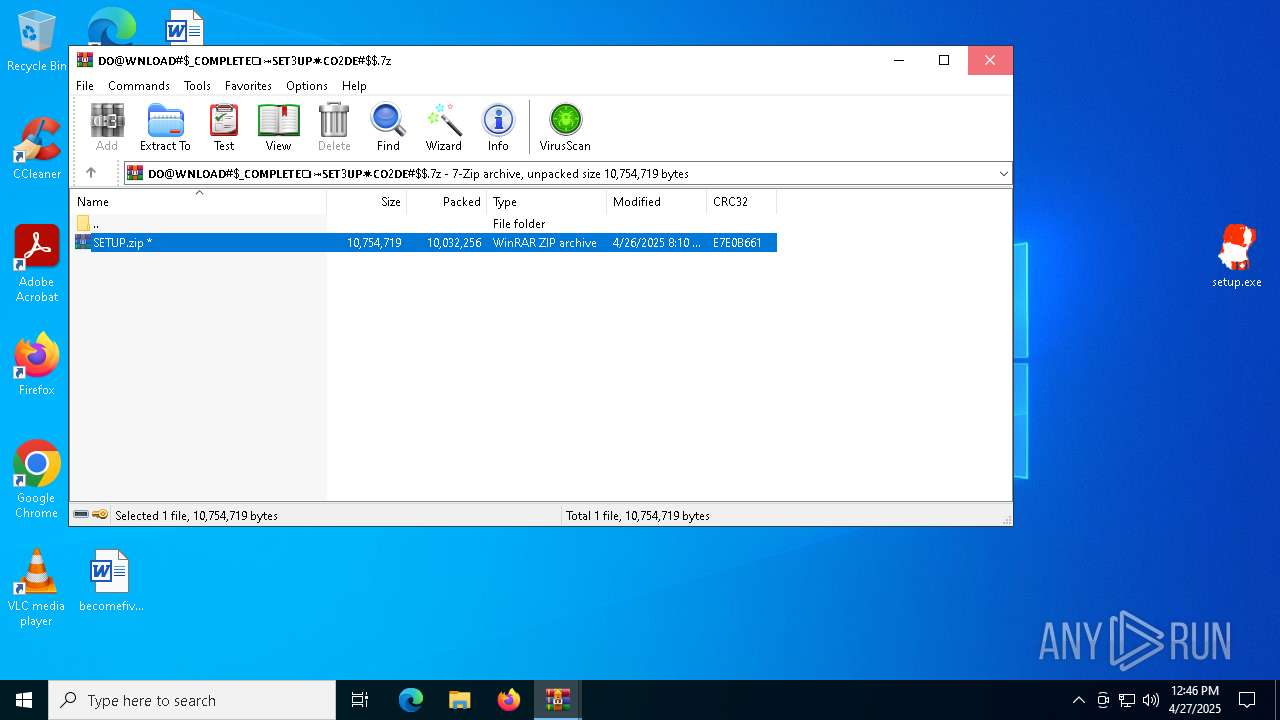
| 1128 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa1116.30349\𝗗𝗢@𝗪𝗡𝗟𝗢𝗔𝗗#$_𝗖𝗢𝗠𝗣𝗟𝗘𝗧𝗘❏⤖𝗦𝗘𝗧3𝗨𝗣✷𝗖𝗢2𝗗𝗘#$.7z | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7220 --field-trial-handle=2444,i,3408334637988764726,6990178192498207955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6192 --field-trial-handle=2444,i,3408334637988764726,6990178192498207955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1492 --field-trial-handle=2444,i,3408334637988764726,6990178192498207955,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4924 --field-trial-handle=2360,i,8414923693248377091,15617776652703935935,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 885
Read events
19 747
Write events
120
Delete events
18
Modification events
