| File name: | 4d18c76bb688c0e0e5988c174d8cea453421b051c6c565ffe381c9537516cd30.dll |
| Full analysis: | https://app.any.run/tasks/3b37acc0-3d25-4178-9b7c-e0aef6bbefbc |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
| Analysis date: | January 12, 2024, 23:02:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 59D218E1634752279E41B9066895A974 |
| SHA1: | F5CAD9101F5F13BF57EFA4F82E4536A4B850DE28 |
| SHA256: | 4D18C76BB688C0E0E5988C174D8CEA453421B051C6C565FFE381C9537516CD30 |
| SSDEEP: | 98304:cyA464cm4Nr4GU4aIh4fy4+Ce41v4Se4LIxl9ATDjn: |
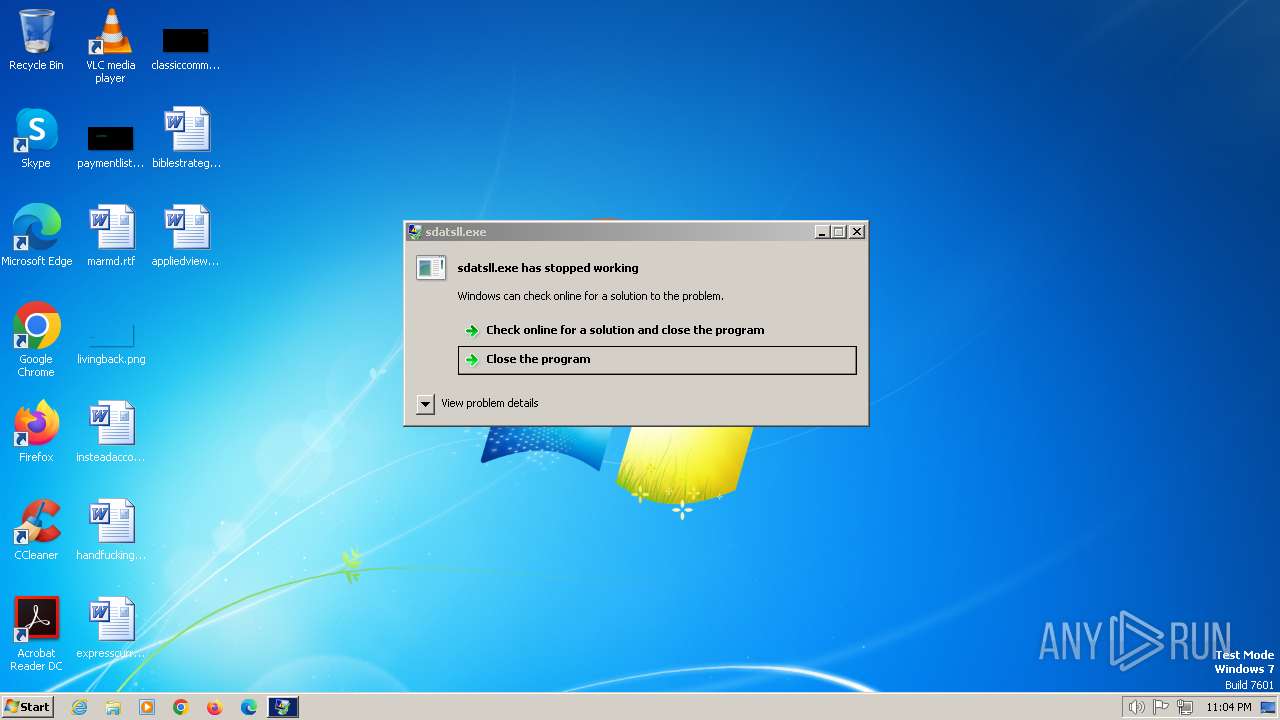
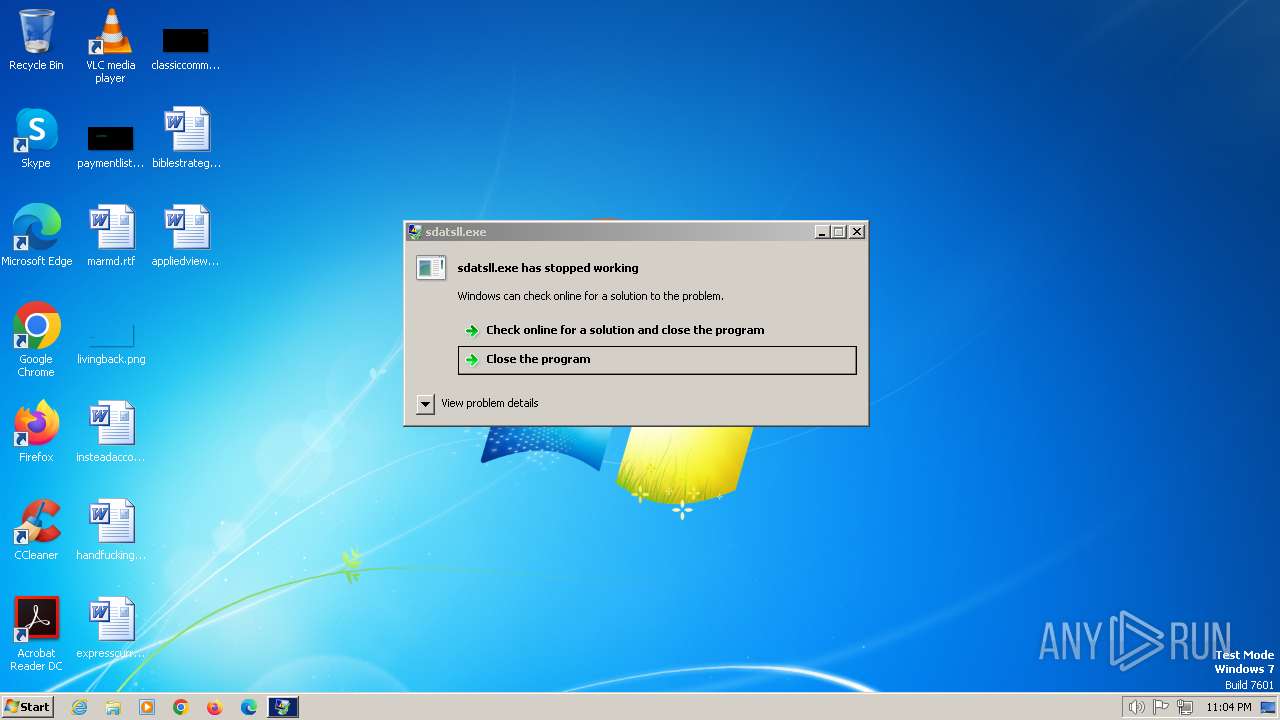
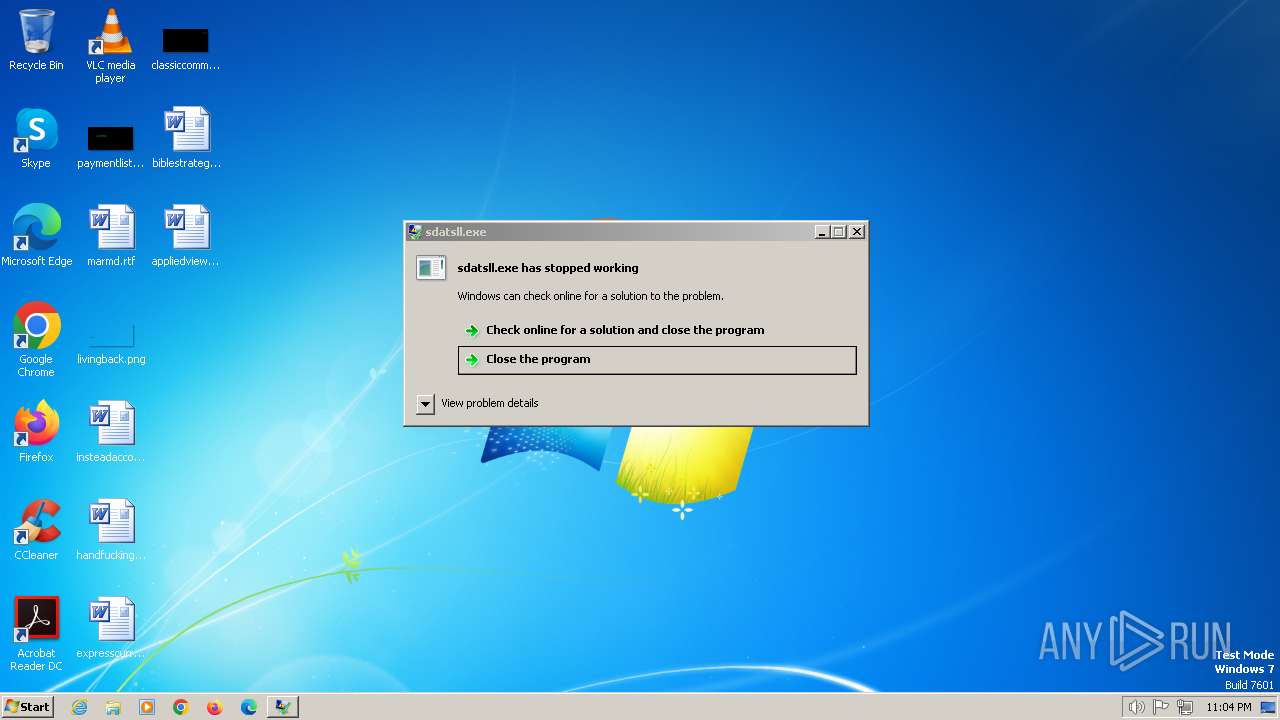
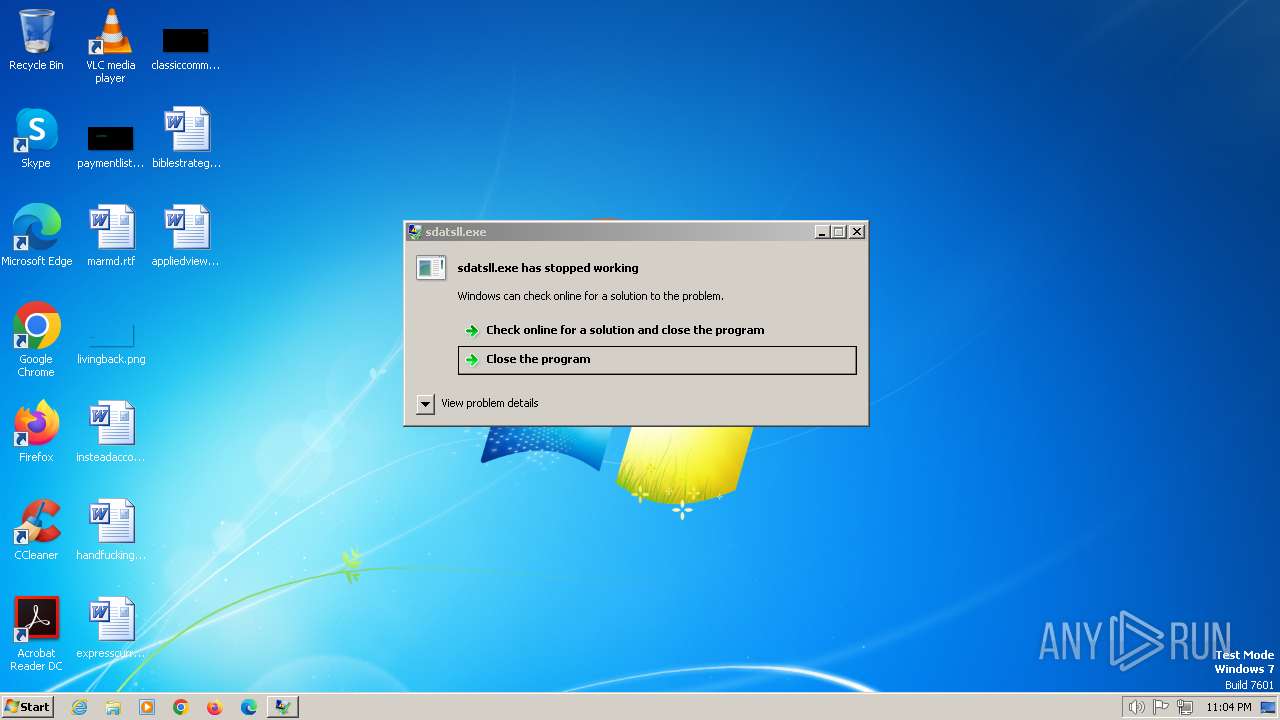
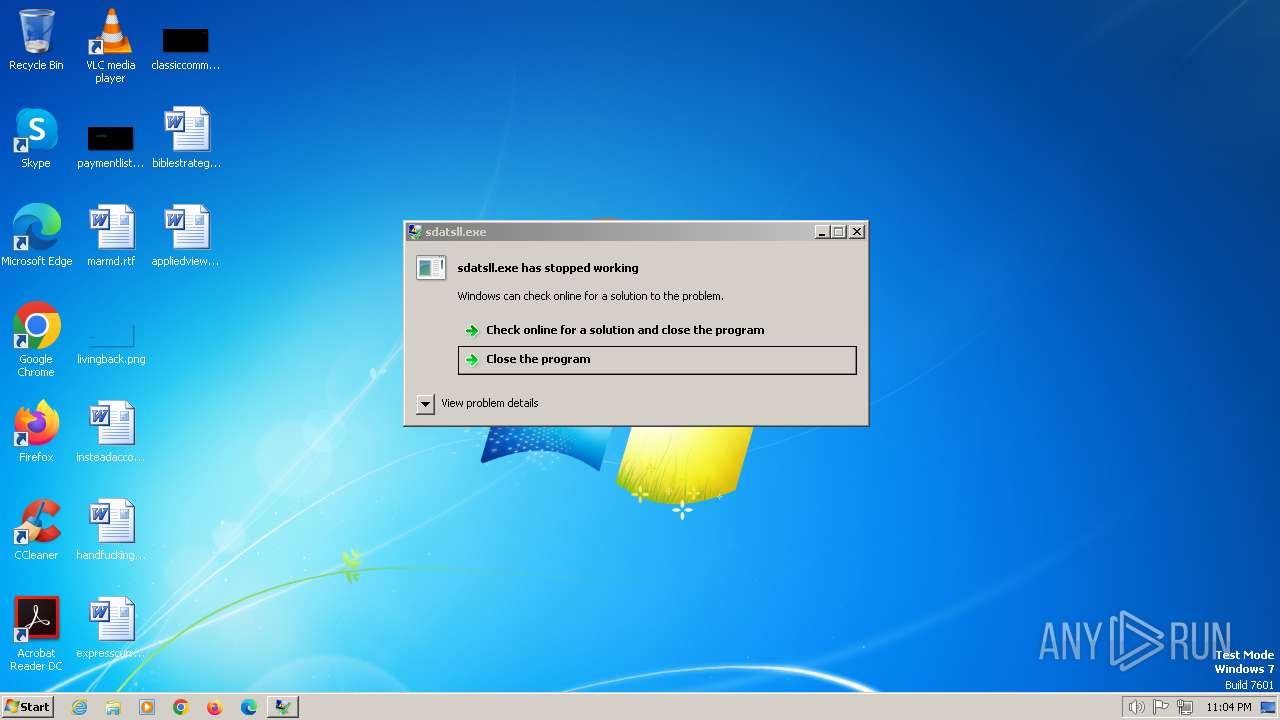
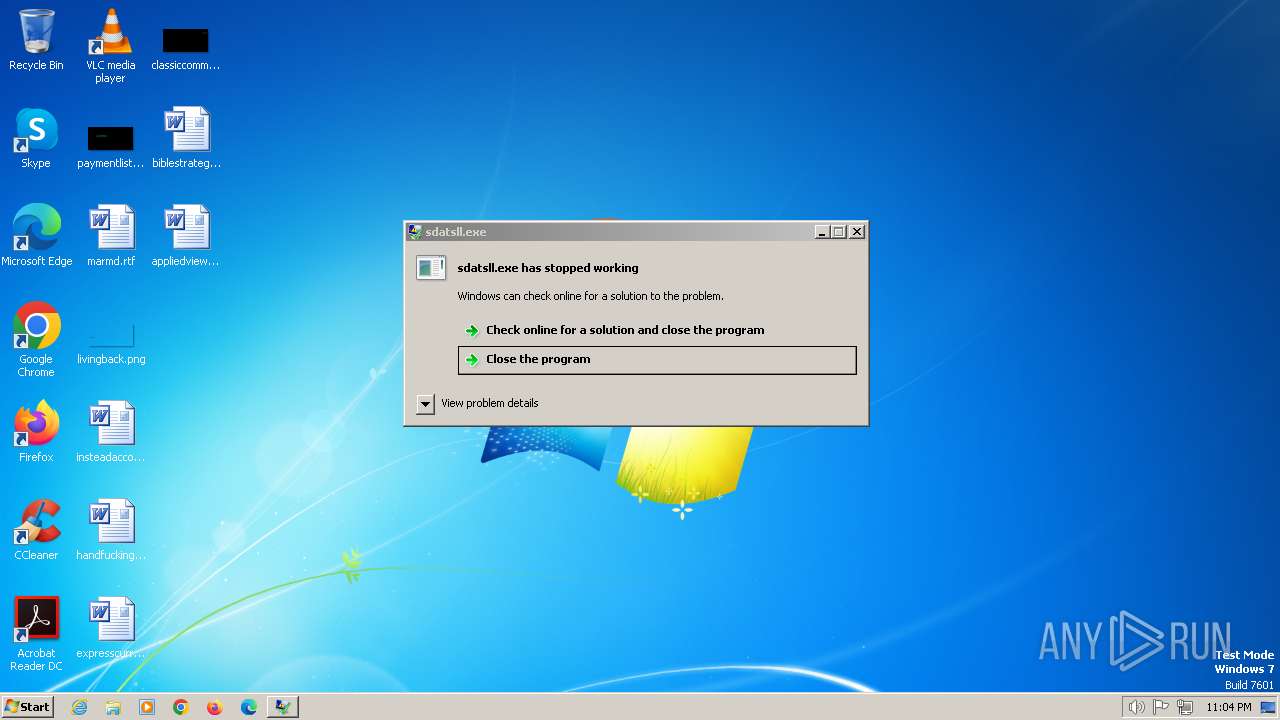
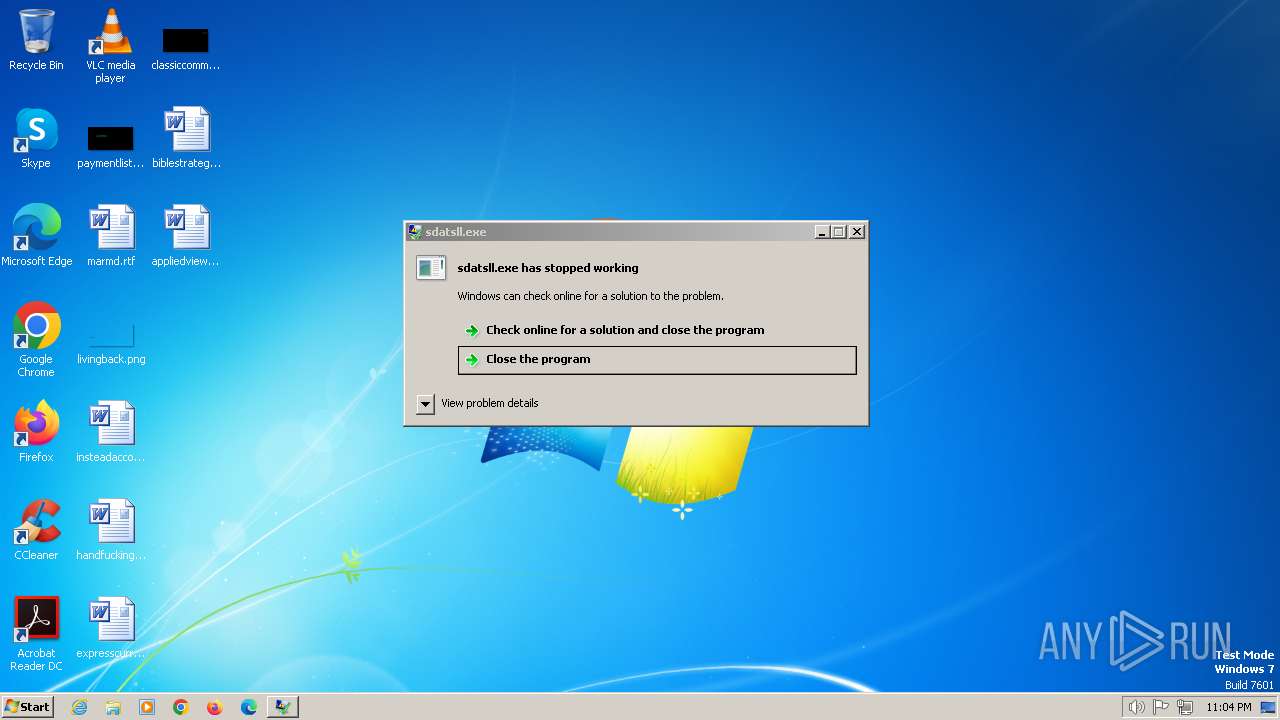
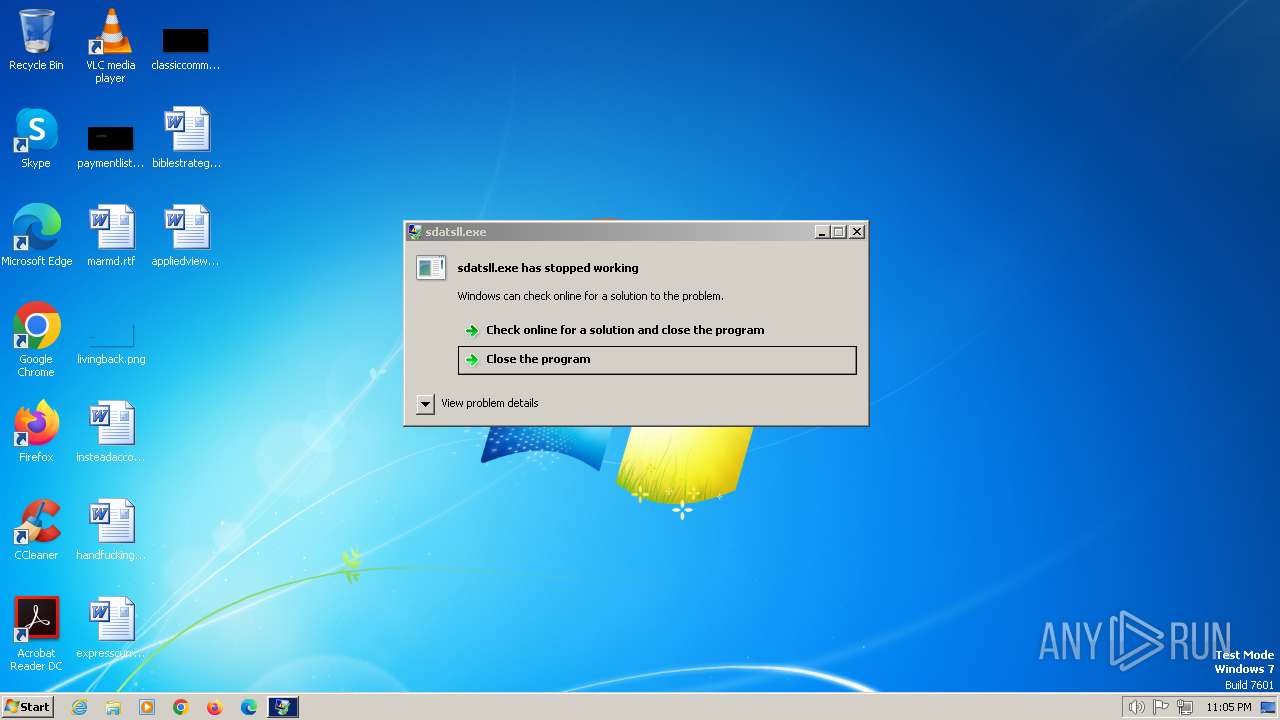
MALICIOUS
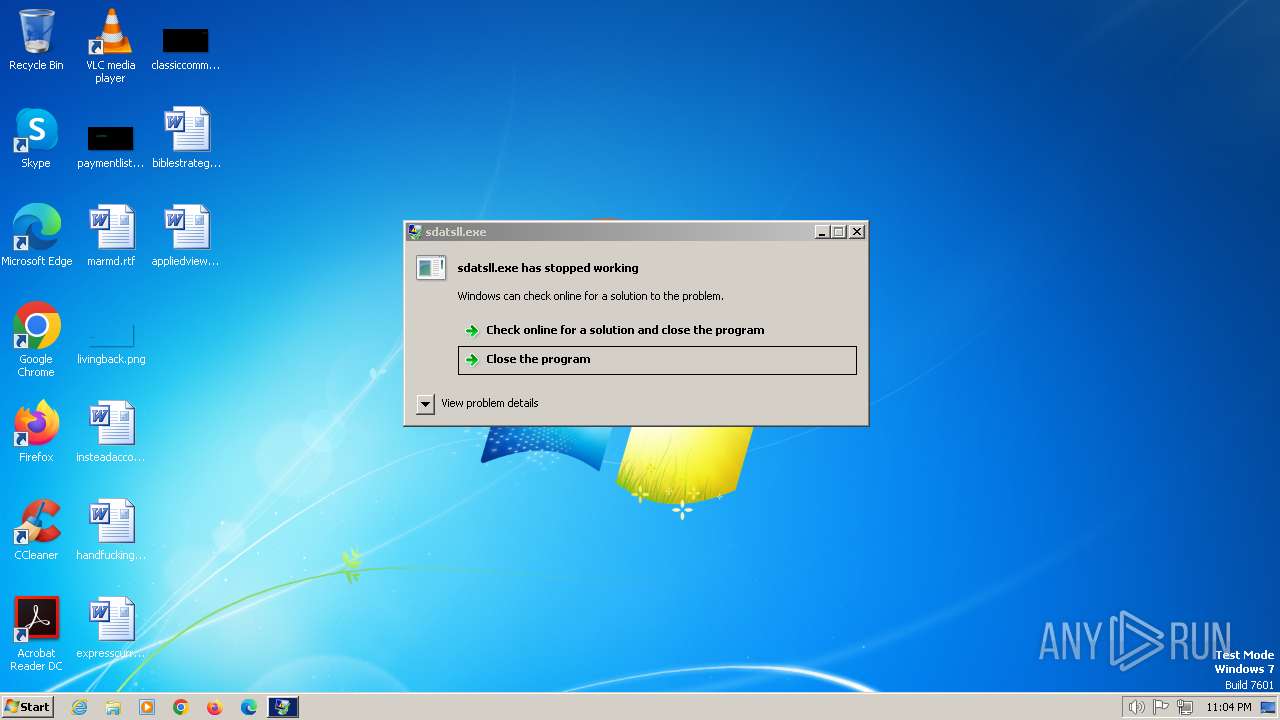
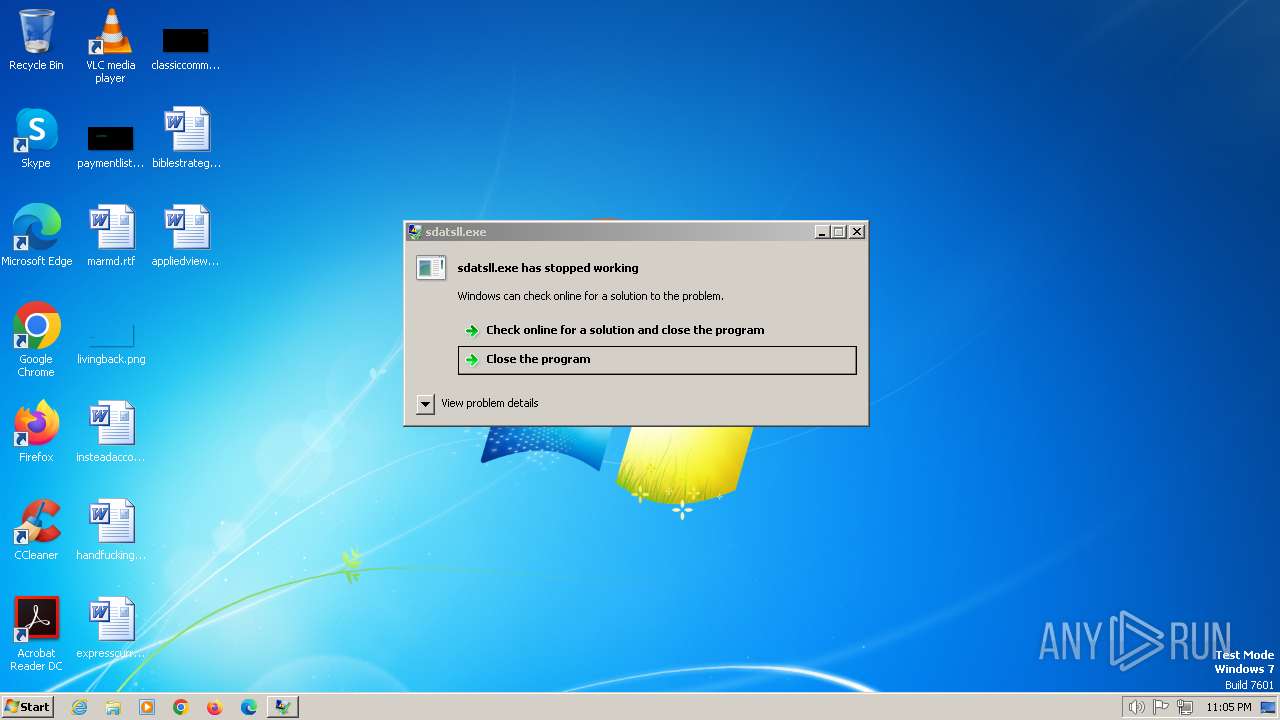
Drops the executable file immediately after the start
- rundll32.exe (PID: 2948)
- QQMusic.exe (PID: 1688)
- WallPaper.exe (PID: 328)
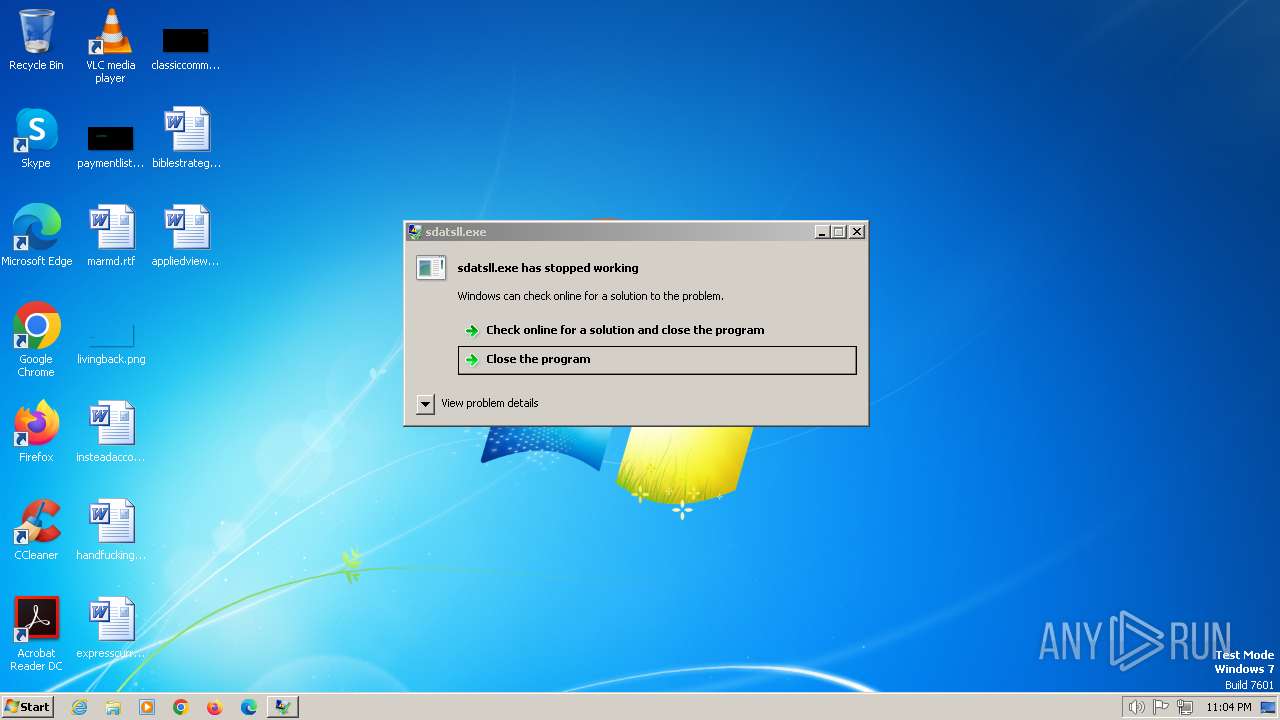
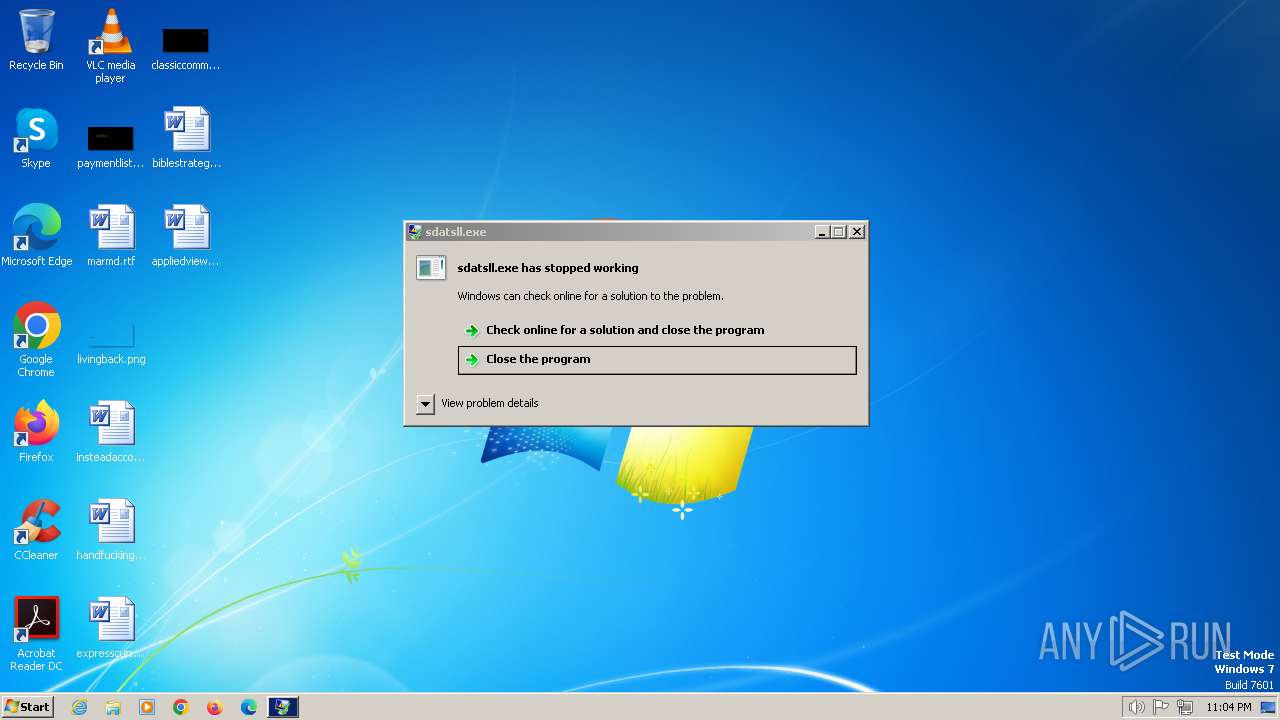
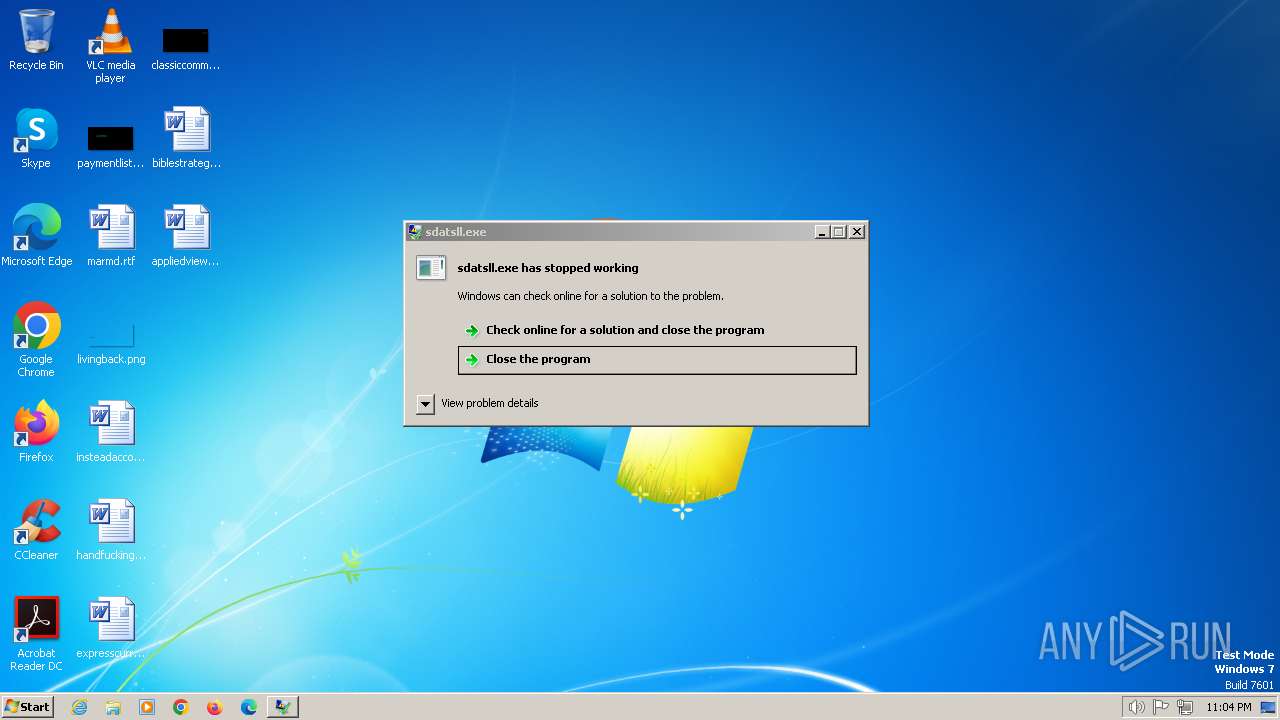
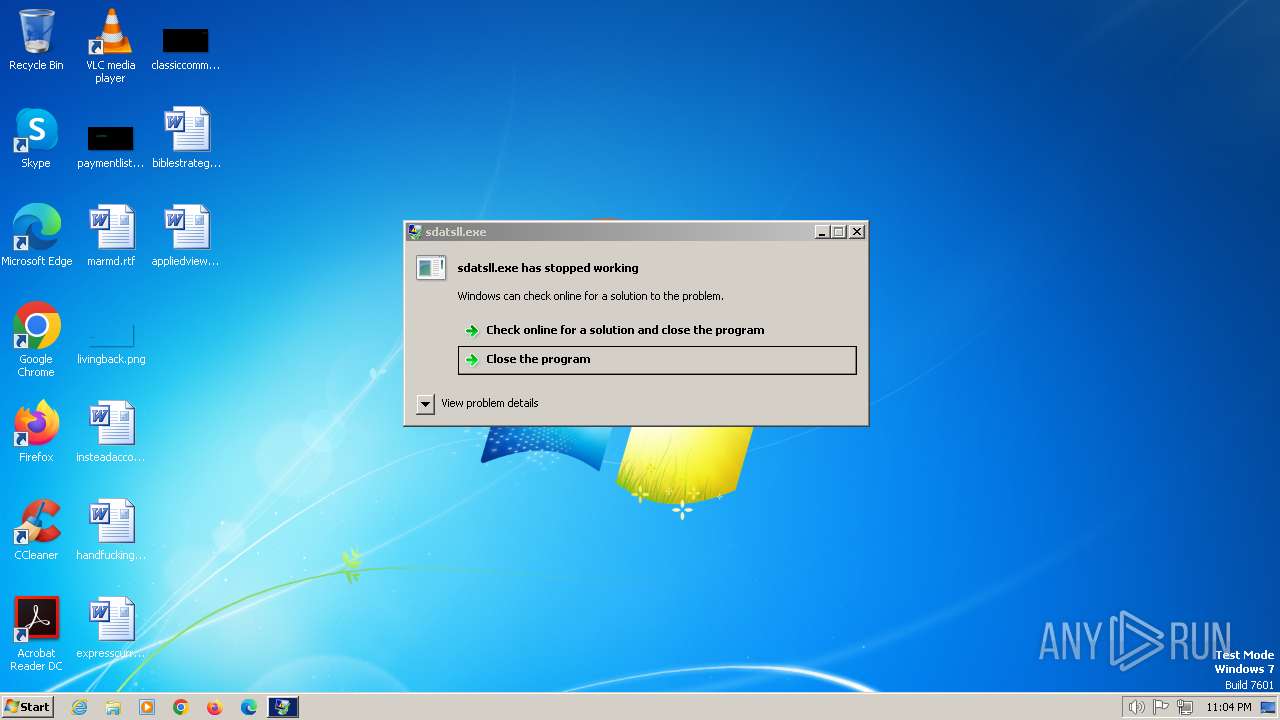
