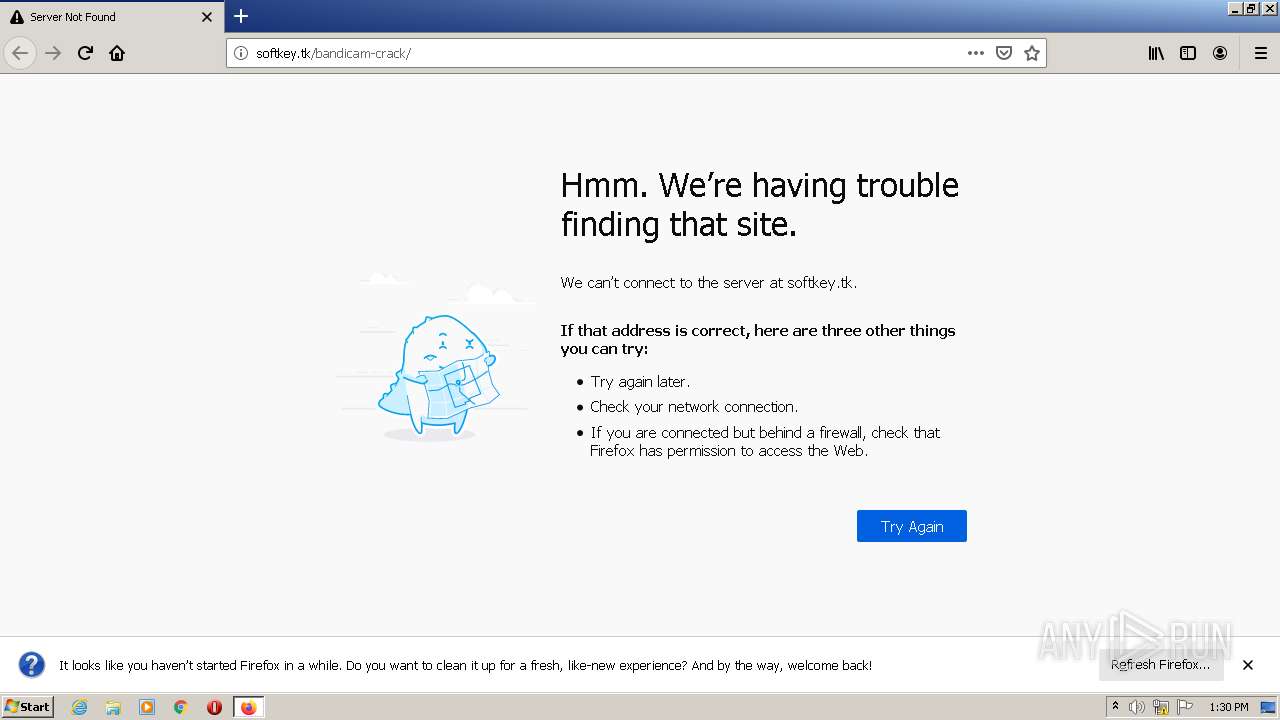
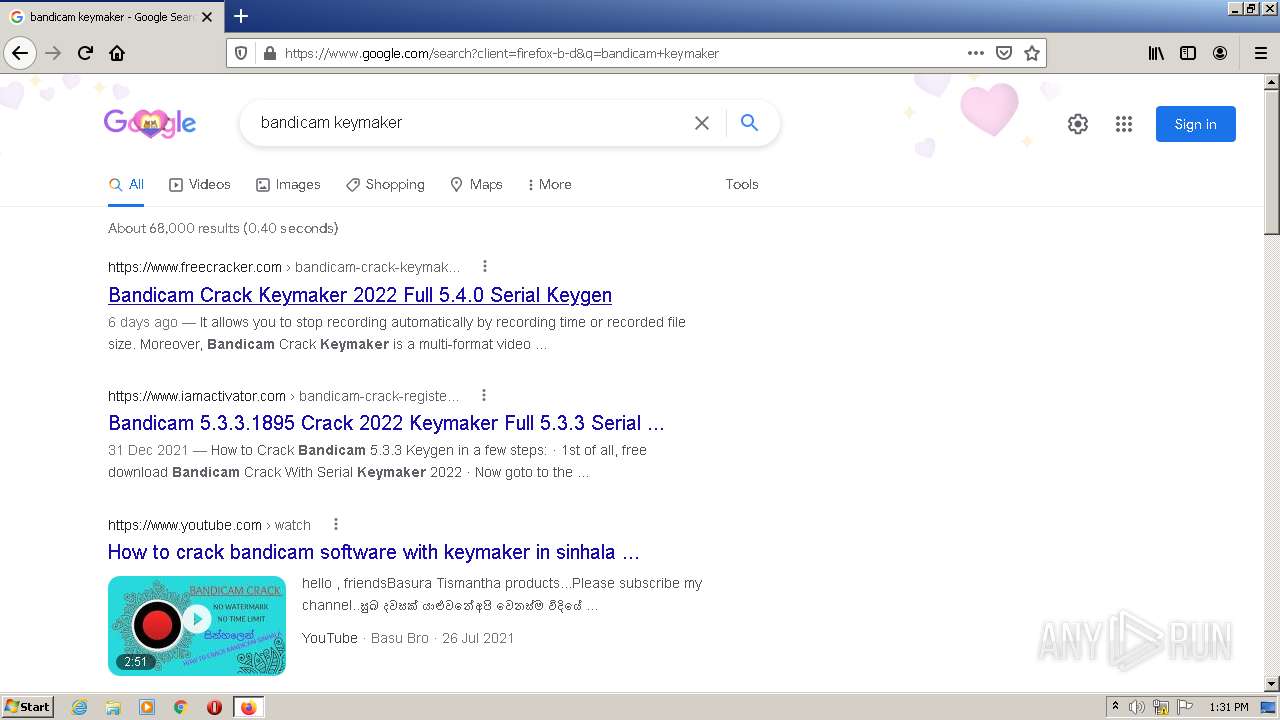
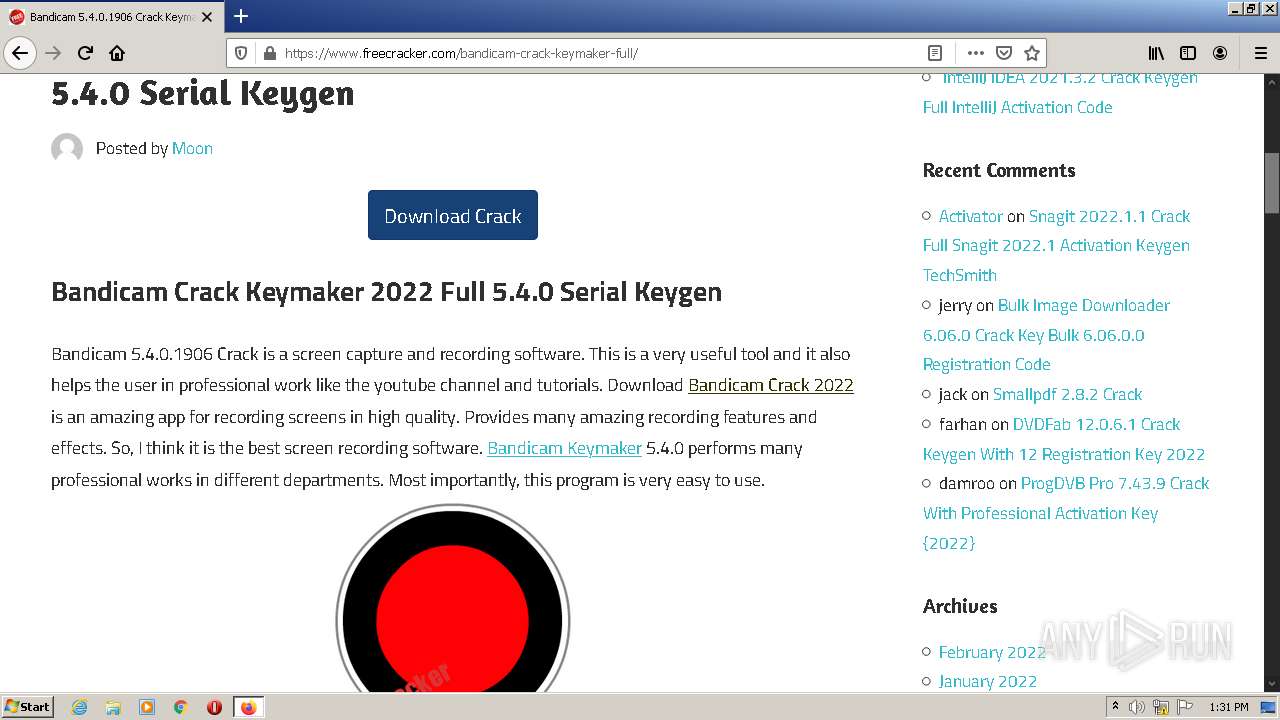
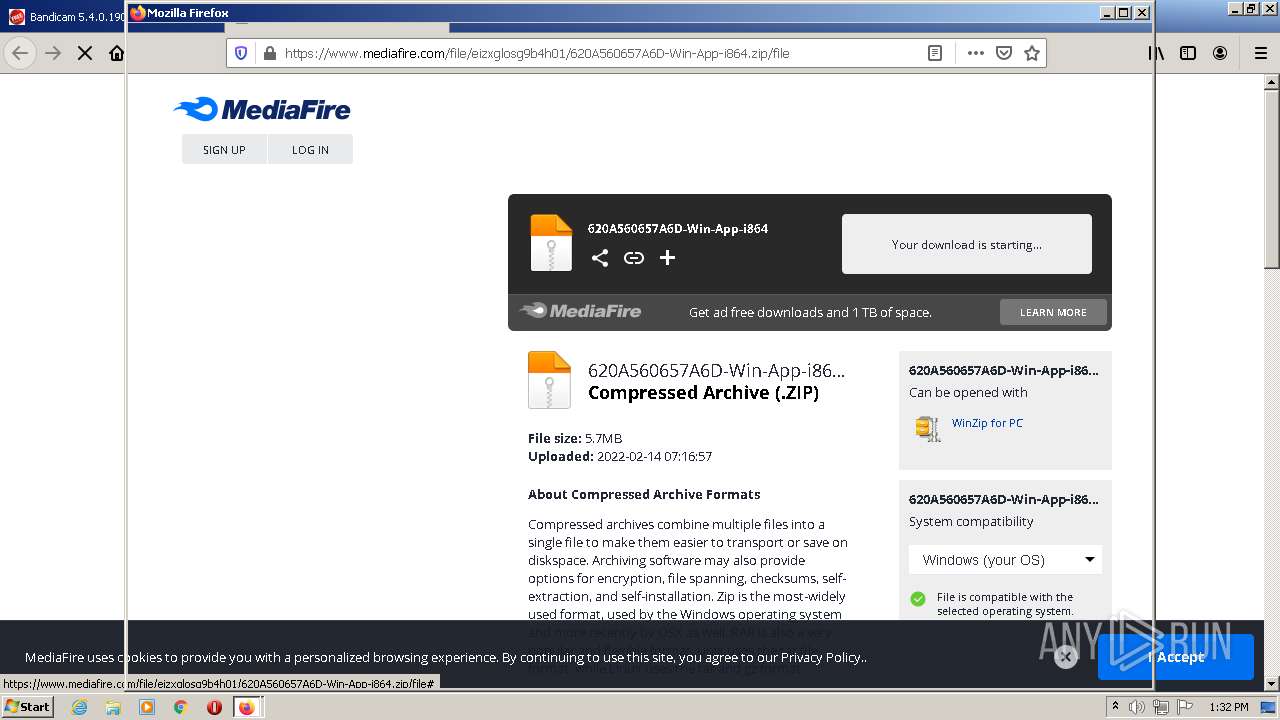
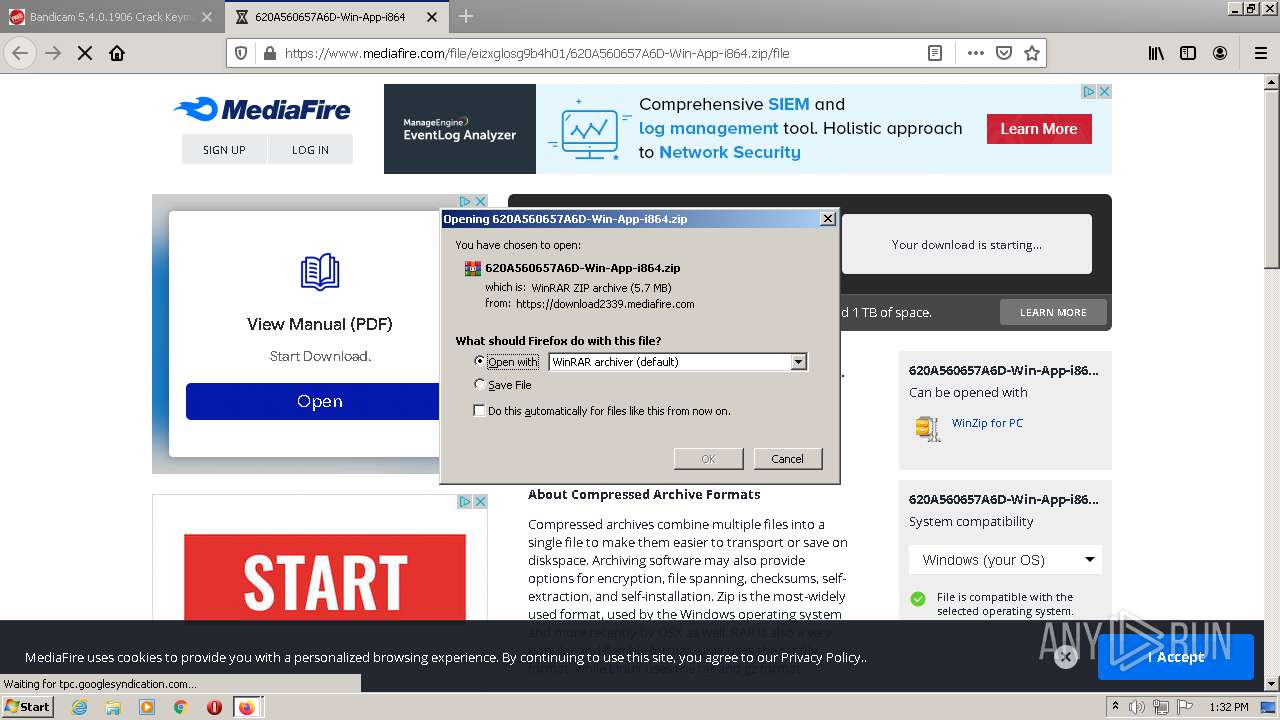
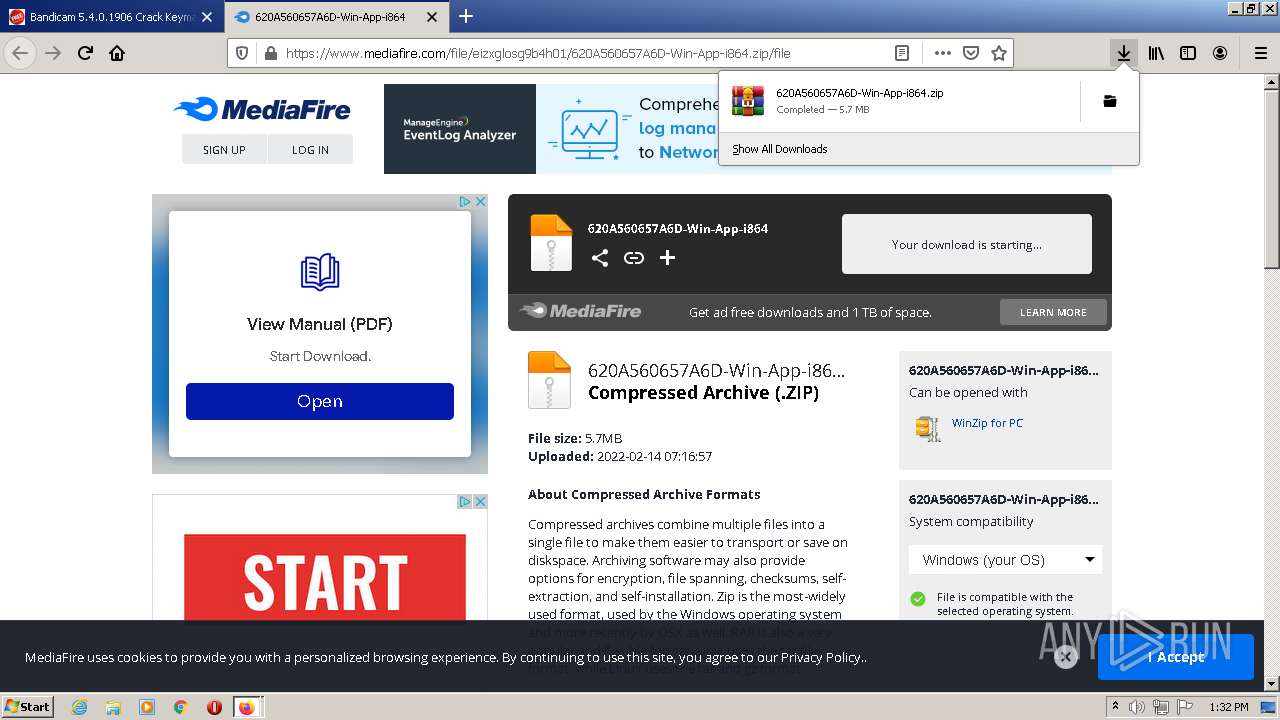
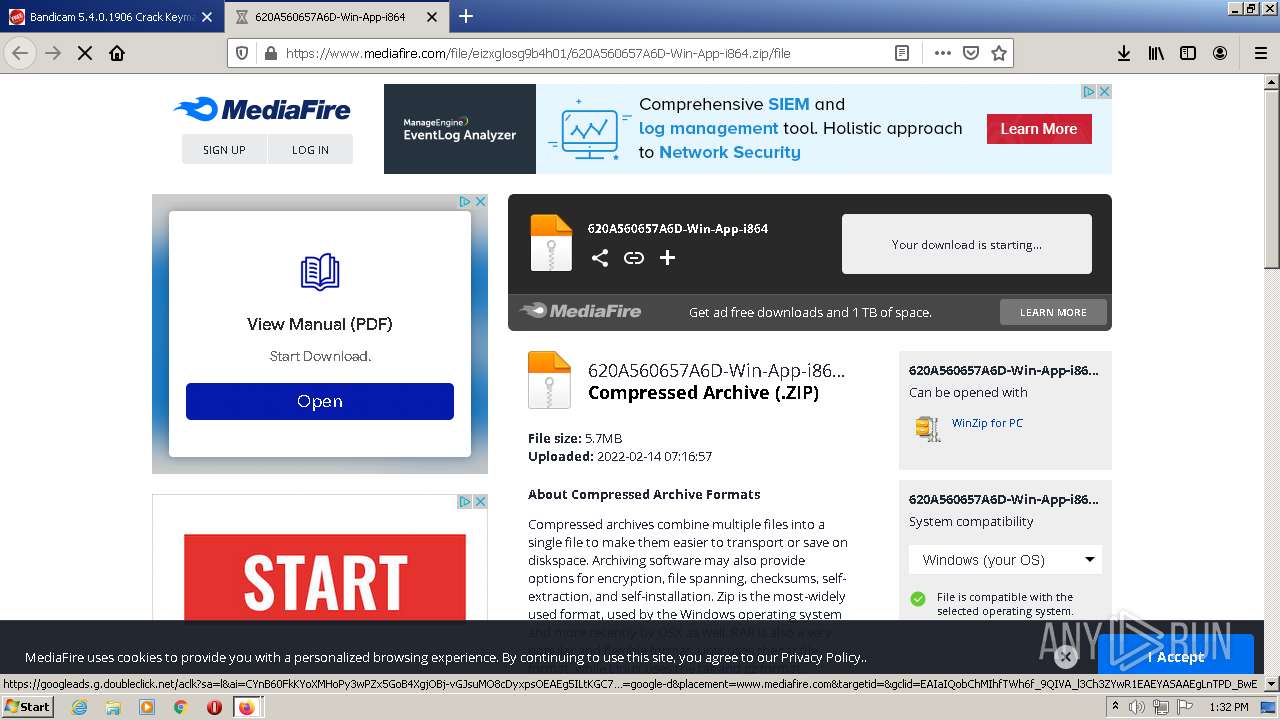
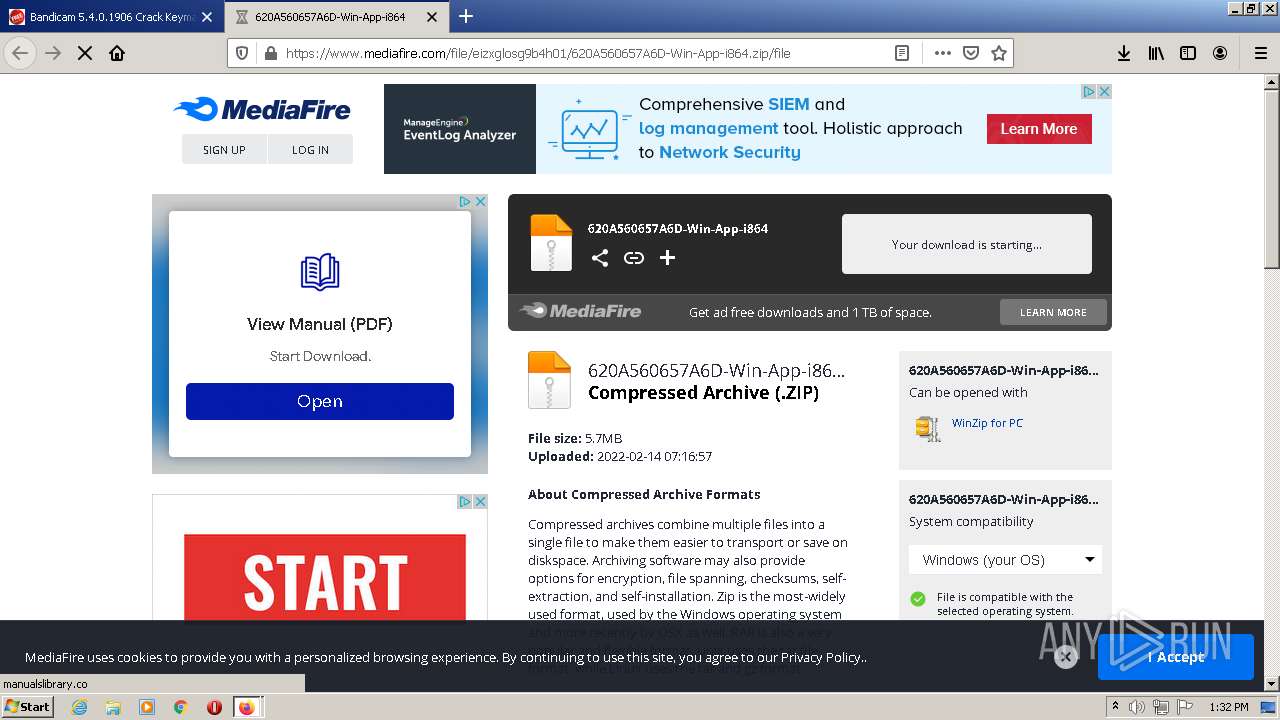
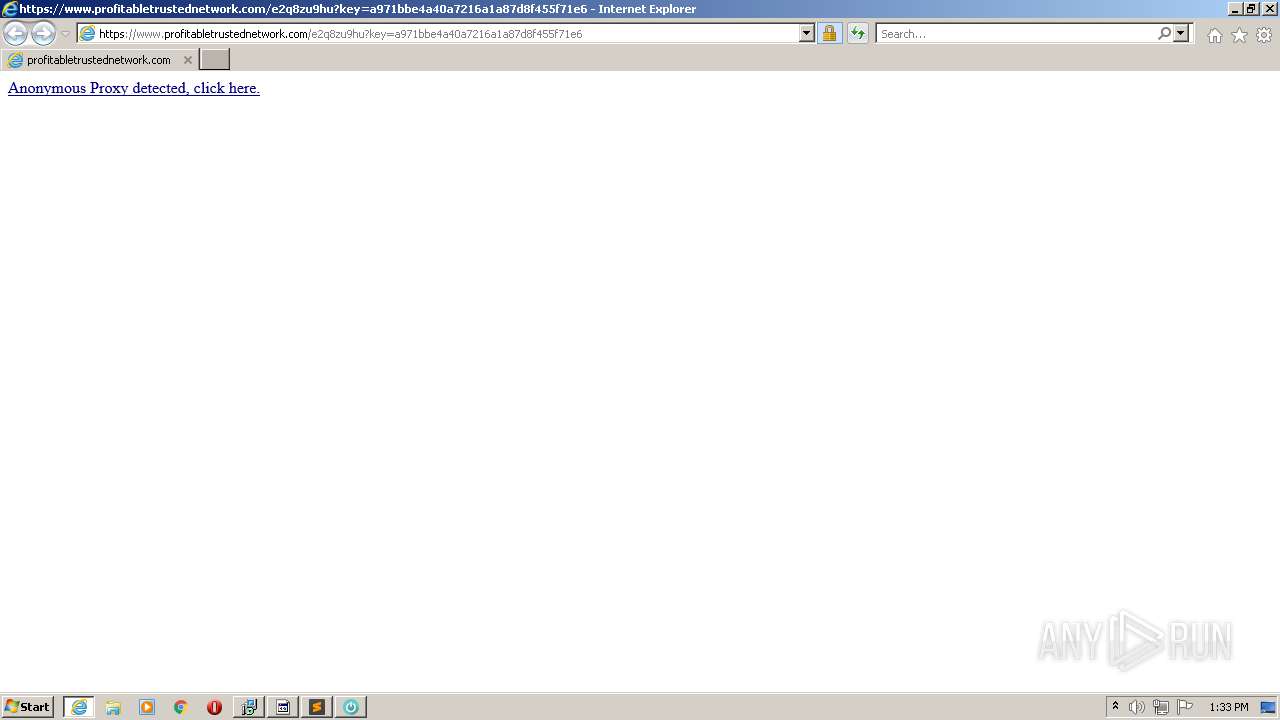
| URL: | http://softkey.tk/bandicam-crack/ |
| Full analysis: | https://app.any.run/tasks/da194c83-3b2a-470b-928f-a129ea596e7b |
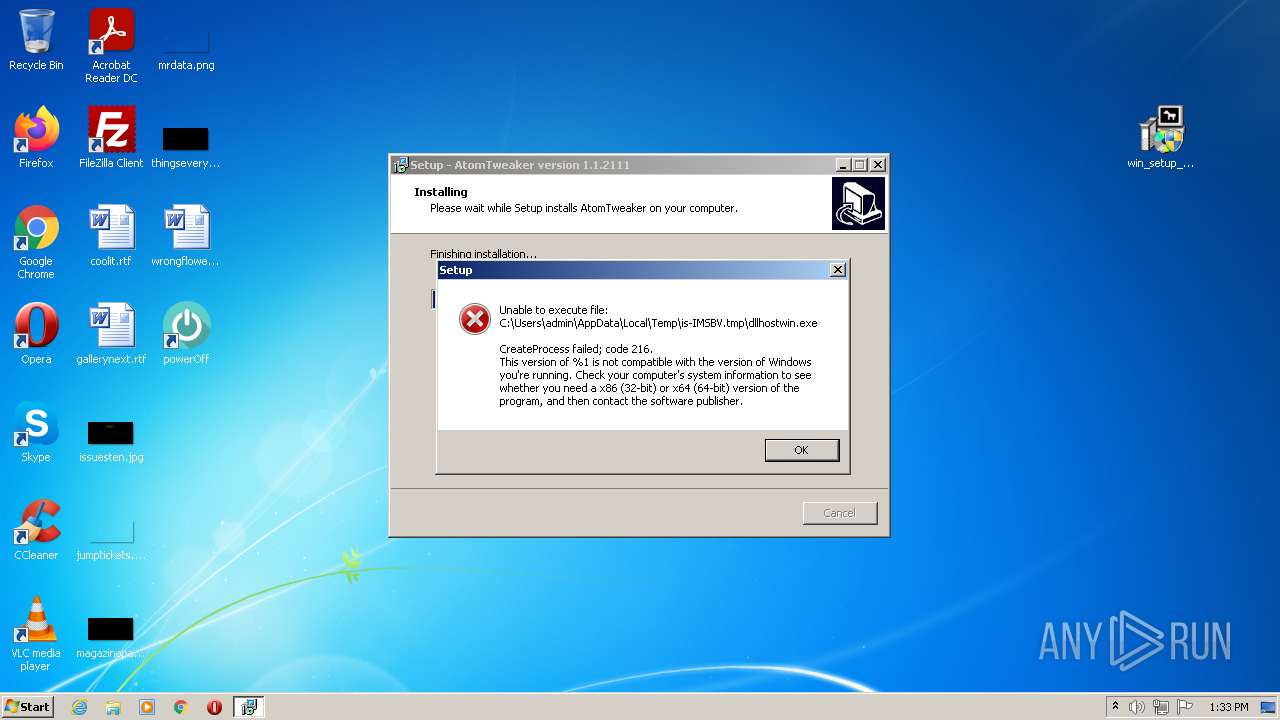
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | February 14, 2022, 13:30:29 |
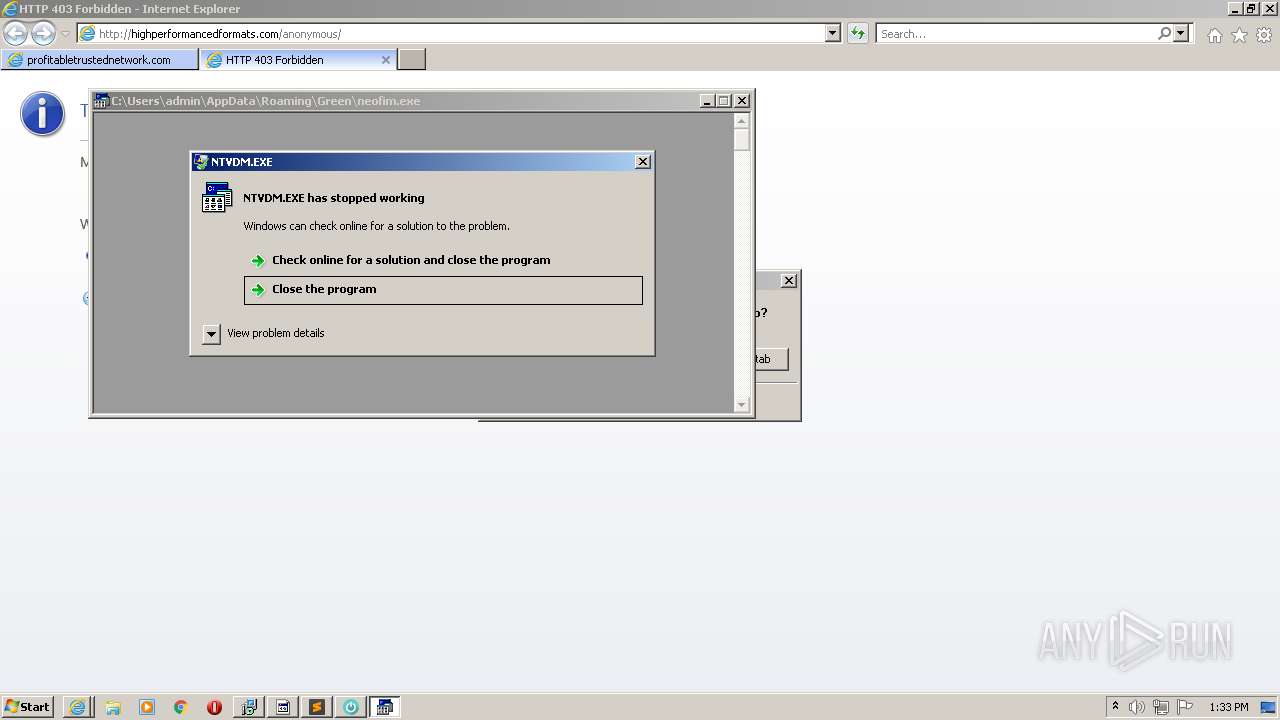
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9239B03F8C5BC272D3C1F25A3DF7480D |
| SHA1: | DF1D07EDB1EB365CF3DB049241C71BD340520C42 |
| SHA256: | 494703E36C5B2CF916E6E84865A98F8E5406181625A2533C81709CA4D07BC594 |
| SSDEEP: | 3:N1KNKRBkM9:CYnkw |
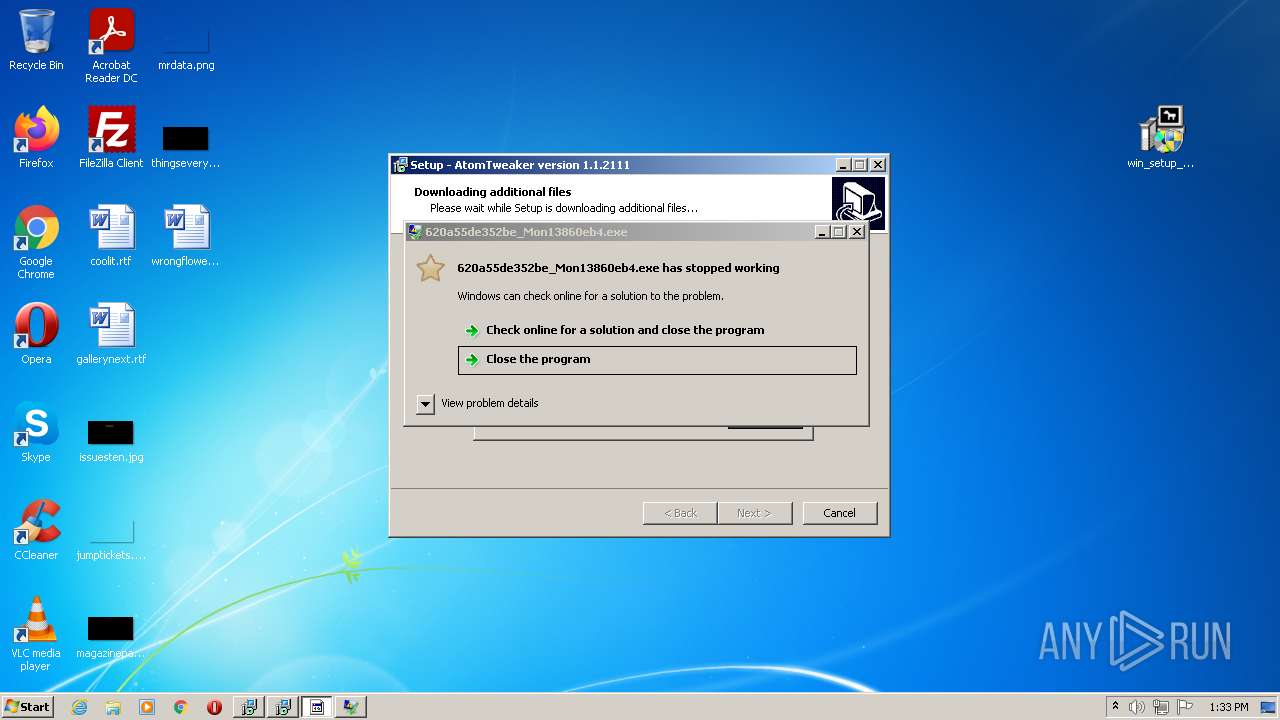
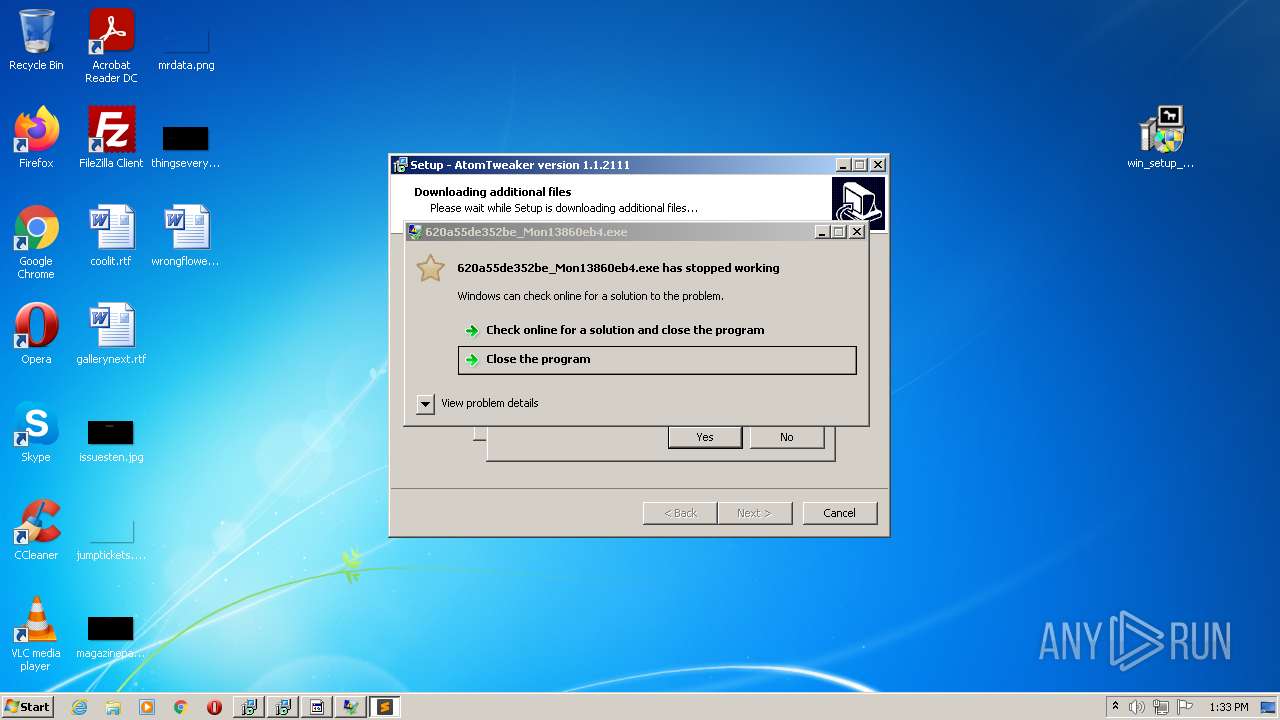
MALICIOUS
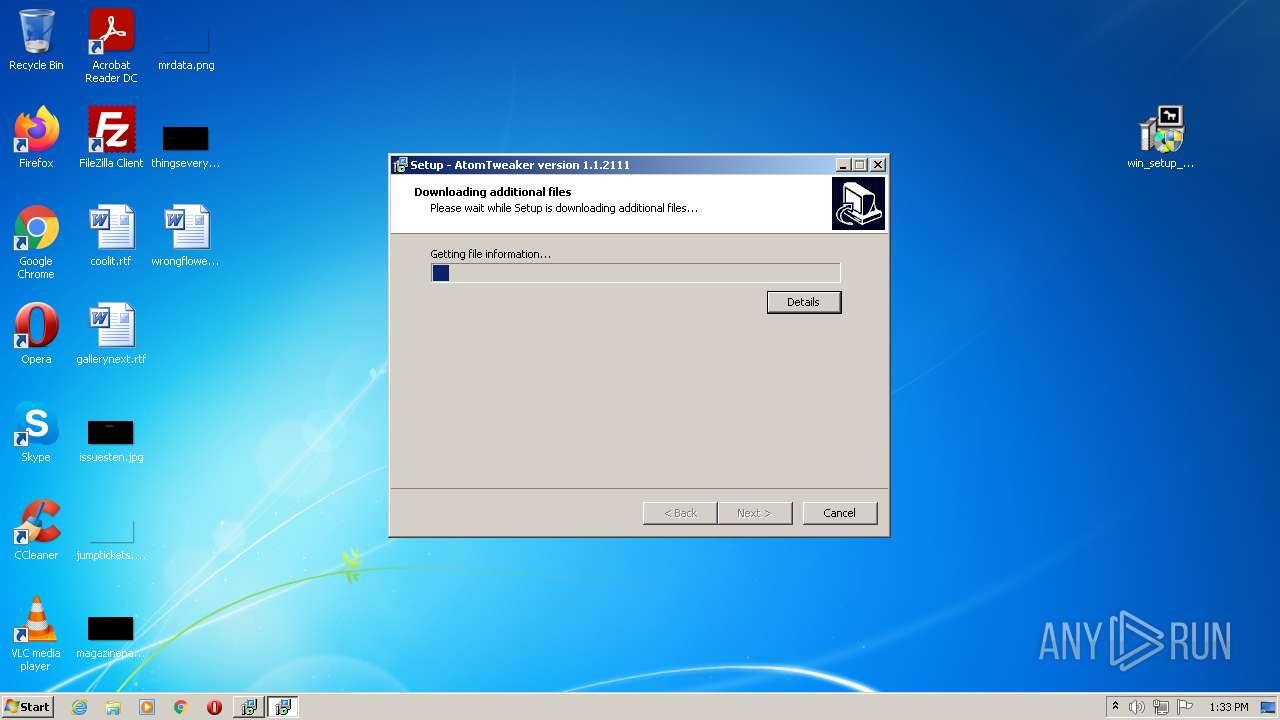
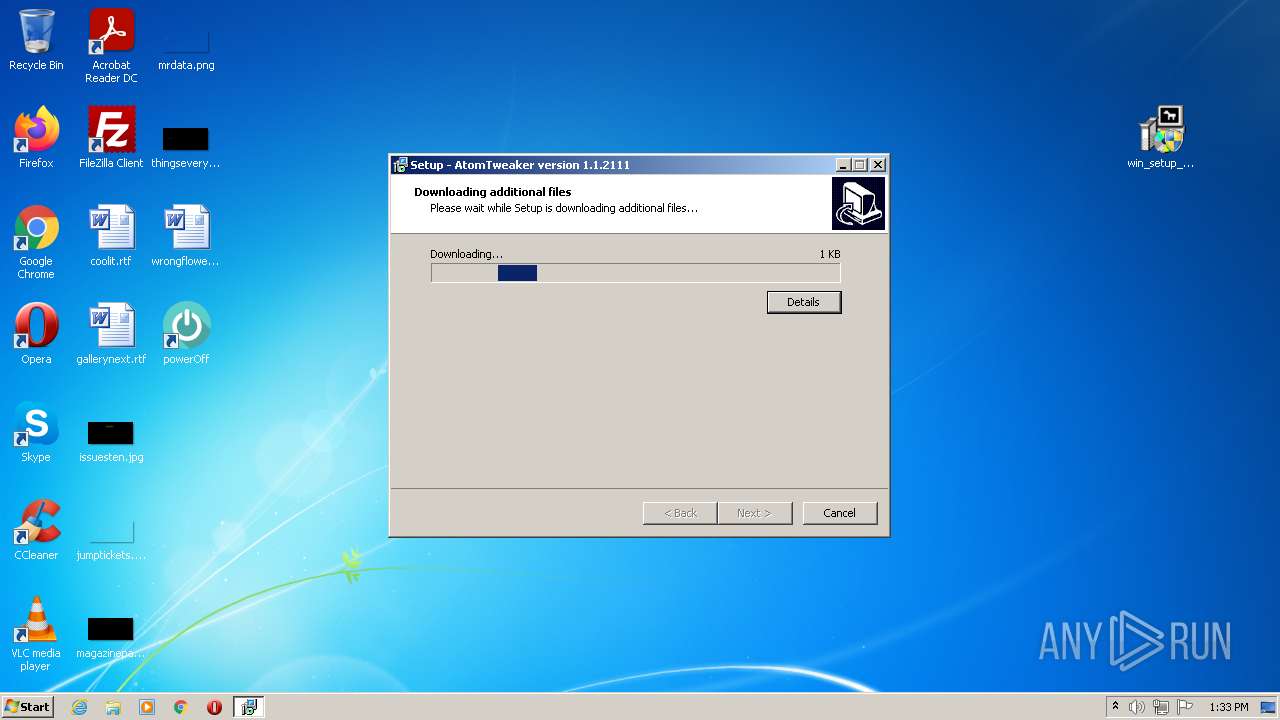
Application was dropped or rewritten from another process
- win_setup__620a55f3425aa.exe (PID: 588)
- win_setup__620a55f3425aa.exe (PID: 4004)
- setup_installer.exe (PID: 416)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 968)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- 620a55d81c392_Mon136482d09ca1.exe (PID: 2324)
- 620a55e9eb4da_Mon13a8533e9.exe (PID: 1740)
- 620a55d81c392_Mon136482d09ca1.exe (PID: 3536)
- 620a55de352be_Mon13860eb4.exe (PID: 2180)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55e17036d_Mon13904120c9.exe (PID: 912)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- 620a55d8c8200_Mon13799069da.exe (PID: 864)
- 620a55ec5b461_Mon13a37ef5691e.exe (PID: 2864)
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- setup_install.exe (PID: 3588)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 2268)
- 620a55e9eb4da_Mon13a8533e9.exe (PID: 1984)
- 4763558182.exe (PID: 2464)
- LzmwAqmV.exe (PID: 3324)
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- 93358088096.exe (PID: 5604)
- 5871929590.exe (PID: 4504)
- 5871929590.exe (PID: 4344)
- 5871929590.exe (PID: 7404)
- 5871929590.exe (PID: 11368)
- 1968950212.exe (PID: 2388)
- 81403156579.exe (PID: 3932)
- Rujumoliso.exe (PID: 356)
- Dacaeshariwa.exe (PID: 1612)
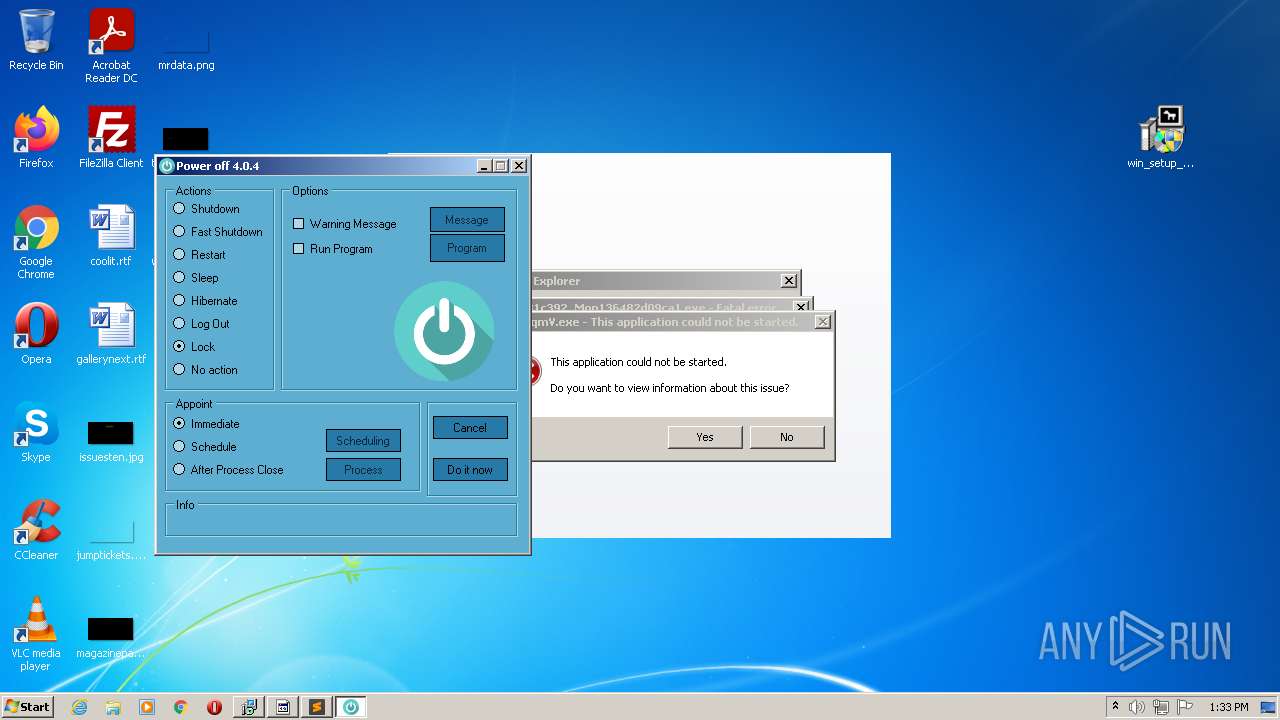
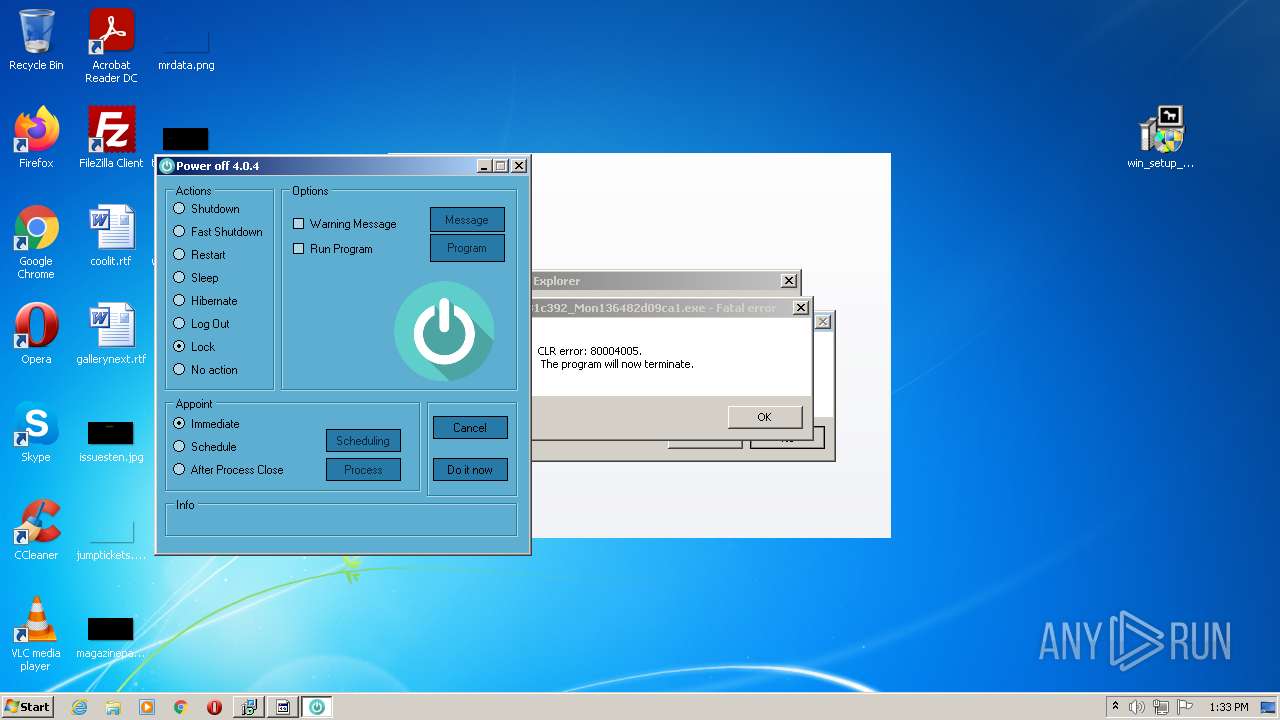
- poweroff.exe (PID: 3644)
- build2.exe (PID: 7676)
- 83323808524.exe (PID: 11204)
- build2.exe (PID: 10792)
- setting.exe (PID: 4720)
- setting.exe (PID: 8264)
- aipackagechainer.exe (PID: 8264)
- Settings%20Installation.exe (PID: 9736)
Drops executable file immediately after starts
- setup_installer.exe (PID: 416)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 968)
- 620a55ec5b461_Mon13a37ef5691e.exe (PID: 2864)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 2268)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- Settings%20Installation.exe (PID: 9736)
Executes PowerShell scripts
- cmd.exe (PID: 3504)
Changes settings of System certificates
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- Dacaeshariwa.exe (PID: 1612)
- setting.exe (PID: 4720)
- msiexec.exe (PID: 6736)
- powershell.exe (PID: 11624)
Actions looks like stealing of personal data
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- 83323808524.exe (PID: 11204)
- build2.exe (PID: 10792)
- 93358088096.exe (PID: 5604)
Application was injected by another process
- svchost.exe (PID: 884)
Runs injected code in another process
- rundll32.exe (PID: 2456)
Changes the autorun value in the registry
- MSekni.exe (PID: 116)
- 5871929590.exe (PID: 4344)
- aipackagechainer.exe (PID: 8264)
- Settings%20Installation.exe (PID: 9736)
Loads the Task Scheduler COM API
- 5871929590.exe (PID: 4344)
- 5871929590.exe (PID: 11368)
- setting.exe (PID: 4720)
- aipackagechainer.exe (PID: 8264)
STOP was detected
- 5871929590.exe (PID: 11368)
Connects to CnC server
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- 93358088096.exe (PID: 5604)
Stealing of credential data
- 93358088096.exe (PID: 5604)
Steals credentials from Web Browsers
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
ARKEI was detected
- 93358088096.exe (PID: 5604)
VIDAR was detected
- build2.exe (PID: 10792)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2672)
- WinRAR.exe (PID: 2888)
- win_setup__620a55f3425aa.exe (PID: 4004)
- setup_installer.exe (PID: 416)
- setup_install.exe (PID: 3588)
- cmd.exe (PID: 3504)
- cmd.exe (PID: 1628)
- powershell.exe (PID: 2576)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 1168)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- cmd.exe (PID: 2468)
- cmd.exe (PID: 3112)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 2796)
- 620a55d8c8200_Mon13799069da.exe (PID: 864)
- cmd.exe (PID: 640)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- 620a55de352be_Mon13860eb4.exe (PID: 2180)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- cmd.exe (PID: 3884)
- 620a55d81c392_Mon136482d09ca1.exe (PID: 2324)
- 620a55e17036d_Mon13904120c9.exe (PID: 912)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- cmd.exe (PID: 3324)
- 620a55e9eb4da_Mon13a8533e9.exe (PID: 1740)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 968)
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- cmd.exe (PID: 3732)
- cmd.exe (PID: 4032)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55ec5b461_Mon13a37ef5691e.exe (PID: 2864)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 2268)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- 620a55e9eb4da_Mon13a8533e9.exe (PID: 1984)
- 620a55d81c392_Mon136482d09ca1.exe (PID: 3536)
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- MSekni.exe (PID: 116)
- cmd.exe (PID: 344)
- LzmwAqmV.exe (PID: 3324)
- 4763558182.exe (PID: 2464)
- Rujumoliso.exe (PID: 356)
- Dacaeshariwa.exe (PID: 1612)
- poweroff.exe (PID: 3644)
- poweroff.tmp (PID: 2096)
- cmd.exe (PID: 3824)
- 1968950212.exe (PID: 2388)
- Power Off.exe (PID: 3900)
- cmd.exe (PID: 5316)
- 93358088096.exe (PID: 5604)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 2392)
- 5871929590.exe (PID: 4344)
- 5871929590.exe (PID: 4504)
- svchost.exe (PID: 884)
- 5871929590.exe (PID: 7404)
- 5871929590.exe (PID: 11368)
- cmd.exe (PID: 2380)
- 81403156579.exe (PID: 3932)
- cmd.exe (PID: 5064)
- setting.exe (PID: 4720)
- cmd.exe (PID: 8120)
- setting.exe (PID: 8264)
- build2.exe (PID: 7676)
- cmd.exe (PID: 10628)
- 83323808524.exe (PID: 11204)
- cmd.exe (PID: 12032)
- build2.exe (PID: 10792)
- cmd.exe (PID: 11400)
- aipackagechainer.exe (PID: 8264)
- Settings%20Installation.exe (PID: 9736)
- cmd.exe (PID: 3672)
- powershell.exe (PID: 11624)
Application launched itself
- WinRAR.exe (PID: 2672)
- 620a55d8c8200_Mon13799069da.exe (PID: 864)
- 620a55d81c392_Mon136482d09ca1.exe (PID: 2324)
- 620a55e9eb4da_Mon13a8533e9.exe (PID: 1740)
- 5871929590.exe (PID: 4504)
- 5871929590.exe (PID: 4344)
- 5871929590.exe (PID: 7404)
- msiexec.exe (PID: 6736)
- build2.exe (PID: 7676)
Reads the computer name
- WinRAR.exe (PID: 2888)
- WinRAR.exe (PID: 2672)
- win_setup__620a55f3425aa.exe (PID: 4004)
- setup_installer.exe (PID: 416)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- powershell.exe (PID: 2576)
- 620a55d81c392_Mon136482d09ca1.exe (PID: 2324)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55d8c8200_Mon13799069da.exe (PID: 864)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- 620a55e17036d_Mon13904120c9.exe (PID: 912)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- MSekni.exe (PID: 116)
- LzmwAqmV.exe (PID: 3324)
- Rujumoliso.exe (PID: 356)
- Dacaeshariwa.exe (PID: 1612)
- poweroff.tmp (PID: 2096)
- 1968950212.exe (PID: 2388)
- 5871929590.exe (PID: 4344)
- 5871929590.exe (PID: 11368)
- setting.exe (PID: 4720)
- setting.exe (PID: 8264)
- 81403156579.exe (PID: 3932)
- 93358088096.exe (PID: 5604)
- 83323808524.exe (PID: 11204)
- build2.exe (PID: 10792)
- Power Off.exe (PID: 3900)
- aipackagechainer.exe (PID: 8264)
- Settings%20Installation.exe (PID: 9736)
- powershell.exe (PID: 11624)
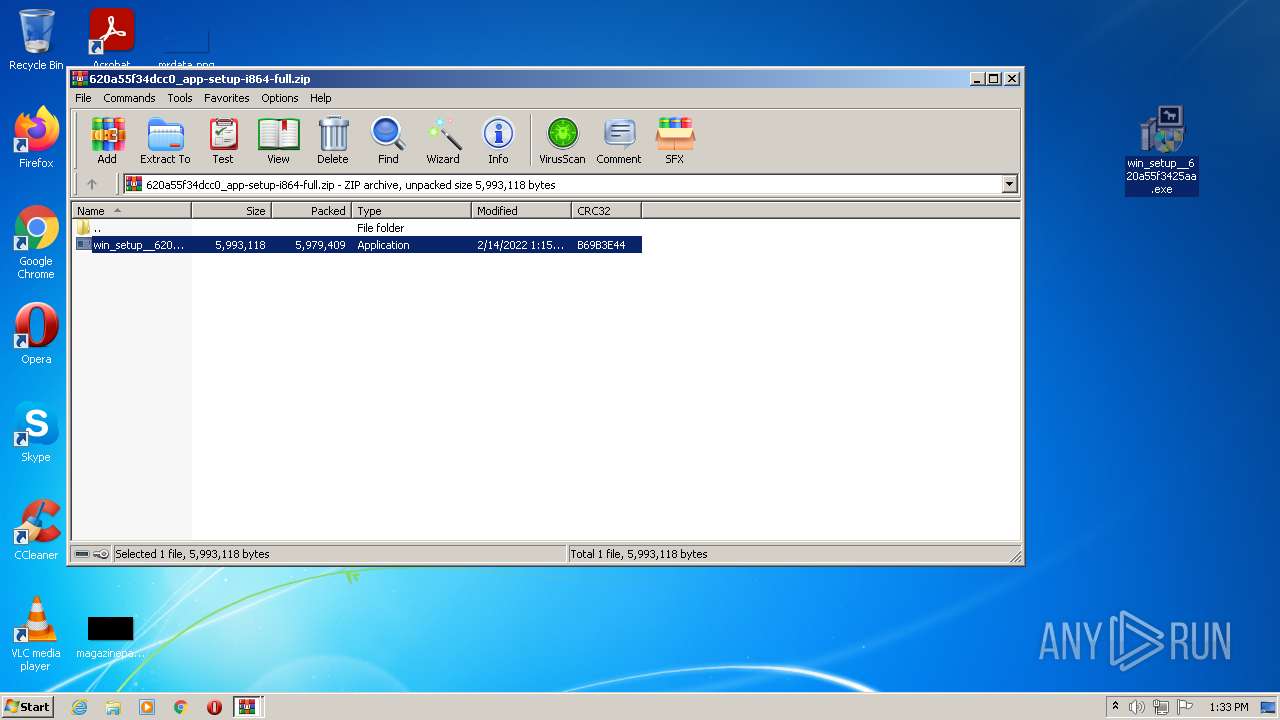
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2888)
- win_setup__620a55f3425aa.exe (PID: 4004)
- setup_installer.exe (PID: 416)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 968)
- 620a55ec5b461_Mon13a37ef5691e.exe (PID: 2864)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 620a55dcd0d2d_Mon131e8fe0098.exe (PID: 2268)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- MSekni.exe (PID: 116)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- Dacaeshariwa.exe (PID: 1612)
- 93358088096.exe (PID: 5604)
- MsiExec.exe (PID: 8764)
- Settings%20Installation.exe (PID: 9736)
Drops a file with a compile date too recent
- setup_installer.exe (PID: 416)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- MSekni.exe (PID: 116)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- Settings%20Installation.exe (PID: 9736)
Drops a file that was compiled in debug mode
- setup_installer.exe (PID: 416)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- MSekni.exe (PID: 116)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- Dacaeshariwa.exe (PID: 1612)
- 93358088096.exe (PID: 5604)
- MsiExec.exe (PID: 8764)
- Settings%20Installation.exe (PID: 9736)
Drops a file with too old compile date
- setup_installer.exe (PID: 416)
- 620a55ec5b461_Mon13a37ef5691e.exe (PID: 2864)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- MSekni.exe (PID: 116)
Starts CMD.EXE for commands execution
- setup_install.exe (PID: 3588)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- 620a55e710f6a_Mon1300c8b34032.exe (PID: 1244)
- Dacaeshariwa.exe (PID: 1612)
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
Reads Environment values
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- MSekni.exe (PID: 116)
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- Rujumoliso.exe (PID: 356)
- Dacaeshariwa.exe (PID: 1612)
- setting.exe (PID: 4720)
- 81403156579.exe (PID: 3932)
- 83323808524.exe (PID: 11204)
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
- aipackagechainer.exe (PID: 8264)
Reads Windows owner or organization settings
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- poweroff.tmp (PID: 2096)
- setting.exe (PID: 4720)
- msiexec.exe (PID: 6736)
Reads the Windows organization settings
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- poweroff.tmp (PID: 2096)
- setting.exe (PID: 4720)
- msiexec.exe (PID: 6736)
Adds / modifies Windows certificates
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- Dacaeshariwa.exe (PID: 1612)
- setting.exe (PID: 4720)
- msiexec.exe (PID: 6736)
- powershell.exe (PID: 11624)
Reads default file associations for system extensions
- 620a55e17036d_Mon13904120c9.exe (PID: 912)
Reads the cookies of Google Chrome
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 2404)
Loads DLL from Mozilla Firefox
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
Reads mouse settings
- 4763558182.exe (PID: 2464)
Reads CPU info
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- 81403156579.exe (PID: 3932)
- 83323808524.exe (PID: 11204)
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
Executed via WMI
- rundll32.exe (PID: 2456)
Searches for installed software
- 357732db-e982-4d03-982b-1ee79dd1143a.exe (PID: 3708)
- 83323808524.exe (PID: 11204)
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
Creates a directory in Program Files
- MSekni.exe (PID: 116)
- poweroff.tmp (PID: 2096)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
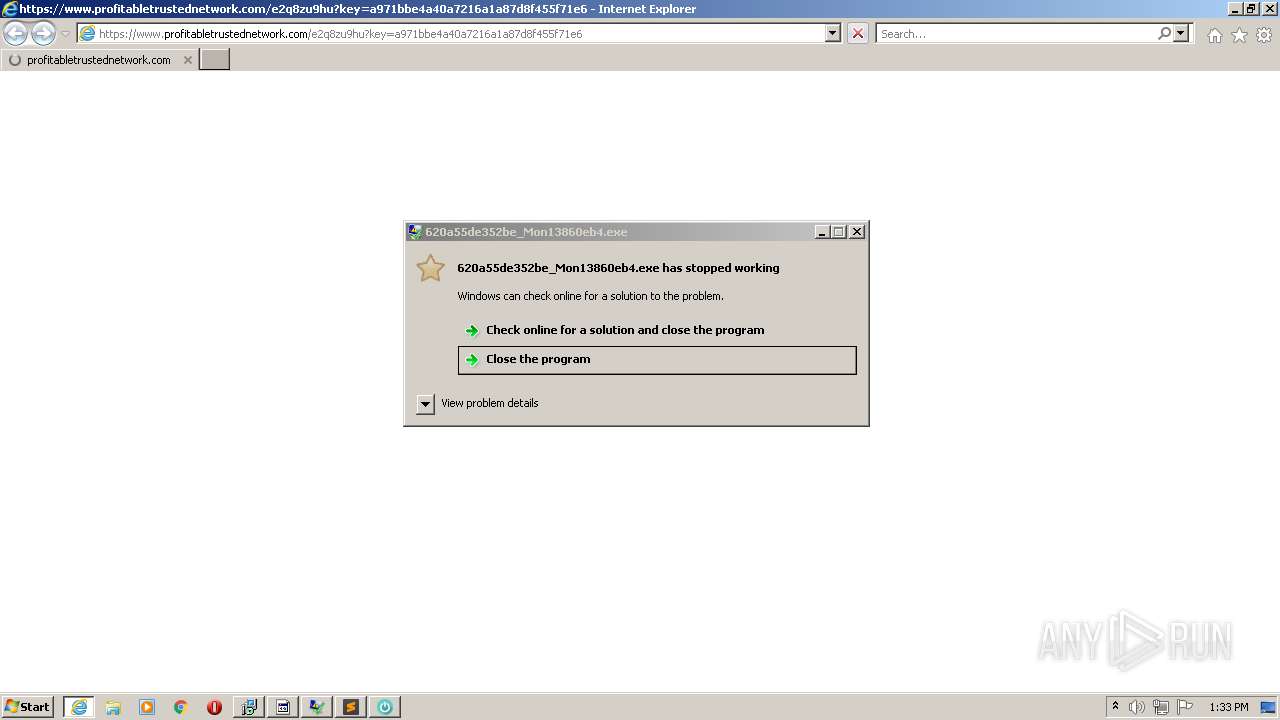
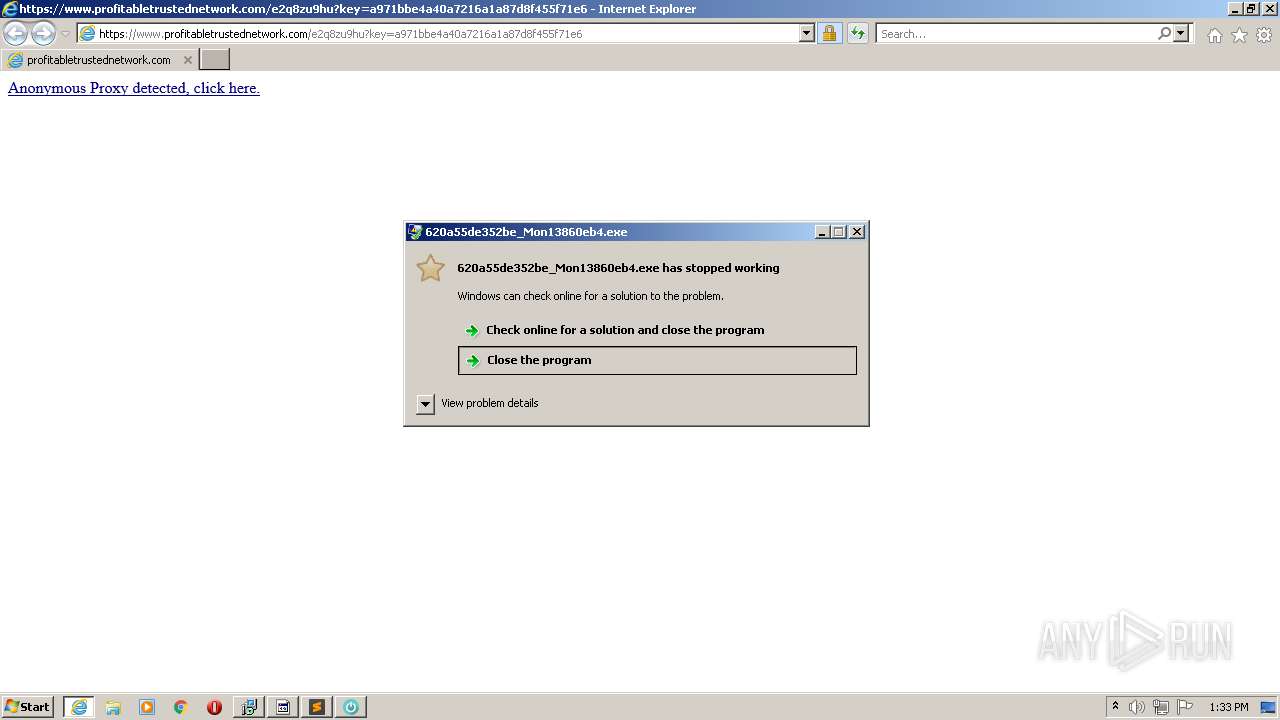
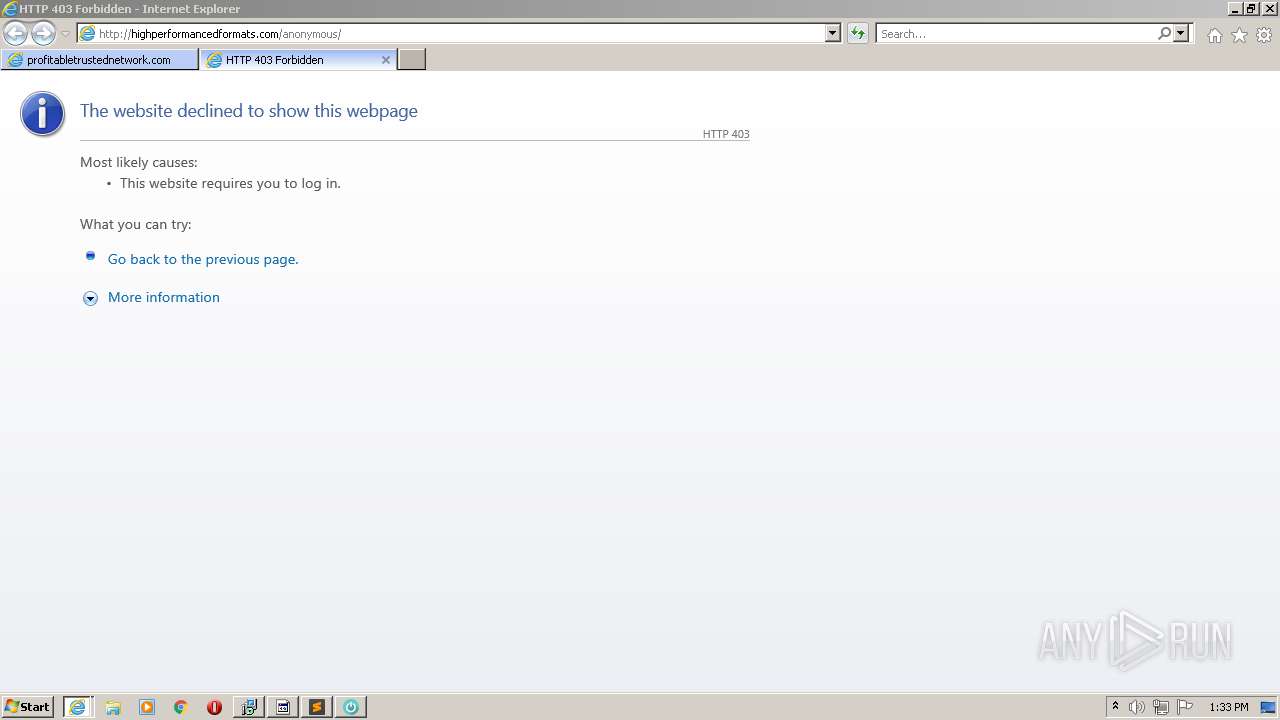
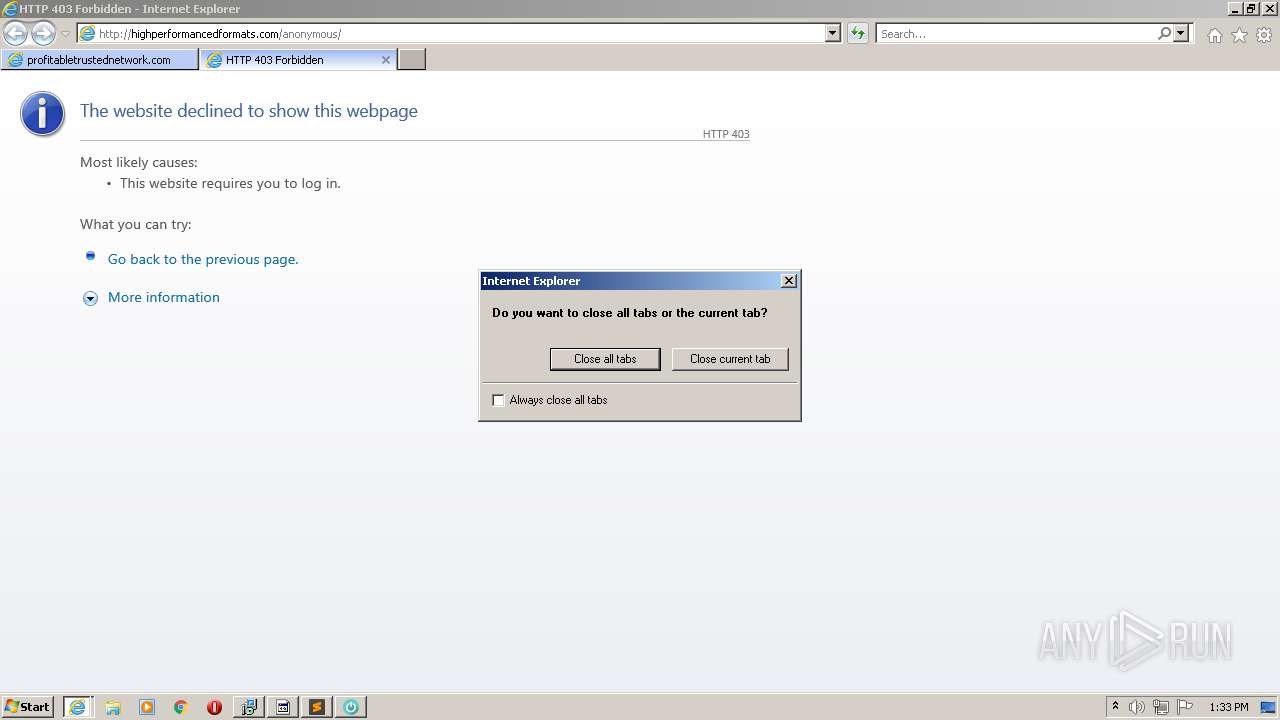
Starts Internet Explorer
- Rujumoliso.exe (PID: 356)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1892)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2392)
- cmd.exe (PID: 12032)
- cmd.exe (PID: 3672)
Uses ICACLS.EXE to modify access control list
- 5871929590.exe (PID: 4344)
Creates files in the Windows directory
- svchost.exe (PID: 884)
Removes files from Windows directory
- svchost.exe (PID: 884)
Creates files in the user directory
- setting.exe (PID: 4720)
- 81403156579.exe (PID: 3932)
- MsiExec.exe (PID: 8764)
- 93358088096.exe (PID: 5604)
- Settings%20Installation.exe (PID: 9736)
Executed as Windows Service
- msiexec.exe (PID: 6736)
Starts Microsoft Installer
- setting.exe (PID: 4720)
Creates files in the program directory
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
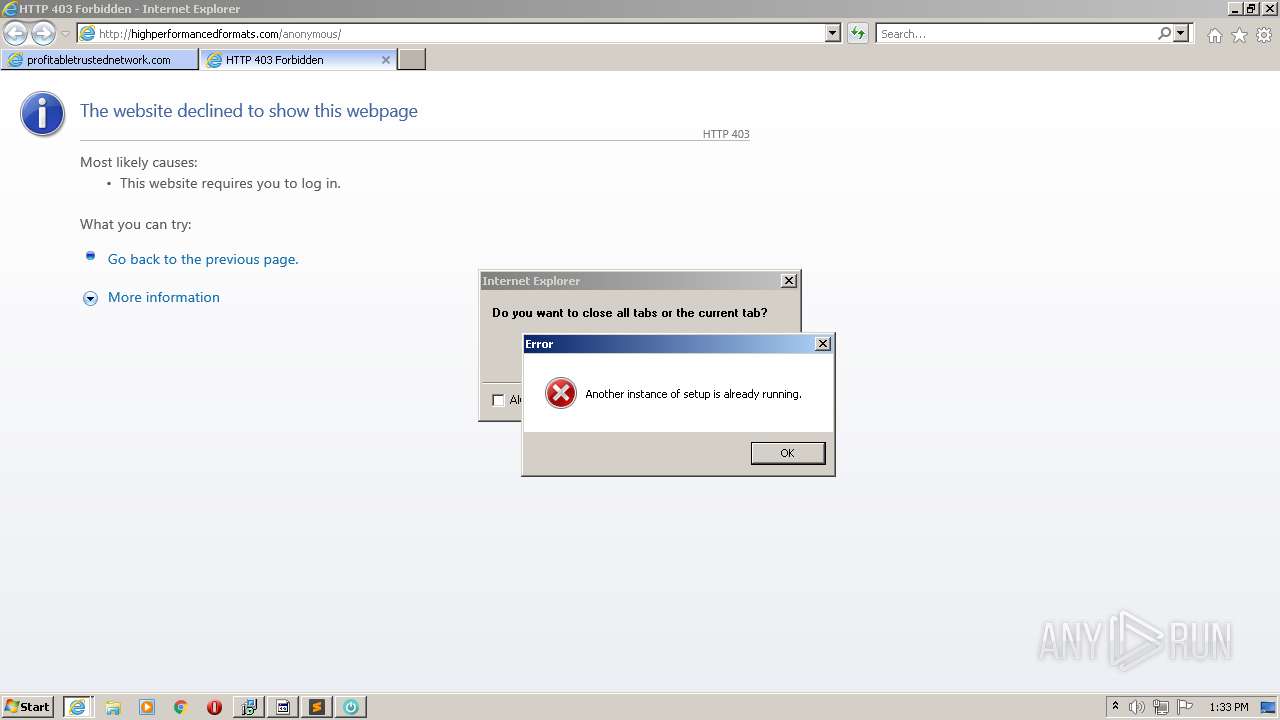
Executes application which crashes
- 81403156579.exe (PID: 3932)
Starts CMD.EXE for self-deleting
- 93358088096.exe (PID: 5604)
- build2.exe (PID: 10792)
Creates a software uninstall entry
- Settings%20Installation.exe (PID: 9736)
Executes PowerShell scripts
- aipackagechainer.exe (PID: 8264)
INFO
Application launched itself
- firefox.exe (PID: 2880)
- firefox.exe (PID: 3224)
- iexplore.exe (PID: 1136)
Checks supported languages
- firefox.exe (PID: 2880)
- firefox.exe (PID: 3224)
- firefox.exe (PID: 3904)
- firefox.exe (PID: 2484)
- firefox.exe (PID: 1976)
- firefox.exe (PID: 908)
- firefox.exe (PID: 2432)
- firefox.exe (PID: 2576)
- firefox.exe (PID: 1628)
- NOTEPAD.EXE (PID: 320)
- control.exe (PID: 2404)
- rundll32.exe (PID: 2384)
- rundll32.exe (PID: 2456)
- iexplore.exe (PID: 1136)
- iexplore.exe (PID: 2068)
- taskkill.exe (PID: 4396)
- icacls.exe (PID: 2388)
- iexplore.exe (PID: 1892)
- msiexec.exe (PID: 6736)
- MsiExec.exe (PID: 7068)
- msiexec.exe (PID: 7604)
- MsiExec.exe (PID: 8764)
- ntvdm.exe (PID: 9896)
- taskkill.exe (PID: 2772)
- timeout.exe (PID: 11932)
- taskkill.exe (PID: 5356)
- timeout.exe (PID: 4636)
Reads the computer name
- firefox.exe (PID: 3224)
- firefox.exe (PID: 3904)
- firefox.exe (PID: 1976)
- firefox.exe (PID: 2484)
- firefox.exe (PID: 908)
- firefox.exe (PID: 2432)
- firefox.exe (PID: 1628)
- firefox.exe (PID: 2576)
- control.exe (PID: 2404)
- rundll32.exe (PID: 2456)
- iexplore.exe (PID: 1136)
- iexplore.exe (PID: 2068)
- taskkill.exe (PID: 4396)
- icacls.exe (PID: 2388)
- iexplore.exe (PID: 1892)
- msiexec.exe (PID: 6736)
- MsiExec.exe (PID: 7068)
- msiexec.exe (PID: 7604)
- MsiExec.exe (PID: 8764)
- taskkill.exe (PID: 2772)
- taskkill.exe (PID: 5356)
Reads CPU info
- firefox.exe (PID: 3224)
Creates files in the program directory
- firefox.exe (PID: 3224)
- MSekni.exe (PID: 116)
- poweroff.tmp (PID: 2096)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
Reads the date of Windows installation
- firefox.exe (PID: 3224)
- iexplore.exe (PID: 1136)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3224)
- Settings%20Installation.exe (PID: 9736)
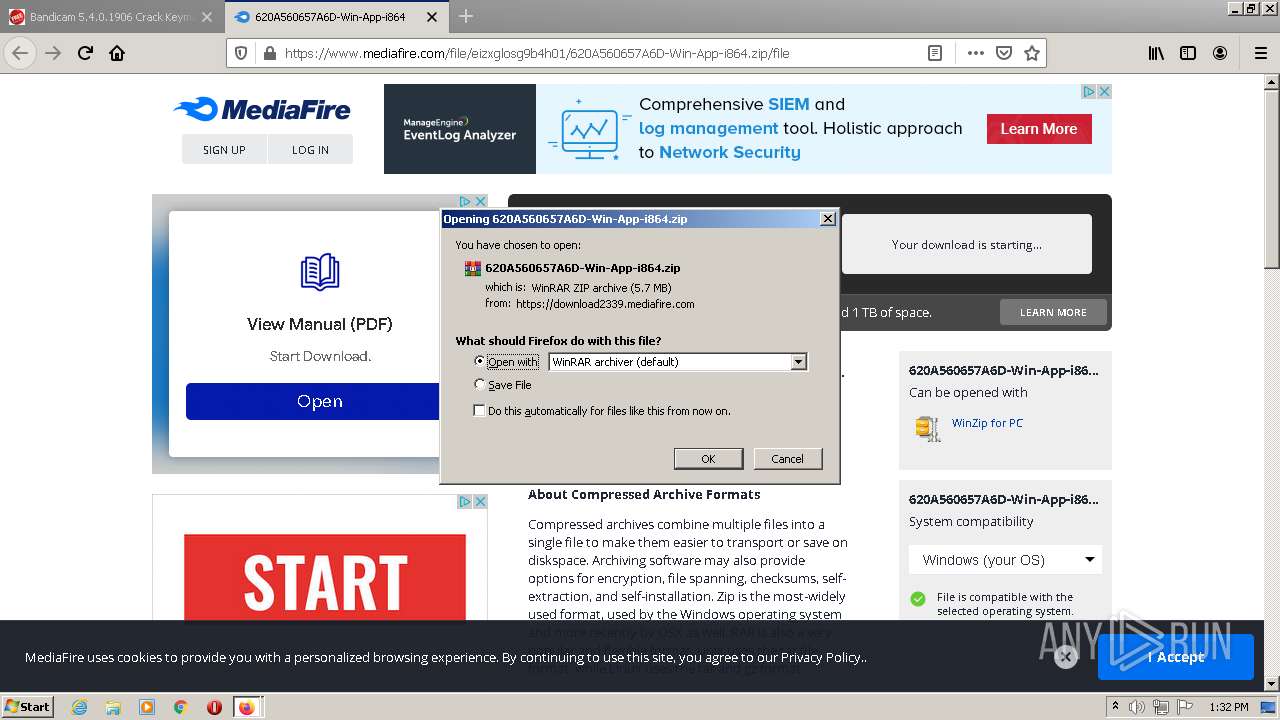
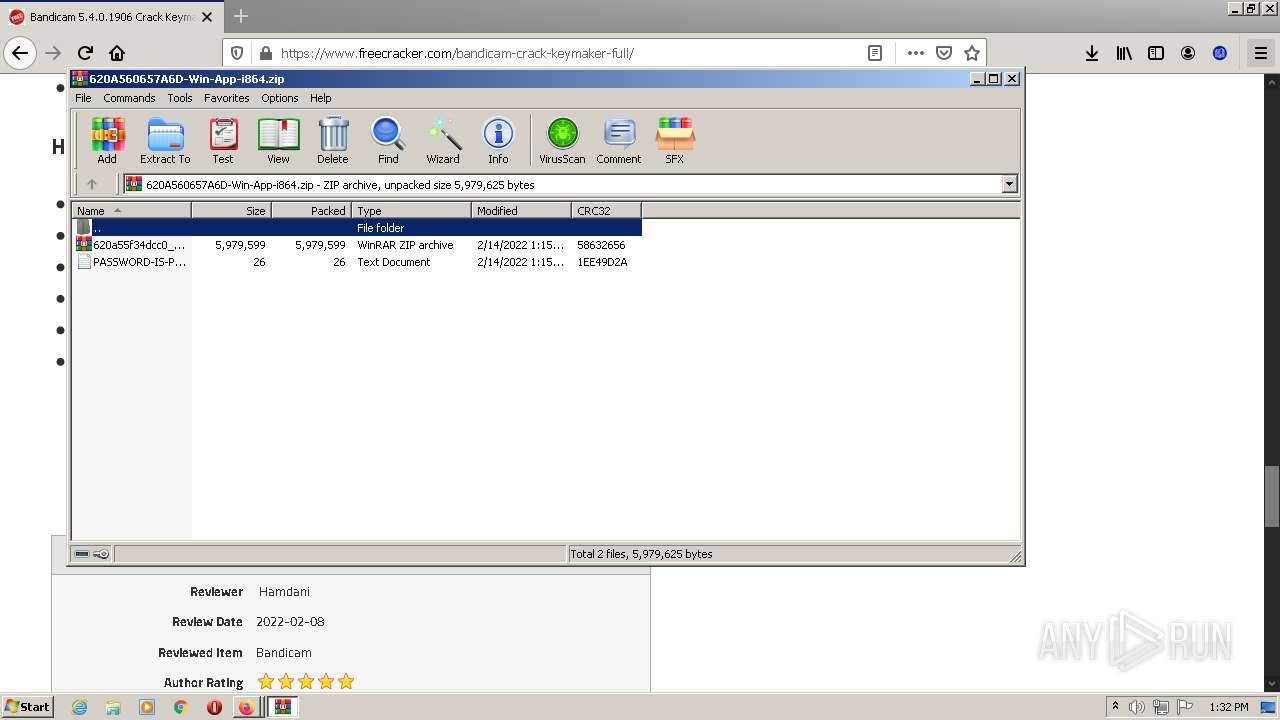
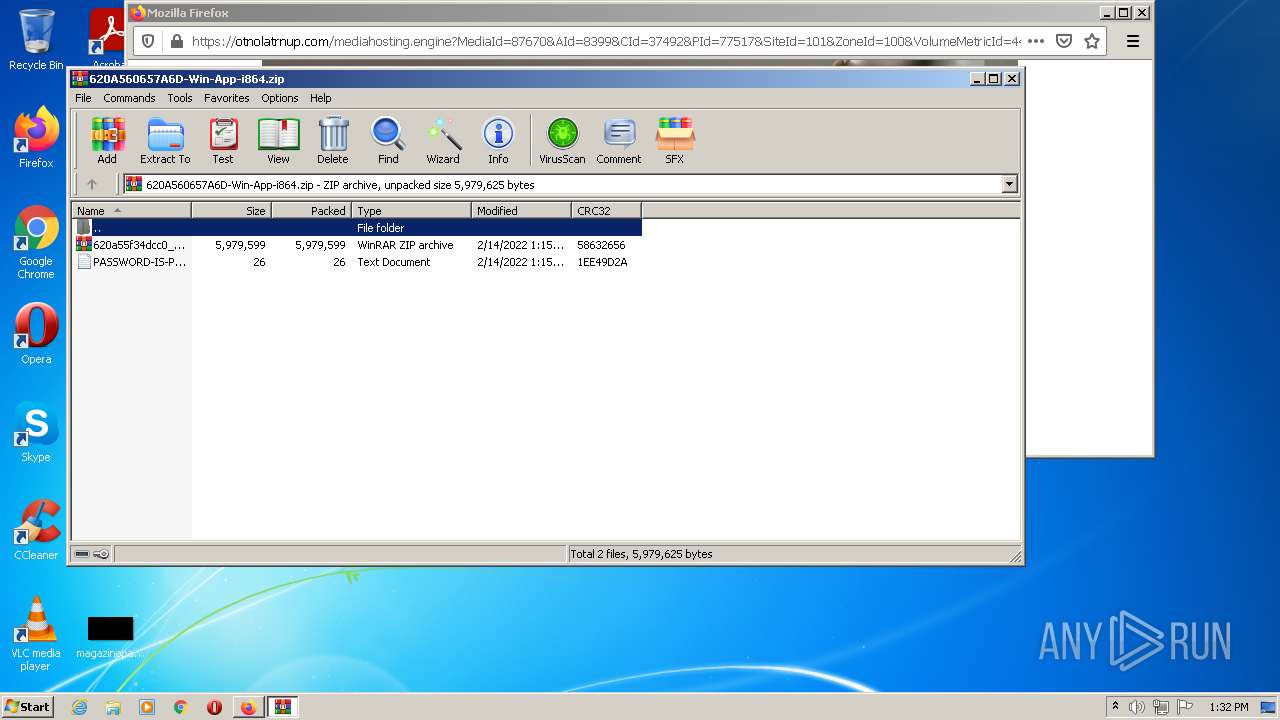
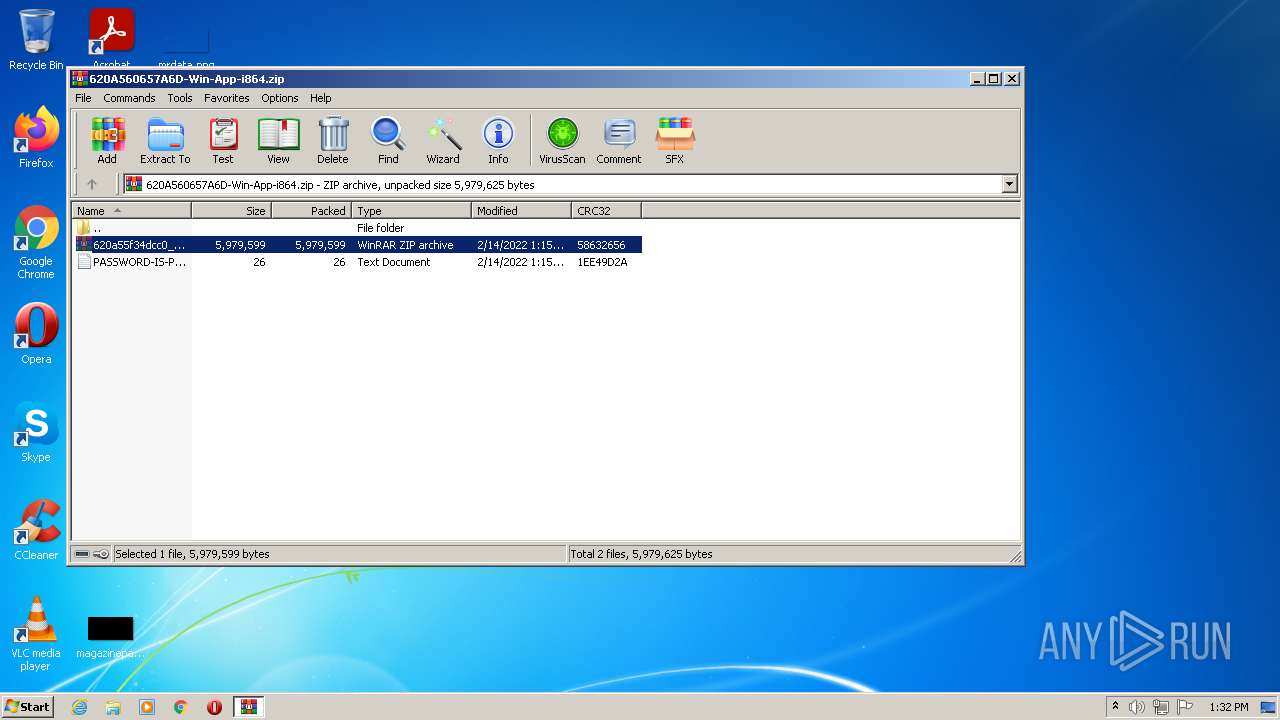
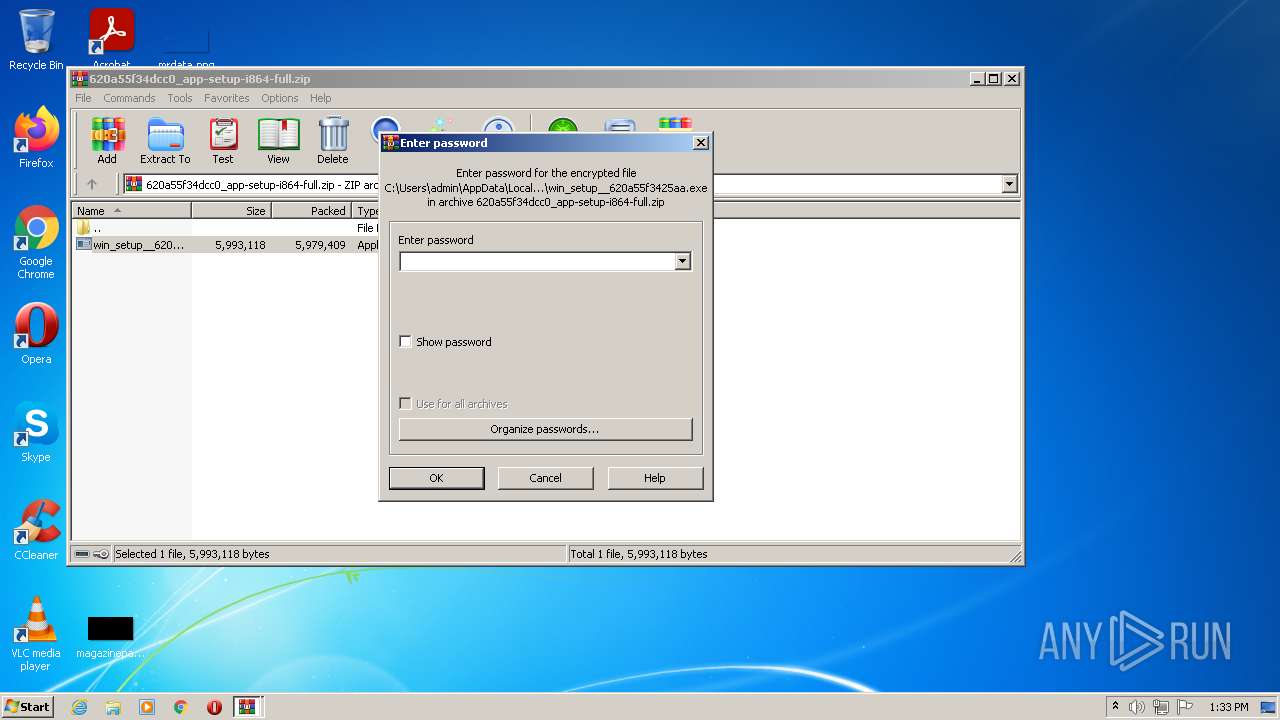
Manual execution by user
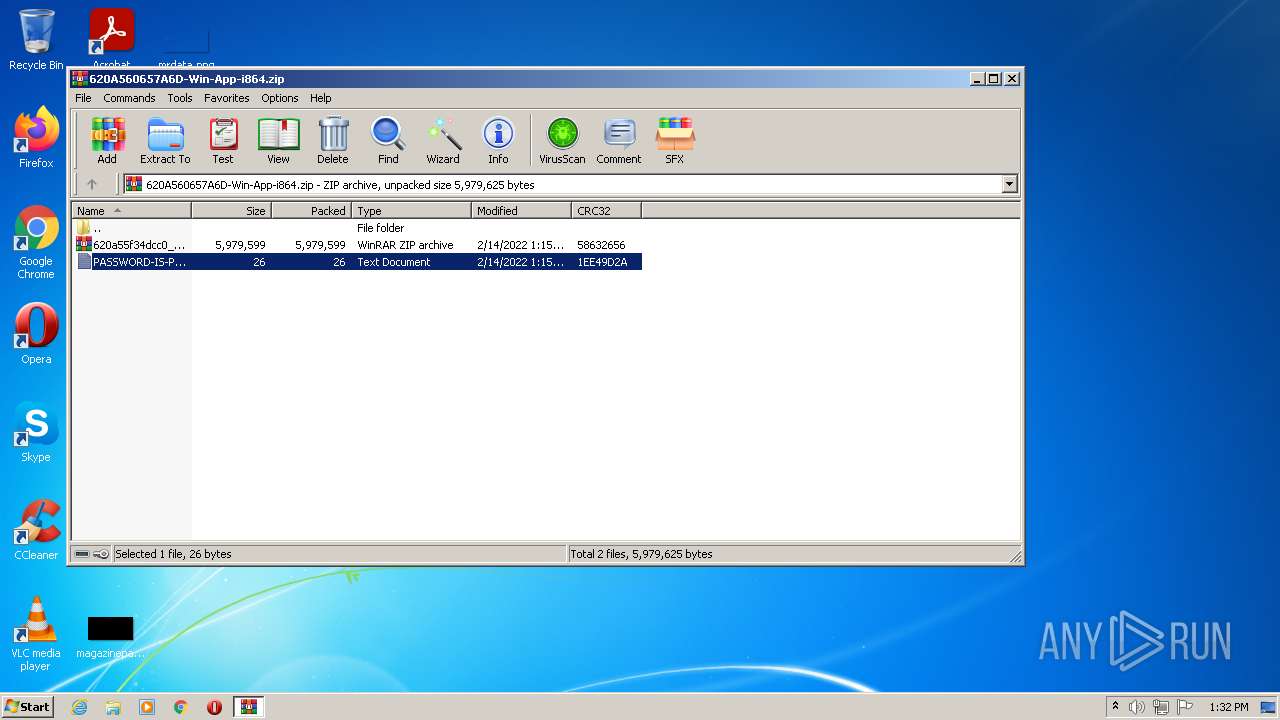
- WinRAR.exe (PID: 2672)
- win_setup__620a55f3425aa.exe (PID: 588)
- win_setup__620a55f3425aa.exe (PID: 4004)
Checks Windows Trust Settings
- firefox.exe (PID: 3224)
- powershell.exe (PID: 2576)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- iexplore.exe (PID: 2068)
- 5871929590.exe (PID: 4344)
- iexplore.exe (PID: 1136)
- 5871929590.exe (PID: 11368)
- setting.exe (PID: 4720)
- msiexec.exe (PID: 6736)
- MsiExec.exe (PID: 8764)
- build2.exe (PID: 10792)
- powershell.exe (PID: 11624)
- Settings%20Installation.exe (PID: 9736)
Creates files in the user directory
- firefox.exe (PID: 3224)
- iexplore.exe (PID: 2068)
Reads settings of System Certificates
- 620a55d8c8200_Mon13799069da.exe (PID: 2024)
- 620a55e464916_Mon13f16795.exe (PID: 1360)
- powershell.exe (PID: 2576)
- 620a55d92d658_Mon1326ed325e.exe (PID: 3448)
- 620a55d64d491_Mon137864f7d.exe (PID: 1780)
- MSekni.exe (PID: 116)
- 620a55eb5b569_Mon137c0781a.exe (PID: 3776)
- Rujumoliso.exe (PID: 356)
- Dacaeshariwa.exe (PID: 1612)
- iexplore.exe (PID: 2068)
- 5871929590.exe (PID: 4344)
- iexplore.exe (PID: 1136)
- 5871929590.exe (PID: 11368)
- setting.exe (PID: 4720)
- msiexec.exe (PID: 6736)
- MsiExec.exe (PID: 8764)
- build2.exe (PID: 10792)
- Settings%20Installation.exe (PID: 9736)
- powershell.exe (PID: 11624)
Application was dropped or rewritten from another process
- MSekni.exe (PID: 116)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 444)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
- 620a55ec5b461_Mon13a37ef5691e.tmp (PID: 856)
Changes internet zones settings
- iexplore.exe (PID: 1136)
Creates a software uninstall entry
- poweroff.tmp (PID: 2096)
- 620a55dcd0d2d_Mon131e8fe0098.tmp (PID: 2536)
Reads internet explorer settings
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 1892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
173
Monitored processes
104
Malicious processes
42
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\is-7FSCA.tmp\MSekni.exe" /S /UID=1405 | C:\Users\admin\AppData\Local\Temp\is-7FSCA.tmp\MSekni.exe | 620a55ec5b461_Mon13a37ef5691e.tmp | |
User: admin Company: powerofftVu2WFnM2mSWgzxE Integrity Level: HIGH Description: powerofftVu2WFnM2mSWgzxE Exit code: 0 Version: 1.5.7.3 | ||||
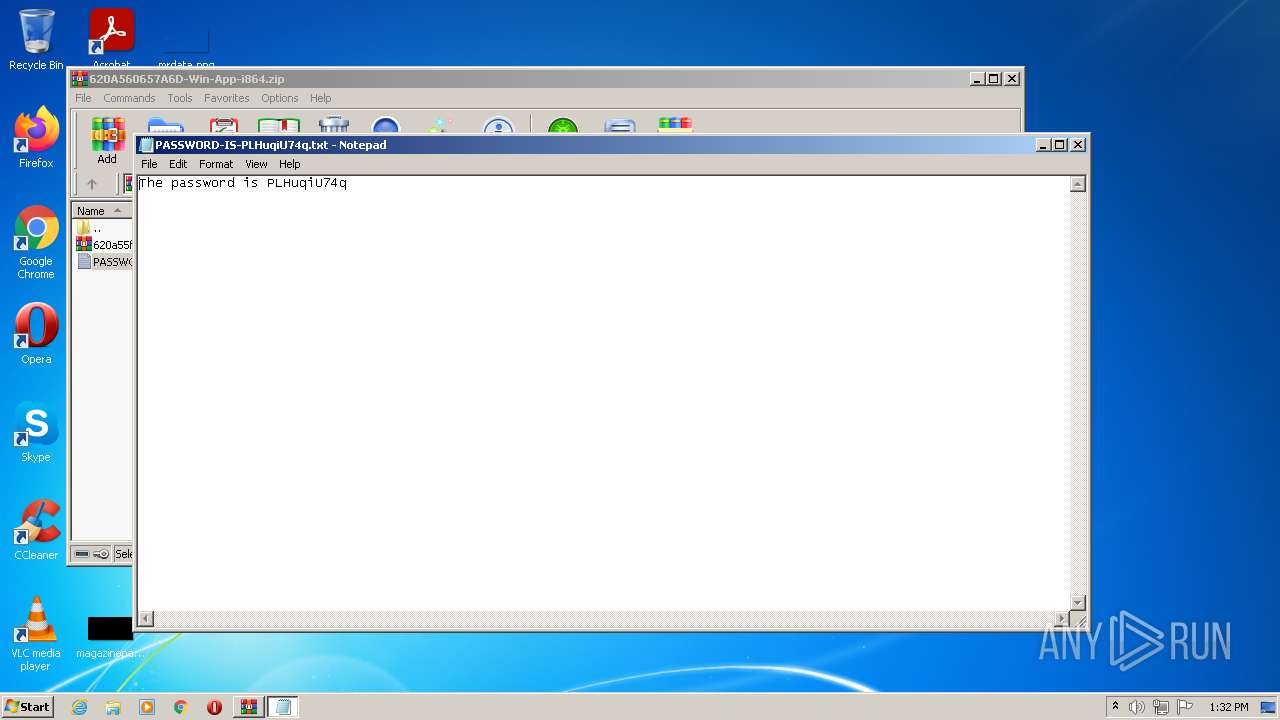
| 320 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa2672.22766\PASSWORD-IS-PLHuqiU74q.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 344 | "C:\Windows\System32\cmd.exe" /c start /I "" "C:\Users\admin\AppData\Local\Temp\4763558182.exe" | C:\Windows\System32\cmd.exe | — | 620a55eb5b569_Mon137c0781a.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 356 | "C:\Users\admin\AppData\Local\Temp\72-3061b-312-d9582-68363f14dc79a\Rujumoliso.exe" | C:\Users\admin\AppData\Local\Temp\72-3061b-312-d9582-68363f14dc79a\Rujumoliso.exe | MSekni.exe | |
User: admin Company: healthy_heart_strength Integrity Level: HIGH Description: healthy_heart_strength Exit code: 0 Version: 1.2.1.0 | ||||
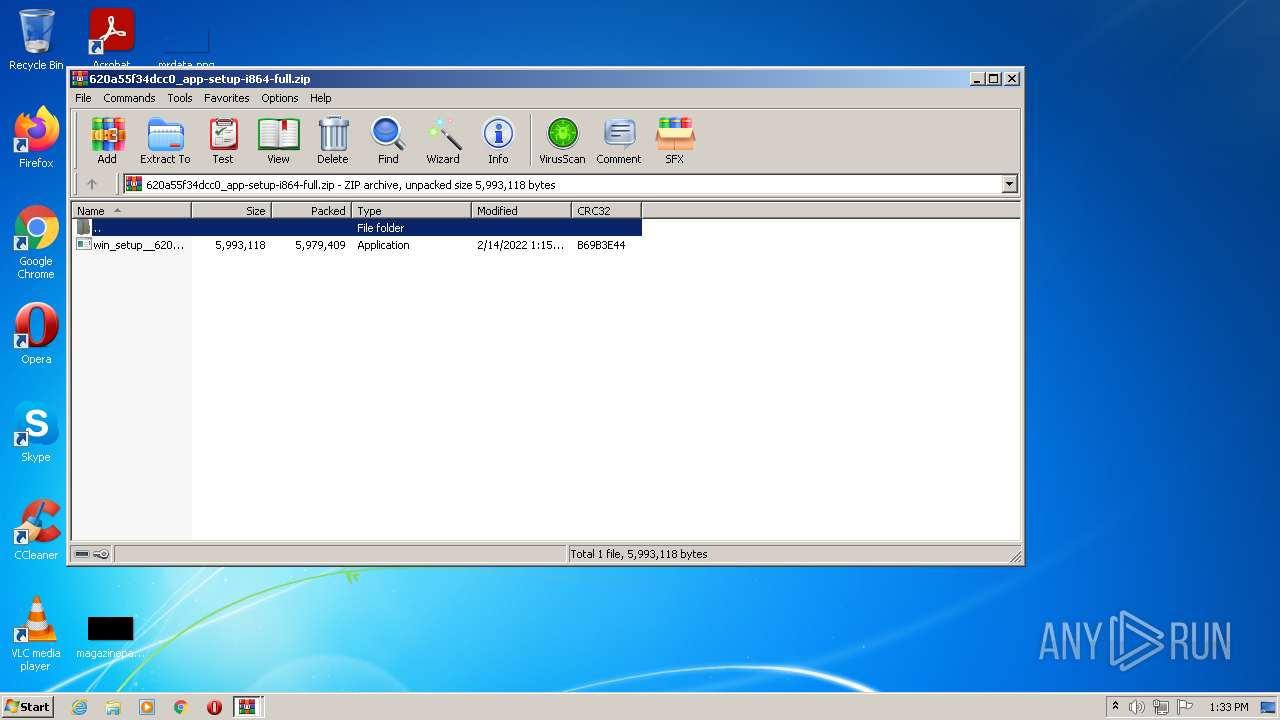
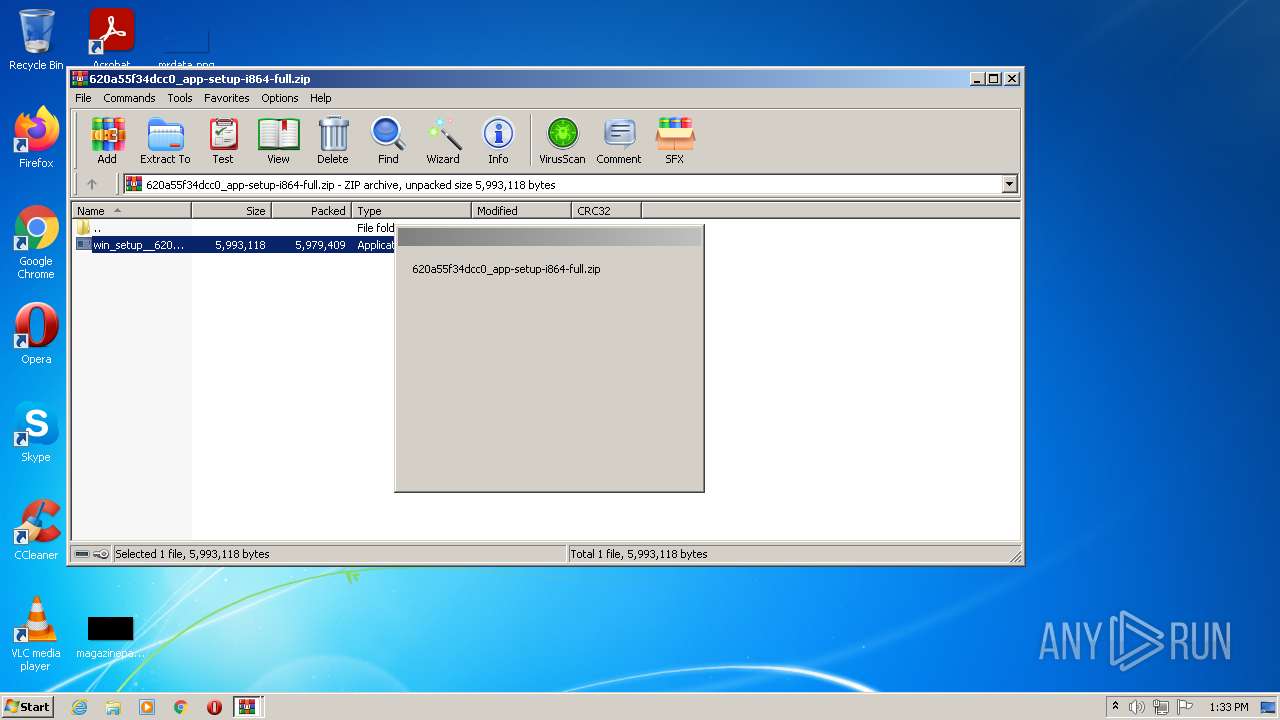
| 416 | "C:\Users\admin\AppData\Local\Temp\setup_installer.exe" | C:\Users\admin\AppData\Local\Temp\setup_installer.exe | win_setup__620a55f3425aa.exe | |
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 19.00 | ||||
| 444 | "C:\Users\admin\AppData\Local\Temp\is-L22J4.tmp\620a55dcd0d2d_Mon131e8fe0098.tmp" /SL5="$5016A,870458,780800,C:\Users\admin\AppData\Local\Temp\7zS0A1C7A61\620a55dcd0d2d_Mon131e8fe0098.exe" | C:\Users\admin\AppData\Local\Temp\is-L22J4.tmp\620a55dcd0d2d_Mon131e8fe0098.tmp | 620a55dcd0d2d_Mon131e8fe0098.exe | |
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 | ||||
| 588 | "C:\Users\admin\Desktop\win_setup__620a55f3425aa.exe" | C:\Users\admin\Desktop\win_setup__620a55f3425aa.exe | — | Explorer.EXE |
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | ||||
| 640 | C:\Windows\system32\cmd.exe /c 620a55d92d658_Mon1326ed325e.exe | C:\Windows\system32\cmd.exe | — | setup_install.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 856 | "C:\Users\admin\AppData\Local\Temp\is-I97ET.tmp\620a55ec5b461_Mon13a37ef5691e.tmp" /SL5="$70130,140559,56832,C:\Users\admin\AppData\Local\Temp\7zS0A1C7A61\620a55ec5b461_Mon13a37ef5691e.exe" | C:\Users\admin\AppData\Local\Temp\is-I97ET.tmp\620a55ec5b461_Mon13a37ef5691e.tmp | 620a55ec5b461_Mon13a37ef5691e.exe | |
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.52.0.0 | ||||
| 864 | 620a55d8c8200_Mon13799069da.exe | C:\Users\admin\AppData\Local\Temp\7zS0A1C7A61\620a55d8c8200_Mon13799069da.exe | — | cmd.exe |
User: admin Company: agent Integrity Level: HIGH Description: agent Exit code: 0 Version: 1.0.0.1 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
85
Suspicious files
233
Text files
99
Unknown types
152
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:708CC3FD3B585DCC75DCE1EA80A1EF86 | SHA256:F5F7B983428A3103CF25E2924A080E9B3C2E4AACA709176E4057C2BFE02F90B4 | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl.tmp | text | |
MD5:3625F1DDA6D119478AD89D13950C9ACA | SHA256:CB40F6A8D58901D612A86690A41D4E273F24936FC926E98F82C0918CBEF4FC64 | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_iFAhUHWQlrocgdc | binary | |
MD5:59077D84984B84F76E008C0CA3173A77 | SHA256:B45ED1F32AA11F1A4981F2665D73CB180B3FC50002FBF552B692080388FA0EC5 | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl | text | |
MD5:3625F1DDA6D119478AD89D13950C9ACA | SHA256:CB40F6A8D58901D612A86690A41D4E273F24936FC926E98F82C0918CBEF4FC64 | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_HN33Jkd1udphmyE | binary | |
MD5:9A0EDA01BA42498BAB4FD92539F62918 | SHA256:7F3243A64D25A0581847FF8635957755E79F61D406C64E4BA9F04128A3F65314 | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3224 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
160
TCP/UDP connections
326
DNS requests
467
Threats
225
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3224 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3224 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3224 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3224 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3224 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3224 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
3224 | firefox.exe | POST | 200 | 143.204.214.142:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
3224 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3224 | firefox.exe | POST | 200 | 184.25.51.82:80 | http://r3.o.lencr.org/ | US | der | 503 b | shared |
3224 | firefox.exe | POST | 200 | 104.18.31.182:80 | http://ocsp.sectigo.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3224 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3224 | firefox.exe | 52.89.43.233:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3224 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3224 | firefox.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3224 | firefox.exe | 18.66.248.40:443 | content-signature-2.cdn.mozilla.net | Massachusetts Institute of Technology | US | suspicious |
3224 | firefox.exe | 142.250.185.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3224 | firefox.exe | 108.157.4.64:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | suspicious |
3224 | firefox.exe | 34.213.247.36:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3224 | firefox.exe | 54.148.127.74:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | suspicious |
3224 | firefox.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
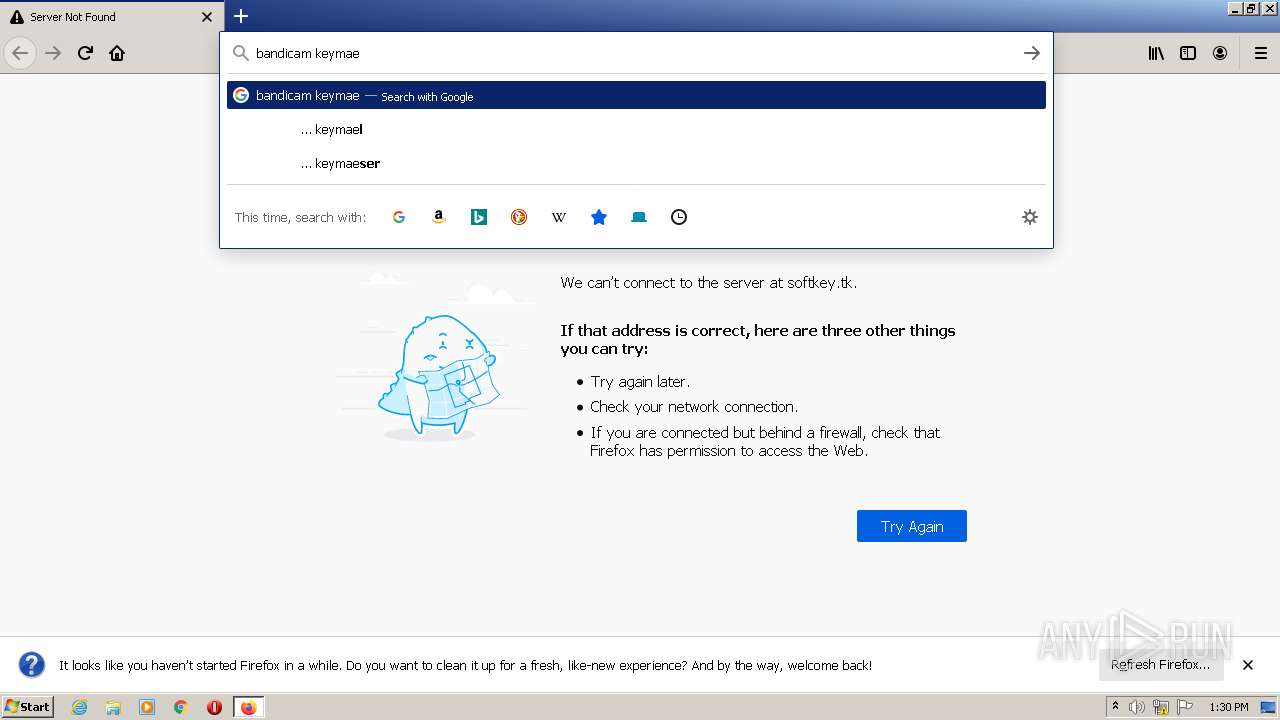
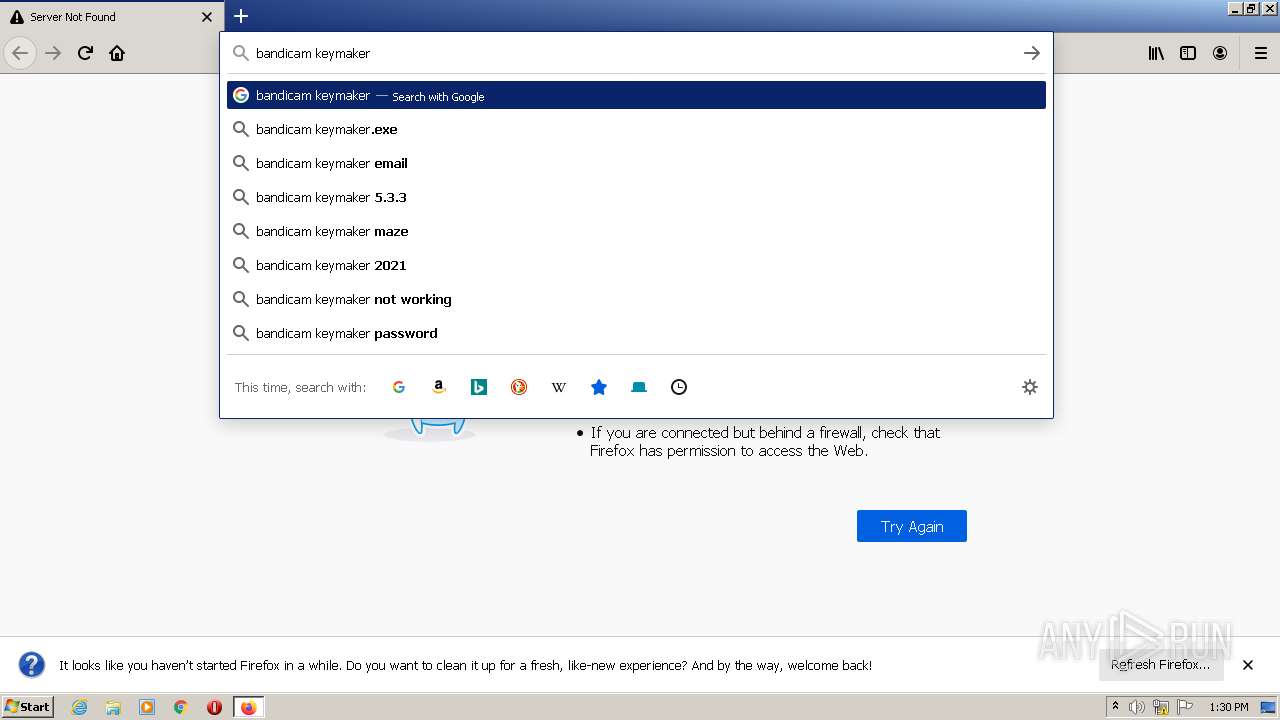
softkey.tk |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
3224 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
3224 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3224 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3224 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3224 | firefox.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
56 ETPRO signatures available at the full report