| File name: | 15-05-2025_FACT_12544872521255699333265552.exe |
| Full analysis: | https://app.any.run/tasks/c5652d2d-a025-4068-ab16-2b3a9ed377f1 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 16, 2025, 22:57:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | DCC9A4B03E126F3205E8596D4F93B4F3 |
| SHA1: | A4FC99BD5DAFAFB8CDA5DA51D1694E2409C209DD |
| SHA256: | 486E05B780FAD9B2281A1923F8653E0C725D2FC304894CD6E9DD5BF3ECCD705F |
| SSDEEP: | 98304:G/9ADTpciOSTmWh5s78aXq7ltAIGYdnIEGrpfcaqJRQ5GU/KqXCJjQKL7sPG4mXT:5d5QnoCbk |
MALICIOUS
Executing a file with an untrusted certificate
- VectorMix32.exe (PID: 3132)
- XPFix.exe (PID: 5056)
ASYNCRAT has been detected (SURICATA)
- VectorMix32.exe (PID: 3132)
SUSPICIOUS
Executable content was dropped or overwritten
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 4424)
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
- LabFusion.exe (PID: 6620)
- LabFusion.exe (PID: 1532)
Starts itself from another location
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 4424)
- LabFusion.exe (PID: 6620)
The process drops C-runtime libraries
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
- LabFusion.exe (PID: 6620)
Process drops legitimate windows executable
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
- LabFusion.exe (PID: 6620)
There is functionality for taking screenshot (YARA)
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
Contacting a server suspected of hosting an CnC
- VectorMix32.exe (PID: 3132)
Connects to unusual port
- VectorMix32.exe (PID: 3132)
INFO
Create files in a temporary directory
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 4424)
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
- LabFusion.exe (PID: 1532)
- XPFix.exe (PID: 5056)
Checks supported languages
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 4424)
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
- LabFusion.exe (PID: 6620)
- LabFusion.exe (PID: 1532)
- VectorMix32.exe (PID: 3132)
- XPFix.exe (PID: 5056)
The sample compiled with english language support
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 4424)
- 15-05-2025_FACT_12544872521255699333265552.exe (PID: 496)
- LabFusion.exe (PID: 6620)
- LabFusion.exe (PID: 1532)
Reads the computer name
- LabFusion.exe (PID: 6620)
- LabFusion.exe (PID: 1532)
- VectorMix32.exe (PID: 3132)
- XPFix.exe (PID: 5056)
Creates files in the program directory
- LabFusion.exe (PID: 6620)
The sample compiled with chinese language support
- LabFusion.exe (PID: 1532)
Creates files or folders in the user directory
- LabFusion.exe (PID: 1532)
Reads the machine GUID from the registry
- VectorMix32.exe (PID: 3132)
Reads the software policy settings
- VectorMix32.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:04:05 13:00:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.34 |
| CodeSize: | 442880 |
| InitializedDataSize: | 237568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x46a50 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.6.1.0 |
| ProductVersionNumber: | 3.6.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | Reclaim |
| FileDescription: | Flagship |
| FileVersion: | 3.6.1.0 |
| InternalName: | burn |
| OriginalFileName: | humour.exe |
| ProductName: | Flagship |
| ProductVersion: | 3.6.1.0 |
| LegalCopyright: | Copyright (c) Reclaim. All rights reserved. |
Total processes
134
Monitored processes
9
Malicious processes
5
Suspicious processes
1
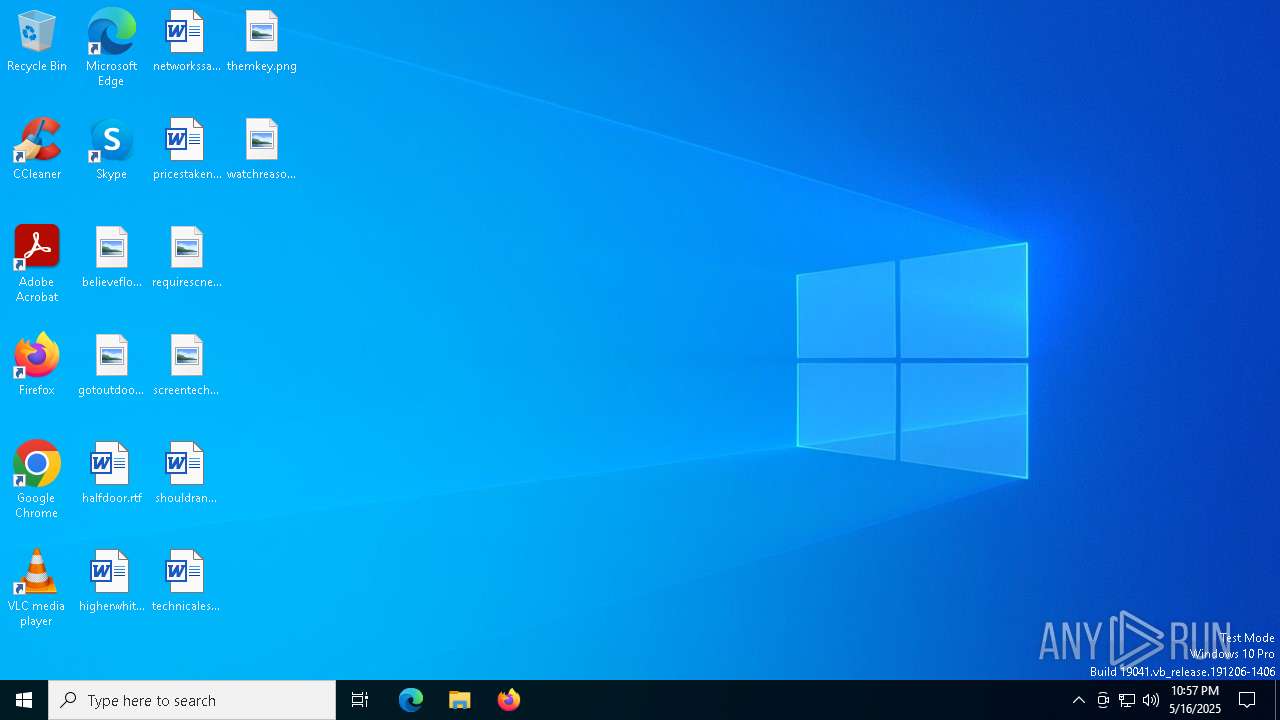
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.cr\15-05-2025_FACT_12544872521255699333265552.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\15-05-2025_FACT_12544872521255699333265552.exe" -burn.filehandle.attached=676 -burn.filehandle.self=732 | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.cr\15-05-2025_FACT_12544872521255699333265552.exe | 15-05-2025_FACT_12544872521255699333265552.exe | ||||||||||||
User: admin Company: Reclaim Integrity Level: MEDIUM Description: Flagship Exit code: 0 Version: 3.6.1.0 Modules
| |||||||||||||||
| 1532 | C:\ProgramData\writerdebug\LabFusion.exe | C:\ProgramData\writerdebug\LabFusion.exe | LabFusion.exe | ||||||||||||
User: admin Company: AnyMP4 Integrity Level: MEDIUM Description: AnyMP4 Blu-ray Player Exit code: 0 Version: 6.5.68.144795 Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3132 | C:\Users\admin\VectorMix32.exe | C:\Users\admin\VectorMix32.exe | LabFusion.exe | ||||||||||||
User: admin Company: Flexera Software LLC Integrity Level: MEDIUM Description: ISAppxStub Version: 23.0.195.0 Modules
| |||||||||||||||
| 4200 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | "C:\Users\admin\AppData\Local\Temp\15-05-2025_FACT_12544872521255699333265552.exe" | C:\Users\admin\AppData\Local\Temp\15-05-2025_FACT_12544872521255699333265552.exe | explorer.exe | ||||||||||||
User: admin Company: Reclaim Integrity Level: MEDIUM Description: Flagship Exit code: 0 Version: 3.6.1.0 Modules
| |||||||||||||||
| 5056 | "C:\Users\admin\AppData\Roaming\writerdebug\XPFix.exe" "C:\Users\admin\AppData\Roaming\writerdebug\XPFix.exe" /update | C:\Users\admin\AppData\Roaming\writerdebug\XPFix.exe | — | LabFusion.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: MEDIUM Description: 360安全卫士 安全防护中心模块 Exit code: 0 Version: 1, 0, 0, 1013 Modules
| |||||||||||||||
| 6620 | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\LabFusion.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\LabFusion.exe | 15-05-2025_FACT_12544872521255699333265552.exe | ||||||||||||
User: admin Company: AnyMP4 Integrity Level: MEDIUM Description: AnyMP4 Blu-ray Player Exit code: 0 Version: 6.5.68.144795 Modules
| |||||||||||||||
Total events
4 082
Read events
4 082
Write events
0
Delete events
0
Modification events
Executable files
16
Suspicious files
8
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4424 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{49D63430-1EFA-4E66-A54F-751AB9022FE1}\.cr\15-05-2025_FACT_12544872521255699333265552.exe | executable | |
MD5:2F545CC6BB61542C1A25608A5B7E53A6 | SHA256:BFF7030495139A59018E88811DE6EF81582A4D6475C0997F21F13BAFCBCC8A29 | |||
| 496 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\Geem.ok | binary | |
MD5:581CE9C3943671883B3D598A68D003F0 | SHA256:BE15144F273ABA828F565397785B460CF9EFE878D199E5B1099A4BE2735F1E36 | |||
| 496 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\msvcp120.dll | executable | |
MD5:EDEF53778EAAFE476EE523BE5C2AB67F | SHA256:92FAEDD18A29E1BD2DD27A1D805EA5AA3E73B954A625AF45A74F49D49506D20F | |||
| 496 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\Jug.dll | executable | |
MD5:F7E5B032E7300C8E9B87A55F57D6FD66 | SHA256:D11DE71A9DEEB3C917DCDEFE0BFD87B0FD4CFAE4FCFD85E7E653290F26D9BB2D | |||
| 496 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\msvcr120.dll | executable | |
MD5:AEB29CCC27E16C4FD223A00189B44524 | SHA256:D28C7AB34842B6149609BD4E6B566DDAB8B891F0D5062480A253EF20A6A2CAAA | |||
| 1532 | LabFusion.exe | C:\Users\admin\AppData\Local\Temp\EBFCF68.tmp | — | |
MD5:— | SHA256:— | |||
| 496 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\Qt5Gui.dll | executable | |
MD5:72AC63E9E9F015D6471DDE58297A4FC6 | SHA256:6B8A49B6B37D69213762C8F2C8A9970014364F4055F08A850D27C0343FBE00DE | |||
| 496 | 15-05-2025_FACT_12544872521255699333265552.exe | C:\Users\admin\AppData\Local\Temp\{81A3C180-5EA4-4609-BB08-E1624429E5EE}\.ba\Qt5Core.dll | executable | |
MD5:B03D12CDE3CECC10FA32D74E5B487F5C | SHA256:58222718A1B04AF9F3578713C190EBA513DA81C37FFF9615E2C43228427206E2 | |||
| 6620 | LabFusion.exe | C:\ProgramData\writerdebug\msvcr120.dll | executable | |
MD5:AEB29CCC27E16C4FD223A00189B44524 | SHA256:D28C7AB34842B6149609BD4E6B566DDAB8B891F0D5062480A253EF20A6A2CAAA | |||
| 6620 | LabFusion.exe | C:\ProgramData\writerdebug\Qt5Gui.dll | executable | |
MD5:72AC63E9E9F015D6471DDE58297A4FC6 | SHA256:6B8A49B6B37D69213762C8F2C8A9970014364F4055F08A850D27C0343FBE00DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
14
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4244 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4244 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
lindo1.dynuddns.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.dynuddns .com Domain |
3132 | VectorMix32.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
3132 | VectorMix32.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
3132 | VectorMix32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
3132 | VectorMix32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |