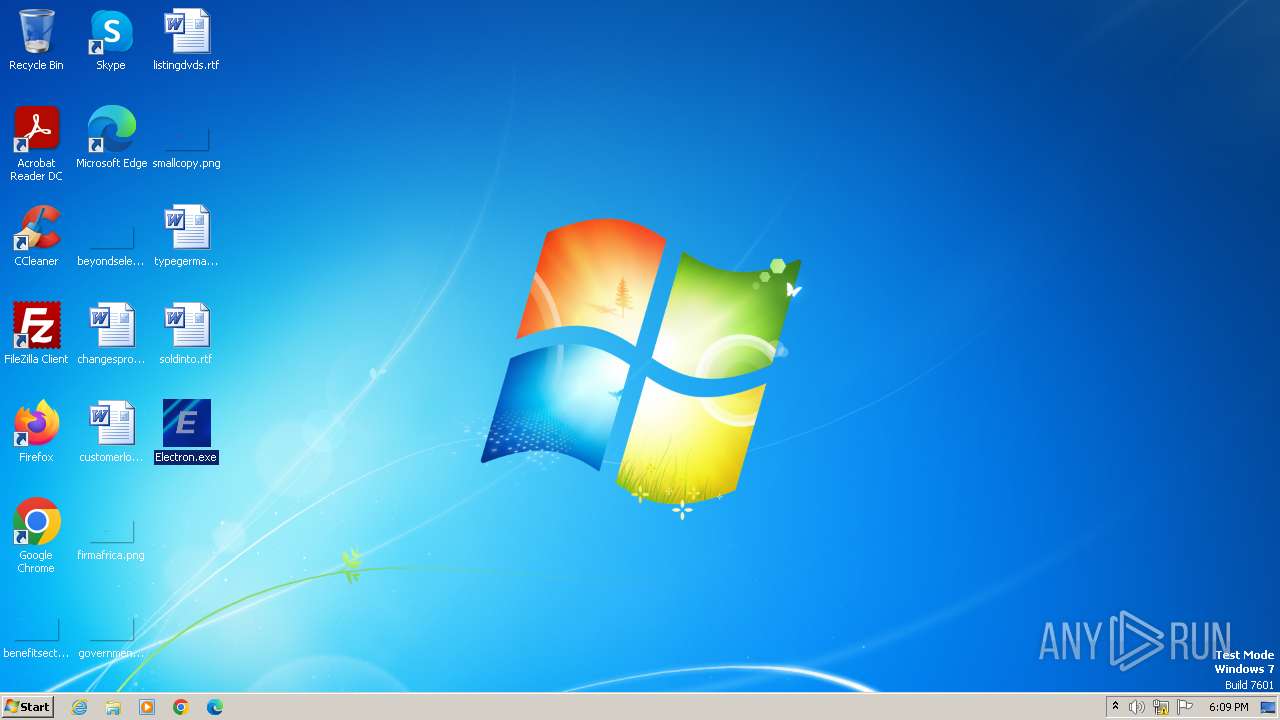
| File name: | Electron.exe |
| Full analysis: | https://app.any.run/tasks/5bf45d9a-dde3-4751-8af6-f5c1338cc86d |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 02, 2023, 18:09:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5DD7500F21ADD8F9BC322529A35CB55F |
| SHA1: | B12EEC8FDF6224F65E27FB9D9B06DC4375E1B37B |
| SHA256: | 48D2D3E579BBCDDDA54AA5BD48197B179CA7B75018D05CE12FF3CF9E7B78E40E |
| SSDEEP: | 98304:x2uiieRyd72QsLDil92m3GJEDgwaRRdX6j77E:amglQ |
MALICIOUS
QUASAR has been detected (SURICATA)
- Electron.exe (PID: 2980)
ASYNCRAT has been detected (SURICATA)
- Electron.exe (PID: 2980)
Connects to the CnC server
- Electron.exe (PID: 2980)
QUASAR has been detected (YARA)
- Electron.exe (PID: 2980)
SUSPICIOUS
Reads the Internet Settings
- Electron.exe (PID: 2980)
Reads settings of System Certificates
- Electron.exe (PID: 2980)
Connects to unusual port
- Electron.exe (PID: 2980)
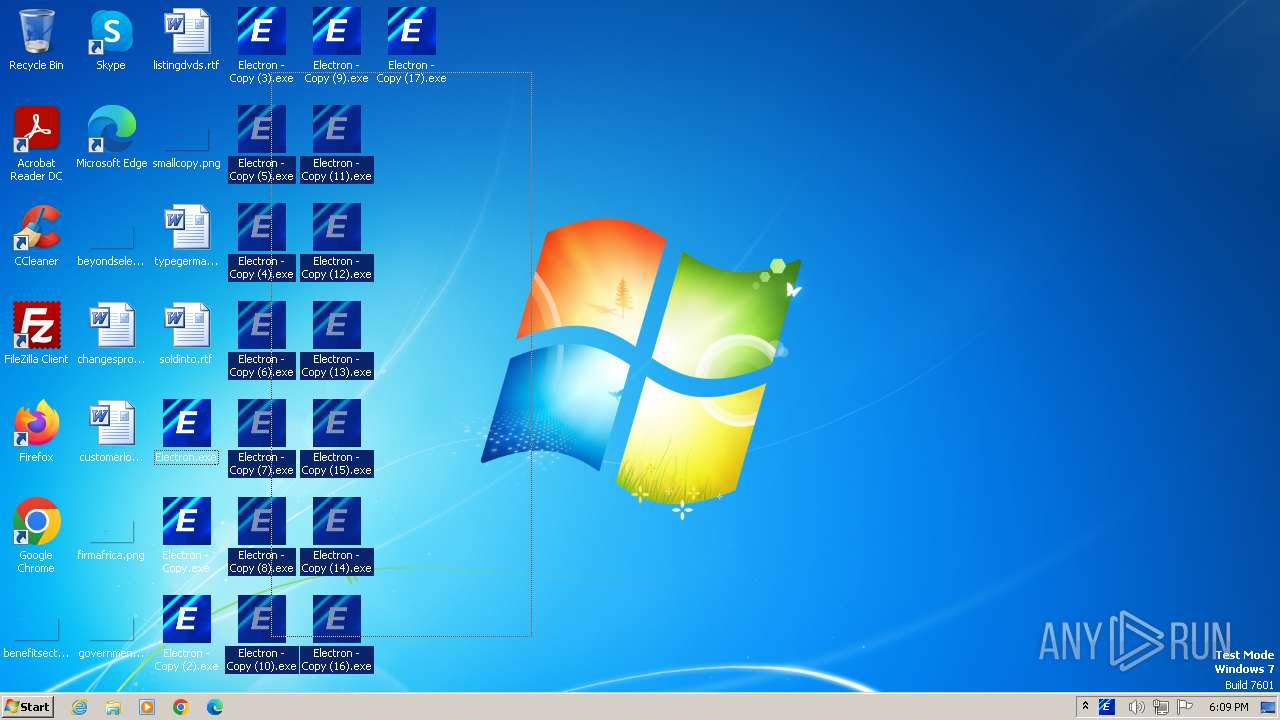
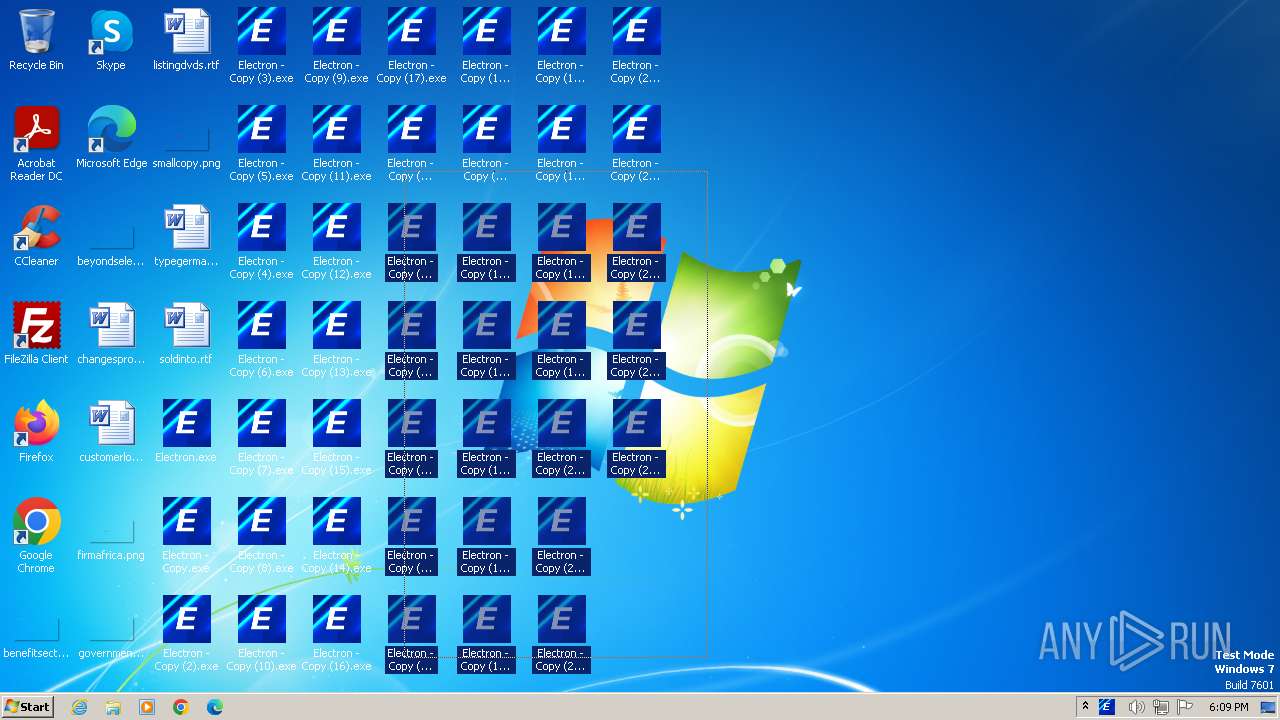
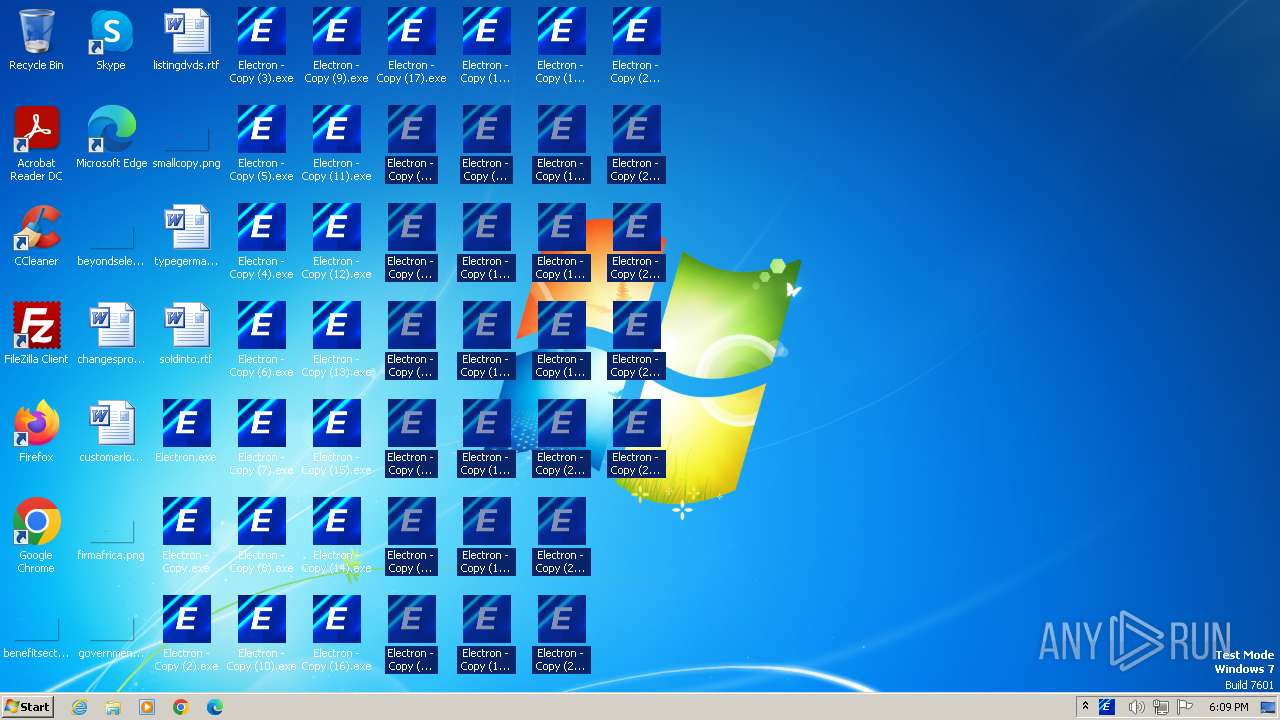
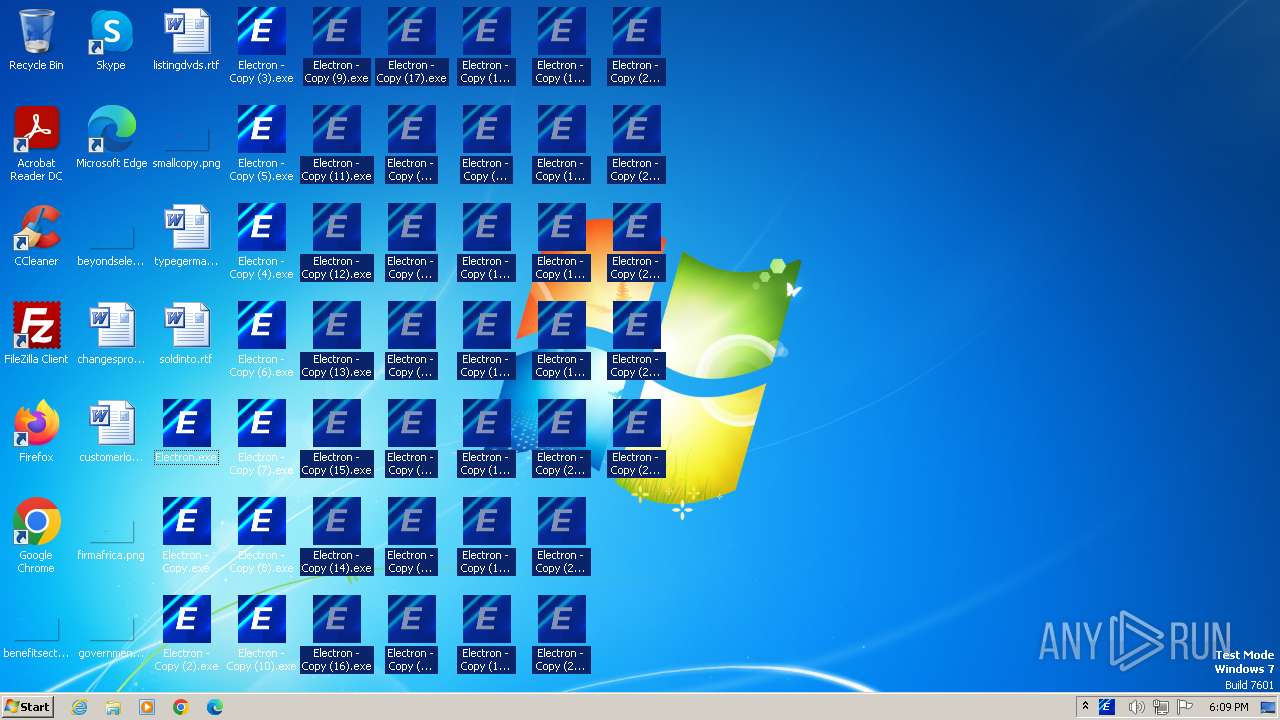
The system shut down or reboot
- Electron.exe (PID: 2980)
INFO
Reads the machine GUID from the registry
- Electron.exe (PID: 2980)
Checks supported languages
- Electron.exe (PID: 2980)
- wmpnscfg.exe (PID: 2220)
Reads Environment values
- Electron.exe (PID: 2980)
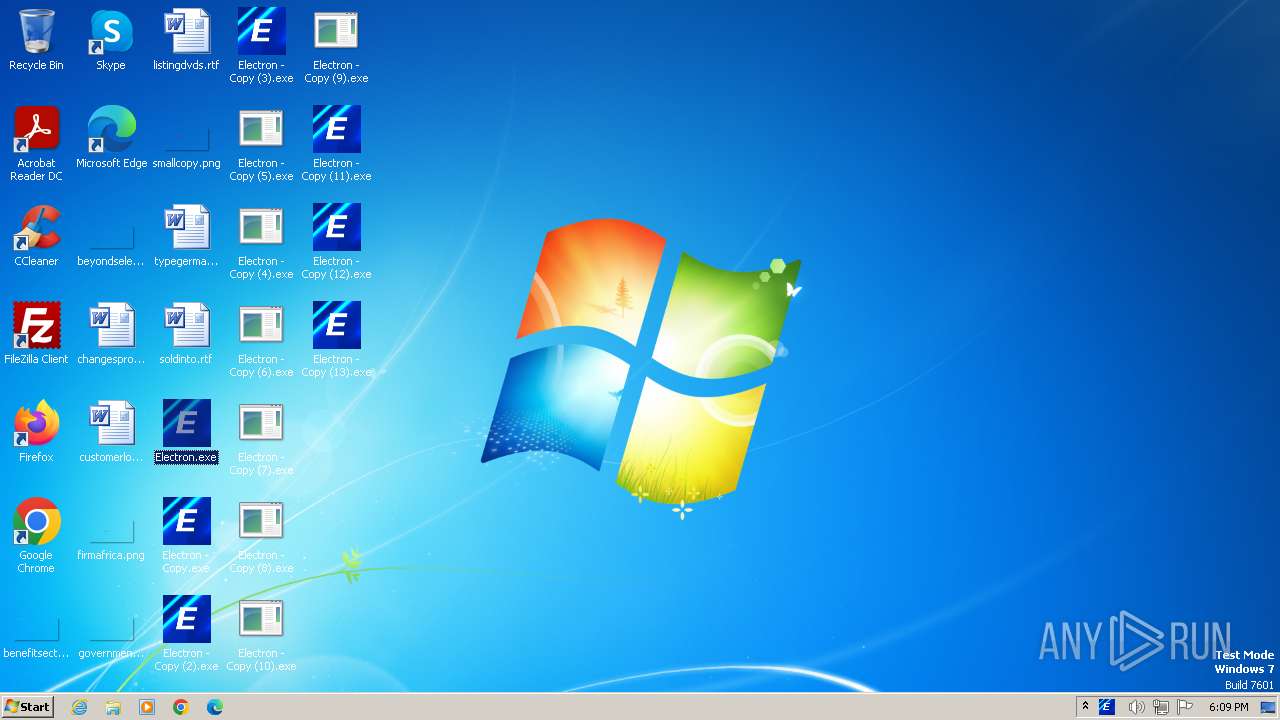
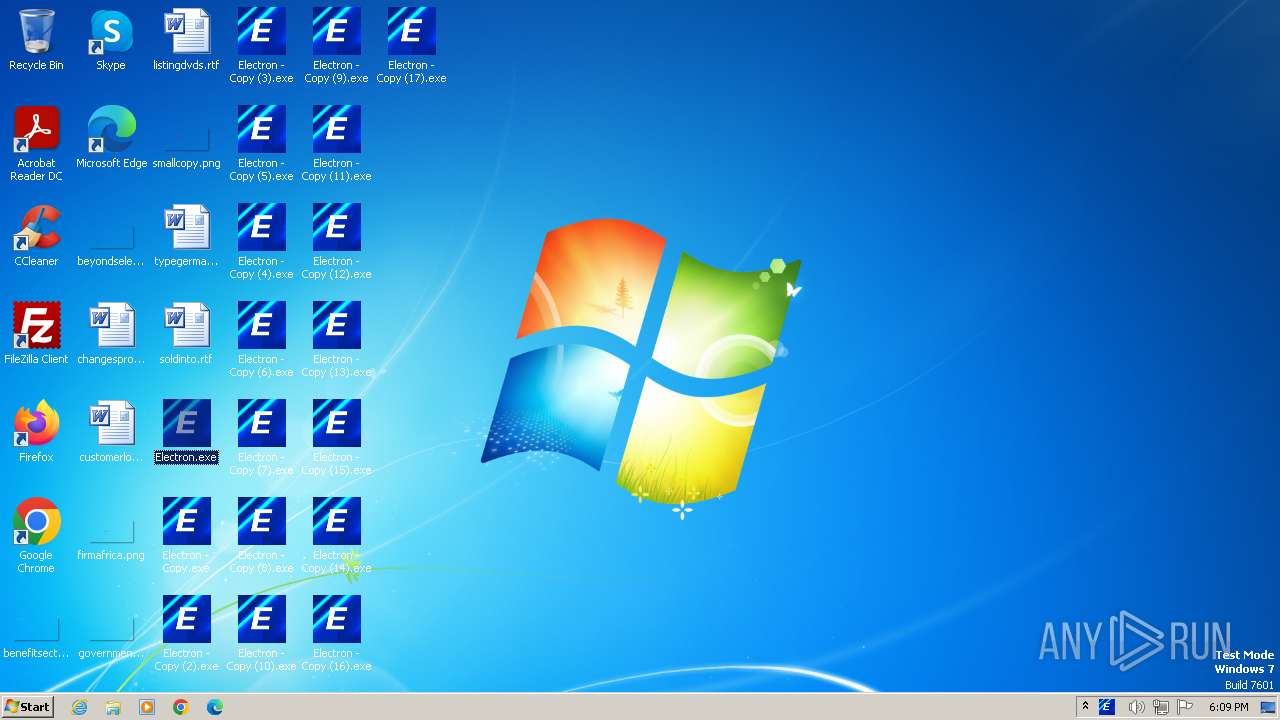
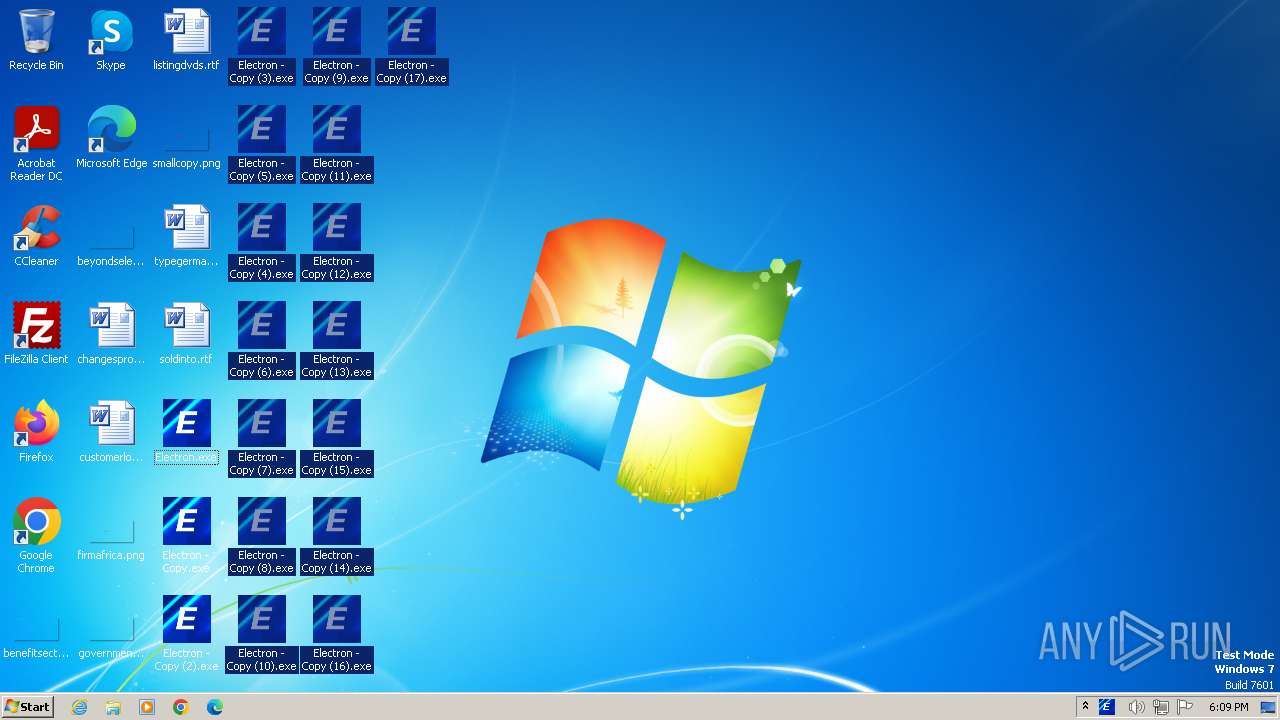
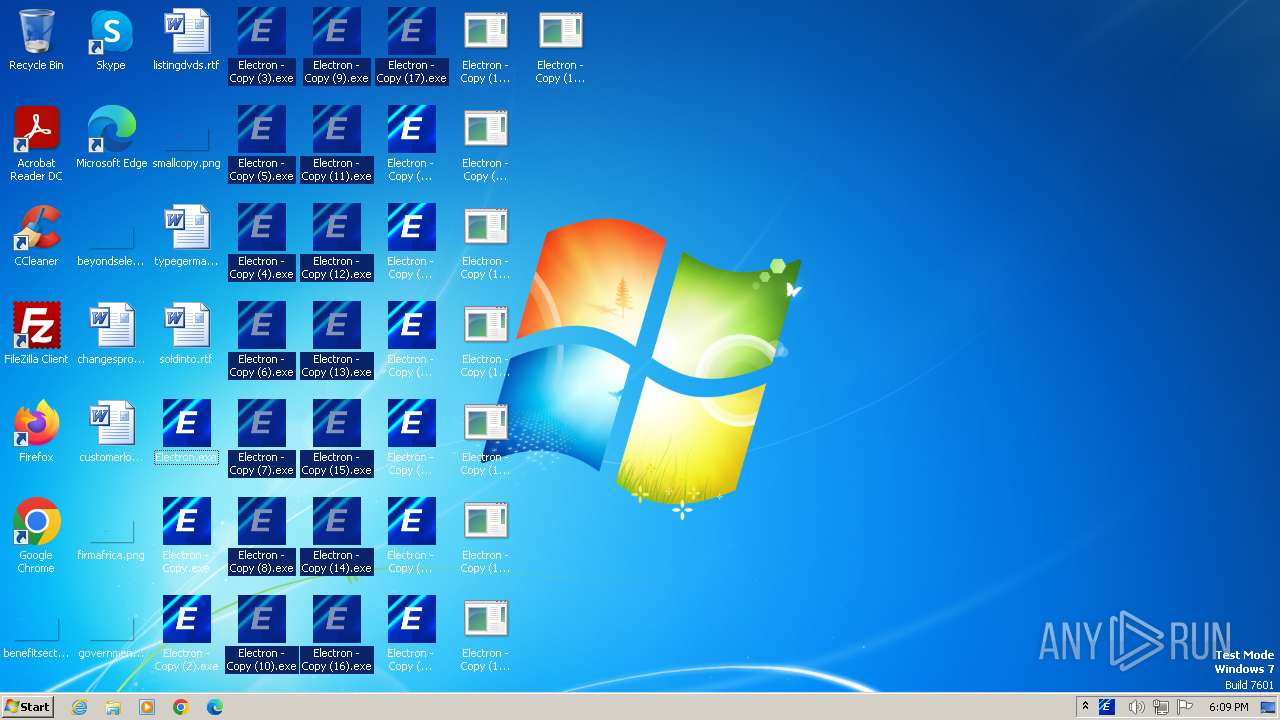
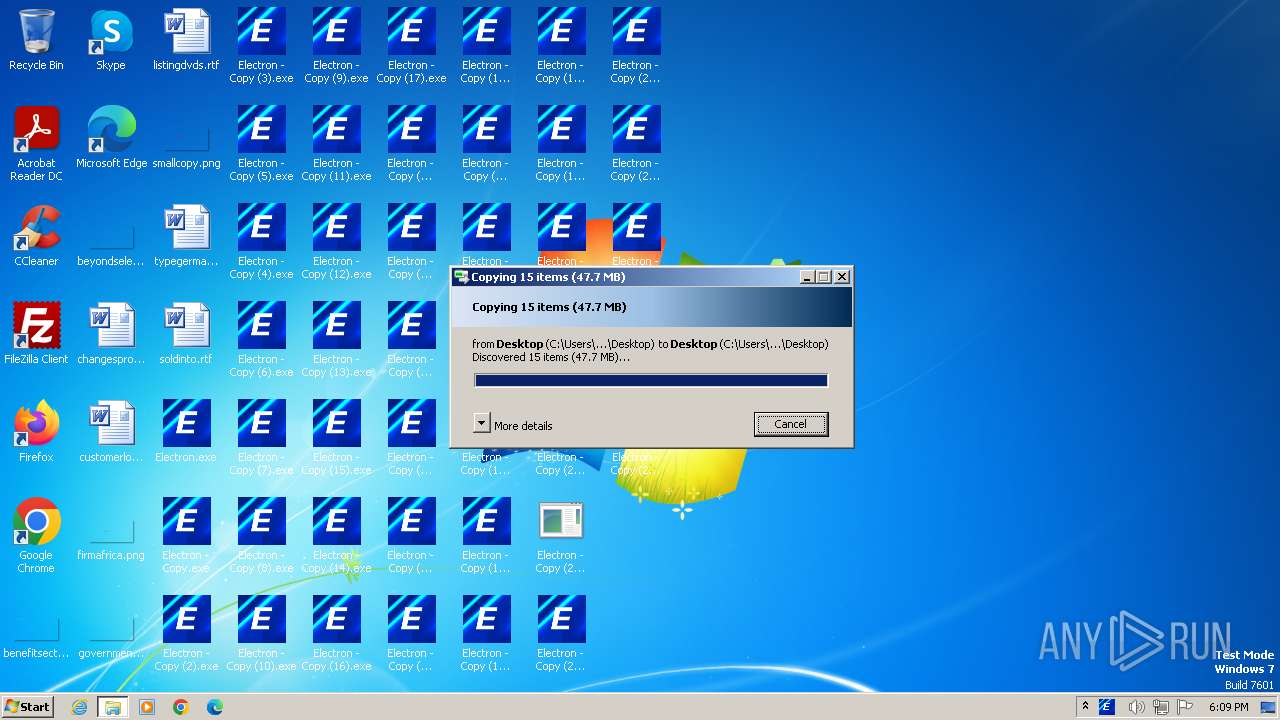
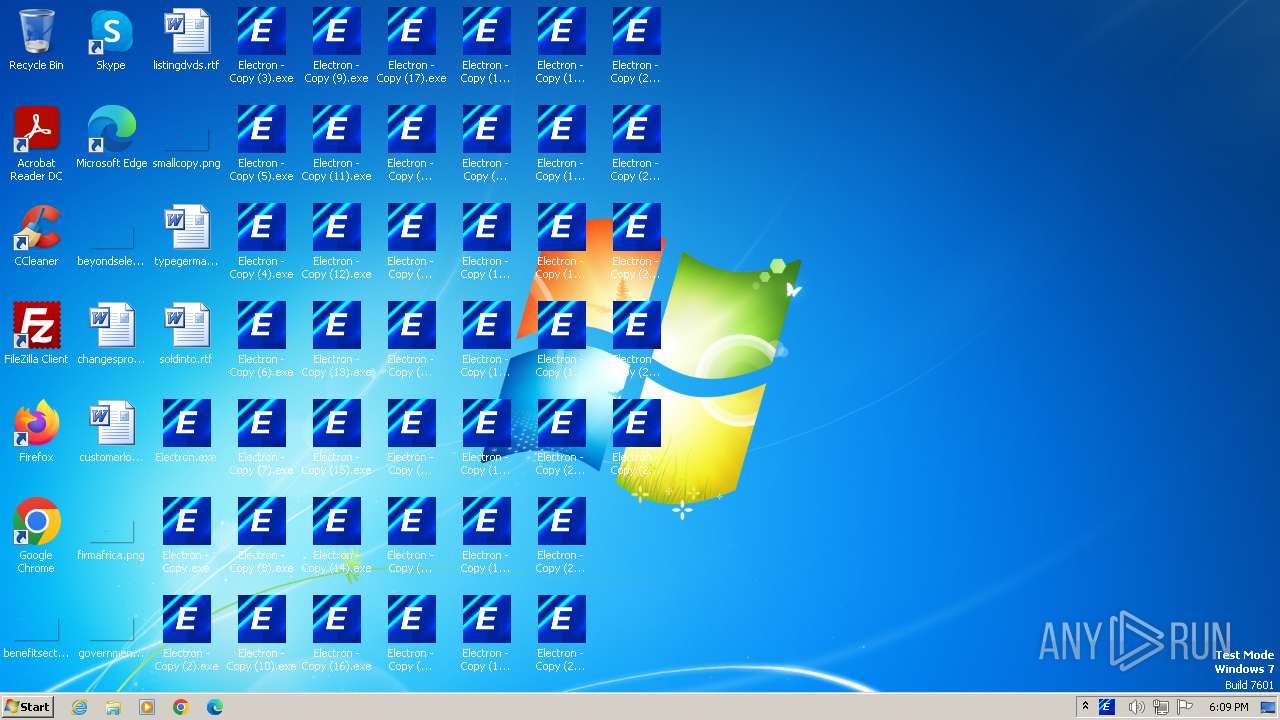
Create files in a temporary directory
- Electron.exe (PID: 2980)
Reads the computer name
- wmpnscfg.exe (PID: 2220)
- Electron.exe (PID: 2980)
Manual execution by a user
- wmpnscfg.exe (PID: 2220)
Creates files or folders in the user directory
- Electron.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(2980) Electron.exe
Version1.4.1
C2 (2)limehag920-33288.portmap.host:33288
Sub_DirSubDir
Install_NameClient.exe
Mutex9818b060-d6e3-4e48-b21e-c9ef7bc65511
StartupQuasar Client Startup
TagOffice04
LogDirLogs
SignaturePWqcW0flofkLccXQ6vZv+kg9jDpZE29KOwoNneFVK1YYLQYAXd3xQpk88PUtDx8eSrGPCyzMM6btyTVze5oWF4wR1IawjPKzUzEVpNtkAe1nbTy/1aGdULlh5E1MmfJ+3eYuO9Cyd4Q23HCf8V0rp565CYNB5mfcgVUVHm/4Wp7jK99QZEh4QkfACNqft3rj1J6XEu8TfKbPLmtrfbDhe8QubeZRn01qfKd7xIosQ2WDSjrth1aoyAcUxXI7DU3S6opREIcDBgxpCbowXxxUd9D08q3TA3tV0thbVzuPJaTE...
CertificateMIIE9DCCAtygAwIBAgIQAOVqm04ujwJLAT5iBKRSKTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTEzMDE3MjE0MFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAlM1LFSxEqvMbNxg6Hq8o8HD5WgZ5409hJBw63LT+shUb6RVIMB8r4E/avNXdMEGE2sprCiHI...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 17:16:39+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e41e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.1.0 |
| ProductVersionNumber: | 1.4.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Quasar Client |
| FileVersion: | 1.4.1 |
| InternalName: | Client.exe |
| LegalCopyright: | Copyright © MaxXor 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | Quasar |
| ProductVersion: | 1.4.1 |
| AssemblyVersion: | 1.4.1.0 |
Total processes
44
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2220 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Windows\System32\shutdown.exe" /s /t 0 | C:\Windows\System32\shutdown.exe | — | Electron.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\Desktop\Electron.exe" | C:\Users\admin\Desktop\Electron.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 1073807364 Version: 1.4.1 Modules
Quasar(PID) Process(2980) Electron.exe Version1.4.1 C2 (2)limehag920-33288.portmap.host:33288 Sub_DirSubDir Install_NameClient.exe Mutex9818b060-d6e3-4e48-b21e-c9ef7bc65511 StartupQuasar Client Startup TagOffice04 LogDirLogs SignaturePWqcW0flofkLccXQ6vZv+kg9jDpZE29KOwoNneFVK1YYLQYAXd3xQpk88PUtDx8eSrGPCyzMM6btyTVze5oWF4wR1IawjPKzUzEVpNtkAe1nbTy/1aGdULlh5E1MmfJ+3eYuO9Cyd4Q23HCf8V0rp565CYNB5mfcgVUVHm/4Wp7jK99QZEh4QkfACNqft3rj1J6XEu8TfKbPLmtrfbDhe8QubeZRn01qfKd7xIosQ2WDSjrth1aoyAcUxXI7DU3S6opREIcDBgxpCbowXxxUd9D08q3TA3tV0thbVzuPJaTE... CertificateMIIE9DCCAtygAwIBAgIQAOVqm04ujwJLAT5iBKRSKTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTEzMDE3MjE0MFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAlM1LFSxEqvMbNxg6Hq8o8HD5WgZ5409hJBw63LT+shUb6RVIMB8r4E/avNXdMEGE2sprCiHI... | |||||||||||||||
Total events
5 744
Read events
5 724
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2980) Electron.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) Electron.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2980) Electron.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2980) Electron.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2980) Electron.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | Electron.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2980 | Electron.exe | C:\Users\admin\AppData\Local\Temp\Cab7B00.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2980 | Electron.exe | C:\Users\admin\AppData\Local\Temp\Tar7B01.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2980 | Electron.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:0E9F1E5EBDA6E8FB09307F1FDBBE5BDD | SHA256:A6C42AC3451B90FB0EBA3C1DFCF35F132872CDC05952207E160720786E107F54 | |||
| 2980 | Electron.exe | C:\Users\admin\AppData\Roaming\Logs\2023-12-02 | binary | |
MD5:C76D8DAD8782869D5501767EF35496B5 | SHA256:AE5045D0D61A4411A8D4D9B32E02466CE2A66E81ABAD04E2CB5592FD23C29F61 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | Electron.exe | GET | 200 | 2.22.242.82:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?067af9b499822491 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2980 | Electron.exe | 193.161.193.99:33288 | limehag920-33288.portmap.host | OOO Bitree Networks | RU | malicious |
2980 | Electron.exe | 2.22.242.82:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2980 | Electron.exe | 195.201.57.90:443 | ipwho.is | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
limehag920-33288.portmap.host |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ipwho.is |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a Reverse Proxy Service Observed |
1080 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .host) |
2980 | Electron.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
2980 | Electron.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
2980 | Electron.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (GCM_SHA384) |