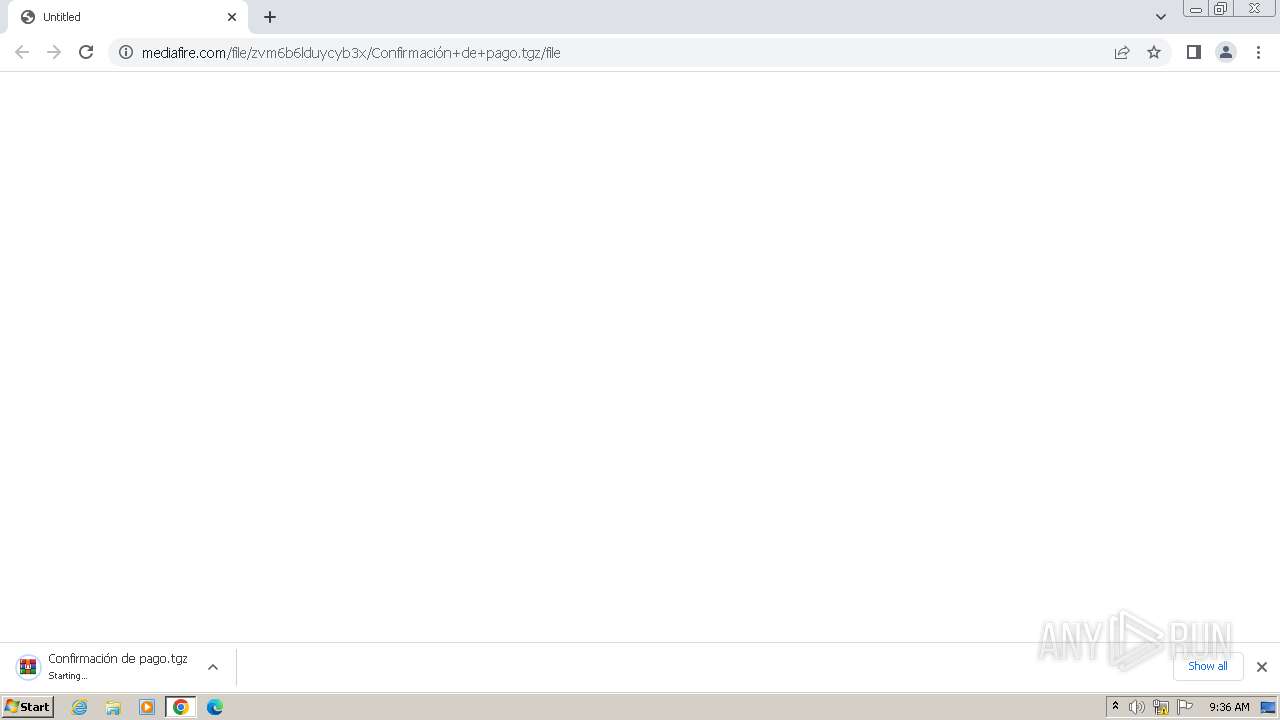
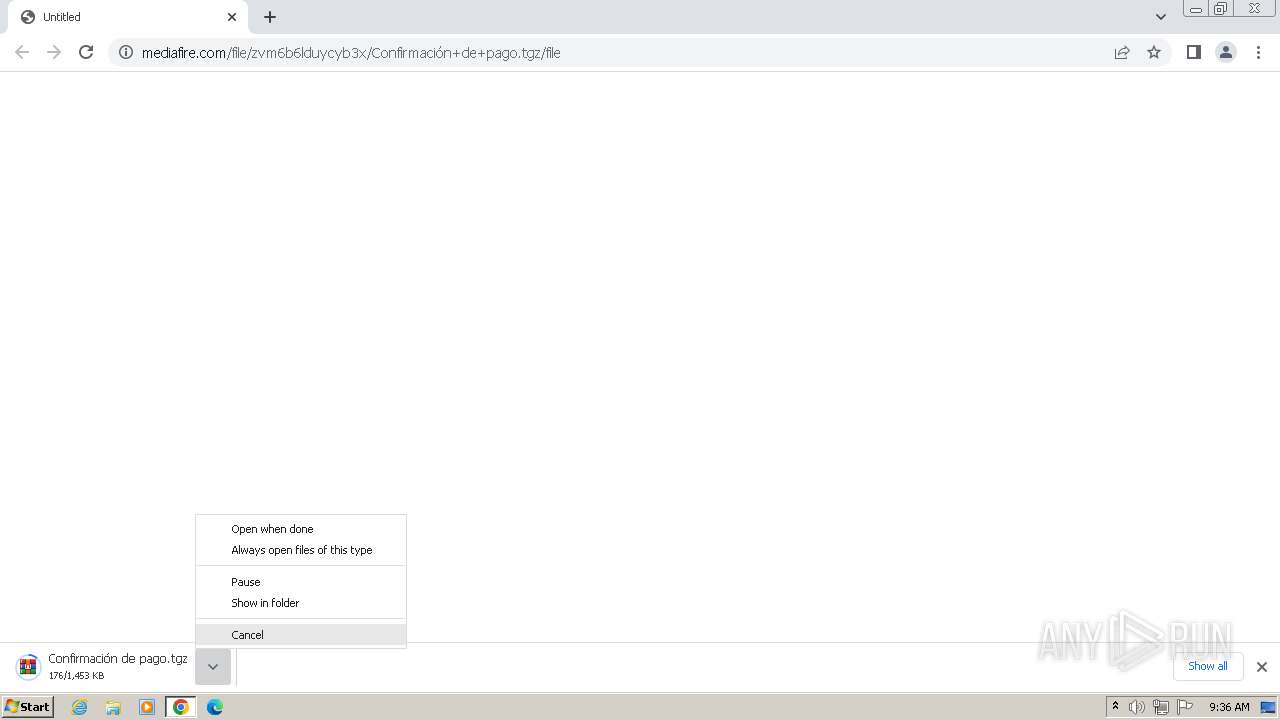
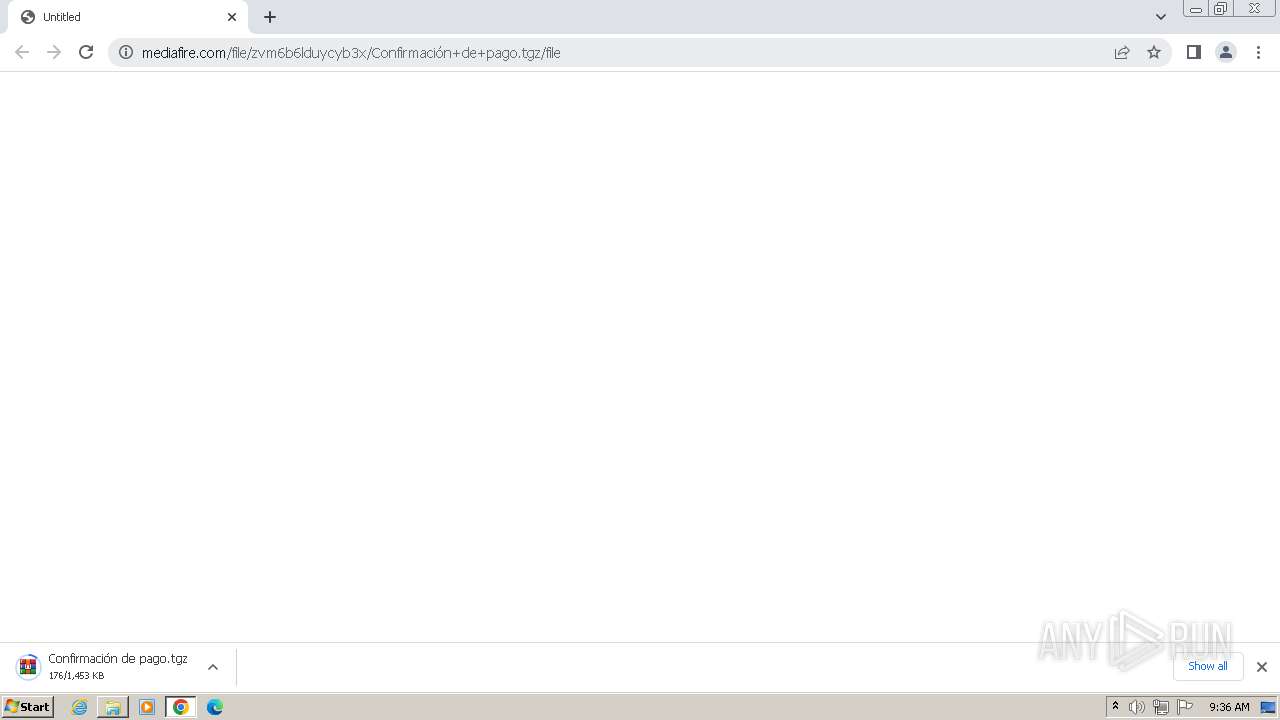
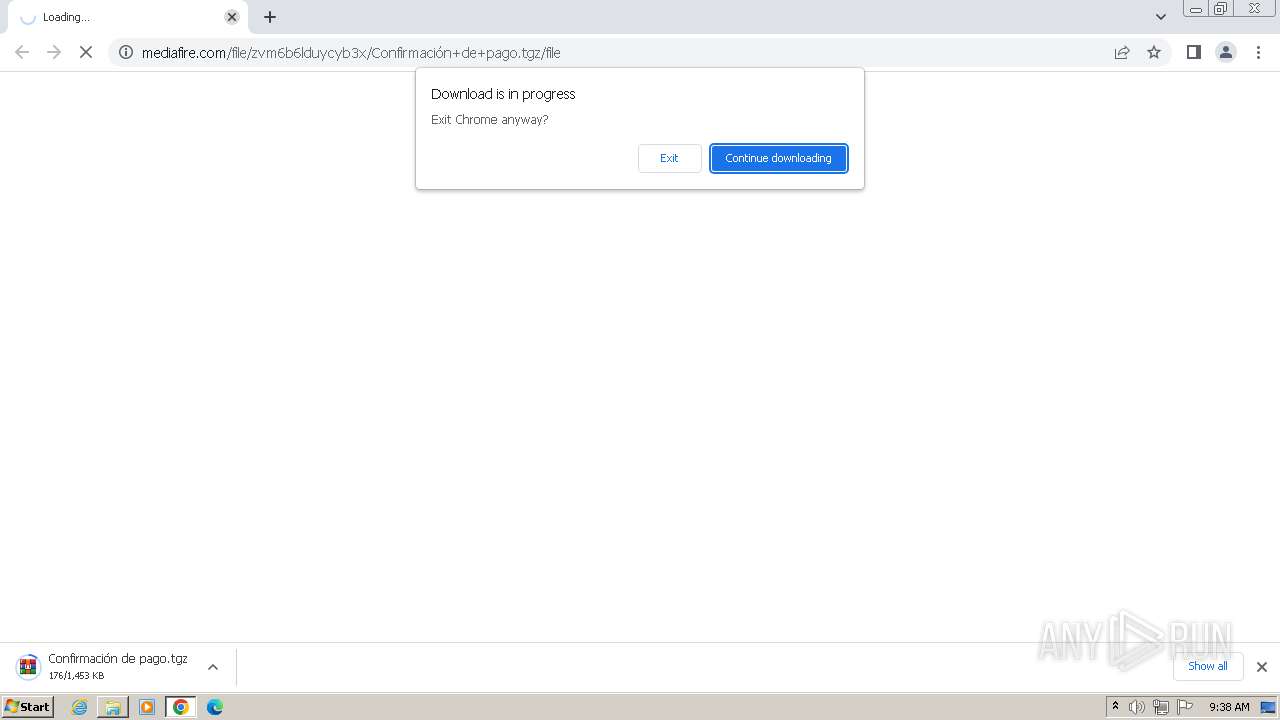
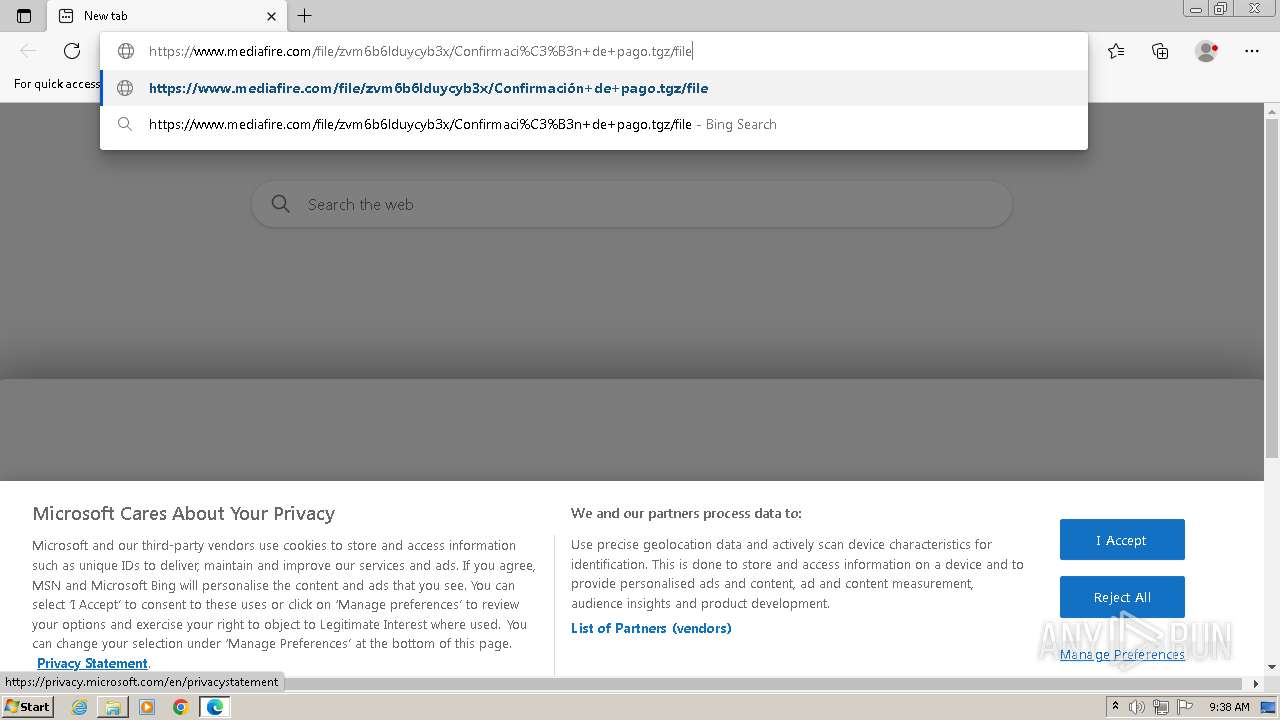
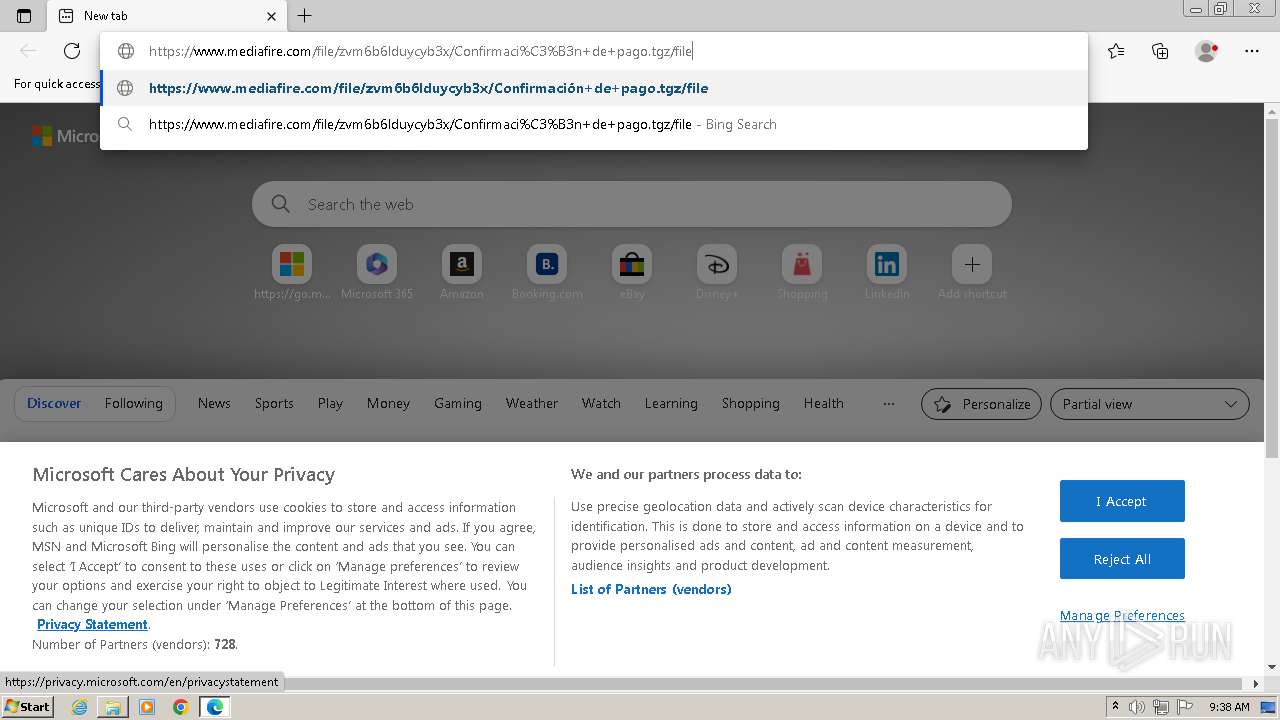
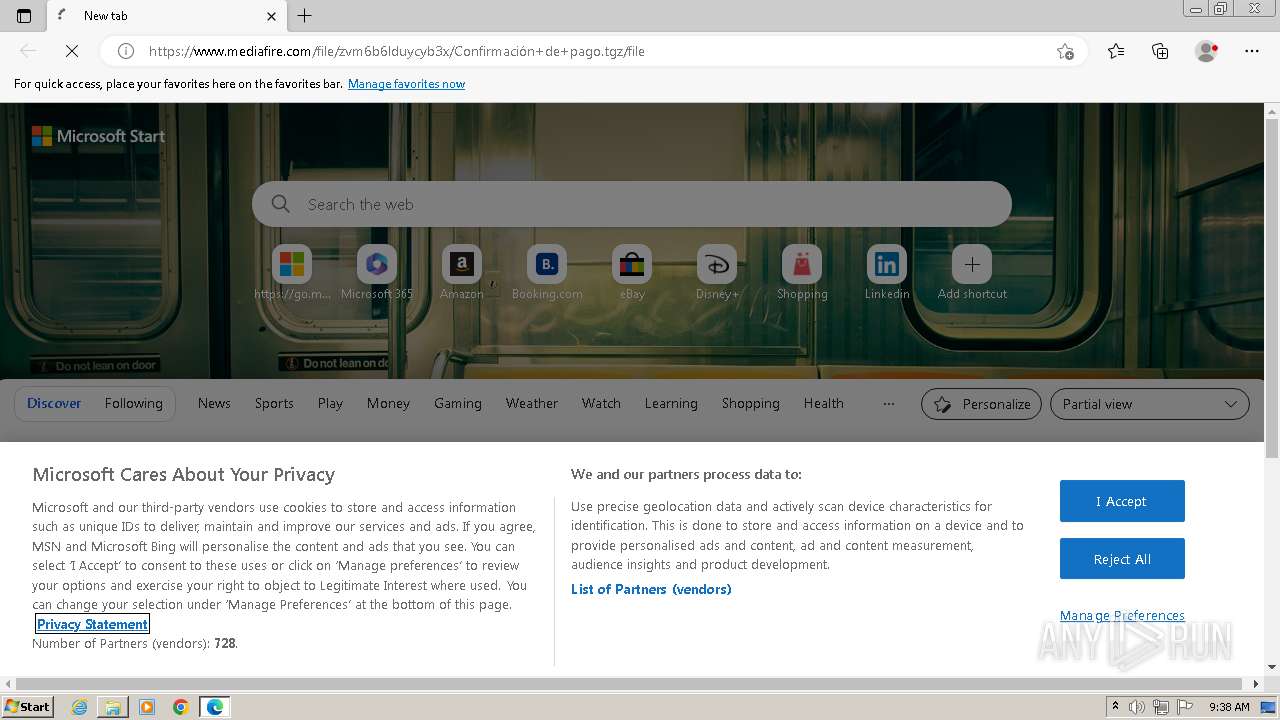
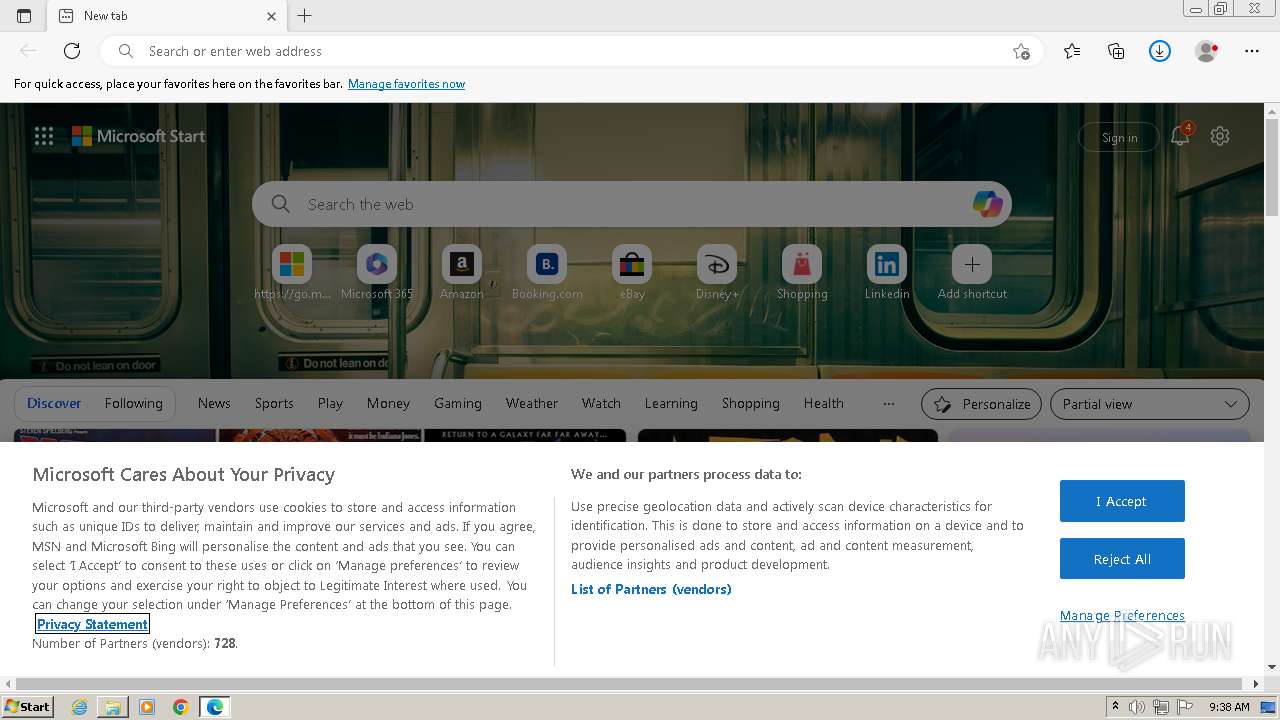
| URL: | https://www.mediafire.com/file/zvm6b6lduycyb3x/Confirmación+de+pago.tgz/file |
| Full analysis: | https://app.any.run/tasks/68b8a6df-c3de-4cc7-b6c1-8d7e2f2989ee |
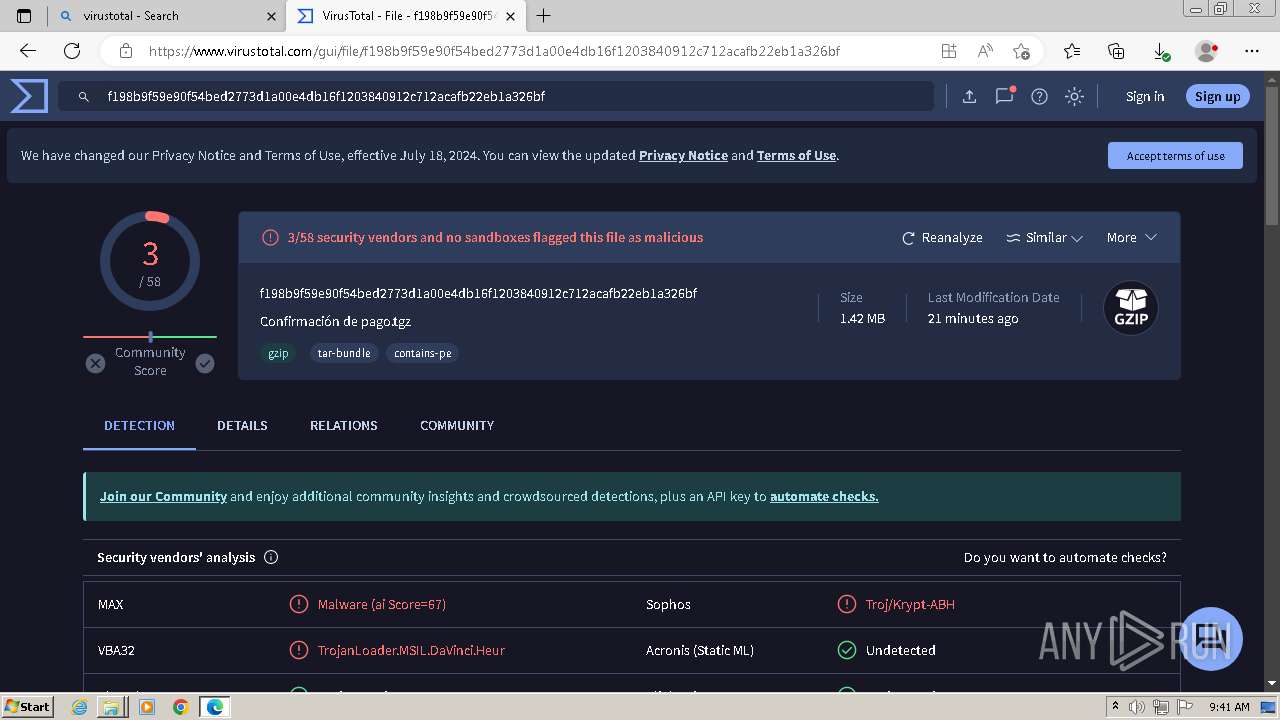
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | June 03, 2024, 08:36:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C07B192B58AE00EE485A204925936324 |
| SHA1: | 03064E41BAFFD8DA09EB5AFAC255C7C1B289B15D |
| SHA256: | 4AB1D579FA59C777DEACFEF1BCC3EC558F085BB18689E93C7029C5EC9C994465 |
