| File name: | Sample1.zip |
| Full analysis: | https://app.any.run/tasks/55db2965-d7bd-4a44-b6ce-233b4ac50285 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | July 17, 2019, 15:13:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
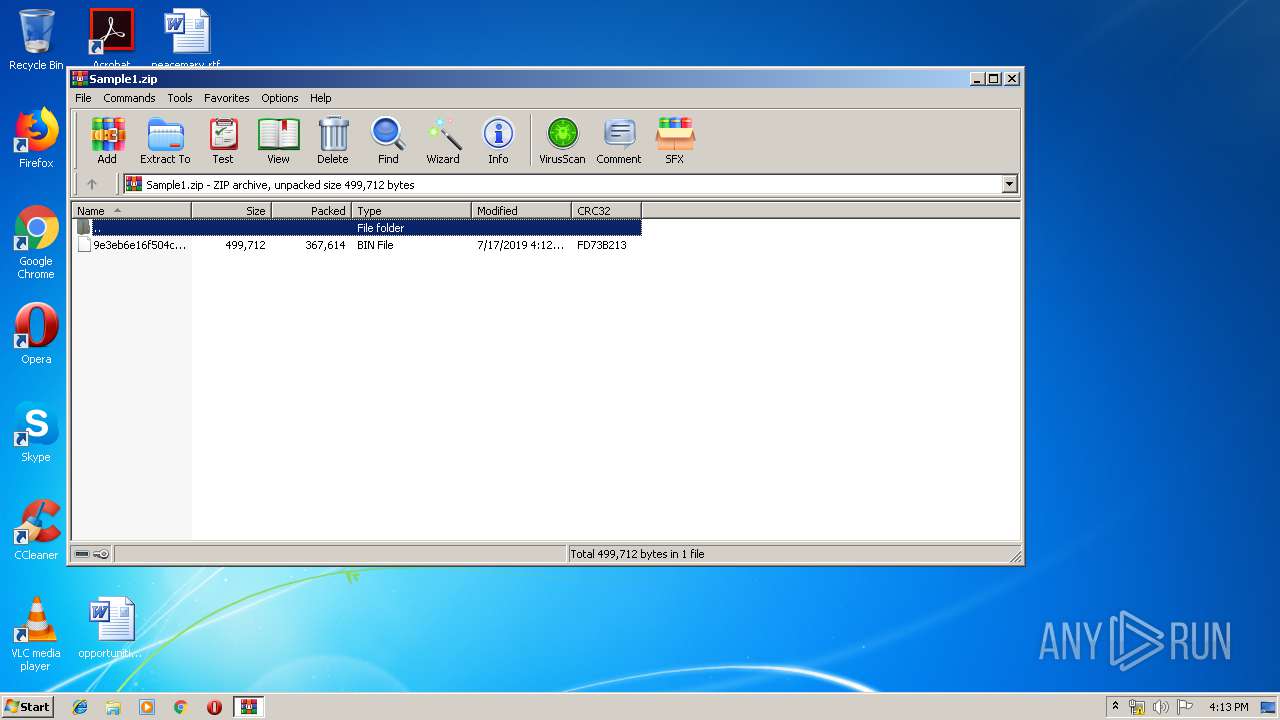
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 55C565CE858B591F764172F7F26B1FC0 |
| SHA1: | 00F6BEC1C5F0CC088C224050DC98CBC6762C5970 |
| SHA256: | 4D3DDDD4AD9AA7EBAC1EB860C69ECA2DA60ACF3769B21D9093556BD28A4EBB66 |
| SSDEEP: | 6144:gylUGPedOIvBm+y2SlHNVZajcX+SM63LlCIQoFUrIZbq8dkgOOZ5Swl0kTPhGu4:gBGPeJkbHNXT+SMg1QoerIZ28z5SqXj4 |
MALICIOUS
FORMBOOK was detected
- explorer.exe (PID: 292)
Application was dropped or rewritten from another process
- ayyy.exe (PID: 1412)
- ayyy.exe (PID: 800)
- gvj8ptitih48.exe (PID: 2852)
- gvj8ptitih48.exe (PID: 2488)
- gvj8ptitih48.exe (PID: 1000)
- gvj8ptitih48.exe (PID: 2884)
- gvj8ptitih48.exe (PID: 3388)
- gvj8ptitih48.exe (PID: 2824)
Formbook was detected
- wlanext.exe (PID: 3976)
- Firefox.exe (PID: 1688)
Changes the autorun value in the registry
- wlanext.exe (PID: 3976)
Actions looks like stealing of personal data
- wlanext.exe (PID: 3976)
Connects to CnC server
- explorer.exe (PID: 292)
Stealing of credential data
- wlanext.exe (PID: 3976)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 292)
- DllHost.exe (PID: 3264)
Starts CMD.EXE for commands execution
- ayyy.exe (PID: 1412)
- wlanext.exe (PID: 3976)
- gvj8ptitih48.exe (PID: 2488)
Application launched itself
- ayyy.exe (PID: 1412)
- gvj8ptitih48.exe (PID: 2488)
Creates files in the user directory
- wlanext.exe (PID: 3976)
Loads DLL from Mozilla Firefox
- wlanext.exe (PID: 3976)
Creates files in the program directory
- DllHost.exe (PID: 3264)
Executed via COM
- DllHost.exe (PID: 3264)
INFO
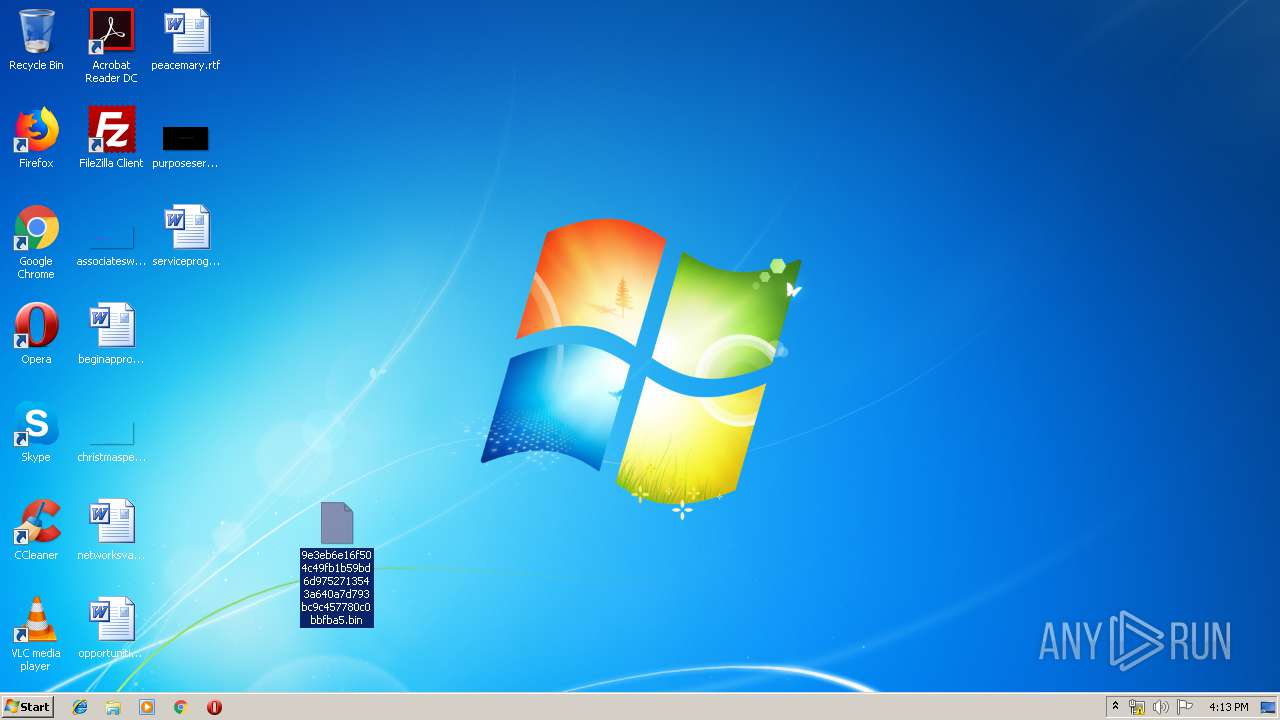
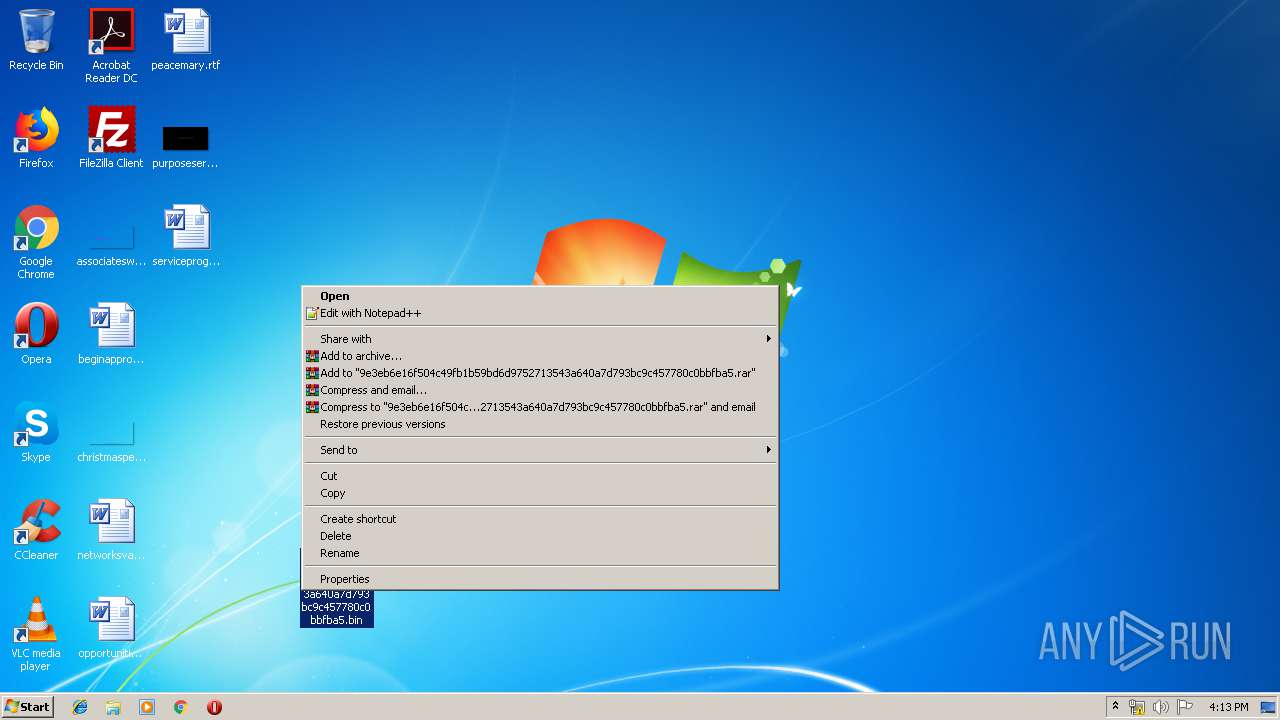
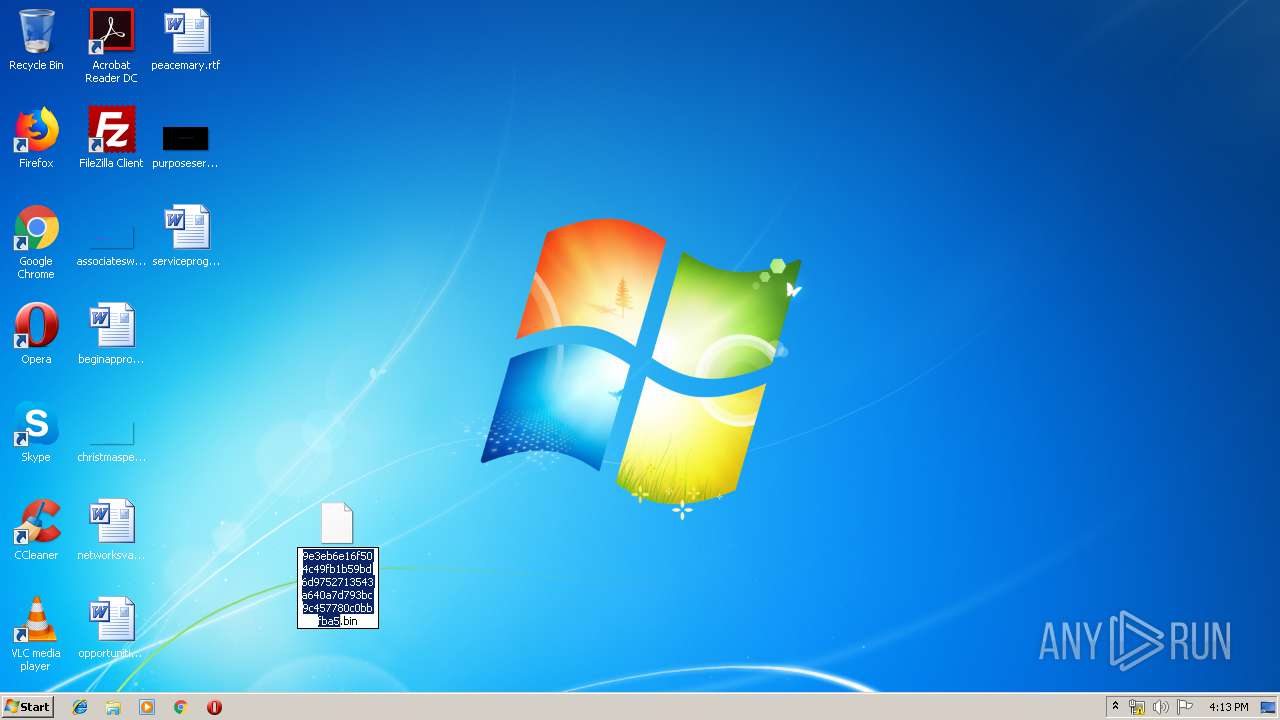
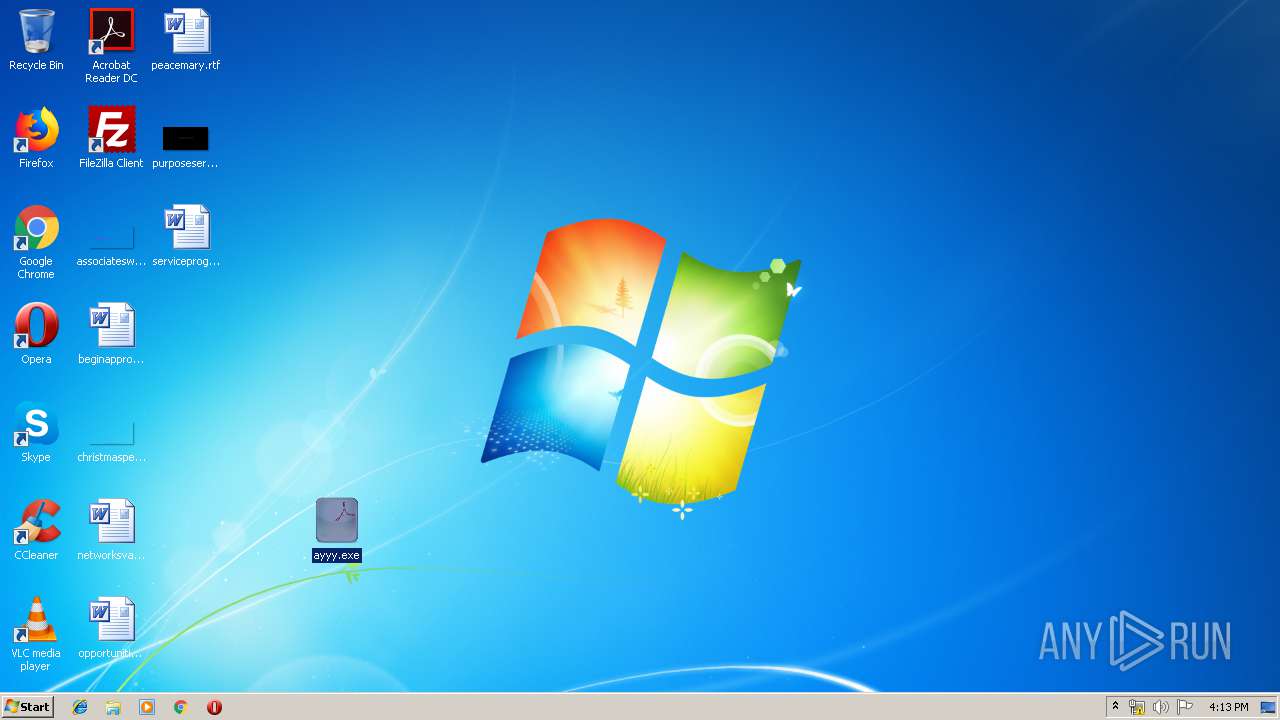
Manual execution by user
- ayyy.exe (PID: 1412)
- wlanext.exe (PID: 3976)
Creates files in the user directory
- Firefox.exe (PID: 1688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:17 15:12:24 |
| ZipCRC: | 0xfd73b213 |
| ZipCompressedSize: | 367614 |
| ZipUncompressedSize: | 499712 |
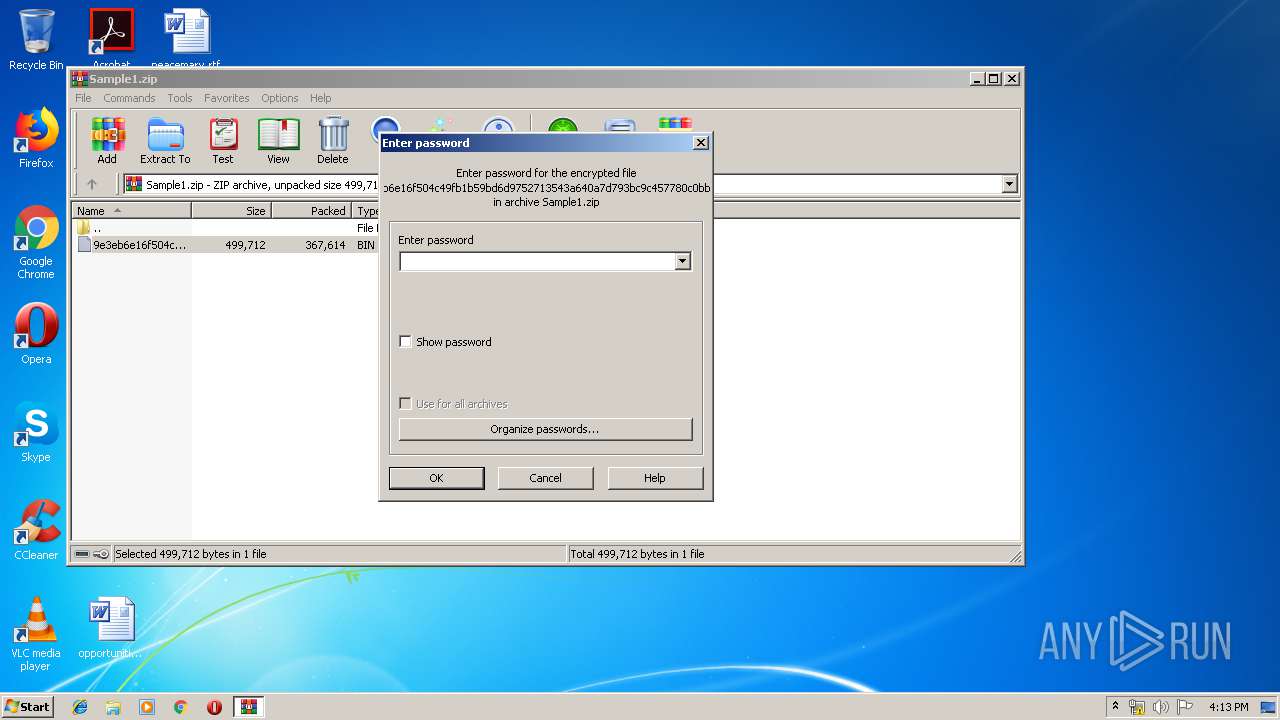
| ZipFileName: | 9e3eb6e16f504c49fb1b59bd6d9752713543a640a7d793bc9c457780c0bbfba5.bin |
Total processes
60
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 340 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Users\admin\Desktop\ayyy.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | ayyy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 800 | "C:\Users\admin\Desktop\ayyy.exe" | C:\Users\admin\Desktop\ayyy.exe | — | ayyy.exe | |||||||||||
User: admin Company: iqevamelicujevomeq Integrity Level: MEDIUM Description: alopefar Exit code: 0 Version: 6.3.3.4 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Mp6q\gvj8ptitih48.exe" | C:\Program Files\Mp6q\gvj8ptitih48.exe | — | gvj8ptitih48.exe | |||||||||||
User: admin Company: iqevamelicujevomeq Integrity Level: MEDIUM Description: alopefar Exit code: 4294967295 Version: 6.3.3.4 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\Desktop\ayyy.exe" | C:\Users\admin\Desktop\ayyy.exe | — | explorer.exe | |||||||||||
User: admin Company: iqevamelicujevomeq Integrity Level: MEDIUM Description: alopefar Exit code: 0 Version: 6.3.3.4 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wlanext.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2120 | "C:\Windows\System32\cmd.exe" /C type nul > "C:\Program Files\Mp6q\gvj8ptitih48.exe:Zone.Identifier" | C:\Windows\System32\cmd.exe | — | gvj8ptitih48.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Mp6q\gvj8ptitih48.exe" | C:\Program Files\Mp6q\gvj8ptitih48.exe | — | explorer.exe | |||||||||||
User: admin Company: iqevamelicujevomeq Integrity Level: MEDIUM Description: alopefar Exit code: 0 Version: 6.3.3.4 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Mp6q\gvj8ptitih48.exe" | C:\Program Files\Mp6q\gvj8ptitih48.exe | — | gvj8ptitih48.exe | |||||||||||
User: admin Company: iqevamelicujevomeq Integrity Level: MEDIUM Description: alopefar Exit code: 4294967295 Version: 6.3.3.4 Modules
| |||||||||||||||
| 2852 | "C:\Program Files\Mp6q\gvj8ptitih48.exe" | C:\Program Files\Mp6q\gvj8ptitih48.exe | — | gvj8ptitih48.exe | |||||||||||
User: admin Company: iqevamelicujevomeq Integrity Level: MEDIUM Description: alopefar Exit code: 4294967295 Version: 6.3.3.4 Modules
| |||||||||||||||
Total events
4 131
Read events
4 076
Write events
55
Delete events
0
Modification events
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Sample1.zip | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
4
Suspicious files
73
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
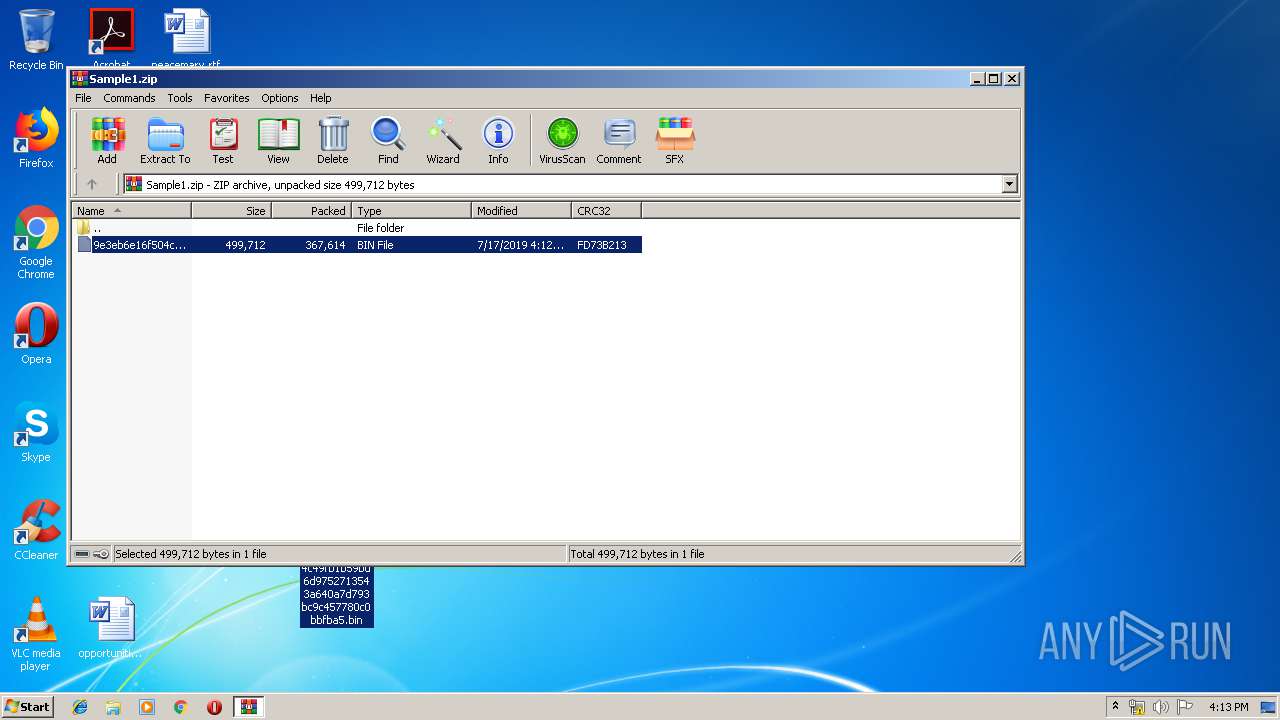
| 3872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3872.41333\9e3eb6e16f504c49fb1b59bd6d9752713543a640a7d793bc9c457780c0bbfba5.bin | — | |
MD5:— | SHA256:— | |||
| 3976 | wlanext.exe | C:\Users\admin\AppData\Roaming\5K14B43E\5K1logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 292 | explorer.exe | C:\Users\admin\Desktop\ayyy.exe | executable | |
MD5:— | SHA256:— | |||
| 292 | explorer.exe | C:\Users\admin\Desktop\9e3eb6e16f504c49fb1b59bd6d9752713543a640a7d793bc9c457780c0bbfba5.bin | executable | |
MD5:— | SHA256:— | |||
| 3976 | wlanext.exe | C:\Users\admin\AppData\Roaming\5K14B43E\5K1logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 3976 | wlanext.exe | C:\Users\admin\AppData\Roaming\5K14B43E\5K1logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 1688 | Firefox.exe | C:\Users\admin\AppData\Roaming\5K14B43E\5K1logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 3264 | DllHost.exe | C:\Program Files\Mp6q\gvj8ptitih48.exe | executable | |
MD5:— | SHA256:— | |||
| 292 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Mp6q\gvj8ptitih48.exe | executable | |
MD5:— | SHA256:— | |||
| 3976 | wlanext.exe | C:\Users\admin\AppData\Roaming\5K14B43E\5K1logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
21
DNS requests
26
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
292 | explorer.exe | GET | — | 103.92.9.131:80 | http://www.neilhenig.com/gl/?T8nLxfw=0RP90QYE7NnpMZdBkguZmHPH2gjY/5IkdCVE7vmYwPKTXv4R1MZnVYIsGz2a9tlO3JEX1Q==&R2Kdp=MjOPrtq8QZcluR60 | CN | — | — | malicious |
292 | explorer.exe | GET | — | 173.234.112.16:80 | http://www.abbeytvl.com/gl/?T8nLxfw=L5oFMYcYJw6+TQBjaNoKyqzkcGMsA+1p8gYdO8ihpeqJtvKHQEevB+asvpFQ7kTXaA29Tg==&R2Kdp=MjOPrtq8QZcluR60&sql=1 | US | — | — | malicious |
292 | explorer.exe | GET | — | 160.153.136.3:80 | http://www.shreveportnightlife.com/gl/?T8nLxfw=JEnoMCr6QAWsG6oY+4+MeDomIqASeEfzm0FPM00nF7Obmh8MVEjjB2LTx3HFlYw13JSFtQ==&R2Kdp=MjOPrtq8QZcluR60&sql=1 | US | — | — | malicious |
292 | explorer.exe | GET | — | 212.95.147.29:80 | http://www.caifuad.com/gl/?T8nLxfw=+8oeQ/ILoNPME6erl34UzcZrURSpkatYag/I/cxVtMsh1JNDmXq6AWorzOV+eRfC+t8WsQ==&R2Kdp=MjOPrtq8QZcluR60&sql=1 | IR | — | — | malicious |
292 | explorer.exe | GET | — | 107.165.220.150:80 | http://www.melomy.com/gl/?T8nLxfw=deD4sgaDa6SHSpyqsbM84RE+d6Nt8vGOmo7uffM9+X8mlPvoJjWLWQVsXzgEVnFgZxL5dg==&R2Kdp=MjOPrtq8QZcluR60&sql=1 | US | — | — | malicious |
292 | explorer.exe | GET | — | 153.126.200.189:80 | http://www.centre-hyperu-lesarcs.com/gl/?T8nLxfw=jTEAptA85JJNDgzb7AKtzl0OW+KqIY4kDyDEthTZrLymlwRXAU0kumsnA/1raYc61z/BmA==&R2Kdp=MjOPrtq8QZcluR60&sql=1 | JP | — | — | malicious |
292 | explorer.exe | POST | — | 173.234.112.16:80 | http://www.abbeytvl.com/gl/ | US | — | — | malicious |
292 | explorer.exe | POST | — | 107.165.220.150:80 | http://www.melomy.com/gl/ | US | — | — | malicious |
292 | explorer.exe | POST | — | 107.165.220.150:80 | http://www.melomy.com/gl/ | US | — | — | malicious |
292 | explorer.exe | POST | — | 160.153.136.3:80 | http://www.shreveportnightlife.com/gl/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
292 | explorer.exe | 103.92.9.131:80 | www.neilhenig.com | DXTL Tseung Kwan O Service | CN | malicious |
292 | explorer.exe | 173.234.112.16:80 | www.abbeytvl.com | Nobis Technology Group, LLC | US | malicious |
292 | explorer.exe | 107.165.220.150:80 | www.melomy.com | EGIHosting | US | malicious |
— | — | 107.165.220.150:80 | www.melomy.com | EGIHosting | US | malicious |
292 | explorer.exe | 160.153.136.3:80 | www.shreveportnightlife.com | GoDaddy.com, LLC | US | malicious |
292 | explorer.exe | 153.126.200.189:80 | www.centre-hyperu-lesarcs.com | SAKURA Internet Inc. | JP | malicious |
292 | explorer.exe | 212.95.147.29:80 | www.caifuad.com | Hesabgar Pardaz Gharb Company (Private Joint Stock) | IR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.neilhenig.com |
| unknown |
www.szhskj.com |
| unknown |
www.abbeytvl.com |
| malicious |
www.shopswon.com |
| unknown |
www.birdicac.reisen |
| unknown |
www.melomy.com |
| malicious |
www.shreveportnightlife.com |
| malicious |
www.centre-hyperu-lesarcs.com |
| malicious |
www.9900cao.com |
| unknown |
www.caifuad.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
292 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
16 ETPRO signatures available at the full report