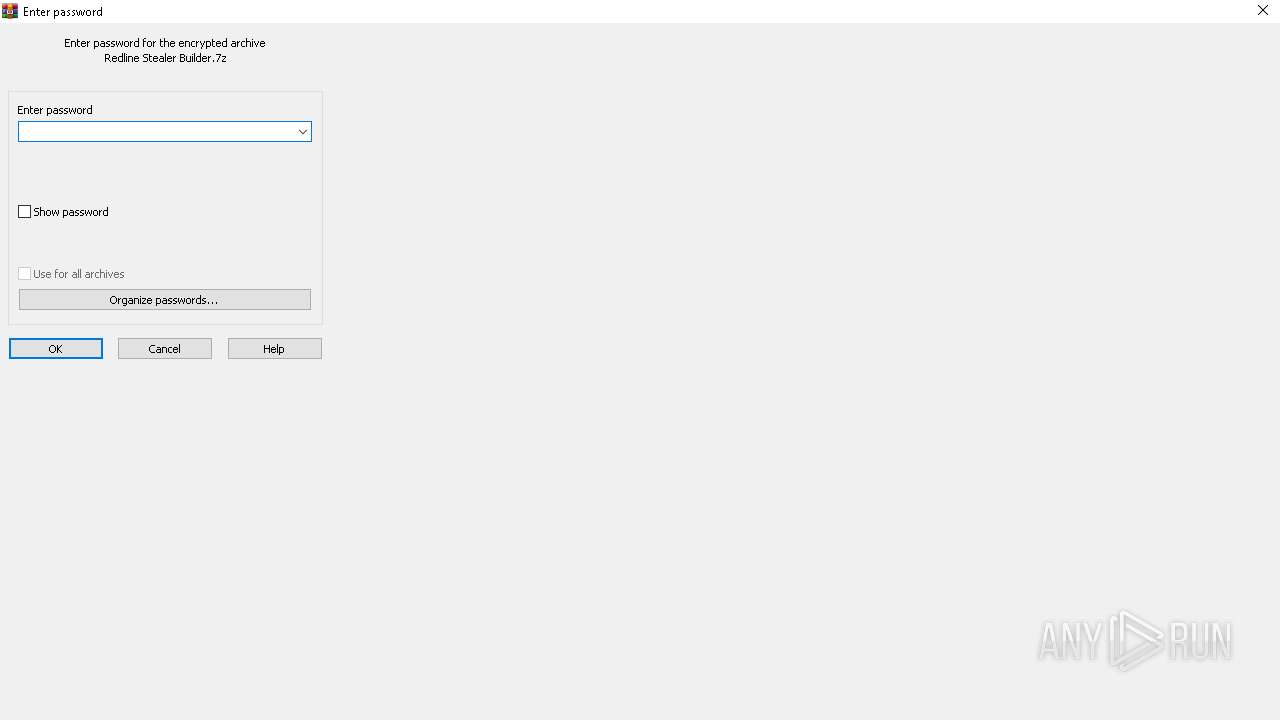
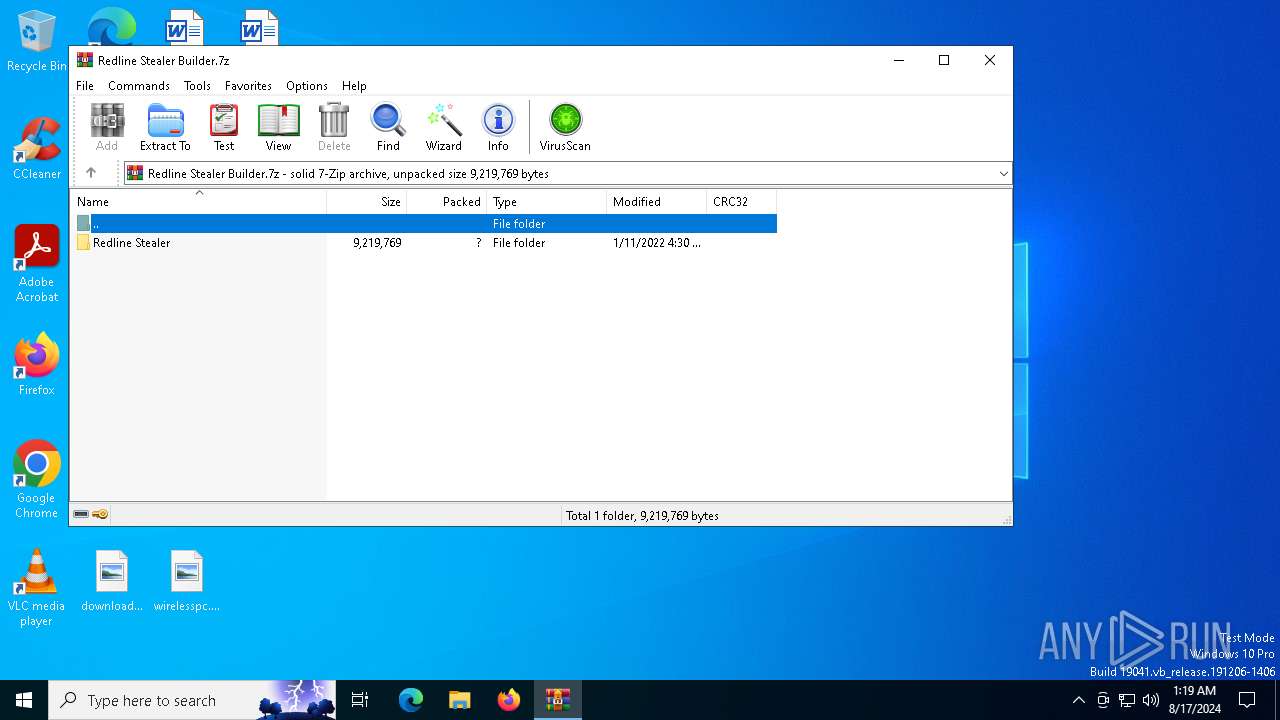
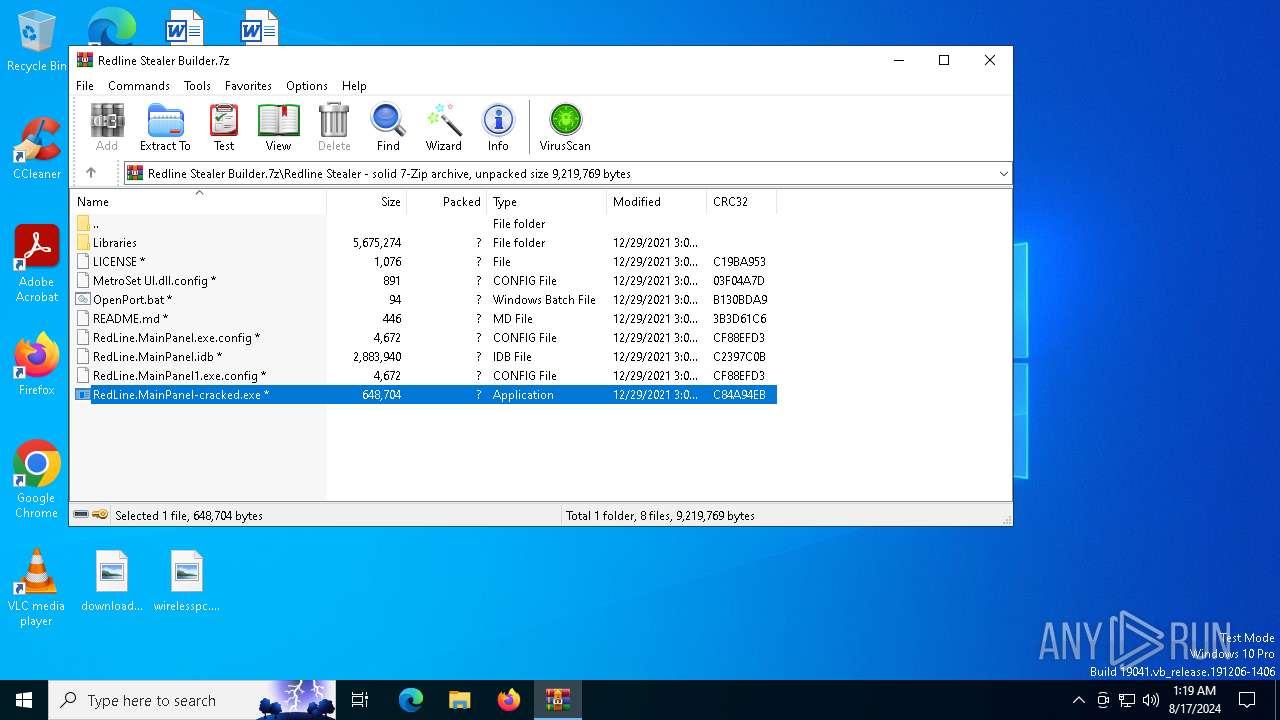
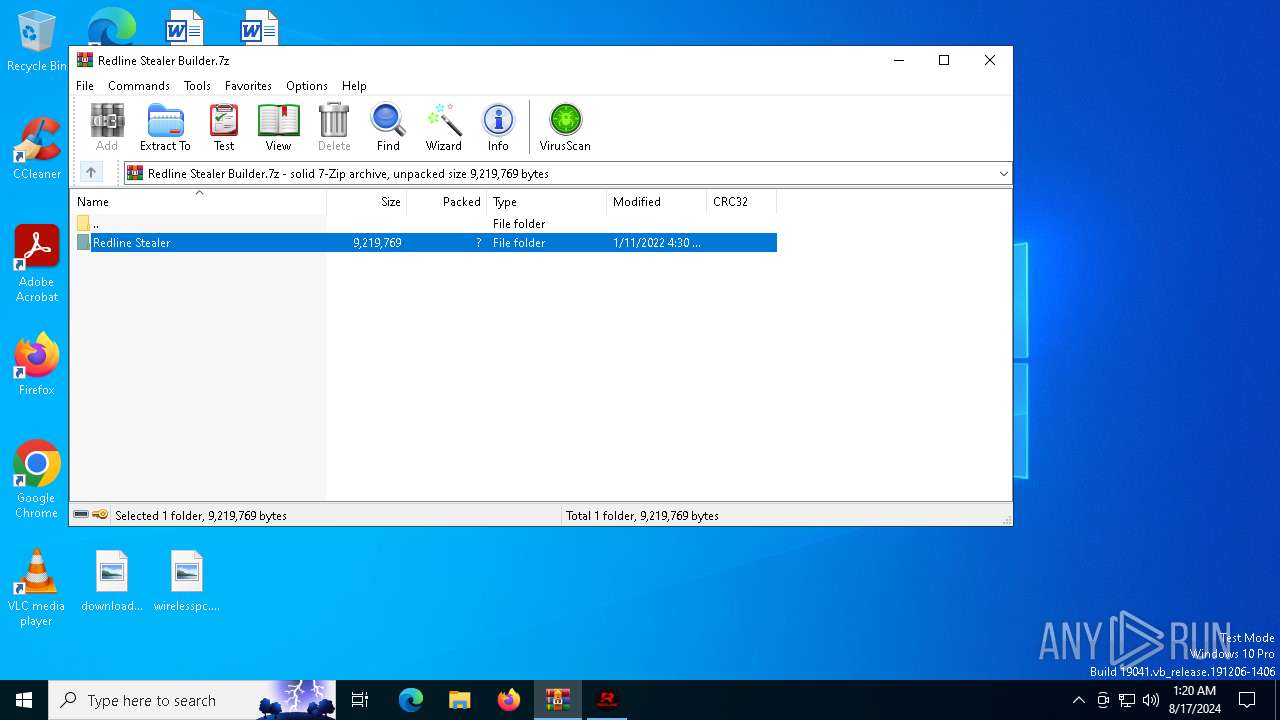
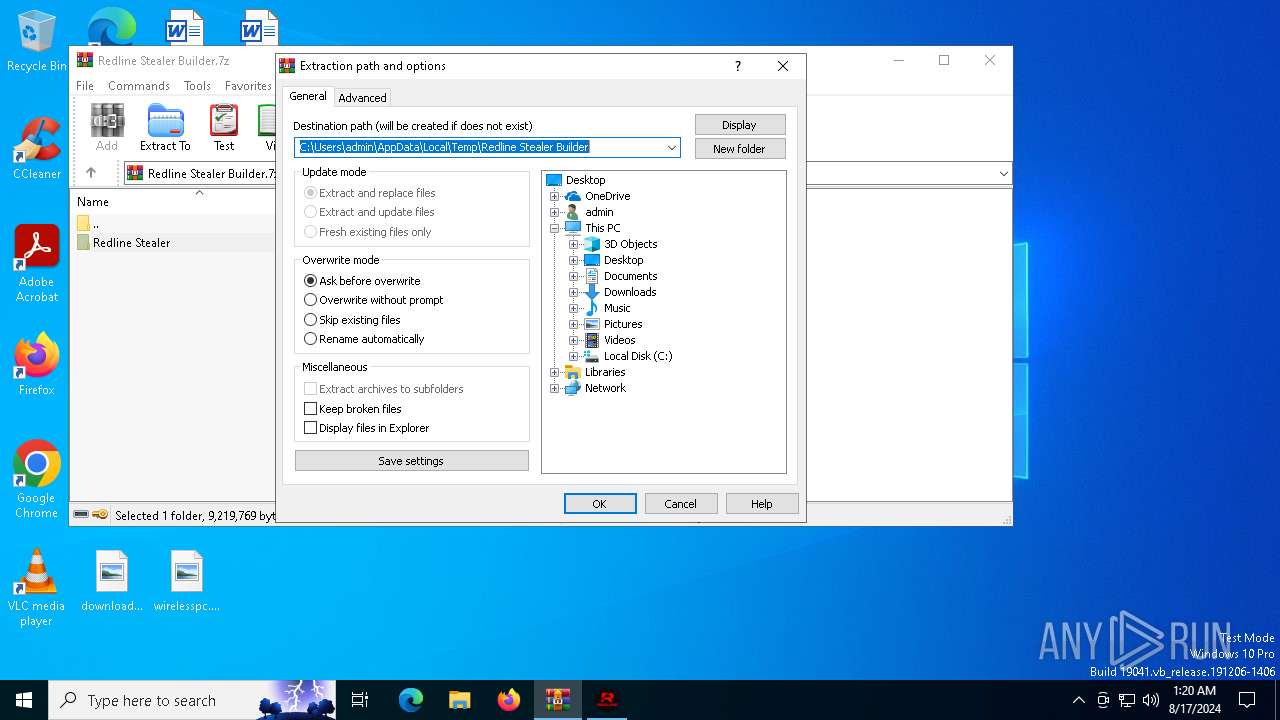
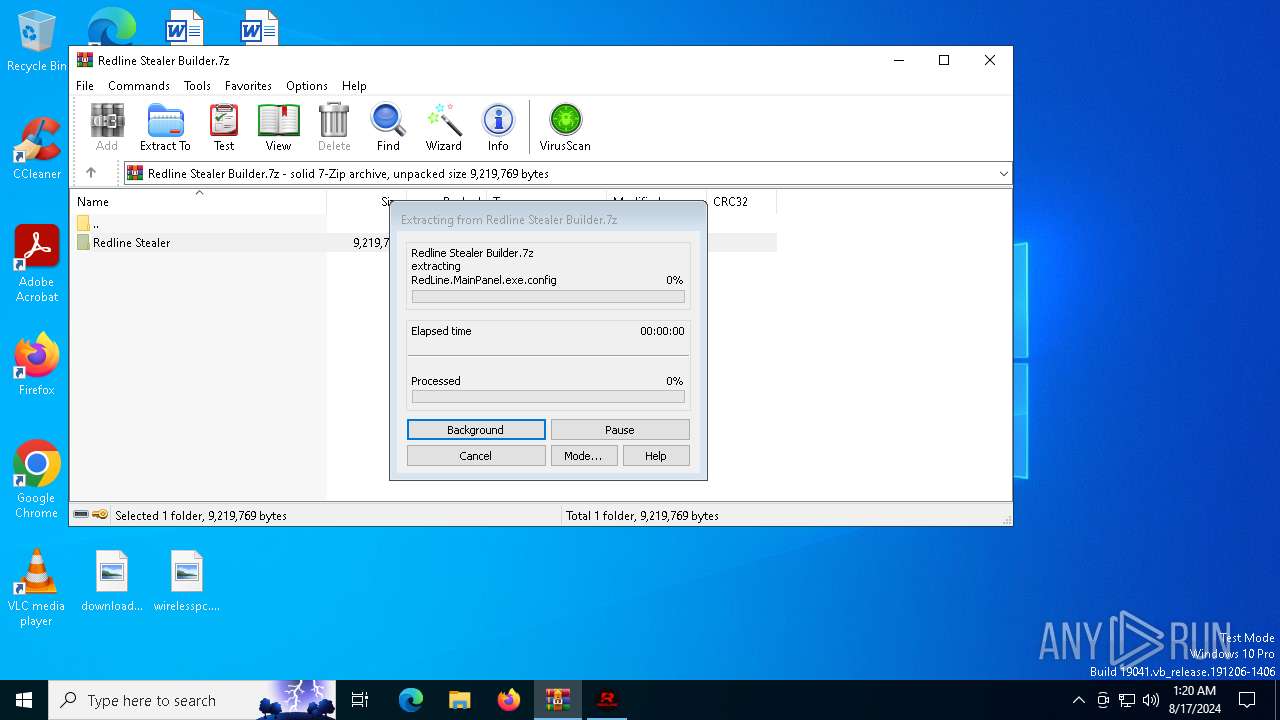
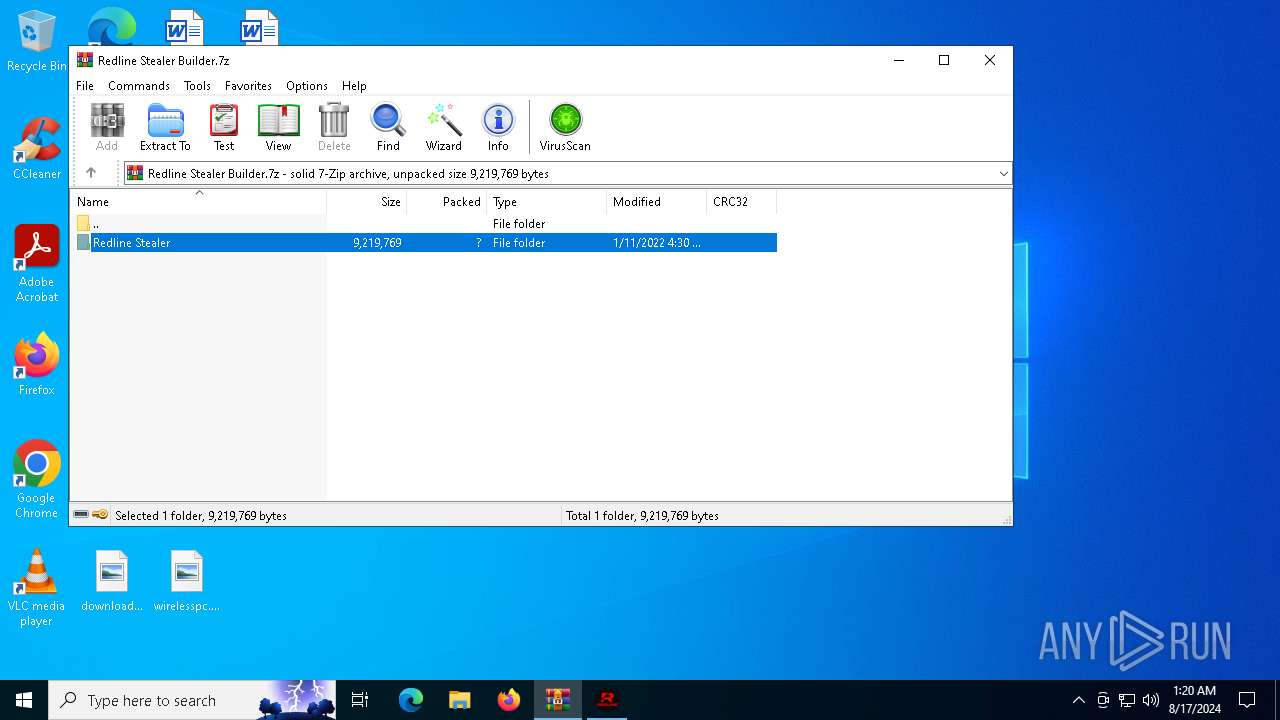
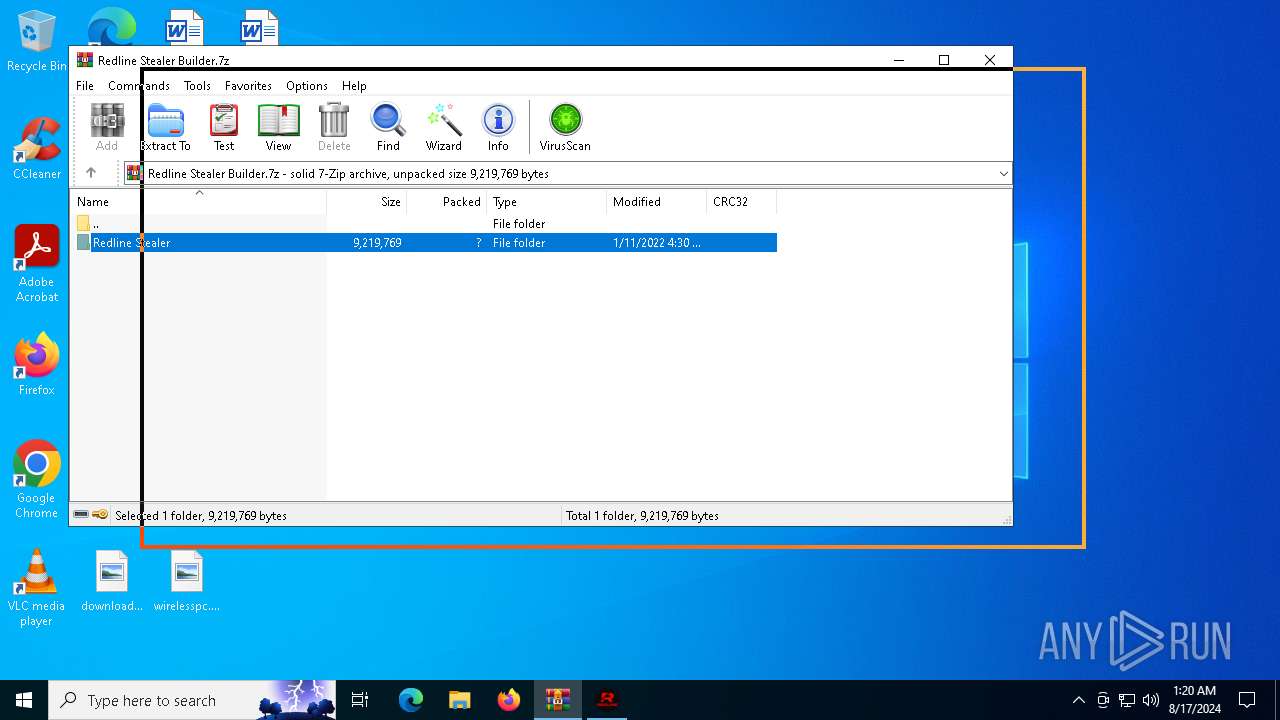
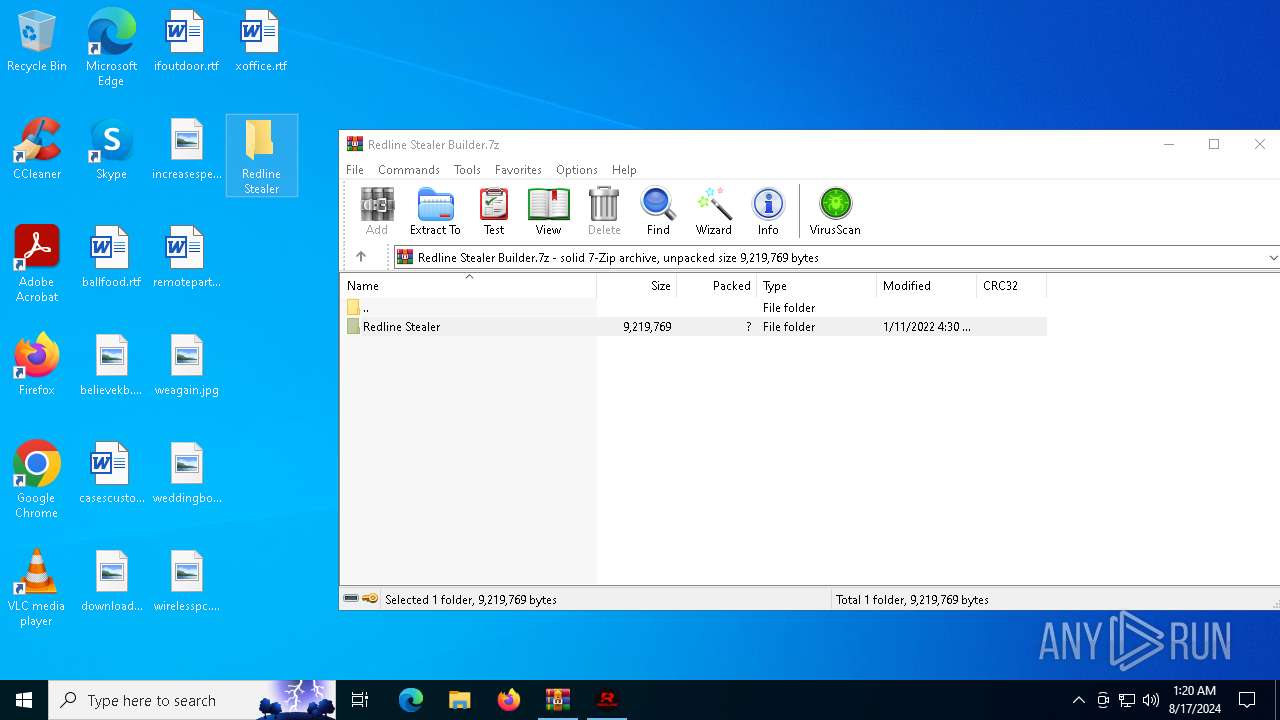
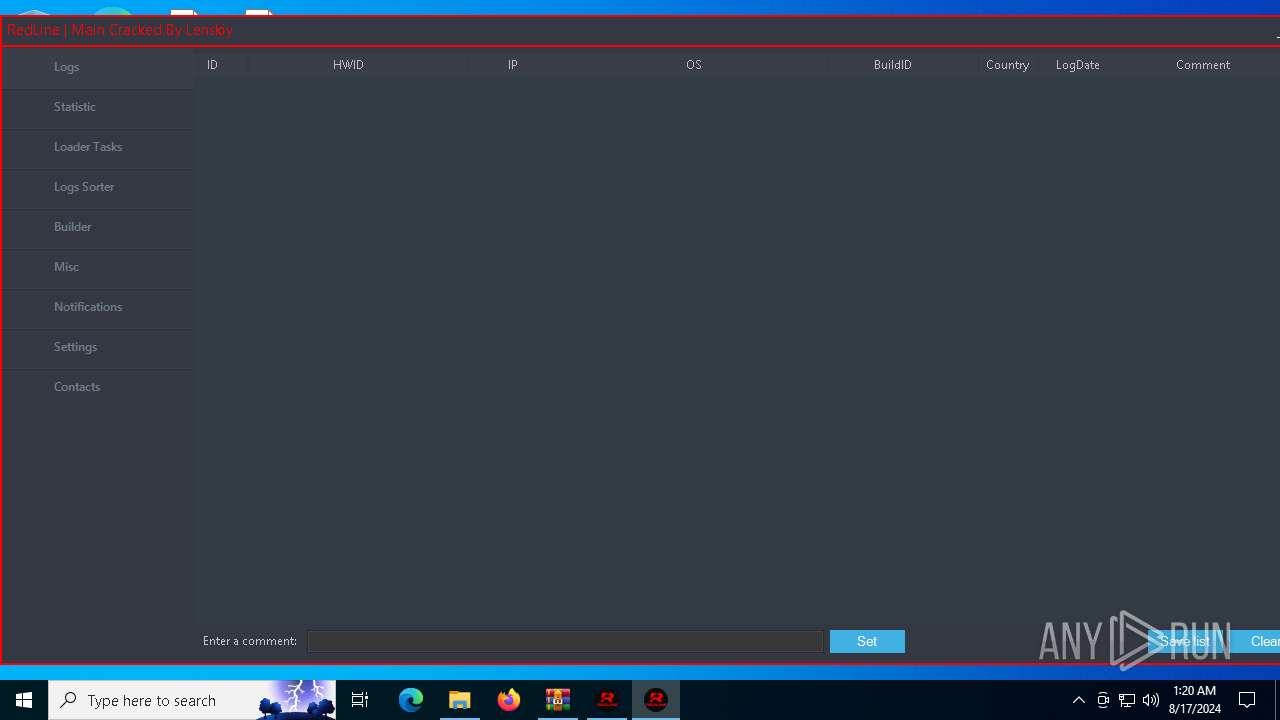
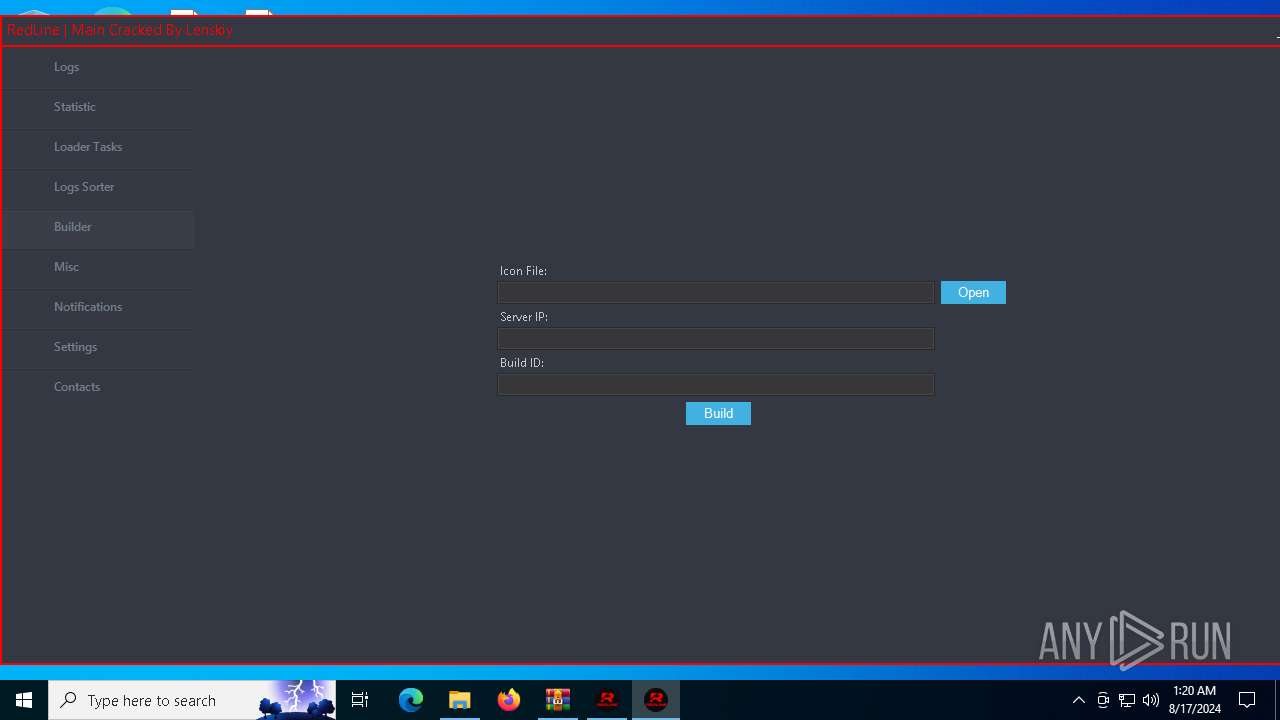
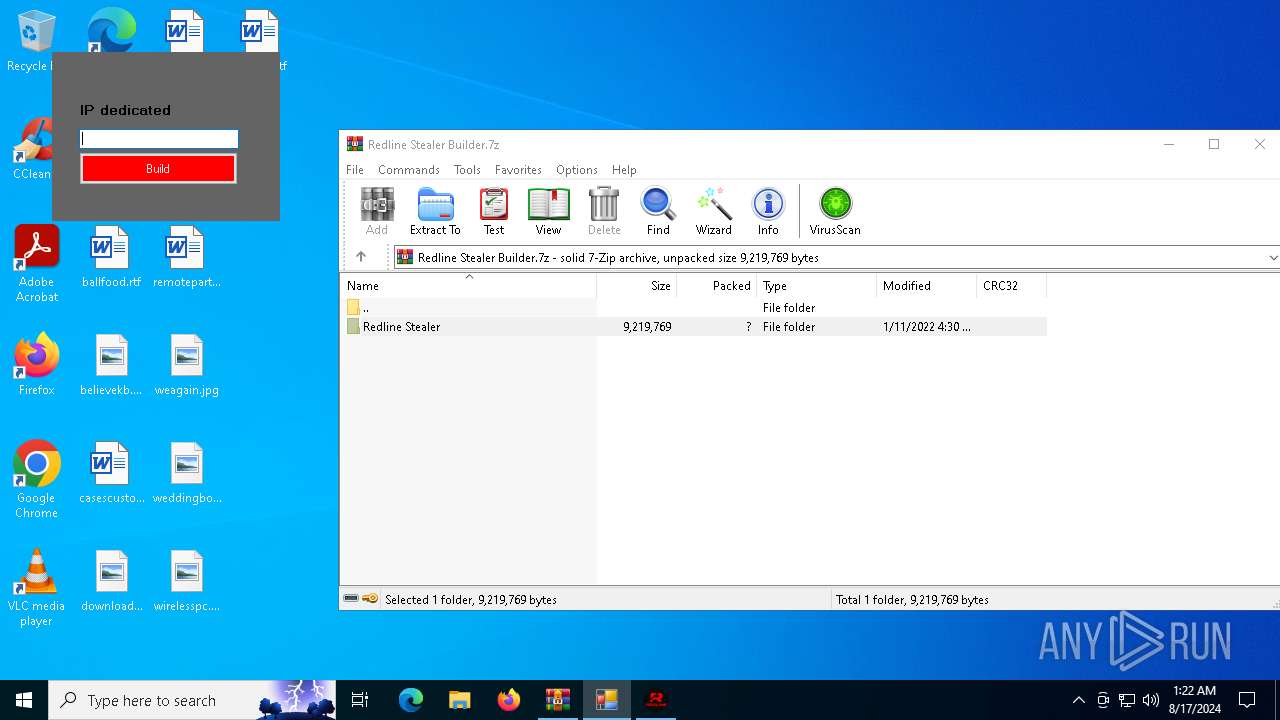
| File name: | Redline Stealer Builder.7z |
| Full analysis: | https://app.any.run/tasks/8c3ca19d-db21-4e11-940d-399933dacf63 |
| Verdict: | Malicious activity |
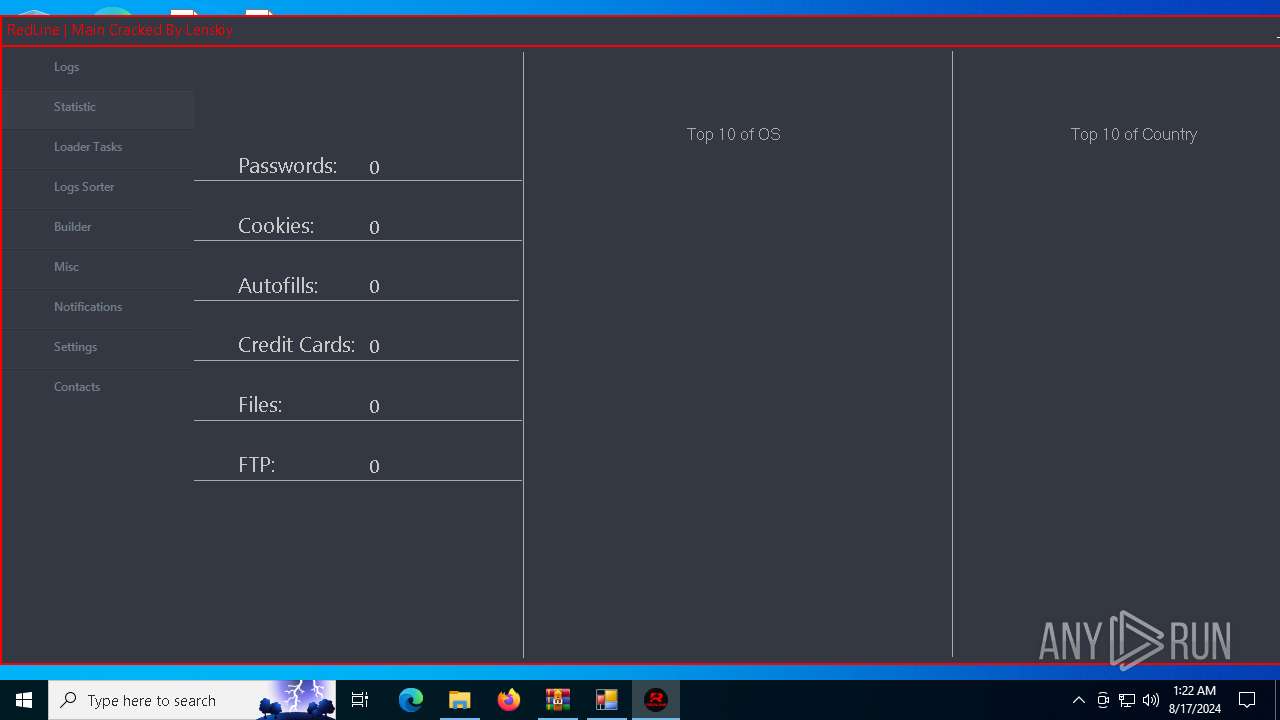
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | August 17, 2024, 01:19:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 3317523FCB65DE0CAD16632D204ADF2C |
| SHA1: | 8D68B943B791774933ACFC6A9B4E6A1E018B2439 |
| SHA256: | 4F758849CC2C1A02BAF4C275EA8FC9CC2FD9A380C157D066A984162FD43CBFE3 |
| SSDEEP: | 49152:w2IewijytNDSZsB3evk3kR7smlPRS1PBYu54GziGaWsIKlb3TRrCyxCIt/UbnxX3:wmBujB3evskR7s0S1PbeGziGaWsIKBVc |
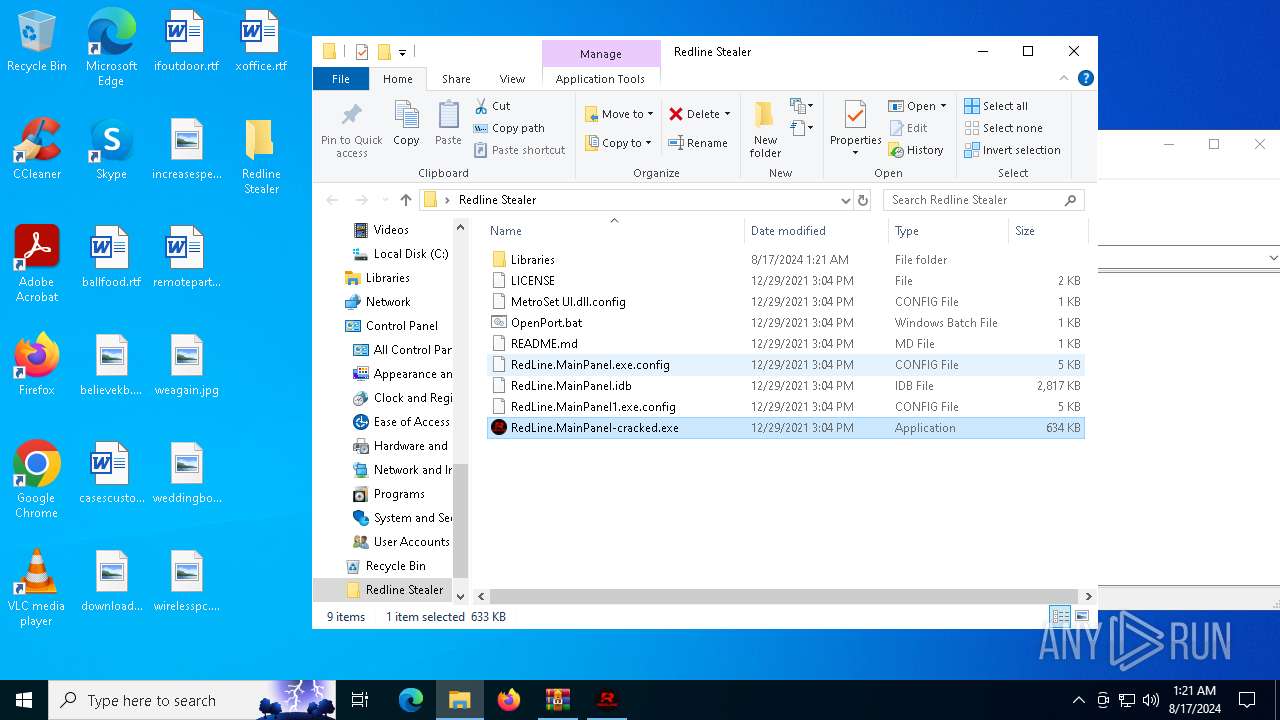
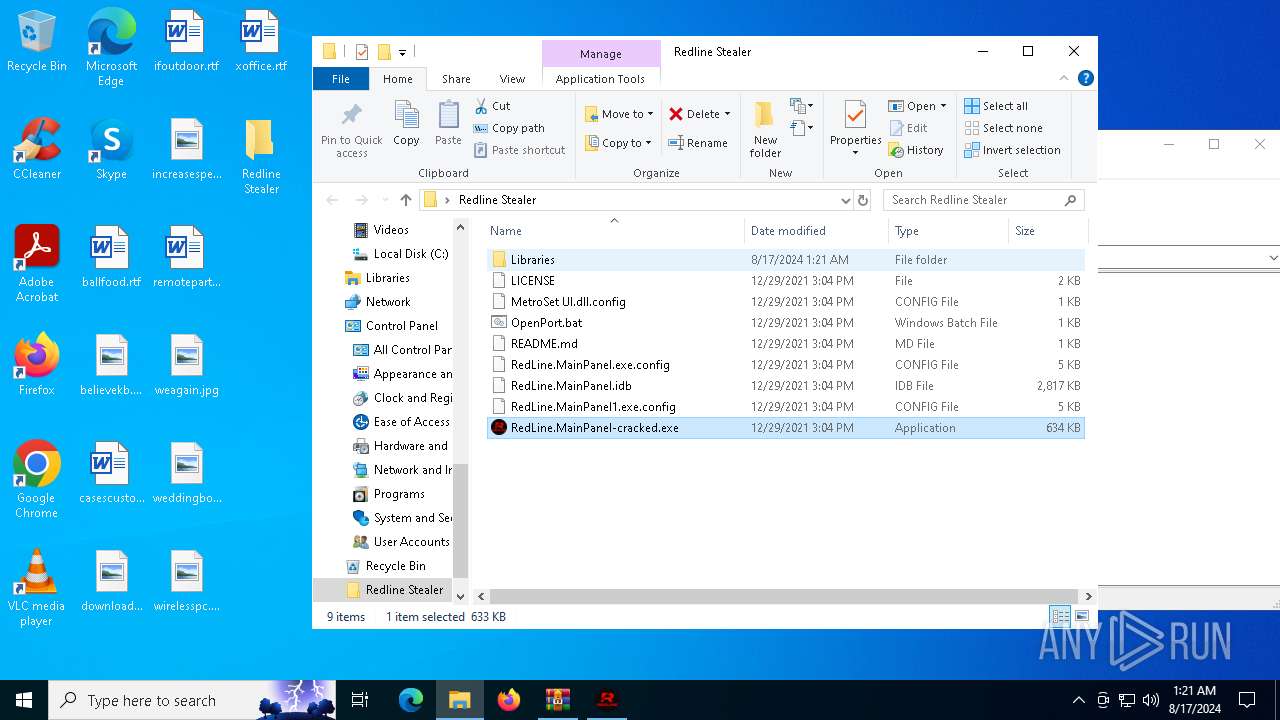
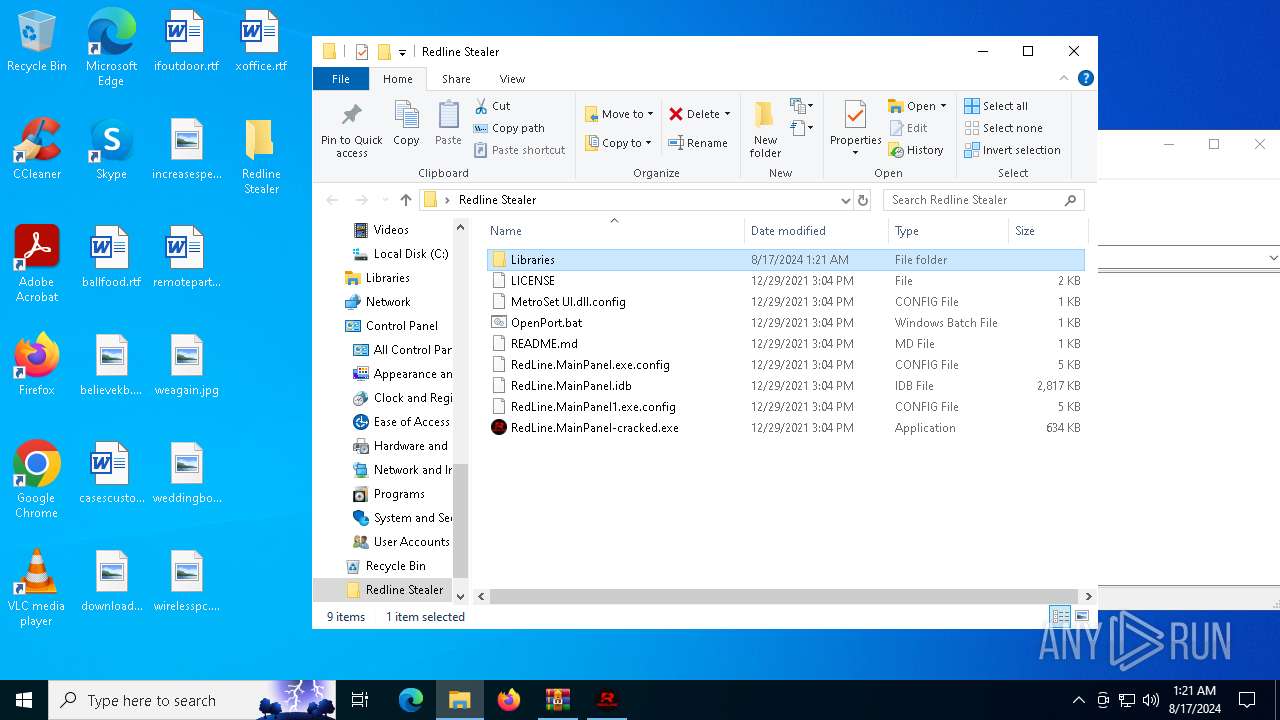
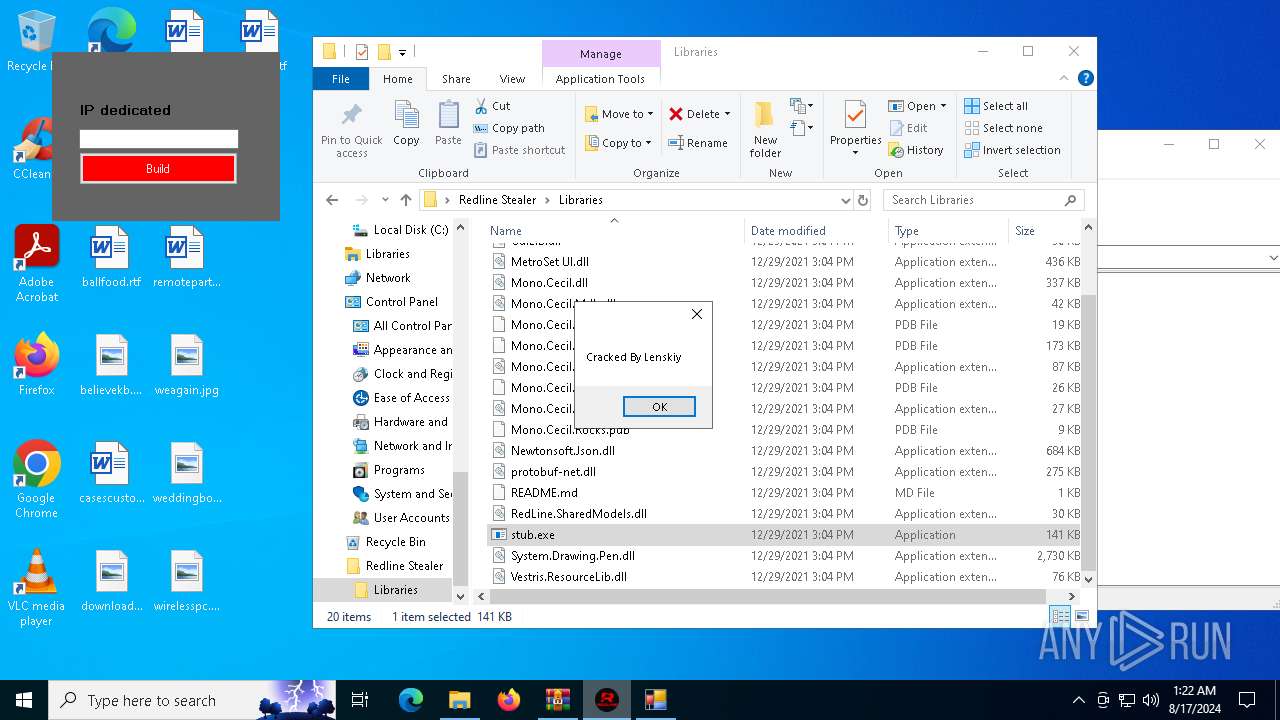
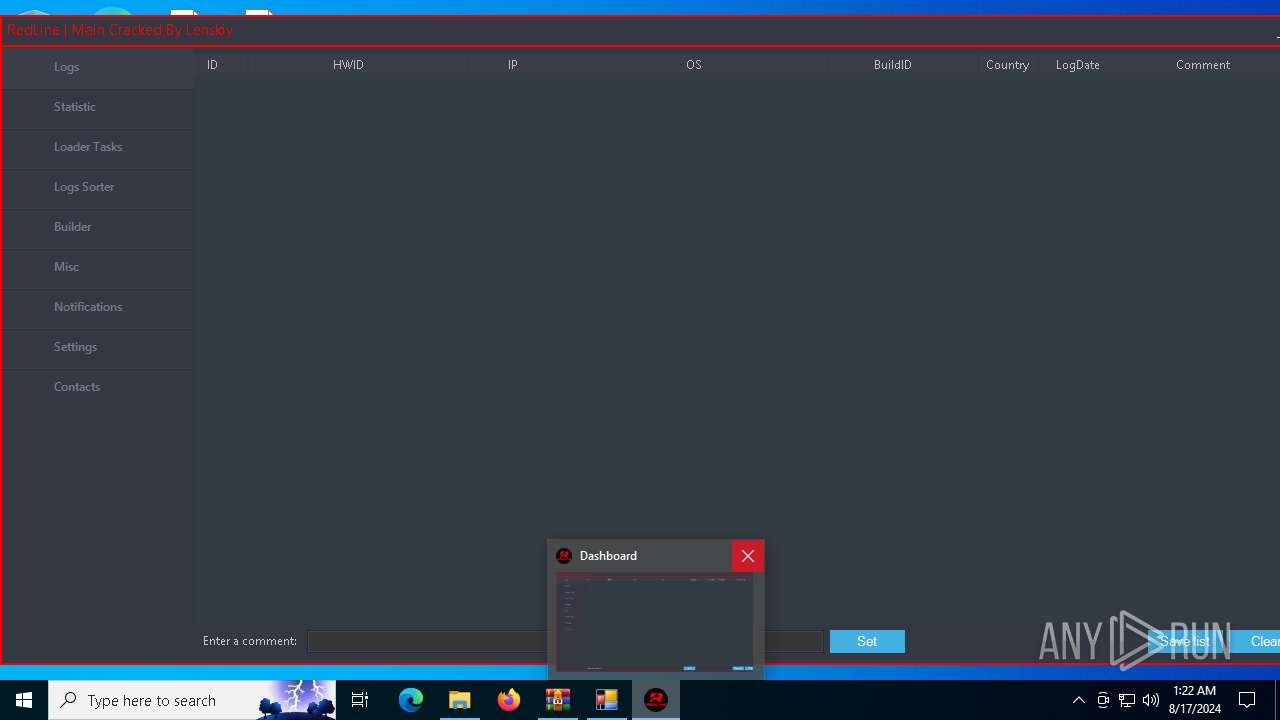
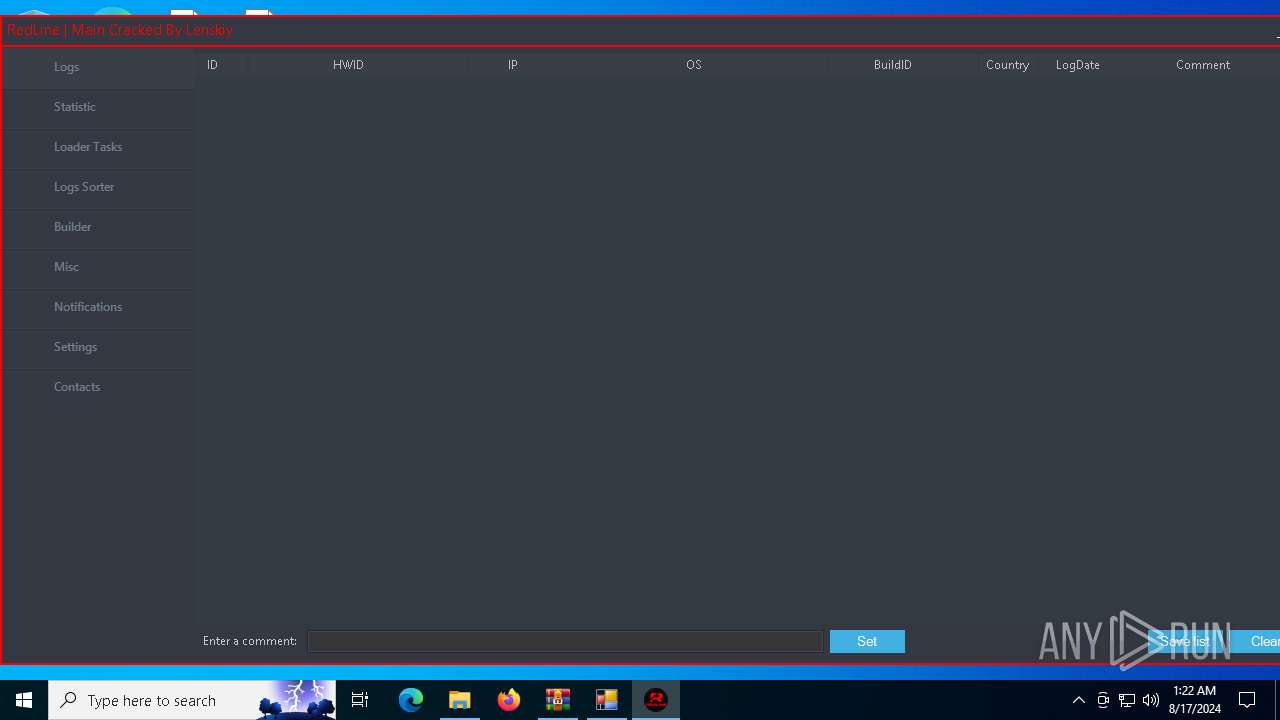
MALICIOUS
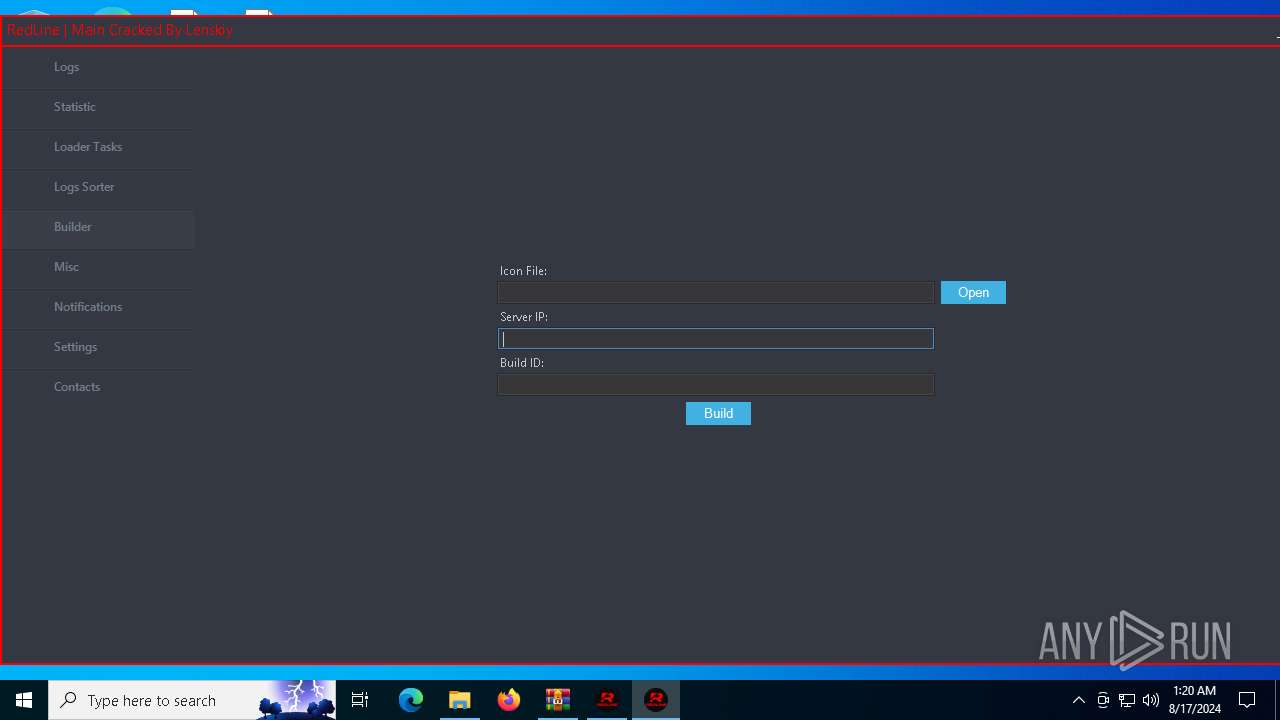
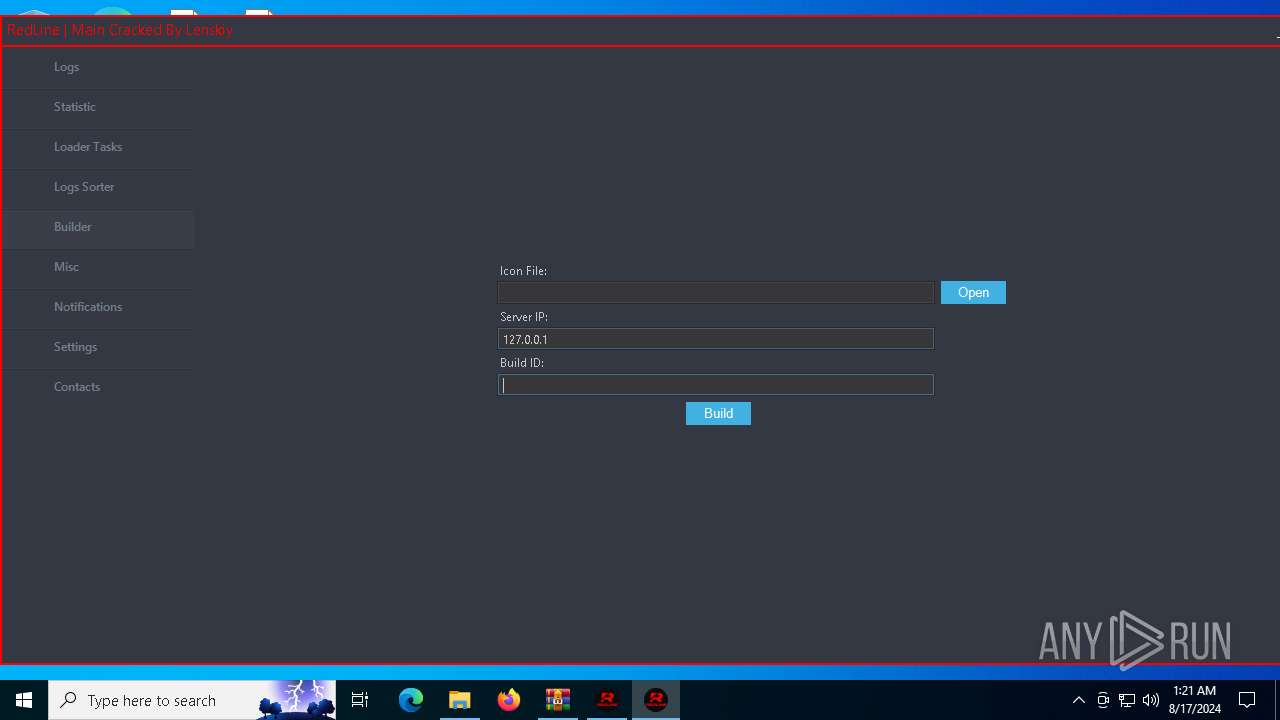
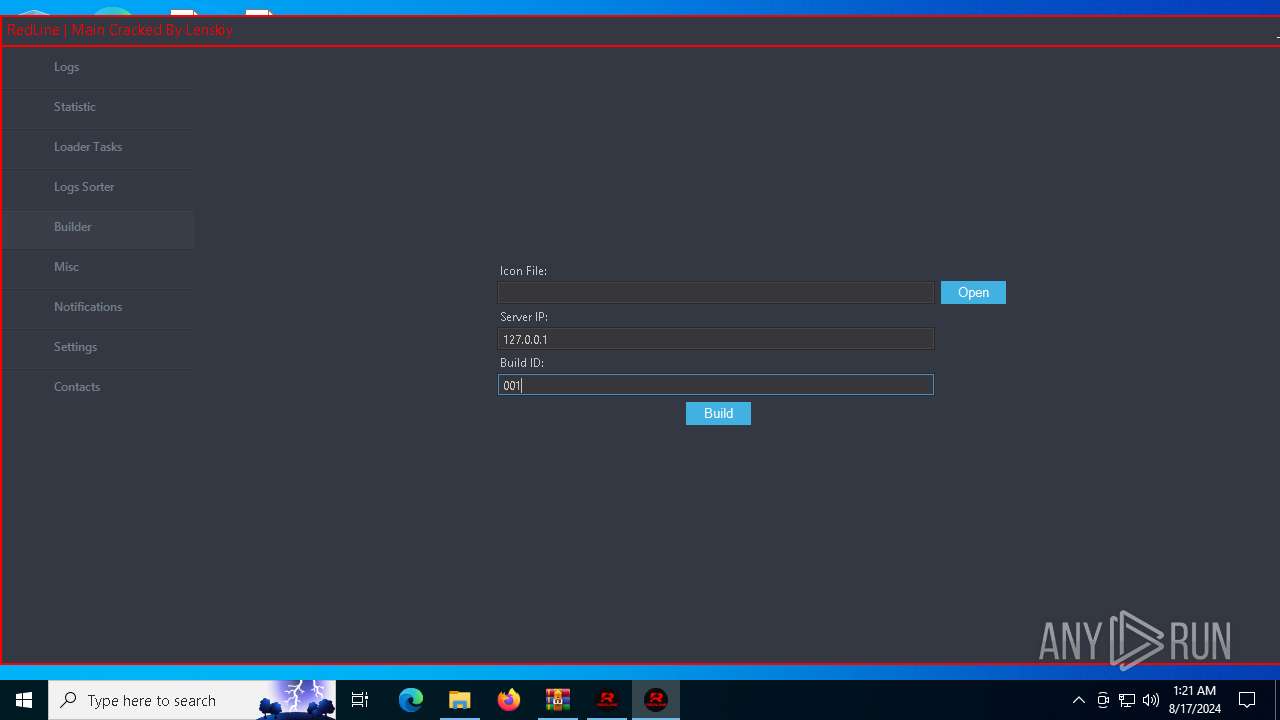
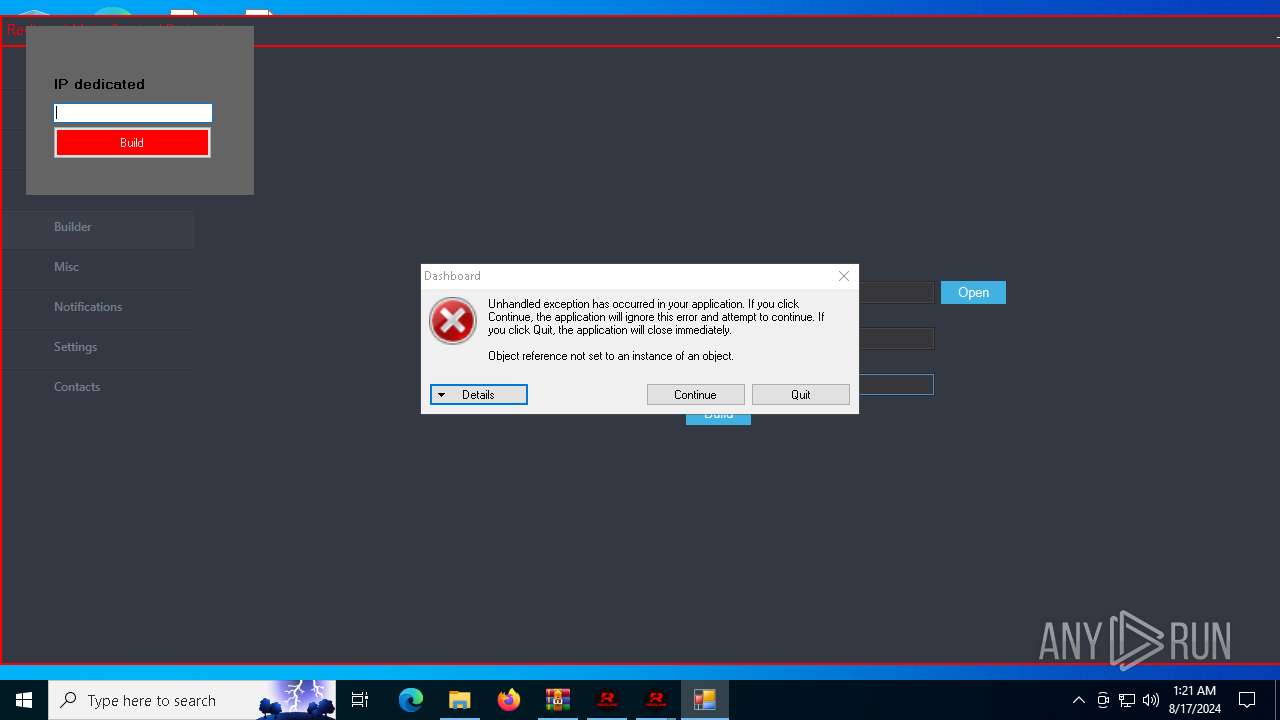
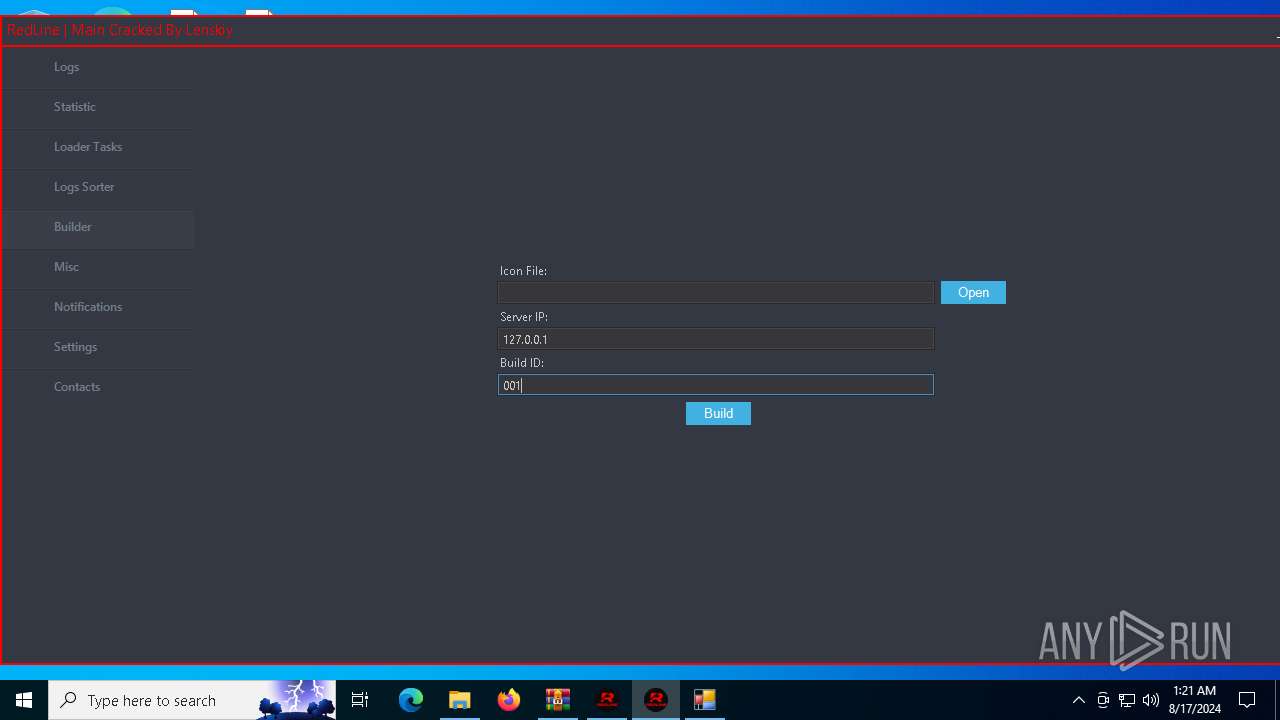
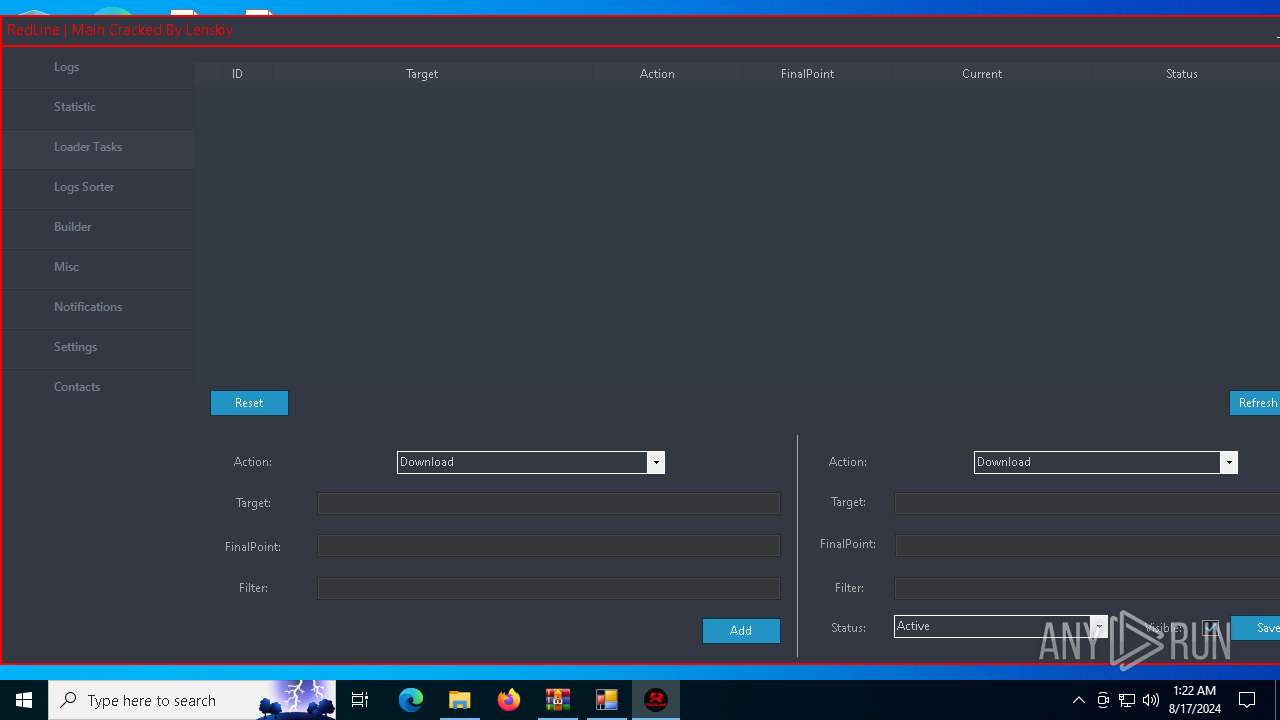
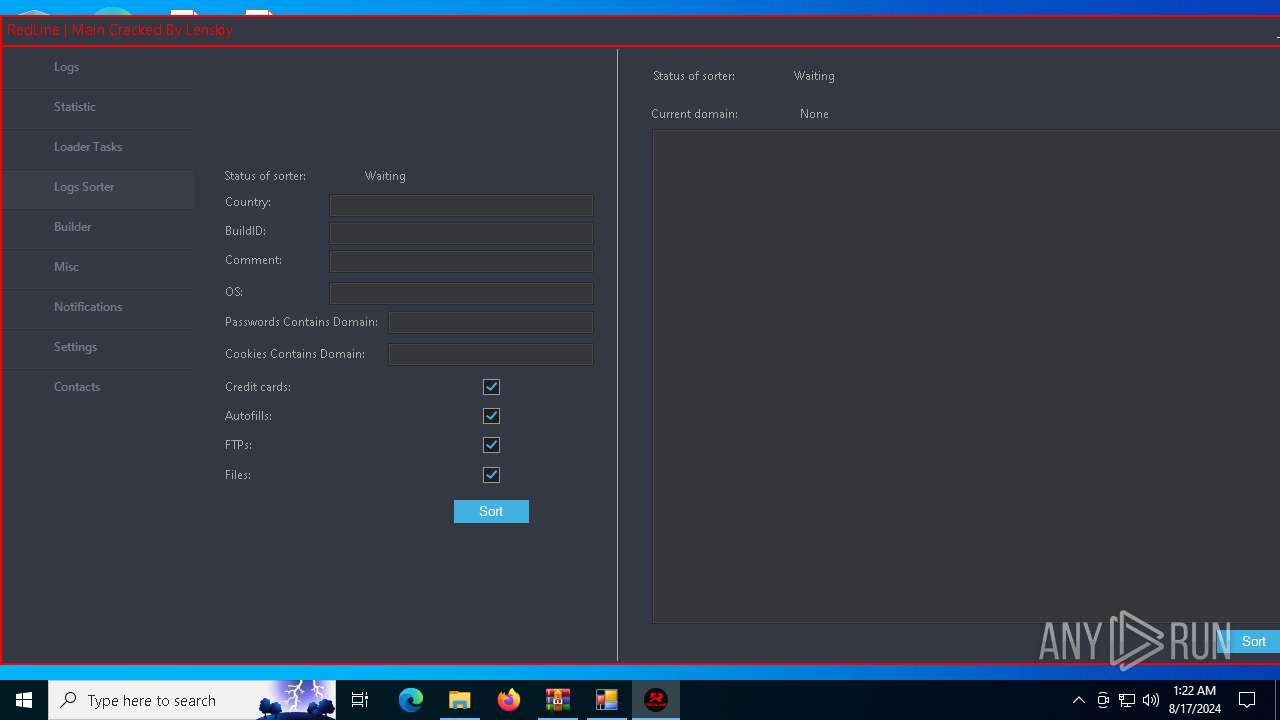
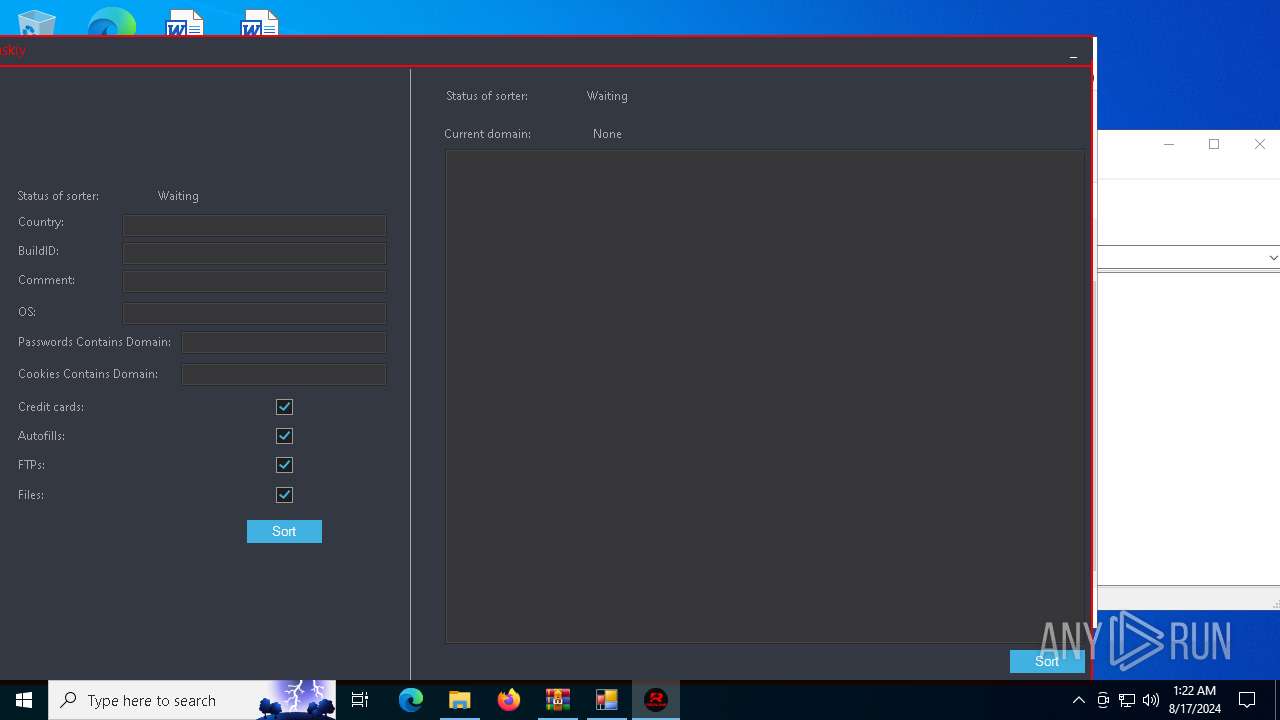
REDLINE has been detected (YARA)
- RedLine.MainPanel-cracked.exe (PID: 6168)
- RedLine.MainPanel-cracked.exe (PID: 6956)
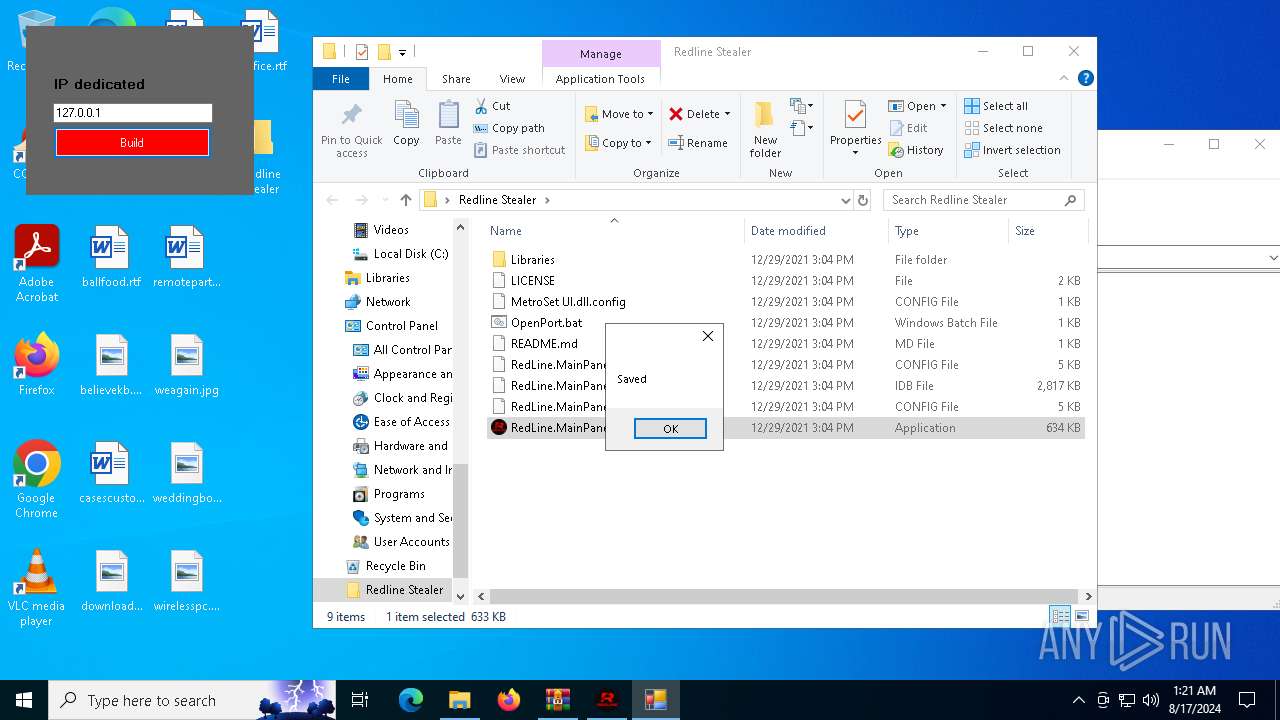
Starts CMD.EXE for self-deleting
- Build.exe (PID: 5092)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6388)
- RedLine.MainPanel-cracked.exe (PID: 6168)
- RedLine.MainPanel-cracked.exe (PID: 6956)
- builder.exe (PID: 872)
Reads the date of Windows installation
- RedLine.MainPanel-cracked.exe (PID: 6956)
Creates file in the systems drive root
- builder.exe (PID: 872)
Starts CMD.EXE for commands execution
- Build.exe (PID: 5092)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
The process checks if it is being run in the virtual environment
- builder.exe (PID: 872)
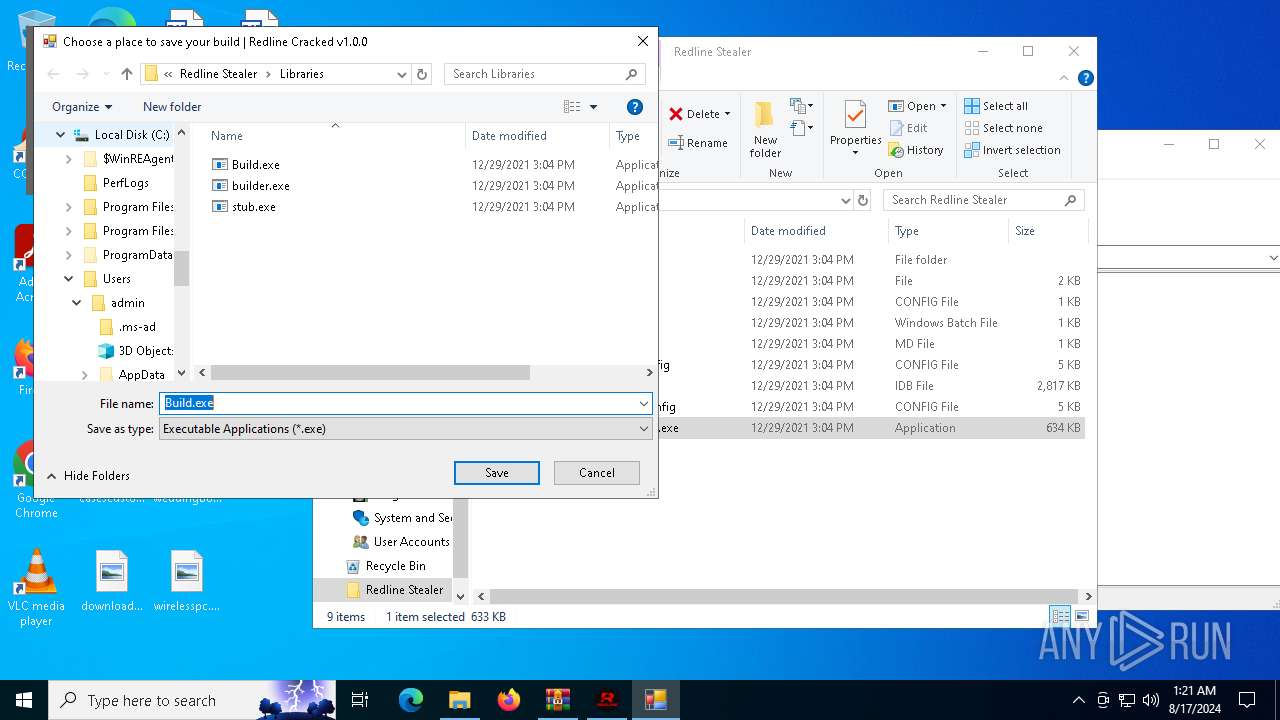
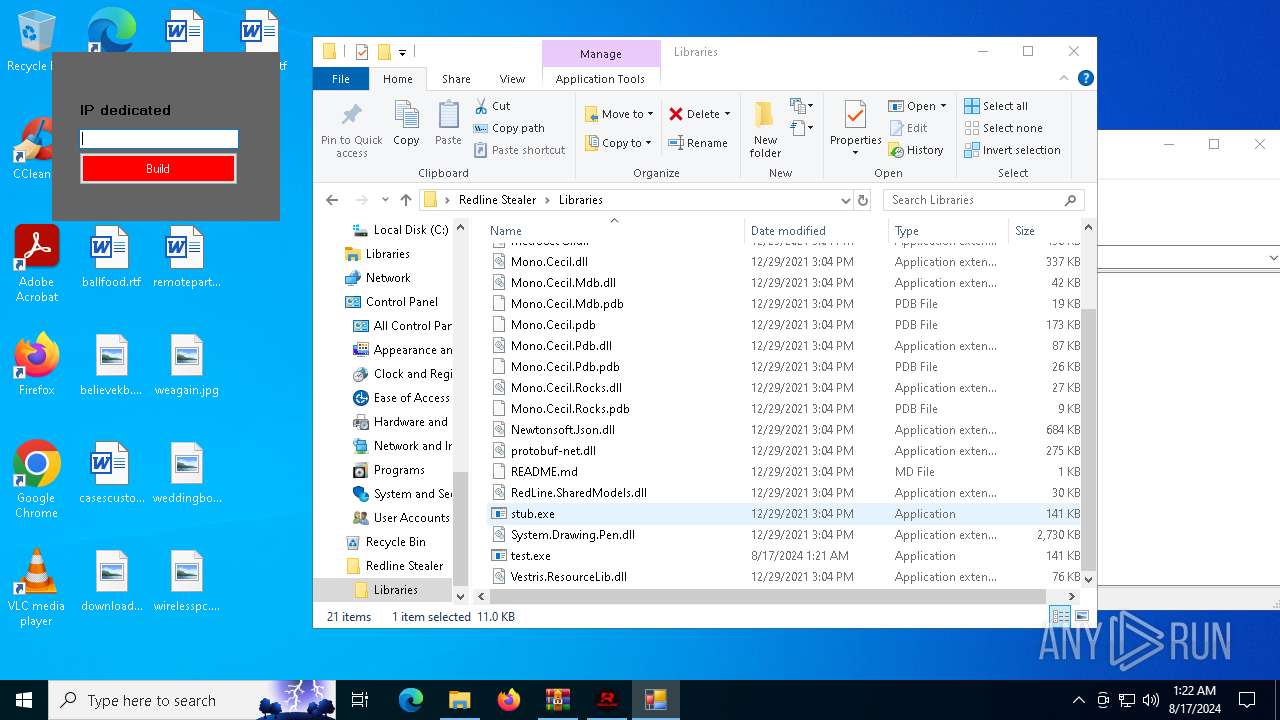
Executable content was dropped or overwritten
- builder.exe (PID: 872)
Drops the executable file immediately after the start
- builder.exe (PID: 872)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1948)
- cmd.exe (PID: 2208)
- cmd.exe (PID: 6936)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6388)
Reads the machine GUID from the registry
- RedLine.MainPanel-cracked.exe (PID: 6168)
- RedLine.MainPanel-cracked.exe (PID: 6956)
- builder.exe (PID: 872)
- Build.exe (PID: 5092)
- builder.exe (PID: 2136)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
Checks supported languages
- RedLine.MainPanel-cracked.exe (PID: 6168)
- RedLine.MainPanel-cracked.exe (PID: 6956)
- builder.exe (PID: 872)
- Build.exe (PID: 5092)
- builder.exe (PID: 2136)
- stub.exe (PID: 3032)
- test.exe (PID: 3540)
Reads the computer name
- RedLine.MainPanel-cracked.exe (PID: 6956)
- RedLine.MainPanel-cracked.exe (PID: 6168)
- builder.exe (PID: 872)
- Build.exe (PID: 5092)
- builder.exe (PID: 2136)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
Manual execution by a user
- RedLine.MainPanel-cracked.exe (PID: 6956)
- Build.exe (PID: 5092)
- builder.exe (PID: 2136)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
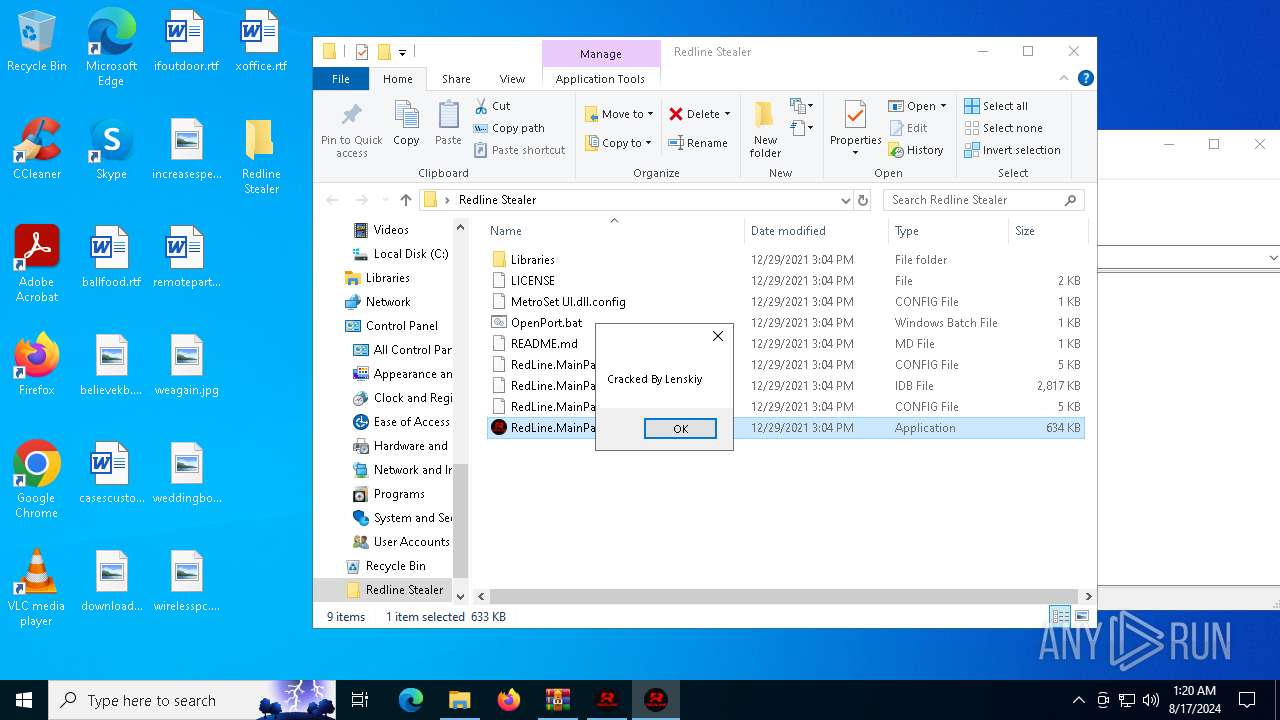
.NET Reactor protector has been detected
- RedLine.MainPanel-cracked.exe (PID: 6168)
- RedLine.MainPanel-cracked.exe (PID: 6956)
Reads Environment values
- RedLine.MainPanel-cracked.exe (PID: 6956)
- Build.exe (PID: 5092)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
- RedLine.MainPanel-cracked.exe (PID: 6168)
Process checks computer location settings
- RedLine.MainPanel-cracked.exe (PID: 6956)
Disables trace logs
- Build.exe (PID: 5092)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
Checks proxy server information
- Build.exe (PID: 5092)
- test.exe (PID: 3540)
- stub.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
155
Monitored processes
21
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
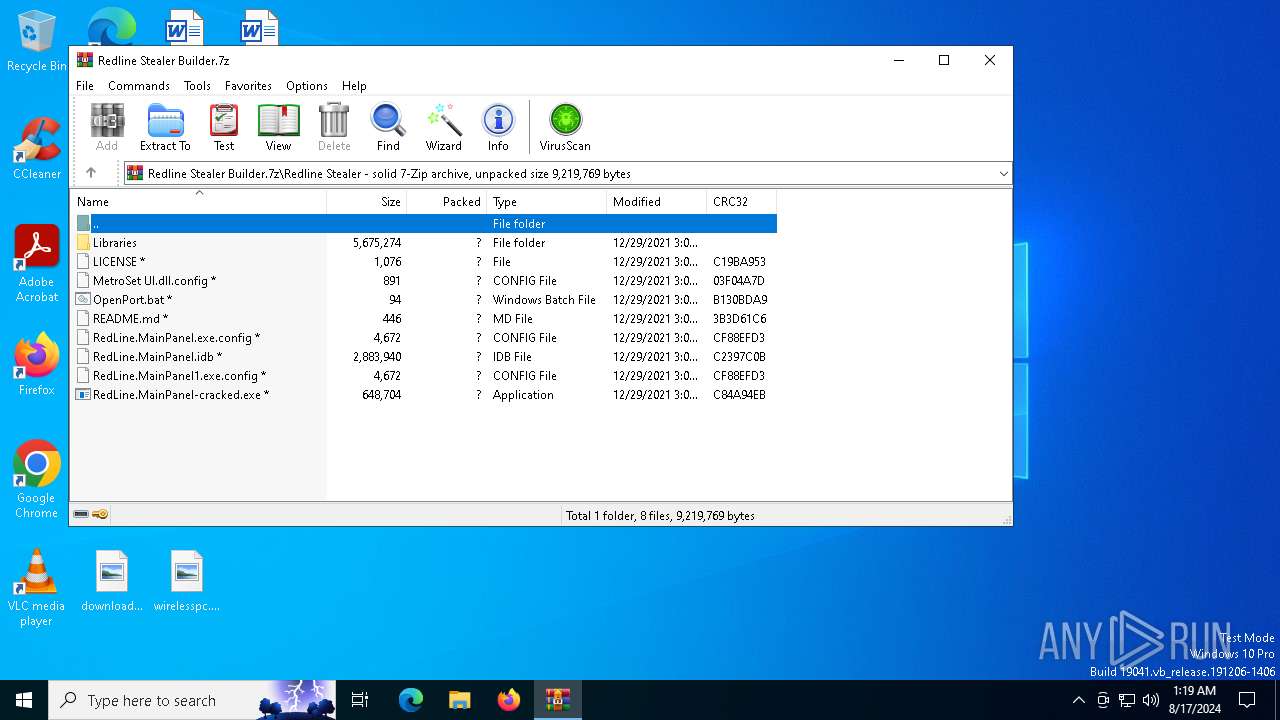
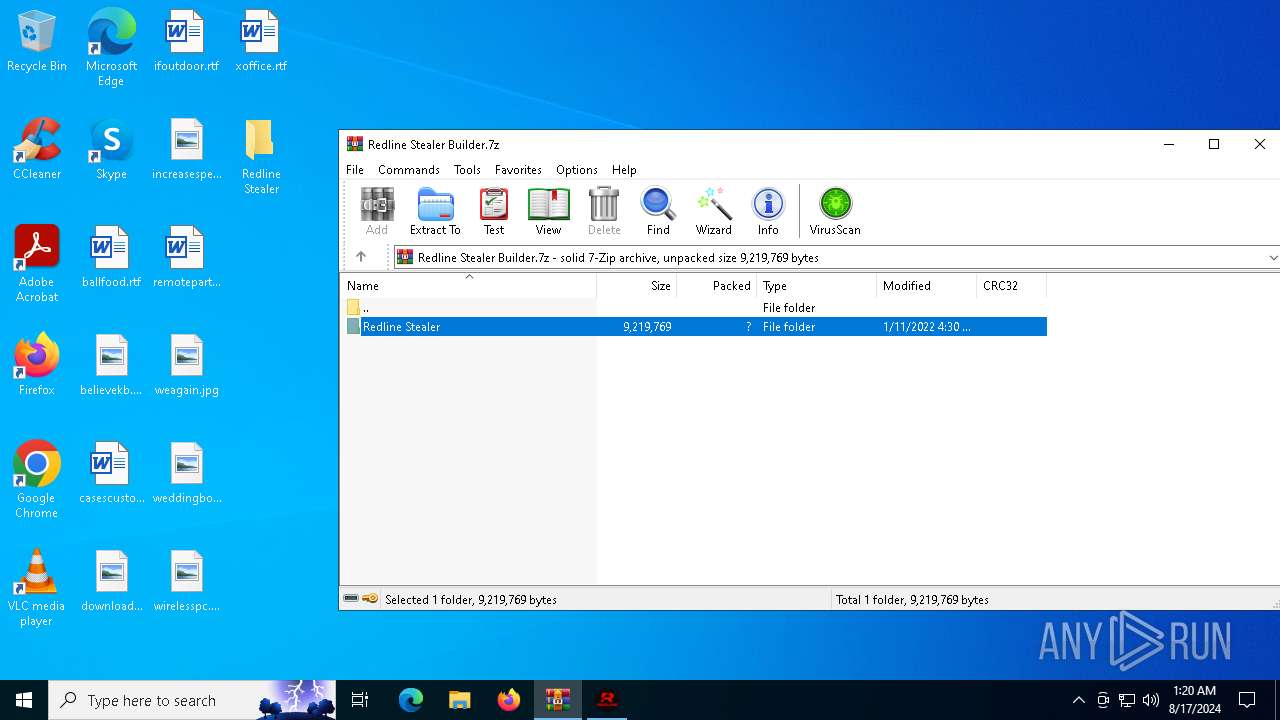
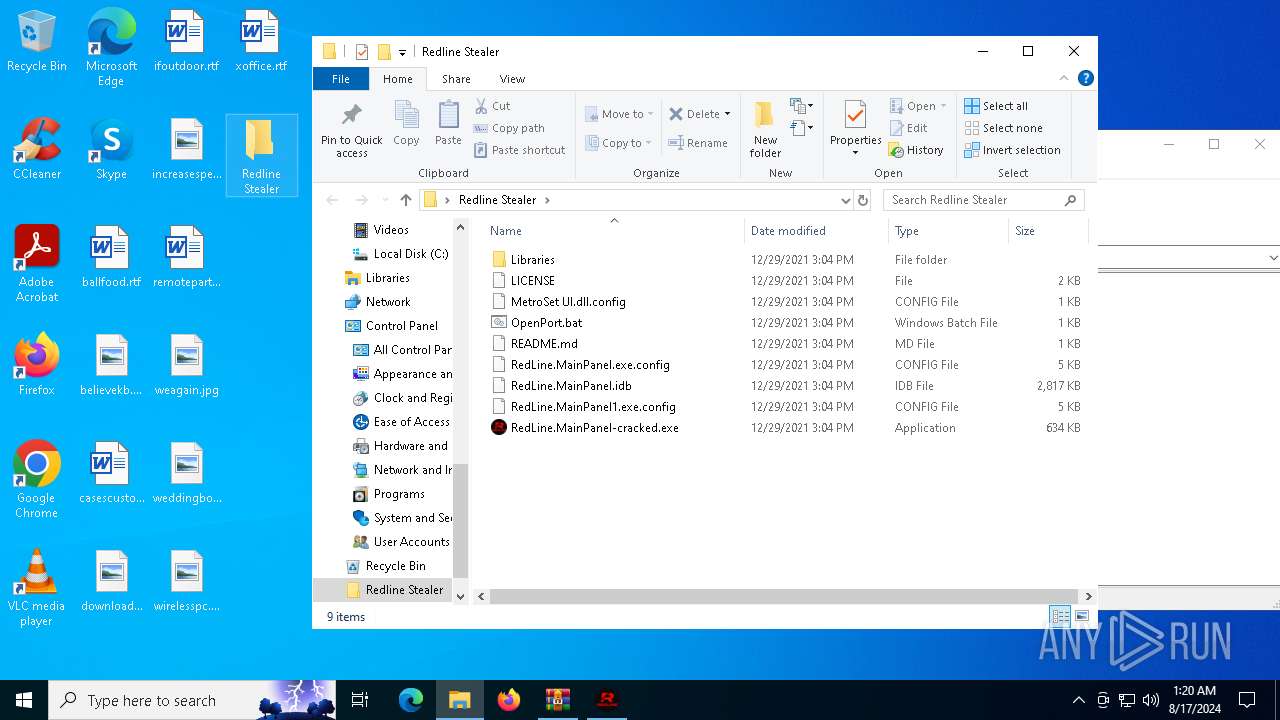
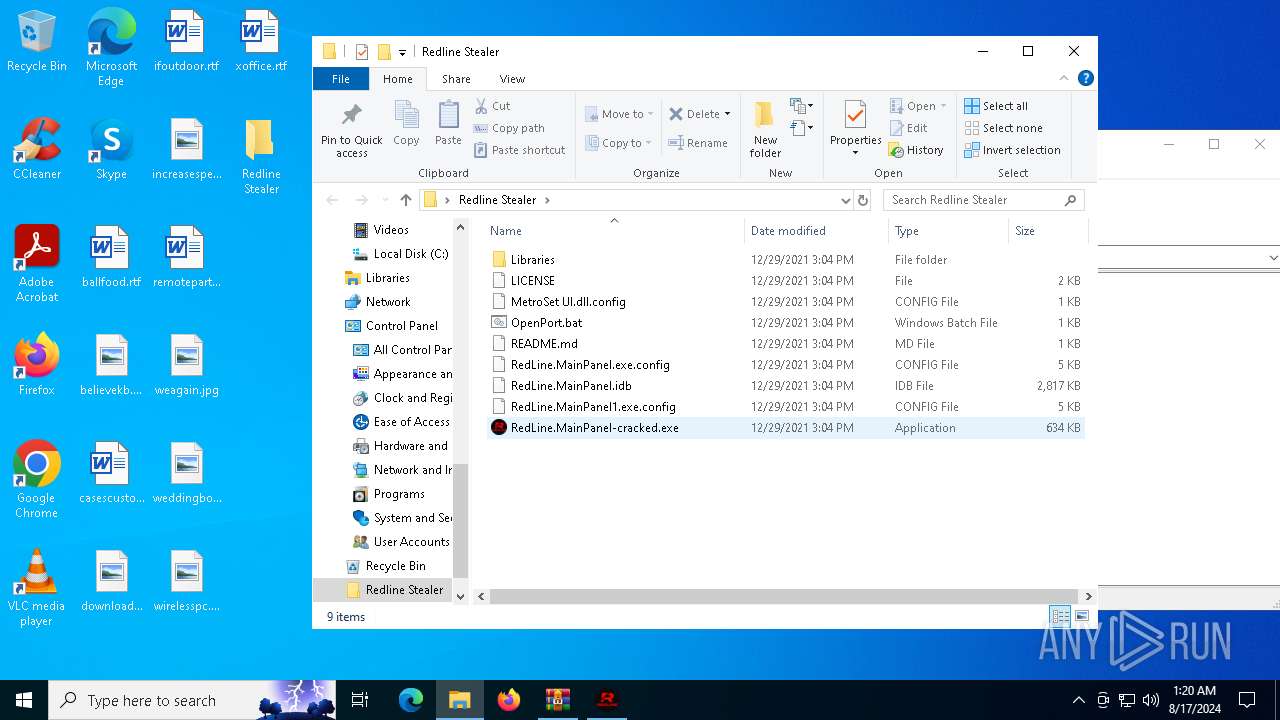
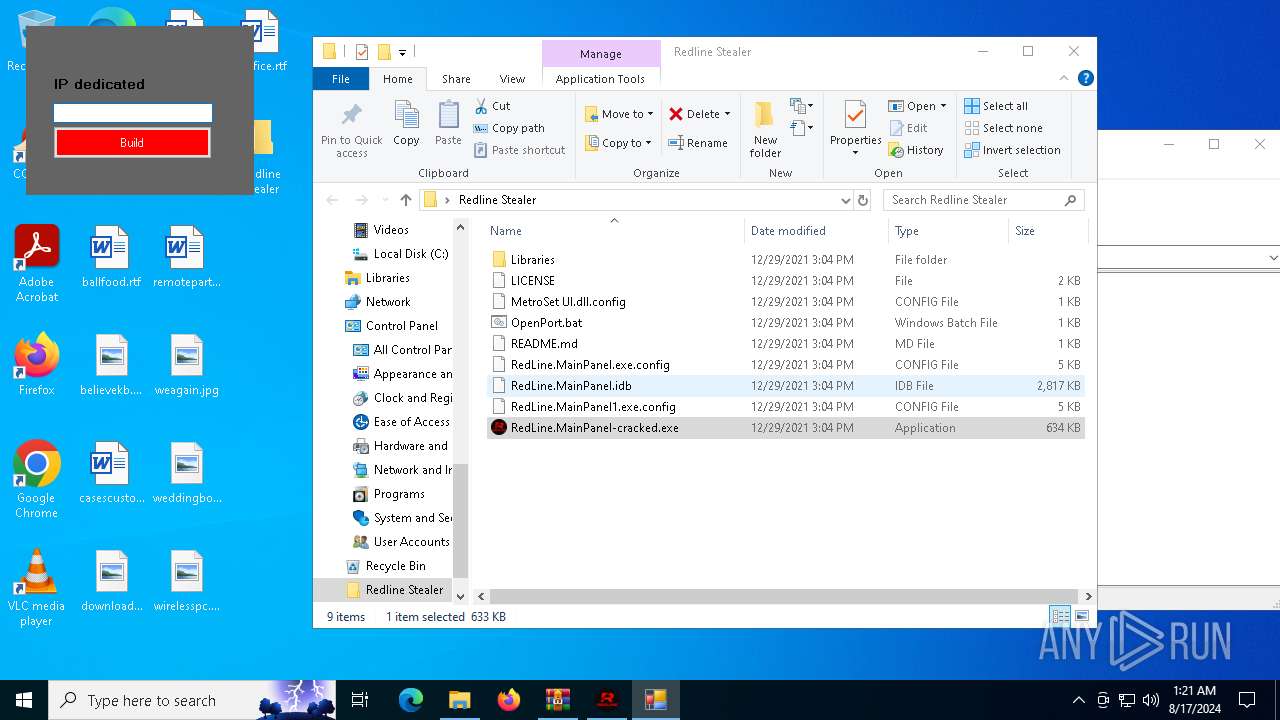
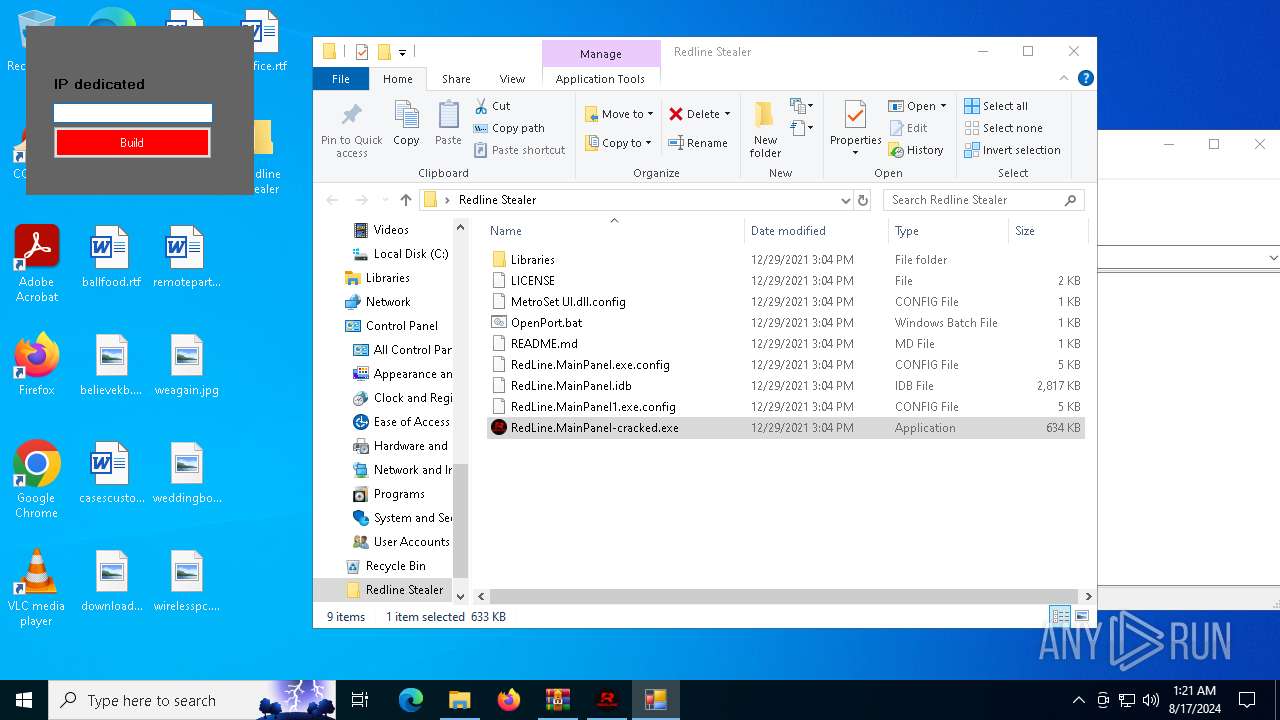
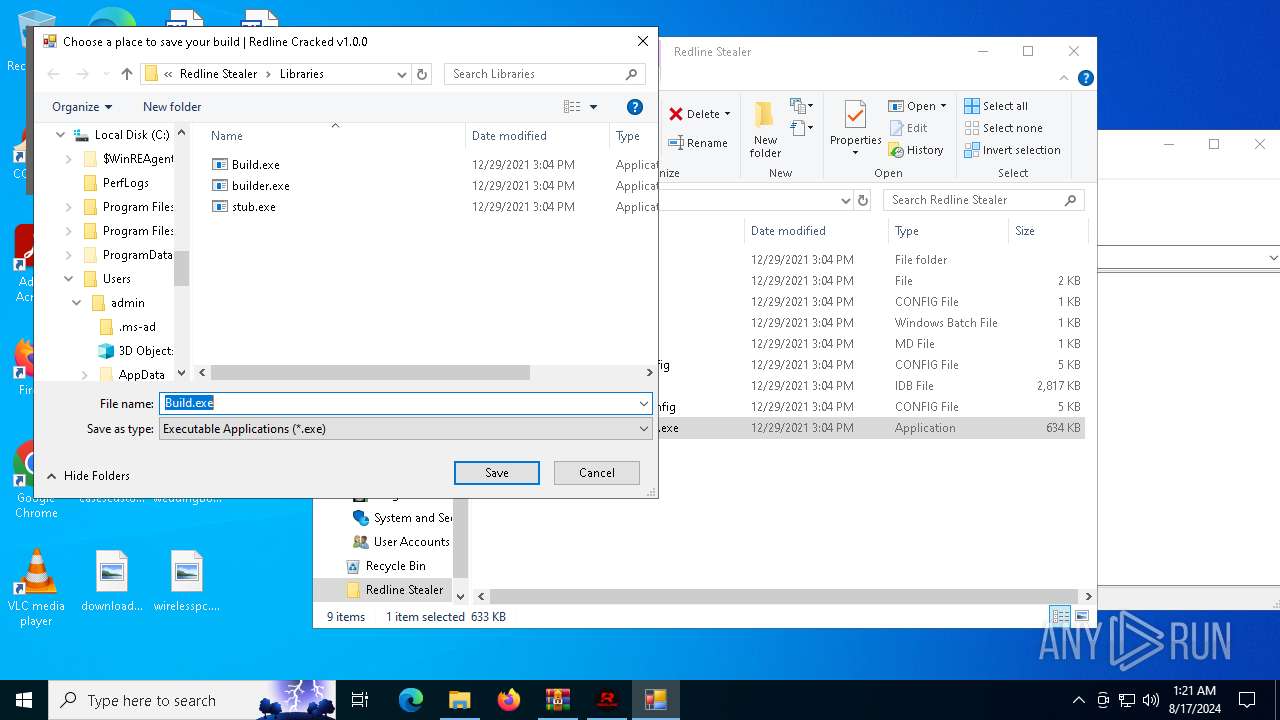
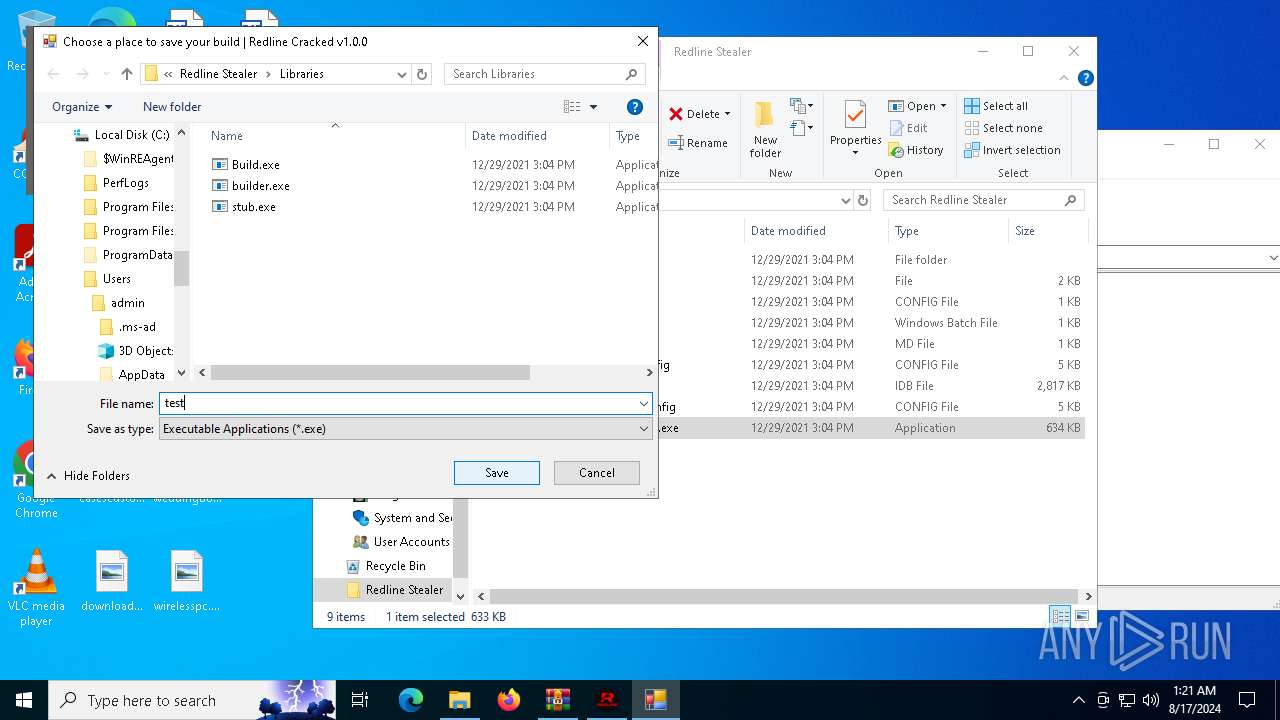
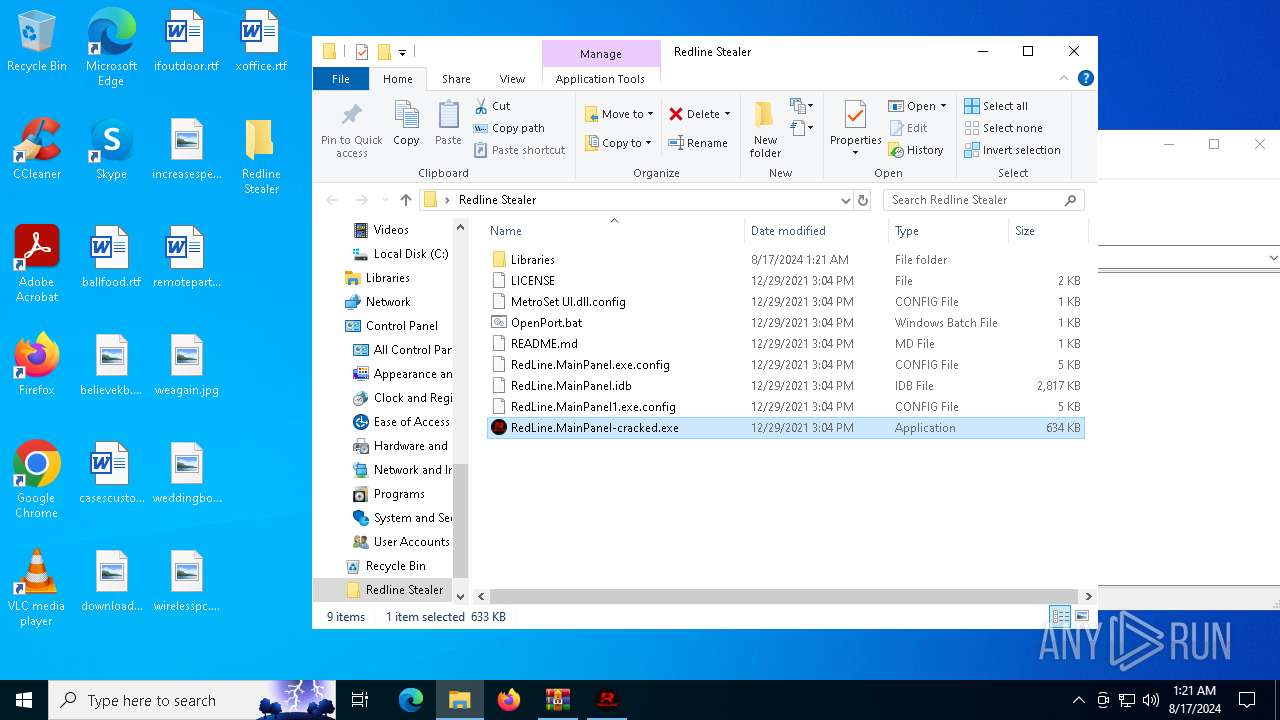
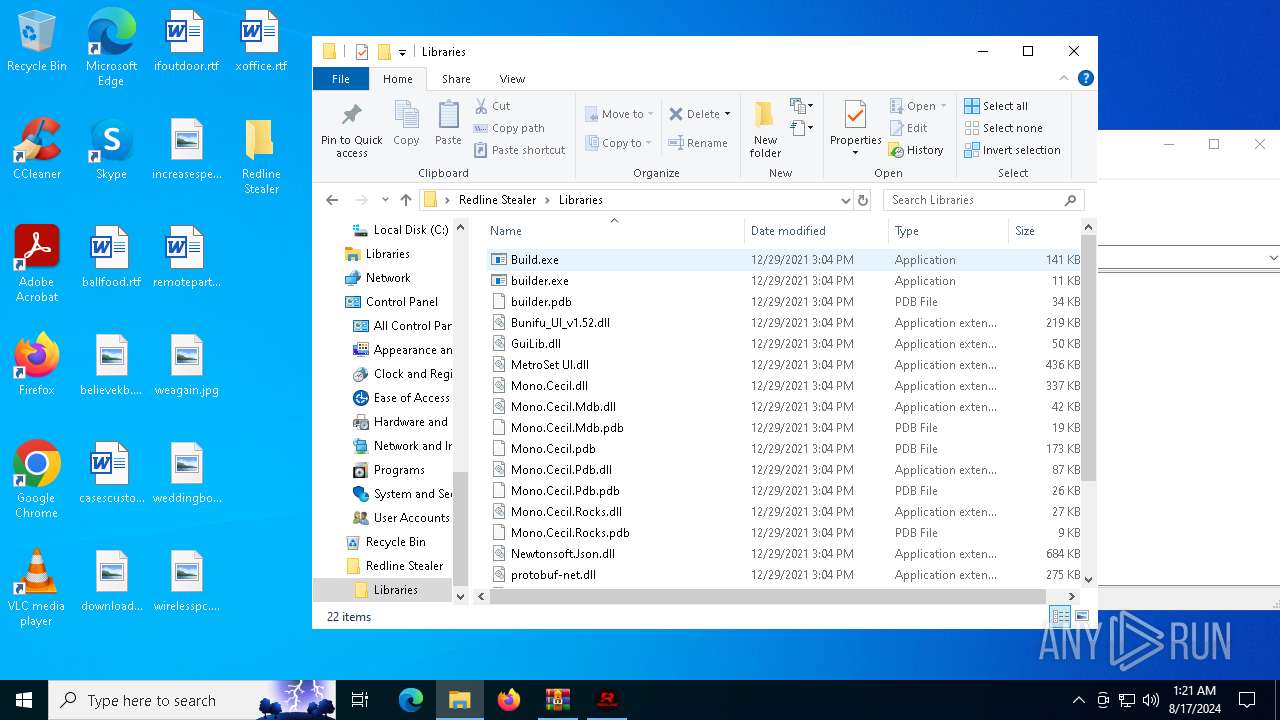
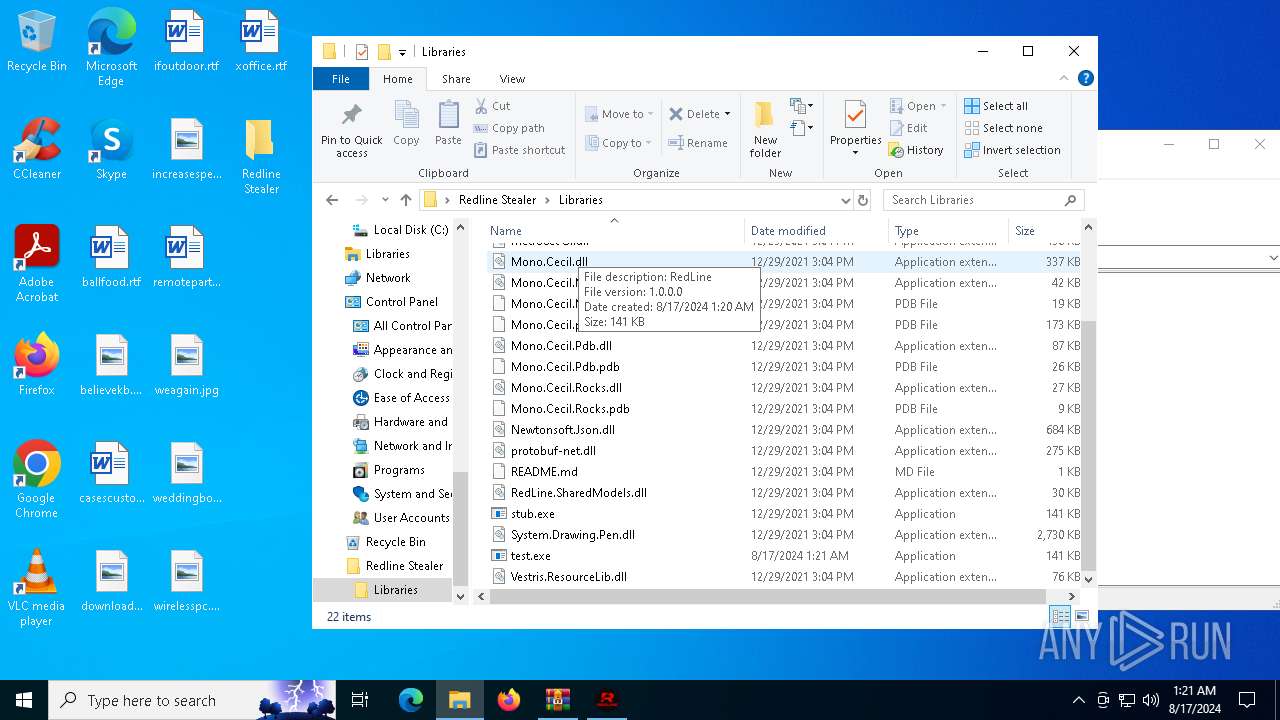
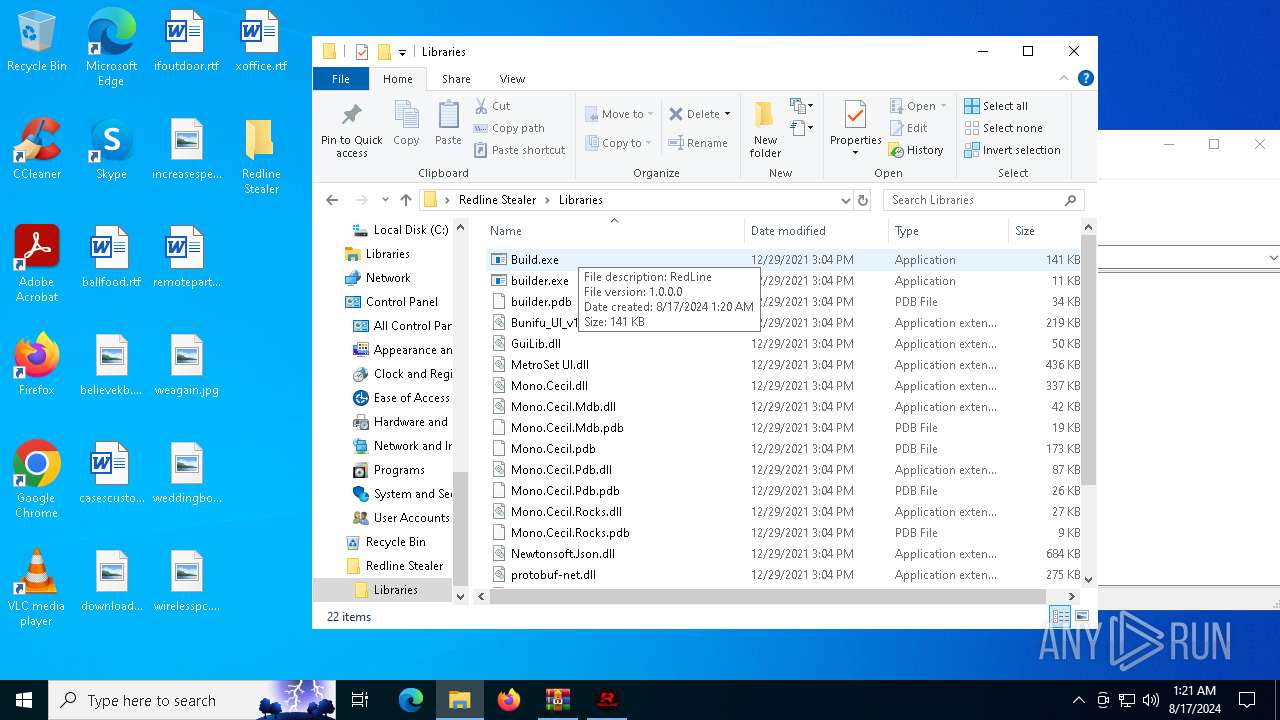
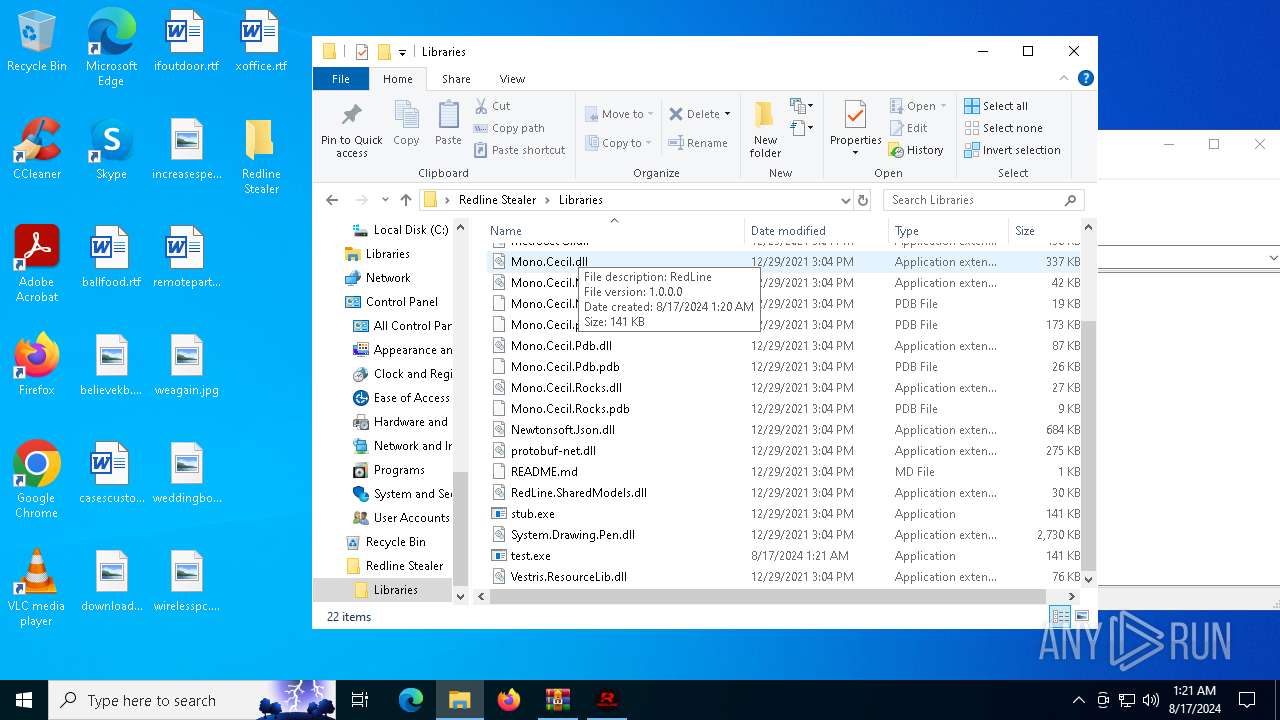
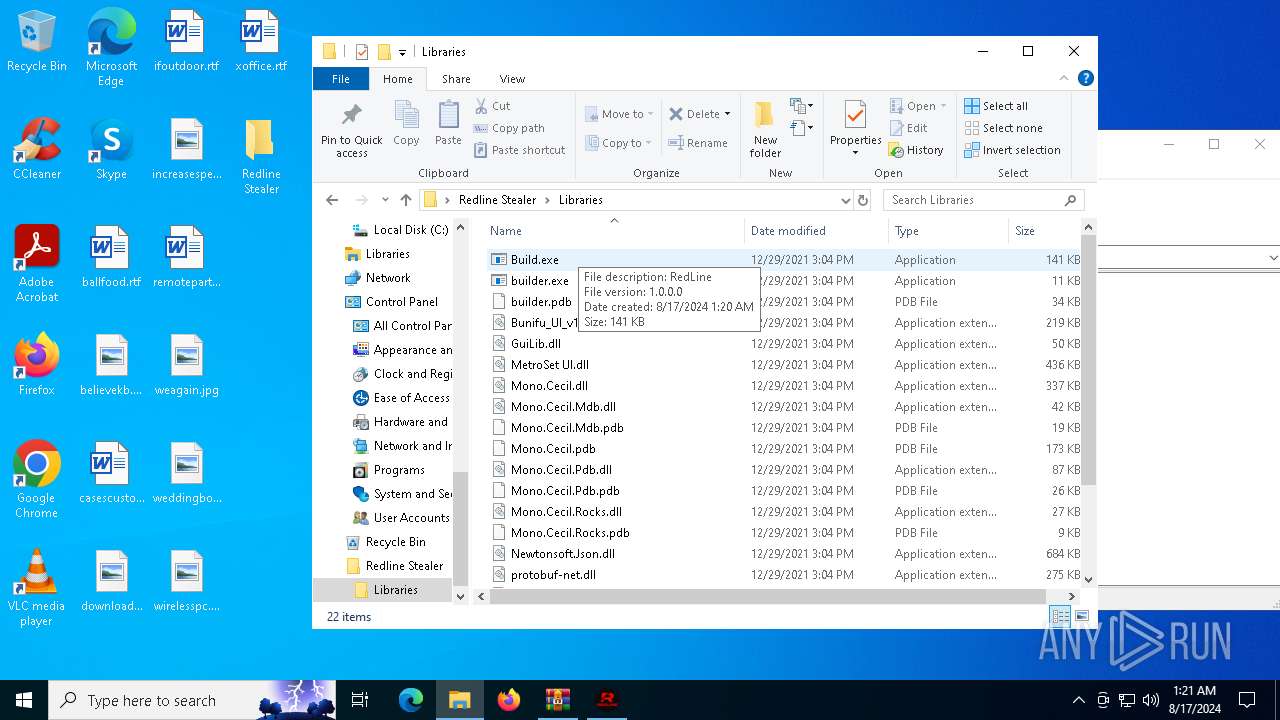
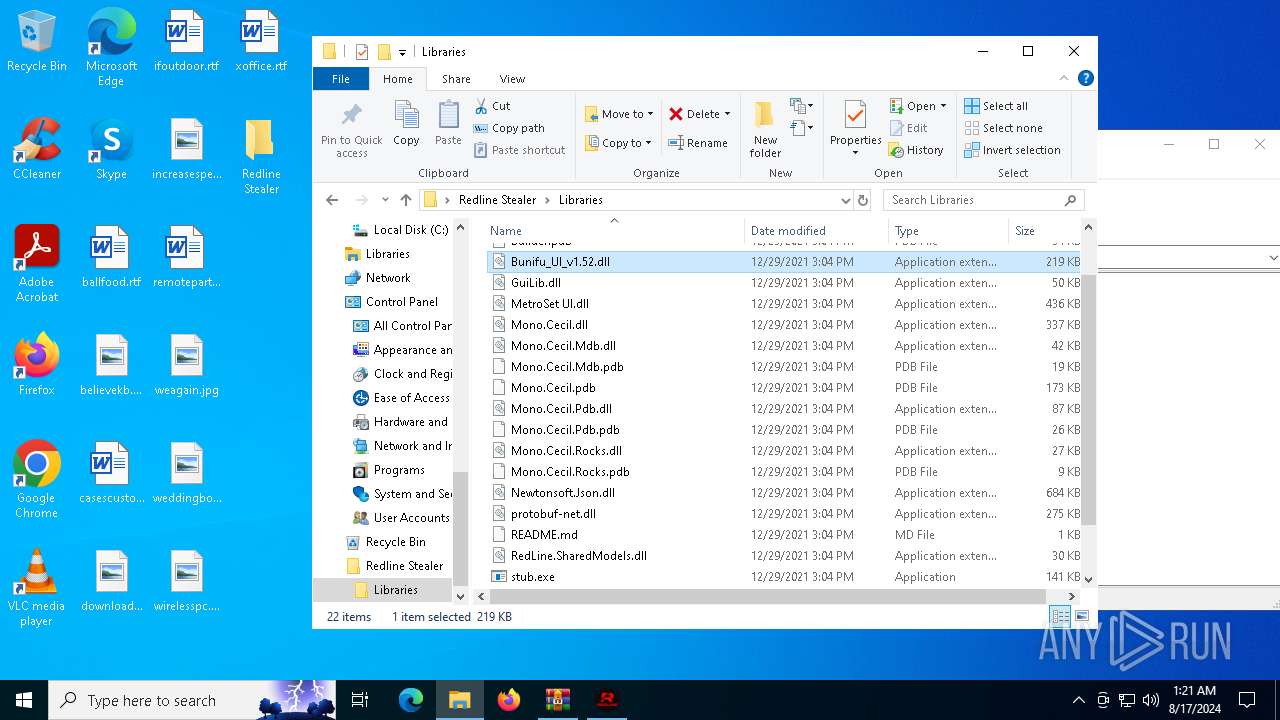
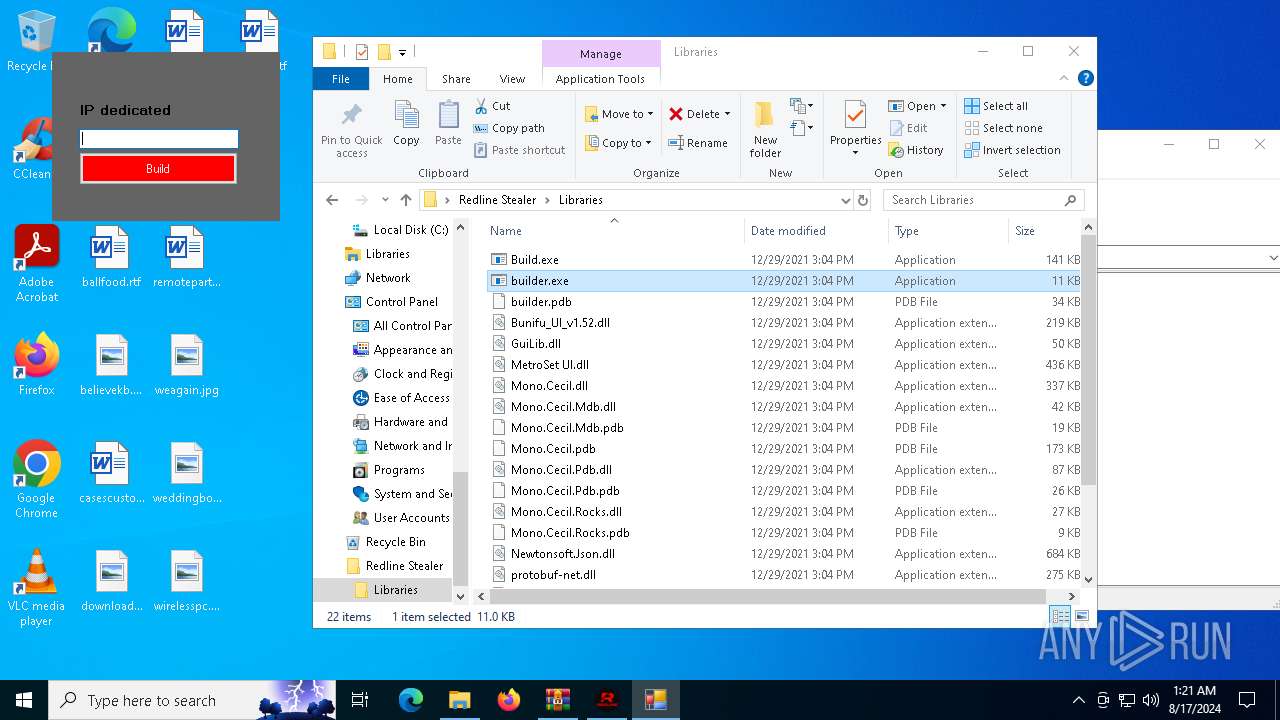
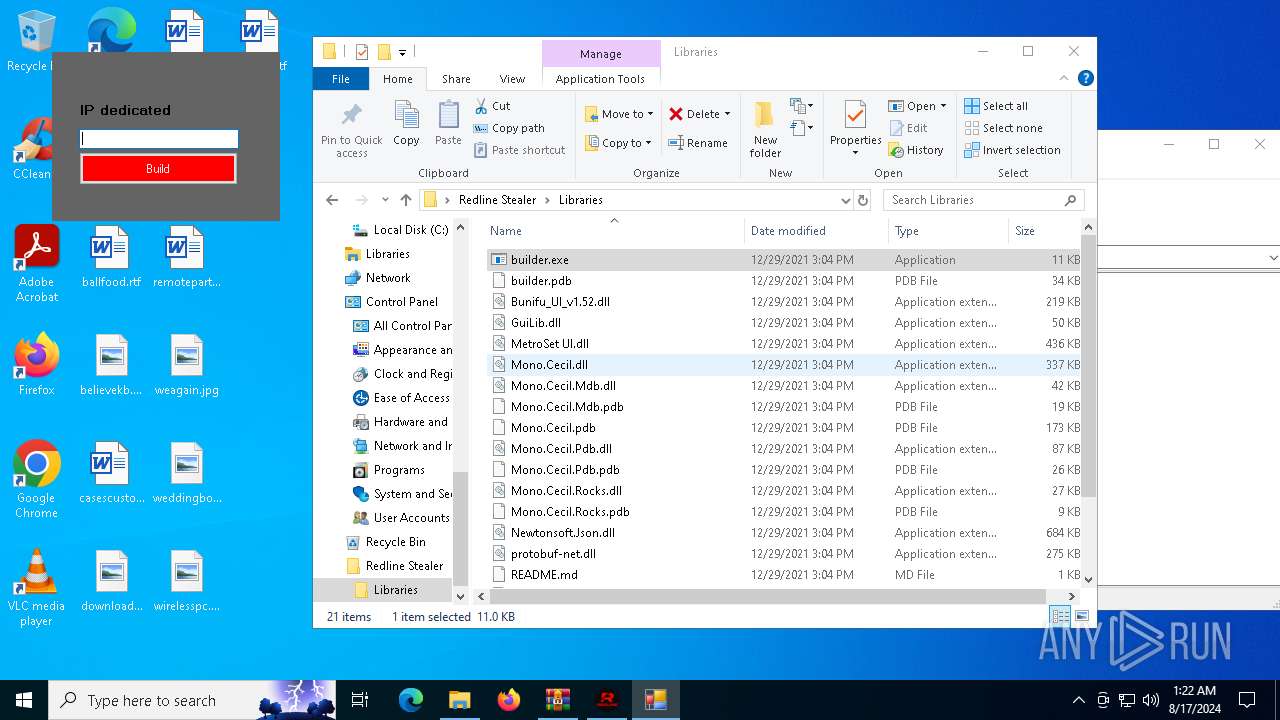
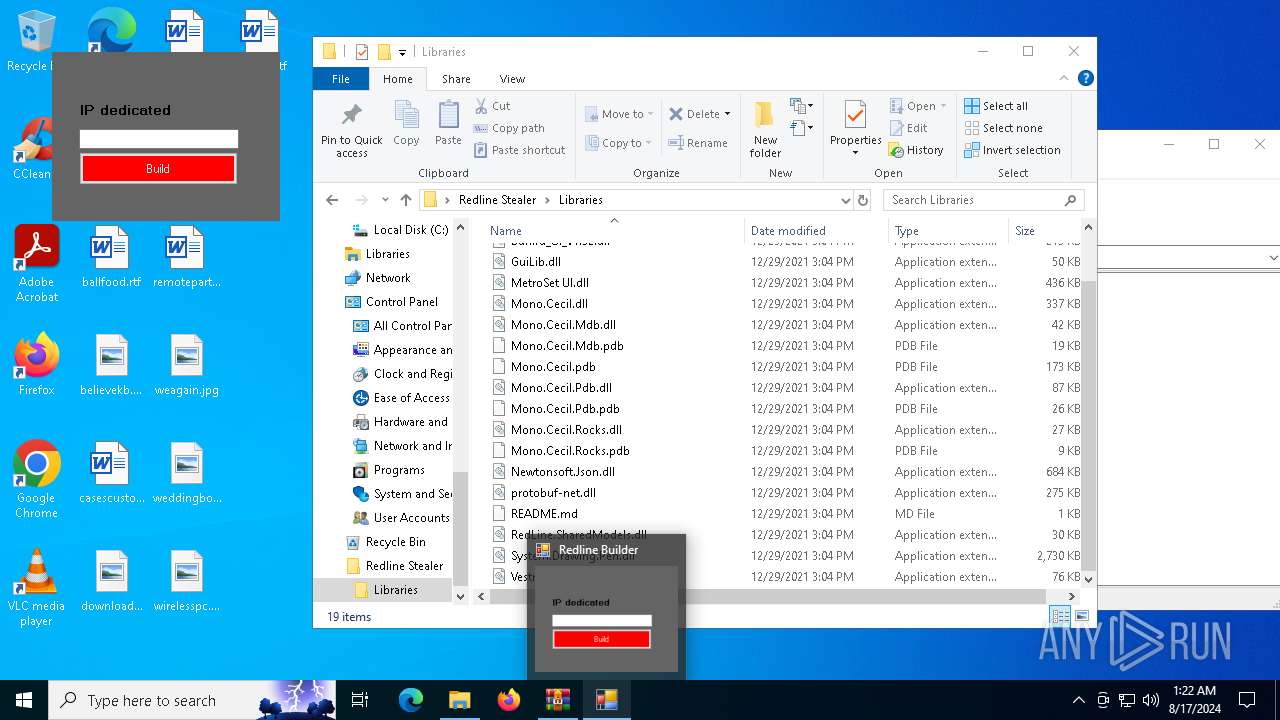
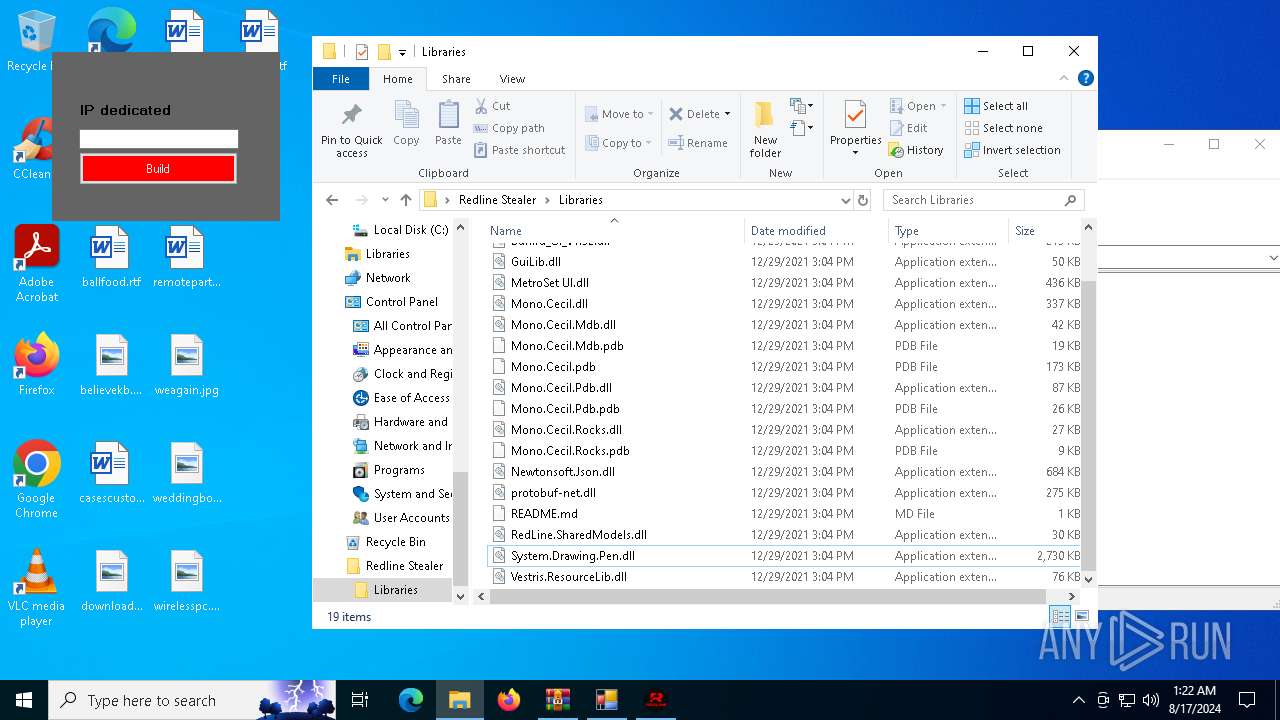
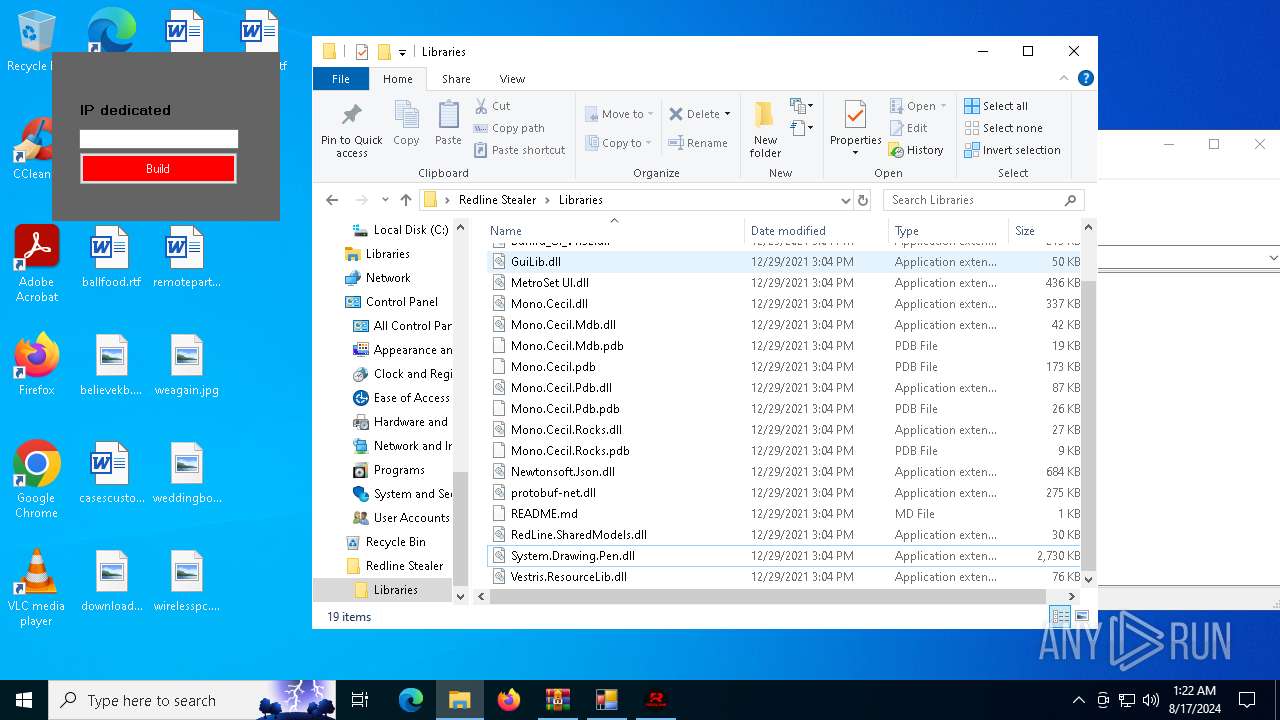
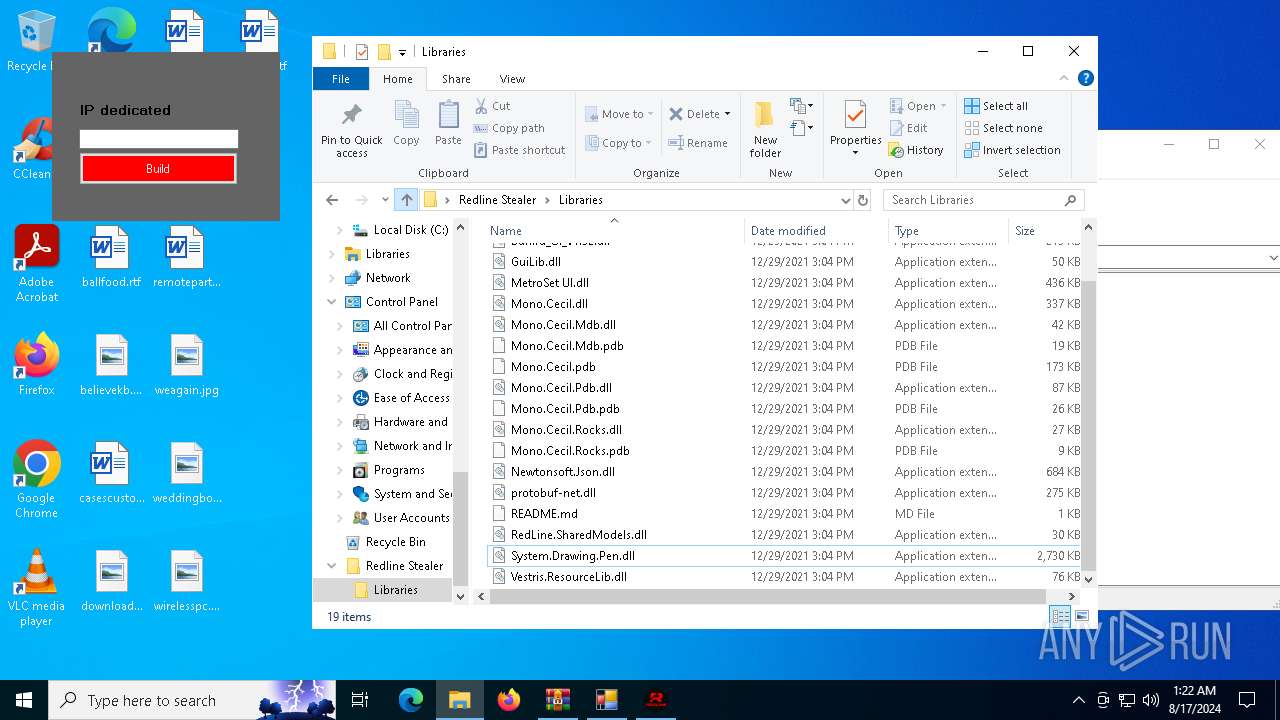
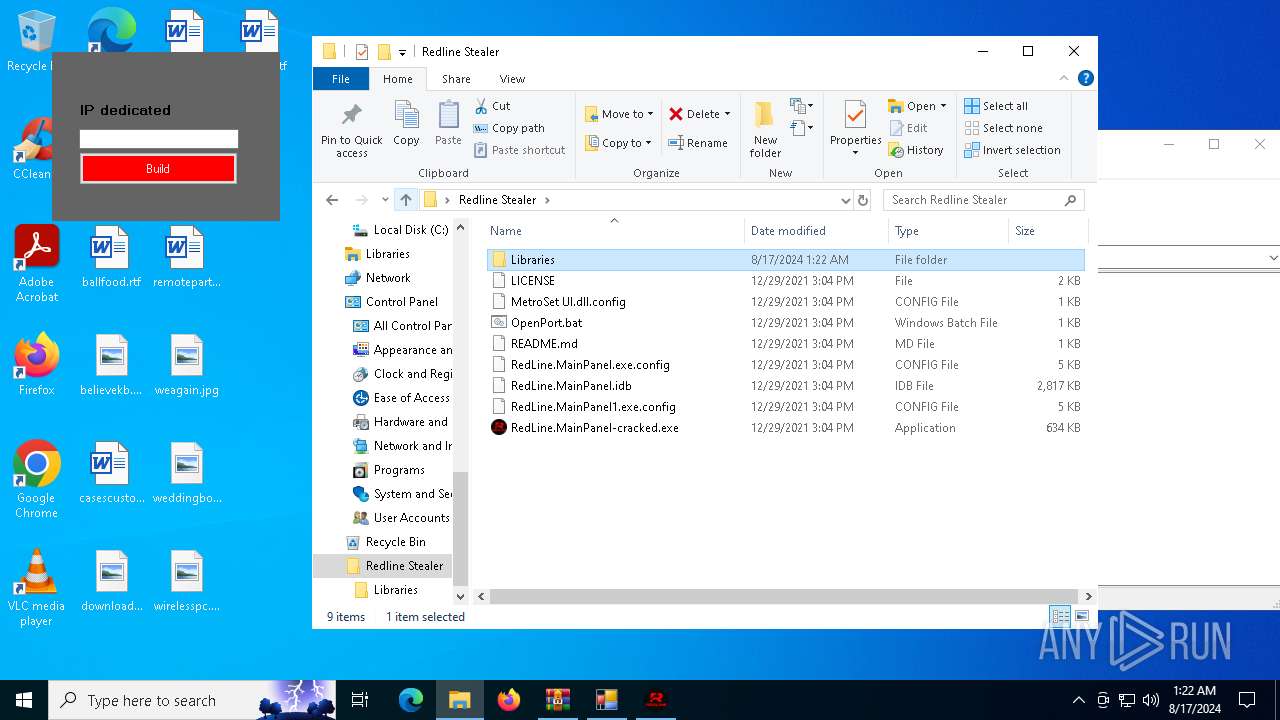
| 872 | "C:\Users\admin\Desktop\Redline Stealer\Libraries\builder.exe" | C:\Users\admin\Desktop\Redline Stealer\Libraries\builder.exe | RedLine.MainPanel-cracked.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1948 | "cmd.exe" /C taskkill /F /PID 5092 && choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\Desktop\Redline Stealer\Libraries\Build.exe" | C:\Windows\SysWOW64\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\Desktop\Redline Stealer\Libraries\builder.exe" | C:\Users\admin\Desktop\Redline Stealer\Libraries\builder.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: builder Version: 1.0.0.0 Modules
| |||||||||||||||
| 2208 | "cmd.exe" /C taskkill /F /PID 3540 && choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\Desktop\Redline Stealer\Libraries\test.exe" | C:\Windows\SysWOW64\cmd.exe | — | test.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | choice /C Y /N /D Y /T 3 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
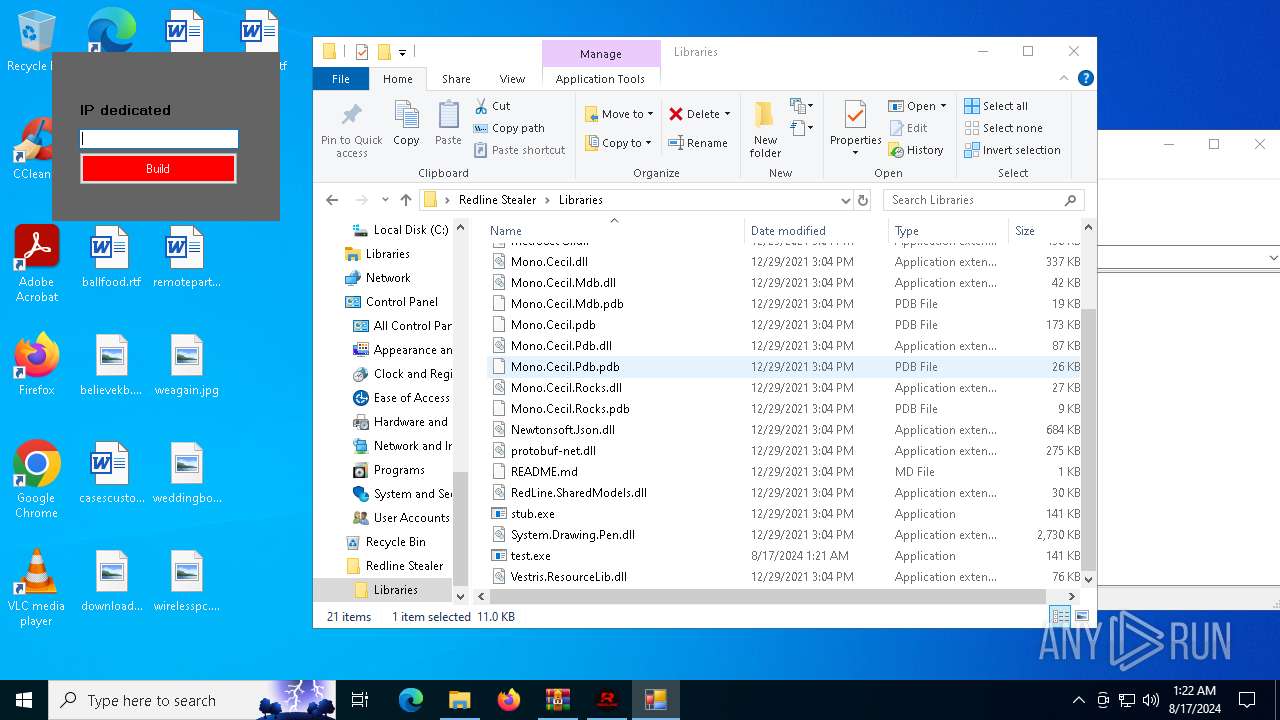
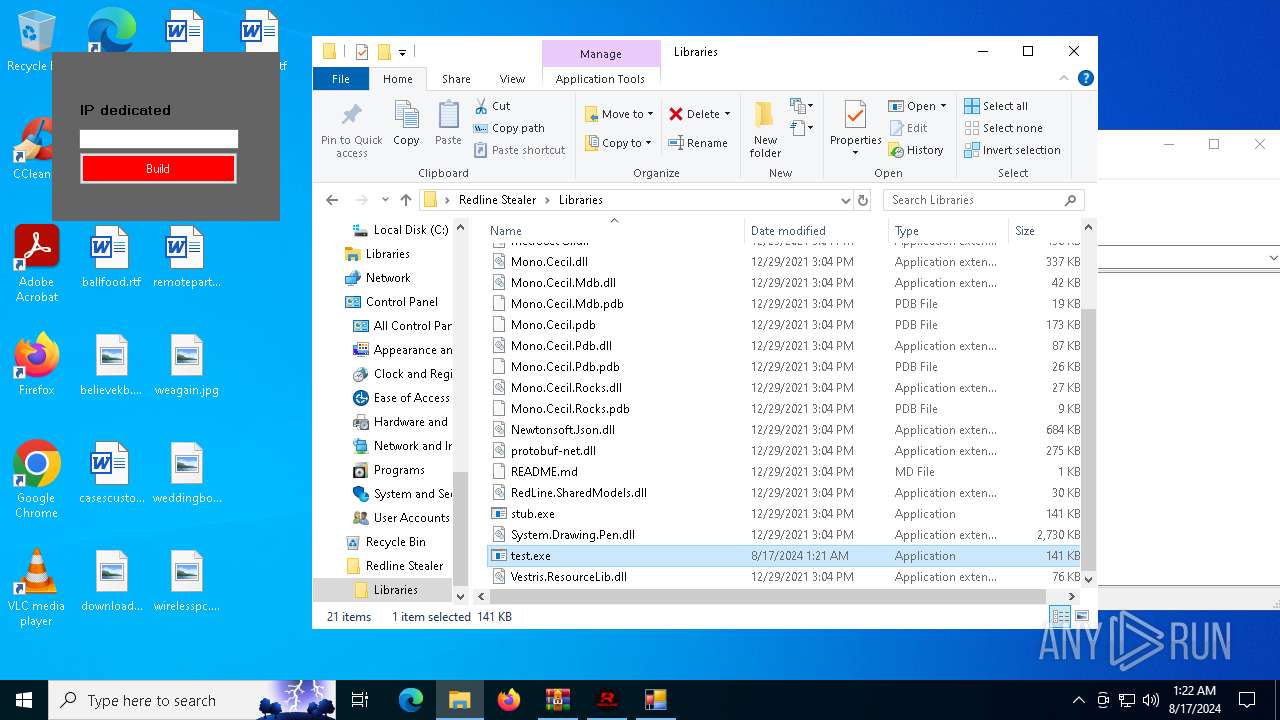
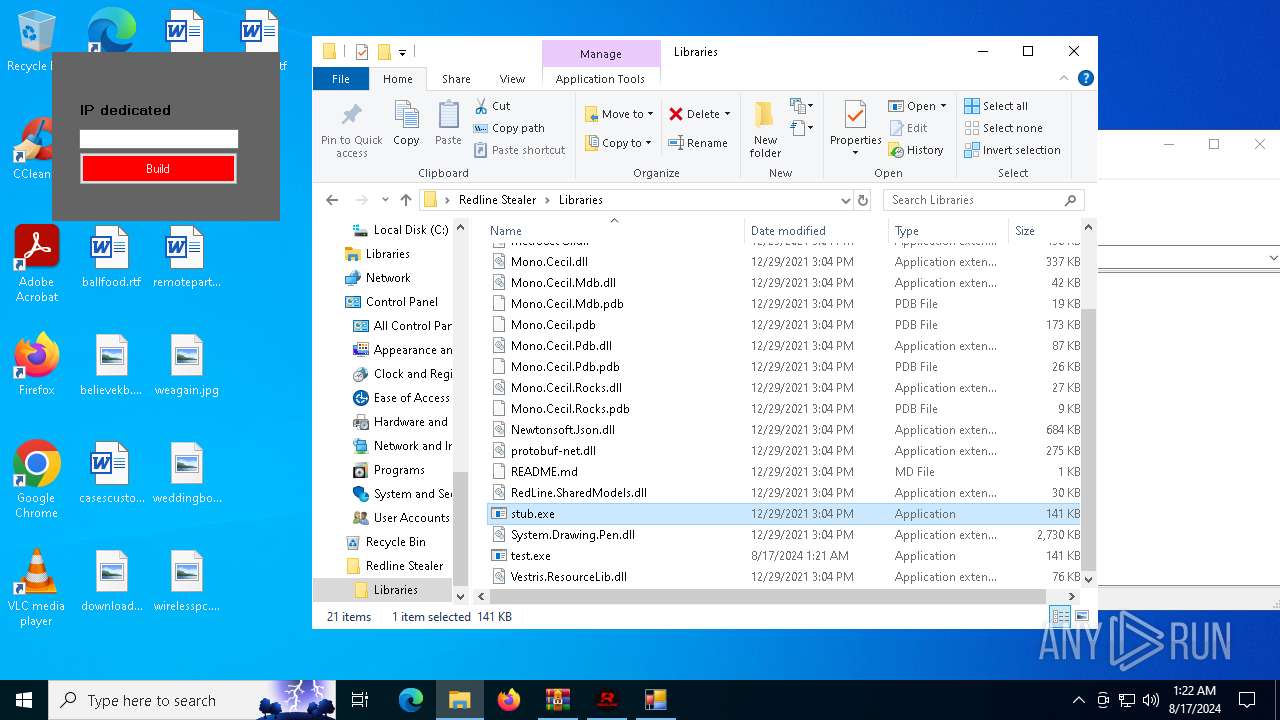
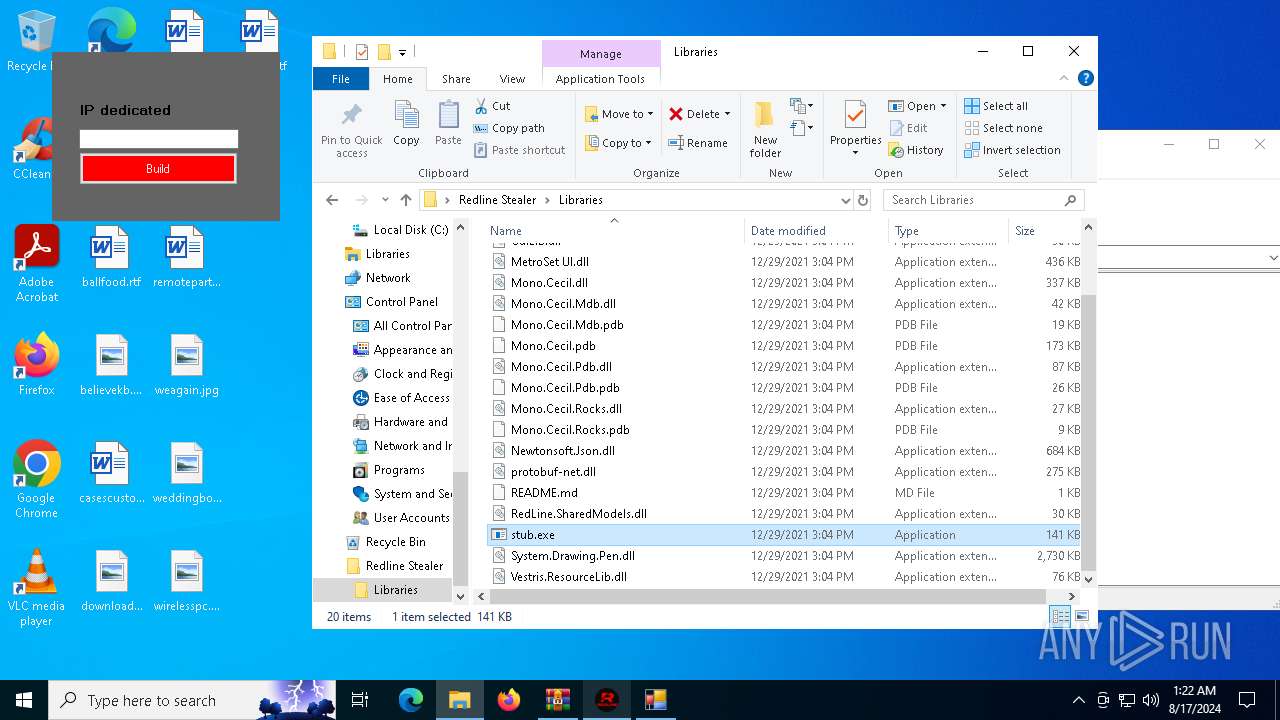
| 3032 | "C:\Users\admin\Desktop\Redline Stealer\Libraries\stub.exe" | C:\Users\admin\Desktop\Redline Stealer\Libraries\stub.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RedLine Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
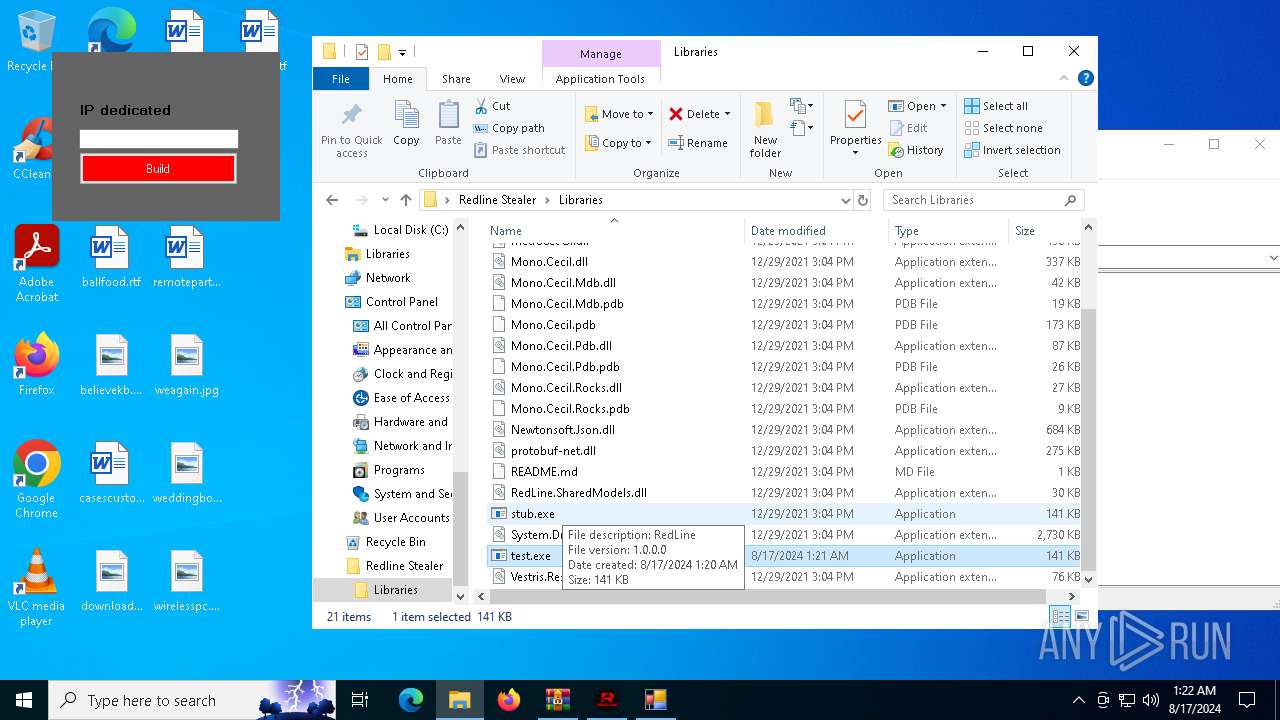
| 3540 | "C:\Users\admin\Desktop\Redline Stealer\Libraries\test.exe" | C:\Users\admin\Desktop\Redline Stealer\Libraries\test.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RedLine Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
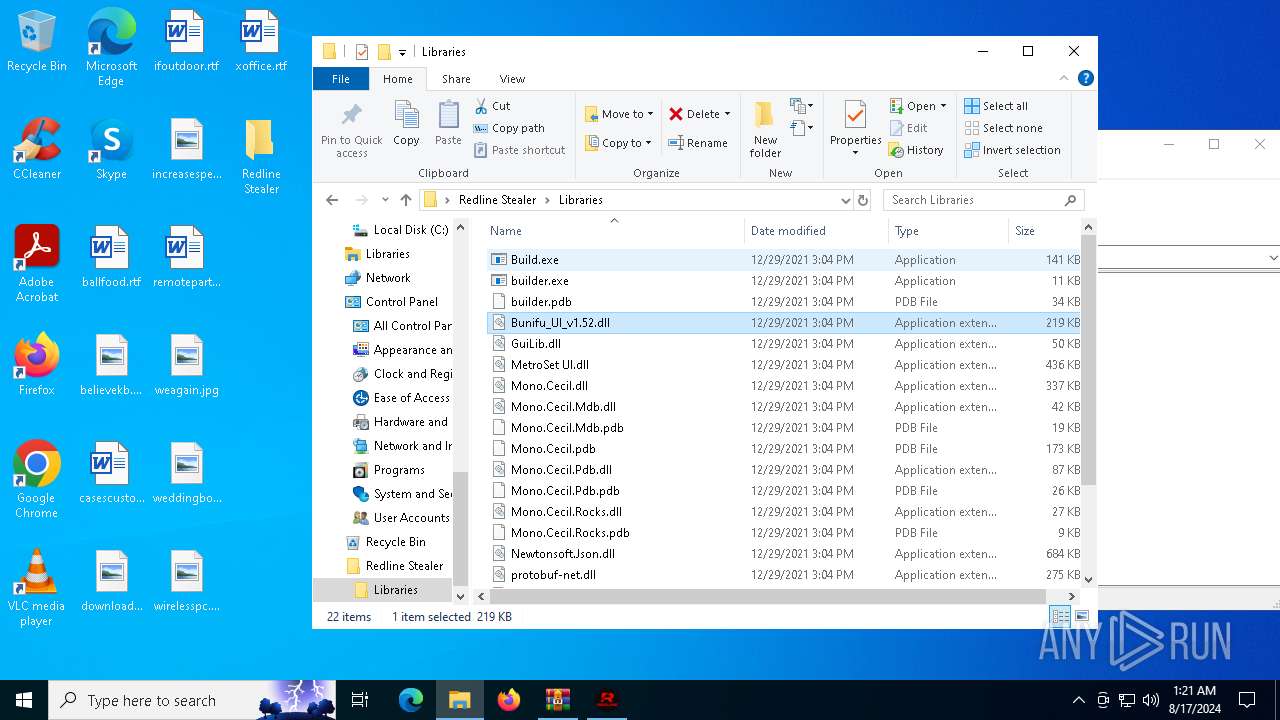
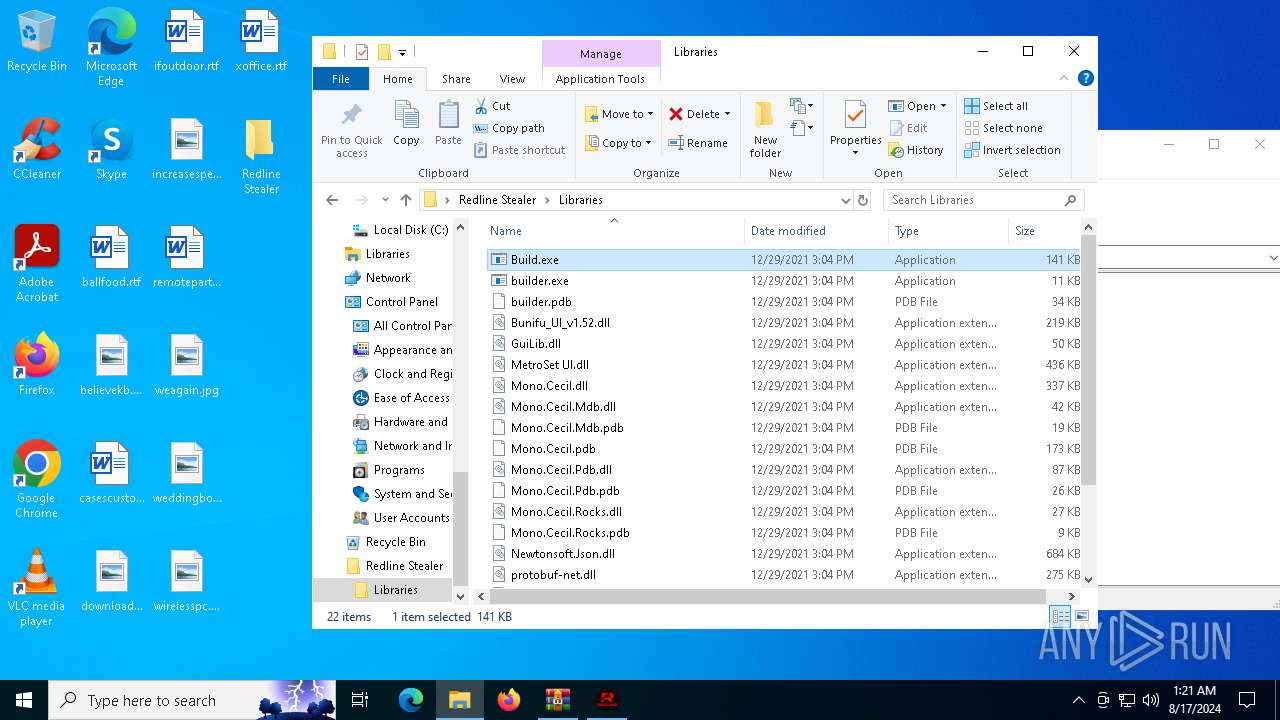
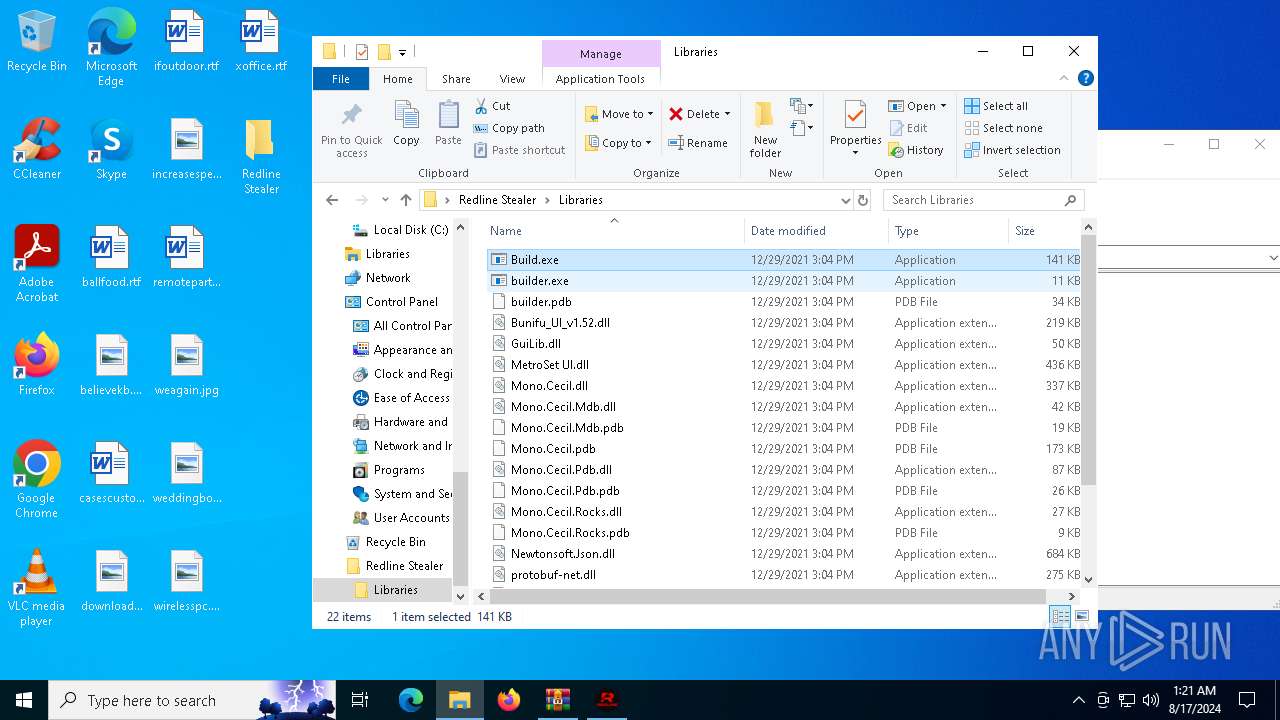
| 5092 | "C:\Users\admin\Desktop\Redline Stealer\Libraries\Build.exe" | C:\Users\admin\Desktop\Redline Stealer\Libraries\Build.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RedLine Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5468 | taskkill /F /PID 5092 | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5632 | choice /C Y /N /D Y /T 3 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 141
Read events
23 996
Write events
138
Delete events
7
Modification events
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Redline Stealer Builder.7z | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6388) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
Executable files
31
Suspicious files
13
Text files
14
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
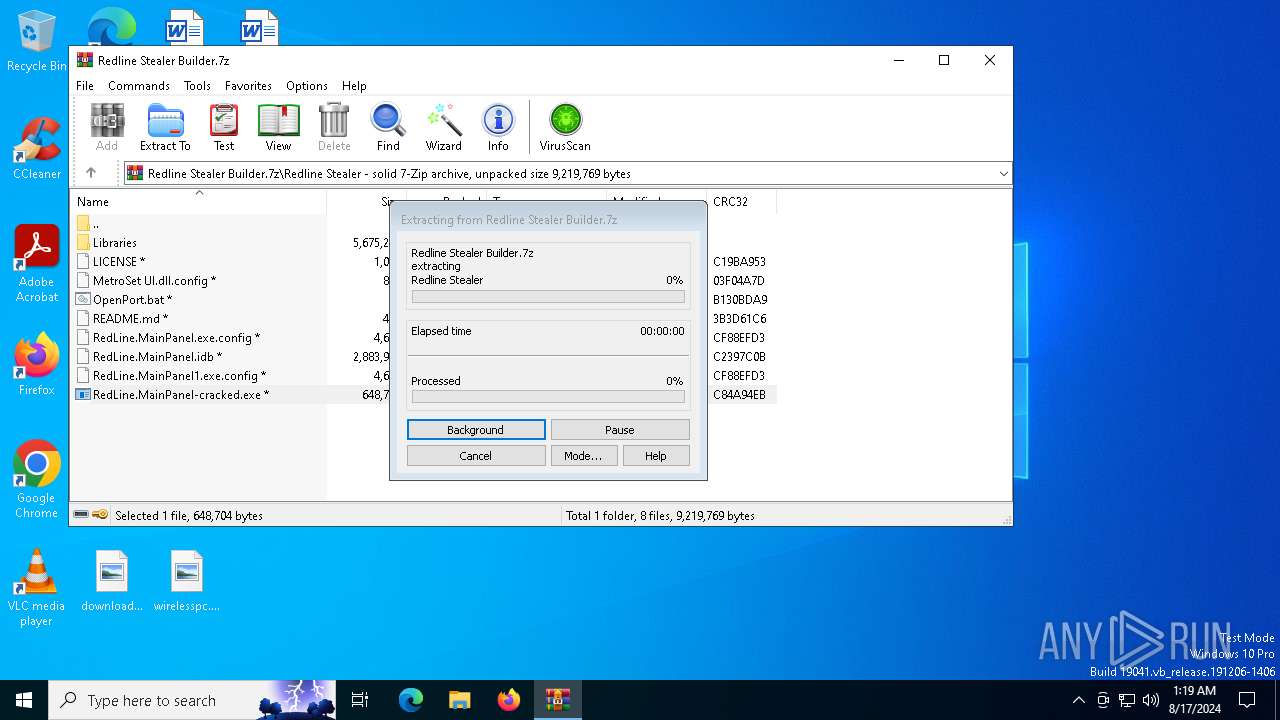
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\Libraries\Mono.Cecil.pdb | binary | |
MD5:C0A69F1B0C50D4F133CD0B278AC2A531 | SHA256:A4F79C99D8923BD6C30EFAFA39363C18BABE95F6609BBAD242BCA44342CCC7BB | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\Libraries\builder.pdb | binary | |
MD5:418DC008EF956465E179EC29D3C3C245 | SHA256:8C7E21B37540211D56C5FDBB7E731655A96945AA83F2988E33D5ADB8AA7C8DF1 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\Libraries\Mono.Cecil.Pdb.pdb | binary | |
MD5:8E07476DB3813903E596B669D3744855 | SHA256:AA6469974D04CBA872F86E6598771663BB8721D43A4A0A2A44CF3E2CD2F1E646 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\MetroSet UI.dll.config | xml | |
MD5:9A25AE6E4FBE956CC33A232AC97D3B16 | SHA256:A407B110C78C0077B651FCBD05CCE073541B61E3E8B4747608069AC5CE686A8C | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\RedLine.MainPanel.exe.config | xml | |
MD5:6EBC9B76090C8C4BF6B65C02503C6CD6 | SHA256:EF9352989527D16CF5BE708B0D8E6D384618746A3999230F477CF50F34FF67C9 | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\Libraries\Mono.Cecil.Rocks.pdb | binary | |
MD5:17E3CCB3A96BE6D93CA3C286CA3B93DC | SHA256:CA54D2395697EFC3163016BBC2BB1E91B13D454B9A5A3EE9A4304012F012E5EB | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\OpenPort.bat | text | |
MD5:CF1CC90281E28CEE22DCE7ED013C2678 | SHA256:84399F8BCCEFA404E156A5351B1DE75A2D5290B4FDDD1754EFB16401ED7218EF | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\README.md | text | |
MD5:E2DB1441B03414CCD5627075A7F567CF | SHA256:41DED26595B824BD680E0B2E895A6B1CA3AE6D0D2260653175DCA35A6A56B54A | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\Libraries\Mono.Cecil.Mdb.pdb | binary | |
MD5:0BA762B6B5FBDA000E51D66722A3BB2C | SHA256:D18EB89421D50F079291B78783408CEE4BAB6810E4C5A4B191849265BDD5BA7C | |||
| 6388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6388.40548\Redline Stealer\Libraries\README.md | text | |
MD5:8CF8463B34CAA8AC871A52D5DD7AD1EF | SHA256:EB4BD64F7014F7D42E9D358035802242741B974E8DFCD37C59F9C21CE29D781E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
48
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4592 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6860 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6908 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | svchost.exe | 52.167.249.196:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3140 | RUXIMICS.exe | 52.167.249.196:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2120 | MoUsoCoreWorker.exe | 52.167.249.196:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4056 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4592 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |