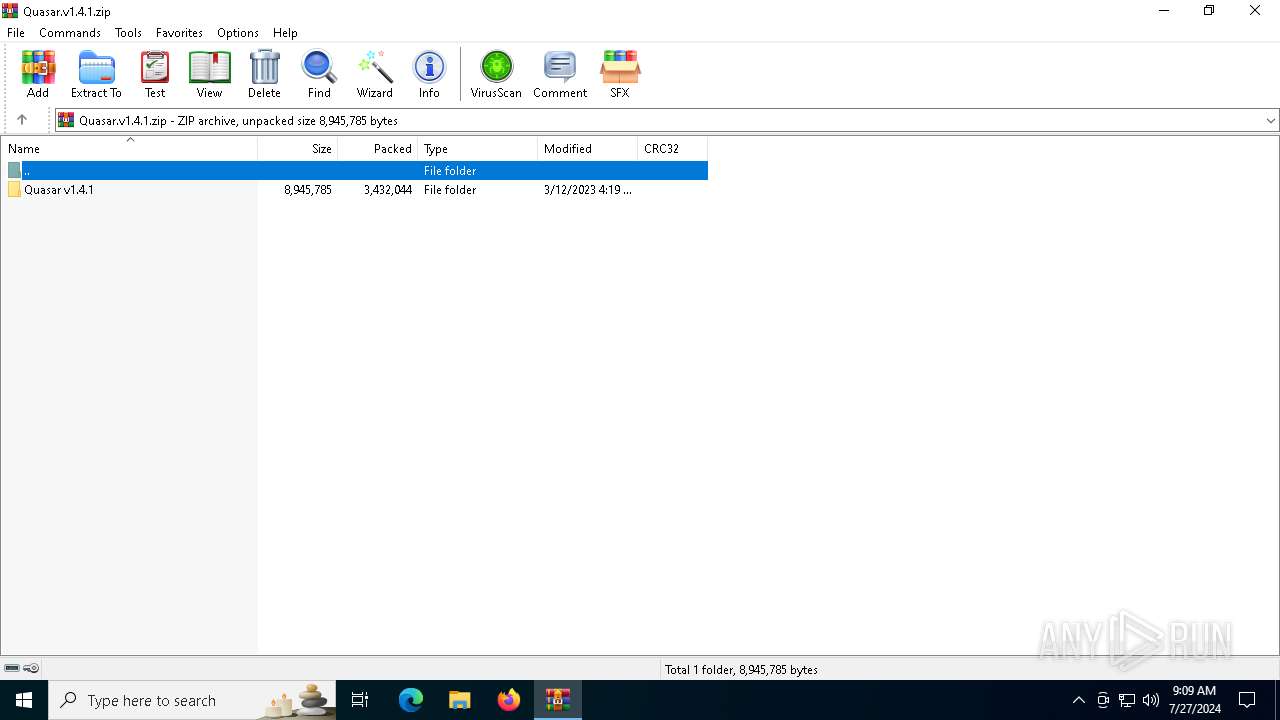
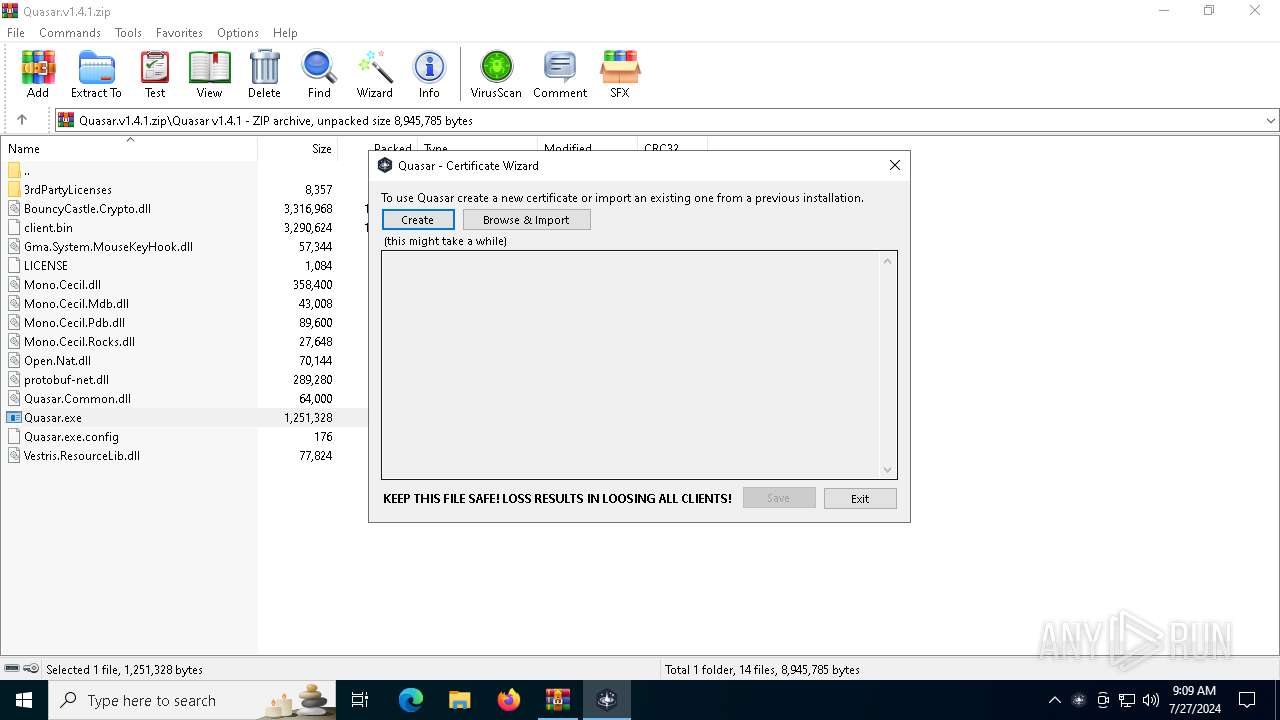
| File name: | Quasar.v1.4.1.zip |
| Full analysis: | https://app.any.run/tasks/2a13463d-5452-4f44-8f8a-21d8c5251455 |
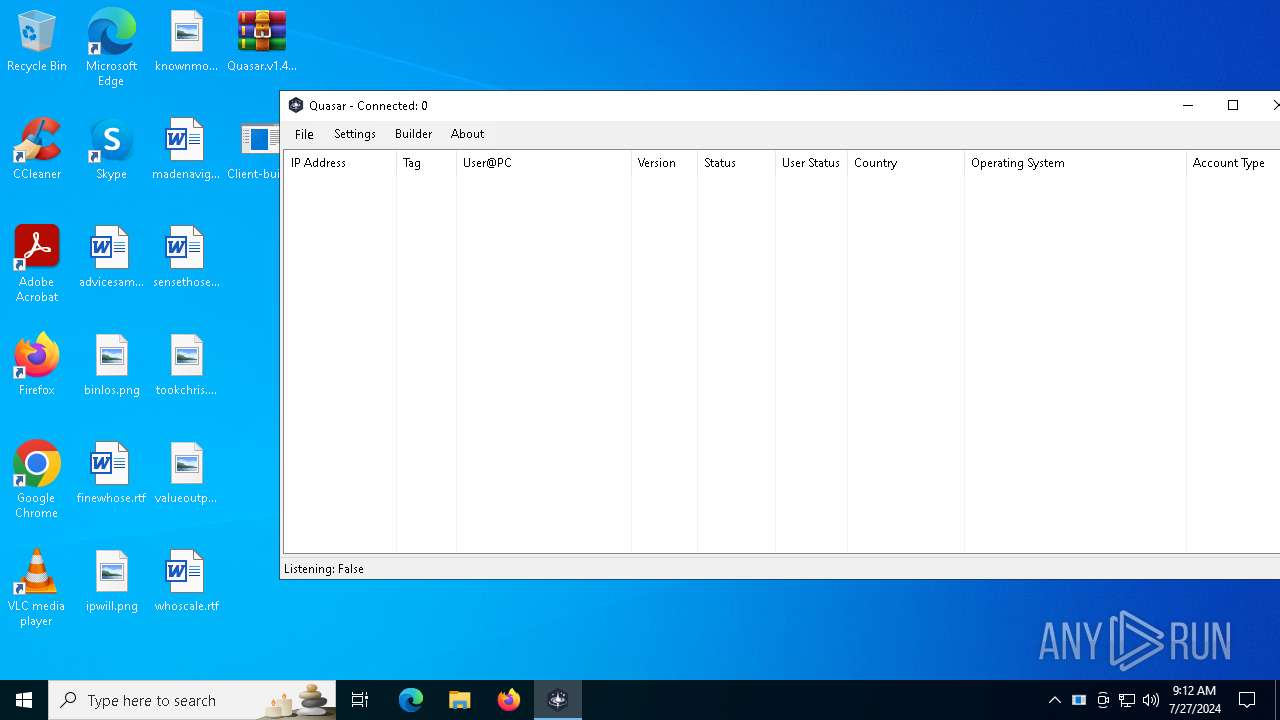
| Verdict: | Malicious activity |
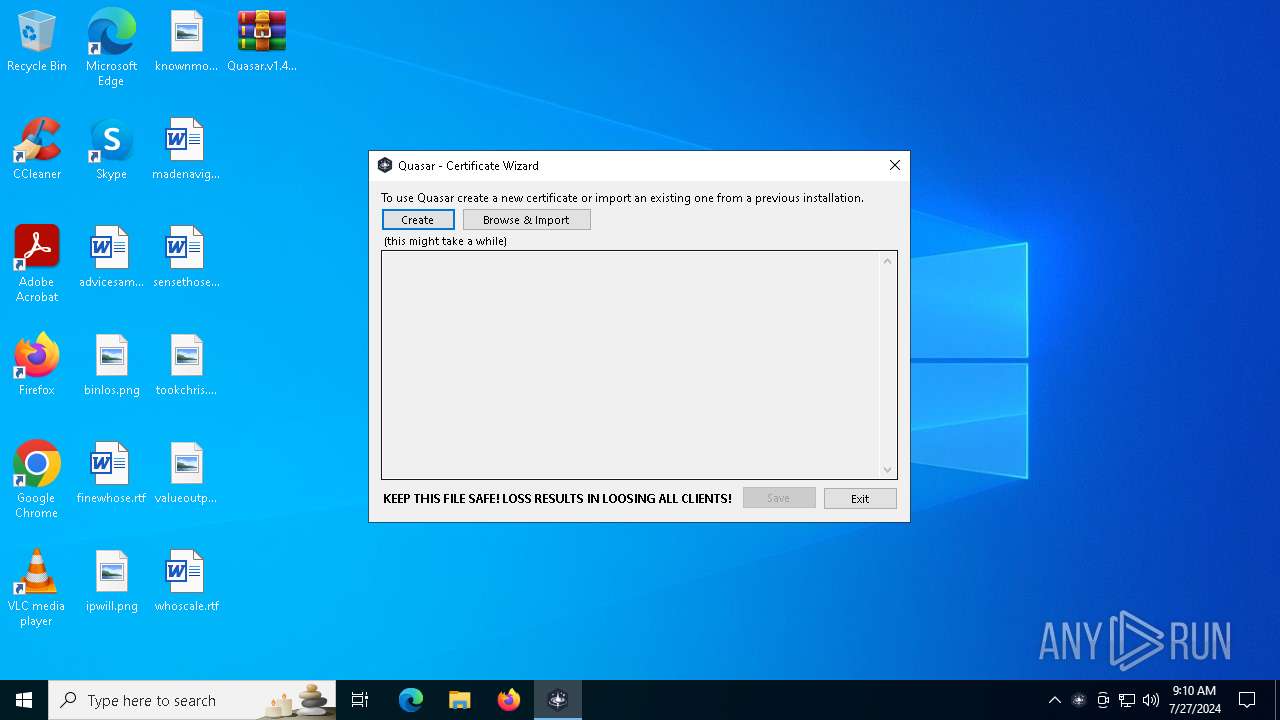
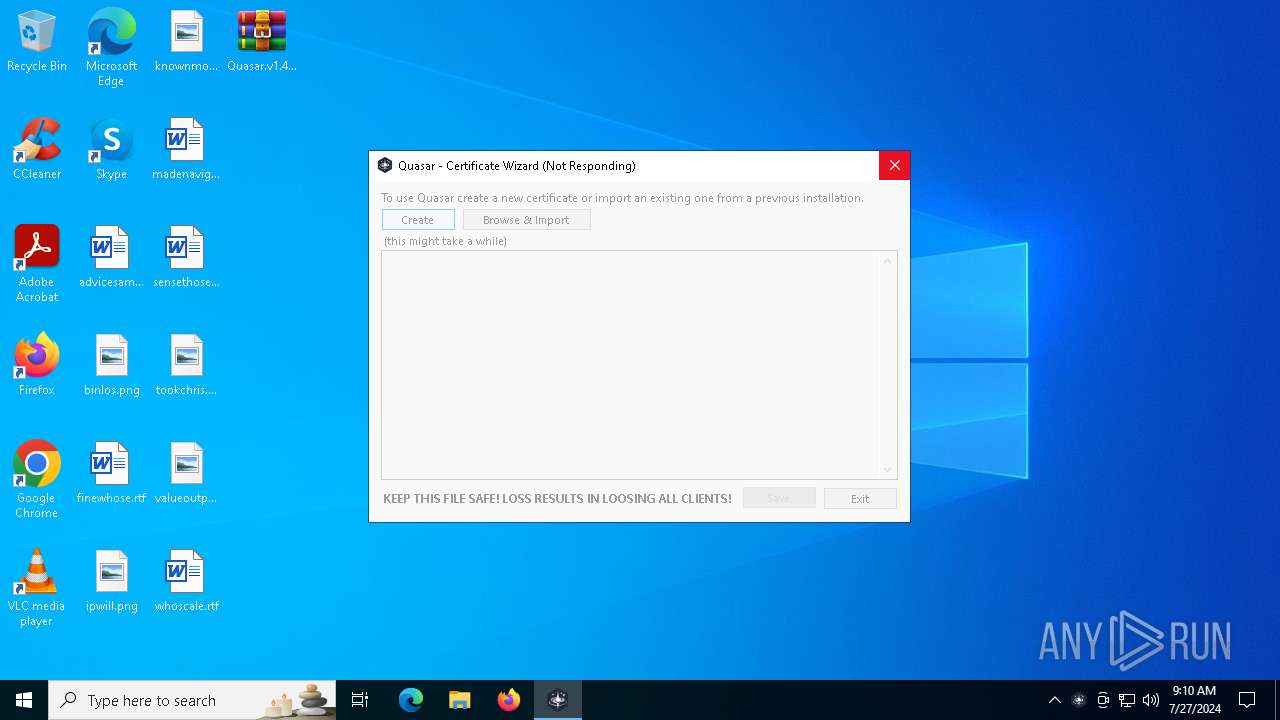
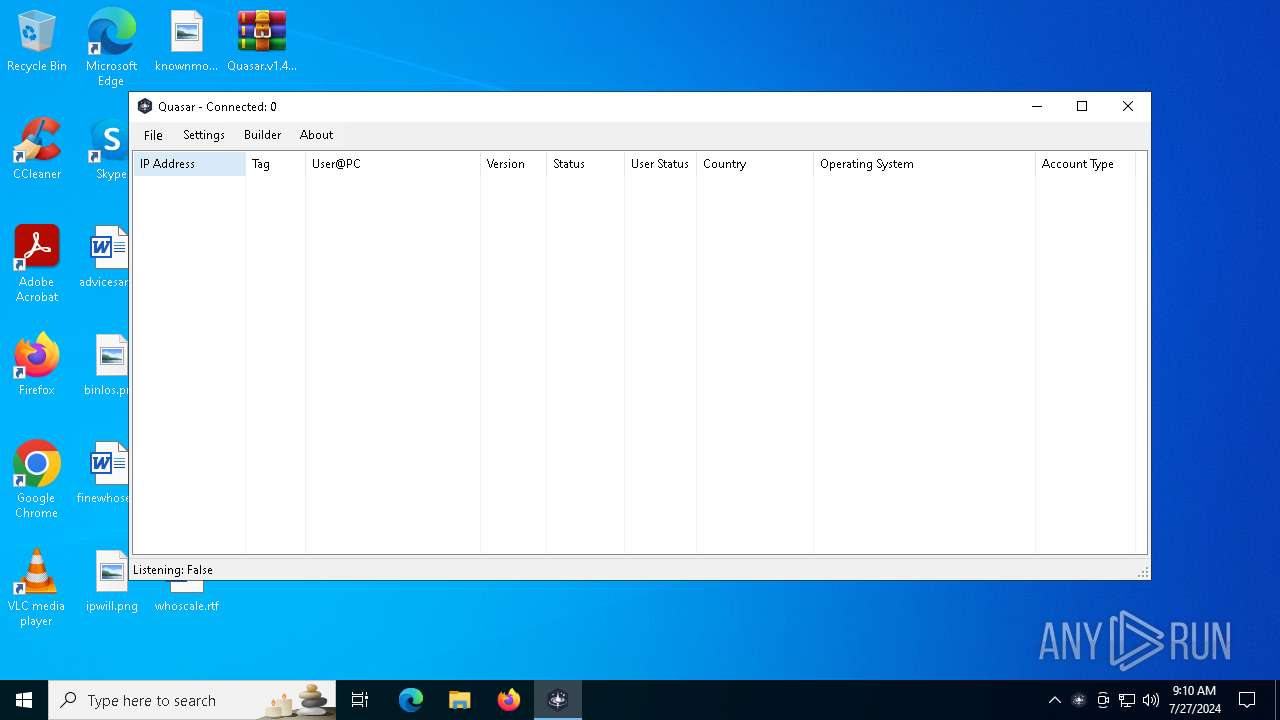
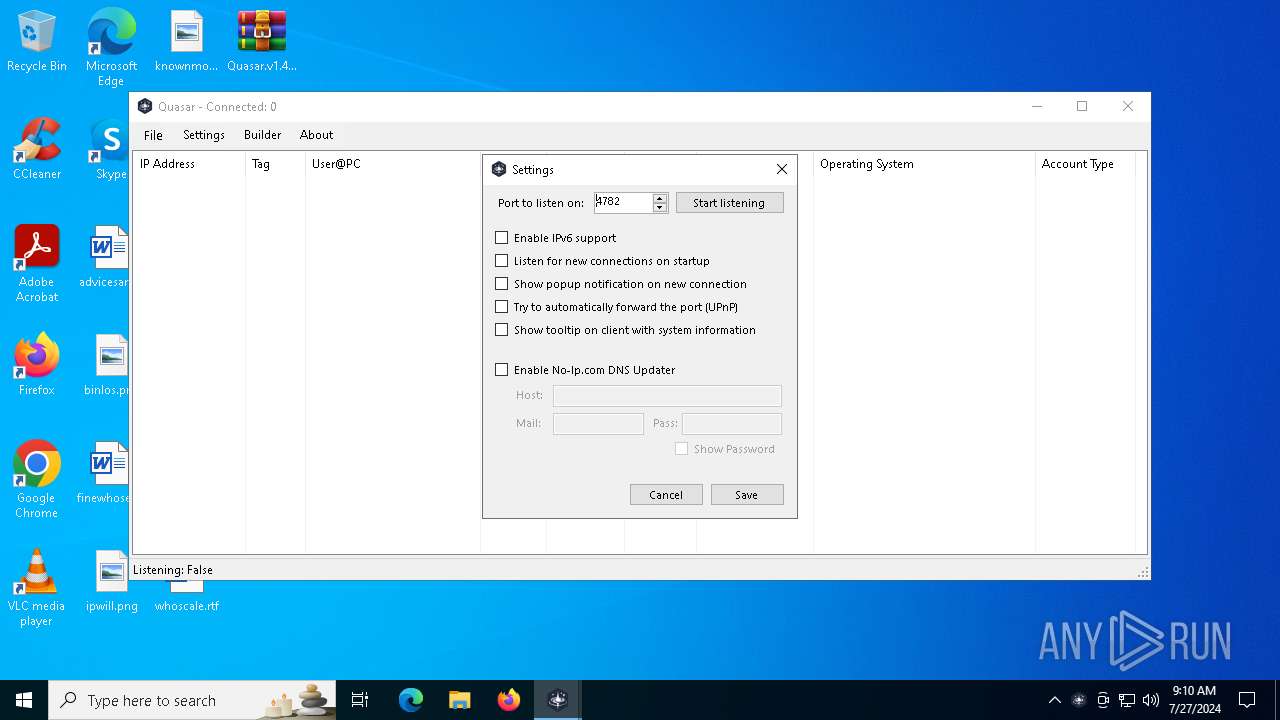
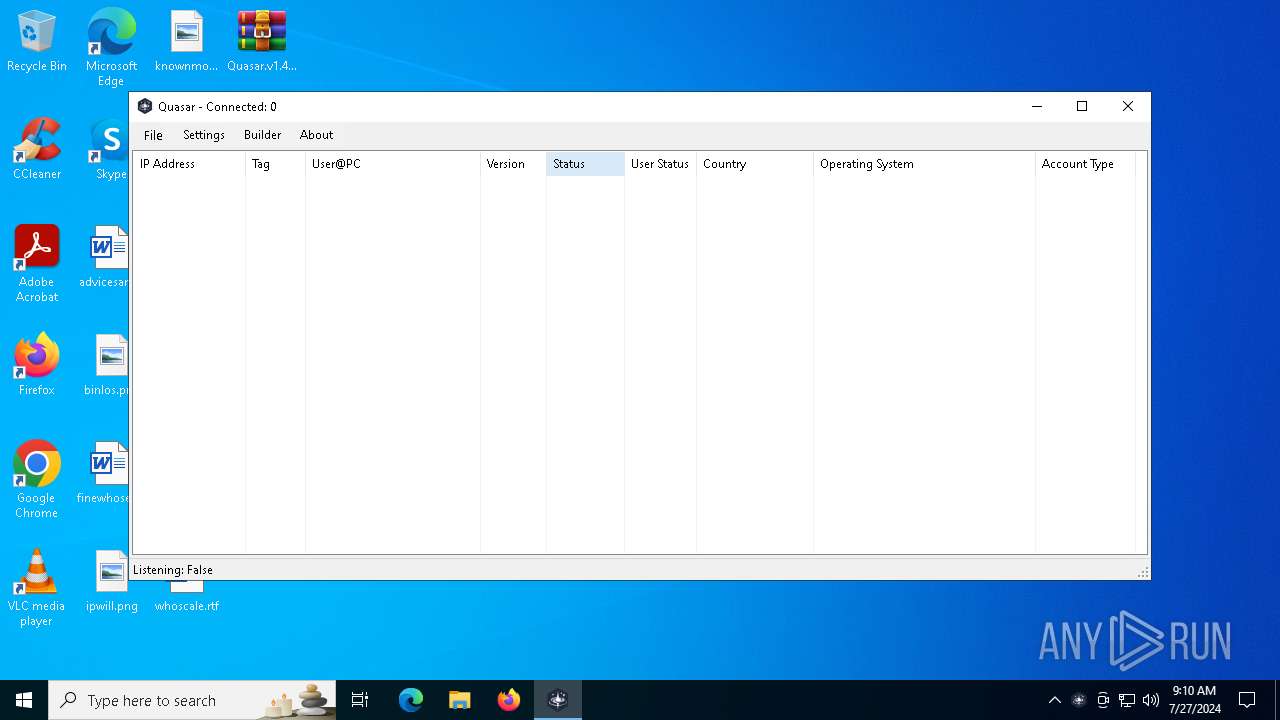
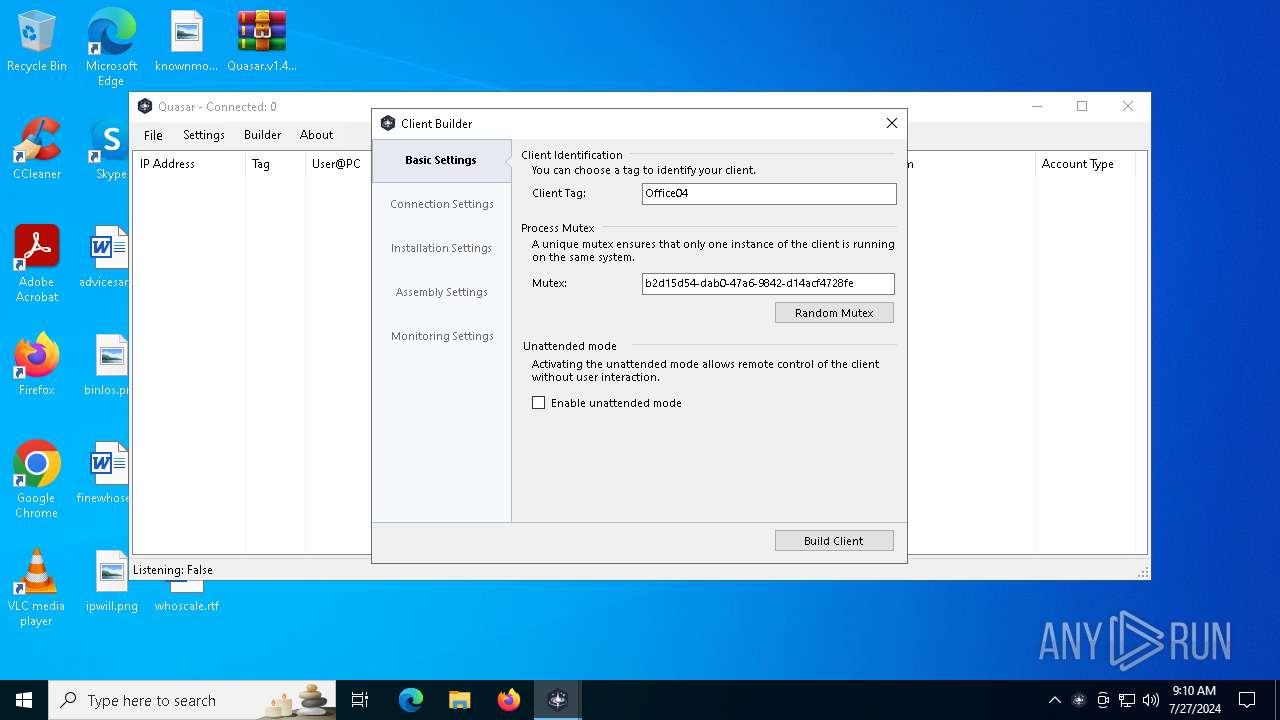
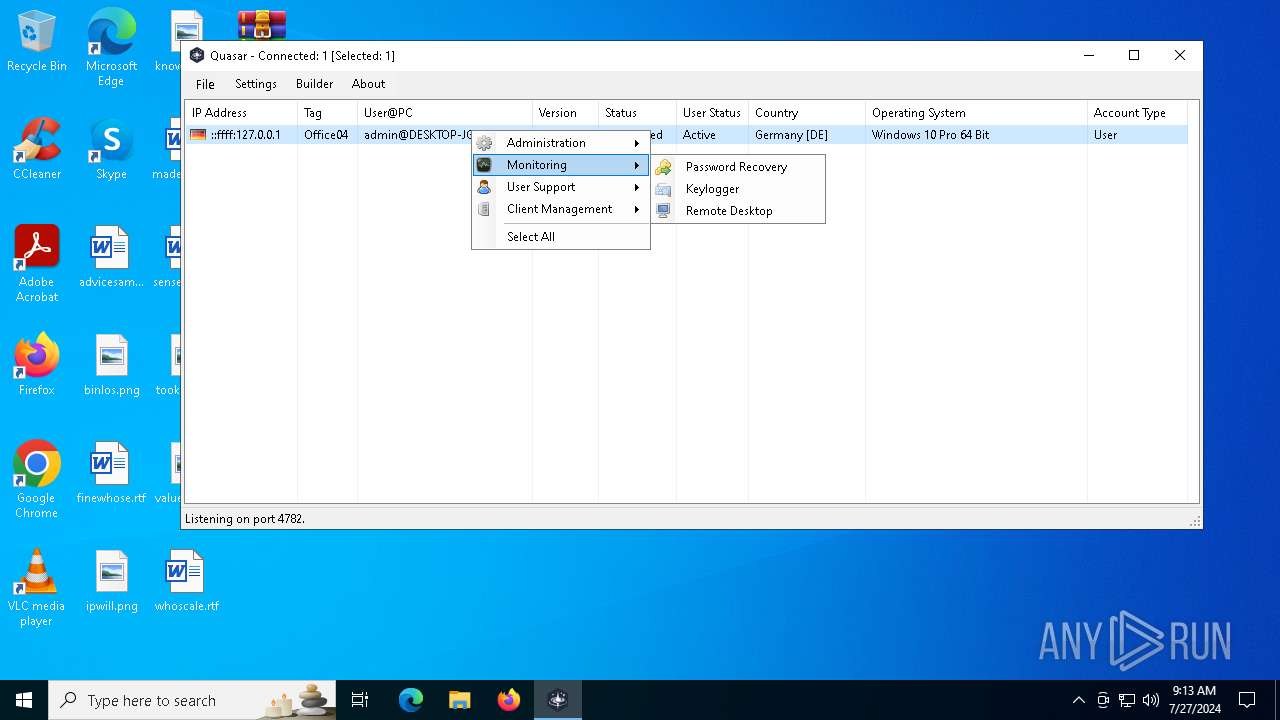
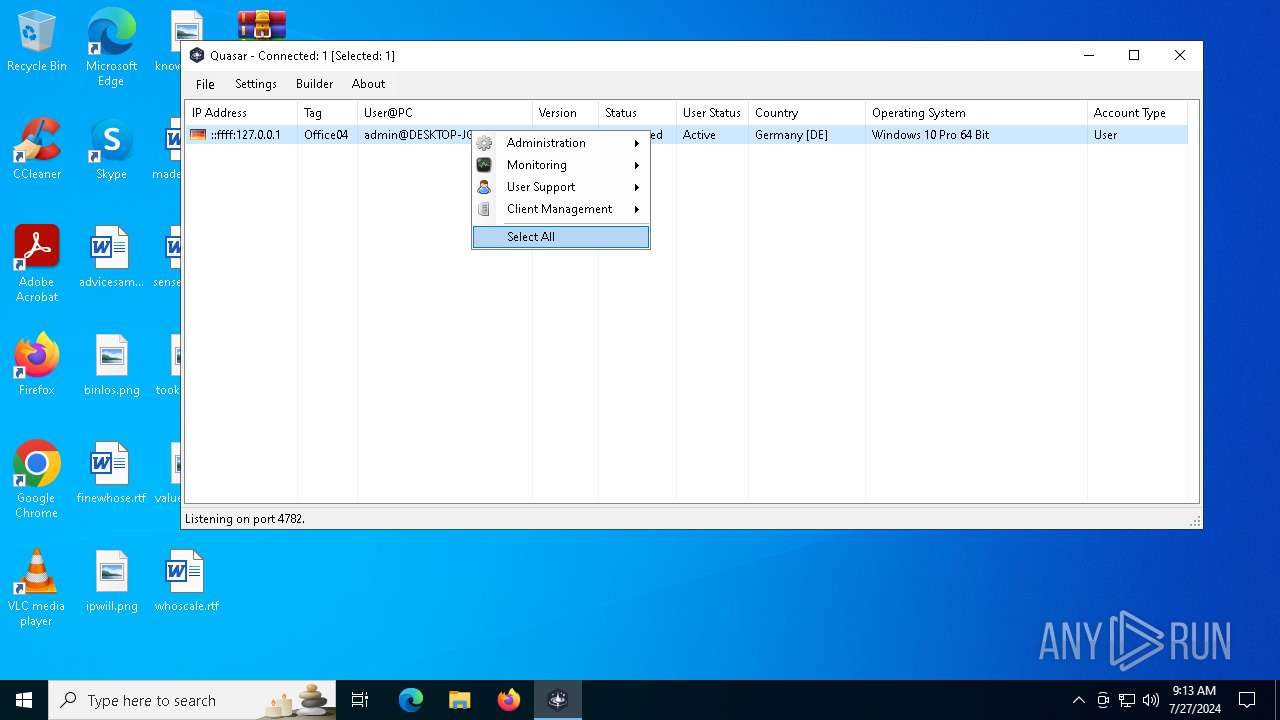
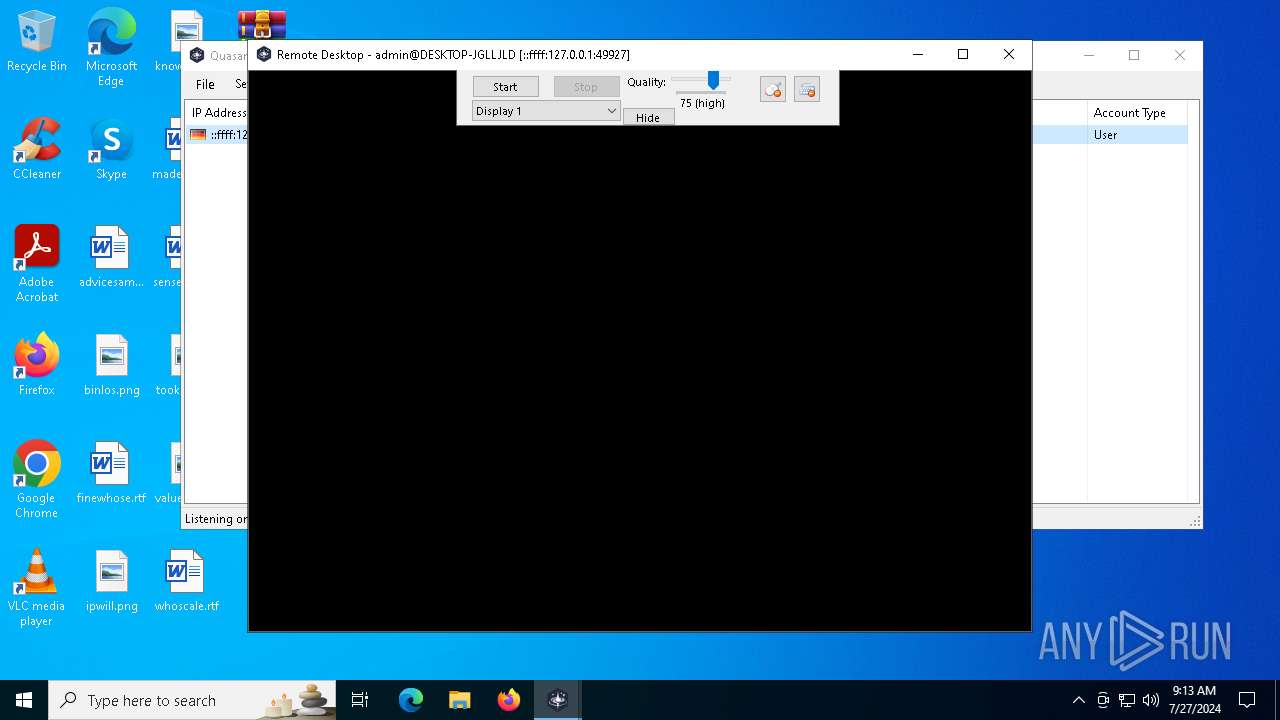
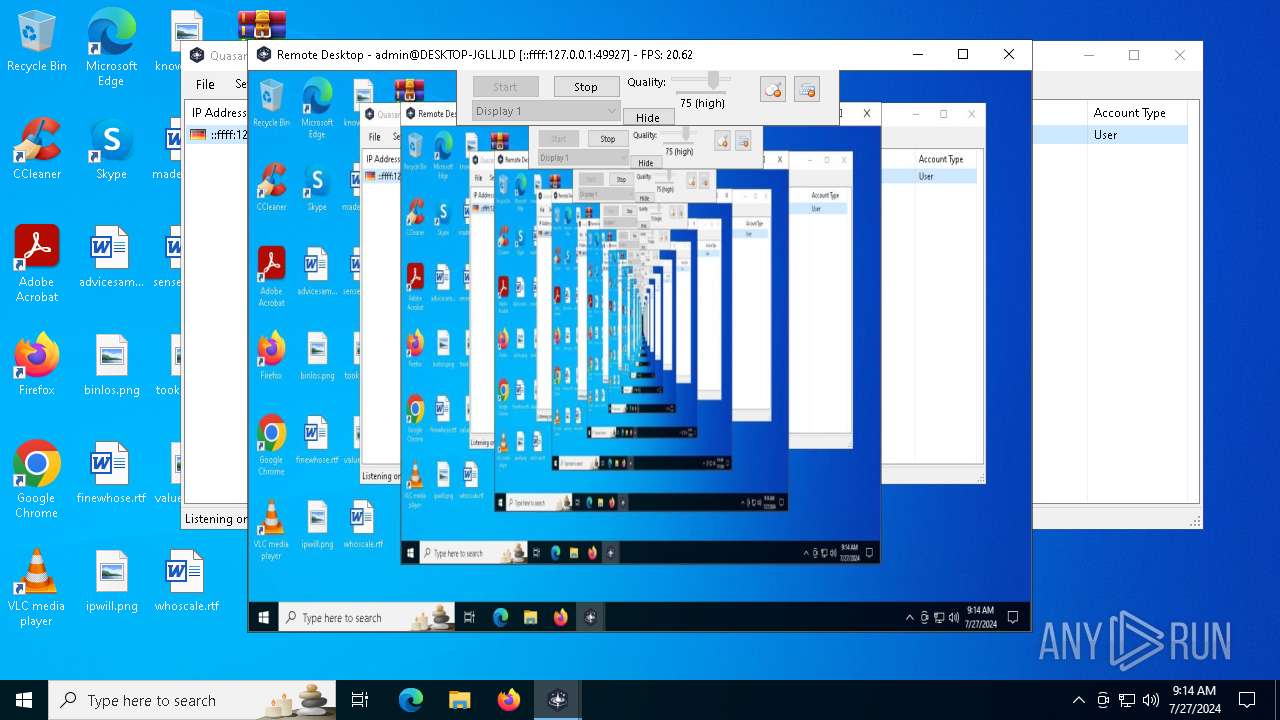
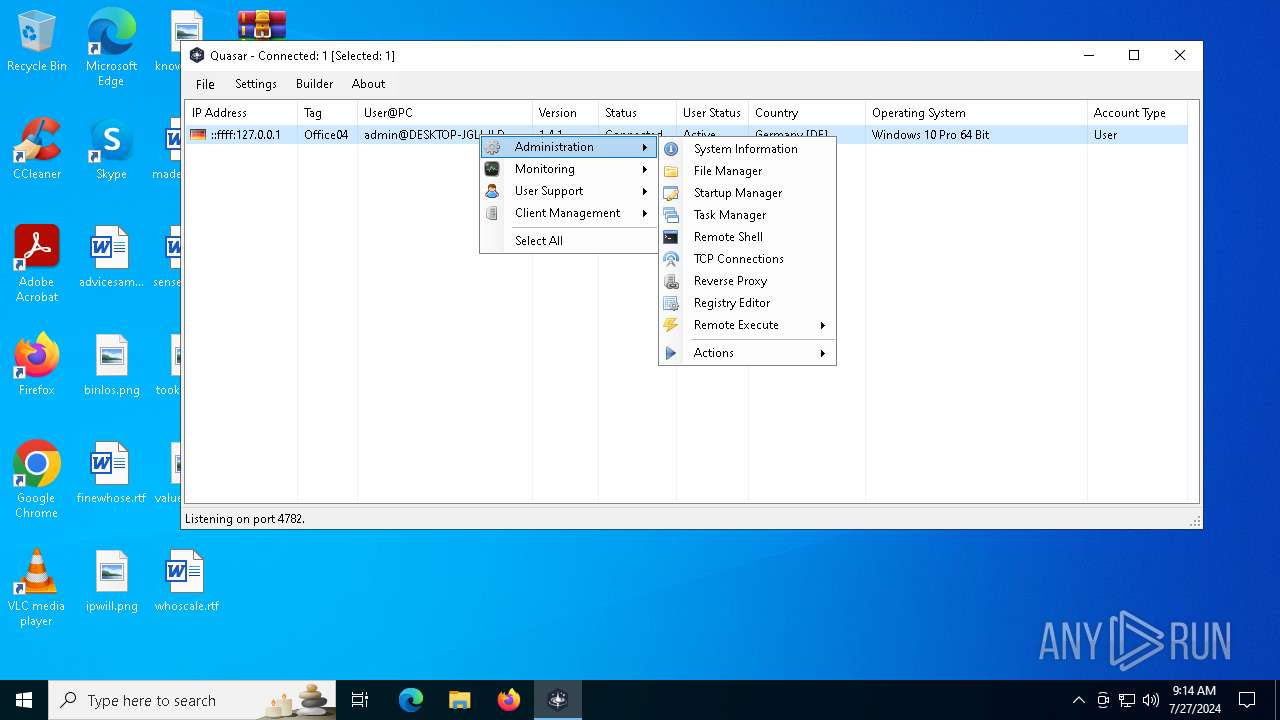
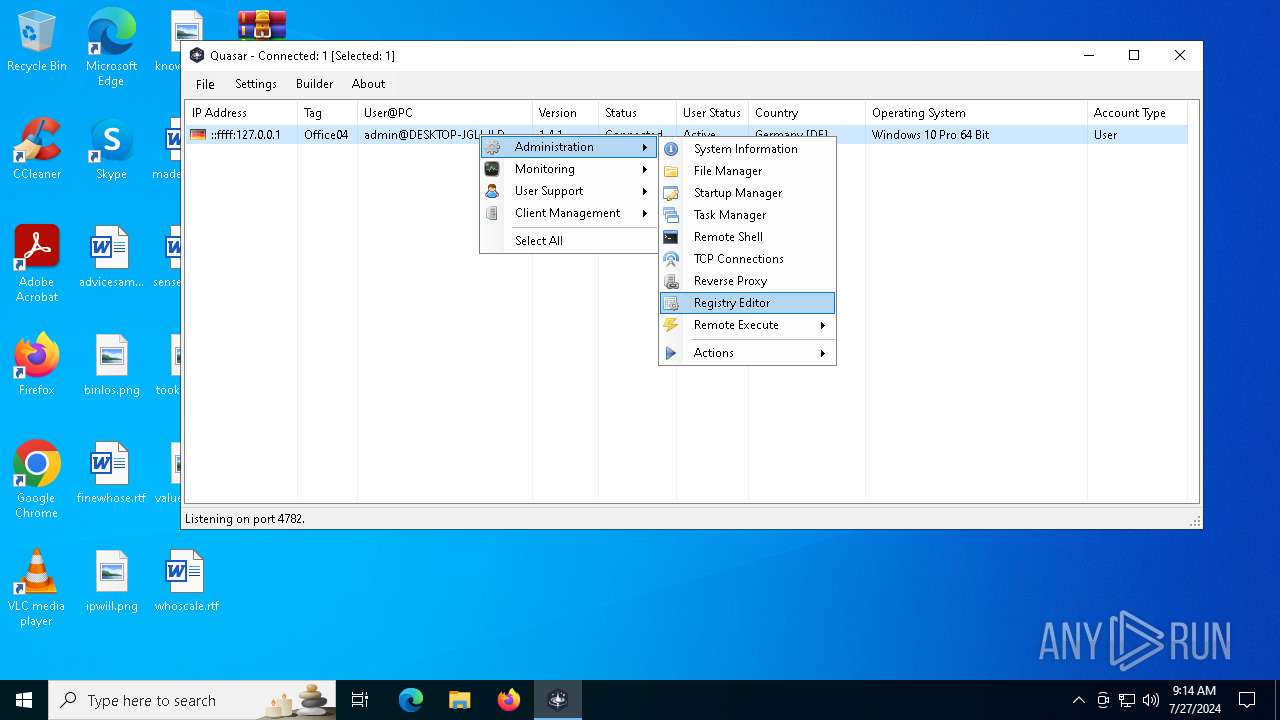
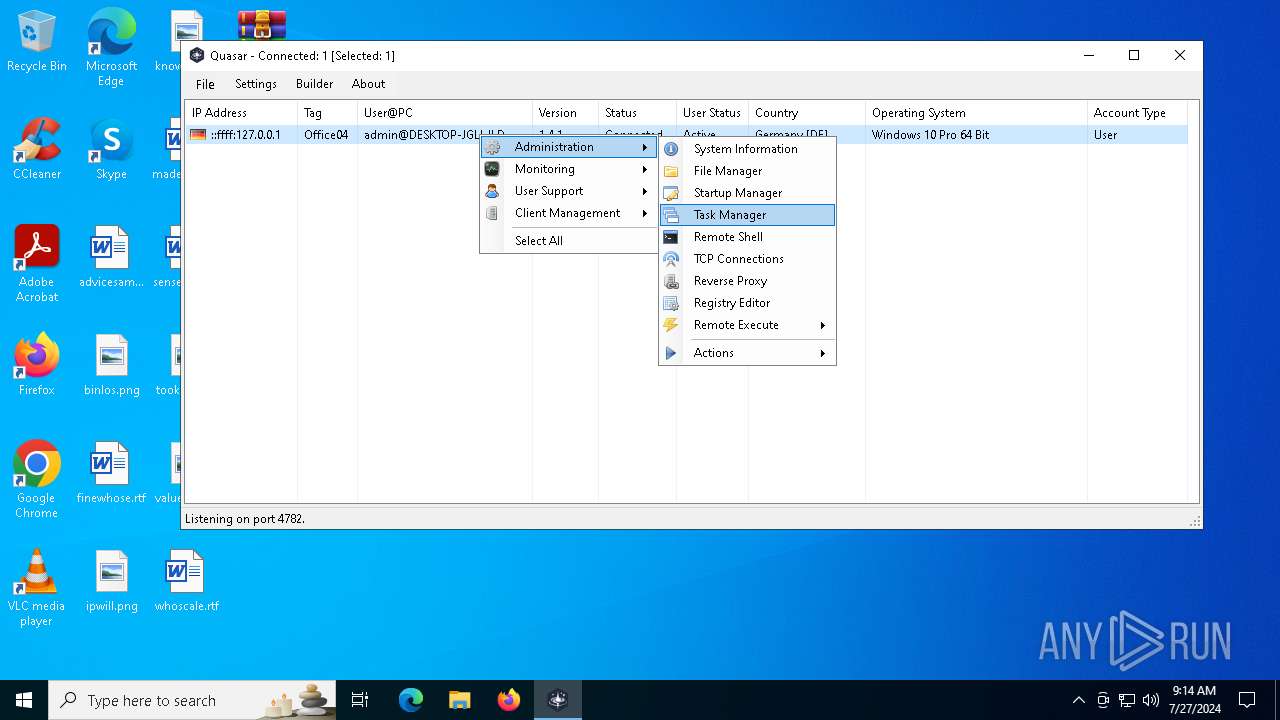
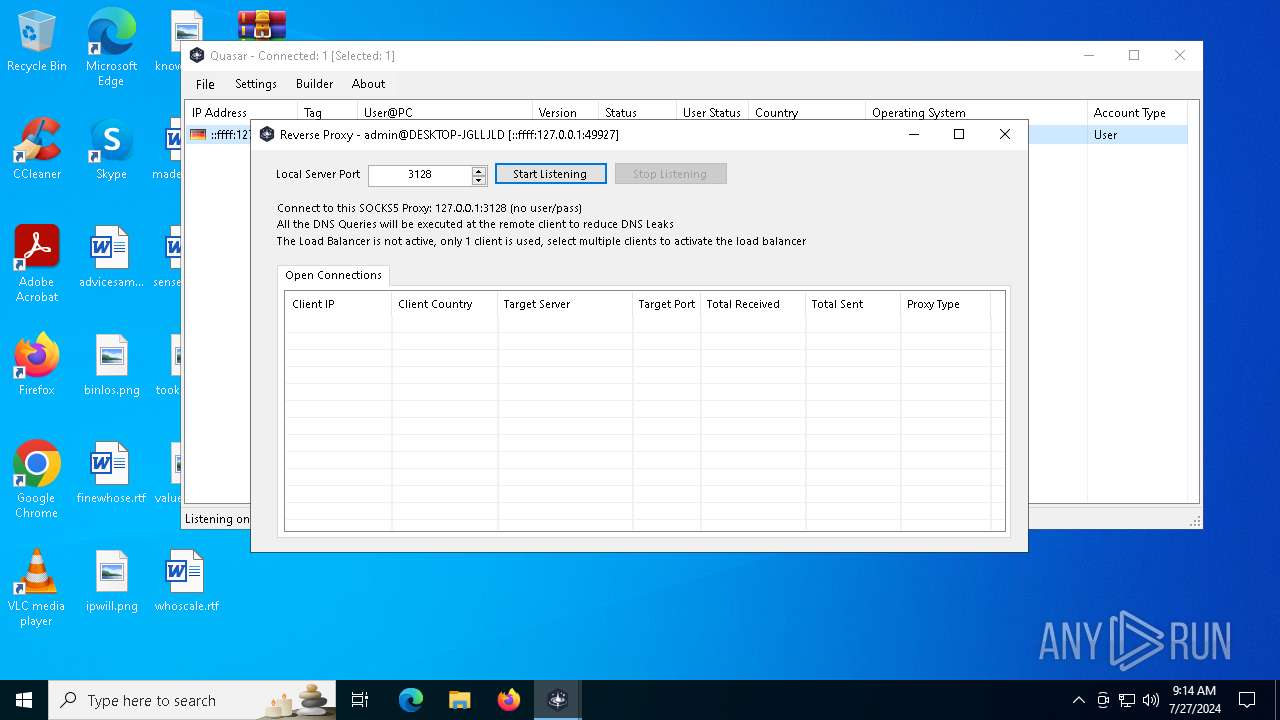
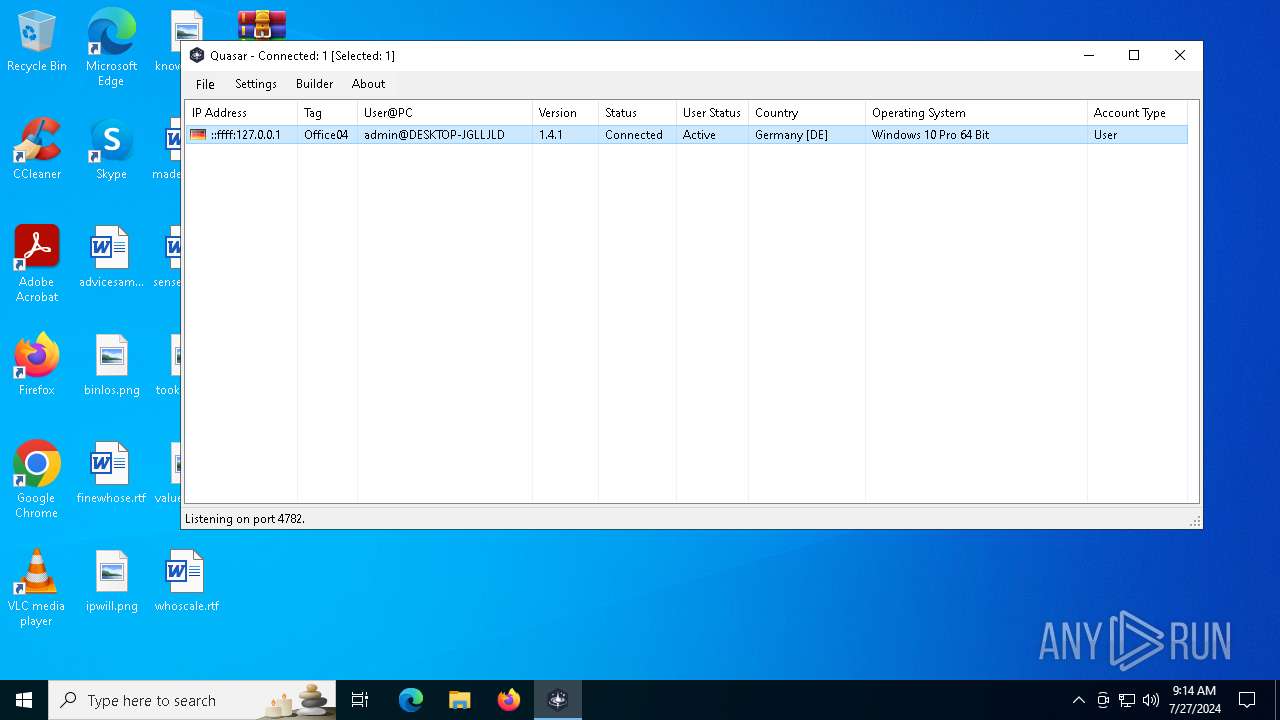
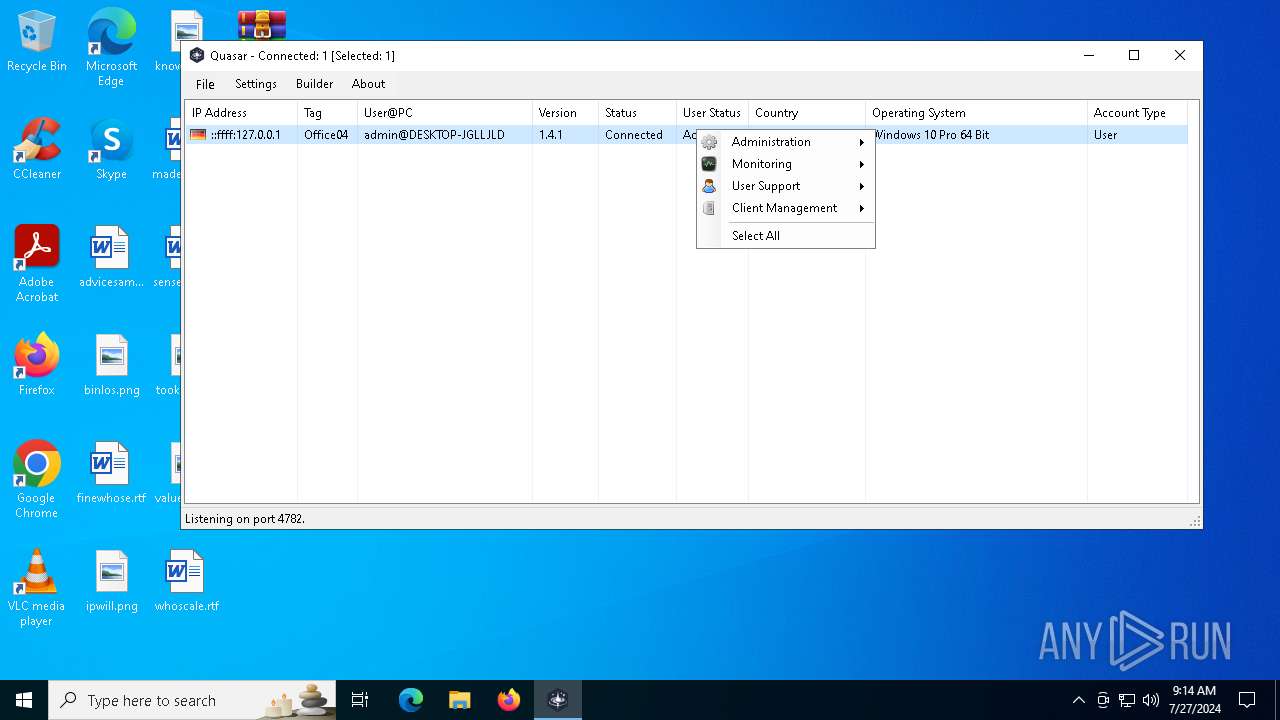
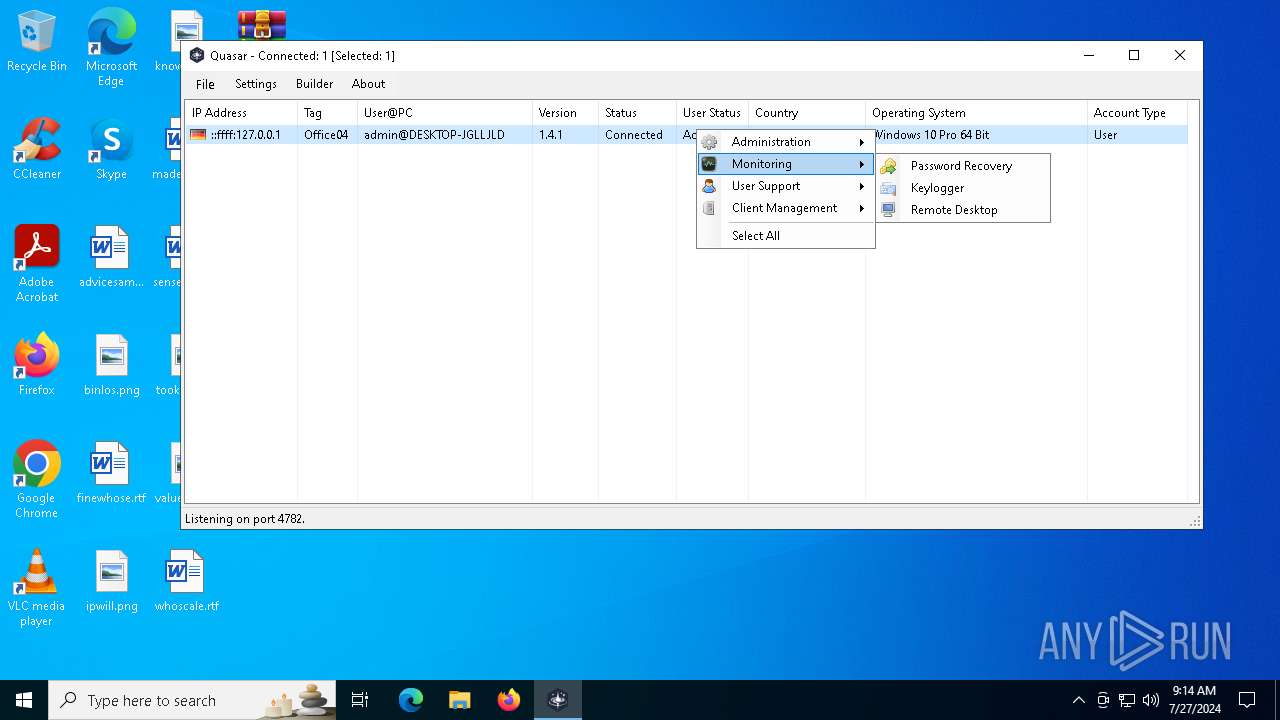
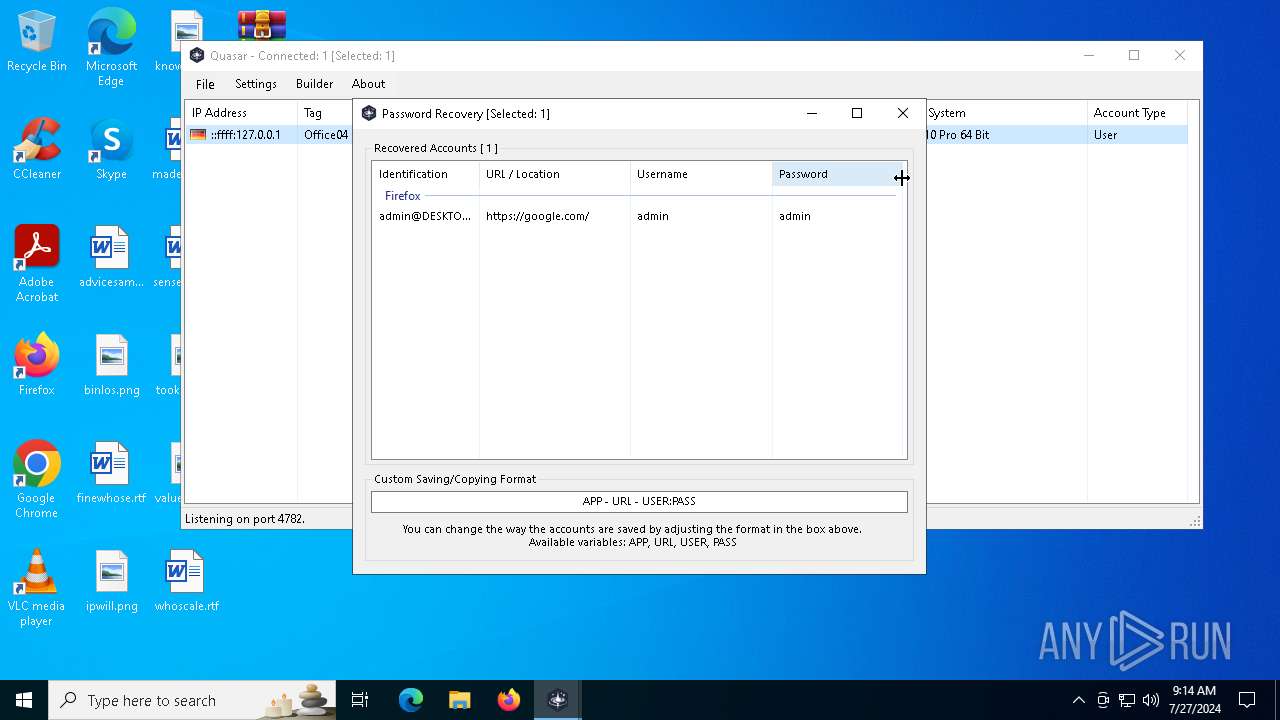
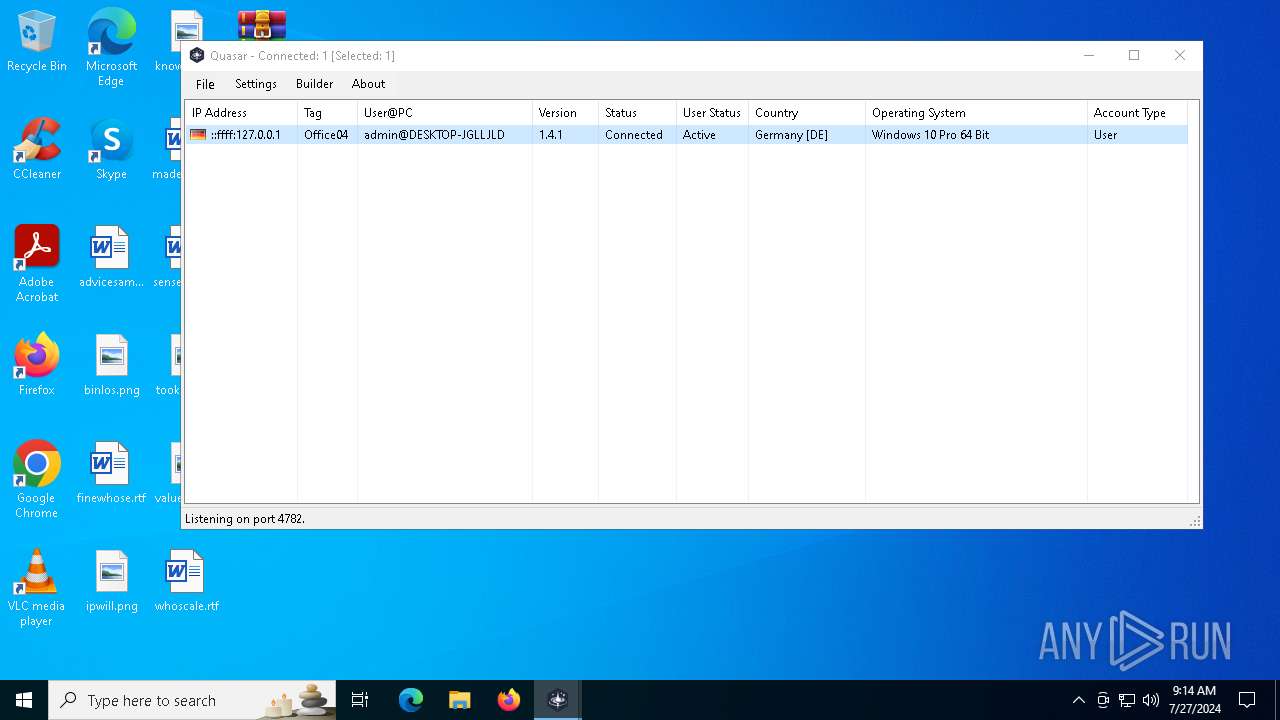
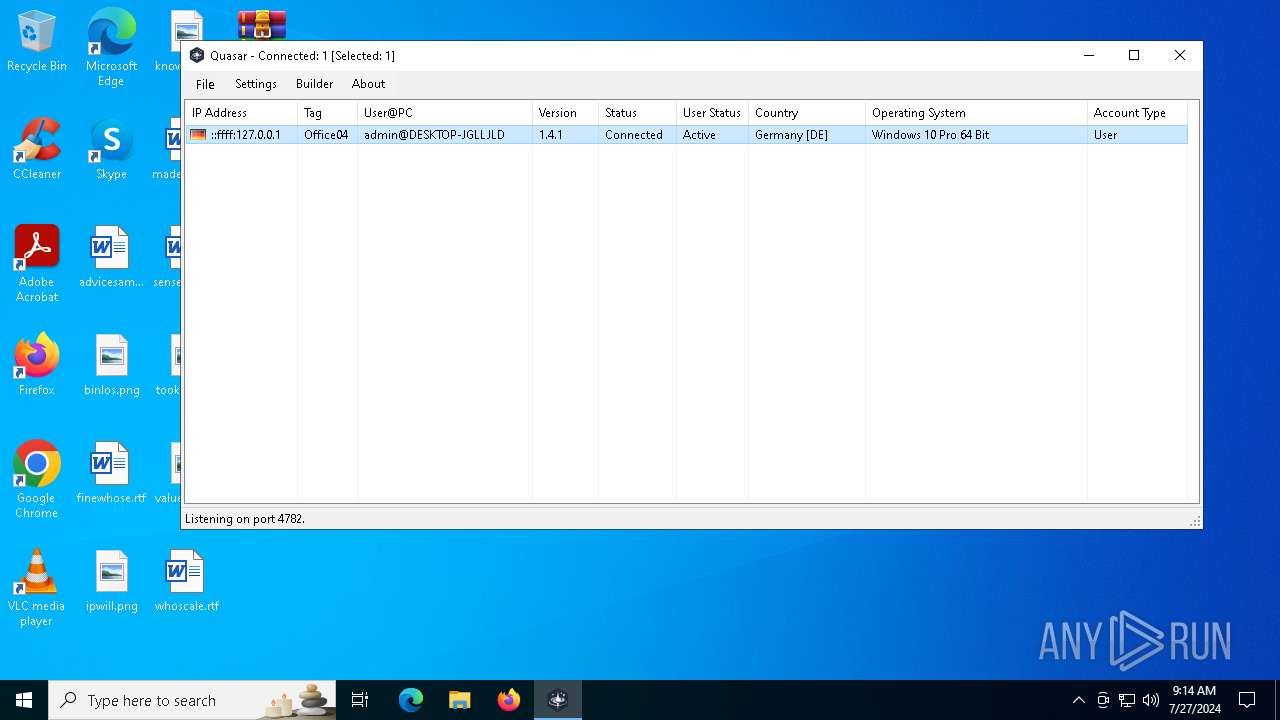
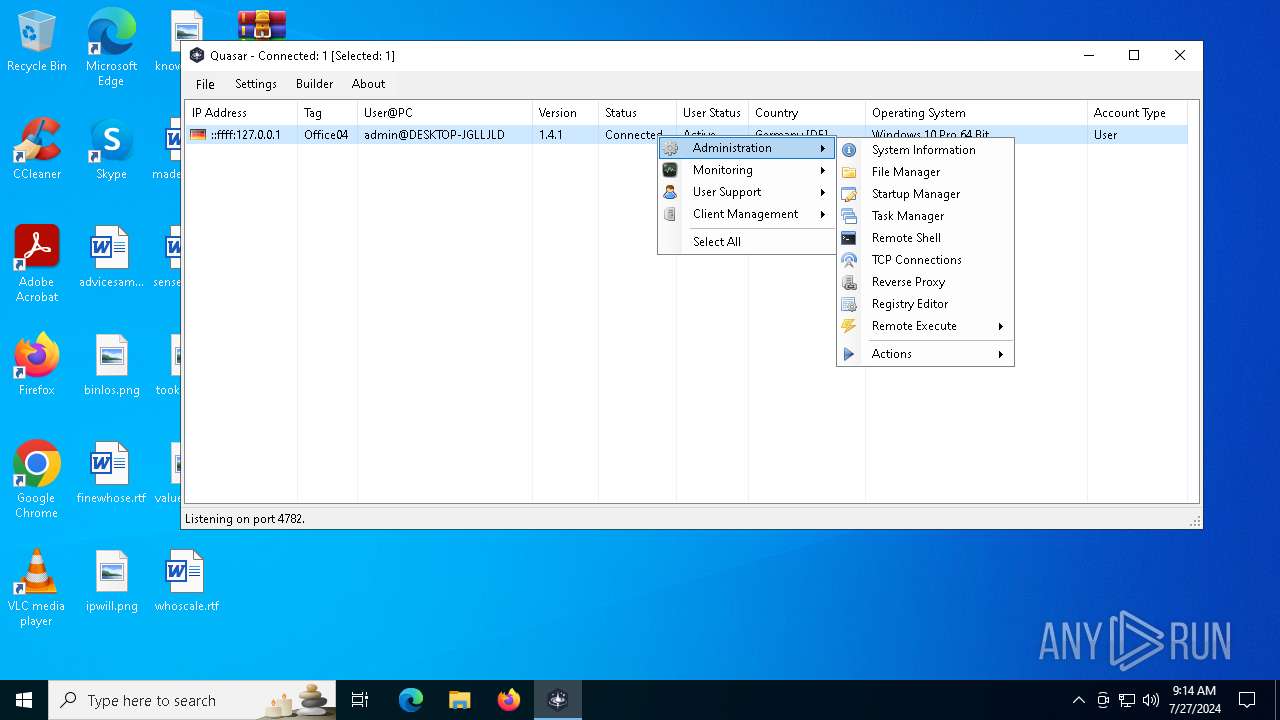
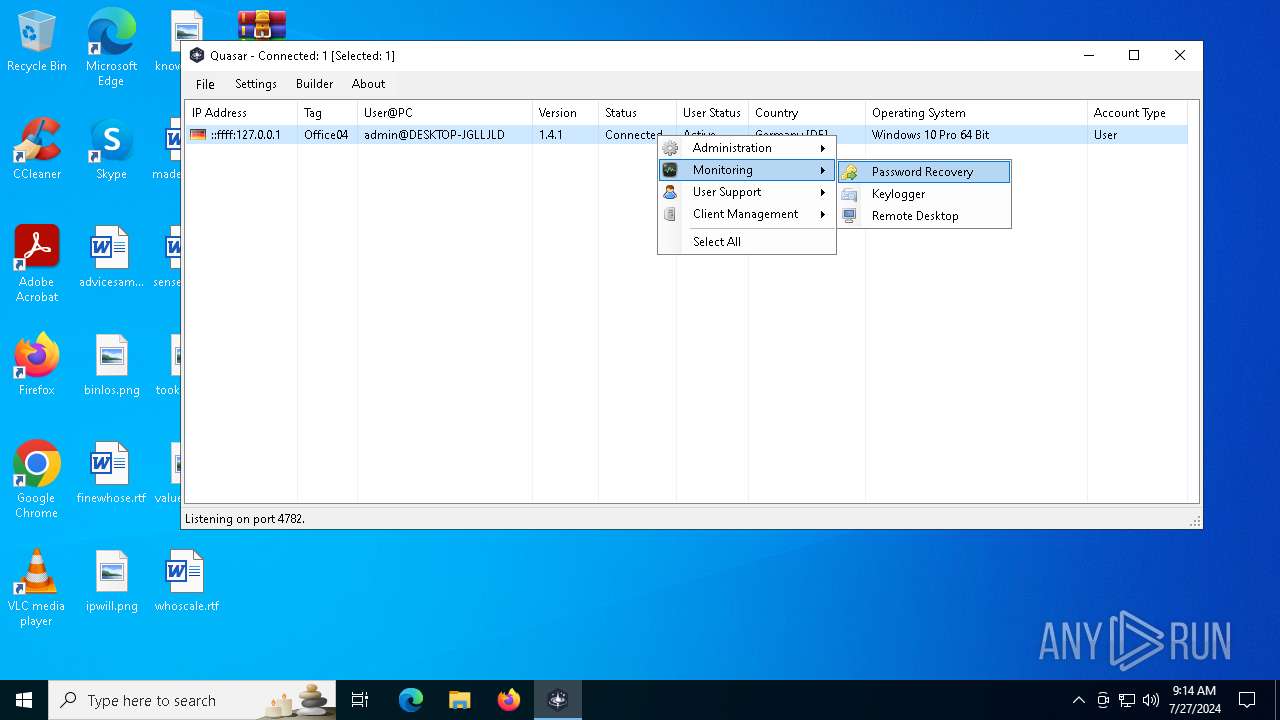
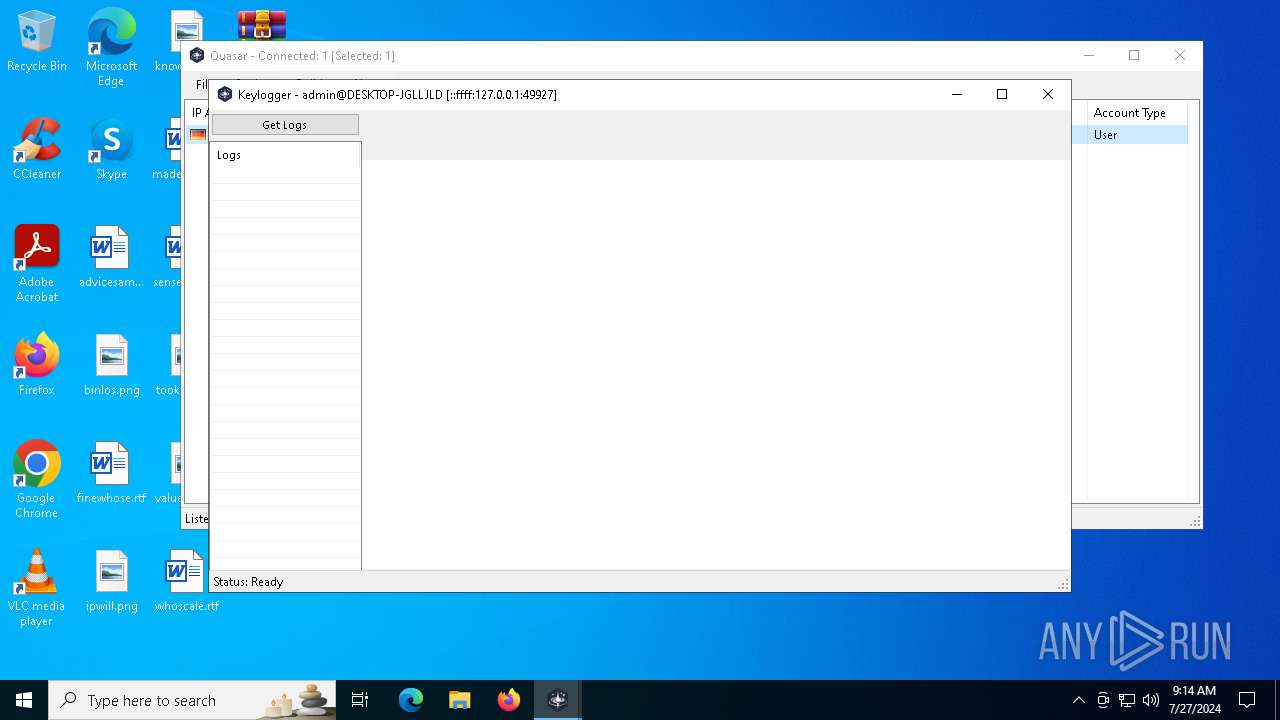
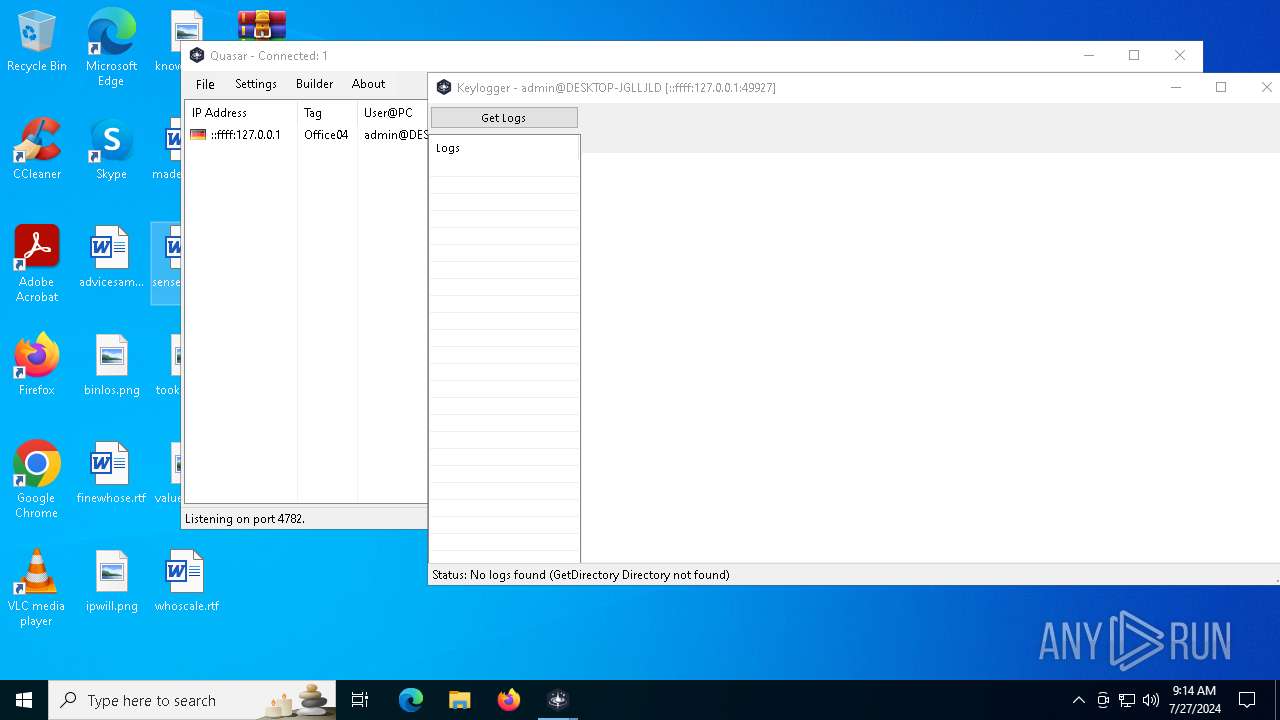
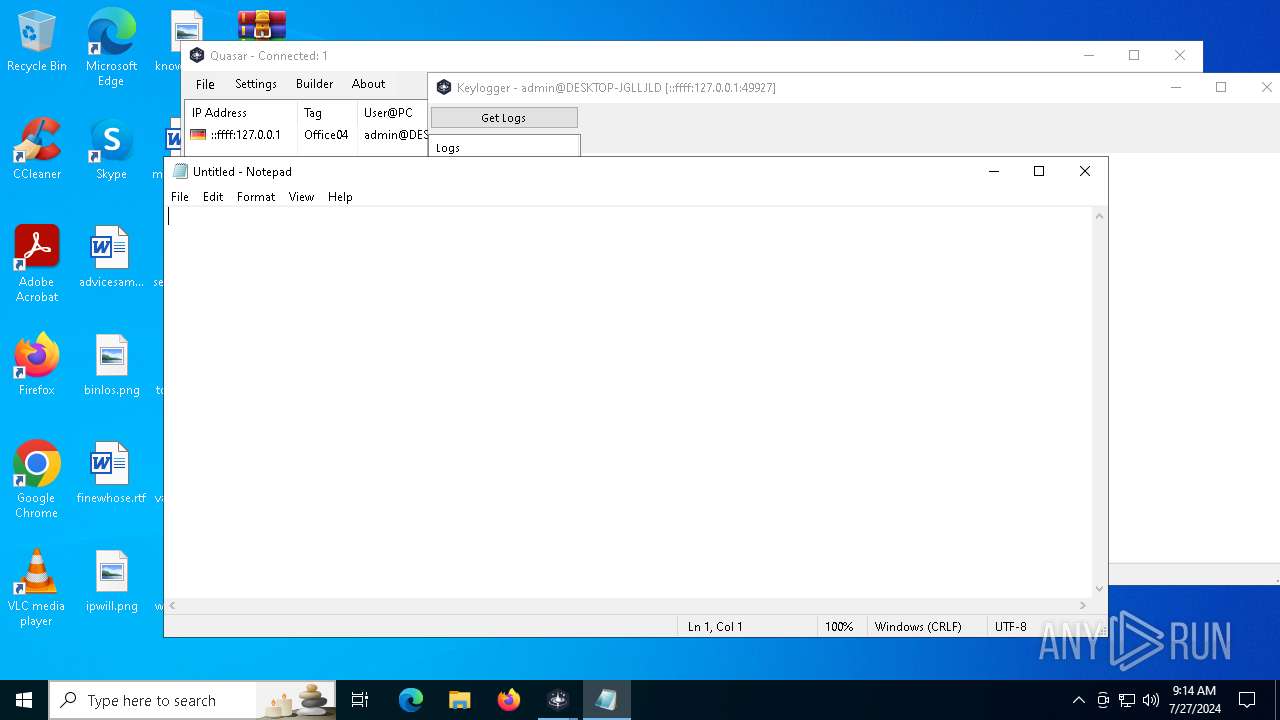
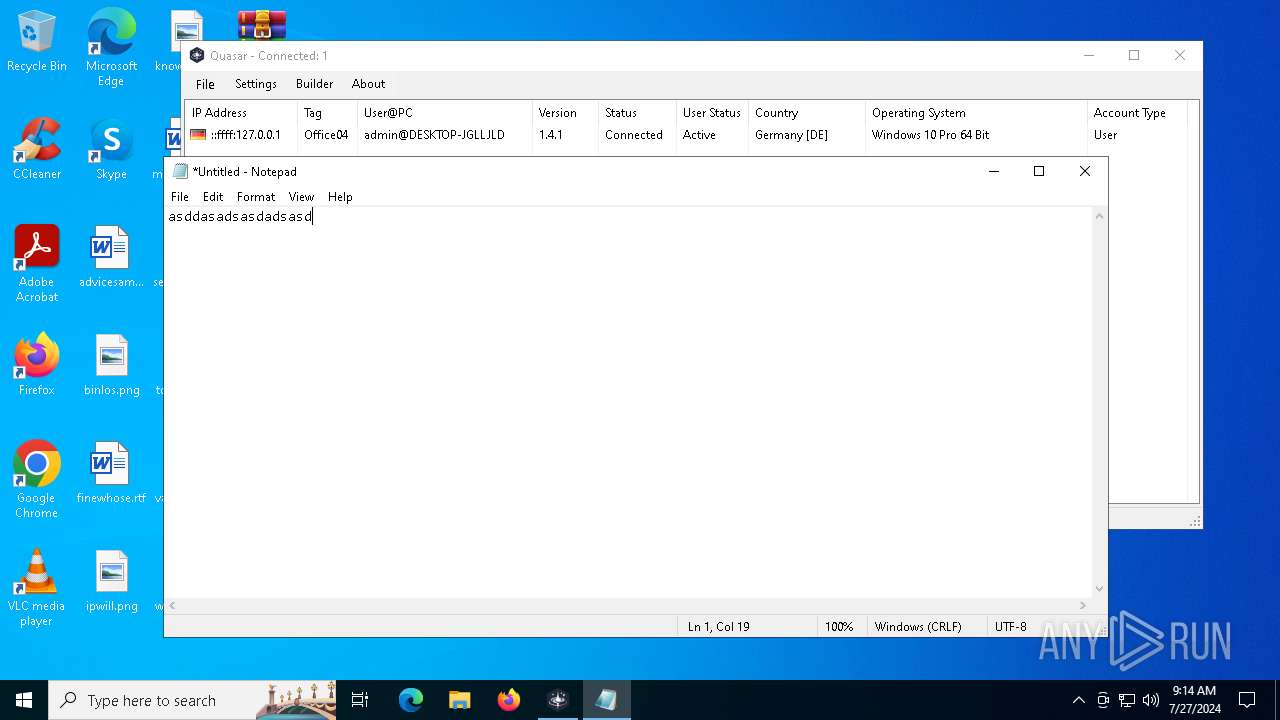
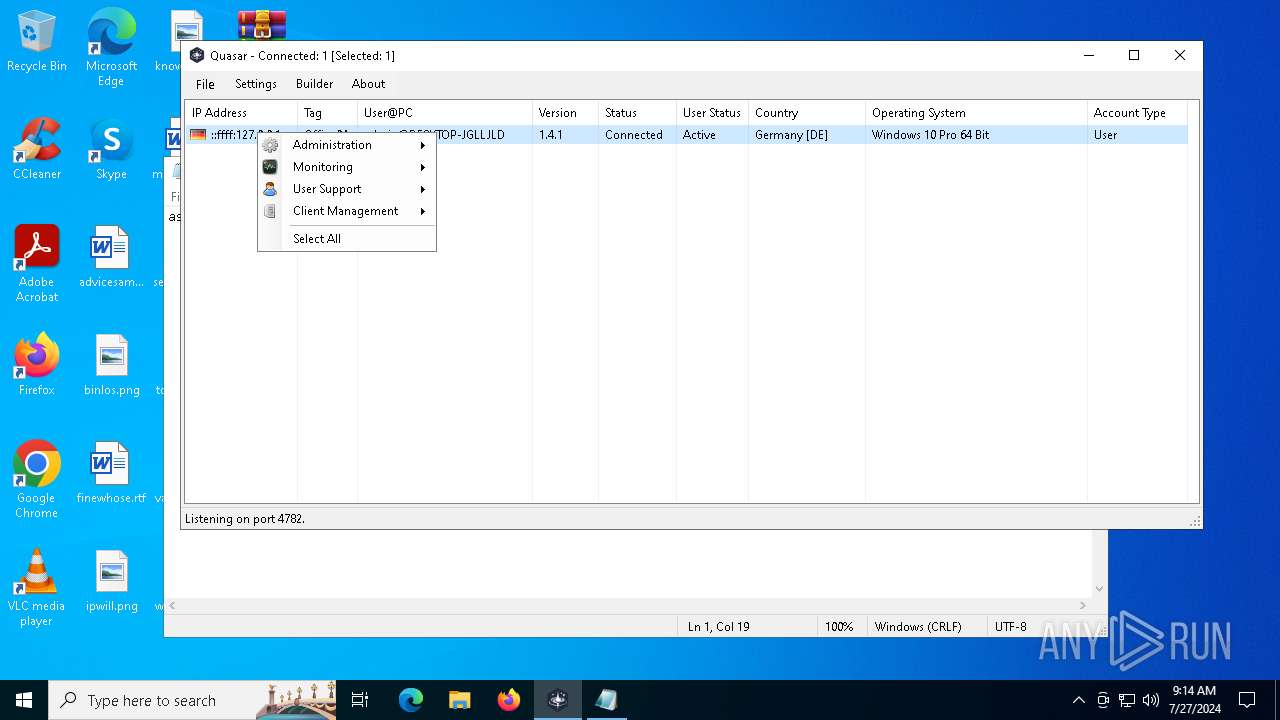
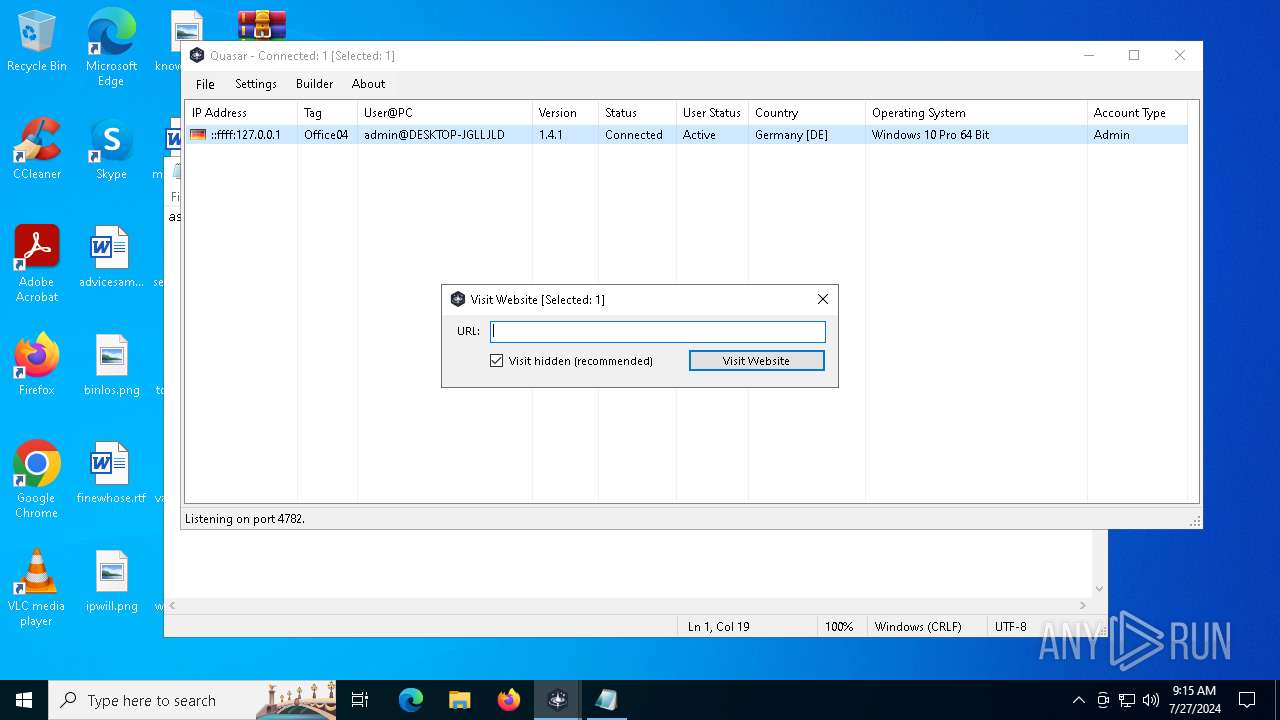
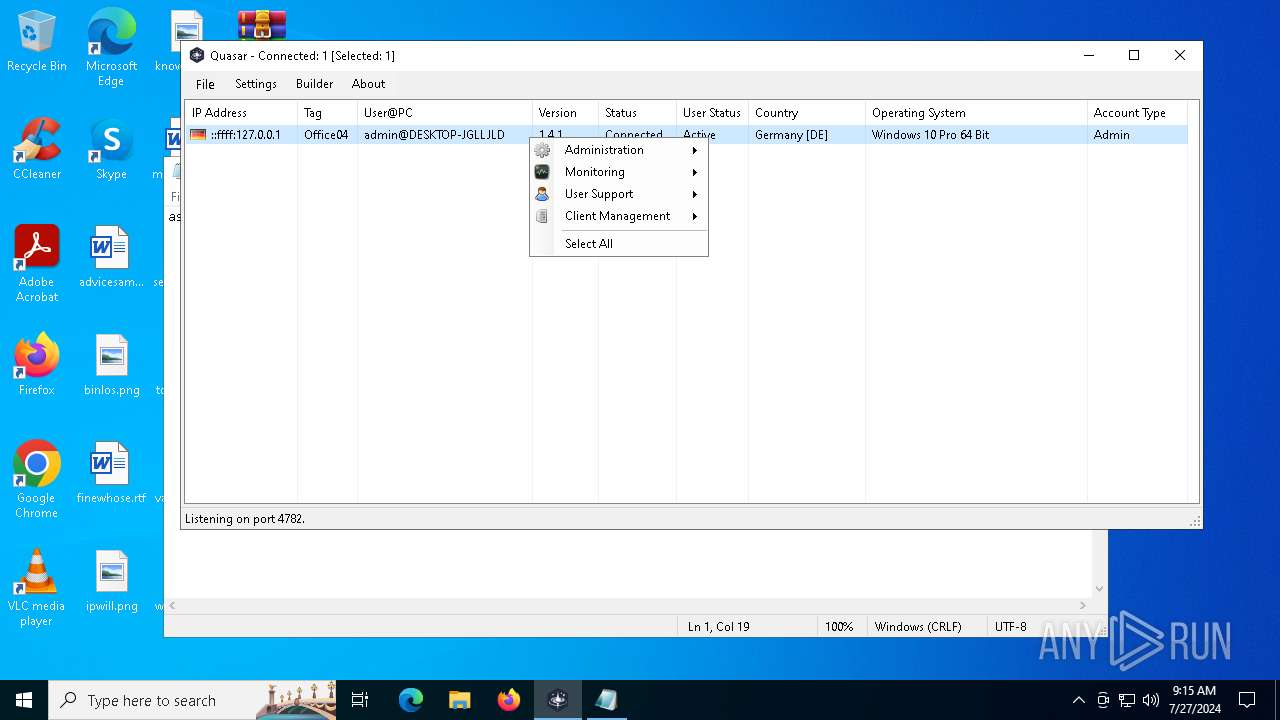
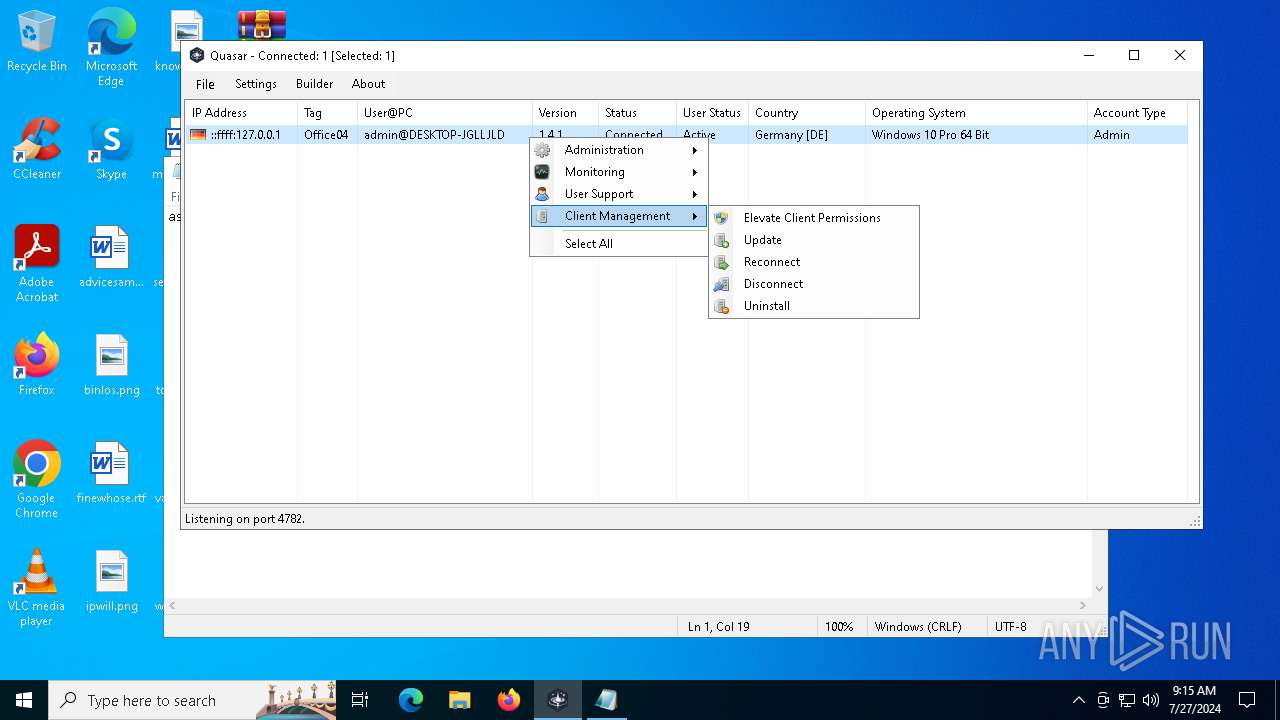
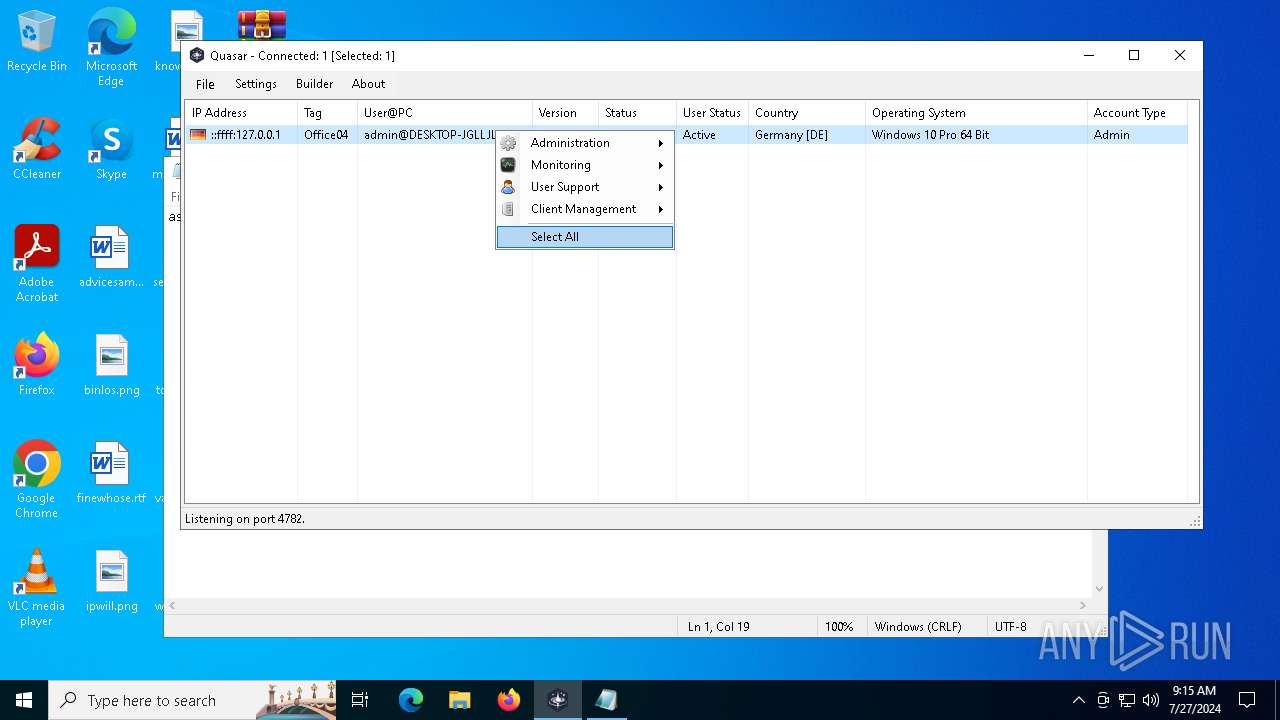
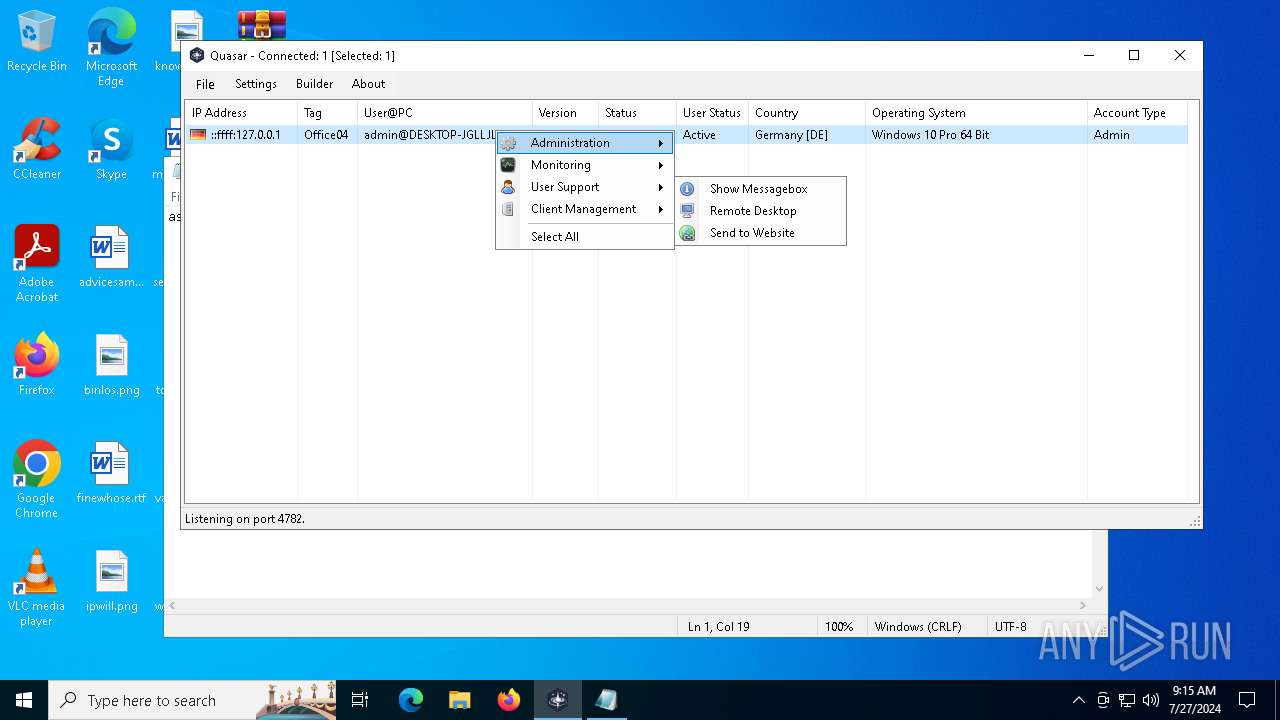
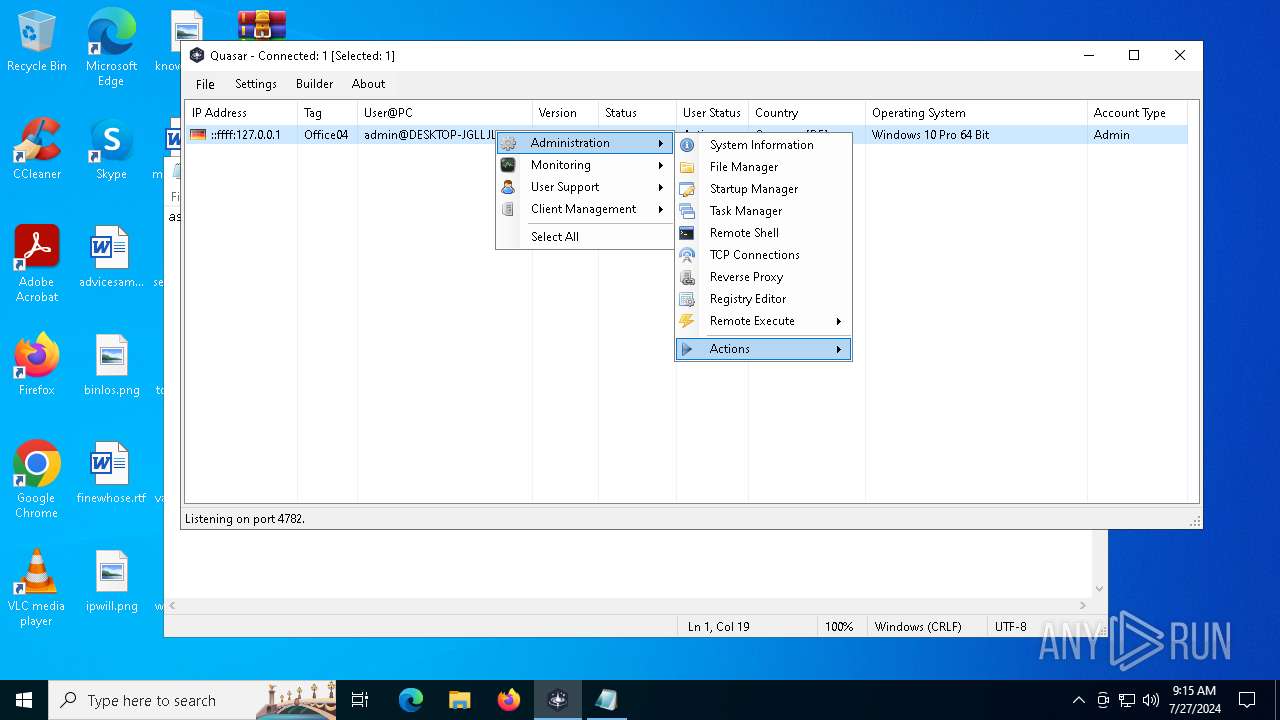
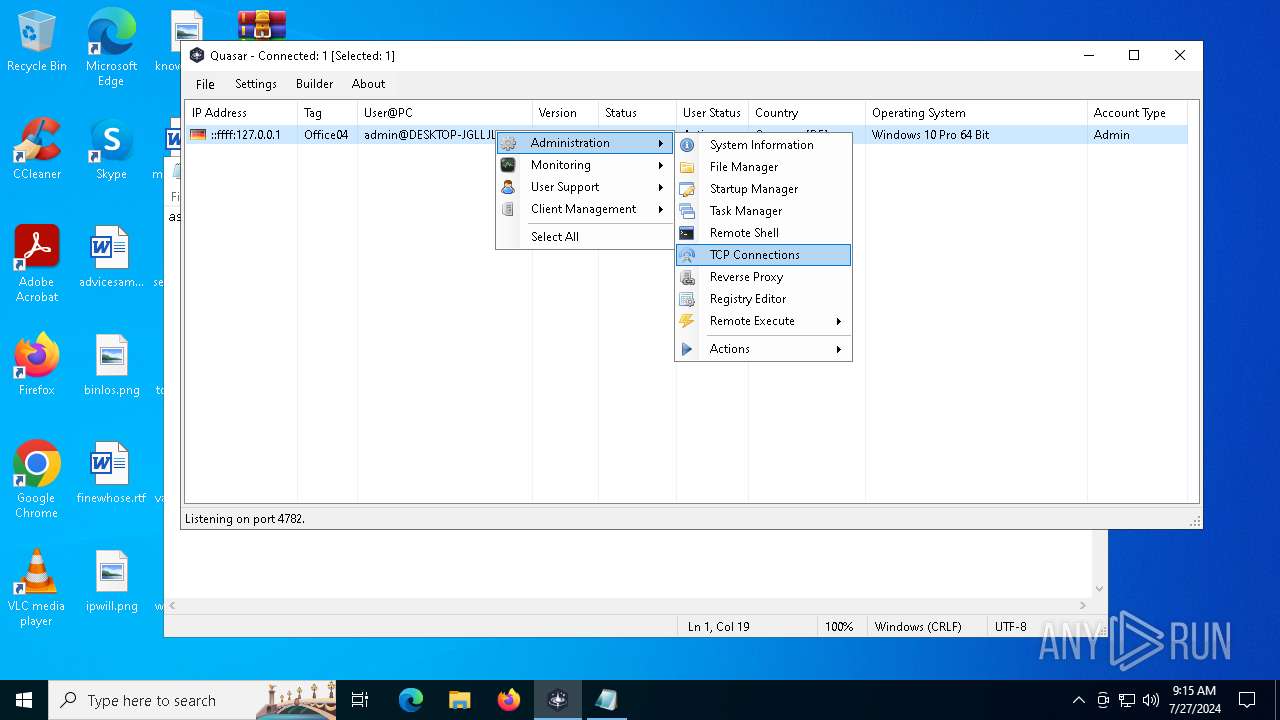
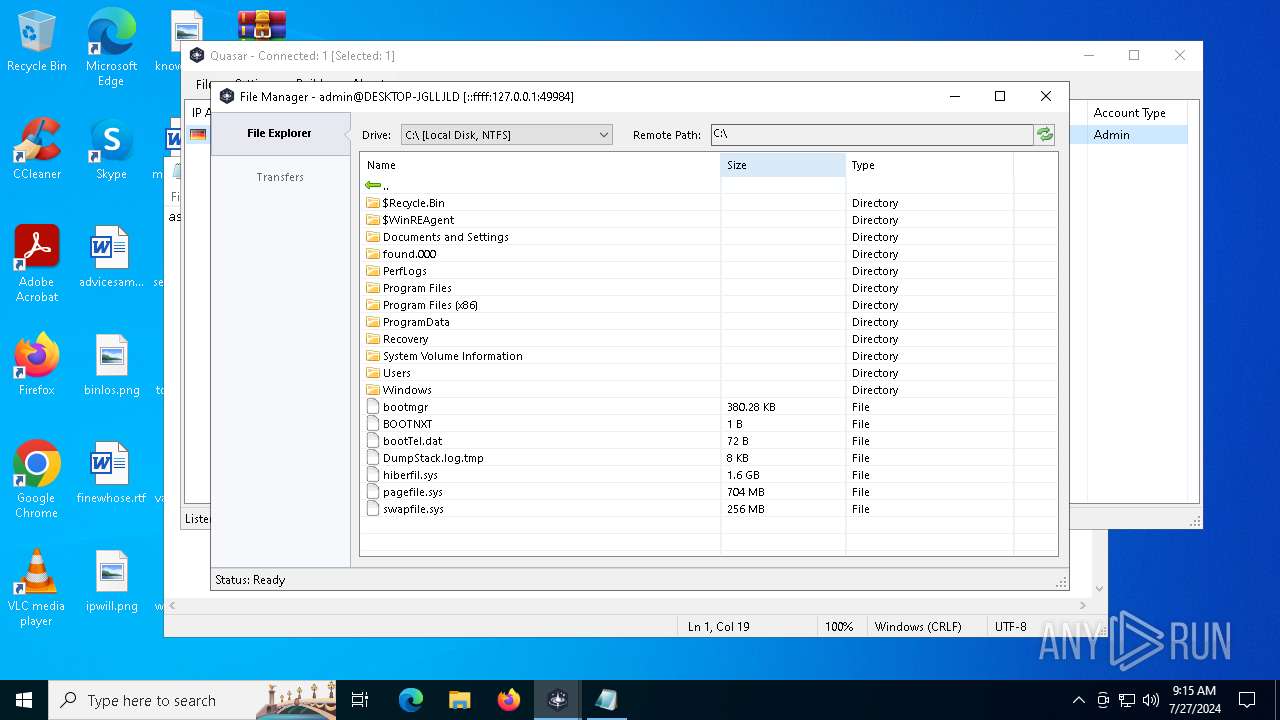
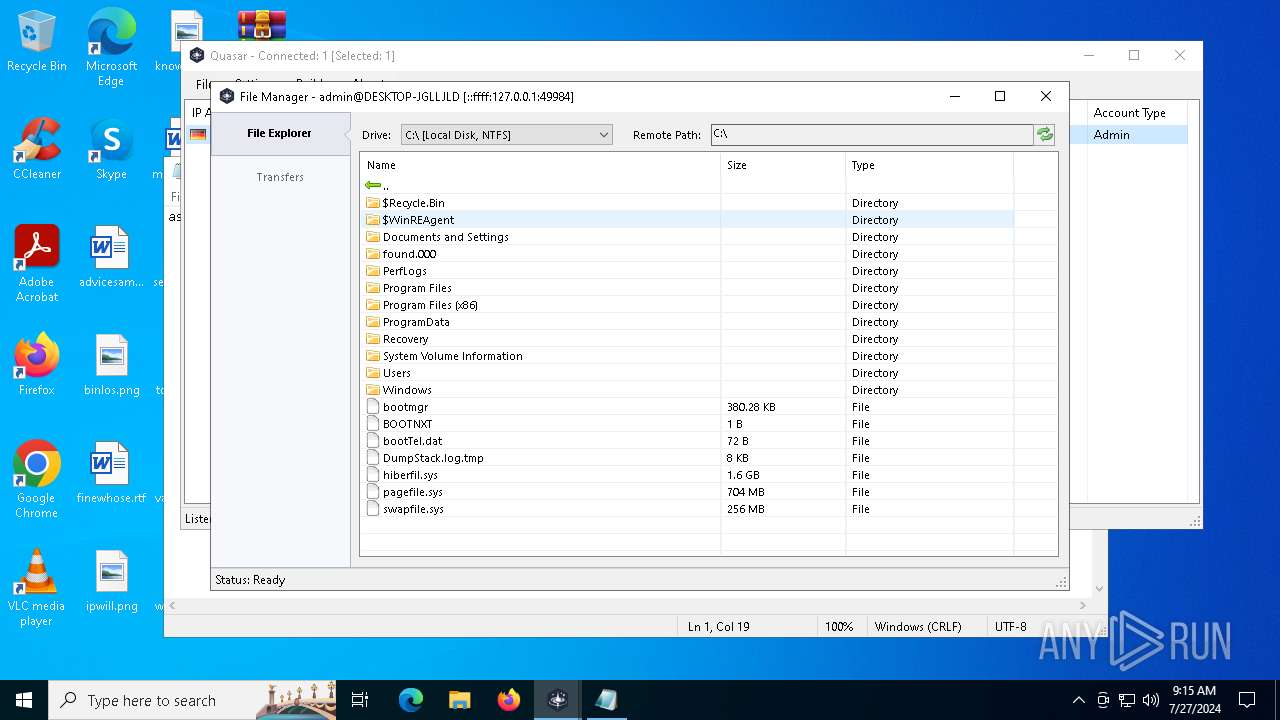
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | July 27, 2024, 09:09:25 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 13AA4BF4F5ED1AC503C69470B1EDE5C1 |
| SHA1: | C0B7DADFF8AC37F6D9FD00AE7F375E12812BFC00 |
| SHA256: | 4CDEB2EAE1CEC1AB07077142313C524E9CF360CDEC63497538C4405C2D8DED62 |
| SSDEEP: | 49152:lYLmNgMh/9yUsRFeWMyYISDSwtfxZQNemi57PdHmeFINp/lFnsDbNFNepL6DJo+J:mL9U1yUUQykOQ91XFYBlR8P9d5uNJo9 |
MALICIOUS
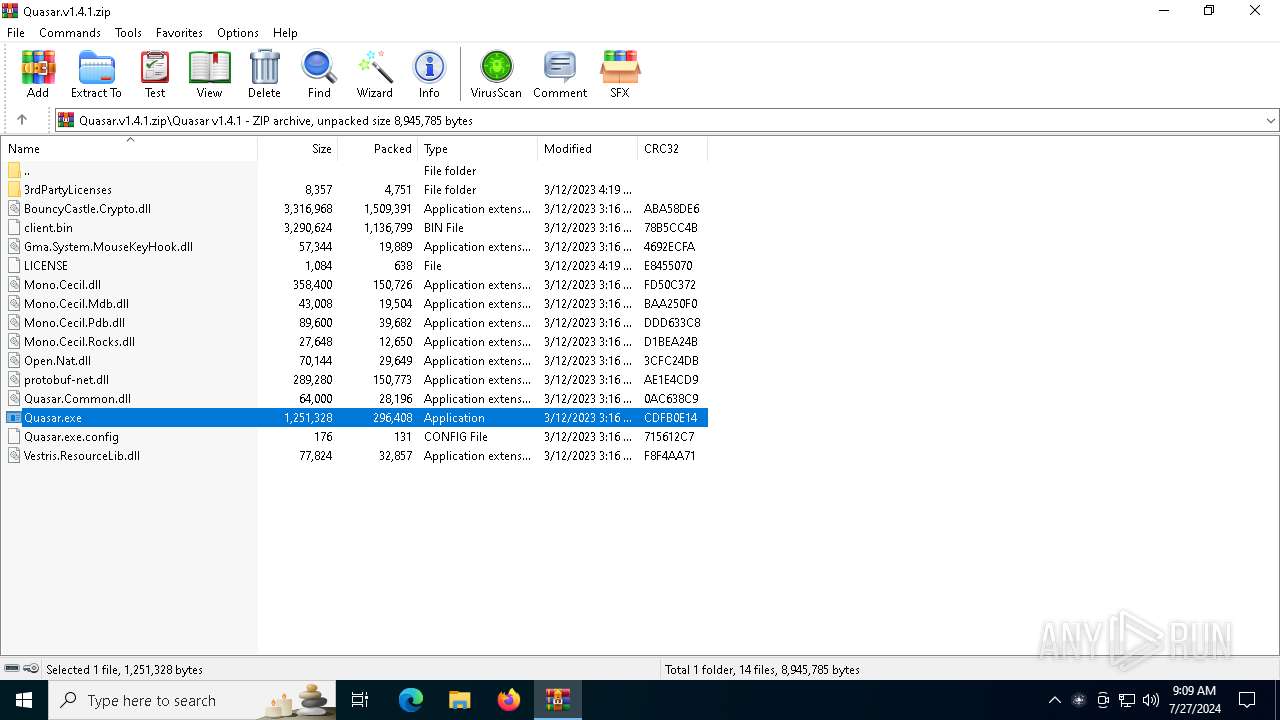
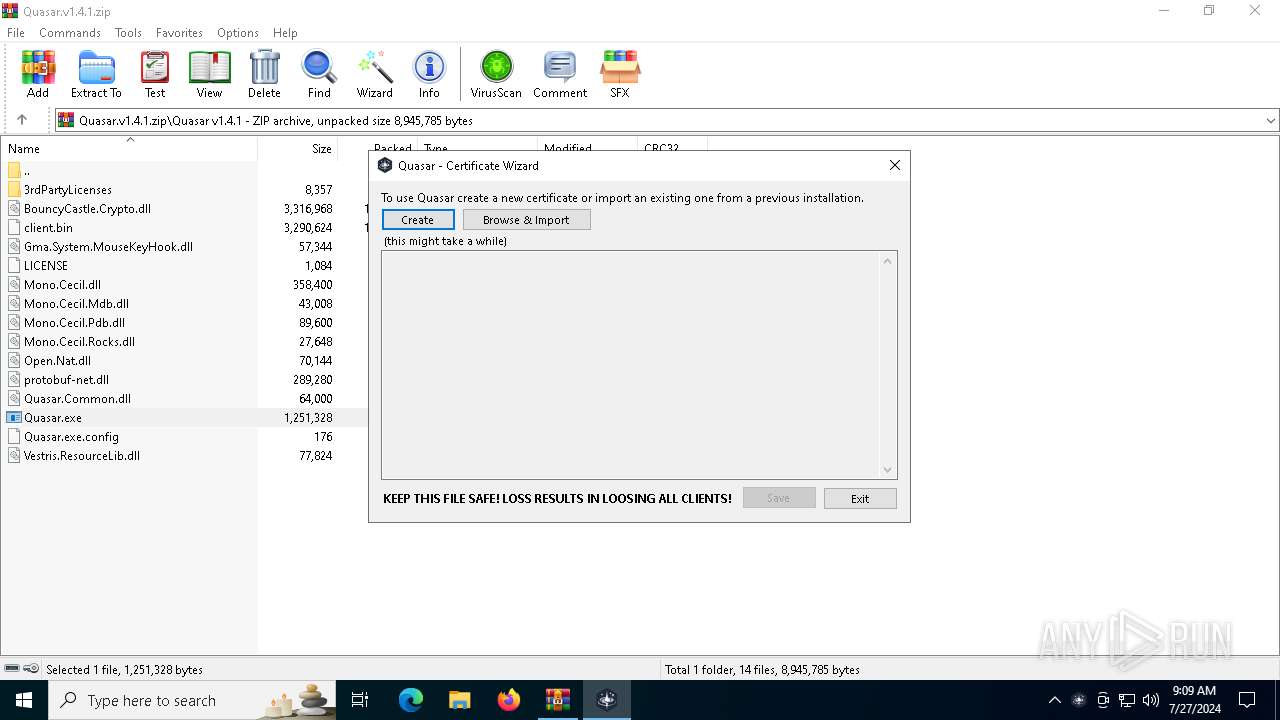
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2340)
- Quasar.exe (PID: 3572)
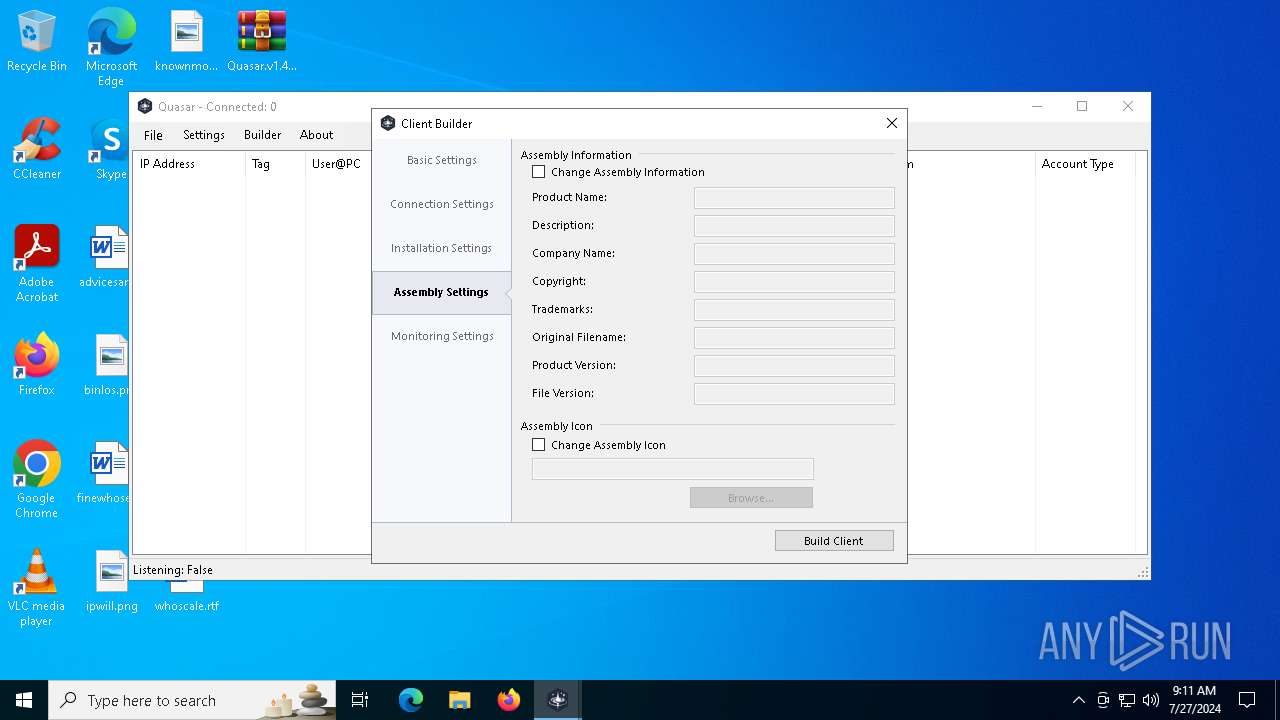
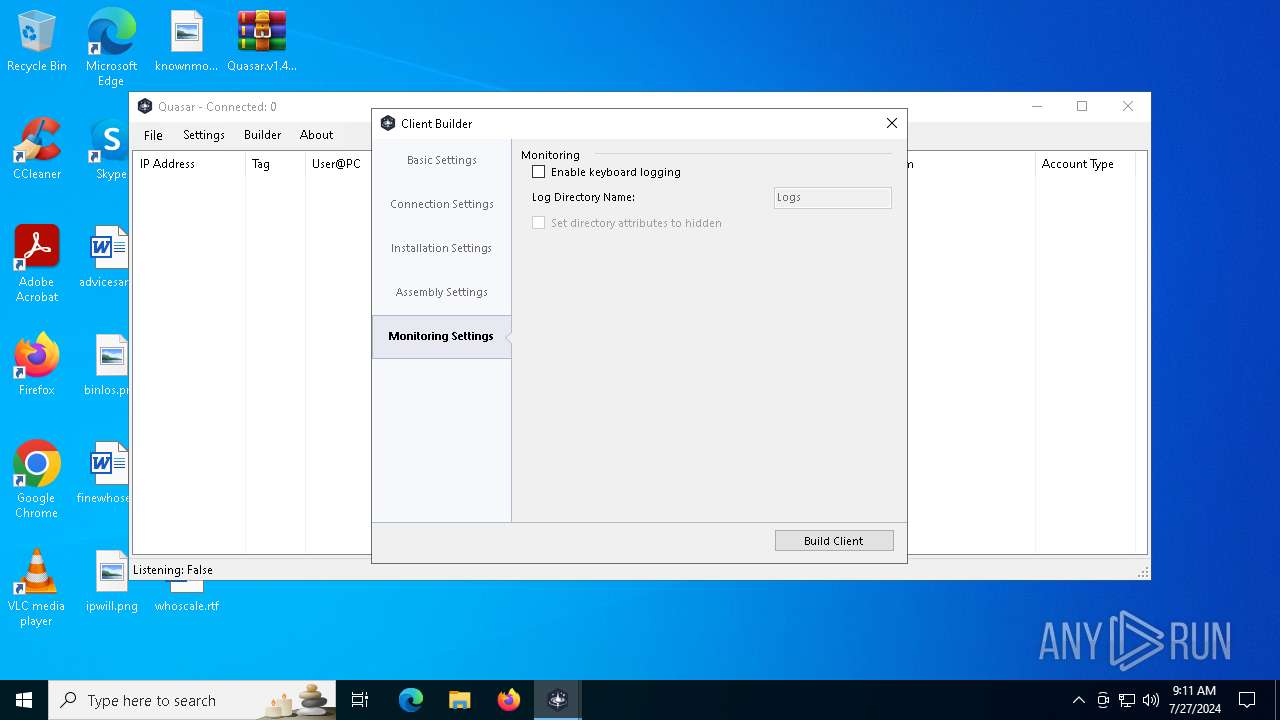
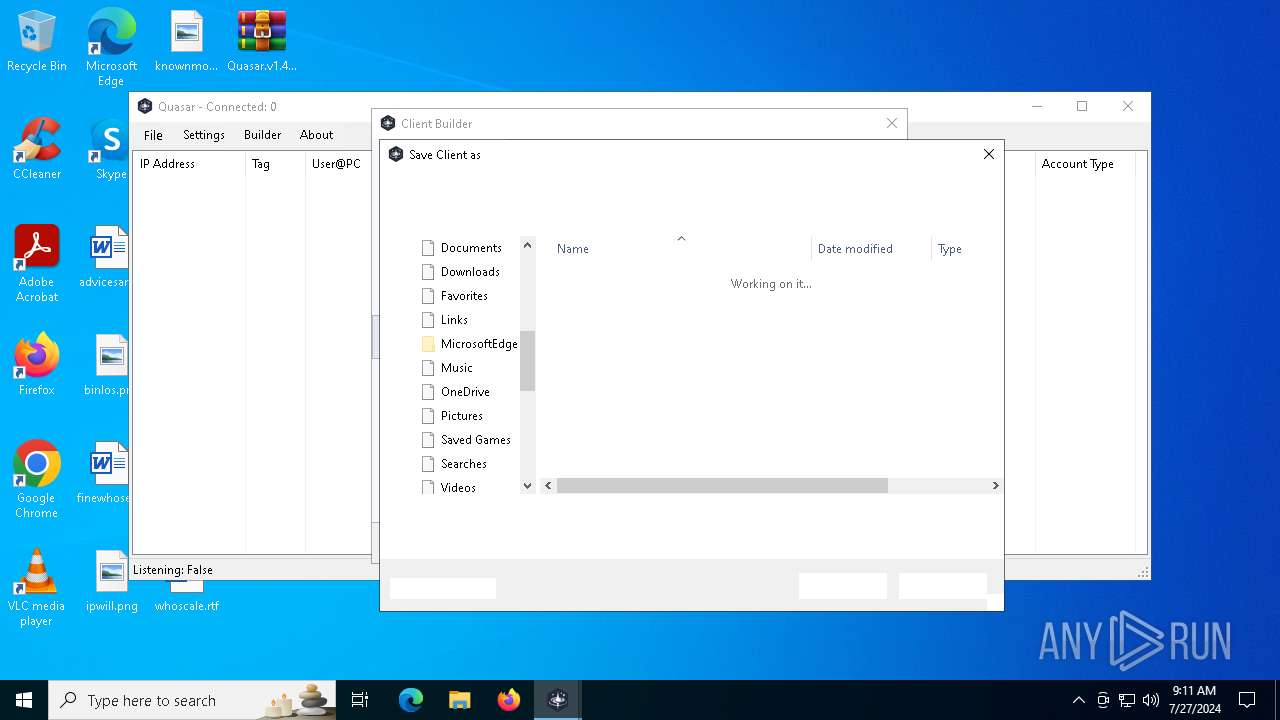
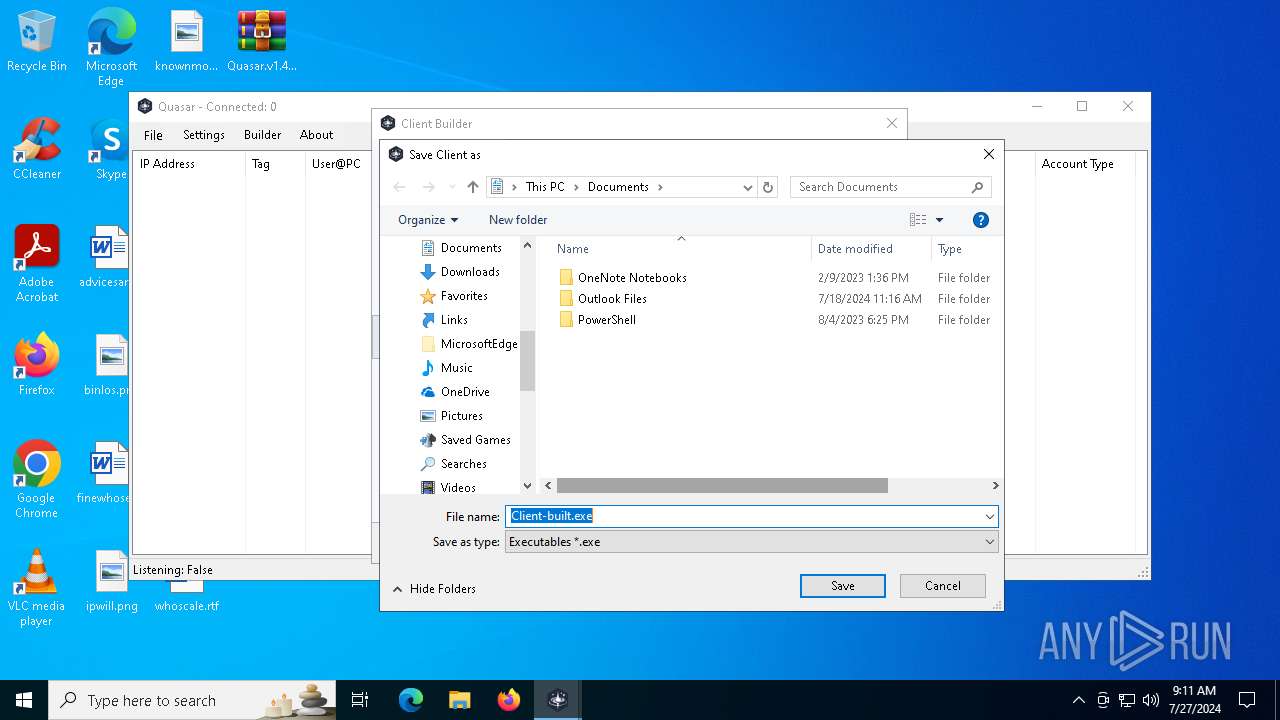
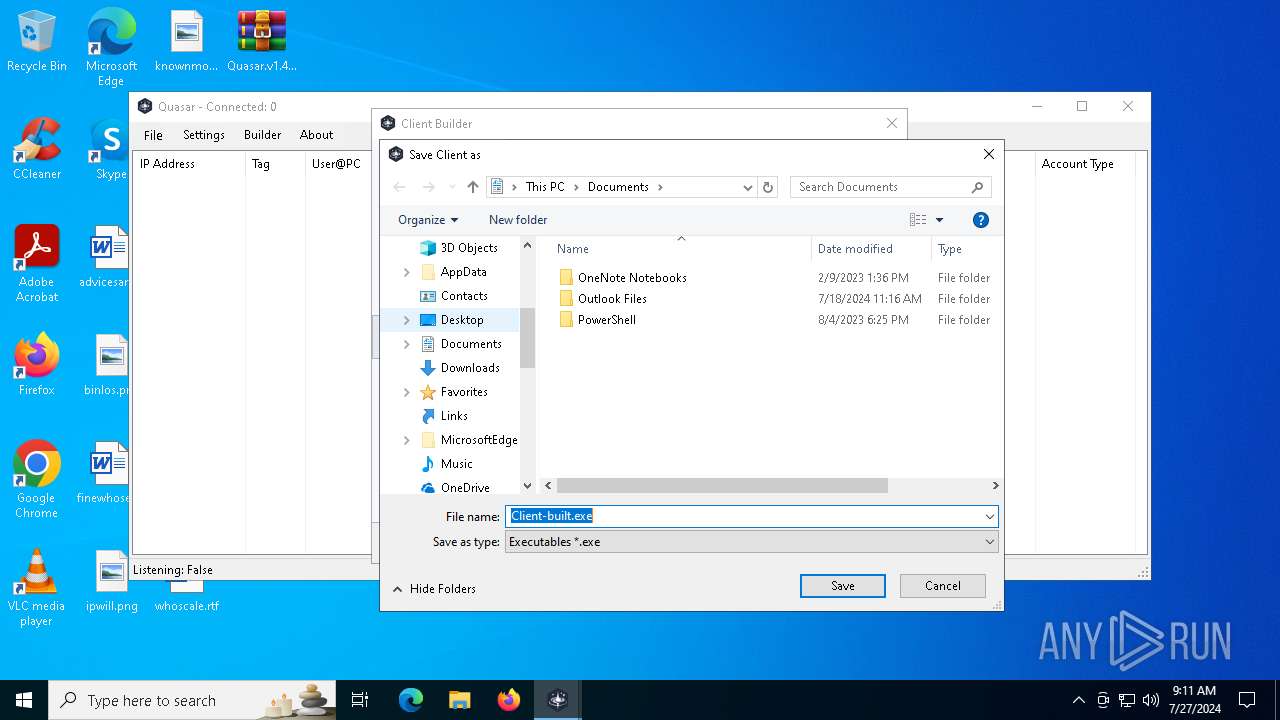
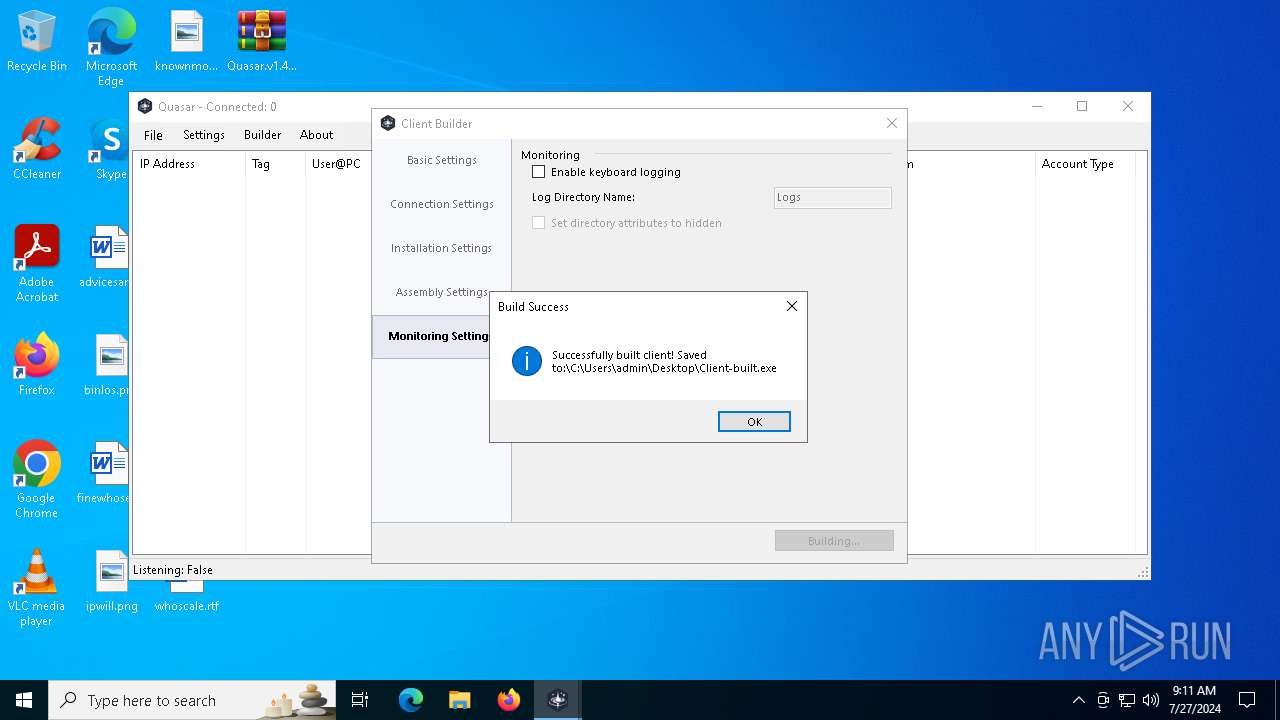
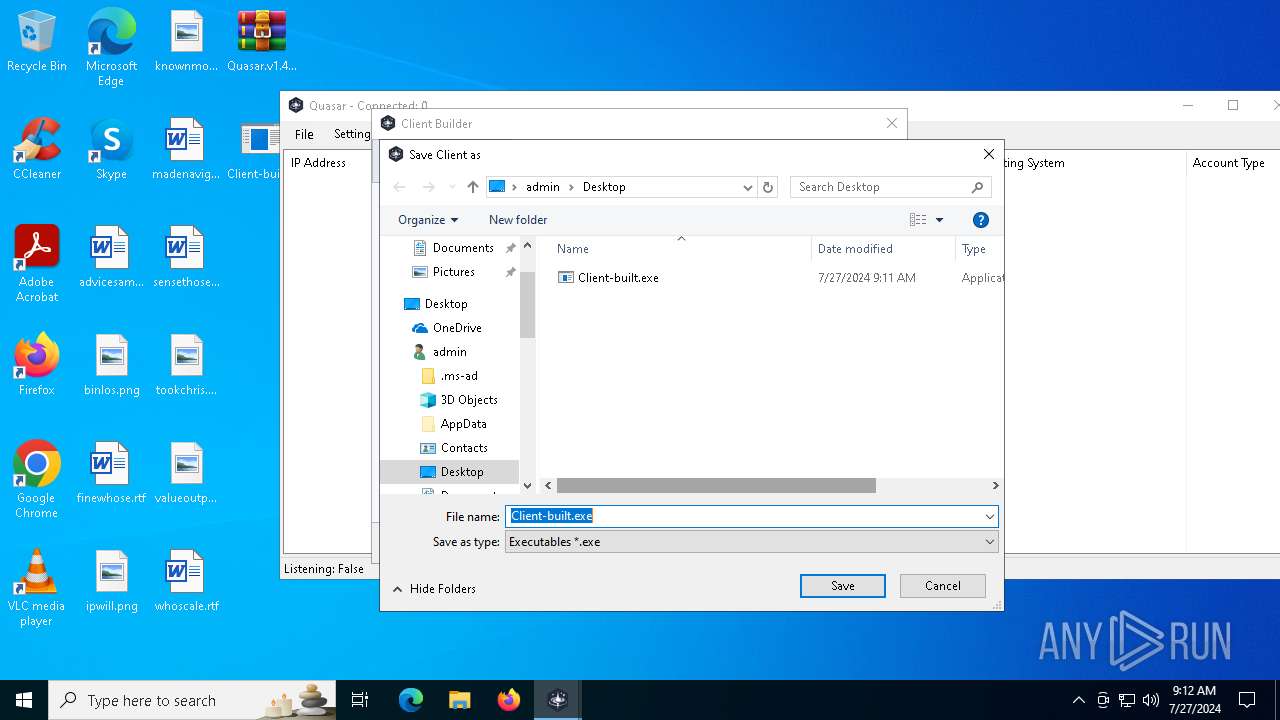
- Client-built.exe (PID: 3488)
QUASAR has been detected (YARA)
- fun.exe (PID: 6812)
- fun.exe (PID: 6728)
- fun.exe (PID: 3968)
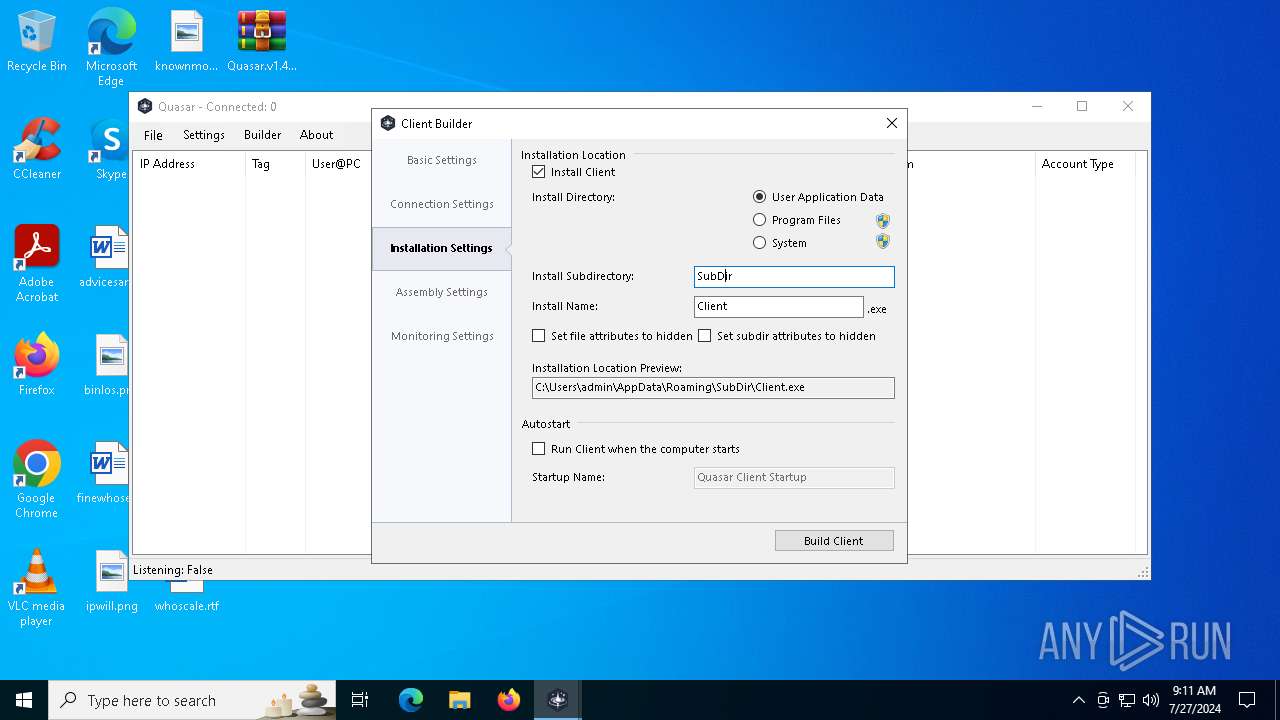
Uses Task Scheduler to autorun other applications
- fun.exe (PID: 3968)
SUSPICIOUS
Reads security settings of Internet Explorer
- Quasar.exe (PID: 3572)
- WinRAR.exe (PID: 2340)
Executable content was dropped or overwritten
- Quasar.exe (PID: 3572)
- Client-built.exe (PID: 3488)
Reads the date of Windows installation
- Quasar.exe (PID: 3572)
Creates file in the systems drive root
- explorer.exe (PID: 4356)
Starts itself from another location
- Client-built.exe (PID: 3488)
The executable file from the user directory is run by the CMD process
- fun.exe (PID: 3968)
Starts CMD.EXE for commands execution
- fun.exe (PID: 6812)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4356)
Reads Environment values
- Quasar.exe (PID: 3572)
Checks supported languages
- Quasar.exe (PID: 3572)
Reads the machine GUID from the registry
- Quasar.exe (PID: 3572)
Process checks computer location settings
- Quasar.exe (PID: 3572)
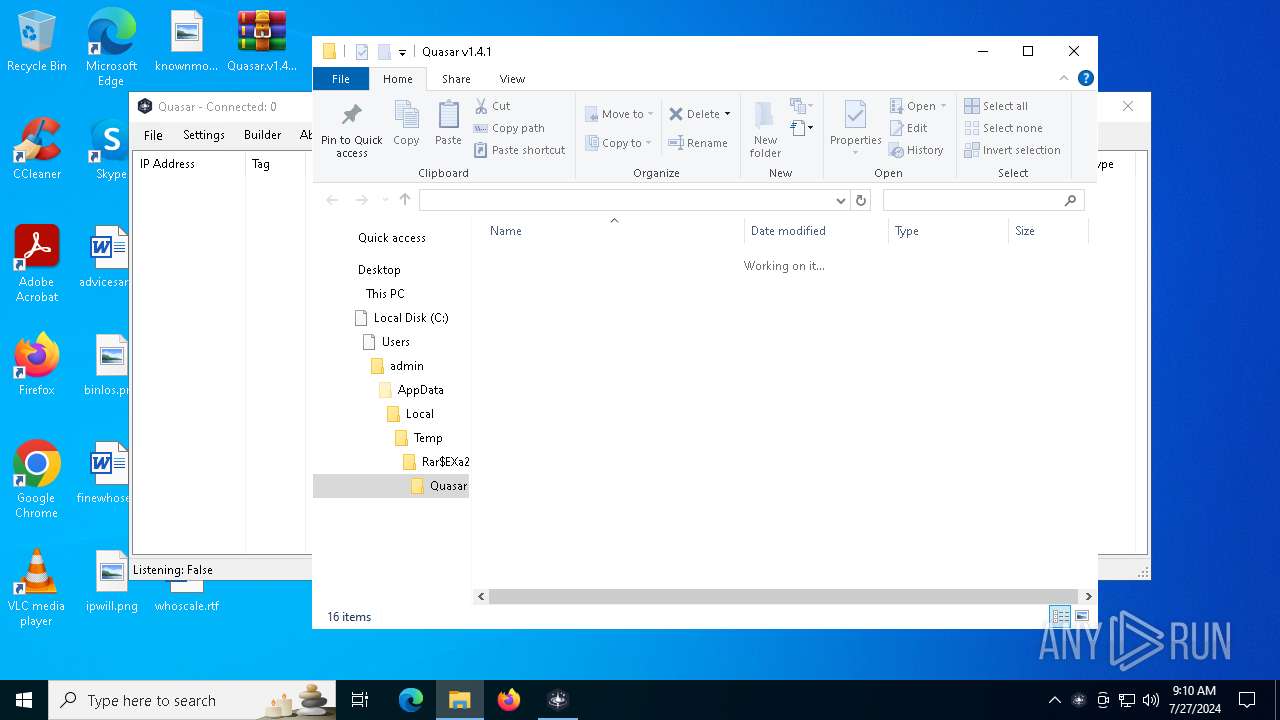
Create files in a temporary directory
- Quasar.exe (PID: 3572)
Reads the computer name
- Quasar.exe (PID: 3572)
Creates files or folders in the user directory
- Quasar.exe (PID: 3572)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2340)
Reads the software policy settings
- slui.exe (PID: 6860)
Checks proxy server information
- slui.exe (PID: 6860)
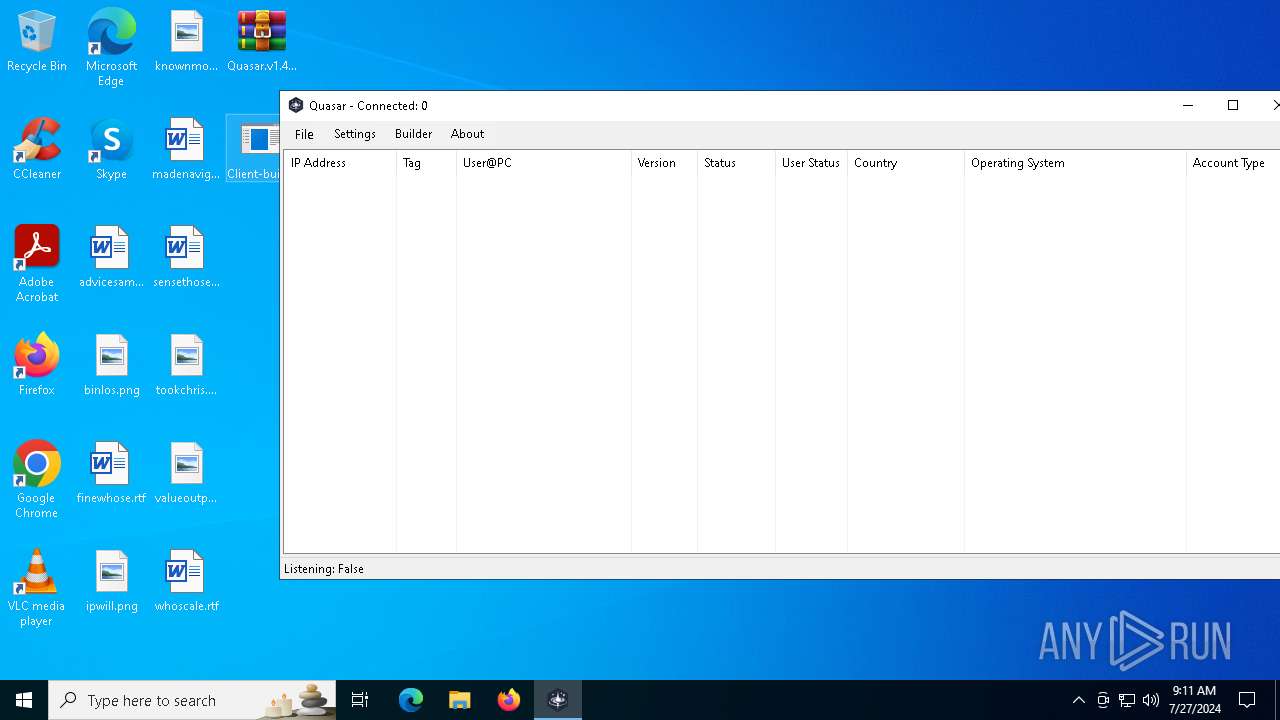
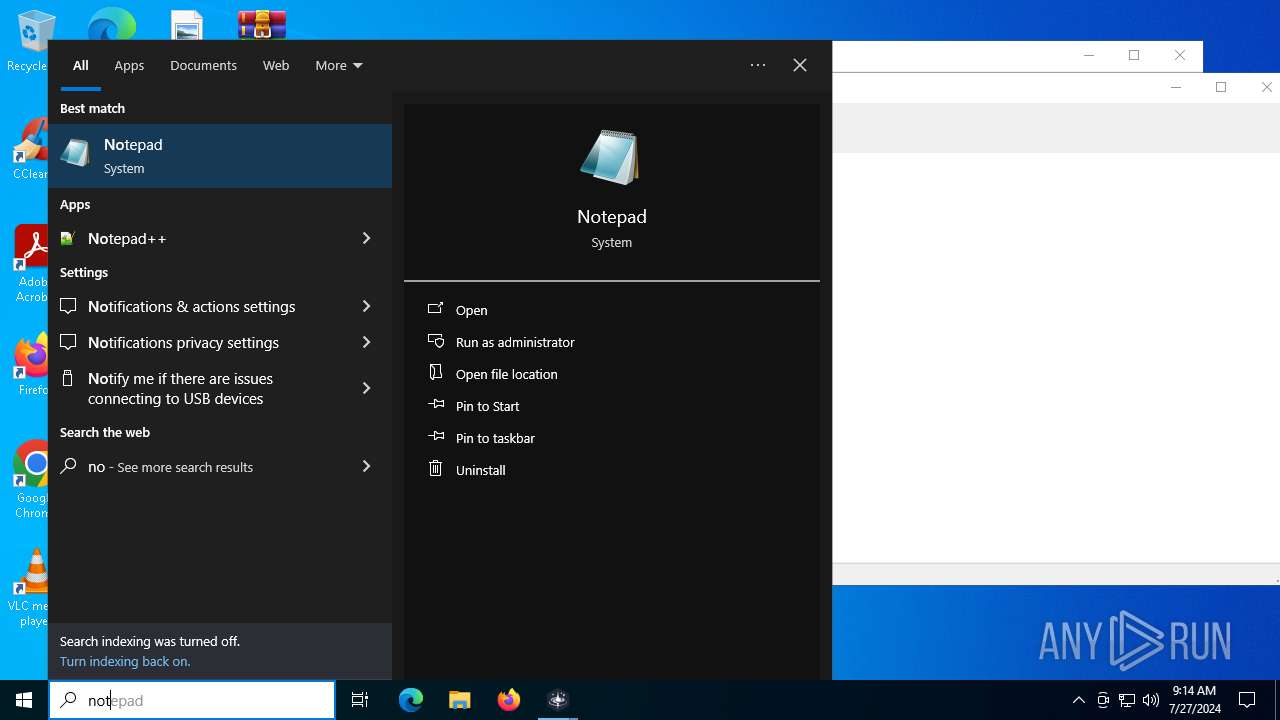
Manual execution by a user
- Client-built.exe (PID: 3488)
- fun.exe (PID: 6728)
- notepad.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
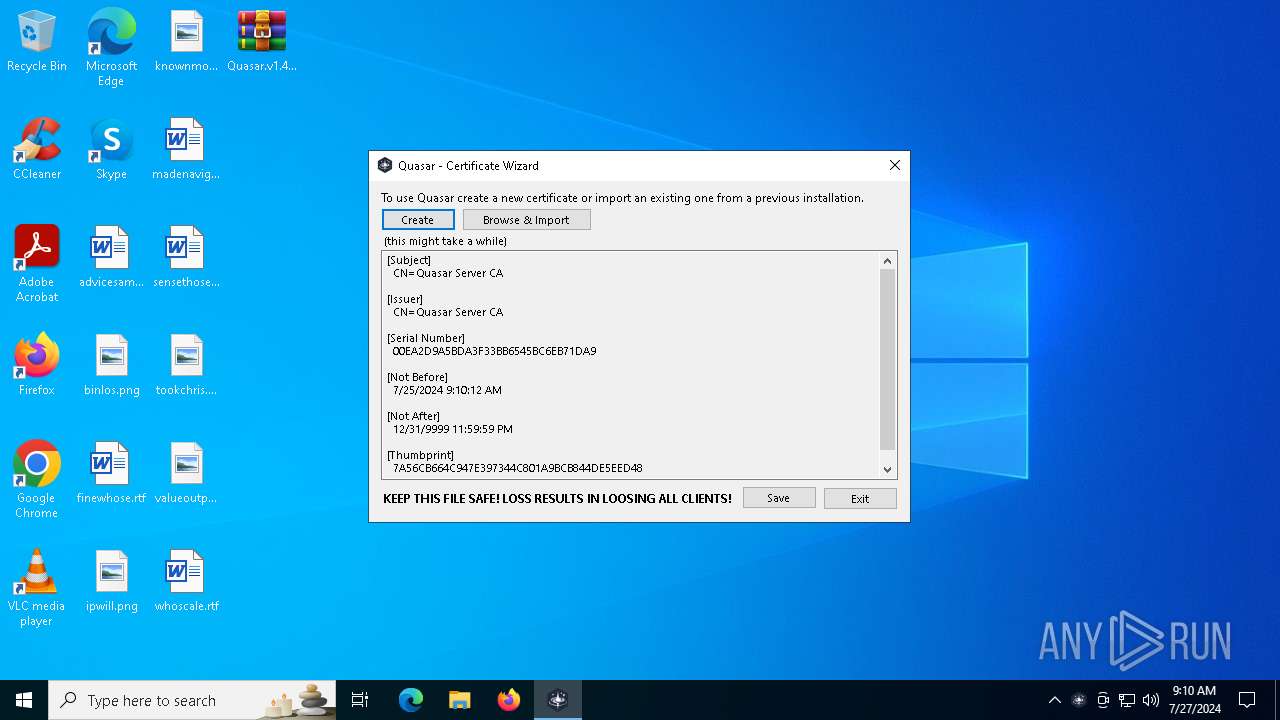
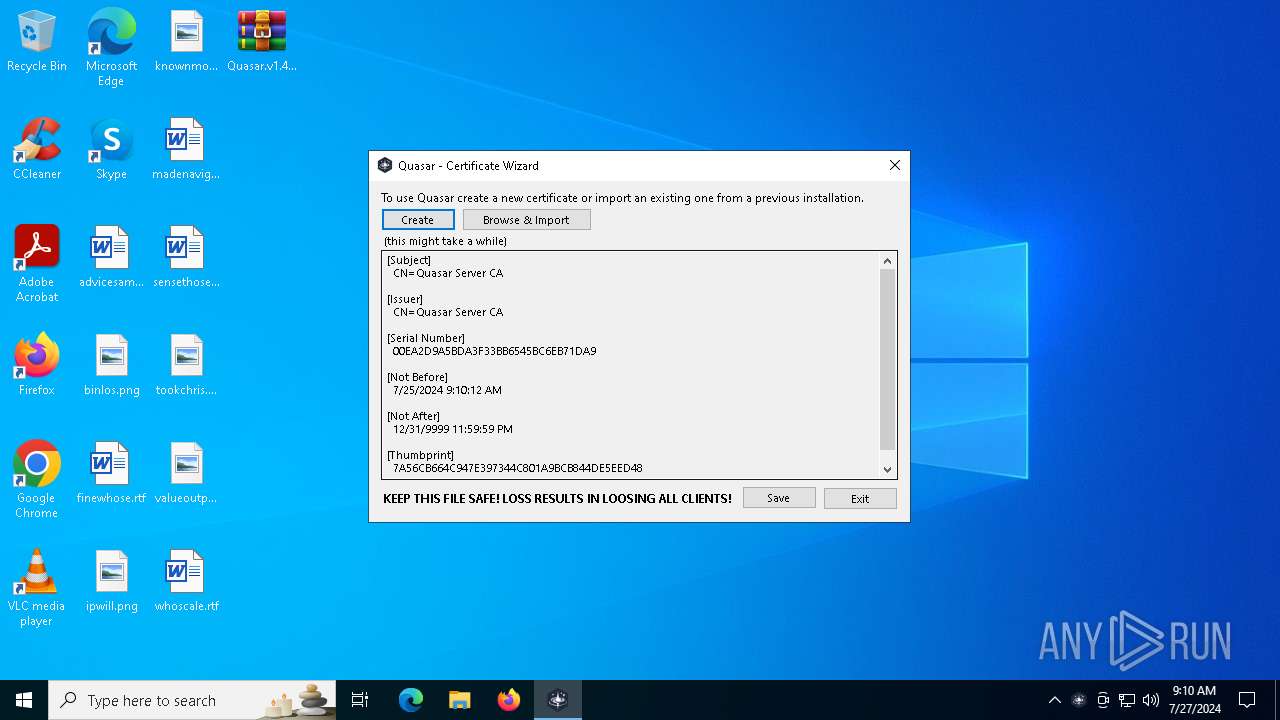
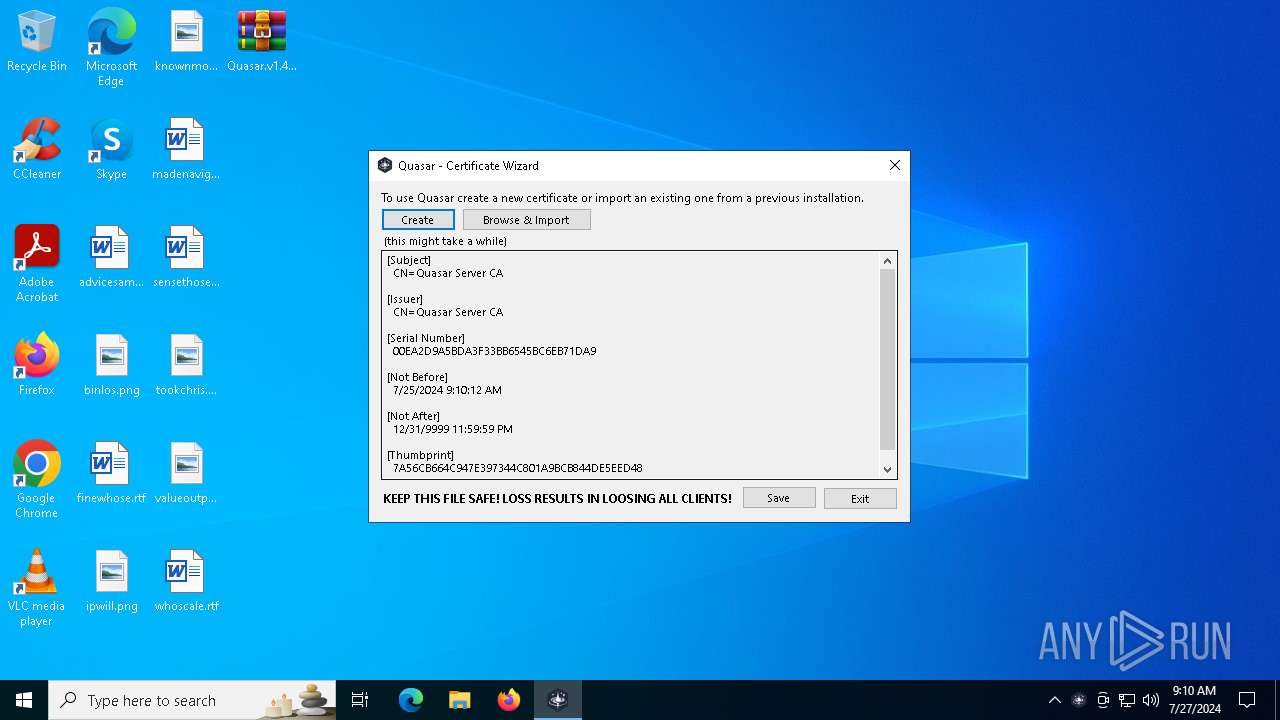
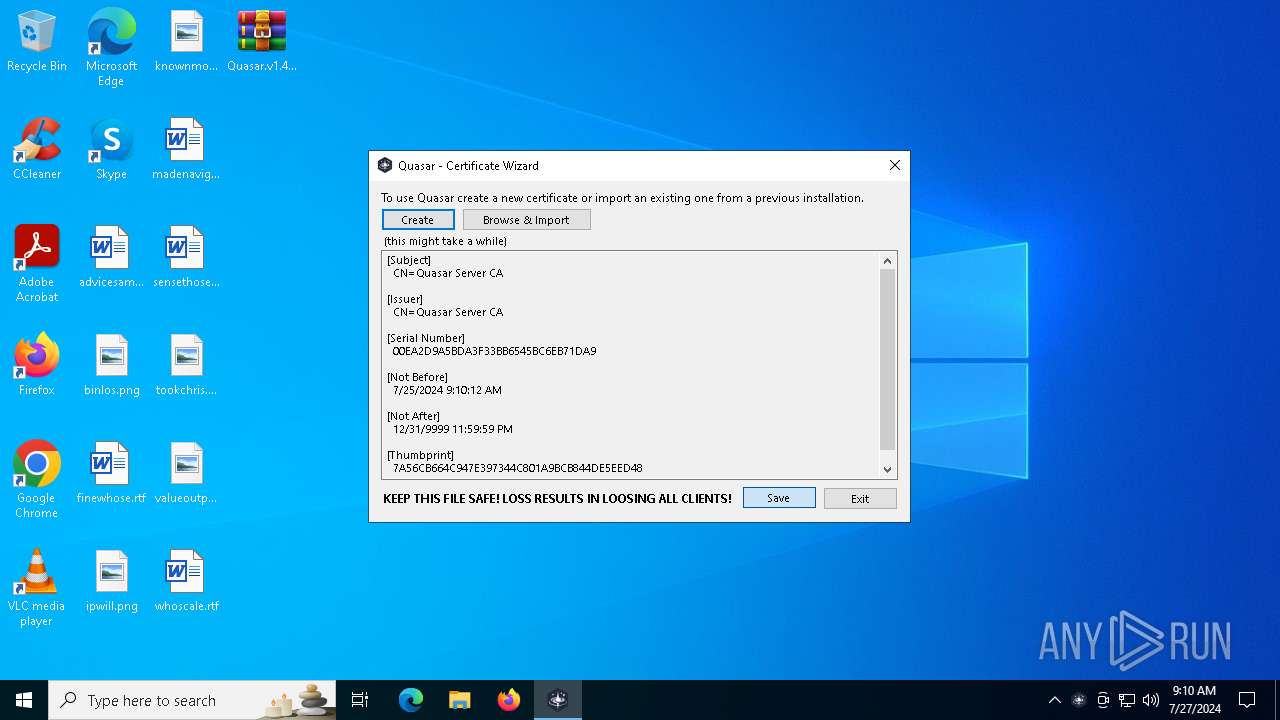
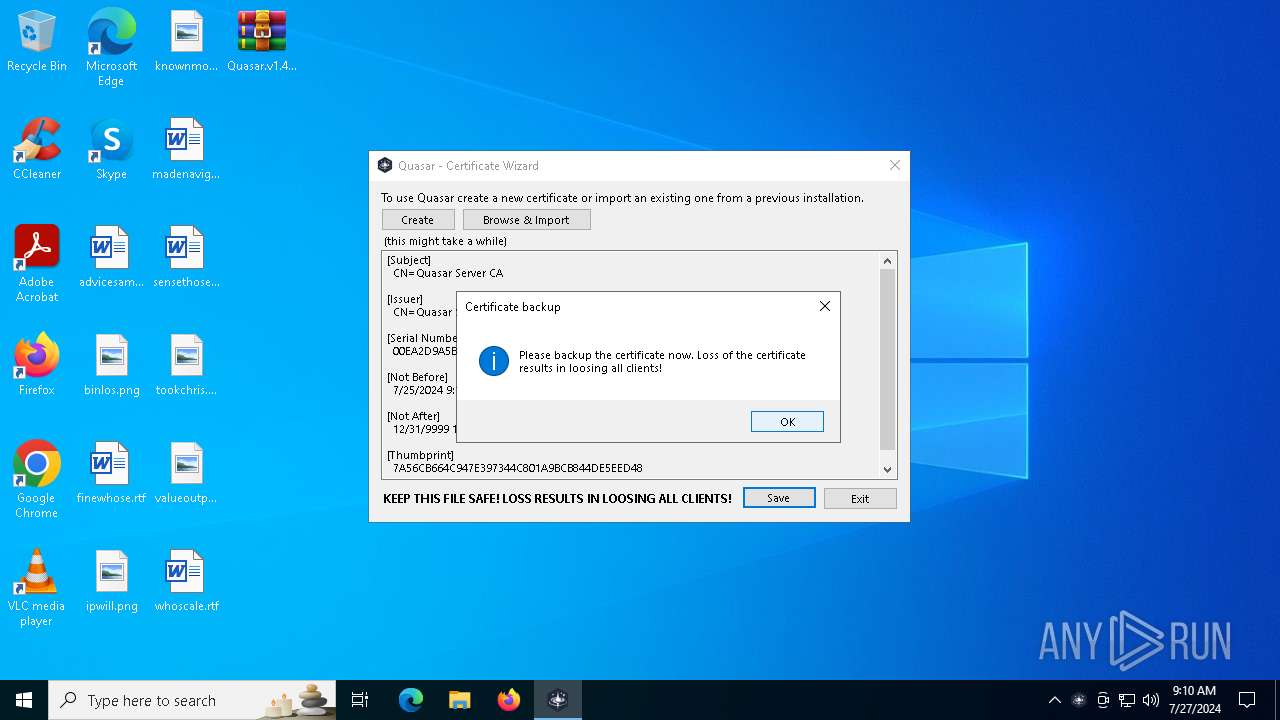
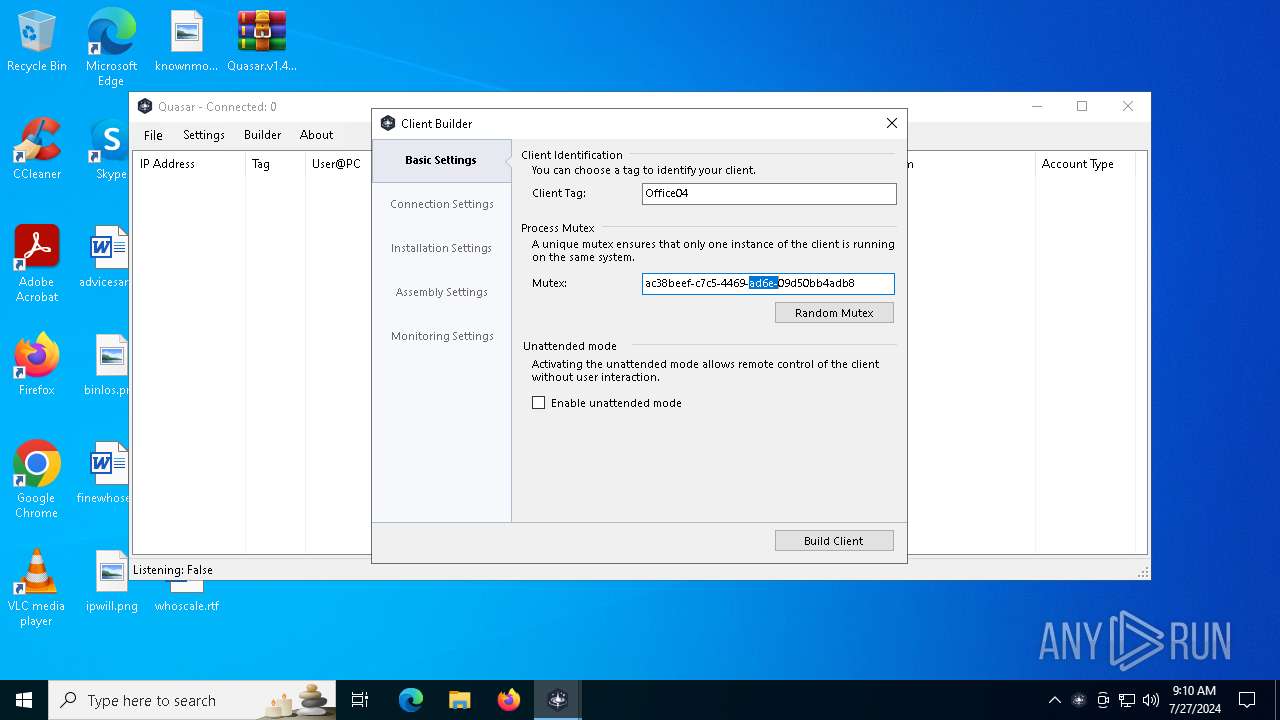
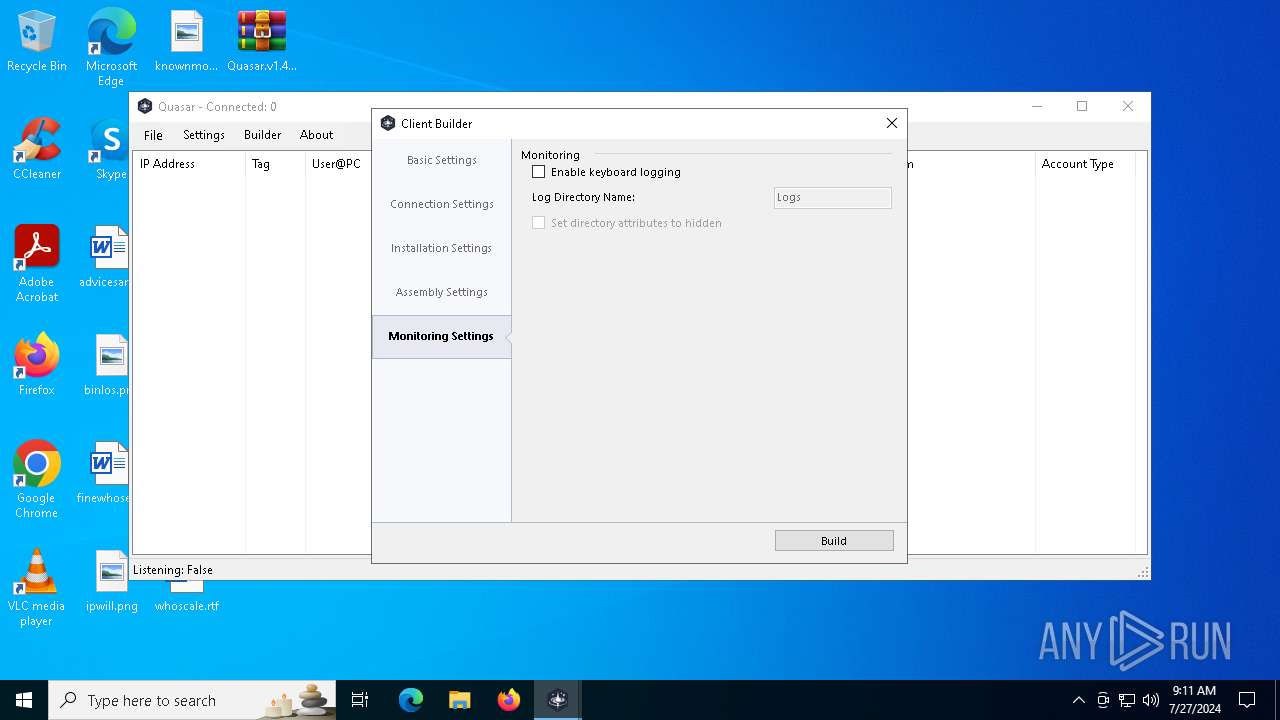
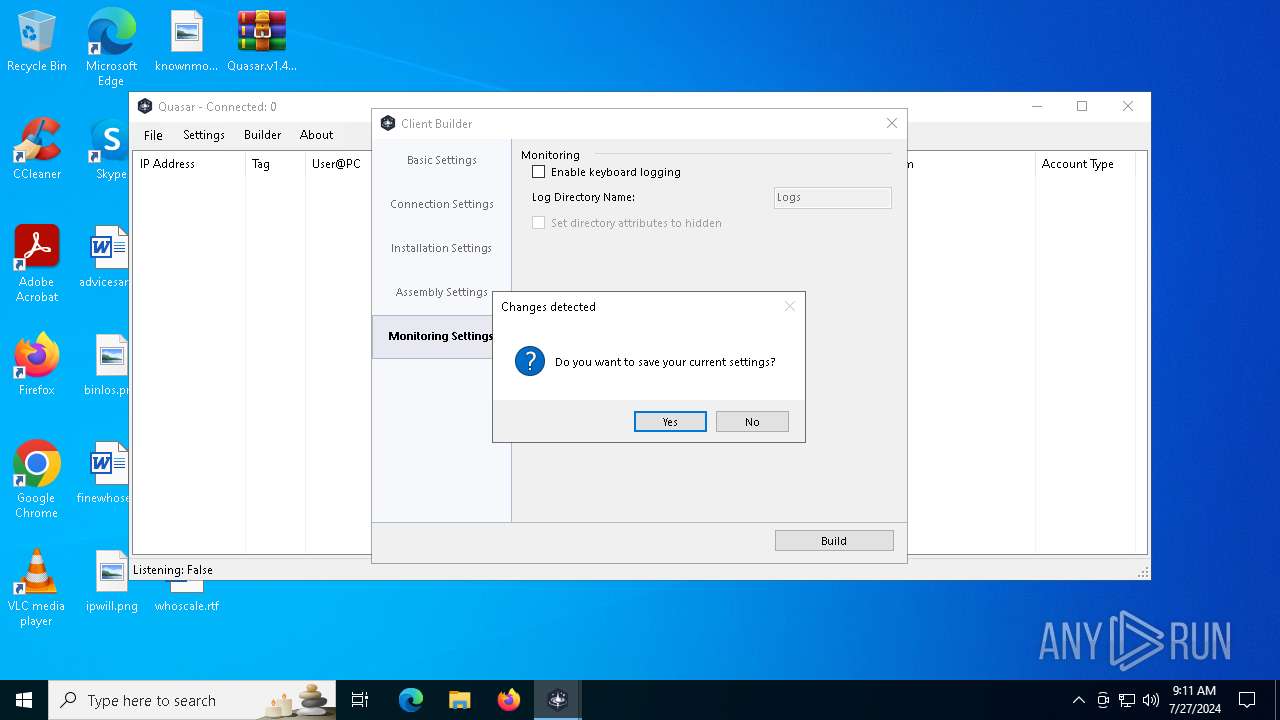
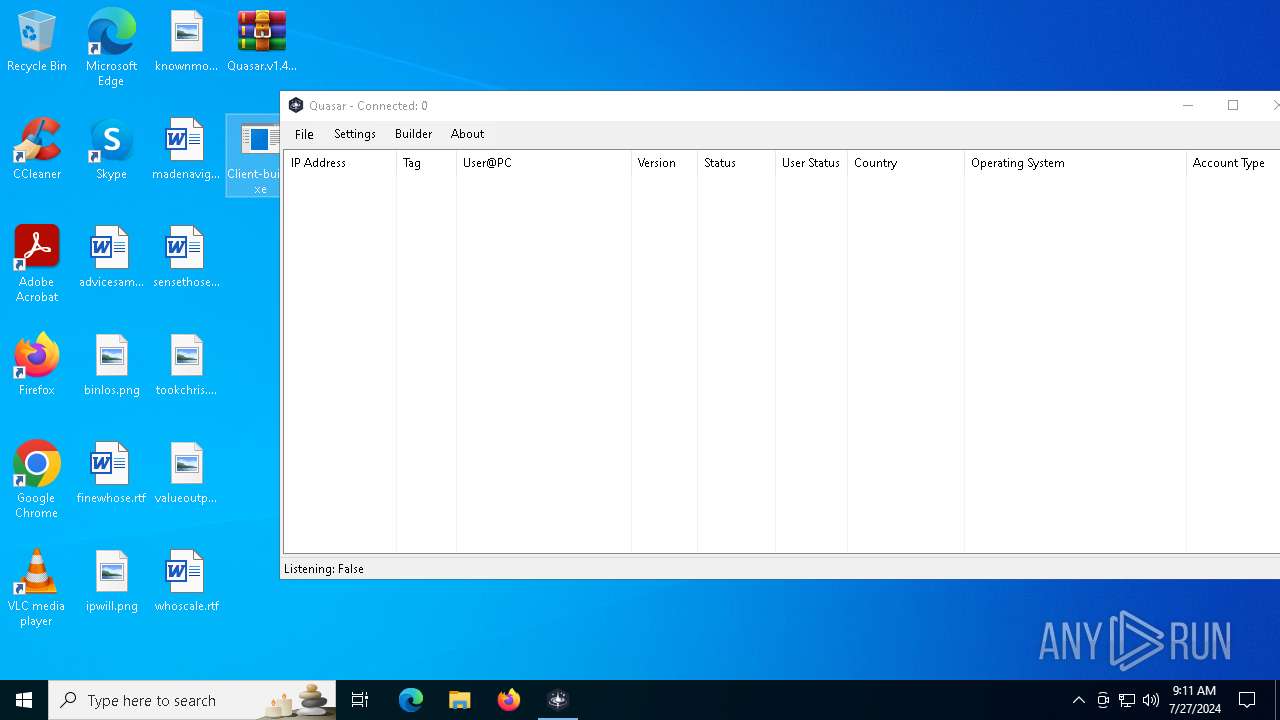
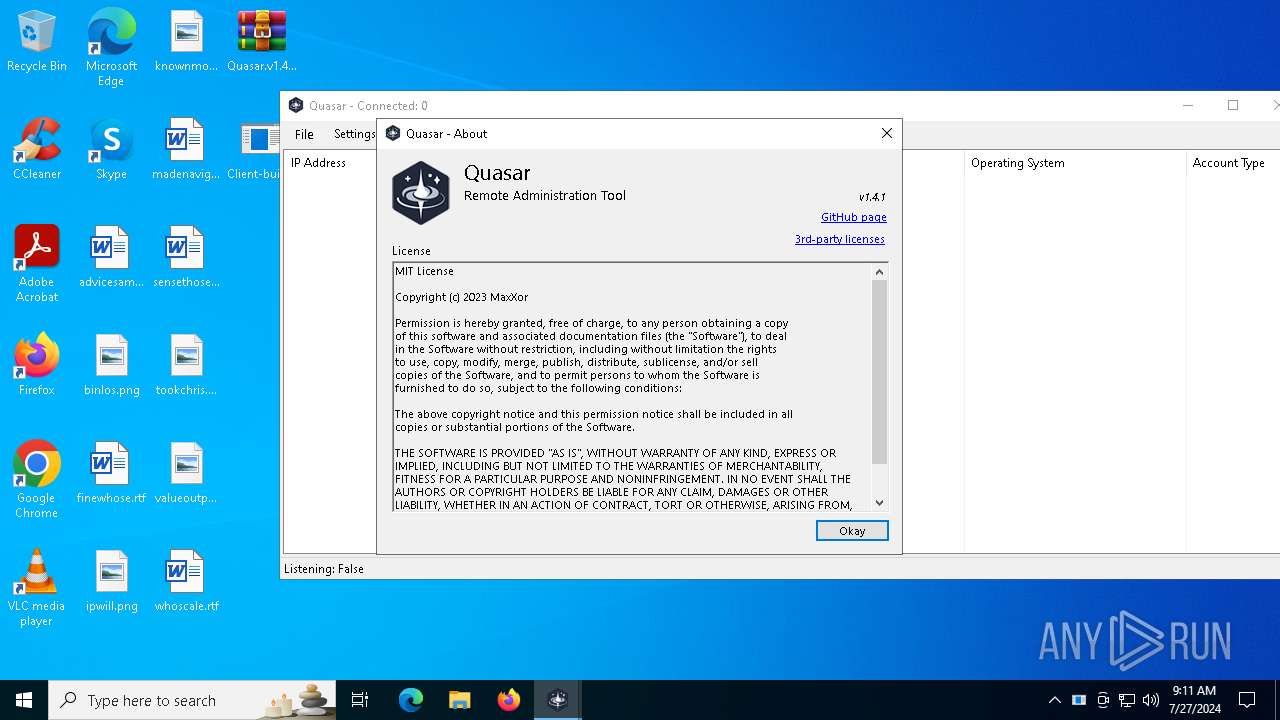
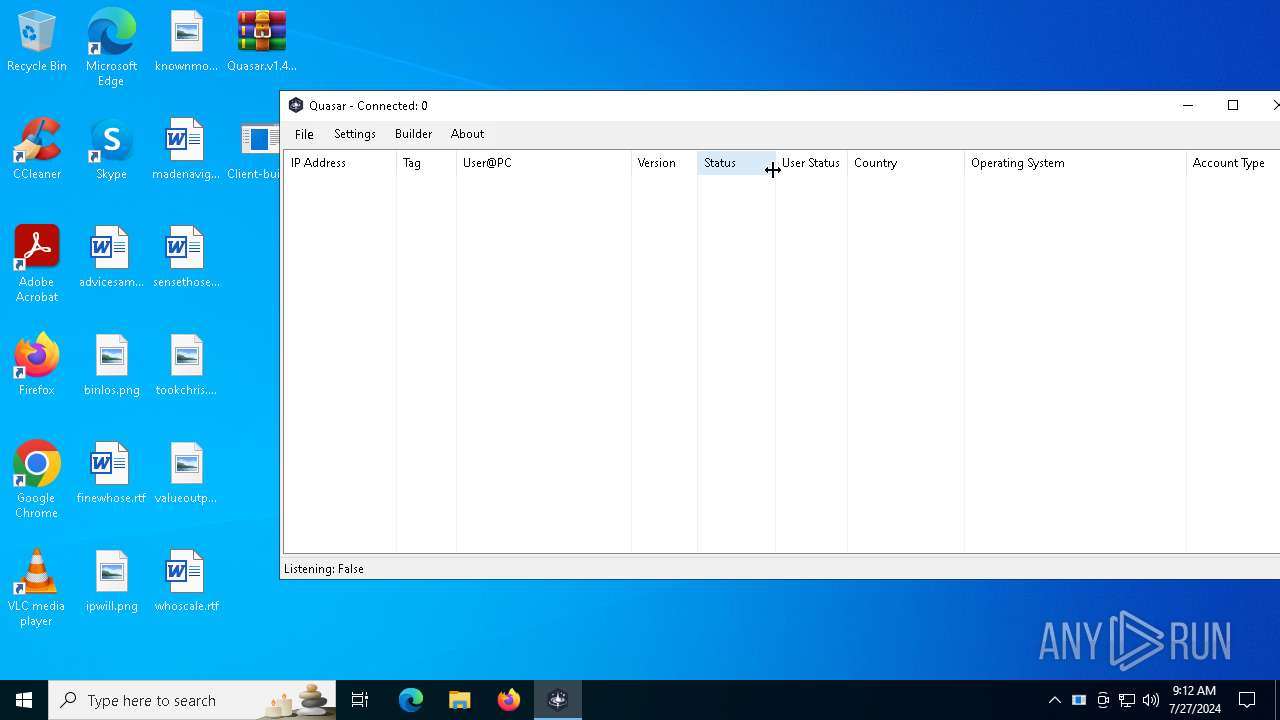
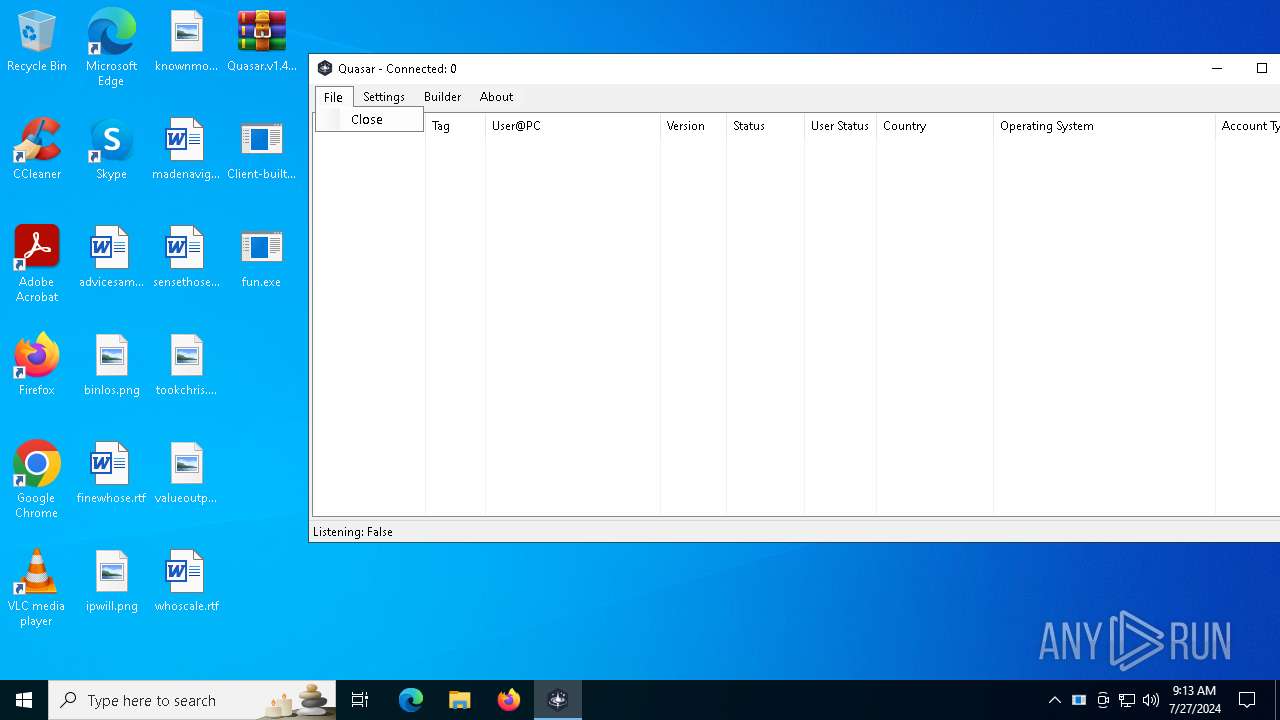
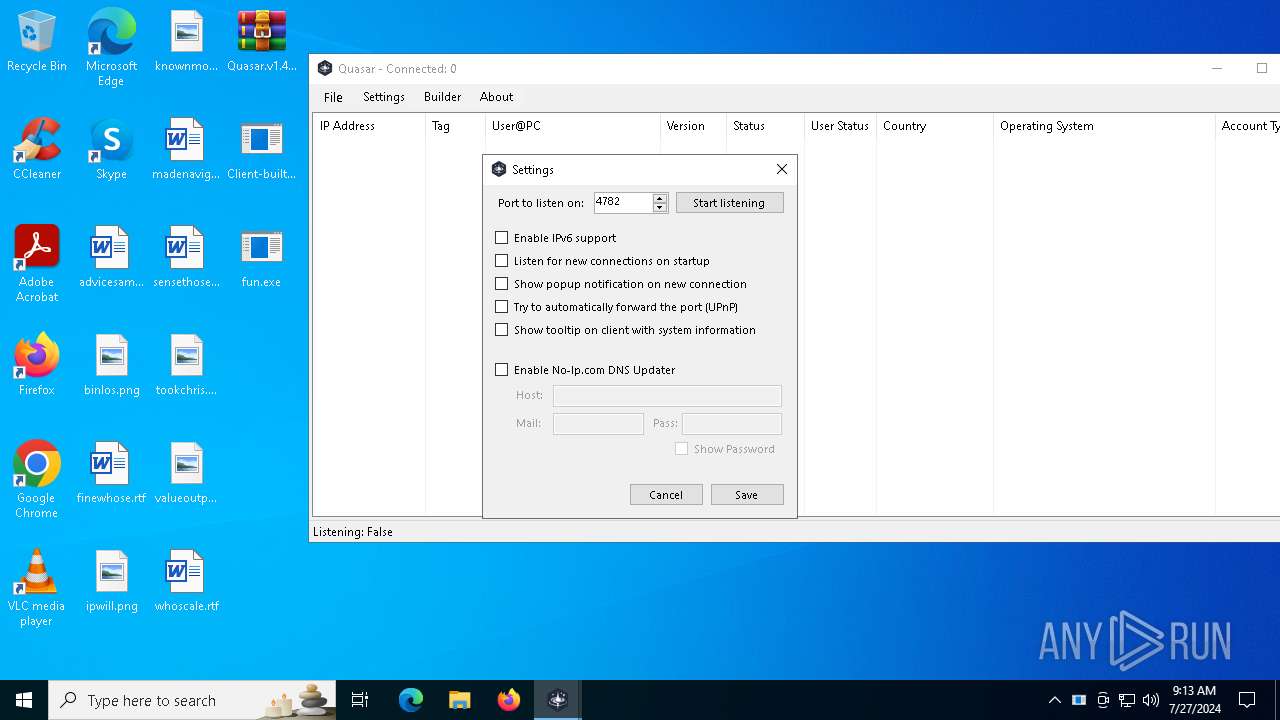
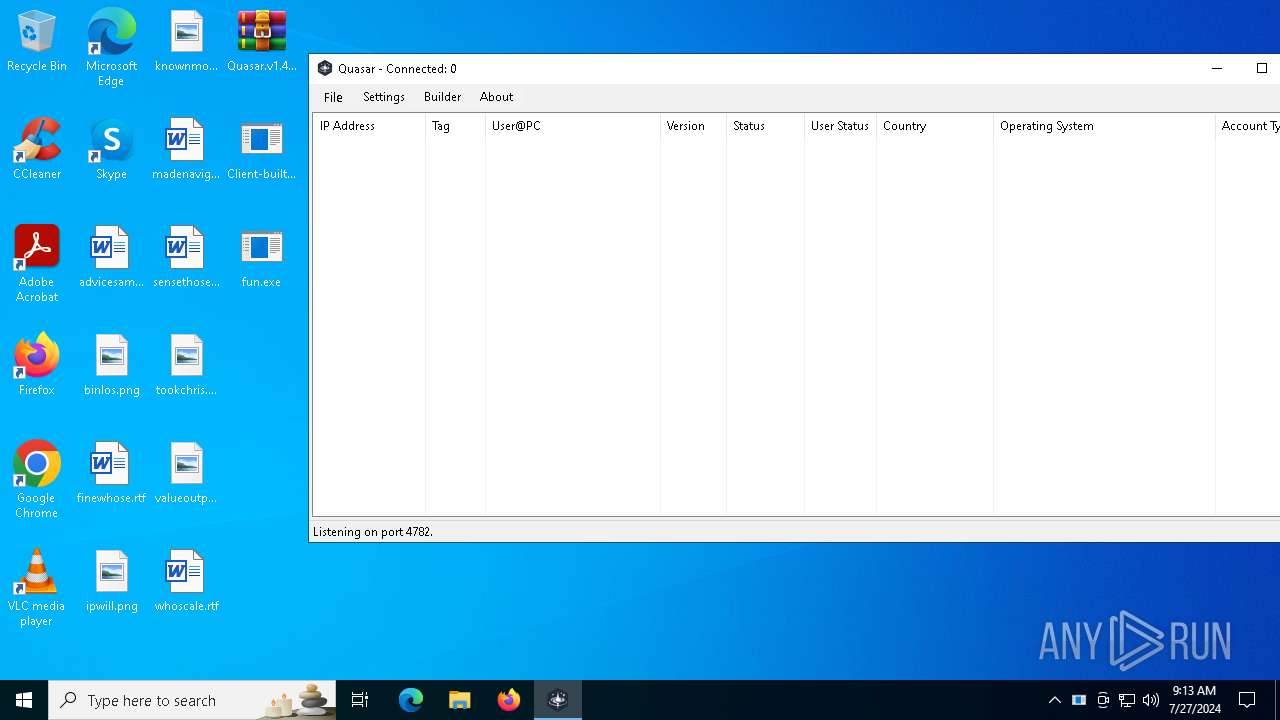
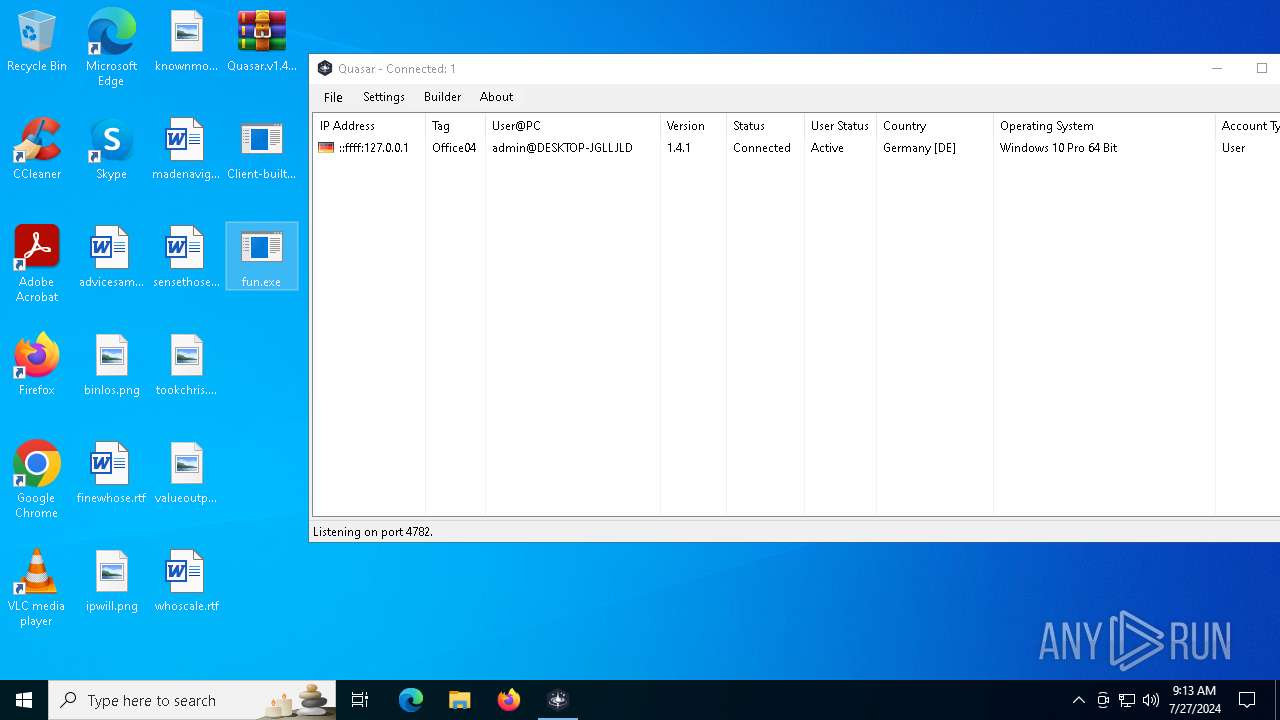
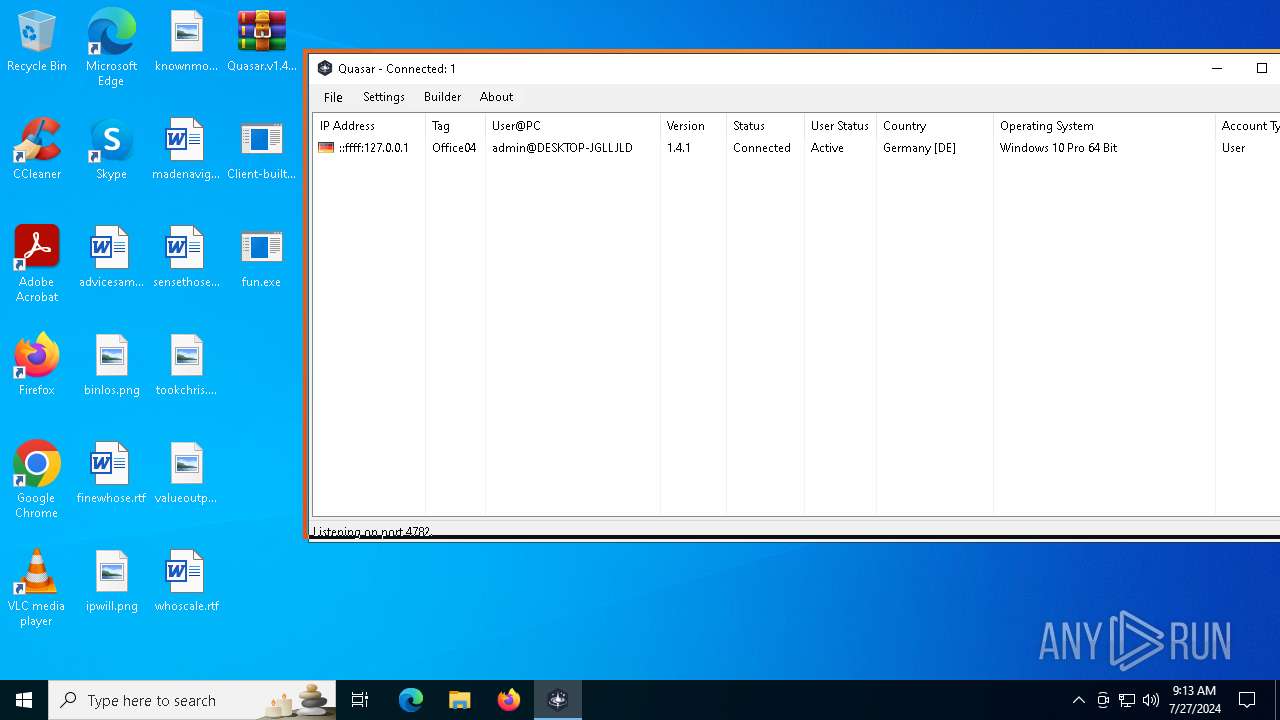
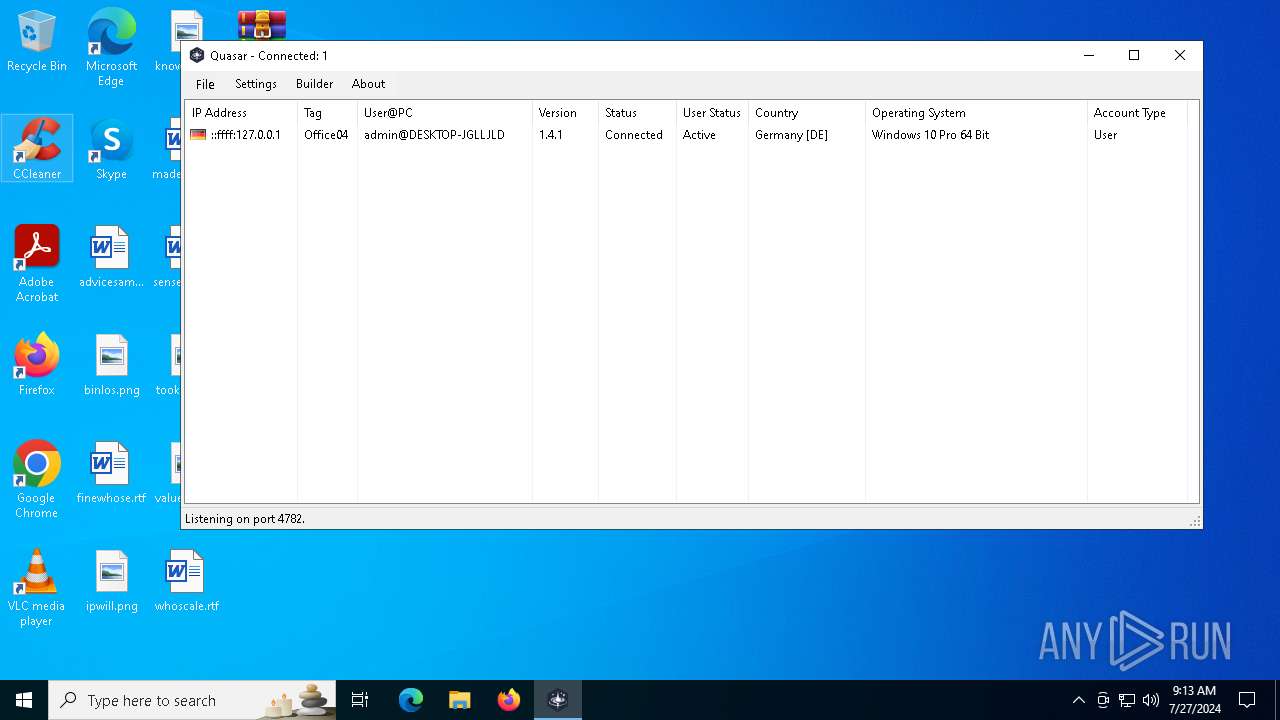
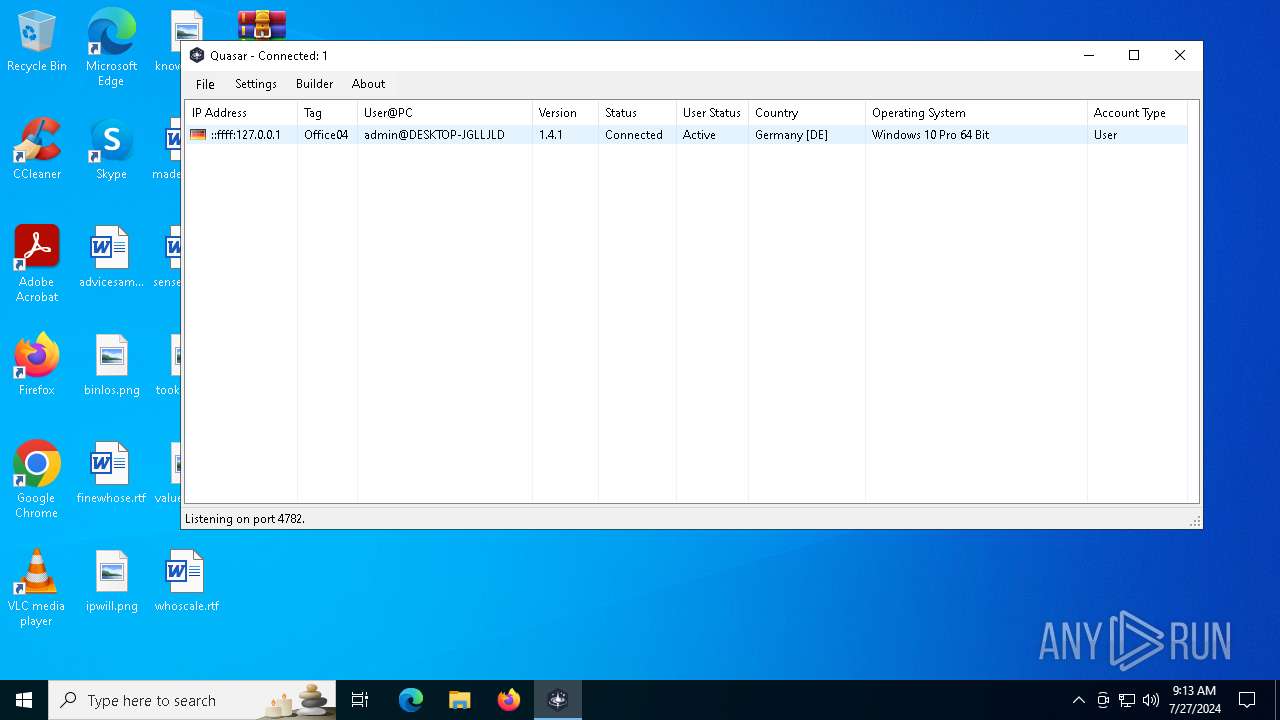
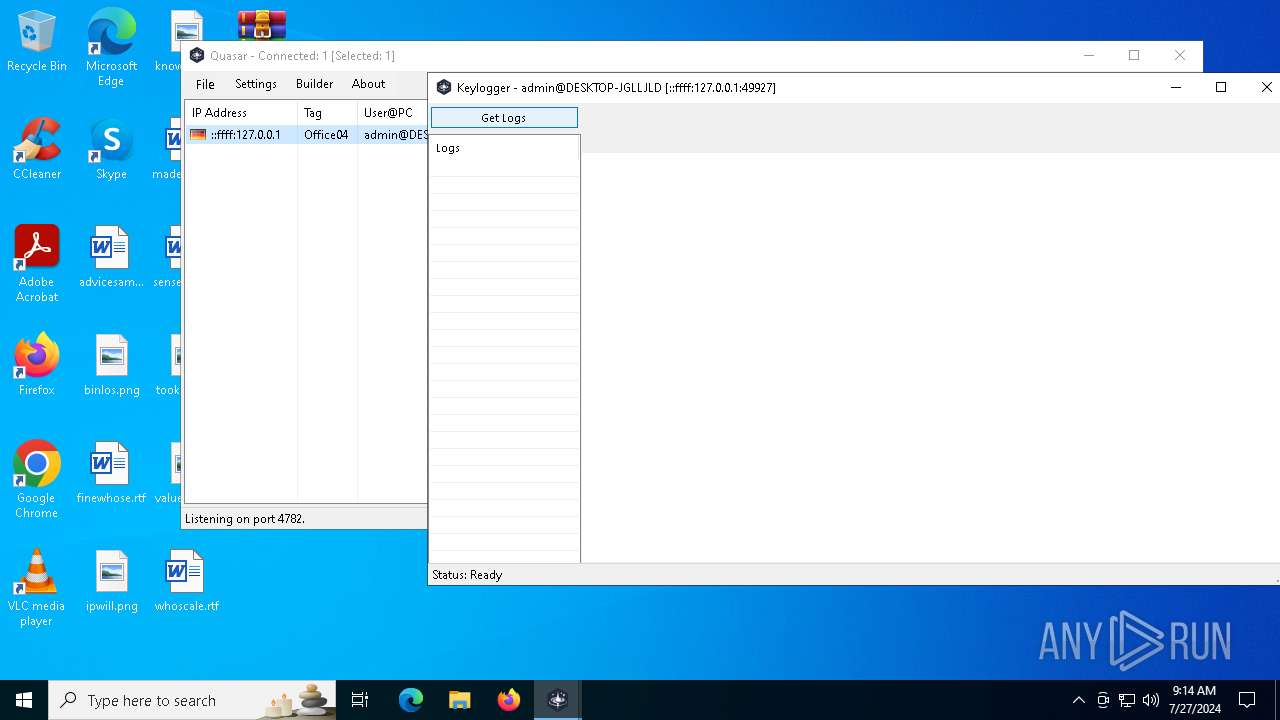
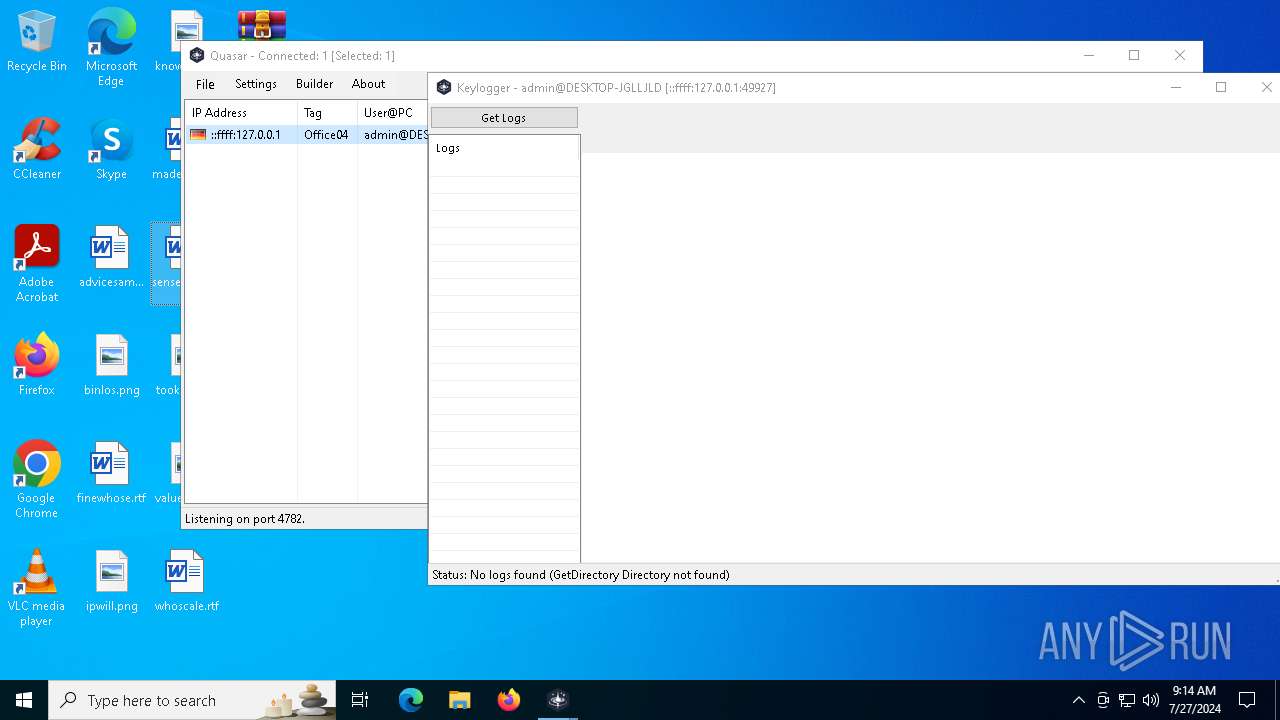
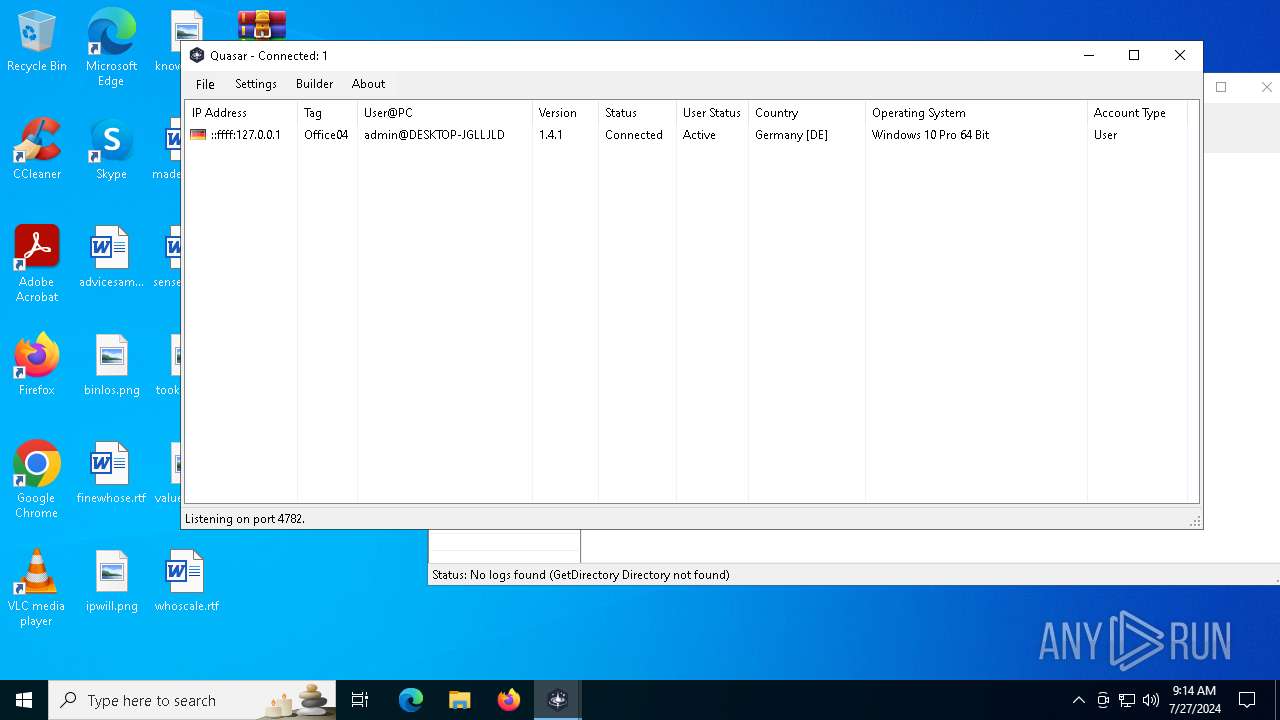
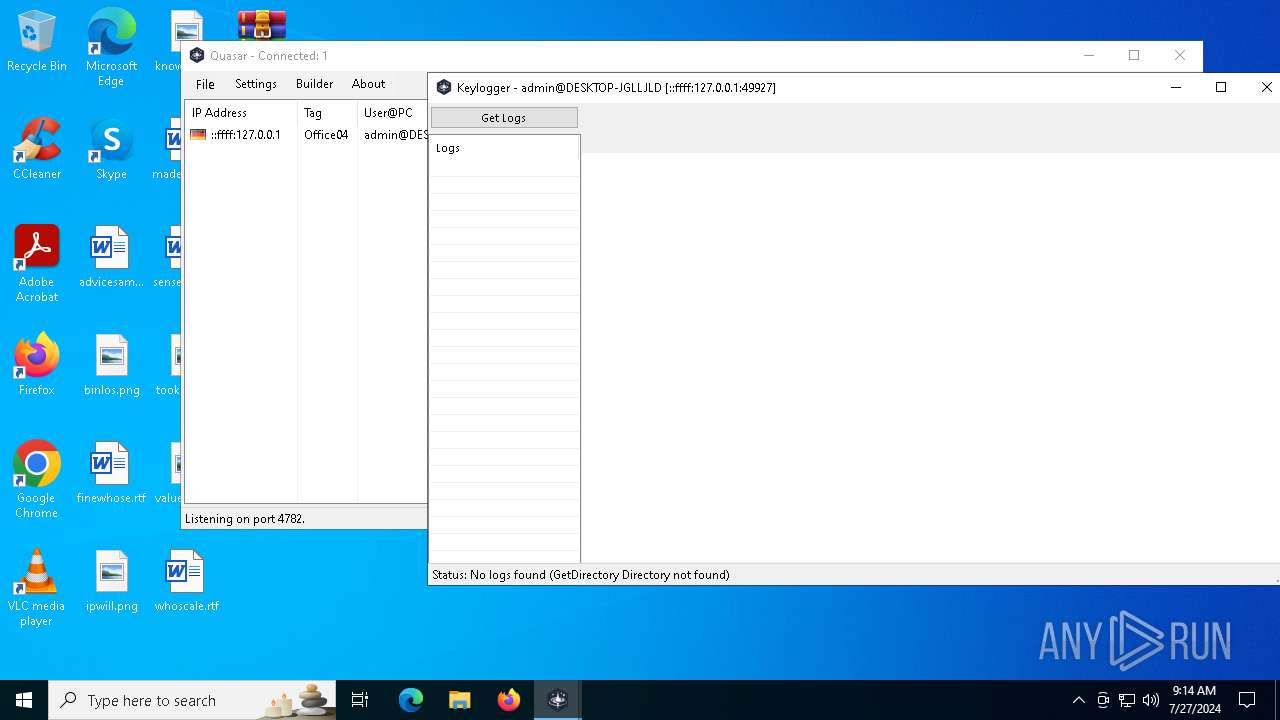
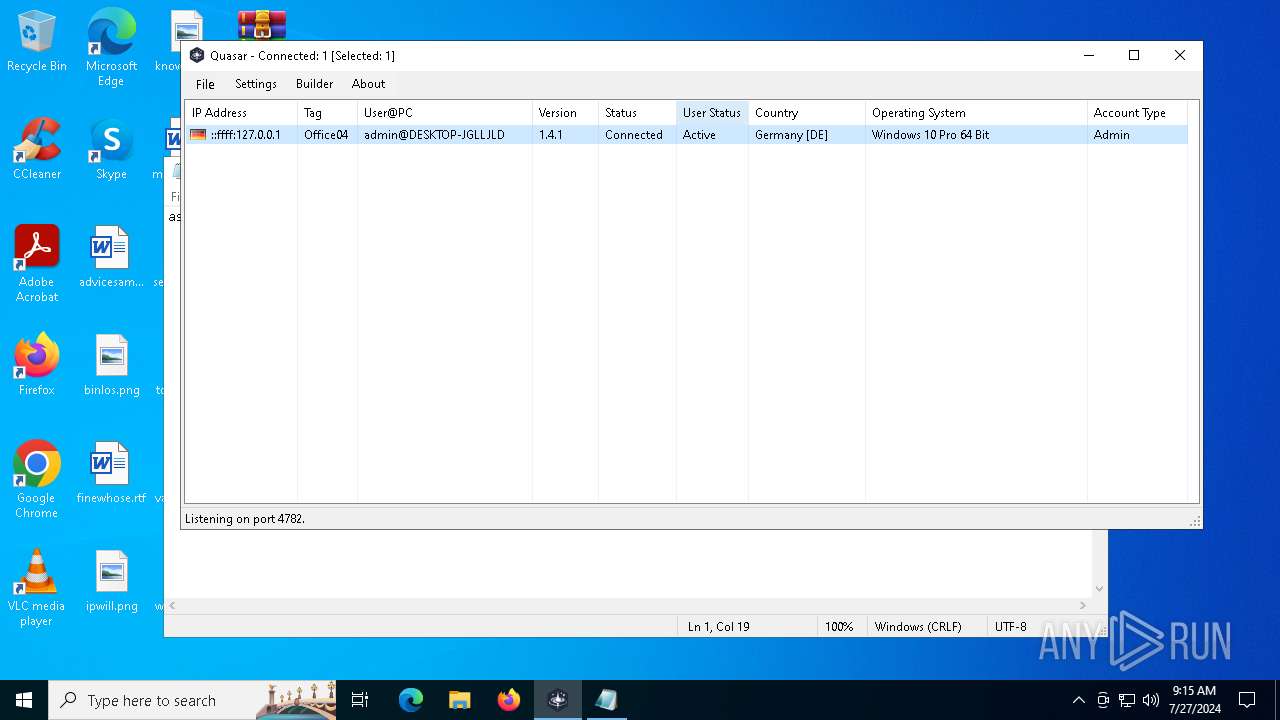
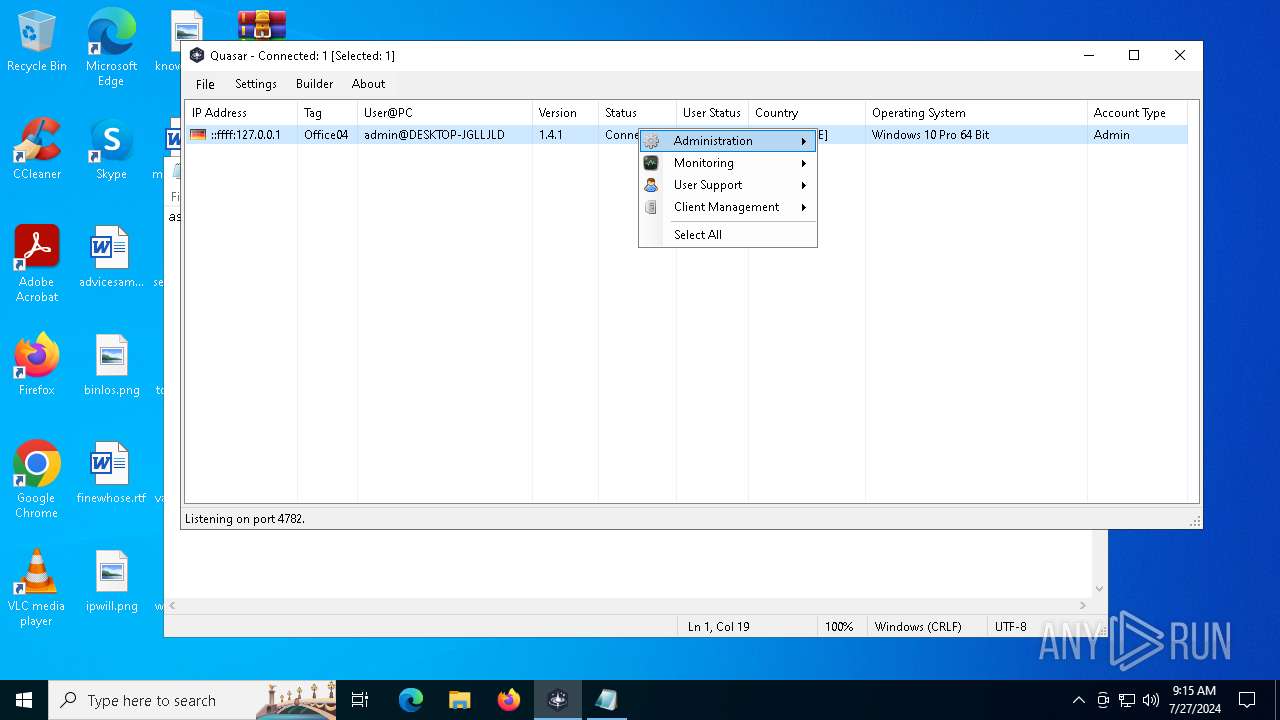
Quasar
(PID) Process(6812) fun.exe
Version1.4.1
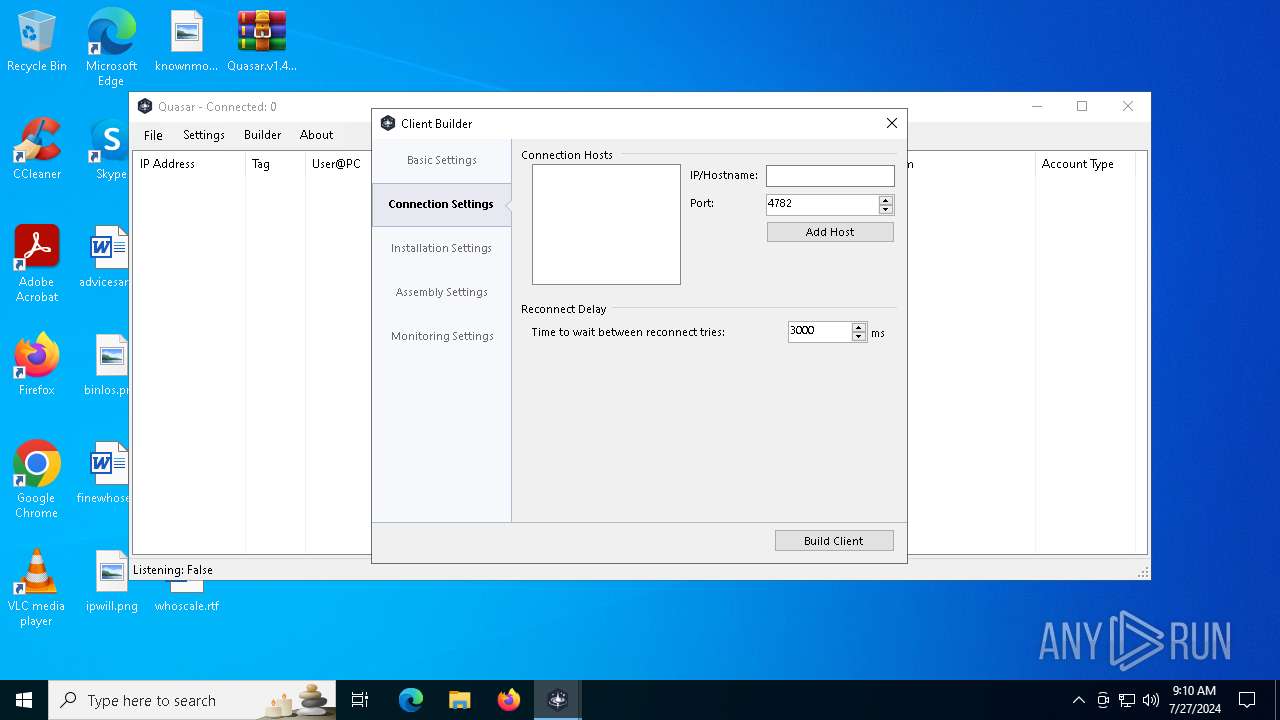
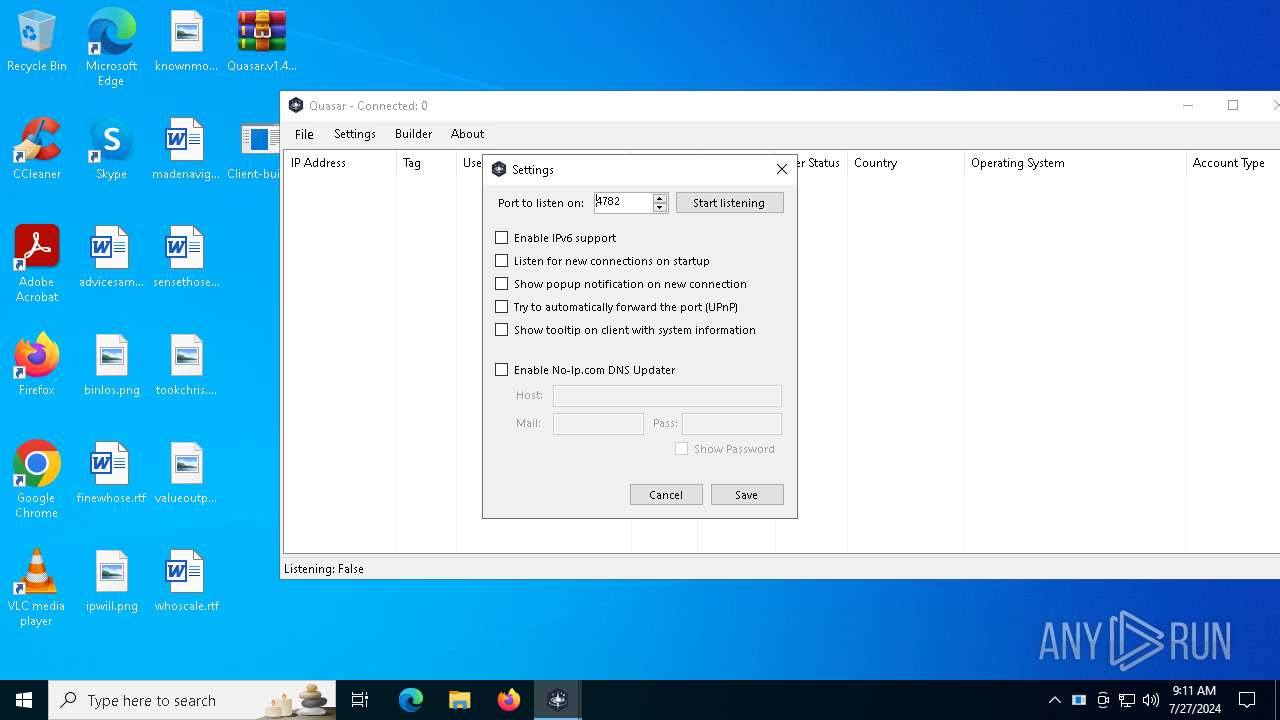
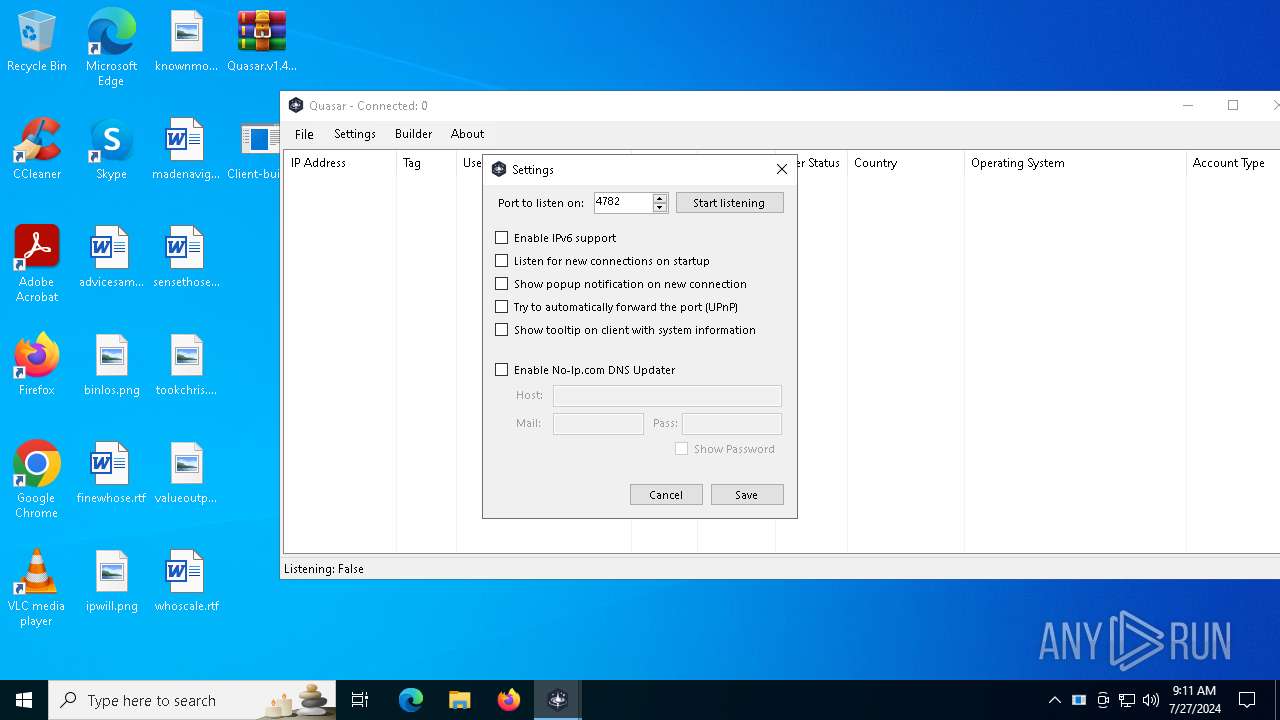
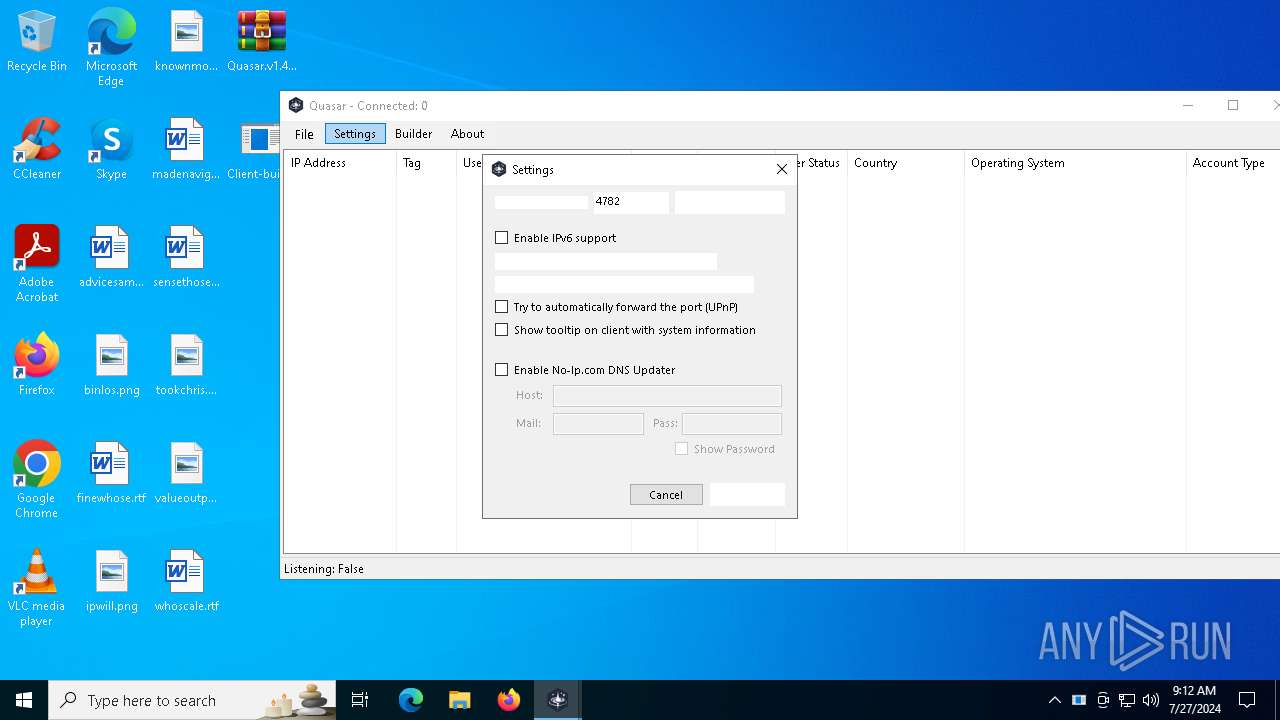
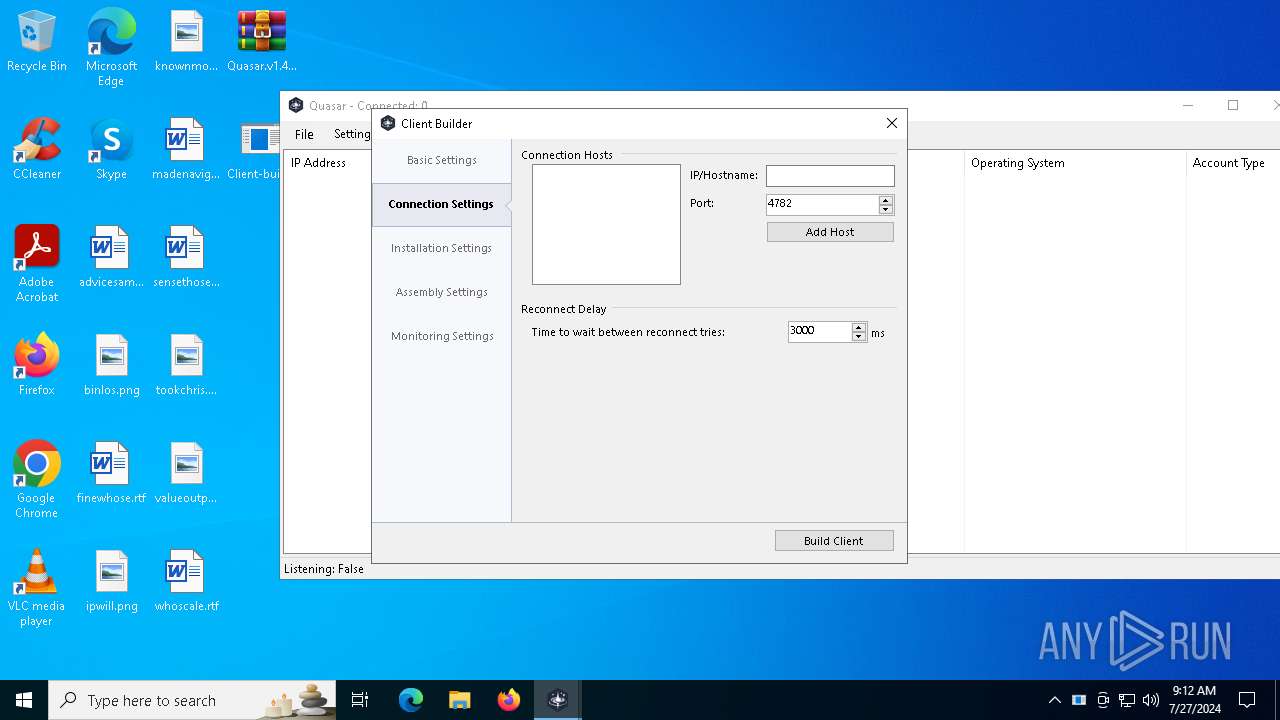
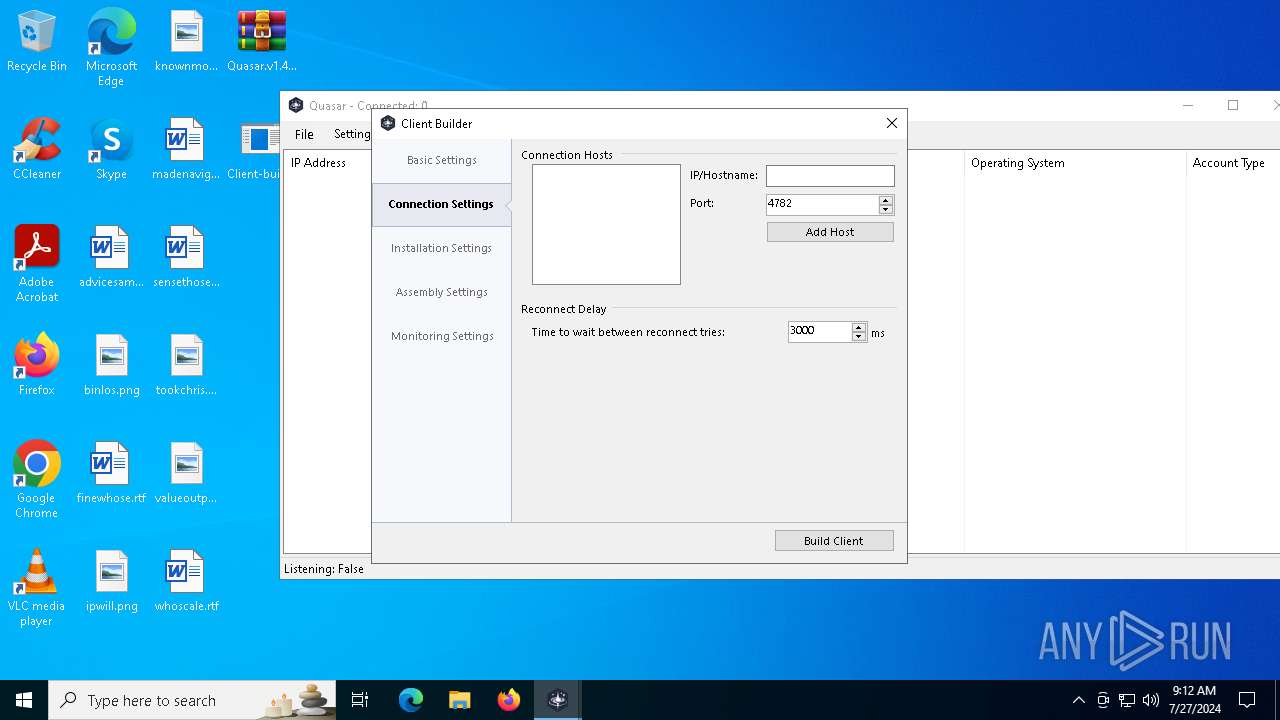
C2 (2)127.0.0.1:4782
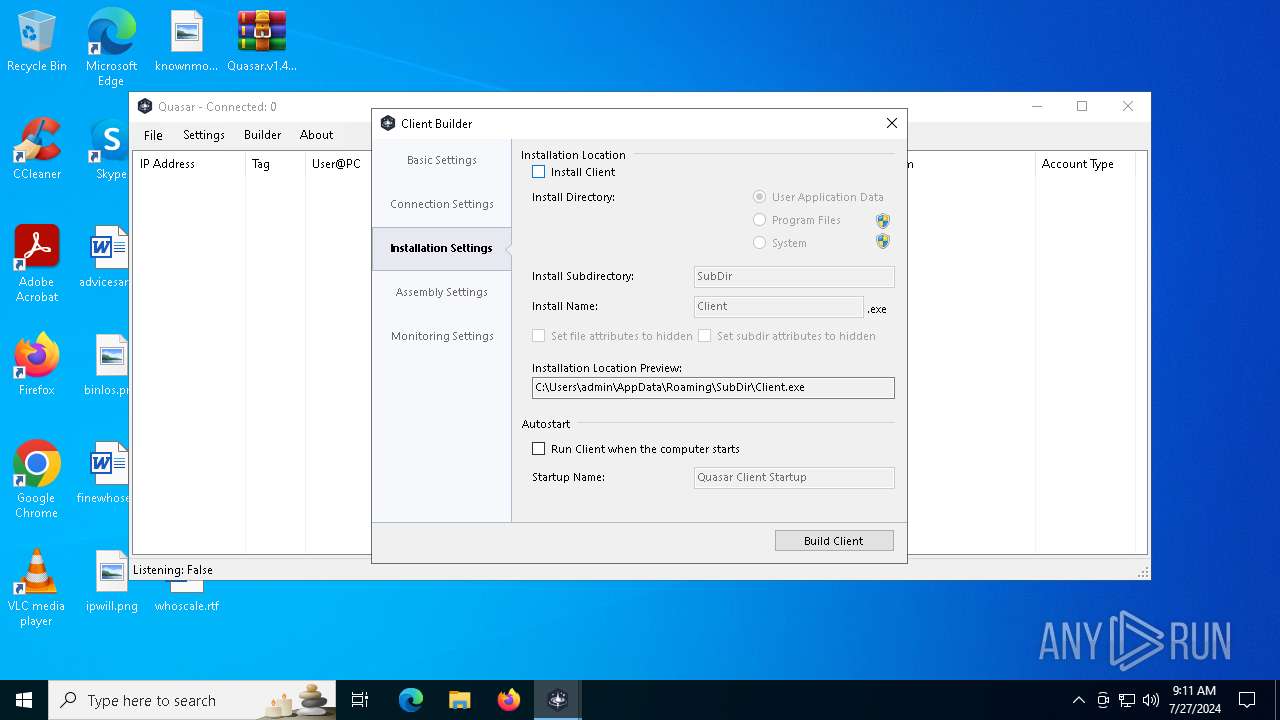
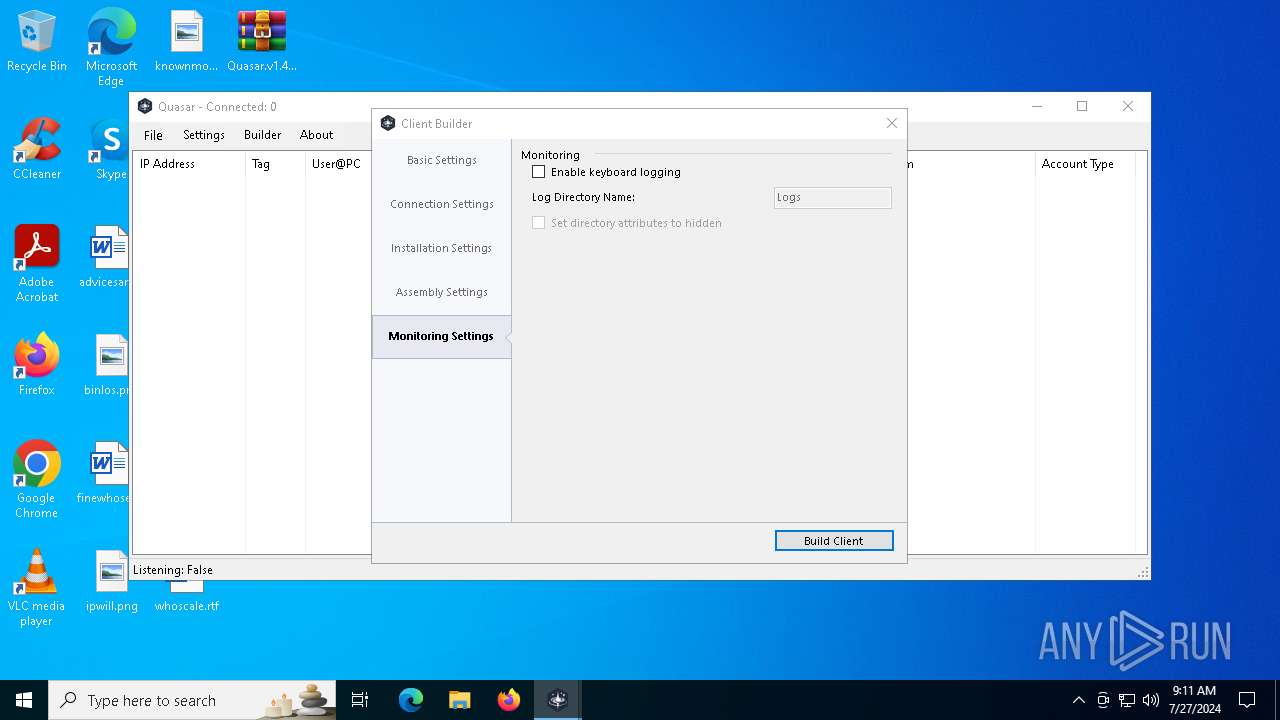
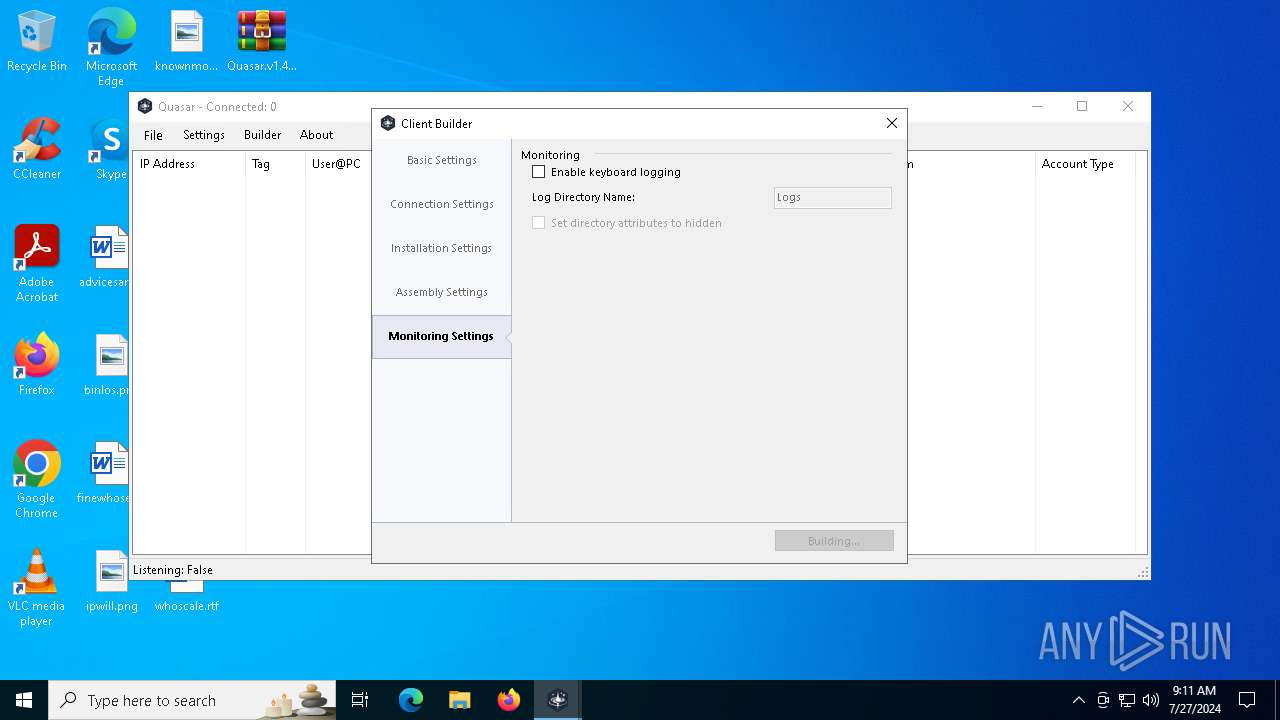
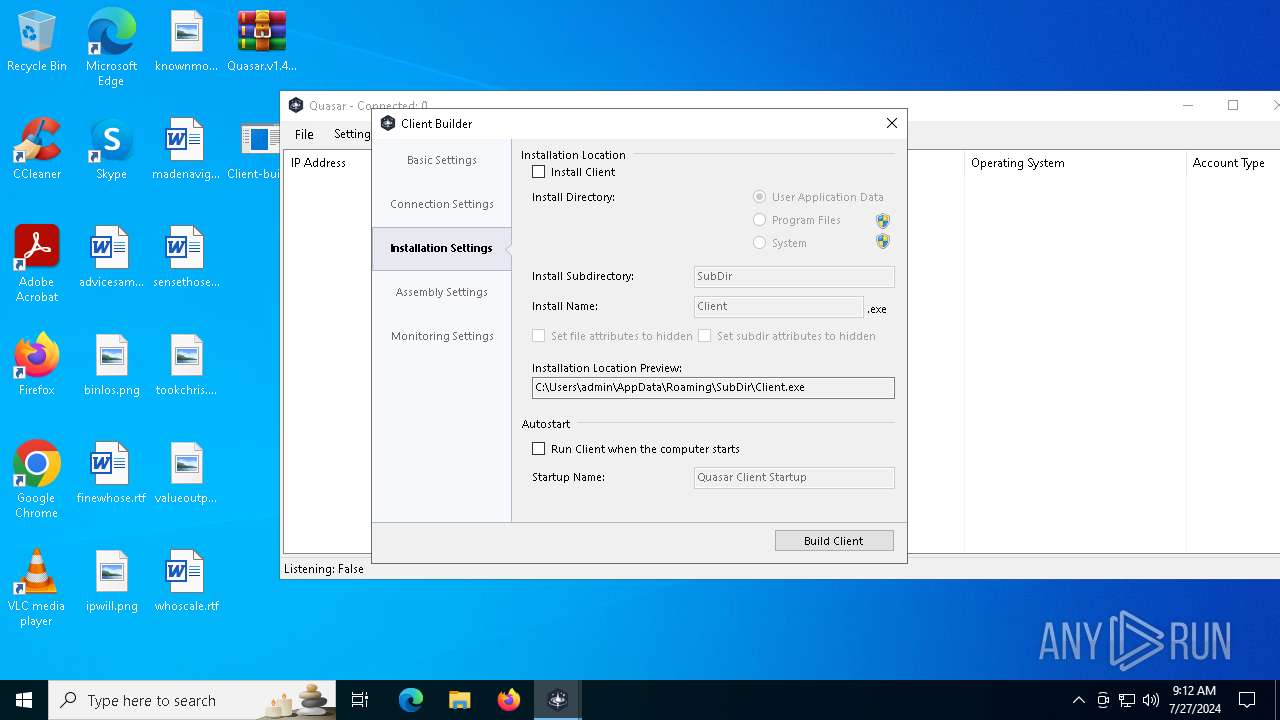
Sub_DirSubDir
Install_Namefun.exe
Mutex2ac3ef1a-e1ed-47b7-ba32-1861c7c8957e
Startupfun
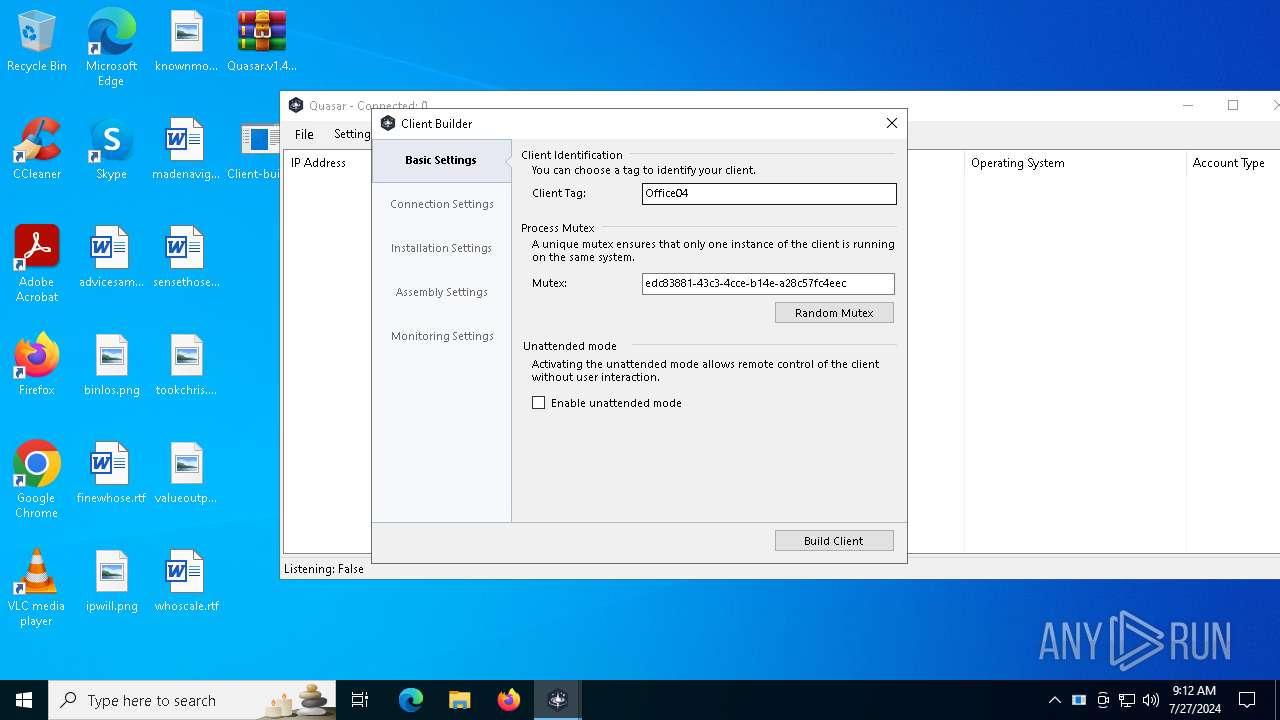
TagOffice04
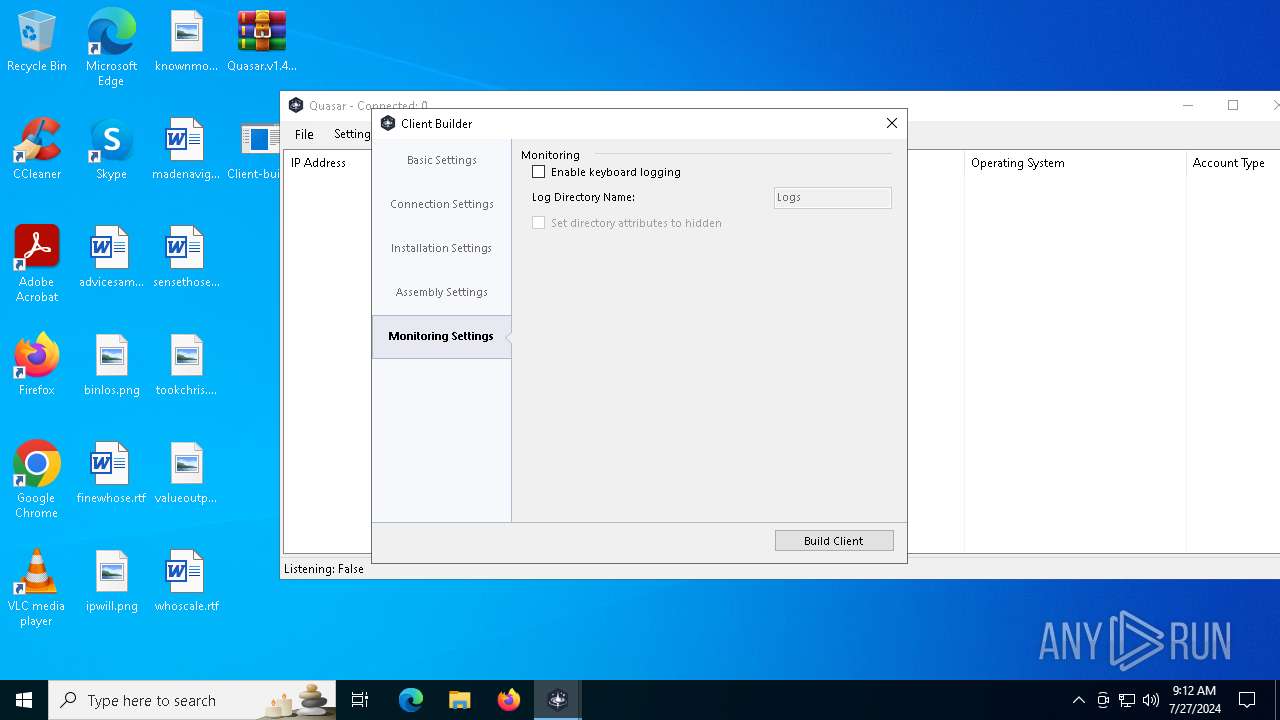
LogDirLogs
SignatureTgS8293ciMgoEpXQdEwa+h8UUksNi2RbJRQSznms+V80jFaBP9e5xgKZ+f0OUvy4tJEv0NBM9Yg5cFJFl+b2MC99RolzElMPQWIvEXA/ud4TuqYi9cWJZh6aYJdAOYfKcvw9UQKSjEL+nY73hBSIAq+OfMBXzvUs7gdI1+Y1LEk5mOFkyRQJXtzTGFhyADWCBZen7LBjDRqgeJwsKASfUbCTdnD3xentxtI2piBU81f345ECFDpUnBdJDbthCAtiJm0KD/CTaGEsF5yWrgTNdyFyFFgppTWXK0zz0se0ZHxe...
CertificateMIIE9DCCAtygAwIBAgIQAOotmlvaPzO7ZUW8brcdqTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcyNTA5MTAxMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAsjWSSC4XPzlnrqgHVYBIQpbXU8FigTauAuFZuPy9DPTbdg4un1VZRspIzTN5LFUwHnIJZywN...
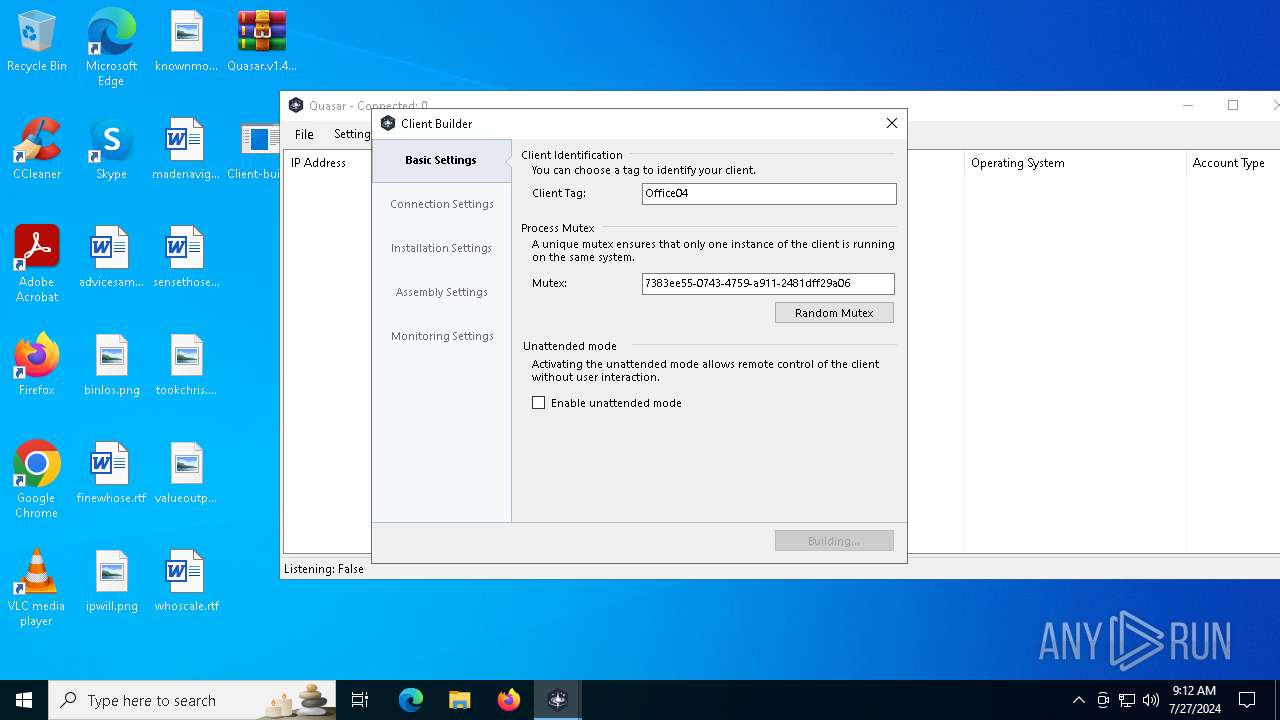
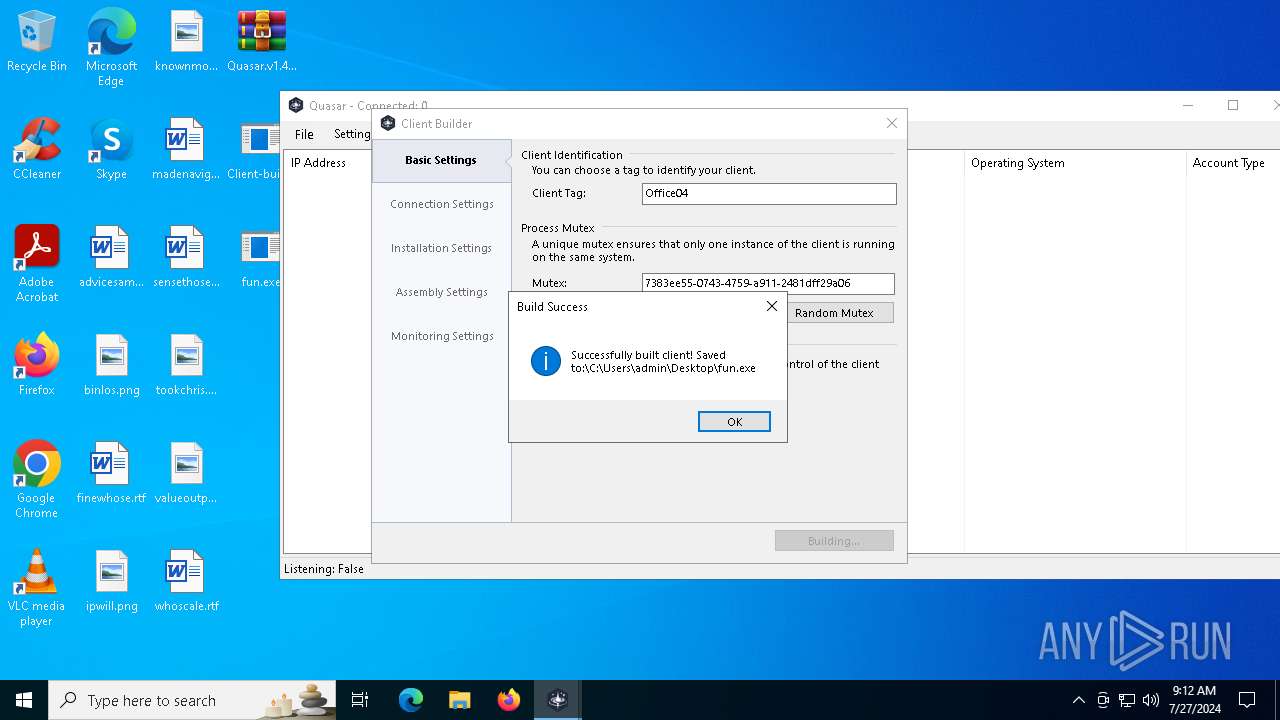
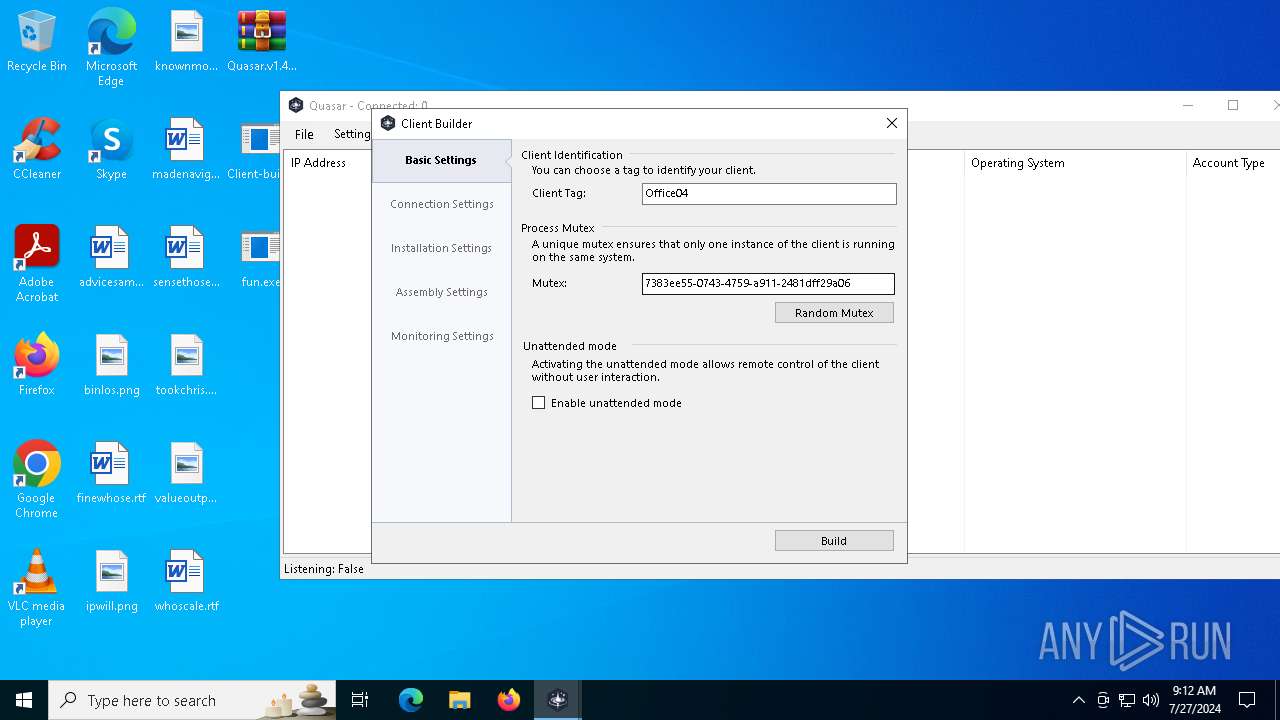
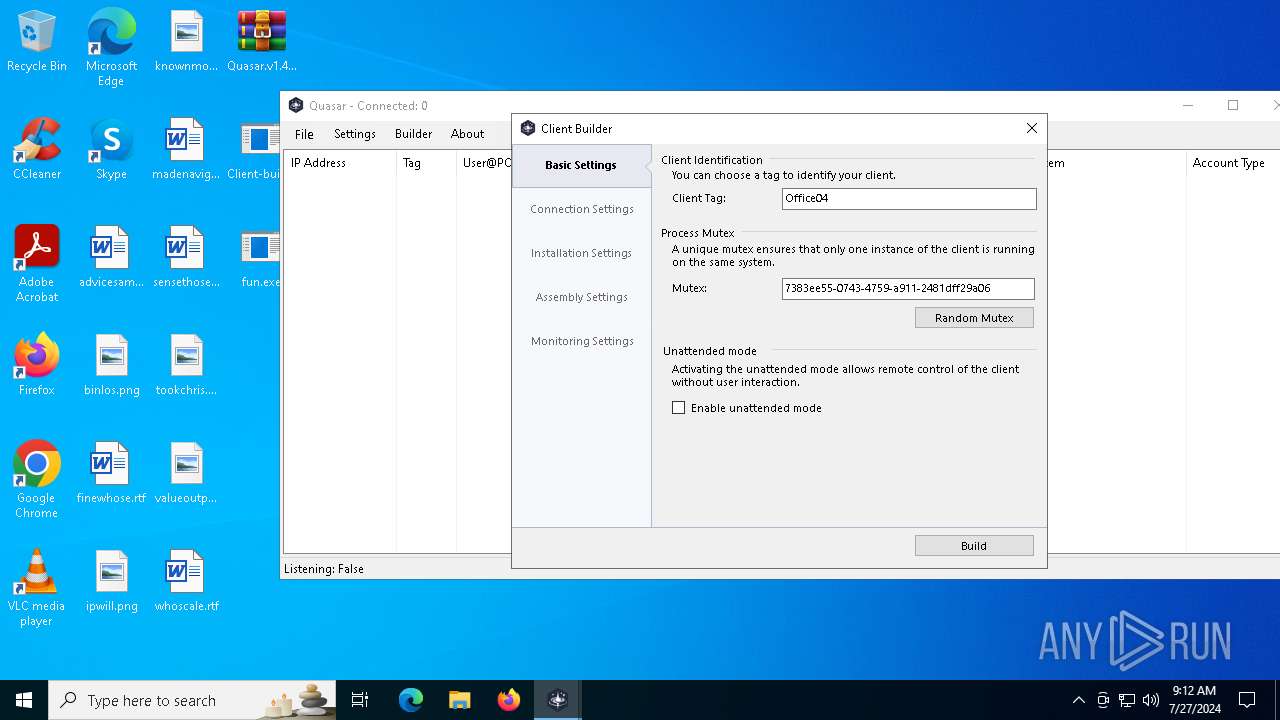
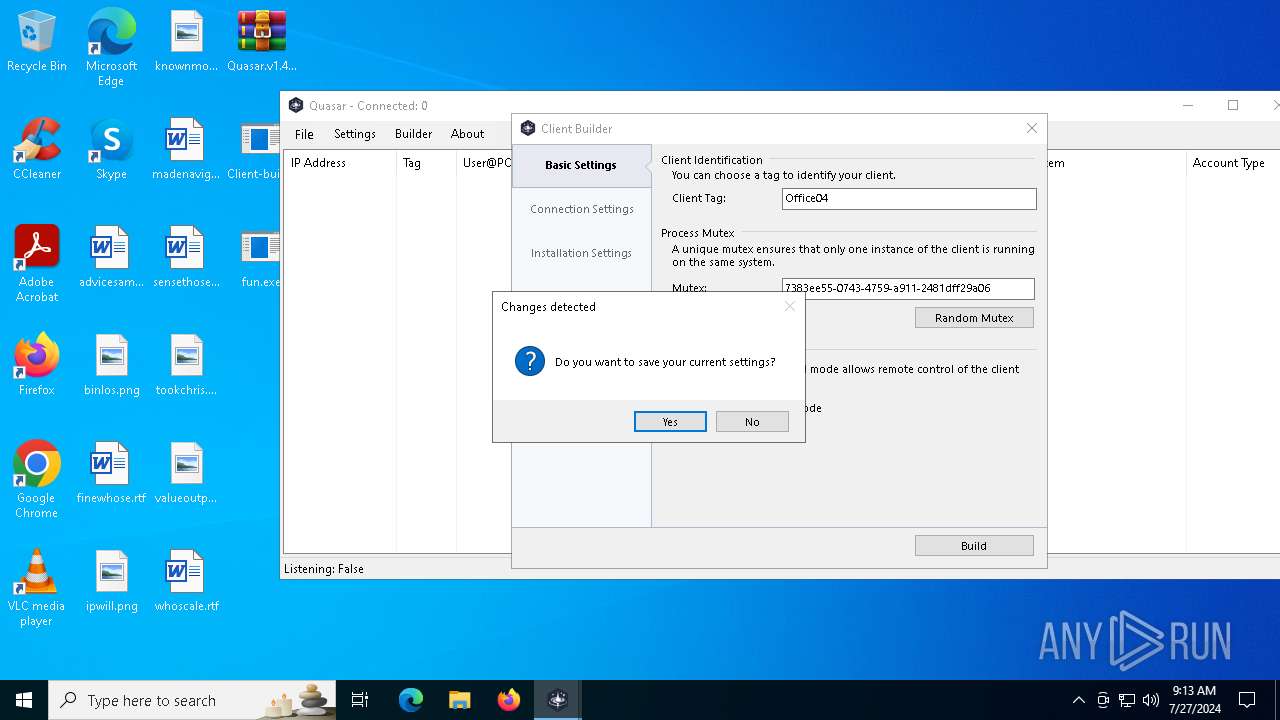
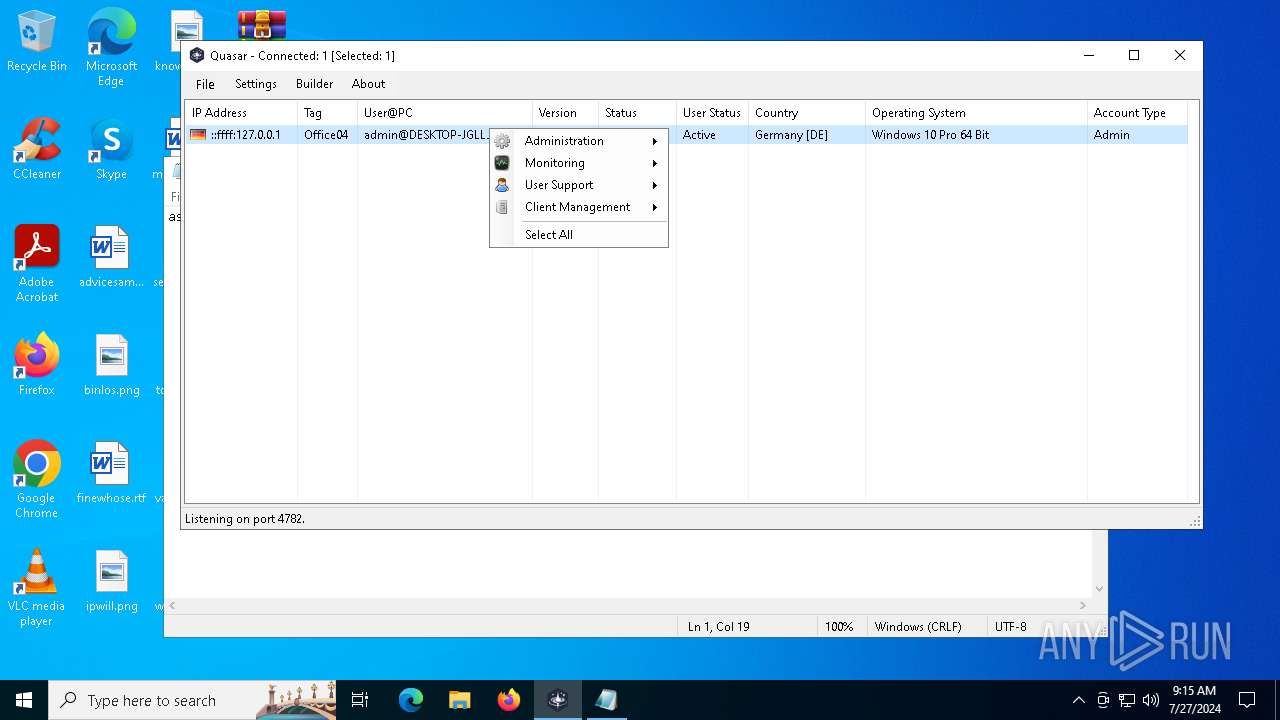
(PID) Process(6728) fun.exe
Version1.4.1
C2 (2)0.0.0.0:4782
Sub_DirSubDir
Install_NameClient.exe
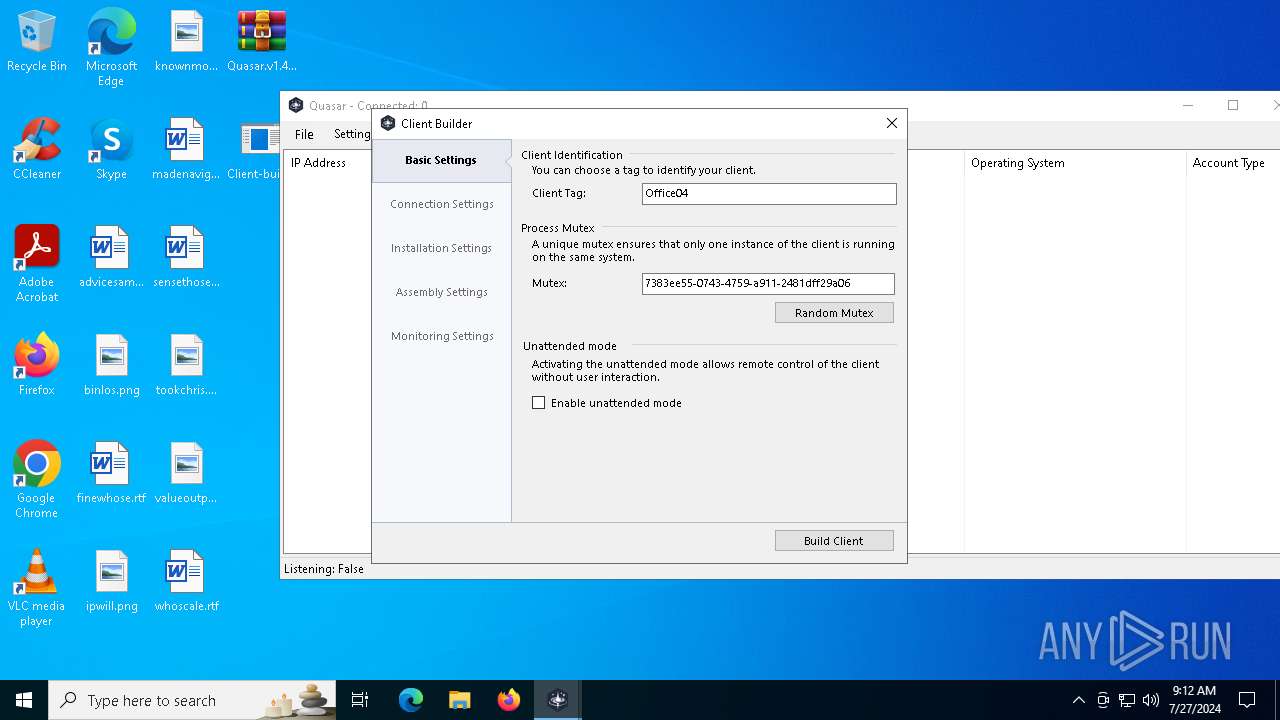
Mutex7383ee55-0743-4759-a911-2481dff29a06
StartupQuasar Client Startup
TagOffice04
LogDirLogs
SignatureTgS8293ciMgoEpXQdEwa+h8UUksNi2RbJRQSznms+V80jFaBP9e5xgKZ+f0OUvy4tJEv0NBM9Yg5cFJFl+b2MC99RolzElMPQWIvEXA/ud4TuqYi9cWJZh6aYJdAOYfKcvw9UQKSjEL+nY73hBSIAq+OfMBXzvUs7gdI1+Y1LEk5mOFkyRQJXtzTGFhyADWCBZen7LBjDRqgeJwsKASfUbCTdnD3xentxtI2piBU81f345ECFDpUnBdJDbthCAtiJm0KD/CTaGEsF5yWrgTNdyFyFFgppTWXK0zz0se0ZHxe...
CertificateMIIE9DCCAtygAwIBAgIQAOotmlvaPzO7ZUW8brcdqTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcyNTA5MTAxMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAsjWSSC4XPzlnrqgHVYBIQpbXU8FigTauAuFZuPy9DPTbdg4un1VZRspIzTN5LFUwHnIJZywN...
(PID) Process(3968) fun.exe
Version1.4.1
C2 (2)127.0.0.1:4782
Sub_DirSubDir
Install_Namefun.exe
Mutex2ac3ef1a-e1ed-47b7-ba32-1861c7c8957e
Startupfun
TagOffice04
LogDirLogs
SignatureTgS8293ciMgoEpXQdEwa+h8UUksNi2RbJRQSznms+V80jFaBP9e5xgKZ+f0OUvy4tJEv0NBM9Yg5cFJFl+b2MC99RolzElMPQWIvEXA/ud4TuqYi9cWJZh6aYJdAOYfKcvw9UQKSjEL+nY73hBSIAq+OfMBXzvUs7gdI1+Y1LEk5mOFkyRQJXtzTGFhyADWCBZen7LBjDRqgeJwsKASfUbCTdnD3xentxtI2piBU81f345ECFDpUnBdJDbthCAtiJm0KD/CTaGEsF5yWrgTNdyFyFFgppTWXK0zz0se0ZHxe...
CertificateMIIE9DCCAtygAwIBAgIQAOotmlvaPzO7ZUW8brcdqTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcyNTA5MTAxMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAsjWSSC4XPzlnrqgHVYBIQpbXU8FigTauAuFZuPy9DPTbdg4un1VZRspIzTN5LFUwHnIJZywN...
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:03:12 17:20:00 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Quasar v1.4.1/ |
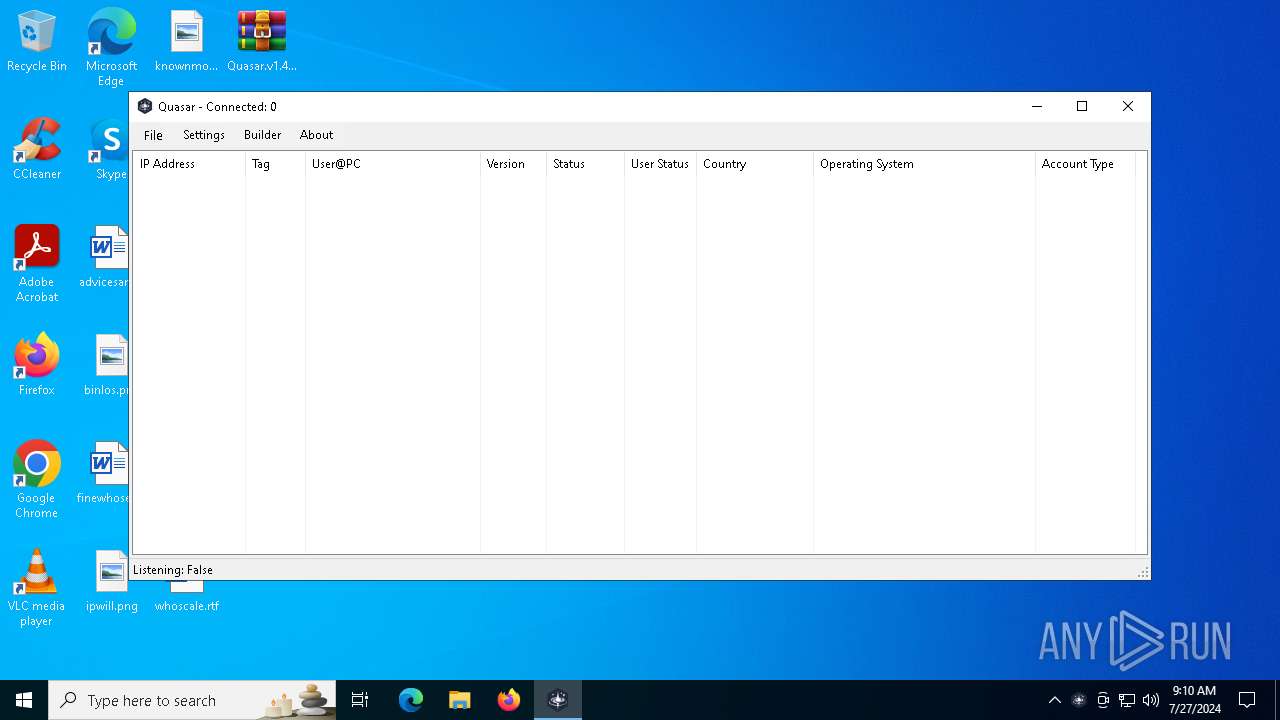
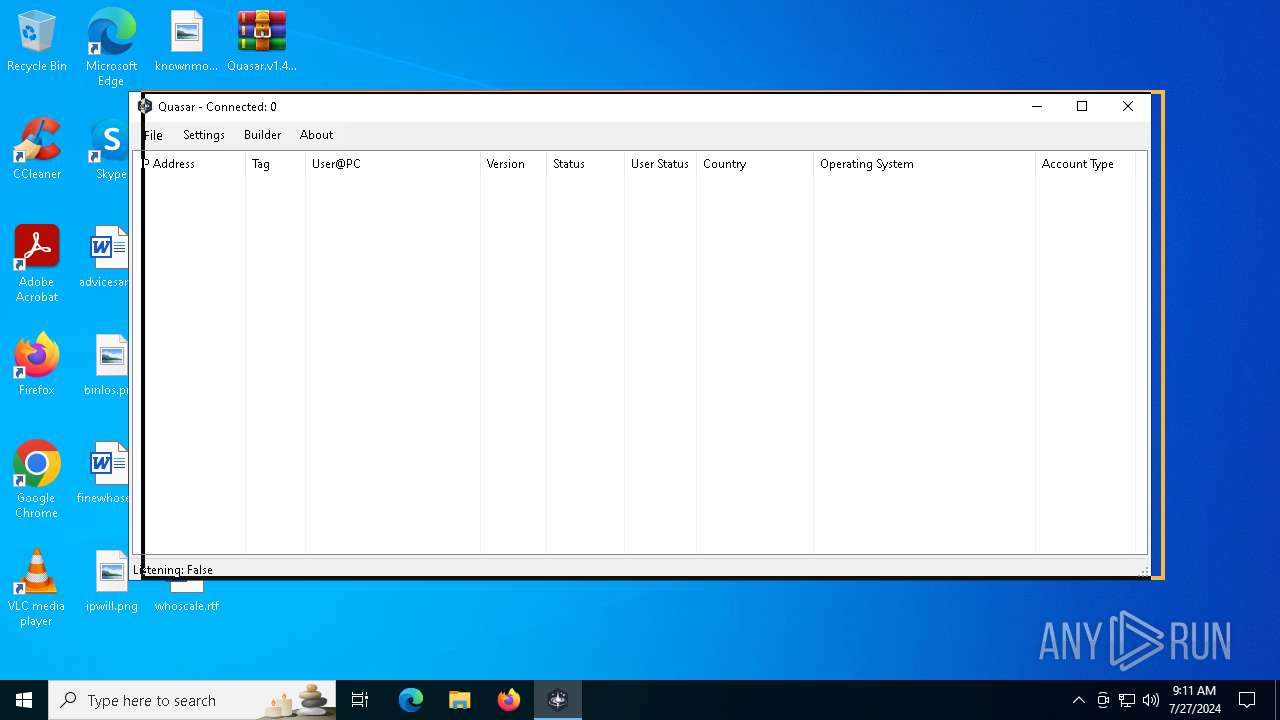
Total processes
156
Monitored processes
14
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
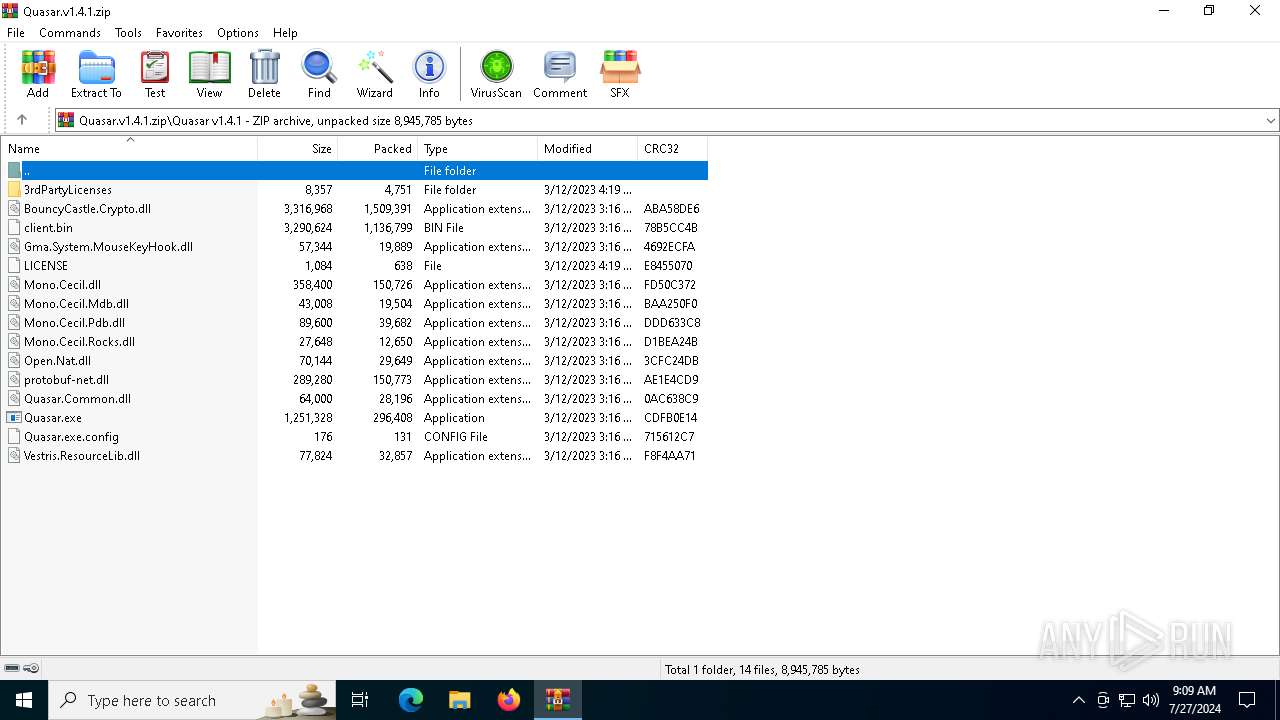
| 2340 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Quasar.v1.4.1.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2996 | "C:\Windows\explorer.exe" /select, "C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\quasar.p12" | C:\Windows\explorer.exe | — | Quasar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
| 3488 | "C:\Users\admin\Desktop\Client-built.exe" | C:\Users\admin\Desktop\Client-built.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 3 Version: 1.4.1 | |||||||||||||||
| 3536 | "C:\WINDOWS\system32\notepad.exe" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
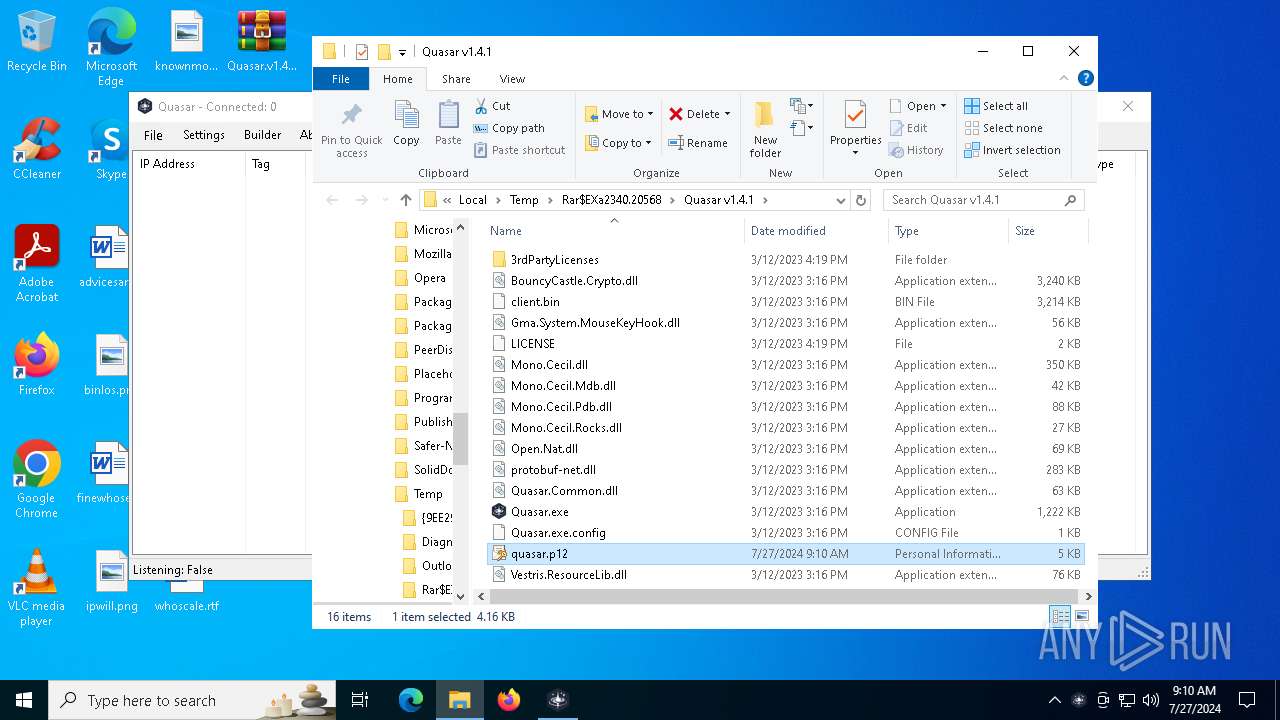
| 3572 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\Quasar.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\Quasar.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Server Version: 1.4.1 Modules
| |||||||||||||||
| 3968 | "C:\Users\admin\AppData\Roaming\SubDir\fun.exe" | C:\Users\admin\AppData\Roaming\SubDir\fun.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Version: 1.4.1 Quasar(PID) Process(3968) fun.exe Version1.4.1 C2 (2)127.0.0.1:4782 Sub_DirSubDir Install_Namefun.exe Mutex2ac3ef1a-e1ed-47b7-ba32-1861c7c8957e Startupfun TagOffice04 LogDirLogs SignatureTgS8293ciMgoEpXQdEwa+h8UUksNi2RbJRQSznms+V80jFaBP9e5xgKZ+f0OUvy4tJEv0NBM9Yg5cFJFl+b2MC99RolzElMPQWIvEXA/ud4TuqYi9cWJZh6aYJdAOYfKcvw9UQKSjEL+nY73hBSIAq+OfMBXzvUs7gdI1+Y1LEk5mOFkyRQJXtzTGFhyADWCBZen7LBjDRqgeJwsKASfUbCTdnD3xentxtI2piBU81f345ECFDpUnBdJDbthCAtiJm0KD/CTaGEsF5yWrgTNdyFyFFgppTWXK0zz0se0ZHxe... CertificateMIIE9DCCAtygAwIBAgIQAOotmlvaPzO7ZUW8brcdqTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcyNTA5MTAxMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAsjWSSC4XPzlnrqgHVYBIQpbXU8FigTauAuFZuPy9DPTbdg4un1VZRspIzTN5LFUwHnIJZywN... | |||||||||||||||
| 4356 | C:\WINDOWS\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
| 5672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 6504 | "schtasks" /create /tn "fun" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\fun.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | fun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 6728 | "C:\Users\admin\Desktop\fun.exe" | C:\Users\admin\Desktop\fun.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Version: 1.4.1 Quasar(PID) Process(6728) fun.exe Version1.4.1 C2 (2)0.0.0.0:4782 Sub_DirSubDir Install_NameClient.exe Mutex7383ee55-0743-4759-a911-2481dff29a06 StartupQuasar Client Startup TagOffice04 LogDirLogs SignatureTgS8293ciMgoEpXQdEwa+h8UUksNi2RbJRQSznms+V80jFaBP9e5xgKZ+f0OUvy4tJEv0NBM9Yg5cFJFl+b2MC99RolzElMPQWIvEXA/ud4TuqYi9cWJZh6aYJdAOYfKcvw9UQKSjEL+nY73hBSIAq+OfMBXzvUs7gdI1+Y1LEk5mOFkyRQJXtzTGFhyADWCBZen7LBjDRqgeJwsKASfUbCTdnD3xentxtI2piBU81f345ECFDpUnBdJDbthCAtiJm0KD/CTaGEsF5yWrgTNdyFyFFgppTWXK0zz0se0ZHxe... CertificateMIIE9DCCAtygAwIBAgIQAOotmlvaPzO7ZUW8brcdqTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MDcyNTA5MTAxMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAsjWSSC4XPzlnrqgHVYBIQpbXU8FigTauAuFZuPy9DPTbdg4un1VZRspIzTN5LFUwHnIJZywN... | |||||||||||||||
Total events
6 007
Read events
5 999
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Quasar.v1.4.1.zip | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
15
Suspicious files
5
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\Be.HexEditor_license.txt | text | |
MD5:0A5C19336B04E958B8E528D66A61D048 | SHA256:D691BA20526ED297DBABFD8BEEC2EF0DD2EE769783152BA5BCB9EB5037435EFB | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\Mono.Cecil_license.txt | text | |
MD5:4CC72AE97C8B623BD69A4DE2539F9728 | SHA256:62DAD7936FC1214D0187B1DD27BD68EC055AF168B7FD1989CC8E36E0E2B9A990 | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\Mono.Cecil.Pdb.dll | executable | |
MD5:6D5EB860C2BE5DBEB470E7D3F3E7DDA4 | SHA256:447EDE1984BB4ACD73BD97C0EC57A11C079CEE8301C91FB199CA98C1906D3CC4 | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\GlobalMouseKeyHook_license.txt | text | |
MD5:33C823163DCE377D283D80C9D7D29DE4 | SHA256:701A899C1BED0DFC8279AC2BA71696A65DBA68DF5F8E09FC1D18014B3CBB7D77 | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\BouncyCastle_license.html | html | |
MD5:BF8D5A737E70DD3493A475B8672F14DF | SHA256:6B73C0A42D138D1F05B527C7B936E79AF9F44A55D52E35F912DA15C0DEA43D30 | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\protobuf-net_license.txt | text | |
MD5:DFE8687C4F152EE2B14F9BE8493FCA9C | SHA256:2B492575A689E98DA5CED83D486A95C03D99F4A318CD4E8B04FE9C8DD53D8E51 | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\client.bin | executable | |
MD5:F4D16CFE4CAD388255E43F258329F805 | SHA256:8FB6AE3496D4AC025EAB443D3E322B0FAA3461D25B54093C9205D35746E3250E | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\Open.Nat_license.txt | text | |
MD5:E306664D753023CA56DBCA39110AE1C4 | SHA256:D9E507EF9EDF463EAF893160F087A1C1A5325147DDD2C9A14C745454EB676DED | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\3rdPartyLicenses\ResourceLib_license.txt | text | |
MD5:26436010667B931EC76662B43577EAA2 | SHA256:2D4F0B0A61082BEE4DED1E80664D228168AD379175AB930D7A00ECBCE163B2AE | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2340.20568\Quasar v1.4.1\Gma.System.MouseKeyHook.dll | executable | |
MD5:BFB3BD1CB571360435100BFA6ED2B997 | SHA256:A67A424013544C8270C12633E2E1E287CD5CF0B3F2E81E8D8204B37A03DA59EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
52
DNS requests
20
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | — | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | — | — | unknown |
— | — | GET | 200 | 195.201.57.90:443 | https://ipwho.is/ | DE | binary | 1008 b | unknown |
— | — | GET | 304 | 13.85.23.86:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
— | — | GET | 200 | 13.85.23.86:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
— | — | GET | 304 | 13.85.23.86:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
— | — | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | unknown |
— | — | GET | 200 | 13.85.23.86:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | unknown |
— | — | POST | 204 | 184.86.251.9:443 | https://www.bing.com/threshold/xls.aspx | US | — | — | unknown |
— | — | GET | 200 | 13.85.23.86:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
— | — | GET | 304 | 13.85.23.86:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4128 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 184.86.251.27:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1800 | slui.exe | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6044 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.91.76.224:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ipwho.is |
| malicious |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
— | — | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
1 ETPRO signatures available at the full report