| (PID) Process: | (5364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (5364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (5364) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
19
Suspicious files
384
Text files
120
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be41.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be31.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10be31.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be60.TMP | — | |
MD5:— | SHA256:— | |||
| 7200 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
126
DNS requests
130
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.16.155:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
7940 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746049805&P2=404&P3=2&P4=HqewrGiWVw5xrGUEoIIqadGKo6eHyRzyqFJoywLYFgu37dVAluWdoJKtUEap%2fSoAbJ2H9qblwZoInGSeFJdqNw%3d%3d | US | — | — | whitelisted |
7940 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746049805&P2=404&P3=2&P4=HqewrGiWVw5xrGUEoIIqadGKo6eHyRzyqFJoywLYFgu37dVAluWdoJKtUEap%2fSoAbJ2H9qblwZoInGSeFJdqNw%3d%3d | US | binary | 1.09 Kb | whitelisted |
6656 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6656 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
7940 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746049805&P2=404&P3=2&P4=HqewrGiWVw5xrGUEoIIqadGKo6eHyRzyqFJoywLYFgu37dVAluWdoJKtUEap%2fSoAbJ2H9qblwZoInGSeFJdqNw%3d%3d | US | binary | 20.3 Kb | whitelisted |
7940 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1746049805&P2=404&P3=2&P4=HqewrGiWVw5xrGUEoIIqadGKo6eHyRzyqFJoywLYFgu37dVAluWdoJKtUEap%2fSoAbJ2H9qblwZoInGSeFJdqNw%3d%3d | US | binary | 1.57 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.16.155:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7432 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
bicfic.net |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7432 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7432 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
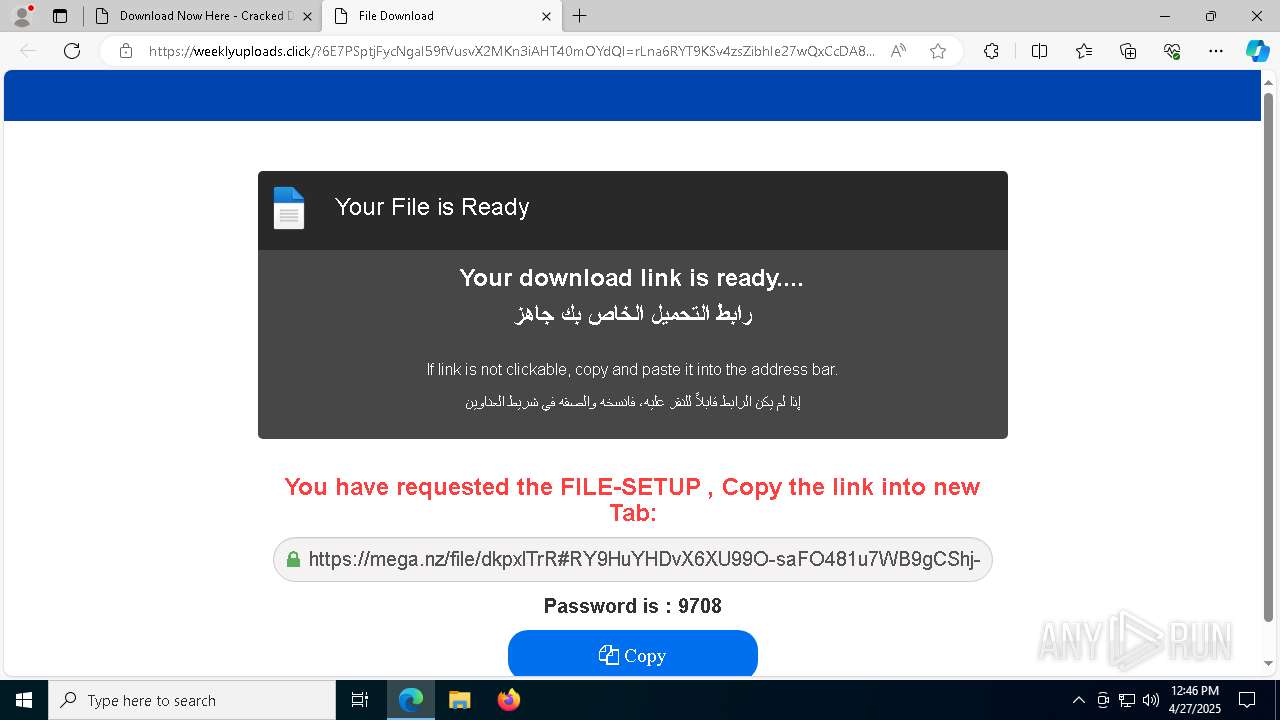
7432 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7432 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7432 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7432 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7432 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (weeklyuploads .click) |
7432 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
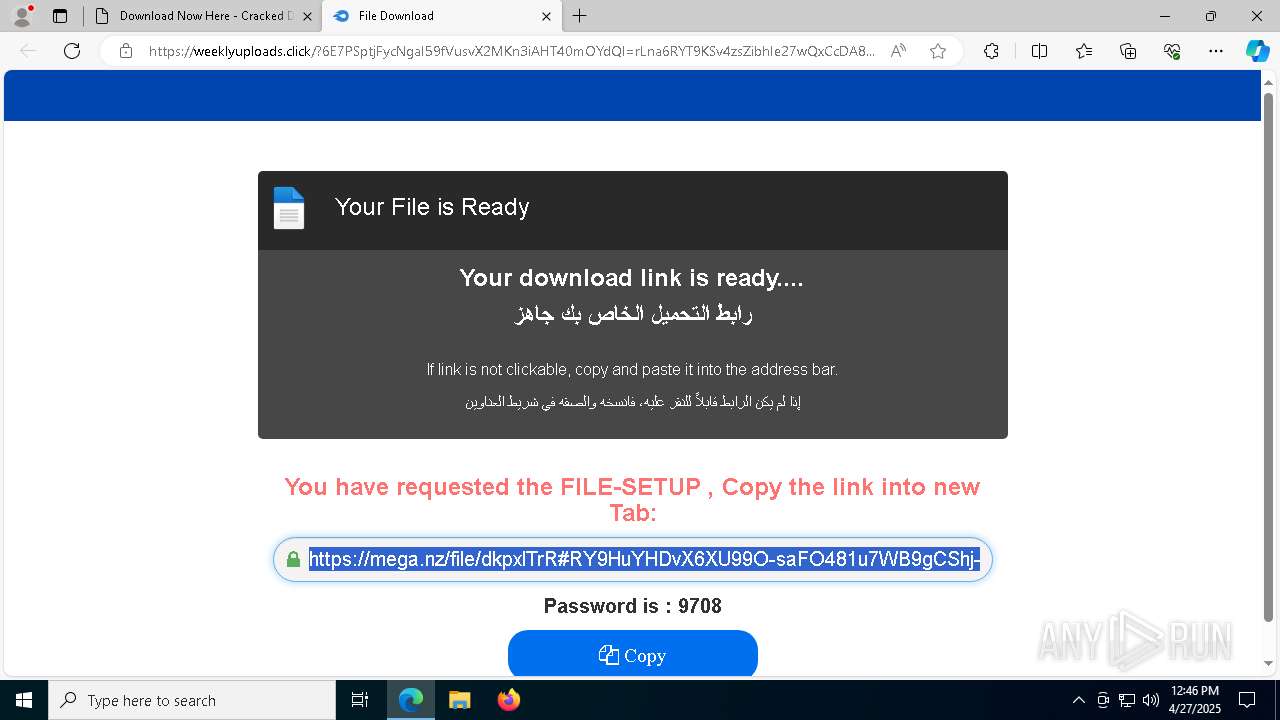
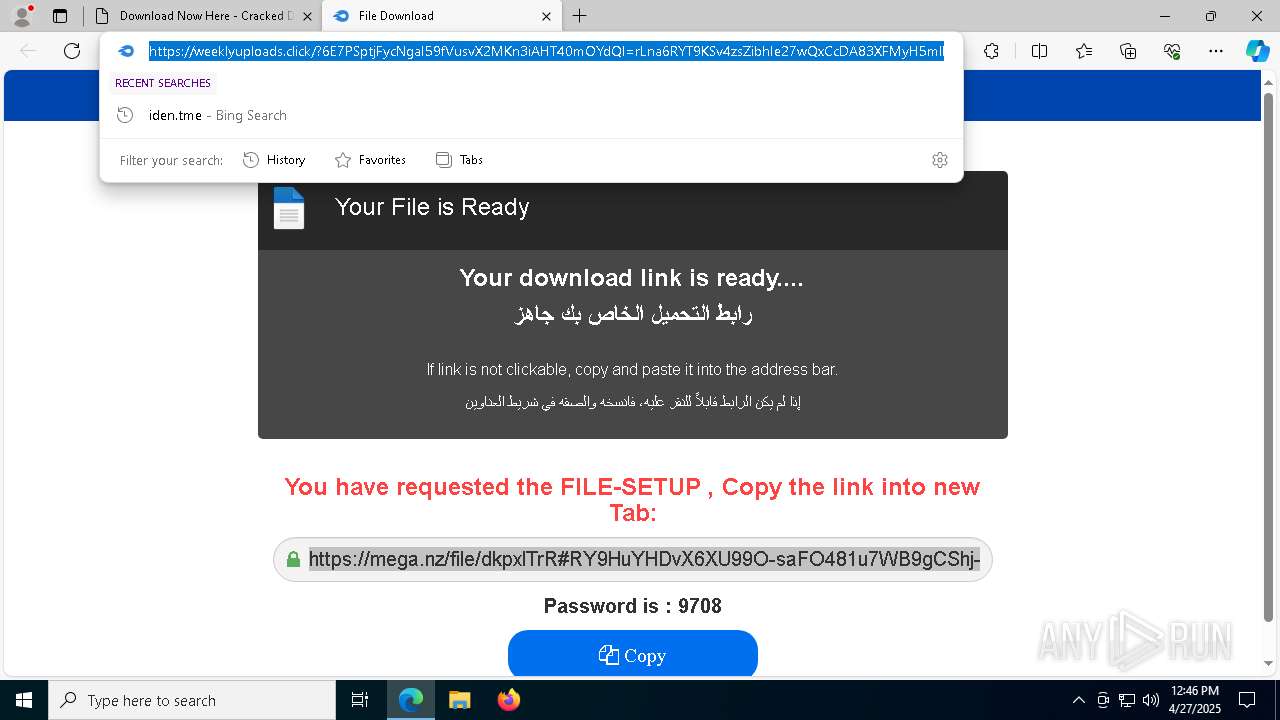
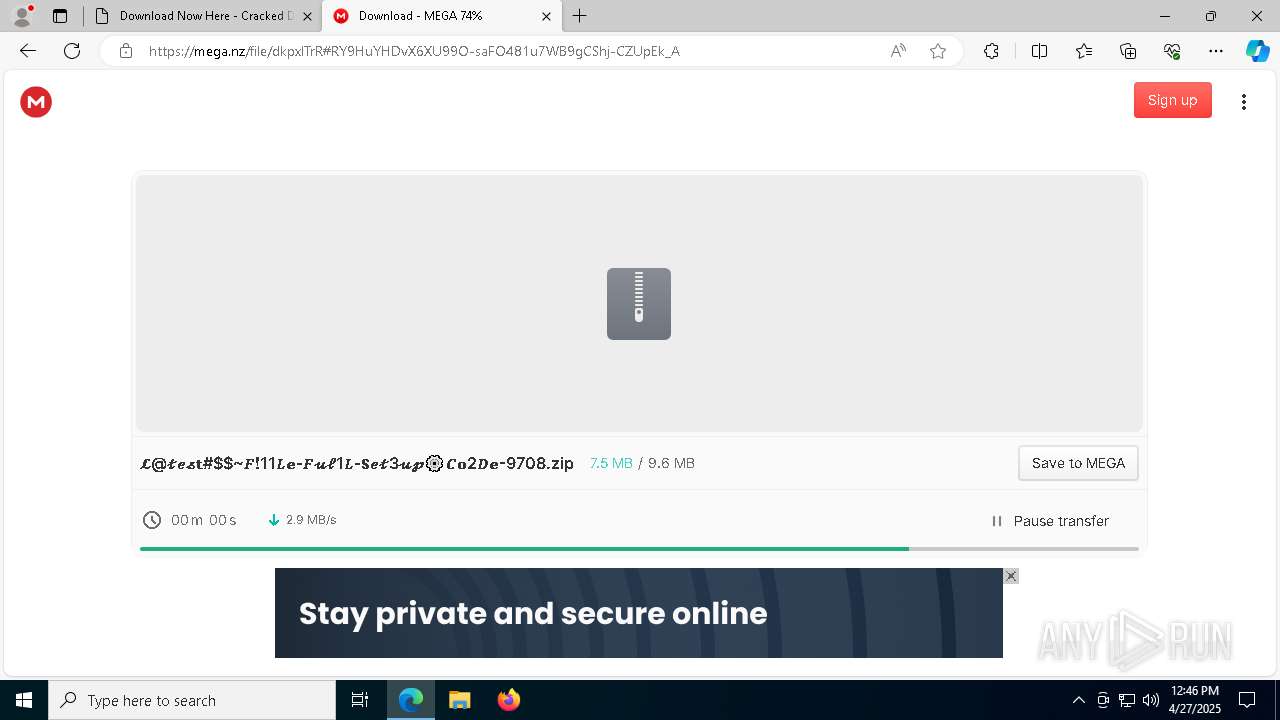
7432 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7432 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |