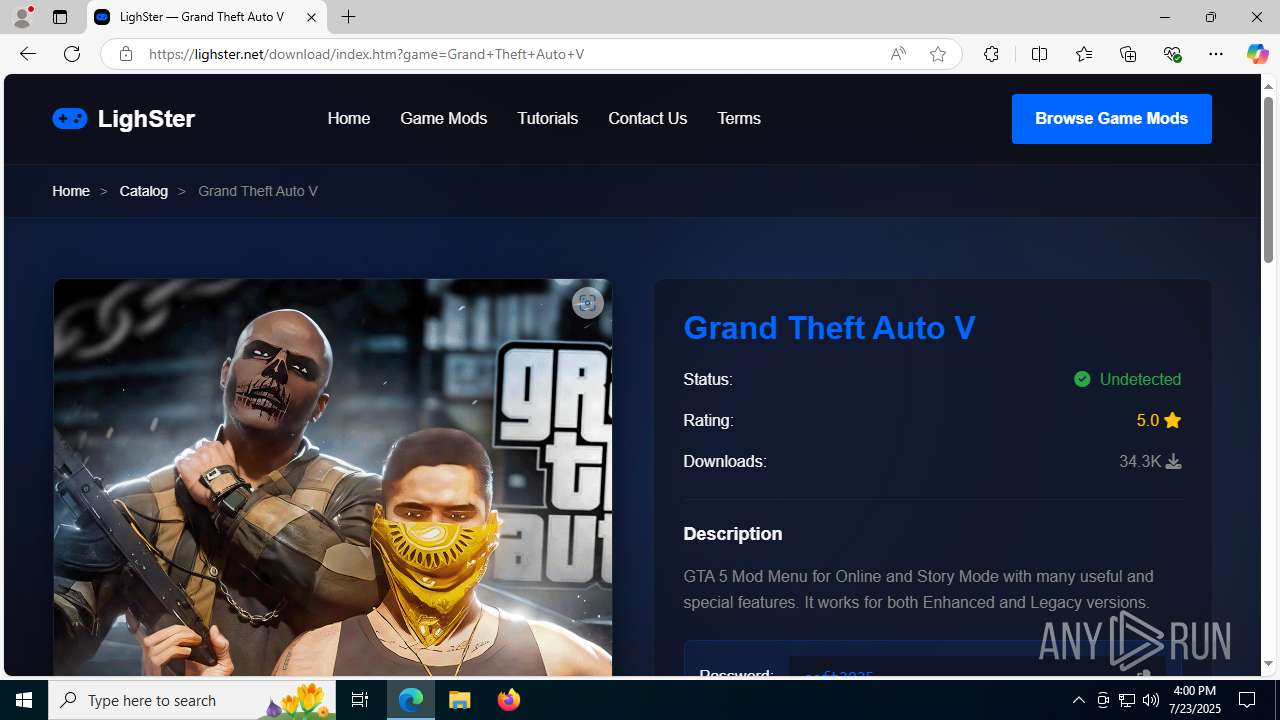
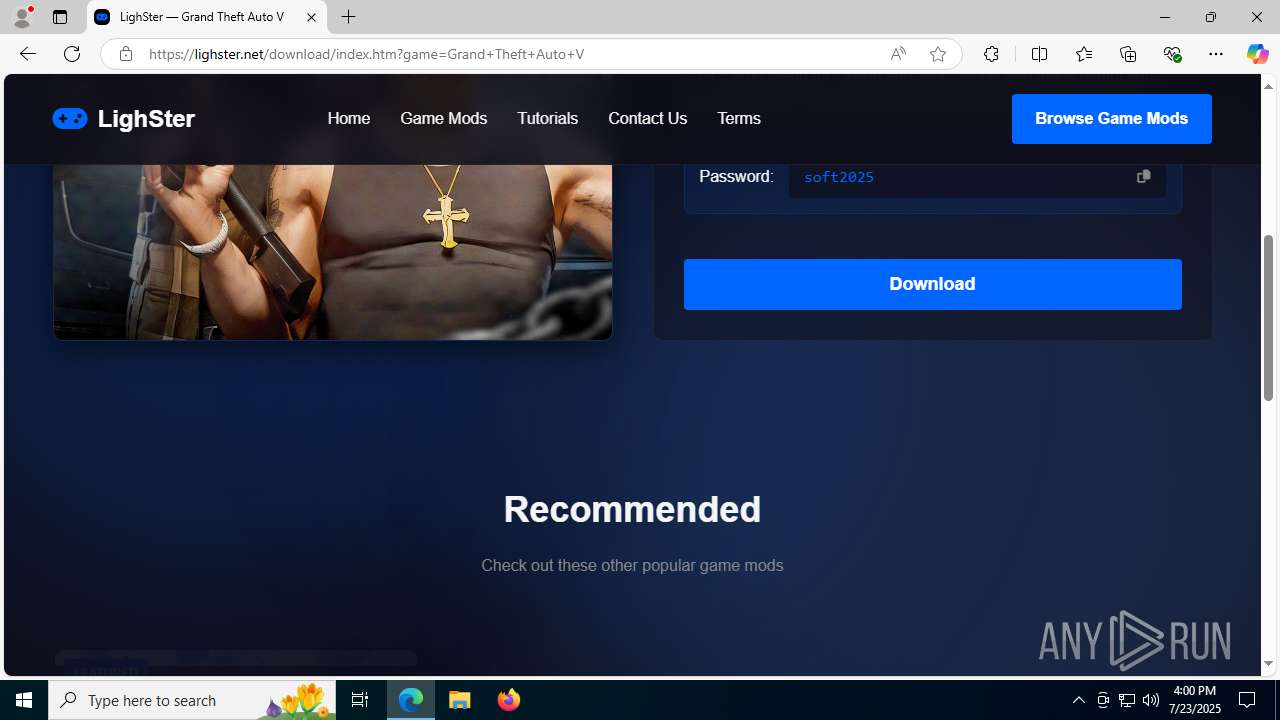
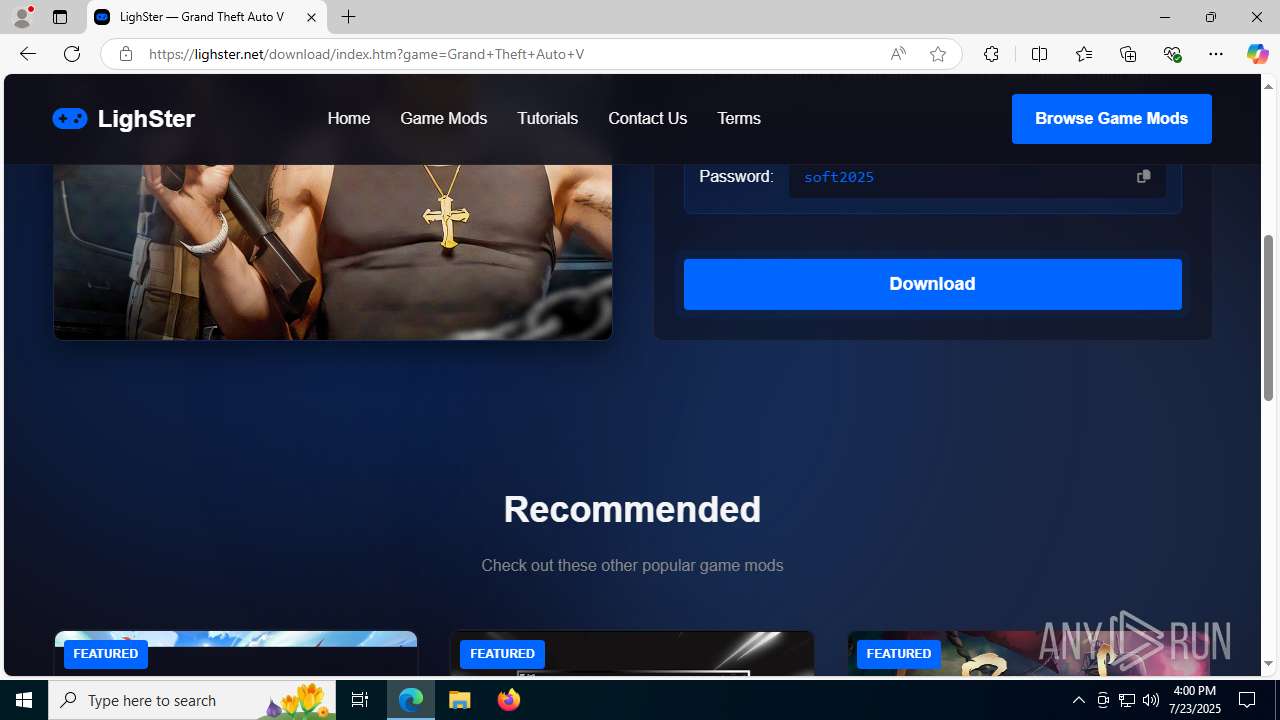
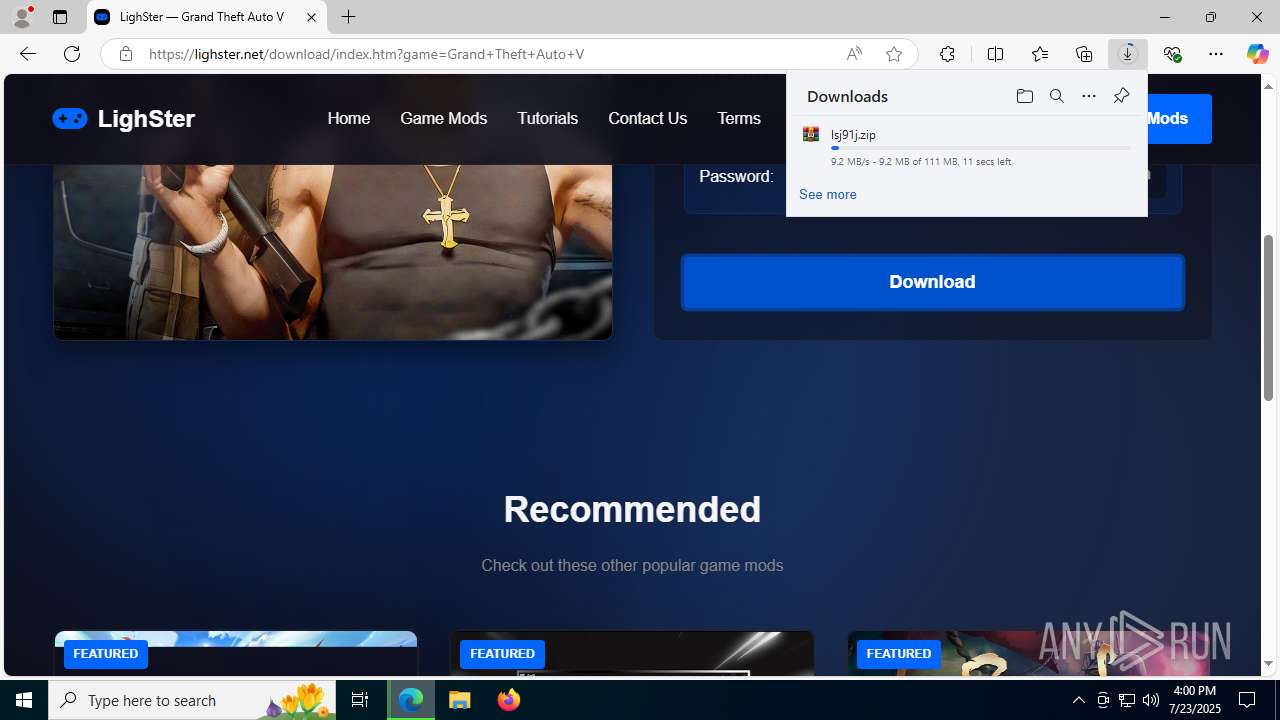
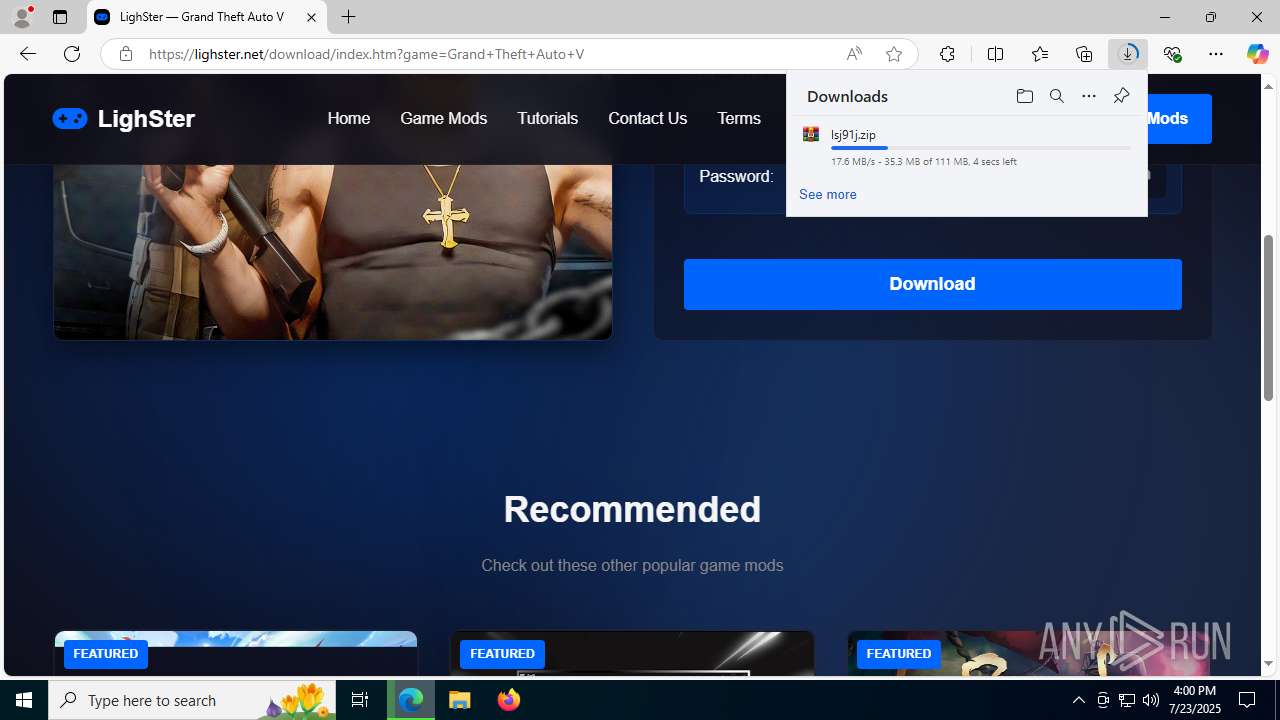
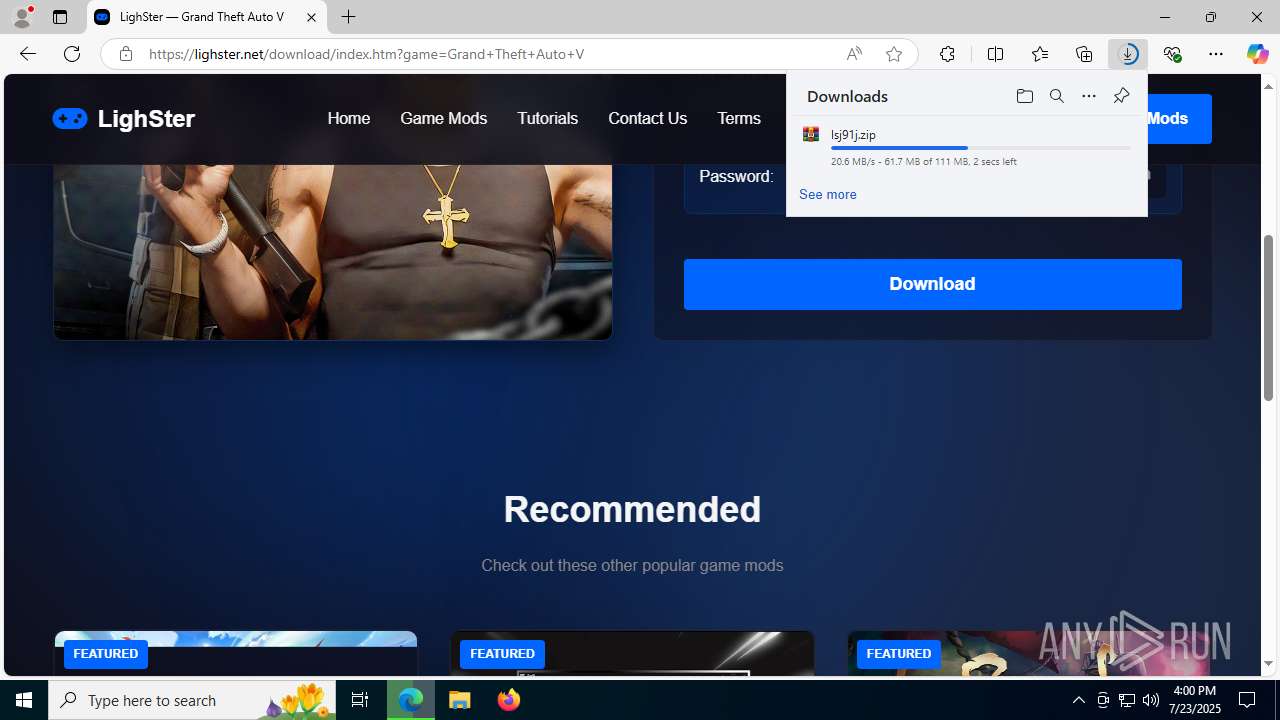
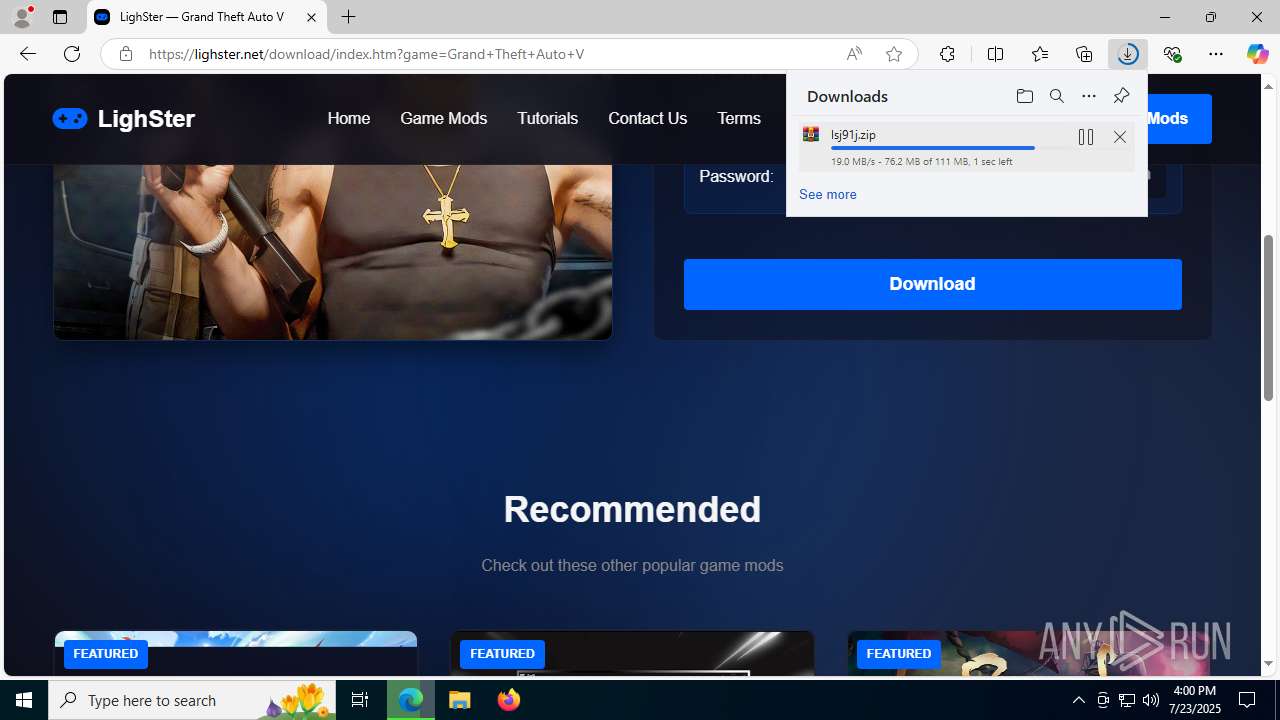
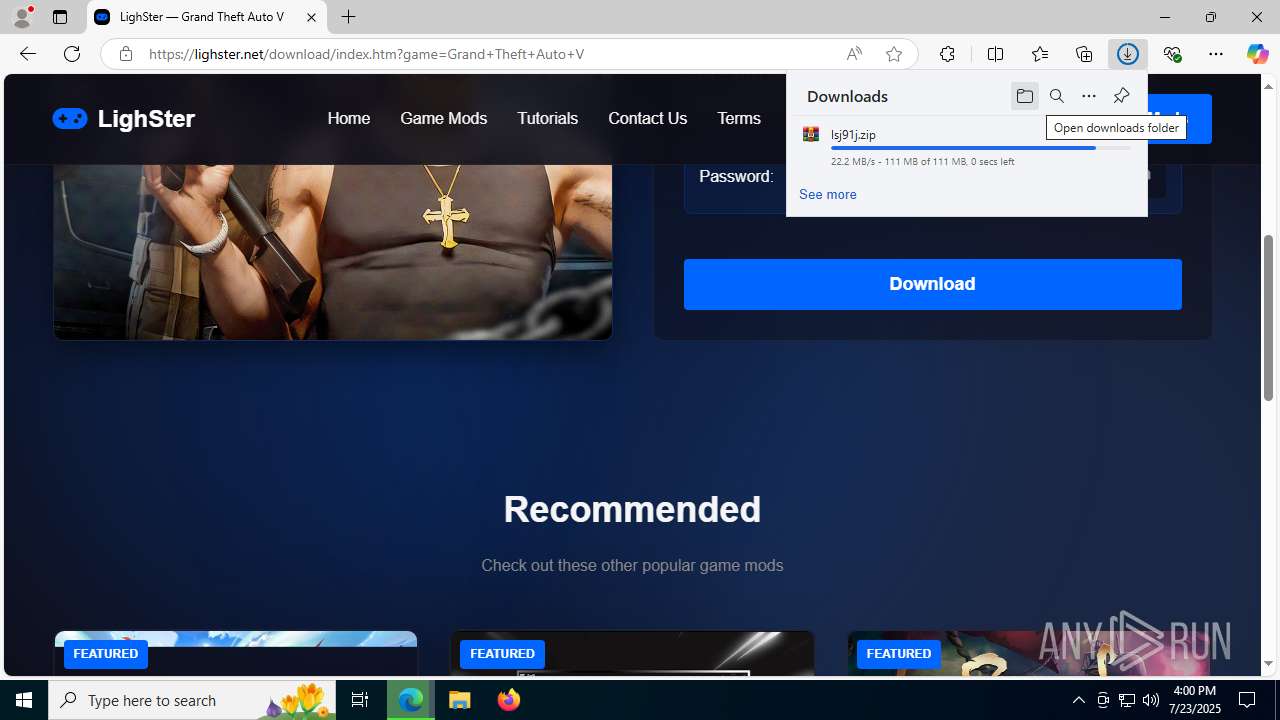
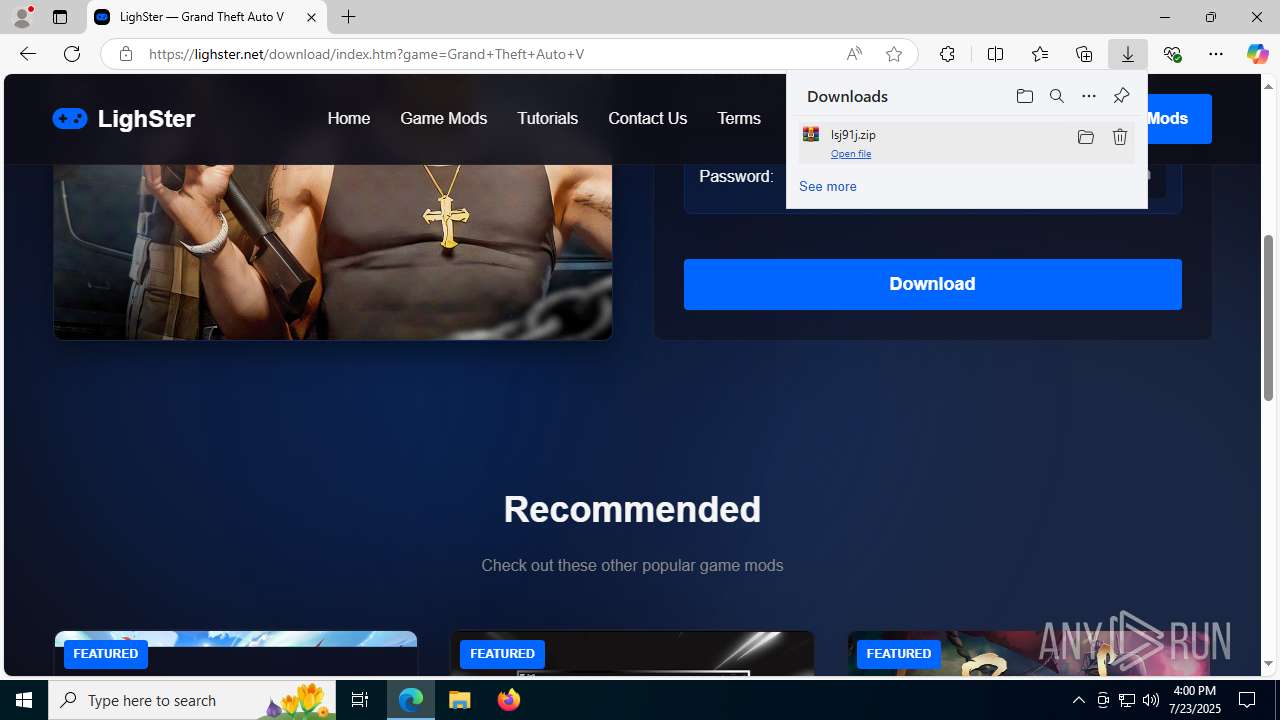
| URL: | https://lighster.net/ |
| Full analysis: | https://app.any.run/tasks/422fd89a-3108-4cbc-ab91-a571e8d2d4b1 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
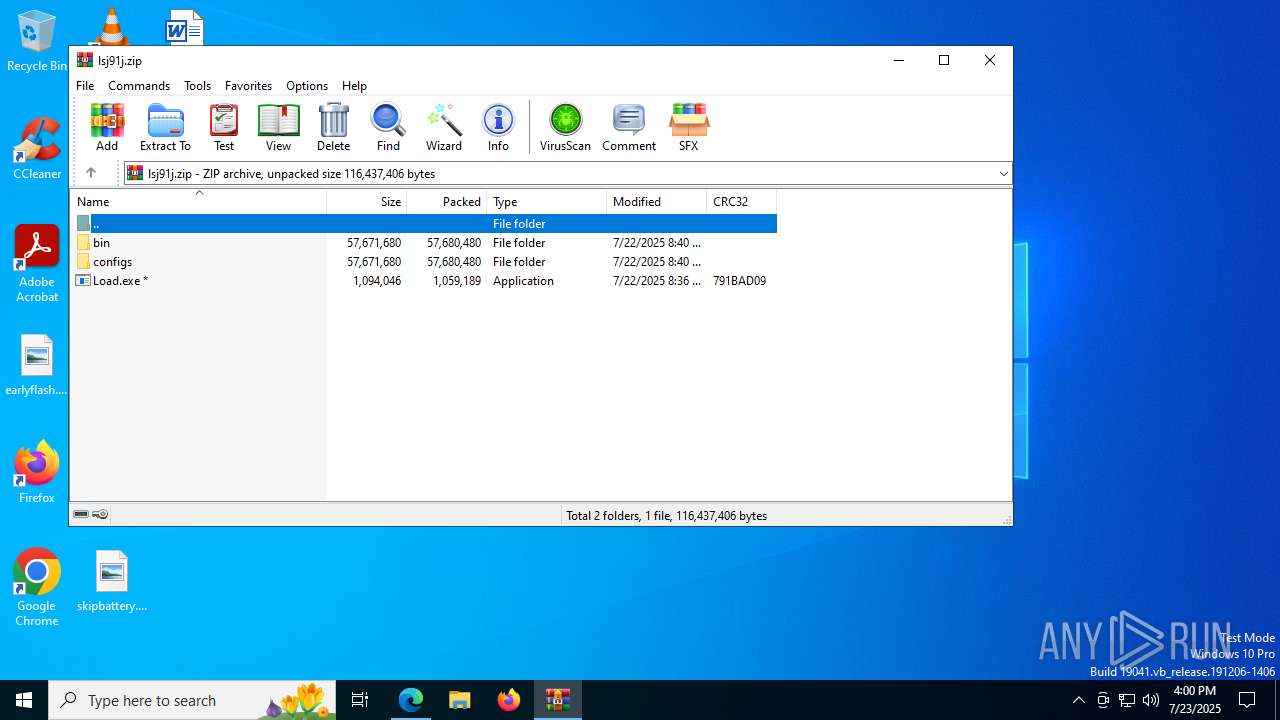
| Analysis date: | July 23, 2025, 16:00:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
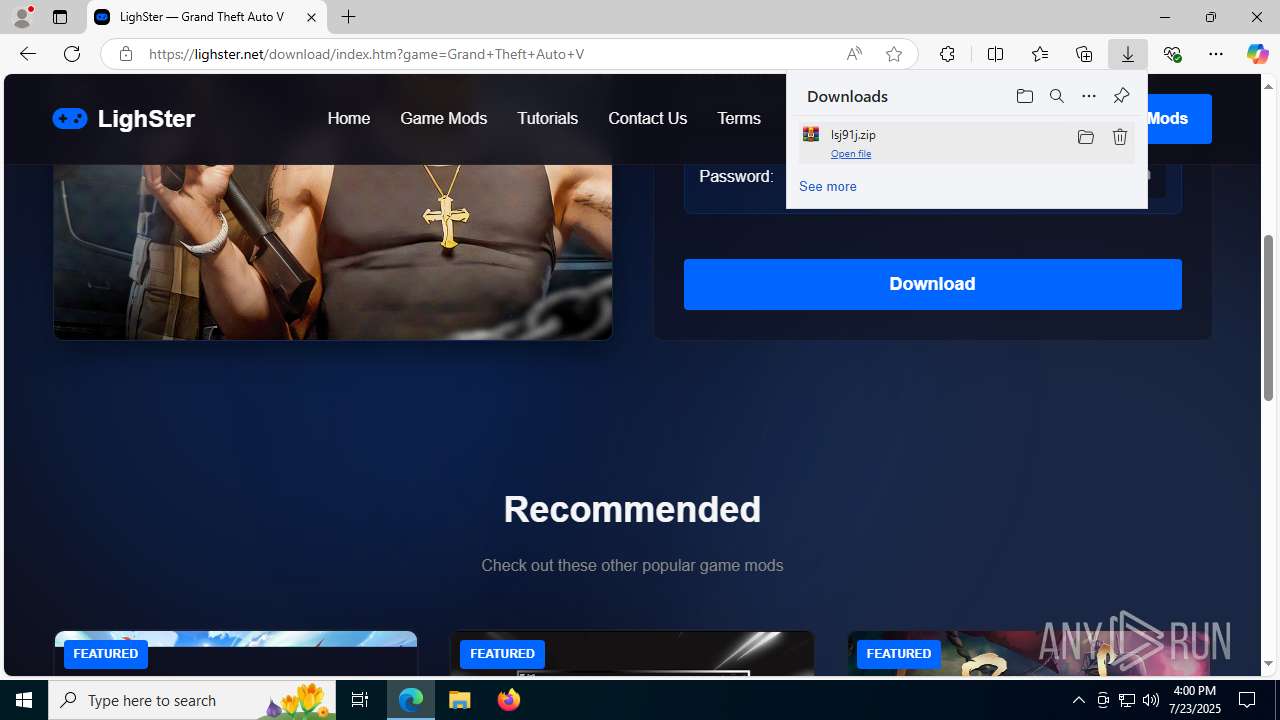
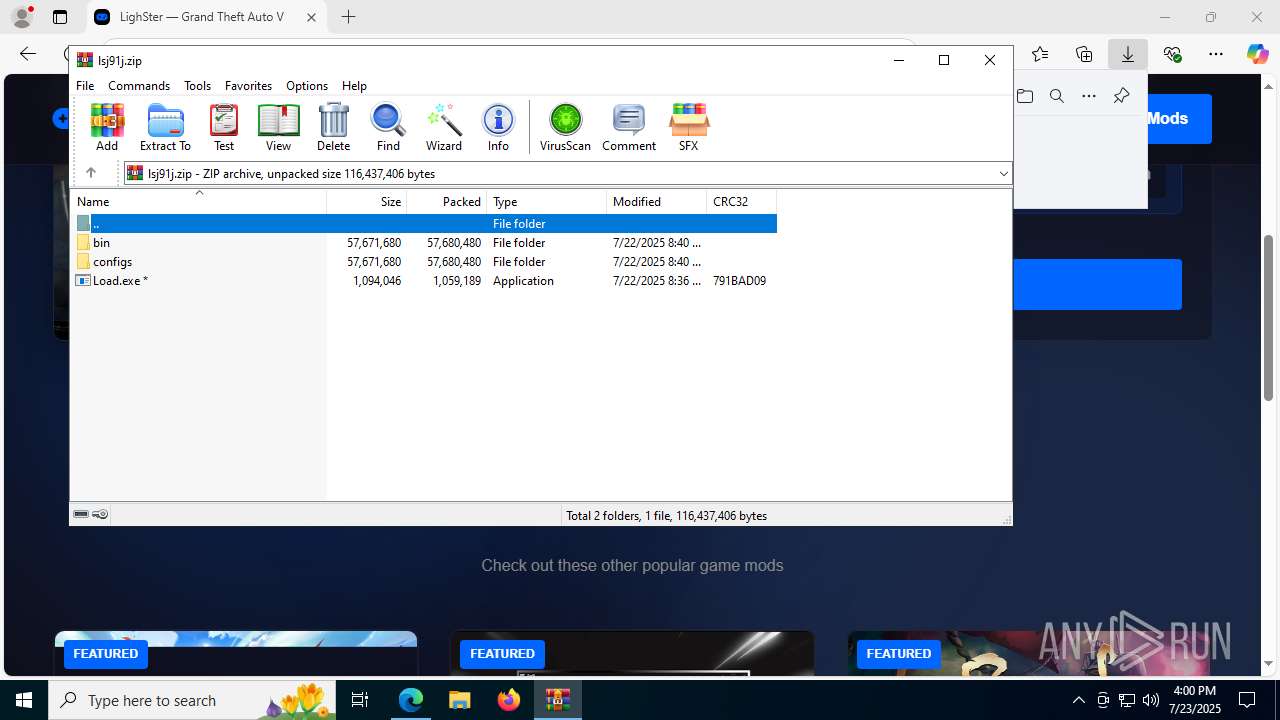
| MD5: | 4BA151BC630A7721159A565634154457 |
| SHA1: | EAB584CDA39E0F82935E2759E5DC591CB619C435 |
| SHA256: | 4FFE9A5D6DBC8B243A5969AB22C1CA67ED1A539D8F3F7DB708D0B2FEDED7DA14 |
| SSDEEP: | 3:N8MC4c:2MCp |
MALICIOUS
LUMMA mutex has been found
- Users.com (PID: 7572)
Steals credentials from Web Browsers
- Users.com (PID: 7572)
Actions looks like stealing of personal data
- Users.com (PID: 7572)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Load.exe (PID: 7972)
Get information on the list of running processes
- cmd.exe (PID: 7936)
Executing commands from ".cmd" file
- Load.exe (PID: 7972)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7936)
Executable content was dropped or overwritten
- Load.exe (PID: 7972)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7936)
Starts application with an unusual extension
- cmd.exe (PID: 7936)
The executable file from the user directory is run by the CMD process
- Users.com (PID: 7572)
There is functionality for taking screenshot (YARA)
- Load.exe (PID: 7972)
- Users.com (PID: 7572)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7936)
Searches for installed software
- Users.com (PID: 7572)
INFO
Application launched itself
- msedge.exe (PID: 1728)
- chrome.exe (PID: 7412)
- chrome.exe (PID: 7940)
- chrome.exe (PID: 7828)
- chrome.exe (PID: 864)
- msedge.exe (PID: 1652)
- msedge.exe (PID: 7600)
- msedge.exe (PID: 592)
- msedge.exe (PID: 8184)
- msedge.exe (PID: 2324)
- msedge.exe (PID: 3948)
- msedge.exe (PID: 7732)
Checks supported languages
- identity_helper.exe (PID: 7652)
- Load.exe (PID: 7972)
- extrac32.exe (PID: 8180)
- Users.com (PID: 7572)
Reads Environment values
- identity_helper.exe (PID: 7652)
Reads the computer name
- identity_helper.exe (PID: 7652)
- extrac32.exe (PID: 8180)
- Users.com (PID: 7572)
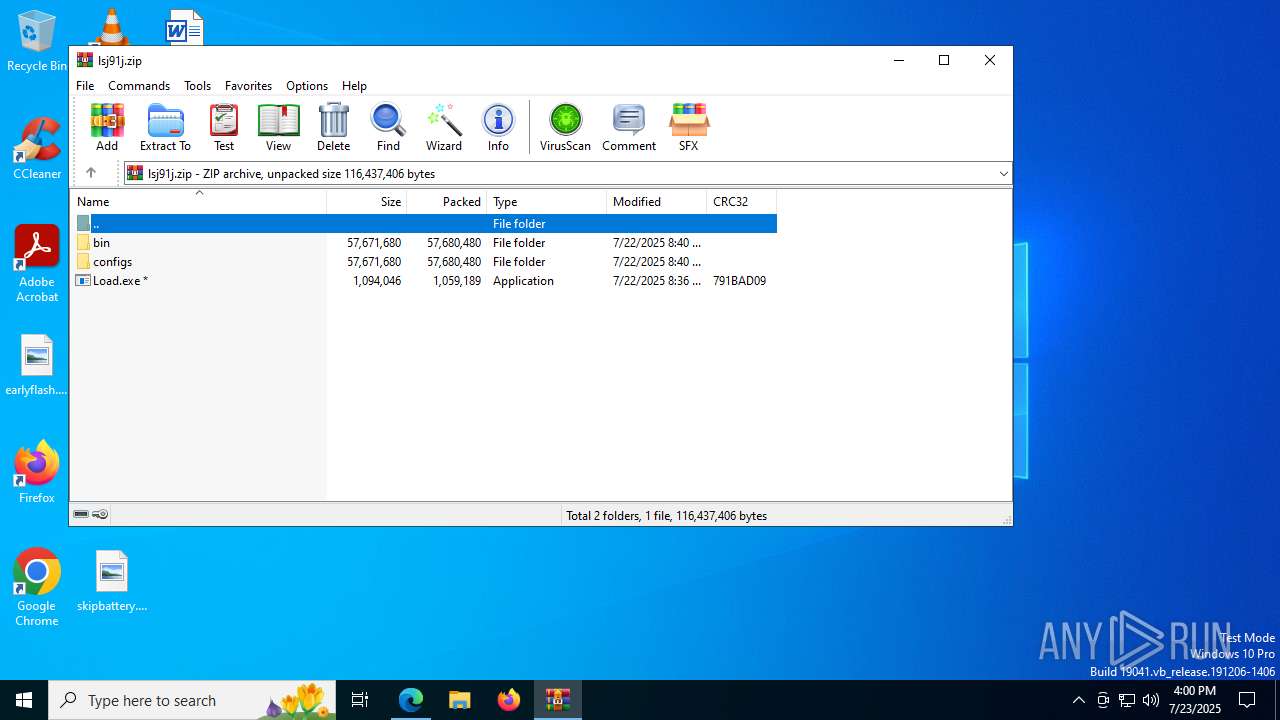
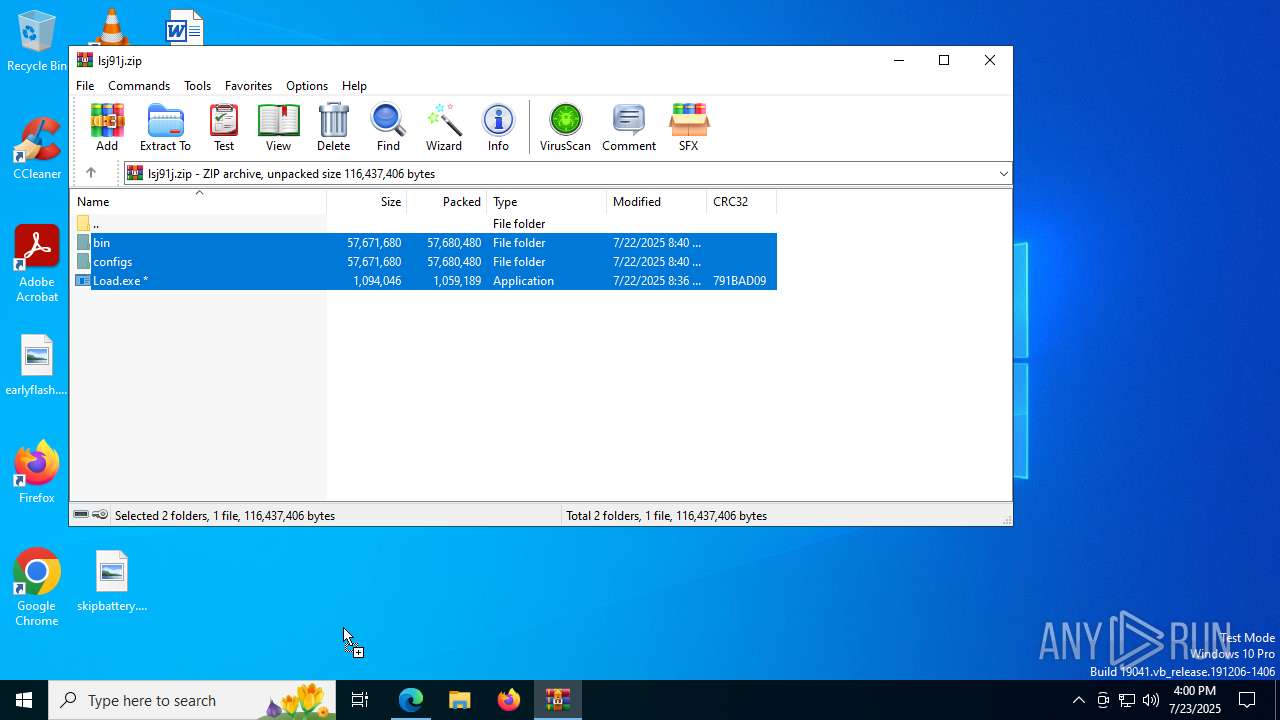
Manual execution by a user
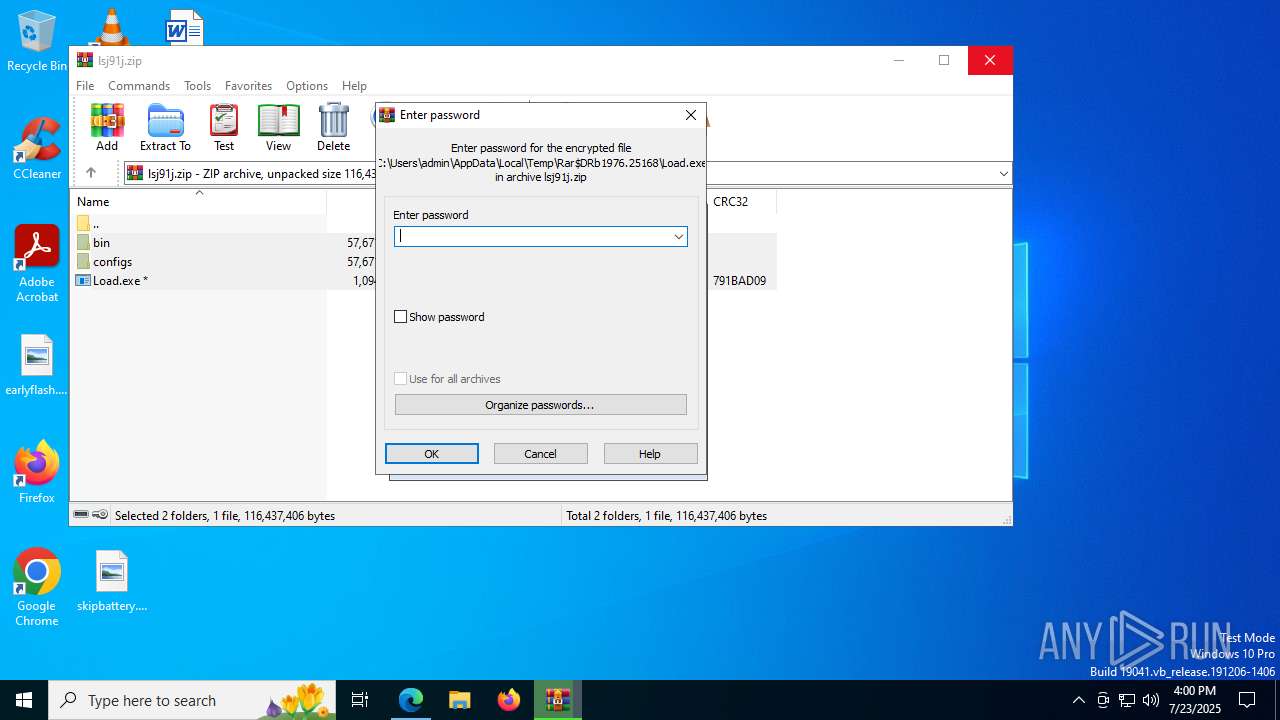
- Load.exe (PID: 7972)
Create files in a temporary directory
- Load.exe (PID: 7972)
- extrac32.exe (PID: 8180)
Executable content was dropped or overwritten
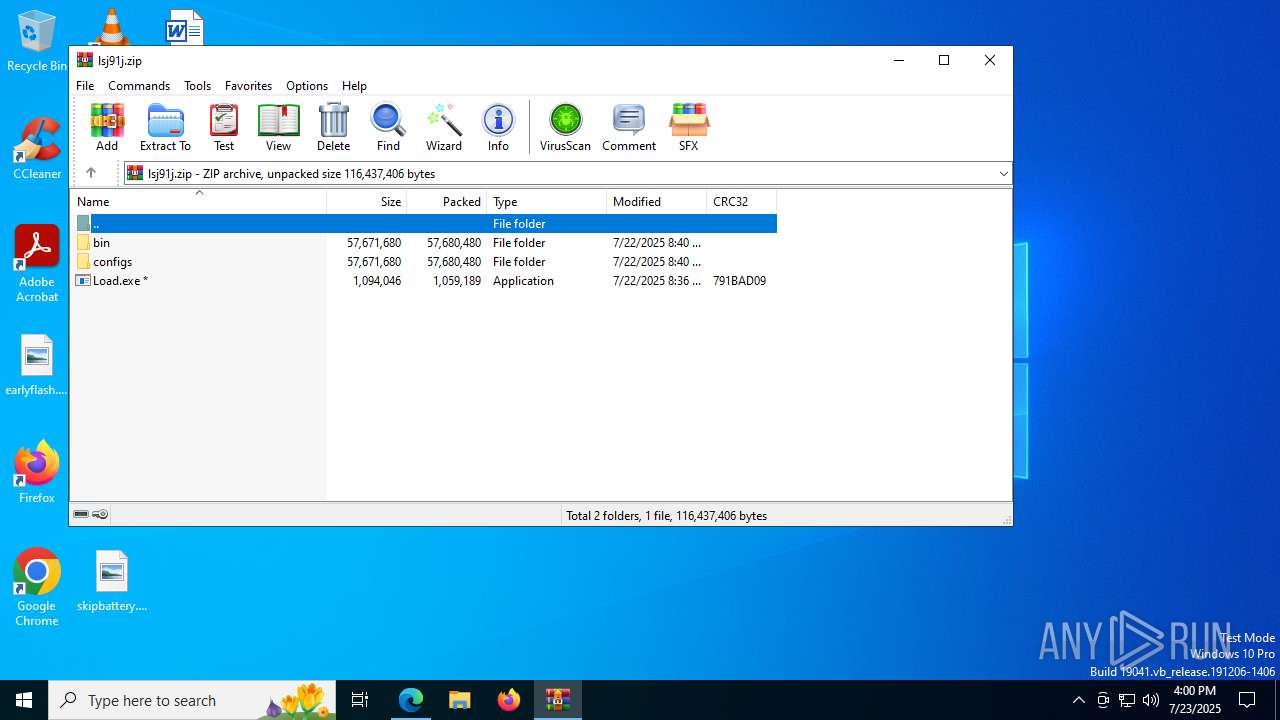
- WinRAR.exe (PID: 1976)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1728)
Reads the machine GUID from the registry
- Users.com (PID: 7572)
Reads mouse settings
- Users.com (PID: 7572)
Reads the software policy settings
- Users.com (PID: 7572)
- slui.exe (PID: 5080)
Checks proxy server information
- slui.exe (PID: 5080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
110
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x2a8,0x2ac,0x2b0,0x2a4,0x164,0x7ffc444ff208,0x7ffc444ff214,0x7ffc444ff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2060,i,3114330296531920346,7378860077508385683,262144 --variations-seed-version --mojo-platform-channel-handle=2056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 | |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x228,0x22c,0x230,0x204,0x234,0x7ffc4251fff8,0x7ffc42520004,0x7ffc42520010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4896,i,3114330296531920346,7378860077508385683,262144 --variations-seed-version --mojo-platform-channel-handle=4788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 | |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3200,i,4816284794805453150,4761226475432164637,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2424,i,9752293583449727047,5747454836621686959,262144 --variations-seed-version --mojo-platform-channel-handle=2084 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Users.com | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 | |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2004,i,4816284794805453150,4761226475432164637,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2000 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4044,i,8822943192932815991,770736869621117590,262144 --variations-seed-version --mojo-platform-channel-handle=4084 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 | |||||||||||||||
Total events
1 770
Read events
1 765
Write events
5
Delete events
0
Modification events
| (PID) Process: | (1728) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B2754A1631992F00 | |||
| (PID) Process: | (1728) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1A093DE3-137E-4E77-9E4E-E2020AB58769} | |||
| (PID) Process: | (1728) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E62525CA-3D57-4863-BAE7-29908AD417D8} | |||
| (PID) Process: | (1728) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (1728) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
2
Suspicious files
540
Text files
391
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d4c0.TMP | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d4df.TMP | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d4ef.TMP | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d4ef.TMP | — | |
MD5:— | SHA256:— | |||
| 1728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
240
DNS requests
218
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2028 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:9VxucAGyEYWwsSA5rlNBk3Zg9cIp0RdJFQ7oOAfO3yE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2460 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7740 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7740 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1800 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
1800 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
5884 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:t3cmBbNmkytgPrY74-cj7dslMw5vEYE9NC4P3cEYWzg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1800 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753751243&P2=404&P3=2&P4=JPM%2bm9OS0NDZA6ASOnGdK2LX69nrppI%2bzvfVFZWMLubcdz3GuKFZBezlHY2okN0%2b1xKjiGd6JjjM2iXb4GnRsQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2992 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2028 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2028 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2028 | msedge.exe | 104.21.32.37:443 | lighster.net | CLOUDFLARENET | — | unknown |
2028 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2028 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
lighster.net |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2028 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7572 | Users.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
7572 | Users.com | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
7572 | Users.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
7572 | Users.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
7572 | Users.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
7572 | Users.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |
7572 | Users.com | Not Suspicious Traffic | ET INFO OpenSSL Demo CA - Internet Widgits Pty (O) |