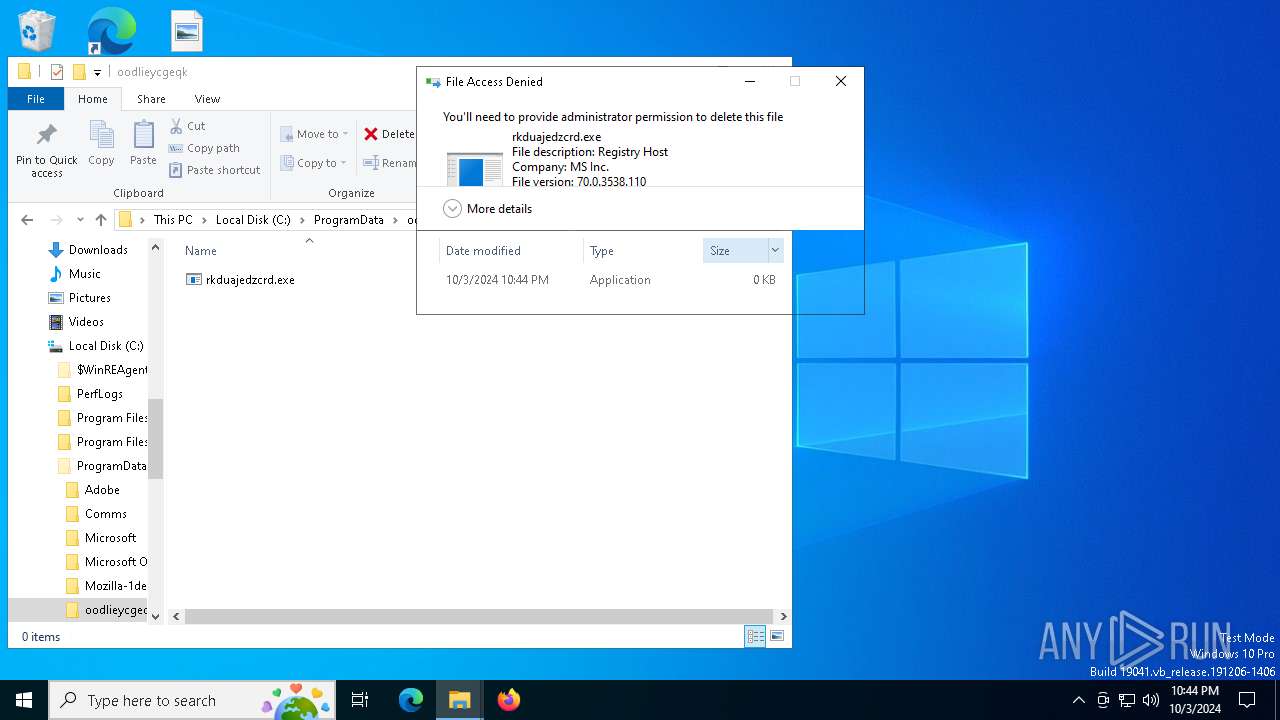
| File name: | rkduajedzcrd.exe |
| Full analysis: | https://app.any.run/tasks/e0cd1a1f-556b-4173-a45f-0add1514a47b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | October 03, 2024, 22:43:46 |
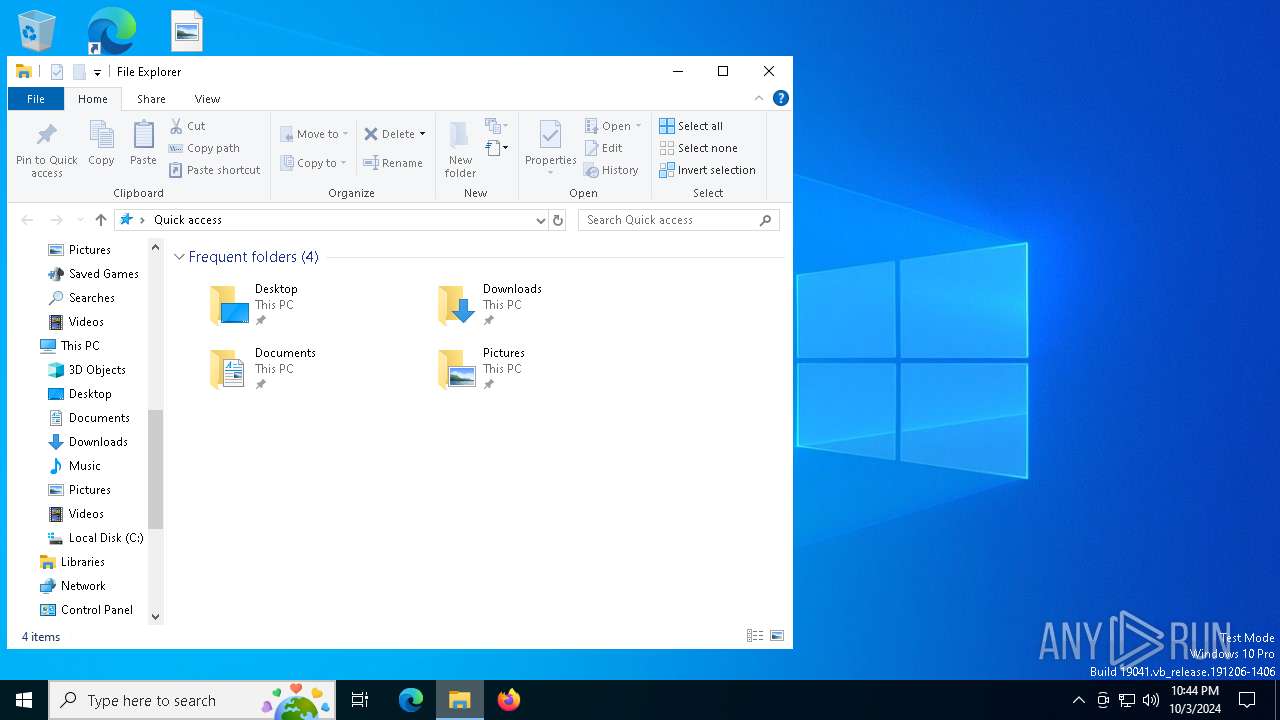
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 0838E4E90814A48E6122F4B0A2B2FC5F |
| SHA1: | 4872080D4398365A93B577B127380F8600A2ECEE |
| SHA256: | 4F63CD101E4BDAACFFD9169610B7BB9430DE6BF87B9016125A3D76368F3E1FA7 |
| SSDEEP: | 98304:YrSpzFH7gGBN9CsoC18nY97TGAQ0U06pDcROsKoE5jVMo9xRCJiWug/T:lpZwsqyVQBQKoENtxREM |
MALICIOUS
Adds extension to the Windows Defender exclusion list
- rkduajedzcrd.exe (PID: 4044)
- rkduajedzcrd.exe (PID: 6632)
- conhost.exe (PID: 7136)
- rkduajedzcrd.exe (PID: 7016)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2256)
- explorer.exe (PID: 3296)
Connects to the CnC server
- explorer.exe (PID: 3296)
SILENTCRYPTOMINER has been detected (SURICATA)
- explorer.exe (PID: 3296)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 3296)
SUSPICIOUS
Powershell scripting: start process
- rkduajedzcrd.exe (PID: 3476)
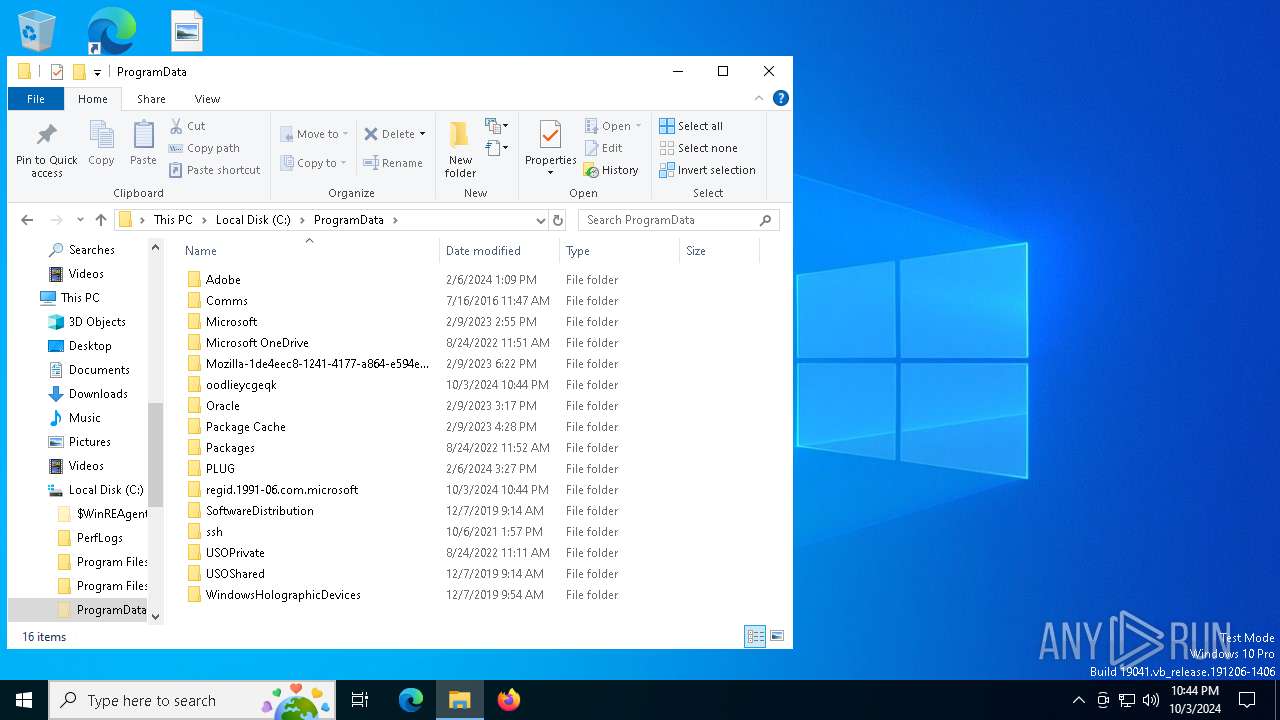
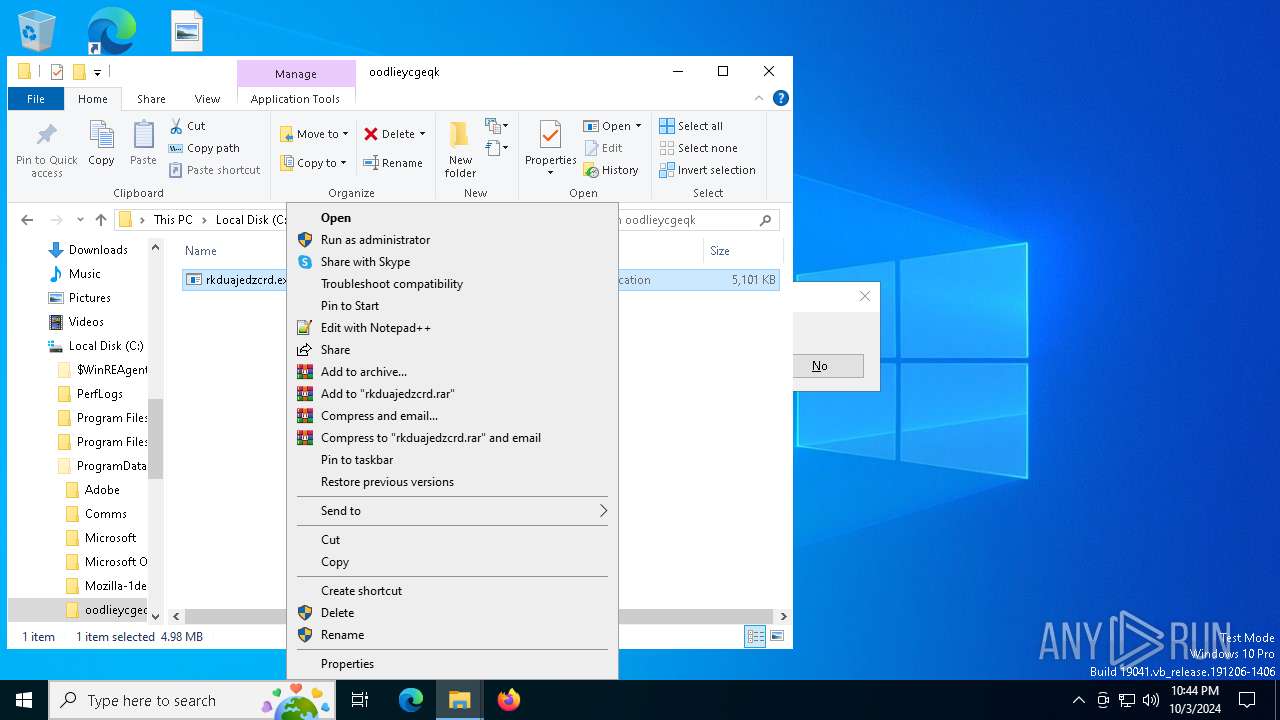
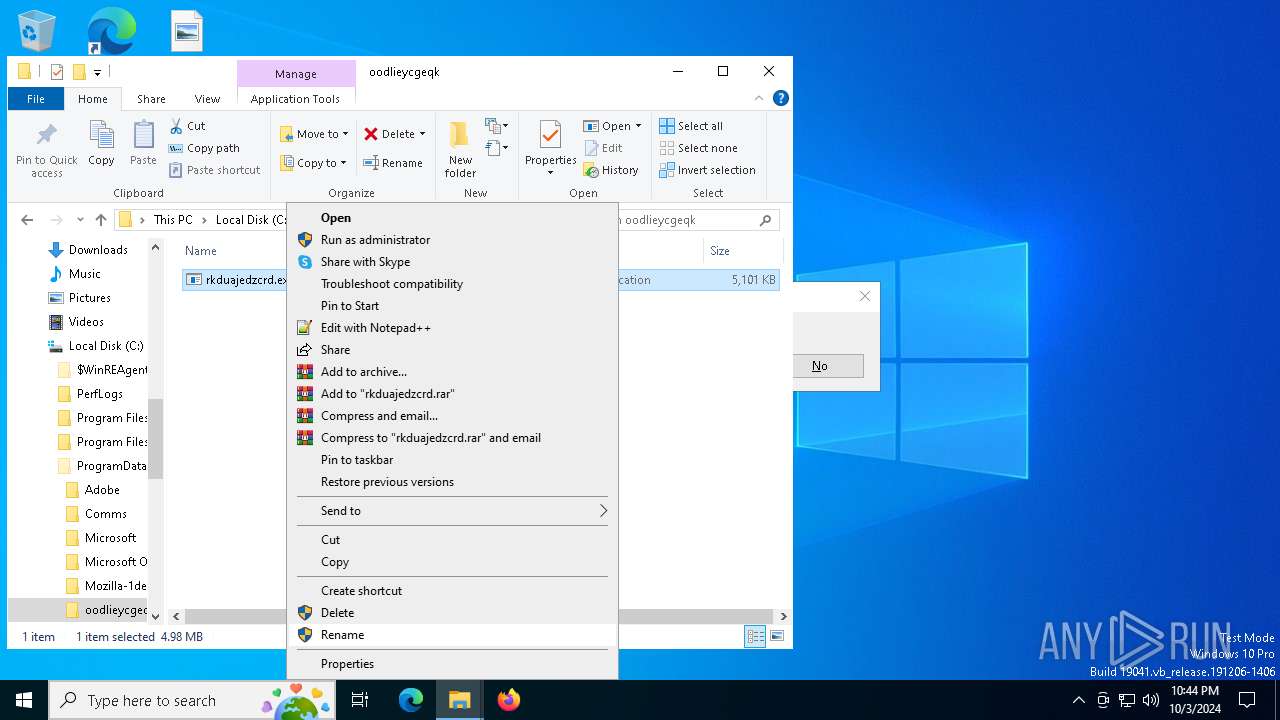
Script adds exclusion path to Windows Defender
- rkduajedzcrd.exe (PID: 4044)
- rkduajedzcrd.exe (PID: 6632)
- conhost.exe (PID: 7136)
- rkduajedzcrd.exe (PID: 7016)
Starts POWERSHELL.EXE for commands execution
- rkduajedzcrd.exe (PID: 3476)
- rkduajedzcrd.exe (PID: 4044)
- rkduajedzcrd.exe (PID: 6632)
- conhost.exe (PID: 7136)
- rkduajedzcrd.exe (PID: 7016)
Script adds exclusion extension to Windows Defender
- rkduajedzcrd.exe (PID: 4044)
- rkduajedzcrd.exe (PID: 6632)
- conhost.exe (PID: 7136)
- rkduajedzcrd.exe (PID: 7016)
Process uninstalls Windows update
- wusa.exe (PID: 2088)
- wusa.exe (PID: 2536)
- wusa.exe (PID: 6760)
Executable content was dropped or overwritten
- rkduajedzcrd.exe (PID: 4044)
- rkduajedzcrd.exe (PID: 6632)
- dllhost.exe (PID: 2036)
- conhost.exe (PID: 7136)
Starts CMD.EXE for commands execution
- rkduajedzcrd.exe (PID: 4044)
- rkduajedzcrd.exe (PID: 6632)
- rkduajedzcrd.exe (PID: 7016)
Executes as Windows Service
- rkduajedzcrd.exe (PID: 6632)
Starts SC.EXE for service management
- rkduajedzcrd.exe (PID: 4044)
Drops a system driver (possible attempt to evade defenses)
- rkduajedzcrd.exe (PID: 6632)
Connects to unusual port
- explorer.exe (PID: 3296)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2256)
- explorer.exe (PID: 3296)
The process connected to a server suspected of theft
- explorer.exe (PID: 3296)
Crypto Currency Mining Activity Detected
- explorer.exe (PID: 3296)
INFO
The process uses the downloaded file
- powershell.exe (PID: 5524)
Checks supported languages
- rkduajedzcrd.exe (PID: 3476)
The executable file from the user directory is run by the Powershell process
- rkduajedzcrd.exe (PID: 4044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:07:29 19:25:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 32768 |
| InitializedDataSize: | 5189632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1140 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 70.0.3538.110 |
| ProductVersionNumber: | 70.0.3538.110 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | MS Inc. |
| FileTitle: | registry.exe |
| FileDescription: | Registry Host |
| FileVersion: | 70,0,3538,110 |
| LegalCopyright: | Copyright 2025 MS Inc. All rights reserved. |
| LegalTrademark: | - |
| ProductName: | Registry Host |
| ProductVersion: | 70,0,3538,110 |
Total processes
164
Monitored processes
35
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2036 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2536 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2820 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramData) -ExclusionExtension '.exe' -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | rkduajedzcrd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3296 | explorer.exe | C:\Windows\explorer.exe | rkduajedzcrd.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
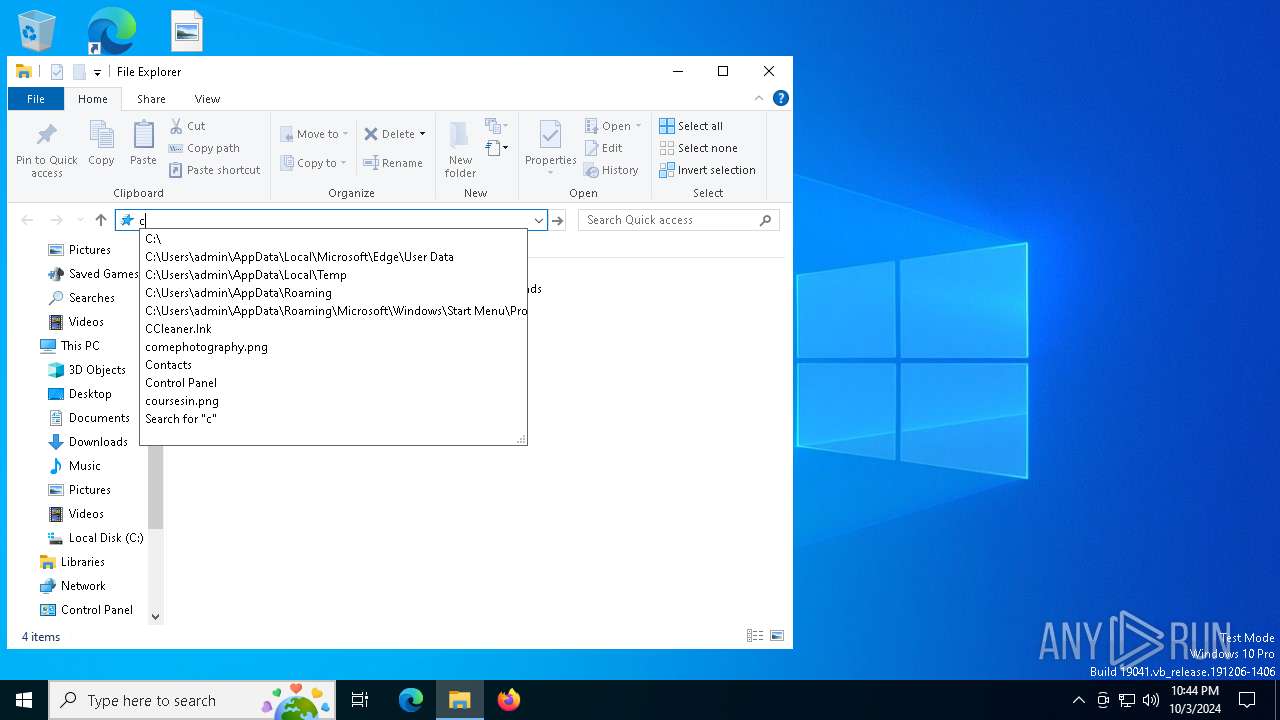
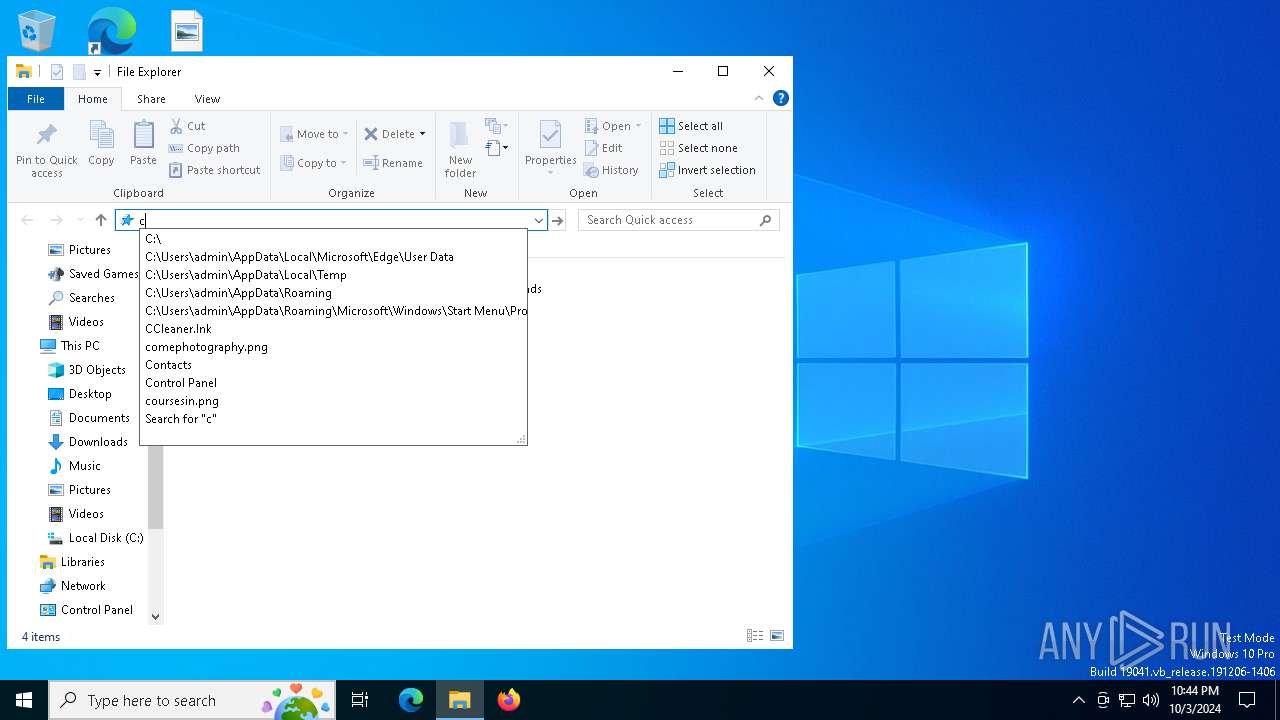
| 3476 | "C:\Users\admin\AppData\Local\Temp\rkduajedzcrd.exe" | C:\Users\admin\AppData\Local\Temp\rkduajedzcrd.exe | — | explorer.exe | |||||||||||
User: admin Company: MS Inc. Integrity Level: MEDIUM Description: Registry Host Exit code: 0 Version: 70,0,3538,110 Modules
| |||||||||||||||
Total events
26 271
Read events
26 267
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4044) rkduajedzcrd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT |
| Operation: | write | Name: | DontOfferThroughWUAU |
Value: 1 | |||
| (PID) Process: | (6632) rkduajedzcrd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT |
| Operation: | write | Name: | DontOfferThroughWUAU |
Value: 1 | |||
| (PID) Process: | (2036) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\BitBucket\Volume\{2f5c5e72-85a9-11eb-90a8-9a9b76358421} |
| Operation: | write | Name: | NeedToPurge |
Value: 1 | |||
| (PID) Process: | (7016) rkduajedzcrd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\MRT |
| Operation: | write | Name: | DontOfferThroughWUAU |
Value: 1 | |||
Executable files
4
Suspicious files
5
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5524 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ebme1qje.eym.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zahbxrqv.rw5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6040 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_fvbvhpxo.cra.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6040 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_iemlrghe.hbe.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6040 | powershell.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C305112C4A8CF62E6B3DB06F480F2E27 | SHA256:618ACB75388BEAD73C005085B03CC51032799FB7C811677CCB1F099854D25F86 | |||
| 2820 | powershell.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B77CD362F428766974C3914D1FA45A43 | SHA256:90C8F1985F3690AAAB4B006FEBB997DDA1A8BA0863FAA8400BB53D4B3E929FEA | |||
| 6632 | rkduajedzcrd.exe | C:\Windows\Temp\pkgiductxtxq.sys | executable | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 2036 | dllhost.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\$RMEJ8ZX.exe | executable | |
MD5:0838E4E90814A48E6122F4B0A2B2FC5F | SHA256:4F63CD101E4BDAACFFD9169610B7BB9430DE6BF87B9016125A3D76368F3E1FA7 | |||
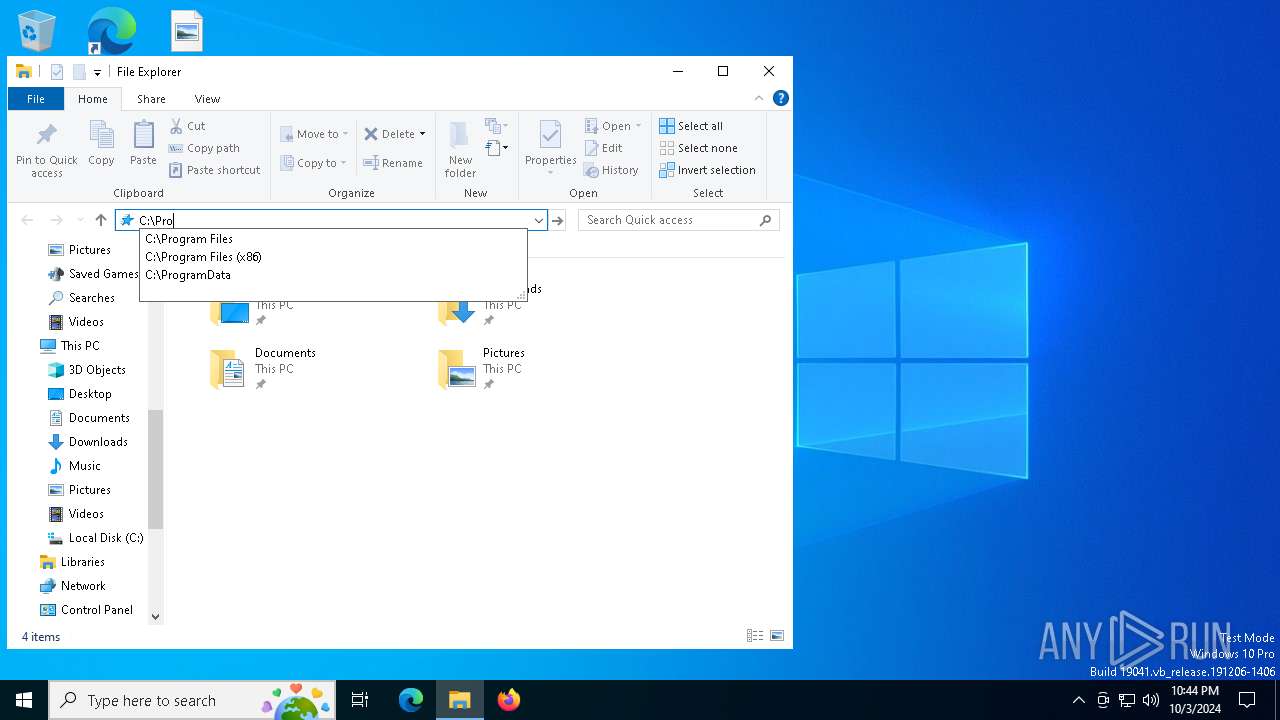
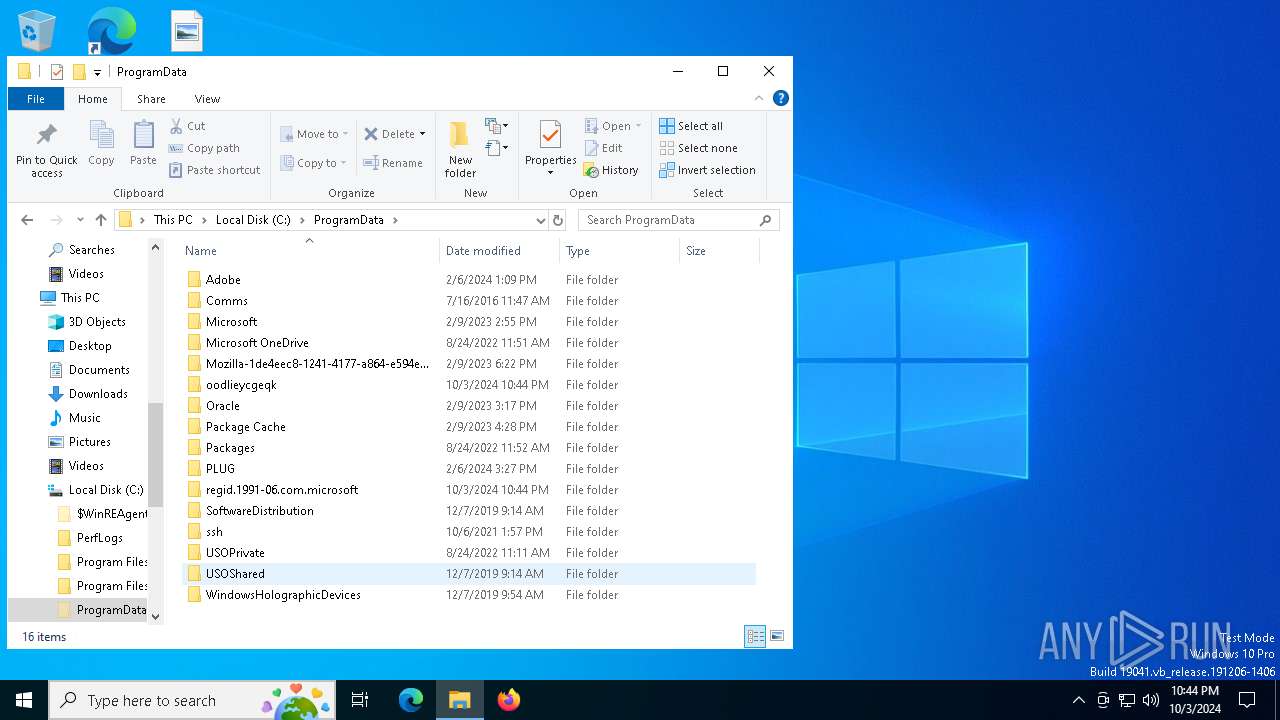
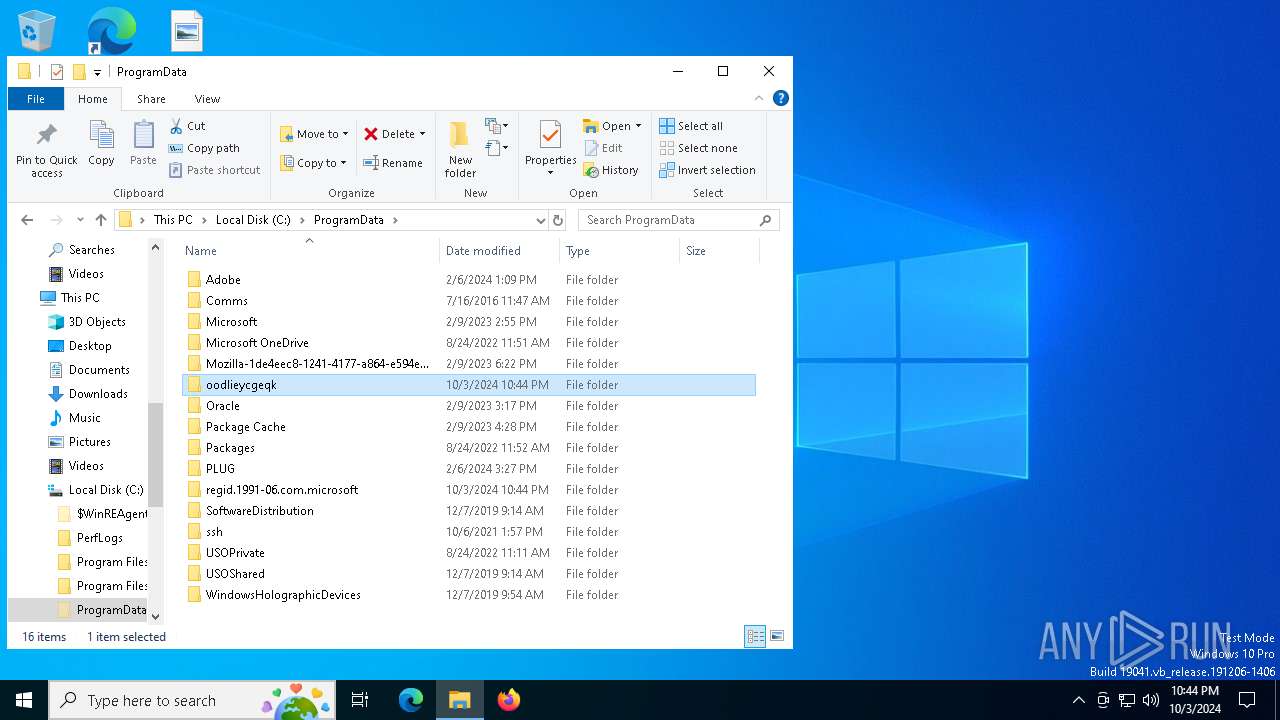
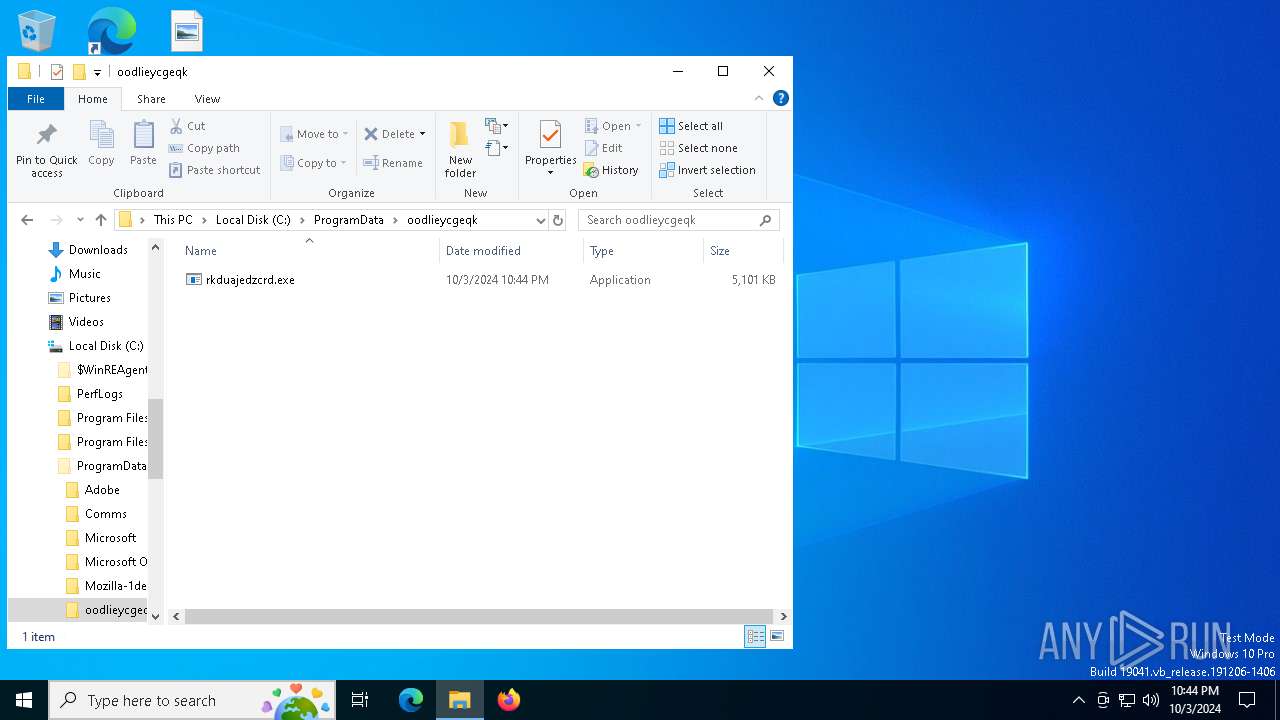
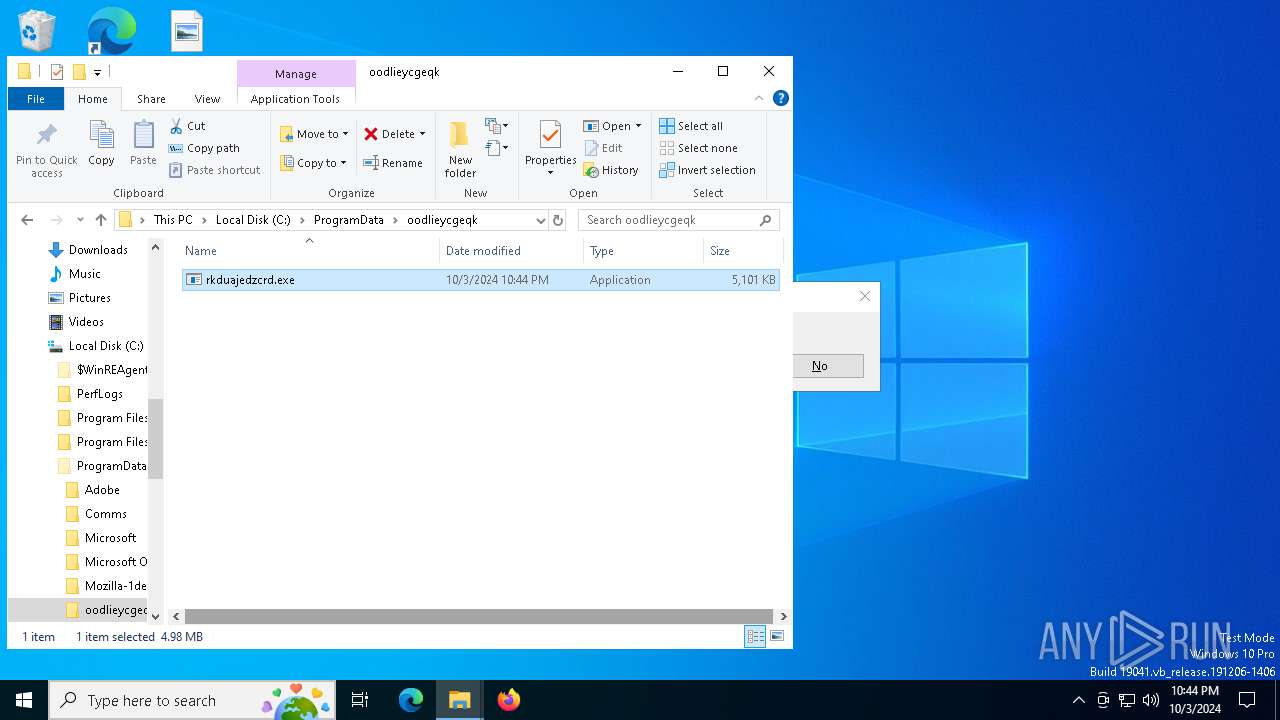
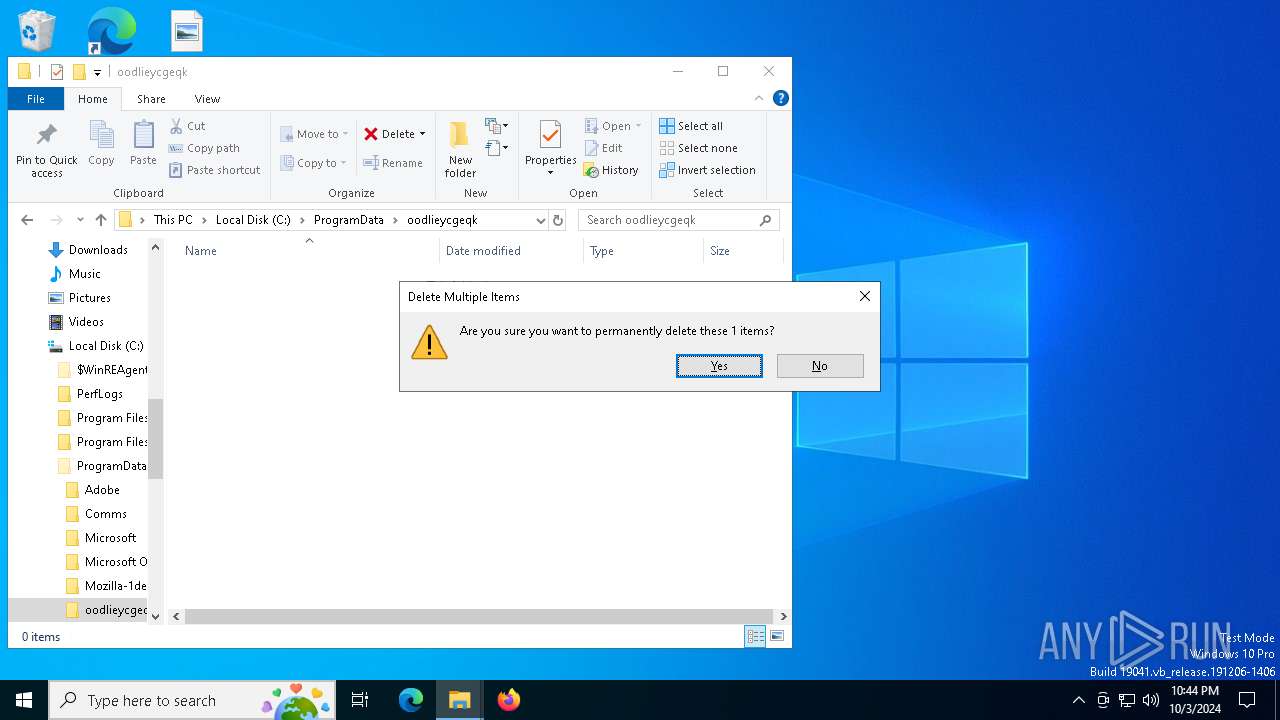
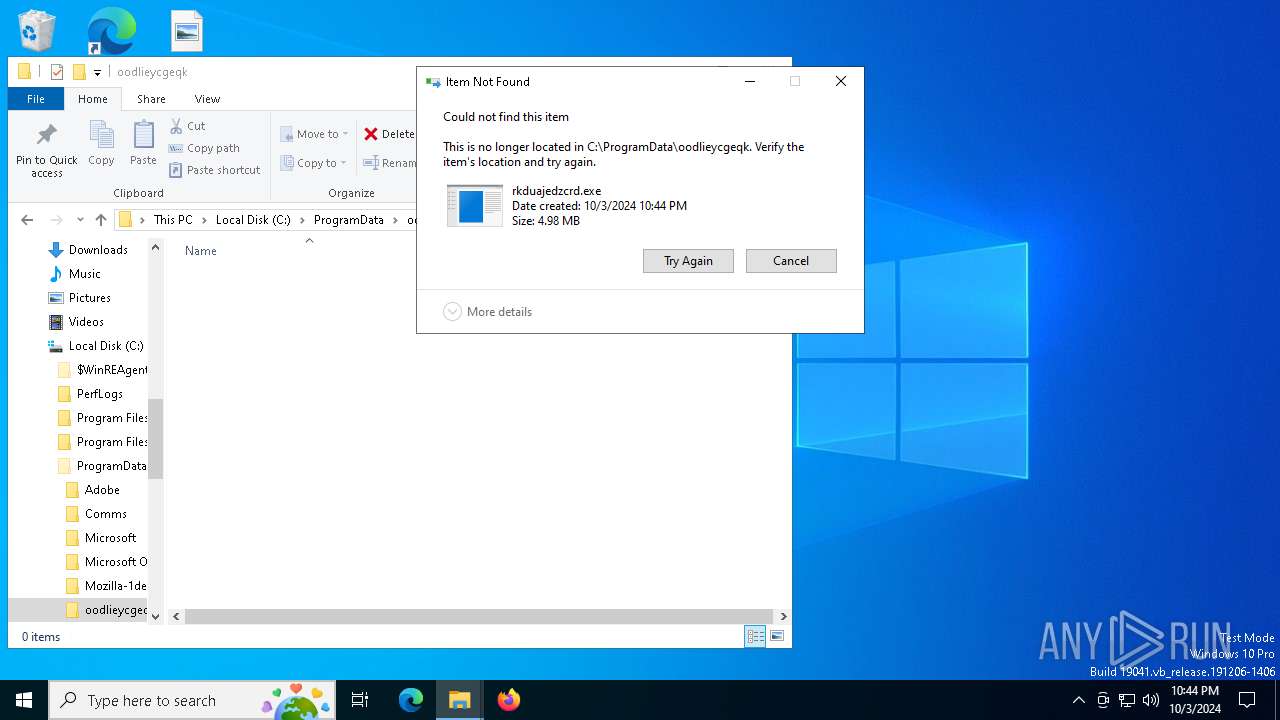
| 7136 | conhost.exe | C:\ProgramData\oodlieycgeqk\rkduajedzcrd.exe | executable | |
MD5:0838E4E90814A48E6122F4B0A2B2FC5F | SHA256:4F63CD101E4BDAACFFD9169610B7BB9430DE6BF87B9016125A3D76368F3E1FA7 | |||
| 6040 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_d5msma4v.mqj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
49
DNS requests
15
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1308 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6168 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3296 | explorer.exe | POST | 200 | 50.87.175.234:80 | http://webserverupdate.com/api/endpoint.php | unknown | — | — | malicious |
4060 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4288 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1308 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1308 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7052 | svchost.exe | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
xmr-asia1.nanopool.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
3296 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3296 | explorer.exe | Successful Credential Theft Detected | SUSPICIOUS [ANY.RUN] Host Name Exfiltration Atempt |
3296 | explorer.exe | A Network Trojan was detected | ET MALWARE SilentCryptoMiner Agent Config Inbound |
3296 | explorer.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M3 |
3296 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
1 ETPRO signatures available at the full report