| File name: | _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe |
| Full analysis: | https://app.any.run/tasks/33714388-5e59-4242-a448-3c8ab0325ac6 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 22, 2025, 12:34:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 1CE9392BB065C76CC0A04EF6B369F1C2 |
| SHA1: | E5099DC55CE40465A2603A1D0507B8D82F02FEF3 |
| SHA256: | 4E98E9C1660FC47D62D53D06279B856ADFFF9A37CA1970B84F07075CEE66ED3E |
| SSDEEP: | 49152:WP3tZ7YIPJ2aLp7RY9L3l+kM1Tgd/kLTAzKY/YQ7cgQy+cunC/fklyLmUXfqKmA7:WP1Aad7gITgdsw+Y/GxyznHklyTXfqK7 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 8040)
Create files in the Startup directory
- Graphs.scr (PID: 7952)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2276)
RHADAMANTHYS has been detected (YARA)
- OpenWith.exe (PID: 5884)
- OpenWith.exe (PID: 6204)
SUSPICIOUS
Get information on the list of running processes
- cmd.exe (PID: 7440)
Starts CMD.EXE for commands execution
- _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe (PID: 7396)
Executing commands from a ".bat" file
- _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe (PID: 7396)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7440)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7440)
The executable file from the user directory is run by the CMD process
- Graphs.scr (PID: 7952)
Starts application with an unusual extension
- cmd.exe (PID: 7440)
Executable content was dropped or overwritten
- Graphs.scr (PID: 7952)
There is functionality for taking screenshot (YARA)
- Graphs.scr (PID: 7952)
Executes application which crashes
- Graphs.scr (PID: 6756)
- Graphs.scr (PID: 5576)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 5884)
- OpenWith.exe (PID: 6204)
Connects to unusual port
- OpenWith.exe (PID: 6204)
- OpenWith.exe (PID: 5884)
INFO
Checks supported languages
- _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe (PID: 7396)
- extrac32.exe (PID: 7844)
- Graphs.scr (PID: 7952)
- Graphs.scr (PID: 6756)
- Graphs.scr (PID: 5576)
Create files in a temporary directory
- _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe (PID: 7396)
- extrac32.exe (PID: 7844)
Reads the computer name
- extrac32.exe (PID: 7844)
- Graphs.scr (PID: 7952)
Reads mouse settings
- Graphs.scr (PID: 7952)
Launching a file from Task Scheduler
- cmd.exe (PID: 8040)
Manual execution by a user
- cmd.exe (PID: 8040)
- OpenWith.exe (PID: 5884)
- Graphs.scr (PID: 6756)
- Graphs.scr (PID: 5576)
- OpenWith.exe (PID: 6204)
The sample compiled with english language support
- Graphs.scr (PID: 7952)
Creates files or folders in the user directory
- Graphs.scr (PID: 7952)
Launching a file from the Startup directory
- Graphs.scr (PID: 7952)
Checks proxy server information
- slui.exe (PID: 2628)
Reads the software policy settings
- slui.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Rhadamanthys
(PID) Process(5884) OpenWith.exe
C2 (2)https://178.16.53.236:6343/gateway/vz2az6v1.hi4j2
https://the-encyclopedia-of-digital-entrepreneurship-and-innovation.com:6343/gateway/vz2az6v1.hi4j2
(PID) Process(6204) OpenWith.exe
C2 (2)https://178.16.53.236:6343/gateway/vz2az6v1.hi4j2
https://the-encyclopedia-of-digital-entrepreneurship-and-innovation.com:6343/gateway/vz2az6v1.hi4j2
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2059:08:08 23:27:35+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 26624 |
| InitializedDataSize: | 1655296 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6d50 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
154
Monitored processes
20
Malicious processes
4
Suspicious processes
2
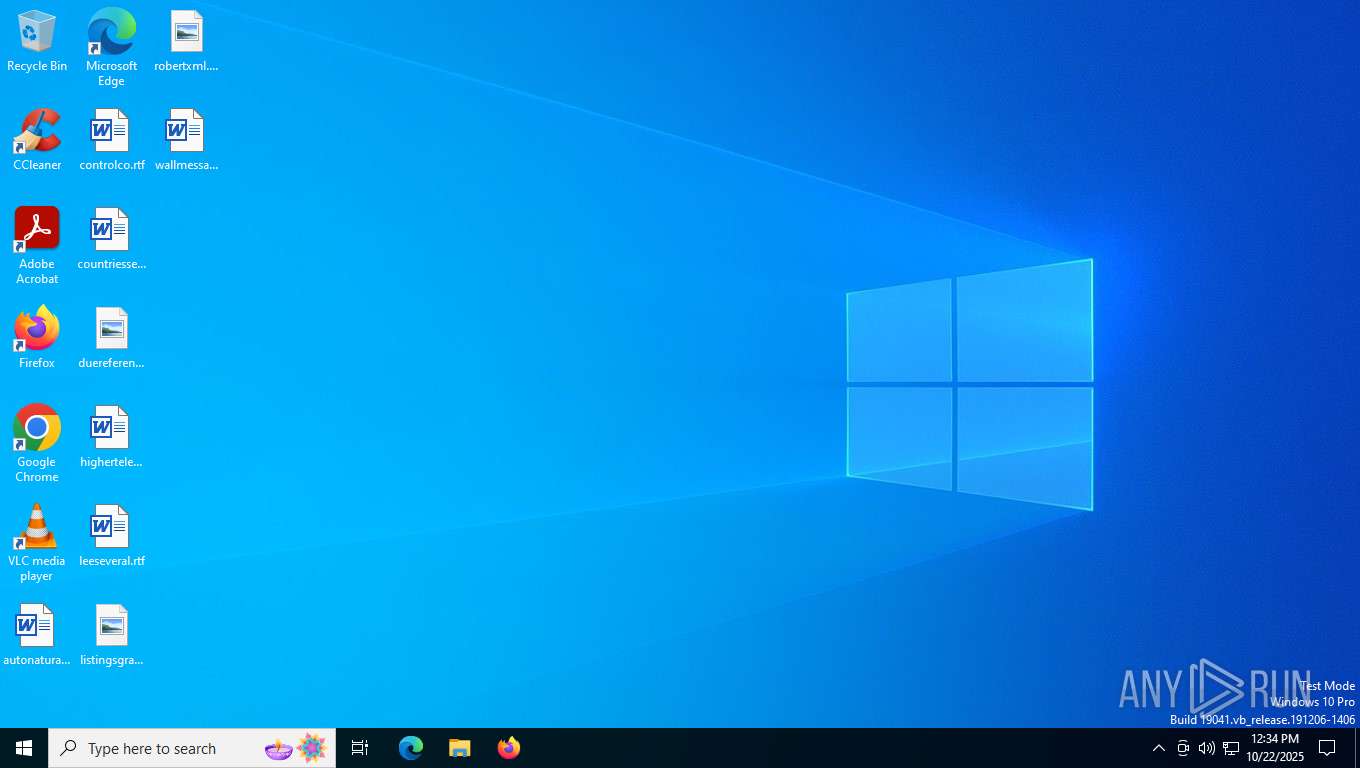
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2628 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3996 | C:\WINDOWS\system32\WerFault.exe -u -p 5576 -s 488 | C:\Windows\System32\WerFault.exe | — | Graphs.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4140 | C:\WINDOWS\system32\WerFault.exe -u -p 6756 -s 528 | C:\Windows\System32\WerFault.exe | — | Graphs.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\240288\Graphs.scr | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\240288\Graphs.scr | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 3221225477 Version: 3, 3, 17, 0 Modules
| |||||||||||||||
| 5884 | "C:\WINDOWS\system32\openwith.exe" | C:\Windows\System32\OpenWith.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Rhadamanthys(PID) Process(5884) OpenWith.exe C2 (2)https://178.16.53.236:6343/gateway/vz2az6v1.hi4j2 https://the-encyclopedia-of-digital-entrepreneurship-and-innovation.com:6343/gateway/vz2az6v1.hi4j2 | |||||||||||||||
| 6204 | "C:\WINDOWS\system32\openwith.exe" | C:\Windows\System32\OpenWith.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Rhadamanthys(PID) Process(6204) OpenWith.exe C2 (2)https://178.16.53.236:6343/gateway/vz2az6v1.hi4j2 https://the-encyclopedia-of-digital-entrepreneurship-and-innovation.com:6343/gateway/vz2az6v1.hi4j2 | |||||||||||||||
| 6756 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\240288\Graphs.scr | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\240288\Graphs.scr | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 3221225477 Version: 3, 3, 17, 0 Modules
| |||||||||||||||
| 7396 | "C:\Users\admin\Desktop\_4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe" | C:\Users\admin\Desktop\_4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7416 | TapiUnattend.exe | C:\Windows\SysWOW64\TapiUnattend.exe | — | _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Windows(TM) Telephony Unattend Action Exit code: 2147942405 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 716
Read events
5 716
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
24
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7396 | _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Edt.pdf | binary | |
MD5:FBDEADAD07114BB1C46543075E5DBFE3 | SHA256:F1F5BCCDC9E359B95C179109F77A85B814380058CA2BC15D29C8FBA505611421 | |||
| 7396 | _4e98e9c1660fc47d62d53d06279b856adfff9a37ca1970b84f07075cee66ed3e.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Josh.pdf | binary | |
MD5:24AFA7B42BD725CC408E14C1D2EEEABF | SHA256:54605046676E679E2D5ECE583337B83DB5CB775DFD8A74E9C754D41FA4C4969D | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Pubs | binary | |
MD5:7DCCF2EF684CC11C086D04C6B30CE648 | SHA256:D3B222F8DE4F0CDF78553FDE52155AEF598E324D1C440900692E4358FA02BB53 | |||
| 7440 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Offers.pdf.bat | text | |
MD5:6AAB6996230E3D198998535B76621BBE | SHA256:4B9188834293842C8FF4935D715F9FA75A68D7EEFFE25DED65A079CFA98F174A | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Teachers | binary | |
MD5:E48188EE2F123025CD27584D903C46C9 | SHA256:E15E07514AE9F090D89B3CE2CE8CE46BF01F55A1E63F7A8C5D44405407F276A0 | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Patients | binary | |
MD5:66AABDF106299C46F7598D5346C15929 | SHA256:2D659596293E7ADDDBD4F99B7124EA0C5F1BCEB664A469037D63F595FCE6DD74 | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Annie | binary | |
MD5:AB33C04A6C5B9EE608337B9CA8A5AF9C | SHA256:E95DDEFCB91DF8CE5825EFD488E0775F6ED02B63DE0FDBF04BB3967796222EE9 | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Stockings | binary | |
MD5:4BAC8FC25C7F43FA147E0F3FB9062D54 | SHA256:89AB1943AB8A1A5173E68B455C15D82D21A60548A1DE3279719E47FED8F7B921 | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Elevation | binary | |
MD5:D11F4F75D8AFE79FF56B2A7720321092 | SHA256:7B34BF85453480815B52A475672416E3595B806CE0251374D49593A941F46942 | |||
| 7844 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Mounts | binary | |
MD5:CDB6B6B3CB96CFD3EAE36B6C7577CB80 | SHA256:3CAF2D9CEC76E176122CBB5AF7DBCB216C7B40CBEB873B978E0209FF28F4C328 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
32
DNS requests
9
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 4.154.209.85:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
— | — | POST | 500 | 4.154.185.43:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5812 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3956 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5812 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5524 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5884 | OpenWith.exe | 104.16.248.249:443 | cloudflare-dns.com | CLOUDFLARENET | — | whitelisted |
5884 | OpenWith.exe | 172.67.162.252:6343 | the-encyclopedia-of-digital-entrepreneurship-and-innovation.com | CLOUDFLARENET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
yyPTUXdYDHhpEHhPSFRJC.yyPTUXdYDHhpEHhPSFRJC |
| unknown |
cloudflare-dns.com |
| whitelisted |
the-encyclopedia-of-digital-entrepreneurship-and-innovation.com |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Lumma DNS Activity observed |
— | — | Generic Protocol Command Decode | SURICATA HTTP Host header invalid |
— | — | Generic Protocol Command Decode | SURICATA HTTP Host header invalid |