| File name: | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c |
| Full analysis: | https://app.any.run/tasks/76147ad3-5f47-4950-99c2-7c502f061da5 |
| Verdict: | Malicious activity |
| Threats: | DeerStealer is an information-stealing malware discovered in 2024 by ANY.RUN, primarily targeting sensitive data such as login credentials, browser history, and cryptocurrency wallet details. It is often distributed through phishing campaigns and fake Google ads that mimic legitimate platforms like Google Authenticator. Once installed, it exfiltrates the stolen data to a remote command and control (C2) server. DeerStealer’s ability to disguise itself as legitimate downloads makes it particularly dangerous for unsuspecting users. |
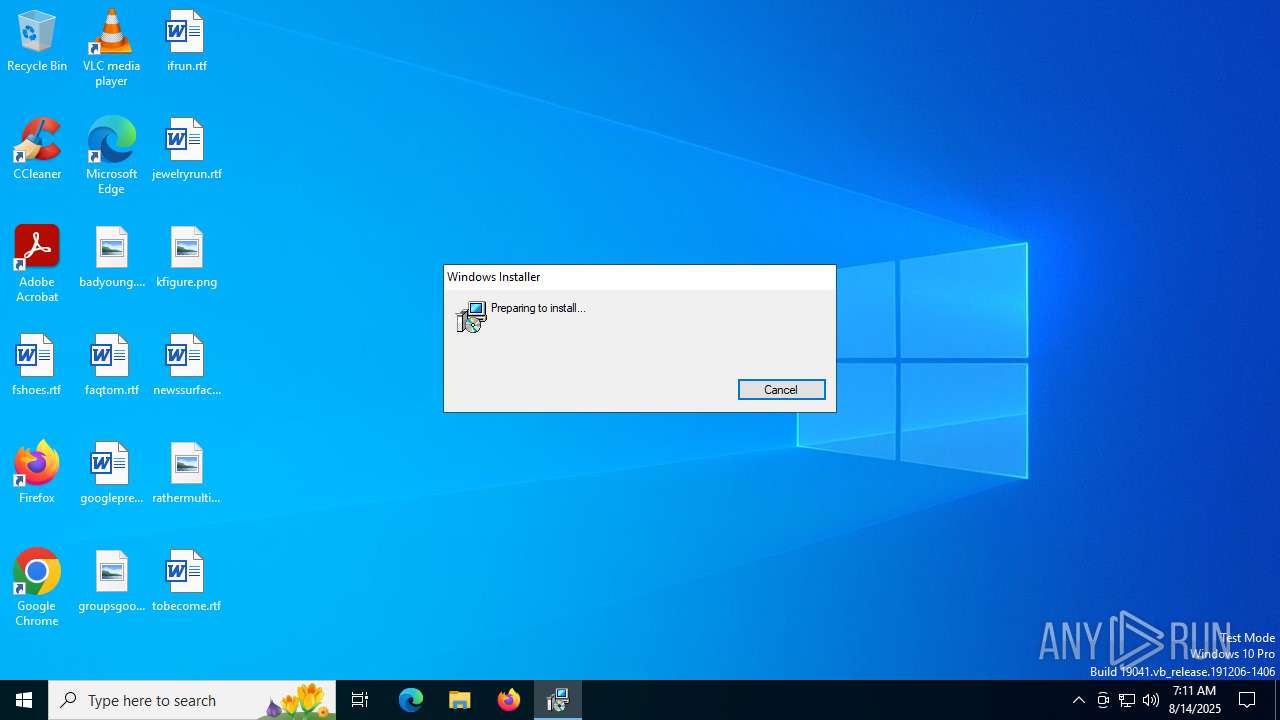
| Analysis date: | August 14, 2025, 07:11:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 12 sections |
| MD5: | 6F216FA5BB7757D3ACE2B6C7E0A2618B |
| SHA1: | 60F52F4335209C4B176157528054BBDBE34D83B5 |
| SHA256: | 4DD106DBCD7B735E05436321E664669B493F57ECBF21BBA8D198DF7815CC288C |
| SSDEEP: | 49152:a2yNEddfvMW9s4SuwAbhbwolm7CEq3tHQ0nvTz3j4sKBBKBL2plXqfV4IrFAU1C+:UuMSsOhkMmOE8nvz+TKBL0XWVrJCUt/j |
MALICIOUS
XORed URL has been found (YARA)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
DEERSTEALER has been detected (YARA)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Actions looks like stealing of personal data
- NodeAnalyz.exe (PID: 7008)
Steals credentials from Web Browsers
- NodeAnalyz.exe (PID: 7008)
SUSPICIOUS
Reads security settings of Internet Explorer
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Executes as Windows Service
- VSSVC.exe (PID: 6128)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5460)
Starts itself from another location
- Dev-Cobalt.exe (PID: 236)
Executable content was dropped or overwritten
- Dev-Cobalt.exe (PID: 236)
- Dev-Cobalt.exe (PID: 6504)
Reads the date of Windows installation
- NodeAnalyz.exe (PID: 7008)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
INFO
The sample compiled with english language support
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
- msiexec.exe (PID: 5460)
- Dev-Cobalt.exe (PID: 236)
- Dev-Cobalt.exe (PID: 6504)
Checks supported languages
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
- msiexec.exe (PID: 5460)
- Dev-Cobalt.exe (PID: 236)
- Dev-Cobalt.exe (PID: 6504)
- NodeAnalyz.exe (PID: 7008)
- identity_helper.exe (PID: 6676)
Reads Microsoft Office registry keys
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Creates files or folders in the user directory
- msiexec.exe (PID: 5460)
- Dev-Cobalt.exe (PID: 236)
- Dev-Cobalt.exe (PID: 6504)
Reads the computer name
- msiexec.exe (PID: 5460)
- Dev-Cobalt.exe (PID: 6504)
- Dev-Cobalt.exe (PID: 236)
- NodeAnalyz.exe (PID: 7008)
- identity_helper.exe (PID: 6676)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Manages system restore points
- SrTasks.exe (PID: 1352)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5460)
Reads the machine GUID from the registry
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
- NodeAnalyz.exe (PID: 7008)
Creates a software uninstall entry
- msiexec.exe (PID: 5460)
Creates files in the program directory
- Dev-Cobalt.exe (PID: 236)
Create files in a temporary directory
- Dev-Cobalt.exe (PID: 6504)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Application launched itself
- chrome.exe (PID: 2120)
- msedge.exe (PID: 6348)
Reads the software policy settings
- NodeAnalyz.exe (PID: 7008)
- slui.exe (PID: 7268)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Checks proxy server information
- NodeAnalyz.exe (PID: 7008)
- slui.exe (PID: 7268)
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
ULTRAVNC has been detected
- NodeAnalyz.exe (PID: 7008)
Reads Environment values
- identity_helper.exe (PID: 6676)
Process checks computer location settings
- 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe (PID: 1592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(1592) 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe
Decrypted-URLs (1)http://opalinewave-cdn.pro/c
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2019:09:11 22:06:20+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 8.8 |
| CodeSize: | 3511808 |
| InitializedDataSize: | 3717632 |
| UninitializedDataSize: | 428032 |
| EntryPoint: | 0x1157 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
Total processes
203
Monitored processes
61
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\AppData\Roaming\Delphinium\Dev-Cobalt.exe" | C:\Users\admin\AppData\Roaming\Delphinium\Dev-Cobalt.exe | msiexec.exe | ||||||||||||
User: admin Company: Smart Game Booster Integrity Level: MEDIUM Description: Bugreport for Smart Game Booster Exit code: 0 Version: 5.2.1.47 Modules
| |||||||||||||||
| 1100 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\JPXJPIBU.msi" | C:\Windows\System32\msiexec.exe | — | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3208,i,7827101537069892173,12402929192112426162,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1352 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=6224,i,7827101537069892173,12402929192112426162,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5512,i,7827101537069892173,12402929192112426162,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\Temp\4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe" | C:\Users\admin\AppData\Local\Temp\4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
xor-url(PID) Process(1592) 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe Decrypted-URLs (1)http://opalinewave-cdn.pro/c | |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3788,i,7827101537069892173,12402929192112426162,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3836 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6164,i,7827101537069892173,12402929192112426162,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1884,i,7827101537069892173,12402929192112426162,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1472 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
22 770
Read events
22 478
Write events
274
Delete events
18
Modification events
| (PID) Process: | (1592) 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Application10 |
| Operation: | write | Name: | b |
Value: 2233613162623939382D326134662D666263322D643861652D66343365656463356161303922 | |||
| (PID) Process: | (1592) 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Application10 |
| Operation: | write | Name: | c |
Value: 7B2231223A225875764E432F4B4868706577734C5A484B45686D356D45316167673D222C2230223A7B2232223A22514A4632504D72336E714337584A72616165454D3358684435726B3D222C2230223A747275652C2231223A5B7B2230223A2231222C2231223A223145754E726D337978625733684E3855737776776E566B6377683575736668427656227D2C7B2230223A2232222C2231223A2262633171733572666C7472797471343030736B657870796B6D3965387063713234396E6333333764676E227D2C7B2230223A2233222C2231223A2234416443764B316439684B3979344758634B664C75743543714370794371656B58464A396A55444A68696E37694E3476457535344C38346933663958636765744634523335645956546D6E4258624E787A6854694475596753424265454878227D2C7B2230223A2234222C2231223A22474355344C4C5255435648524E56544E4B3343343447504B4A374F34554859445A51504654495542564443574D34374D5159474253453342227D2C7B2230223A2235222C2231223A22724D53783371367A3854734C755A74344170424D485035645439536934774B4A6A66227D2C7B2230223A2236222C2231223A224C576D3247554737504D486A4445554868344C4377696A6473474A6147627033794D227D2C7B2230223A2239222C2231223A2271726A756B6733636830763838336B336B776B776A766576396668776D3063336167797A6B6C77323866227D2C7B2230223A223130222C2231223A225864574A4D676F5A537335573736484356766565524545614D70456A745443355753227D2C7B2230223A223131222C2231223A2244476B3255466B447437666E336F726D6944797063554D44553551503742354B6350227D2C7B2230223A223133222C2231223A22307835313036396263446137306331393745323546444431373231333739313137344561344430383035227D2C7B2230223A223134222C2231223A22544B4276776F6F6F58644538396775683164744B524A424264654E674E4E44484E44227D2C7B2230223A223135222C2231223A2274314A3361445175357071366742666F6B6D64364569686635447A4C64465438323662227D2C7B2230223A223136222C2231223A223667624E31337742584B4A4E4473636D4C42394E4677455178764E3669385146416E31314C7666466851476F227D2C7B2230223A223137222C2231223A2261646472317139666C716664656C326C33306437677A646164636676667A75667870386D3035336C39366E6A716C7475656364326E37716A6D6E37346C7A376D7573796D366D736A636A39636A767A306B6C66723774343879703768656E733673386B68656C71227D5D7D7D | |||
| (PID) Process: | (1592) 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000003FC0D8A6EA0CDC01541500004C1A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000003FC0D8A6EA0CDC01541500004C1A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000076BF5A6EA0CDC01541500004C1A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000076BF5A6EA0CDC01541500004C1A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000076BF5A6EA0CDC01541500004C1A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000085BBF7A6EA0CDC01541500004C1A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5460) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
Executable files
14
Suspicious files
591
Text files
132
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1592 | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | C:\Users\admin\AppData\Local\Temp\JPXJPIBU.msi | — | |
MD5:— | SHA256:— | |||
| 5460 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5460 | msiexec.exe | C:\Windows\Installer\191320.msi | — | |
MD5:— | SHA256:— | |||
| 5460 | msiexec.exe | C:\Windows\Installer\191322.msi | — | |
MD5:— | SHA256:— | |||
| 5460 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{9c55f29c-9f4e-445f-96b6-9a9bf2960b9b}_OnDiskSnapshotProp | binary | |
MD5:E61F411BFF4020881CB55694F4433F12 | SHA256:3DBE885A9A59B257601C470A3E9047D6B850BBD4BA3BAB50ABCDC4AC9E896550 | |||
| 5460 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:8C9384675EF8508E991AEBD994E30DE4 | SHA256:2DDA895D81518EE638E6ADE23A28F27BC3461E397825FBD424BFBB5BBA2F0F91 | |||
| 5460 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:E61F411BFF4020881CB55694F4433F12 | SHA256:3DBE885A9A59B257601C470A3E9047D6B850BBD4BA3BAB50ABCDC4AC9E896550 | |||
| 5460 | msiexec.exe | C:\Windows\Installer\MSI140B.tmp | binary | |
MD5:6D181478129EB5F37069510E922C8C93 | SHA256:73605F439BECA33CAD3EFAAB0EBF408EA01FF087D365E6C18F63E604F0C301C2 | |||
| 5460 | msiexec.exe | C:\Users\admin\AppData\Roaming\Delphinium\Zangraedshoong.nx | abr | |
MD5:1966AA0DBFAC136FC6CF1E17F094ABFA | SHA256:9CF6D30B9D8F128E099A94C8070AFD4B0D1BF66DCEE39DD5E3A1A98B7048B99E | |||
| 5460 | msiexec.exe | C:\Windows\Temp\~DFC392E175F11FE986.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
119
DNS requests
121
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1592 | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | GET | 101 | 104.21.70.11:80 | http://opalinewave-cdn.pro/c | unknown | — | — | unknown |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4528 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4948 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
3760 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:HdYgOpcINc5k21QTqEIHj_5dusvJXdvgiJFjYgm1pvo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
7664 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:uALDGMEdfqUW2mqUoCIkvjfarFztjEdyg54MFSe_Jrk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
6820 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
6820 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5884 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1592 | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | 104.21.70.11:80 | opalinewave-cdn.pro | CLOUDFLARENET | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1592 | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | 104.21.48.1:443 | phone-nis-tu.club | CLOUDFLARENET | — | unknown |
1268 | svchost.exe | 23.216.77.22:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
opalinewave-cdn.pro |
| unknown |
phone-nis-tu.club |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1592 | 4dd106dbcd7b735e05436321e664669b493f57ecbf21bba8d198df7815cc288c.exe | A Network Trojan was detected | ET MALWARE DeerStealer Websocket Initial Request |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
Process | Message |
|---|---|
Dev-Cobalt.exe | Win32MinorVersion: 0 |
Dev-Cobalt.exe | Win32MinorVersion: 0 |