| File name: | PO-990101-0703.doc |
| Full analysis: | https://app.any.run/tasks/ed6d8330-af0d-4625-8e1a-d2f357338ef7 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
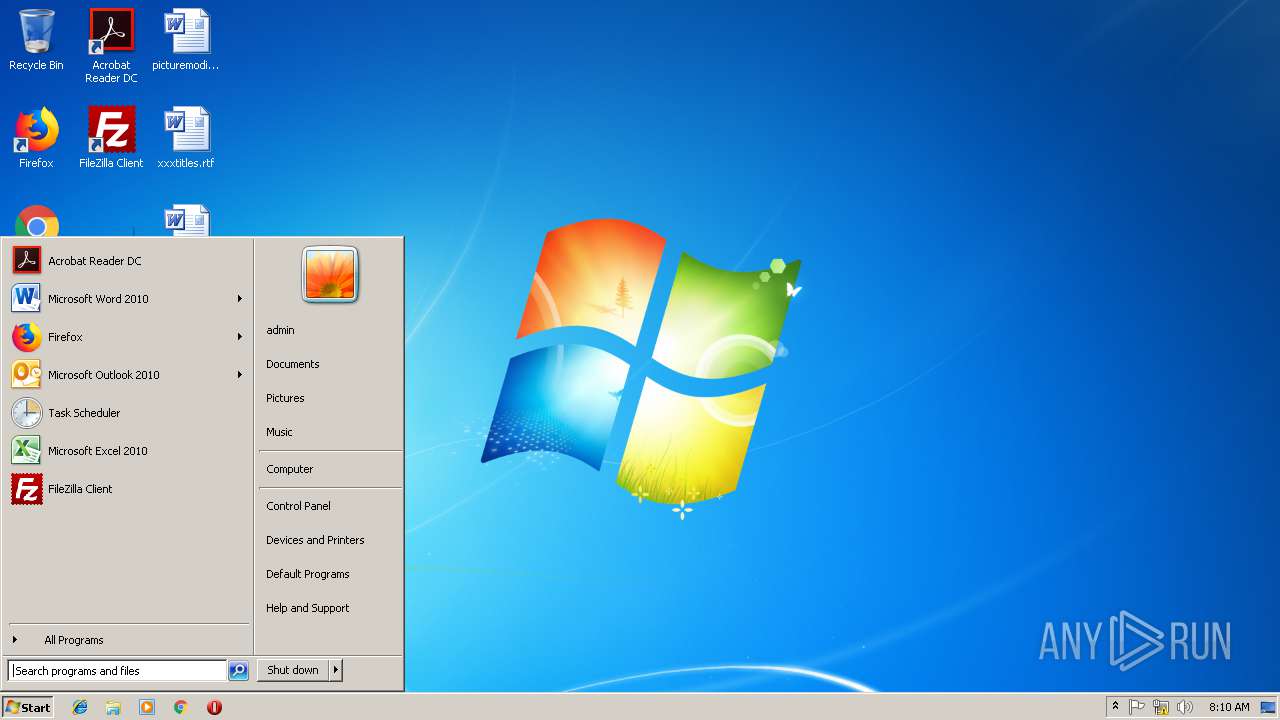
| Analysis date: | March 14, 2019, 08:08:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: PC, Template: Normal.dotm, Last Saved By: PC, Revision Number: 4, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Mar 13 22:55:00 2019, Last Saved Time/Date: Wed Mar 13 22:55:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | E3B75B5421C383D26B3DAA28D550AEEF |
| SHA1: | 249FC53405AA94F66B71CD29855A9A70FF47F9EA |
| SHA256: | 4EB0D63BDEAE06A5DE41E0E858316FE9A67D6305D003A6745DDEAC0E493B1929 |
| SSDEEP: | 1536:UYxSupfQcHOhWy9z40mamePd6ZpA+6LOA9iMPfaqx:UASupzukCz40rd6Zmt9iMPC |
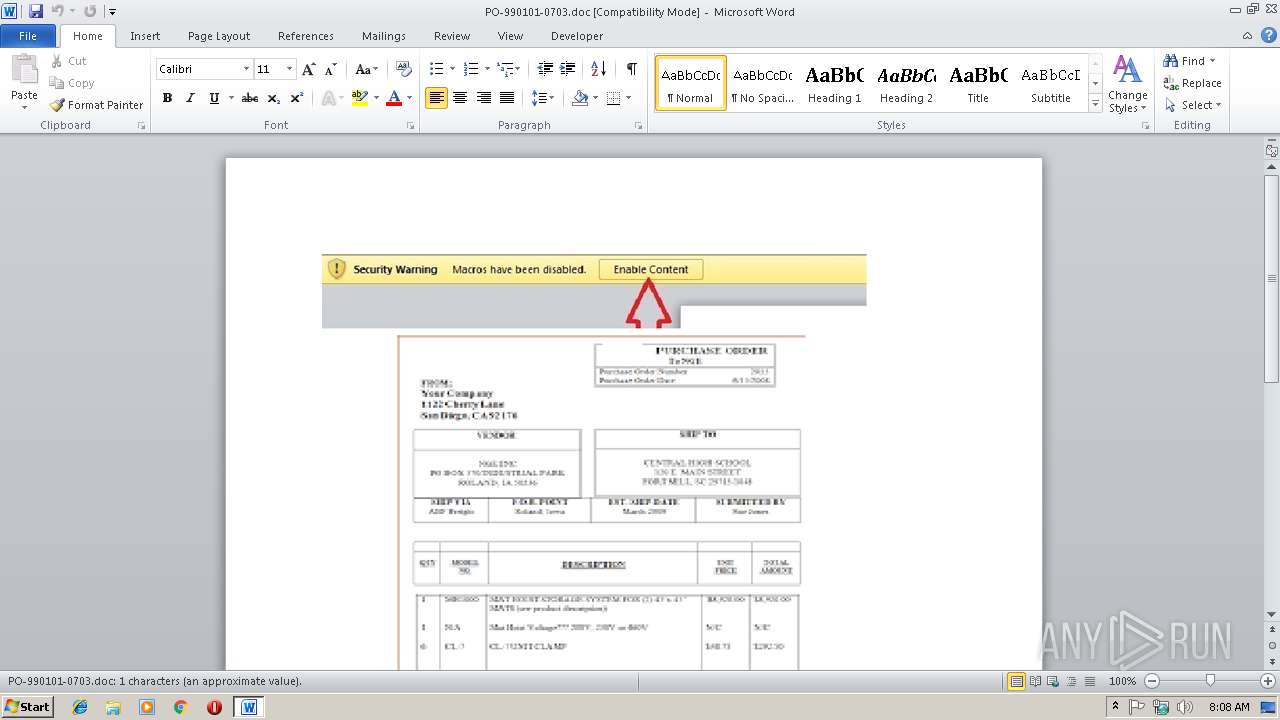
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2864)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2864)
Application was dropped or rewritten from another process
- 0956877.exe (PID: 3560)
- 0956877.exe (PID: 3296)
- b6qbld.exe (PID: 1688)
- b6qbld.exe (PID: 4048)
Downloads executable files from the Internet
- powershell.exe (PID: 3416)
Changes the autorun value in the registry
- 0956877.exe (PID: 3560)
- b6qbld.exe (PID: 1688)
- cmd.exe (PID: 3732)
Runs app for hidden code execution
- explorer.exe (PID: 116)
FORMBOOK was detected
- explorer.exe (PID: 116)
Formbook was detected
- cmd.exe (PID: 3732)
- Firefox.exe (PID: 1704)
Connects to CnC server
- explorer.exe (PID: 116)
Actions looks like stealing of personal data
- cmd.exe (PID: 3732)
Stealing of credential data
- cmd.exe (PID: 3732)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 116)
- powershell.exe (PID: 3416)
- cmd.exe (PID: 3732)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
Executable content was dropped or overwritten
- powershell.exe (PID: 3416)
- 0956877.exe (PID: 3560)
- b6qbld.exe (PID: 1688)
- DllHost.exe (PID: 2392)
- explorer.exe (PID: 116)
Application launched itself
- 0956877.exe (PID: 3560)
- cmd.exe (PID: 3732)
- b6qbld.exe (PID: 1688)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 116)
- cmd.exe (PID: 3732)
Creates files in the program directory
- DllHost.exe (PID: 2392)
Loads DLL from Mozilla Firefox
- cmd.exe (PID: 3732)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2864)
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Creates files in the user directory
- WINWORD.EXE (PID: 2864)
- Firefox.exe (PID: 1704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | PC |
| RevisionNumber: | 4 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:03:13 22:55:00 |
| ModifyDate: | 2019:03:13 22:55:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
46
Monitored processes
12
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\K8pmxrtbp\b6qbld.exe" | C:\Program Files\K8pmxrtbp\b6qbld.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | cmd.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2156 | /c del "C:\Users\admin\AppData\Roaming\0956877.exe" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2392 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | "C:\Windows\System32\cmstp.exe" | C:\Windows\System32\cmstp.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 0 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\PO-990101-0703.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3296 | "C:\Users\admin\AppData\Roaming\0956877.exe" | C:\Users\admin\AppData\Roaming\0956877.exe | — | 0956877.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3416 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -ExecutionPolicy Bypass C:\Users\admin\AppData\Roaming\dxfChFC.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3560 | "C:\Users\admin\AppData\Roaming\0956877.exe" | C:\Users\admin\AppData\Roaming\0956877.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 293
Read events
3 846
Write events
432
Delete events
15
Modification events
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7;$ |
Value: 373B2400300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {97E467B4-98C6-4F19-9588-161B7773D6F6} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 0100000000000000AE5A861E3DDAD401 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831838 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831952 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831953 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 300B0000343CC51D3DDAD40100000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 5>$ |
Value: 353E2400300B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2864) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 5>$ |
Value: 353E2400300B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
5
Suspicious files
75
Text files
4
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8737.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3416 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CNMJAUL7XT8WSWH3VZN5.temp | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF0777FFBBFCD89794.TMP | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{0838EBC3-5685-4072-B773-B9657C2A57CB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{11726436-D478-4C30-A3D8-3ACEA91D099F}.tmp | — | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019031420190315\index.dat | dat | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\PO-990101-0703.doc.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2864 | WINWORD.EXE | C:\Users\admin\Desktop\~$-990101-0703.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
22
DNS requests
10
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | explorer.exe | GET | — | 107.180.12.36:80 | http://www.fumigacionesgrupomarroking.com/br/?8p=Gw8YIfbuZIAWdO6zSaqnbSyjTOQEkziATnx49FNtLJK8GtoM25npbaAX1u2PmizkisIA5g==&o2=iLj8LXix&sql=1 | US | — | — | malicious |
3416 | powershell.exe | GET | 200 | 107.180.27.166:80 | http://mincoindia.com/wp-admin/AI/0956877.exe | US | executable | 1.05 Mb | malicious |
116 | explorer.exe | POST | — | 107.180.12.36:80 | http://www.fumigacionesgrupomarroking.com/br/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 107.180.12.36:80 | http://www.fumigacionesgrupomarroking.com/br/ | US | — | — | malicious |
116 | explorer.exe | GET | 301 | 85.13.147.154:80 | http://www.schulhaus-hotel.com/br/?8p=zL2RefN61iOY/8W4kVfHqdT9HVuHnwg/LBYM68C9CdtlHfMecvOpgBAuR4REB3lbuK5aiA==&o2=iLj8LXix&sql=1 | DE | html | 343 b | malicious |
116 | explorer.exe | GET | 200 | 74.220.199.6:80 | http://www.bigsavings2day.com/br/?8p=sHGnyDvH+3+NfxRA9o4tV2tmc5uhhLzTgSd4jExe9n2m1YQzVMadvLjtxOs99fSuI4EwZA==&o2=iLj8LXix | US | html | 4.71 Kb | malicious |
116 | explorer.exe | POST | — | 107.180.12.36:80 | http://www.fumigacionesgrupomarroking.com/br/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 85.13.147.154:80 | http://www.schulhaus-hotel.com/br/ | DE | — | — | malicious |
116 | explorer.exe | GET | 302 | 23.20.239.12:80 | http://www.please-click.com/br/?8p=lODd2yOHwPMHKmdm4lbcmyo24Chj4nAJmAS9oR/QxW9lTHye55OayHDh/+cUrNEv7cQAsg==&o2=iLj8LXix | US | html | 188 b | shared |
116 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.please-click.com/br/ | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | powershell.exe | 107.180.27.166:80 | mincoindia.com | GoDaddy.com, LLC | US | malicious |
116 | explorer.exe | 74.220.199.6:80 | www.bigsavings2day.com | Unified Layer | US | malicious |
116 | explorer.exe | 192.64.116.17:80 | www.vaxosyk.com | Namecheap, Inc. | US | malicious |
116 | explorer.exe | 107.180.12.36:80 | www.fumigacionesgrupomarroking.com | GoDaddy.com, LLC | US | malicious |
116 | explorer.exe | 85.13.147.154:80 | www.schulhaus-hotel.com | Neue Medien Muennich GmbH | DE | malicious |
116 | explorer.exe | 154.220.176.82:80 | www.mobetier.com | MULTACOM CORPORATION | US | malicious |
116 | explorer.exe | 23.20.239.12:80 | www.please-click.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mincoindia.com |
| malicious |
www.bigsavings2day.com |
| malicious |
www.luba63631.com |
| unknown |
www.fumigacionesgrupomarroking.com |
| malicious |
www.schulhaus-hotel.com |
| malicious |
www.nj-aisino.com |
| unknown |
www.vaxosyk.com |
| malicious |
www.mobetier.com |
| malicious |
www.please-click.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3416 | powershell.exe | A Network Trojan was detected | ET TROJAN EXE Download Request To Wordpress Folder Likely Malicious |
3416 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3416 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
15 ETPRO signatures available at the full report