| File name: | System32.bin |
| Full analysis: | https://app.any.run/tasks/11e380d5-5371-4fc4-bbfc-19da86134571 |
| Verdict: | Malicious activity |
| Threats: | Raccoon is an info stealer type malware available as a Malware as a Service. It can be obtained for a subscription and costs $200 per month. Raccoon malware has already infected over 100,000 devices and became one of the most mentioned viruses on the underground forums in 2019. |
| Analysis date: | November 08, 2019, 12:20:59 |
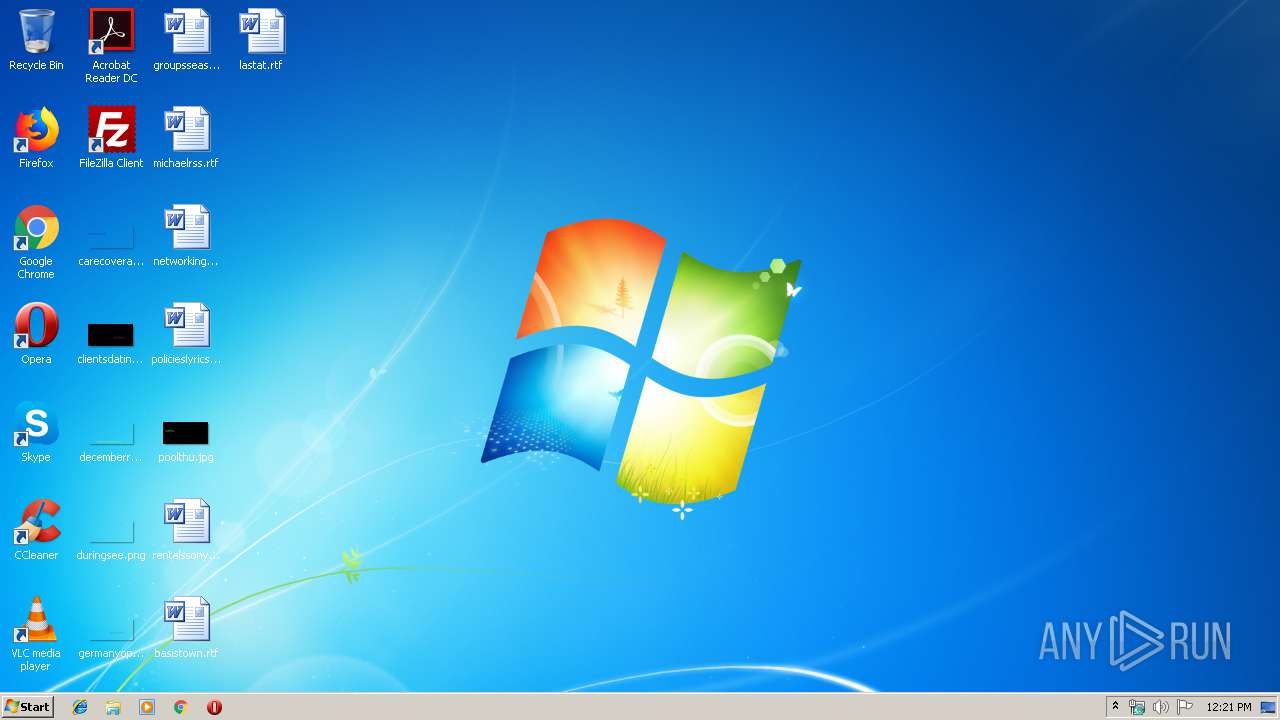
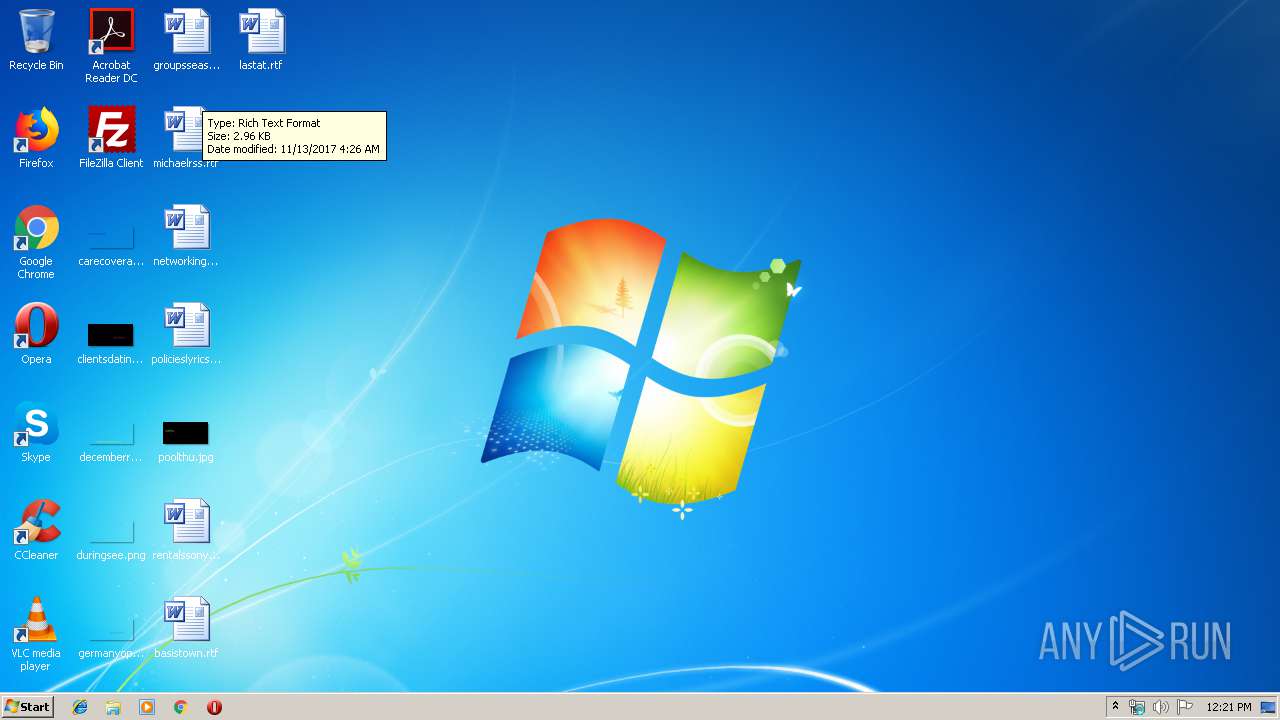
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 049EF18418AFFCD542D9AA545BB07EE3 |
| SHA1: | 994B2B316ED112D81C697294405DCF15F9193DEB |
| SHA256: | 4D056B87049EC7FCE672B40190BF8B5F9185395B7313D05BC196A655E7FE0C7A |
| SSDEEP: | 12288:3gCR9iaPJIdPVe97Apsyajgga9wm3K0nFY0wN:3gCq6idPVe97ApsyajgTw5iFO |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- System32.bin.exe (PID: 2748)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45178 |
.rdata | 0x00008000 | 0x000014A2 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02518 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x00004990 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.49909 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2992 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2748 | "C:\Users\admin\AppData\Local\Temp\System32.bin.exe" | C:\Users\admin\AppData\Local\Temp\System32.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
335
Read events
335
Write events
0
Delete events
0
Modification events
Executable files
4
Suspicious files
2
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\objbrowser.gif | image | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\color-widget.css | text | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\x-ms-wmv.xml | xml | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\cert2spc.exe | executable | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\crtowordschs.dll | executable | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\snd-soc-spdif-rx.ko | o | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\convrt3d.png | image | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\eo-h-fundamente.png | image | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\votes\m3ufilename\contacts.xml | xml | |
MD5:— | SHA256:— | |||
| 2748 | System32.bin.exe | C:\Users\admin\AppData\Local\Temp\etchings.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 34.77.135.60:80 | http://34.77.135.60/gate/log.php | US | text | 398 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 216.58.210.14:443 | drive.google.com | Google Inc. | US | whitelisted |
— | — | 34.77.135.60:80 | — | — | US | malicious |
— | — | 172.217.22.33:443 | doc-08-cc-docs.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
doc-08-cc-docs.googleusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | AV TROJAN Trojan-Spy.MSIL.Stealer.ahp CnC Checkin |
— | — | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.RaccoonStealer |
— | — | Potentially Bad Traffic | ET INFO Dotted Quad Host DLL Request |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1 ETPRO signatures available at the full report