| File name: | 3763496cf1fcb3c839e591a8b61f69bdb1947517 |
| Full analysis: | https://app.any.run/tasks/d4589b75-728b-4294-848a-e221dd4c1c3b |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | October 09, 2019, 13:43:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 79BD98B276E4D843D656E19FB837A36A |
| SHA1: | 3763496CF1FCB3C839E591A8B61F69BDB1947517 |
| SHA256: | 498DE1787D18E17C4CC900CF975F721E6275E0AA34669F2D3271F7666F1F583E |
| SSDEEP: | 12288:bn9ulRHCBFXZN7rnWGBccrzDEVBnQTw2Yx/jST:bnXtZNeGBHsBnr2YxS |
MALICIOUS
Runs app for hidden code execution
- microsoft.exe (PID: 2380)
Loads dropped or rewritten executable
- dism.exe (PID: 3020)
AVEMARIA was detected
- microsoft.exe (PID: 612)
- microsoft.exe (PID: 2380)
Connects to CnC server
- microsoft.exe (PID: 612)
- microsoft.exe (PID: 2380)
Changes the autorun value in the registry
- 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe (PID: 2068)
SUSPICIOUS
Starts itself from another location
- 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe (PID: 2068)
Application launched itself
- 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe (PID: 3388)
- microsoft.exe (PID: 2316)
- microsoft.exe (PID: 2868)
Creates files in the user directory
- 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe (PID: 2068)
Executable content was dropped or overwritten
- cmd.exe (PID: 3032)
- DllHost.exe (PID: 2528)
- 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe (PID: 2068)
Executed via COM
- DllHost.exe (PID: 2528)
Starts CMD.EXE for commands execution
- microsoft.exe (PID: 2380)
Reads the machine GUID from the registry
- microsoft.exe (PID: 612)
- microsoft.exe (PID: 2380)
INFO
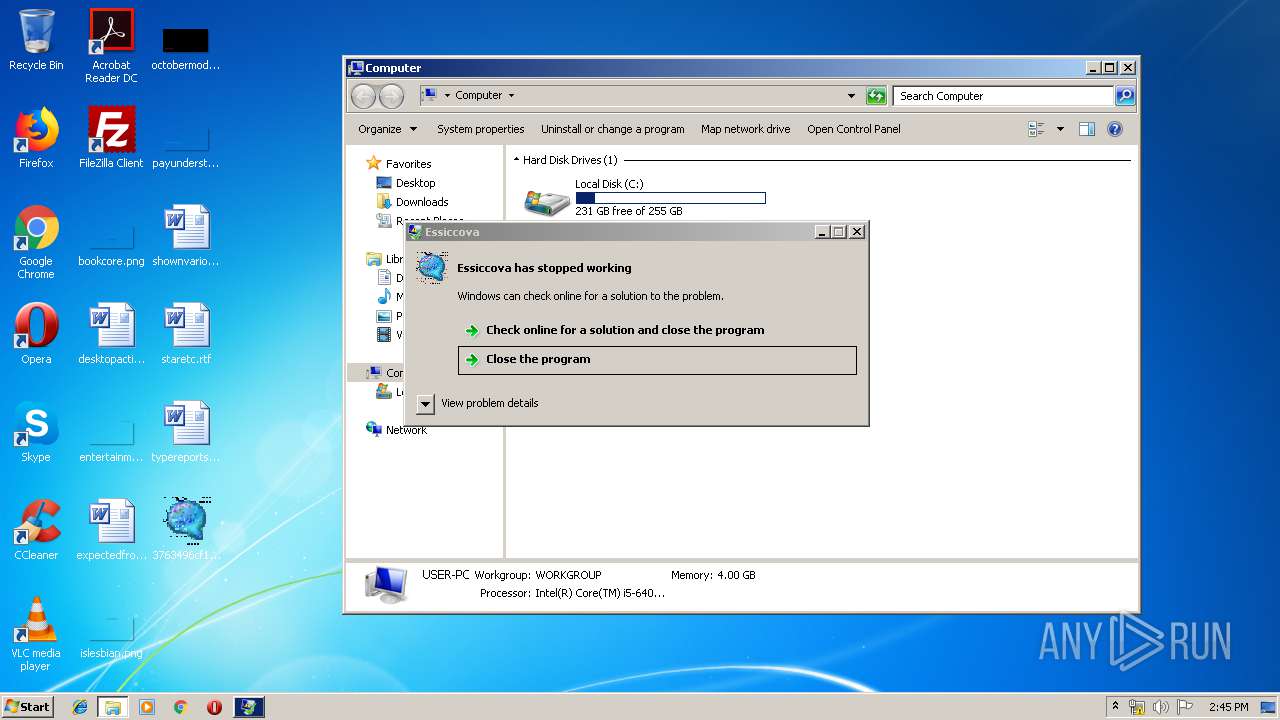
Application was crashed
- microsoft.exe (PID: 2380)
- microsoft.exe (PID: 612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:01:13 12:27:39+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 585728 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1348 |
| OSVersion: | 4 |
| ImageVersion: | 1.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.0.9 |
| ProductVersionNumber: | 1.2.0.9 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Essiccova |
| FileVersion: | 1.02.0009 |
| ProductVersion: | 1.02.0009 |
| InternalName: | Gasns |
| OriginalFileName: | Gasns.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2004 11:27:39 |
| Detected languages: |
|
| ProductName: | Essiccova |
| FileVersion: | 1.02.0009 |
| ProductVersion: | 1.02.0009 |
| InternalName: | Gasns |
| OriginalFilename: | Gasns.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Jan-2004 11:27:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008E6D4 | 0x0008F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57235 |
.data | 0x00090000 | 0x00001170 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00092000 | 0x00001296 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.76784 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.22618 | 484 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 5.98516 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 6.1089 | 1736 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
54
Monitored processes
11
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Users\admin\AppData\Roaming\microsoft.exe" | C:\Users\admin\AppData\Roaming\microsoft.exe | microsoft.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Version: 1.02.0009 Modules
| |||||||||||||||
| 1748 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\Desktop\3763496cf1fcb3c839e591a8b61f69bdb1947517.exe" | C:\Users\admin\Desktop\3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.02.0009 Modules
| |||||||||||||||
| 2212 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Roaming\microsoft.exe" | C:\Users\admin\AppData\Roaming\microsoft.exe | — | dism.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.02.0009 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Roaming\microsoft.exe" | C:\Users\admin\AppData\Roaming\microsoft.exe | microsoft.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.02.0009 Modules
| |||||||||||||||
| 2528 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Users\admin\AppData\Roaming\microsoft.exe" | C:\Users\admin\AppData\Roaming\microsoft.exe | — | 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.02.0009 Modules
| |||||||||||||||
| 3020 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | microsoft.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
483
Read events
450
Write events
33
Delete events
0
Modification events
| (PID) Process: | (2068) 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (2068) 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (2068) 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\T1WRVMPRSA |
| Operation: | write | Name: | inst |
Value: CFFB3A6F36BF7154969A026B1501B58D5E3D9D5CBC3B515235F3F1329928068EE4548A06FE93ACFAD102C4F4A4A194FA3600BF22E238556A103BB7BF4E32AF9C5E0334ADF11CB11EFDA06597A6554A80CC0BDBDBC2693E52A9EC | |||
| (PID) Process: | (2068) 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | windows |
Value: C:\Users\admin\AppData\Roaming\microsoft.exe | |||
| (PID) Process: | (2380) microsoft.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (2380) microsoft.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (2380) microsoft.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\AppData\Roaming\microsoft.exe | |||
| (PID) Process: | (2380) microsoft.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\microsoft_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2380) microsoft.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\microsoft_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2380) microsoft.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\microsoft_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
3
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | 3763496cf1fcb3c839e591a8b61f69bdb1947517.exe | C:\Users\admin\AppData\Roaming\microsoft.exe | executable | |
MD5:— | SHA256:— | |||
| 3032 | cmd.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 1748 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 2528 | DllHost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 3032 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ellocnak.xml | xml | |
MD5:427EB7374887305B72F5C552837C9036 | SHA256:B3F421780A49CBE680A317259D4DF9CE1D0CDACA3020B4DF0DC18CC01D68CCBB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
5
Threats
21
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2380 | microsoft.exe | 79.134.225.10:2888 | — | Andreas Fink trading as Fink Telecom Services | CH | malicious |
612 | microsoft.exe | 79.134.225.10:2888 | — | Andreas Fink trading as Fink Telecom Services | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sun-clear.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2380 | microsoft.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
2380 | microsoft.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
612 | microsoft.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
612 | microsoft.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
612 | microsoft.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
612 | microsoft.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
612 | microsoft.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
612 | microsoft.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
612 | microsoft.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
612 | microsoft.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |