| File name: | KMSpico.exe |
| Full analysis: | https://app.any.run/tasks/1e470c48-a18f-4cc5-82c1-108b74deabbf |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
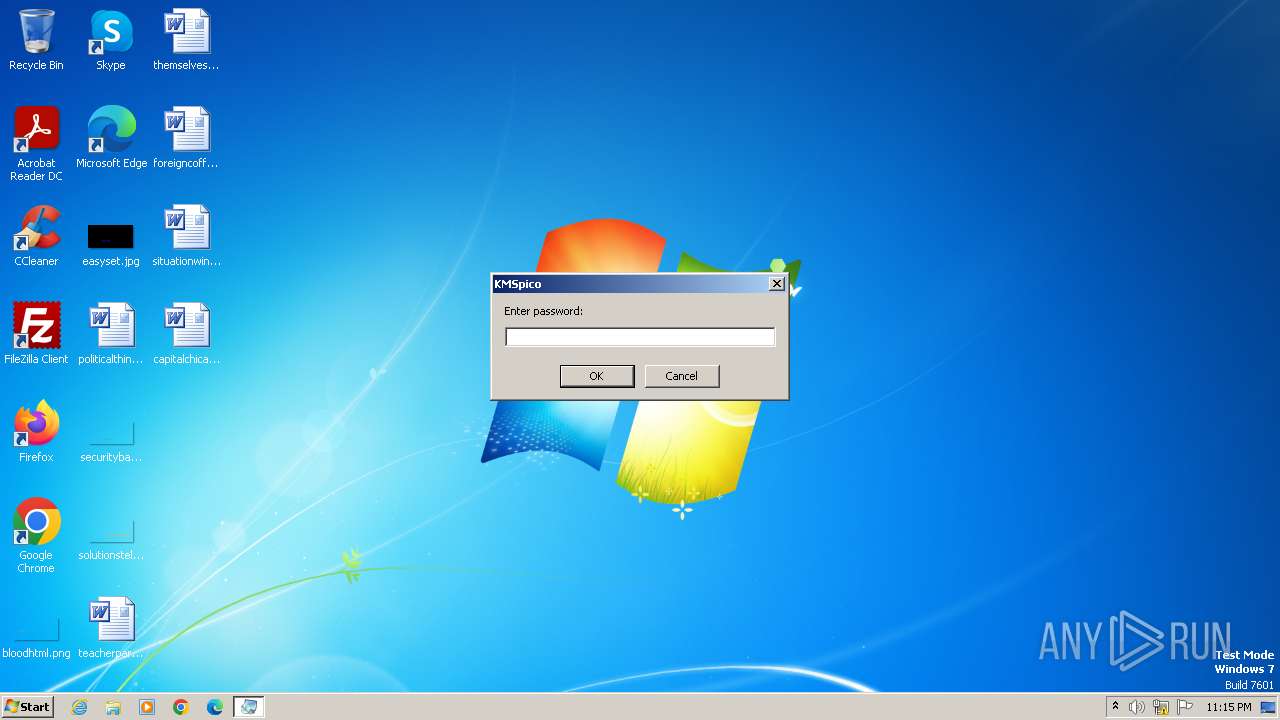
| Analysis date: | November 04, 2023, 23:15:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 47E561D87E4D44DB0198EC60A9BD918D |
| SHA1: | 095597C728136F2506AC1EF145497E7E6859CD31 |
| SHA256: | 4BC415E2173C02216432F6D484CAD1CE362E44F4FD577F0B819716CF6603DF03 |
| SSDEEP: | 98304:7/Op2wwJdB0Nc2l4k0zVme/8orlnX/IIXzMlENmSijjqAjLBHZqAFTQ2KS3n7YVT:rQPuAxSrPuC5Who |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3564)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3564)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3564)
Drops the executable file immediately after the start
- KMSpico.exe (PID: 3196)
- KMSpico.exe (PID: 3732)
- KMSpico.exe (PID: 3676)
- KMSpico.tmp (PID: 3592)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3564)
Unusual connection from system programs
- wscript.exe (PID: 3564)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3564)
LUMMA has been detected (SURICATA)
- MEGAsync.exe (PID: 3864)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 3564)
Connects to the CnC server
- MEGAsync.exe (PID: 3864)
LUMMA has been detected (YARA)
- MEGAsync.exe (PID: 3864)
Actions looks like stealing of personal data
- MEGAsync.exe (PID: 3864)
SUSPICIOUS
Reads the Internet Settings
- KMSpico.exe (PID: 3196)
- wscript.exe (PID: 3564)
- MEGAsync.exe (PID: 3864)
The process executes VB scripts
- KMSpico.exe (PID: 3196)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 3564)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3564)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3564)
Adds/modifies Windows certificates
- KMSpico.exe (PID: 3196)
Searches for installed software
- MEGAsync.exe (PID: 3864)
Reads browser cookies
- MEGAsync.exe (PID: 3864)
Process drops legitimate windows executable
- KMSpico.tmp (PID: 3592)
Reads the Windows owner or organization settings
- KMSpico.tmp (PID: 3592)
INFO
Reads the computer name
- KMSpico.exe (PID: 3196)
- wmpnscfg.exe (PID: 3632)
- MEGAsync.exe (PID: 3864)
- KMSpico.tmp (PID: 3992)
- KMSpico.tmp (PID: 3592)
Checks supported languages
- KMSpico.exe (PID: 3196)
- wmpnscfg.exe (PID: 3632)
- MEGAsync.exe (PID: 3864)
- KMSpico.exe (PID: 3732)
- KMSpico.tmp (PID: 3592)
- KMSpico.tmp (PID: 3992)
- KMSpico.exe (PID: 3676)
Checks proxy server information
- wscript.exe (PID: 3564)
- MEGAsync.exe (PID: 3864)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3632)
- MEGAsync.exe (PID: 3864)
Manual execution by a user
- wmpnscfg.exe (PID: 3632)
Create files in a temporary directory
- MEGAsync.exe (PID: 3864)
- KMSpico.exe (PID: 3732)
- KMSpico.exe (PID: 3676)
- KMSpico.tmp (PID: 3592)
Creates files or folders in the user directory
- KMSpico.exe (PID: 3196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 00:14:34+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 73728 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | 114688 |
| EntryPoint: | 0x2e400 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.6.0 |
| ProductVersionNumber: | 2.0.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | PortableApps.com |
| LegalCopyright: | John T. Haller |
| LegalTrademarks: | Firefox is a Registered Trademark of The Mozilla Foundation. PortableApps.com is a Registered Trademark of Rare Ideas, LLC. |
| OriginalFileName: | FirefoxPortable.exe |
| Comments: | Allows Firefox to be run from a removable drive. For additional details, visit PortableApps.com/FirefoxPortable |
| FileVersion: | 2.0.6.0 |
| ProductName: | Mozilla Firefox, Portable Edition |
| ProductVersion: | 2.0.6.0 |
| InternalName: | Mozilla Firefox, Portable Edition |
| FileDescription: | Mozilla Firefox, Portable Edition |
| Created: | 7z SFX Constructor v4.5.0.0 (http://usbtor.ru/viewtopic.php?t=798) |
| Builder: | host 16:44:29 04/11/2023 |
Total processes
47
Monitored processes
8
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
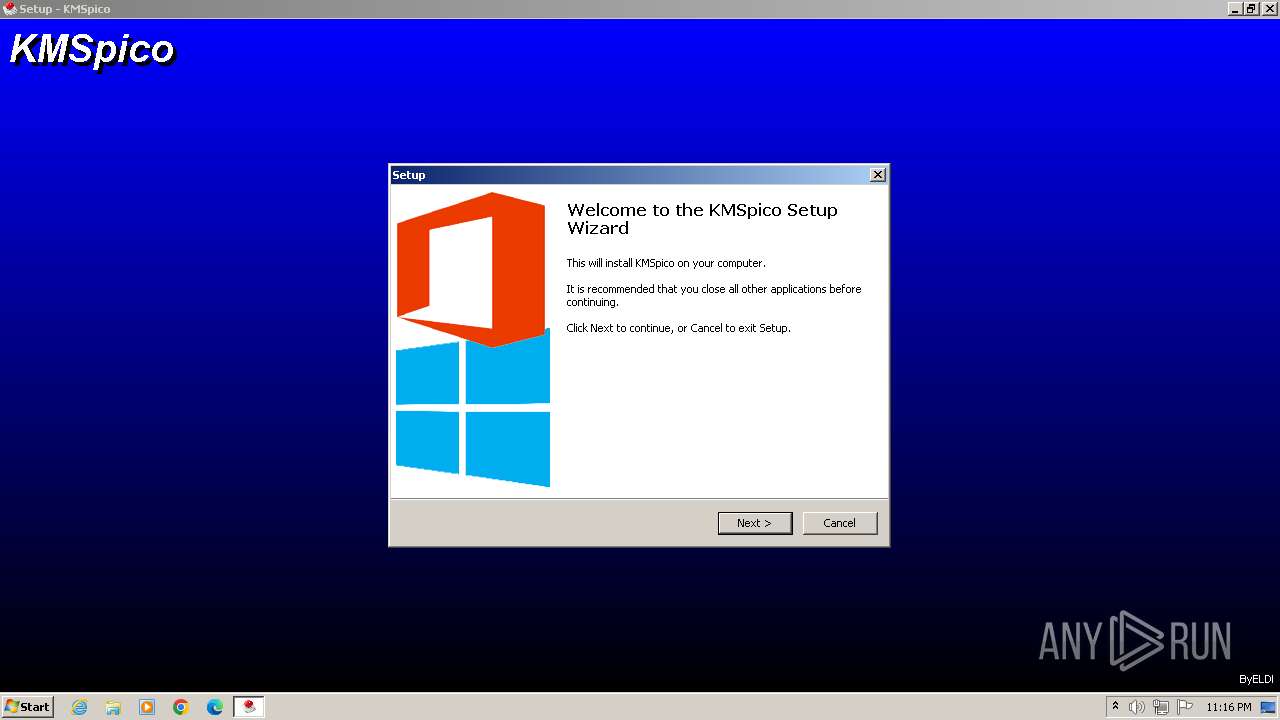
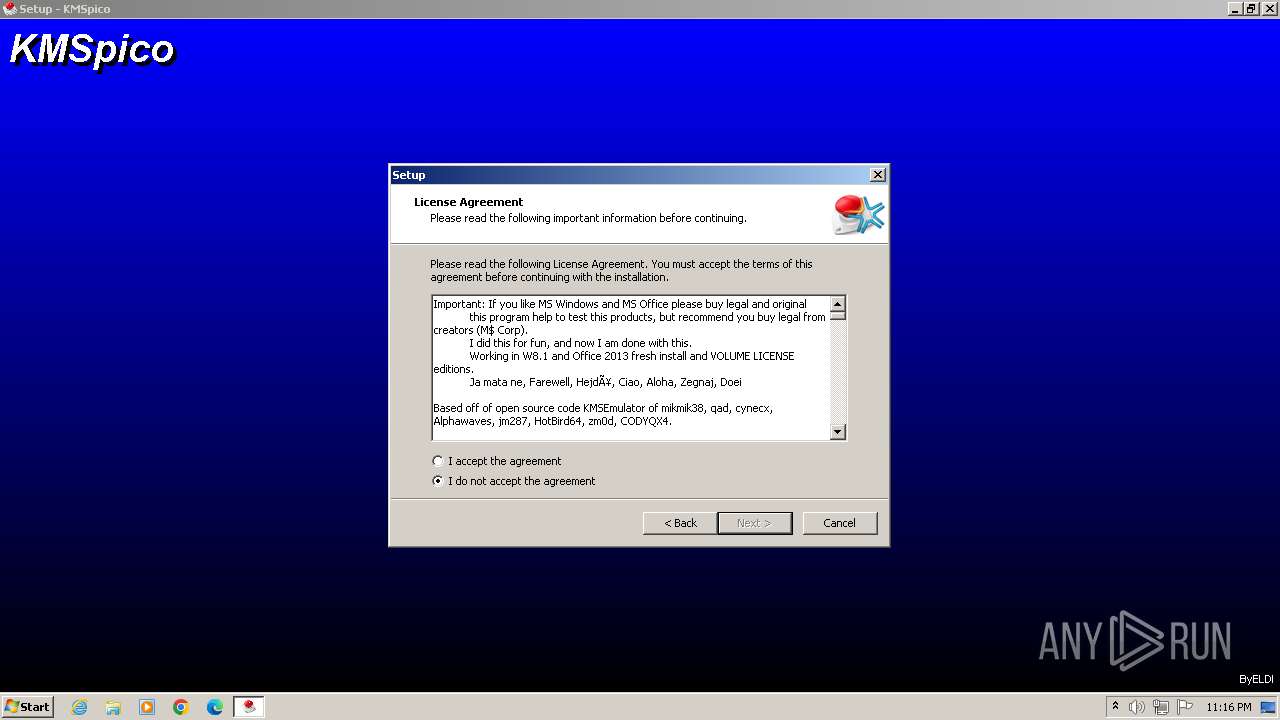
| 3196 | "C:\Users\admin\AppData\Local\Temp\KMSpico.exe" | C:\Users\admin\AppData\Local\Temp\KMSpico.exe | — | explorer.exe | |||||||||||
User: admin Company: PortableApps.com Integrity Level: MEDIUM Description: Mozilla Firefox, Portable Edition Exit code: 0 Version: 2.0.6.0 Modules
| |||||||||||||||
| 3564 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\kmspico\script.vbs" | C:\Windows\System32\wscript.exe | KMSpico.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3592 | "C:\Users\admin\AppData\Local\Temp\is-0SF9O.tmp\KMSpico.tmp" /SL5="$701F4,2952592,69120,C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe" /SPAWNWND=$F012C /NOTIFYWND=$70180 | C:\Users\admin\AppData\Local\Temp\is-0SF9O.tmp\KMSpico.tmp | — | KMSpico.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe" /SPAWNWND=$F012C /NOTIFYWND=$70180 | C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe | KMSpico.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 3732 | "C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe" | C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe | — | KMSpico.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 3864 | "C:\Users\admin\AppData\Roaming\kmspico\MEGAsync.exe" | C:\Users\admin\AppData\Roaming\kmspico\MEGAsync.exe | KMSpico.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\is-QS2G5.tmp\KMSpico.tmp" /SL5="$70180,2952592,69120,C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe" | C:\Users\admin\AppData\Local\Temp\is-QS2G5.tmp\KMSpico.tmp | — | KMSpico.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
7 991
Read events
7 930
Write events
55
Delete events
6
Modification events
| (PID) Process: | (3196) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3196) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3196) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3196) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
8
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3196 | KMSpico.exe | C:\Users\admin\AppData\Roaming\kmspico\script.vbs | text | |
MD5:F36610429206BEDC68AA24297D12B226 | SHA256:7AA03510650E63EE67B84825B12DB12660569019394BD515983FA2C01208C671 | |||
| 3564 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3564 | wscript.exe | C:\Users\admin\AppData\Local\Temp\CabF3DA.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3564 | wscript.exe | C:\Users\admin\AppData\Local\Temp\TarF3DB.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 3564 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:59D6E9576C97D57BF68C63C669DC9262 | SHA256:B20EC9DCAAF46D7427735CBAFCD52366E6B4149EAEB290334CFD18EA05568748 | |||
| 3196 | KMSpico.exe | C:\Users\admin\AppData\Roaming\kmspico\KMSpico.exe | executable | |
MD5:A02164371A50C5FF9FA2870EF6E8CFA3 | SHA256:64C731ADBE1B96CB5765203B1E215093DCF268D020B299445884A4AE62ED2D3A | |||
| 3196 | KMSpico.exe | C:\Users\admin\AppData\Roaming\kmspico\MEGAsync.exe | executable | |
MD5:E0958AAC5E30978763D48D4843FBADD4 | SHA256:69E91AE384A2C5561D8D6BCBEF238BBFF64992AD4DE8B67DE39C09F8ACFF3F04 | |||
| 3564 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 3732 | KMSpico.exe | C:\Users\admin\AppData\Local\Temp\is-QS2G5.tmp\KMSpico.tmp | executable | |
MD5:1778C1F66FF205875A6435A33229AB3C | SHA256:95C06ACAC4FE4598840E5556F9613D43AA1039C52DAC64536F59E45A70F79DA6 | |||
| 3564 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:CDC2F1B97FB78BF584B2A1F16184ABF2 | SHA256:50145813B58909C629E3E29F7A50836EF230D29E32DC0ED8CBDD57F2EE09AEFE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
48
DNS requests
5
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3564 | wscript.exe | GET | 200 | 8.248.93.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6298d358b00fb574 | unknown | compressed | 4.66 Kb | unknown |
3564 | wscript.exe | GET | 200 | 8.248.93.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?701c3e5c65d0417b | unknown | compressed | 61.6 Kb | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
3864 | MEGAsync.exe | POST | 200 | 188.114.96.3:80 | http://plengreg.fun/api | unknown | text | 2 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3564 | wscript.exe | 148.251.234.93:443 | maper.info | Hetzner Online GmbH | DE | unknown |
3564 | wscript.exe | 8.248.93.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3564 | wscript.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
3864 | MEGAsync.exe | 188.114.96.3:80 | plengreg.fun | CLOUDFLARENET | NL | unknown |
3864 | MEGAsync.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
maper.info |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
plengreg.fun |
| unknown |
cdn.discordapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3564 | wscript.exe | Potential Corporate Privacy Violation | ET POLICY IP Logger Redirect Domain in SNI |
3864 | MEGAsync.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Check-In |
3864 | MEGAsync.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
3864 | MEGAsync.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Exfiltration |
3864 | MEGAsync.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Exfiltration |
1080 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
3864 | MEGAsync.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
1 ETPRO signatures available at the full report