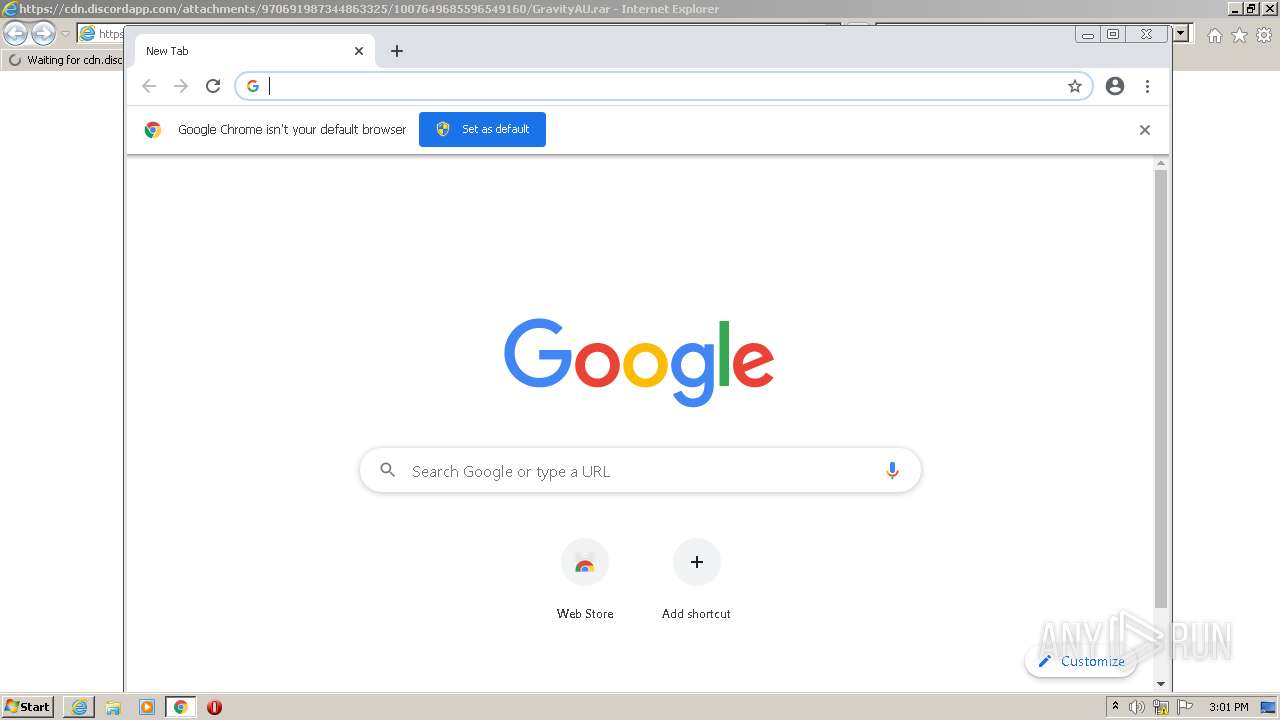
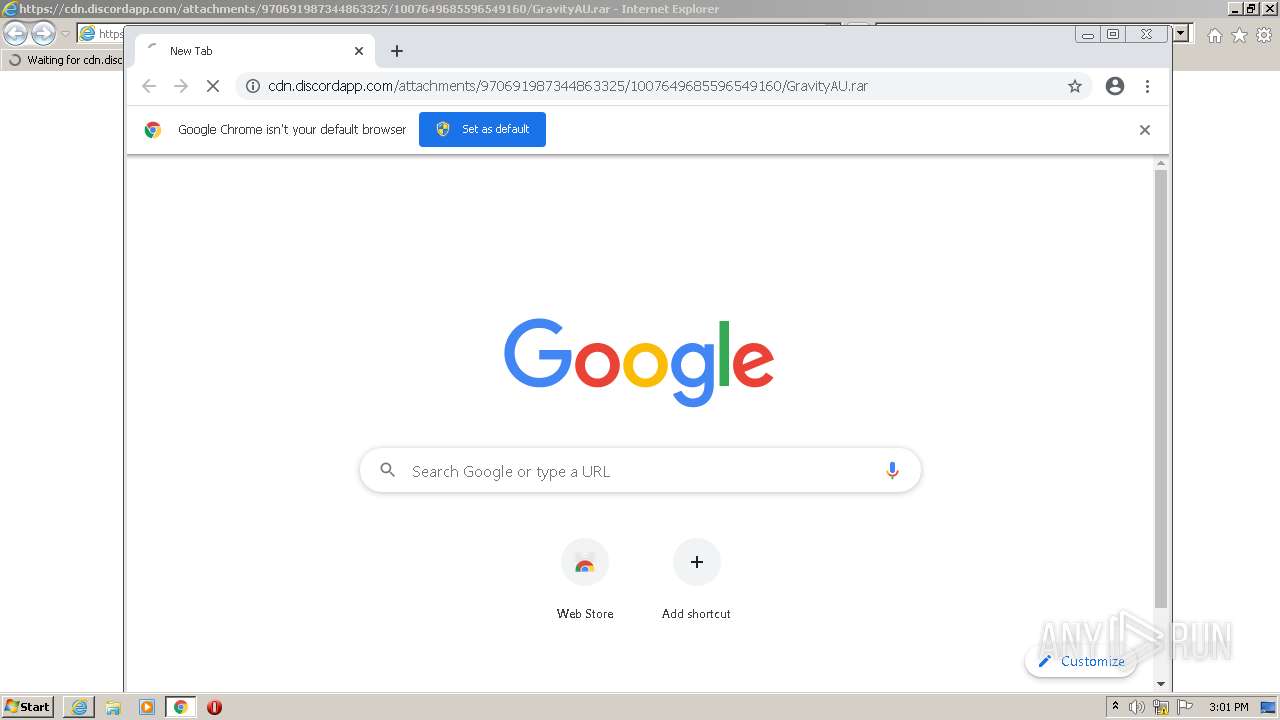
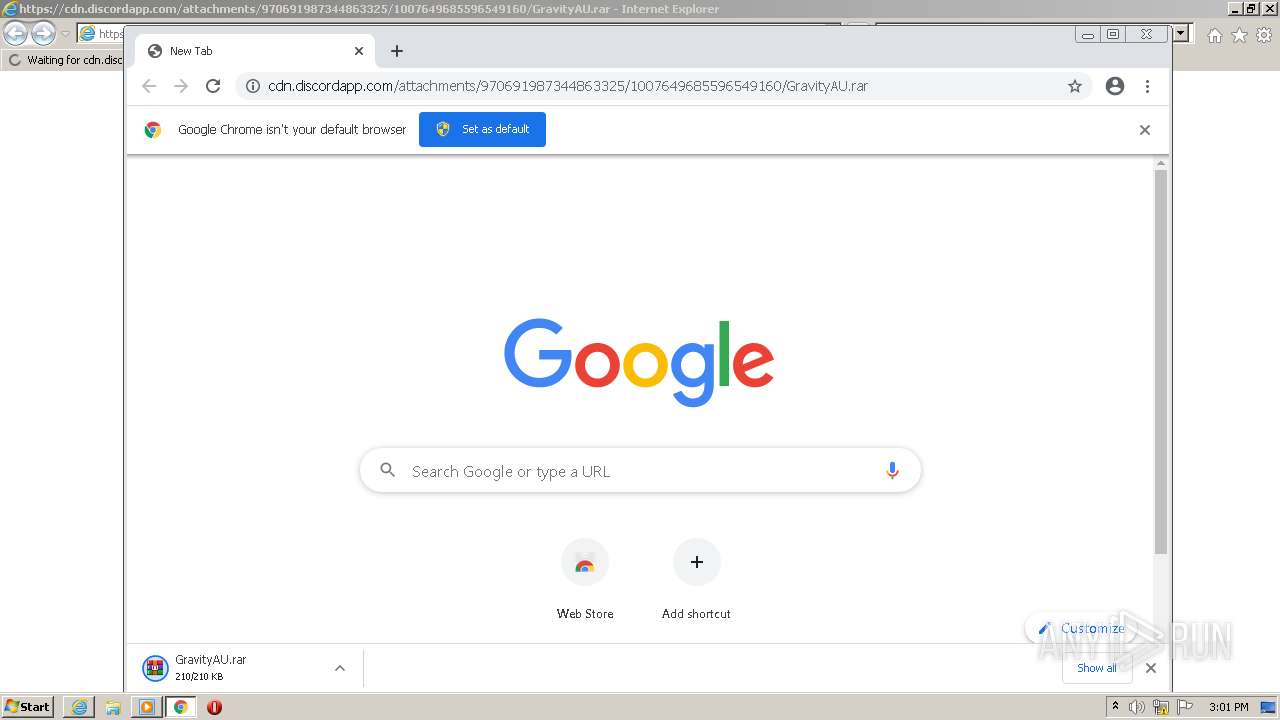
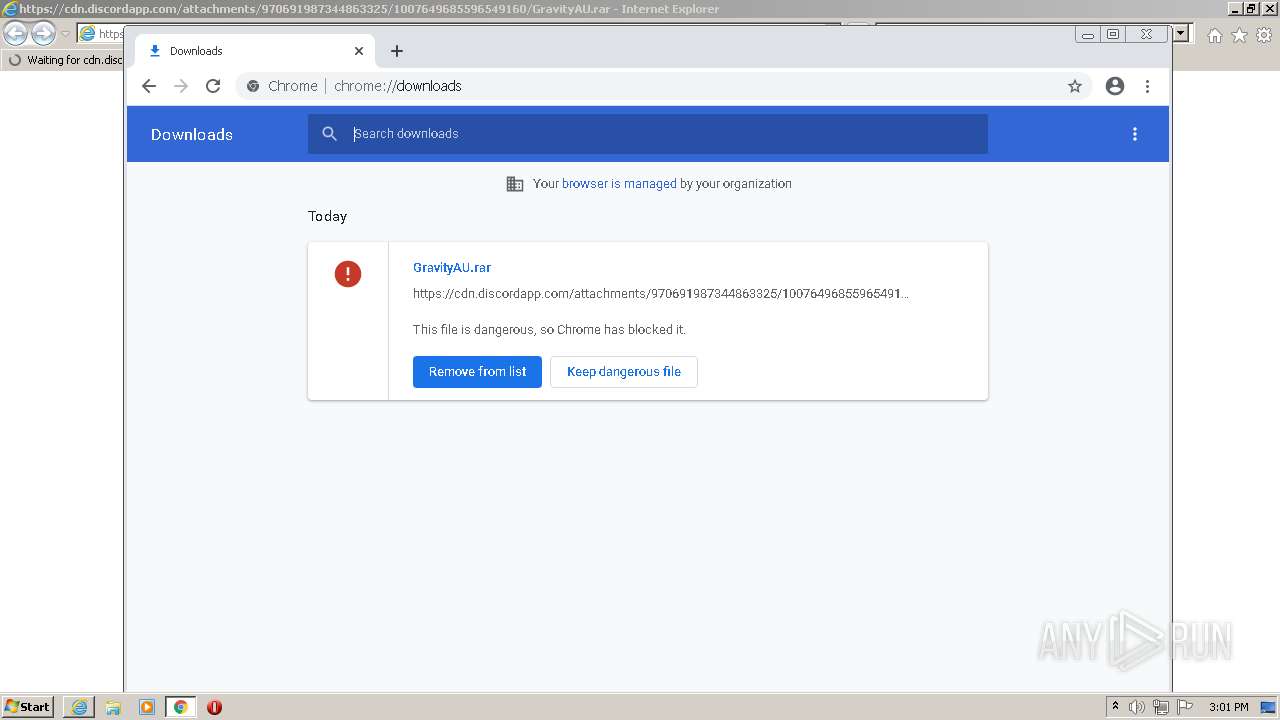
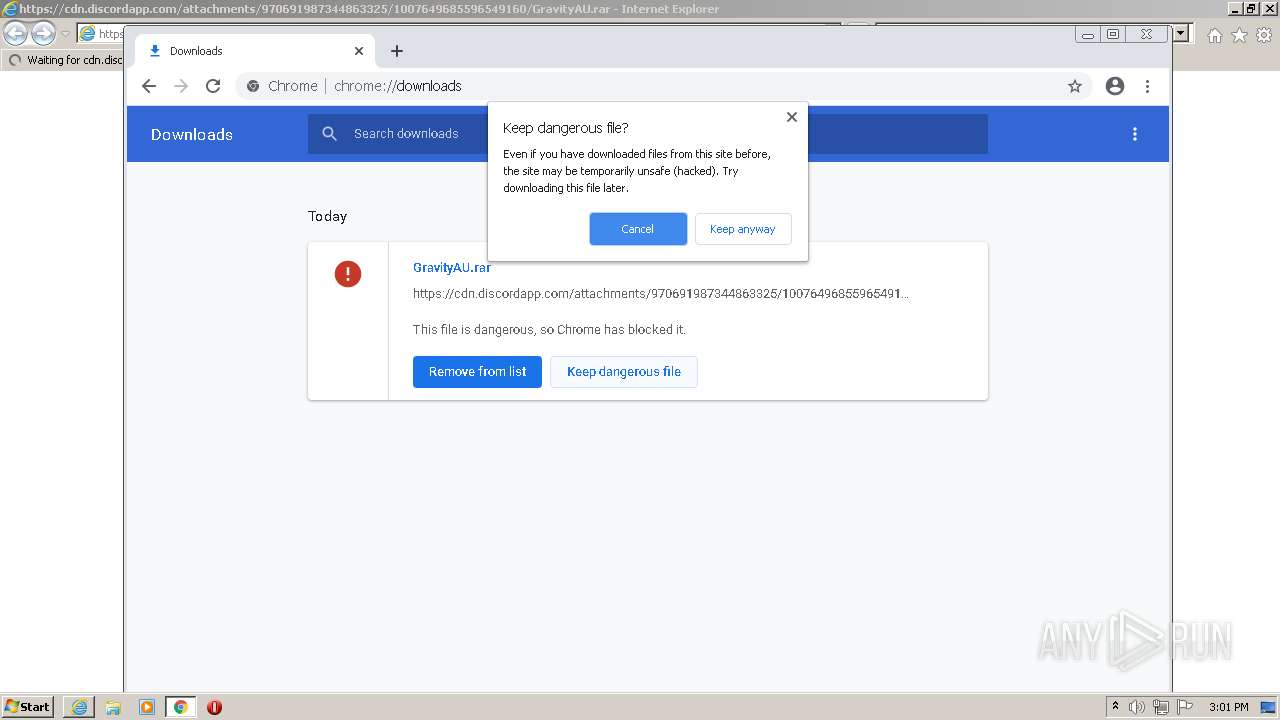
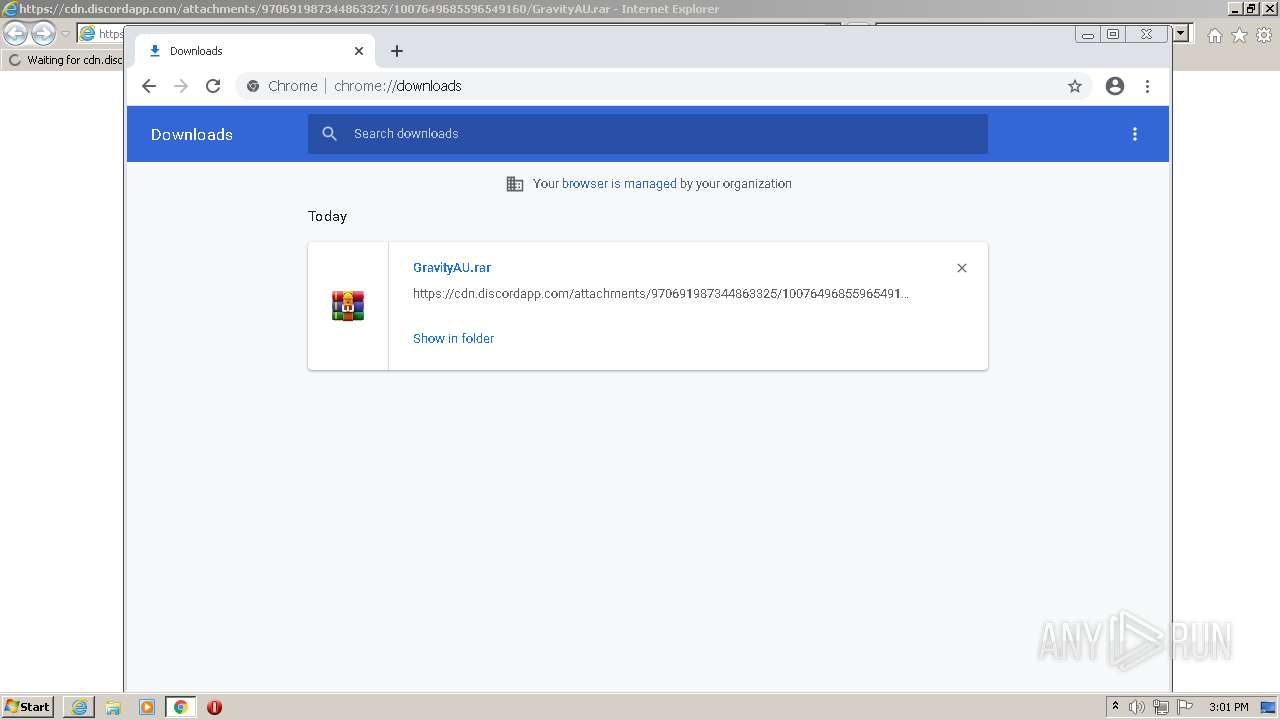
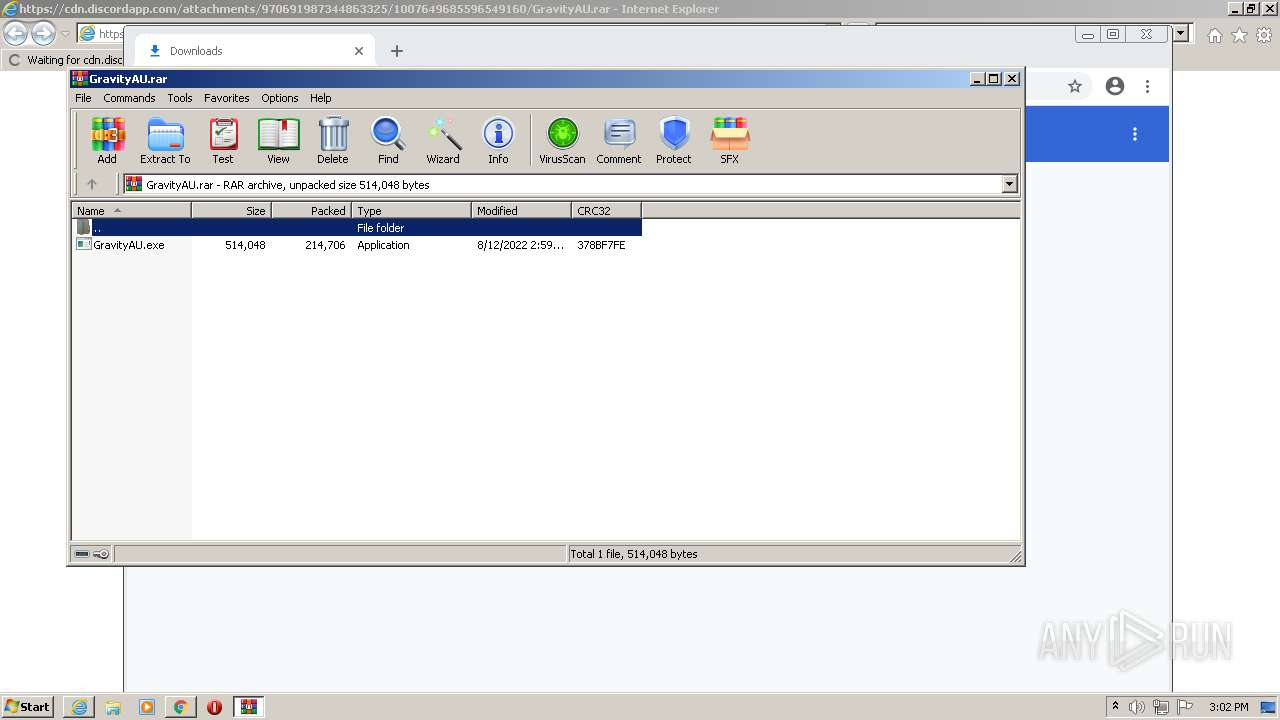
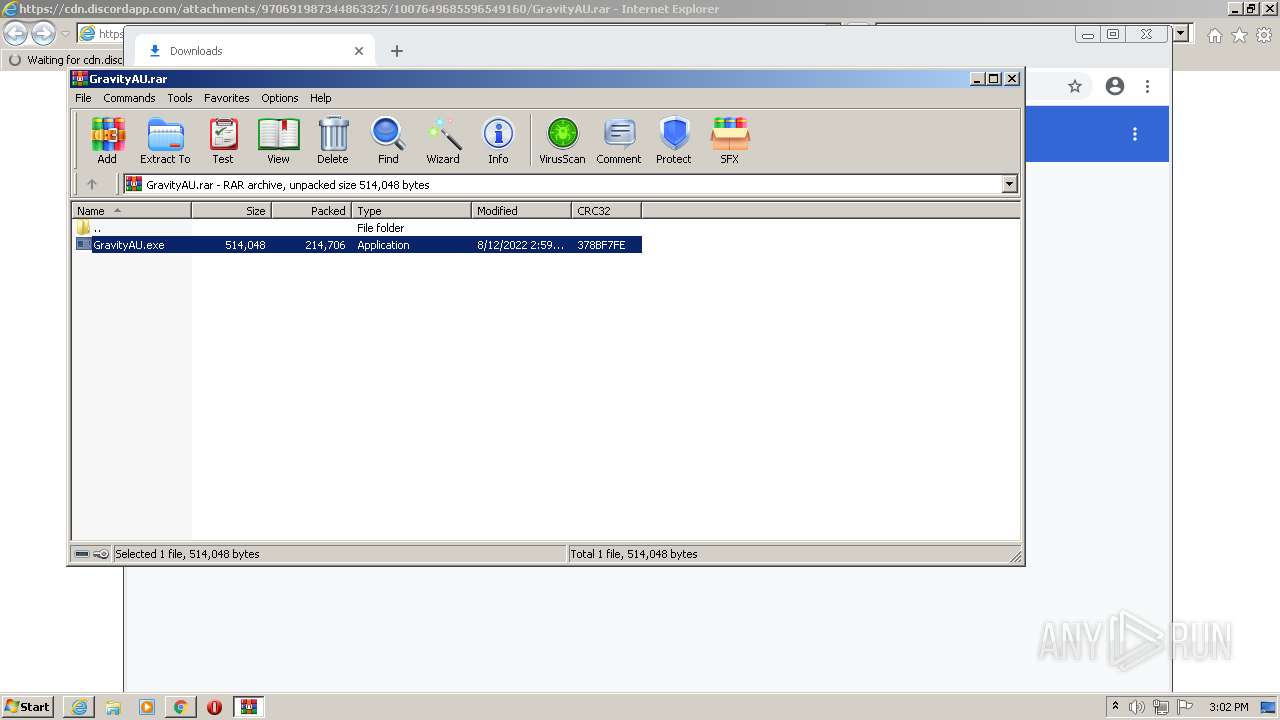
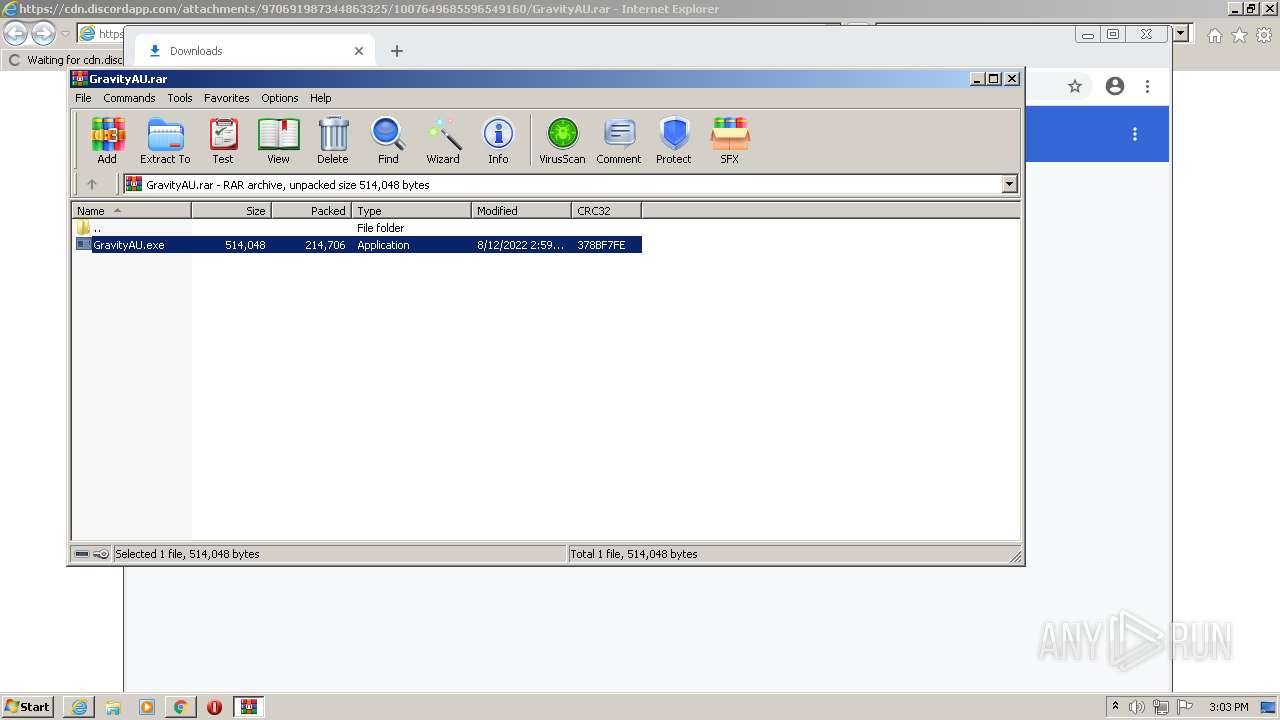
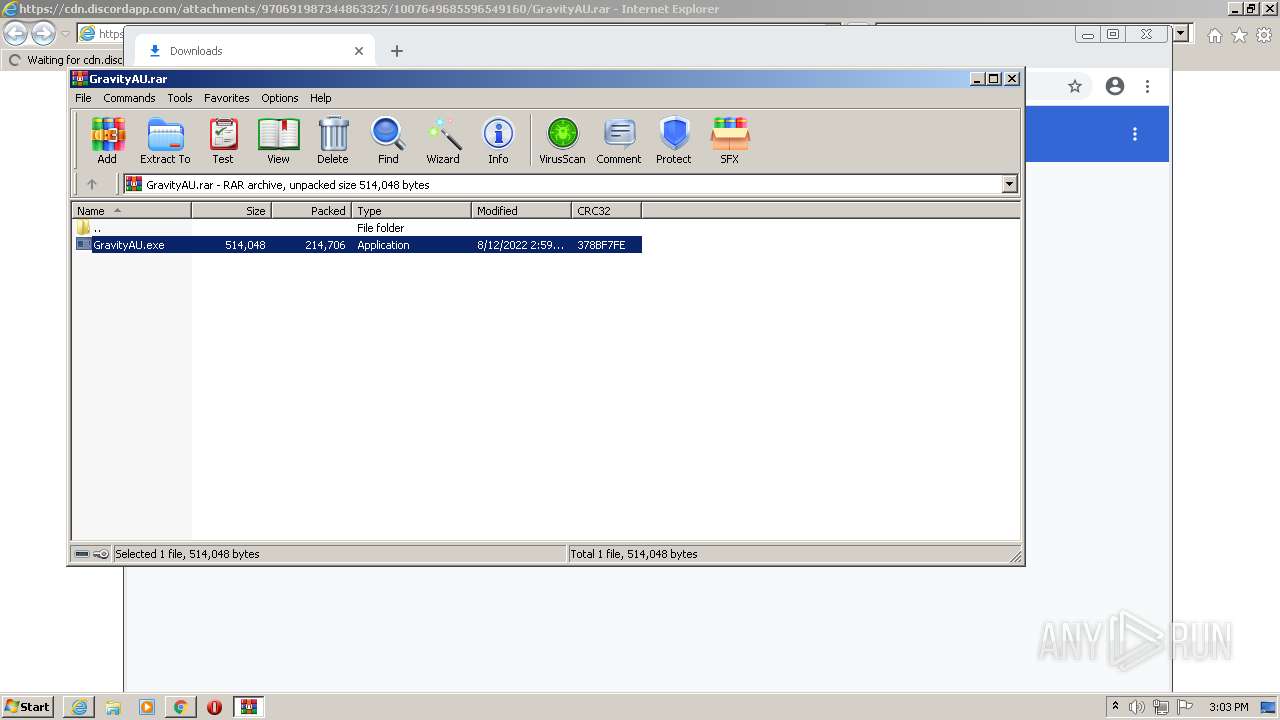
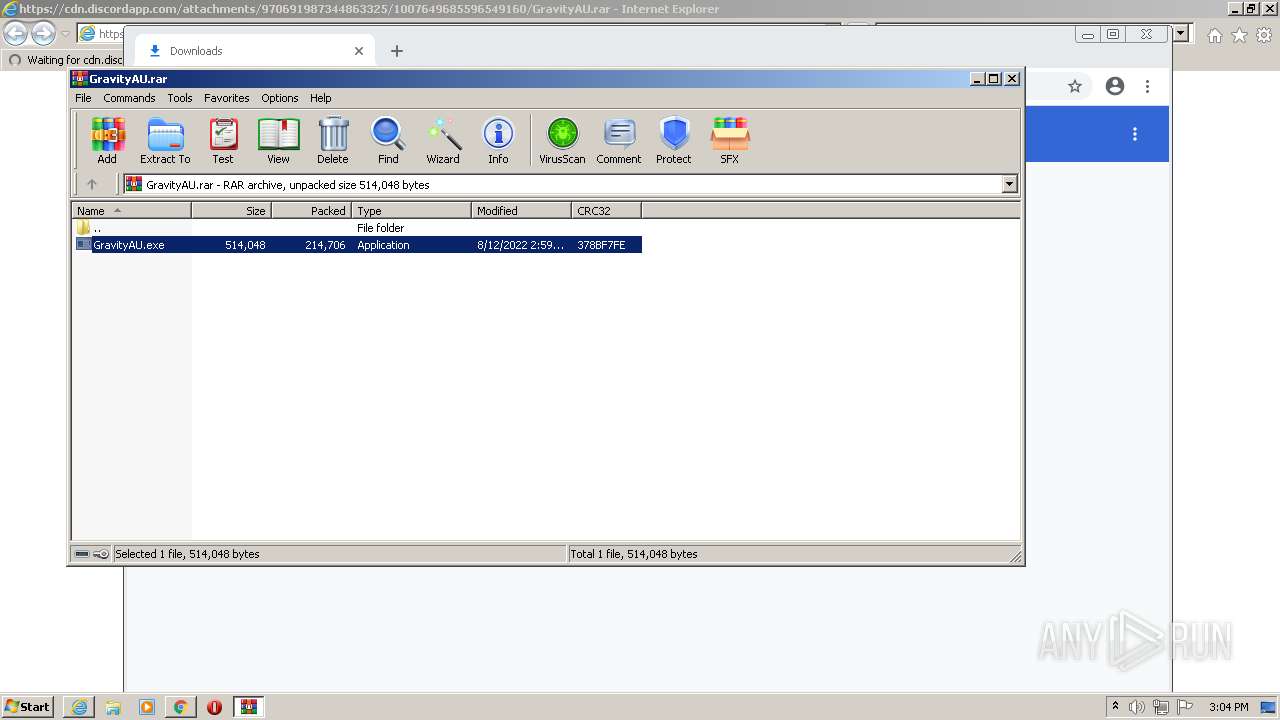
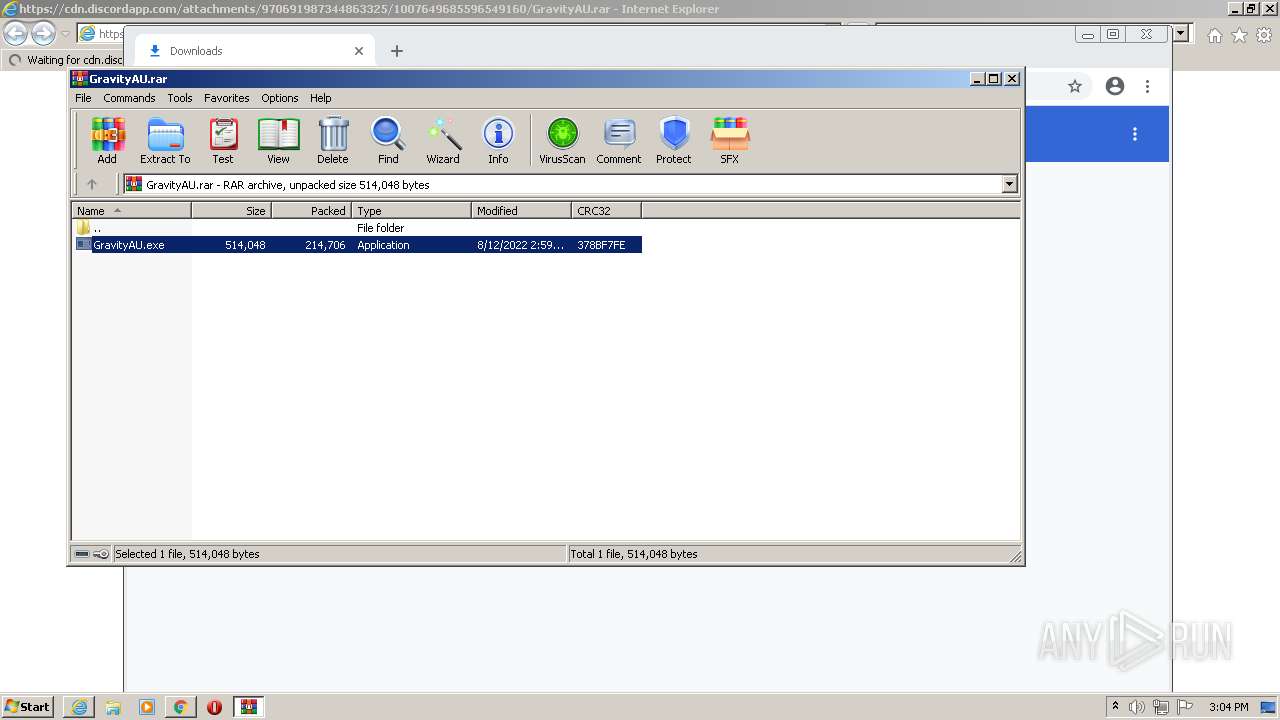
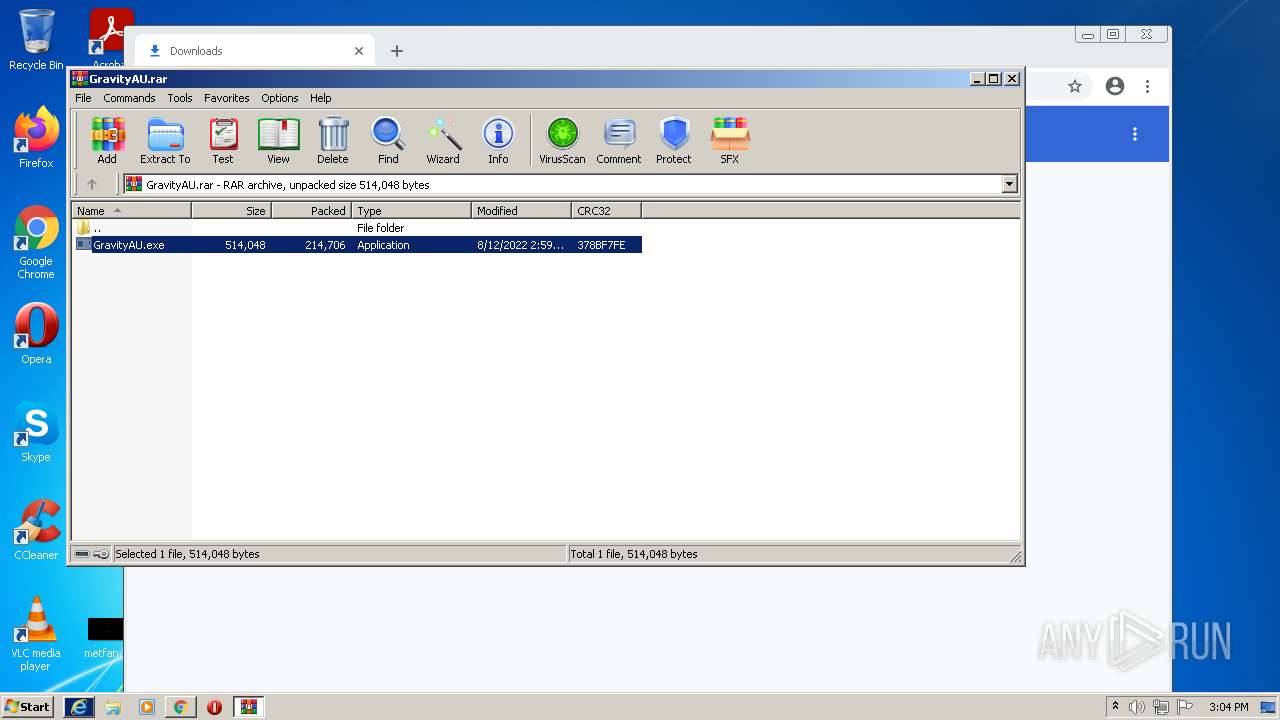
| URL: | https://cdn.discordapp.com/attachments/970691987344863325/1007649685596549160/GravityAU.rar |
| Full analysis: | https://app.any.run/tasks/e50b2343-1054-4980-880b-78b2e5c2d782 |
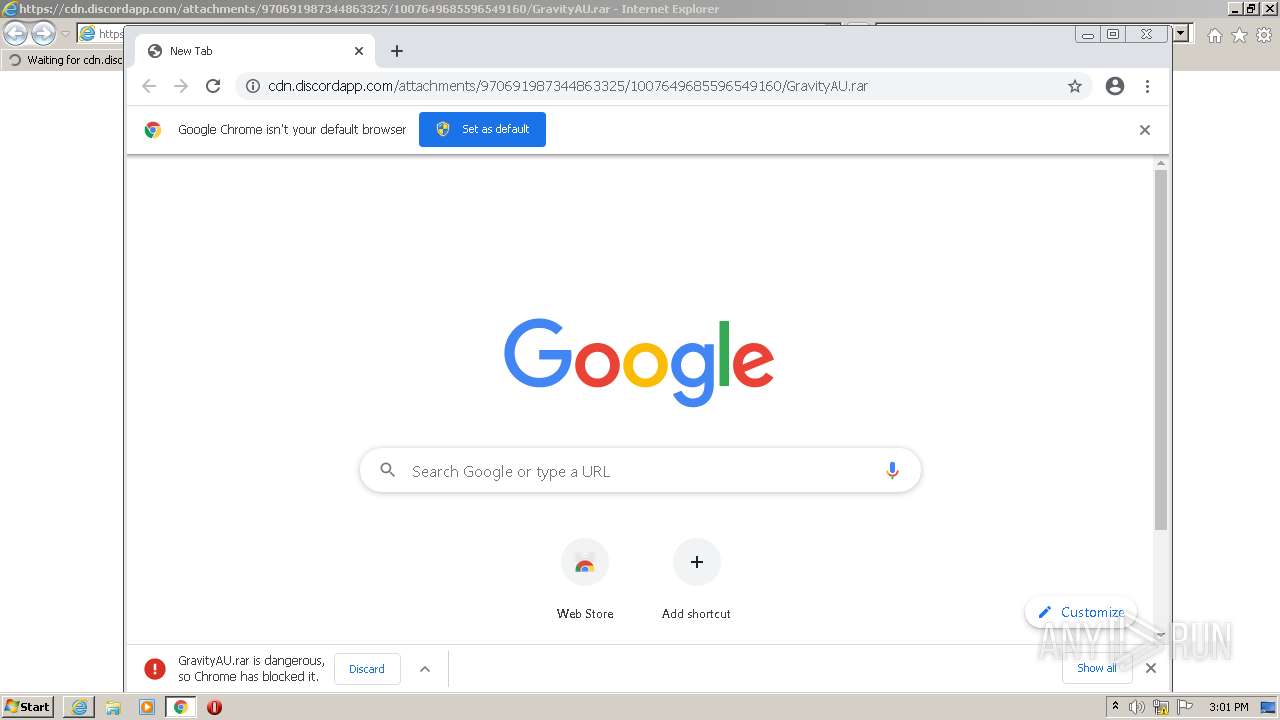
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | August 12, 2022, 14:00:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7FB814270A4CE29AAB74A1F0B15326D2 |
| SHA1: | 0CFFDD0AD8DE23406DB67FE35F2445E7688D4AA3 |
| SHA256: | 48C2CC371DC076E4A1E21CFBE24D26756D75E7BB78461215F24F3C5666677F31 |
| SSDEEP: | 3:N8cCWdy6//j5JWRxfLTRhoV5KQc5LUX:2cry6XjkxfLdhonBcVUX |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 1544)
- GravityAU.exe (PID: 2364)
Application was dropped or rewritten from another process
- logs.exe (PID: 1844)
- GravityAU.exe (PID: 2364)
Changes the autorun value in the registry
- GravityAU.exe (PID: 2364)
- logs.exe (PID: 1844)
QUASAR detected by memory dumps
- logs.exe (PID: 1844)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2052)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3104)
Reads the computer name
- WinRAR.exe (PID: 1544)
- GravityAU.exe (PID: 2364)
- logs.exe (PID: 1844)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1544)
- GravityAU.exe (PID: 2364)
Checks supported languages
- GravityAU.exe (PID: 2364)
- logs.exe (PID: 1844)
- WinRAR.exe (PID: 1544)
Reads Environment values
- GravityAU.exe (PID: 2364)
- logs.exe (PID: 1844)
Starts itself from another location
- GravityAU.exe (PID: 2364)
Executable content was dropped or overwritten
- GravityAU.exe (PID: 2364)
- WinRAR.exe (PID: 1544)
INFO
Reads the computer name
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2052)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 1484)
Checks supported languages
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2052)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 616)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 640)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2492)
- chrome.exe (PID: 3344)
- chrome.exe (PID: 3532)
Application launched itself
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 3104)
Changes internet zones settings
- iexplore.exe (PID: 2988)
Checks Windows Trust Settings
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 2052)
Reads settings of System Certificates
- iexplore.exe (PID: 2052)
- iexplore.exe (PID: 2988)
- chrome.exe (PID: 2756)
Reads internet explorer settings
- iexplore.exe (PID: 2052)
Manual execution by user
- chrome.exe (PID: 3104)
Reads the date of Windows installation
- chrome.exe (PID: 3488)
- iexplore.exe (PID: 2988)
Changes settings of System certificates
- iexplore.exe (PID: 2988)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2988)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(1844) logs.exe
Version1.4.0
C2 (2)160.202.141.191:5353
Sub_DirSubDir
Install_Namelogs.exe
Mutexdd2e0512-68c3-4f9a-9b20-869b83375667
StartupWindows Security
TagOffice04
LogDirLogs
SignatureqcxOnTNiJjtTAmgqhXJUtY+4lTzCz4qKOlKyXxMuPu7Baf6AiiFw5cuKBaMdofdqo3mhCeDS0A0l9Tv+3P/G7M2MFnM0Fhwi185zTiomrzdVZMHEPJREura4vdZFyFPk5y1rAH/bTSgkTZdvlfnrTPJGbP+cuk9K/e8JjTInQdKUR6EhXmtNhtkFY12NxYyo+vGCjNxYkm8UL0MpI27Di7iGHLvaE7mObRUrCTw6s68y36idOEWRsXGYxsIov1IF+TFE40X04Ela+JlfkecX6ifef1SDsdZvPDhpMvv3qS8B...
CertificateMIIE9DCCAtygAwIBAgIQAMC4lJxWq6ATI44gVYm/WzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIyMDUxNTA4MDYzM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAyyhIL7arsFvfUQAgxYWR+cuJjwWtJAL9YHTT30jMfM2rWQs8GELj51MY9EjLwDsBf7QHlDj+...
Total processes
70
Monitored processes
33
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3104 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1396 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3204 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1856 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\GravityAU.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1844 | "C:\Users\admin\AppData\Roaming\SubDir\logs.exe" | C:\Users\admin\AppData\Roaming\SubDir\logs.exe | GravityAU.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Quasar Client Exit code: 0 Version: 1.4.0 Modules
Quasar(PID) Process(1844) logs.exe Version1.4.0 C2 (2)160.202.141.191:5353 Sub_DirSubDir Install_Namelogs.exe Mutexdd2e0512-68c3-4f9a-9b20-869b83375667 StartupWindows Security TagOffice04 LogDirLogs SignatureqcxOnTNiJjtTAmgqhXJUtY+4lTzCz4qKOlKyXxMuPu7Baf6AiiFw5cuKBaMdofdqo3mhCeDS0A0l9Tv+3P/G7M2MFnM0Fhwi185zTiomrzdVZMHEPJREura4vdZFyFPk5y1rAH/bTSgkTZdvlfnrTPJGbP+cuk9K/e8JjTInQdKUR6EhXmtNhtkFY12NxYyo+vGCjNxYkm8UL0MpI27Di7iGHLvaE7mObRUrCTw6s68y36idOEWRsXGYxsIov1IF+TFE40X04Ela+JlfkecX6ifef1SDsdZvPDhpMvv3qS8B... CertificateMIIE9DCCAtygAwIBAgIQAMC4lJxWq6ATI44gVYm/WzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIyMDUxNTA4MDYzM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAyyhIL7arsFvfUQAgxYWR+cuJjwWtJAL9YHTT30jMfM2rWQs8GELj51MY9EjLwDsBf7QHlDj+... | |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,843587056555413169,10238148920861449773,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2988 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
30 205
Read events
29 852
Write events
342
Delete events
11
Modification events
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977619 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 104789480 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977620 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
144
Text files
160
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F65D3B-C20.pma | — | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe173d.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3104 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
66
DNS requests
43
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
856 | svchost.exe | HEAD | 200 | 74.125.162.202:80 | http://r5---sn-4g5ednds.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=84.247.59.65&mm=28&mn=sn-4g5ednds&ms=nvh&mt=1660312824&mv=m&mvi=5&pl=24&shardbypass=sd&smhost=r4---sn-4g5edn6y.gvt1.com | US | — | — | whitelisted |
2988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2756 | chrome.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
2052 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
2988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
856 | svchost.exe | GET | 206 | 173.194.187.42:80 | http://r5---sn-4g5e6nsd.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=84.247.59.65&mm=28&mn=sn-4g5e6nsd&ms=nvh&mt=1660312586&mv=m&mvi=5&pl=24&rmhost=r1---sn-4g5e6nsd.gvt1.com&shardbypass=sd&smhost=r4---sn-4g5lznek.gvt1.com | US | flc | 10.3 Kb | whitelisted |
856 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | html | 610 b | whitelisted |
856 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | html | 610 b | whitelisted |
856 | svchost.exe | GET | 206 | 173.194.187.42:80 | http://r5---sn-4g5e6nsd.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=84.247.59.65&mm=28&mn=sn-4g5e6nsd&ms=nvh&mt=1660312586&mv=m&mvi=5&pl=24&rmhost=r1---sn-4g5e6nsd.gvt1.com&shardbypass=sd&smhost=r4---sn-4g5lznek.gvt1.com | US | bs | 21.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2052 | iexplore.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2052 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2988 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2988 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2052 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2988 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2756 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2756 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2988 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2756 | chrome.exe | 142.250.185.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2052 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2052 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2756 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2756 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2052 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2052 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |