| File name: | Mars Stealer 8 cracked.exe |
| Full analysis: | https://app.any.run/tasks/75e91345-3034-4e8b-8e05-6792b8120cfa |
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | April 26, 2022, 15:19:38 |
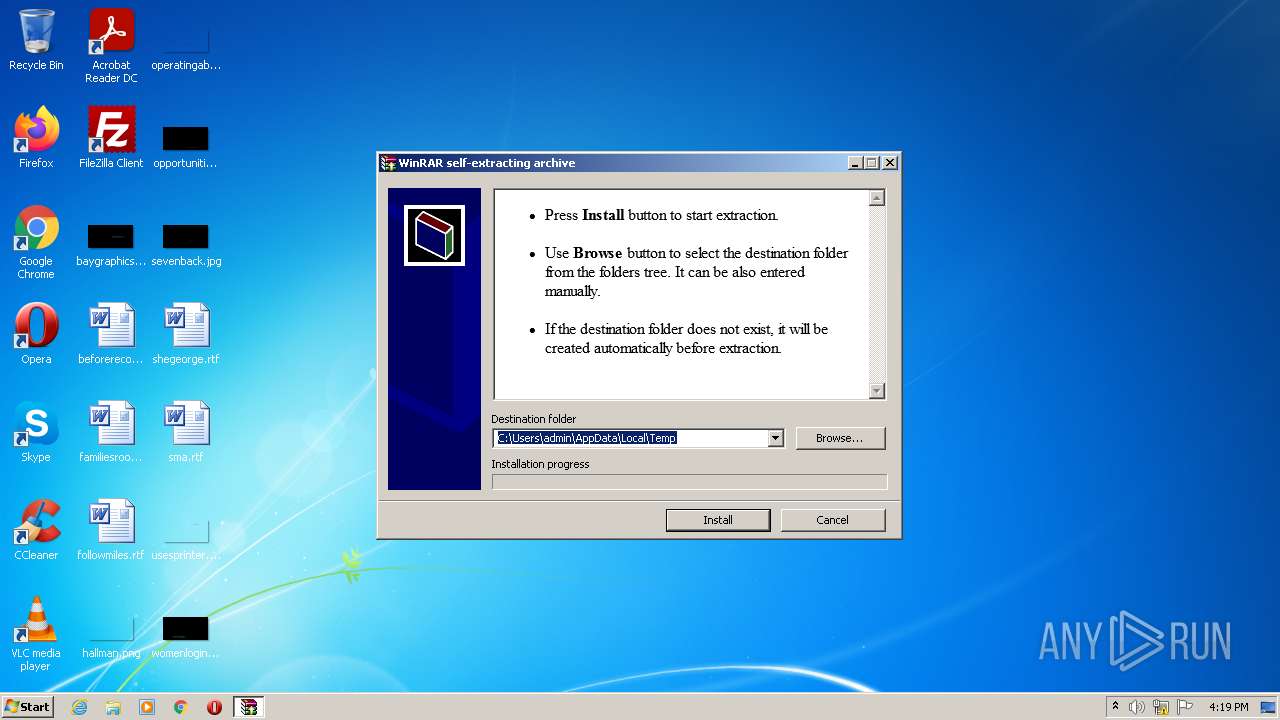
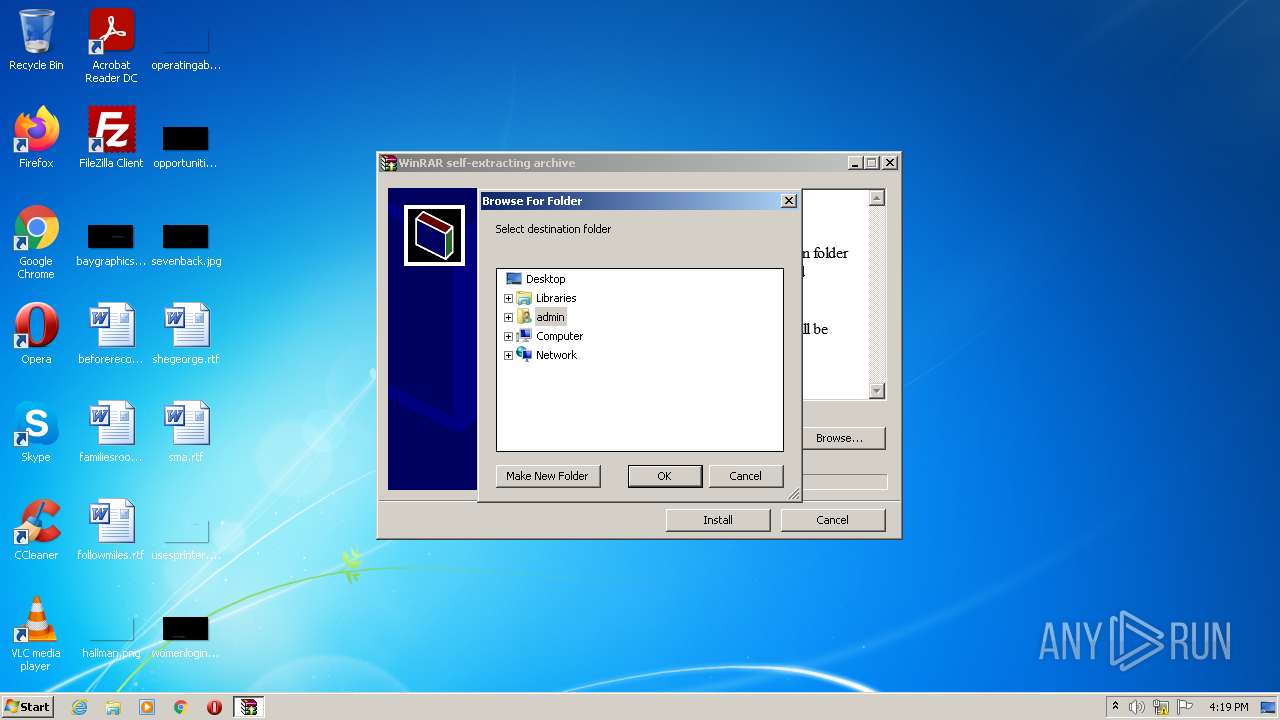
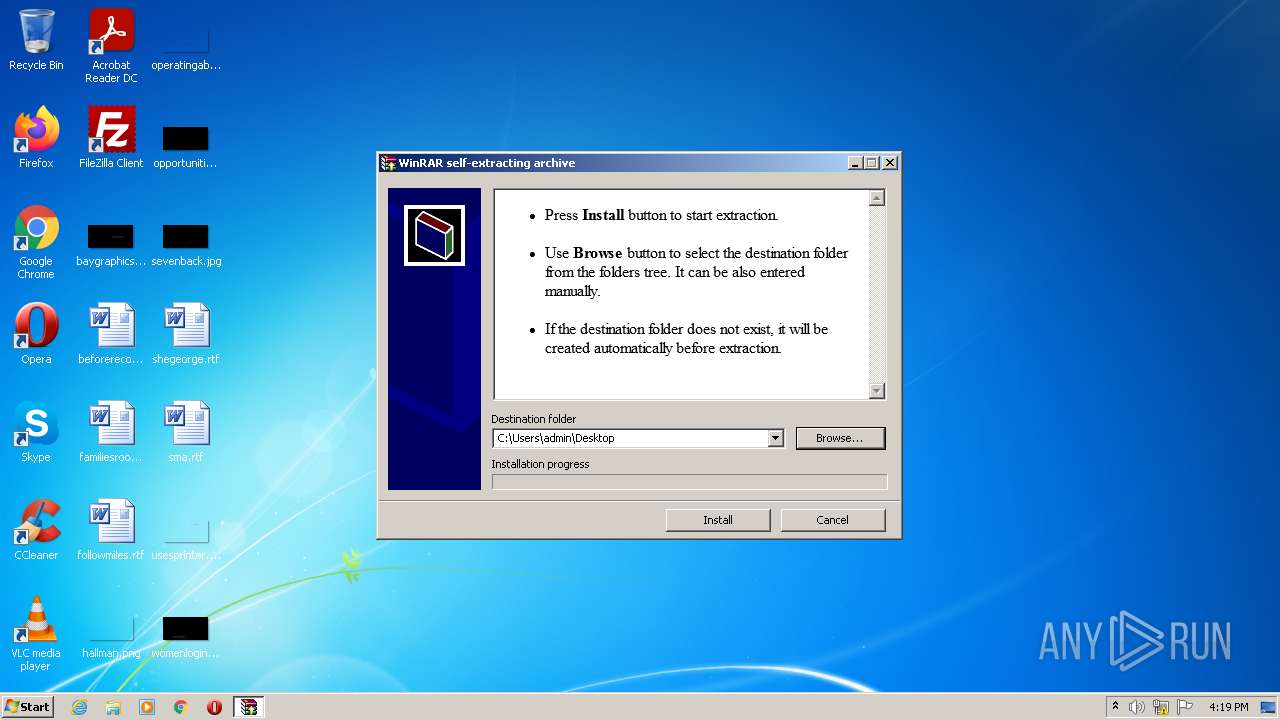
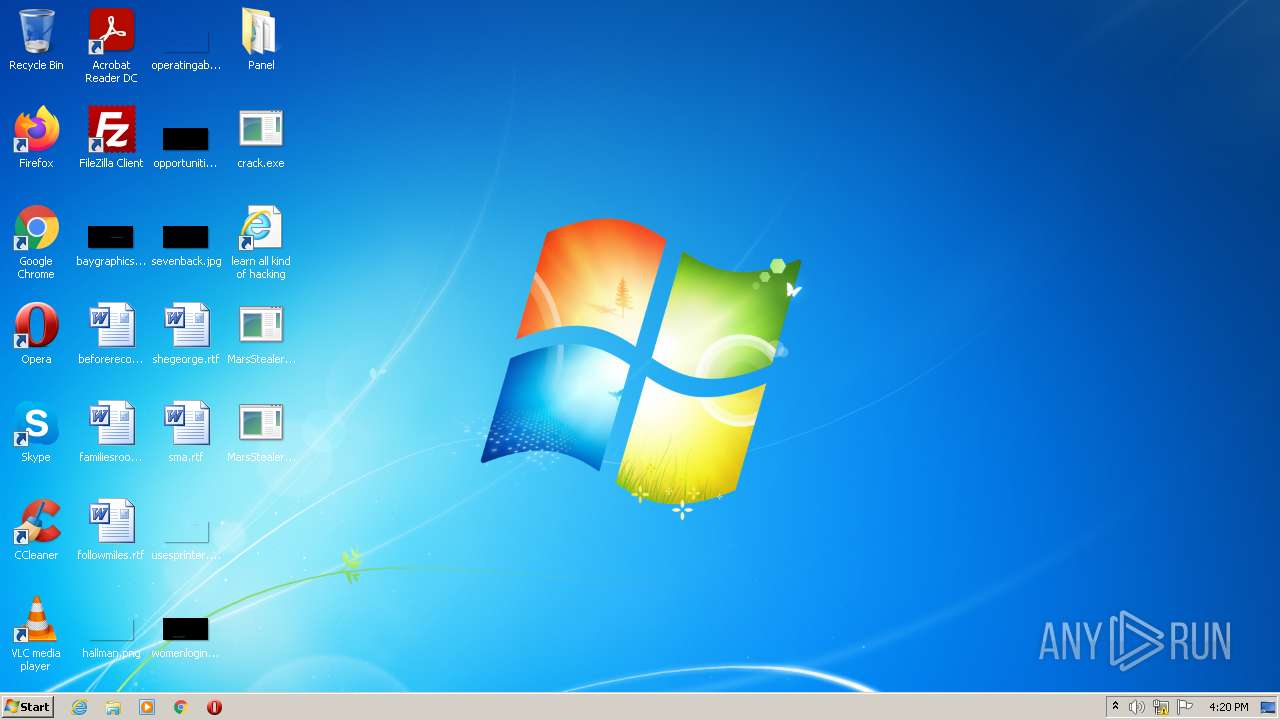
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 64B469AB282DAAD4F7EDEFBBF20787EE |
| SHA1: | D3207E901902E70CD85ABA149CEACF1A6CC74CB9 |
| SHA256: | 4EB7B842EE048E9F92F40FEC513BEE7D97148DDCBBE43652D5D1146D35A2C330 |
| SSDEEP: | 196608:JpeeOCr4PpZVzx60Iwx2BbjHsa051ekLR08nbQZmmsARR:JpeZW4PpZVUy2pM7jfRJ8xsARR |
MALICIOUS
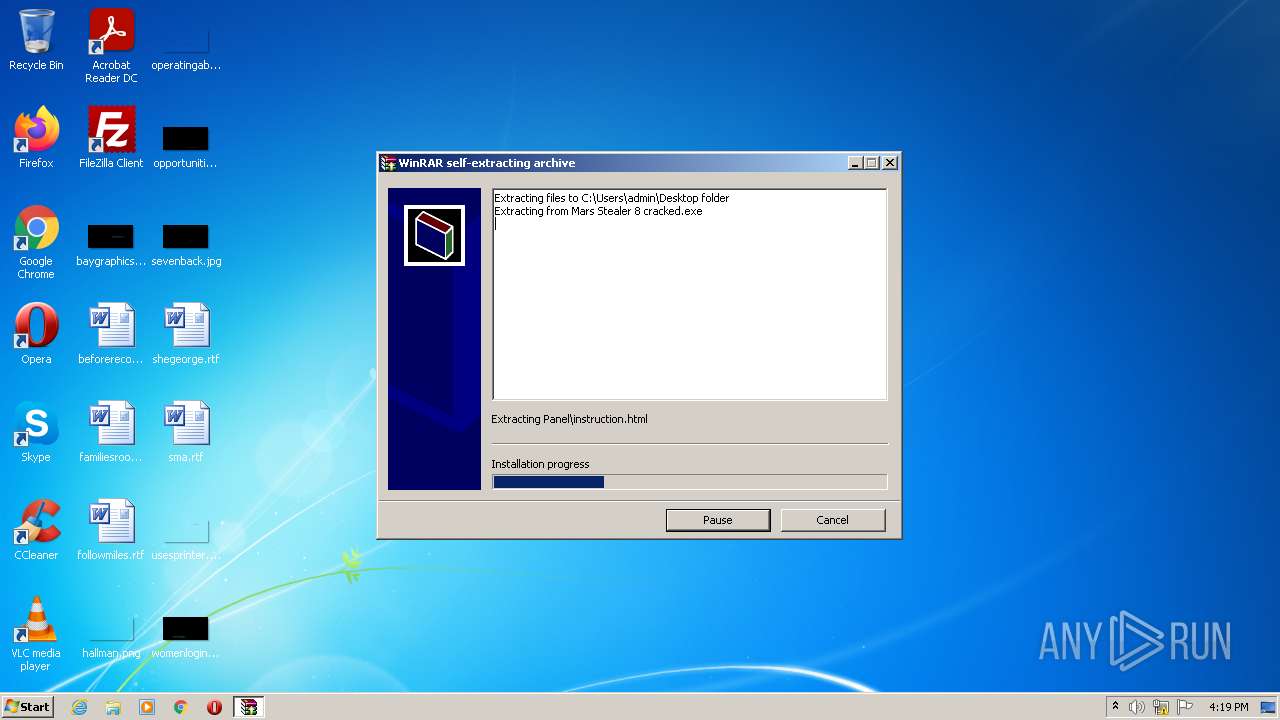
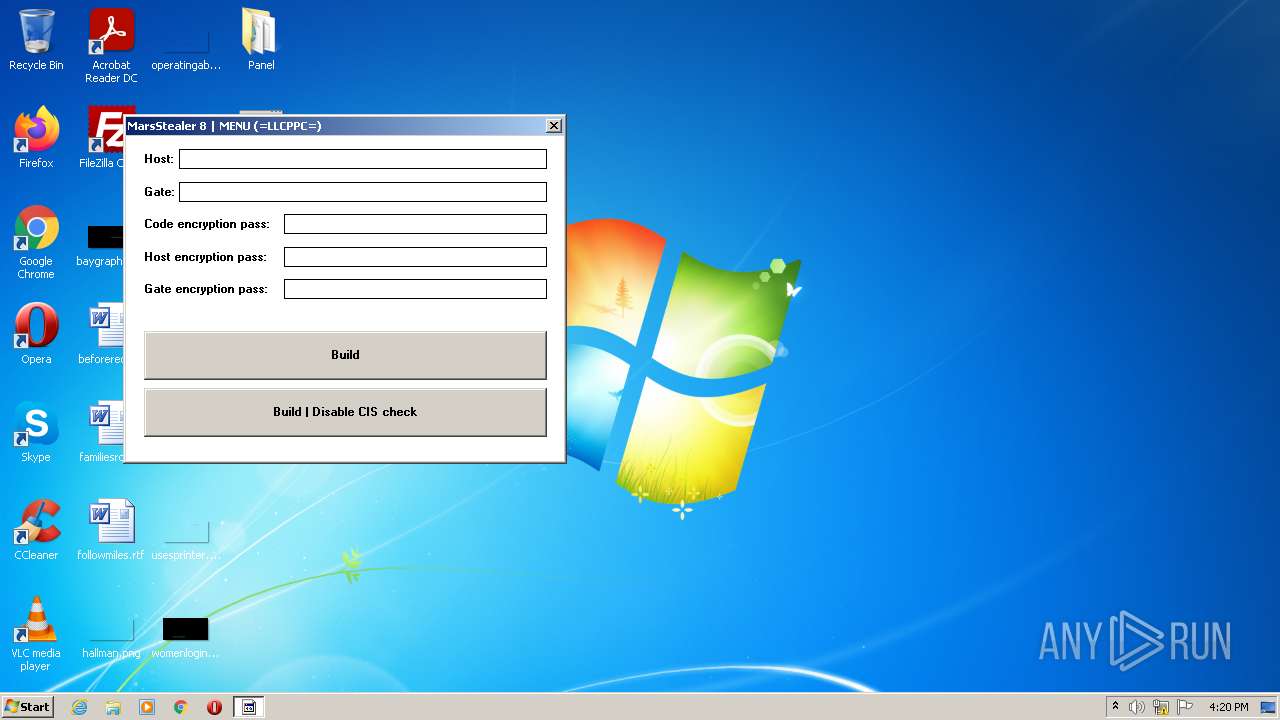
Drops executable file immediately after starts
- Mars Stealer 8 cracked.exe (PID: 2992)
- crack.exe (PID: 1348)
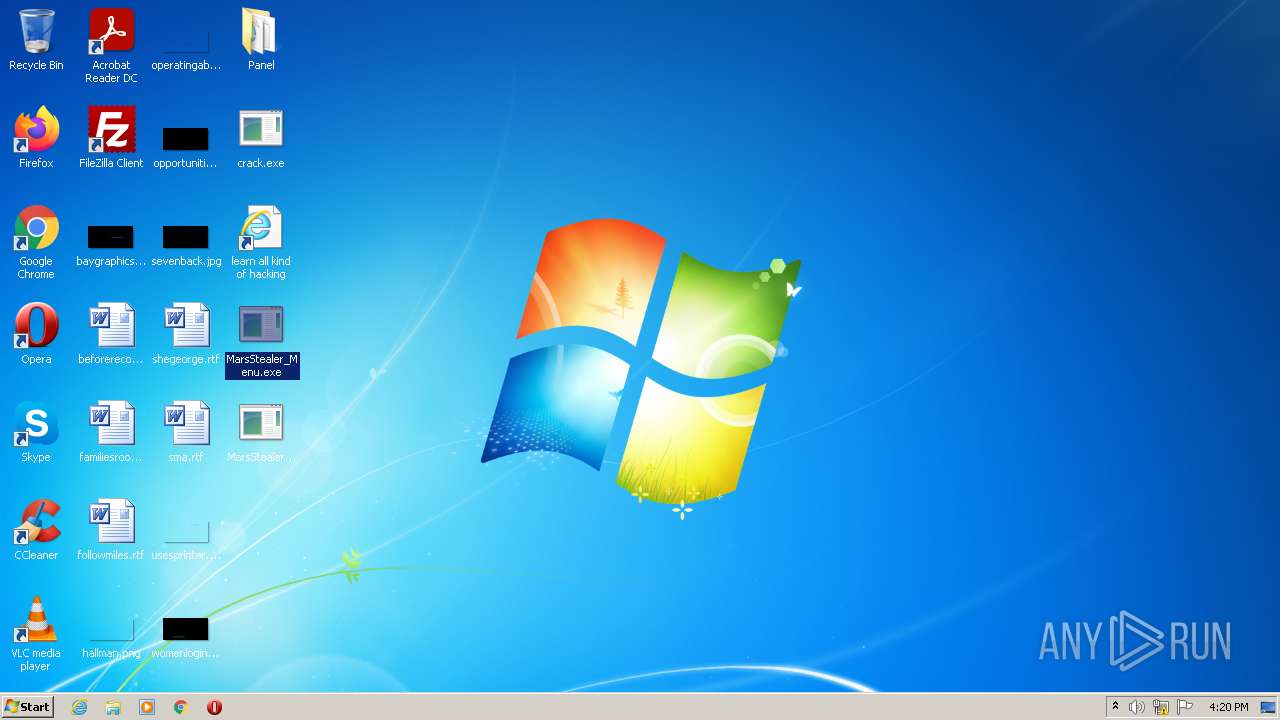
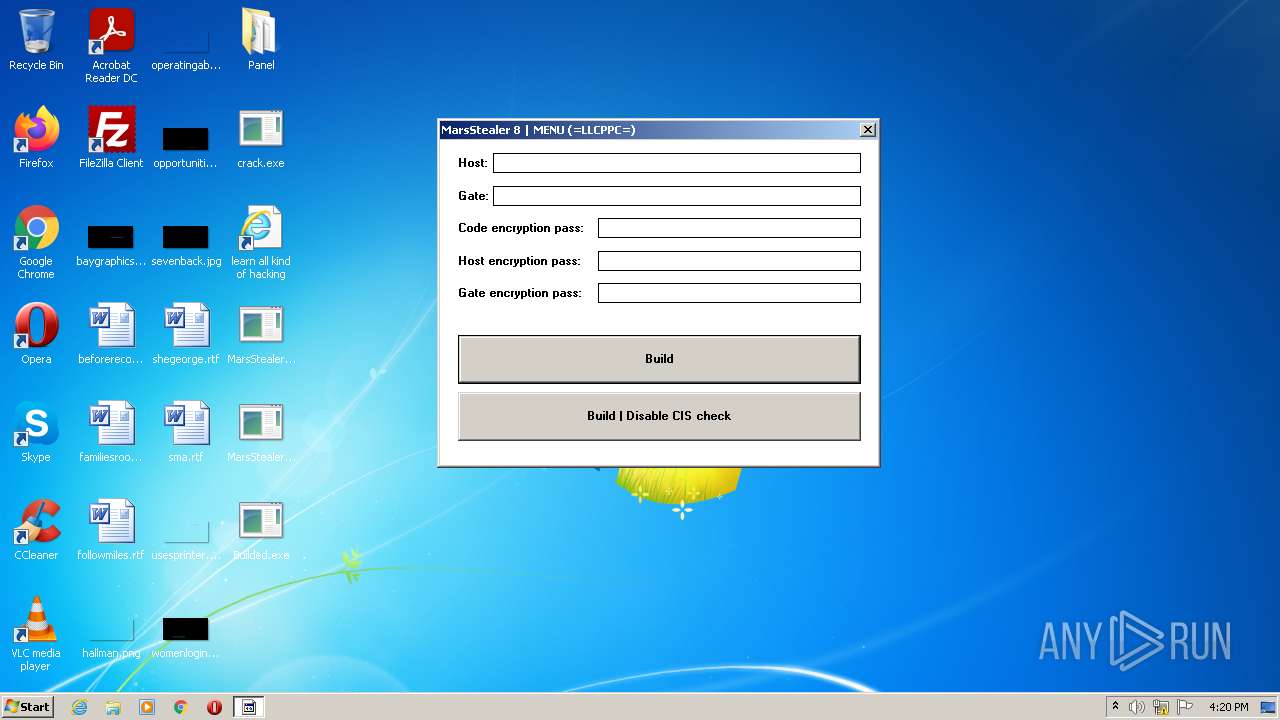
- MarsStealer_Menu.exe (PID: 3532)
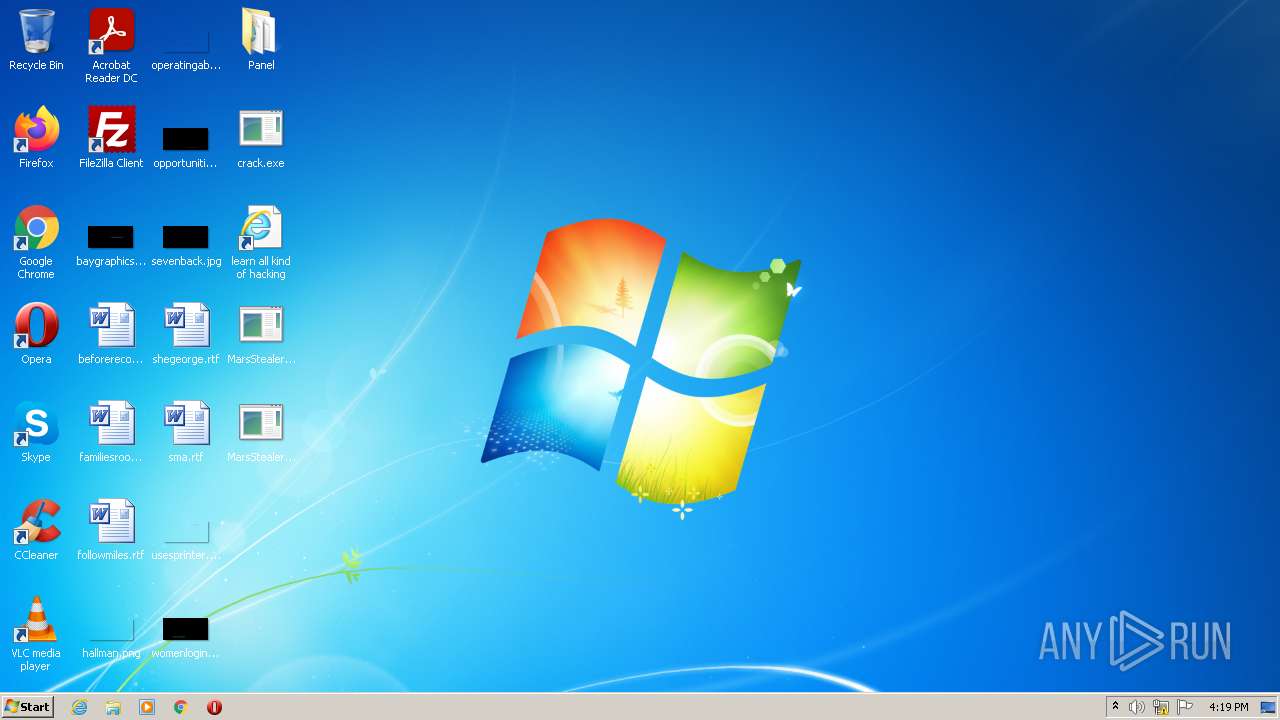
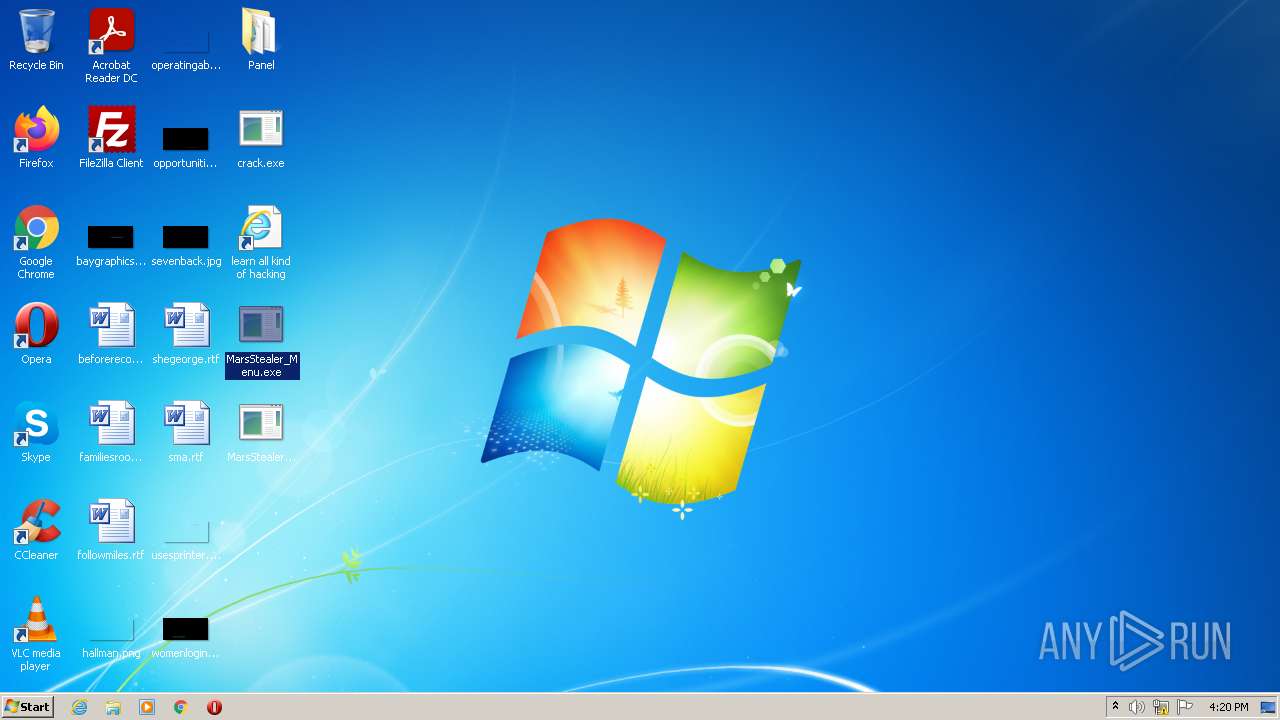
Application was dropped or rewritten from another process
- crack.exe (PID: 1348)
- MarsStealer_Menu.exe (PID: 4056)
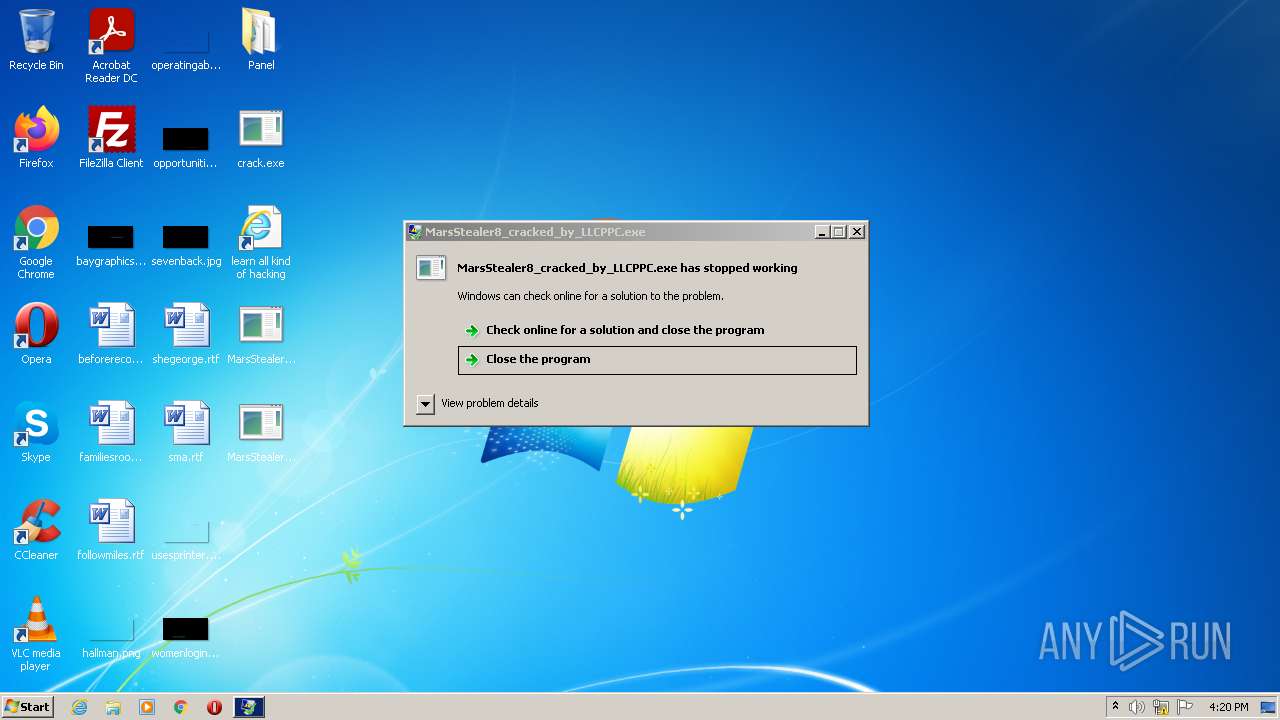
- MarsStealer8_cracked_by_LLCPPC.exe (PID: 2852)
- MarsStealer_Menu.exe (PID: 2040)
- crack.exe (PID: 3792)
- MarsStealer_Menu.exe (PID: 3532)
ARKEI detected by memory dumps
- MarsStealer8_cracked_by_LLCPPC.exe (PID: 2852)
Writes to a start menu file
- crack.exe (PID: 1348)
Changes the autorun value in the registry
- crack.exe (PID: 1348)
- crack.exe (PID: 3792)
SUSPICIOUS
Checks supported languages
- Mars Stealer 8 cracked.exe (PID: 2992)
- crack.exe (PID: 1348)
- MarsStealer_Menu.exe (PID: 4056)
- crack.exe (PID: 3792)
- MarsStealer_Menu.exe (PID: 2040)
- MarsStealer_Menu.exe (PID: 3532)
- MarsStealer8_cracked_by_LLCPPC.exe (PID: 2852)
Reads the computer name
- Mars Stealer 8 cracked.exe (PID: 2992)
- crack.exe (PID: 1348)
- MarsStealer8_cracked_by_LLCPPC.exe (PID: 2852)
- crack.exe (PID: 3792)
Reads Microsoft Outlook installation path
- Mars Stealer 8 cracked.exe (PID: 2992)
Executable content was dropped or overwritten
- Mars Stealer 8 cracked.exe (PID: 2992)
- crack.exe (PID: 1348)
- MarsStealer_Menu.exe (PID: 3532)
Reads internet explorer settings
- Mars Stealer 8 cracked.exe (PID: 2992)
Drops a file with a compile date too recent
- Mars Stealer 8 cracked.exe (PID: 2992)
- crack.exe (PID: 1348)
- MarsStealer_Menu.exe (PID: 3532)
Creates files in the user directory
- crack.exe (PID: 1348)
INFO
Dropped object may contain Bitcoin addresses
- Mars Stealer 8 cracked.exe (PID: 2992)
- crack.exe (PID: 1348)
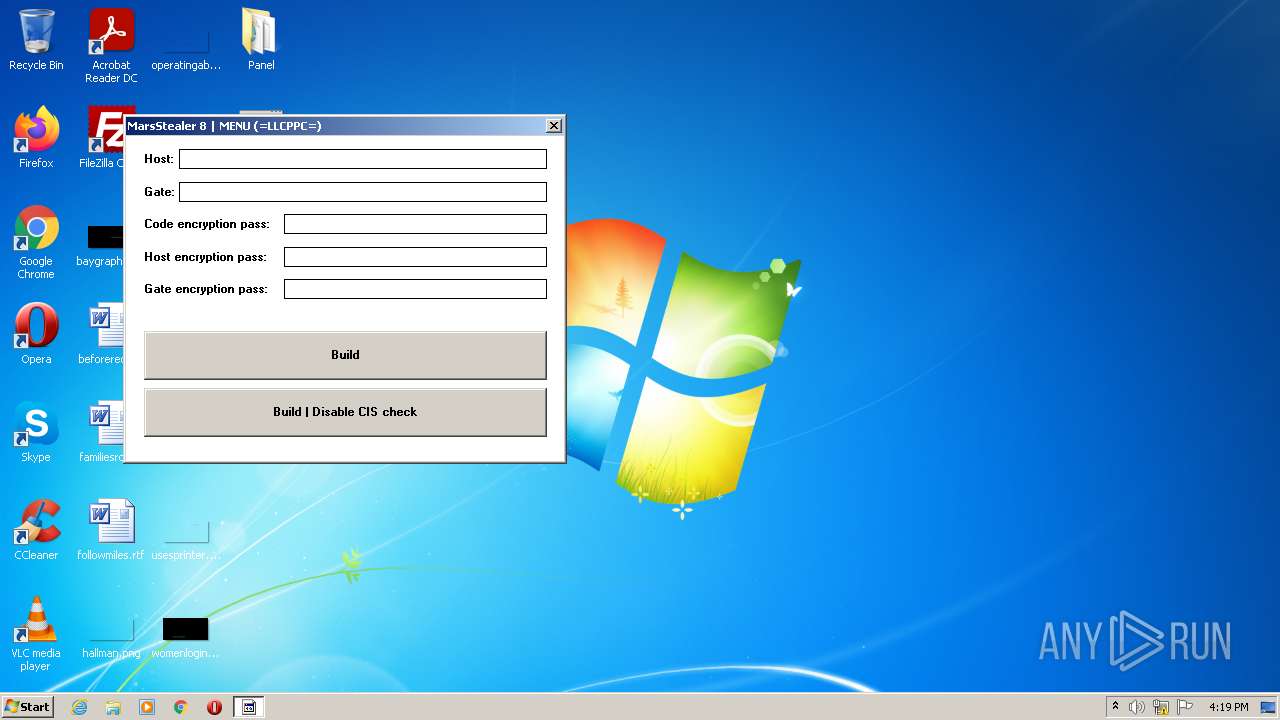
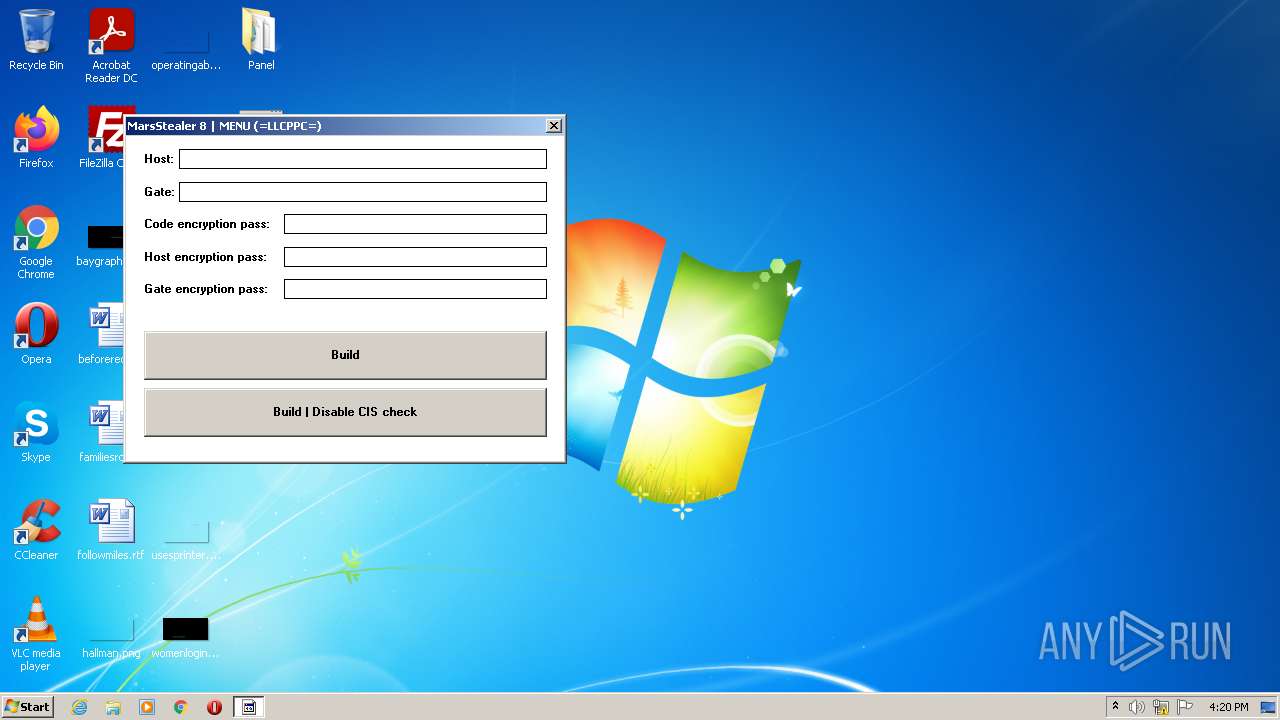
Manual execution by user