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 308)
- sdatsll.exe (PID: 2932)
- sdatsll.exe (PID: 1424)
- sdatsll.exe (PID: 2476)
- sdatsll.exe (PID: 2520)
- sdatsll.exe (PID: 2668)
- sdatsll.exe (PID: 272)
- sdatsll.exe (PID: 2512)
- sdatsll.exe (PID: 1860)
- sdatsll.exe (PID: 2988)
- sdatsll.exe (PID: 3032)
- sdatsll.exe (PID: 1996)
- sdatsll.exe (PID: 2076)
- sdatsll.exe (PID: 1036)
GH0ST has been detected (SURICATA)
- rundll32.exe (PID: 2740)
Unusual connection from system programs
- rundll32.exe (PID: 2740)
UAC/LUA settings modification
- rundll32.exe (PID: 2740)
Changes the autorun value in the registry
- rundll32.exe (PID: 1848)
SUSPICIOUS
Connects to unusual port
- rundll32.exe (PID: 2740)
The process drops C-runtime libraries
- rundll32.exe (PID: 2740)
- WallPaper.exe (PID: 328)
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 308)
- sdatsll.exe (PID: 2932)
- sdatsll.exe (PID: 1424)
- sdatsll.exe (PID: 2476)
- sdatsll.exe (PID: 2520)
- sdatsll.exe (PID: 2668)
- sdatsll.exe (PID: 272)
- sdatsll.exe (PID: 2512)
- sdatsll.exe (PID: 1860)
- sdatsll.exe (PID: 2988)
- sdatsll.exe (PID: 3032)
- sdatsll.exe (PID: 1996)
- sdatsll.exe (PID: 2076)
- sdatsll.exe (PID: 1036)
Process drops legitimate windows executable
- rundll32.exe (PID: 2740)
- WallPaper.exe (PID: 328)
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 2932)
- sdatsll.exe (PID: 308)
- sdatsll.exe (PID: 2476)
- sdatsll.exe (PID: 2520)
- sdatsll.exe (PID: 272)
- sdatsll.exe (PID: 2512)
- sdatsll.exe (PID: 1860)
- sdatsll.exe (PID: 2988)
- sdatsll.exe (PID: 3032)
- sdatsll.exe (PID: 1996)
- sdatsll.exe (PID: 2076)
- sdatsll.exe (PID: 1424)
- sdatsll.exe (PID: 1036)
- sdatsll.exe (PID: 2668)
Executable content was dropped or overwritten
- rundll32.exe (PID: 2740)
- WallPaper.exe (PID: 328)
- sdatsll.exe (PID: 308)
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 2932)
- sdatsll.exe (PID: 1424)
- sdatsll.exe (PID: 2476)
- sdatsll.exe (PID: 2520)
- sdatsll.exe (PID: 2668)
- sdatsll.exe (PID: 272)
- sdatsll.exe (PID: 2512)
- sdatsll.exe (PID: 1860)
- sdatsll.exe (PID: 2988)
- QQMusic.exe (PID: 1688)
- sdatsll.exe (PID: 3032)
- sdatsll.exe (PID: 1996)
- sdatsll.exe (PID: 2076)
- sdatsll.exe (PID: 1036)
Application launched itself
- QQMusic.exe (PID: 1688)
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 308)
Reads the Internet Settings
- rundll32.exe (PID: 2740)
- QQMusic.exe (PID: 1688)
Reads the date of Windows installation
- QQMusic.exe (PID: 1688)
Starts itself from another location
- WallPaper.exe (PID: 328)
INFO
Creates files or folders in the user directory
- rundll32.exe (PID: 2740)
- QQMusic.exe (PID: 1688)
- WallPaper.exe (PID: 328)
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 308)
- sdatsll.exe (PID: 2932)
- sdatsll.exe (PID: 1424)
- sdatsll.exe (PID: 2520)
- sdatsll.exe (PID: 2476)
- sdatsll.exe (PID: 2668)
- sdatsll.exe (PID: 272)
- sdatsll.exe (PID: 1860)
- sdatsll.exe (PID: 2512)
- sdatsll.exe (PID: 2988)
- sdatsll.exe (PID: 3032)
- sdatsll.exe (PID: 1996)
- sdatsll.exe (PID: 2076)
- sdatsll.exe (PID: 1036)
Creates files in the program directory
- rundll32.exe (PID: 2740)
Drops the executable file immediately after the start
- rundll32.exe (PID: 2740)
Checks supported languages
- QQMusic.exe (PID: 1688)
- WallPaper.exe (PID: 328)
- QQMusic.exe (PID: 2916)
- sdatsll.exe (PID: 1420)
- sdatsll.exe (PID: 308)
- sdatsll.exe (PID: 2932)
- sdatsll.exe (PID: 1424)
- sdatsll.exe (PID: 2072)
- sdatsll.exe (PID: 2476)
- sdatsll.exe (PID: 2668)
- sdatsll.exe (PID: 2520)
- sdatsll.exe (PID: 2512)
- sdatsll.exe (PID: 2988)
- sdatsll.exe (PID: 3032)
- sdatsll.exe (PID: 1996)
- sdatsll.exe (PID: 2076)
- sdatsll.exe (PID: 1036)
- sdatsll.exe (PID: 1860)
- sdatsll.exe (PID: 272)
Reads the computer name
- QQMusic.exe (PID: 1688)
Reads the machine GUID from the registry
- QQMusic.exe (PID: 1688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:06 21:46:47+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 61440 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x978d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
72
Monitored processes
23
Malicious processes
20
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe" | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | sdatsll.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 308 | "C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe" | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | sdatsll.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 328 | "C:\Users\Public\Documents\RECSLLE.BIN\WallPaper.exe" | C:\Users\Public\Documents\RECSLLE.BIN\WallPaper.exe | QQMusic.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe" | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | sdatsll.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1420 | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | WallPaper.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe" | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | sdatsll.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1688 | "C:\Users\Public\Documents\RECSLLE.BIN\system\QQMusic.exe" | C:\Users\Public\Documents\RECSLLE.BIN\system\QQMusic.exe | rundll32.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Description: QQMusic Exit code: 0 Version: 12.03.3447.0812 Modules
| |||||||||||||||
| 1848 | "C:\Windows\SysWOW64\rundll32.exe" advpack.dll,LaunchINFSectionEx C:\Users\admin\AppData\Roaming\apple\Runinf.inf ,DefaultInstall,,32 | C:\Windows\SysWOW64\rundll32.exe | QQMusic.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | "C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe" | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | sdatsll.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1996 | "C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe" | C:\Users\admin\AppData\Roaming\Temp\qduryefqa\sdatsll.exe | sdatsll.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
Total events
4 484
Read events
3 915
Write events
569
Delete events
0
Modification events
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MICROSOFT\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MICROSOFT\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 1 | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MICROSOFT\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 1 | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2740) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1688) QQMusic.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1688) QQMusic.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
77
Suspicious files
7
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | rundll32.exe | C:\Users\admin\AppData\Local\_2 | binary | |
MD5:F33B6F843EE5EC7D12252931440842B7 | SHA256:F746A66D432520FAF1F04EB269C73BFD7B622B7FE4476CDFBA6FF38FF09B3830 | |||
| 2740 | rundll32.exe | C:\Users\admin\AppData\Roaming\install.ini | text | |
MD5:79D1AAD24986B52C296B3F3F929E7D46 | SHA256:7923CDA0AD29649AC34259ECBF02F140A2EA278D00CB7564317713B752C6A017 | |||
| 2740 | rundll32.exe | C:\Users\Public\Documents\RECSLLE.BIN\system\crt.dll | executable | |
MD5:231CCEB5005A9E71C114CBDAC63C3EE1 | SHA256:61CDF4BE615472D358F6B91FA06AC0D17E59E92C2D33165A331BAF1548A4A6A2 | |||
| 2740 | rundll32.exe | C:\Users\admin\AppData\Local\Finkit\ManicTime.xml | xml | |
MD5:DFE8DEF4E493EAE4CE53296CB2E035BA | SHA256:AF0B40B517B1FD802F9E19CD6C15FD15BE4E9EA259F747A8456253C7329F3792 | |||
| 2740 | rundll32.exe | C:\ProgramData\_3 | binary | |
MD5:F45F1BBAFFF0E64C9918C3F48D193A8D | SHA256:EDBFF077F700DB50B2051FFB1CFC472614CFC173FF59833689FC5D78BB496359 | |||
| 2740 | rundll32.exe | C:\ProgramData\cba.bat | text | |
MD5:FC22F14D2EF42789A388972E5E0CE6AF | SHA256:DC9EF4EBB8F84192D15D3C4DF26717AABC72AE2E5276BD034946F208DF897F00 | |||
| 2740 | rundll32.exe | C:\ProgramData\vcruntime140.dll | executable | |
MD5:1B171F9A428C44ACF85F89989007C328 | SHA256:9D02E952396BDFF3ABFE5654E07B7A713C84268A225E11ED9A3BF338ED1E424C | |||
| 2740 | rundll32.exe | C:\ProgramData\a.ini | text | |
MD5:82BEF32153657DC25DC439A3B500A614 | SHA256:D14214E95C9D1EA850E508DFE27928494F2155A7597E4EA0BAD9F70690ABB397 | |||
| 2740 | rundll32.exe | C:\ProgramData\l.dll | binary | |
MD5:8515D0F8C1DB6FACC42DA907FA924BC6 | SHA256:3084ED8A4177BCE83400CDEA260654B5E7BDE85B7E49E98E1803E1E23D7A834E | |||
| 2740 | rundll32.exe | C:\Users\admin\AppData\Local\_2.dll | executable | |
MD5:B49DABC92DDD63C4EC1F06C9AC8D87C9 | SHA256:2ED9F7DBA2838A1FA956E5C2F7B56F406D5DE828160A8D6A83E33767BAC9D930 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
352 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1220 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
2740 | rundll32.exe | 154.39.241.63:6180 | — | HONG KONG Megalayer Technology Co.,Limited | US | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2740 | rundll32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Gh0stRat |