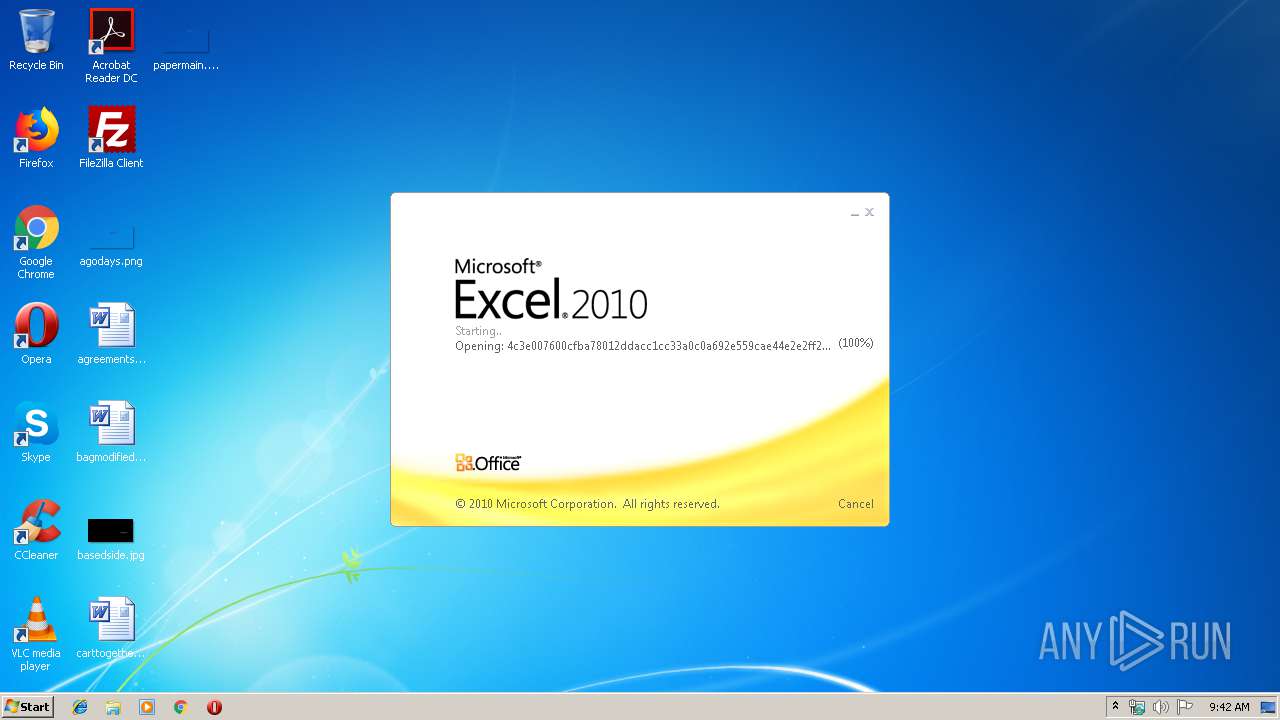
| File name: | 4c3e007600cfba78012ddacc1cc33a0c0a692e559cae44e2e2ff2cdc599b64e3.xlsx |
| Full analysis: | https://app.any.run/tasks/4617e688-cb64-4e64-89d1-0bd603d4f83e |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | March 21, 2019, 09:42:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | A38CE7686E6D0F58630B70DE23356792 |
| SHA1: | EF3BDF19DC15775E2CABDBD38904C90B832283E4 |
| SHA256: | 4C3E007600CFBA78012DDACC1CC33A0C0A692E559CAE44E2E2FF2CDC599B64E3 |
| SSDEEP: | 768:Fk755xqmvHAPQODPxsvWITTKosiG5F6XunnuIlop:F6qVPQODPxsvWIaosds4n9a |
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 1624)
Application was dropped or rewritten from another process
- petitpor47494.exe (PID: 1552)
- petitze.exe (PID: 540)
- petitze.exe (PID: 3816)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 1624)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 1624)
Detected Hawkeye Keylogger
- petitze.exe (PID: 3816)
SUSPICIOUS
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 1624)
- petitpor47494.exe (PID: 1552)
Creates files in the user directory
- EQNEDT32.EXE (PID: 1624)
- petitpor47494.exe (PID: 1552)
Application launched itself
- petitze.exe (PID: 540)
Starts itself from another location
- petitpor47494.exe (PID: 1552)
Executes scripts
- petitze.exe (PID: 3816)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:21 00:04:22 |
| ZipCRC: | 0x6096dbee |
| ZipCompressedSize: | 405 |
| ZipUncompressedSize: | 1811 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | Modey |
|---|
XML
| LastModifiedBy: | Modey |
|---|---|
| CreateDate: | 2018:11:29 09:50:53Z |
| ModifyDate: | 2018:11:29 09:53:26Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
36
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Users\admin\AppData\Roaming\petiter\petitze.exe" | C:\Users\admin\AppData\Roaming\petiter\petitze.exe | — | petitpor47494.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 964 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpEC7.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | petitze.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 1552 | "C:\Users\admin\AppData\Roaming\petitpor47494.exe" | C:\Users\admin\AppData\Roaming\petitpor47494.exe | EQNEDT32.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3816 | "C:\Users\admin\AppData\Roaming\petiter\petitze.exe" | C:\Users\admin\AppData\Roaming\petiter\petitze.exe | petitze.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
579
Read events
536
Write events
36
Delete events
7
Modification events
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | `=3 |
Value: 603D3300A0030000010000000000000000000000 | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: A003000084D03C6BCADFD40100000000 | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | `=3 |
Value: 603D3300A0030000010000000000000000000000 | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (928) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\F8C1B |
| Operation: | write | Name: | F8C1B |
Value: 04000000A00300006700000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0034006300330065003000300037003600300030006300660062006100370038003000310032006400640061006300630031006300630033003300610030006300300061003600390032006500350035003900630061006500340034006500320065003200660066003200630064006300350039003900620036003400650033002E0078006C0073007800000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000B038D96CCADFD4011B8C0F001B8C0F0000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 928 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR85D0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1552 | petitpor47494.exe | C:\Users\admin\AppData\Roaming\petiter\petitze.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 1624 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\petitpor47494.exe | executable | |
MD5:— | SHA256:— | |||
| 1624 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\petit[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3816 | petitze.exe | C:\Users\admin\AppData\Local\Temp\c4e681c3-f0d5-5260-1e84-0e7fc68922c3 | text | |
MD5:— | SHA256:— | |||
| 1552 | petitpor47494.exe | C:\Users\admin\AppData\Roaming\petiter\petitze.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1624 | EQNEDT32.EXE | GET | 200 | 217.182.138.150:80 | http://megaklik.top/petit/petit.exe | FR | executable | 904 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1624 | EQNEDT32.EXE | 217.182.138.150:80 | megaklik.top | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
megaklik.top |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1072 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1624 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
1624 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
1624 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1624 | EQNEDT32.EXE | Misc activity | ET INFO Possible EXE Download From Suspicious TLD |