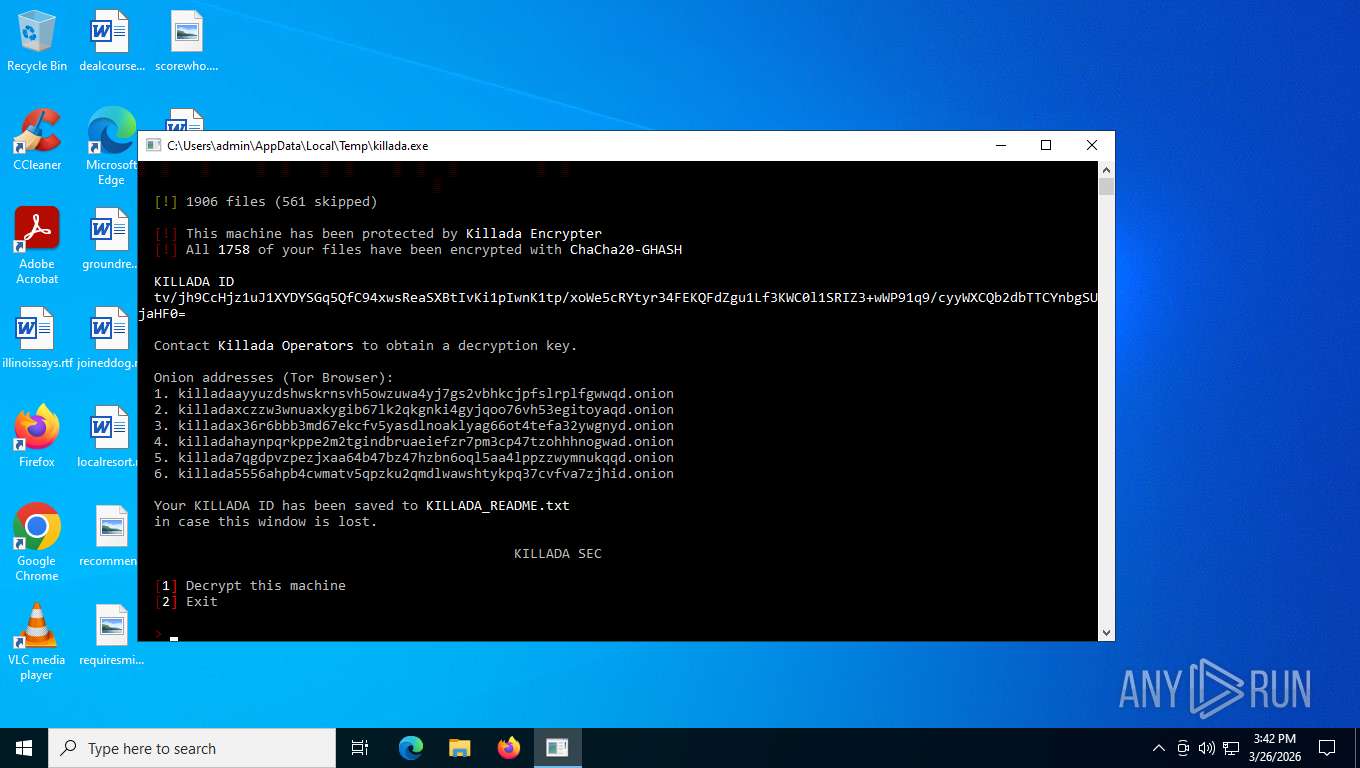
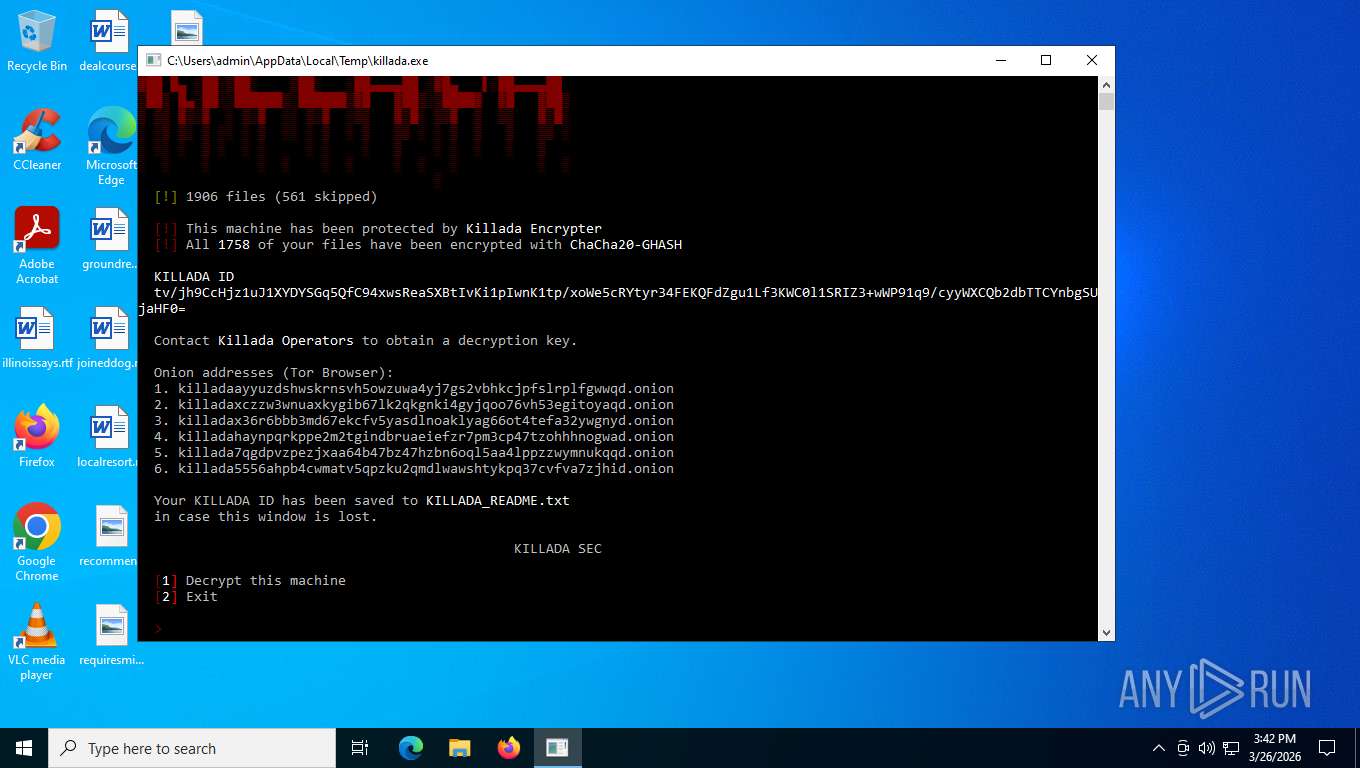
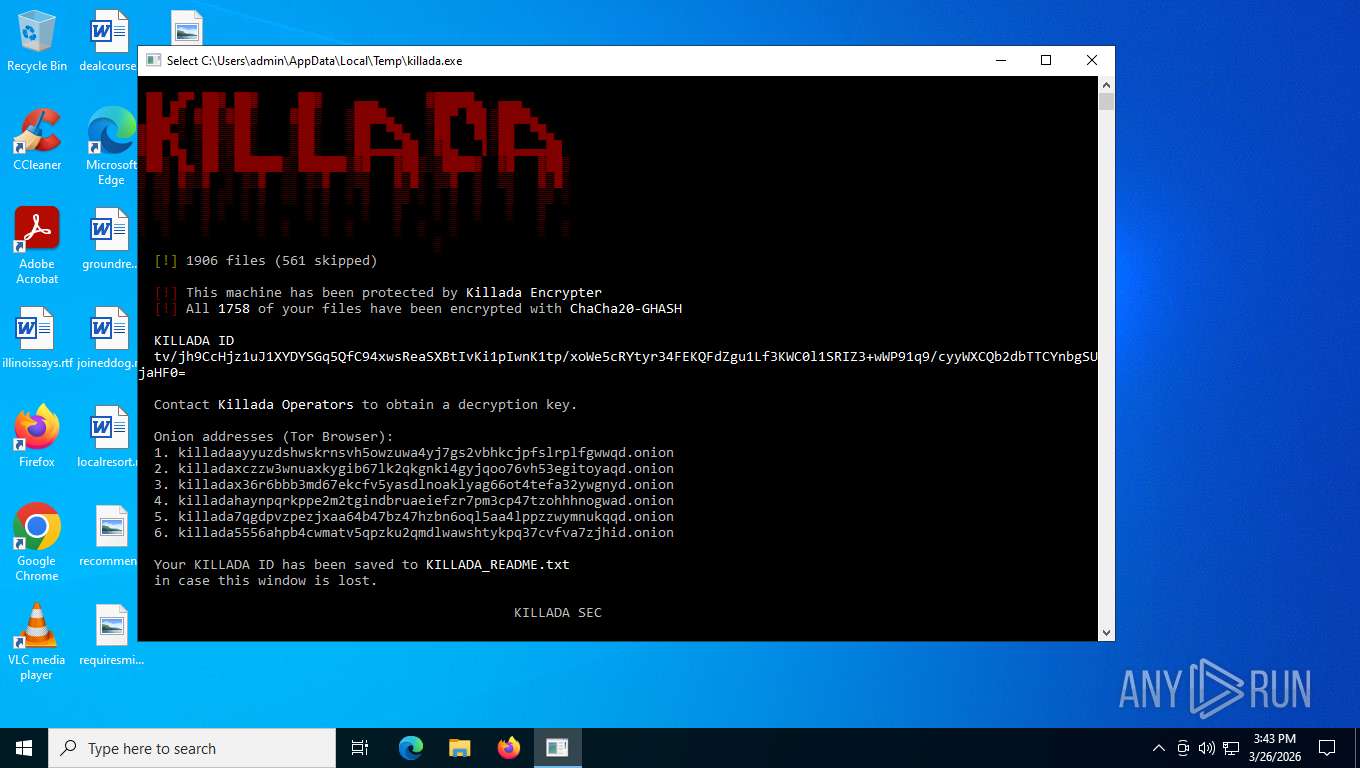
| File name: | killada.exe |
| Full analysis: | https://app.any.run/tasks/9eb1d0d2-afe4-4fc4-b633-c4bf1260278d |
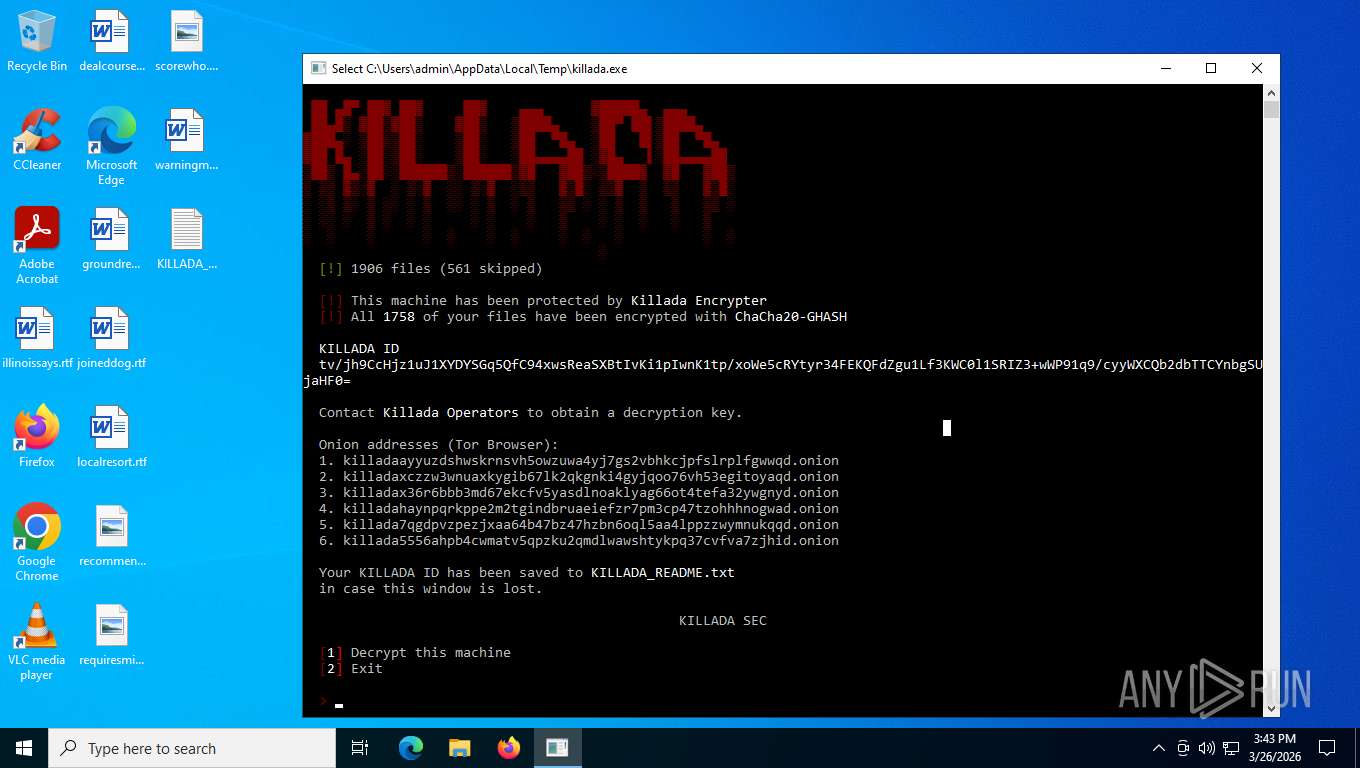
| Verdict: | Malicious activity |
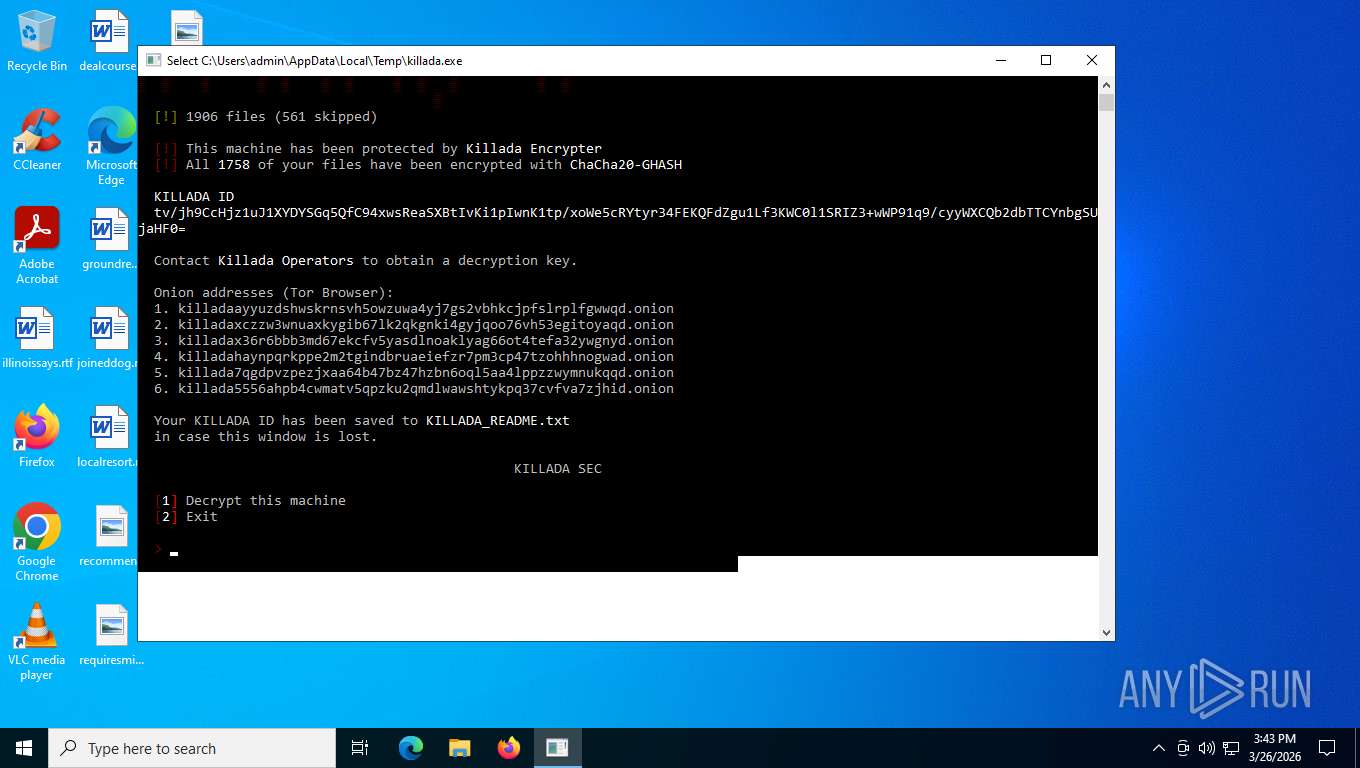
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | March 26, 2026, 19:40:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | F1FAA9F63C3FC5B73DEFE6A6CFEE09B4 |
| SHA1: | B3F5417D80F238683C72C2395D0F8AFC9795E368 |
| SHA256: | 4E080F3CAC62C55D80827DAAD538F67E7DE813ABC67E6620384B1AA4BE12E1F4 |
| SSDEEP: | 12288:u6wsT1PAjhCwKBICdRrgPSukotJMRMdrV+ZjfhstxRmCW:u6p1PAc5RrsdgNhstxRmCW |
MALICIOUS
Modifies files in the Chrome extension folder
- killada.exe (PID: 2876)
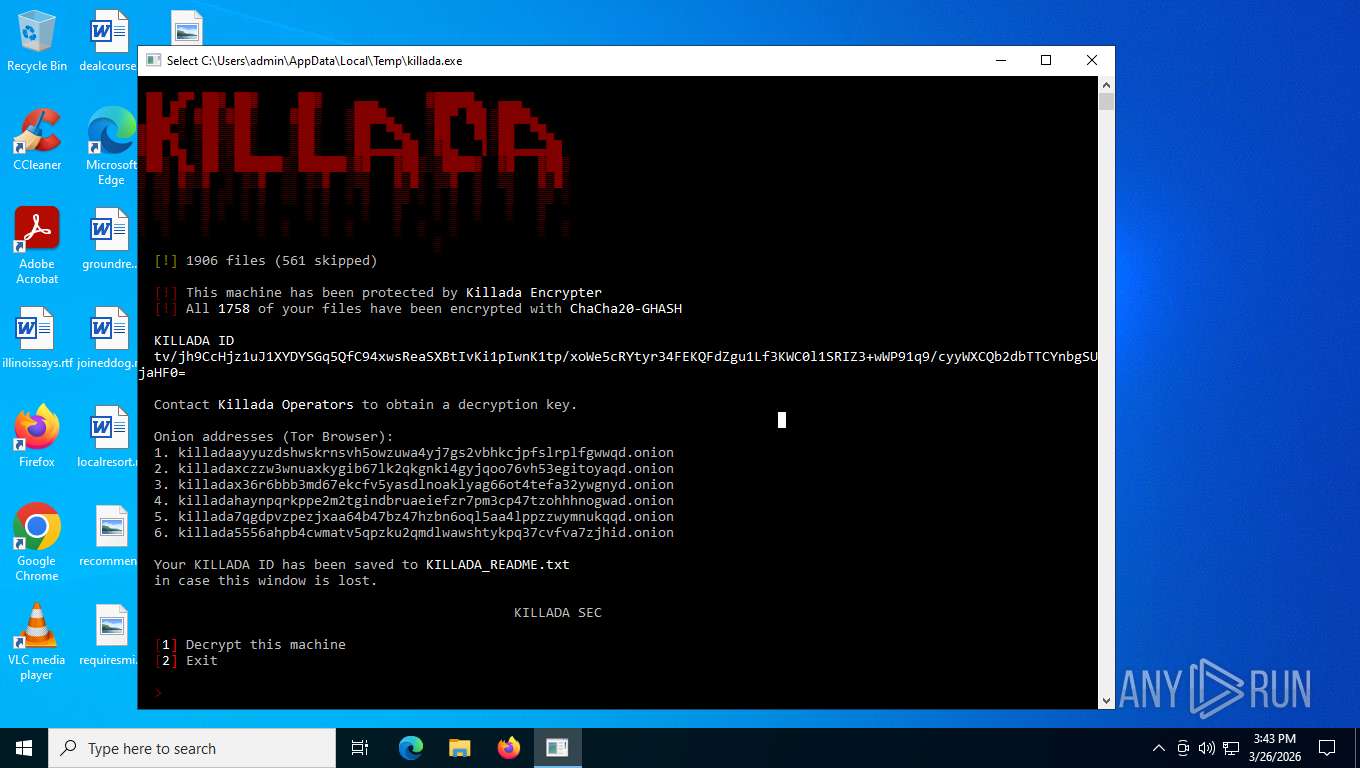
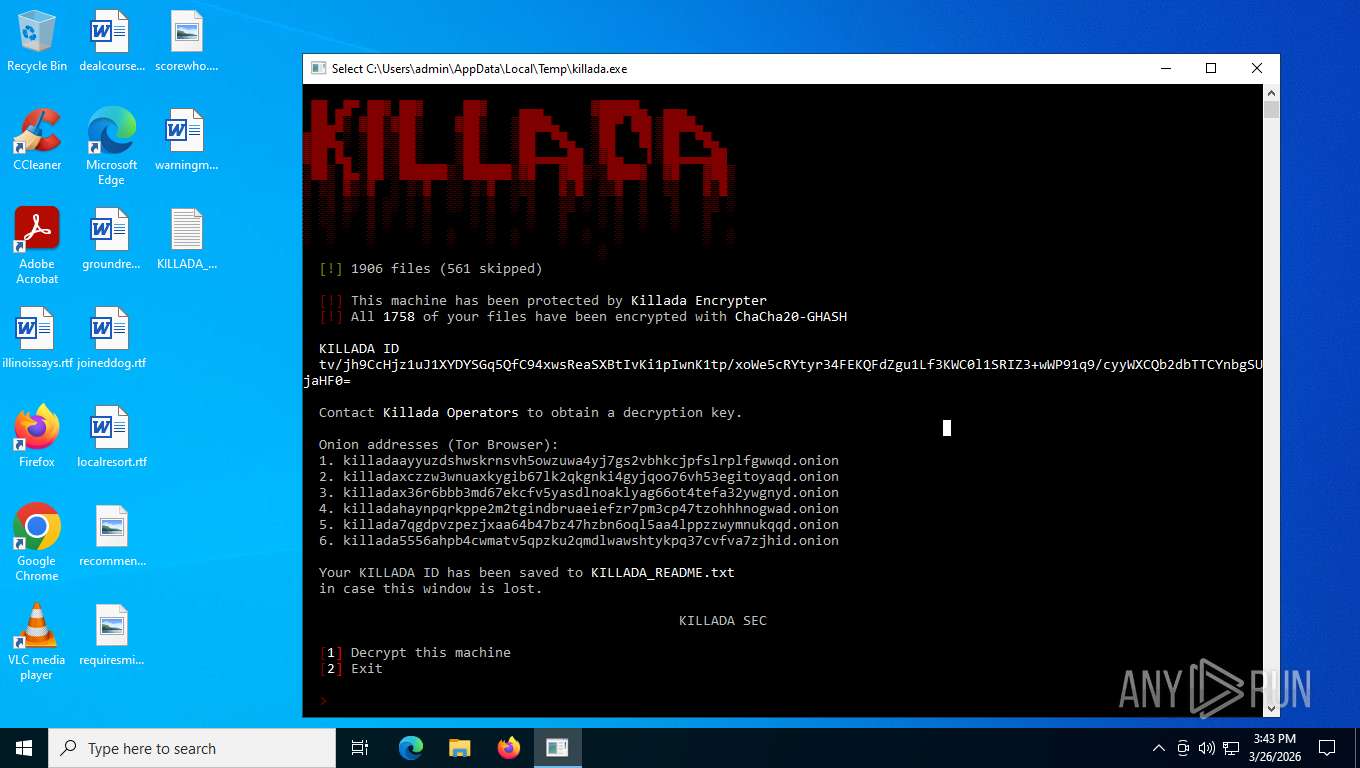
RANSOMWARE has been detected
- killada.exe (PID: 2876)
SUSPICIOUS
Creates file in the systems drive root
- killada.exe (PID: 2876)
Reads the date of Windows installation
- SearchApp.exe (PID: 5228)
INFO
Reads the computer name
- killada.exe (PID: 2876)
- SearchApp.exe (PID: 5228)
Checks supported languages
- killada.exe (PID: 2876)
- SearchApp.exe (PID: 5228)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5228)
Reads Environment values
- SearchApp.exe (PID: 5228)
Creates files or folders in the user directory
- killada.exe (PID: 2876)
Application based on Rust
- killada.exe (PID: 2876)
Create files in a temporary directory
- killada.exe (PID: 2876)
Manual execution by a user
- notepad.exe (PID: 8028)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (82) |
|---|---|---|
| .exe | | | Clipper DOS Executable (5.9) |
| .exe | | | Generic Win/DOS Executable (5.9) |
| .exe | | | DOS Executable Generic (5.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | - |
| CodeSize: | 352256 |
| InitializedDataSize: | 200704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4807c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
134
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | killada.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2876 | "C:\Users\admin\AppData\Local\Temp\killada.exe" | C:\Users\admin\AppData\Local\Temp\killada.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5228 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8028 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\KILLADA_README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 977
Read events
5 782
Write events
194
Delete events
1
Modification events
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\German\Attributes |
| Operation: | write | Name: | Language |
Value: 407 | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Japanese |
| Operation: | write | Name: | CLSID |
Value: {C6FABB24-E332-46FB-BC91-FF331B2D51F0} | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Japanese |
| Operation: | write | Name: | PhoneMap |
Value: 309C 309C 30A1 30A1 30A2 30A2 30A3 30A3 30A4 30A4 30A5 30A5 30A6 30A6 30A7 30A7 30A8 30A8 30A9 30A9 30AA 30AA 30AB 30AB 30AC 30AC 30AD 30AD 30AE 30AE 30AF 30AF 30B0 30B0 30B1 30B1 30B2 30B2 30B3 30B3 30B4 30B4 30B5 30B5 30B6 30B6 30B7 30B7 30B8 30B8 30B9 30B9 30BA 30BA 30BB 30BB 30BC 30BC 30BD 30BD 30BE 30BE 30BF 30BF 30C0 30C0 30C1 30C1 30C2 30C2 30C3 30C3 30C4 30C4 30C5 30C5 30C6 30C6 30C7 30C7 30C8 30C8 30C9 30C9 30CA 30CA 30CB 30CB 30CC 30CC 30CD 30CD 30CE 30CE 30CF 30CF 30D0 30D0 30D1 30D1 30D2 30D2 30D3 30D3 30D4 30D4 30D5 30D5 30D6 30D6 30D7 30D7 30D8 30D8 30D9 30D9 30DA 30DA 30DB 30DB 30DC 30DC 30DD 30DD 30DE 30DE 30DF 30DF 30E0 30E0 30E1 30E1 30E2 30E2 30E3 30E3 30E4 30E4 30E5 30E5 30E6 30E6 30E7 30E7 30E8 30E8 30E9 30E9 30EA 30EA 30EB 30EB 30EC 30EC 30ED 30ED 30EE 30EE 30EF 30EF 30F0 30F0 30F1 30F1 30F2 30F2 30F3 30F3 30F4 30F4 30F5 30F5 30F6 30F6 30F7 30F7 30F8 30F8 30F9 30F9 30FA 30FA 30FB 30FB 30FC 30FC 30FD 30FD 30FE 30FE 0021 0021 0027 0027 002B 002B 002E 002E 003F 003F 005F 005F 007C 007C | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Japanese\Attributes |
| Operation: | write | Name: | Language |
Value: 411 | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Japanese\Attributes |
| Operation: | write | Name: | NoDelimiter |
Value: | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Japanese\Attributes |
| Operation: | write | Name: | NumericPhones |
Value: | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Spanish |
| Operation: | write | Name: | CLSID |
Value: {C6FABB24-E332-46FB-BC91-FF331B2D51F0} | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Spanish |
| Operation: | write | Name: | PhoneMap |
Value: - 0001 ! 0002 & 0003 , 0004 . 0005 ? 0006 _ 0007 1 0008 2 0009 a 000a e 000b i 000c o 000d u 000e t 000f d 0010 p 0011 b 0012 k 0013 g 0014 ch 0015 jj 0016 f 0017 s 0018 x 0019 m 001a n 001b nj 001c l 001d ll 001e r 001f rr 0020 j 0021 w 0022 th 0023 | |||
| (PID) Process: | (5228) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\SOFTWARE\Microsoft\Speech_OneCore\Isolated\A1hdl50UVDh2ZbG324Nx-6fZgntcGnHOs5kHLdmaJYE\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech_OneCore\PhoneConverters\Tokens\Spanish\Attributes |
| Operation: | write | Name: | Language |
Value: 40A;C0A | |||
Executable files
0
Suspicious files
14
Text files
26
Unknown types
1 870
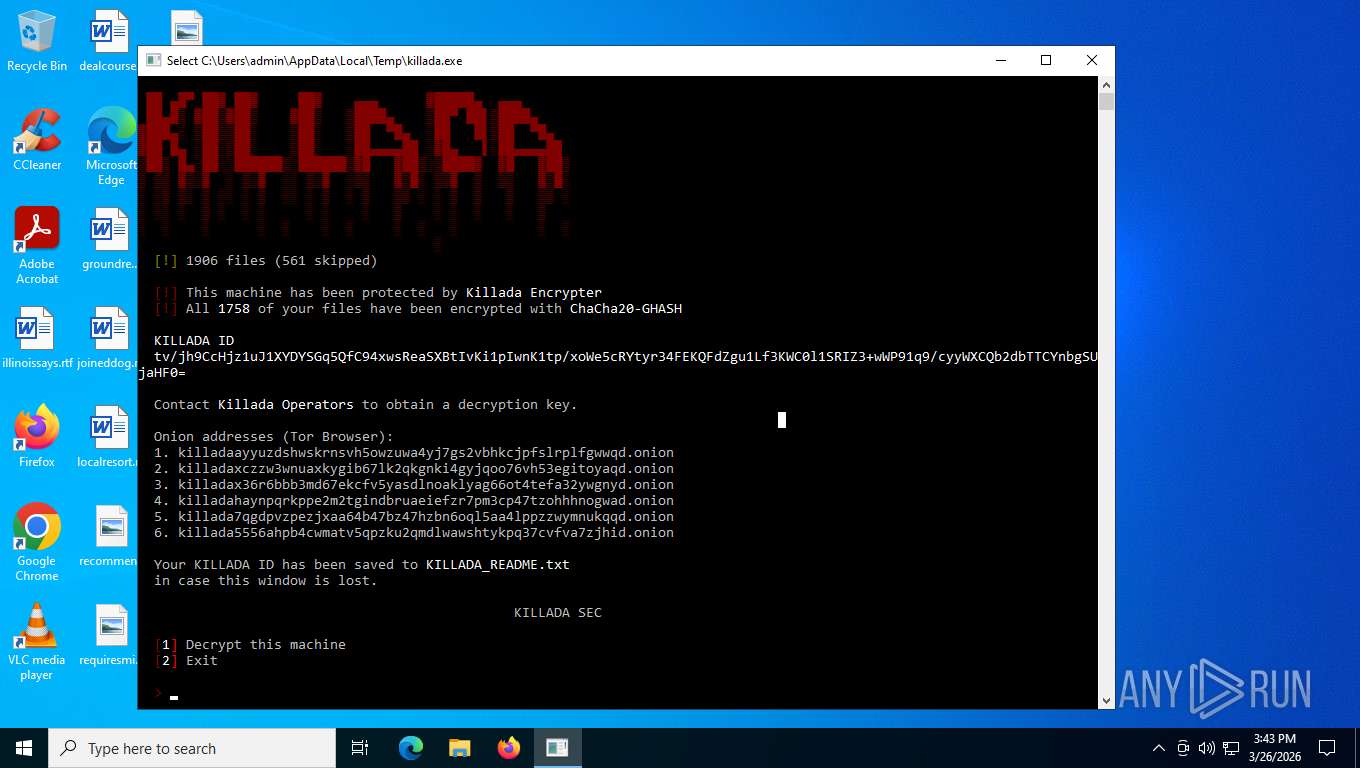
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | killada.exe | C:\Users\admin\Pictures\shegold.png | binary | |
MD5:E5A7CF4BA244ECCF40382D289E88F41C | SHA256:AF86CEC992B806D17B425E9AB67572BCB0F5FAE28D3B45A74E0BA179699A35B6 | |||
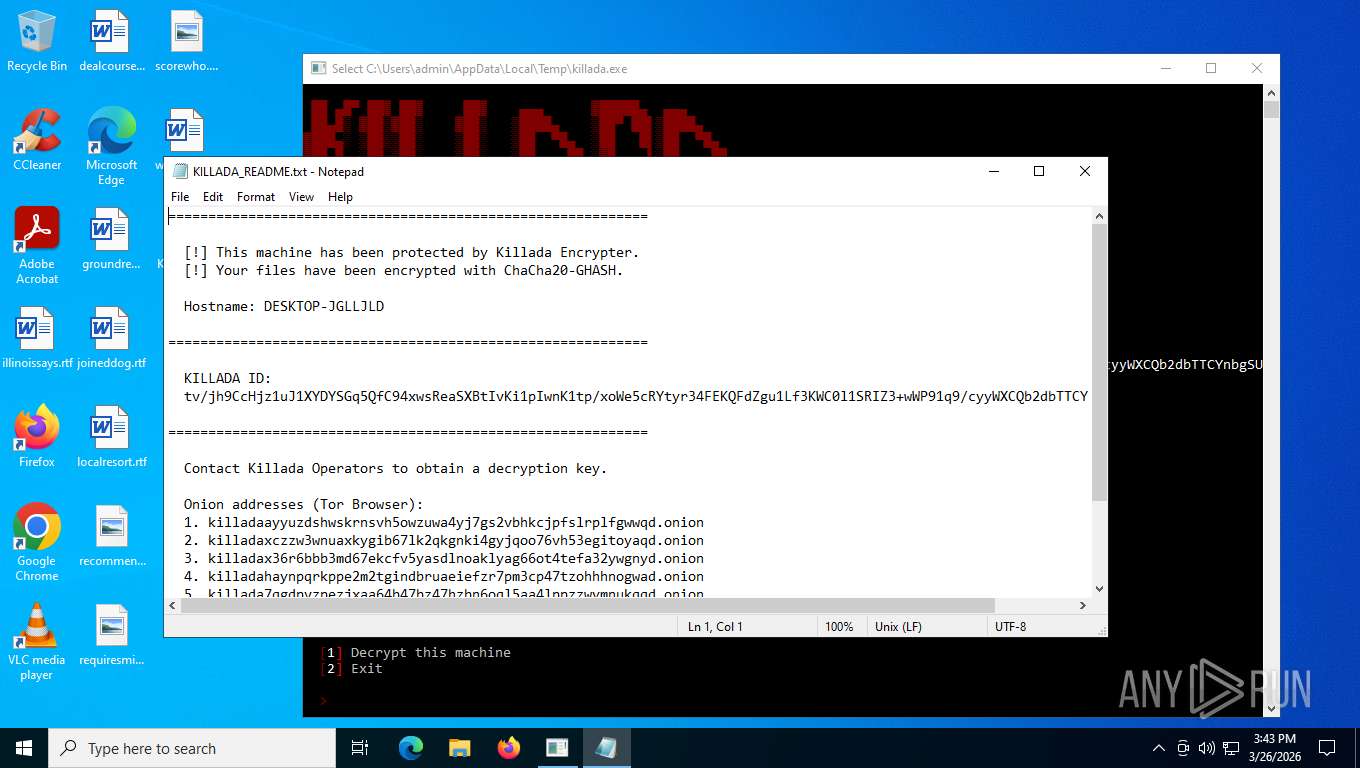
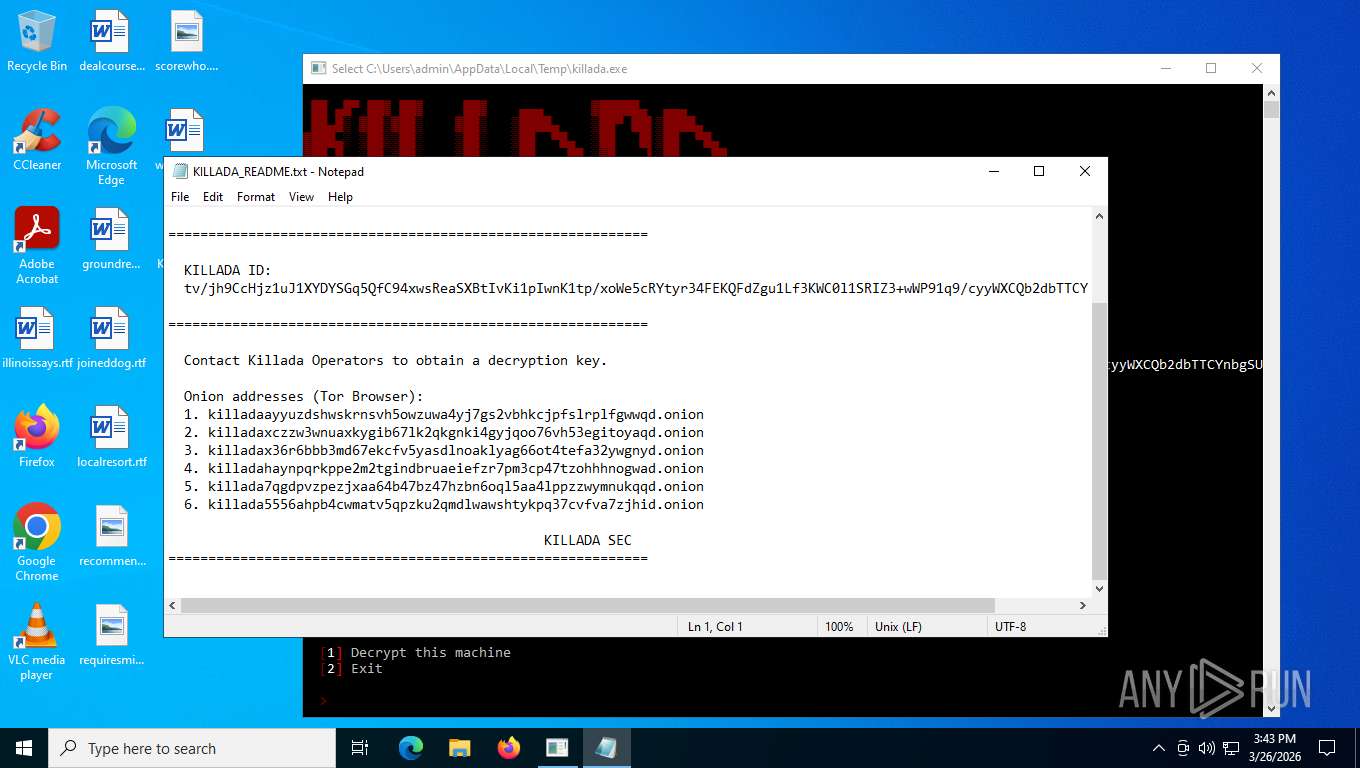
| 2876 | killada.exe | C:\Users\admin\Desktop\KILLADA_README.txt | binary | |
MD5:D5FC56998BEC135086C4B827EC58C3F4 | SHA256:C922F807EA3E6E921103D711A346A3153F151A51E4763F1DD7D46FC511F1F372 | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Web Applications\Manifest Resources\agimnkijcaahngcdmfeangaknmldooml\Icons\32.png | binary | |
MD5:65D4B89BD66F3F1727C0418481D56DF6 | SHA256:93D7B10208811C651E4E195240CC7E57C8E1B841A3B22F7AAF094E90F556BDCD | |||
| 2876 | killada.exe | C:\Users\admin\KILLADA_README.txt | binary | |
MD5:D5FC56998BEC135086C4B827EC58C3F4 | SHA256:C922F807EA3E6E921103D711A346A3153F151A51E4763F1DD7D46FC511F1F372 | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Extensions\ghbmnnjooekpmoecnnnilnnbdlolhkhi\1.99.1_0\_locales\fil\messages.json | binary | |
MD5:27AA062407258D61386566B50788AAEF | SHA256:9FCF1C6AFAD982DAD574D34DFC72D4771157B8DA2A9A5943A6EA870EC60C40CA | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Microsoft\Office\SolutionPackages\4cbd178c1d90aa388a105a9925ef93e\PackageResources\OfflineFiles\uistrings_64fcd33abeafaa511851db33e5de311e.json | binary | |
MD5:AF4ABC97731E3DFB1BF4EE8724E0B02E | SHA256:68F2F2006F39FD5AD686D31827C48CDD31308FCDFBC1D355F3BA857CECDC6DC9 | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ShellFeeds\GLEAM-DARK.svg | binary | |
MD5:B7141B369BC72A346EEB825B7BD1AABB | SHA256:3933E66F5E2BD7E193F22B49400EA09F7DAD126A042322DCD5F8D735BDAA16D9 | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\images\lightTheme\checkmark_in_progress.svg | binary | |
MD5:1E0E5F088649D3B42E46A10A3A3CDC98 | SHA256:7FB8D3729243597BB2AACE1436205D3629BFD335F6C1916BC2CCD1D52A870EB0 | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Edge Wallet\126.18013.17773.1\json\i18n-hub\en-GB\strings.json | binary | |
MD5:0EB08379EDB073D097D61B91787384BD | SHA256:52C2EAA6EEF0F83C6441322DB5966119B81FAB2BD8534E23316ABBDC59A894EE | |||
| 2876 | killada.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\Q84V0JUH\th[10].png | binary | |
MD5:BC060CCAF3EE4DF2A839DE4285E31062 | SHA256:99BC3823B698B57574DAAB97016FC05CFE8946351C0AA4A19EC124111054006C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
75
TCP/UDP connections
32
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.132:443 | https://login.live.com/RST2.srf | US | binary | 1.24 Kb | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.132:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | binary | 203 b | whitelisted |
5228 | SearchApp.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
5228 | SearchApp.exe | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
5228 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/rp/Cwfcx9xW-vinAjNDThniIqPq3sE.br.js | NL | binary | 42.8 Kb | whitelisted |
5228 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/rp/XJOaPjp3ukmFLCzB8jxRu9ObBS8.br.js | NL | binary | 203 Kb | whitelisted |
5228 | SearchApp.exe | GET | 200 | 2.16.241.207:443 | https://www.bing.com/rp/ANzUnPnVY0oL0XWxs0RLJxjJLUo.br.js | NL | text | 20.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3352 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.55.110.211:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3428 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5316 | svchost.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3352 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |