| File name: | 29f96d0.dll |
| Full analysis: | https://app.any.run/tasks/103ee37b-767c-4f70-b370-628a07923d3c |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
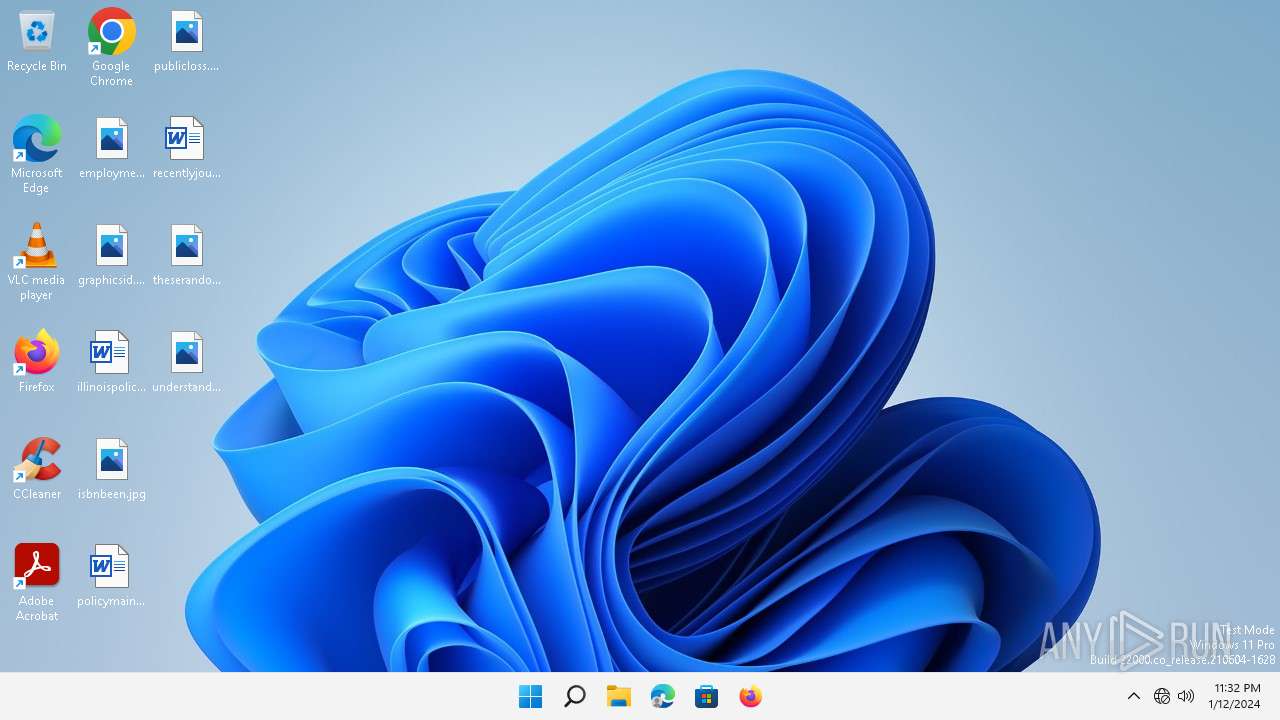
| Analysis date: | January 12, 2024, 23:32:01 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 59D218E1634752279E41B9066895A974 |
| SHA1: | F5CAD9101F5F13BF57EFA4F82E4536A4B850DE28 |
| SHA256: | 4D18C76BB688C0E0E5988C174D8CEA453421B051C6C565FFE381C9537516CD30 |
| SSDEEP: | 98304:cyA464cm4Nr4GU4aIh4fy4+Ce41v4Se4LIxl9ATDjn: |
MALICIOUS
Unusual connection from system programs
- rundll32.exe (PID: 132)
Drops the executable file immediately after the start
- rundll32.exe (PID: 156)
- WallPaper.exe (PID: 3644)
- QQMusic.exe (PID: 3340)
GH0ST has been detected (SURICATA)
- rundll32.exe (PID: 132)
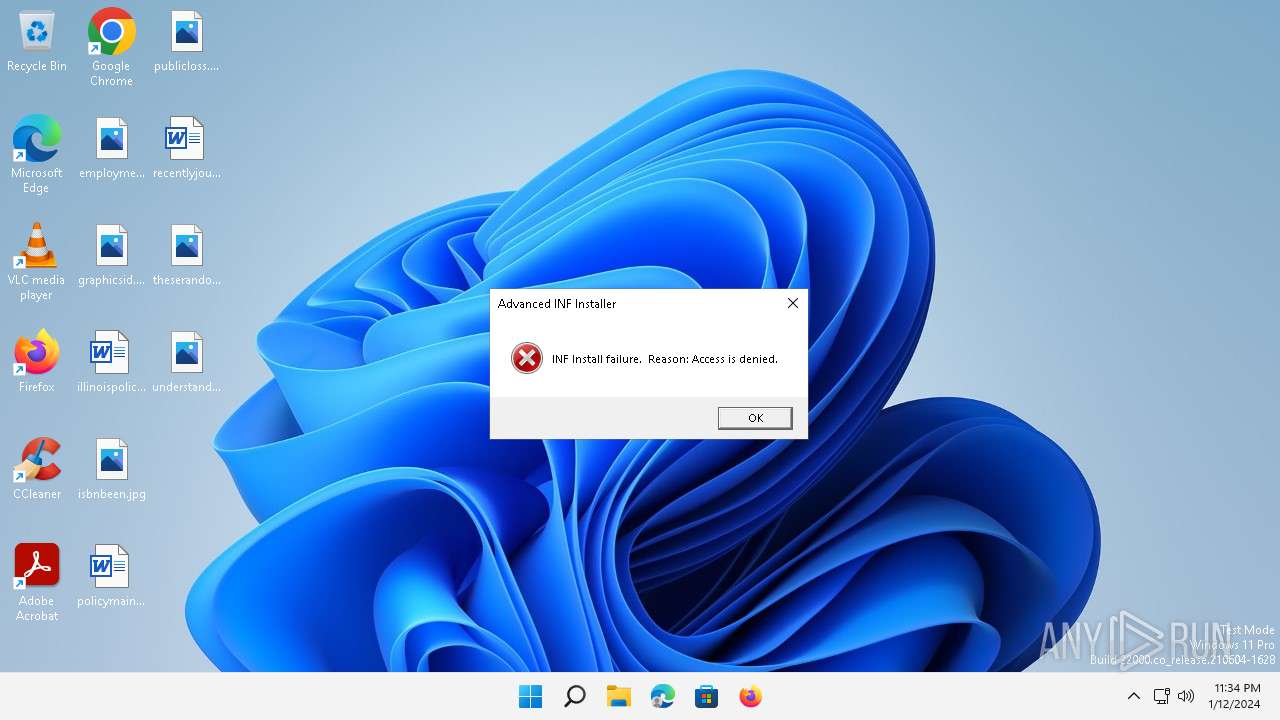
UAC/LUA settings modification
- rundll32.exe (PID: 132)
Changes the autorun value in the registry
- rundll32.exe (PID: 2160)
SUSPICIOUS
Process drops legitimate windows executable
- rundll32.exe (PID: 132)
- WallPaper.exe (PID: 3644)
The process drops C-runtime libraries
- rundll32.exe (PID: 132)
- WallPaper.exe (PID: 3644)
Executable content was dropped or overwritten
- rundll32.exe (PID: 132)
- QQMusic.exe (PID: 3340)
- WallPaper.exe (PID: 3644)
Reads the Internet Settings
- rundll32.exe (PID: 132)
- QQMusic.exe (PID: 3340)
Connects to unusual port
- rundll32.exe (PID: 132)
Application launched itself
- QQMusic.exe (PID: 3340)
Reads the date of Windows installation
- QQMusic.exe (PID: 3340)
Executes application which crashes
- rundll32.exe (PID: 132)
Starts itself from another location
- WallPaper.exe (PID: 3644)
INFO
Creates files in the program directory
- rundll32.exe (PID: 132)
Creates files or folders in the user directory
- rundll32.exe (PID: 132)
- QQMusic.exe (PID: 3340)
- WallPaper.exe (PID: 3644)
- WerFault.exe (PID: 5288)
Drops the executable file immediately after the start
- rundll32.exe (PID: 132)
Checks supported languages
- QQMusic.exe (PID: 3340)
- QQMusic.exe (PID: 3256)
- WallPaper.exe (PID: 3644)
- sdatsll.exe (PID: 1200)
Reads the machine GUID from the registry
- QQMusic.exe (PID: 3340)
Reads the computer name
- QQMusic.exe (PID: 3340)
- sdatsll.exe (PID: 1200)
Reads the Internet Settings
- WerFault.exe (PID: 5288)
Checks proxy server information
- WerFault.exe (PID: 5288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:06 21:46:47+01:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit, DLL |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 61440 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x978d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
121
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\29f96d0.dll.exe", #1 | C:\Windows\SysWOW64\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 156 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\29f96d0.dll.exe", #1 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | C:\Users\admin\AppData\Roaming\Temp\ydcrogfcg\sdatsll.exe | C:\Users\admin\AppData\Roaming\Temp\ydcrogfcg\sdatsll.exe | — | WallPaper.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2160 | "C:\Windows\SysWOW64\rundll32.exe" advpack.dll,LaunchINFSectionEx C:\Users\admin\AppData\Roaming\apple\Runinf.inf ,DefaultInstall,,32 | C:\Windows\SysWOW64\rundll32.exe | QQMusic.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3256 | "C:\Users\Public\Documents\RECSLLE.BIN\system\QQMusic.exe" | C:\Users\Public\Documents\RECSLLE.BIN\system\QQMusic.exe | — | QQMusic.exe | |||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Description: QQMusic Exit code: 0 Version: 12.03.3447.0812 Modules
| |||||||||||||||
| 3340 | "C:\Users\Public\Documents\RECSLLE.BIN\system\QQMusic.exe" | C:\Users\Public\Documents\RECSLLE.BIN\system\QQMusic.exe | rundll32.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: MEDIUM Description: QQMusic Exit code: 0 Version: 12.03.3447.0812 Modules
| |||||||||||||||
| 3644 | "C:\Users\Public\Documents\RECSLLE.BIN\WallPaper.exe" | C:\Users\Public\Documents\RECSLLE.BIN\WallPaper.exe | QQMusic.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4808 | "C:\Windows\system32\rundll32.exe" advpack.dll,LaunchINFSectionEx C:\Users\admin\AppData\Roaming\apple\Runinf.inf ,DefaultInstall,,32 | C:\Windows\SysWOW64\rundll32.exe | — | QQMusic.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5288 | C:\Windows\SysWOW64\WerFault.exe -u -p 132 -s 1516 | C:\Windows\SysWOW64\WerFault.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 946
Read events
8 711
Write events
235
Delete events
0
Modification events
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 1 | |||
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 1 | |||
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (132) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3340) QQMusic.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | DpiScalingVer |
Value: 4096 | |||
| (PID) Process: | (3340) QQMusic.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Win8DpiScaling |
Value: 0 | |||
| (PID) Process: | (3340) QQMusic.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 5B97796500000000 | |||
Executable files
27
Suspicious files
9
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 132 | rundll32.exe | C:\Users\admin\AppData\Roaming\Consys21.png | binary | |
MD5:66FEF576A8F341E7EBCF62C8B4F30B30 | SHA256:7916E4F02C3A9F264E3CC3EE56CAC84BA0E9C1BFD81529E5B4A430D17DAAC4D8 | |||
| 132 | rundll32.exe | C:\Users\admin\AppData\Roaming\_1 | binary | |
MD5:2752D23C57B7F92F55AE8CDB30A1324D | SHA256:27D16F44DE66B413EEF4844723E72B1D01176E944BDD2EF80F4A0741BEDE0A5F | |||
| 132 | rundll32.exe | C:\Users\Public\Documents\RECSLLE.BIN\system\crt.dll | executable | |
MD5:231CCEB5005A9E71C114CBDAC63C3EE1 | SHA256:61CDF4BE615472D358F6B91FA06AC0D17E59E92C2D33165A331BAF1548A4A6A2 | |||
| 132 | rundll32.exe | C:\Users\Public\Documents\install.ini | text | |
MD5:84643585BC1D47D118CFBA3AAEDAE3F1 | SHA256:C57956D205445D6470682A6DAA09BC6D901DA52F37CFED232F63B18B041666BD | |||
| 132 | rundll32.exe | C:\ProgramData\_3 | binary | |
MD5:F45F1BBAFFF0E64C9918C3F48D193A8D | SHA256:EDBFF077F700DB50B2051FFB1CFC472614CFC173FF59833689FC5D78BB496359 | |||
| 132 | rundll32.exe | C:\Users\admin\AppData\Roaming\ConsysFun.png | binary | |
MD5:856A676EB6D5DBE74D6FA334BE630E51 | SHA256:36E13F968167A79421CC69F21421CCE8A356DAE1F909F38976E3A95F600AEF0E | |||
| 132 | rundll32.exe | C:\Users\admin\AppData\Local\_2 | binary | |
MD5:F33B6F843EE5EC7D12252931440842B7 | SHA256:F746A66D432520FAF1F04EB269C73BFD7B622B7FE4476CDFBA6FF38FF09B3830 | |||
| 132 | rundll32.exe | C:\Users\admin\AppData\Local\_2.dll | executable | |
MD5:B49DABC92DDD63C4EC1F06C9AC8D87C9 | SHA256:2ED9F7DBA2838A1FA956E5C2F7B56F406D5DE828160A8D6A83E33767BAC9D930 | |||
| 132 | rundll32.exe | C:\Users\admin\AppData\Roaming\_1.dll | executable | |
MD5:B49DABC92DDD63C4EC1F06C9AC8D87C9 | SHA256:2ED9F7DBA2838A1FA956E5C2F7B56F406D5DE828160A8D6A83E33767BAC9D930 | |||
| 132 | rundll32.exe | C:\Users\admin\AppData\Roaming\install.ini | text | |
MD5:79D1AAD24986B52C296B3F3F929E7D46 | SHA256:7923CDA0AD29649AC34259ECBF02F140A2EA278D00CB7564317713B752C6A017 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
31
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1412 | svchost.exe | GET | 200 | 2.21.20.140:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | text | 22 b | unknown |
5676 | smartscreen.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6787b71640c43ae | unknown | compressed | 4.66 Kb | unknown |
— | — | GET | 200 | 13.107.6.156:443 | https://mrodevicemgr.officeapps.live.com/mrodevicemgrsvc/api/v1/C2RTargetAudienceData?omid=97560490bafb0d49bca6f8f0df91025d&susid=c408ee57-2103-4c34-9e6f-30bdf6c87e50&audienceFFN=492350f6-3a01-4f97-b9c0-c7c6ddf67d60&tid=&osver=Client%7C10.0.22000&offver=16.0.16626.20134&ring=Production&aud=Production&ch=CC&osarch=x64&manstate=6 | unknown | — | — | unknown |
3752 | svchost.exe | POST | 200 | 40.126.32.68:443 | https://login.live.com/RST2.srf | unknown | — | 1.25 Kb | unknown |
— | — | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | unknown | — | 1.29 Kb | unknown |
— | — | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | — | — | unknown |
— | — | PUT | 200 | null:443 | https://cs.dds.microsoft.com/Command/user/RegisterDeviceV2 | unknown | — | — | unknown |
— | — | POST | 200 | 20.105.95.163:443 | https://checkappexec.microsoft.com/windows/shell/actions | unknown | — | 175 b | unknown |
3752 | svchost.exe | POST | 400 | 20.190.160.14:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 210 b | unknown |
— | — | POST | 200 | 20.190.159.4:443 | https://login.live.com/RST2.srf | unknown | — | 11.1 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1412 | svchost.exe | 2.21.20.155:80 | — | Akamai International B.V. | DE | unknown |
5676 | smartscreen.exe | 20.31.251.109:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
132 | rundll32.exe | 154.39.241.63:6180 | — | HONG KONG Megalayer Technology Co.,Limited | US | unknown |
5944 | svchost.exe | 184.30.17.174:443 | — | AKAMAI-AS | DE | unknown |
5676 | smartscreen.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3752 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1412 | svchost.exe | 2.21.20.140:80 | — | Akamai International B.V. | DE | unknown |
3752 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
login.live.com |
| whitelisted |
dns.msftncsi.com |
| shared |
umwatson.events.data.microsoft.com |
| whitelisted |
cs.dds.microsoft.com |
| whitelisted |
v20.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
132 | rundll32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Gh0stRat |
1412 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |