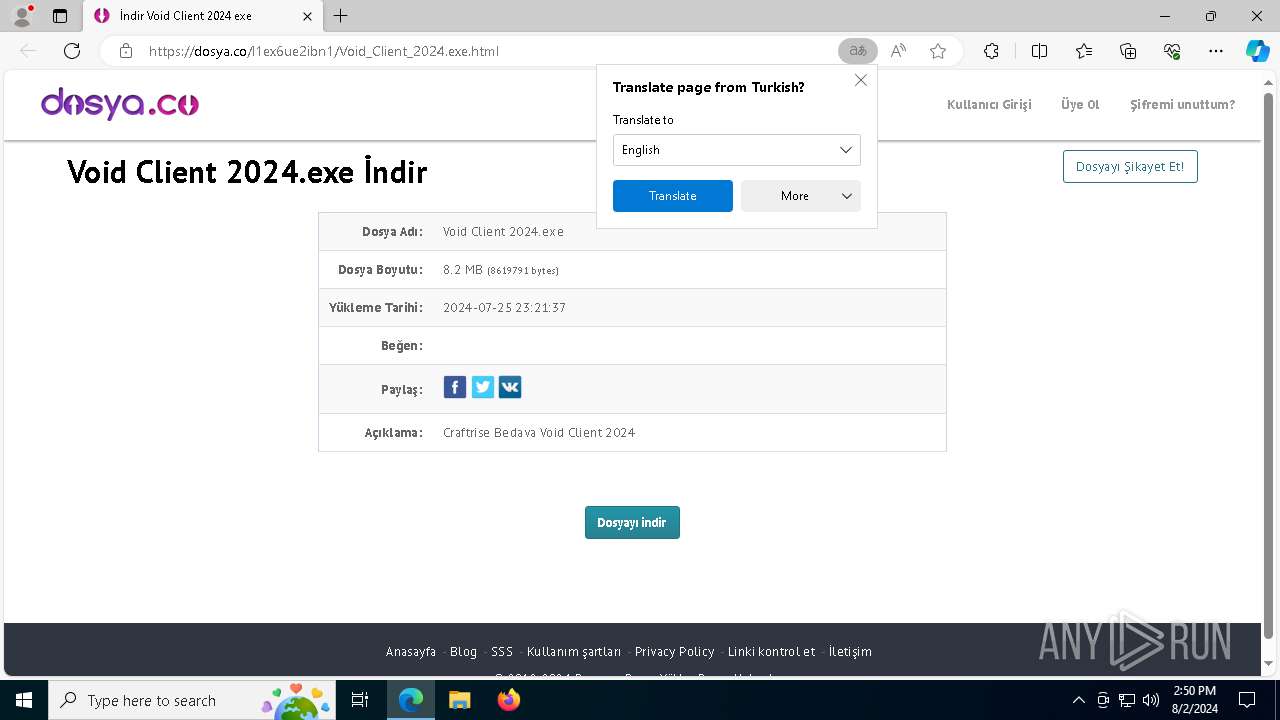
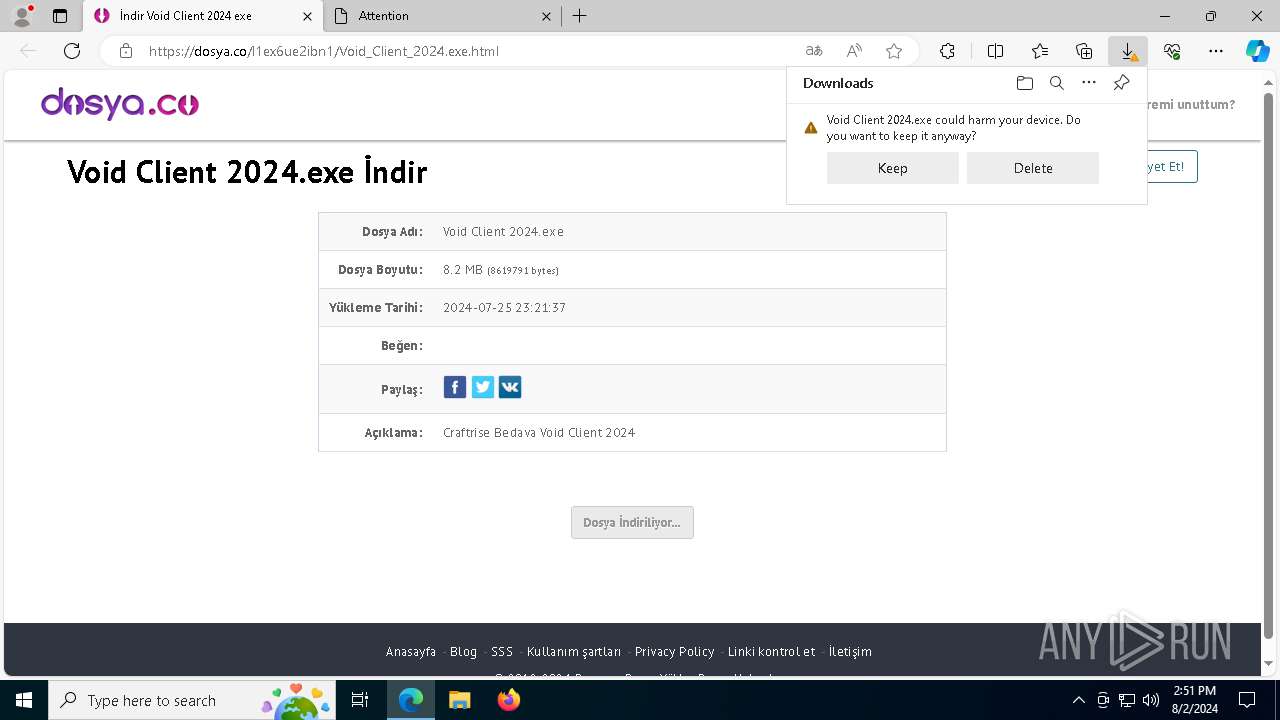
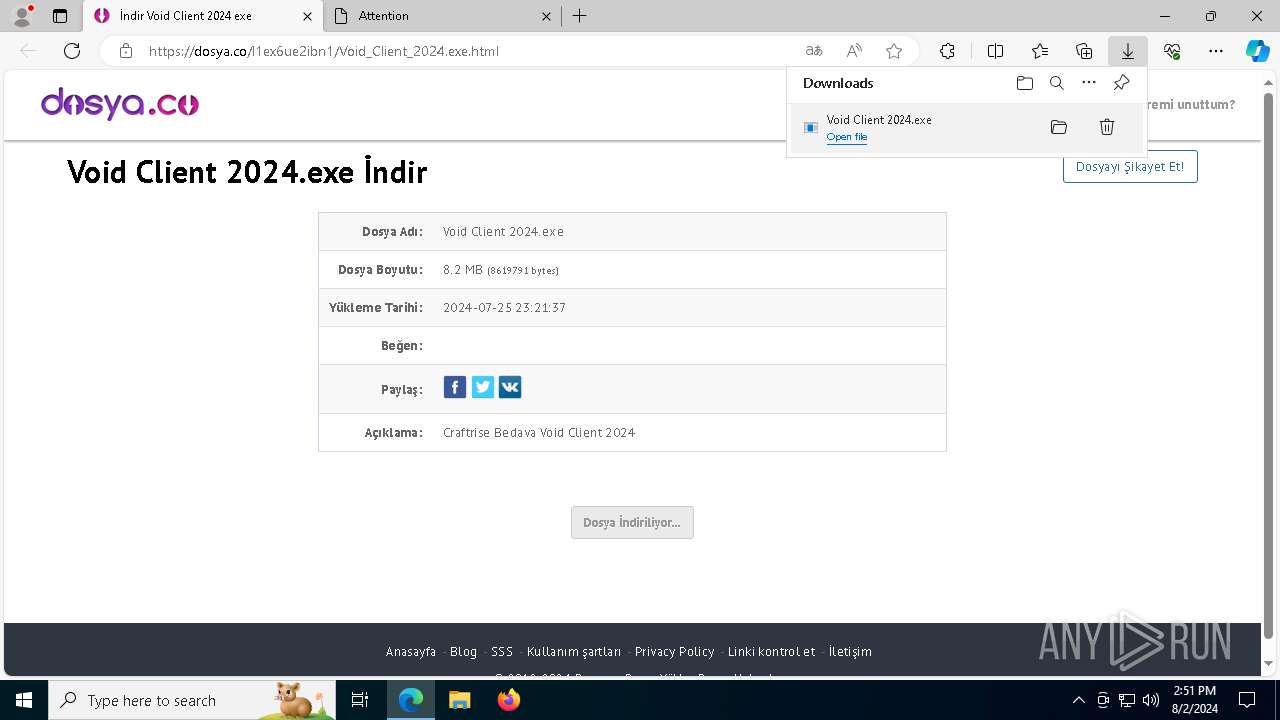
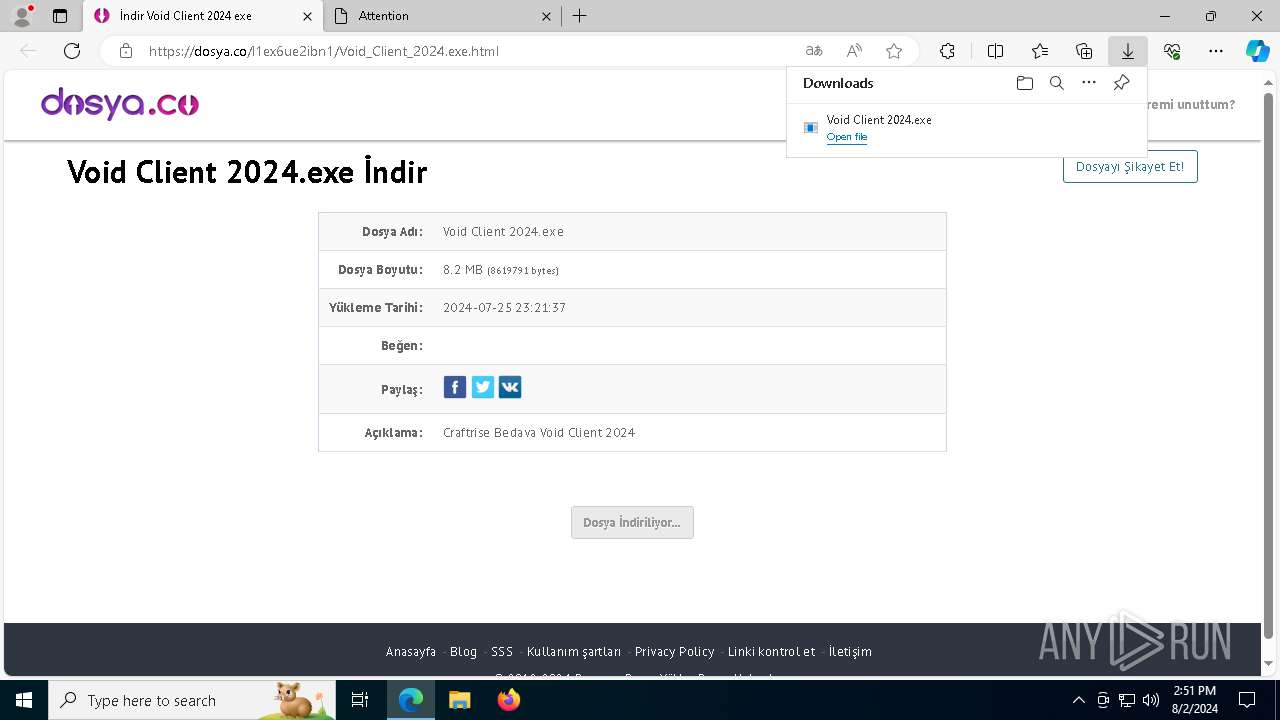
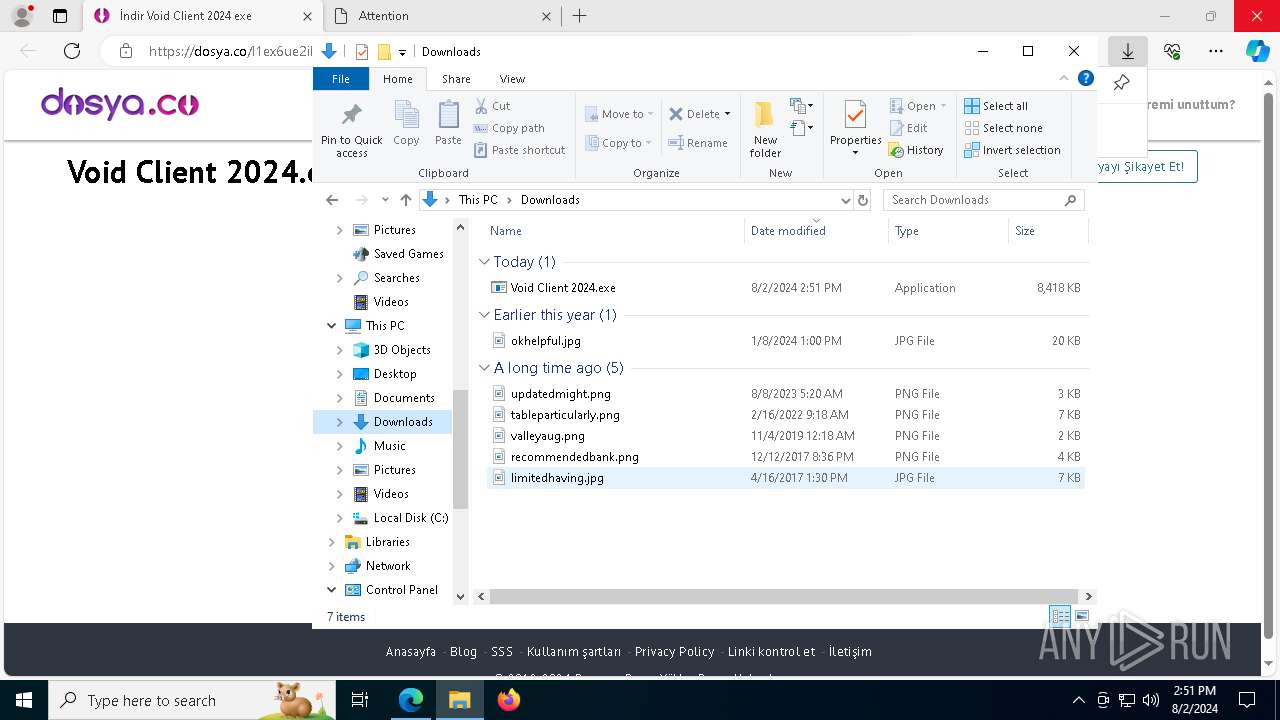
| URL: | https://dosya.co/l1ex6ue2ibn1/Void_Client_2024.exe.html |
| Full analysis: | https://app.any.run/tasks/577f49dd-cc31-4f9a-8f55-0b6f4417a55b |
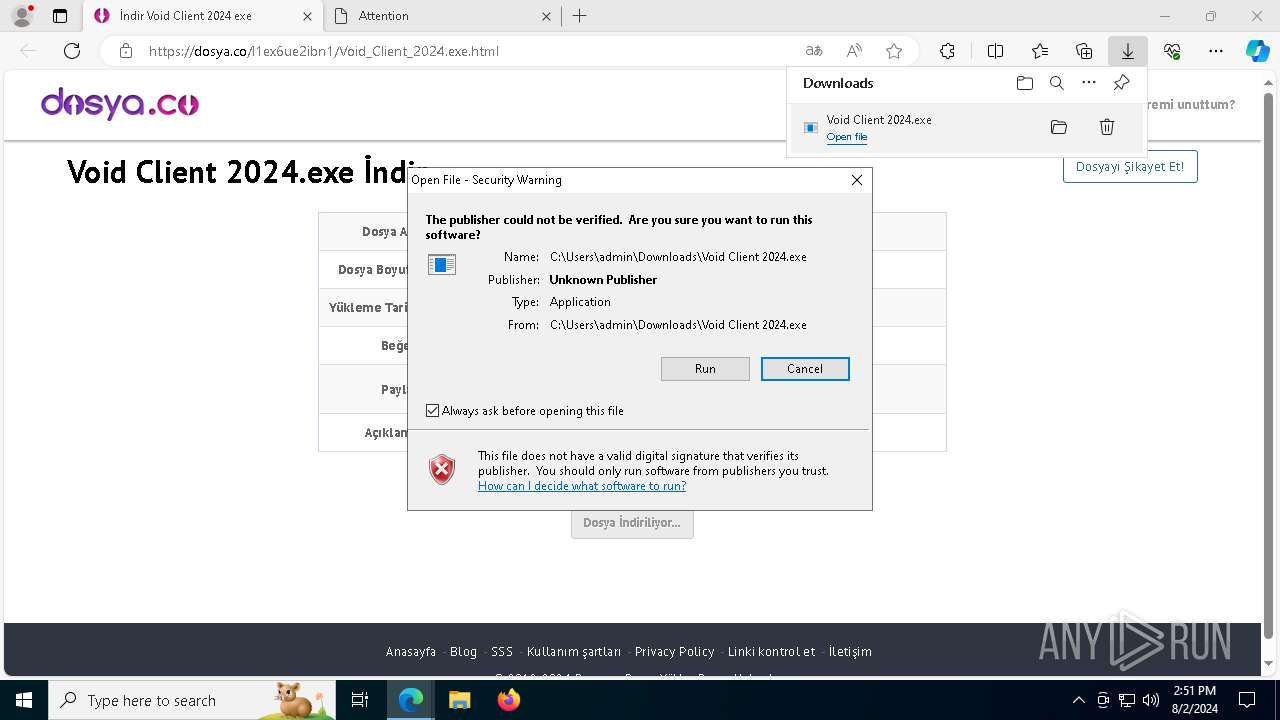
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
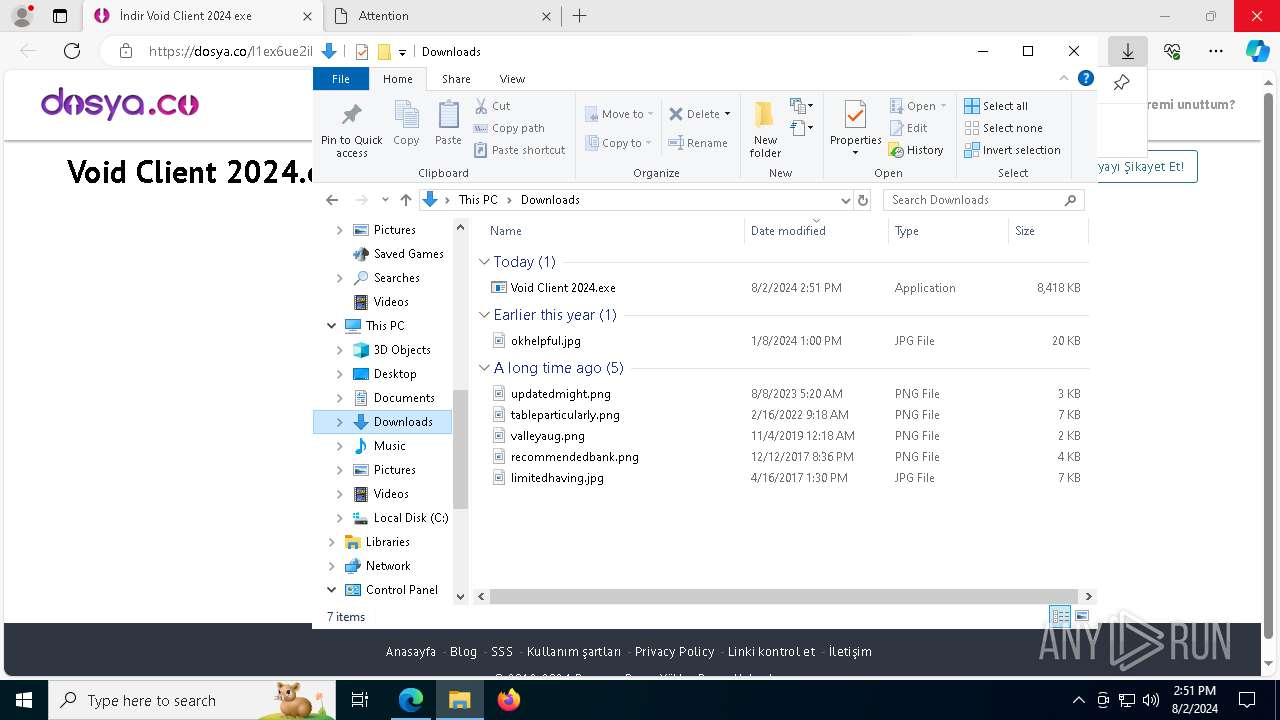
| Analysis date: | August 02, 2024, 14:50:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3F32A3E4B8D2A964BEEC98EAAFFFC2DA |
| SHA1: | B5B68E9DC375F9D42B274801FEA2797B34AC6614 |
| SHA256: | 4CCD25E84D0282DB8352D42A6A9A2B287AC815C89B440BC73EF390316366CDE3 |
| SSDEEP: | 3:N8SgLdnAR9MAWMe6XN5G:2StLf8 |
MALICIOUS
BlankGrabber has been detected
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 4100)
Drops the executable file immediately after the start
- Void Client 2024.exe (PID: 2508)
- Void Client 2024.exe (PID: 7272)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 5904)
Adds path to the Windows Defender exclusion list
- Void Client 2024.exe (PID: 8120)
- cmd.exe (PID: 6384)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 8152)
- MpCmdRun.exe (PID: 8072)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 8152)
SUSPICIOUS
Reads security settings of Internet Explorer
- cookie_exporter.exe (PID: 7376)
Process drops legitimate windows executable
- msedge.exe (PID: 7016)
- msedge.exe (PID: 6760)
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
Process drops python dynamic module
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6336)
- cmd.exe (PID: 5908)
- cmd.exe (PID: 6172)
Executable content was dropped or overwritten
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
Starts CMD.EXE for commands execution
- Void Client 2024.exe (PID: 6188)
- Void Client 2024.exe (PID: 8120)
Application launched itself
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
Loads Python modules
- Void Client 2024.exe (PID: 6188)
- Void Client 2024.exe (PID: 8120)
Changes default file association
- reg.exe (PID: 4100)
The process drops C-runtime libraries
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 1432)
- cmd.exe (PID: 2680)
Get information on the list of running processes
- cmd.exe (PID: 8144)
- Void Client 2024.exe (PID: 8120)
Found strings related to reading or modifying Windows Defender settings
- Void Client 2024.exe (PID: 8120)
- Void Client 2024.exe (PID: 6188)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6384)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6384)
- cmd.exe (PID: 8152)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 8152)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 1664)
Script disables Windows Defender's IPS
- cmd.exe (PID: 8152)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7404)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 5880)
Checks for external IP
- svchost.exe (PID: 2256)
- Void Client 2024.exe (PID: 8120)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6760)
- ComputerDefaults.exe (PID: 5904)
Checks supported languages
- cookie_exporter.exe (PID: 7376)
- identity_helper.exe (PID: 6504)
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 6188)
- Void Client 2024.exe (PID: 2508)
- Void Client 2024.exe (PID: 8120)
- MpCmdRun.exe (PID: 8072)
Reads the computer name
- cookie_exporter.exe (PID: 7376)
- identity_helper.exe (PID: 6504)
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 2508)
- Void Client 2024.exe (PID: 8120)
- MpCmdRun.exe (PID: 8072)
Reads Environment values
- identity_helper.exe (PID: 6504)
- cookie_exporter.exe (PID: 7376)
Checks proxy server information
- cookie_exporter.exe (PID: 7376)
Application launched itself
- msedge.exe (PID: 6760)
Drops the executable file immediately after the start
- msedge.exe (PID: 6760)
- msedge.exe (PID: 7016)
Executable content was dropped or overwritten
- msedge.exe (PID: 6760)
- msedge.exe (PID: 7016)
The process uses the downloaded file
- msedge.exe (PID: 7364)
- msedge.exe (PID: 6760)
Create files in a temporary directory
- Void Client 2024.exe (PID: 7272)
- Void Client 2024.exe (PID: 6188)
- Void Client 2024.exe (PID: 2508)
- Void Client 2024.exe (PID: 8120)
- MpCmdRun.exe (PID: 8072)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 5904)
- WMIC.exe (PID: 5880)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1664)
- powershell.exe (PID: 5920)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5920)
- powershell.exe (PID: 1664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
211
Monitored processes
79
Malicious processes
10
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | reg delete hkcu\Software\Classes\ms-settings /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\cmd.exe /c "computerdefaults --nouacbypass" | C:\Windows\System32\cmd.exe | — | Void Client 2024.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | C:\WINDOWS\system32\cmd.exe /c "wevtutil qe "Microsoft-Windows-Windows Defender/Operational" /f:text" | C:\Windows\System32\cmd.exe | — | Void Client 2024.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5252 --field-trial-handle=2308,i,611890019877724789,11362724636700134618,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1664 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\Downloads\Void Client 2024.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7392 --field-trial-handle=2308,i,611890019877724789,11362724636700134618,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 089
Read events
30 929
Write events
149
Delete events
11
Modification events
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31122667 | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6568) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
122
Suspicious files
75
Text files
48
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe5724.TMP | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe5724.TMP | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe5734.TMP | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe5734.TMP | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe5743.TMP | — | |
MD5:— | SHA256:— | |||
| 6760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
99
DNS requests
93
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3164 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7764 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7800 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6760 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
6760 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
6760 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQC%2FsVABu%2FWS1JYqd5fqc2%2Bj | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723188787&P2=404&P3=2&P4=g1iuO0yp4I6wjyc2NtmJi6jxEm1eA%2f5kxjWXgbGanBPLYQE%2f8YrqdLJfFKEgC8Wk8QiLBkfJ%2fTzC46Gm2gFFjA%3d%3d | unknown | — | — | whitelisted |
8120 | Void Client 2024.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
— | — | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/369e8e41-5ce3-4eb8-9826-427d58ae27b0?P1=1723188787&P2=404&P3=2&P4=g1iuO0yp4I6wjyc2NtmJi6jxEm1eA%2f5kxjWXgbGanBPLYQE%2f8YrqdLJfFKEgC8Wk8QiLBkfJ%2fTzC46Gm2gFFjA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2680 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6760 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7016 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7016 | msedge.exe | 195.201.111.49:443 | dosya.co | Hetzner Online GmbH | DE | unknown |
7016 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
7016 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
dosya.co |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7016 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7016 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
8120 | Void Client 2024.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7016 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7016 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |