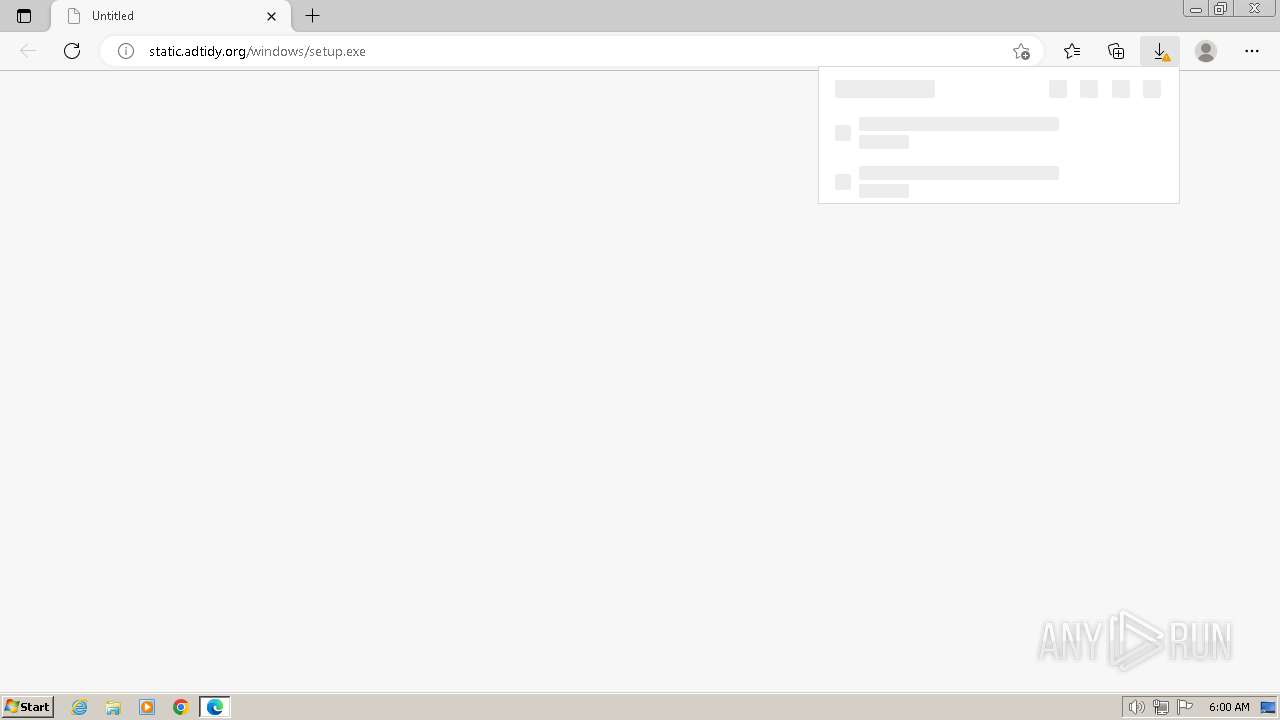
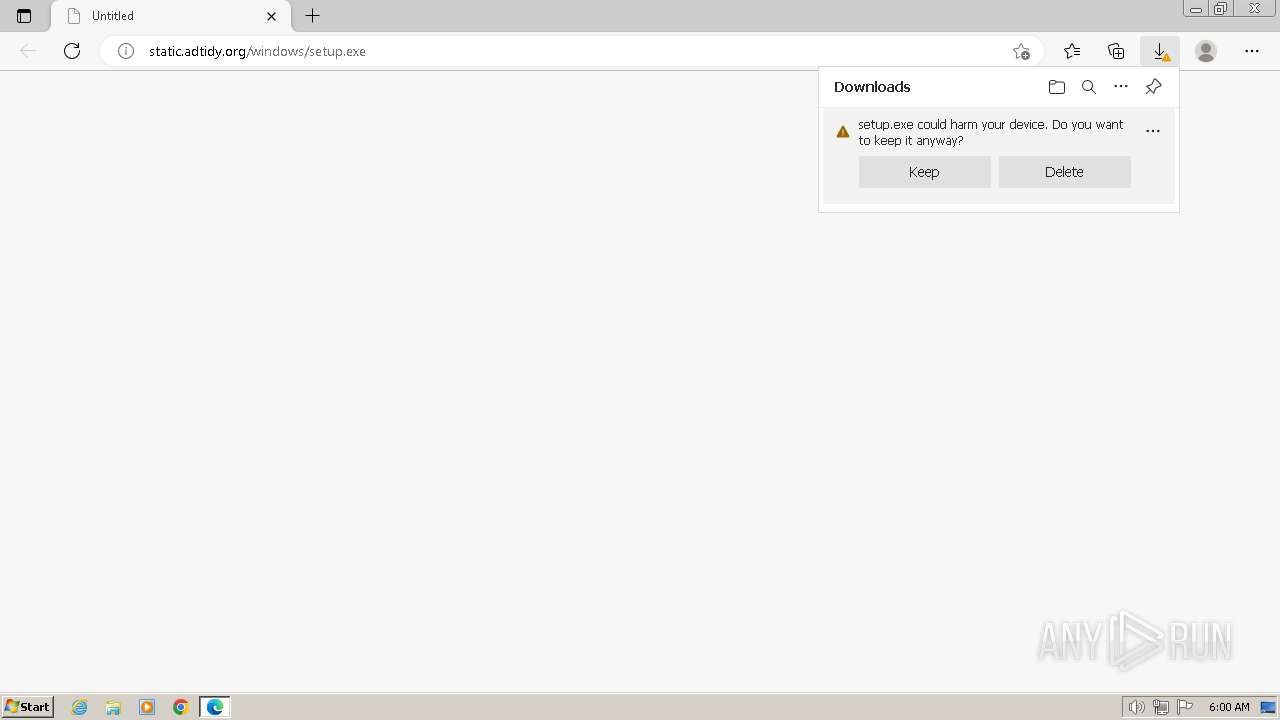
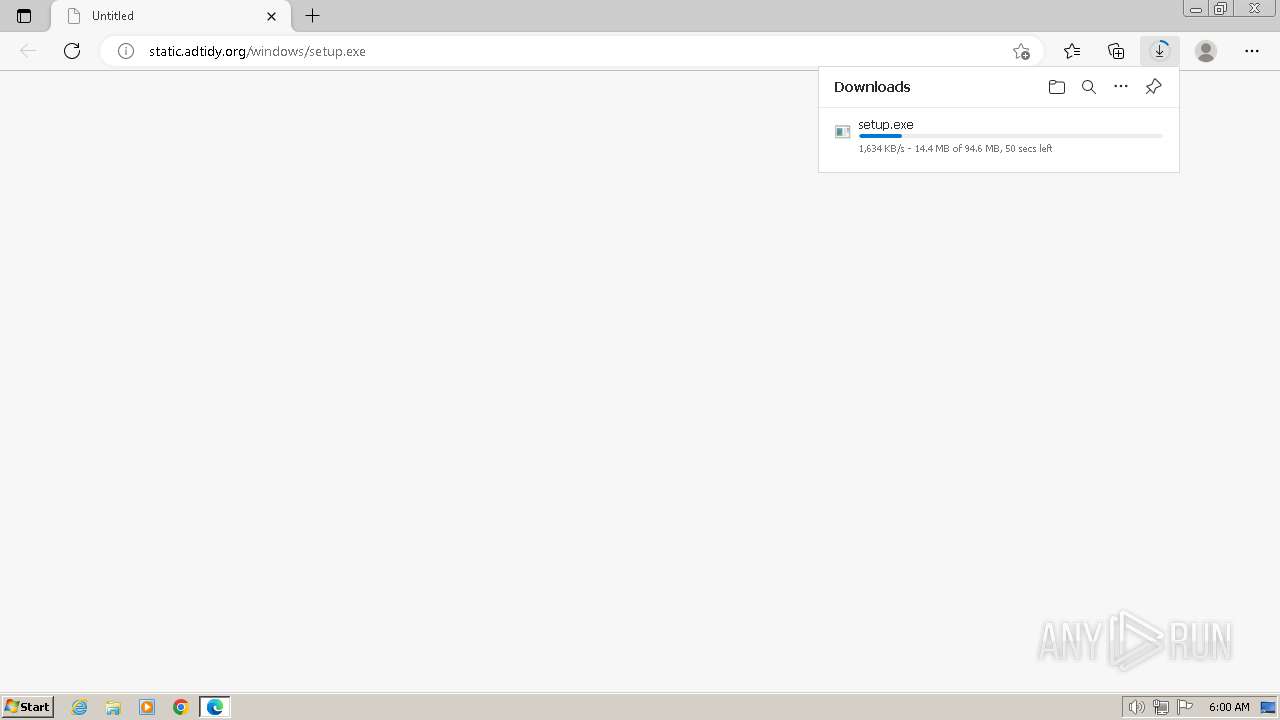
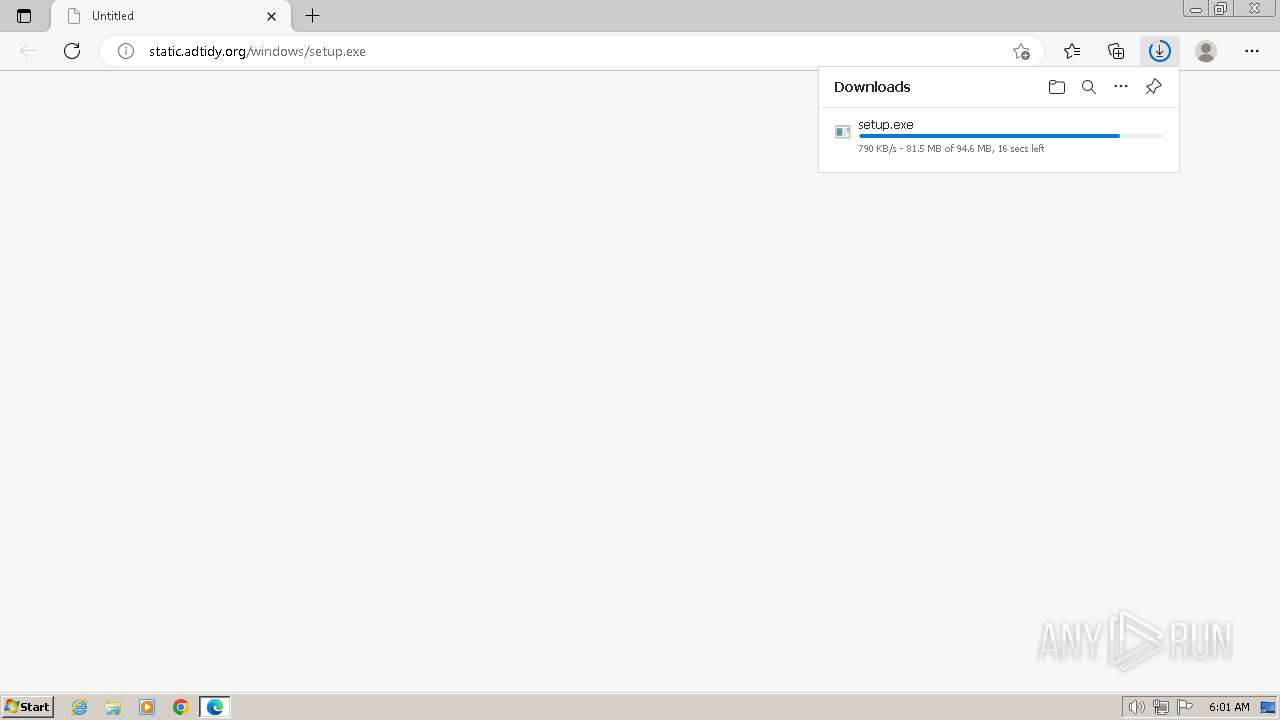
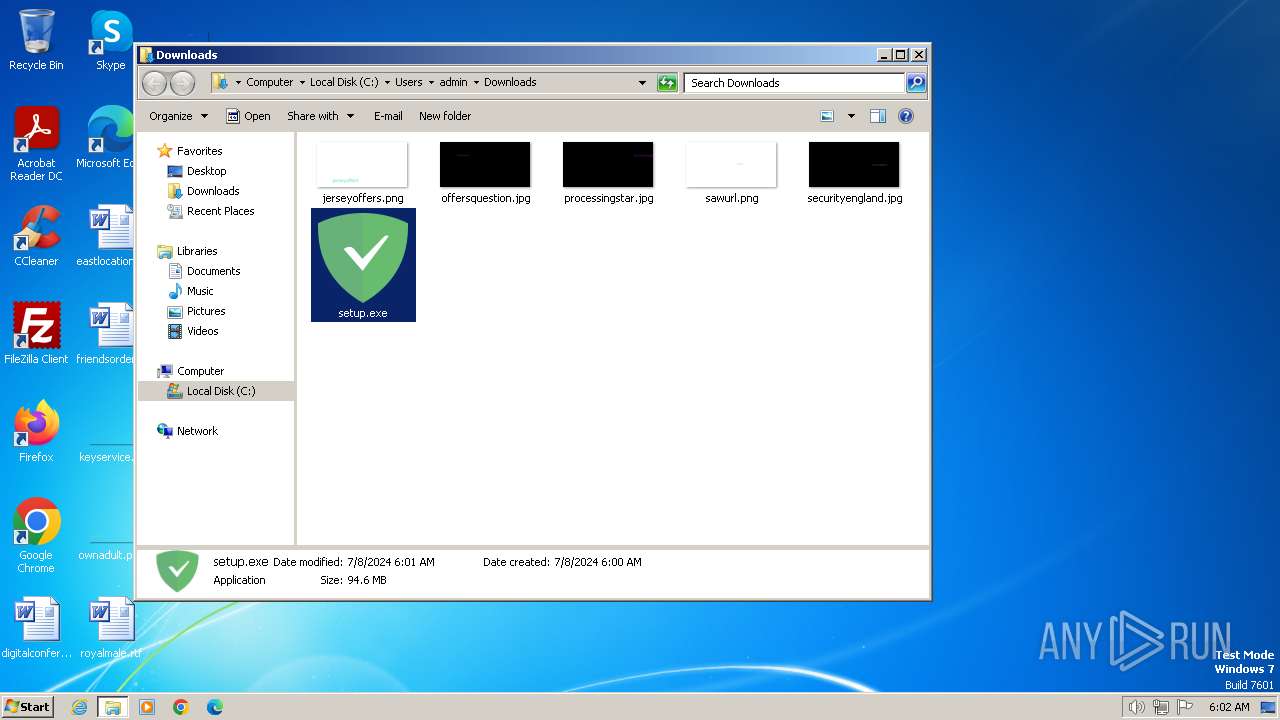
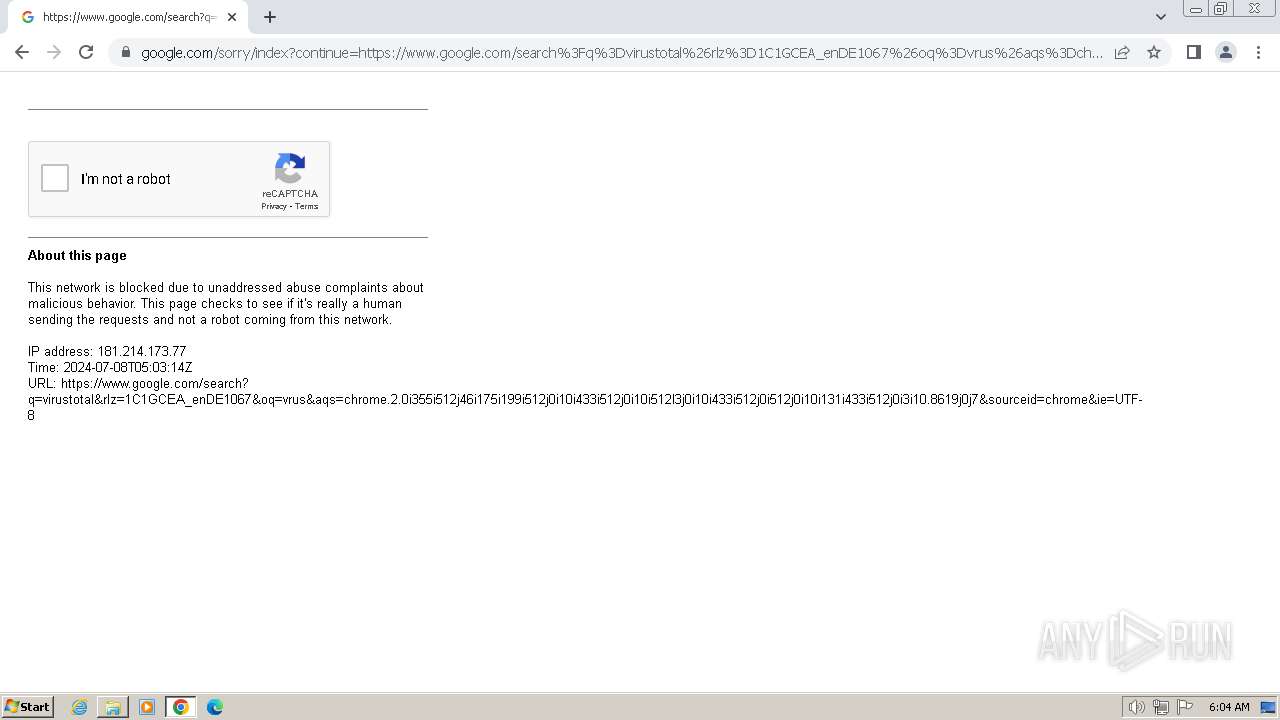
| URL: | static.adtidy.org/windows/setup.exe |
| Full analysis: | https://app.any.run/tasks/2be21e96-9095-42d7-8966-7e6166d5ad26 |
| Verdict: | Malicious activity |
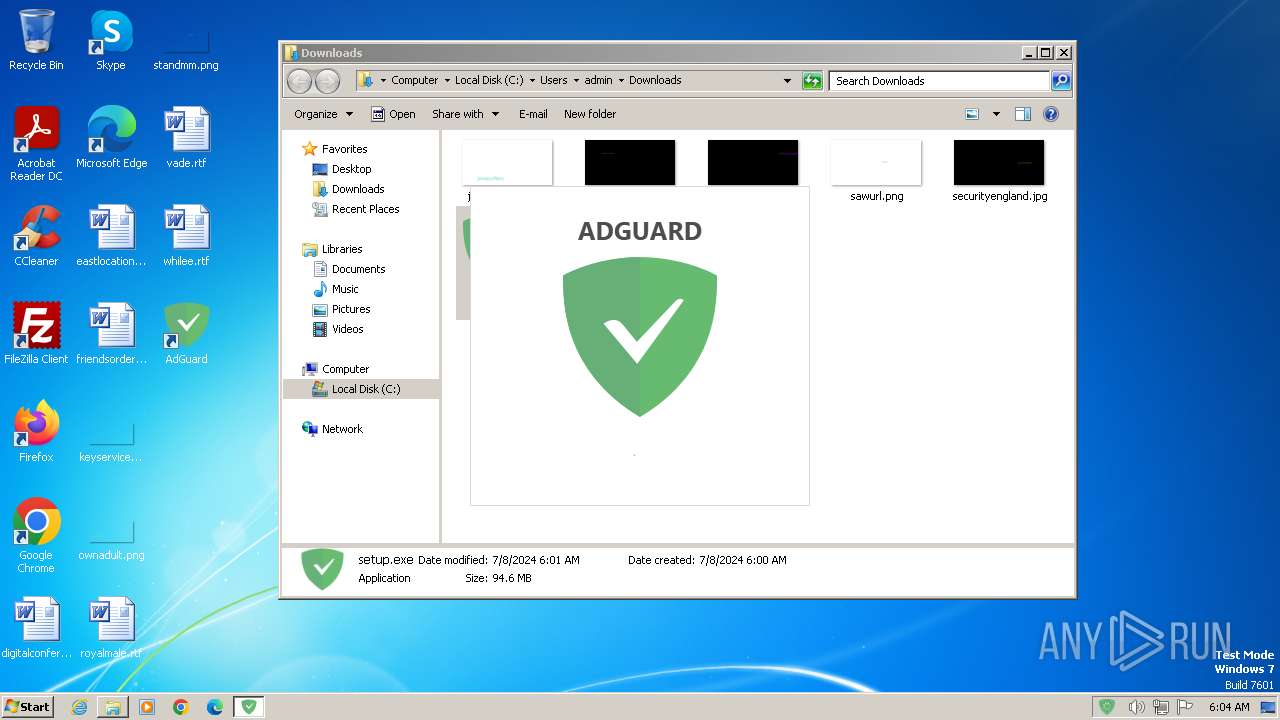
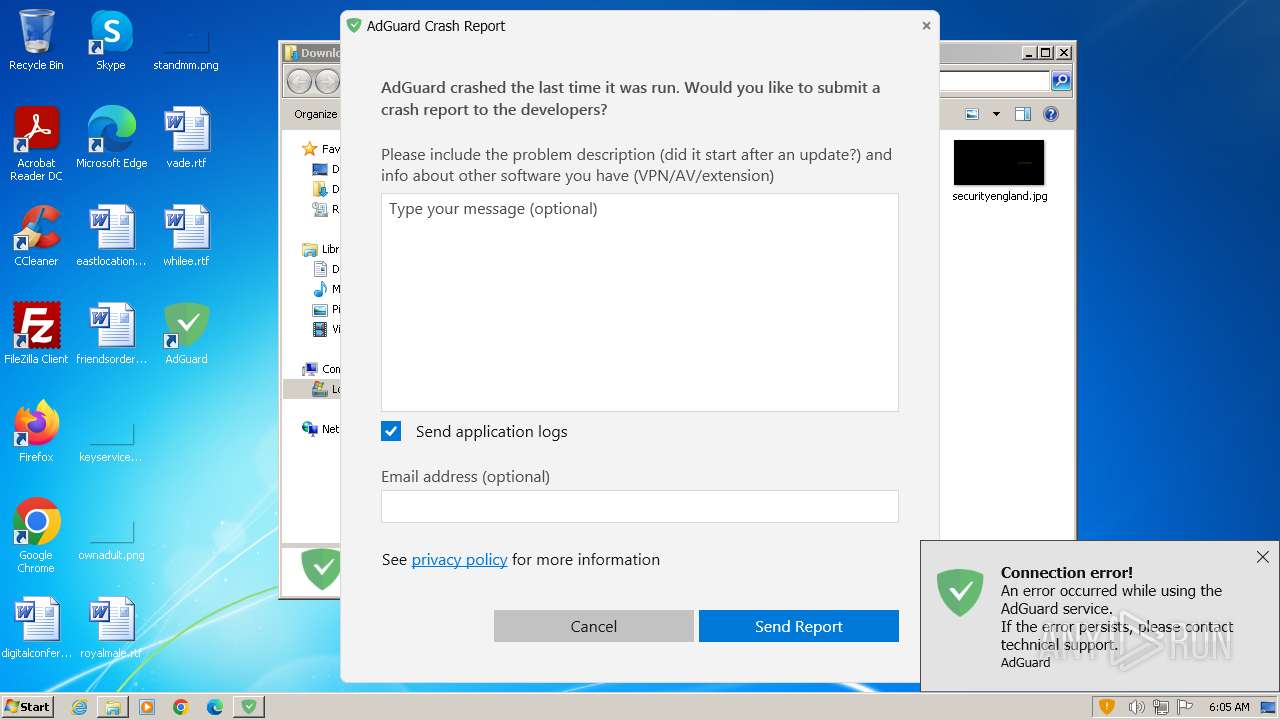
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | July 08, 2024, 05:00:01 |
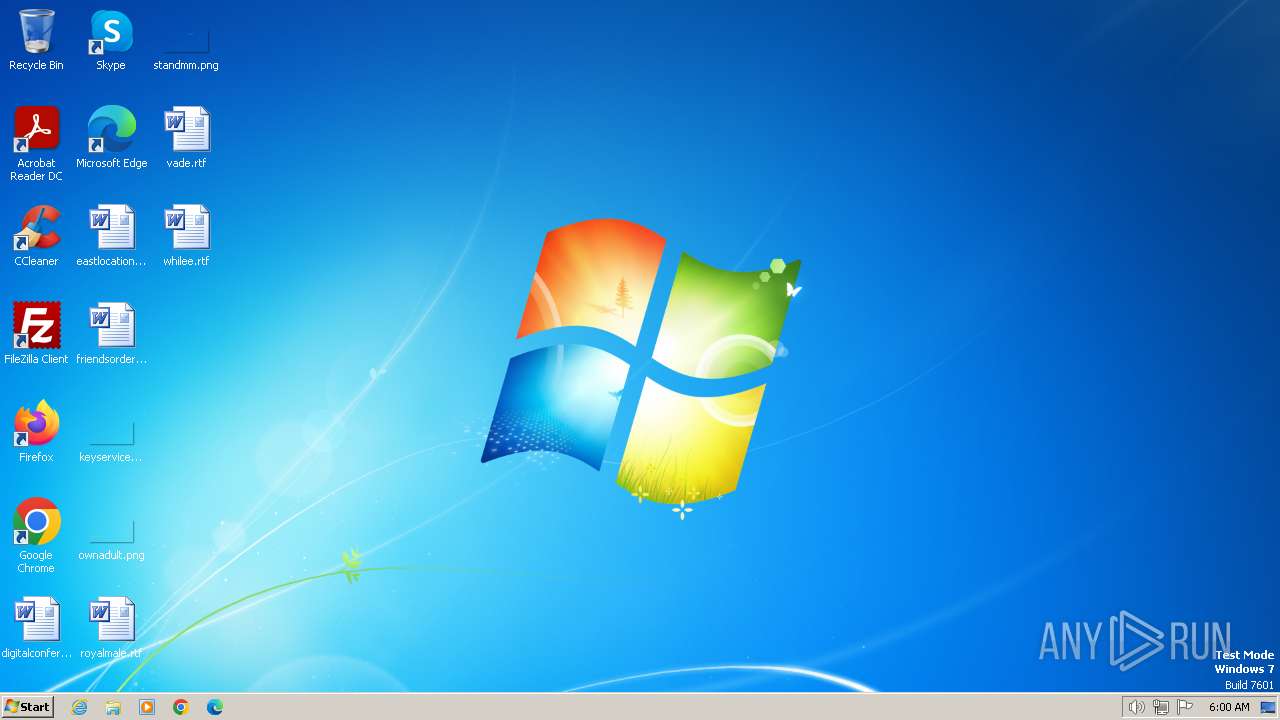
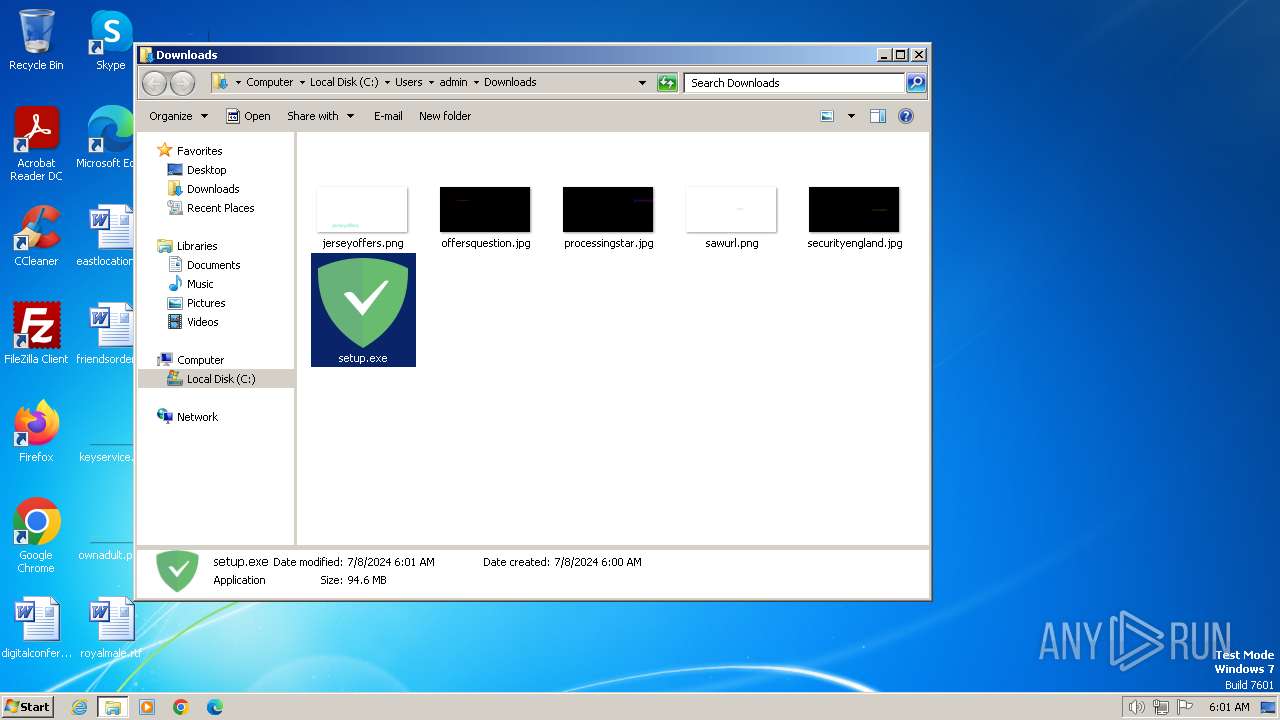
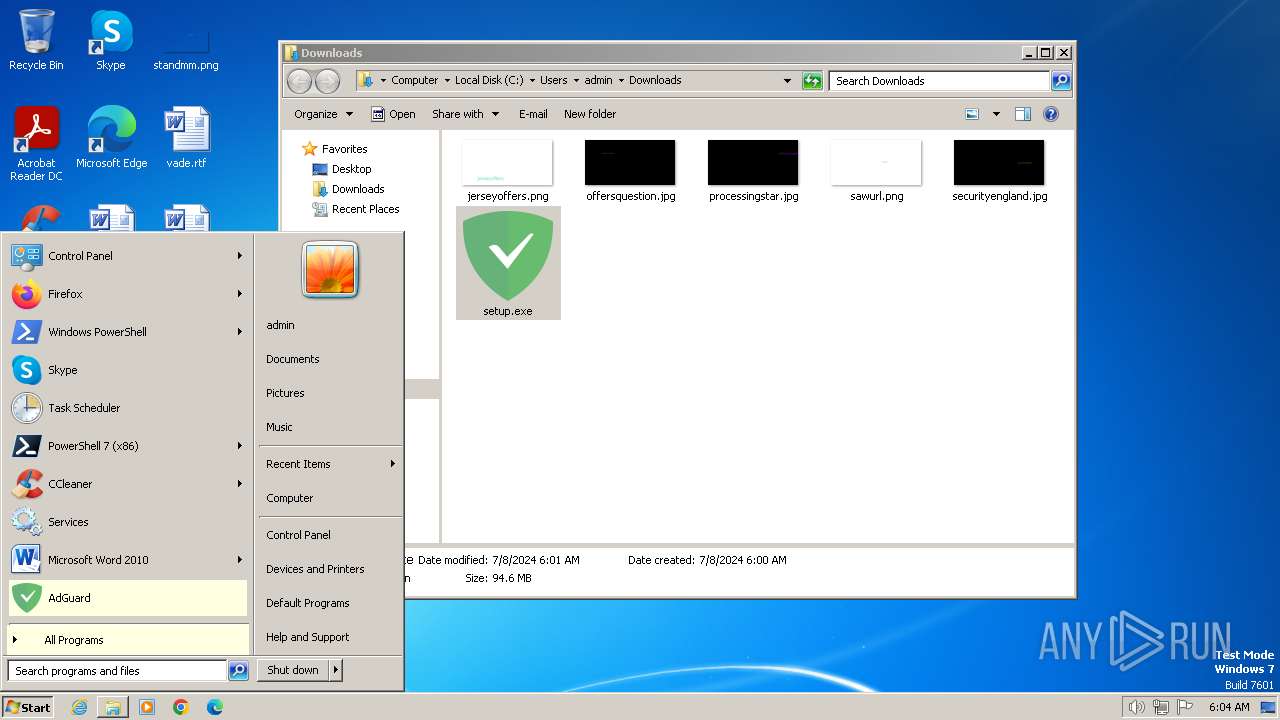
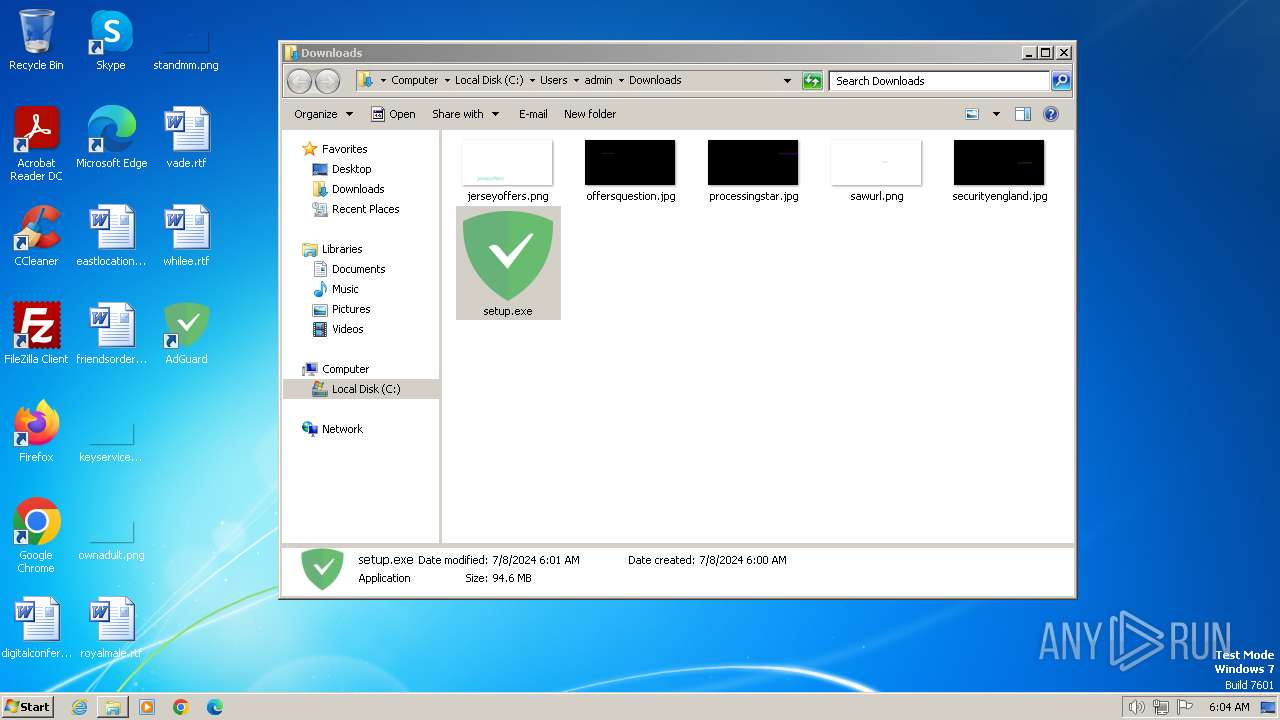
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
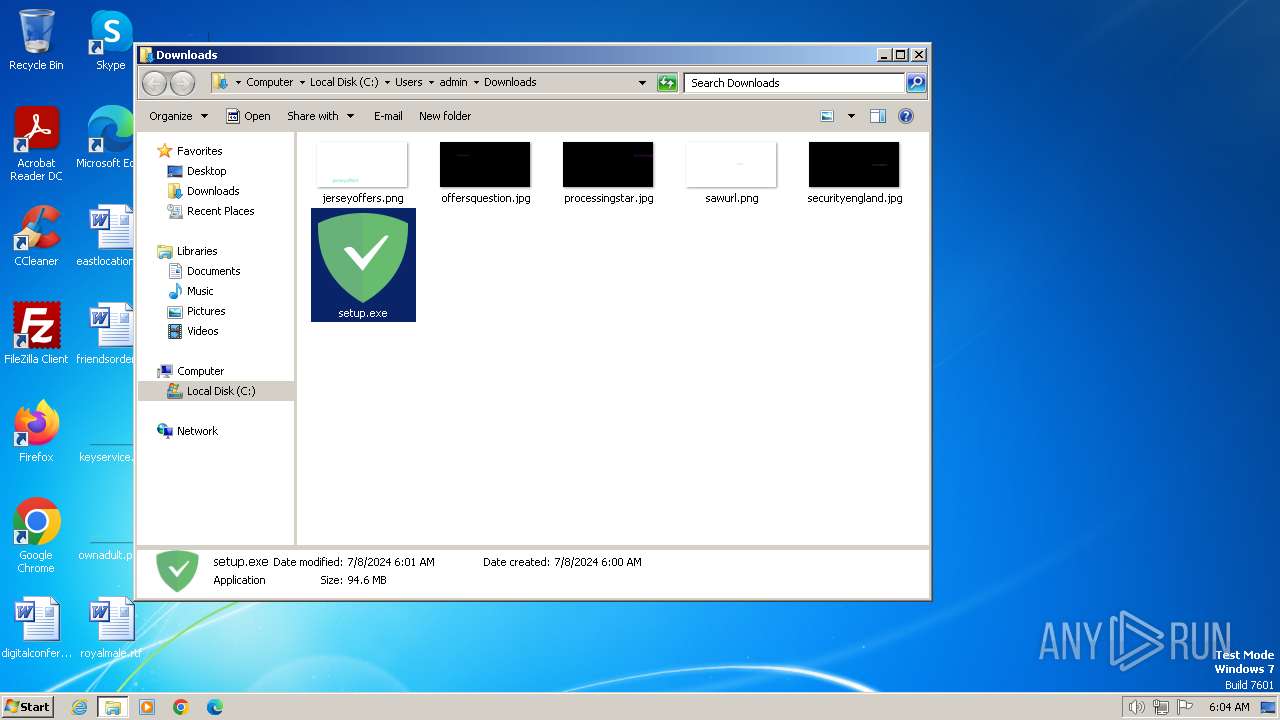
| MD5: | 466EC73FE0737549E42470D31F185C55 |
| SHA1: | 092E4220B6C5BE03B446DA925331DBF8116DE2A8 |
| SHA256: | 50C38F5C4BAD17295102F465676F03083BC48ECB936E779262B1BA6EC482BC35 |
| SSDEEP: | 3:NrMgXJIDAyL4A:1MgXSD7L4A |
MALICIOUS
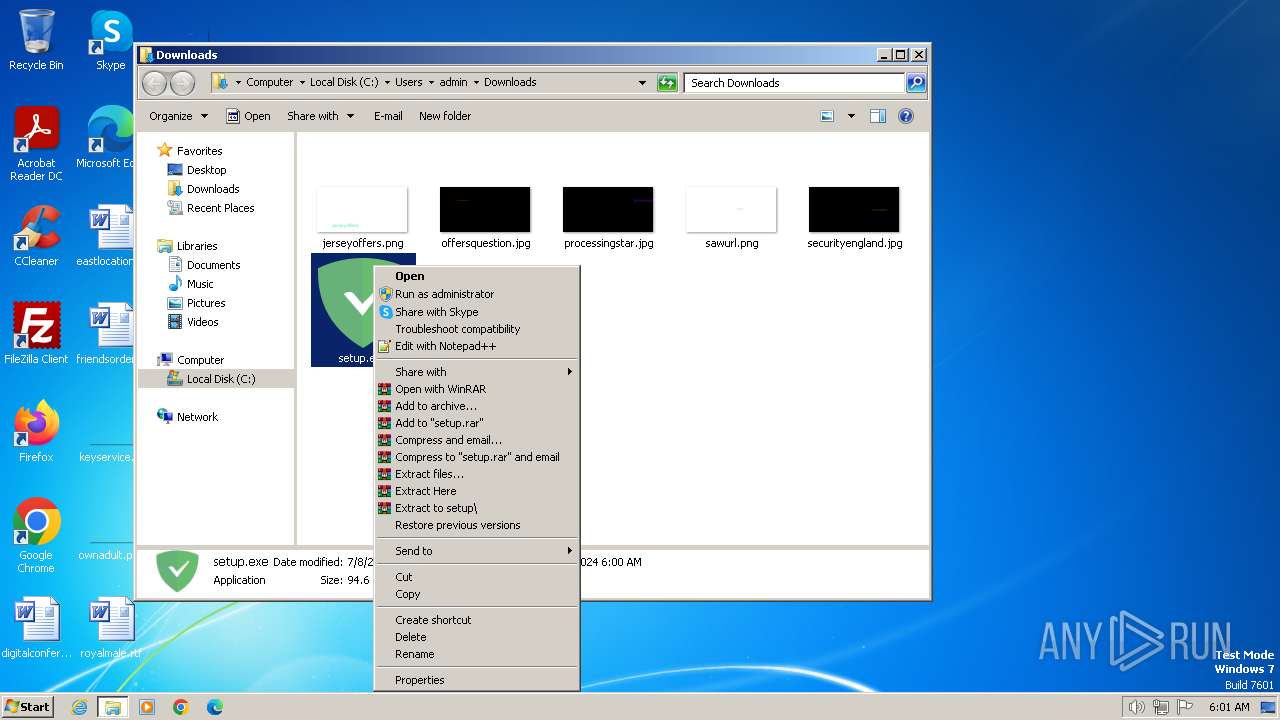
Drops the executable file immediately after the start
- setup.exe (PID: 2776)
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
- AdguardSvc.exe (PID: 2020)
- msiexec.exe (PID: 1404)
Changes the autorun value in the registry
- adgSetup.exe (PID: 3004)
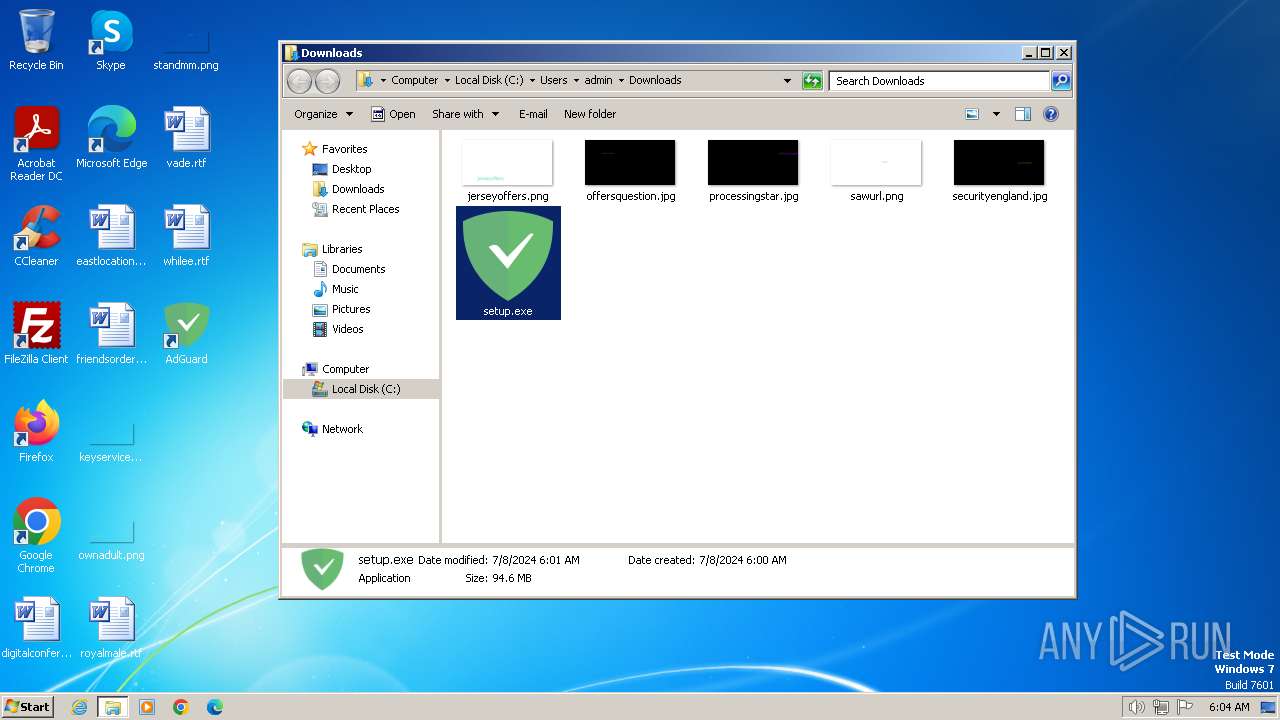
METASTEALER has been detected (YARA)
- setup.exe (PID: 2780)
- AdguardSvc.exe (PID: 3036)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
Starts NET.EXE for service management
- cmd.exe (PID: 2840)
- net.exe (PID: 3872)
Creates a writable file in the system directory
- AdguardSvc.exe (PID: 2908)
SUSPICIOUS
Process drops legitimate windows executable
- setup.exe (PID: 2780)
- rundll32.exe (PID: 3356)
- rundll32.exe (PID: 2956)
- rundll32.exe (PID: 2740)
- msiexec.exe (PID: 1404)
- rundll32.exe (PID: 1596)
- rundll32.exe (PID: 4040)
- rundll32.exe (PID: 3764)
The process creates files with name similar to system file names
- setup.exe (PID: 2780)
- msiexec.exe (PID: 1404)
Executable content was dropped or overwritten
- setup.exe (PID: 2776)
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
- rundll32.exe (PID: 2956)
- rundll32.exe (PID: 2740)
- rundll32.exe (PID: 3356)
- rundll32.exe (PID: 4040)
- rundll32.exe (PID: 1596)
- AdguardSvc.exe (PID: 2020)
- rundll32.exe (PID: 3764)
Reads the Internet Settings
- setup.exe (PID: 2780)
- Adguard.exe (PID: 1892)
Searches for installed software
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
Reads security settings of Internet Explorer
- setup.exe (PID: 2780)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
Reads settings of System Certificates
- setup.exe (PID: 2780)
Adds/modifies Windows certificates
- setup.exe (PID: 2780)
- msiexec.exe (PID: 1404)
- AdguardSvc.exe (PID: 2908)
Process requests binary or script from the Internet
- setup.exe (PID: 2780)
Starts itself from another location
- setup.exe (PID: 2780)
Checks Windows Trust Settings
- msiexec.exe (PID: 1404)
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- AdguardSvc.exe (PID: 2908)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1404)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 3284)
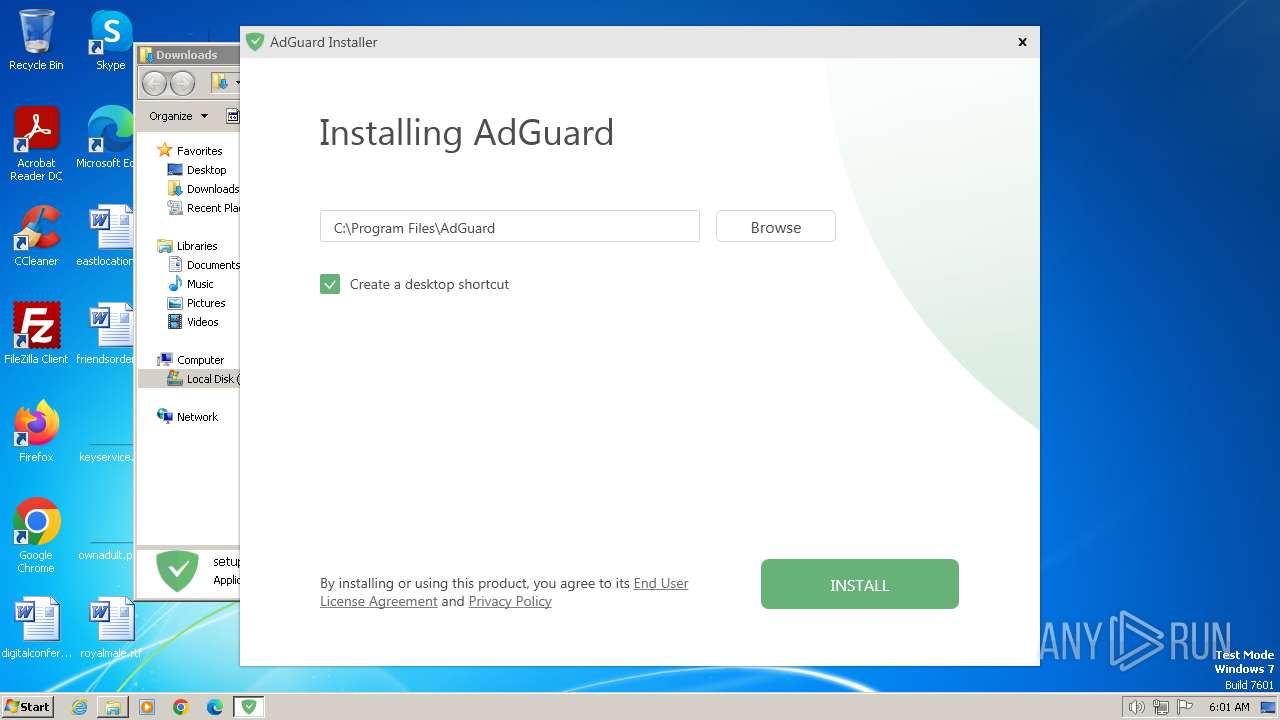
Creates a software uninstall entry
- adgSetup.exe (PID: 3004)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 2780)
- AdguardSvc.exe (PID: 3036)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 1596)
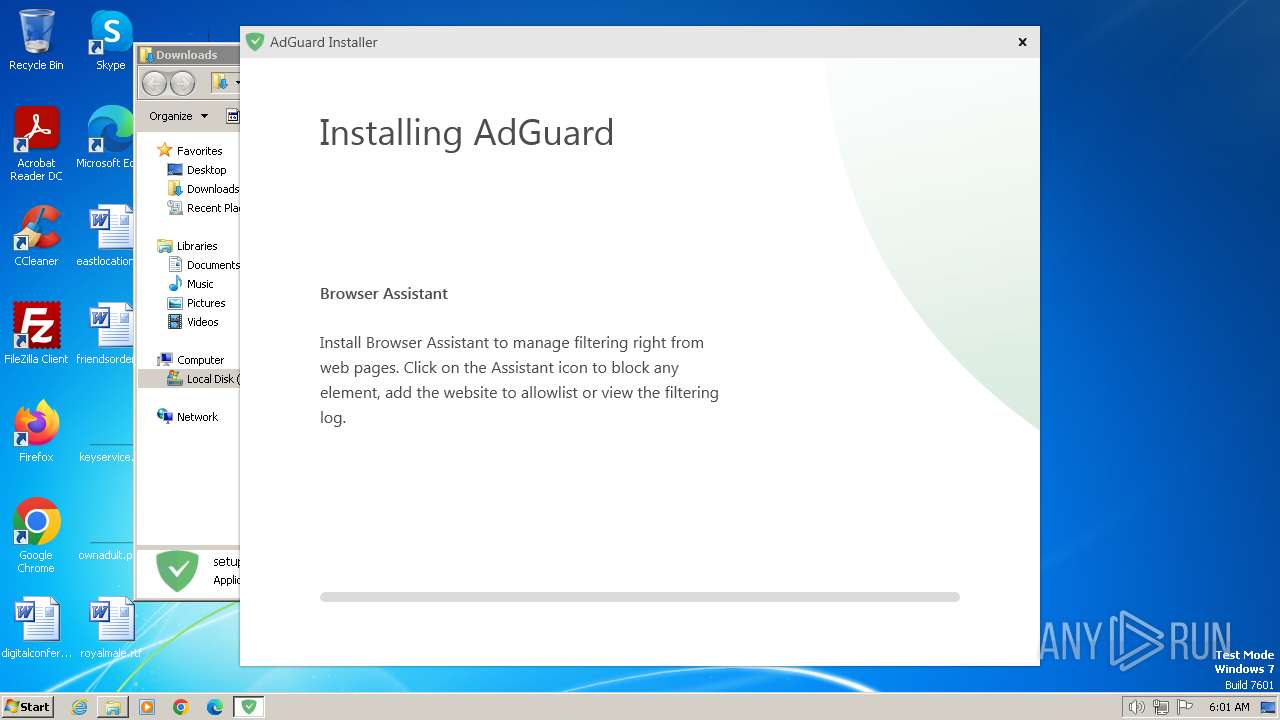
Executes as Windows Service
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- AdguardSvc.exe (PID: 2908)
Drops a system driver (possible attempt to evade defenses)
- AdguardSvc.exe (PID: 2020)
Starts SC.EXE for service management
- setup.exe (PID: 2780)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
Found regular expressions for crypto-addresses (YARA)
- AdguardSvc.exe (PID: 2908)
Creates files in the driver directory
- AdguardSvc.exe (PID: 2908)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3584)
- setup.exe (PID: 2776)
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
- msiexec.exe (PID: 3284)
- msiexec.exe (PID: 1404)
- msiexec.exe (PID: 2764)
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- Adguard.Tools.exe (PID: 2388)
- Adguard.exe (PID: 1892)
- Adguard.BrowserExtensionHost.exe (PID: 3712)
- AdguardSvc.exe (PID: 2908)
- Adguard.Tools.exe (PID: 2792)
Application launched itself
- msedge.exe (PID: 3348)
- msiexec.exe (PID: 1404)
- chrome.exe (PID: 3068)
Reads the computer name
- setup.exe (PID: 2780)
- wmpnscfg.exe (PID: 3584)
- adgSetup.exe (PID: 3004)
- msiexec.exe (PID: 3284)
- msiexec.exe (PID: 1404)
- msiexec.exe (PID: 2764)
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- Adguard.Tools.exe (PID: 2388)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
- Adguard.BrowserExtensionHost.exe (PID: 3712)
- Adguard.Tools.exe (PID: 2792)
Reads the machine GUID from the registry
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
- msiexec.exe (PID: 1404)
- msiexec.exe (PID: 3284)
- msiexec.exe (PID: 2764)
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
- Adguard.BrowserExtensionHost.exe (PID: 3712)
- Adguard.Tools.exe (PID: 2388)
- Adguard.Tools.exe (PID: 2792)
Disables trace logs
- setup.exe (PID: 2780)
- AdguardSvc.exe (PID: 2908)
Executable content was dropped or overwritten
- msedge.exe (PID: 3348)
- msiexec.exe (PID: 1404)
The process uses the downloaded file
- msedge.exe (PID: 3632)
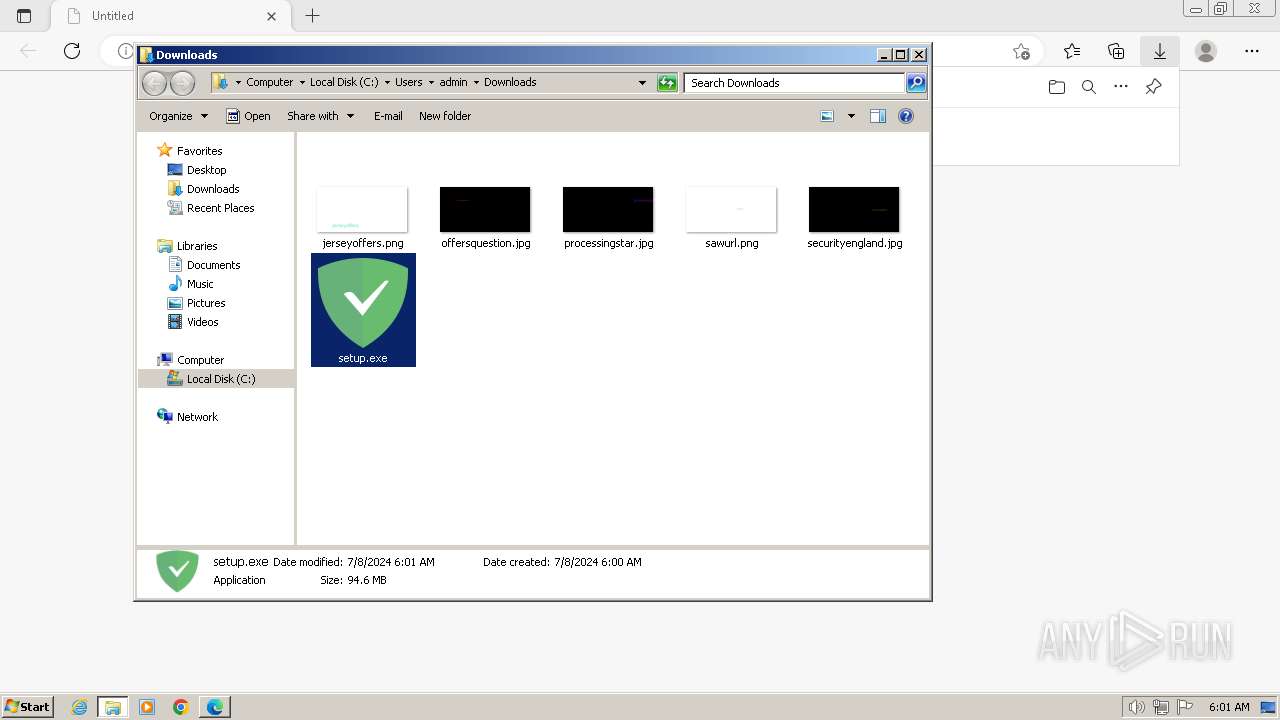
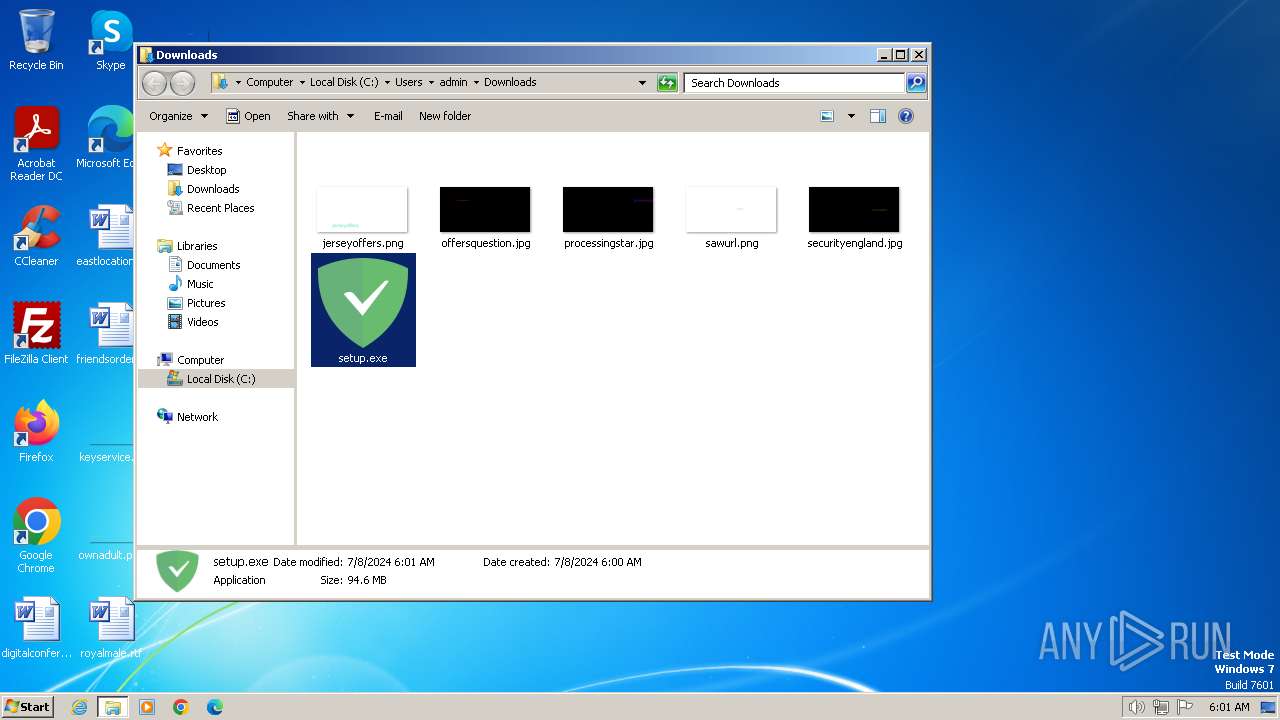
Manual execution by a user
- wmpnscfg.exe (PID: 3584)
- setup.exe (PID: 2776)
- chrome.exe (PID: 3068)
- Adguard.exe (PID: 1892)
Create files in a temporary directory
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
- msiexec.exe (PID: 1404)
Drops the executable file immediately after the start
- msedge.exe (PID: 3348)
- rundll32.exe (PID: 2956)
- rundll32.exe (PID: 2740)
- rundll32.exe (PID: 3356)
- rundll32.exe (PID: 1596)
- rundll32.exe (PID: 4040)
- rundll32.exe (PID: 3764)
Reads the software policy settings
- setup.exe (PID: 2780)
- msiexec.exe (PID: 1404)
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- AdguardSvc.exe (PID: 2908)
Creates files in the program directory
- setup.exe (PID: 2780)
- adgSetup.exe (PID: 3004)
- AdguardSvc.exe (PID: 2020)
- AdguardSvc.exe (PID: 3620)
- AdguardSvc.exe (PID: 3036)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
- Adguard.Tools.exe (PID: 2388)
- Adguard.BrowserExtensionHost.exe (PID: 3712)
- Adguard.Tools.exe (PID: 2792)
Reads Environment values
- setup.exe (PID: 2780)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
Reads Microsoft Office registry keys
- rundll32.exe (PID: 3356)
.NET Reactor protector has been detected
- setup.exe (PID: 2780)
- AdguardSvc.exe (PID: 3036)
- Adguard.exe (PID: 1892)
- AdguardSvc.exe (PID: 2908)
Dropped object may contain TOR URL's
- msiexec.exe (PID: 1404)
- AdguardSvc.exe (PID: 2908)
Creates a software uninstall entry
- msiexec.exe (PID: 1404)
Creates files or folders in the user directory
- Adguard.exe (PID: 1892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
57
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=900 --field-trial-handle=1364,i,1755127950683982140,401079909404922000,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3096 --field-trial-handle=1144,i,4525575578022581379,4090859793590126120,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1172 --field-trial-handle=1144,i,4525575578022581379,4090859793590126120,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1608 --field-trial-handle=1144,i,4525575578022581379,4090859793590126120,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1072 | "C:\Windows\system32\ie4uinit.exe" -ClearIconCache | C:\Windows\System32\ie4uinit.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1404 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | rundll32.exe "C:\Windows\Installer\MSIA394.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_435093 97 Adguard.CustomActions!Adguard.CustomActions.CustomActions.OnInstallFinalize | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3664 --field-trial-handle=1144,i,4525575578022581379,4090859793590126120,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1832 | C:\Windows\system32\net1 start "Adguard Service" | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1892 | "C:\Program Files\AdGuard\Adguard.exe" | C:\Program Files\AdGuard\Adguard.exe | explorer.exe | ||||||||||||
User: admin Company: Adguard Software Limited Integrity Level: MEDIUM Description: AdGuard for Windows Version: 7.18.4774.0 Modules
| |||||||||||||||
Total events
78 982
Read events
78 343
Write events
590
Delete events
49
Modification events
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 3D27E6914B7B2F00 | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3348) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
271
Suspicious files
385
Text files
150
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4e27d.TMP | — | |
MD5:— | SHA256:— | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4e29c.TMP | — | |
MD5:— | SHA256:— | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4e2ea.TMP | — | |
MD5:— | SHA256:— | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF4e28c.TMP | text | |
MD5:646FEFDB4D82709E3056F5C71953783C | SHA256:7B83D8689750F64D31016F1E8AC2A4EB9D7DB406E4C9C66211D4ED17DEBFEAD9 | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:F3FC0F220E8B793D2F3D821F0175B1D3 | SHA256:F37C4FC378816A8B7C657298C9EA7F9A0E6DF6853D876851178D20792E2180DB | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF4e396.TMP | text | |
MD5:00AA7B4B4257D481C40A58482D5D6B24 | SHA256:65A7BF11BD80C6FE73C58A20E4BB0F8FA653EEB70B707DA7D16DD9E7F954CA21 | |||
| 3348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:9D14DCB158E3908F7CBFB13D762D8F6A | SHA256:D339CBEF1BC3E4CDF15D0DCE9E2D77324E5B4F7EE4F2749472BFCEA91BB54ACE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
64
DNS requests
52
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
2944 | msedge.exe | GET | 301 | 156.146.33.137:80 | http://static.adtidy.org/windows/setup.exe | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
2780 | setup.exe | GET | 301 | 212.102.56.178:80 | http://static.adguard.com/installer.v1.0.json | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2908 | AdguardSvc.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?cc9f8c39a27b0efb | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3348 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2944 | msedge.exe | 156.146.33.137:80 | static.adtidy.org | Datacamp Limited | DE | unknown |
2944 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2944 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2944 | msedge.exe | 156.146.33.137:443 | static.adtidy.org | Datacamp Limited | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
static.adtidy.org |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
time.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2908 | AdguardSvc.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
AdguardSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\AdGuard\x86\SQLite.Interop.dll"...
|
AdguardSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\AdGuard\x86\SQLite.Interop.dll"...
|
AdguardSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\AdGuard\x86\SQLite.Interop.dll"...
|
AdguardSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\AdGuard\x86\SQLite.Interop.dll"...
|
AdguardSvc.exe | SQLite error (5): database is locked
|
AdguardSvc.exe | SQLite error (5): database is locked
|
AdguardSvc.exe | SQLite error (5): database is locked
|
AdguardSvc.exe | SQLite error (5): database is locked
|
AdguardSvc.exe | SQLite error (11): database corruption at line 61461 of [1a584e4999]
|
AdguardSvc.exe | SQLite error (11): database corruption at line 61502 of [1a584e4999]
|