| File name: | 48b8d9ebc4b8d00d258b223732c8fafc1e2b935f7064df9d6520b68c04418c38 |
| Full analysis: | https://app.any.run/tasks/89f7f34b-da7c-4b89-912d-84078ed3c040 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 25, 2019, 16:37:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
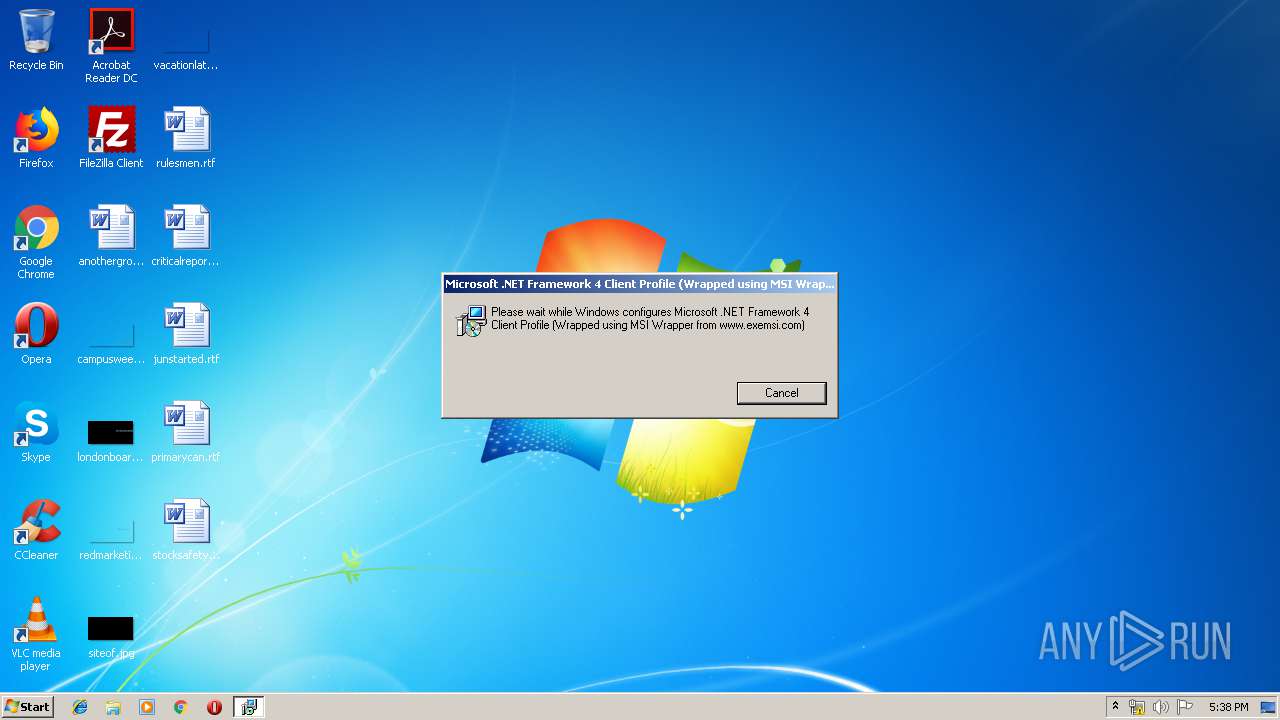
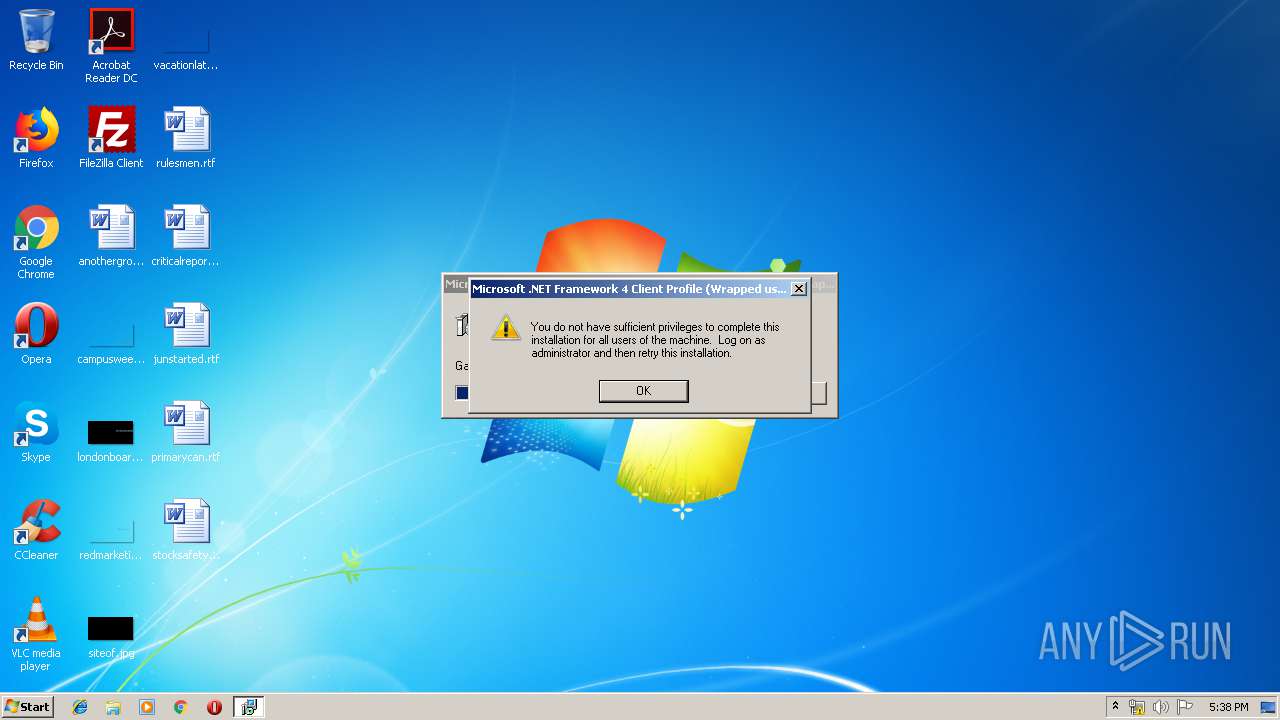
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Microsoft .NET Framework 4 Client Profile 4.0.30319.0, Subject: Microsoft .NET Framework 4 Client Profile, Author: Microsoft Corporation, Keywords: Installer, Template: Intel;1033, Revision Number: {EECF31ED-6347-4845-83CA-CB7F67FDE2C8}, Create Time/Date: Mon Aug 13 19:00:06 2018, Last Saved Time/Date: Mon Aug 13 19:00:06 2018, Number of Pages: 200, Number of Words: 12, Name of Creating Application: MSI Wrapper (8.0.26.0), Security: 2 |
| MD5: | AA16EBC633DFDE159A23B83F7F77E4F3 |
| SHA1: | 5A48311FB7F5EBEC1F84639EF57E17935D7ACC2C |
| SHA256: | 48B8D9EBC4B8D00D258B223732C8FAFC1E2B935F7064DF9D6520B68C04418C38 |
| SSDEEP: | 98304:G43dxBvxBvxBvxBvxB1FYwBvxBvxBfrOxB02vjdJnHbBLK33Fs2FH72lqm:VF56bdJSK2FqlB |
MALICIOUS
Writes to a start menu file
- cmd.exe (PID: 4084)
Application was dropped or rewritten from another process
- Edge.exe (PID: 764)
- MicrosoftEdge.exe (PID: 2244)
AGENTTESLA was detected
- MicrosoftEdge.exe (PID: 2244)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 4060)
- expand.exe (PID: 3292)
- Edge.exe (PID: 764)
- cmd.exe (PID: 4084)
Starts CMD.EXE for commands execution
- Edge.exe (PID: 764)
- MicrosoftEdge.exe (PID: 2244)
Creates files in the user directory
- cmd.exe (PID: 4084)
Checks for external IP
- MicrosoftEdge.exe (PID: 2244)
Uses WMIC.EXE to obtain a list of AntiViruses
- cmd.exe (PID: 1736)
Reads Environment values
- MicrosoftEdge.exe (PID: 2244)
INFO
Changes settings of System certificates
- DrvInst.exe (PID: 3276)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4068)
Searches for installed software
- msiexec.exe (PID: 4060)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3276)
Application launched itself
- msiexec.exe (PID: 4060)
Reads settings of System Certificates
- MicrosoftEdge.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Title: | Microsoft .NET Framework 4 Client Profile 4.0.30319.0 |
|---|---|
| Subject: | Microsoft .NET Framework 4 Client Profile |
| Author: | Microsoft Corporation |
| Keywords: | Installer |
| Comments: | - |
| Template: | Intel;1033 |
| RevisionNumber: | {EECF31ED-6347-4845-83CA-CB7F67FDE2C8} |
| CreateDate: | 2018:08:13 18:00:06 |
| ModifyDate: | 2018:08:13 18:00:06 |
| Pages: | 200 |
| Words: | 12 |
| Software: | MSI Wrapper (8.0.26.0) |
| Security: | Read-only recommended |
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1025 |
| Company: | Microsoft Corporation |
| Category: | - |
Total processes
49
Monitored processes
12
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Users\admin\AppData\Local\Temp\MW-71af44d9-bda8-44ae-ba5f-862048c8b3e7\files\Edge.exe" | C:\Users\admin\AppData\Local\Temp\MW-71af44d9-bda8-44ae-ba5f-862048c8b3e7\files\Edge.exe | MsiExec.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1532 | WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1712 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\48b8d9ebc4b8d00d258b223732c8fafc1e2b935f7064df9d6520b68c04418c38.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | "cmd.exe" /C WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List | C:\Windows\system32\cmd.exe | — | MicrosoftEdge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1924 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | C:\Users\admin\AppData\Local\Temp/MicrosoftEdge.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdge.exe | Edge.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3276 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004C0" "000004AC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3292 | "C:\Windows\System32\expand.exe" -R files.cab -F:* files | C:\Windows\System32\expand.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | C:\Windows\system32\MsiExec.exe -Embedding 74F3D08EC0C0A3A4C949DC99E9226327 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
971
Read events
764
Write events
195
Delete events
12
Modification events
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000983C303F85FBD401DC0F0000240F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000983C303F85FBD401DC0F0000240F0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000E036AC3F85FBD401DC0F0000240F0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4060) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000003A99AE3F85FBD401DC0F0000680A0000E8030000010000000000000000000000606F566B492C0C4592A26856D6AA51B30000000000000000 | |||
| (PID) Process: | (4068) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FC84BA3F85FBD401E40F0000FC0A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FC84BA3F85FBD401E40F0000CC0A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FC84BA3F85FBD401E40F0000B4040000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FC84BA3F85FBD401E40F000090030000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4068) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000640EC43F85FBD401E40F0000CC0A0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
7
Text files
139
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3276 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 4060 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3276 | DrvInst.exe | C:\Windows\INF\setupapi.ev3 | binary | |
MD5:— | SHA256:— | |||
| 3276 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 4060 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF5F3EBB025DA44A3C.TMP | — | |
MD5:— | SHA256:— | |||
| 3292 | expand.exe | C:\Users\admin\AppData\Local\Temp\MW-71af44d9-bda8-44ae-ba5f-862048c8b3e7\files\$dpx$.tmp\6924815e859b994bbfc387733c3ee6d6.tmp | — | |
MD5:— | SHA256:— | |||
| 4068 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 764 | Edge.exe | C:\Users\admin\AppData\Local\Temp\autC63A.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | msiexec.exe | C:\Config.Msi\ebb01.rbs | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2244 | MicrosoftEdge.exe | GET | 200 | 52.206.161.133:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2244 | MicrosoftEdge.exe | 172.217.21.234:443 | www.googleapis.com | Google Inc. | US | whitelisted |
2244 | MicrosoftEdge.exe | 52.206.161.133:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.googleapis.com |
| whitelisted |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2244 | MicrosoftEdge.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2 ETPRO signatures available at the full report