| SSDEEP: | 3:N8DSLw3eGUoMw2aEPXBBXKDMO:2OLw3eGrE/BBxO |
MALICIOUS
Uses Task Scheduler to run other applications
- Confirmación de pago.exe (PID: 3688)
Actions looks like stealing of personal data
- Confirmación de pago.exe (PID: 284)
Steals credentials from Web Browsers
- Confirmación de pago.exe (PID: 284)
AGENTTESLA has been detected (YARA)
- Confirmación de pago.exe (PID: 284)
SUSPICIOUS
Reads security settings of Internet Explorer
- Confirmación de pago.exe (PID: 3688)
Application launched itself
- Confirmación de pago.exe (PID: 3688)
Accesses Microsoft Outlook profiles
- Confirmación de pago.exe (PID: 284)
Reads the Internet Settings
- Confirmación de pago.exe (PID: 284)
- Confirmación de pago.exe (PID: 3688)
Reads settings of System Certificates
- Confirmación de pago.exe (PID: 284)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Confirmación de pago.exe (PID: 284)
INFO
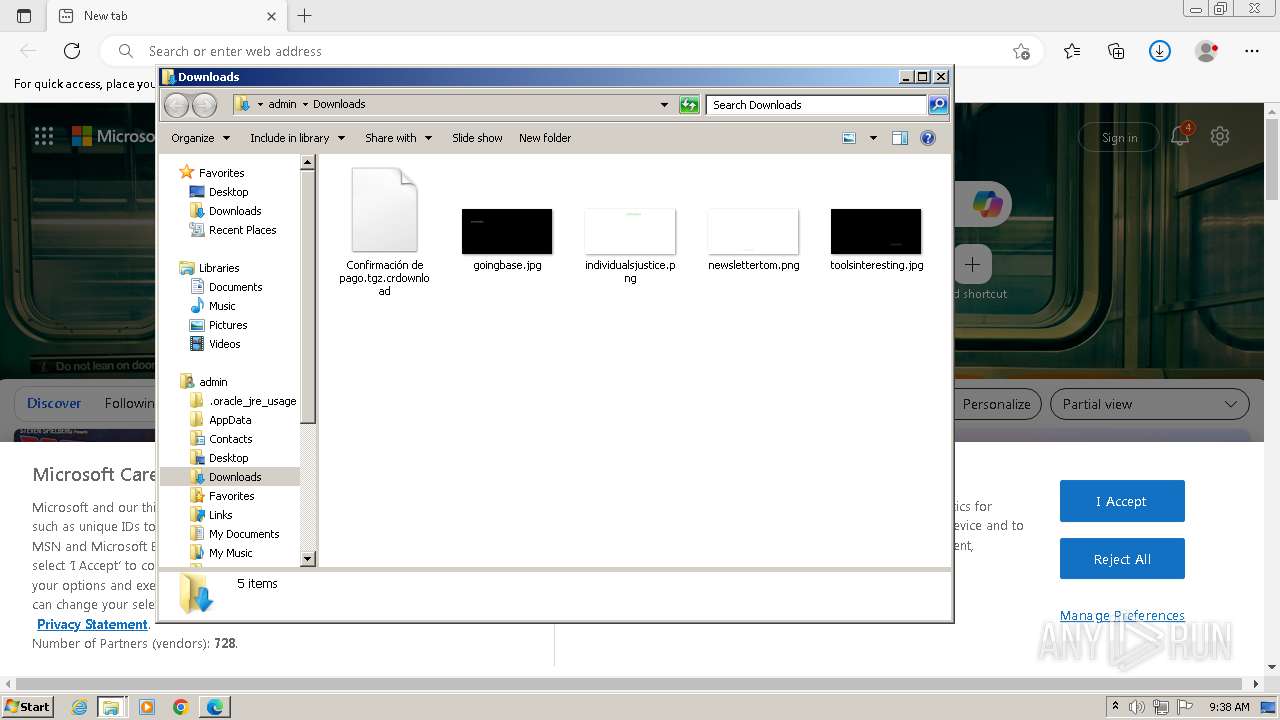
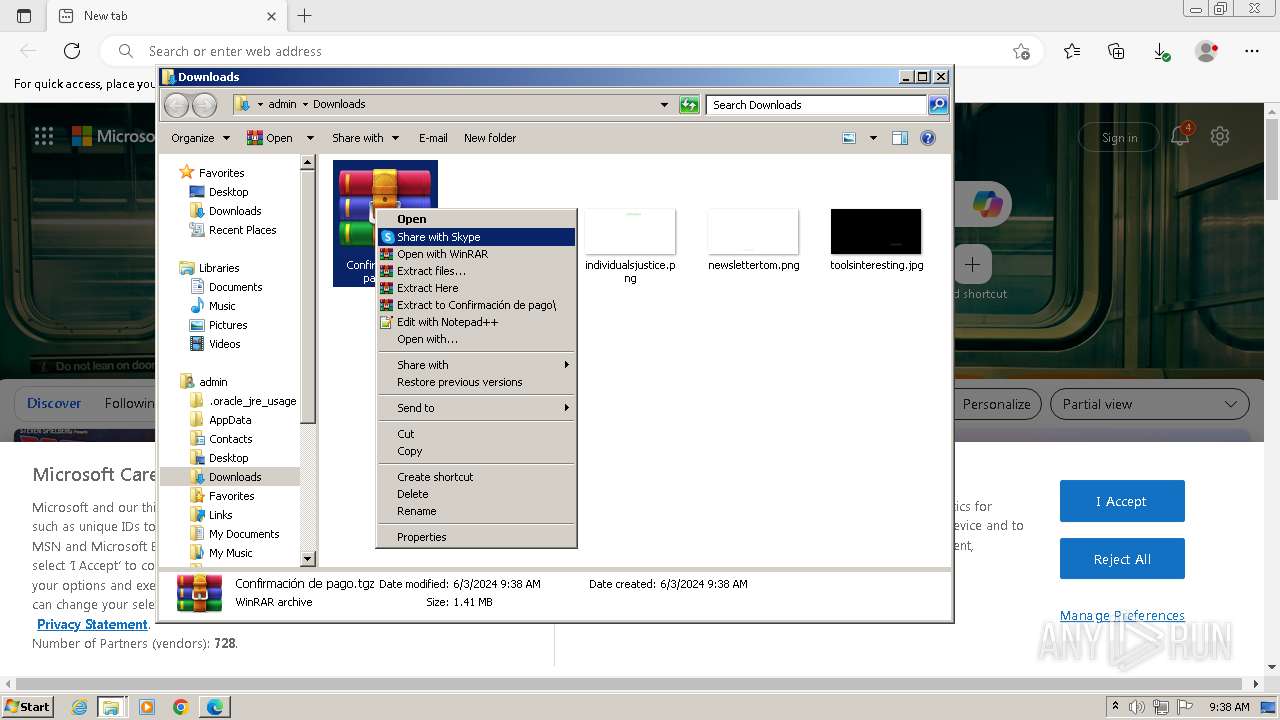
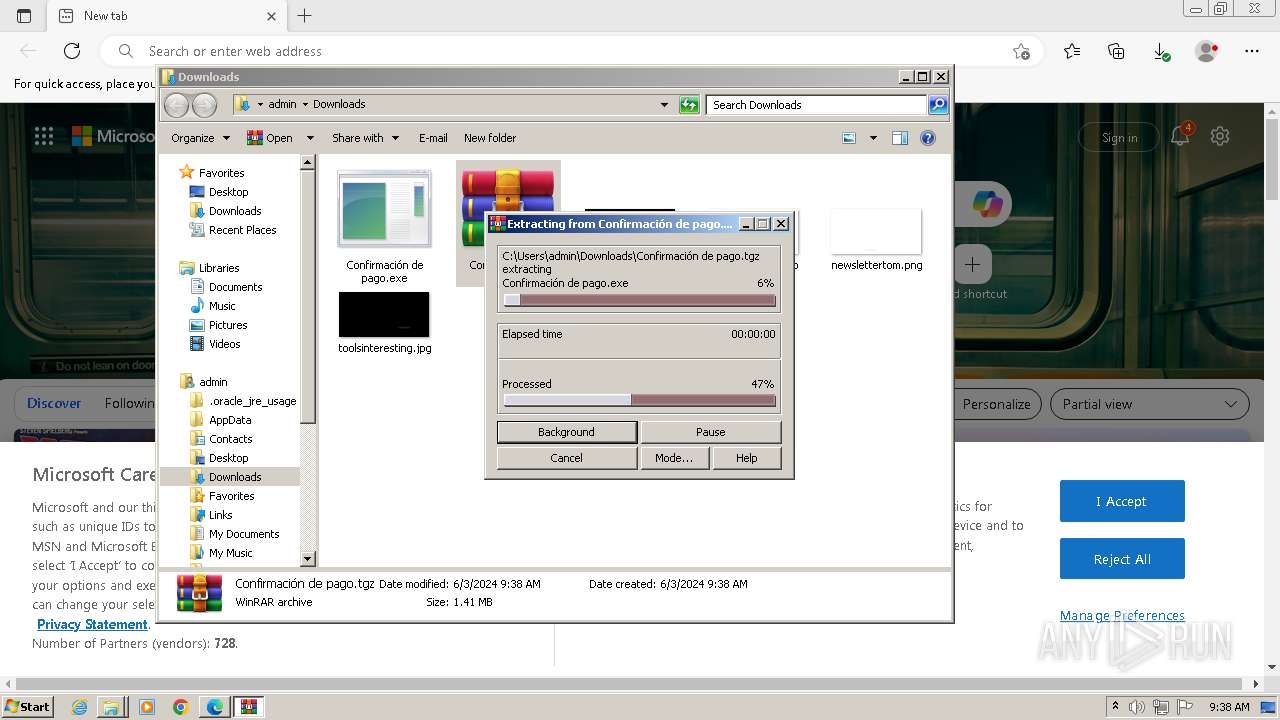
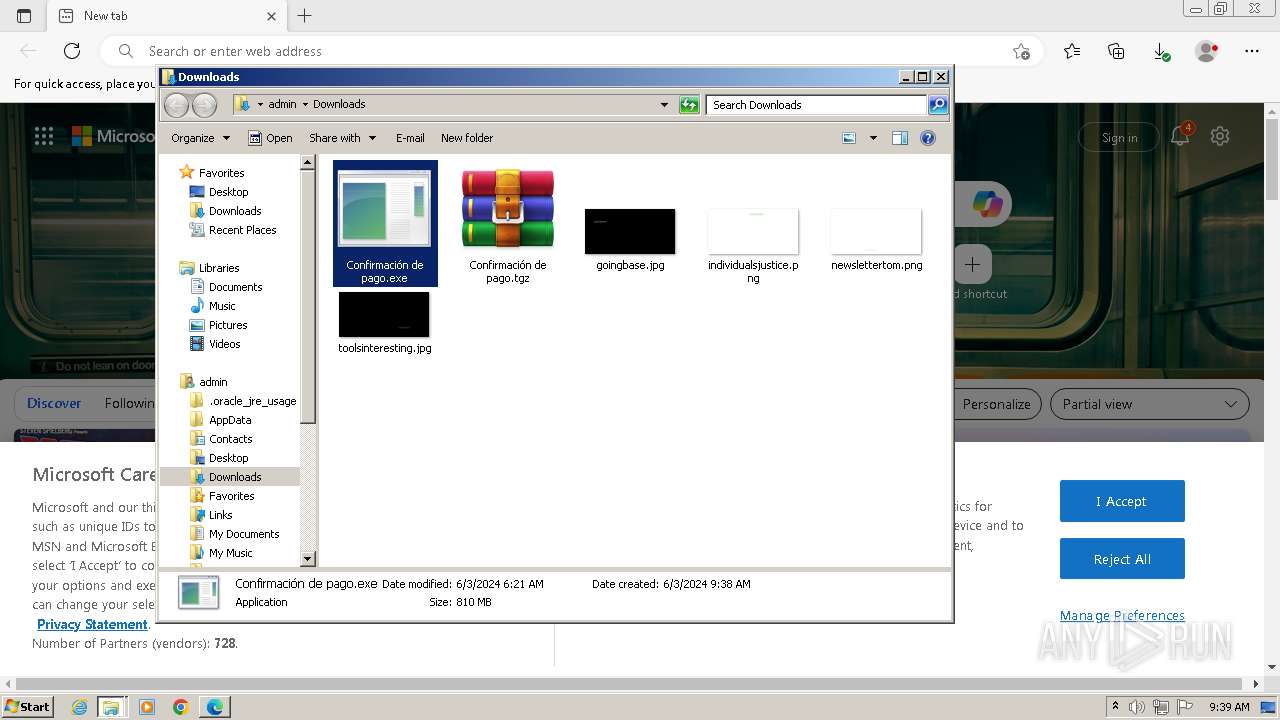
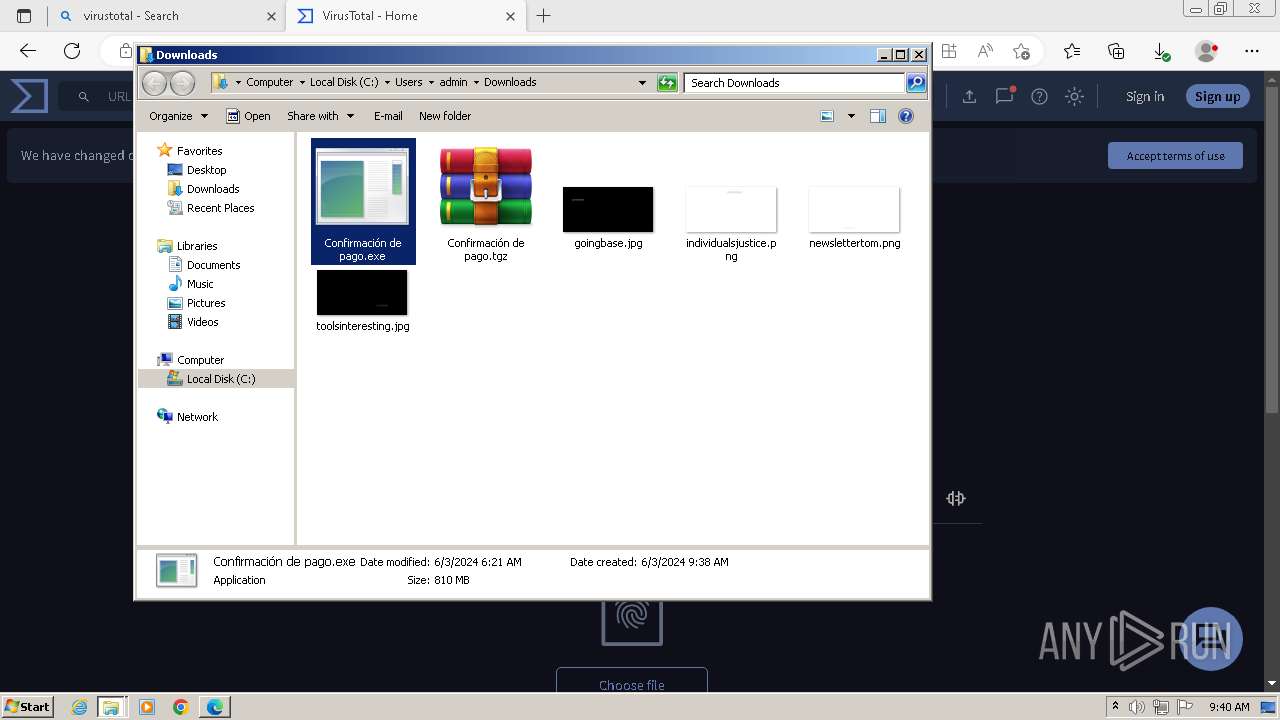
Manual execution by a user
- wmpnscfg.exe (PID: 1884)
- msedge.exe (PID: 2836)
- Confirmación de pago.exe (PID: 3688)
- WinRAR.exe (PID: 3372)
- Confirmación de pago.exe (PID: 1488)
Checks supported languages
- wmpnscfg.exe (PID: 1884)
- Confirmación de pago.exe (PID: 1488)
- Confirmación de pago.exe (PID: 284)
- Confirmación de pago.exe (PID: 3688)
Reads the machine GUID from the registry
- Confirmación de pago.exe (PID: 1488)
- Confirmación de pago.exe (PID: 3688)
- Confirmación de pago.exe (PID: 284)
Creates files or folders in the user directory
- Confirmación de pago.exe (PID: 3688)
Reads the computer name
- wmpnscfg.exe (PID: 1884)
- Confirmación de pago.exe (PID: 284)
- Confirmación de pago.exe (PID: 3688)
- Confirmación de pago.exe (PID: 1488)
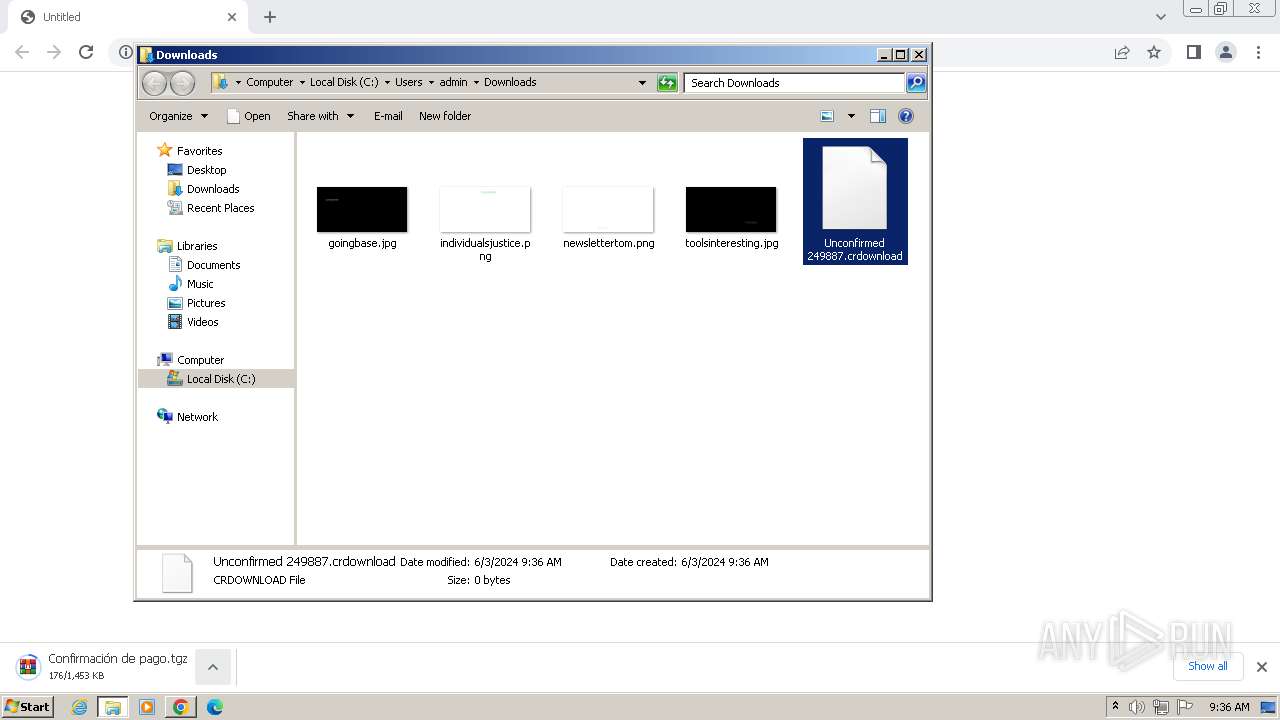
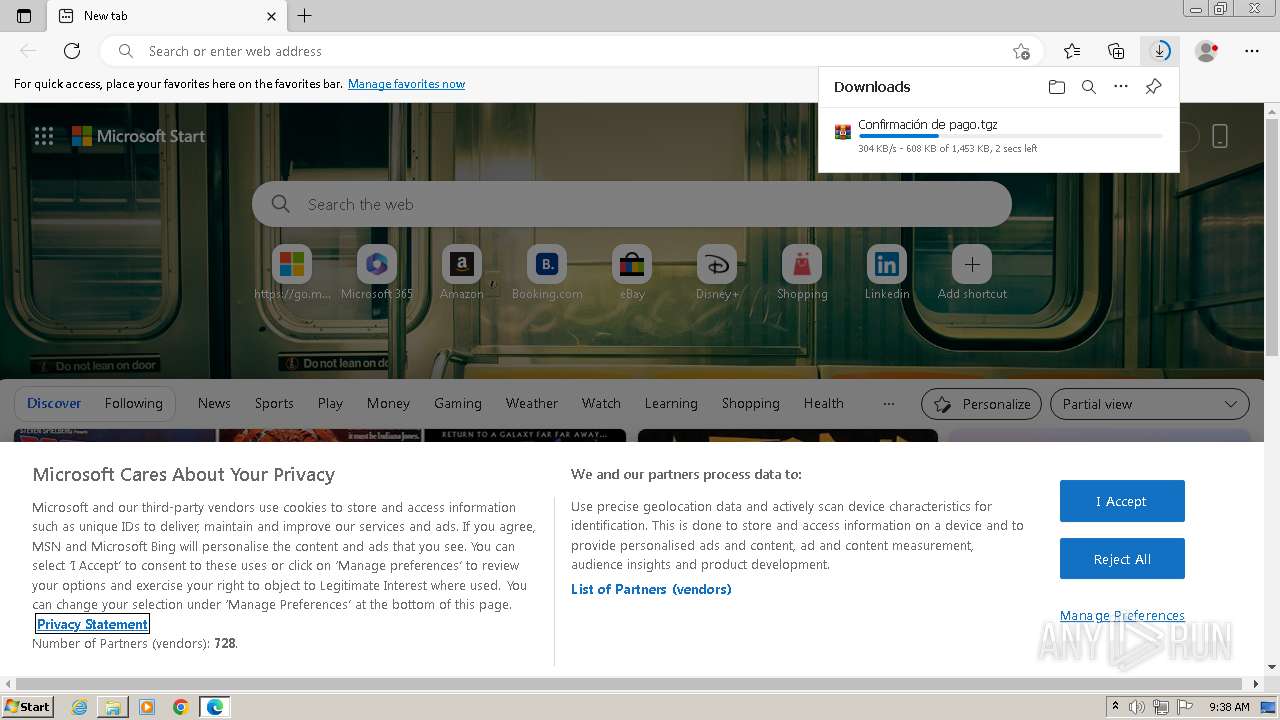
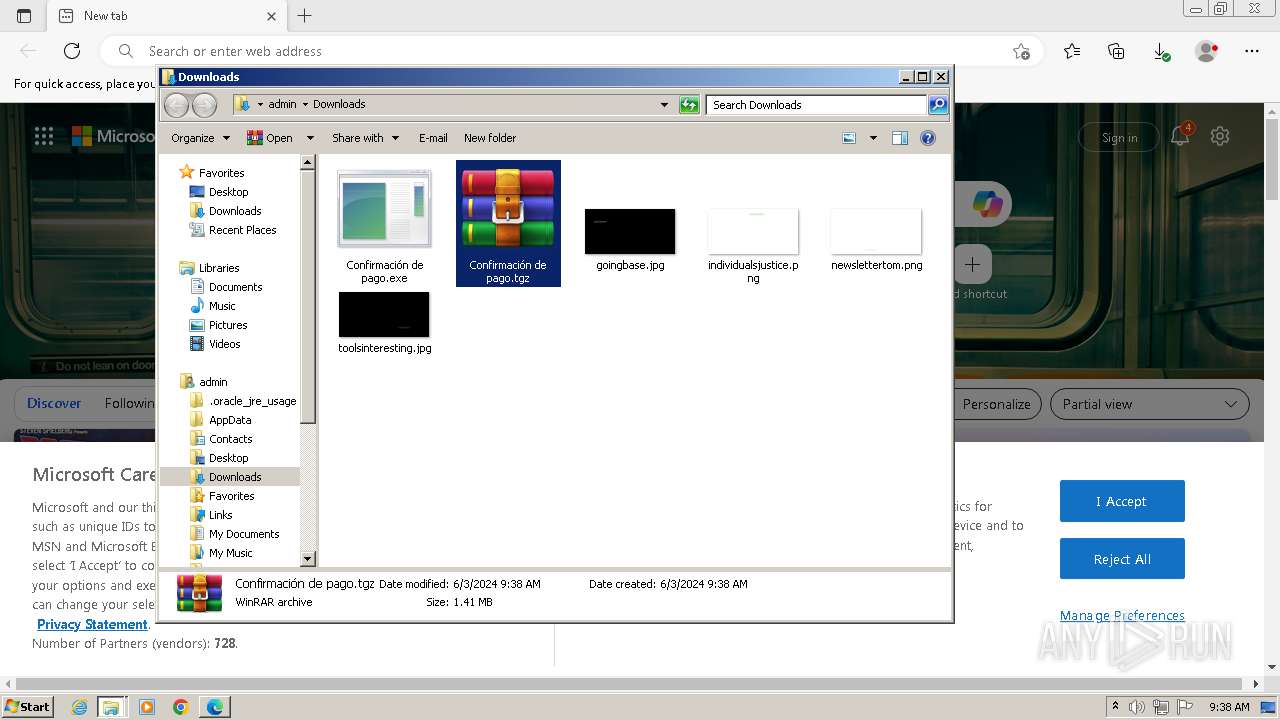
The process uses the downloaded file
- msedge.exe (PID: 1804)
- WinRAR.exe (PID: 3372)
Application launched itself
- chrome.exe (PID: 3964)
- msedge.exe (PID: 2836)
Create files in a temporary directory
- Confirmación de pago.exe (PID: 3688)
Reads Environment values
- Confirmación de pago.exe (PID: 284)
Disables trace logs
- Confirmación de pago.exe (PID: 284)
Reads the software policy settings
- Confirmación de pago.exe (PID: 284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
89
Monitored processes
49
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Users\admin\Downloads\Confirmación de pago.exe" | C:\Users\admin\Downloads\Confirmación de pago.exe | Confirmación de pago.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Energy Runtime Version: 1.0.0.0 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1028 --field-trial-handle=1152,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3868 --field-trial-handle=1212,i,4936420814594950134,14769468633220949907,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4452 --field-trial-handle=1212,i,4936420814594950134,14769468633220949907,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1504 --field-trial-handle=1152,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\Downloads\Confirmación de pago.exe" | C:\Users\admin\Downloads\Confirmación de pago.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Energy Runtime Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2356 --field-trial-handle=1212,i,4936420814594950134,14769468633220949907,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=3832 --field-trial-handle=1212,i,4936420814594950134,14769468633220949907,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2028 --field-trial-handle=1152,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2016 --field-trial-handle=1152,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
25 992
Read events
25 812
Write events
166
Delete events
14
Modification events
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
20
Suspicious files
667
Text files
95
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1042f6.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:7CC8F2B9E0FB4C25D7DEC651196EF439 | SHA256:D9D73DECB3BA242315B2D4DCB84D5CDF2B568FA632F548DB2857B27D6144C11A | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10447d.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF10495f.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\Downloads\Unconfirmed 249887.crdownload | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:23E954DCE0FB0ECF46A96FF4ACBE66F4 | SHA256:68F3B7AA8367C46273C296103B799A112DE3B70DE873C16F7166496CA31C3DDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
93
DNS requests
125
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac77gi5ikvorj4i2qq7bej7ghrmq_975/efniojlnjndmcbiieegkicadnoecjjef_975_all_gbfm3z5xnhiwzkug3wnwxeesvy.crx3 | unknown | — | — | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2108 | chrome.exe | 104.16.113.74:443 | www.mediafire.com | CLOUDFLARENET | — | unknown |
3964 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2108 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
3964 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2108 | chrome.exe | 199.91.155.106:443 | download2365.mediafire.com | MEDIAFIRE | US | unknown |
2108 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
download2365.mediafire.com |
| unknown |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2108 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2108 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2108 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2108 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
3028 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
— | — | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
— | — | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
— | — | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |