| File name: | ENCRYPTED.ps1 |
| Full analysis: | https://app.any.run/tasks/5a894cac-49d8-4328-89a2-b92f9135c0d9 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 15, 2026, 08:54:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (65400), with CRLF line terminators |
| MD5: | 01B290009BE560F4E0B0E9BDFAE20FCB |
| SHA1: | F17782E2E94795B082A0147197CBC0B0F6DB2665 |
| SHA256: | 4F6F49D76B427ECD1DF55D94A028A143E1F3795C938C0612EC546775395FB130 |
| SSDEEP: | 24576:7YUavdDHHKf4x+nyiFOHb4g4pEmvrZPo5prLwX/bh4z:7Sl7wvO5YPGBLwXiz |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7480)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 7480)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 7480)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 7480)
Changes powershell execution policy (Bypass)
- explorer.exe (PID: 4972)
FORMBOOK has been detected
- systray.exe (PID: 7940)
- explorer.exe (PID: 4972)
- cmstp.exe (PID: 752)
- mstsc.exe (PID: 4968)
- rundll32.exe (PID: 7204)
- NETSTAT.EXE (PID: 8060)
- netsh.exe (PID: 6156)
- control.exe (PID: 6664)
- cscript.exe (PID: 5172)
- raserver.exe (PID: 508)
- WWAHost.exe (PID: 7348)
- cmmon32.exe (PID: 7884)
- wlanext.exe (PID: 7984)
- rundll32.exe (PID: 4144)
- control.exe (PID: 6600)
- colorcpl.exe (PID: 5680)
- svchost.exe (PID: 7920)
- systray.exe (PID: 8092)
- msiexec.exe (PID: 2856)
- ipconfig.exe (PID: 2672)
- help.exe (PID: 7420)
- msiexec.exe (PID: 8124)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7480)
FORMBOOK has been detected (SURICATA)
- explorer.exe (PID: 4972)
FORMBOOK has been detected (YARA)
- systray.exe (PID: 7940)
Connects to the CnC server
- explorer.exe (PID: 4972)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 4972)
The process executes Powershell scripts
- explorer.exe (PID: 4972)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7480)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7480)
Starts CMD.EXE for commands execution
- systray.exe (PID: 7940)
Suspicious use of NETSH.EXE
- explorer.exe (PID: 4972)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 4972)
Process uses IPCONFIG to get network configuration information
- explorer.exe (PID: 4972)
INFO
Gets data length (POWERSHELL)
- powershell.exe (PID: 7480)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4972)
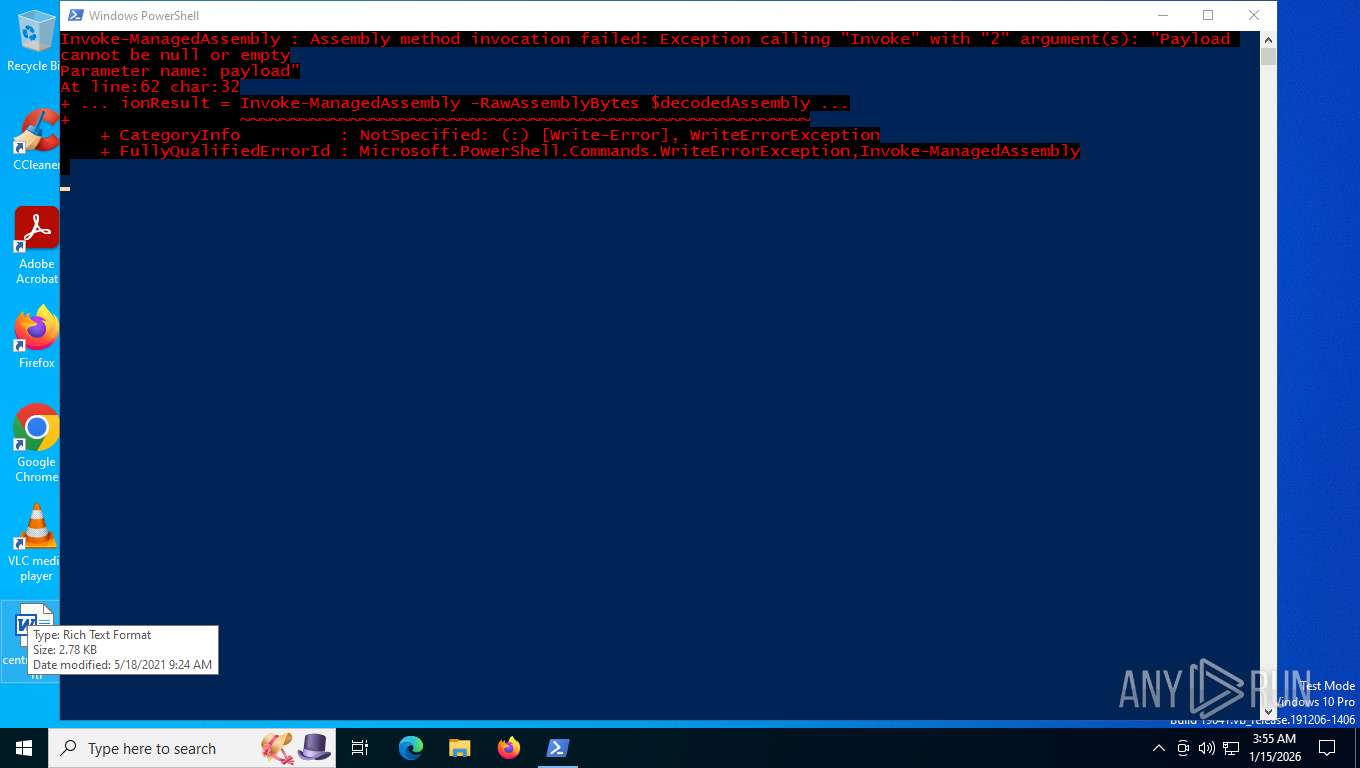
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7480)
Reads the computer name
- aspnet_compiler.exe (PID: 7904)
- aspnet_compiler.exe (PID: 8036)
- aspnet_compiler.exe (PID: 2416)
- aspnet_compiler.exe (PID: 5044)
- aspnet_compiler.exe (PID: 7296)
- aspnet_compiler.exe (PID: 7360)
- aspnet_compiler.exe (PID: 792)
- aspnet_compiler.exe (PID: 7504)
- aspnet_compiler.exe (PID: 7660)
- aspnet_compiler.exe (PID: 7344)
- aspnet_compiler.exe (PID: 7868)
- aspnet_compiler.exe (PID: 1368)
- aspnet_compiler.exe (PID: 7072)
- aspnet_compiler.exe (PID: 7600)
- aspnet_compiler.exe (PID: 8080)
- aspnet_compiler.exe (PID: 8152)
- aspnet_compiler.exe (PID: 7704)
- aspnet_compiler.exe (PID: 1772)
- aspnet_compiler.exe (PID: 8108)
- aspnet_compiler.exe (PID: 7404)
- aspnet_compiler.exe (PID: 4300)
- aspnet_compiler.exe (PID: 2900)
Checks supported languages
- aspnet_compiler.exe (PID: 7904)
- aspnet_compiler.exe (PID: 8036)
- aspnet_compiler.exe (PID: 2416)
- aspnet_compiler.exe (PID: 5044)
- aspnet_compiler.exe (PID: 7296)
- aspnet_compiler.exe (PID: 7360)
- aspnet_compiler.exe (PID: 7504)
- aspnet_compiler.exe (PID: 7660)
- aspnet_compiler.exe (PID: 792)
- aspnet_compiler.exe (PID: 7704)
- aspnet_compiler.exe (PID: 7344)
- aspnet_compiler.exe (PID: 7868)
- aspnet_compiler.exe (PID: 7072)
- aspnet_compiler.exe (PID: 1368)
- aspnet_compiler.exe (PID: 7600)
- aspnet_compiler.exe (PID: 8080)
- aspnet_compiler.exe (PID: 8152)
- aspnet_compiler.exe (PID: 7404)
- aspnet_compiler.exe (PID: 8108)
- aspnet_compiler.exe (PID: 4300)
- aspnet_compiler.exe (PID: 1772)
- aspnet_compiler.exe (PID: 2900)
Manual execution by a user
- systray.exe (PID: 7940)
- NETSTAT.EXE (PID: 8060)
- mstsc.exe (PID: 4968)
- cmstp.exe (PID: 752)
- rundll32.exe (PID: 7204)
- WWAHost.exe (PID: 7348)
Checks proxy server information
- slui.exe (PID: 7612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(7940) systray.exe
C2 (1)www.convertfusionpro.cloud/n43s/
Decoy C2 (64)iranconsole.shop
hj223.top
k207ix.top
klima-celje.com
nuartstore.in
nana288.biz
harivo.live
ttd.mobi
henrydog.xyz
ve88ss.com
conferencejwtbts.sbs
grokv3.pro
b5b28e.top
31dpc.top
78452780.xyz
senthread.com
jingzhouhemingyang.com
eco-houses.xyz
twocai.com
noobycloud.xyz
nsujjv.top
nspwealthofficesolutions.info
ptzdv.irish
55006666.cn
remont-priborov.online
atorinovintage.com
zahid-official.xyz
yaksa.tech
primecyber.ru
epicrider590.info
outpost.bio
streams2sea.net
exqup.shop
ku204.xyz
hernandezrudy.net
databnt.xyz
aircrawler.xyz
ax9l8r.top
vsi5hu.top
bizeco.xyz
minicooper.uk
grinthold.shop
shopperclickzone800.info
boucrflow.com
car-insurance-companies.cfd
vpncharts.xyz
anzhou.tech
luxecomfortoasis.shop
1123576.xyz
bqzl36.vip
201-ikutangabung.shop
attorney-us-en-7347626.zone
ag111.shop
denisbutorin.xyz
makearkansashomes.com
chiropractors-directory.xyz
skin-rejuvenation-67180.bond
llmrating.online
mymoviz372.xyz
bj217o.top
lorazepam-f2-33.xyz
inthe.business
33f.live
alwayssavl.sbs
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Total processes
195
Monitored processes
53
Malicious processes
23
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Windows\SysWOW64\raserver.exe" | C:\Windows\SysWOW64\raserver.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Remote Assistance COM Server Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | "C:\Windows\SysWOW64\cmstp.exe" | C:\Windows\SysWOW64\cmstp.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 0 Version: 7.2.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 792 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1368 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1772 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2364 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2416 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2672 | "C:\Windows\SysWOW64\ipconfig.exe" | C:\Windows\SysWOW64\ipconfig.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2856 | "C:\Windows\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2900 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Aspnet_compiler.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_compiler.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_compiler.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
9 125
Read events
9 123
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000170022 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456E9BC50E45F05DB4C86F7D791C25A96C7 | |||
| (PID) Process: | (4972) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\JumplistData |
| Operation: | write | Name: | {1AC14E77-02E7-4E5D-B744-2EB1AE5198B7}\WindowsPowerShell\v1.0\powershell.exe |
Value: F8F333A2FC85DC01 | |||
Executable files
0
Suspicious files
4
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4972 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | text | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 7480 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:B01D4BC09B6EF2732439AE5BE07F411B | SHA256:D9F4E3E4D4F5E910D1518E22B3275FB741C495C5C5DC9867D68B51E07296DEAD | |||
| 7480 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7FUGVTAKCNZR29JYMGUB.temp | binary | |
MD5:75A8053E2509EA087608678773473B0F | SHA256:5F1E985F34D9DB93060CADA09034101E6108F1ED32820D8611526BF33205E491 | |||
| 7480 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFfe035.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 7480 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1w5d4qii.eae.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7480 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_s0i40dqp.k1q.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7480 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:75A8053E2509EA087608678773473B0F | SHA256:5F1E985F34D9DB93060CADA09034101E6108F1ED32820D8611526BF33205E491 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
32
DNS requests
21
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
2228 | SIHClient.exe | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
2228 | SIHClient.exe | GET | 200 | 135.233.95.144:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
2228 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
6300 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6300 | svchost.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.58 Kb | whitelisted |
6300 | svchost.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3440 | svchost.exe | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
6300 | svchost.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 1.43 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6300 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6300 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6300 | svchost.exe | 2.16.241.14:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6300 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4972 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
4972 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
4972 | explorer.exe | Potentially Bad Traffic | ET HUNTING Request to .XYZ Domain with Minimal Headers |
4972 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
4972 | explorer.exe | Malware Command and Control Activity Detected | ET MALWARE FormBook CnC Checkin (GET) |
Process | Message |
|---|---|
powershell.exe | Attempt 2 failed: Failed to allocate memory in target process
|
powershell.exe | Attempt 1 failed: Failed to allocate memory in target process
|
powershell.exe | Attempt 1 failed: Failed to allocate memory in target process
|