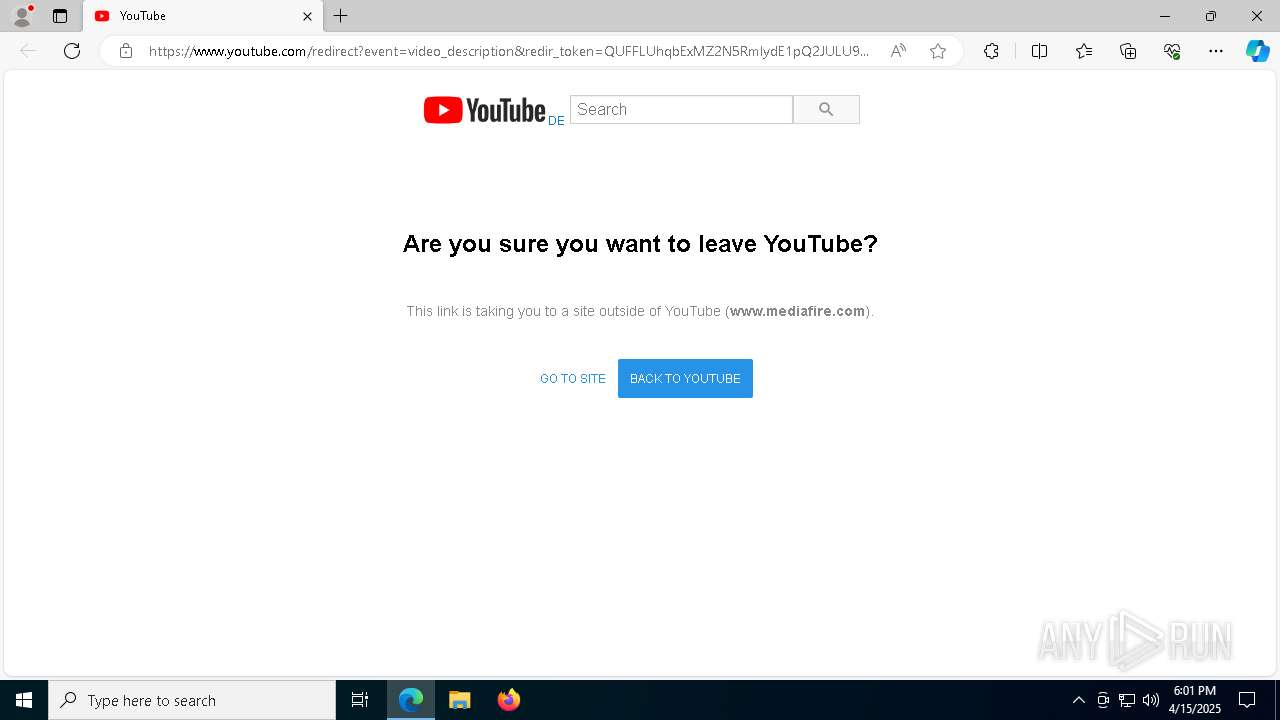
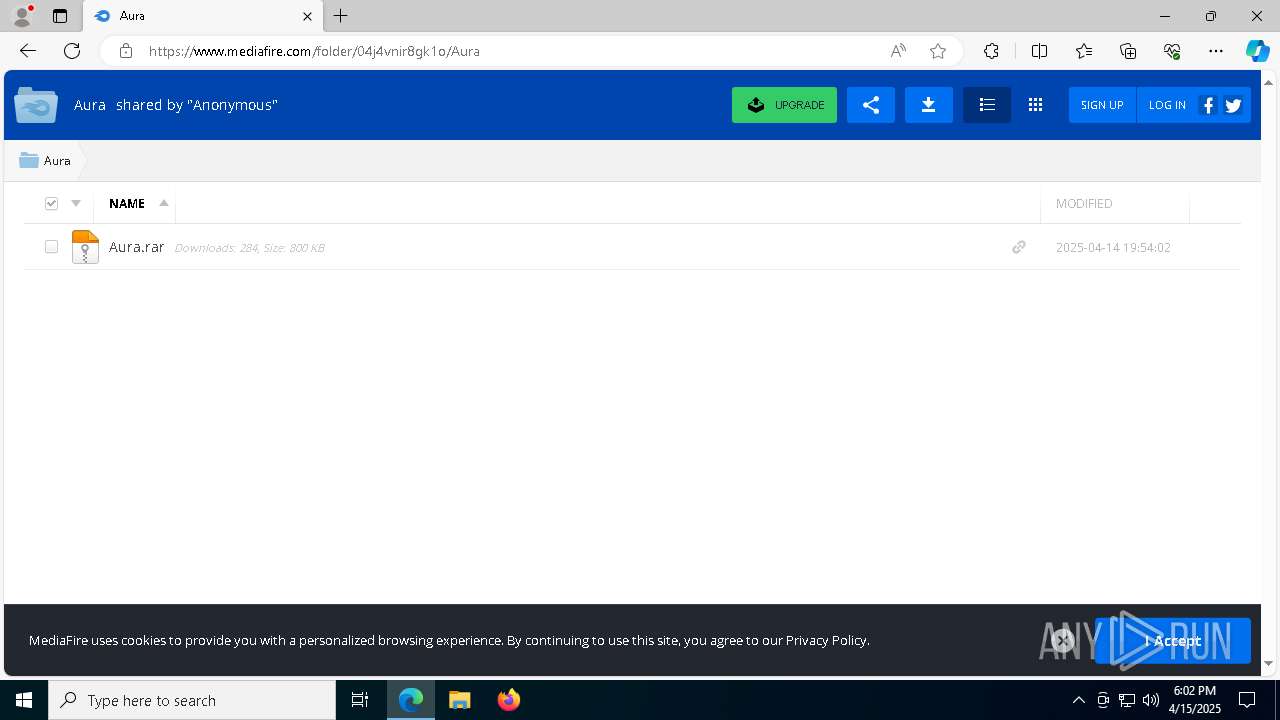
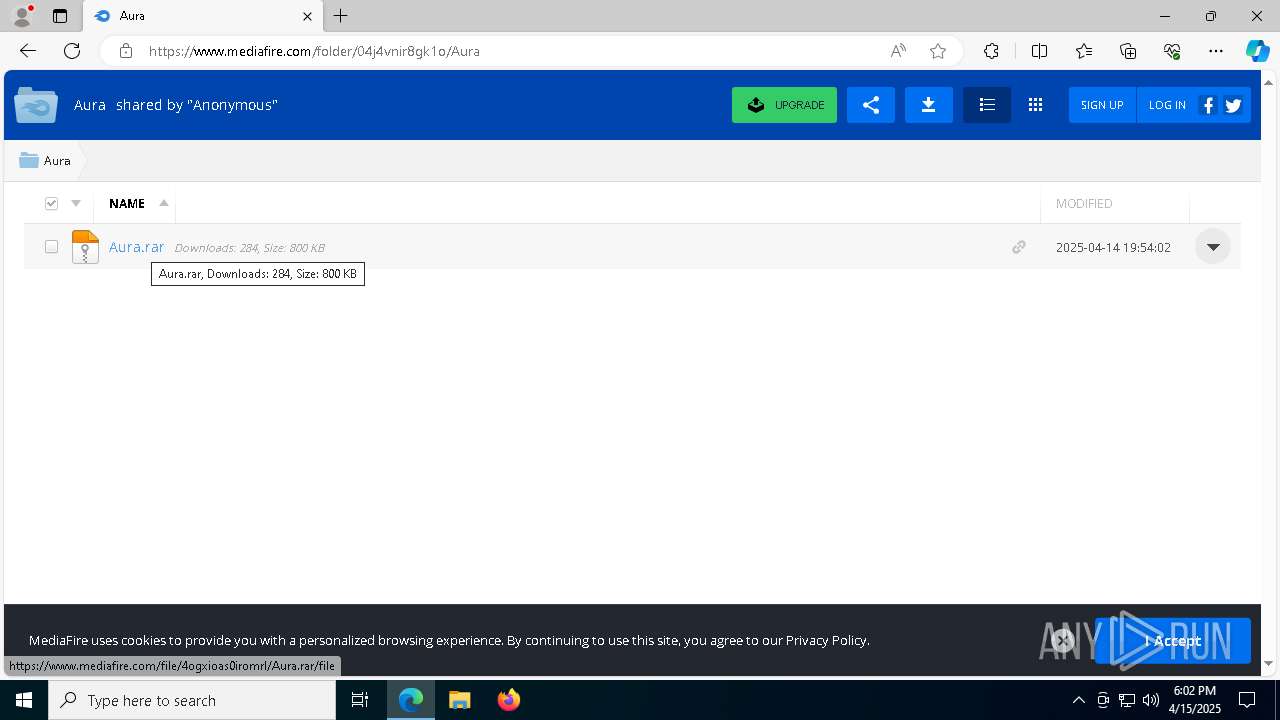
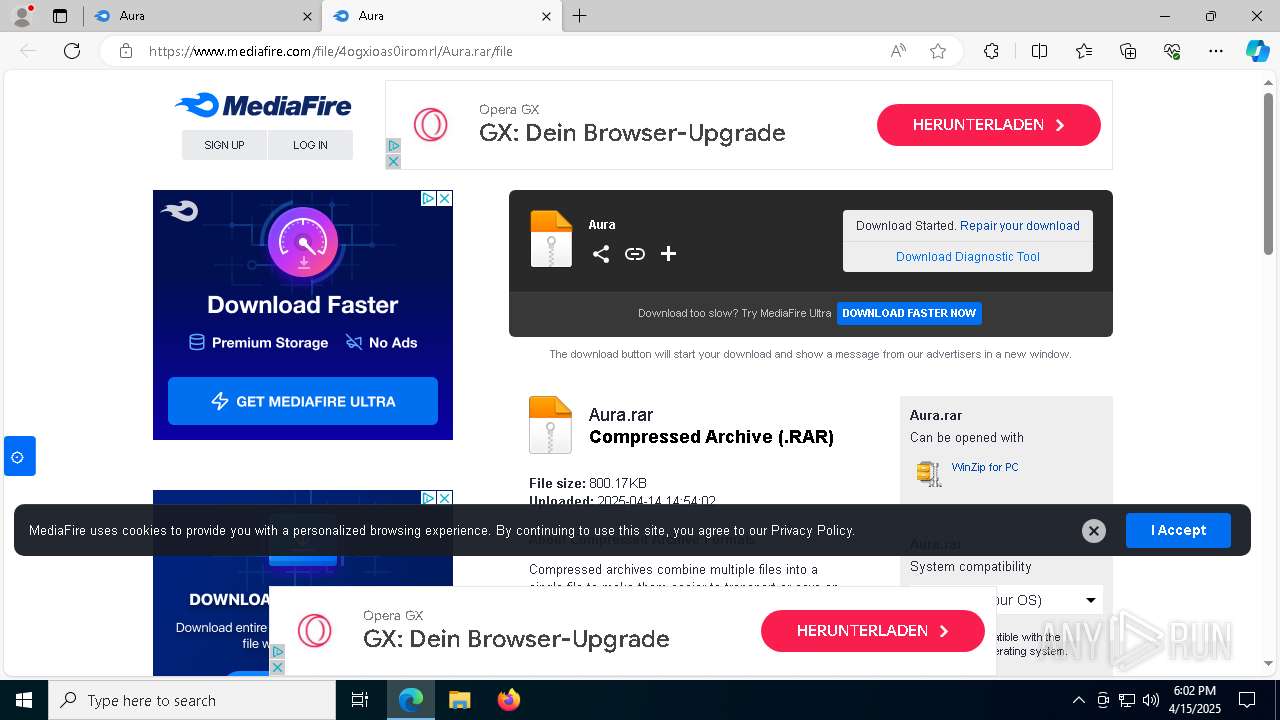
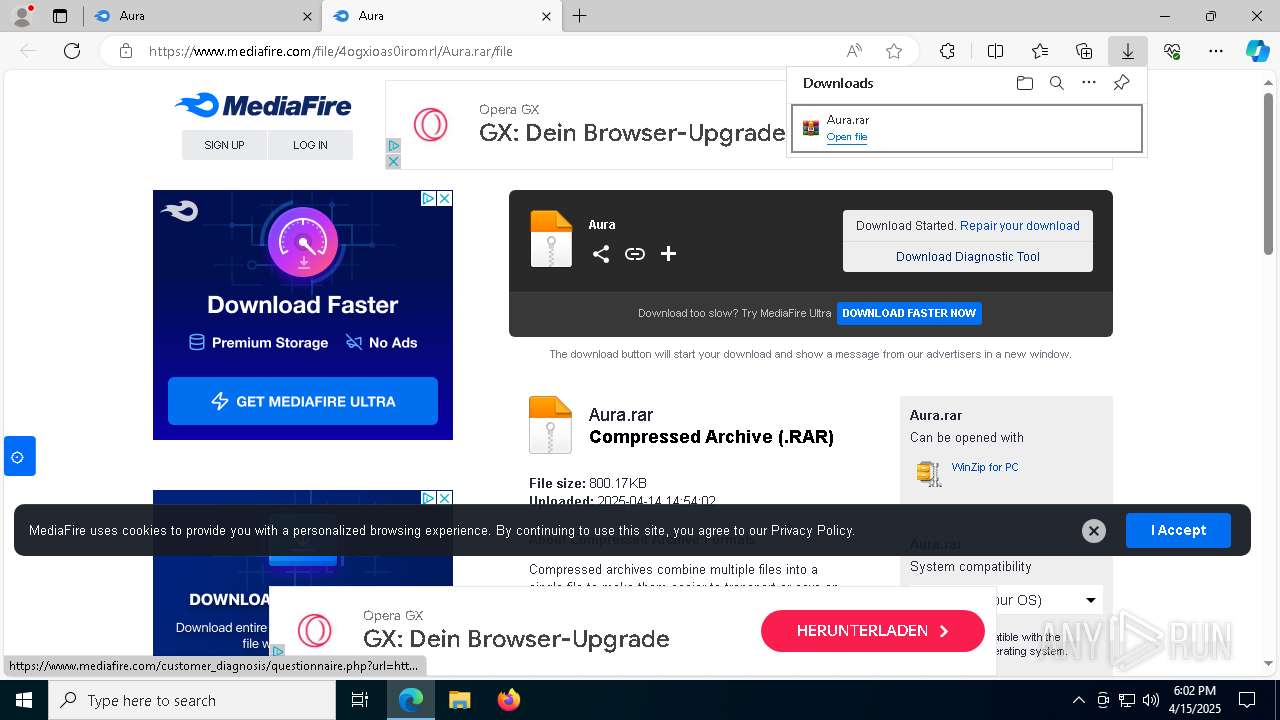
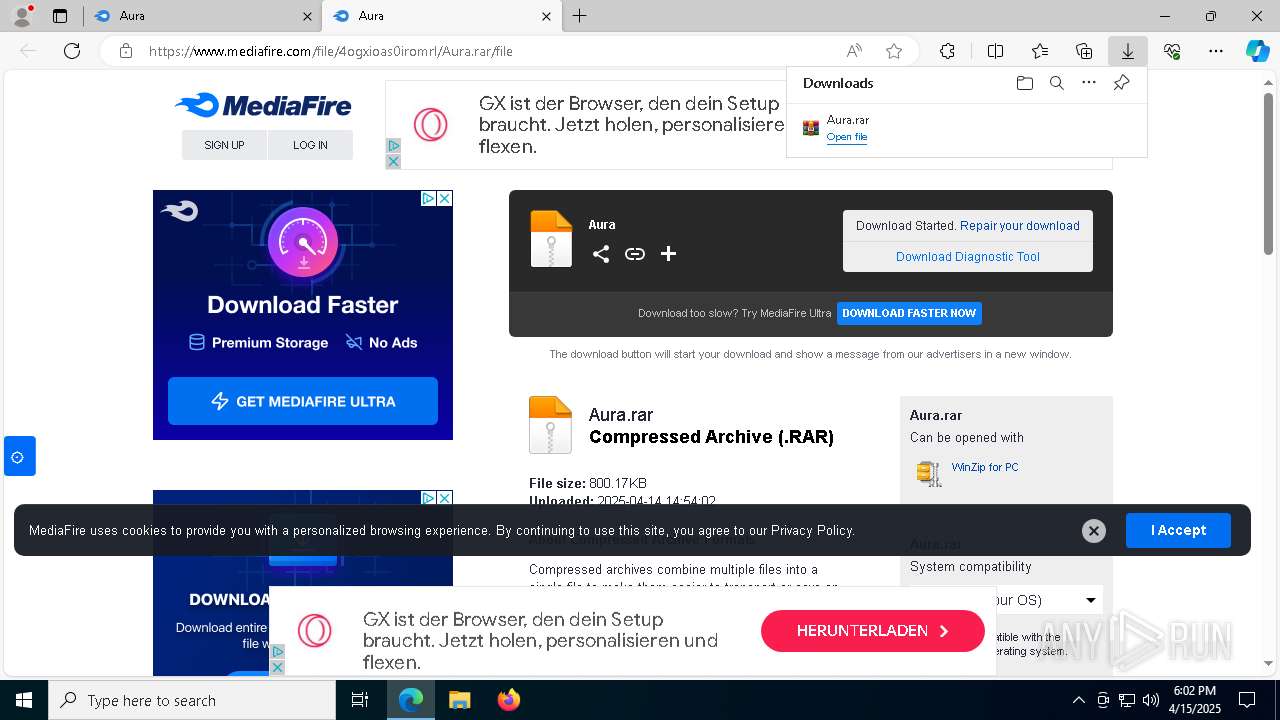
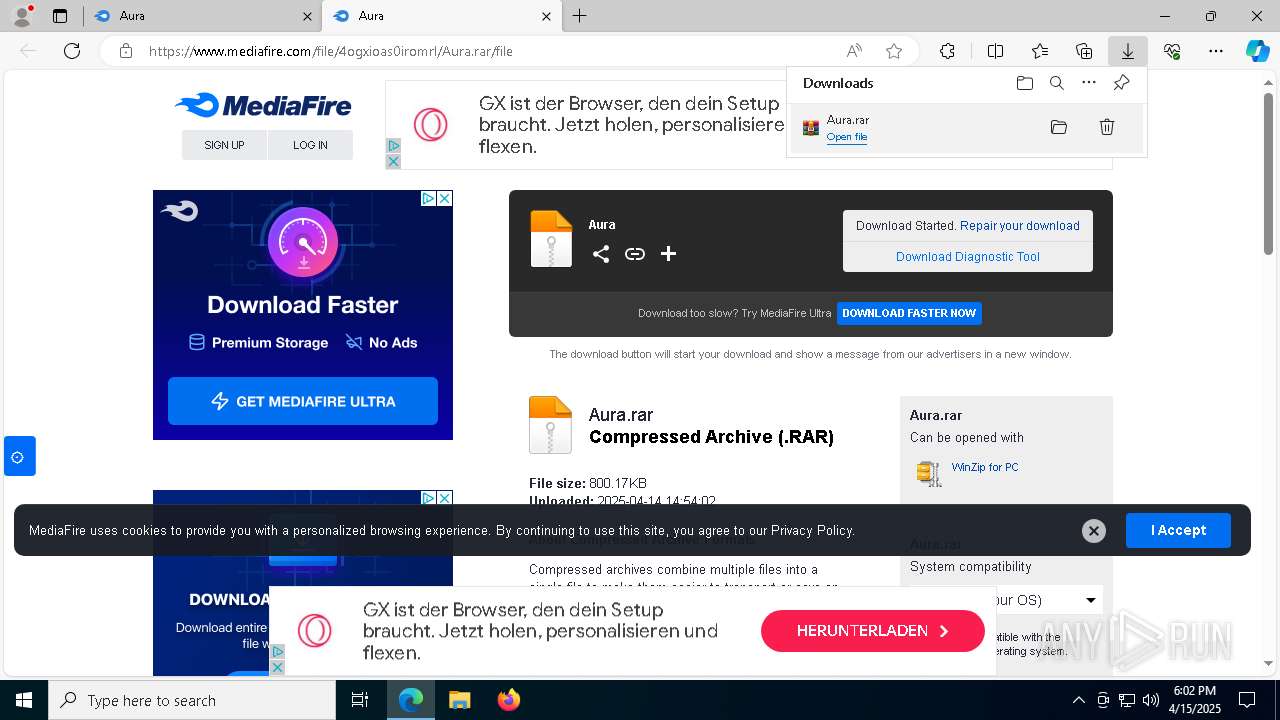
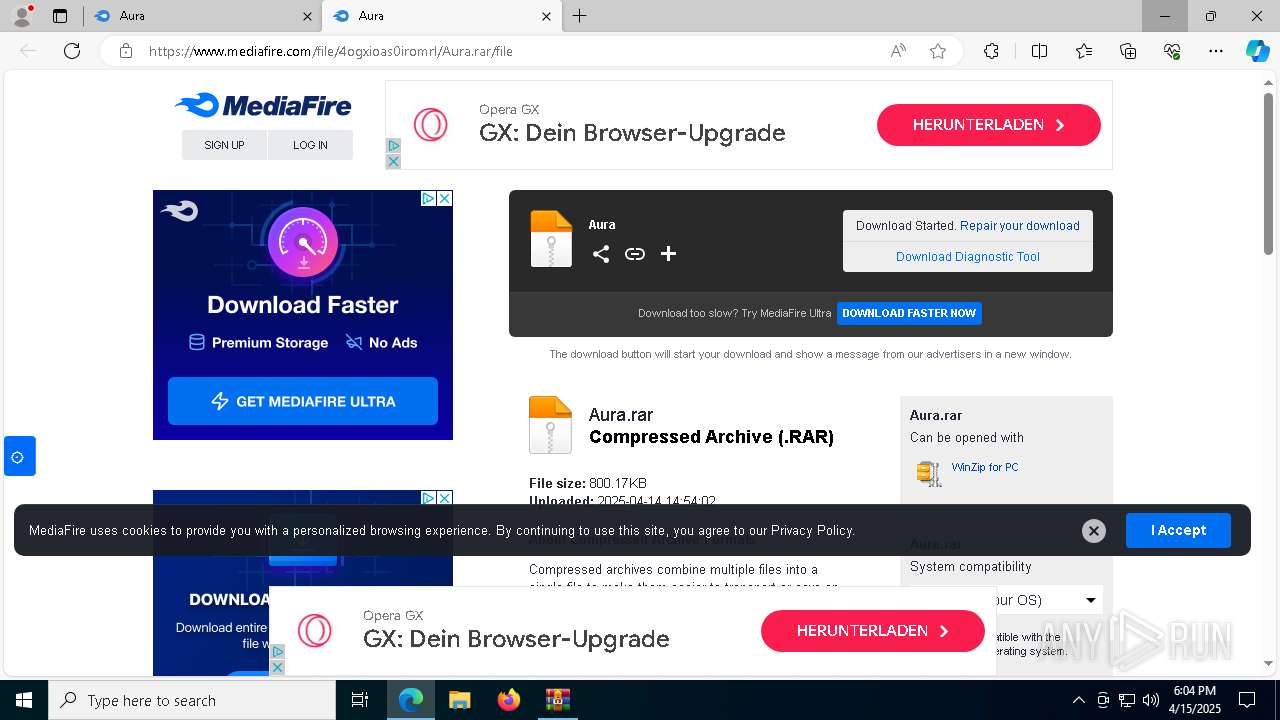
| URL: | https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbExMZ2N5RmlydE1pQ2JULU9UY1loZVlDRUJmZ3xBQ3Jtc0tsUUtKUkZwTkxTeFNZNFlKcnJ0VTVoUXpNdERscjRjZW1zcEJ1VDJubHdId2E0UjRKTnI5ZXQzeG9ISzVJekk5c0g0aUdsTWx0bjdFRWJXNWFuUWVYUDlXaTlUZnl0eEpnSW9RRWY2bUZEekNQdDJoTQ&q=https%3A%2F%2Fwww.mediafire.com%2Ffolder%2F04j4vnir8gk1o%2FAura&v=5xrQ_9sfipA |
| Full analysis: | https://app.any.run/tasks/0e67747f-7cd8-4b42-9a36-e0bde688c0c8 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 15, 2025, 18:01:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
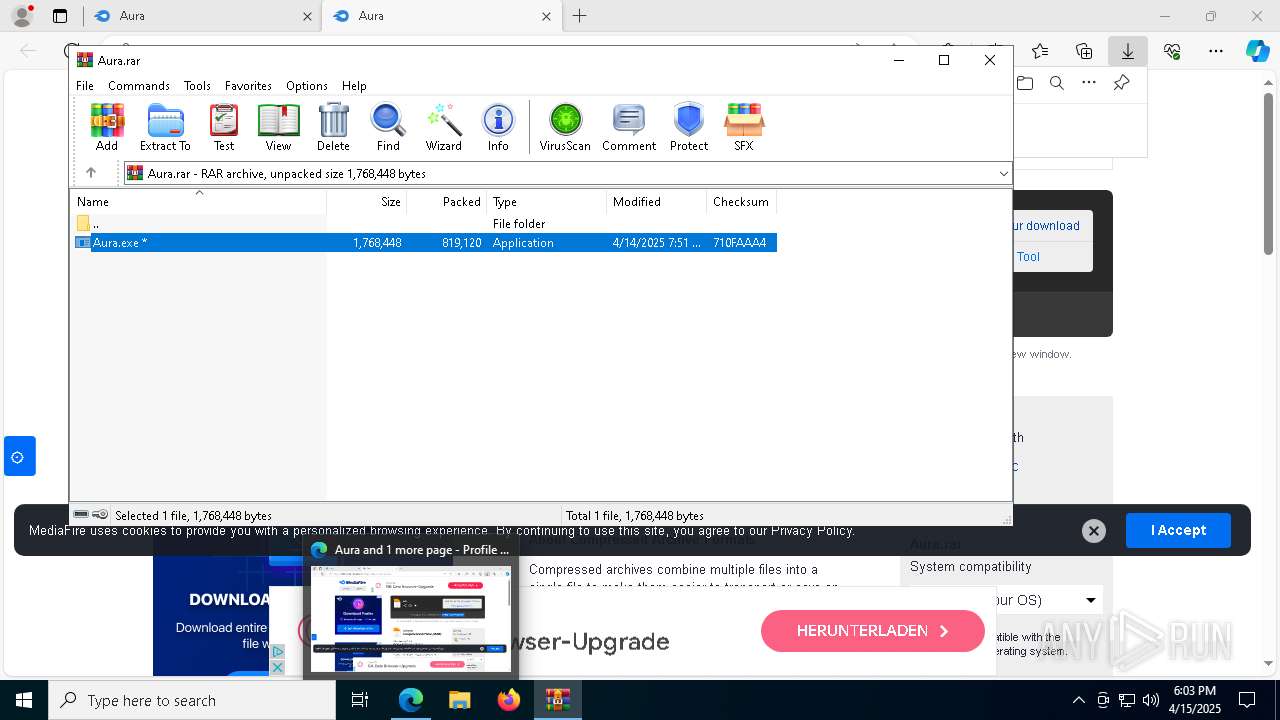
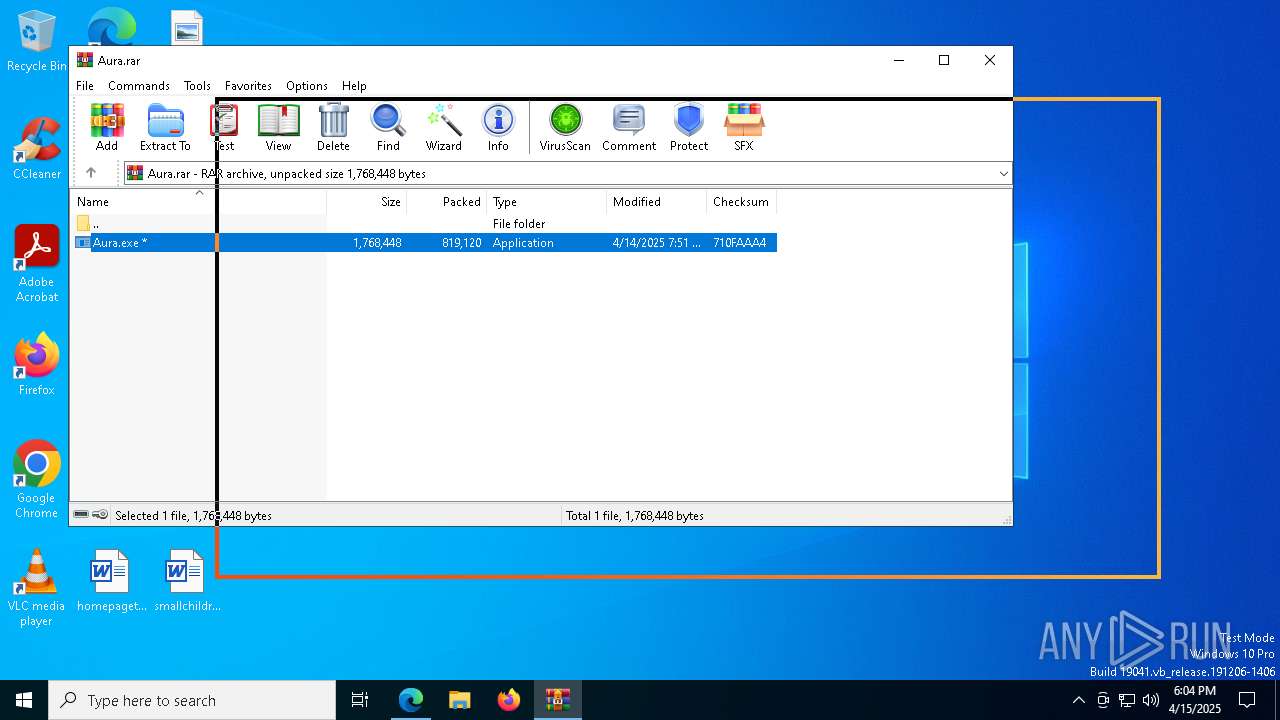
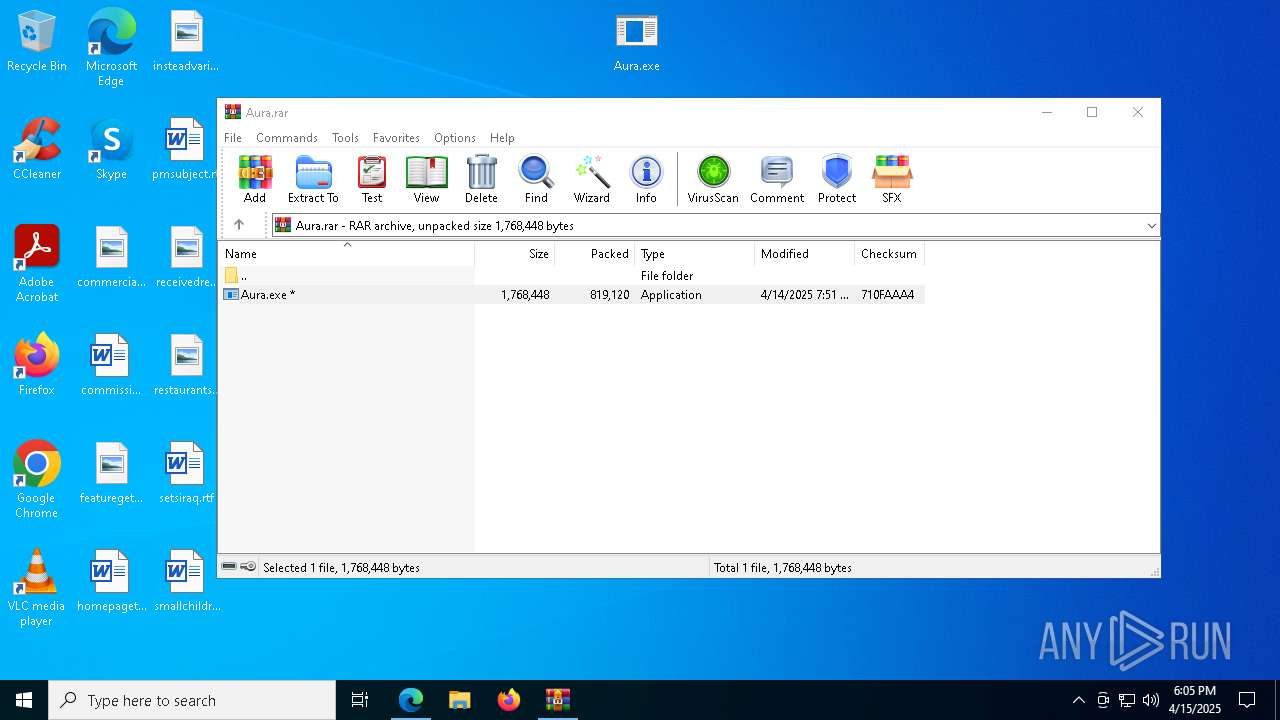
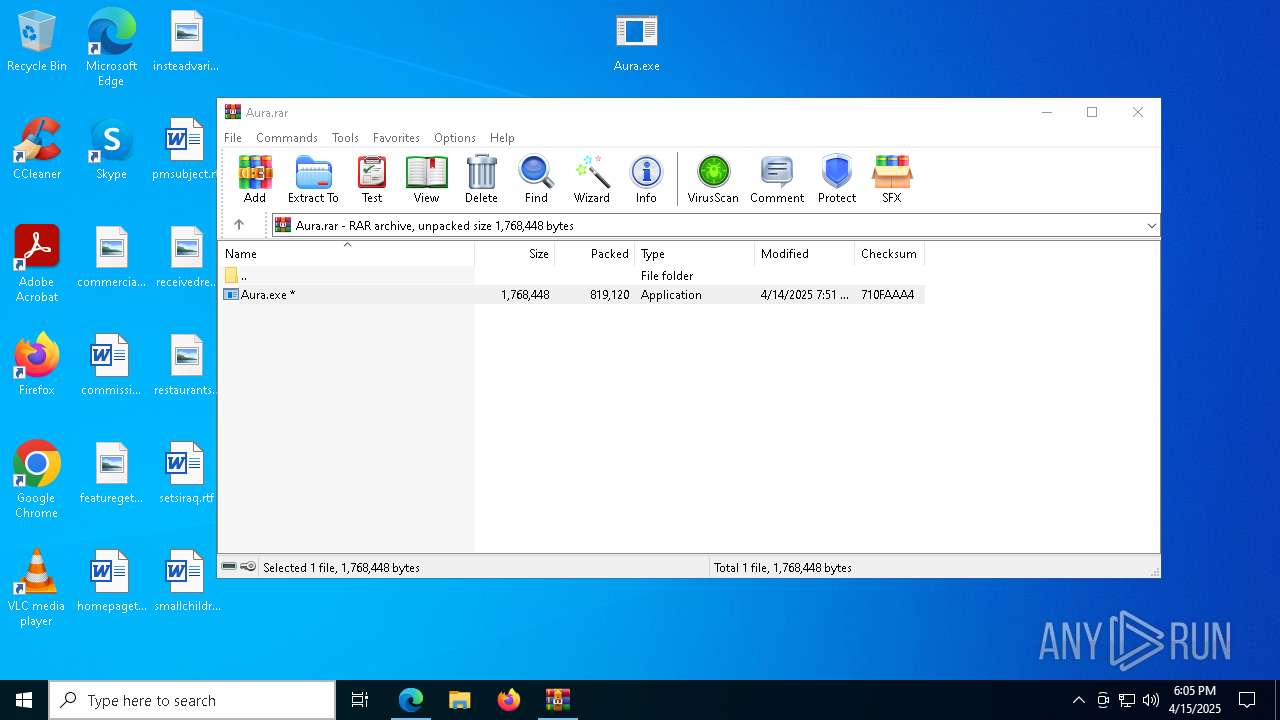
| MD5: | 9A251629279421C16BA69C3E61AB62D1 |
| SHA1: | 5CFA1B38E9220D91156B2AA9628110EEDE4E2FD0 |
| SHA256: | 48E864A976F9A54D4354408070551498D872C26E0125F8F3680F99C9B0D7D113 |
| SSDEEP: | 6:2OLUxGKmKLqZAdovYjpankMTyG3ZnFGP/nx/SeBjGx9jhVMA33zh3eG669YYql:2jGRf4ovYj6deetFGP/9SMGx97M6F3en |
MALICIOUS
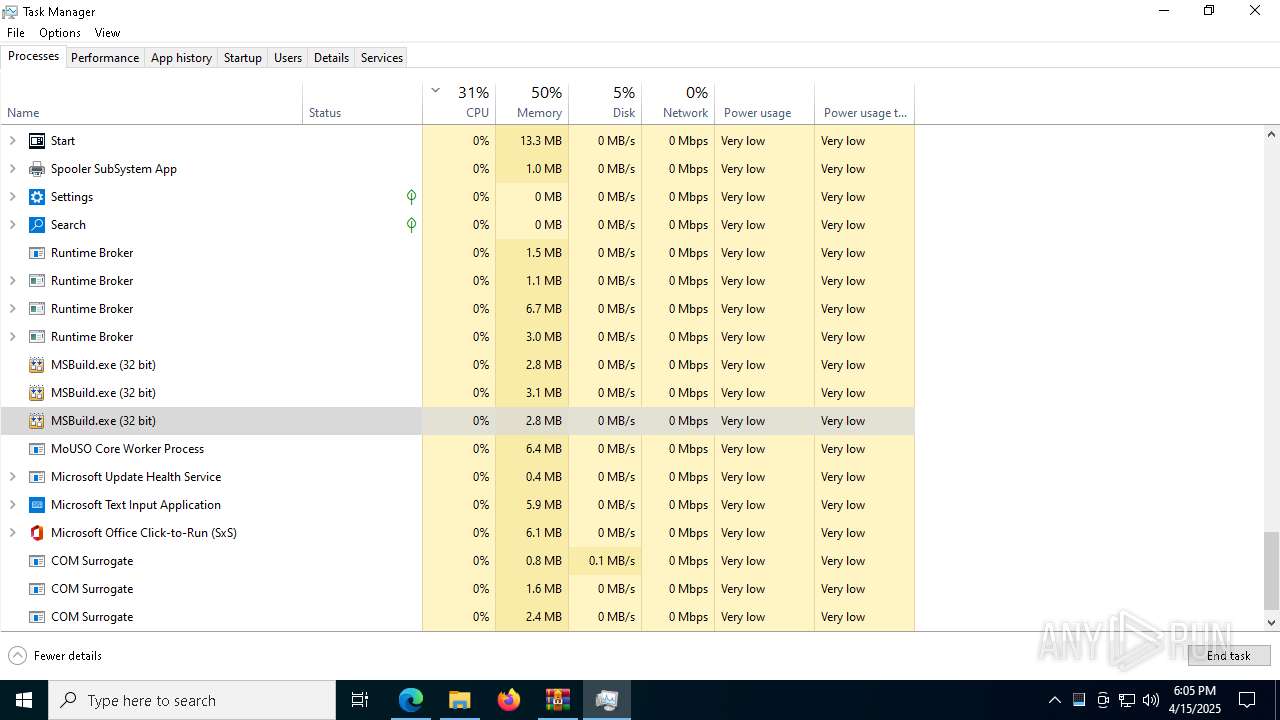
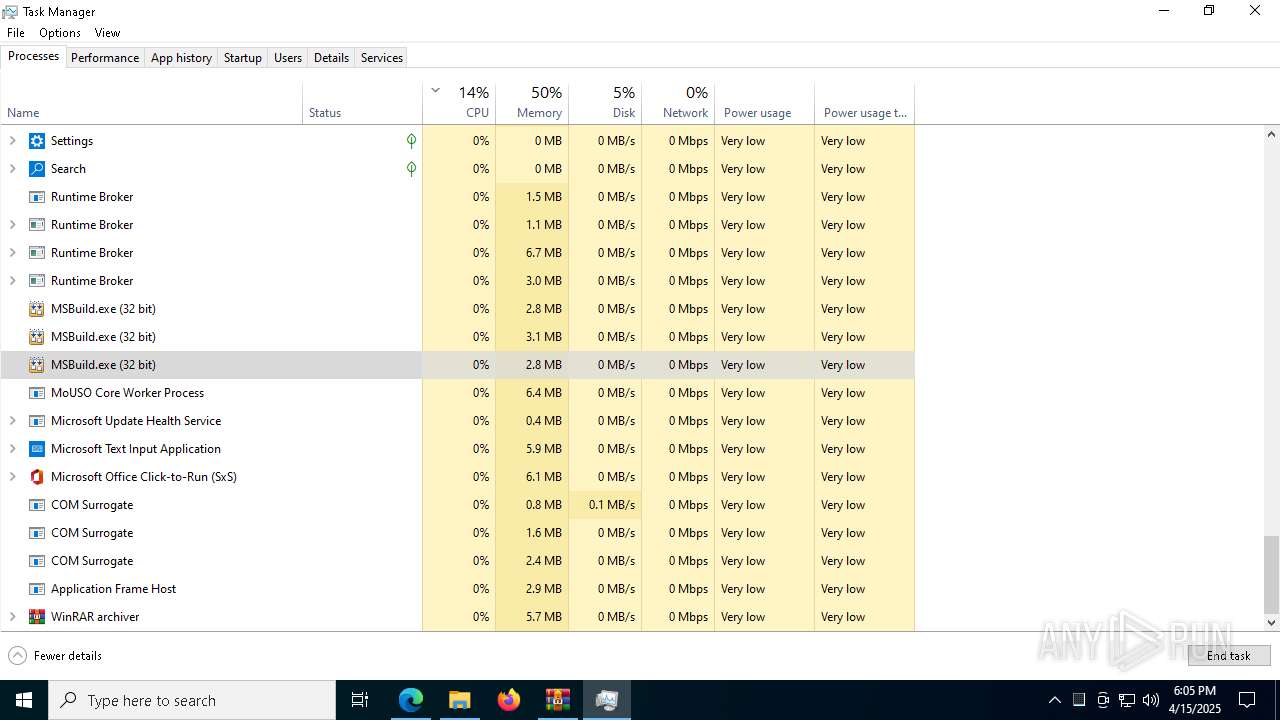
LUMMA has been detected (SURICATA)
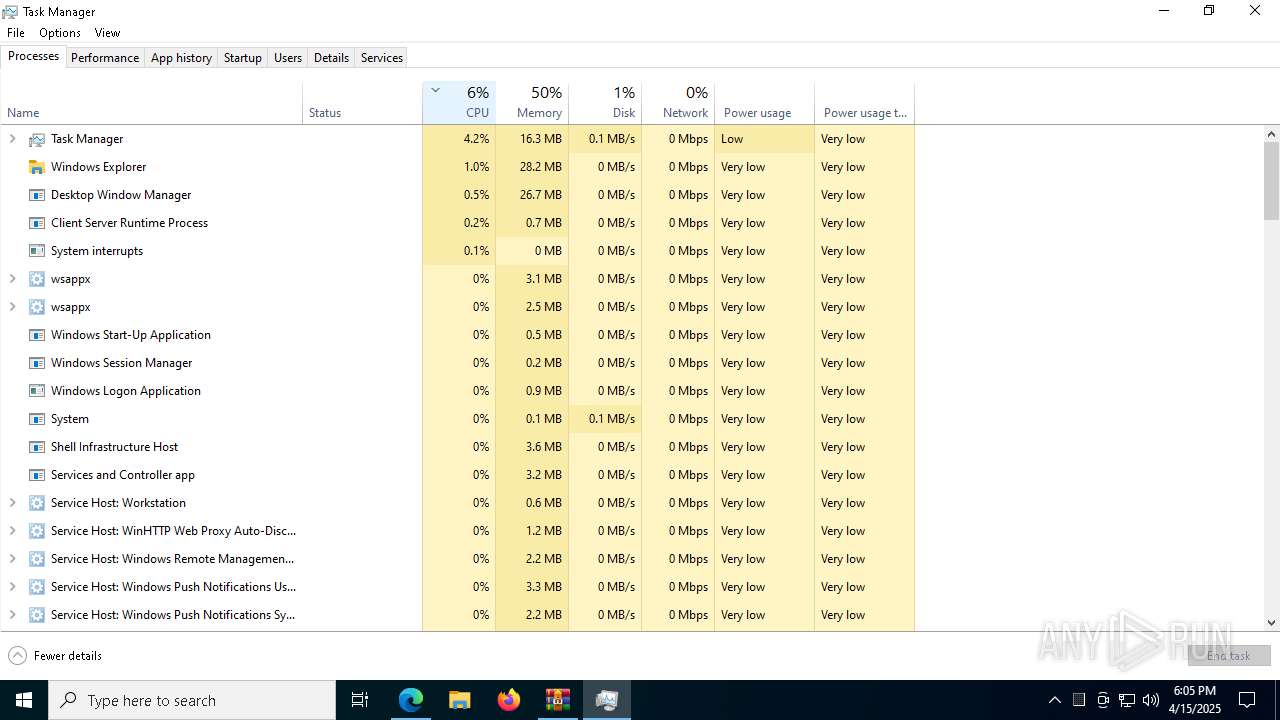
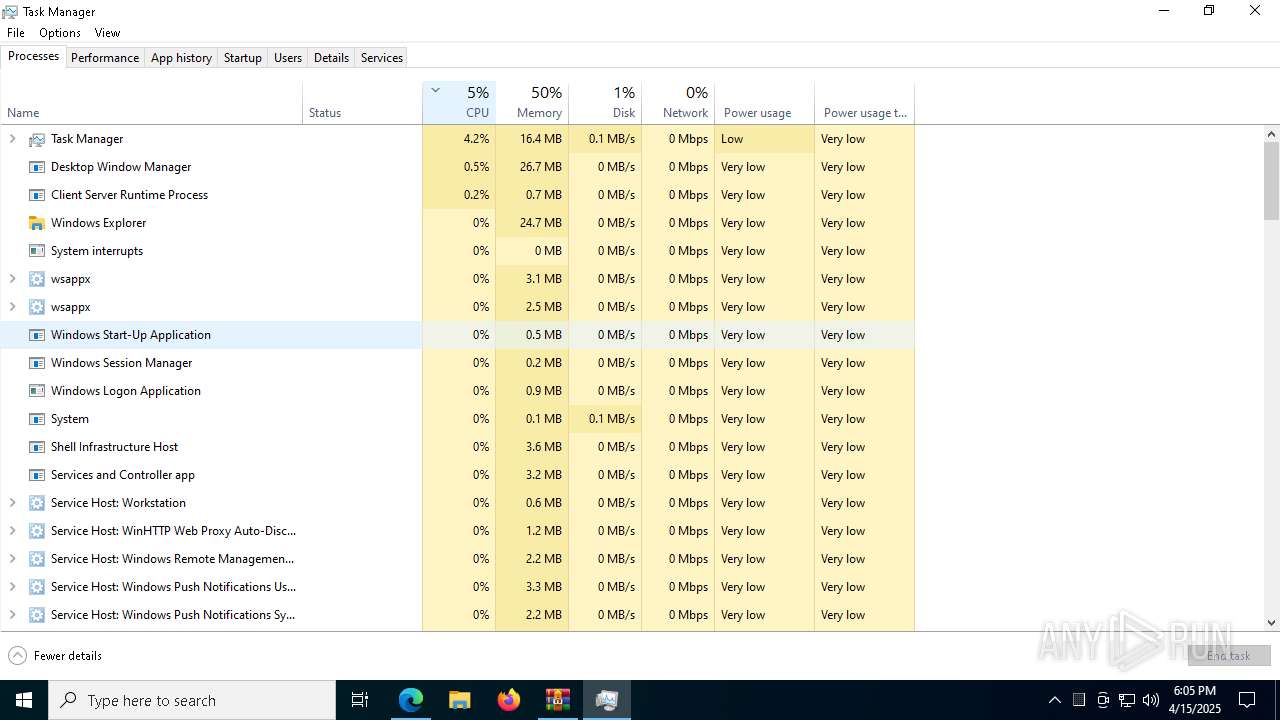
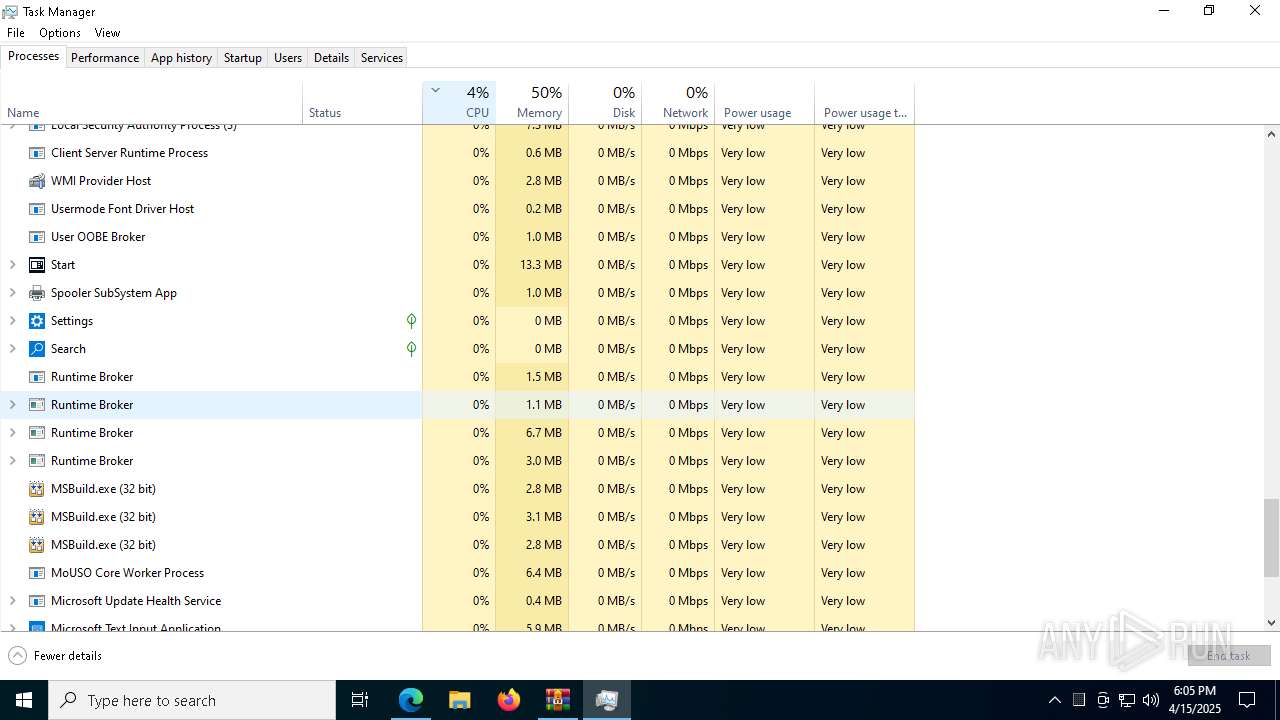
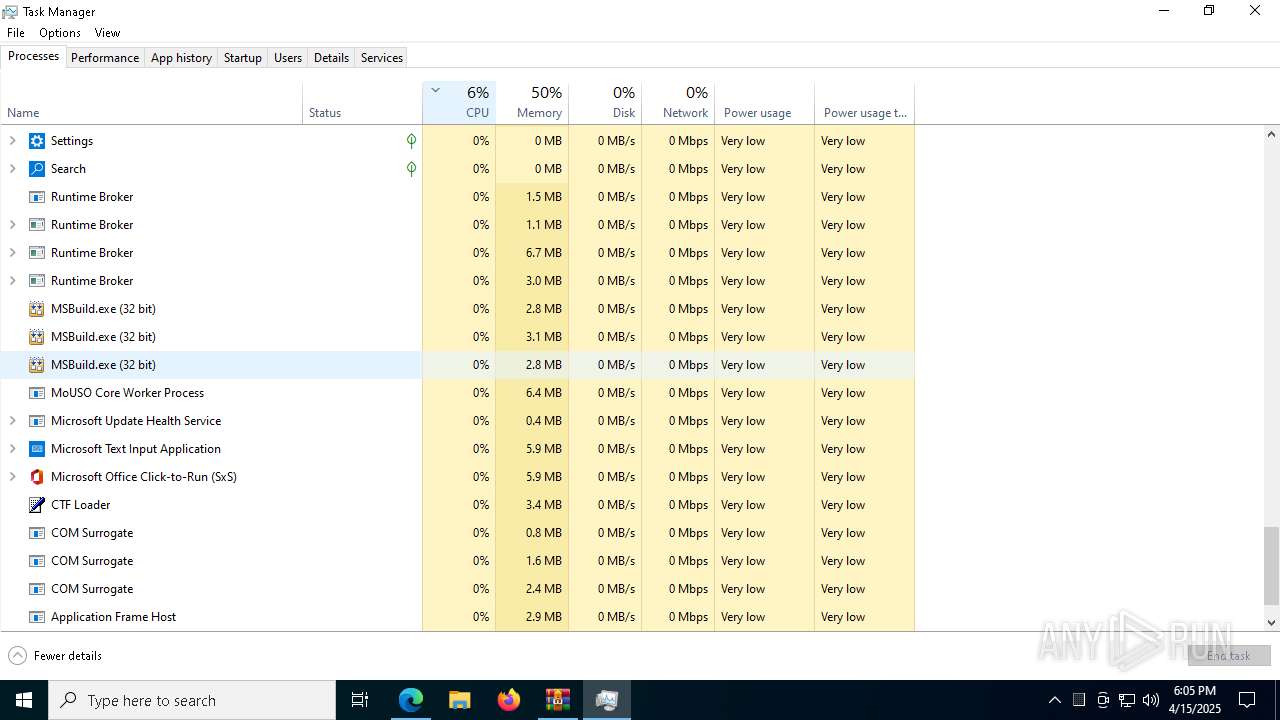
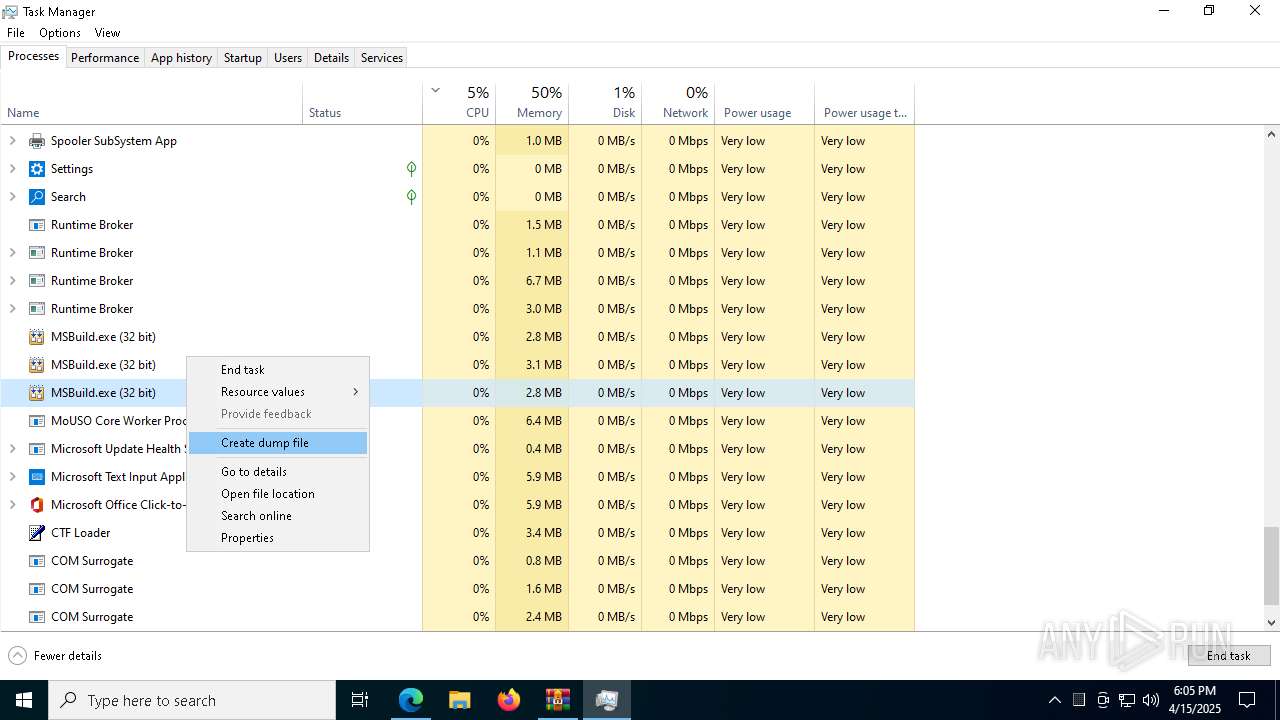
- svchost.exe (PID: 2196)
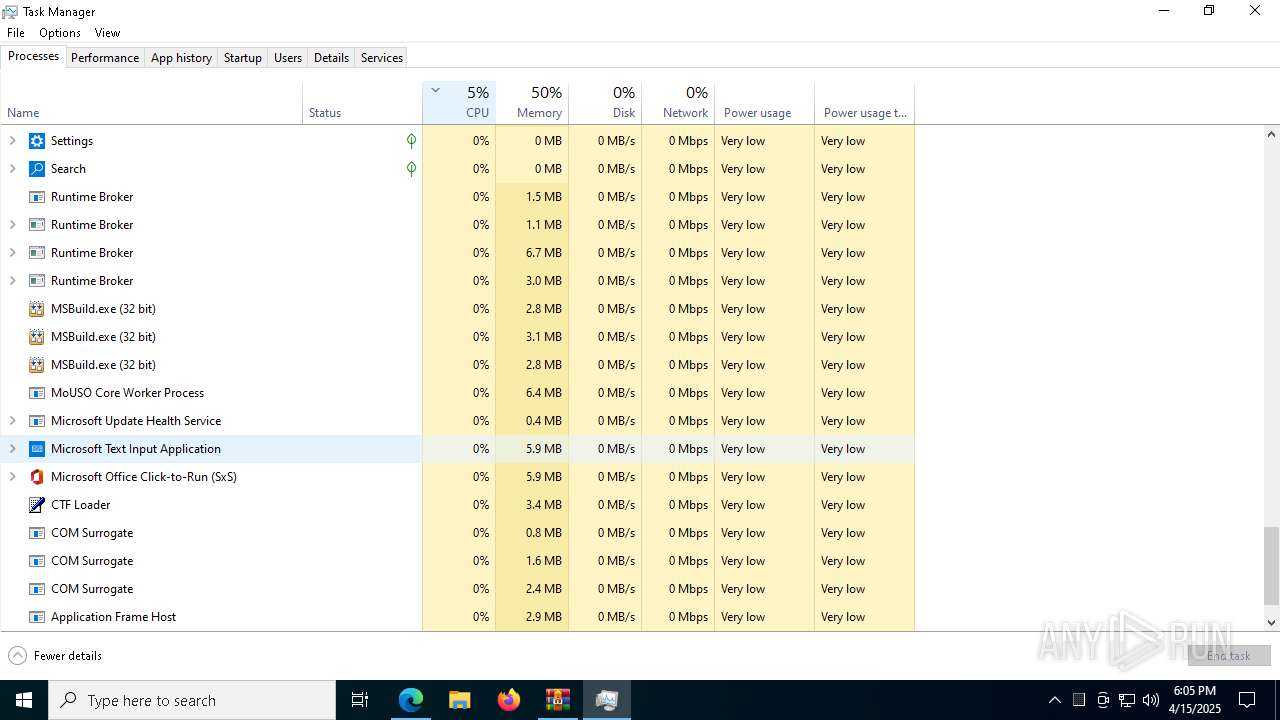
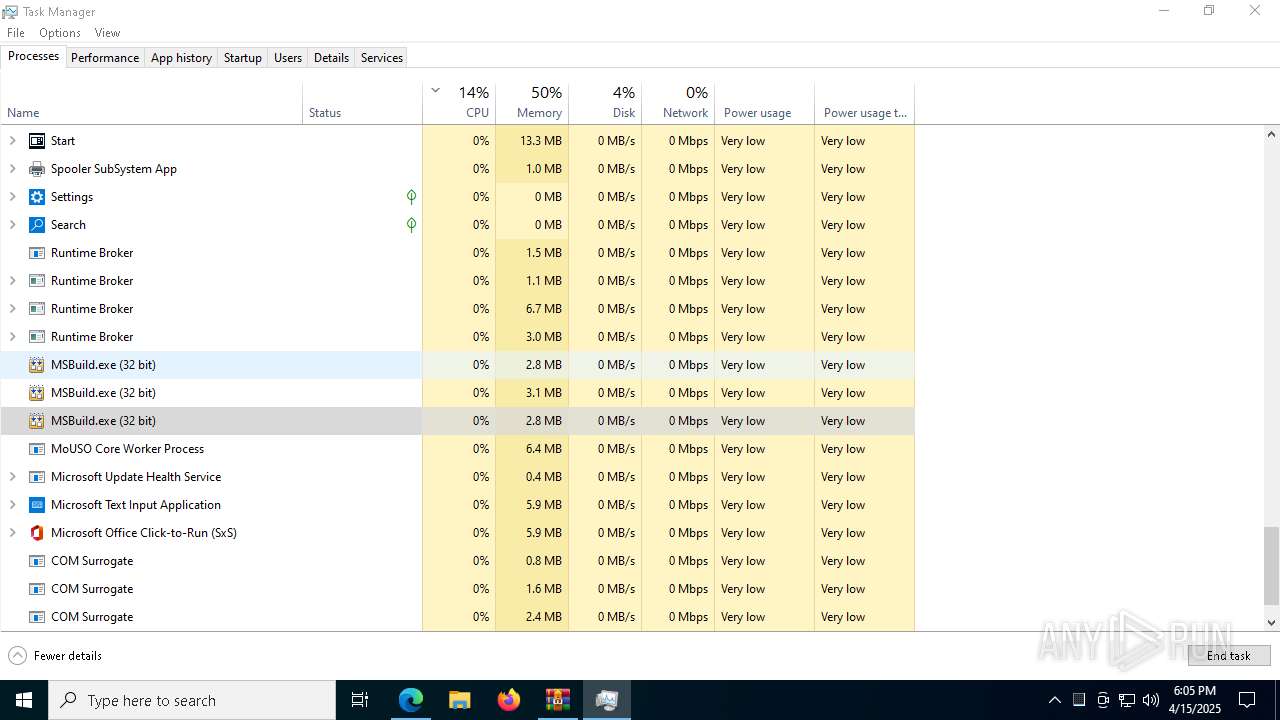
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
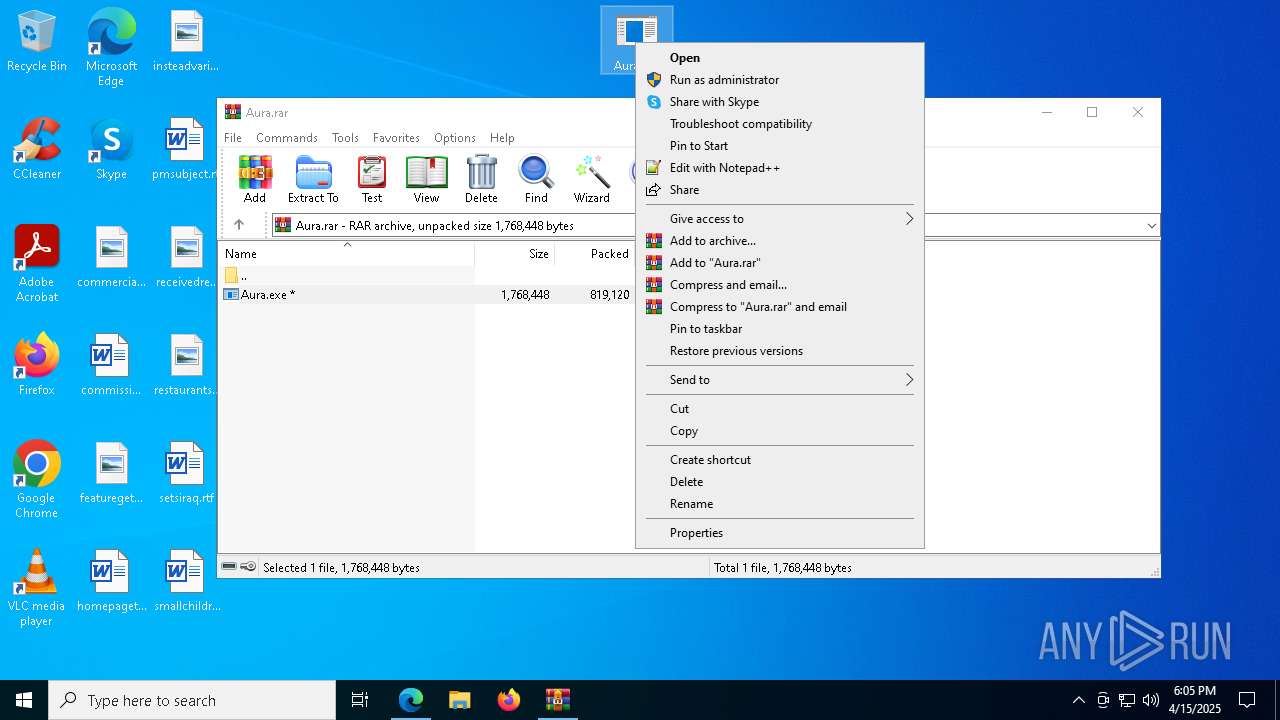
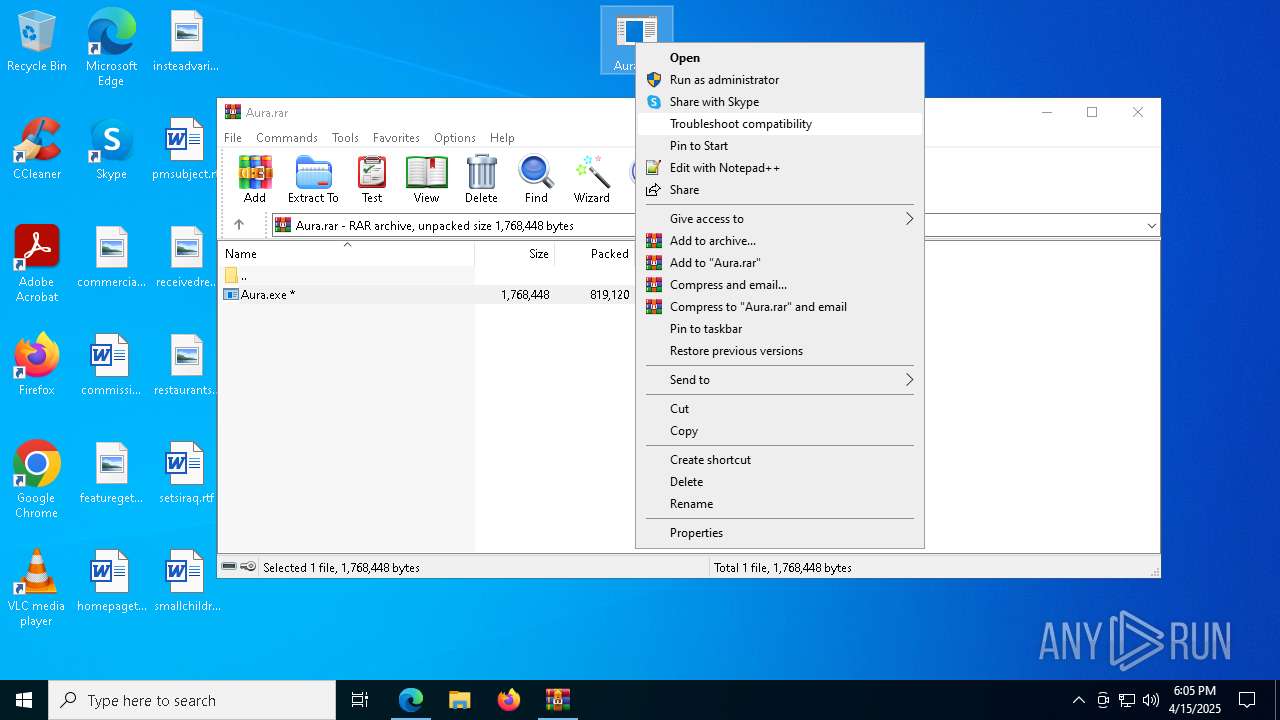
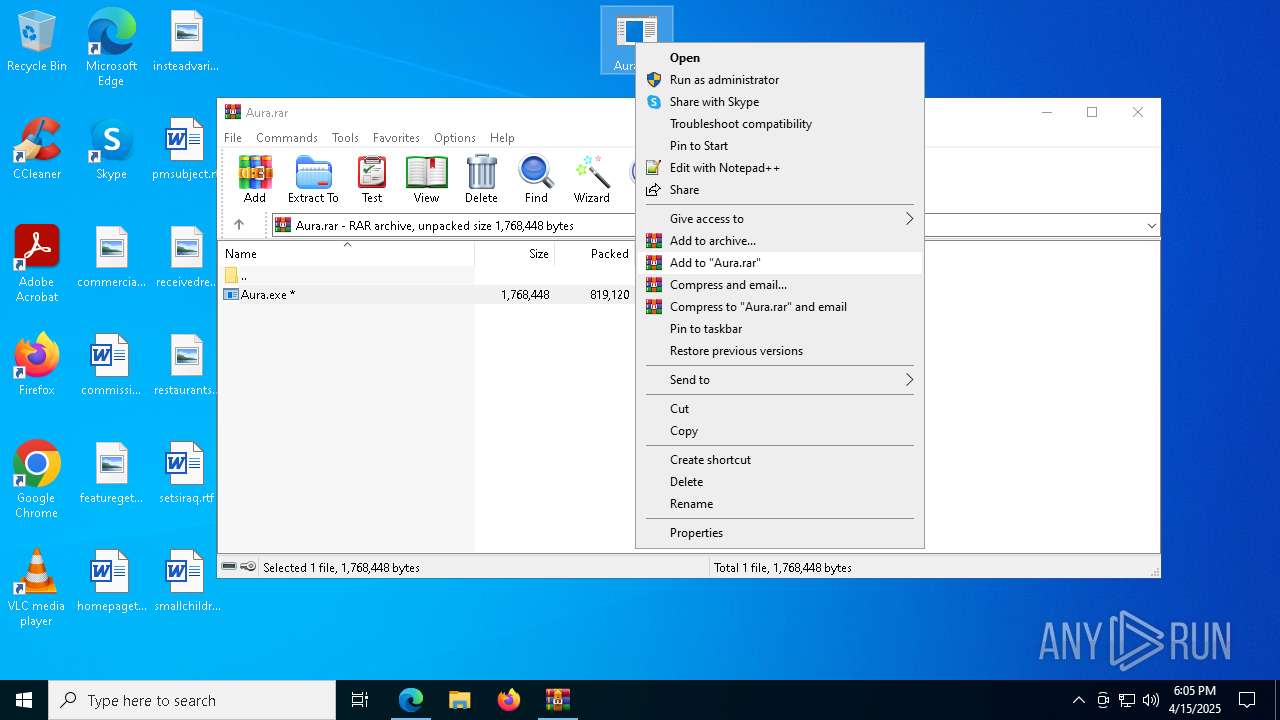
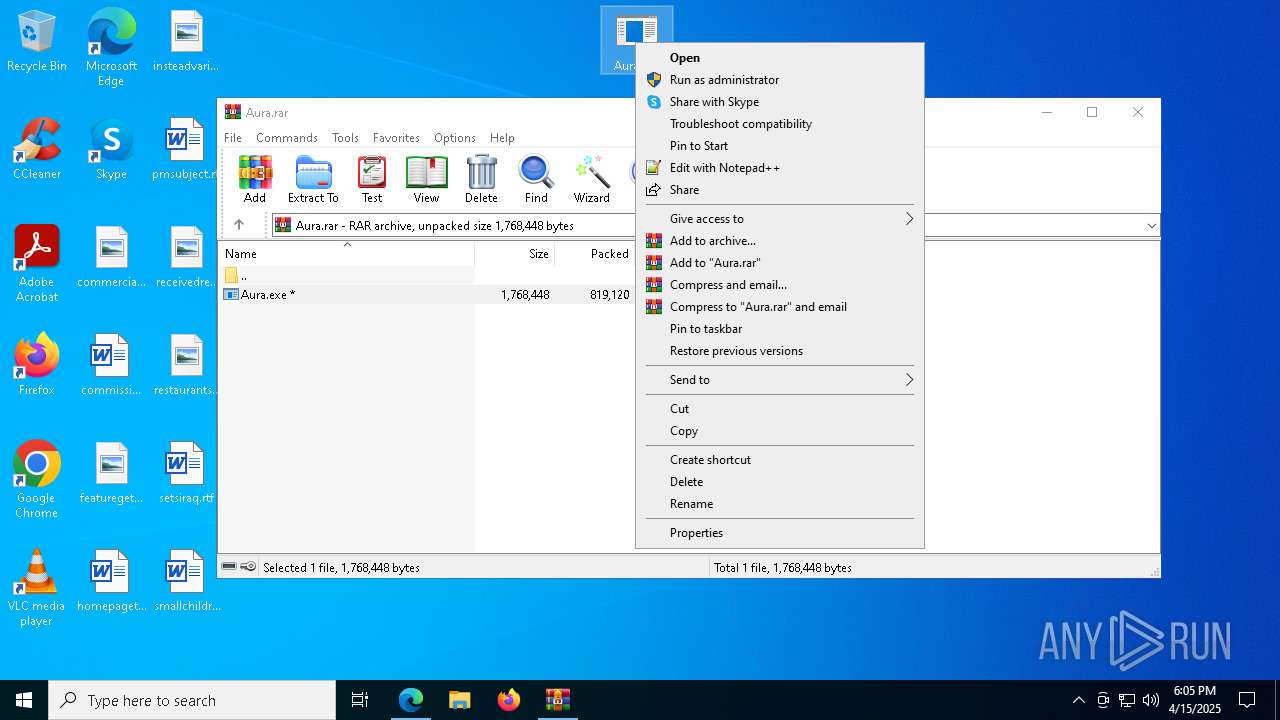
SUSPICIOUS
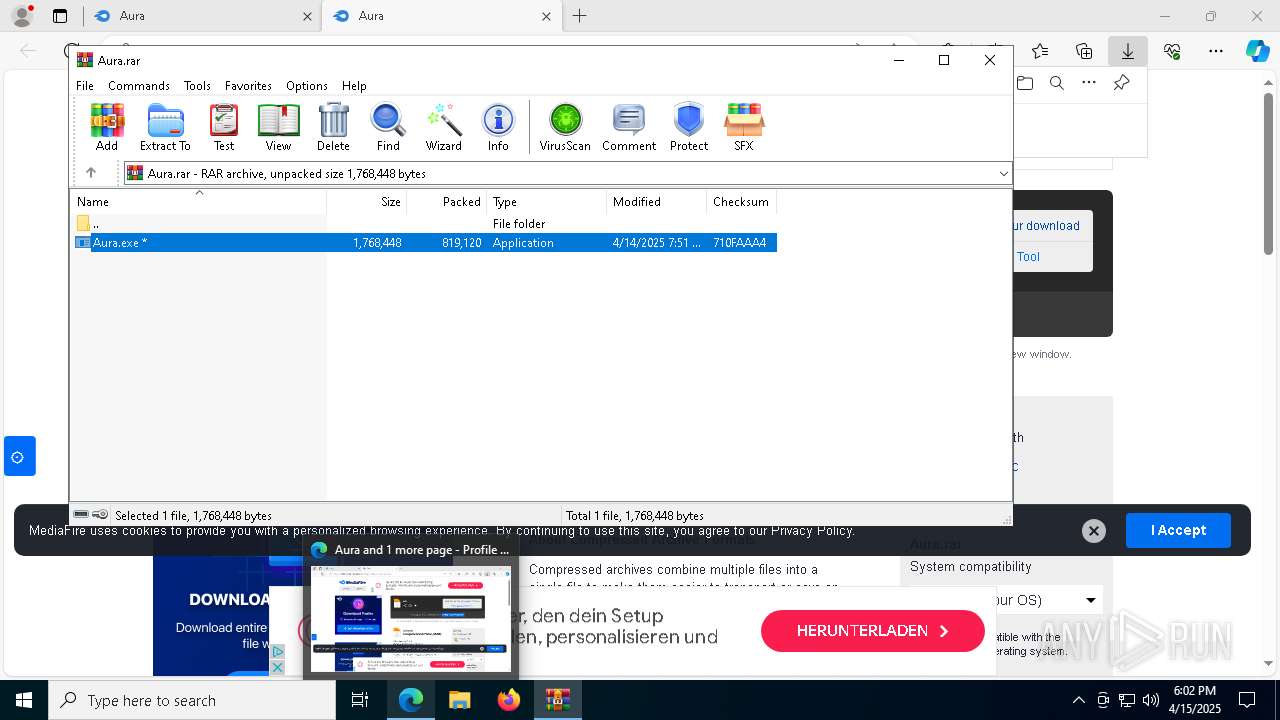
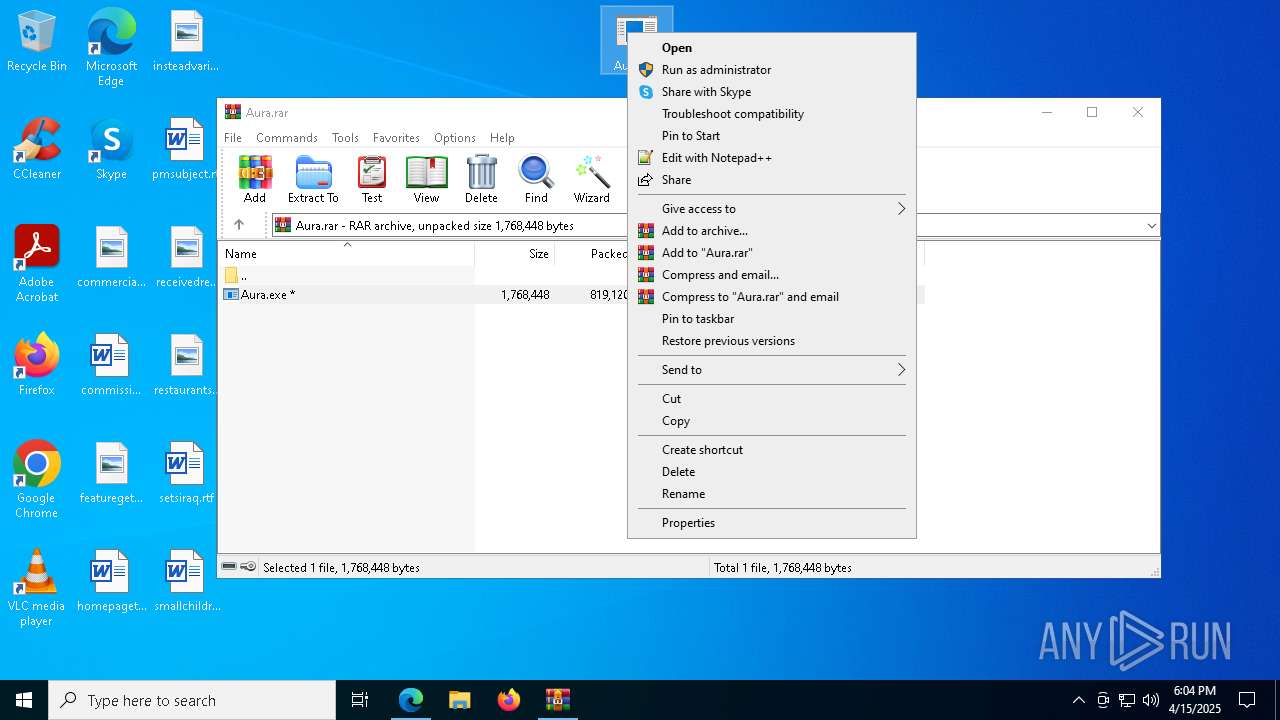
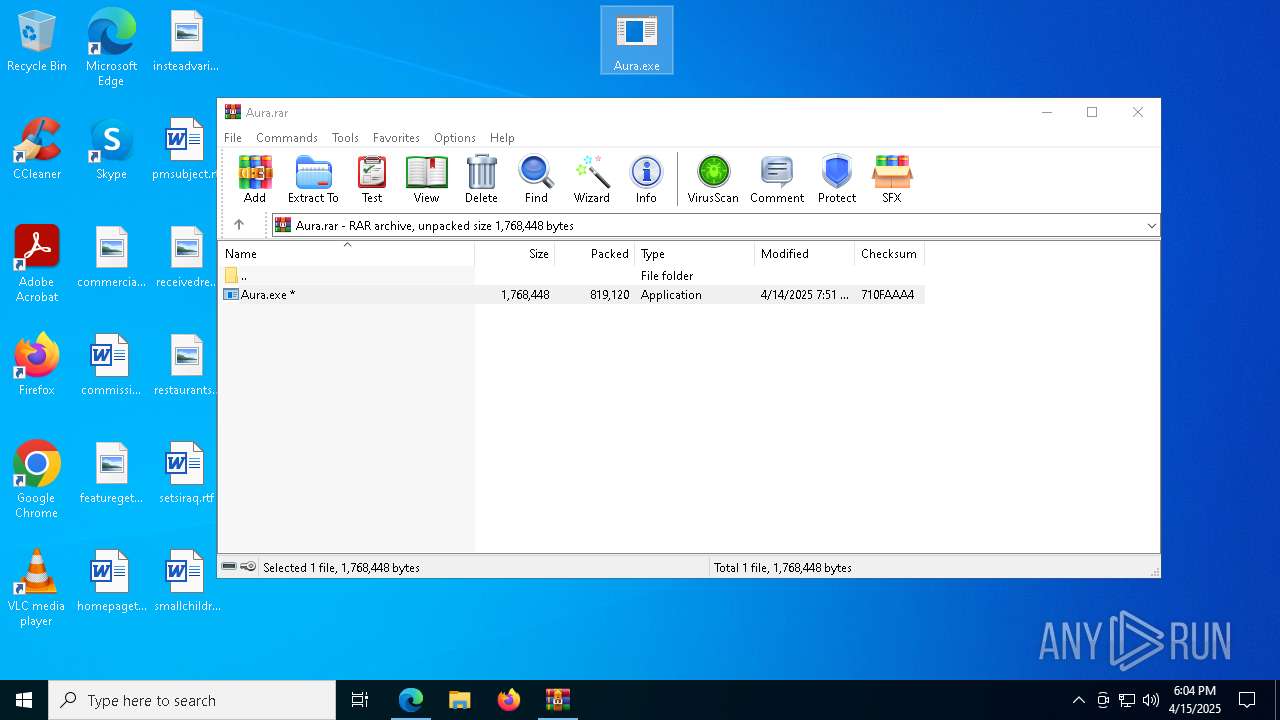
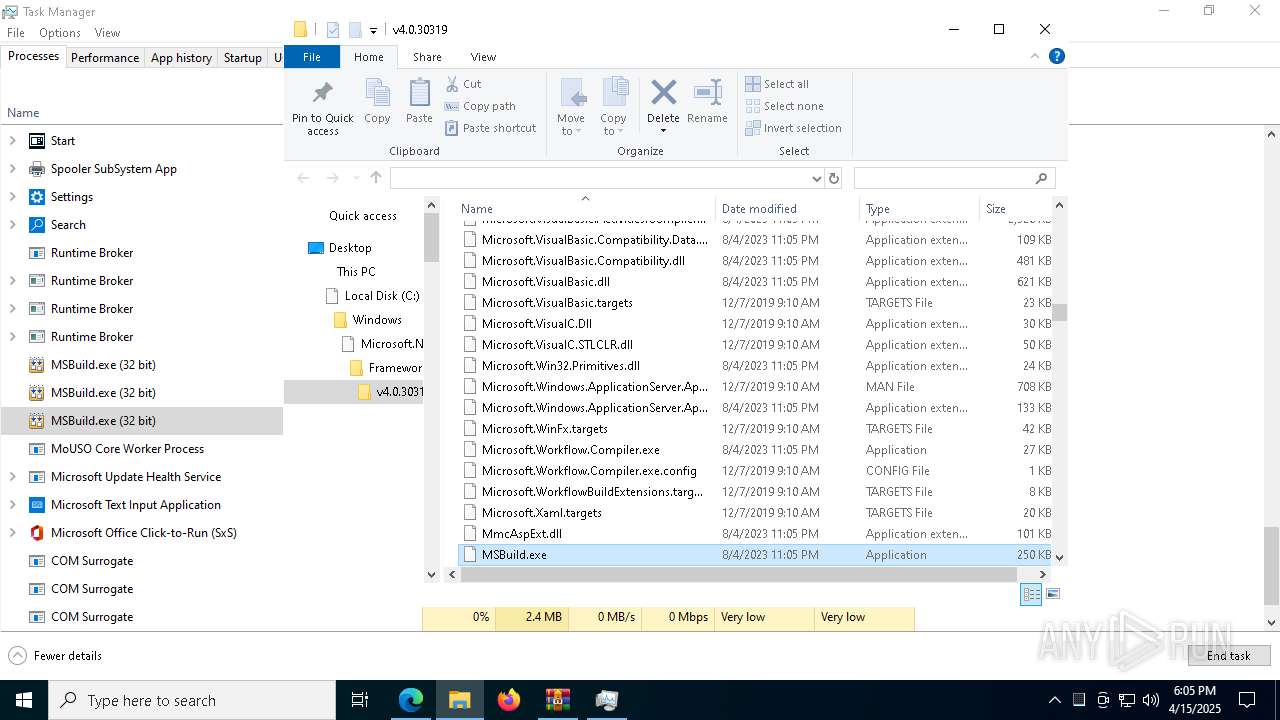
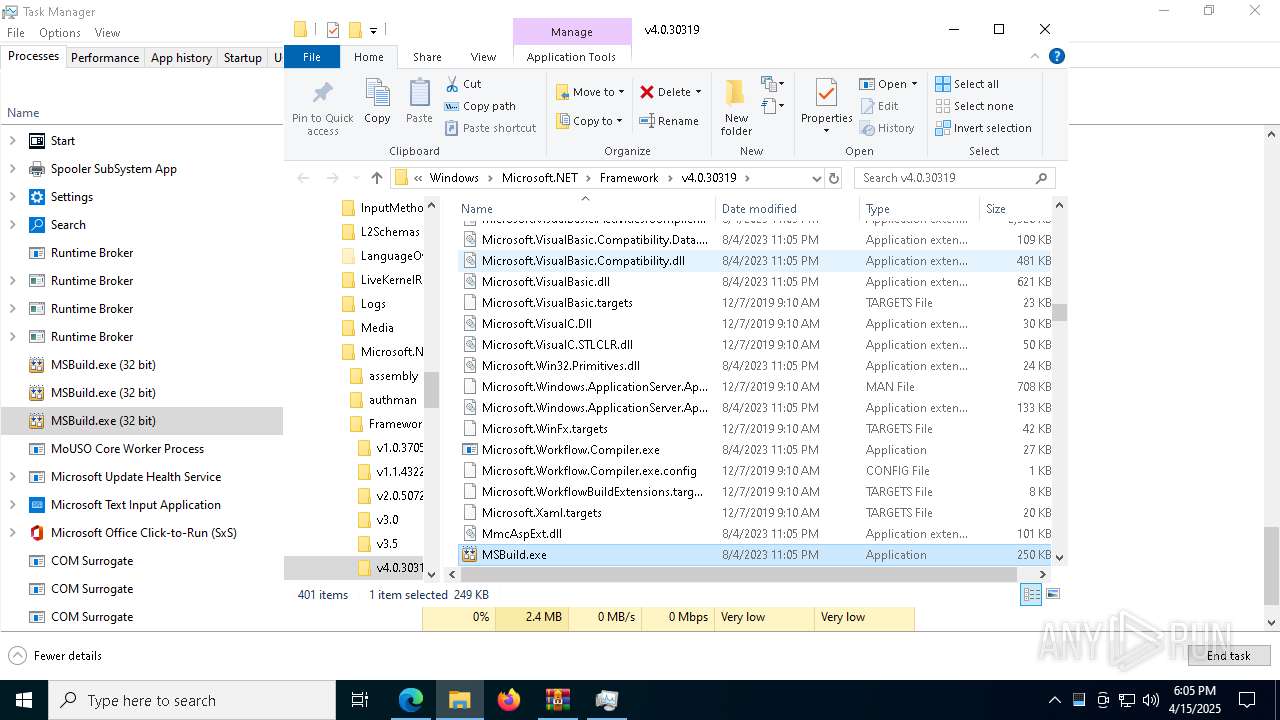
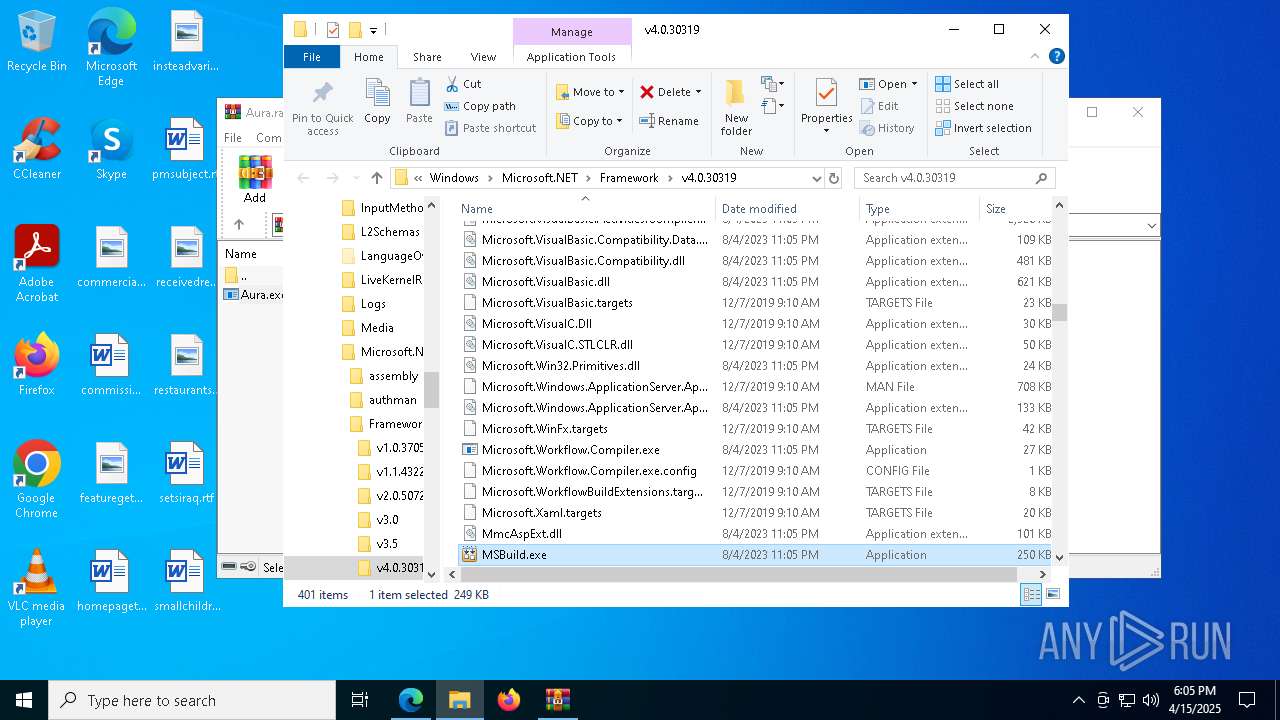
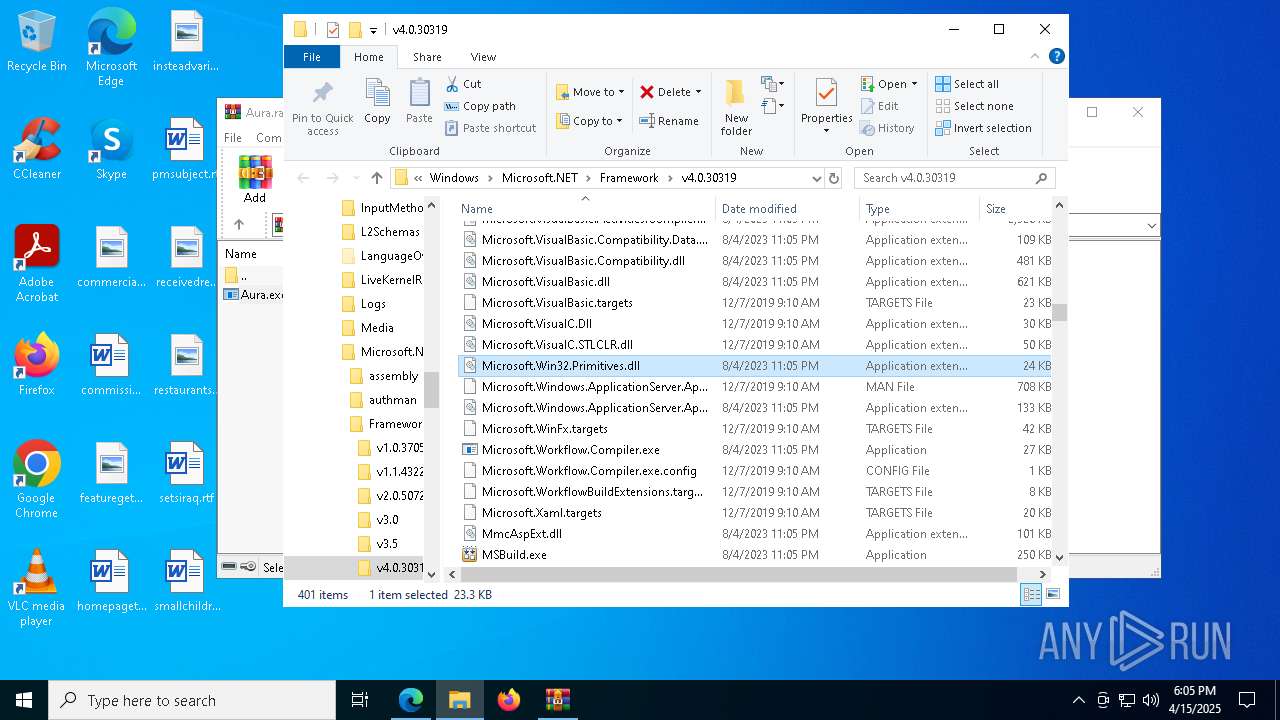
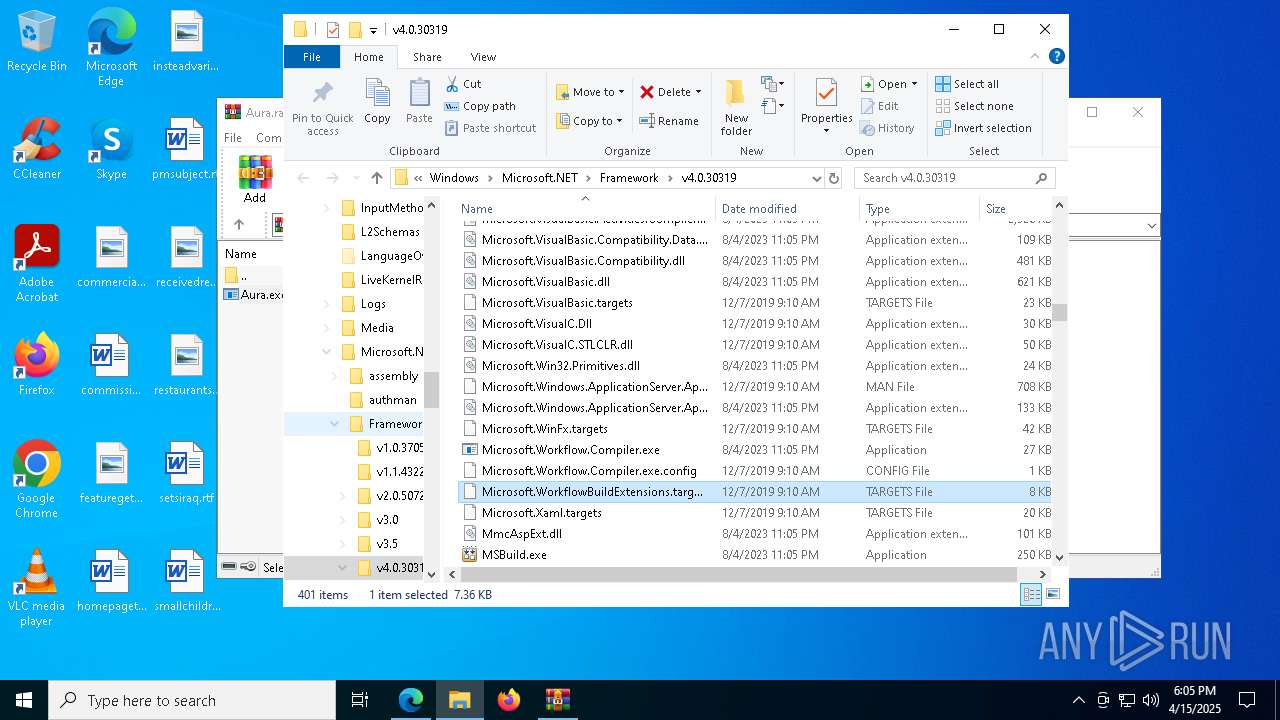
Starts a Microsoft application from unusual location
- Aura.exe (PID: 5428)
- Aura.exe (PID: 8176)
- Aura.exe (PID: 5956)
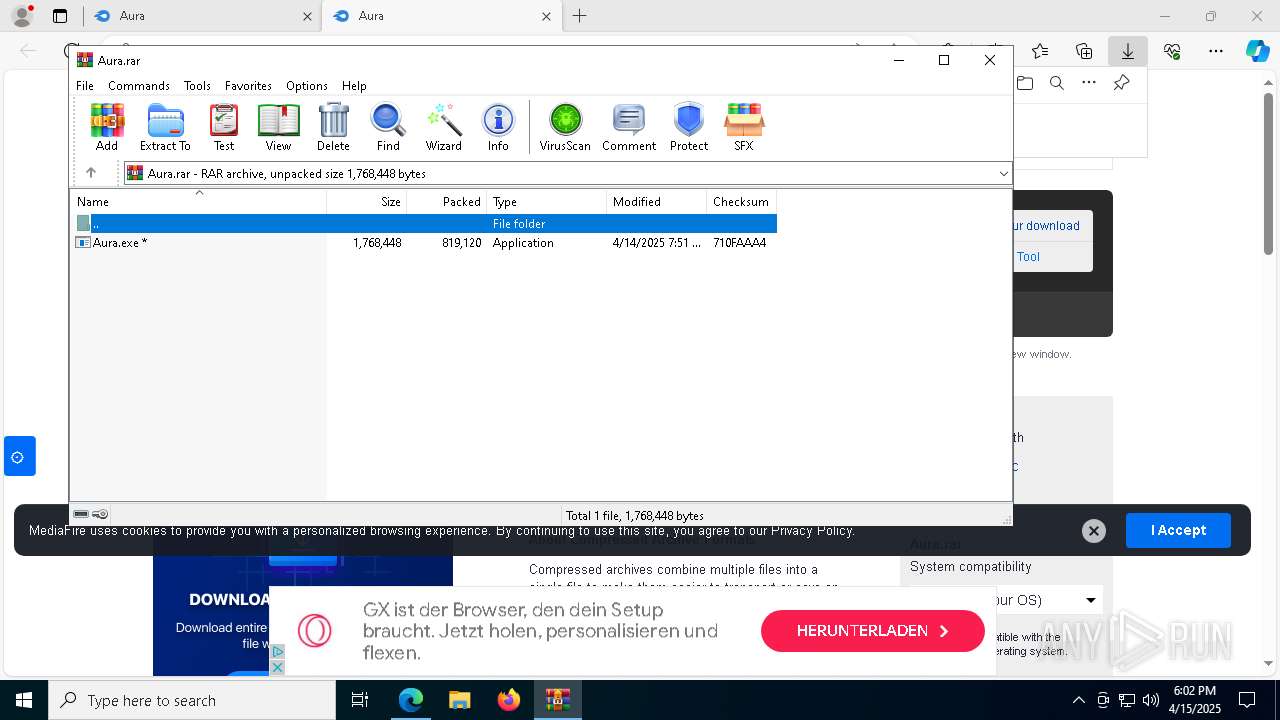
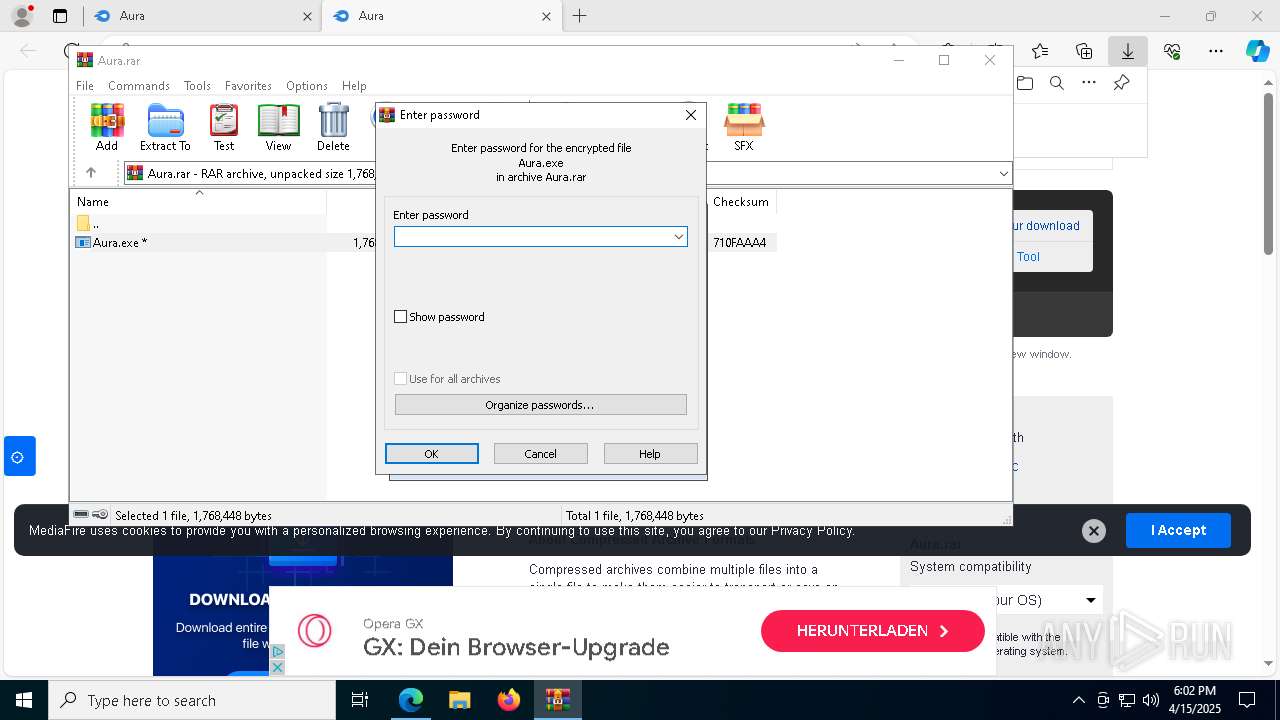
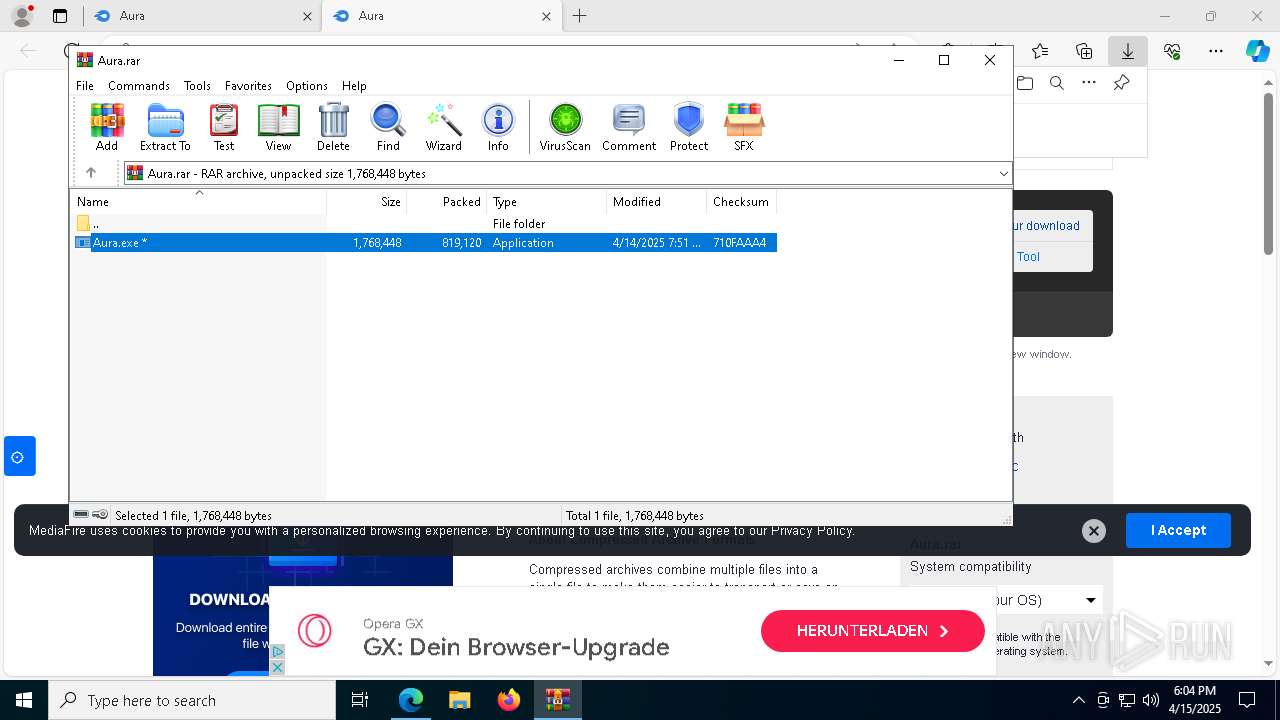
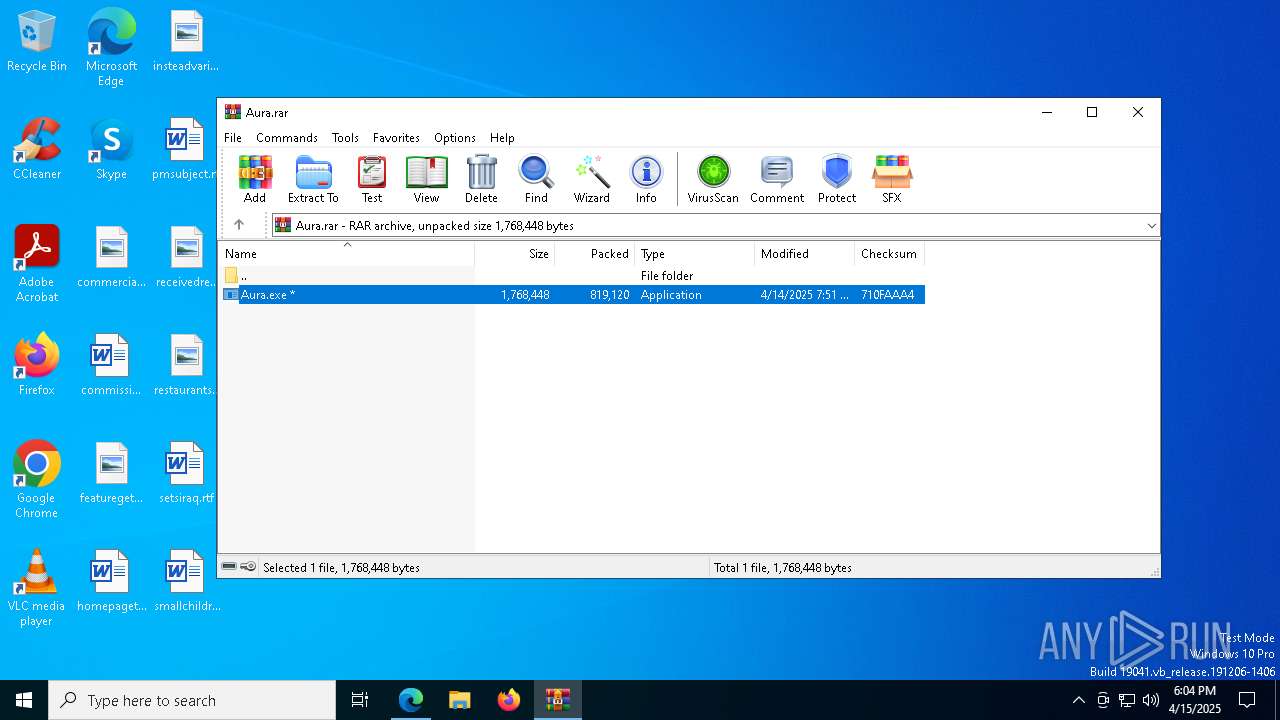
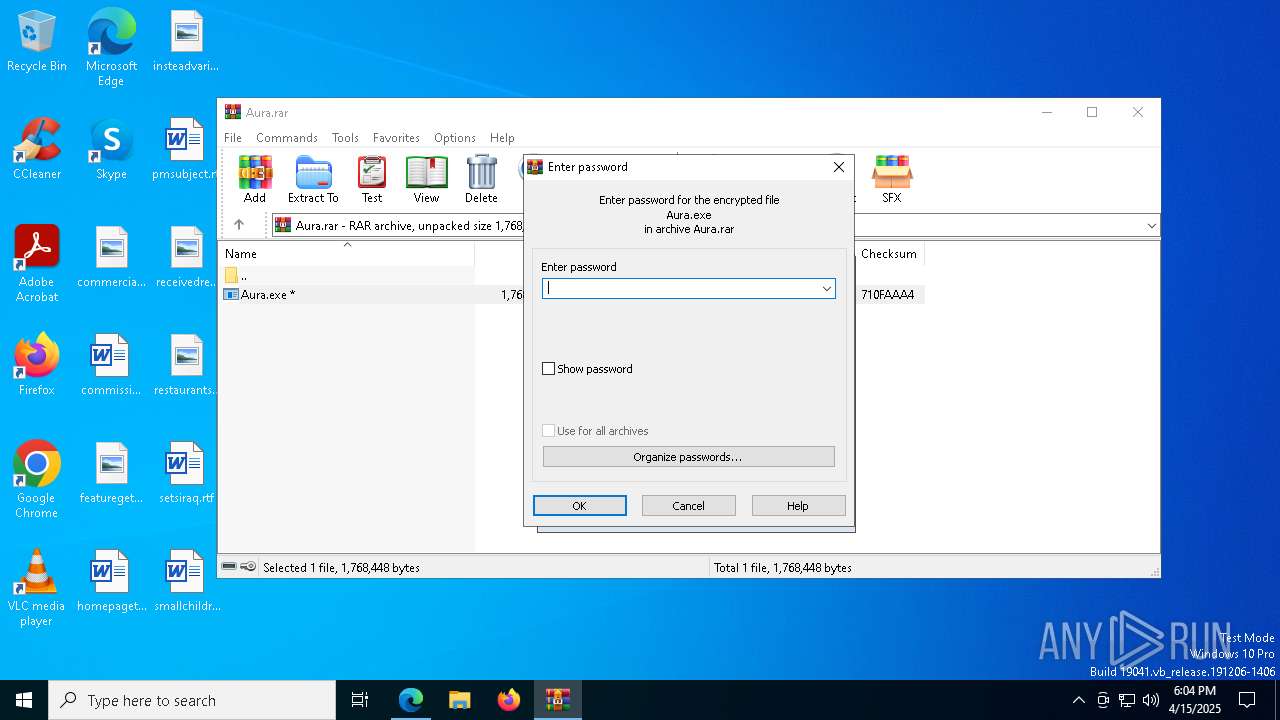
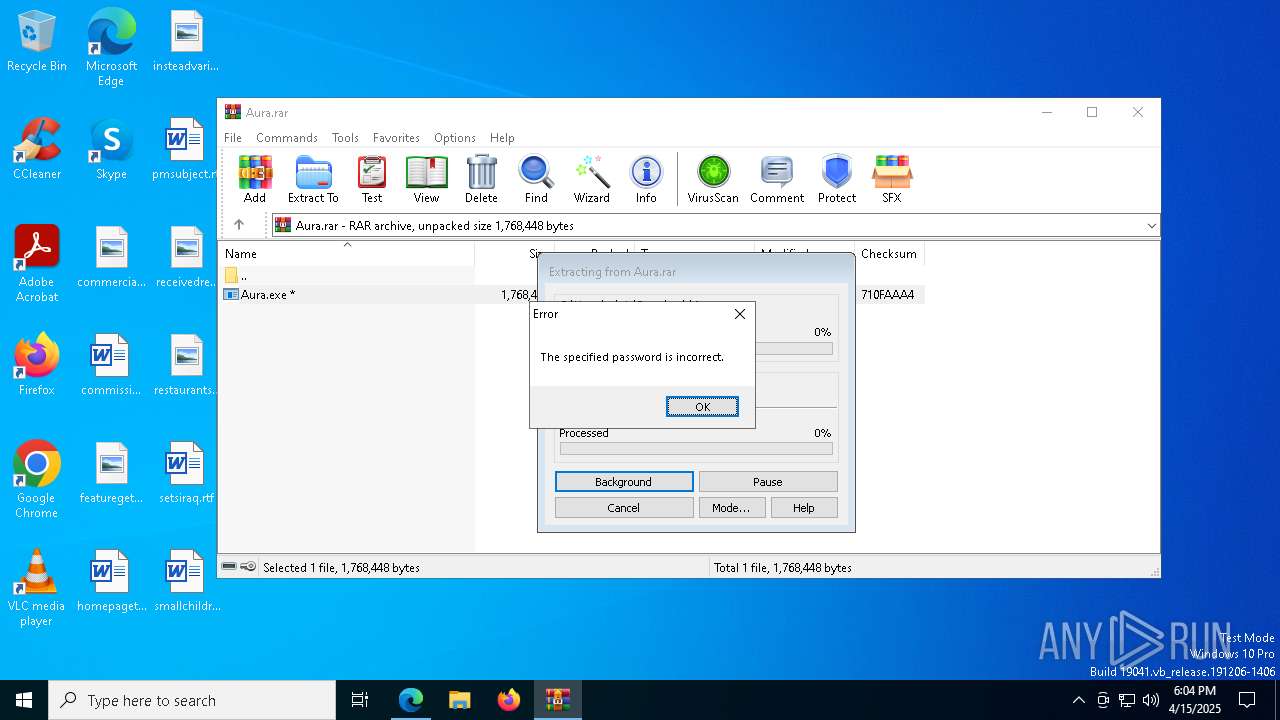
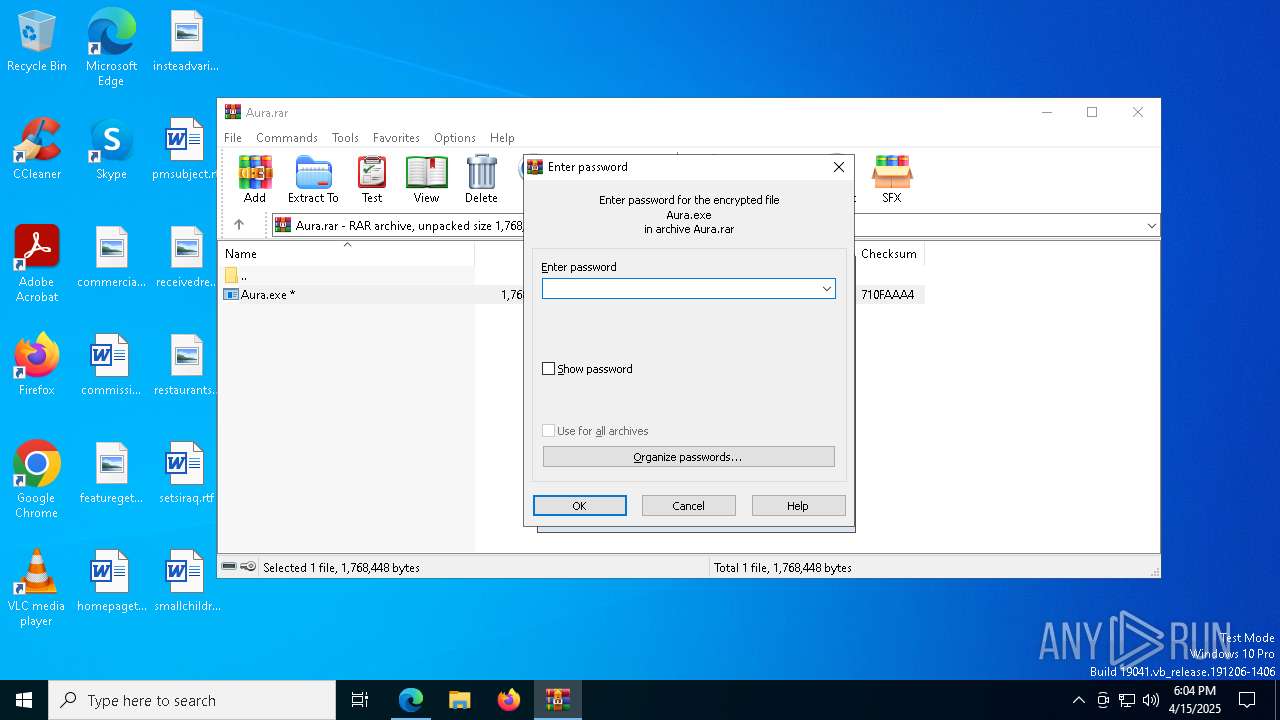
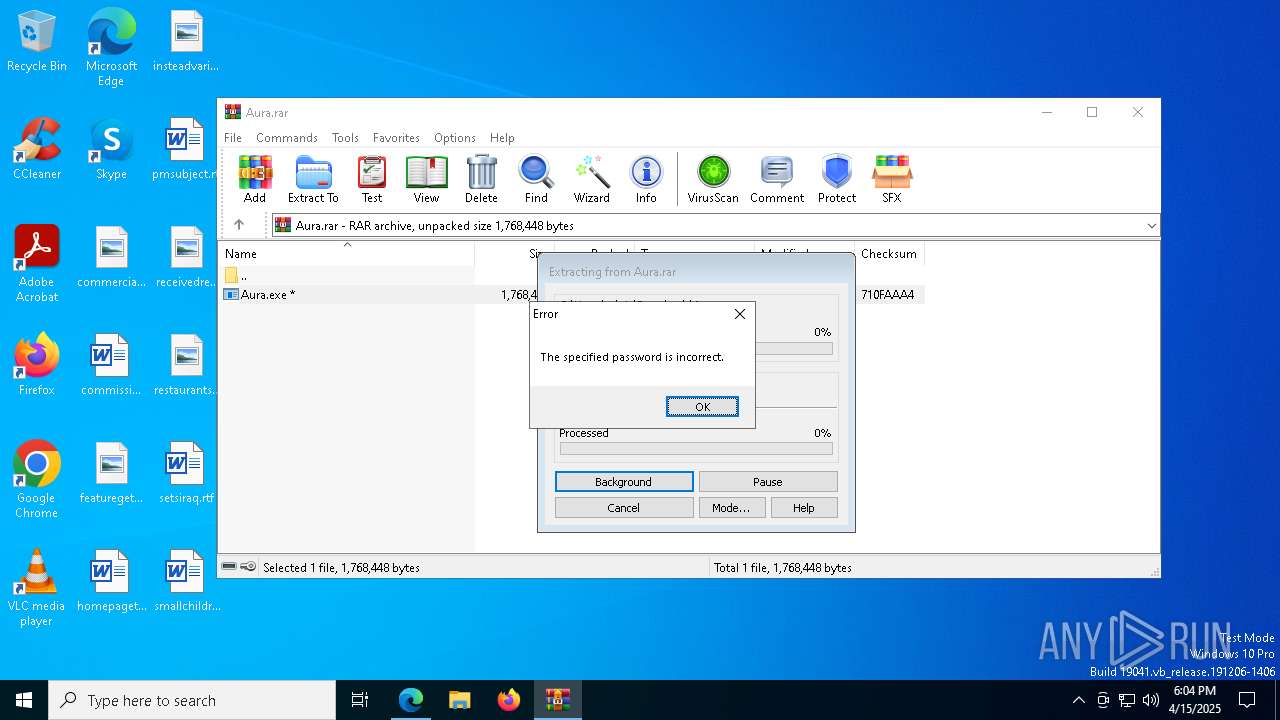
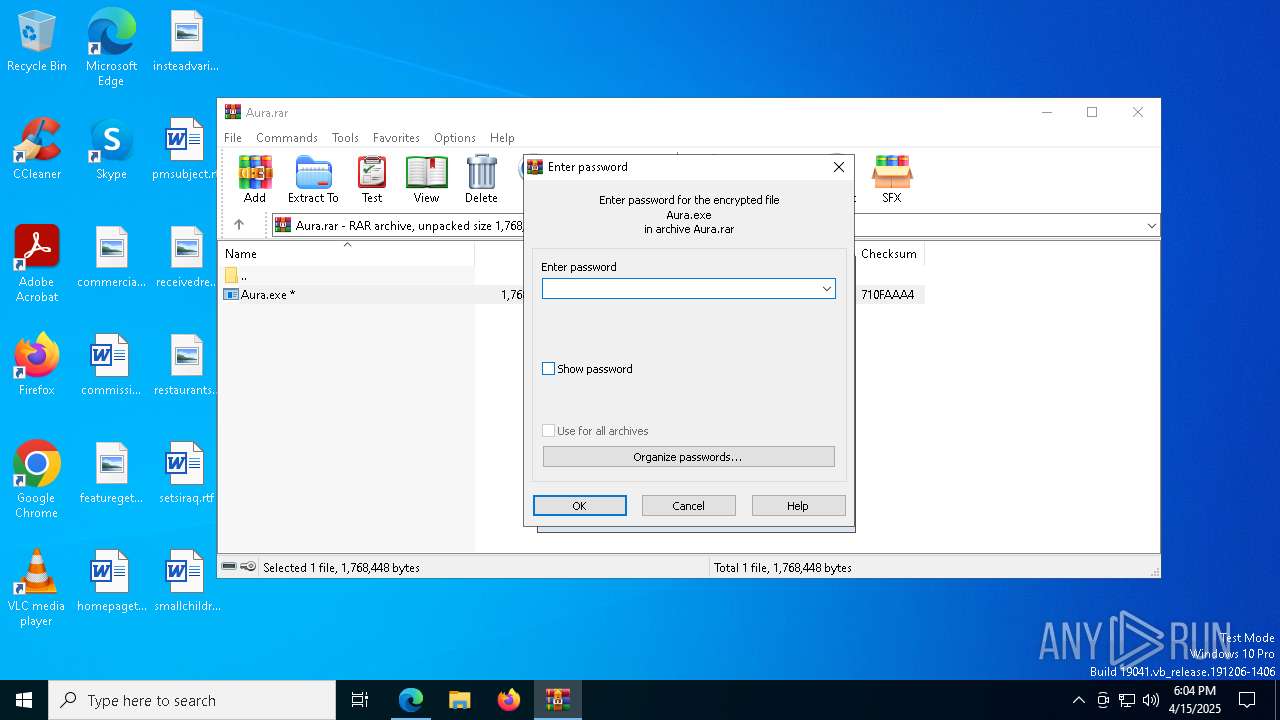
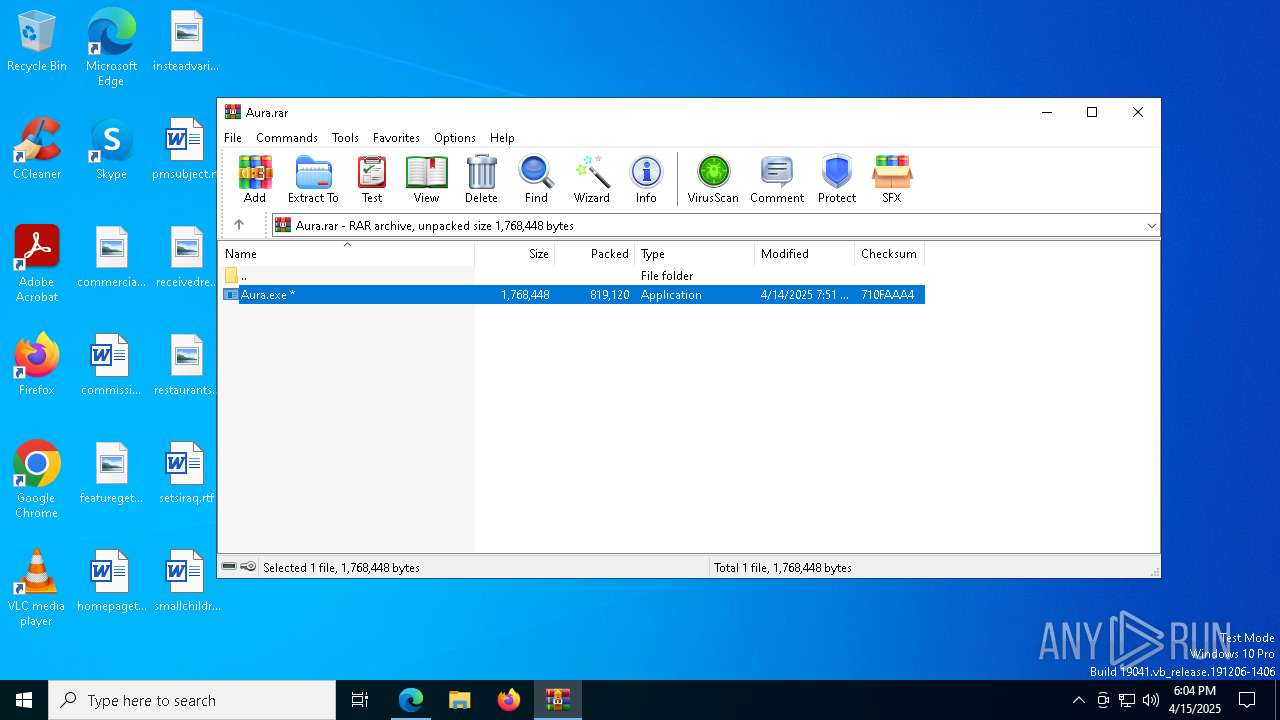
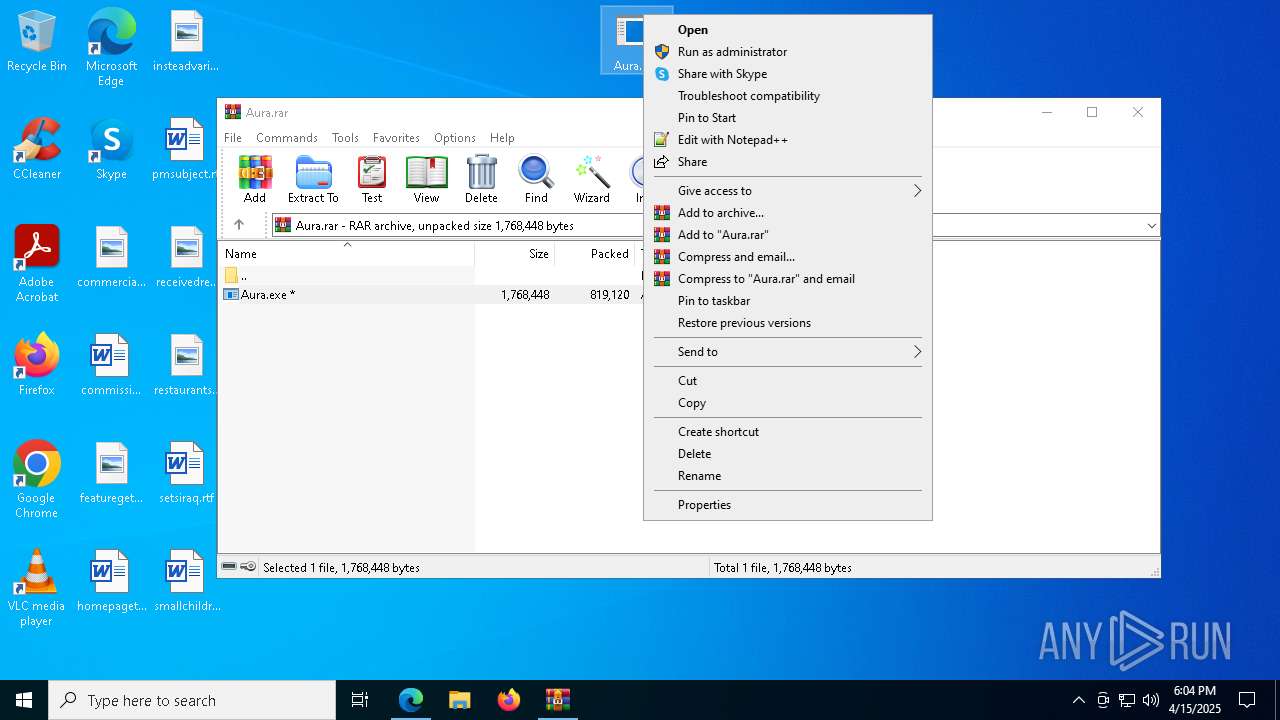
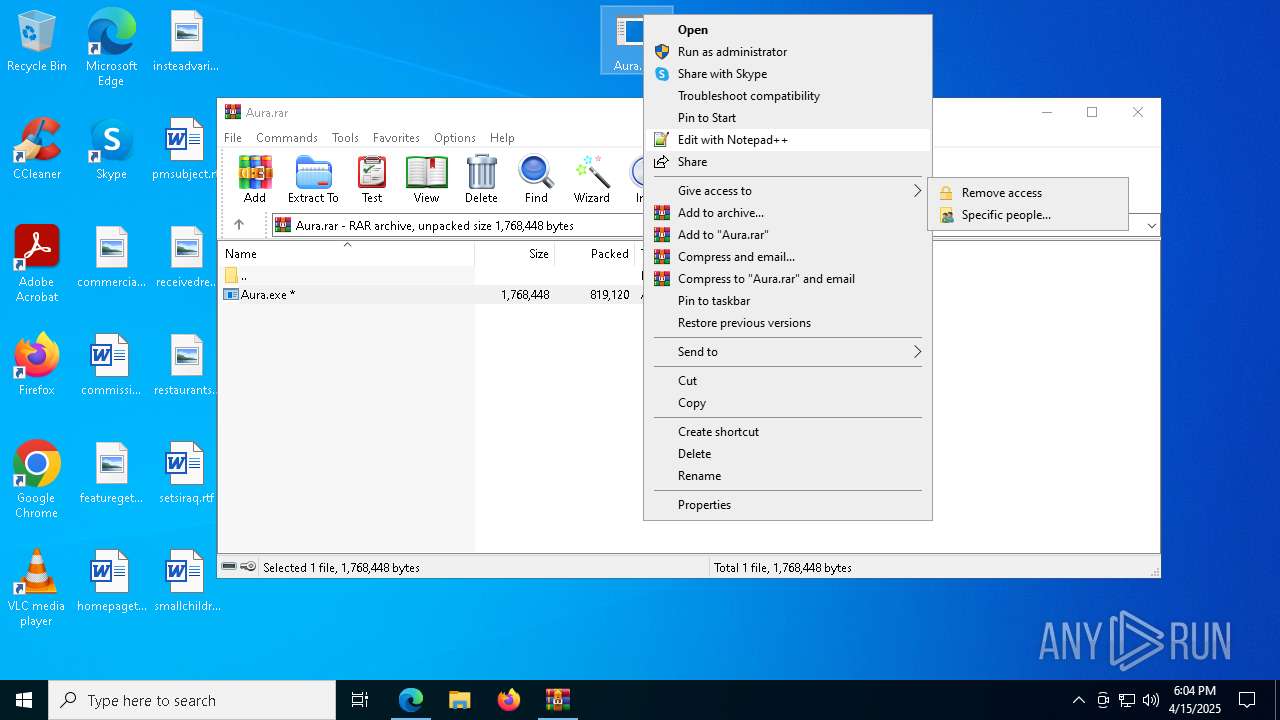
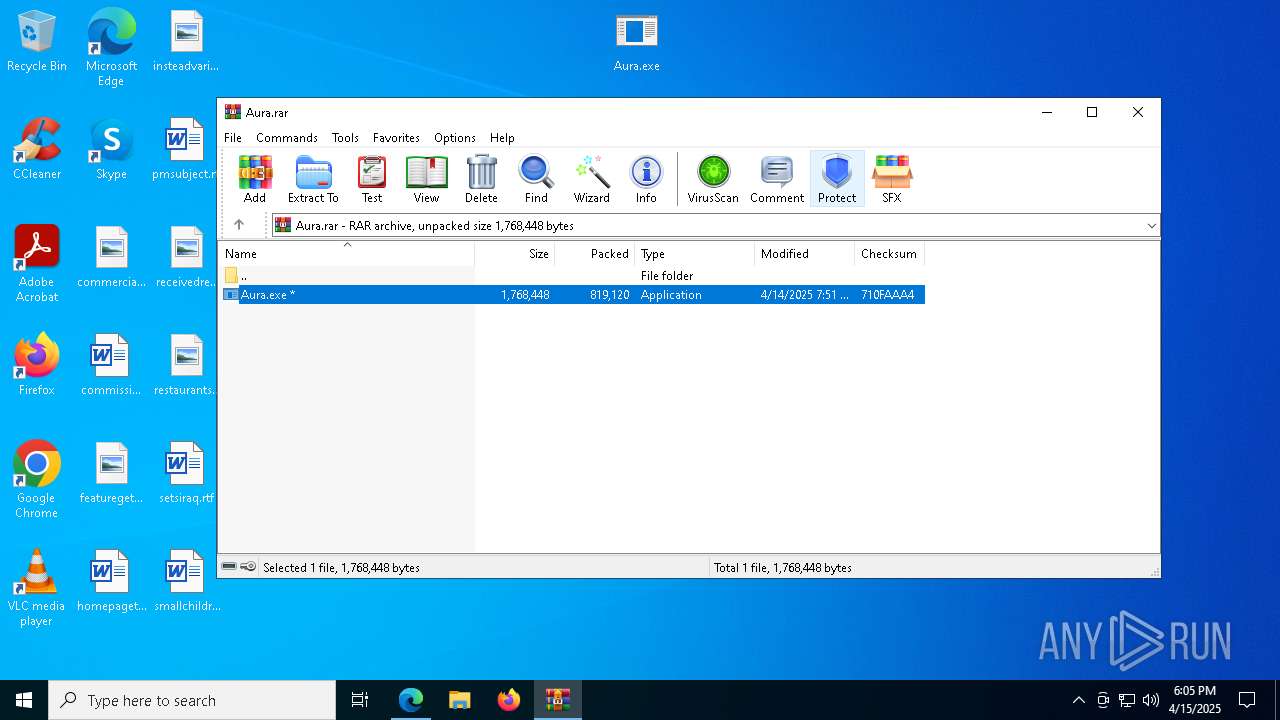
Process drops legitimate windows executable
- WinRAR.exe (PID: 2800)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2800)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
Searches for installed software
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 2316)
- MSBuild.exe (PID: 7156)
INFO
Checks supported languages
- identity_helper.exe (PID: 9096)
- Aura.exe (PID: 5428)
- MSBuild.exe (PID: 2316)
- identity_helper.exe (PID: 8176)
- MSBuild.exe (PID: 8456)
- Aura.exe (PID: 8176)
- Aura.exe (PID: 5956)
- MSBuild.exe (PID: 7156)
Reads Environment values
- identity_helper.exe (PID: 9096)
- identity_helper.exe (PID: 8176)
Reads the computer name
- identity_helper.exe (PID: 9096)
- MSBuild.exe (PID: 2316)
- identity_helper.exe (PID: 8176)
- MSBuild.exe (PID: 8456)
- MSBuild.exe (PID: 7156)
The sample compiled with english language support
- WinRAR.exe (PID: 2800)
- msedge.exe (PID: 8344)
Reads the software policy settings
- MSBuild.exe (PID: 2316)
- slui.exe (PID: 8084)
- MSBuild.exe (PID: 8456)
- slui.exe (PID: 8144)
- MSBuild.exe (PID: 7156)
Application launched itself
- msedge.exe (PID: 2140)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2800)
- msedge.exe (PID: 8344)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2140)
Checks proxy server information
- slui.exe (PID: 8144)
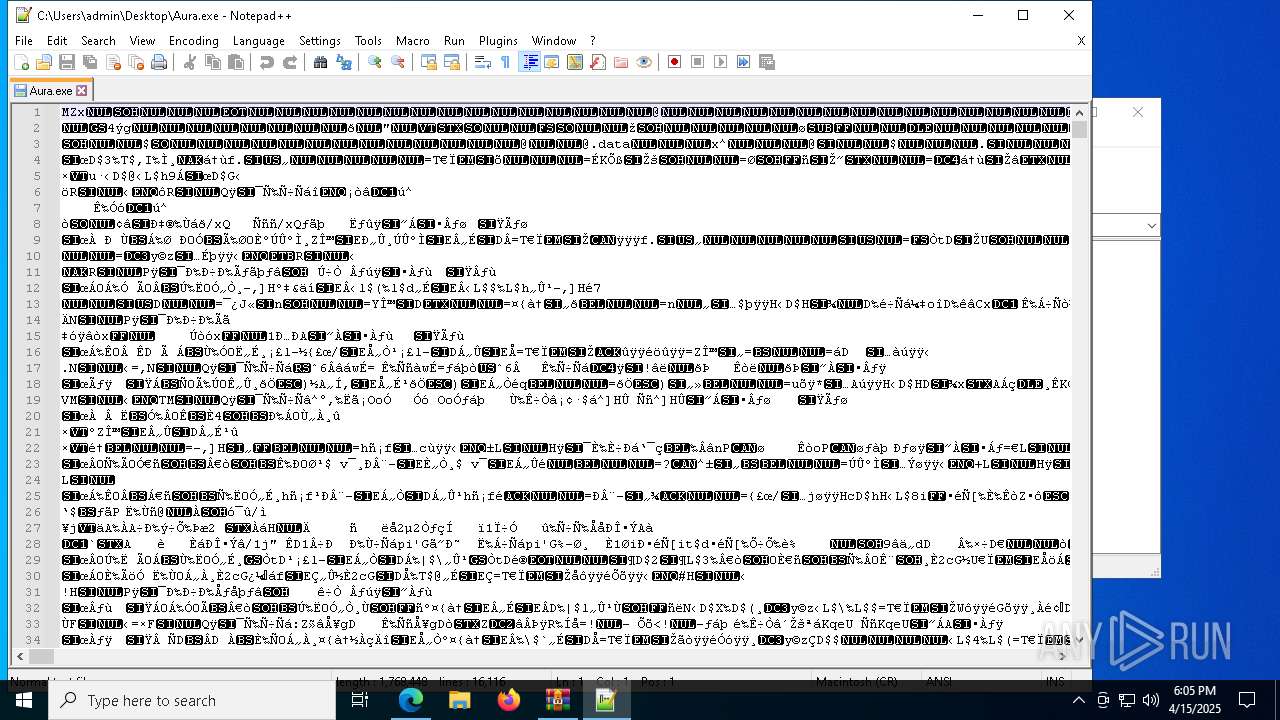
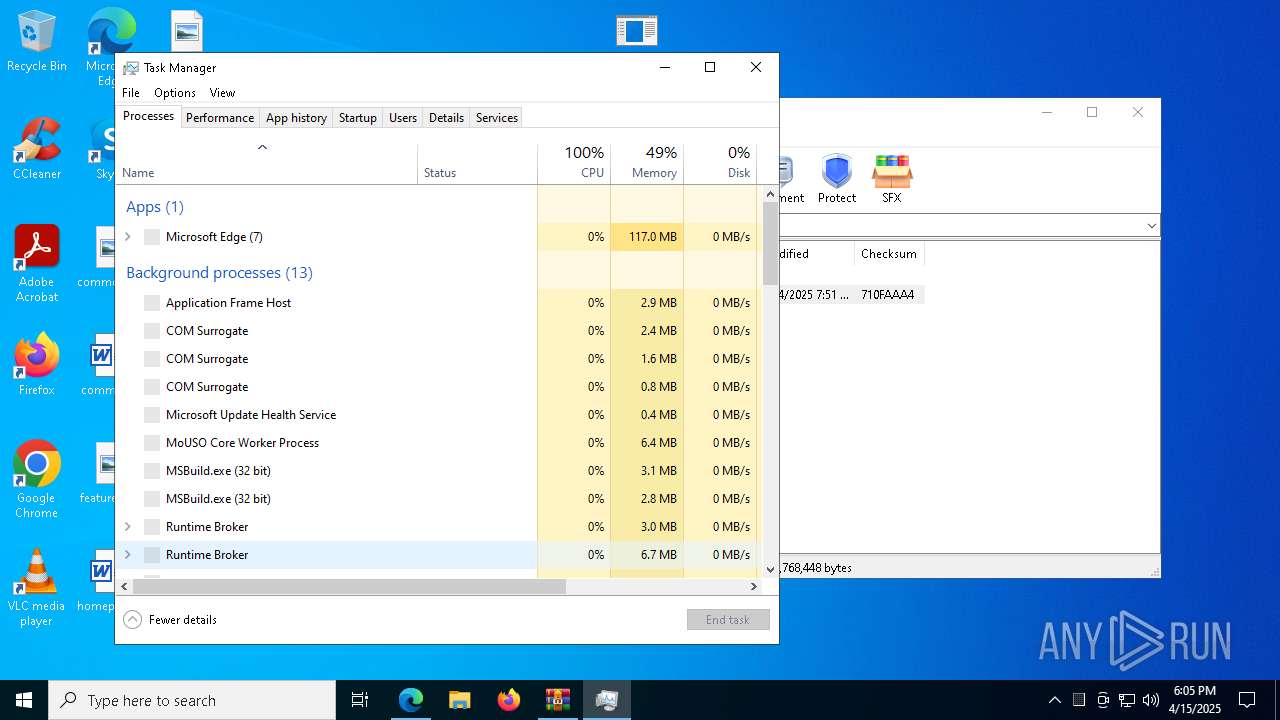
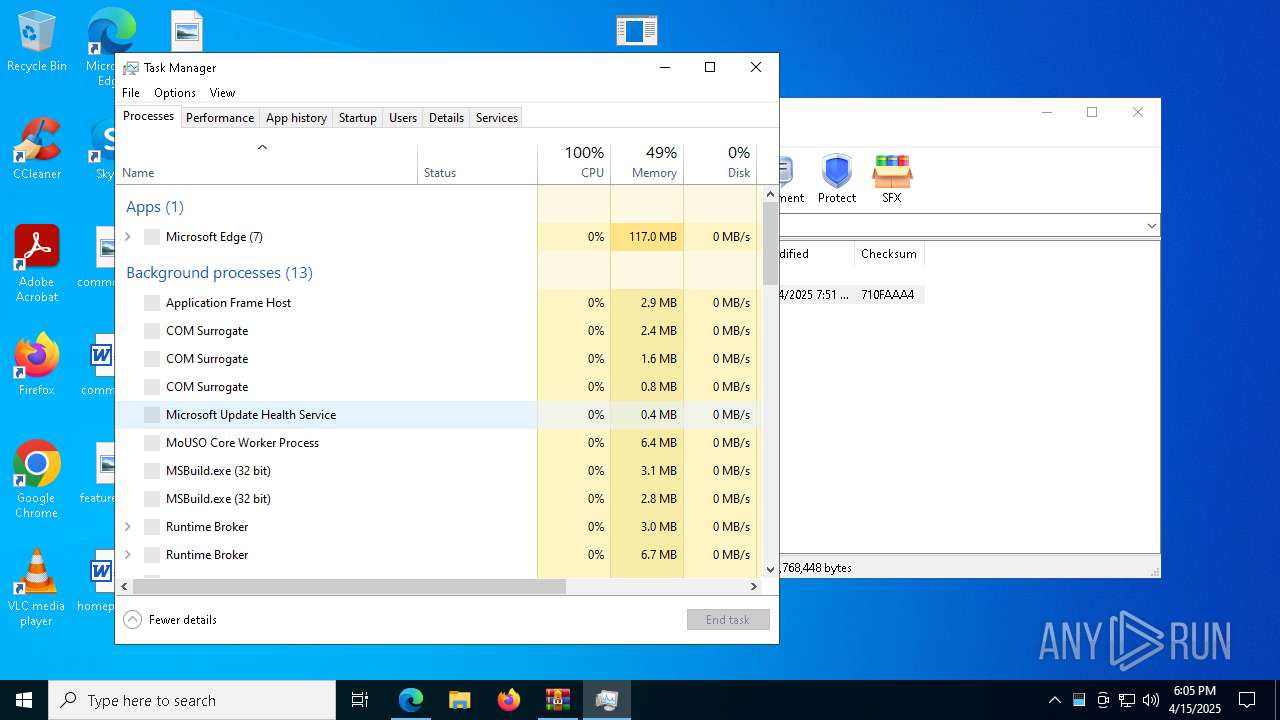
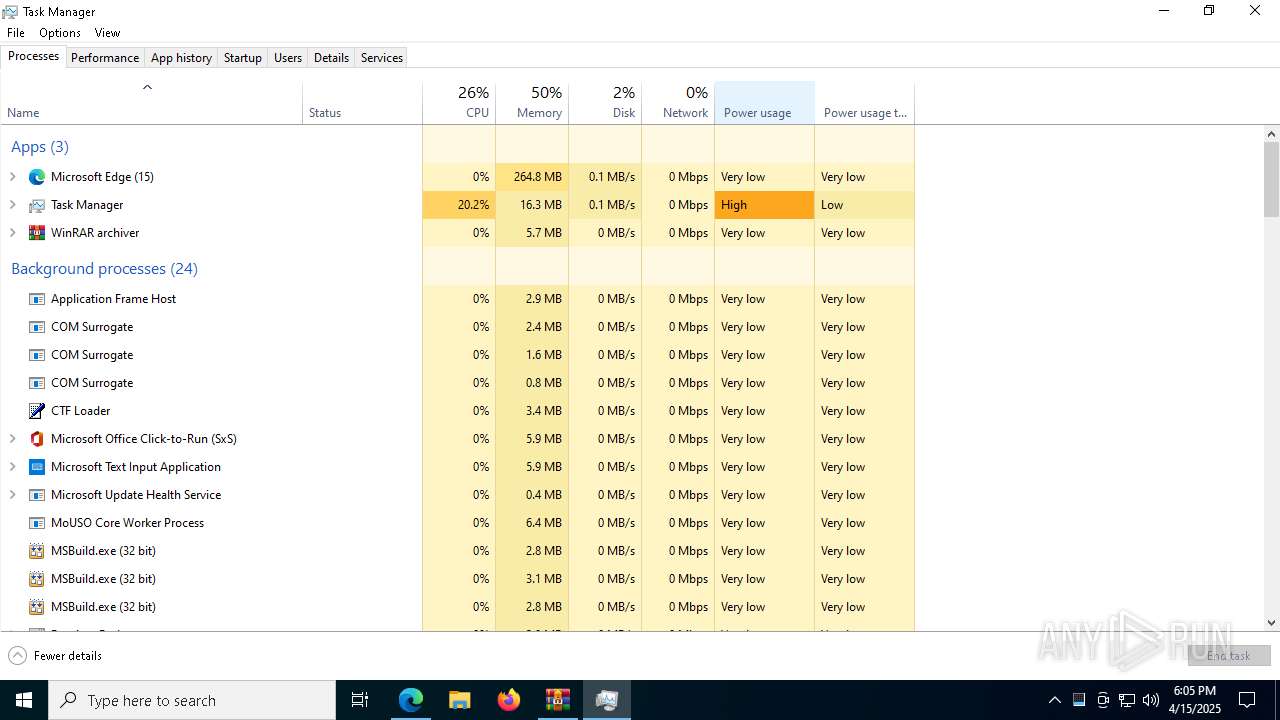
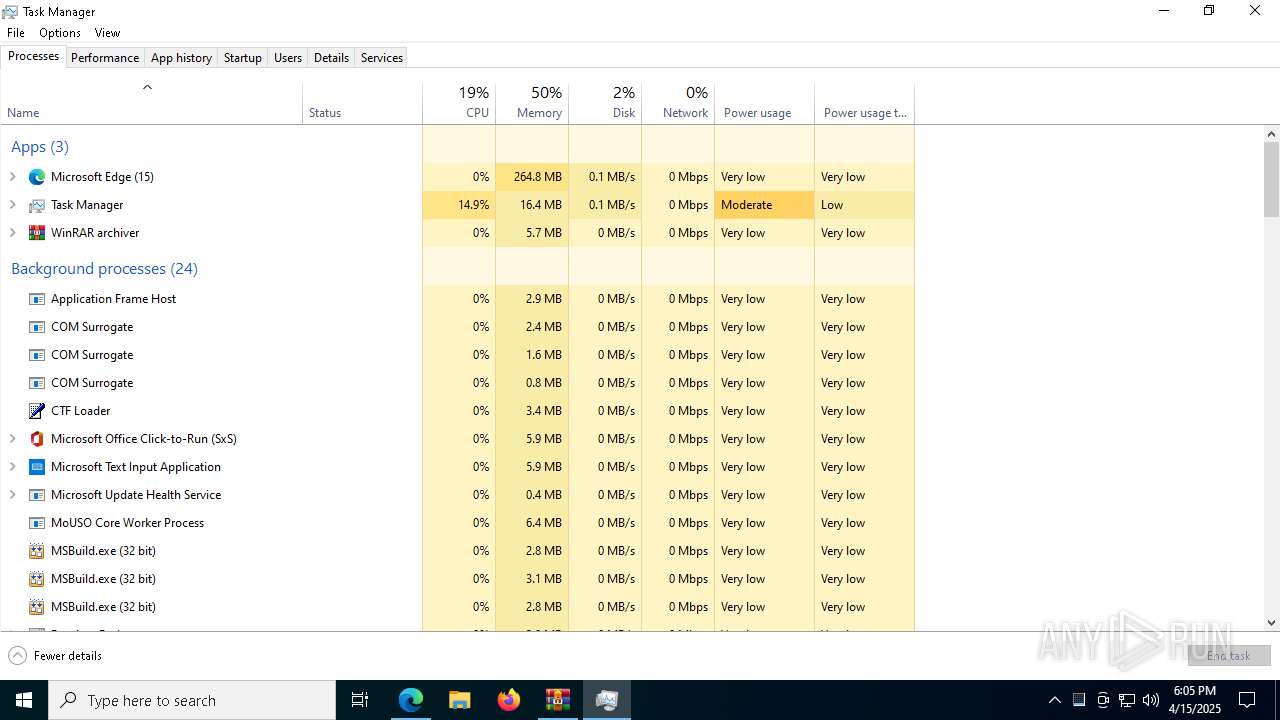
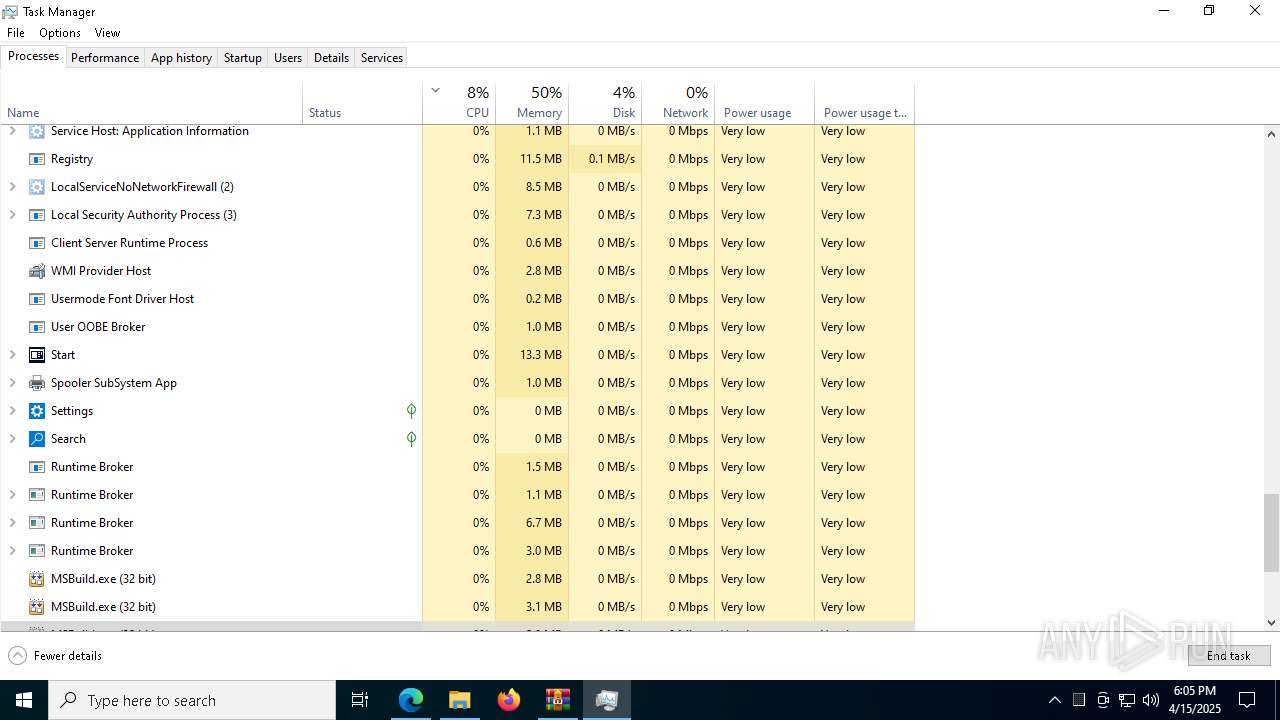
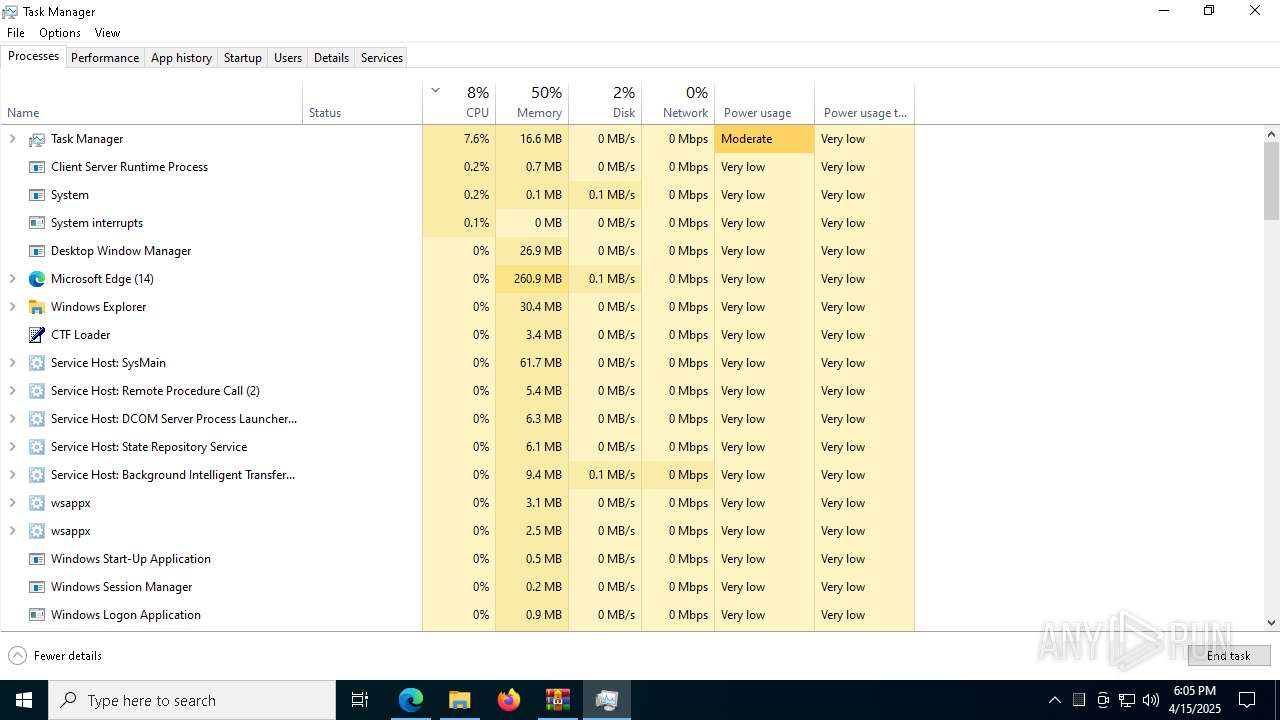
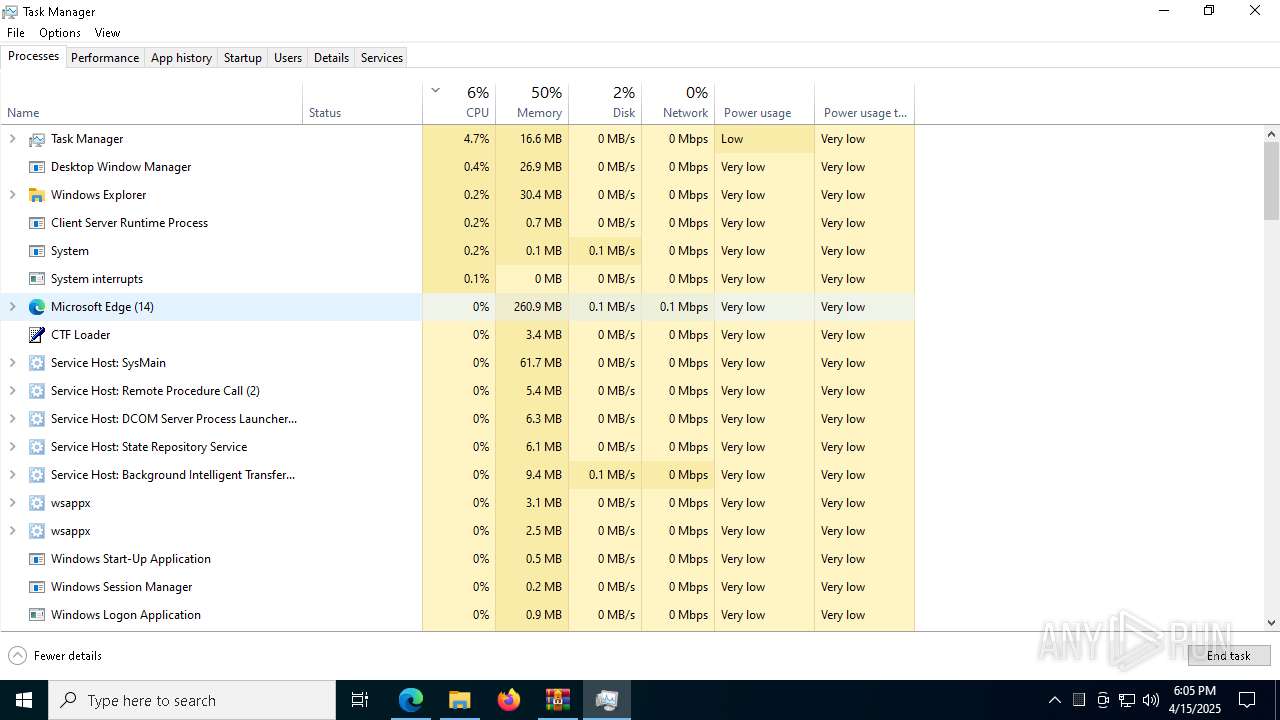
Manual execution by a user
- Aura.exe (PID: 5956)
- notepad++.exe (PID: 1812)
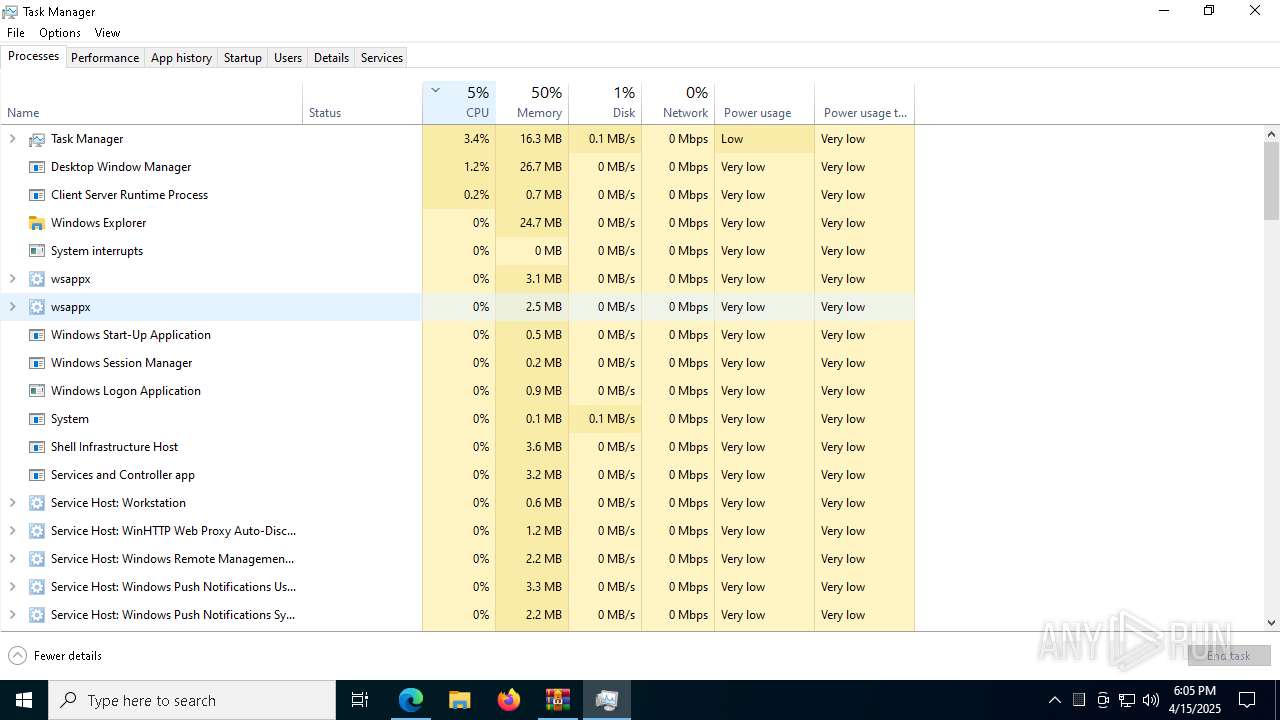
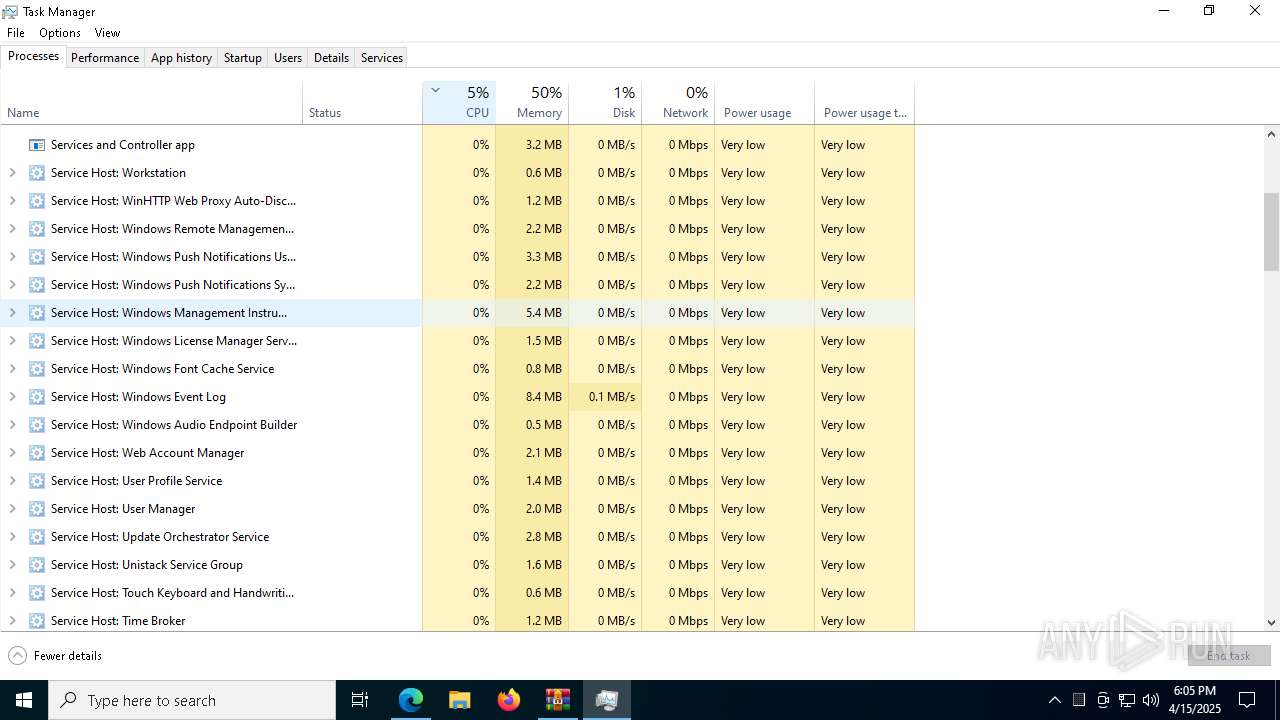
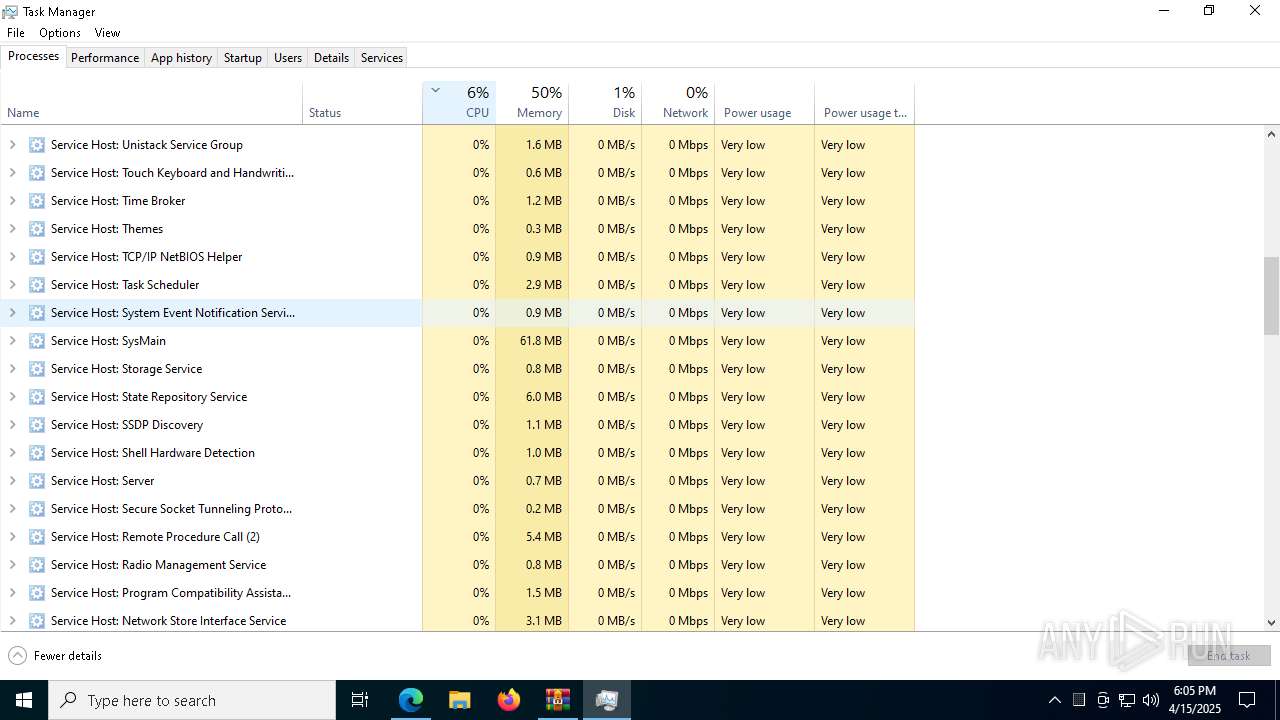
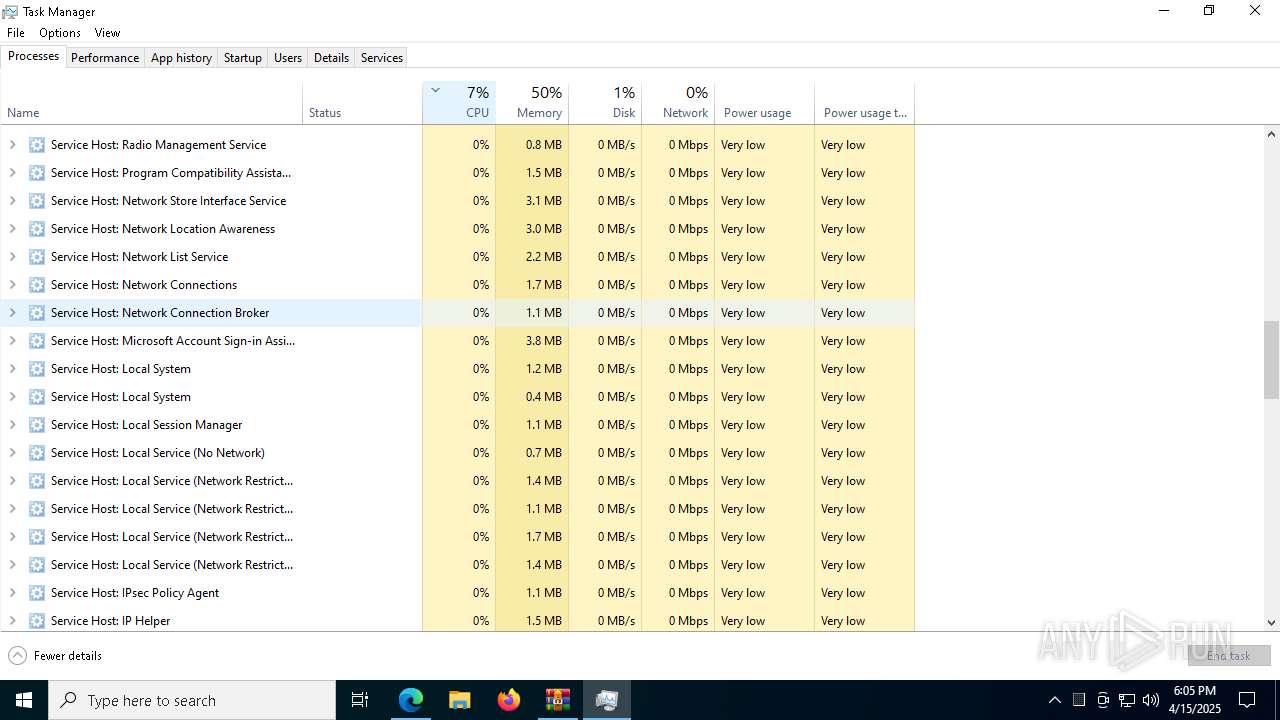
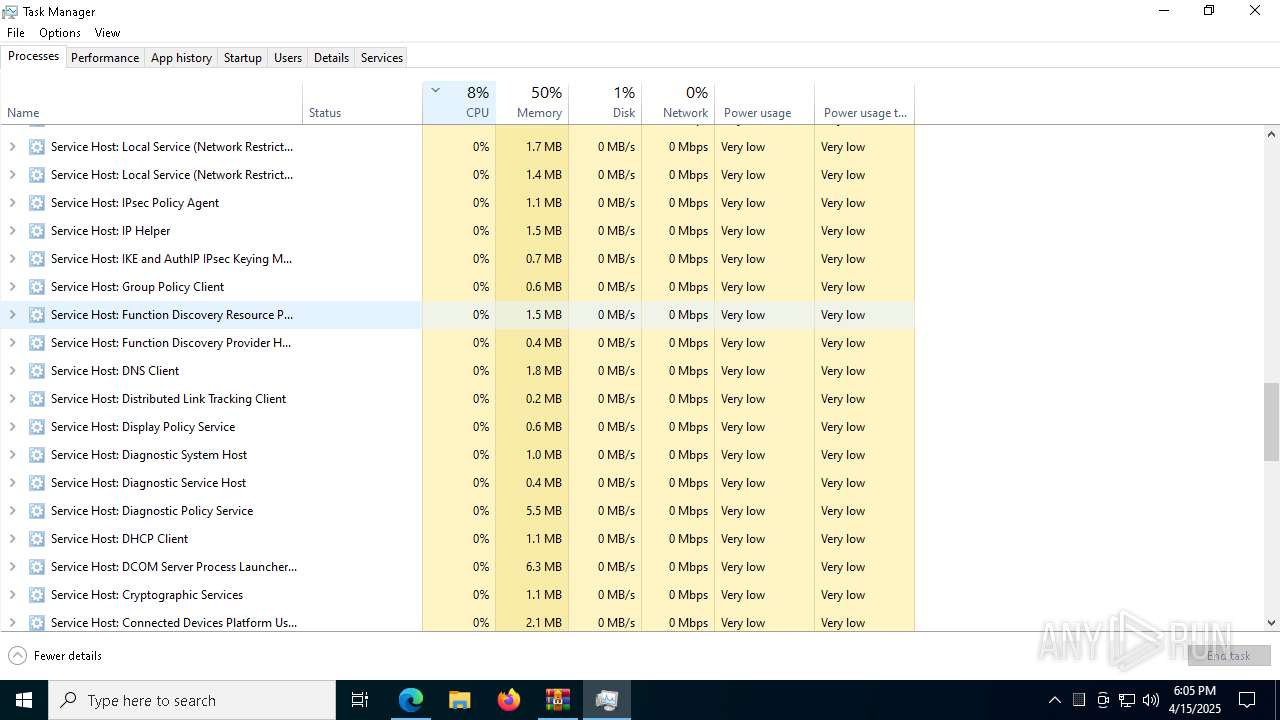
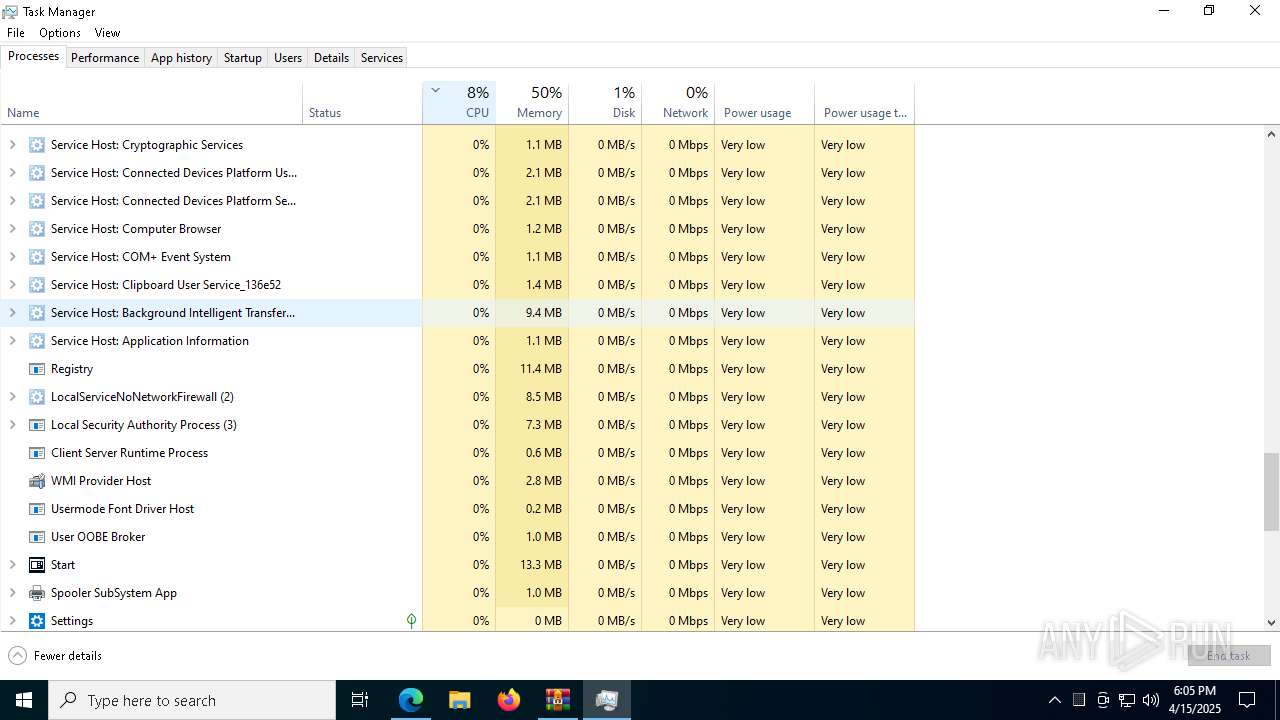
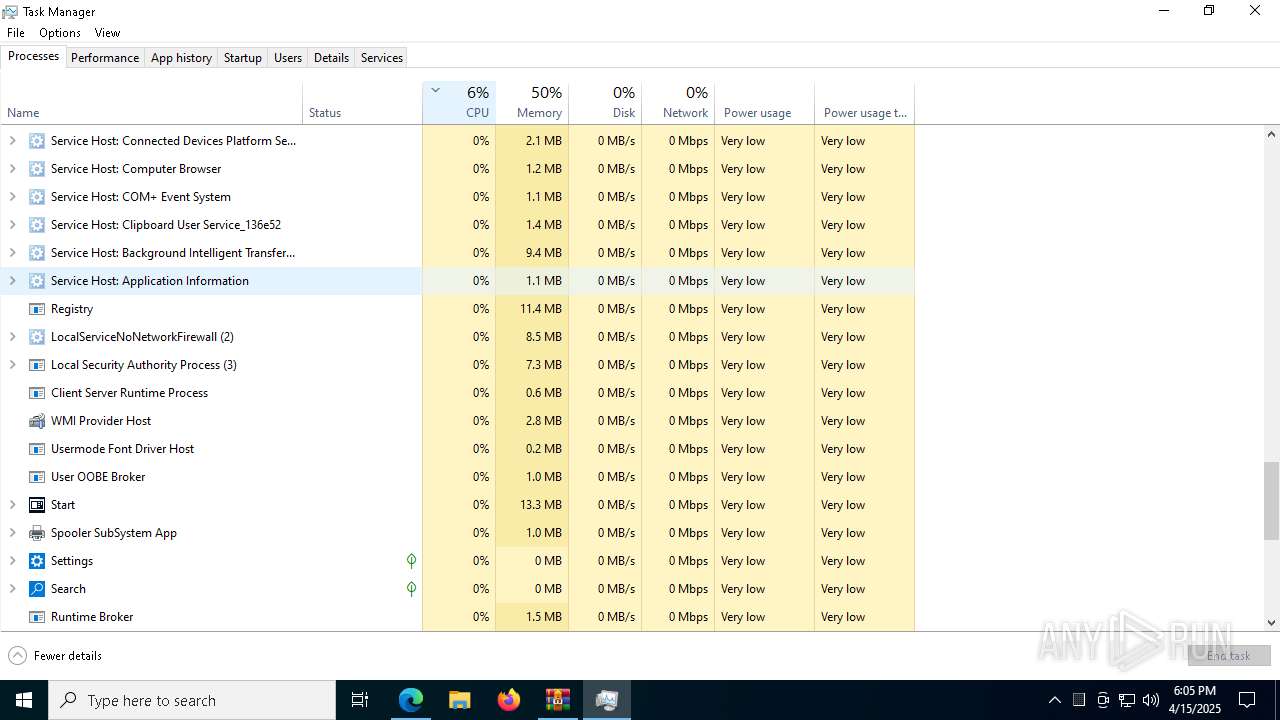
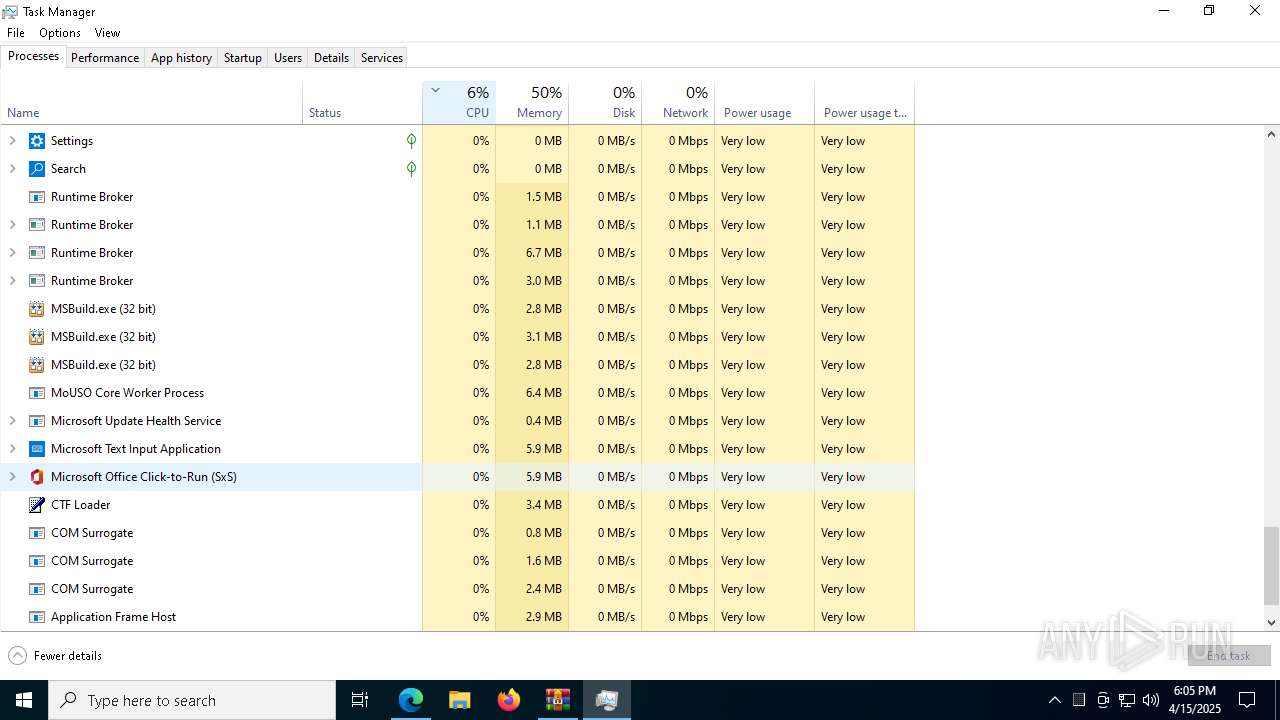
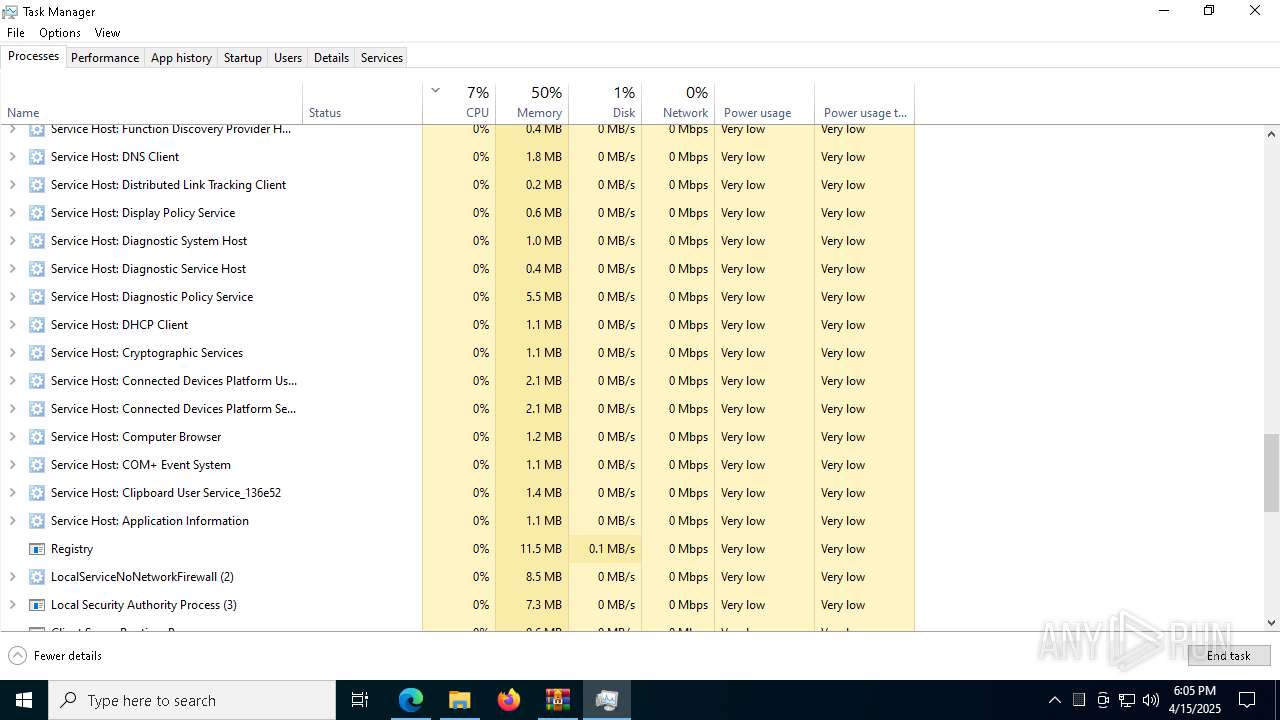
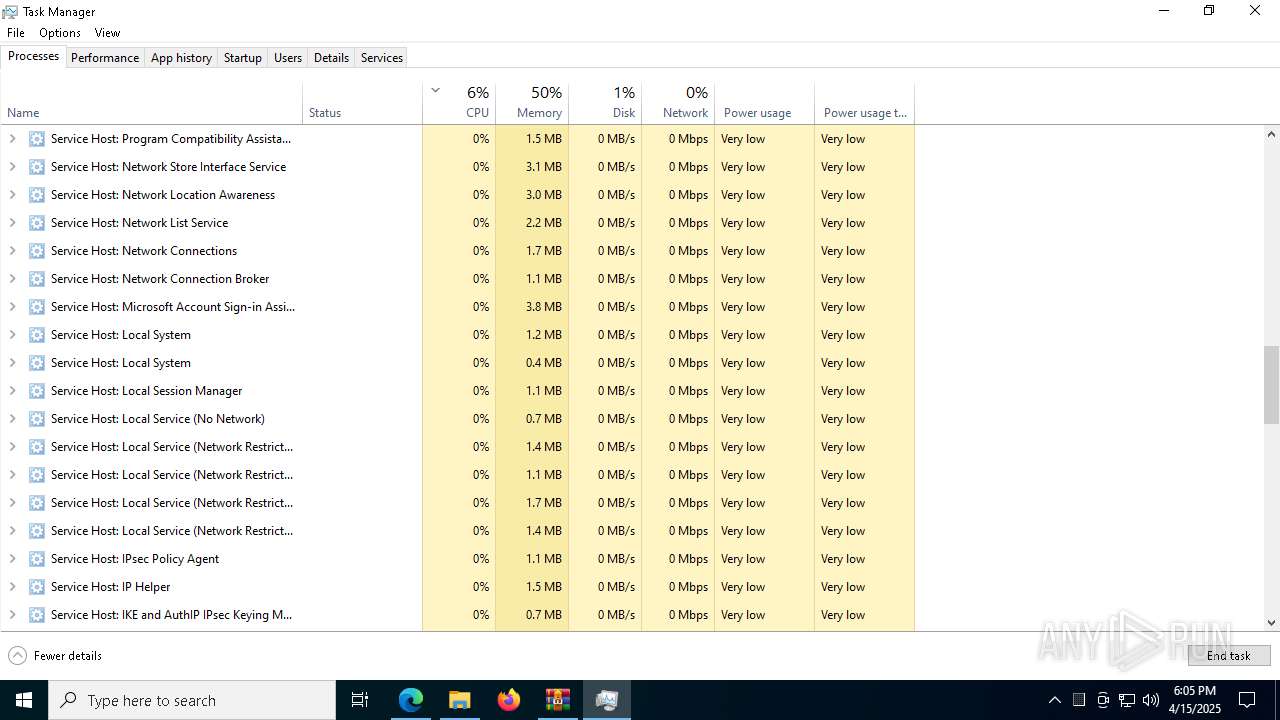
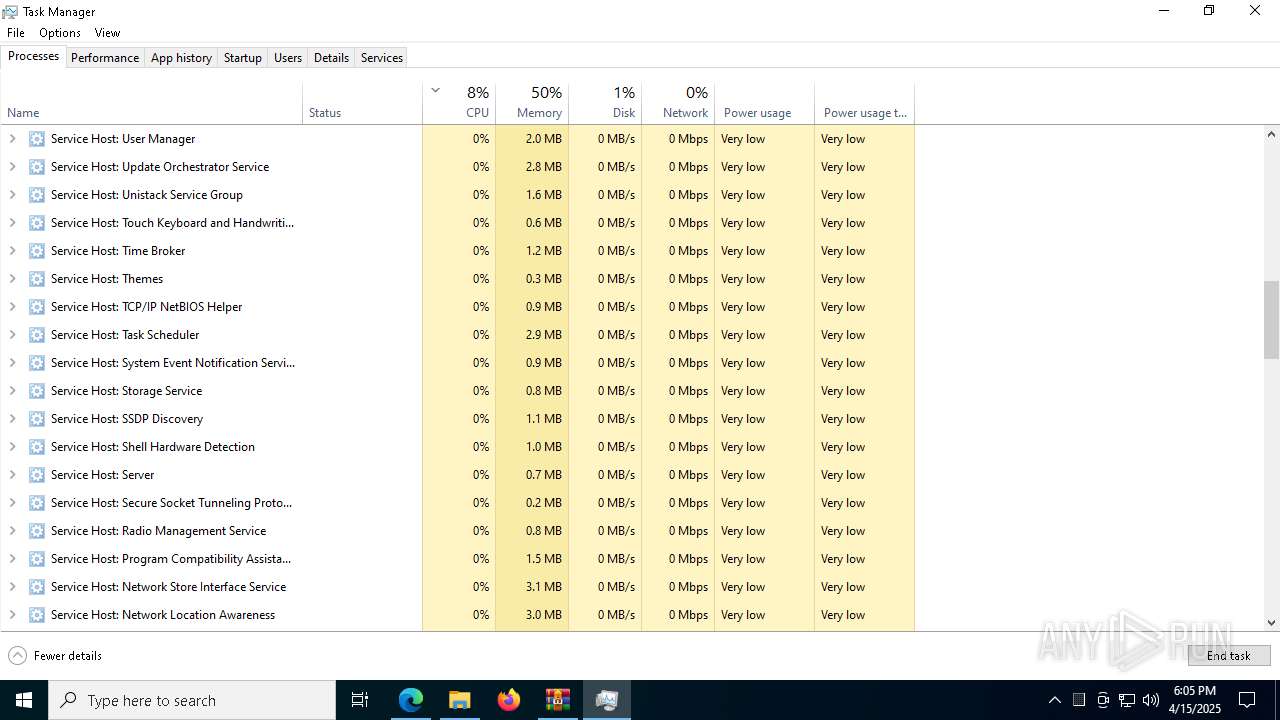
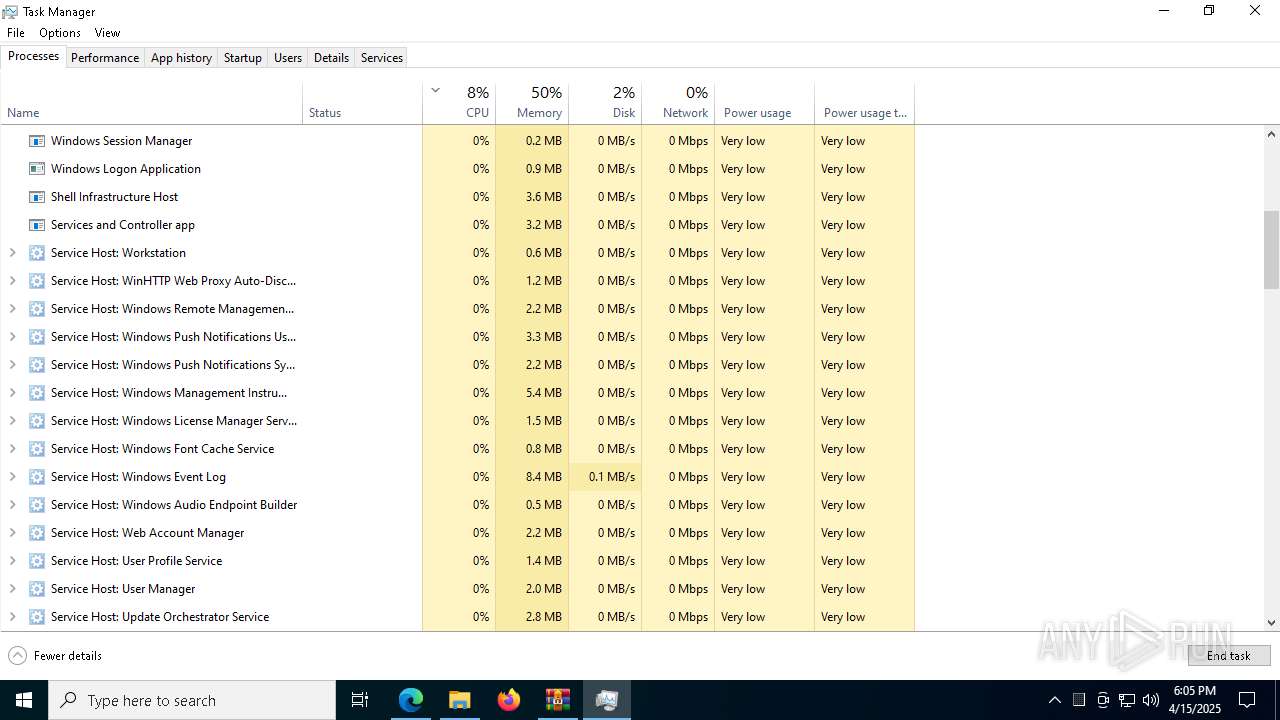
- Taskmgr.exe (PID: 8220)
- Taskmgr.exe (PID: 7708)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(2316) MSBuild.exe
C2 (9)changeaie.top/geps
jawdedmirror.run/ewqd
owlflright.digital/qopy
zestmodp.top/zeda
lonfgshadow.live/xawi
clarmodq.top/qoxo
nighetwhisper.top/lekd
liftally.top/xasj
salaccgfa.top/gsooz
(PID) Process(8456) MSBuild.exe
C2 (9)changeaie.top/geps
jawdedmirror.run/ewqd
owlflright.digital/qopy
zestmodp.top/zeda
lonfgshadow.live/xawi
clarmodq.top/qoxo
nighetwhisper.top/lekd
liftally.top/xasj
salaccgfa.top/gsooz
(PID) Process(7156) MSBuild.exe
C2 (9)changeaie.top/geps
jawdedmirror.run/ewqd
owlflright.digital/qopy
zestmodp.top/zeda
lonfgshadow.live/xawi
clarmodq.top/qoxo
nighetwhisper.top/lekd
liftally.top/xasj
salaccgfa.top/gsooz
Total processes
228
Monitored processes
91
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=6448 --field-trial-handle=2340,i,5897419830959788550,17312062379349259699,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=9204 --field-trial-handle=2340,i,5897419830959788550,17312062379349259699,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8104 --field-trial-handle=2340,i,5897419830959788550,17312062379349259699,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=7068 --field-trial-handle=2340,i,5897419830959788550,17312062379349259699,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
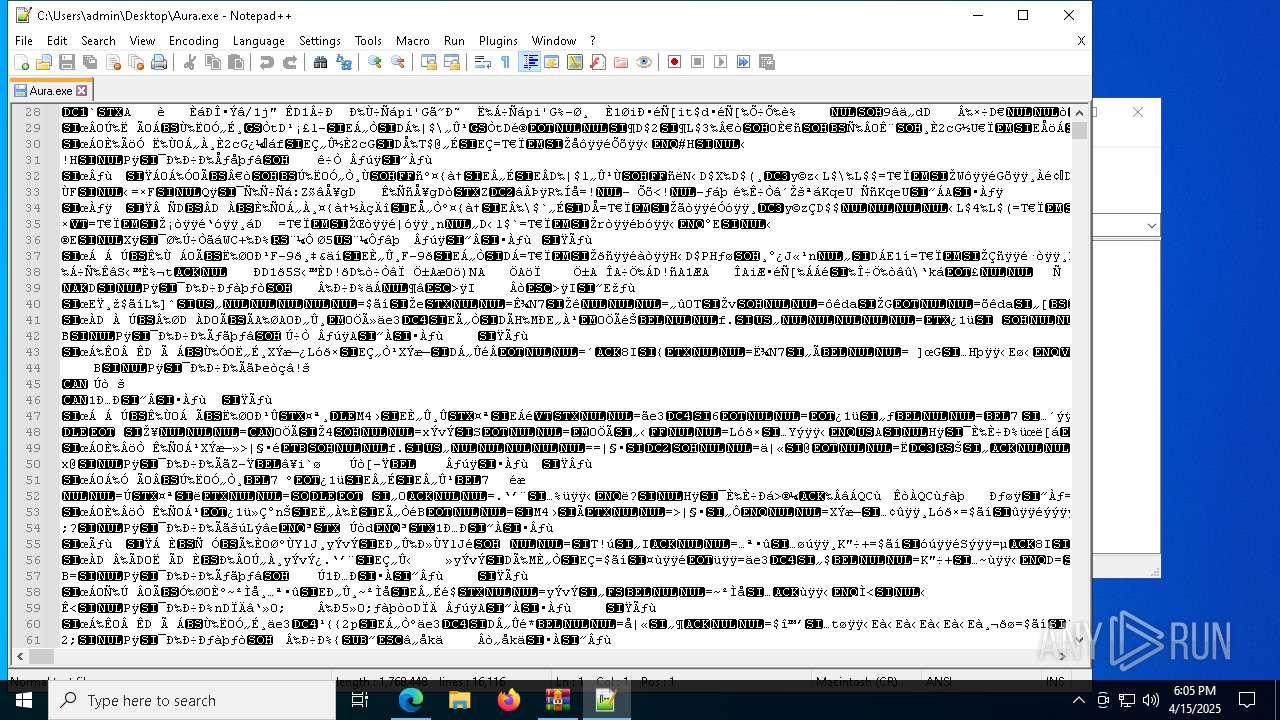
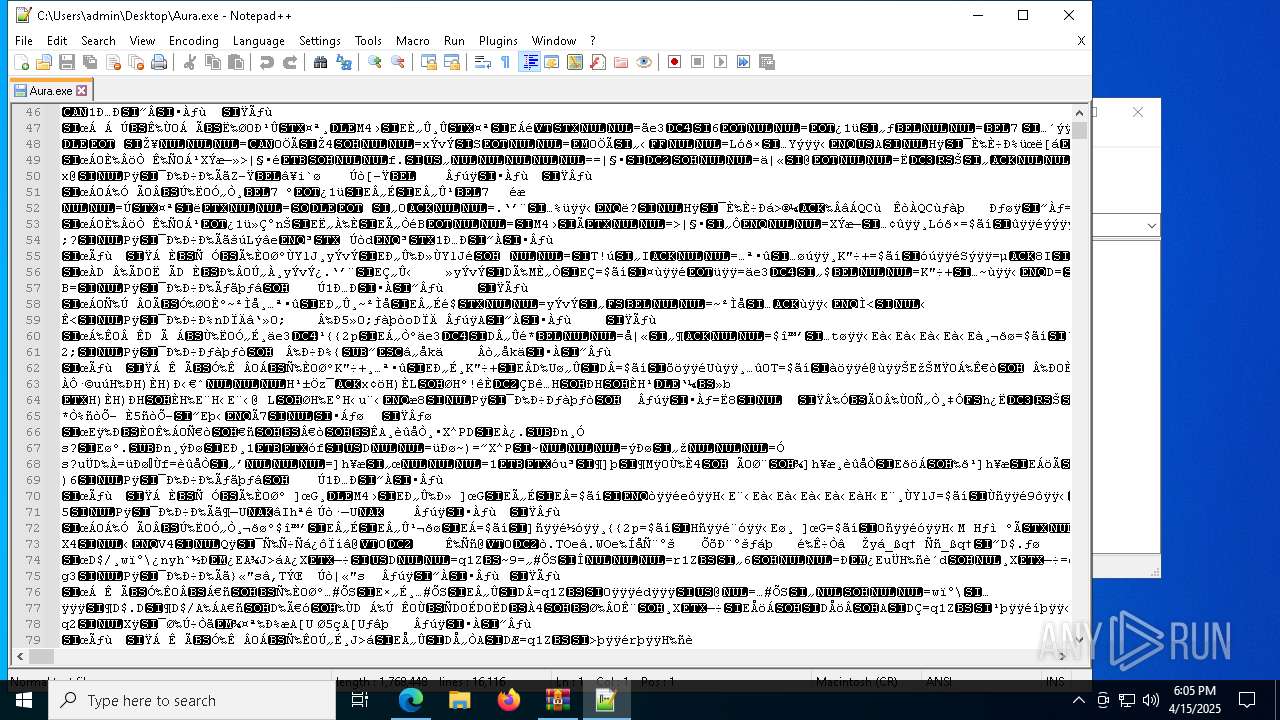
| 1812 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\Aura.exe" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 2084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6216 --field-trial-handle=2340,i,5897419830959788550,17312062379349259699,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.youtube.com/redirect?event=video_description&redir_token=QUFFLUhqbExMZ2N5RmlydE1pQ2JULU9UY1loZVlDRUJmZ3xBQ3Jtc0tsUUtKUkZwTkxTeFNZNFlKcnJ0VTVoUXpNdERscjRjZW1zcEJ1VDJubHdId2E0UjRKTnI5ZXQzeG9ISzVJekk5c0g0aUdsTWx0bjdFRWJXNWFuUWVYUDlXaTlUZnl0eEpnSW9RRWY2bUZEekNQdDJoTQ&q=https%3A%2F%2Fwww.mediafire.com%2Ffolder%2F04j4vnir8gk1o%2FAura&v=5xrQ_9sfipA" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7744 --field-trial-handle=2340,i,5897419830959788550,17312062379349259699,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2316 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | Aura.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
Lumma(PID) Process(2316) MSBuild.exe C2 (9)changeaie.top/geps jawdedmirror.run/ewqd owlflright.digital/qopy zestmodp.top/zeda lonfgshadow.live/xawi clarmodq.top/qoxo nighetwhisper.top/lekd liftally.top/xasj salaccgfa.top/gsooz | |||||||||||||||
Total events
13 575
Read events
13 526
Write events
48
Delete events
1
Modification events
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3804813F6B912F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4B3E913F6B912F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5A47CC1F-3453-4870-97BC-12EEEBAE71DB} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {99F1EC47-0BC0-4CC6-AA40-4AF88C73EFD8} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BB95C43F6B912F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
28
Suspicious files
582
Text files
99
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b9cc.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b9cc.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b9dc.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba0b.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ba0b.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
296
DNS requests
370
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7556 | svchost.exe | HEAD | 200 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
7556 | svchost.exe | GET | 206 | 23.50.131.85:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1744952135&P2=404&P3=2&P4=BmTvkt275MV5sAta9%2fSdhHiNGMScn0xirWuIDIj7csuS61z%2b54MufrFI1Y2Pp7rRa%2fKIr%2f25d%2bmi4m0y3Kg2iw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.48.23.190:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2140 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7216 | msedge.exe | 142.250.184.238:443 | www.youtube.com | — | — | whitelisted |
7216 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7216 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7216 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.youtube.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7216 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7216 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7216 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7216 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7216 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |