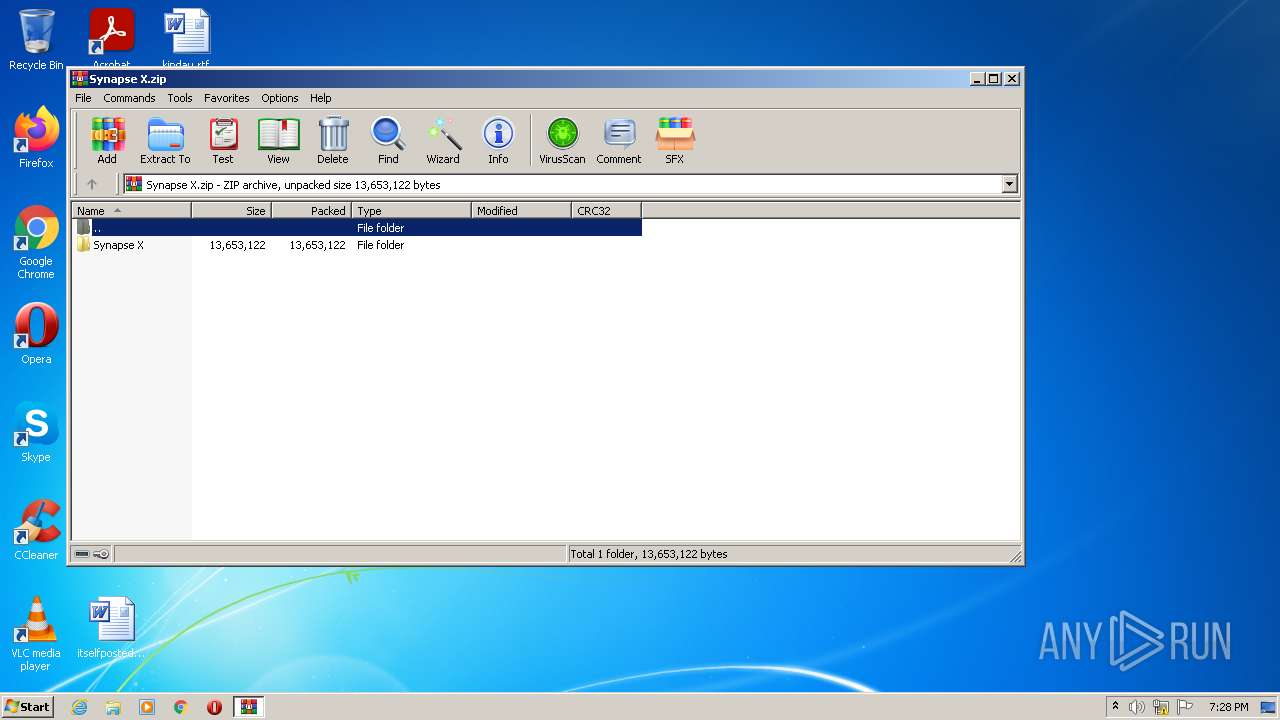
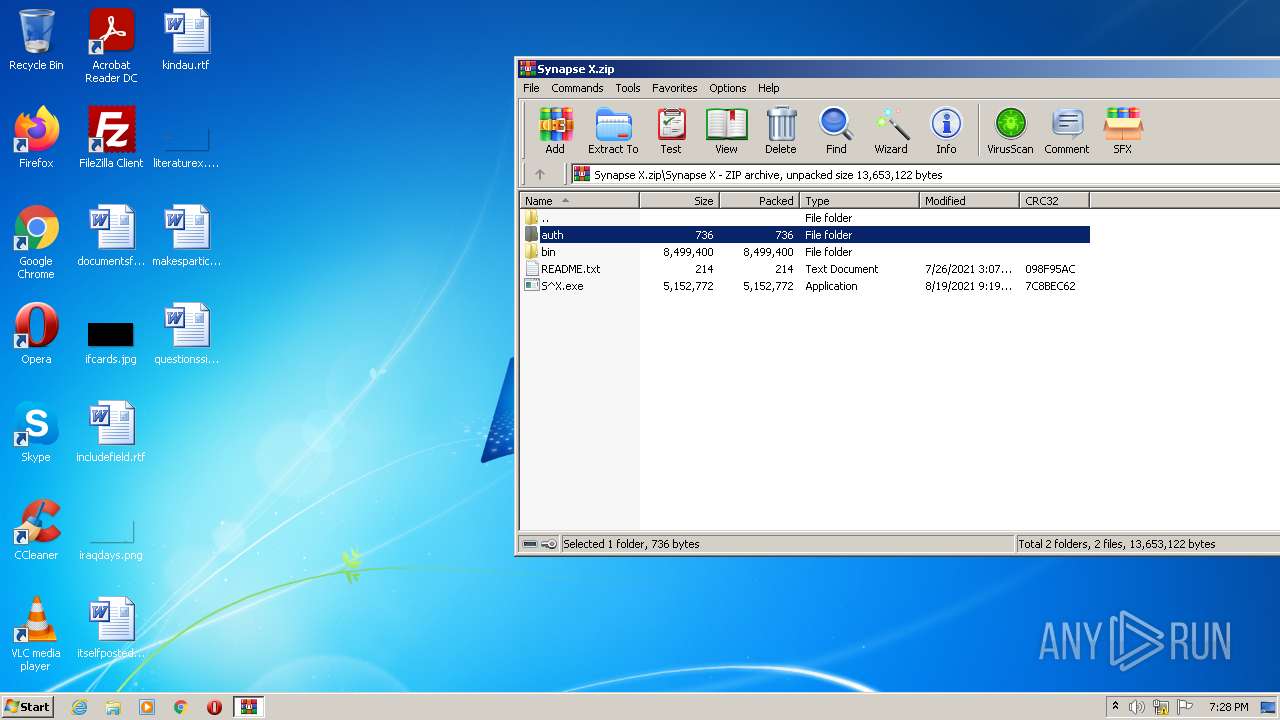
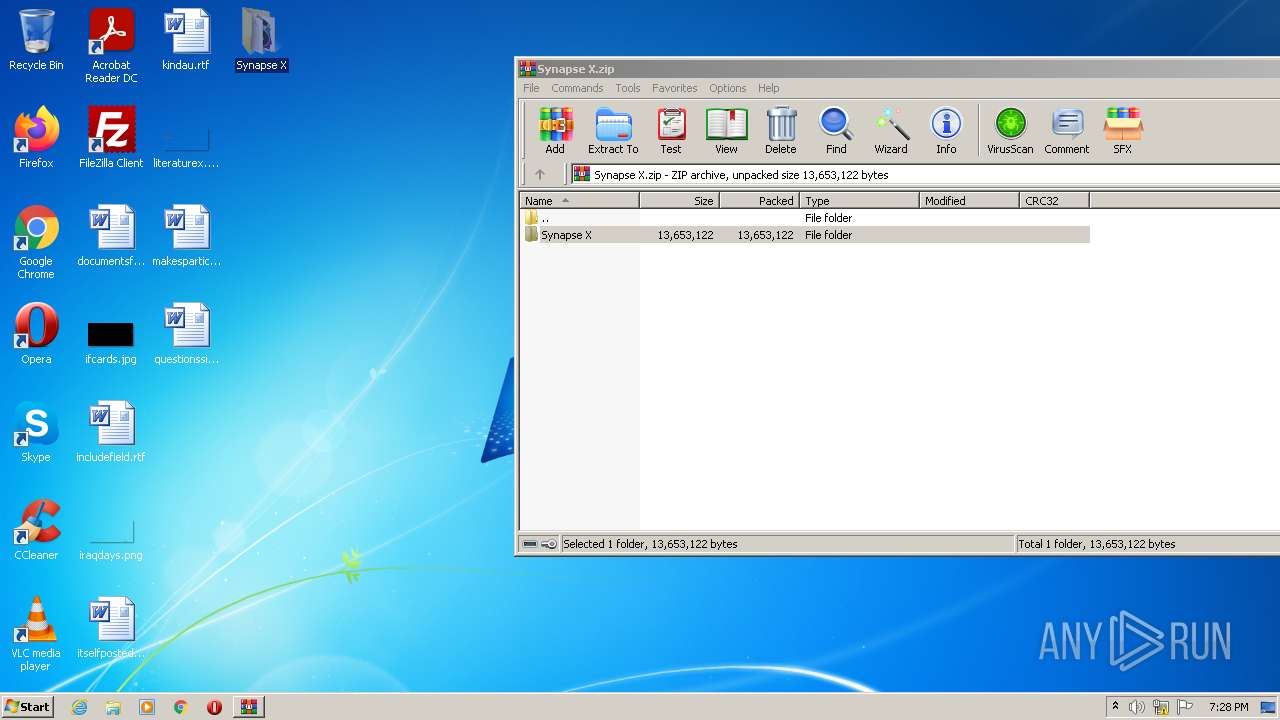
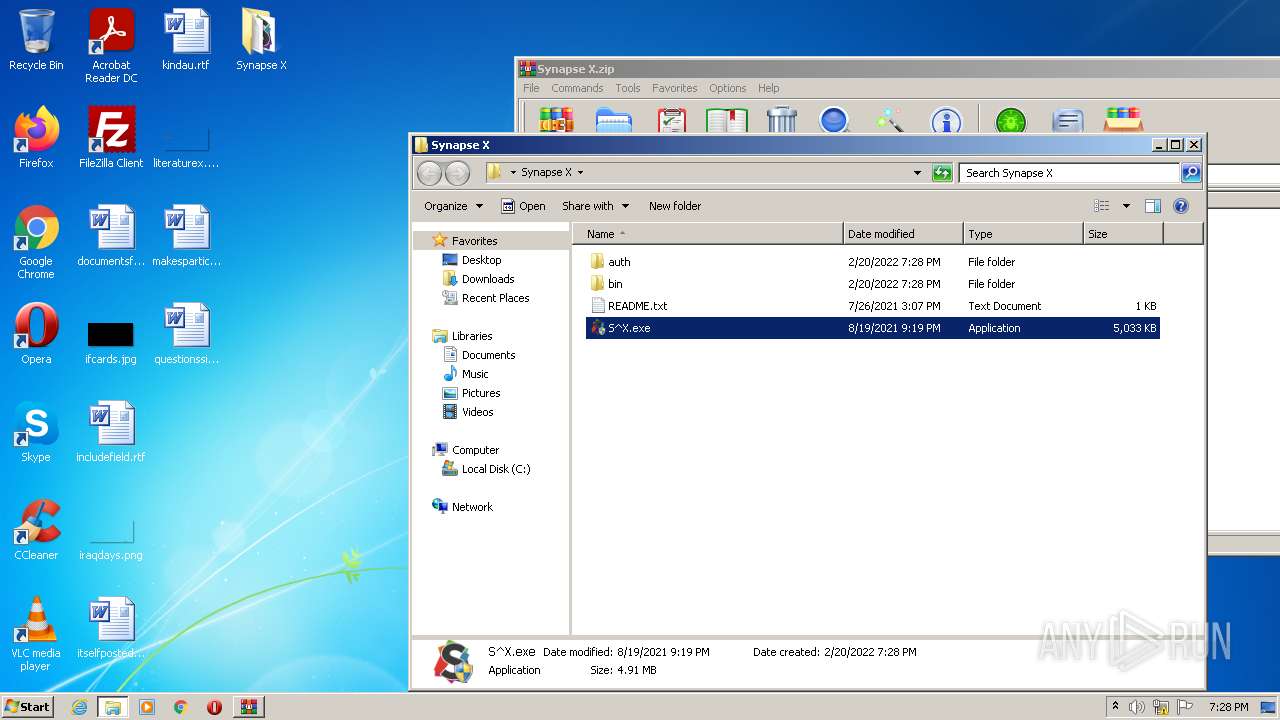
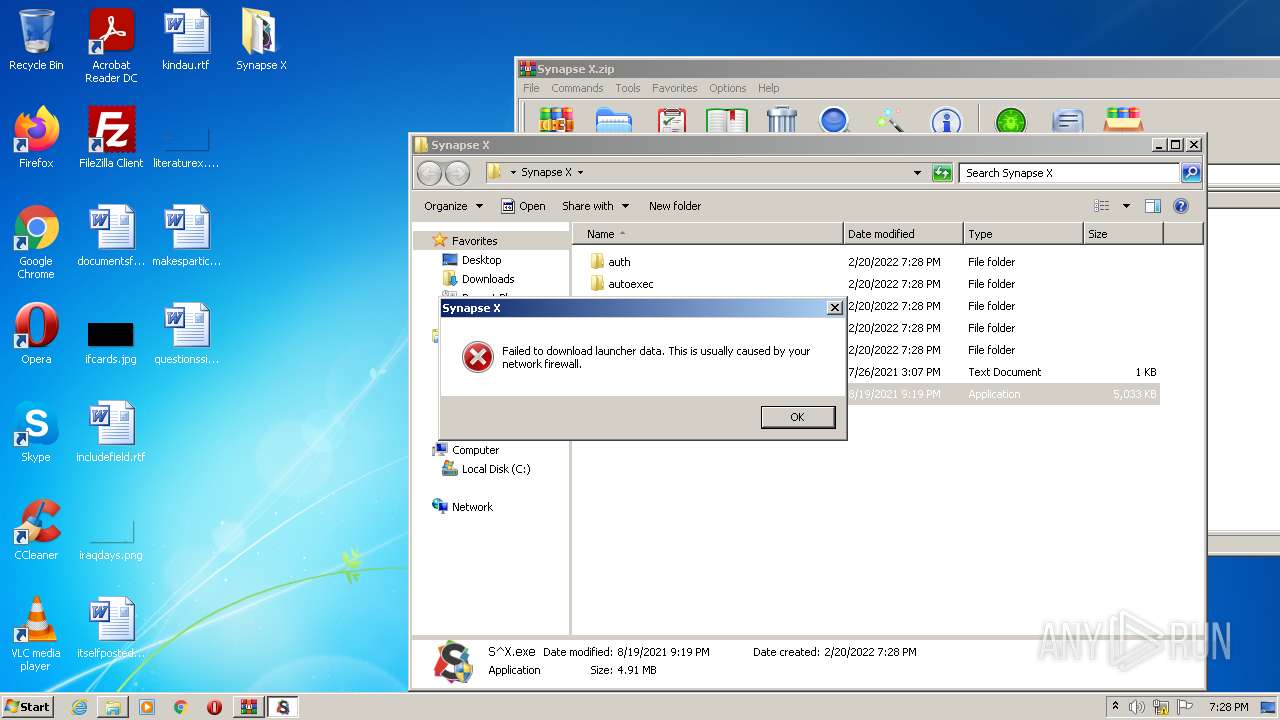
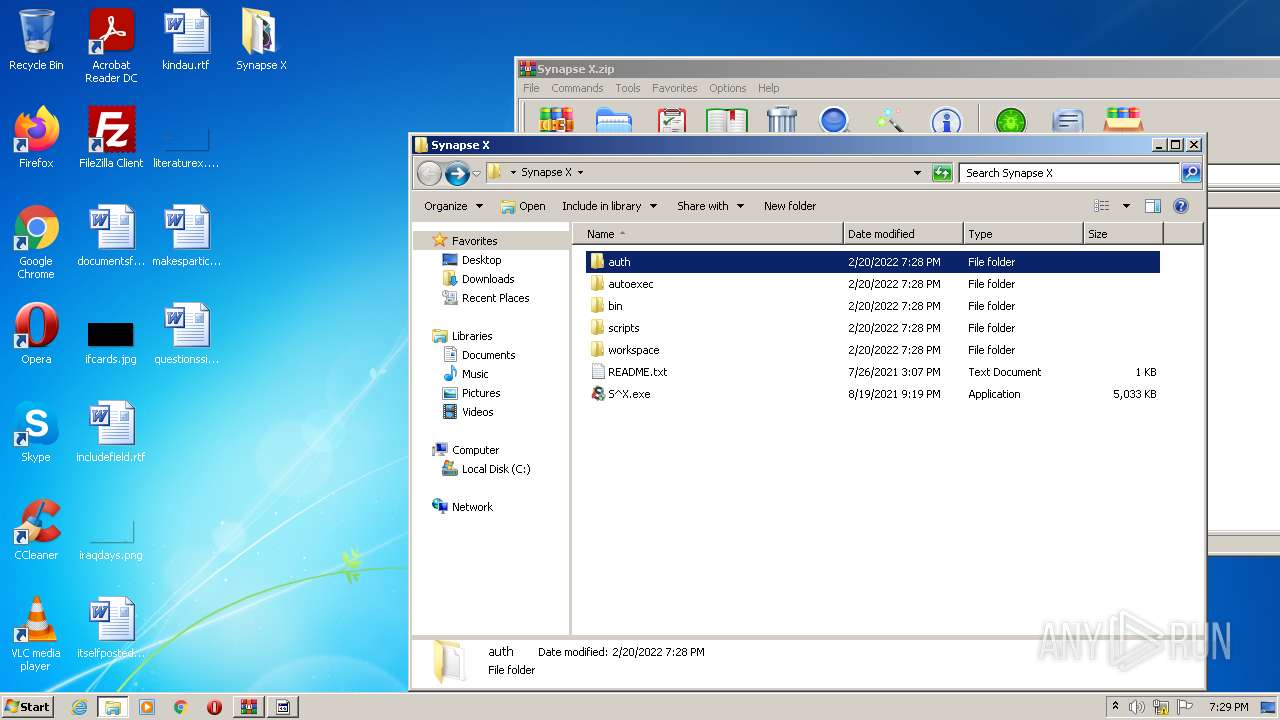
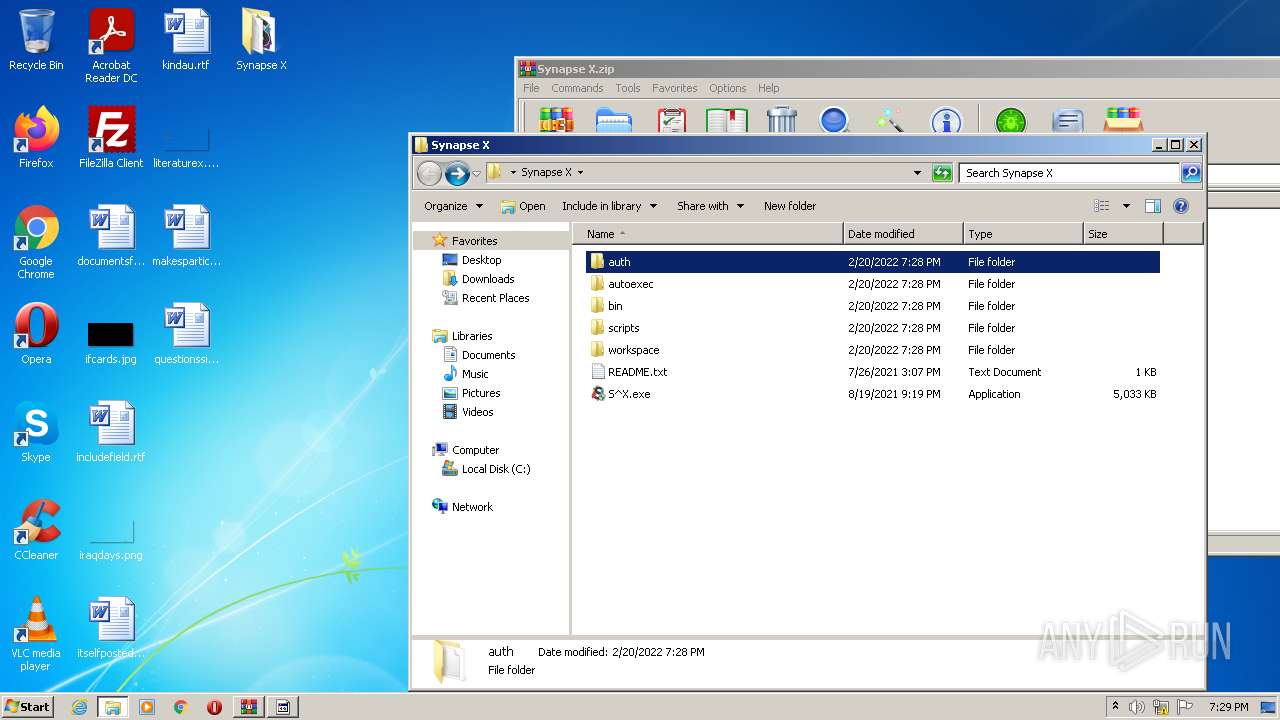
| File name: | Synapse X.zip |
| Full analysis: | https://app.any.run/tasks/ae32de07-a9ef-42c0-9d49-07e1f5879ed8 |
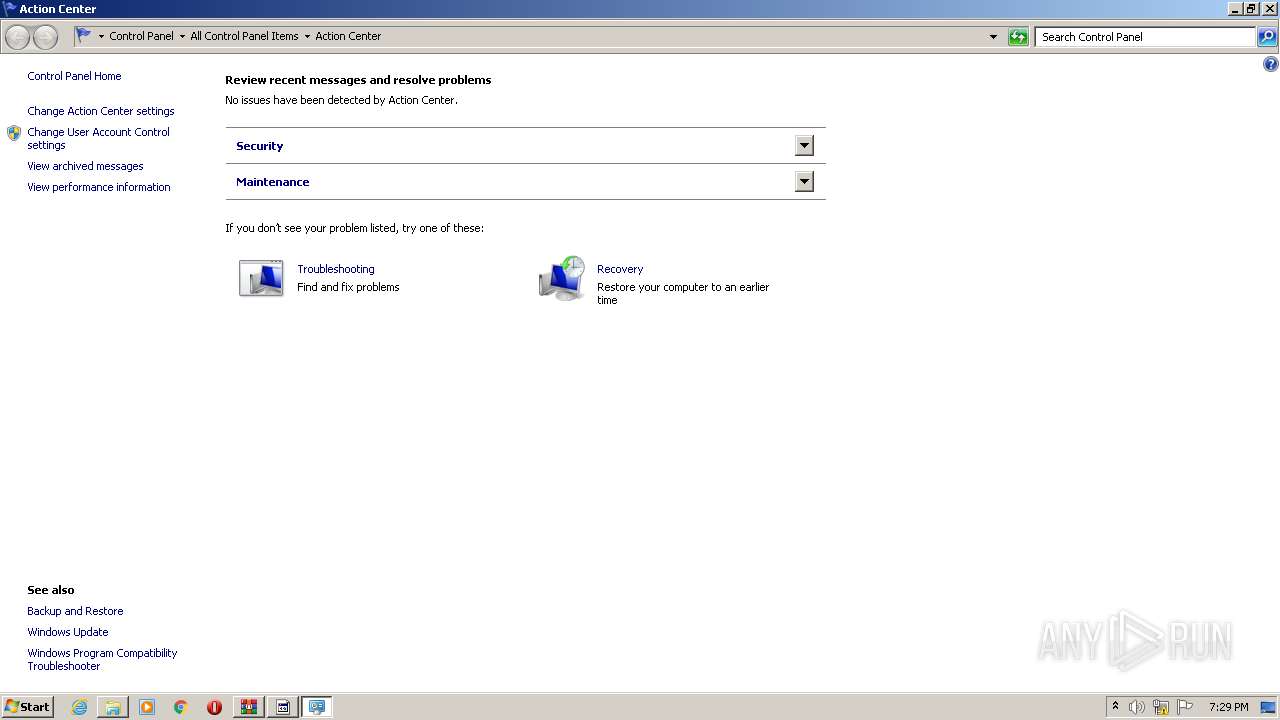
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | February 20, 2022, 19:28:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2FC9EF54A56BB388AFD2896224070F1A |
| SHA1: | 9D94EDA36D9CD554B7F729DFCCBA61EA347AB139 |
| SHA256: | 490ADDC4C2A529E49B1A65EC8F7ECF88056DE2BA3BA92F0033E1405BBA087735 |
| SSDEEP: | 393216:sD3eN6M/NUIhpzjHmPGOlPhFKHuu/enq3gE:S3eVUIhNjHm5pFjIGq3j |
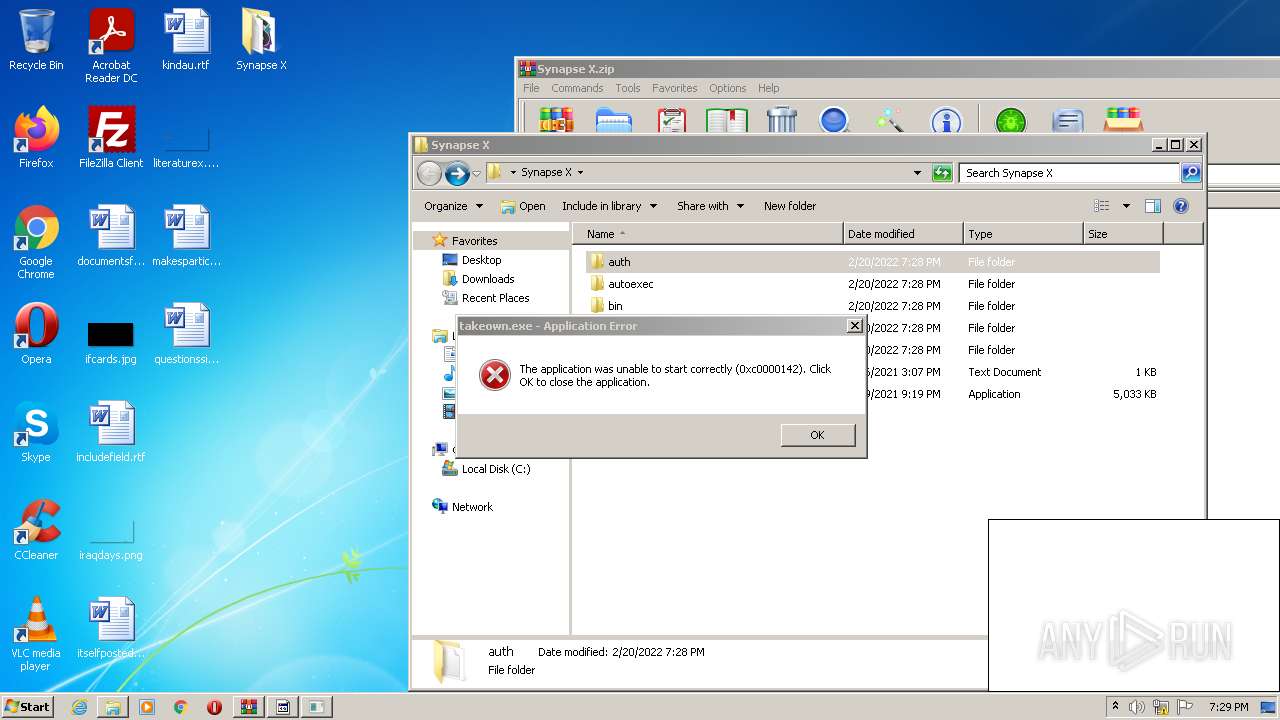
MALICIOUS
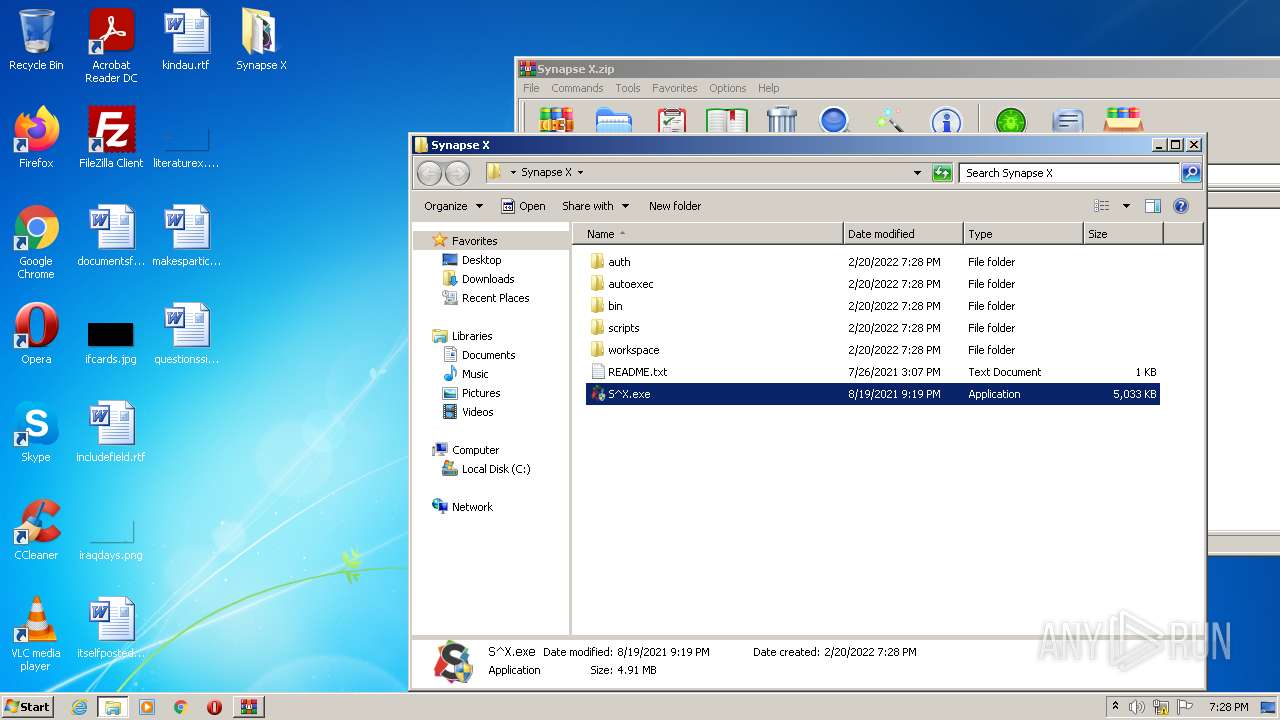
Application was dropped or rewritten from another process
- S^X.exe (PID: 3936)
- S^X.exe (PID: 2788)
- S^X.exe (PID: 1252)
- $77main1.exe (PID: 2232)
- $77Redownloader.exe (PID: 504)
- $77main1.exe (PID: 2196)
- S^X.exe (PID: 2276)
- S^X.exe (PID: 1468)
- S^X.exe (PID: 2472)
- $77Redownloader.exe (PID: 2876)
- $77Stellacy.exe (PID: 3140)
- $77STLR.exe (PID: 1468)
- RtkBtManServ.exe (PID: 3820)
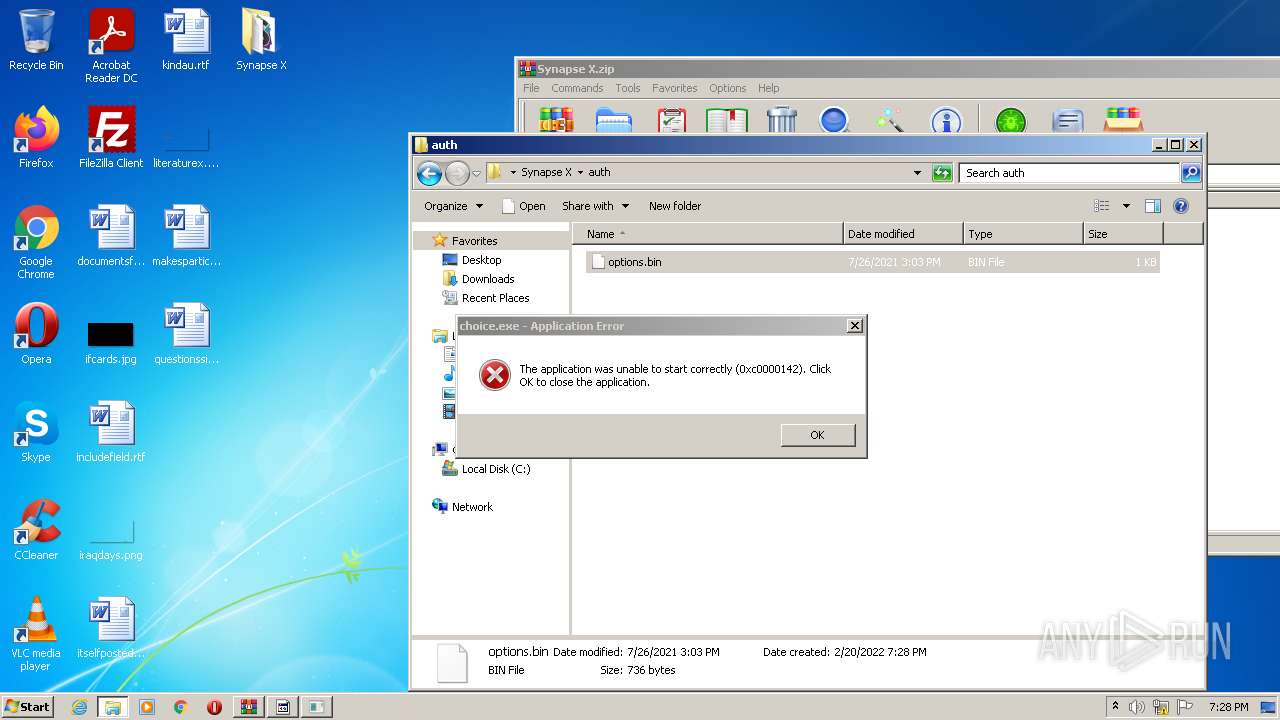
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3812)
Drops executable file immediately after starts
- S^X.exe (PID: 2788)
- $77Redownloader.exe (PID: 504)
- $77Redownloader.exe (PID: 2876)
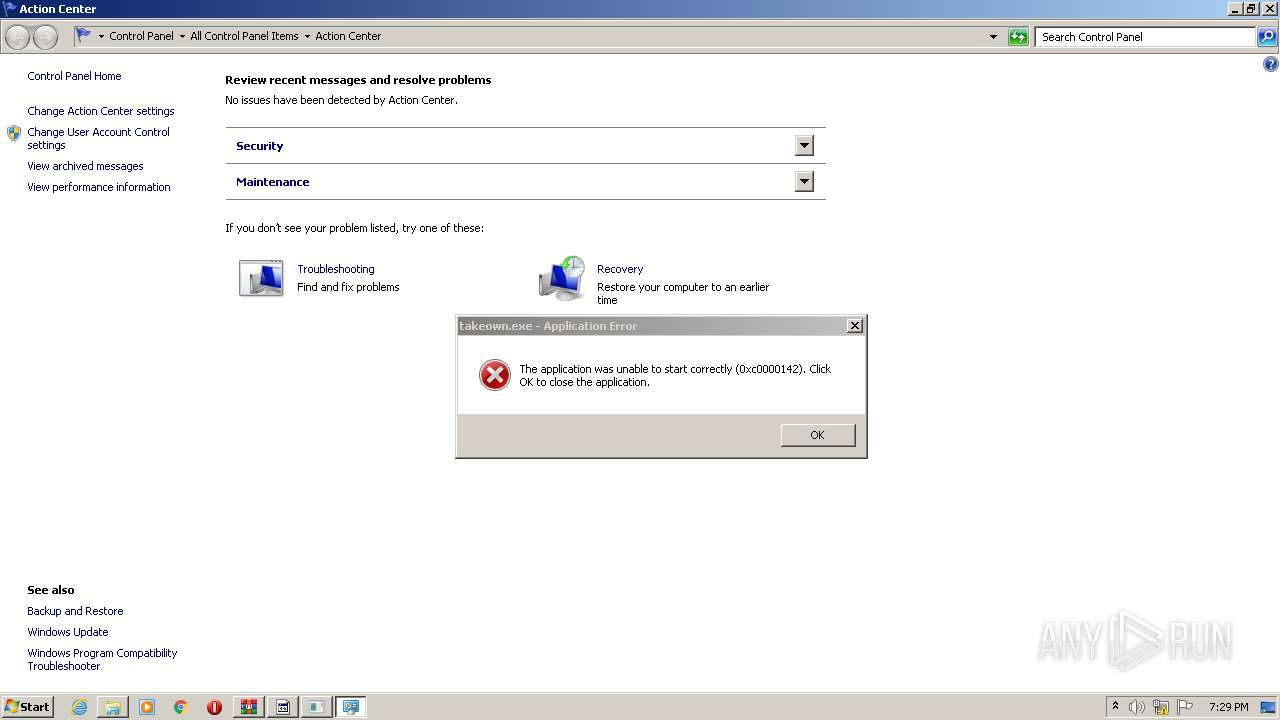
Executes PowerShell scripts
- cmd.exe (PID: 1740)
- cmd.exe (PID: 3692)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1740)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2276)
- schtasks.exe (PID: 504)
- schtasks.exe (PID: 2356)
- schtasks.exe (PID: 1012)
Uses Task Scheduler to autorun other applications
- $77Stellacy.exe (PID: 3140)
Stealing of credential data
- snuvcdsm.exe (PID: 3628)
Steals credentials from Web Browsers
- RtkBtManServ.exe (PID: 3820)
Actions looks like stealing of personal data
- RtkBtManServ.exe (PID: 3820)
QUASAR was detected
- $77Stellacy.exe (PID: 3140)
Uses NirSoft utilities to collect credentials
- snuvcdsm.exe (PID: 3628)
SUSPICIOUS
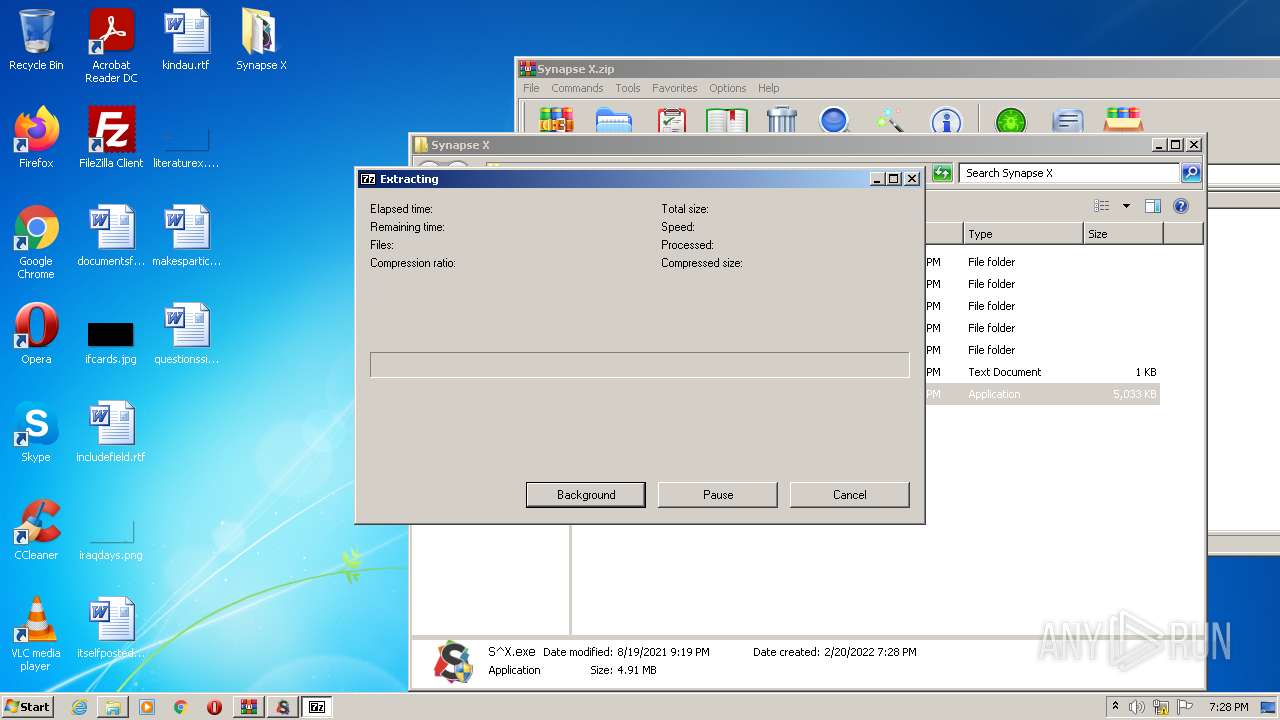
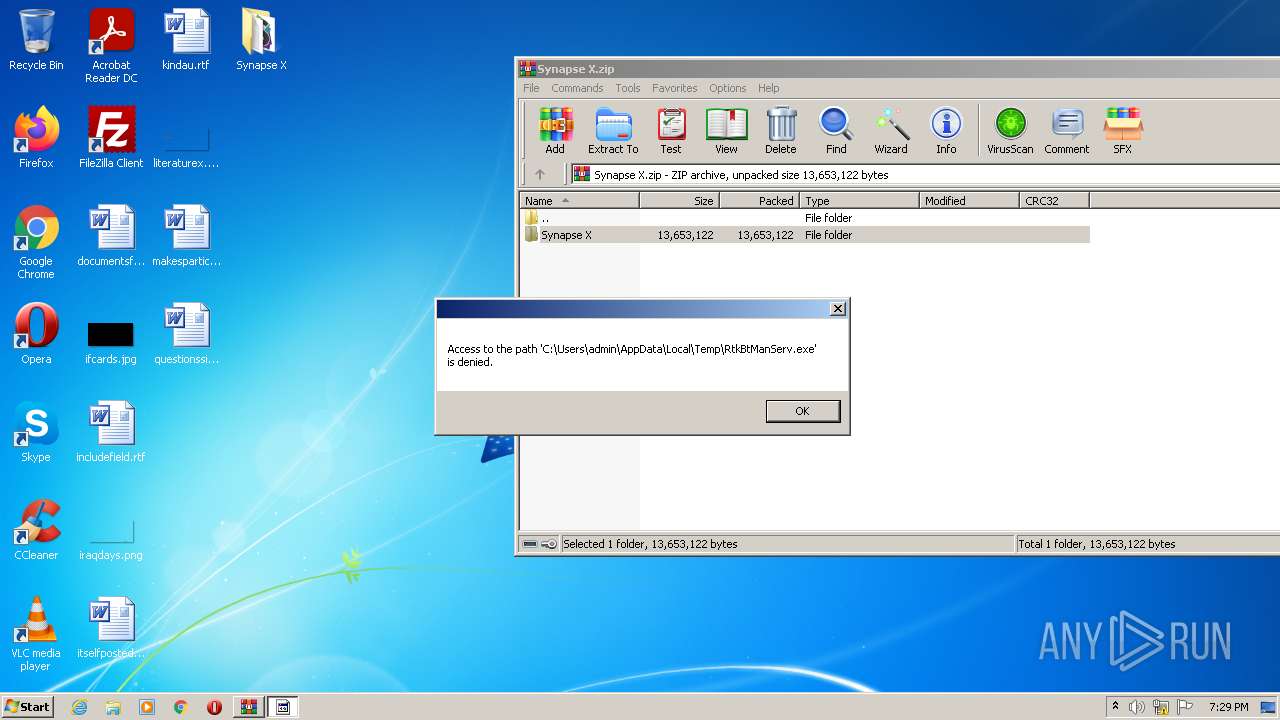
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3940)
- S^X.exe (PID: 2788)
- $77Redownloader.exe (PID: 504)
- $77STLR.exe (PID: 1468)
- RtkBtManServ.exe (PID: 3820)
- $77Redownloader.exe (PID: 2876)
Reads the computer name
- WinRAR.exe (PID: 3940)
- S^X.exe (PID: 2788)
- $77main1.exe (PID: 2196)
- S^X.exe (PID: 1252)
- powershell.exe (PID: 3344)
- S^X.exe (PID: 1468)
- powershell.exe (PID: 3836)
- $77main1.exe (PID: 2232)
- S^X.exe (PID: 2472)
- $77Stellacy.exe (PID: 3140)
- $77STLR.exe (PID: 1468)
- RtkBtManServ.exe (PID: 3820)
Checks supported languages
- WinRAR.exe (PID: 3940)
- $77main1.exe (PID: 2196)
- S^X.exe (PID: 2788)
- S^X.exe (PID: 1252)
- cmd.exe (PID: 1740)
- $77Redownloader.exe (PID: 504)
- powershell.exe (PID: 3344)
- S^X.exe (PID: 1468)
- cmd.exe (PID: 3692)
- powershell.exe (PID: 3836)
- $77main1.exe (PID: 2232)
- S^X.exe (PID: 2472)
- $77Redownloader.exe (PID: 2876)
- $77Stellacy.exe (PID: 3140)
- $77STLR.exe (PID: 1468)
- RtkBtManServ.exe (PID: 3820)
- WScript.exe (PID: 2992)
Starts CMD.EXE for commands execution
- $77main1.exe (PID: 2196)
- $77main1.exe (PID: 2232)
- WScript.exe (PID: 2992)
Drops a file that was compiled in debug mode
- $77Redownloader.exe (PID: 504)
- $77Redownloader.exe (PID: 2876)
- RtkBtManServ.exe (PID: 3820)
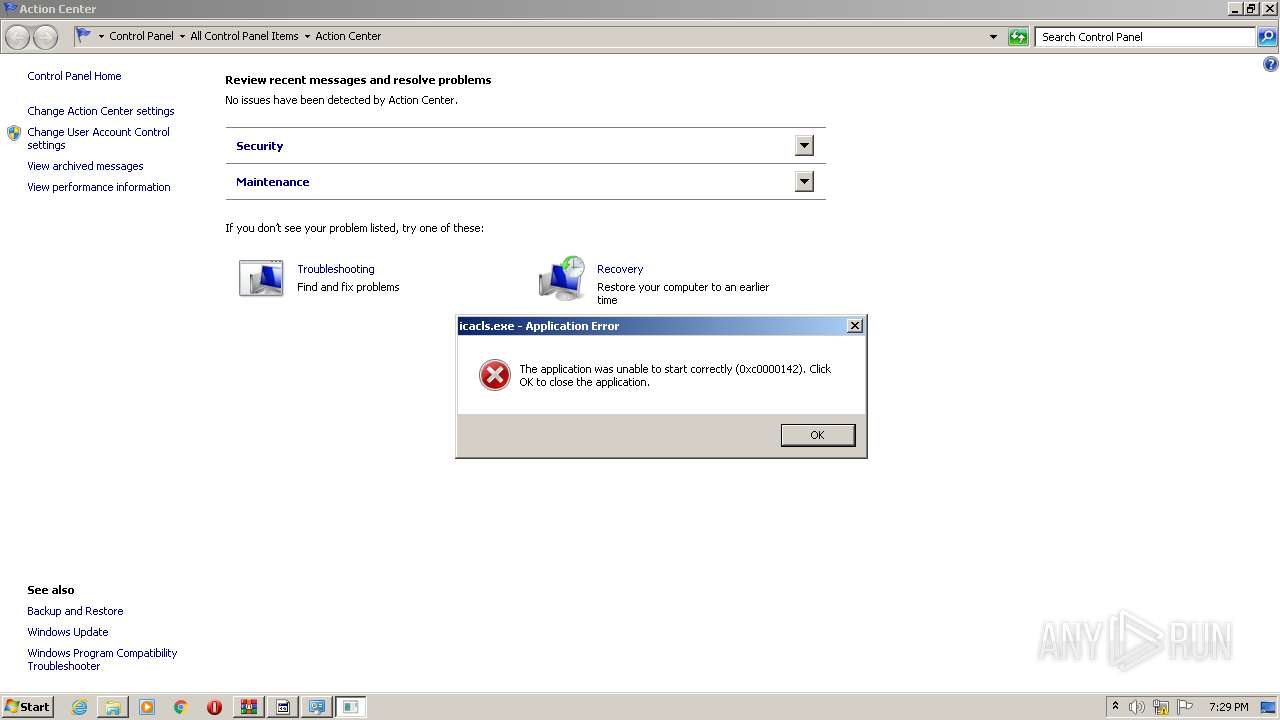
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1740)
- cmd.exe (PID: 3692)
Reads Environment values
- S^X.exe (PID: 1252)
- S^X.exe (PID: 2472)
- $77Stellacy.exe (PID: 3140)
- RtkBtManServ.exe (PID: 3820)
Reads the cookies of Mozilla Firefox
- RtkBtManServ.exe (PID: 3820)
Creates files in the user directory
- $77Stellacy.exe (PID: 3140)
Checks for external IP
- $77Stellacy.exe (PID: 3140)
Executes scripts
- RtkBtManServ.exe (PID: 3820)
INFO
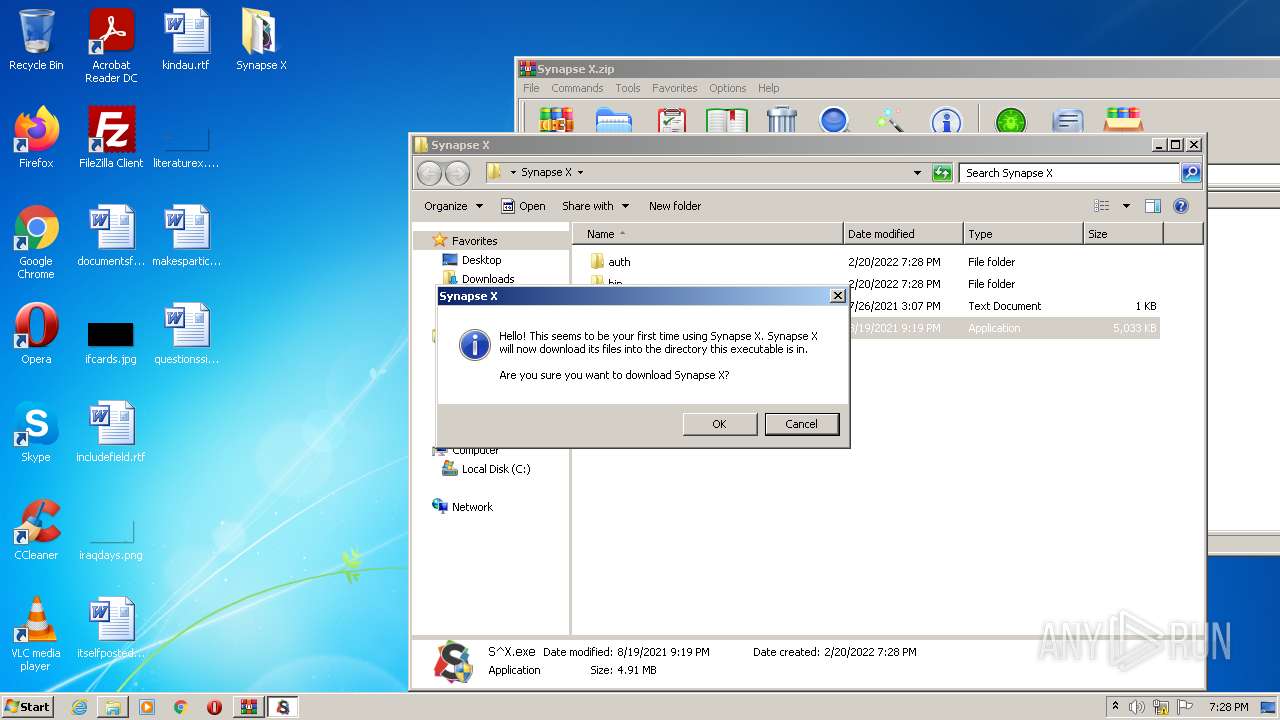
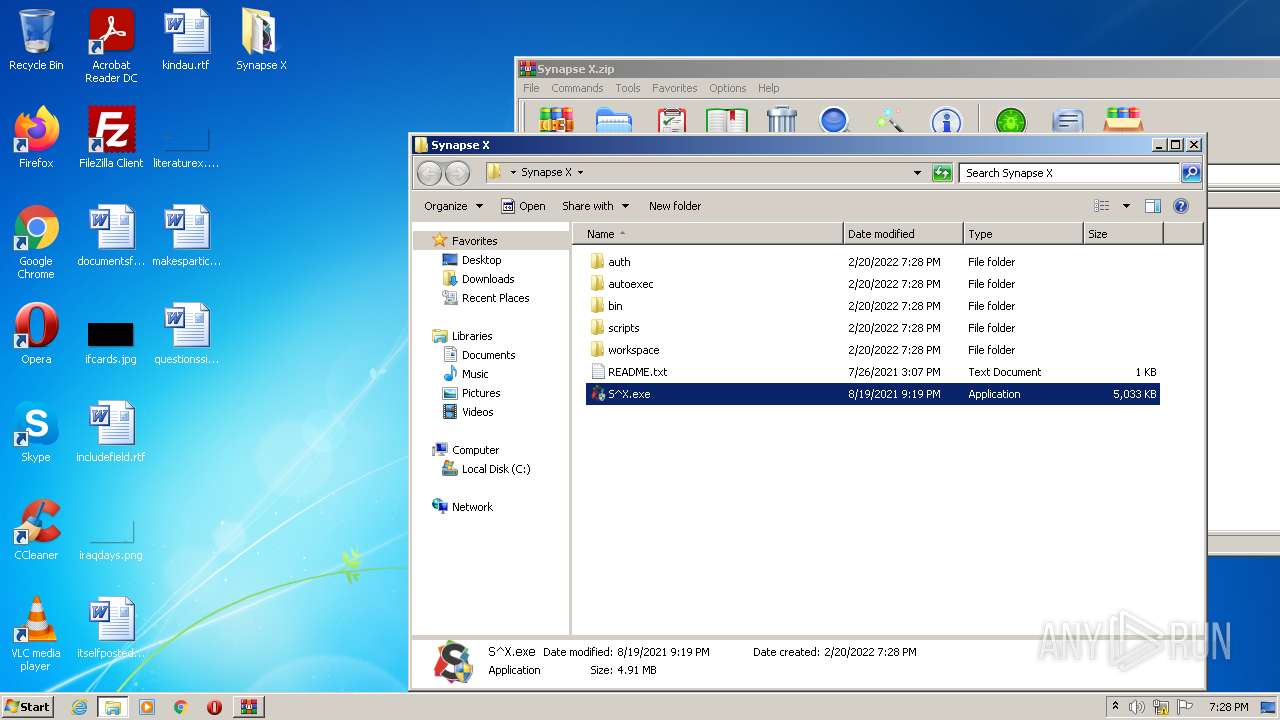
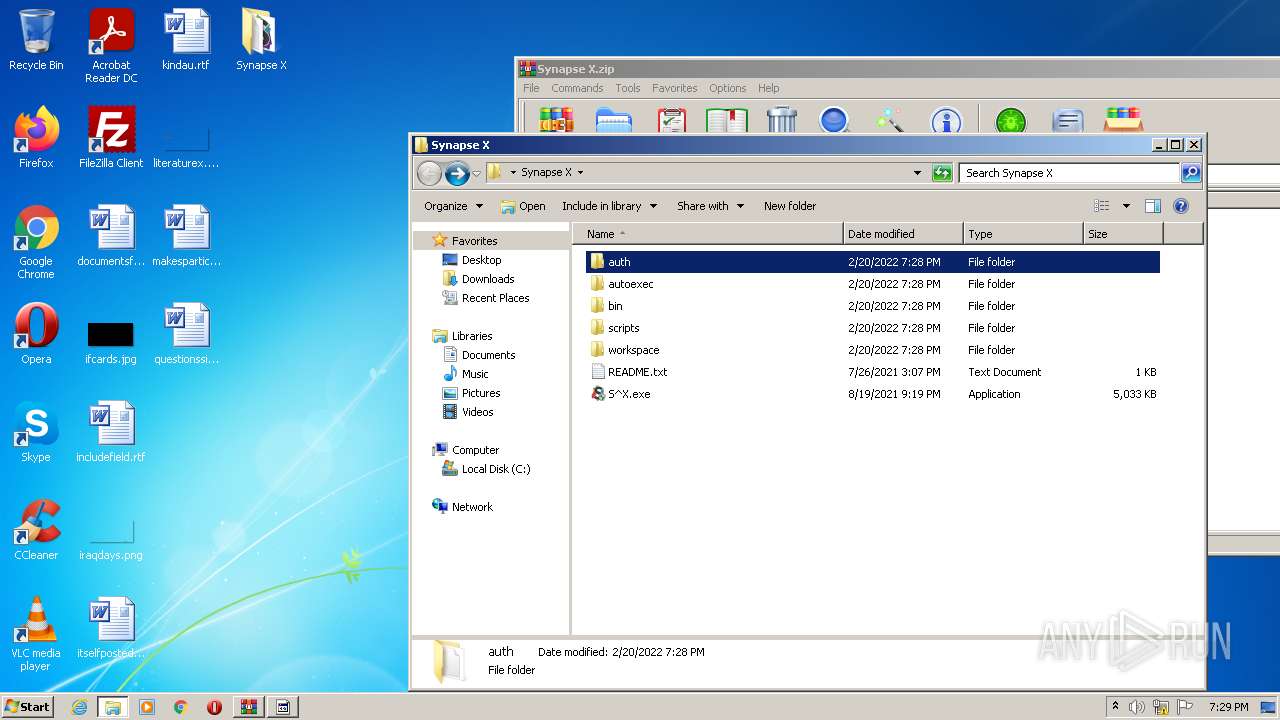
Manual execution by user
- S^X.exe (PID: 3936)
- S^X.exe (PID: 2788)
- S^X.exe (PID: 2276)
- S^X.exe (PID: 1468)
Checks Windows Trust Settings
- powershell.exe (PID: 3344)
- powershell.exe (PID: 3836)
Reads settings of System Certificates
- powershell.exe (PID: 3344)
- powershell.exe (PID: 3836)
- RtkBtManServ.exe (PID: 3820)
Checks supported languages
- reg.exe (PID: 3096)
- reg.exe (PID: 292)
- reg.exe (PID: 3508)
- reg.exe (PID: 2524)
- reg.exe (PID: 2756)
- reg.exe (PID: 2796)
- reg.exe (PID: 1636)
- reg.exe (PID: 2772)
- reg.exe (PID: 1588)
- timeout.exe (PID: 3304)
- reg.exe (PID: 2452)
- reg.exe (PID: 1492)
- reg.exe (PID: 2976)
- reg.exe (PID: 884)
- reg.exe (PID: 3360)
- reg.exe (PID: 3092)
- reg.exe (PID: 3672)
- reg.exe (PID: 3680)
- reg.exe (PID: 3676)
- timeout.exe (PID: 328)
- schtasks.exe (PID: 504)
- schtasks.exe (PID: 2276)
- schtasks.exe (PID: 2356)
- reg.exe (PID: 3956)
- reg.exe (PID: 2128)
- timeout.exe (PID: 3432)
- schtasks.exe (PID: 1012)
Reads the computer name
- schtasks.exe (PID: 2276)
- schtasks.exe (PID: 504)
- schtasks.exe (PID: 2356)
- schtasks.exe (PID: 1012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
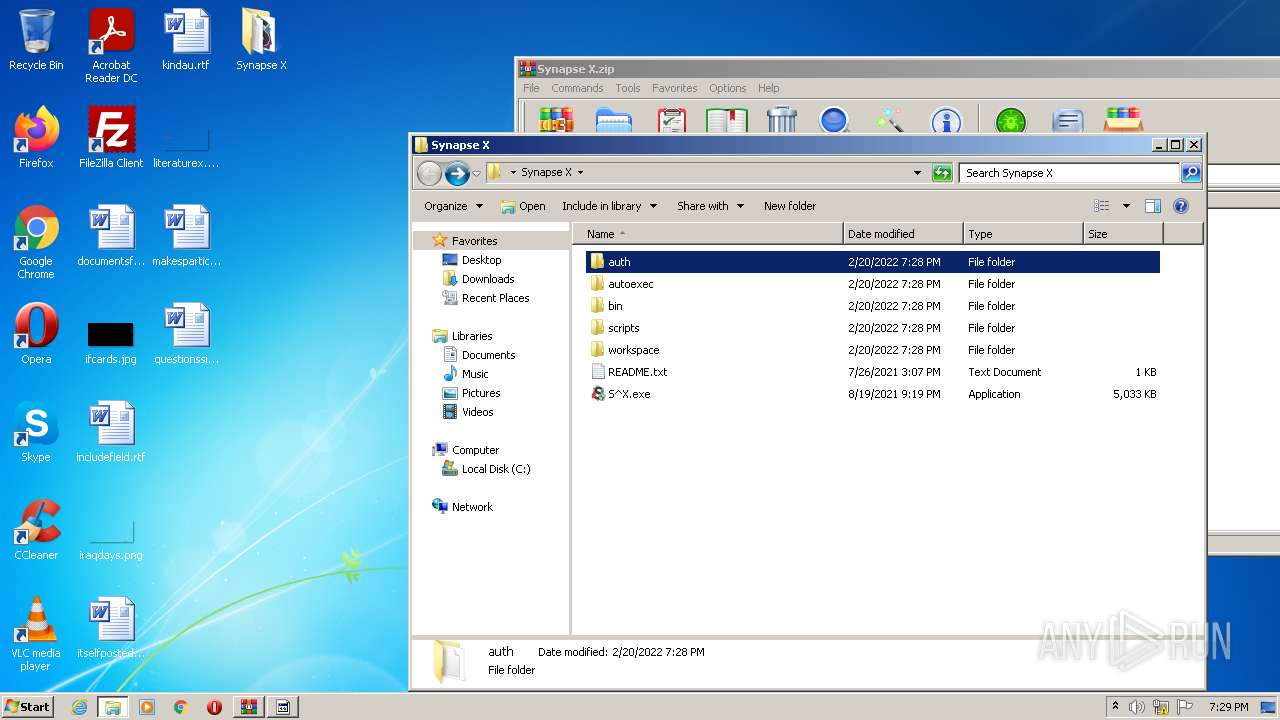
| ZipFileName: | Synapse X/README.txt |
|---|---|
| ZipUncompressedSize: | 214 |
| ZipCompressedSize: | 214 |
| ZipCRC: | 0x098f95ac |
| ZipModifyDate: | 2021:07:26 15:07:27 |
| ZipCompression: | None |
| ZipBitFlag: | 0x0808 |
| ZipRequiredVersion: | 20 |
Total processes
100
Monitored processes
54
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | Reg add "HKLM\SOFTWARE\Microsoft\Windows Defender Security Center\Notifications" /v "DisableNotifications" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | timeout 10 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 504 | "C:\Users\$77Redownloader.exe" -o"C:\Users\admin\AppData\Local\Microsoft\Windows" -y | C:\Users\$77Redownloader.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 504 | schtasks.exe /RU admin /create /tn "$77SX.job" /tr "'C:\Windows\System32\Wscript.exe'C:\Users\admin\AppData\Local\Microsoft\Windows\$77vbs.vbs" /sc minute /mo 40 /RL HIGHEST /f | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 884 | Reg add "HKLM\SOFTWARE\Microsoft\Windows Defender Security Center\Notifications" /v "DisableNotifications" /t REG_DWORD /d "1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "schtasks" /create /tn "$77Quasar.job" /sc ONLOGON /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\$77Stellacy.exe" /rl HIGHEST /f | C:\Windows\system32\schtasks.exe | — | $77Stellacy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\AppData\Local\Temp\S^X.exe" 0 | C:\Users\admin\AppData\Local\Temp\S^X.exe | S^X.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Synapse X Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\Desktop\Synapse X\S^X.exe" | C:\Users\admin\Desktop\Synapse X\S^X.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: Synapse X Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Microsoft\Windows\$77STLR.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\$77STLR.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1492 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Threats\ThreatIdDefaultAction" /v "2147735505" /t REG_SZ /d "6" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 082
Read events
16 899
Write events
183
Delete events
0
Modification events
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Synapse X.zip | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
23
Suspicious files
25
Text files
22
Unknown types
4
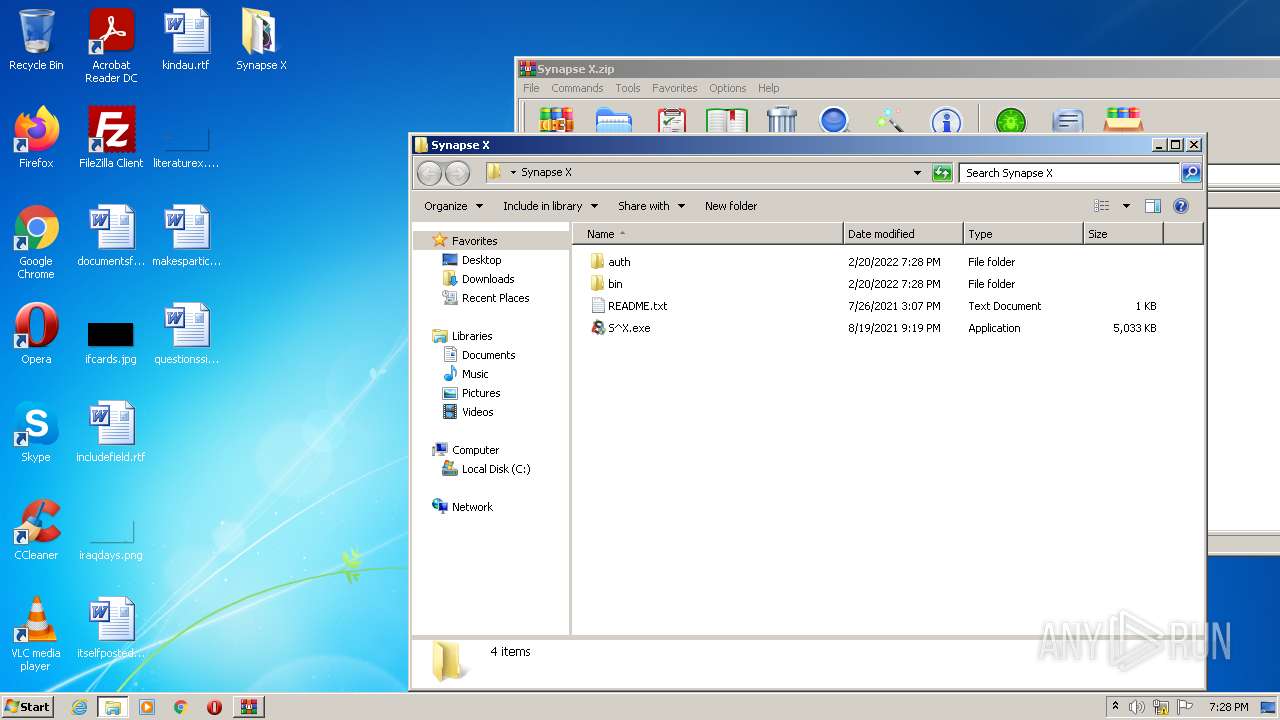
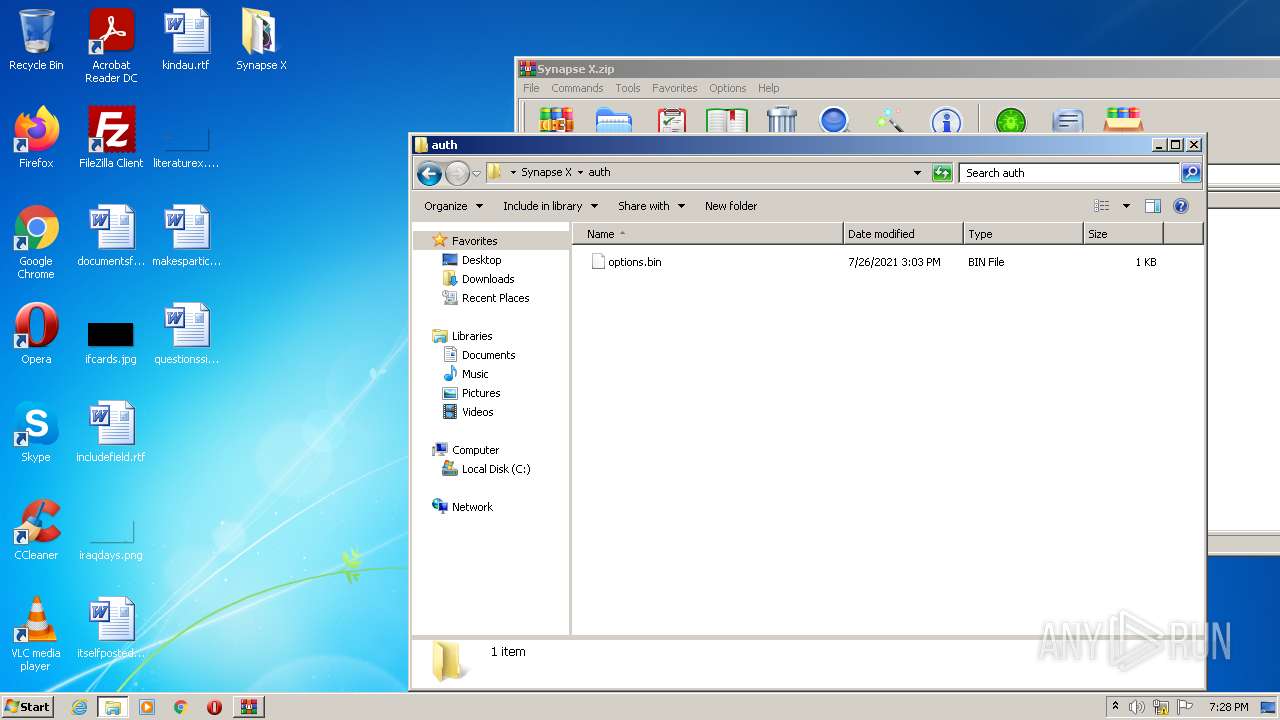
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3940.46150\Synapse X\README.txt | text | |
MD5:— | SHA256:— | |||
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3940.46150\Synapse X\bin\B7FbSSgf.bin | executable | |
MD5:— | SHA256:— | |||
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3940.46150\Synapse X\S^X.exe | executable | |
MD5:— | SHA256:— | |||
| 2788 | S^X.exe | C:\Users\admin\AppData\Local\Temp\S^X.exe | executable | |
MD5:— | SHA256:— | |||
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3940.46150\Synapse X\bin\theme-wpf.json | binary | |
MD5:F92E57A56C890DA7B29A80219EDA8B76 | SHA256:A55CF3C1A752CECCE303C97F08FEA682644297CDE884AFFB25849E2CB7B90A30 | |||
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3940.46150\Synapse X\bin\SynapseInjector.dll | executable | |
MD5:— | SHA256:— | |||
| 3940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3940.46150\Synapse X\auth\options.bin | text | |
MD5:— | SHA256:— | |||
| 3344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5ydrimrj.2gt.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3344 | powershell.exe | C:\Users\admin\AppData\Local\Temp\phcoj3jw.pby.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 504 | $77Redownloader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Backup.bat | text | |
MD5:73336BEE4FA2B1C3751FA012C9333A79 | SHA256:435662C5B86525B076AA25AA55F06AB2F41BF34BB032544C466FEAC53EA378B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
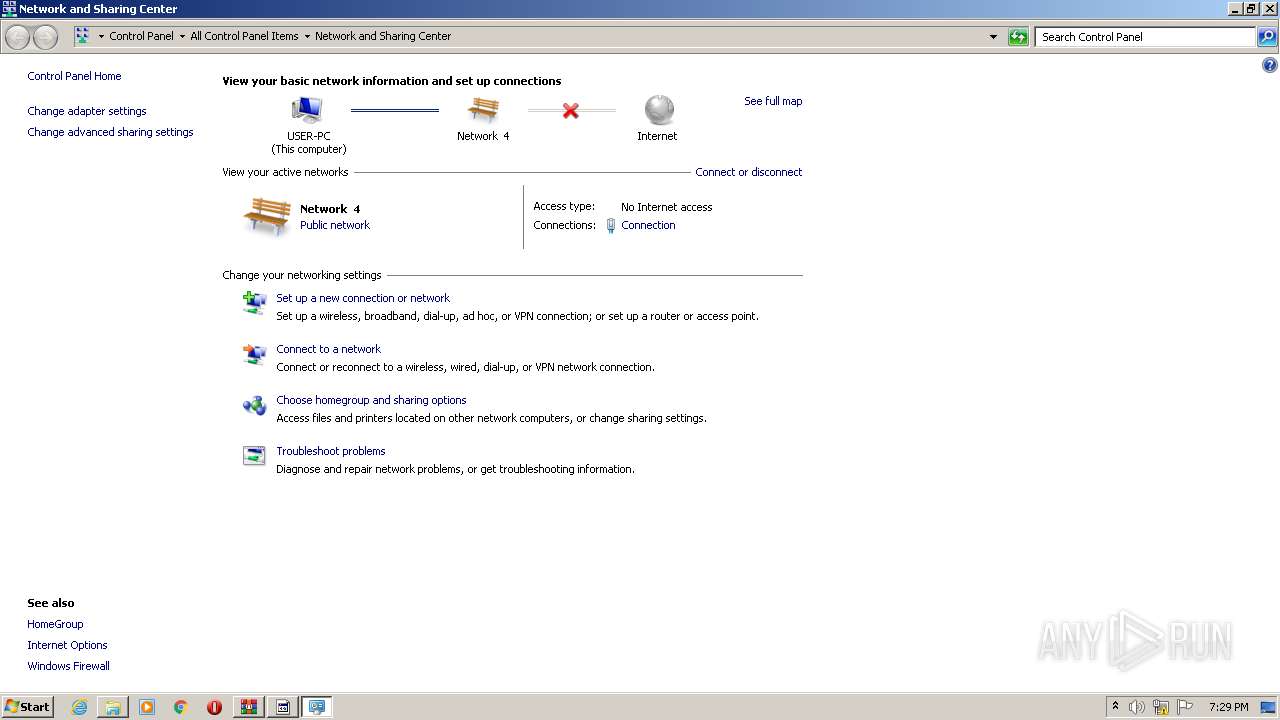
HTTP(S) requests
3
TCP/UDP connections
13
DNS requests
8
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | $77Stellacy.exe | GET | 404 | 3.232.242.170:80 | http://api.ipify.org/ | US | xml | 341 b | shared |
3140 | $77Stellacy.exe | GET | 404 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | xml | 341 b | malicious |
3140 | $77Stellacy.exe | GET | 404 | 172.67.75.176:80 | http://freegeoip.net/xml/ | US | xml | 341 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
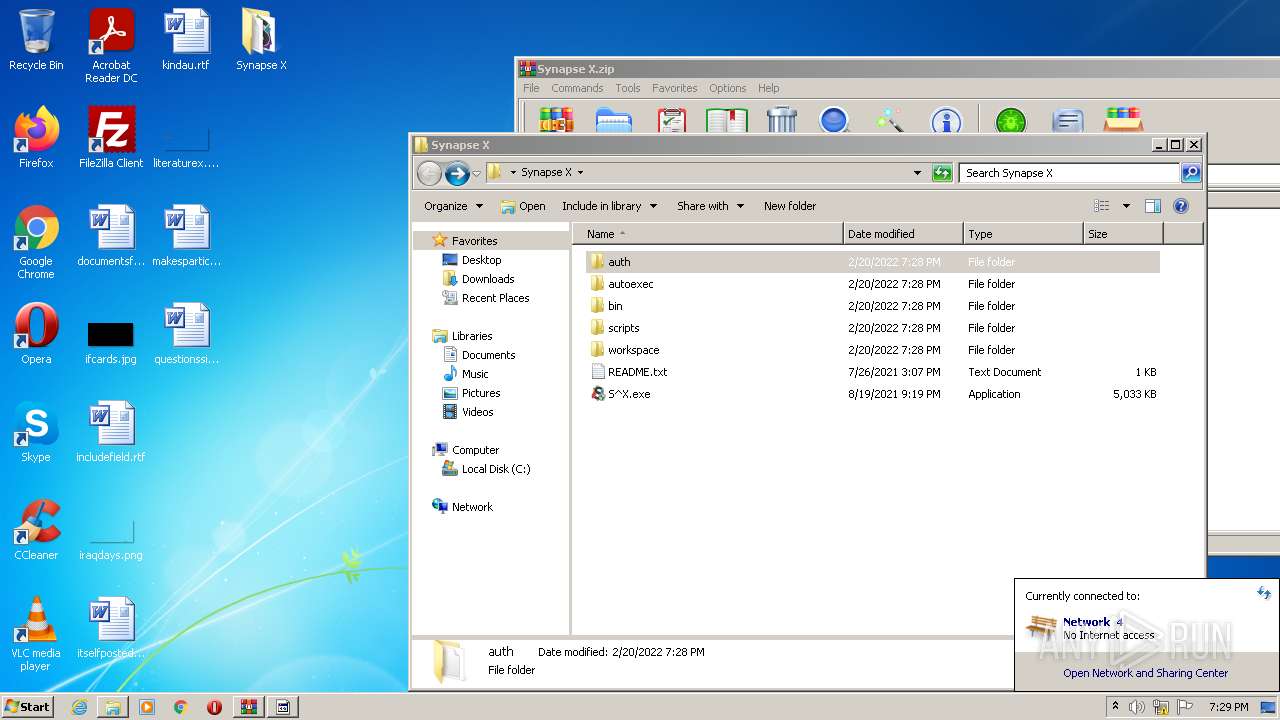
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
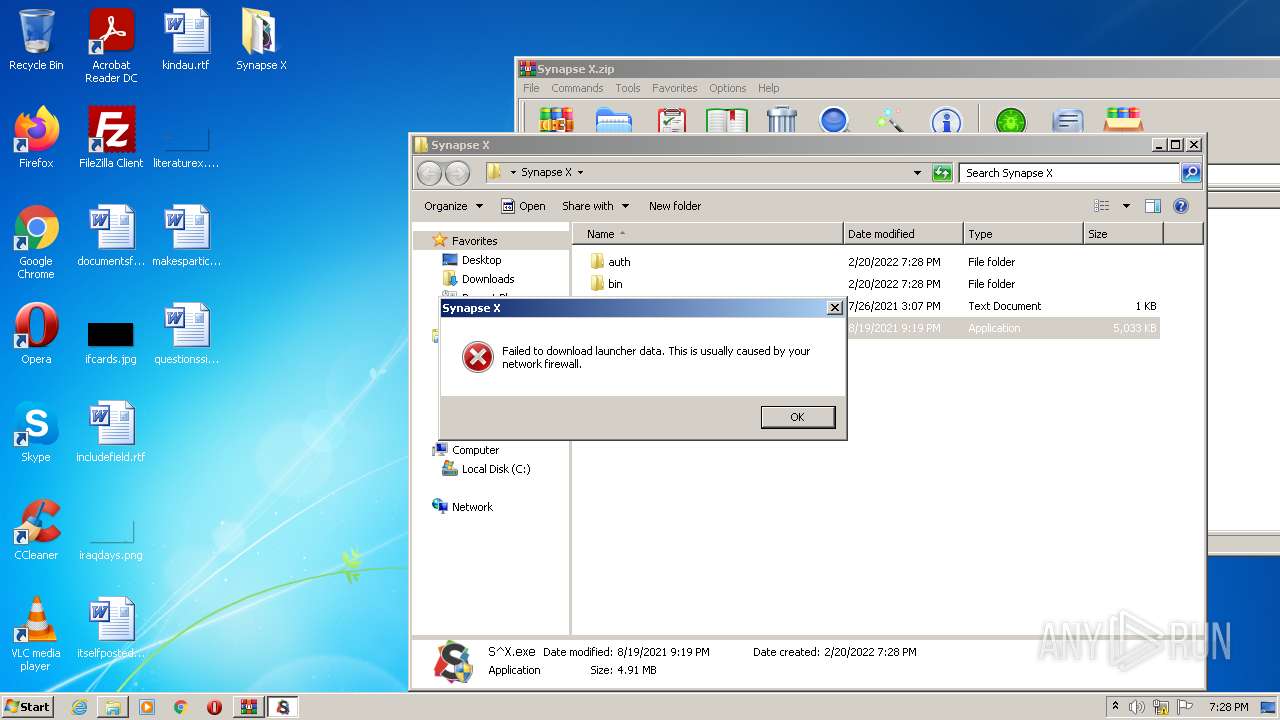
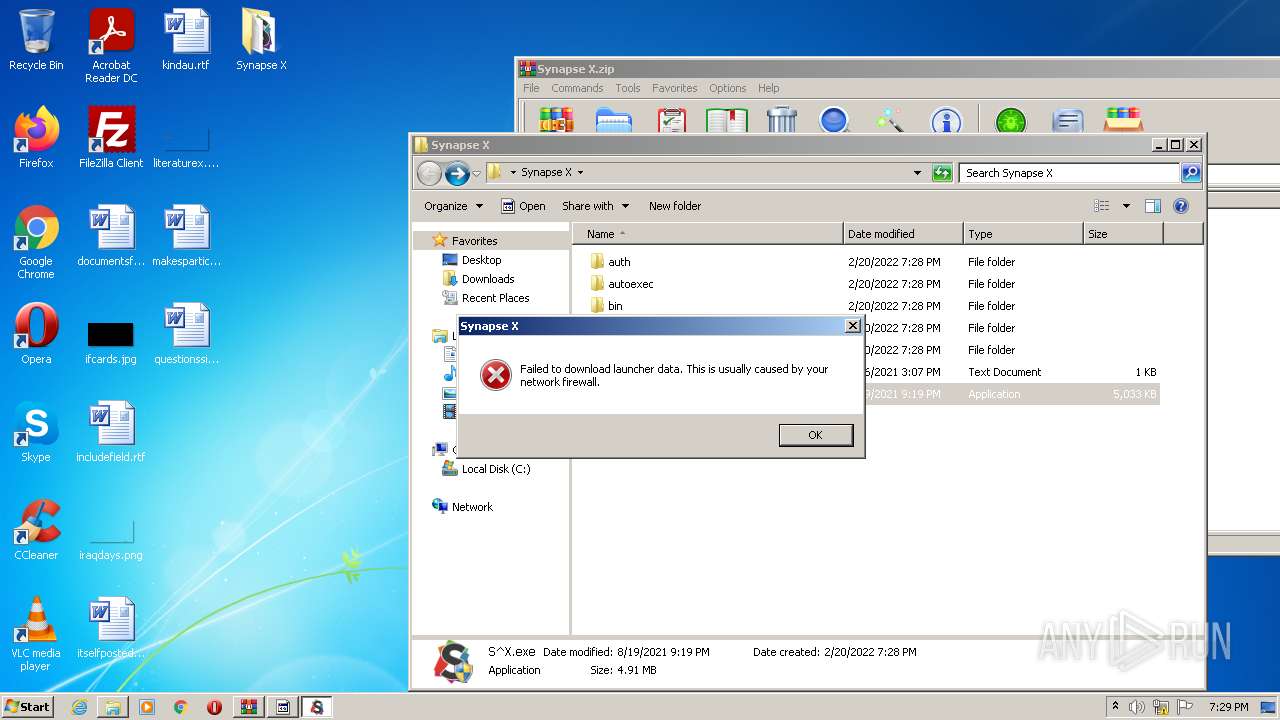
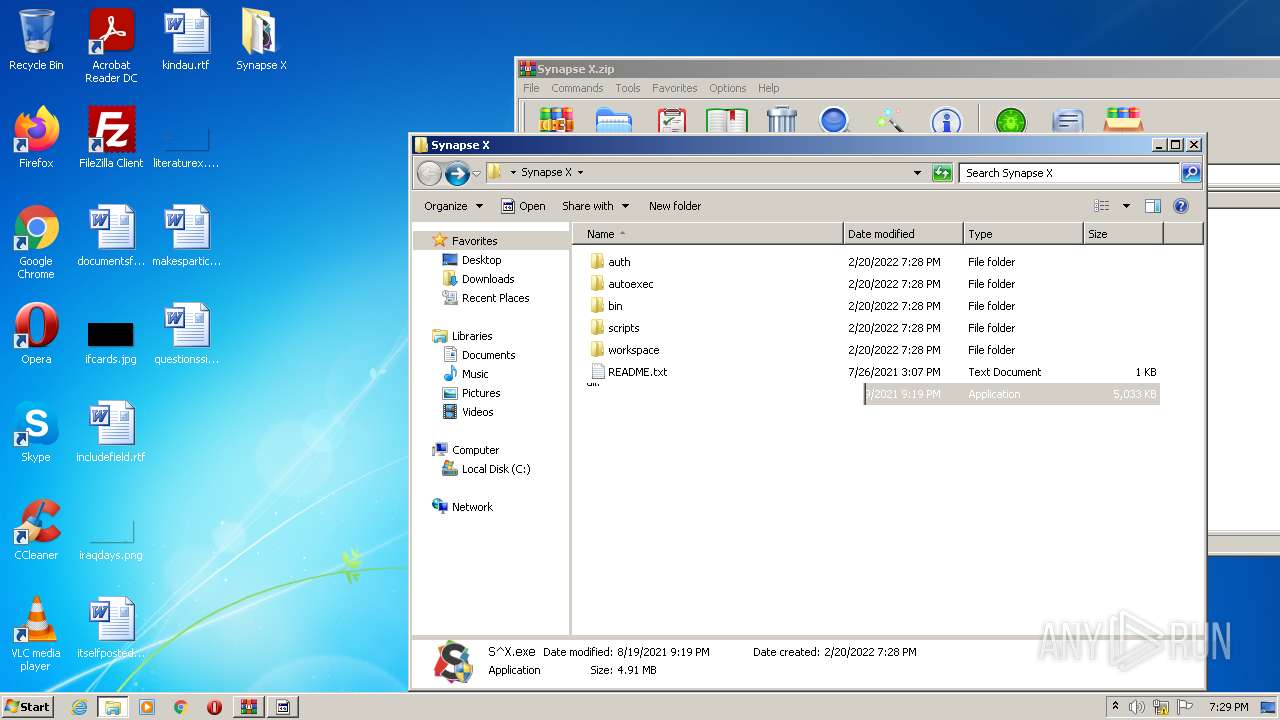
1252 | S^X.exe | 104.18.13.83:443 | synapse.to | Cloudflare Inc | US | suspicious |
2472 | S^X.exe | 104.18.13.83:443 | synapse.to | Cloudflare Inc | US | suspicious |
3140 | $77Stellacy.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
3140 | $77Stellacy.exe | 172.67.75.176:80 | freegeoip.net | — | US | malicious |
3140 | $77Stellacy.exe | 134.195.89.96:55562 | stellacy.duckdns.org | — | — | malicious |
3140 | $77Stellacy.exe | 3.232.242.170:80 | api.ipify.org | — | US | malicious |
3820 | RtkBtManServ.exe | 162.159.138.232:443 | discord.com | Cloudflare Inc | — | malicious |
— | — | 104.18.13.83:443 | synapse.to | Cloudflare Inc | US | suspicious |
— | — | 162.159.138.232:443 | discord.com | Cloudflare Inc | — | malicious |
— | — | 193.138.218.173:55562 | stellacy.ydns.eu | 31173 Services AB | SE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
synapse.to |
| whitelisted |
ip-api.com |
| malicious |
freegeoip.net |
| malicious |
api.ipify.org |
| shared |
stellacy.duckdns.org |
| unknown |
itroublvehacker.gq |
| whitelisted |
discord.com |
| whitelisted |
stellacy.ydns.eu |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
3140 | $77Stellacy.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3140 | $77Stellacy.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3140 | $77Stellacy.exe | A Network Trojan was detected | ET TROJAN W32/Quasar 1.3/Venom RAT Connectivity Check 3 |
3140 | $77Stellacy.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
7 ETPRO signatures available at the full report