- MarsStealer_Menu.exe (PID: 4056)
- MarsStealer8_cracked_by_LLCPPC.exe (PID: 2852)
- MarsStealer_Menu.exe (PID: 2040)
- MarsStealer_Menu.exe (PID: 3532)
- crack.exe (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Arkei
(PID) Process(2852) MarsStealer8_cracked_by_LLCPPC.exe
C2http://
Mutex
other (618)LoadLibraryA
GetProcAddress
ExitProcess
advapi32.dll
crypt32.dll
GetTickCount
Sleep
GetUserDefaultLangID
CreateMutexA
GetLastError
HeapAlloc
GetProcessHeap
GetComputerNameA
VirtualProtect
GetCurrentProcess
VirtualAllocExNuma
GetUserNameA
CryptStringToBinaryA
HAL9TH
JohnDoe
21/04/2022 20:00:00
http://
Default
%hu/%hu/%hu %hu:%hu:%hu
open
sqlite3.dll
C:\ProgramData\sqlite3.dll
freebl3.dll
C:\ProgramData\freebl3.dll
mozglue.dll
C:\ProgramData\mozglue.dll
msvcp140.dll
C:\ProgramData\msvcp140.dll
nss3.dll
C:\ProgramData\nss3.dll
softokn3.dll
C:\ProgramData\softokn3.dll
vcruntime140.dll
C:\ProgramData\vcruntime140.dll
.zip
Tag:
IP: IP?
Country: Country?
Working Path:
Local Time:
TimeZone:
Display Language:
Keyboard Languages:
Is Laptop:
Processor:
Installed RAM:
OS:
(
Bit)
Videocard:
Display Resolution:
PC name:
User name:
Domain name:
MachineID:
GUID:
Installed Software:
system.txt
Grabber\%s.zip
%APPDATA%
%LOCALAPPDATA%
%USERPROFILE%
%DESKTOP%
Wallets\
Ethereum
\Ethereum\
keystore
Electrum
\Electrum\wallets\
*.*
ElectrumLTC
\Electrum-LTC\wallets\
Exodus
\Exodus\
exodus.conf.json
window-state.json
\Exodus\exodus.wallet\
passphrase.json
seed.seco
info.seco
ElectronCash
\ElectronCash\wallets\
default_wallet
MultiDoge
\MultiDoge\
multidoge.wallet
JAXX
\jaxx\Local Storage\
file__0.localstorage
Atomic
\atomic\Local Storage\leveldb\
000003.log
CURRENT
LOCK
LOG
MANIFEST-000001
0000*
Binance
\Binance\
app-store.json
Coinomi
\Coinomi\Coinomi\wallets\
*.wallet
*.config
*wallet*.dat
GetSystemTime
lstrcatA
SystemTimeToFileTime
ntdll.dll
sscanf
memset
memcpy
wininet.dll
user32.dll
gdi32.dll
netapi32.dll
psapi.dll
bcrypt.dll
vaultcli.dll
shlwapi.dll
shell32.dll
gdiplus.dll
ole32.dll
dbghelp.dll
CreateFileA
WriteFile
CloseHandle
GetFileSize
lstrlenA
LocalAlloc
GlobalFree
ReadFile
OpenProcess
SetFilePointer
SetEndOfFile
GetCurrentProcessId
GetLocalTime
GetTimeZoneInformation
GetUserDefaultLocaleName
LocalFree
GetSystemPowerStatus
GetSystemInfo
GlobalMemoryStatusEx
IsWow64Process
GetTempPathA
GetLocaleInfoA
GetFileSizeEx
GetFileAttributesA
FindFirstFileA
FindNextFileA
FindClose
GetCurrentDirectoryA
CopyFileA
DeleteFileA
lstrcmpW
GlobalAlloc
FreeLibrary
SetCurrentDirectoryA
CreateFileMappingA
MapViewOfFile
UnmapViewOfFile
FileTimeToSystemTime
GetFileInformationByHandle
GlobalLock
GlobalSize
WideCharToMultiByte
GetWindowsDirectoryA
GetVolumeInformationA
GetVersionExA
GetModuleFileNameA
CreateFileW
CreateFileMappingW
MultiByteToWideChar
CreateThread
GetEnvironmentVariableA
SetEnvironmentVariableA
lstrcpyA
lstrcpynA
InternetOpenA
InternetConnectA
HttpOpenRequestA
HttpSendRequestA
HttpQueryInfoA
InternetCloseHandle
InternetReadFile
InternetSetOptionA
InternetOpenUrlA
InternetCrackUrlA
wsprintfA
CharToOemW
GetKeyboardLayoutList
EnumDisplayDevicesA
ReleaseDC
GetDC
GetSystemMetrics
GetDesktopWindow
GetWindowRect
GetWindowDC
CloseWindow
RegOpenKeyExA
RegQueryValueExA
RegCloseKey
GetCurrentHwProfileA
RegEnumKeyExA
RegGetValueA
CreateDCA
GetDeviceCaps
CreateCompatibleDC
CreateCompatibleBitmap
SelectObject
BitBlt
DeleteObject
StretchBlt
GetObjectW
GetDIBits
SaveDC
CreateDIBSection
DeleteDC
RestoreDC
DsRoleGetPrimaryDomainInformation
GetModuleFileNameExA
CryptUnprotectData
BCryptCloseAlgorithmProvider
BCryptDestroyKey
BCryptOpenAlgorithmProvider
BCryptSetProperty
BCryptGenerateSymmetricKey
BCryptDecrypt
VaultOpenVault
VaultCloseVault
VaultEnumerateItems
VaultGetItemWin8
VaultGetItemWin7
VaultFree
StrCmpCA
StrStrA
PathMatchSpecA
SHGetFolderPathA
ShellExecuteExA
GdipGetImageEncodersSize
GdipGetImageEncoders
GdipCreateBitmapFromHBITMAP
GdiplusStartup
GdiplusShutdown
GdipSaveImageToStream
GdipDisposeImage
GdipFree
CreateStreamOnHGlobal
GetHGlobalFromStream
SymMatchString
HEAD
HTTP/1.1
GET
POST
file
Content-Type: multipart/form-data; boundary=----
Content-Disposition: form-data; name="
Content-Disposition: form-data; name="file"; filename="
Content-Type: application/octet-stream
Content-Transfer-Encoding: binary
SOFT:
PROF: ?
PROF:
HOST:
USER:
PASS:
sqlite3_open
sqlite3_prepare_v2
sqlite3_step
sqlite3_column_text
sqlite3_finalize
sqlite3_close
sqlite3_column_bytes
sqlite3_column_blob
encrypted_key
"}
PATH
PATH=
NSS_Init
NSS_Shutdown
PK11_GetInternalKeySlot
PK11_FreeSlot
PK11_Authenticate
PK11SDR_Decrypt
SELECT origin_url, username_value, password_value FROM logins
Cookies\%s_%s.txt
SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies
TRUE
FALSE
Autofill\%s_%s.txt
SELECT name, value FROM autofill
CC\%s_%s.txt
SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards
Card number:
Name on card:
Expiration date:
History\%s_%s.txt
SELECT url FROM urls
Downloads\%s_%s.txt
SELECT target_path, tab_url from downloads
Login Data
Cookies
Web Data
History
SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies
logins.json
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
guid
SELECT fieldname, value FROM moz_formhistory
SELECT url FROM moz_places
cookies.sqlite
formhistory.sqlite
places.sqlite
\Local State
..\profiles.ini
C:\ProgramData\
Chrome
\Google\Chrome\User Data
ChromeBeta
\Google\Chrome Beta\User Data
ChromeCanary
\Google\Chrome SxS\User Data
Chromium
\Chromium\User Data
Edge_Chromium
\Microsoft\Edge\User Data
Kometa
\Kometa\User Data
Amigo
\Amigo\User Data
Torch
\Torch\User Data
Orbitum
\Orbitum\User Data
Comodo
\Comodo\Dragon\User Data
Nichrome
\Nichrome\User Data
Maxthon5
\Maxthon5\Users
Sputnik
\Sputnik\User Data
EPB
\Epic Privacy Browser\User Data
Vivaldi
\Vivaldi\User Data
CocCoc
\CocCoc\Browser\User Data
Uran
\uCozMedia\Uran\User Data
QIP
\QIP Surf\User Data
Cent
\CentBrowser\User Data
Elements
\Elements Browser\User Data
TorBro
\TorBro\Profile
CryptoTab
\CryptoTab Browser\User Data
Brave
\BraveSoftware\Brave-Browser\User Data
Opera
\Opera Software\Opera Stable\
OperaGX
\Opera Software\Opera GX Stable\
OperaNeon
\Opera Software\Opera Neon\User Data
Firefox
\Mozilla\Firefox\Profiles\
SlimBrowser
\FlashPeak\SlimBrowser\Profiles\
PaleMoon
\Moonchild Productions\Pale Moon\Profiles\
Waterfox
\Waterfox\Profiles\
Cyberfox
\8pecxstudios\Cyberfox\Profiles\
BlackHawk
\NETGATE Technologies\BlackHawk\Profiles\
IceCat
\Mozilla\icecat\Profiles\
KMeleon
\K-Meleon\
Thunderbird
\Thunderbird\Profiles\
passwords.txt
ibnejdfjmmkpcnlpebklmnkoeoihofec
TronLink
nkbihfbeogaeaoehlefnkodbefgpgknn
MetaMask
fhbohimaelbohpjbbldcngcnapndodjp
Binance Chain Wallet
ffnbelfdoeiohenkjibnmadjiehjhajb
Yoroi
jbdaocneiiinmjbjlgalhcelgbejmnid
Nifty Wallet
afbcbjpbpfadlkmhmclhkeeodmamcflc
Math Wallet
hnfanknocfeofbddgcijnmhnfnkdnaad
Coinbase Wallet
hpglfhgfnhbgpjdenjgmdgoeiappafln
Guarda
blnieiiffboillknjnepogjhkgnoapac
EQUAL Wallet
cjelfplplebdjjenllpjcblmjkfcffne
Jaxx Liberty
fihkakfobkmkjojpchpfgcmhfjnmnfpi
BitApp Wallet
kncchdigobghenbbaddojjnnaogfppfj
iWallet
amkmjjmmflddogmhpjloimipbofnfjih
Wombat
nlbmnnijcnlegkjjpcfjclmcfggfefdm
MEW CX
nanjmdknhkinifnkgdcggcfnhdaammmj
GuildWallet
nkddgncdjgjfcddamfgcmfnlhccnimig
Saturn Wallet
fnjhmkhhmkbjkkabndcnnogagogbneec
Ronin Wallet
cphhlgmgameodnhkjdmkpanlelnlohao
NeoLine
nhnkbkgjikgcigadomkphalanndcapjk
Clover Wallet
kpfopkelmapcoipemfendmdcghnegimn
Liquality Wallet
aiifbnbfobpmeekipheeijimdpnlpgpp
Terra Station
dmkamcknogkgcdfhhbddcghachkejeap
Keplr
fhmfendgdocmcbmfikdcogofphimnkno
Sollet
cnmamaachppnkjgnildpdmkaakejnhae
Auro Wallet
jojhfeoedkpkglbfimdfabpdfjaoolaf
Polymesh Wallet
flpiciilemghbmfalicajoolhkkenfel
ICONex
nknhiehlklippafakaeklbeglecifhad
Nabox Wallet
hcflpincpppdclinealmandijcmnkbgn
KHC
ookjlbkiijinhpmnjffcofjonbfbgaoc
Temple
mnfifefkajgofkcjkemidiaecocnkjeh
TezBox
dkdedlpgdmmkkfjabffeganieamfklkm
Cyano Wallet
nlgbhdfgdhgbiamfdfmbikcdghidoadd
Byone
infeboajgfhgbjpjbeppbkgnabfdkdaf
OneKey
cihmoadaighcejopammfbmddcmdekcje
LeafWallet
lodccjjbdhfakaekdiahmedfbieldgik
DAppPlay
ijmpgkjfkbfhoebgogflfebnmejmfbml
BitClip
lkcjlnjfpbikmcmbachjpdbijejflpcm
Steem Keychain
onofpnbbkehpmmoabgpcpmigafmmnjhl
Nash Extension
bcopgchhojmggmffilplmbdicgaihlkp
Hycon Lite Client
klnaejjgbibmhlephnhpmaofohgkpgkd
ZilPay
aeachknmefphepccionboohckonoeemg
Coin98 Wallet
bfnaelmomeimhlpmgjnjophhpkkoljpa
Phantom
hifafgmccdpekplomjjkcfgodnhcellj
Crypto.com
dngmlblcodfobpdpecaadgfbcggfjfnm
Maiar DeFi Wallet
ppdadbejkmjnefldpcdjhnkpbjkikoip
Oasis
hpbgcgmiemanfelegbndmhieiigkackl
MonstaWallet
fcckkdbjnoikooededlapcalpionmalo
MOBOX
jccapkebeeiajkkdemacblkjhhhboiek
Crust Wallet
mgffkfbidihjpoaomajlbgchddlicgpn
Pali Wallet
nphplpgoakhhjchkkhmiggakijnkhfnd
TON Wallet
ldinpeekobnhjjdofggfgjlcehhmanlj
Hiro Wallet
pocmplpaccanhmnllbbkpgfliimjljgo
Slope Wallet
bhhhlbepdkbapadjdnnojkbgioiodbic
Solflare Wallet
pgiaagfkgcbnmiiolekcfmljdagdhlcm
Stargazer Wallet
cgeeodpfagjceefieflmdfphplkenlfk
EVER Wallet
gjkdbeaiifkpoencioahhcilildpjhgh
partisia-wallet
bgjogpoidejdemgoochpnkmdjpocgkha
Ecto Wallet
ifckdpamphokdglkkdomedpdegcjhjdp
ONTO Wallet
agechnindjilpccclelhlbjphbgnobpf
Fractal Wallet
algblmhagnobbnmakepomicmfljlbehg
ADS Wallet
imijjbmbnebfnbmonjeileijahaipglj
Moonlet Wallet
kpjdchaapjheajadlaakiiigcbhoppda
ZEBEDEE
dlcobpjiigpikoobohmabehhmhfoodbb
Argent X StarkNet Wallet
bofddndhbegljegmpmnlbhcejofmjgbn
X-Wallet
mapbhaebnddapnmifbbkgeedkeplgjmf
Biport Wallet
kfdniefadaanbjodldohaedphafoffoh
Typhon Wallet
jaooiolkmfcmloonphpiiogkfckgciom
Twetch Wallet
aijcbedoijmgnlmjeegjaglmepbmpkpi
Leap Wallet
fhfffofbcgbjjojdnpcfompojdjjhdim
Lamden Wallet
agkfnefiabmfpanochlcakggnkdfmmjd
Earth Wallet
lpfcbjknijpeeillifnkikgncikgfhdo
Nami
fecfflganphcinpahcklgahckeohalog
Coin Wallet
ilhaljfiglknggcoegeknjghdgampffk
Beam Web Wallet
dklmlehijiaepdijfnbbhncfpcoeeljf
FShares Wallet
fkhebcilafocjhnlcngogekljmllgdhd
WAGMIswap.io Wallet
laphpbhjhhgigmjoflgcchgodbbclahk
BLUE - Worlds Safest and Simplest Wallet
mkjjflkhdddfjhonakofipfojoepfndk
Unification Web Wallet
jnldfbidonfeldmalbflbmlebbipcnle
Infinity Wallet
ellkdbaphhldpeajbepobaecooaoafpg
Fetch.ai Network Wallet
iokeahhehimjnekafflcihljlcjccdbe
Alby Wallet
omajpeaffjgmlpmhbfdjepdejoemifpe
xBull Wallet
pgojdfajgcjjpjnbpfaelnpnjocakldb
Sugarchain Wallet
pnndplcbkakcplkjnolgbkdgjikjednm
Tronium
fnnegphlobjdpkhecapkijjdkgcjhkib
Harmony
fhilaheimglignddkjgofkcbgekhenbh
Oxygen
cmbagcoinhmacpcgmbiniijboejgiahi
JustLiquidity Wallet
kmmolakhbgdlpkjkcjkebenjheonagdm
AlgoSigner
fnabdmcgpkkjjegokfcnfbpneacddpfh
Goldmint Lite Wallet
bgpipimickeadkjlklgciifhnalhdjhe
GeroWallet
hoighigmnhgkkdaenafgnefkcmipfjon
EO.Finance
nlgnepoeokdfodgjkjiblkadkjbdfmgd
Multi Wallet
nhihjlnjgibefgjhobhcphmnckoogdea
Waves Enterprise Wallet
ehibhohmlpipbaogcknmpmiibbllplph
Bluehelix Wallet
magbanejlegnbcppjljfhnmfmghialkl
Nebulas Wallet
fgkaeeikaoeiiggggbgdcjchmdfmamla
Vtimes
pnlfjmlcjdjgkddecgincndfgegkecke
Crocobit Wallet
bhghoamapcdpbohphigoooaddinpkbai
Authenticator
gaedmjdfmmahhbjefcbgaolhhanlaolb
Authy
oeljdldpnmdbchonielidgobddffflal
EOS Authenticator
ilgcnhelpchnceeipipijaljkblbcobl
GAuth Authenticator
imloifkgjagghnncjkhggdhalmcnfklk
Trezor Password Manager
%s\%s\Local Extension Settings\%s
%s\CURRENT
%s\%s\Sync Extension Settings\%s
%s\%s\IndexedDB\chrome-extension_%s_0.indexeddb.leveldb
Plugins\
HARDWARE\DESCRIPTION\System\CentralProcessor\0
ProcessorNameString
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
x64
x86
DISPLAY
SOFTWARE\Microsoft\Cryptography
MachineGuid
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
DisplayName
DisplayVersion
screenshot.jpg
ABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890
/c timeout /t 5 & del /f /q "%s" & exit
C:\Windows\System32\cmd.exe
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1cab5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 196096 |
| CodeSize: | 188416 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00004680 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63811 |
.reloc | 0x0005F000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
45
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Users\admin\Desktop\crack.exe" | C:\Users\admin\Desktop\crack.exe | Mars Stealer 8 cracked.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Get Cliboard Address Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\Desktop\MarsStealer_Menu.exe" | C:\Users\admin\Desktop\MarsStealer_Menu.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\Desktop\MarsStealer8_cracked_by_LLCPPC.exe" | C:\Users\admin\Desktop\MarsStealer8_cracked_by_LLCPPC.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
Arkei(PID) Process(2852) MarsStealer8_cracked_by_LLCPPC.exe C2http:// Mutex other (618)LoadLibraryA GetProcAddress ExitProcess advapi32.dll crypt32.dll GetTickCount Sleep GetUserDefaultLangID CreateMutexA GetLastError HeapAlloc GetProcessHeap GetComputerNameA VirtualProtect GetCurrentProcess VirtualAllocExNuma GetUserNameA CryptStringToBinaryA HAL9TH JohnDoe 21/04/2022 20:00:00 http:// Default %hu/%hu/%hu %hu:%hu:%hu open sqlite3.dll C:\ProgramData\sqlite3.dll freebl3.dll C:\ProgramData\freebl3.dll mozglue.dll C:\ProgramData\mozglue.dll msvcp140.dll C:\ProgramData\msvcp140.dll nss3.dll C:\ProgramData\nss3.dll softokn3.dll C:\ProgramData\softokn3.dll vcruntime140.dll C:\ProgramData\vcruntime140.dll .zip Tag: IP: IP? Country: Country? Working Path: Local Time: TimeZone: Display Language: Keyboard Languages: Is Laptop: Processor: Installed RAM: OS: ( Bit) Videocard: Display Resolution: PC name: User name: Domain name: MachineID: GUID: Installed Software: system.txt Grabber\%s.zip %APPDATA% %LOCALAPPDATA% %USERPROFILE% %DESKTOP% Wallets\ Ethereum \Ethereum\ keystore Electrum \Electrum\wallets\ *.* ElectrumLTC \Electrum-LTC\wallets\ Exodus \Exodus\ exodus.conf.json window-state.json \Exodus\exodus.wallet\ passphrase.json seed.seco info.seco ElectronCash \ElectronCash\wallets\ default_wallet MultiDoge \MultiDoge\ multidoge.wallet JAXX \jaxx\Local Storage\ file__0.localstorage Atomic \atomic\Local Storage\leveldb\ 000003.log CURRENT LOCK LOG MANIFEST-000001 0000* Binance \Binance\ app-store.json Coinomi \Coinomi\Coinomi\wallets\ *.wallet *.config *wallet*.dat GetSystemTime lstrcatA SystemTimeToFileTime ntdll.dll sscanf memset memcpy wininet.dll user32.dll gdi32.dll netapi32.dll psapi.dll bcrypt.dll vaultcli.dll shlwapi.dll shell32.dll gdiplus.dll ole32.dll dbghelp.dll CreateFileA WriteFile CloseHandle GetFileSize lstrlenA LocalAlloc GlobalFree ReadFile OpenProcess SetFilePointer SetEndOfFile GetCurrentProcessId GetLocalTime GetTimeZoneInformation GetUserDefaultLocaleName LocalFree GetSystemPowerStatus GetSystemInfo GlobalMemoryStatusEx IsWow64Process GetTempPathA GetLocaleInfoA GetFileSizeEx GetFileAttributesA FindFirstFileA FindNextFileA FindClose GetCurrentDirectoryA CopyFileA DeleteFileA lstrcmpW GlobalAlloc FreeLibrary SetCurrentDirectoryA CreateFileMappingA MapViewOfFile UnmapViewOfFile FileTimeToSystemTime GetFileInformationByHandle GlobalLock GlobalSize WideCharToMultiByte GetWindowsDirectoryA GetVolumeInformationA GetVersionExA GetModuleFileNameA CreateFileW CreateFileMappingW MultiByteToWideChar CreateThread GetEnvironmentVariableA SetEnvironmentVariableA lstrcpyA lstrcpynA InternetOpenA InternetConnectA HttpOpenRequestA HttpSendRequestA HttpQueryInfoA InternetCloseHandle InternetReadFile InternetSetOptionA InternetOpenUrlA InternetCrackUrlA wsprintfA CharToOemW GetKeyboardLayoutList EnumDisplayDevicesA ReleaseDC GetDC GetSystemMetrics GetDesktopWindow GetWindowRect GetWindowDC CloseWindow RegOpenKeyExA RegQueryValueExA RegCloseKey GetCurrentHwProfileA RegEnumKeyExA RegGetValueA CreateDCA GetDeviceCaps CreateCompatibleDC CreateCompatibleBitmap SelectObject BitBlt DeleteObject StretchBlt GetObjectW GetDIBits SaveDC CreateDIBSection DeleteDC RestoreDC DsRoleGetPrimaryDomainInformation GetModuleFileNameExA CryptUnprotectData BCryptCloseAlgorithmProvider BCryptDestroyKey BCryptOpenAlgorithmProvider BCryptSetProperty BCryptGenerateSymmetricKey BCryptDecrypt VaultOpenVault VaultCloseVault VaultEnumerateItems VaultGetItemWin8 VaultGetItemWin7 VaultFree StrCmpCA StrStrA PathMatchSpecA SHGetFolderPathA ShellExecuteExA GdipGetImageEncodersSize GdipGetImageEncoders GdipCreateBitmapFromHBITMAP GdiplusStartup GdiplusShutdown GdipSaveImageToStream GdipDisposeImage GdipFree CreateStreamOnHGlobal GetHGlobalFromStream SymMatchString HEAD HTTP/1.1 GET POST file Content-Type: multipart/form-data; boundary=---- Content-Disposition: form-data; name=" Content-Disposition: form-data; name="file"; filename=" Content-Type: application/octet-stream Content-Transfer-Encoding: binary SOFT: PROF: ? PROF: HOST: USER: PASS: sqlite3_open sqlite3_prepare_v2 sqlite3_step sqlite3_column_text sqlite3_finalize sqlite3_close sqlite3_column_bytes sqlite3_column_blob encrypted_key "} PATH PATH= NSS_Init NSS_Shutdown PK11_GetInternalKeySlot PK11_FreeSlot PK11_Authenticate PK11SDR_Decrypt SELECT origin_url, username_value, password_value FROM logins Cookies\%s_%s.txt SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies TRUE FALSE Autofill\%s_%s.txt SELECT name, value FROM autofill CC\%s_%s.txt SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards Card number: Name on card: Expiration date: History\%s_%s.txt SELECT url FROM urls Downloads\%s_%s.txt SELECT target_path, tab_url from downloads Login Data Cookies Web Data History SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies logins.json formSubmitURL usernameField encryptedUsername encryptedPassword guid SELECT fieldname, value FROM moz_formhistory SELECT url FROM moz_places cookies.sqlite formhistory.sqlite places.sqlite \Local State ..\profiles.ini C:\ProgramData\ Chrome \Google\Chrome\User Data ChromeBeta \Google\Chrome Beta\User Data ChromeCanary \Google\Chrome SxS\User Data Chromium \Chromium\User Data Edge_Chromium \Microsoft\Edge\User Data Kometa \Kometa\User Data Amigo \Amigo\User Data Torch \Torch\User Data Orbitum \Orbitum\User Data Comodo \Comodo\Dragon\User Data Nichrome \Nichrome\User Data Maxthon5 \Maxthon5\Users Sputnik \Sputnik\User Data EPB \Epic Privacy Browser\User Data Vivaldi \Vivaldi\User Data CocCoc \CocCoc\Browser\User Data Uran \uCozMedia\Uran\User Data QIP \QIP Surf\User Data Cent \CentBrowser\User Data Elements \Elements Browser\User Data TorBro \TorBro\Profile CryptoTab \CryptoTab Browser\User Data Brave \BraveSoftware\Brave-Browser\User Data Opera \Opera Software\Opera Stable\ OperaGX \Opera Software\Opera GX Stable\ OperaNeon \Opera Software\Opera Neon\User Data Firefox \Mozilla\Firefox\Profiles\ SlimBrowser \FlashPeak\SlimBrowser\Profiles\ PaleMoon \Moonchild Productions\Pale Moon\Profiles\ Waterfox \Waterfox\Profiles\ Cyberfox \8pecxstudios\Cyberfox\Profiles\ BlackHawk \NETGATE Technologies\BlackHawk\Profiles\ IceCat \Mozilla\icecat\Profiles\ KMeleon \K-Meleon\ Thunderbird \Thunderbird\Profiles\ passwords.txt ibnejdfjmmkpcnlpebklmnkoeoihofec TronLink nkbihfbeogaeaoehlefnkodbefgpgknn MetaMask fhbohimaelbohpjbbldcngcnapndodjp Binance Chain Wallet ffnbelfdoeiohenkjibnmadjiehjhajb Yoroi jbdaocneiiinmjbjlgalhcelgbejmnid Nifty Wallet afbcbjpbpfadlkmhmclhkeeodmamcflc Math Wallet hnfanknocfeofbddgcijnmhnfnkdnaad Coinbase Wallet hpglfhgfnhbgpjdenjgmdgoeiappafln Guarda blnieiiffboillknjnepogjhkgnoapac EQUAL Wallet cjelfplplebdjjenllpjcblmjkfcffne Jaxx Liberty fihkakfobkmkjojpchpfgcmhfjnmnfpi BitApp Wallet kncchdigobghenbbaddojjnnaogfppfj iWallet amkmjjmmflddogmhpjloimipbofnfjih Wombat nlbmnnijcnlegkjjpcfjclmcfggfefdm MEW CX nanjmdknhkinifnkgdcggcfnhdaammmj GuildWallet nkddgncdjgjfcddamfgcmfnlhccnimig Saturn Wallet fnjhmkhhmkbjkkabndcnnogagogbneec Ronin Wallet cphhlgmgameodnhkjdmkpanlelnlohao NeoLine nhnkbkgjikgcigadomkphalanndcapjk Clover Wallet kpfopkelmapcoipemfendmdcghnegimn Liquality Wallet aiifbnbfobpmeekipheeijimdpnlpgpp Terra Station dmkamcknogkgcdfhhbddcghachkejeap Keplr fhmfendgdocmcbmfikdcogofphimnkno Sollet cnmamaachppnkjgnildpdmkaakejnhae Auro Wallet jojhfeoedkpkglbfimdfabpdfjaoolaf Polymesh Wallet flpiciilemghbmfalicajoolhkkenfel ICONex nknhiehlklippafakaeklbeglecifhad Nabox Wallet hcflpincpppdclinealmandijcmnkbgn KHC ookjlbkiijinhpmnjffcofjonbfbgaoc Temple mnfifefkajgofkcjkemidiaecocnkjeh TezBox dkdedlpgdmmkkfjabffeganieamfklkm Cyano Wallet nlgbhdfgdhgbiamfdfmbikcdghidoadd Byone infeboajgfhgbjpjbeppbkgnabfdkdaf OneKey cihmoadaighcejopammfbmddcmdekcje LeafWallet lodccjjbdhfakaekdiahmedfbieldgik DAppPlay ijmpgkjfkbfhoebgogflfebnmejmfbml BitClip lkcjlnjfpbikmcmbachjpdbijejflpcm Steem Keychain onofpnbbkehpmmoabgpcpmigafmmnjhl Nash Extension bcopgchhojmggmffilplmbdicgaihlkp Hycon Lite Client klnaejjgbibmhlephnhpmaofohgkpgkd ZilPay aeachknmefphepccionboohckonoeemg Coin98 Wallet bfnaelmomeimhlpmgjnjophhpkkoljpa Phantom hifafgmccdpekplomjjkcfgodnhcellj Crypto.com dngmlblcodfobpdpecaadgfbcggfjfnm Maiar DeFi Wallet ppdadbejkmjnefldpcdjhnkpbjkikoip Oasis hpbgcgmiemanfelegbndmhieiigkackl MonstaWallet fcckkdbjnoikooededlapcalpionmalo MOBOX jccapkebeeiajkkdemacblkjhhhboiek Crust Wallet mgffkfbidihjpoaomajlbgchddlicgpn Pali Wallet nphplpgoakhhjchkkhmiggakijnkhfnd TON Wallet ldinpeekobnhjjdofggfgjlcehhmanlj Hiro Wallet pocmplpaccanhmnllbbkpgfliimjljgo Slope Wallet bhhhlbepdkbapadjdnnojkbgioiodbic Solflare Wallet pgiaagfkgcbnmiiolekcfmljdagdhlcm Stargazer Wallet cgeeodpfagjceefieflmdfphplkenlfk EVER Wallet gjkdbeaiifkpoencioahhcilildpjhgh partisia-wallet bgjogpoidejdemgoochpnkmdjpocgkha Ecto Wallet ifckdpamphokdglkkdomedpdegcjhjdp ONTO Wallet agechnindjilpccclelhlbjphbgnobpf Fractal Wallet algblmhagnobbnmakepomicmfljlbehg ADS Wallet imijjbmbnebfnbmonjeileijahaipglj Moonlet Wallet kpjdchaapjheajadlaakiiigcbhoppda ZEBEDEE dlcobpjiigpikoobohmabehhmhfoodbb Argent X StarkNet Wallet bofddndhbegljegmpmnlbhcejofmjgbn X-Wallet mapbhaebnddapnmifbbkgeedkeplgjmf Biport Wallet kfdniefadaanbjodldohaedphafoffoh Typhon Wallet jaooiolkmfcmloonphpiiogkfckgciom Twetch Wallet aijcbedoijmgnlmjeegjaglmepbmpkpi Leap Wallet fhfffofbcgbjjojdnpcfompojdjjhdim Lamden Wallet agkfnefiabmfpanochlcakggnkdfmmjd Earth Wallet lpfcbjknijpeeillifnkikgncikgfhdo Nami fecfflganphcinpahcklgahckeohalog Coin Wallet ilhaljfiglknggcoegeknjghdgampffk Beam Web Wallet dklmlehijiaepdijfnbbhncfpcoeeljf FShares Wallet fkhebcilafocjhnlcngogekljmllgdhd WAGMIswap.io Wallet laphpbhjhhgigmjoflgcchgodbbclahk BLUE - Worlds Safest and Simplest Wallet mkjjflkhdddfjhonakofipfojoepfndk Unification Web Wallet jnldfbidonfeldmalbflbmlebbipcnle Infinity Wallet ellkdbaphhldpeajbepobaecooaoafpg Fetch.ai Network Wallet iokeahhehimjnekafflcihljlcjccdbe Alby Wallet omajpeaffjgmlpmhbfdjepdejoemifpe xBull Wallet pgojdfajgcjjpjnbpfaelnpnjocakldb Sugarchain Wallet pnndplcbkakcplkjnolgbkdgjikjednm Tronium fnnegphlobjdpkhecapkijjdkgcjhkib Harmony fhilaheimglignddkjgofkcbgekhenbh Oxygen cmbagcoinhmacpcgmbiniijboejgiahi JustLiquidity Wallet kmmolakhbgdlpkjkcjkebenjheonagdm AlgoSigner fnabdmcgpkkjjegokfcnfbpneacddpfh Goldmint Lite Wallet bgpipimickeadkjlklgciifhnalhdjhe GeroWallet hoighigmnhgkkdaenafgnefkcmipfjon EO.Finance nlgnepoeokdfodgjkjiblkadkjbdfmgd Multi Wallet nhihjlnjgibefgjhobhcphmnckoogdea Waves Enterprise Wallet ehibhohmlpipbaogcknmpmiibbllplph Bluehelix Wallet magbanejlegnbcppjljfhnmfmghialkl Nebulas Wallet fgkaeeikaoeiiggggbgdcjchmdfmamla Vtimes pnlfjmlcjdjgkddecgincndfgegkecke Crocobit Wallet bhghoamapcdpbohphigoooaddinpkbai Authenticator gaedmjdfmmahhbjefcbgaolhhanlaolb Authy oeljdldpnmdbchonielidgobddffflal EOS Authenticator ilgcnhelpchnceeipipijaljkblbcobl GAuth Authenticator imloifkgjagghnncjkhggdhalmcnfklk Trezor Password Manager %s\%s\Local Extension Settings\%s %s\CURRENT %s\%s\Sync Extension Settings\%s %s\%s\IndexedDB\chrome-extension_%s_0.indexeddb.leveldb Plugins\ HARDWARE\DESCRIPTION\System\CentralProcessor\0 ProcessorNameString SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName x64 x86 DISPLAY SOFTWARE\Microsoft\Cryptography MachineGuid SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall DisplayName DisplayVersion screenshot.jpg ABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890 /c timeout /t 5 & del /f /q "%s" & exit C:\Windows\System32\cmd.exe | |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Temp\Mars Stealer 8 cracked.exe" | C:\Users\admin\AppData\Local\Temp\Mars Stealer 8 cracked.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\Desktop\MarsStealer_Menu.exe" | C:\Users\admin\Desktop\MarsStealer_Menu.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3792 | "C:\Users\admin\Desktop\crack.exe" | C:\Users\admin\Desktop\crack.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Get Cliboard Address Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4056 | "C:\Users\admin\Desktop\MarsStealer_Menu.exe" | C:\Users\admin\Desktop\MarsStealer_Menu.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 791
Read events
1 759
Write events
32
Delete events
0
Modification events
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (2992) Mars Stealer 8 cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
Executable files
6
Suspicious files
2
Text files
339
Unknown types
4
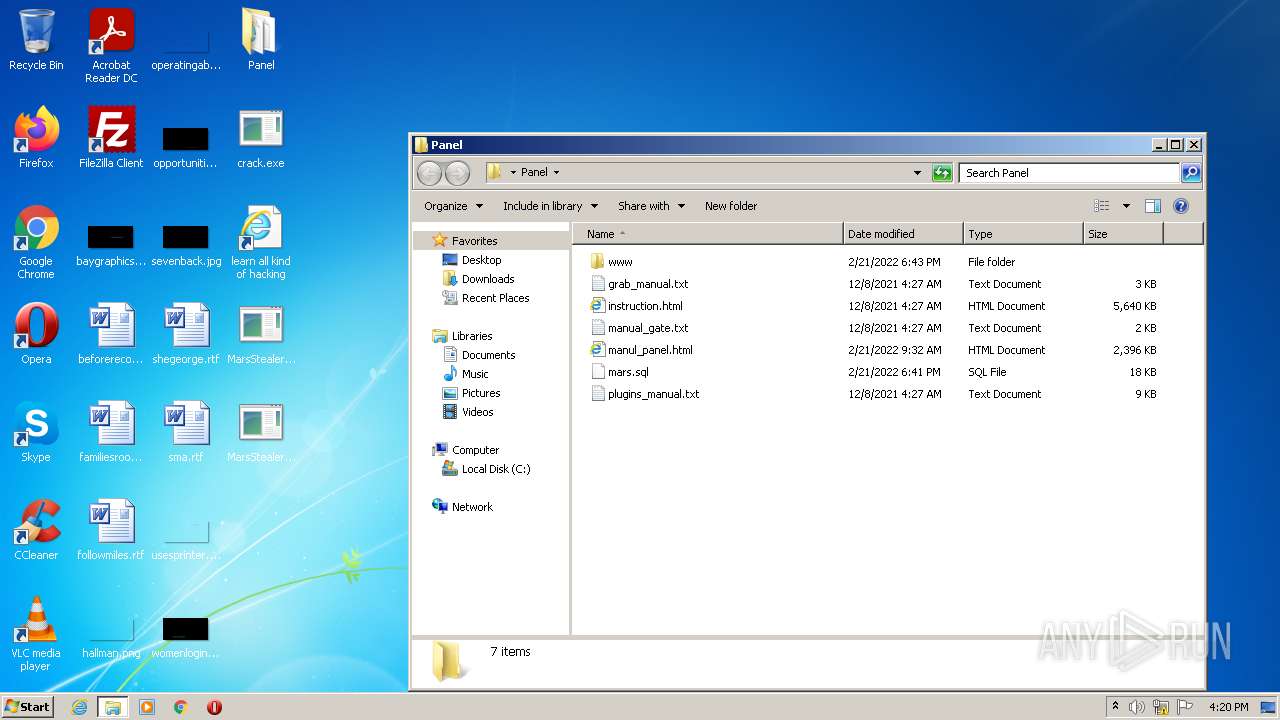
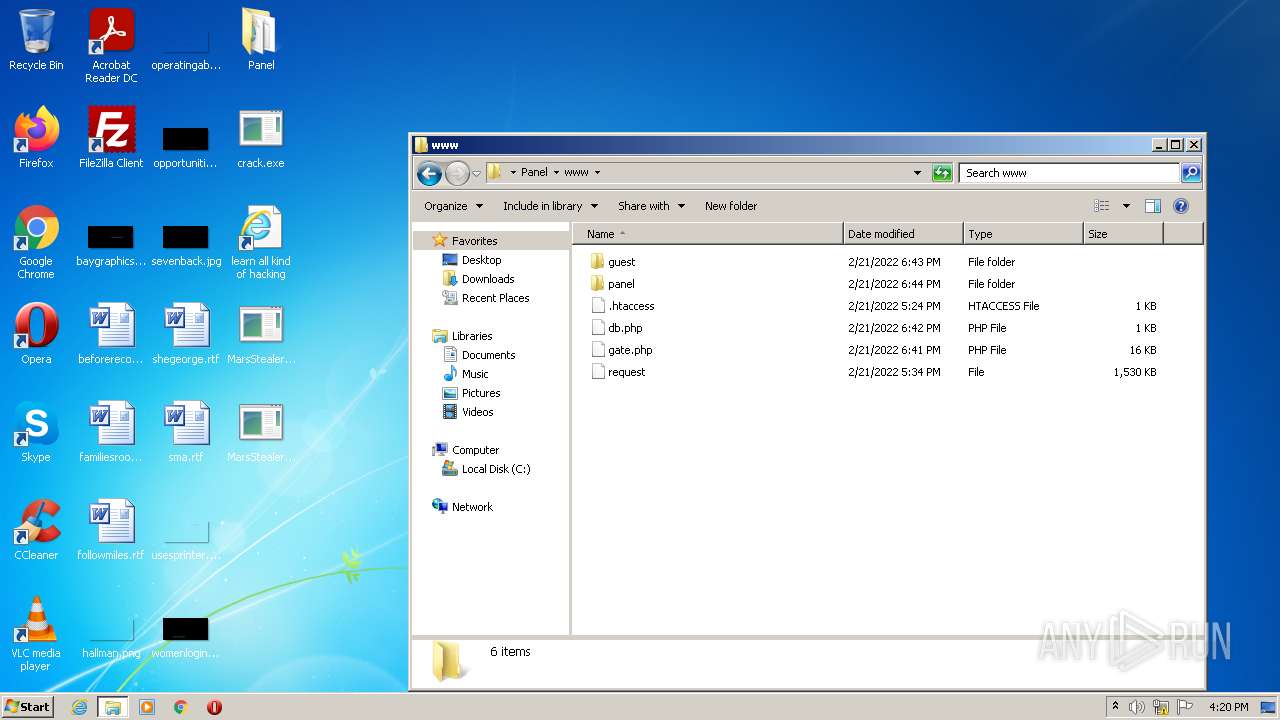
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\instruction.html | — | |
MD5:— | SHA256:— | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\plugins_manual.txt | text | |
MD5:FDC3D90112A72CAEB83C0AA9B38E89BD | SHA256:D8ADF295702FB08EB32020DE7B156B3DCD2C49992AB18D4776556A6566256781 | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\grab_manual.txt | text | |
MD5:9CFDD86059CAFBA662B5C8AB902D28F4 | SHA256:6AD2E1DB91903F669DC85461970D45370E2F00515EEE1A9101576A7E95B505CD | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\www\panel\assets\css\jquery-ui.min.html | html | |
MD5:3D94C5DB6219640112A01C9F126E894F | SHA256:D36921D85F158A051DAED4DD44CA81FC98A4B707C71F0B587A3E8DF8D683F5A2 | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\www\guest\assets\css\app.min.css | text | |
MD5:44FF01B96F88ED1E70BC44CBD096BFCD | SHA256:DDB09D35F279DD9FE20AD8569D6BF306C71B1DBC453964968720B90DEDFC5276 | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\www\panel\assets\css\app.min.css | text | |
MD5:44FF01B96F88ED1E70BC44CBD096BFCD | SHA256:DDB09D35F279DD9FE20AD8569D6BF306C71B1DBC453964968720B90DEDFC5276 | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\www\panel\assets\css\metisMenu.min.css | text | |
MD5:8577B369F2381960D8AC2FE7F31E54F6 | SHA256:099AC56E52F547F59624894DD9416AFBCD13BA299BD439F649F597BEE2B7A9C6 | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\www\panel\assets\css\bootstrap.min.css | text | |
MD5:9A073152F0D7006C650C9633E06181F8 | SHA256:9FAF0345BF0785854343B9303734C2F4D3ADBA818CB408DCC6E2384CCC8A7AA2 | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\www\guest\assets\js\apexcharts.min.js | text | |
MD5:AE50ED75DBD16A56AB772663CD3BCF9C | SHA256:95483691E4771B81A36C0D4DCA22A429041B96F099C88CF20619D32CF0B50C3F | |||
| 2992 | Mars Stealer 8 cracked.exe | C:\Users\admin\Desktop\Panel\manul_panel.html | html | |
MD5:4DA0595D97FFFABEA58FFDB6CC493353 | SHA256:D6D3B257E3E35D9088A4051F612605C4459BE0E7D5C27E687B82275331082FCF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report