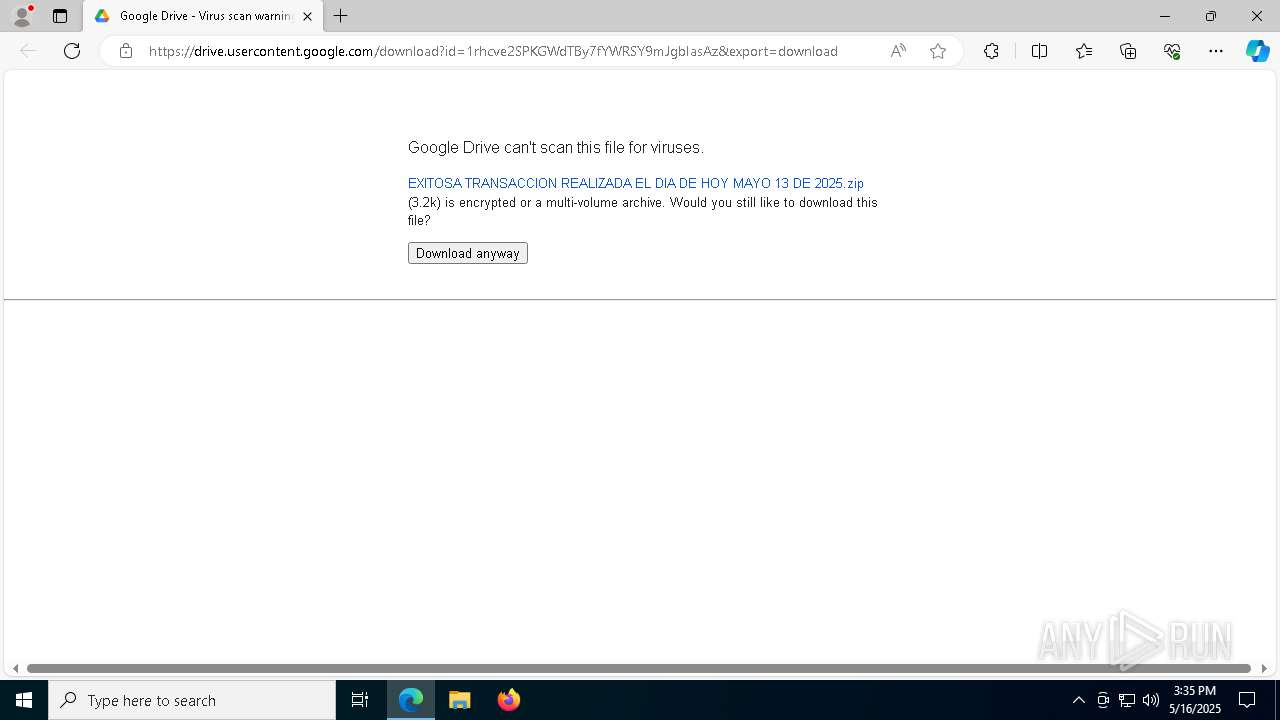
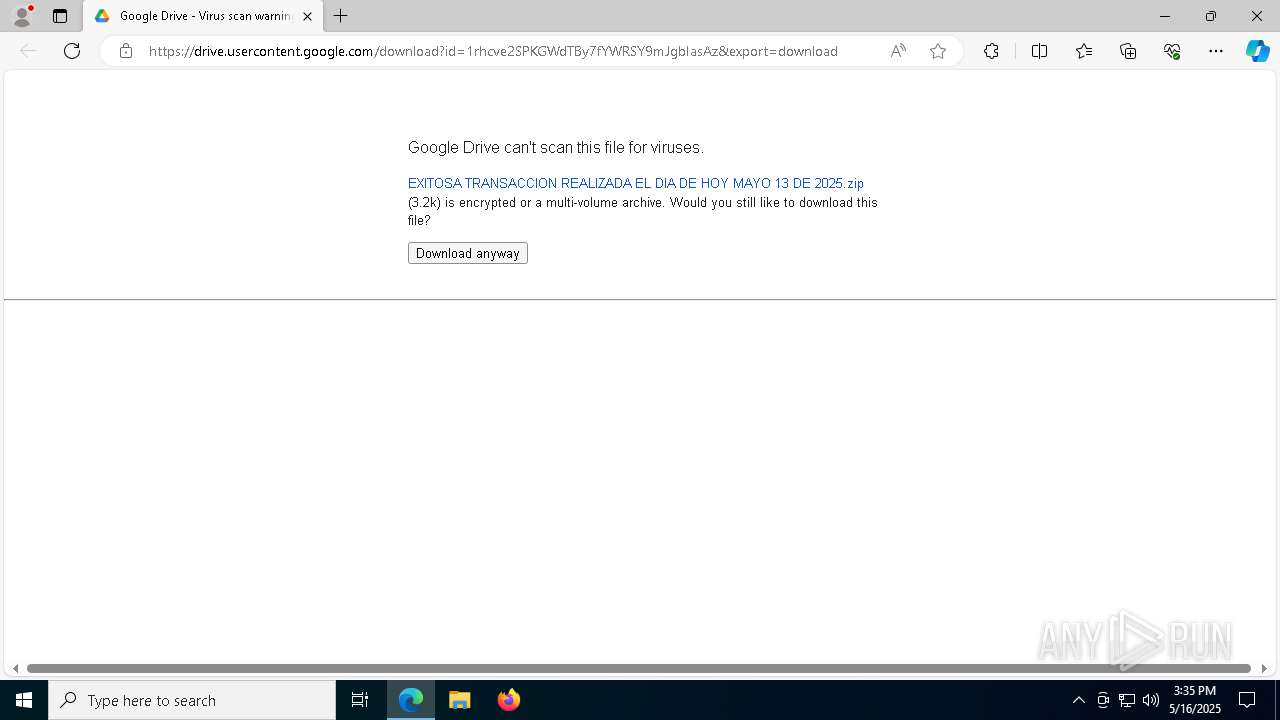
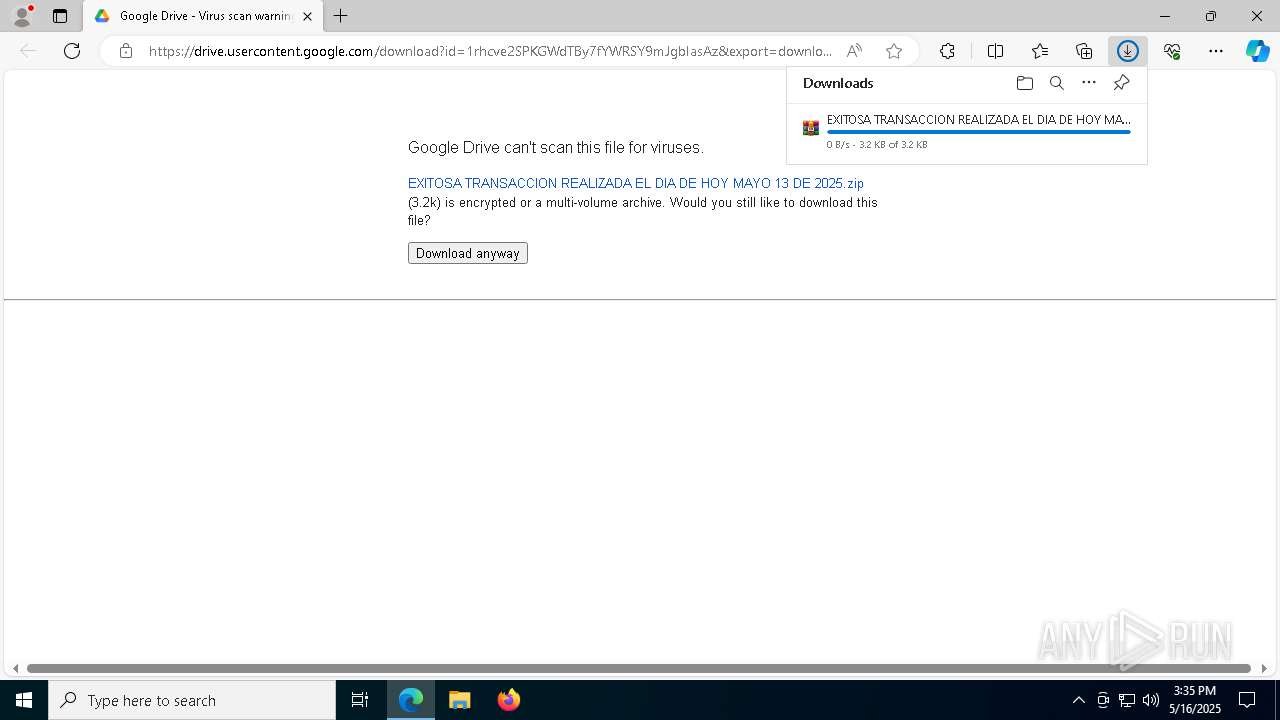
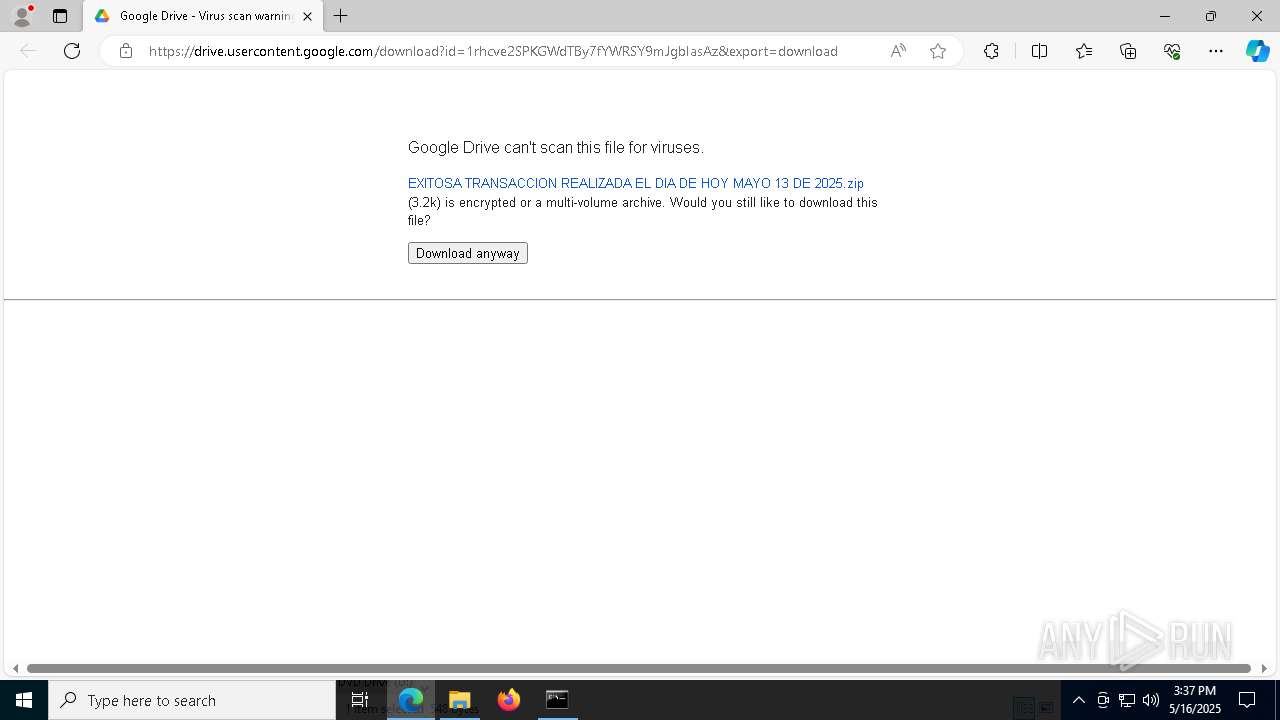
| URL: | https://docs.google.com/uc?export=download&id=1rhcve2SPKGWdTBy7fYWRSY9mJgbIasAz |
| Full analysis: | https://app.any.run/tasks/26dd697d-43ad-4dec-95a3-2dee1d1c54c9 |
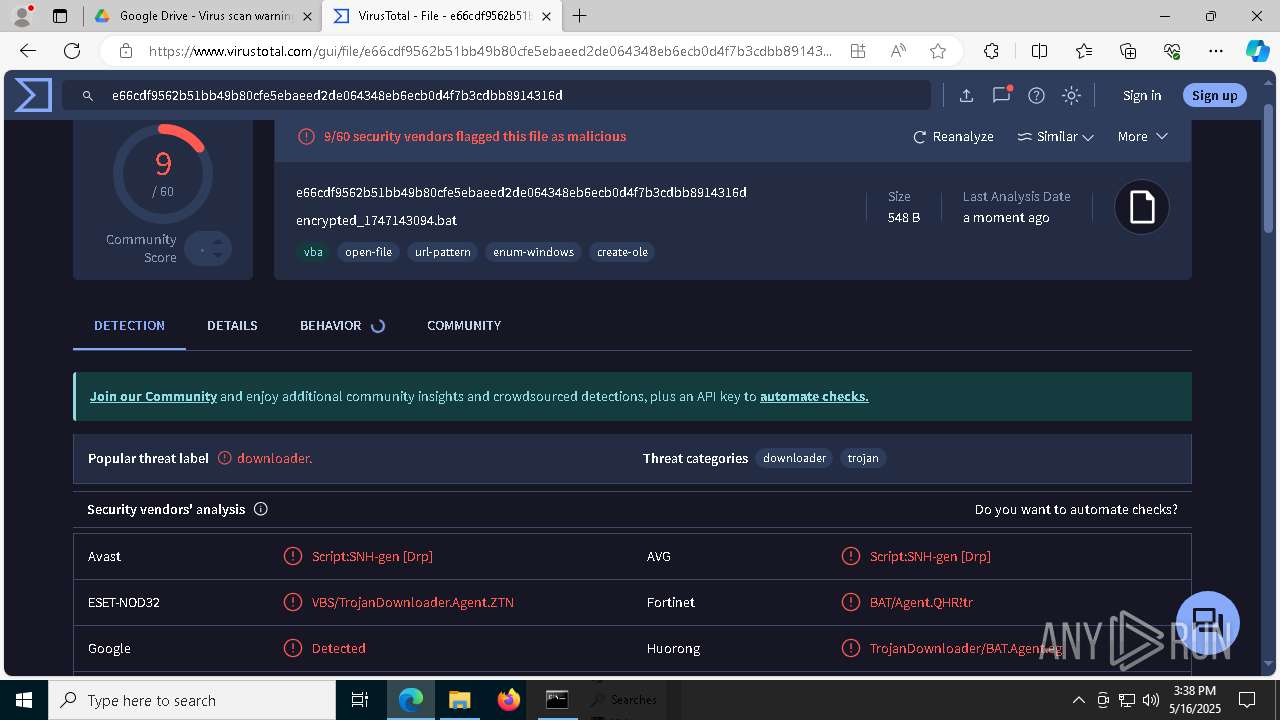
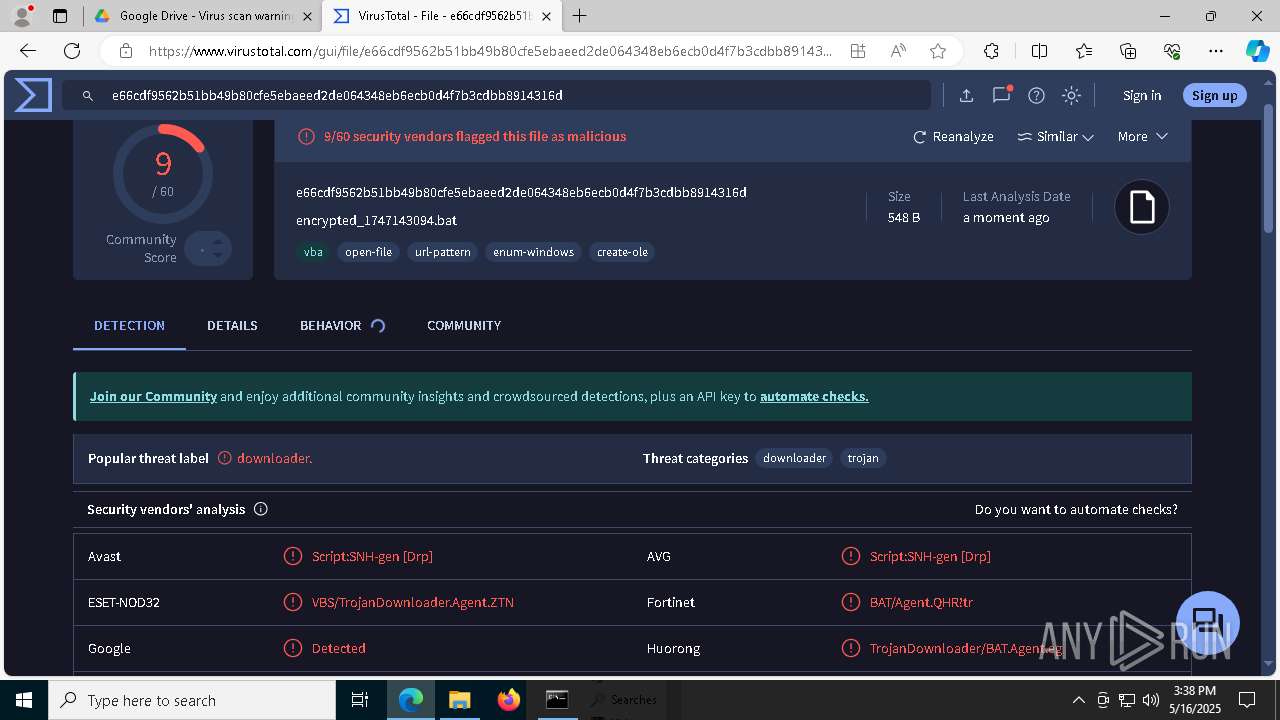
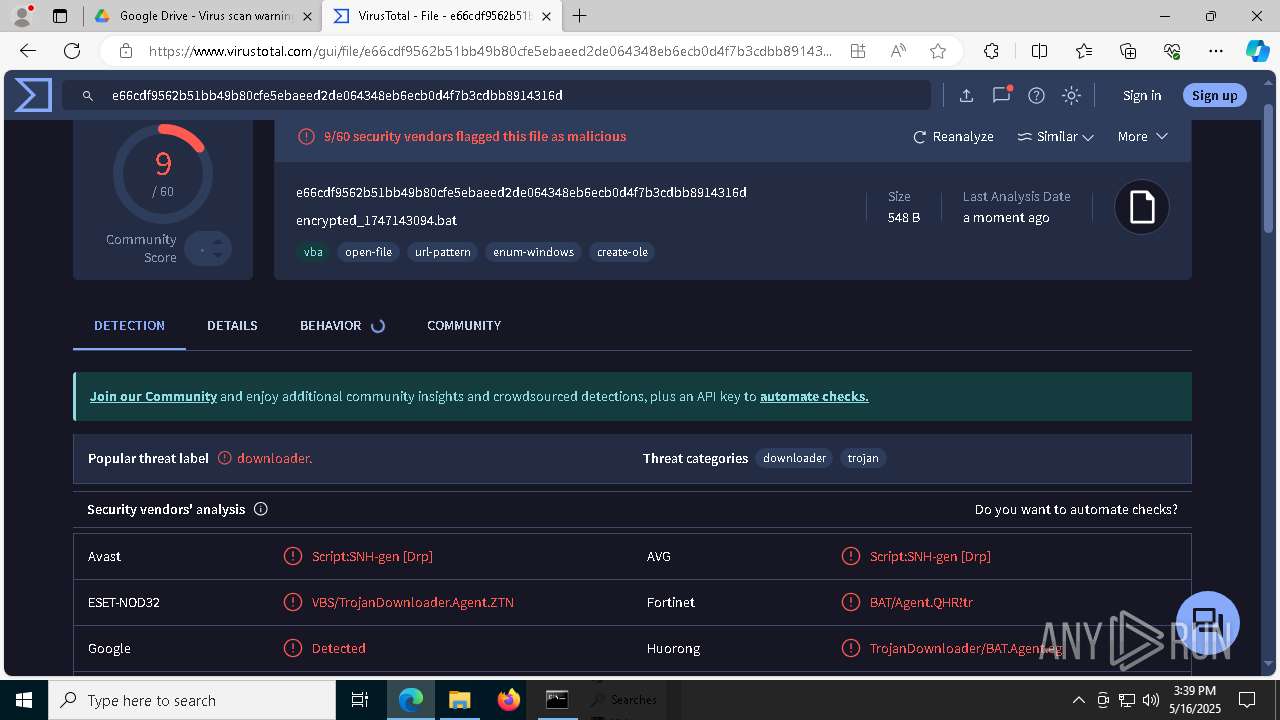
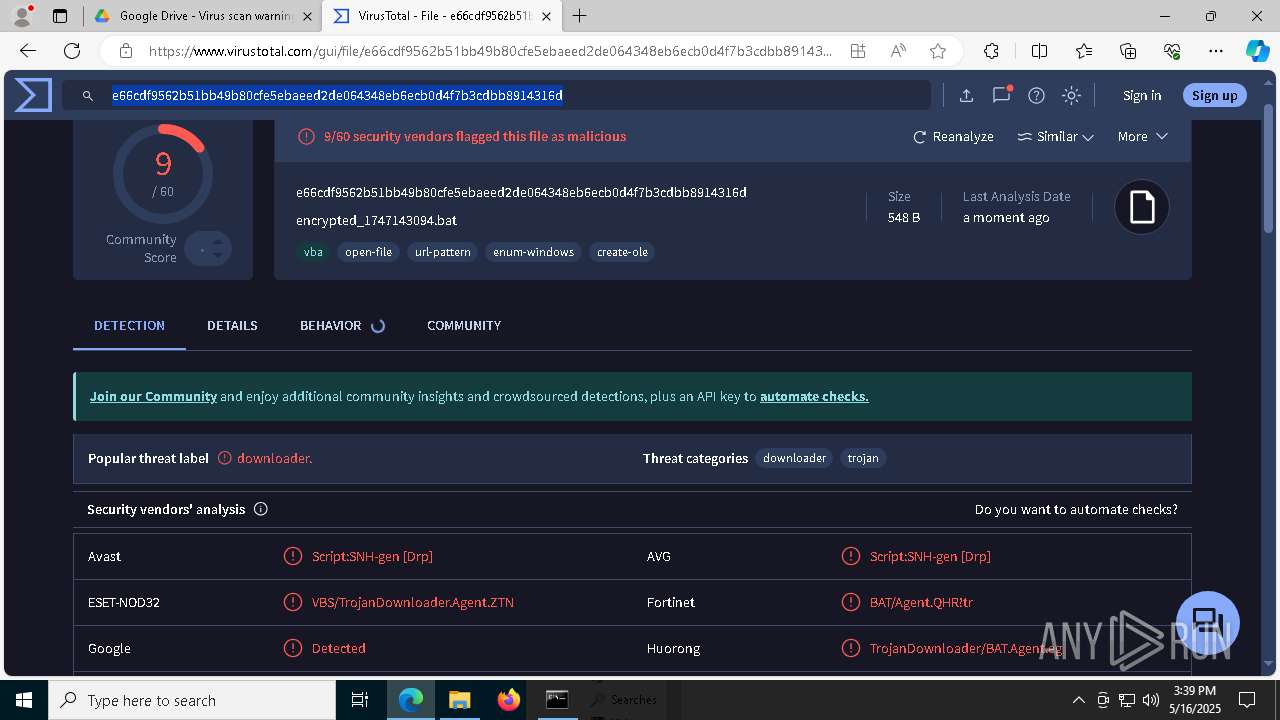
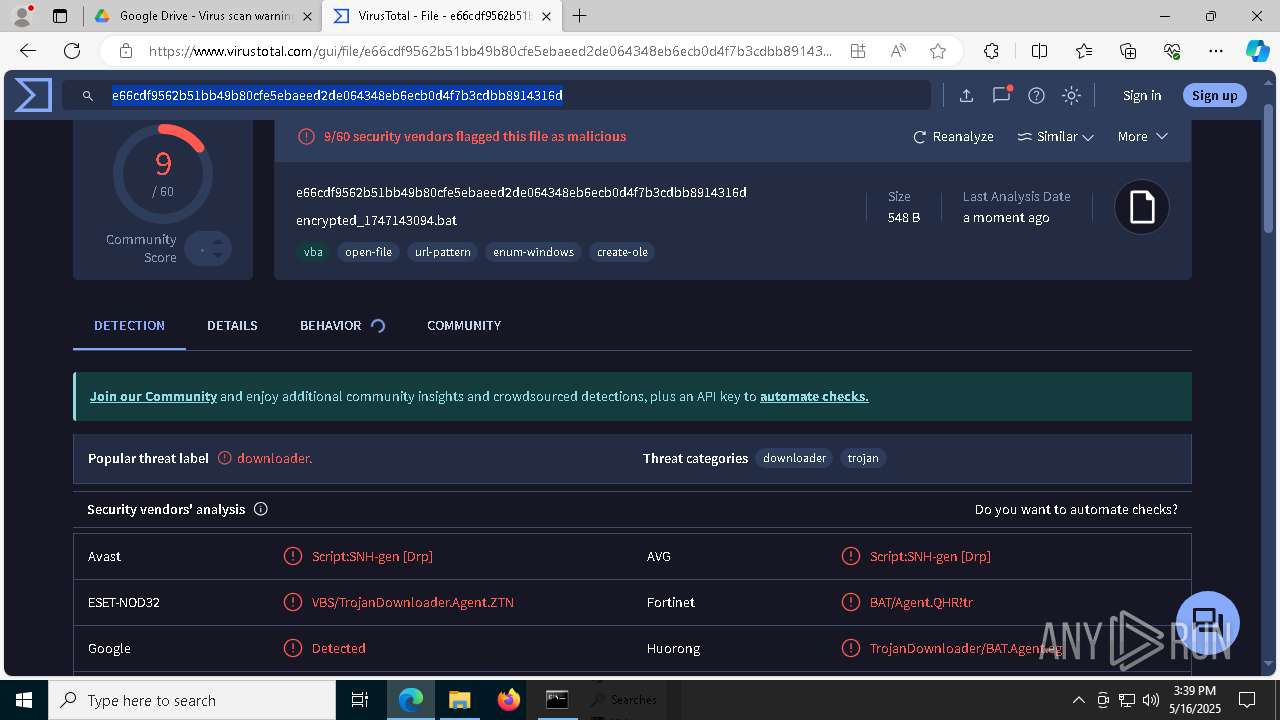
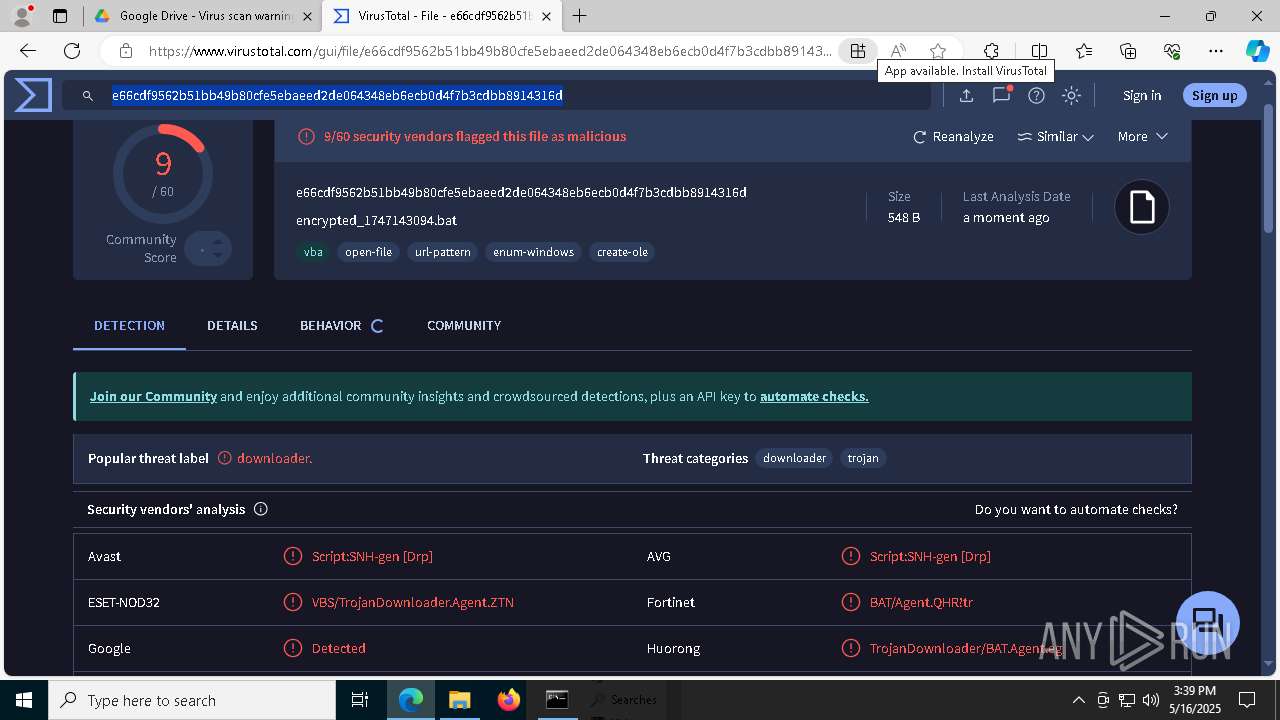
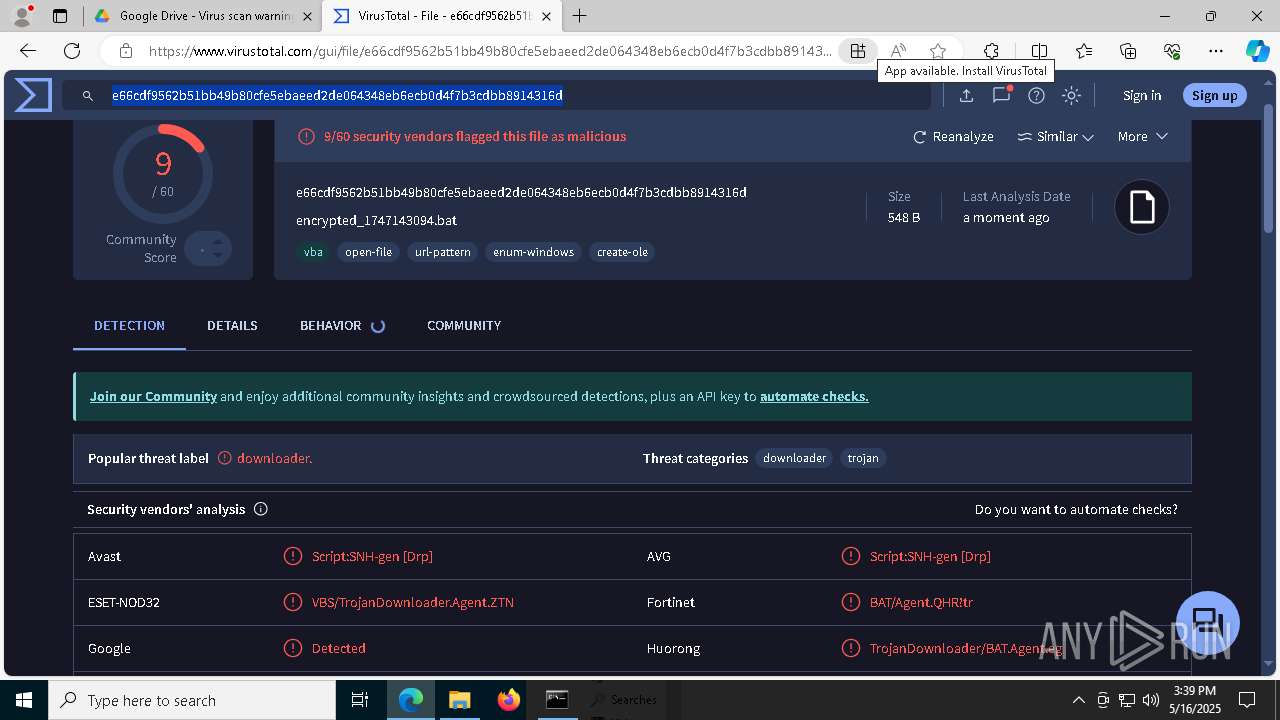
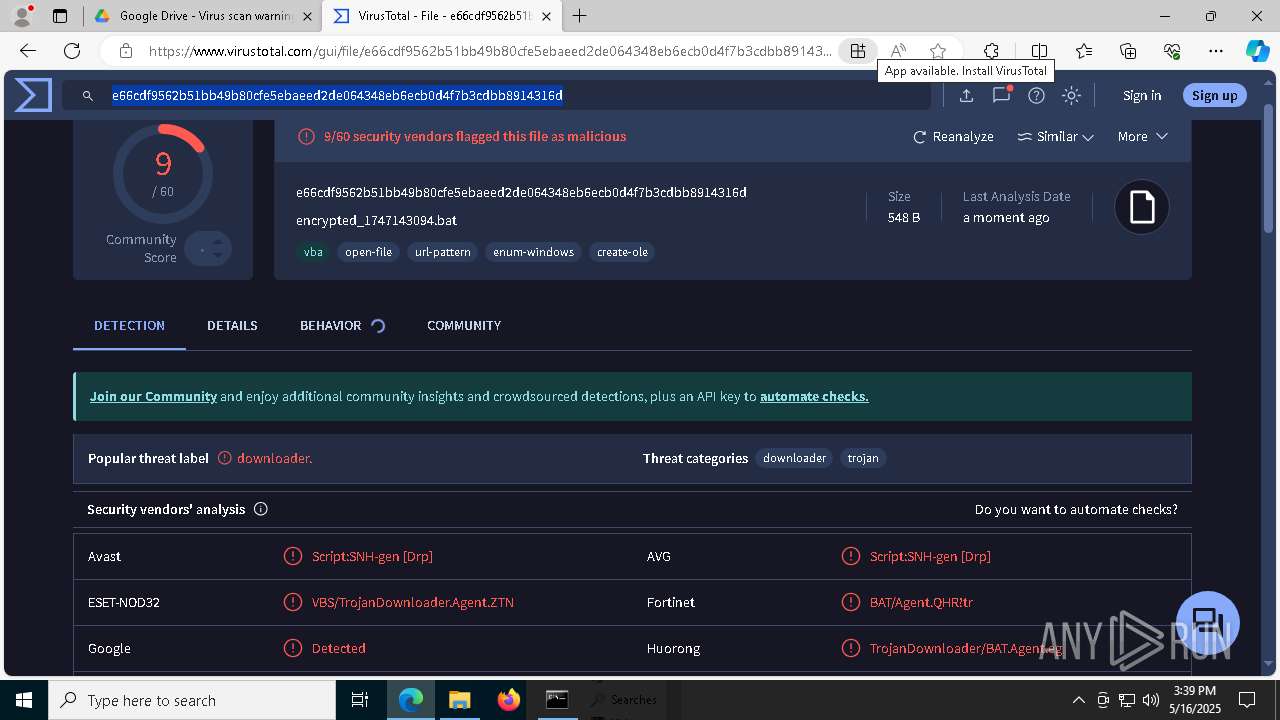
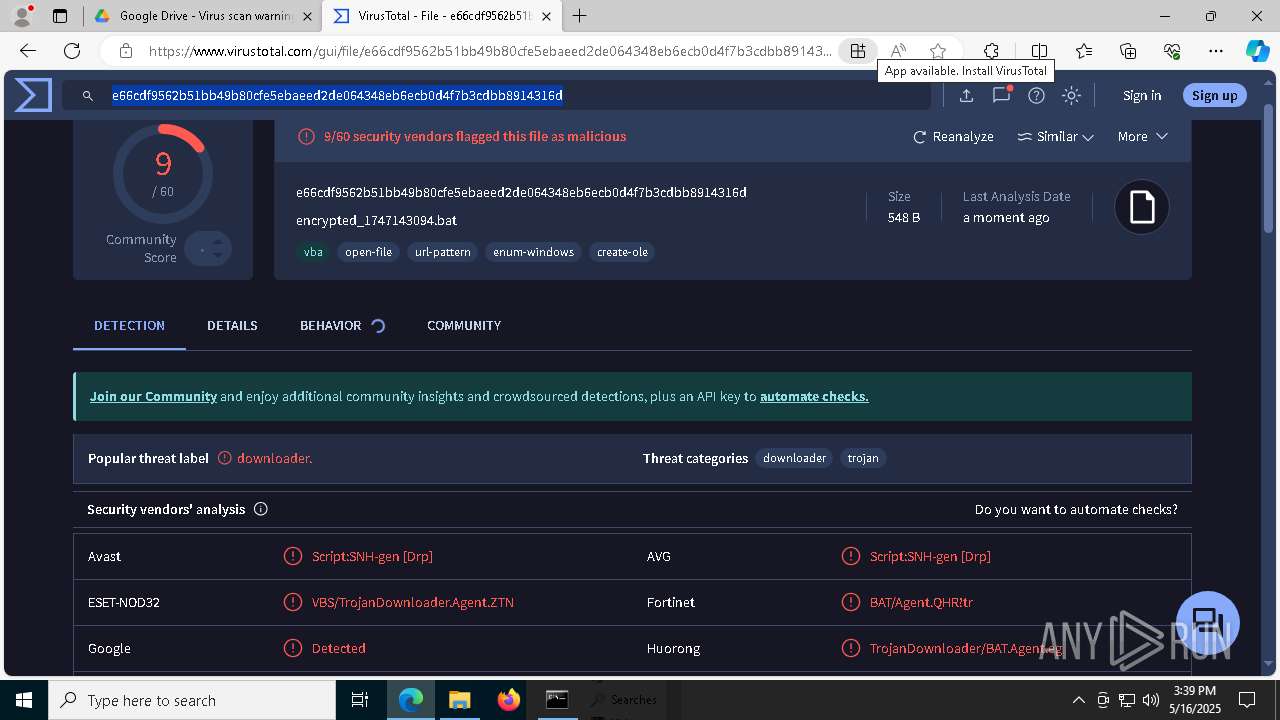
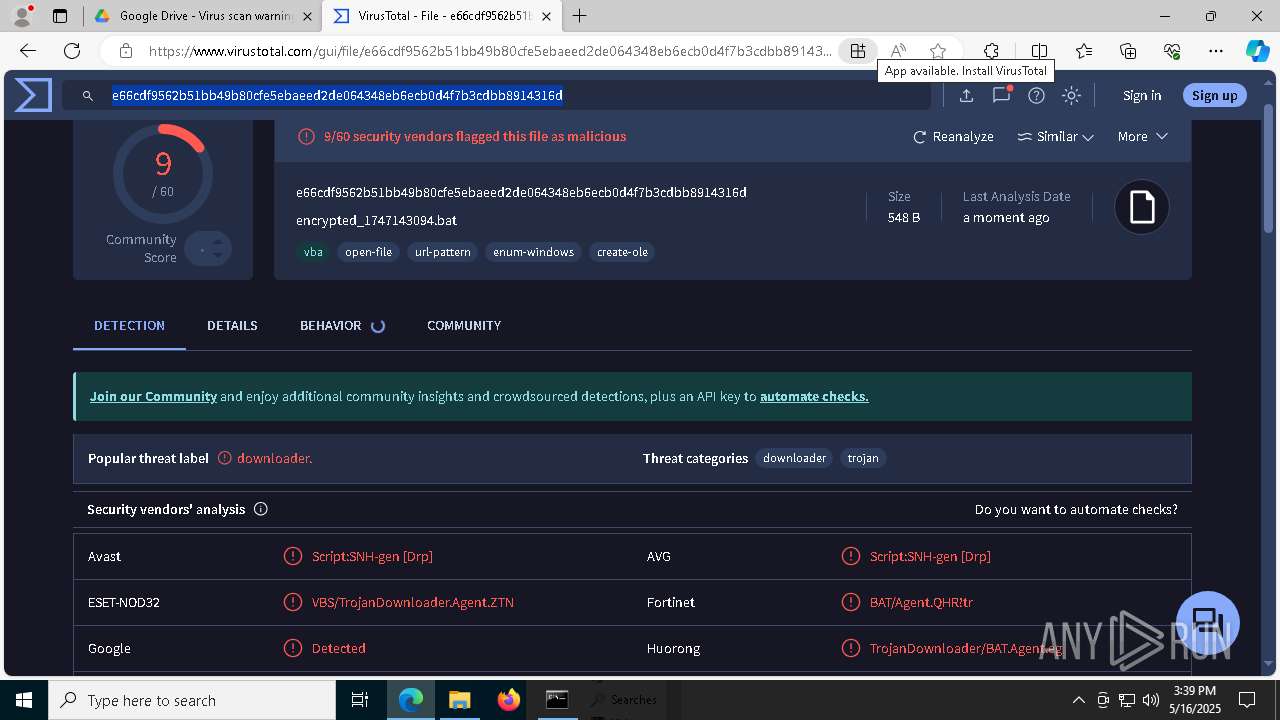
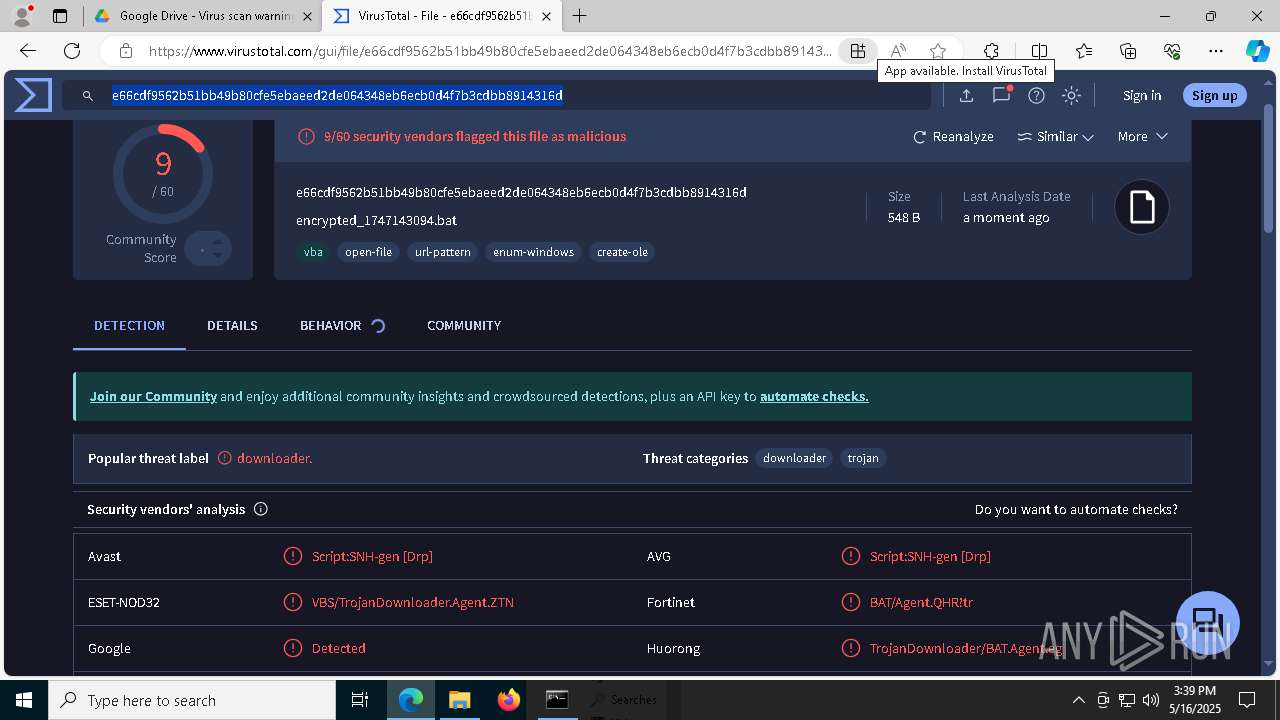
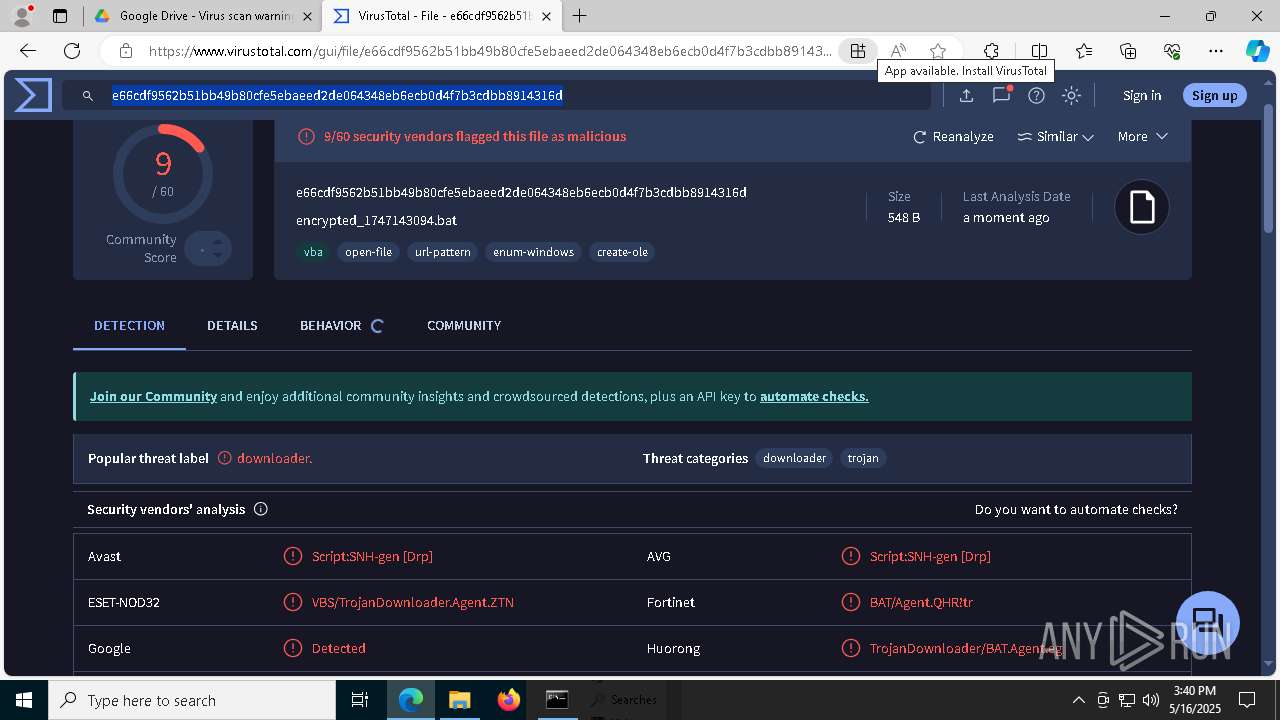
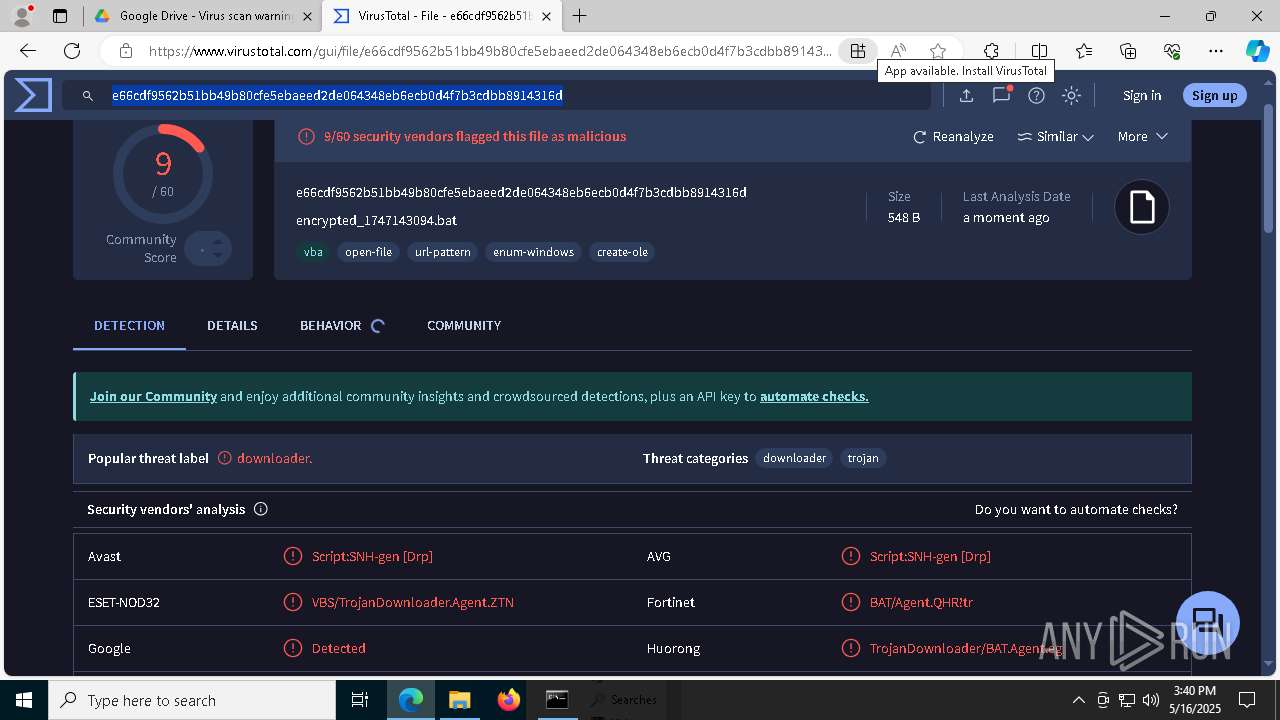
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
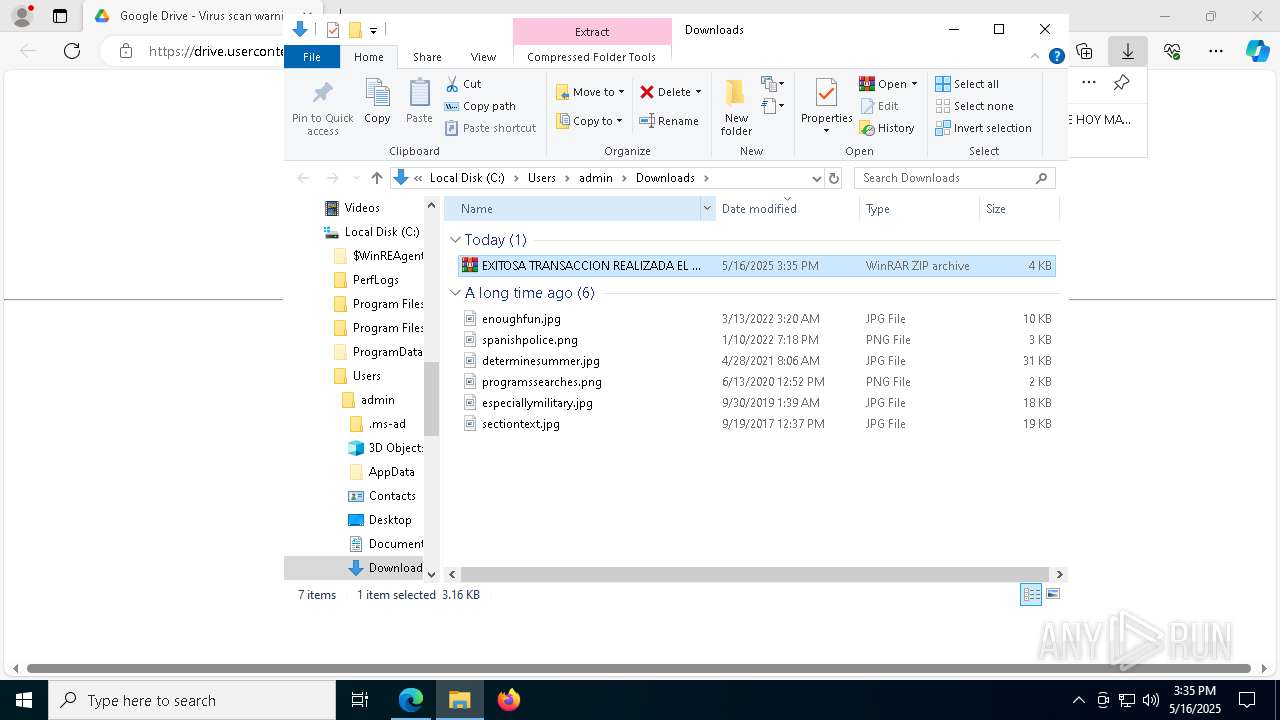
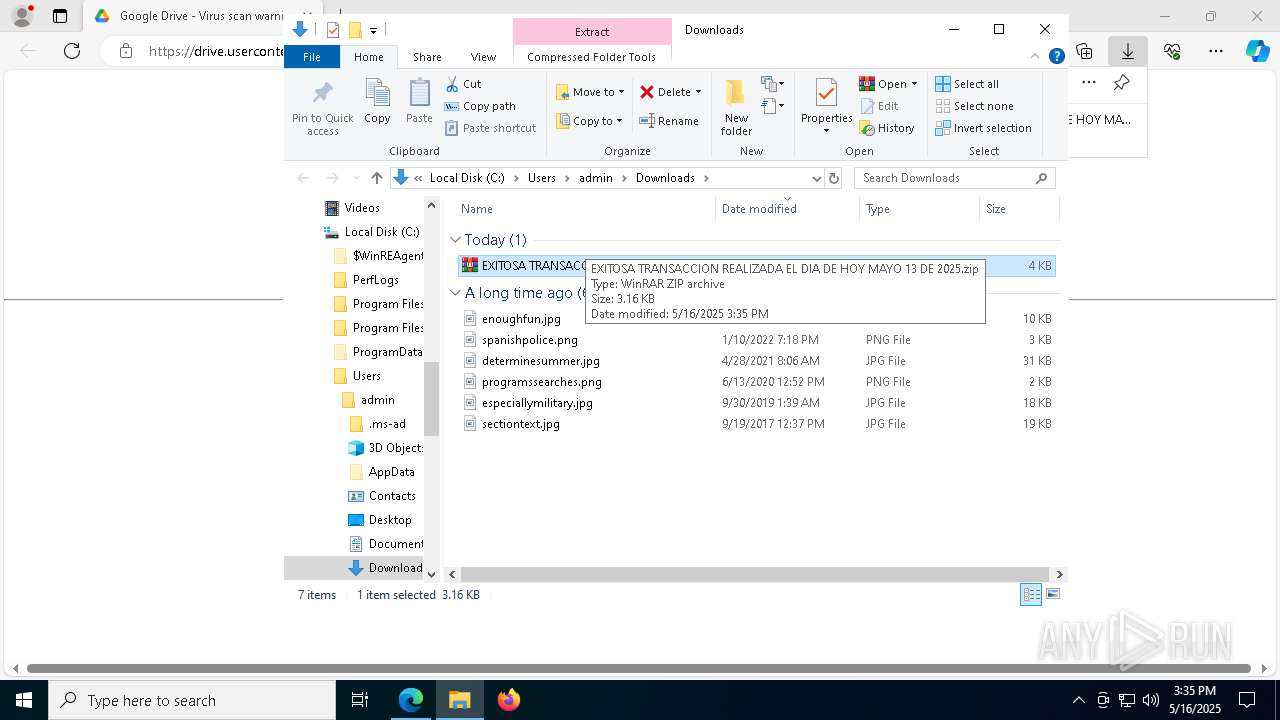
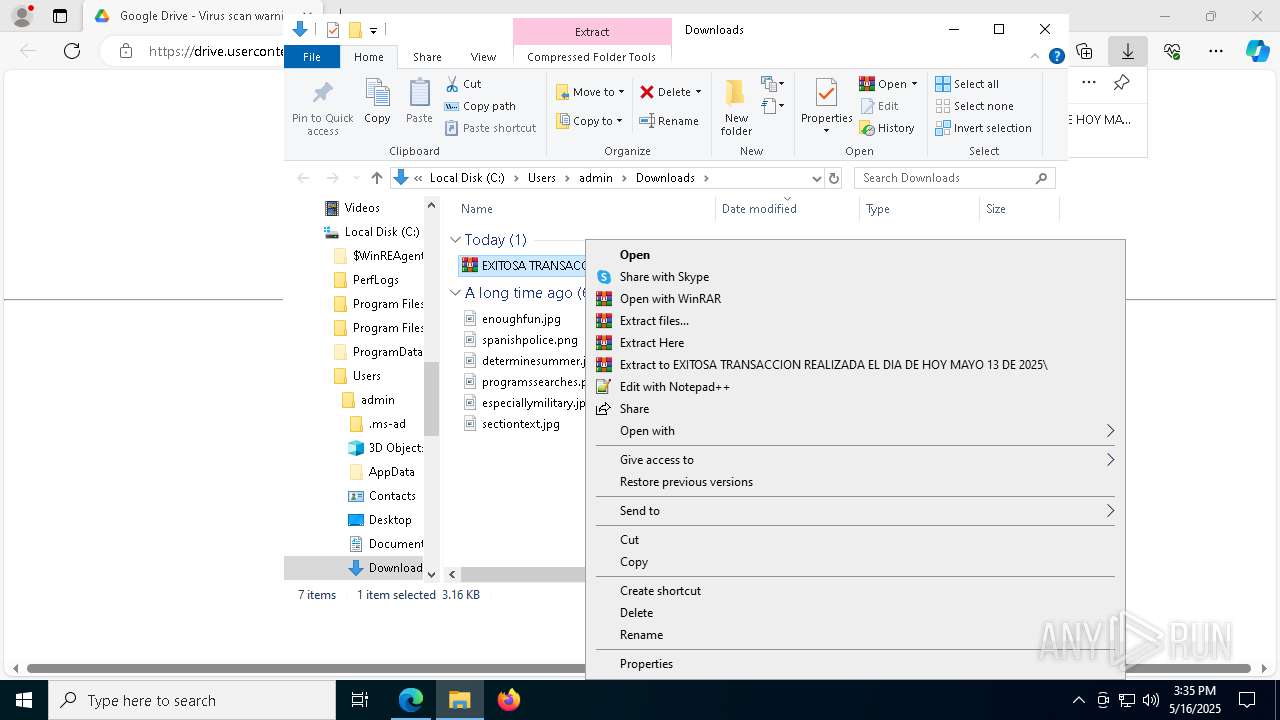
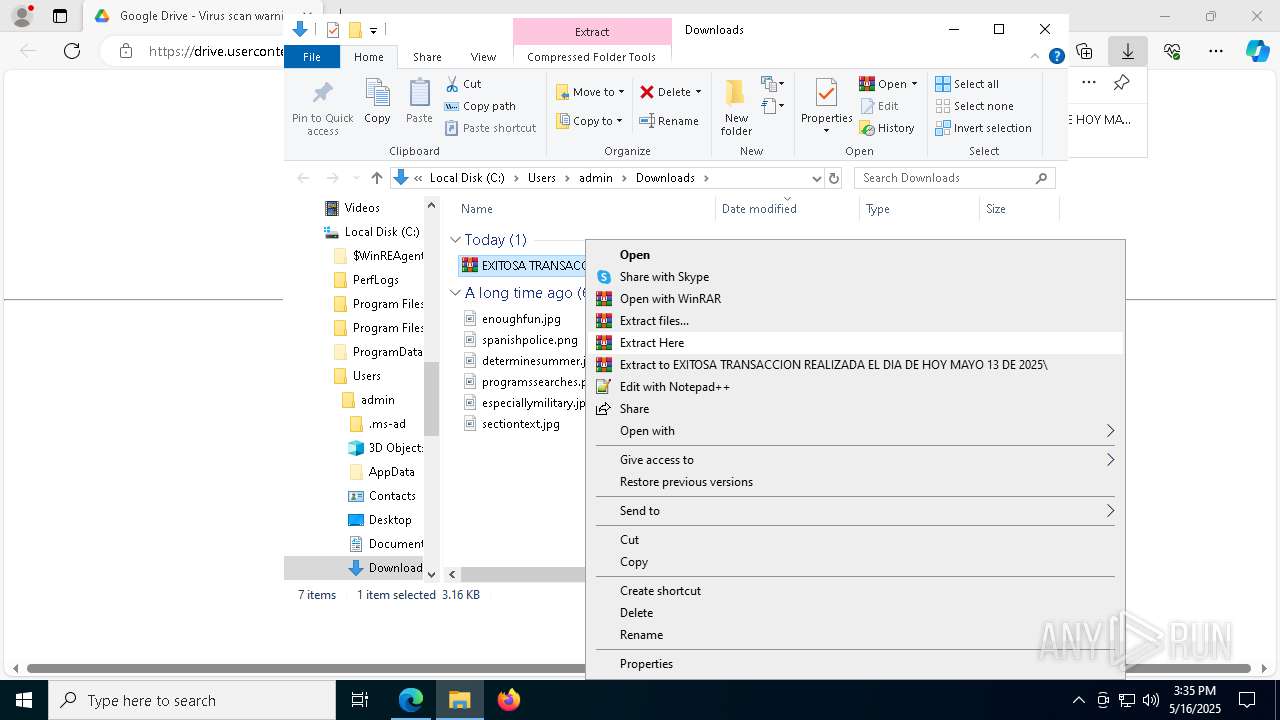
| Analysis date: | May 16, 2025, 15:35:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
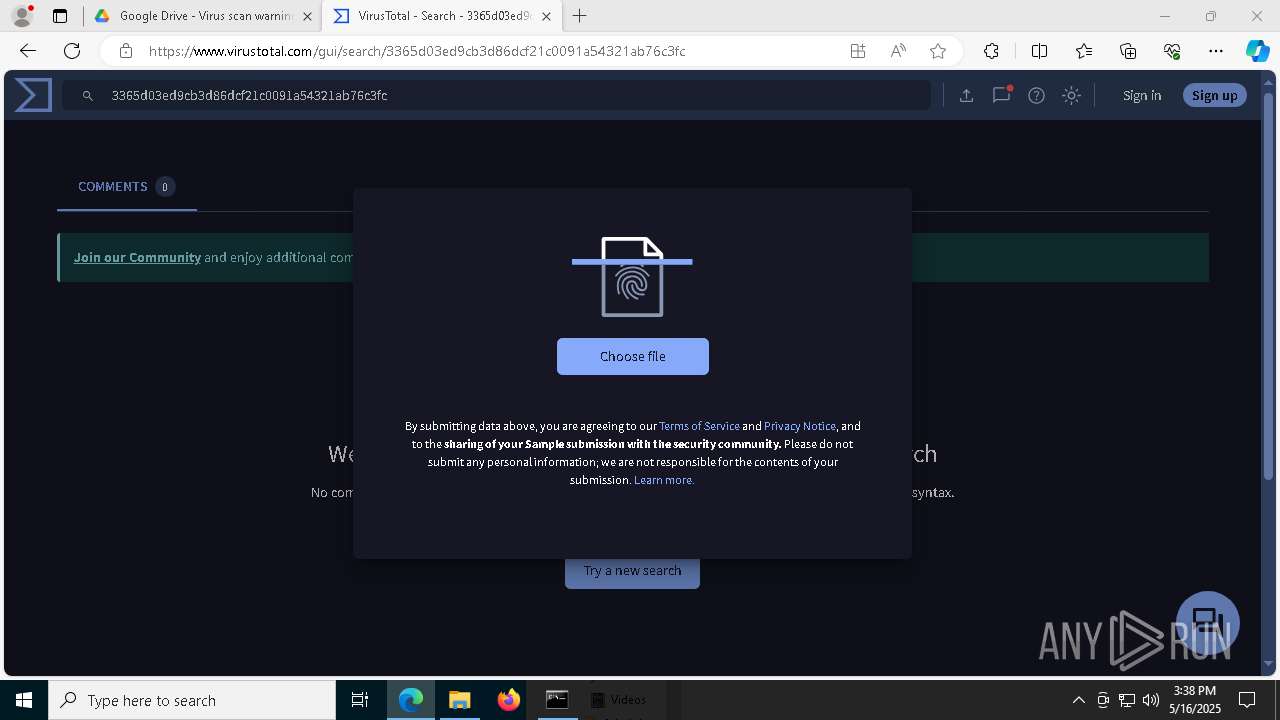
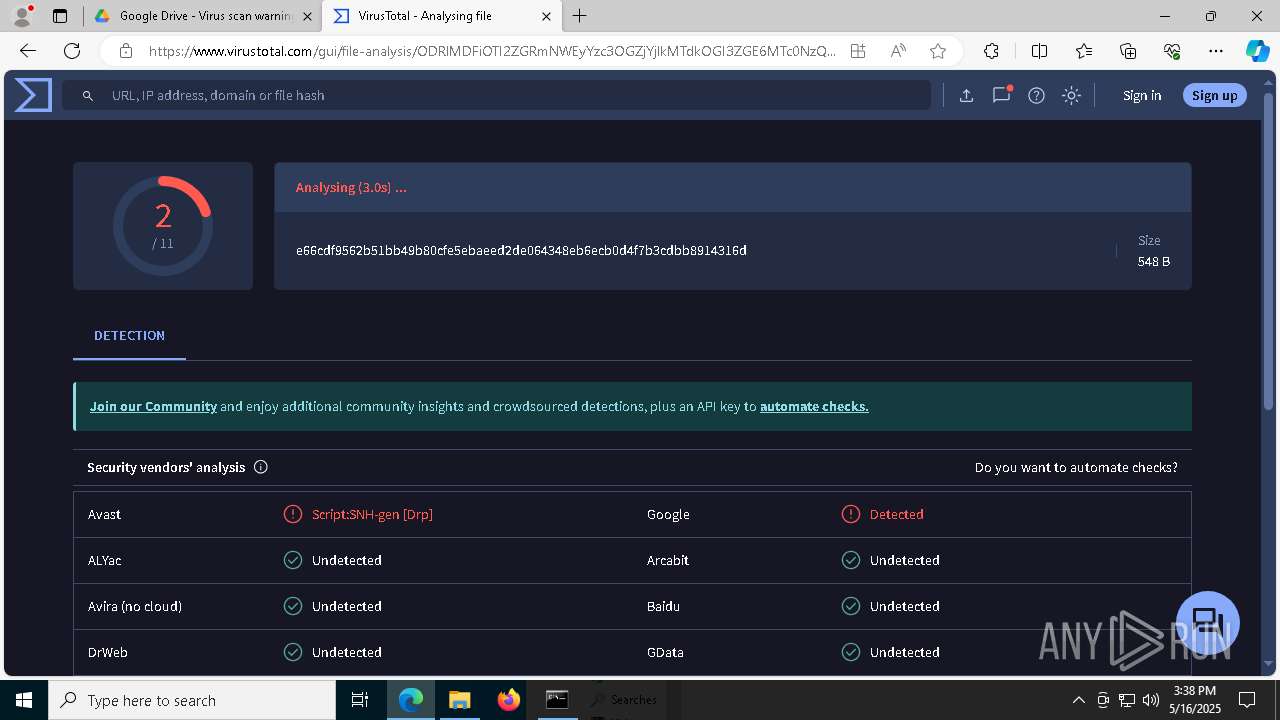
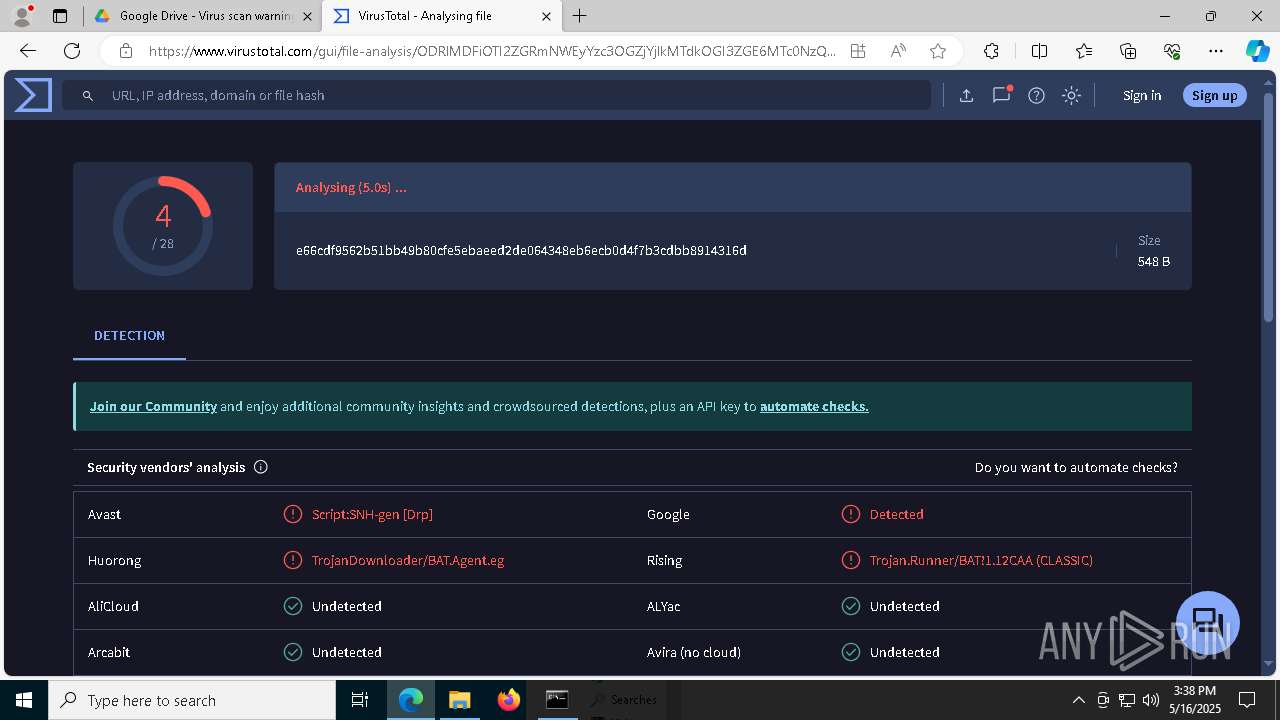
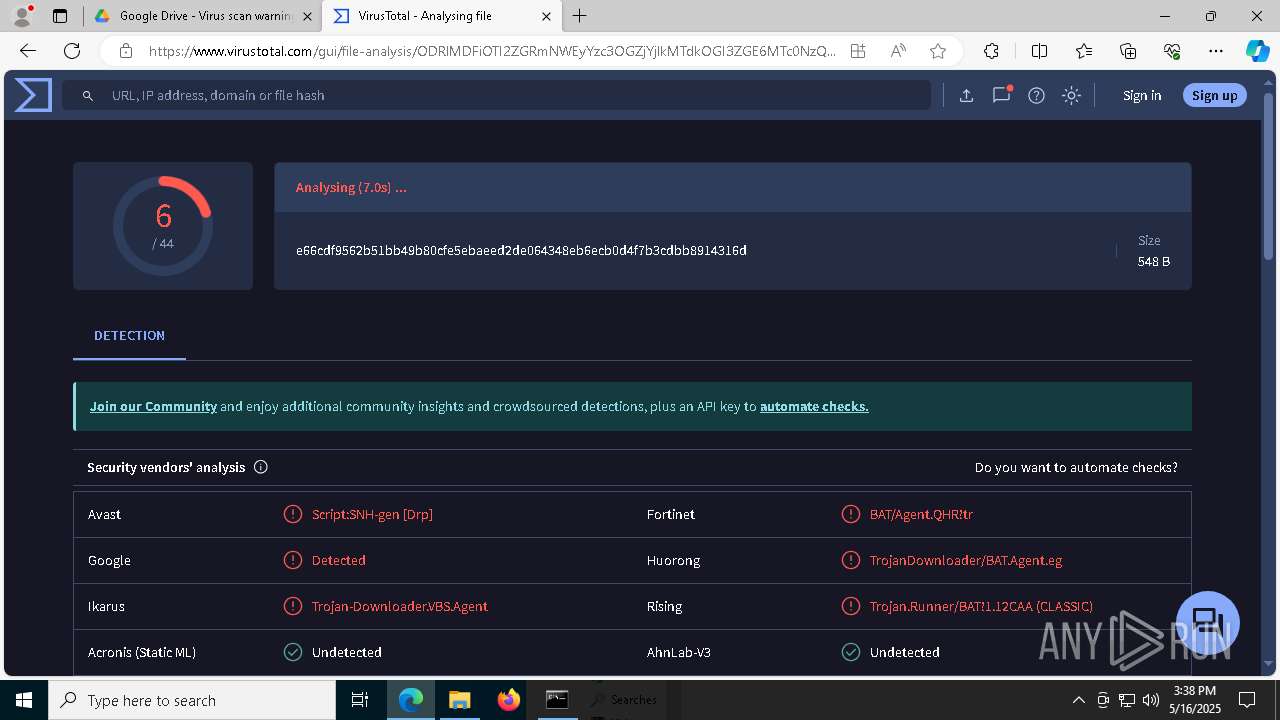
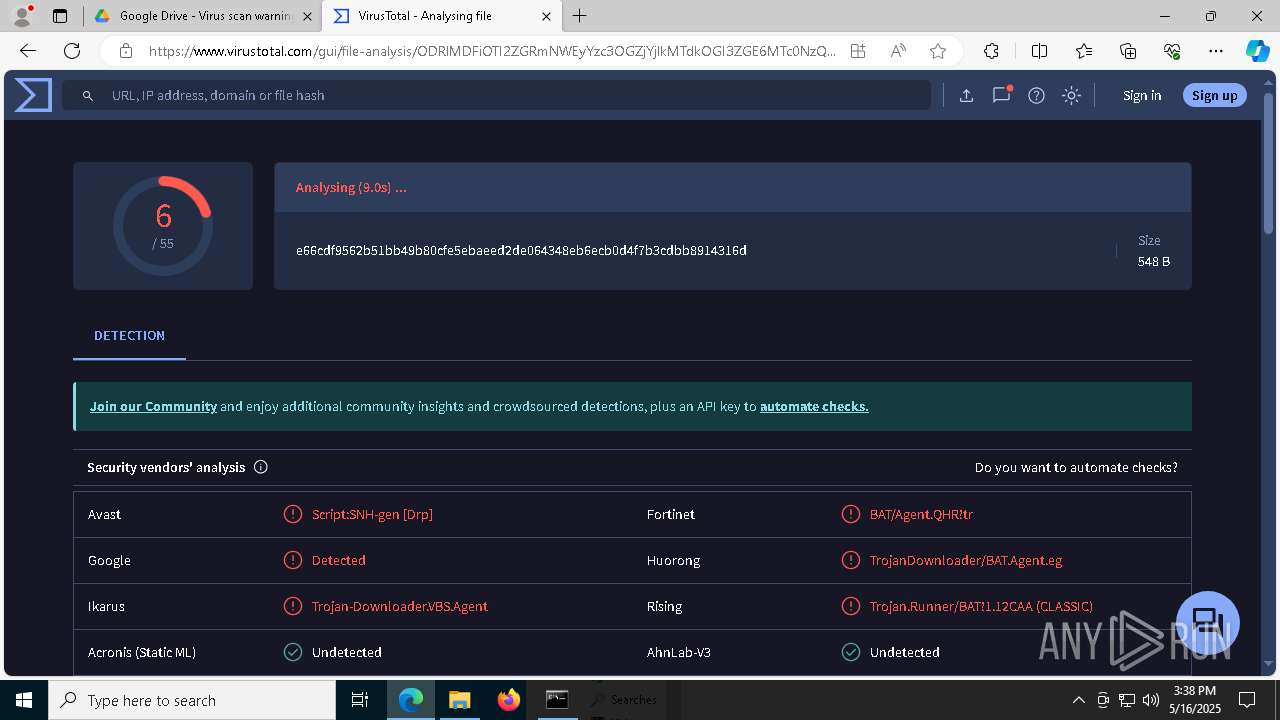
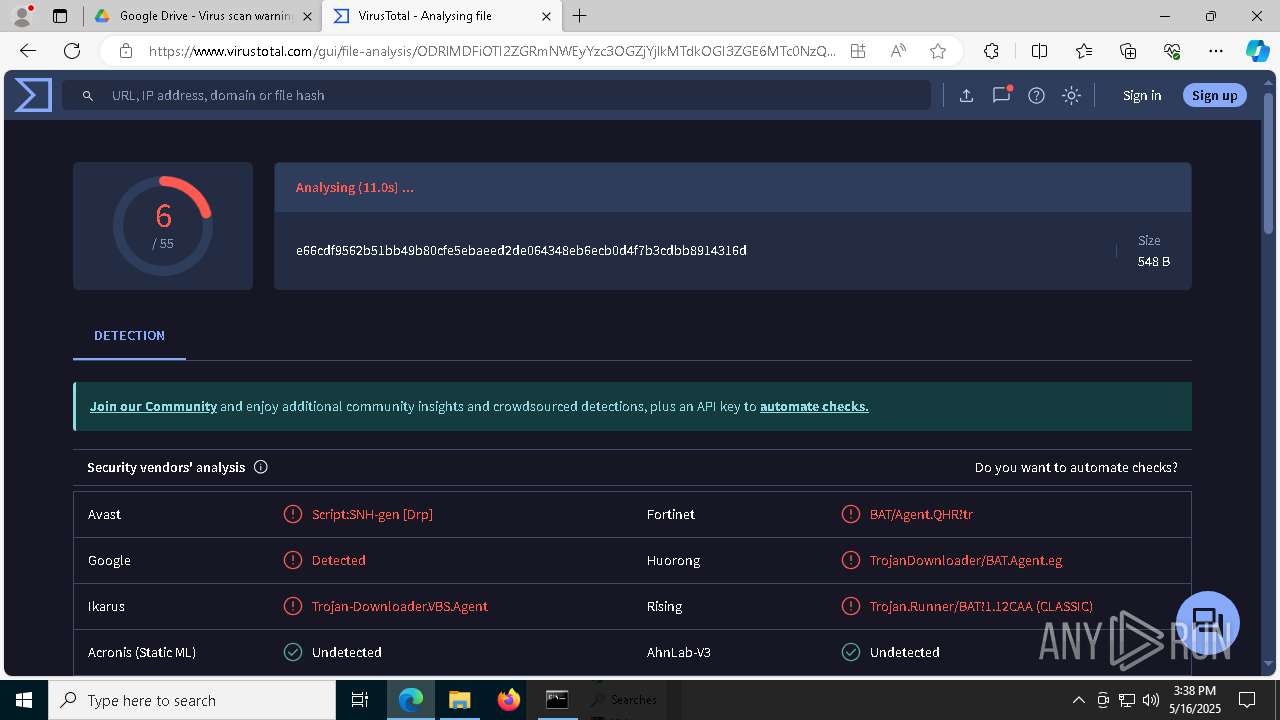
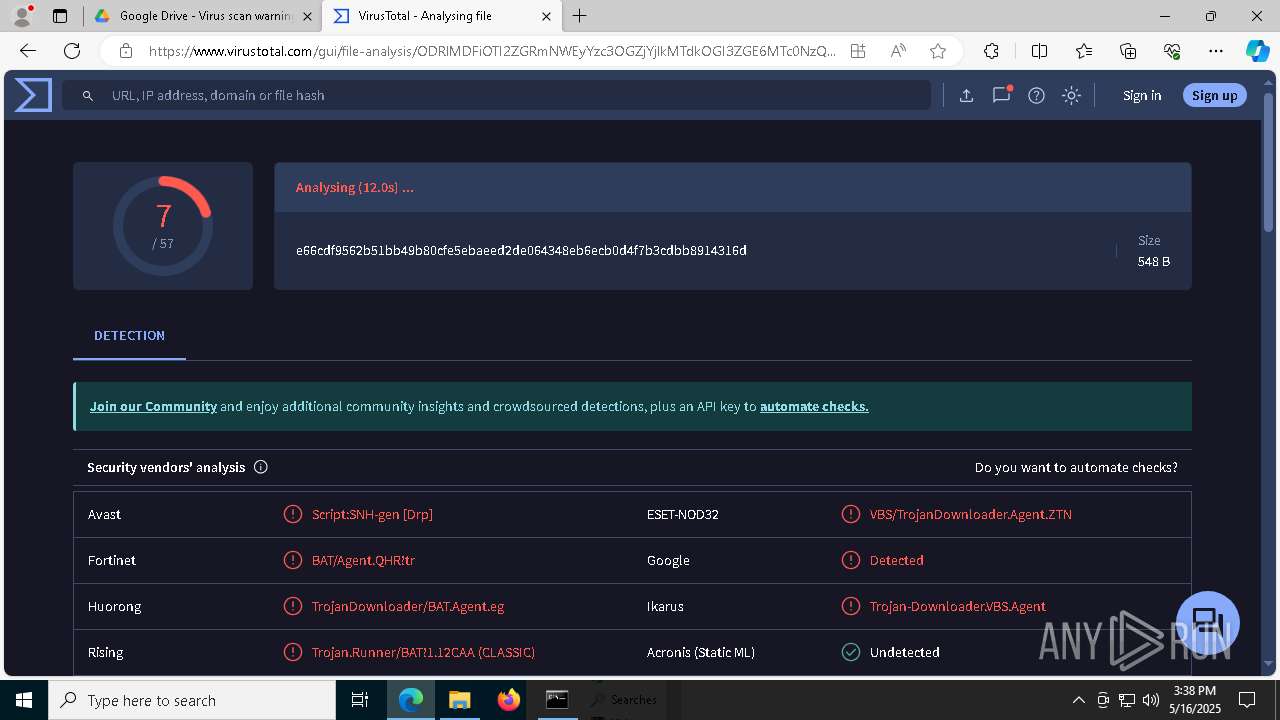
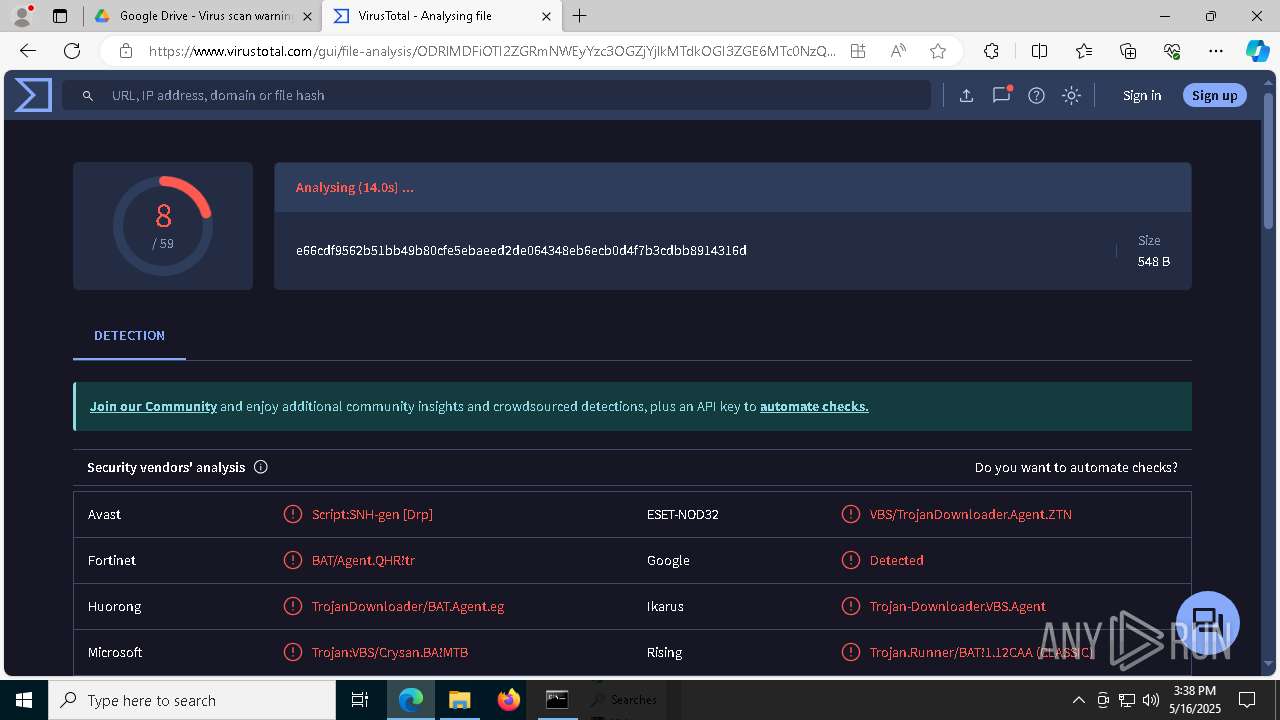
| MD5: | EF9CFA4CFD16C7CC4BBC8757AB88DDF1 |
| SHA1: | EF861DF192AEBC79D8A72BF9DEBB9D5D081ED8C5 |
| SHA256: | 4D3D73B91A01FA15CD9A5008F3FB34B9F73291978780C09B8FE90D797DB9E402 |
| SSDEEP: | 3:N8SP3u2NAaBrC2D21wLoFWW:2Sm2BB+2q1wMl |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 1328)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 1328)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 1328)
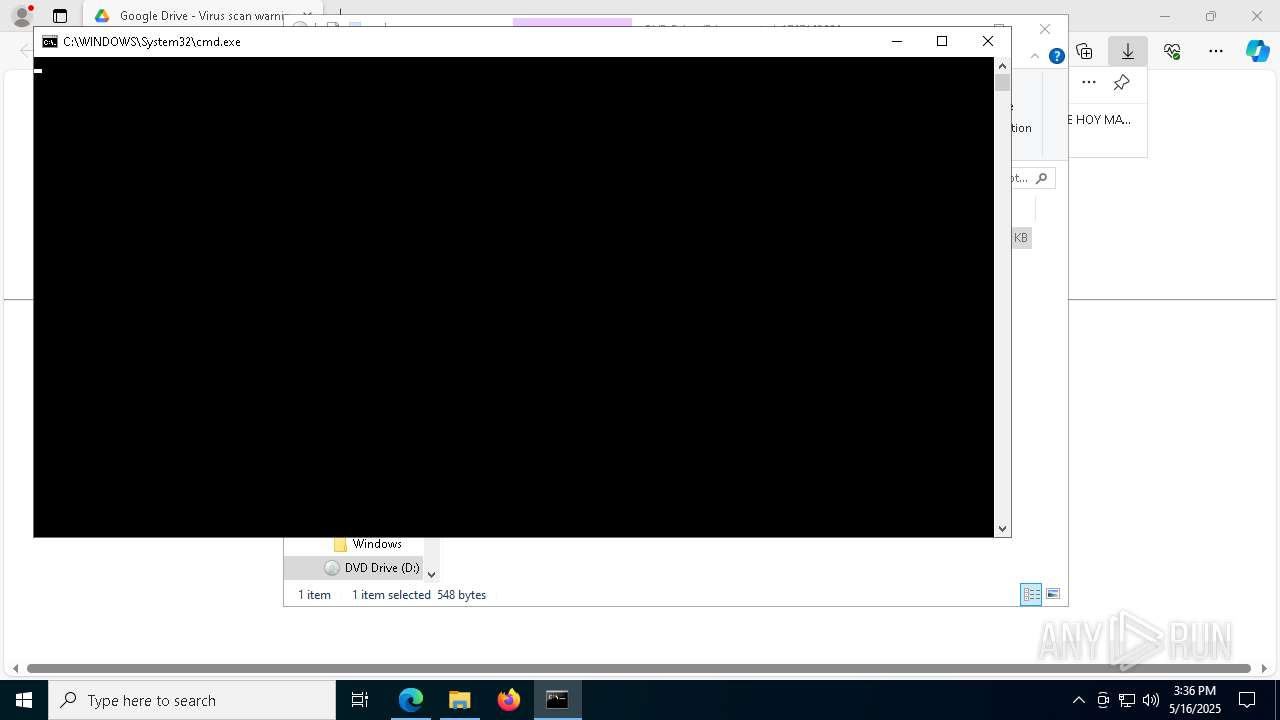
Run PowerShell with an invisible window
- powershell.exe (PID: 3396)
- powershell.exe (PID: 5200)
ASYNCRAT has been detected (SURICATA)
- aspnet_regsql.exe (PID: 5508)
ASYNCRAT has been detected (YARA)
- aspnet_regsql.exe (PID: 5508)
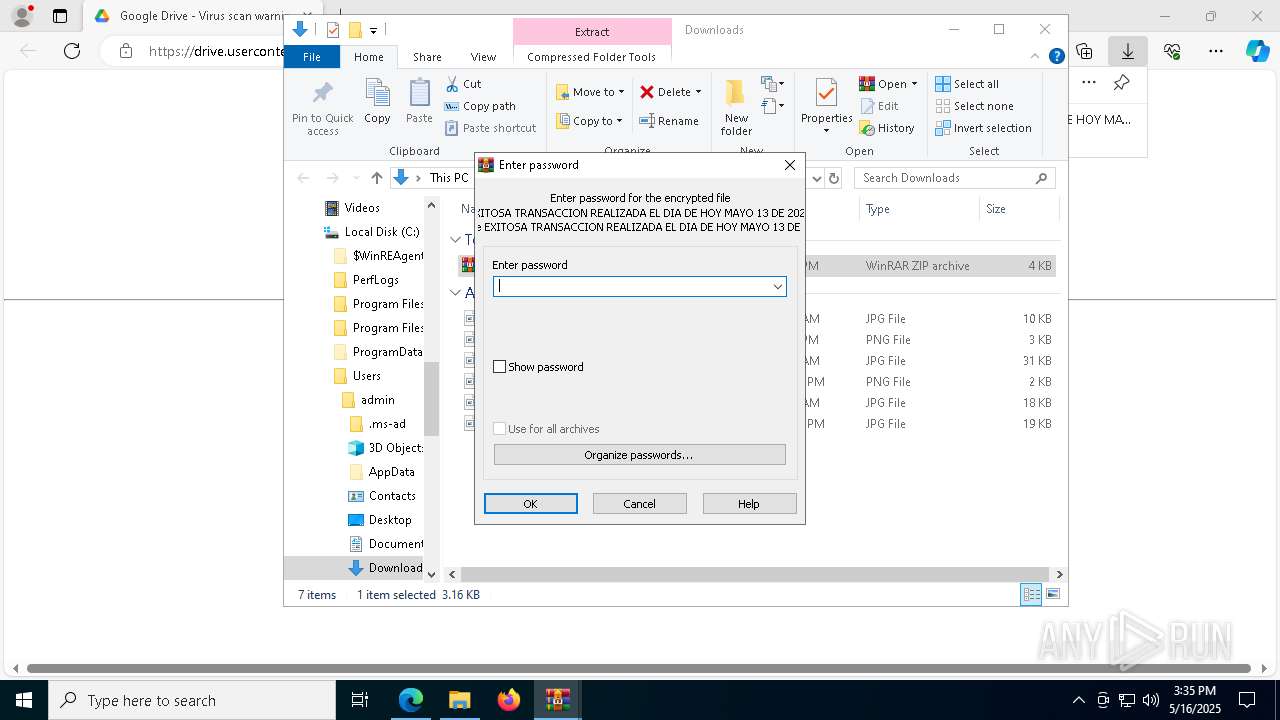
SUSPICIOUS
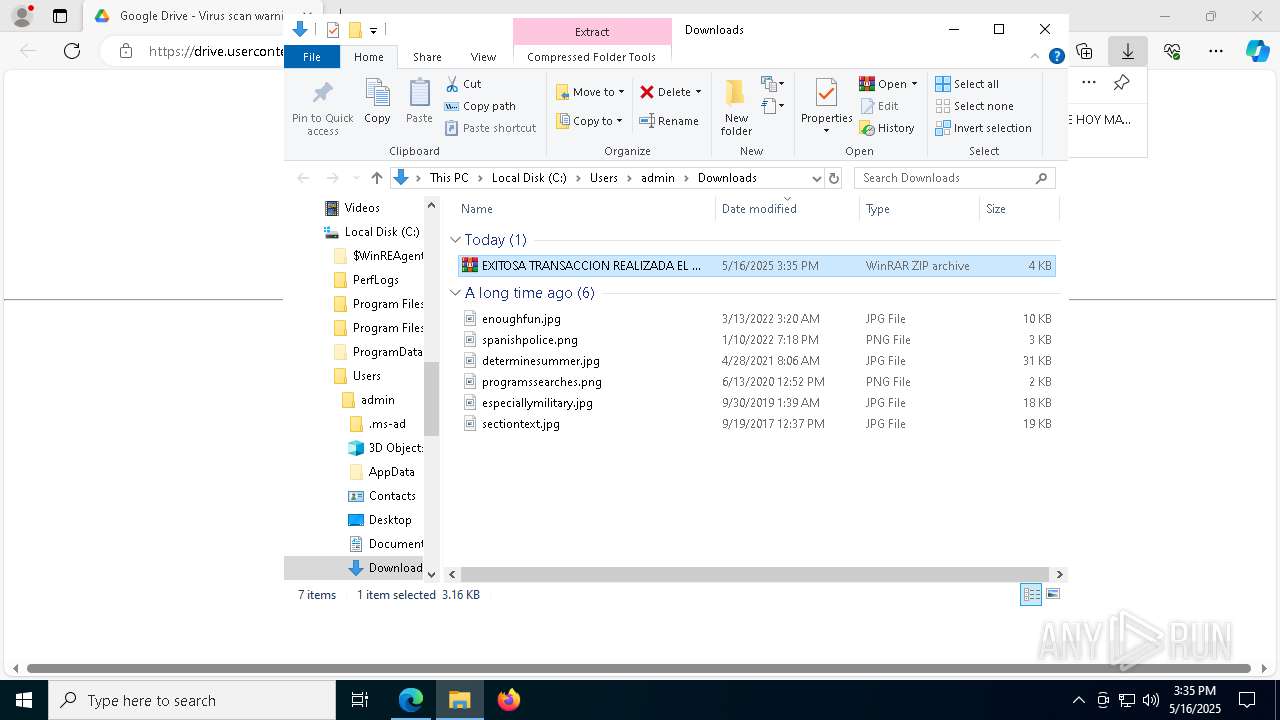
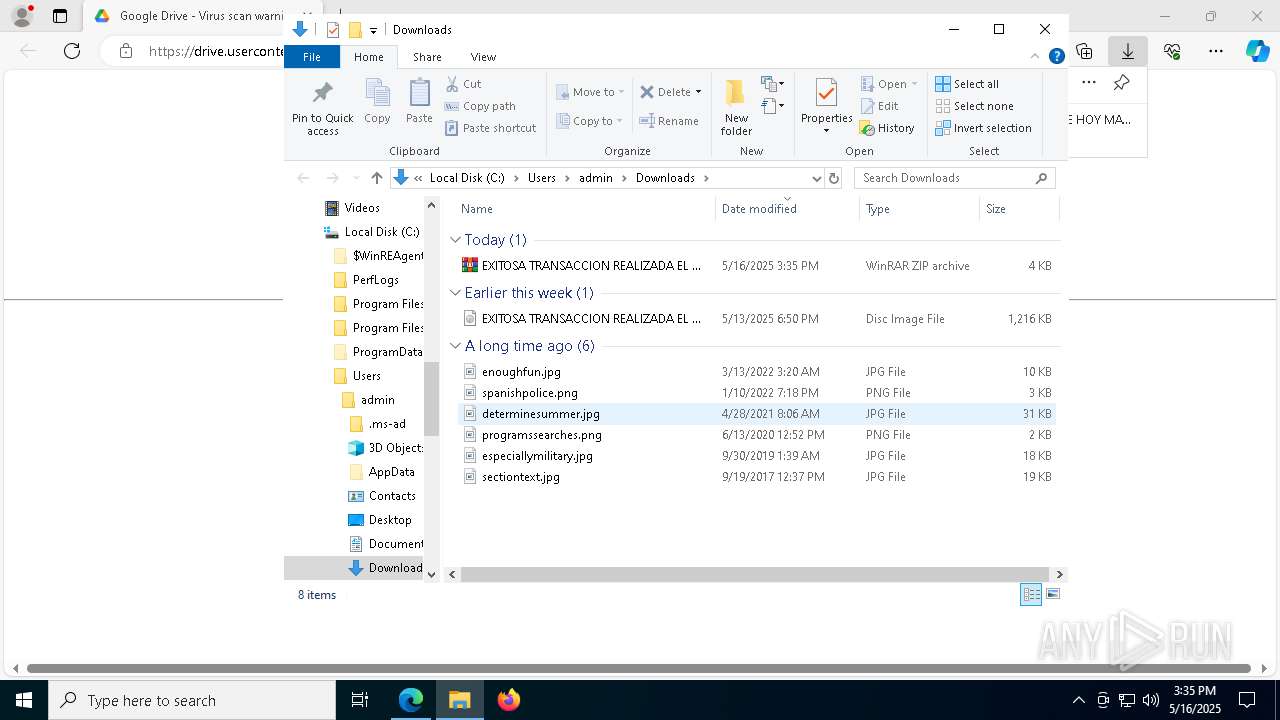
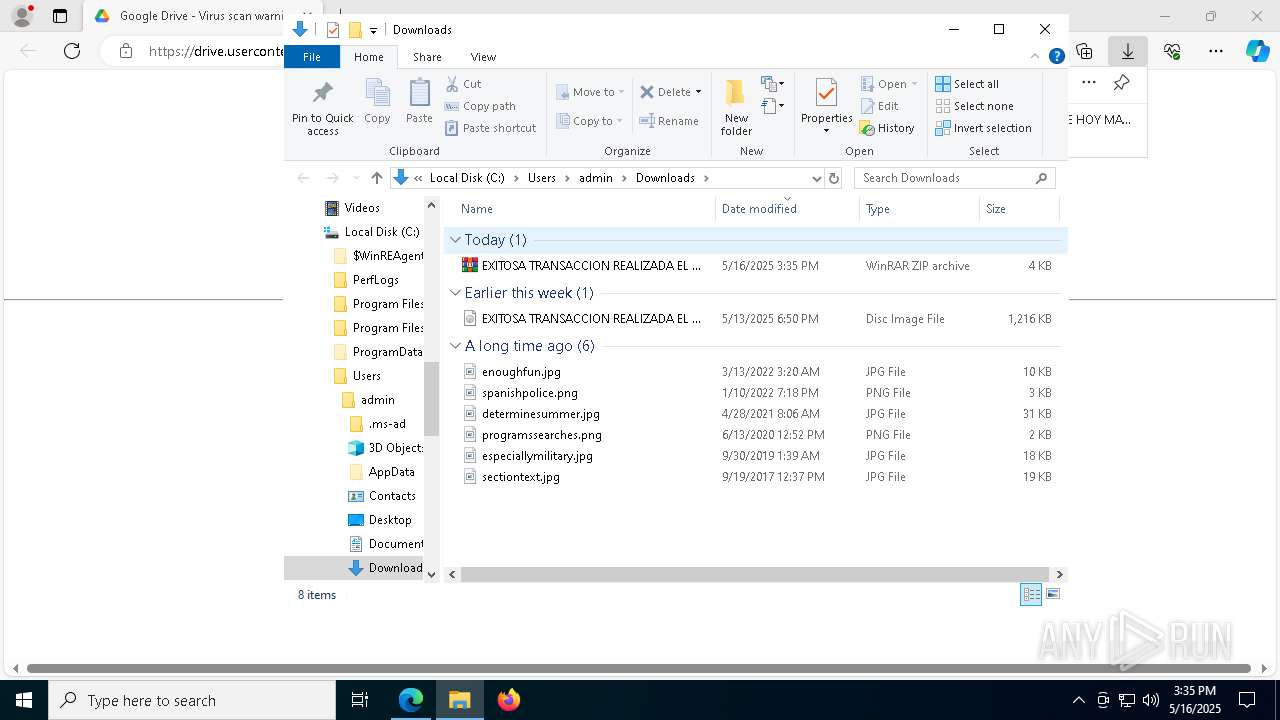
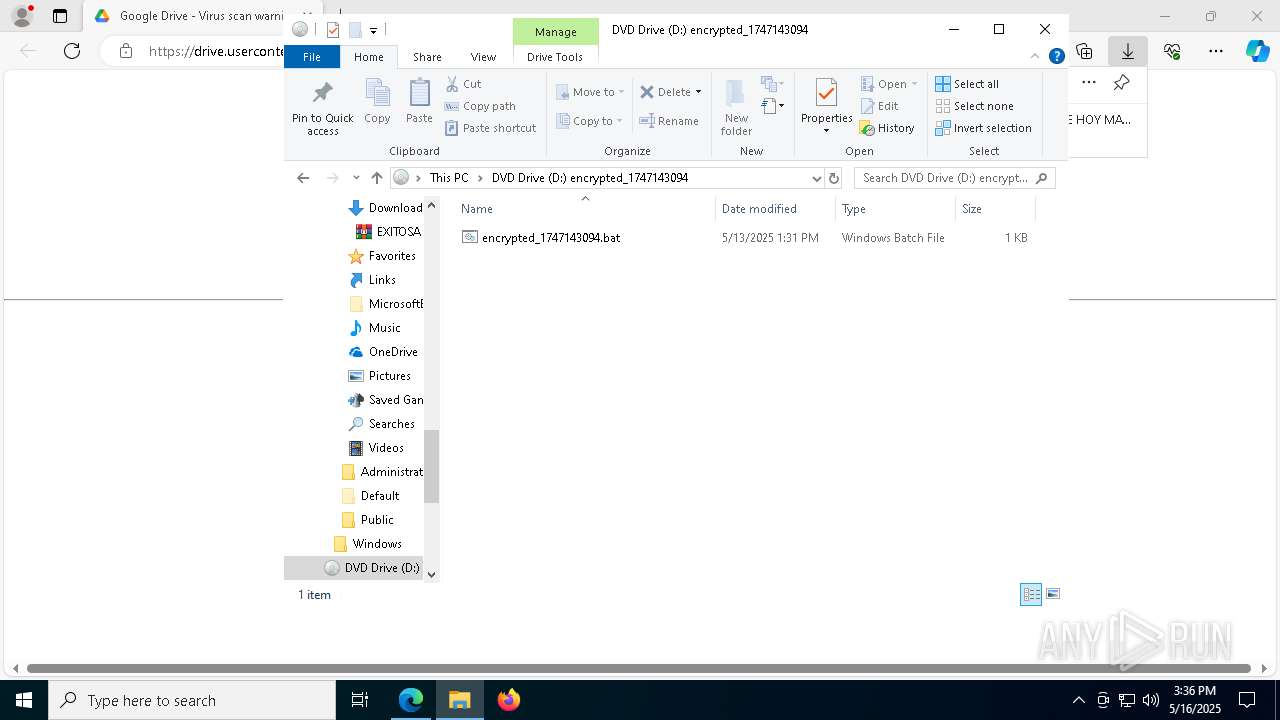
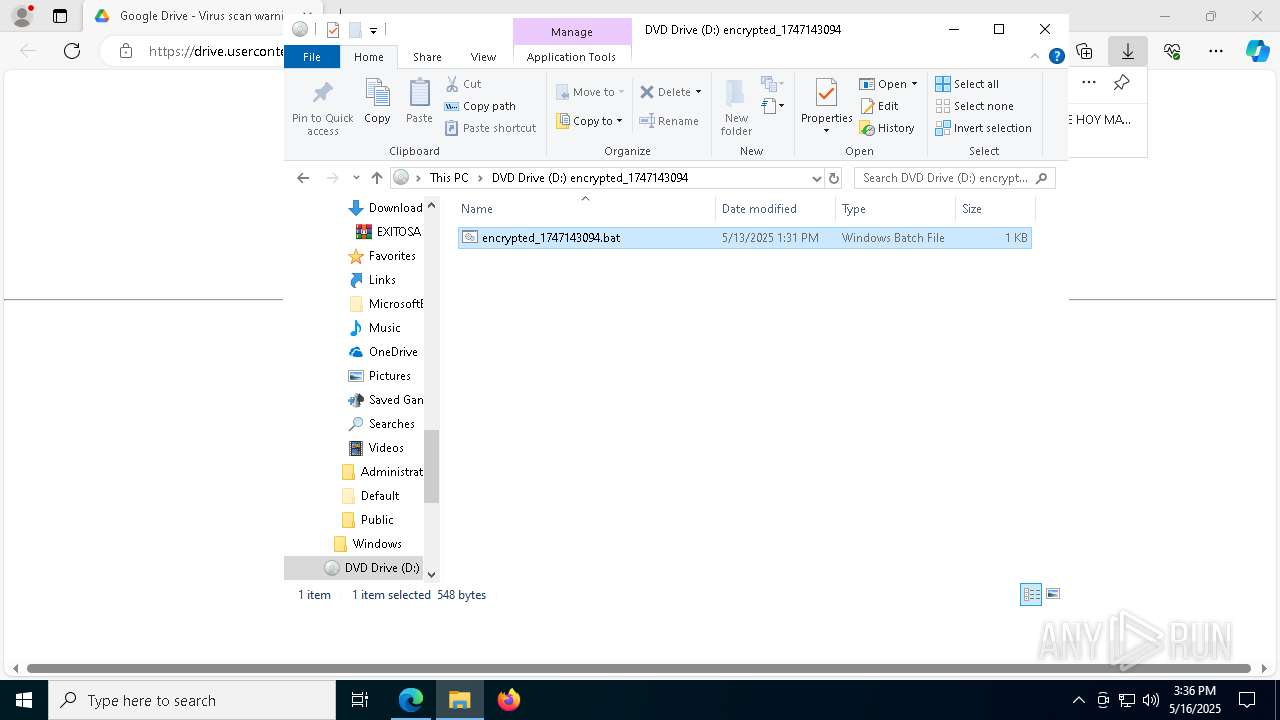
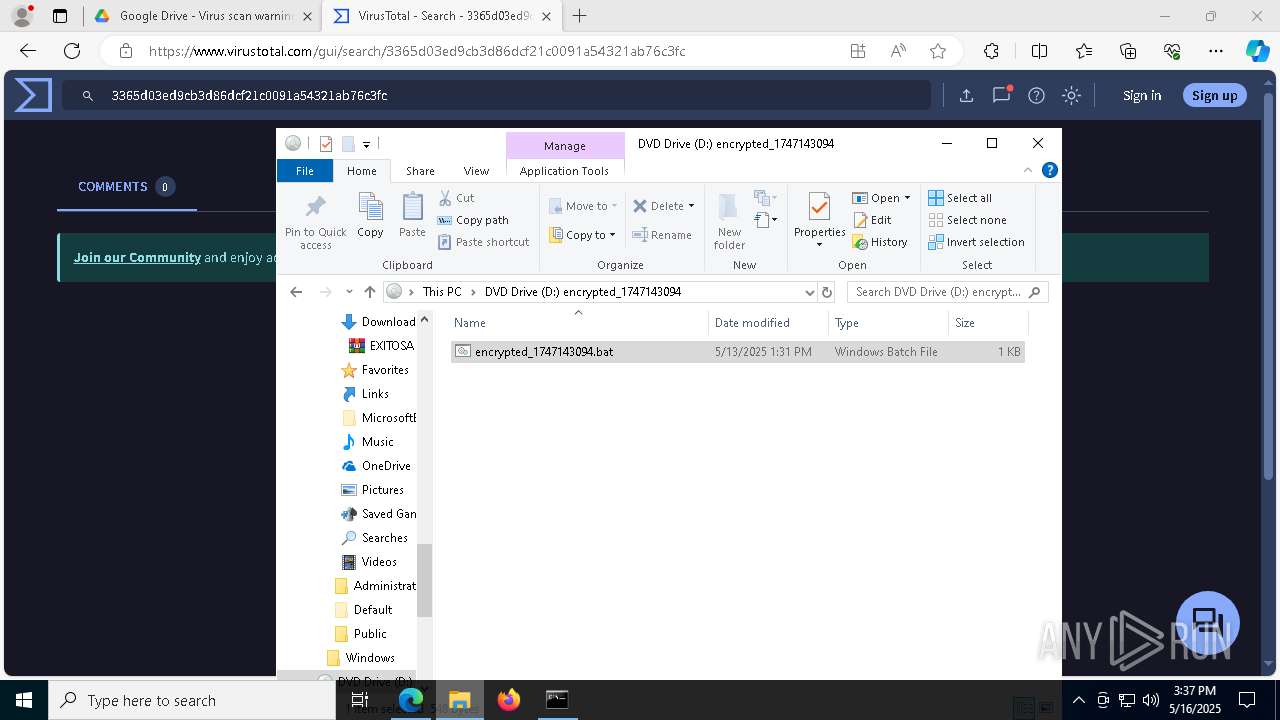
Creates file in the systems drive root
- explorer.exe (PID: 5492)
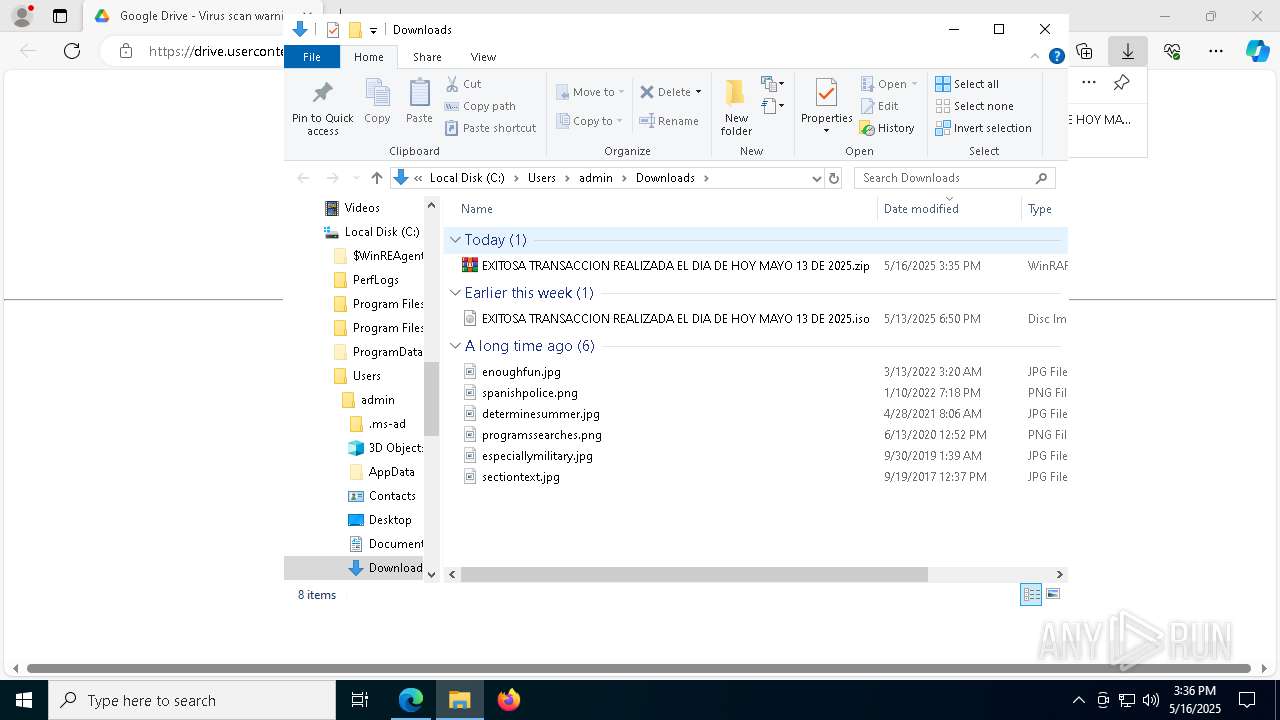
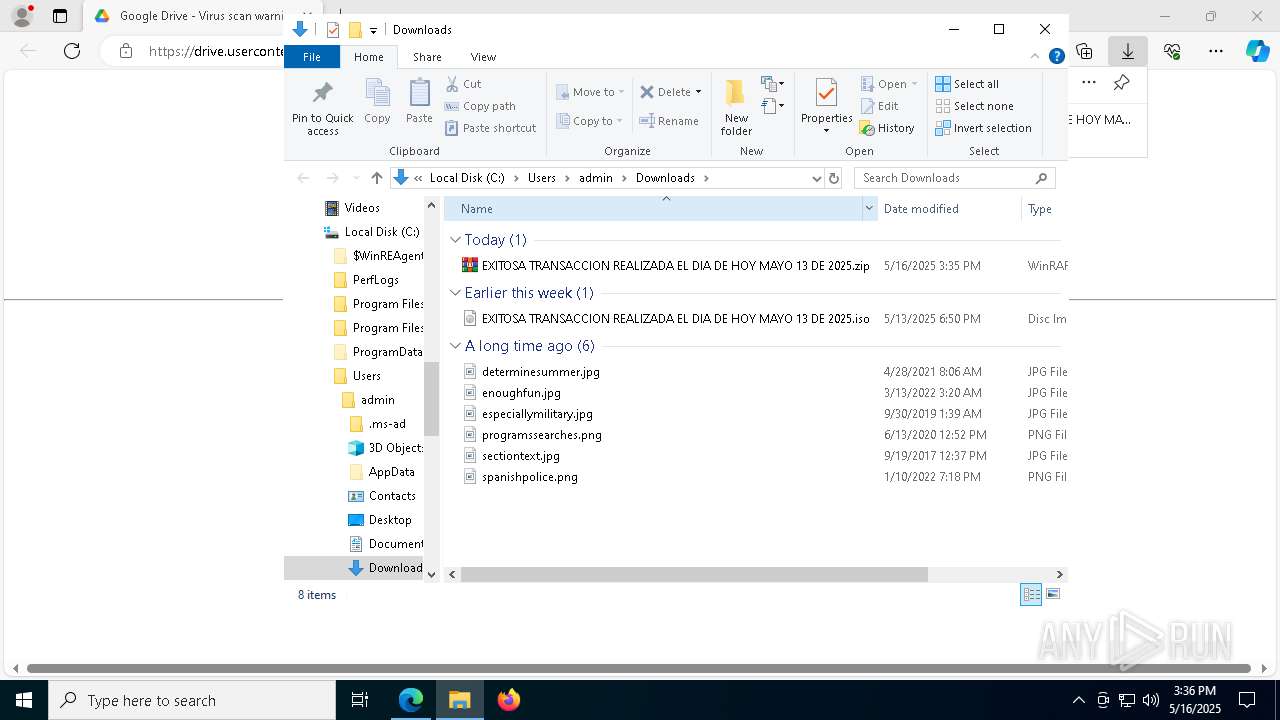
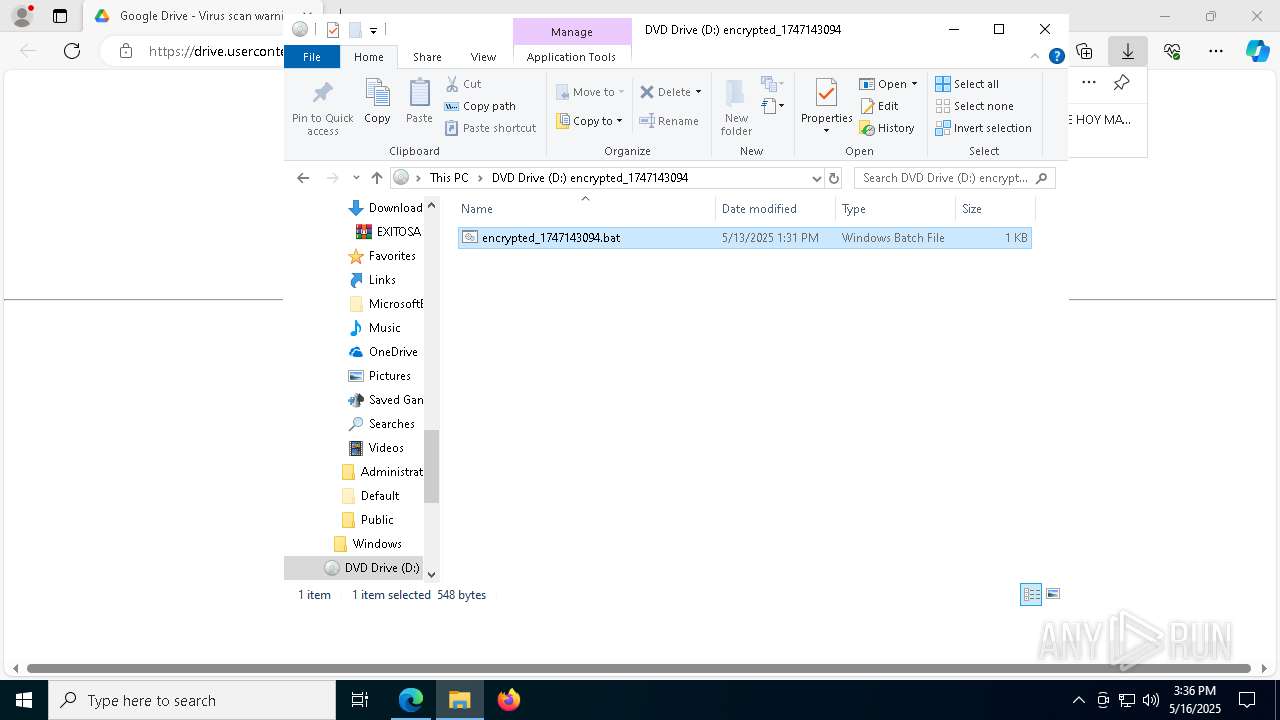
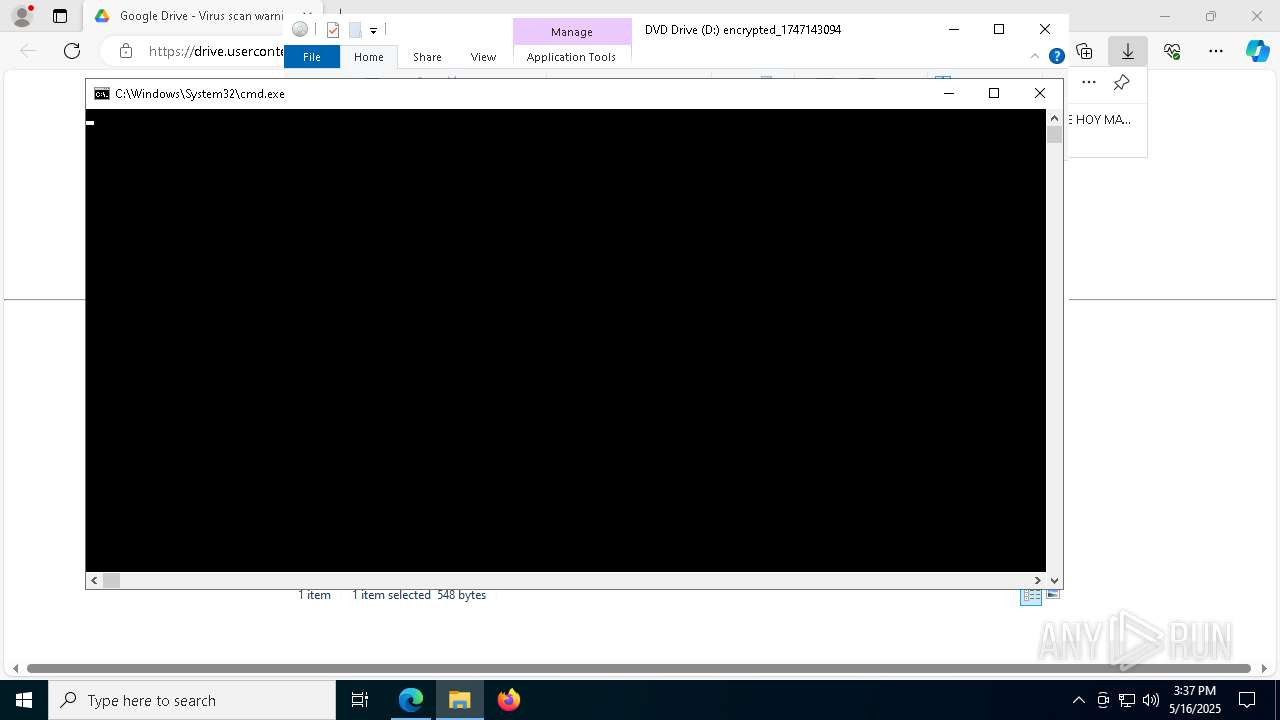
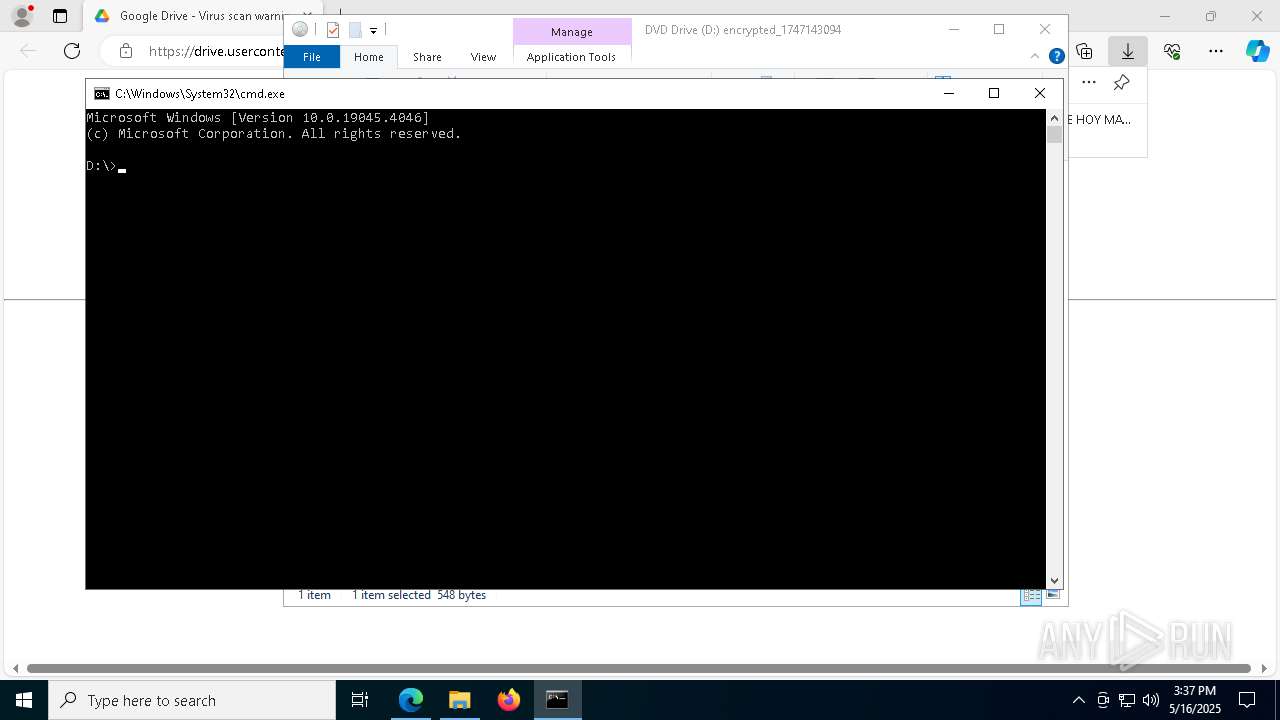
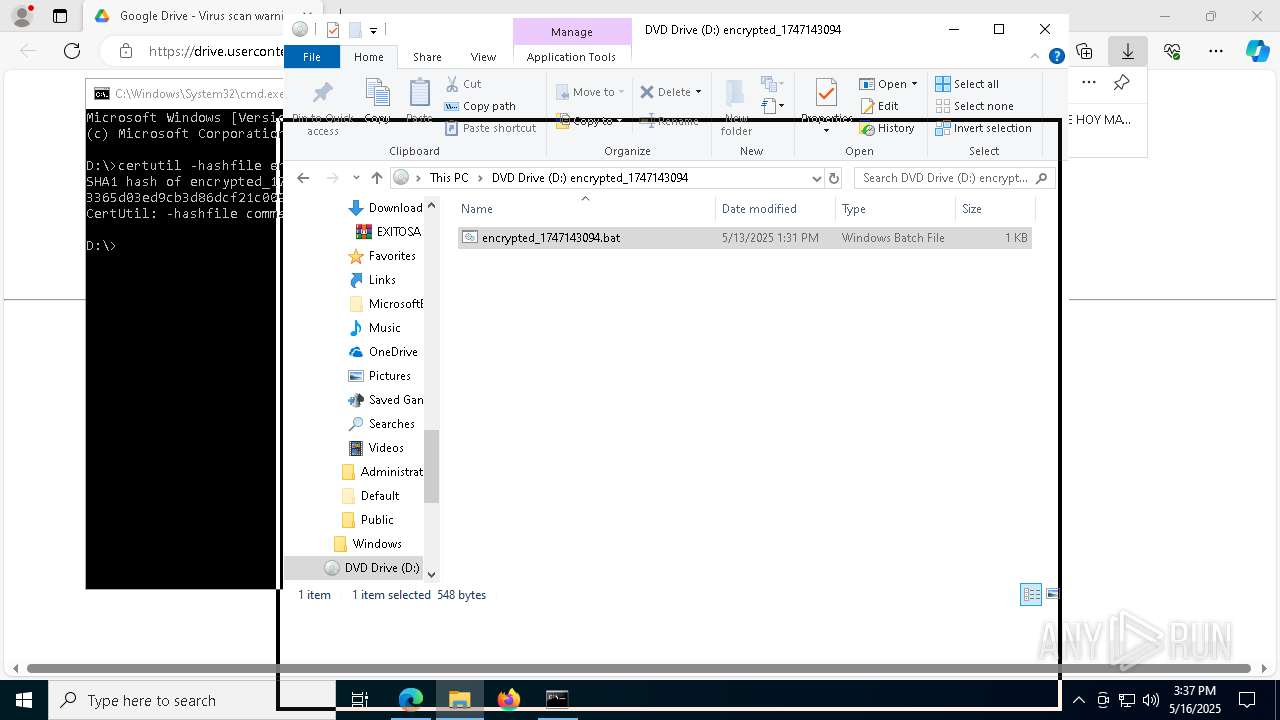
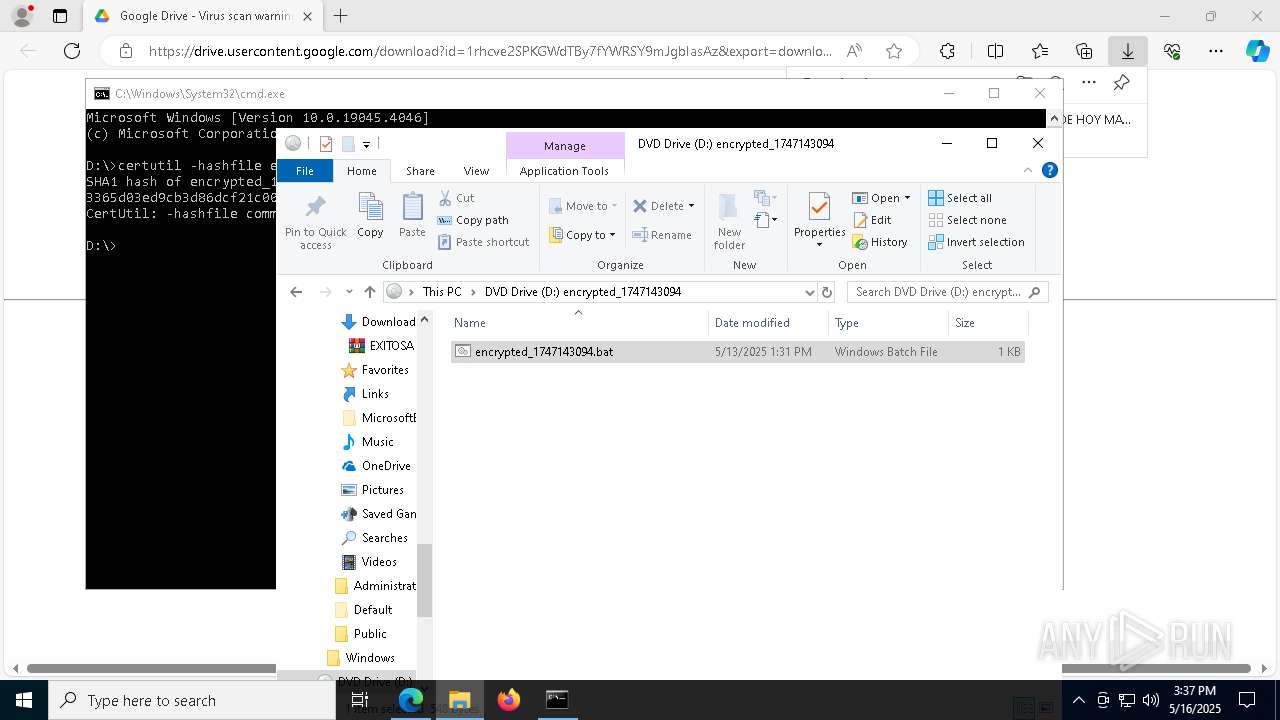
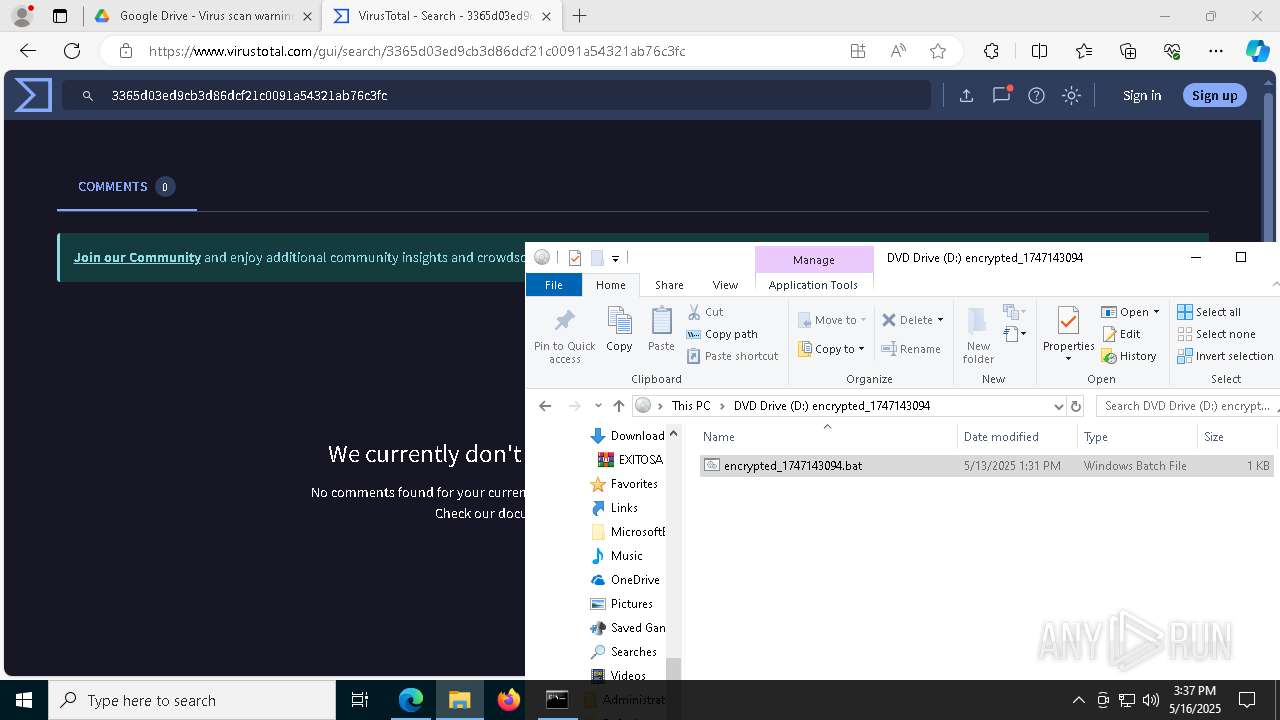
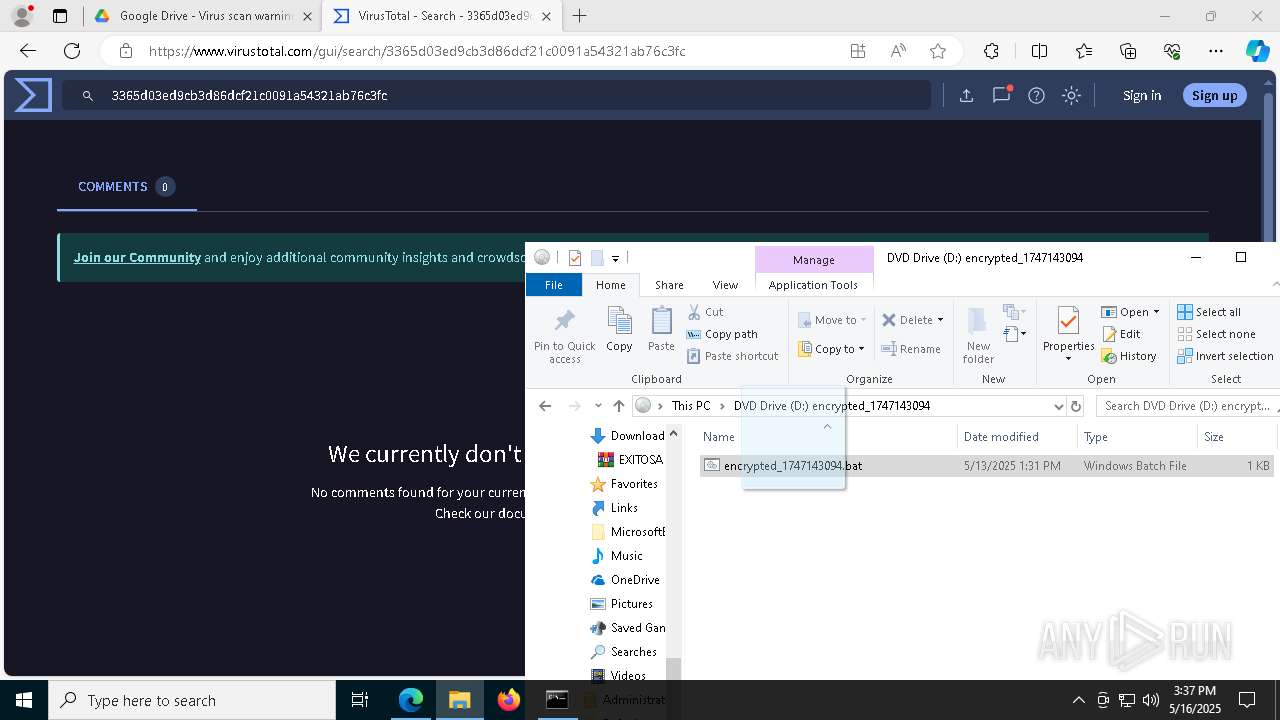
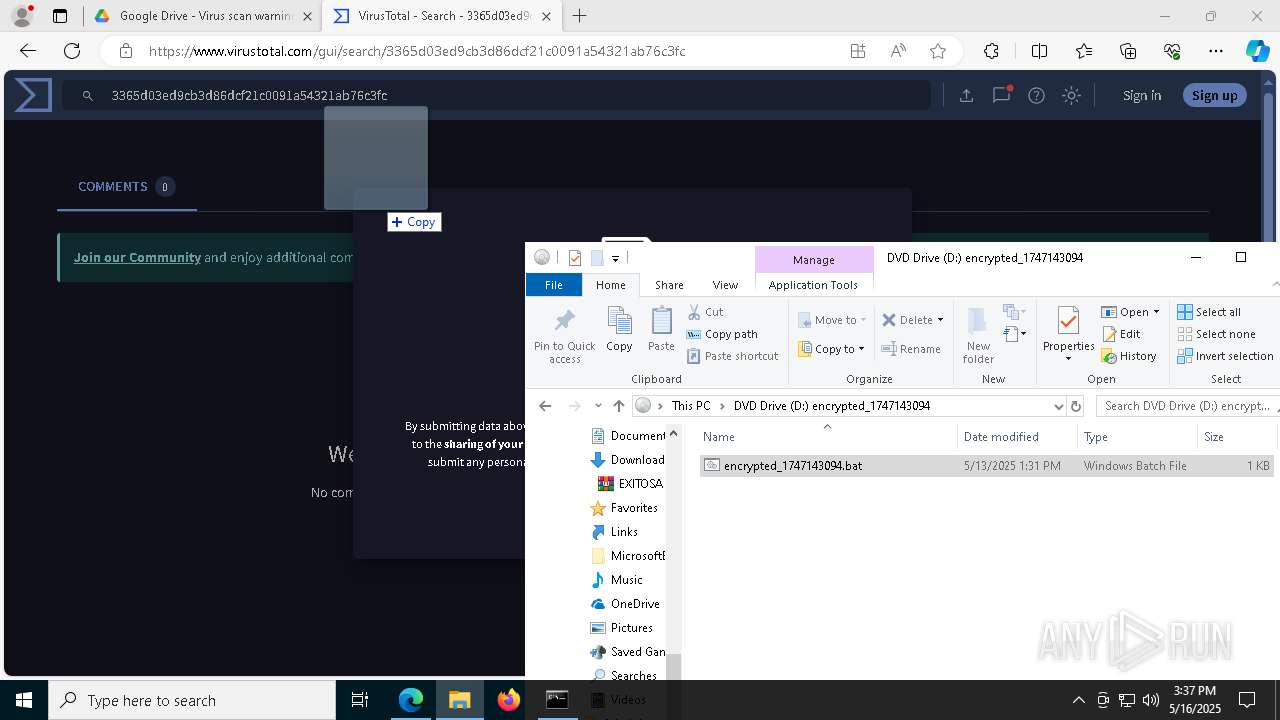
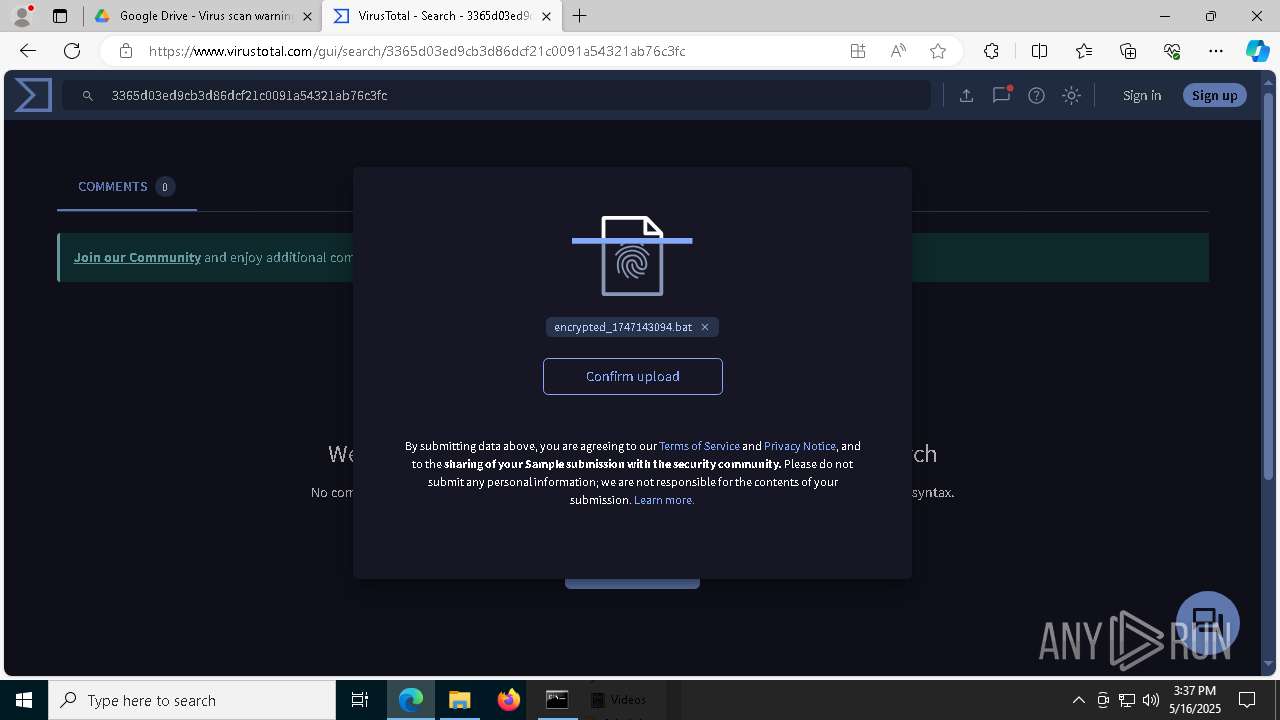
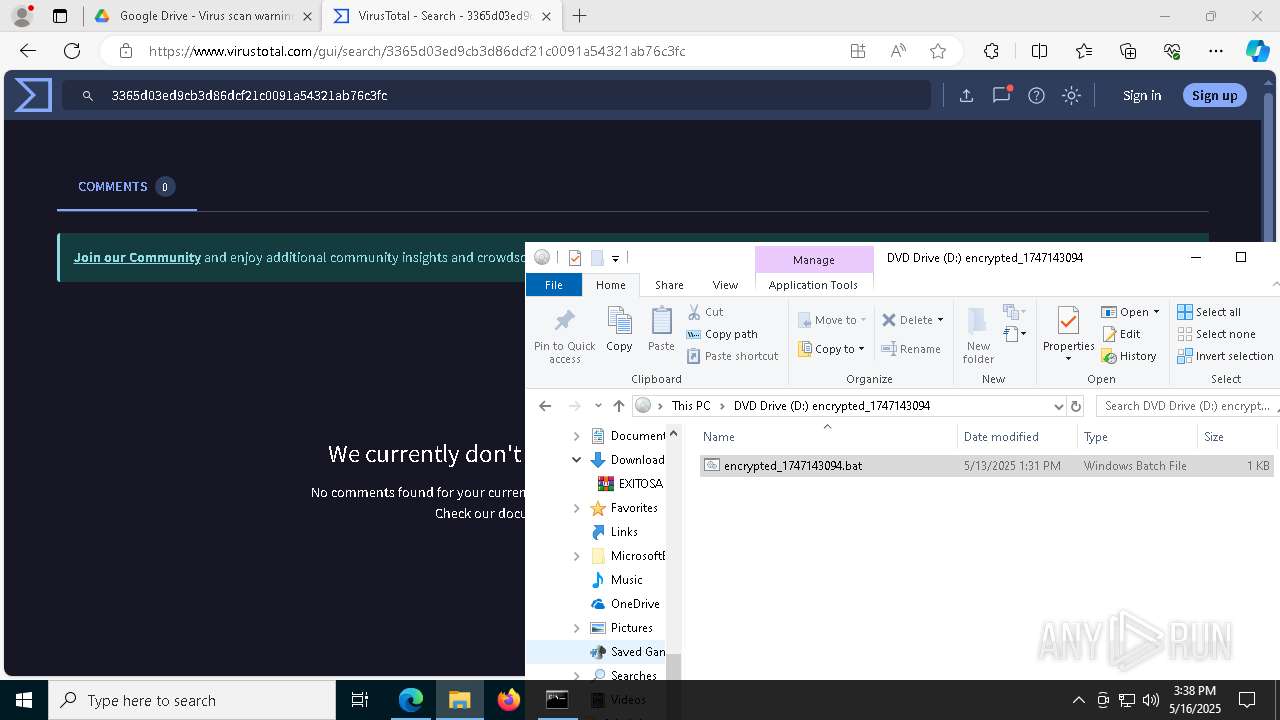
Image mount has been detect
- explorer.exe (PID: 5492)
Potential Corporate Privacy Violation
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 3396)
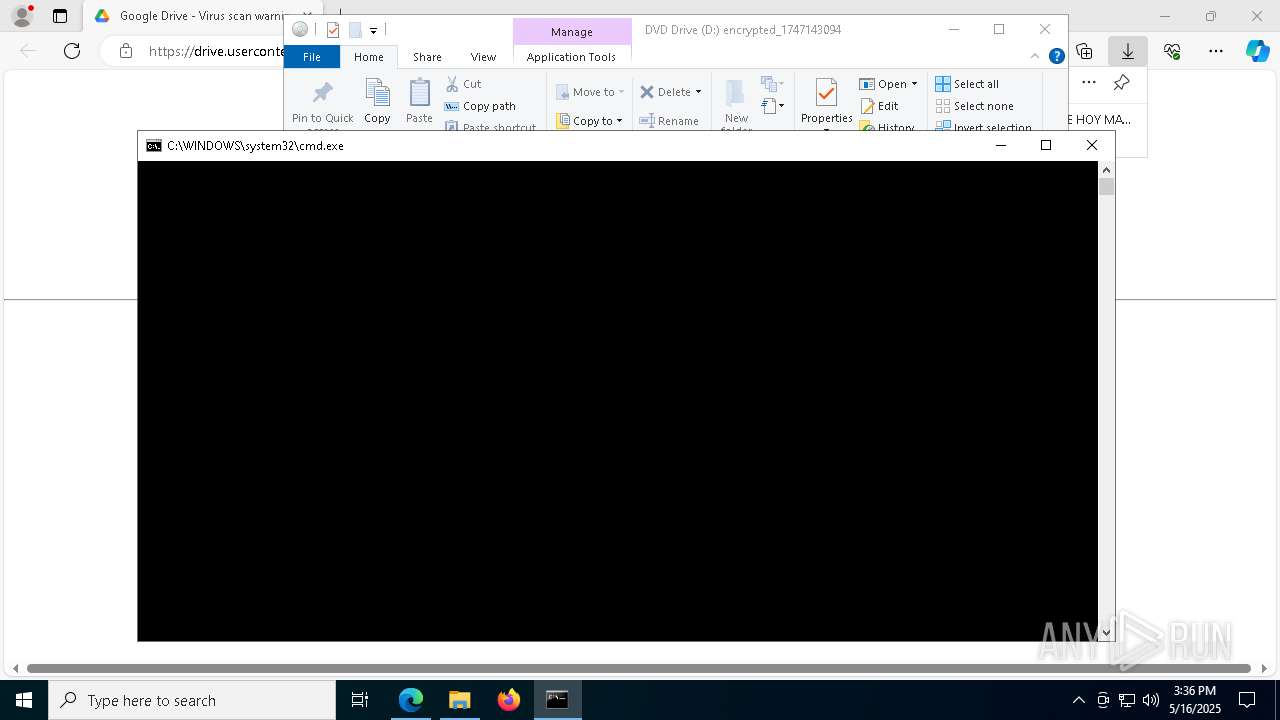
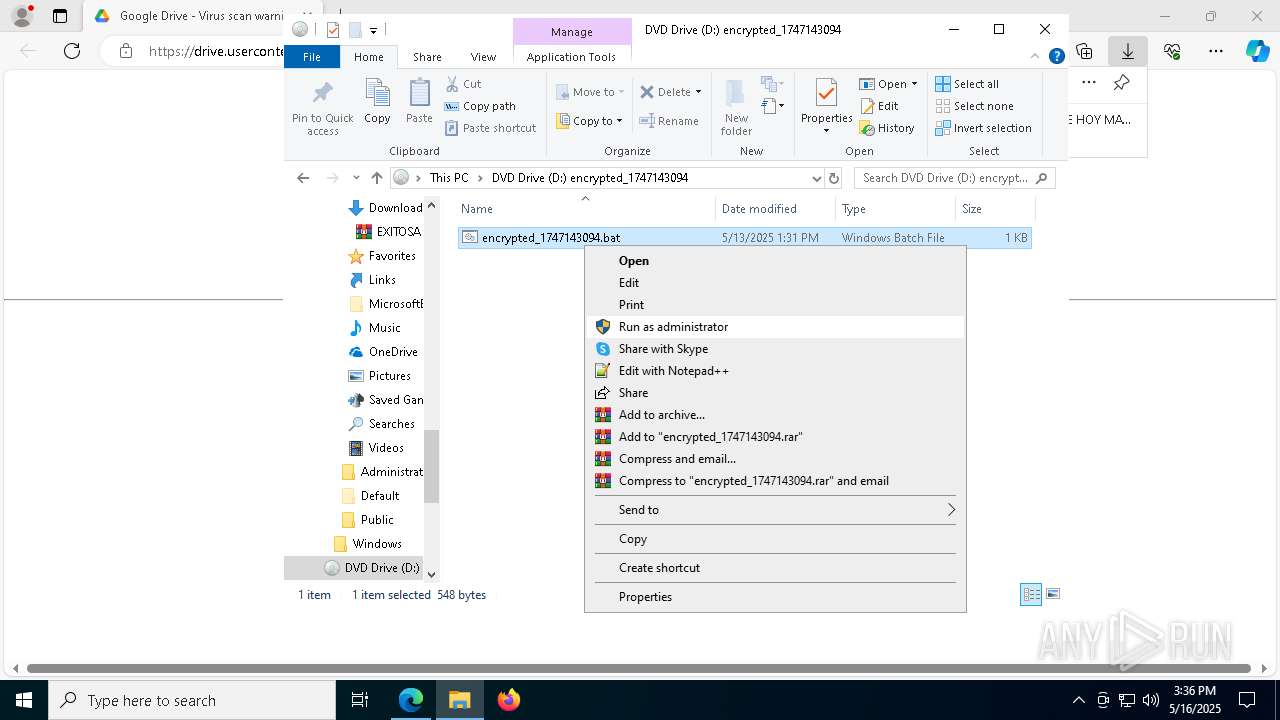
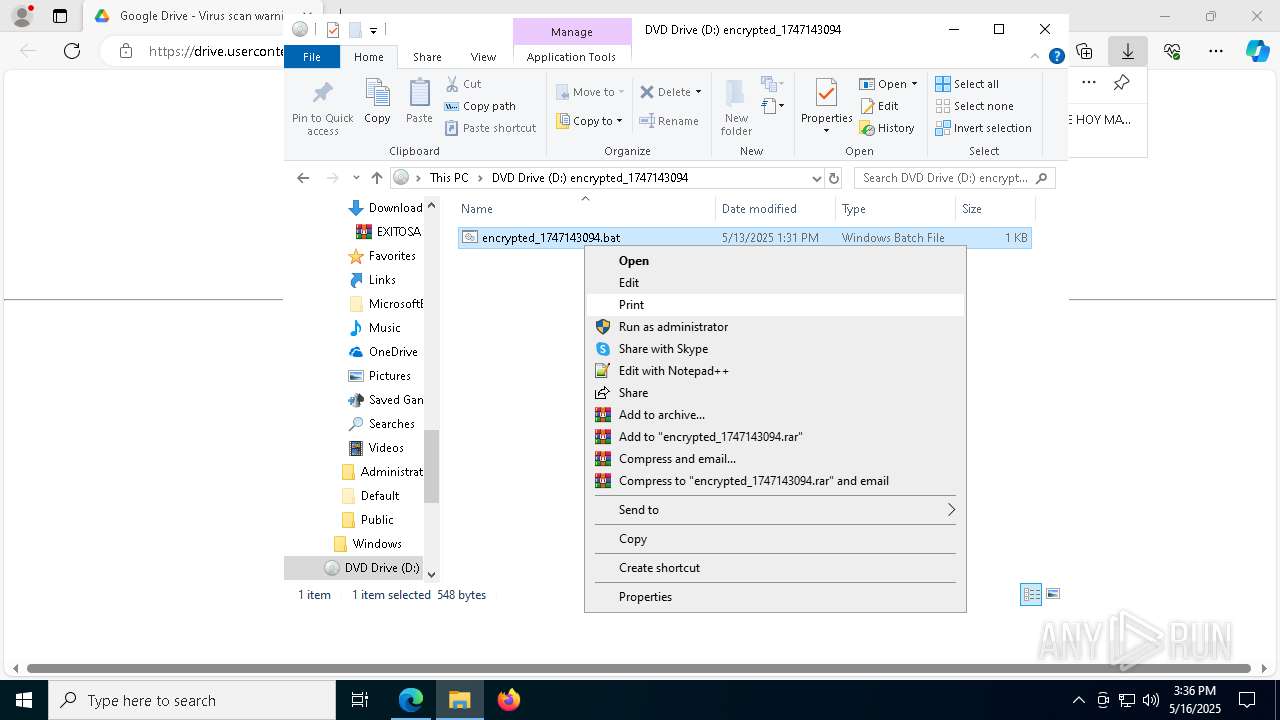
Executing commands from a ".bat" file
- explorer.exe (PID: 5492)
- powershell.exe (PID: 3396)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7316)
- cmd.exe (PID: 2096)
The process executes VB scripts
- cmd.exe (PID: 7316)
- cmd.exe (PID: 2096)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 5492)
- powershell.exe (PID: 3396)
Runs WScript without displaying logo
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1328)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
Base64-obfuscated command line is found
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
Executes script without checking the security policy
- powershell.exe (PID: 3396)
- powershell.exe (PID: 5200)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 1328)
- wscript.exe (PID: 4244)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 3396)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2896)
Contacting a server suspected of hosting an CnC
- aspnet_regsql.exe (PID: 5508)
Connects to unusual port
- aspnet_regsql.exe (PID: 5508)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Reads Environment values
- identity_helper.exe (PID: 2692)
Checks supported languages
- identity_helper.exe (PID: 2692)
Application launched itself
- msedge.exe (PID: 7472)
Reads the computer name
- identity_helper.exe (PID: 2692)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5492)
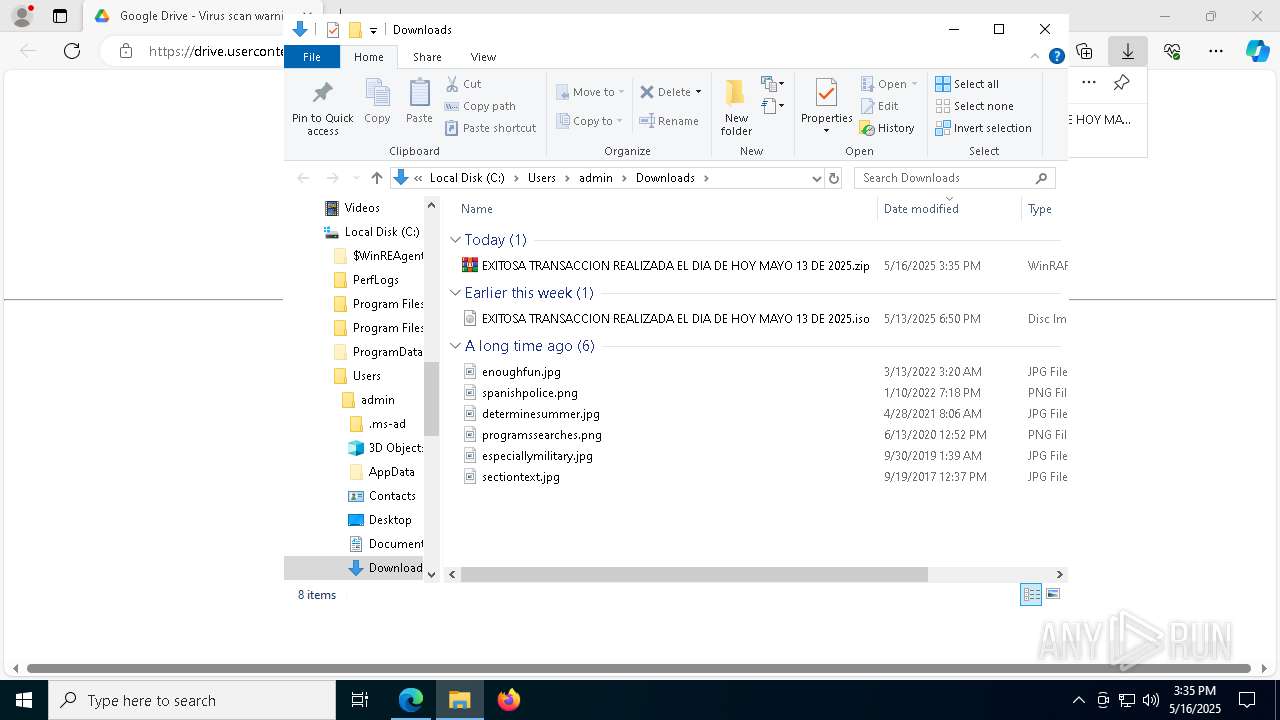
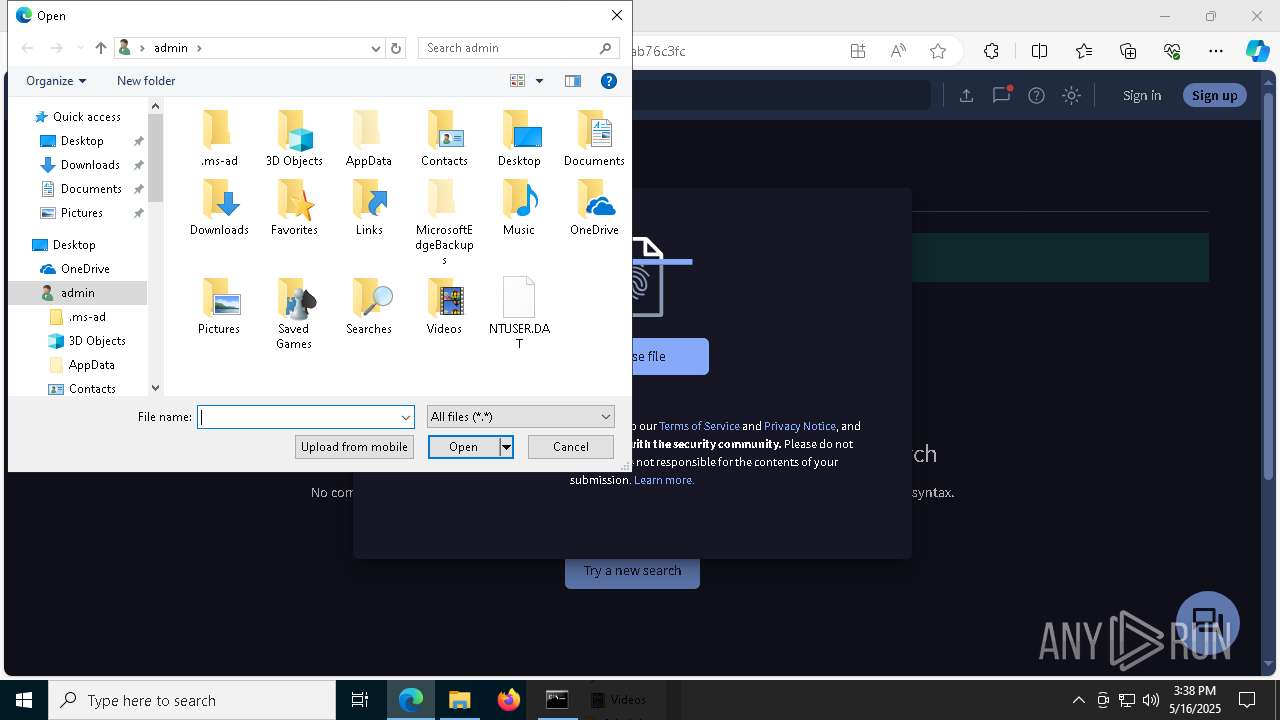
Manual execution by a user
- WinRAR.exe (PID: 6740)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 2084)
Reads the software policy settings
- slui.exe (PID: 5868)
Checks proxy server information
- wscript.exe (PID: 1328)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 3396)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3396)
Executable content was dropped or overwritten
- msedge.exe (PID: 536)
The sample compiled with english language support
- msedge.exe (PID: 536)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 5188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(5508) aspnet_regsql.exe
C2 (1)176.65.142.234
Ports (1)6874
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdanchun
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAJfnii5D7xiAXoriX8/xQb9AW0jxMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDcyNjEyMzM1NFoXDTM1MDUwNTEyMzM1NFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignaturefQZ+F1YgOUfUNJgGmi0VDXRSKOkRzMH/USZiCXlvx/58h9JOEhptesQ5KfErbTLfkhkru3/Y8zLHSTAEwftQPyraqxbLM6GspsHThqxdZfQA0KqgZ4msF2cjSjxzY8IjF9m9cg5v8fzzoHM5B6Px1I9/QKkuYh14aUtqw2RZrV0=
Keys
AESa2edfeff81585e00f75e0431c80ca6b5b1152313b9983095da91603a73d6f39c
SaltDcRatByqwqdanchun
Total processes
228
Monitored processes
91
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | timeout /t 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1496 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=6680 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8064 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4444 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6040 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6268 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6616 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | wscript //nologo "C:\Windows\Temp\becquerel.vbs" | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5076 --field-trial-handle=2196,i,18241215970852936743,16483447326764465990,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
46 101
Read events
45 917
Write events
176
Delete events
8
Modification events
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 442ECFCFD8932F00 | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5493D6CFD8932F00 | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197222 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4C0A4E90-AF15-42E1-B270-BC8E35AC724A} | |||
| (PID) Process: | (7472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197222 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FD94DB98-1146-4F17-B187-C93236322BA7} | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000030266 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000030262 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
Executable files
44
Suspicious files
935
Text files
178
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10be22.TMP | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10be31.TMP | — | |
MD5:— | SHA256:— | |||
| 7472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
178
DNS requests
157
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2340 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6816 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747703977&P2=404&P3=2&P4=l2uuLvpqA%2fLeSN8At3S%2byiVa%2bYZSGPt5Y3uD0DgciEO%2fVH9qF87pEYGuIxUd7LMnXN7riv2I229T7Ds2qgvrwg%3d%3d | unknown | — | — | whitelisted |
2340 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747703977&P2=404&P3=2&P4=l2uuLvpqA%2fLeSN8At3S%2byiVa%2bYZSGPt5Y3uD0DgciEO%2fVH9qF87pEYGuIxUd7LMnXN7riv2I229T7Ds2qgvrwg%3d%3d | unknown | — | — | whitelisted |
6816 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747703977&P2=404&P3=2&P4=l2uuLvpqA%2fLeSN8At3S%2byiVa%2bYZSGPt5Y3uD0DgciEO%2fVH9qF87pEYGuIxUd7LMnXN7riv2I229T7Ds2qgvrwg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7768 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7472 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
docs.google.com |
| whitelisted |
business.bing.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
1328 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
4244 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
3396 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5508 | aspnet_regsql.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
5200 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5508 | aspnet_regsql.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
5508 | aspnet_regsql.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
5508 | aspnet_regsql.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
7768 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |