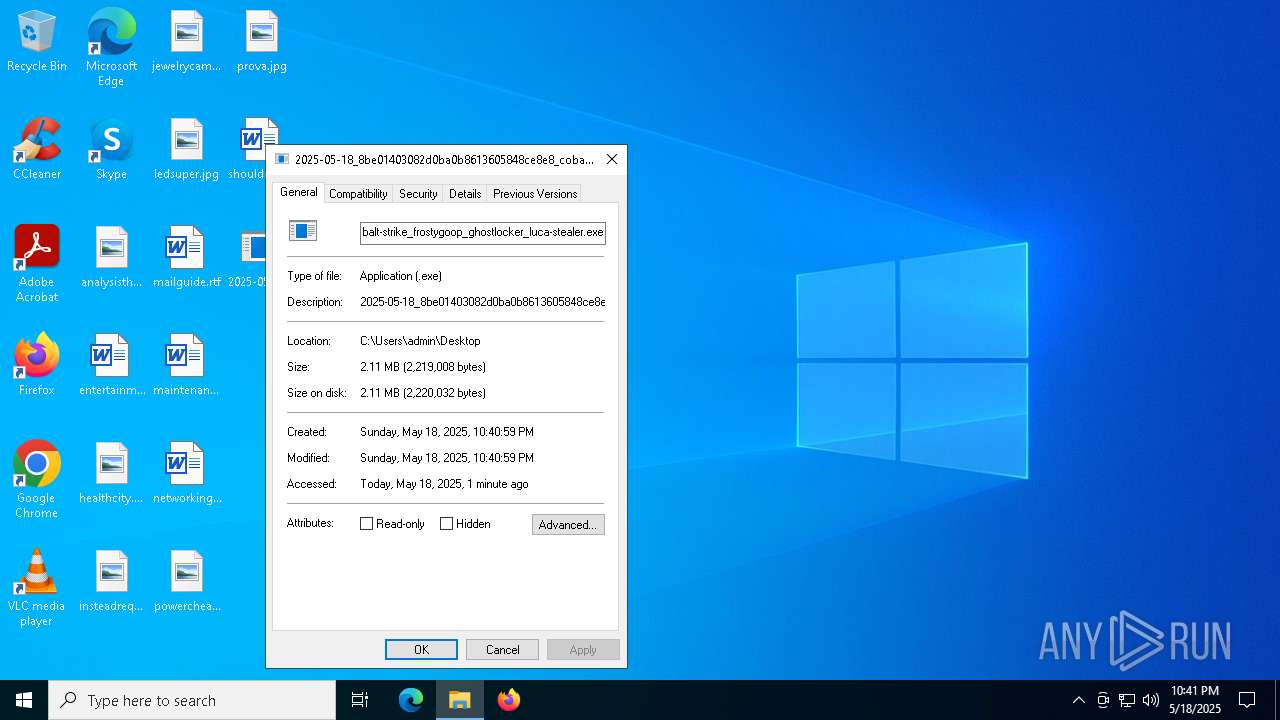
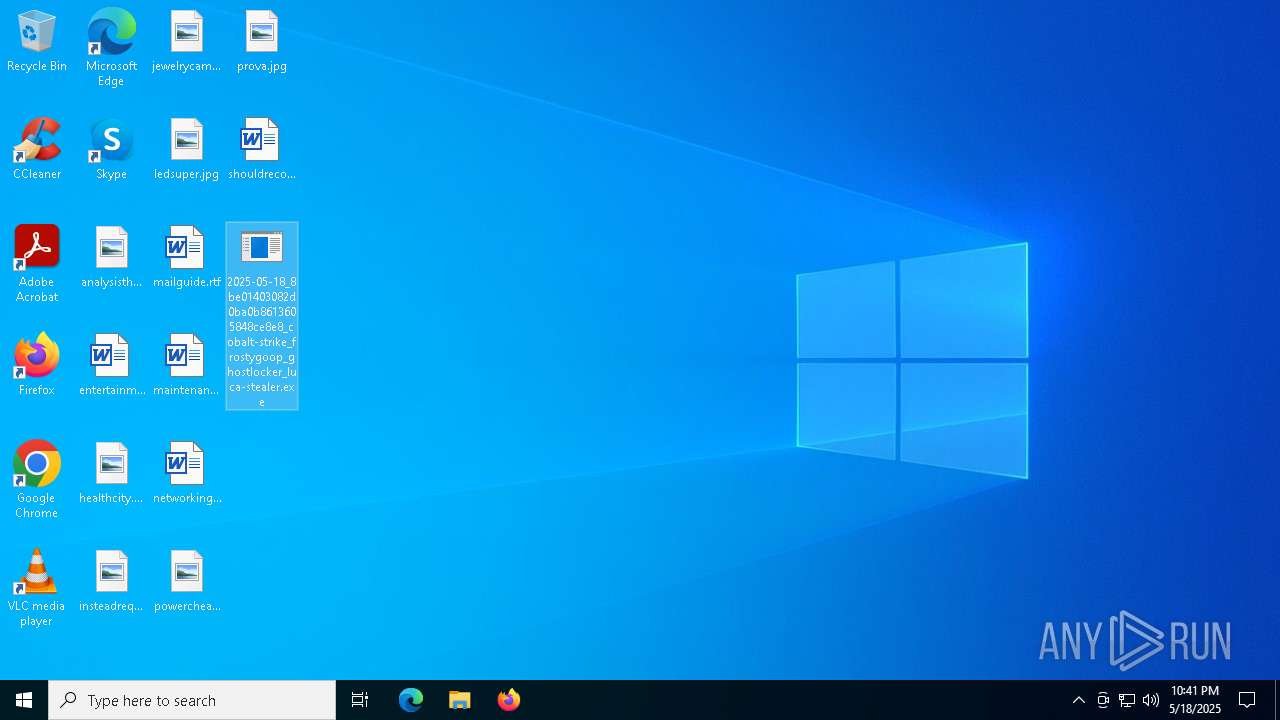
| File name: | 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer |
| Full analysis: | https://app.any.run/tasks/8e57bbab-580e-4f12-aba0-7ab4215787b0 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | May 18, 2025, 22:40:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 13 sections |
| MD5: | 8BE01403082D0BA0B8613605848CE8E8 |
| SHA1: | 8626660CE11C05D0FDA2620425B515BAB8079600 |
| SHA256: | 48698DF9F88DBEE85A8AF7C974B77A130E3F7E41A14AA6E1962F7778AB092661 |
| SSDEEP: | 49152:v3VO/erNwFhPAdKjCEeAA+uOgbspoUGZTMTMX4lvfSbIHvhK1gAlGvX6xzTKCABp:wd3sTMcbIPGkvXIzTseF/vMNo/M |
MALICIOUS
COBALTSTRIKE has been detected (YARA)
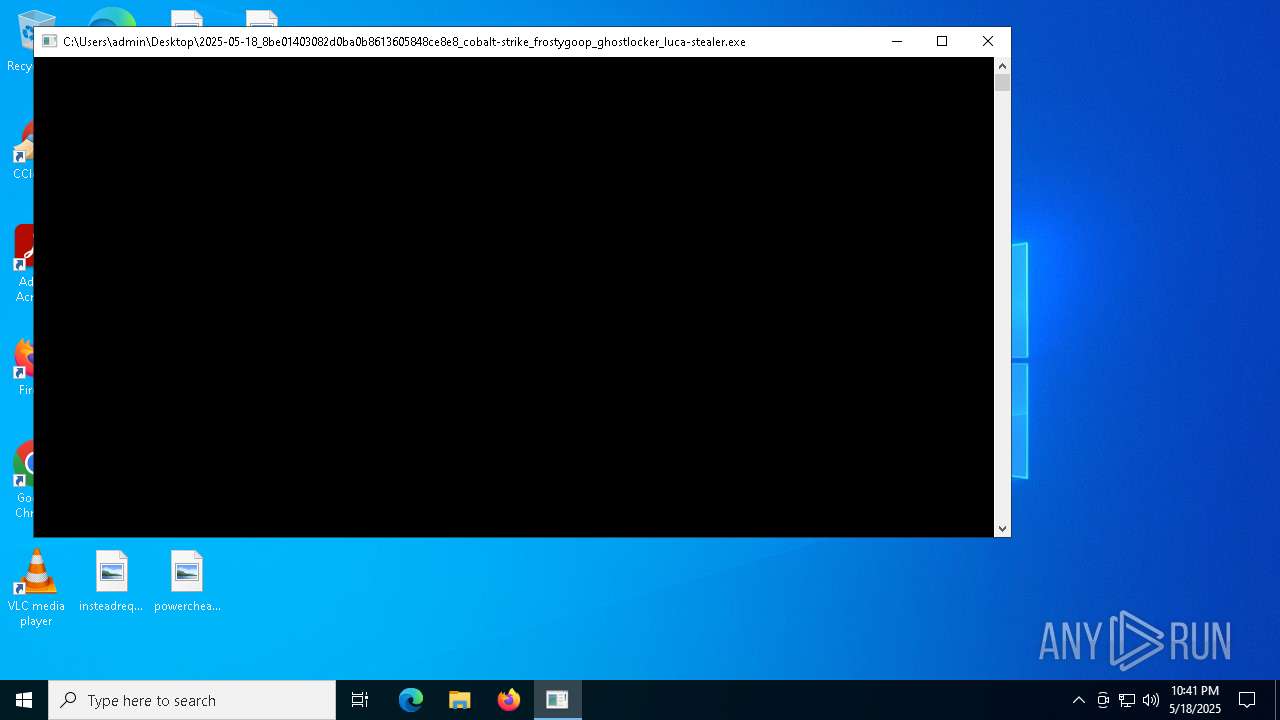
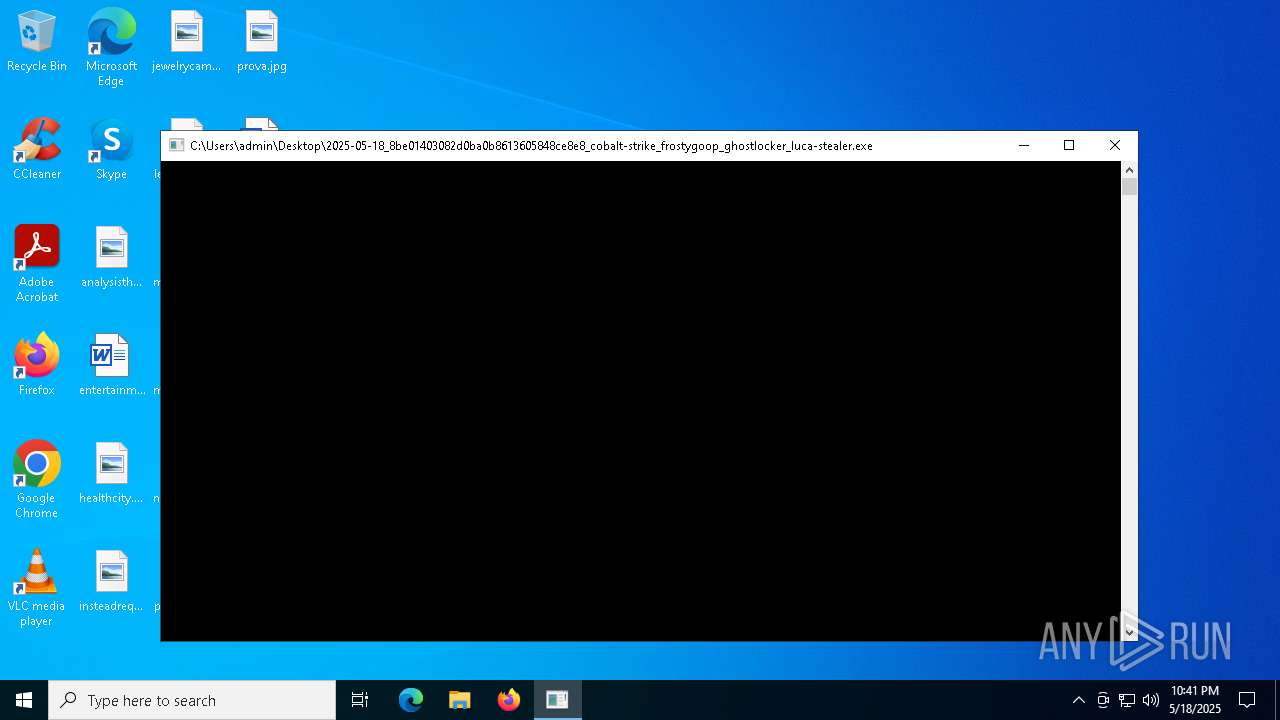
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 2136)
SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 2136)
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 7984)
INFO
Checks supported languages
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 2136)
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 7984)
Application based on Golang
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 2136)
Checks proxy server information
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 2136)
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 7984)
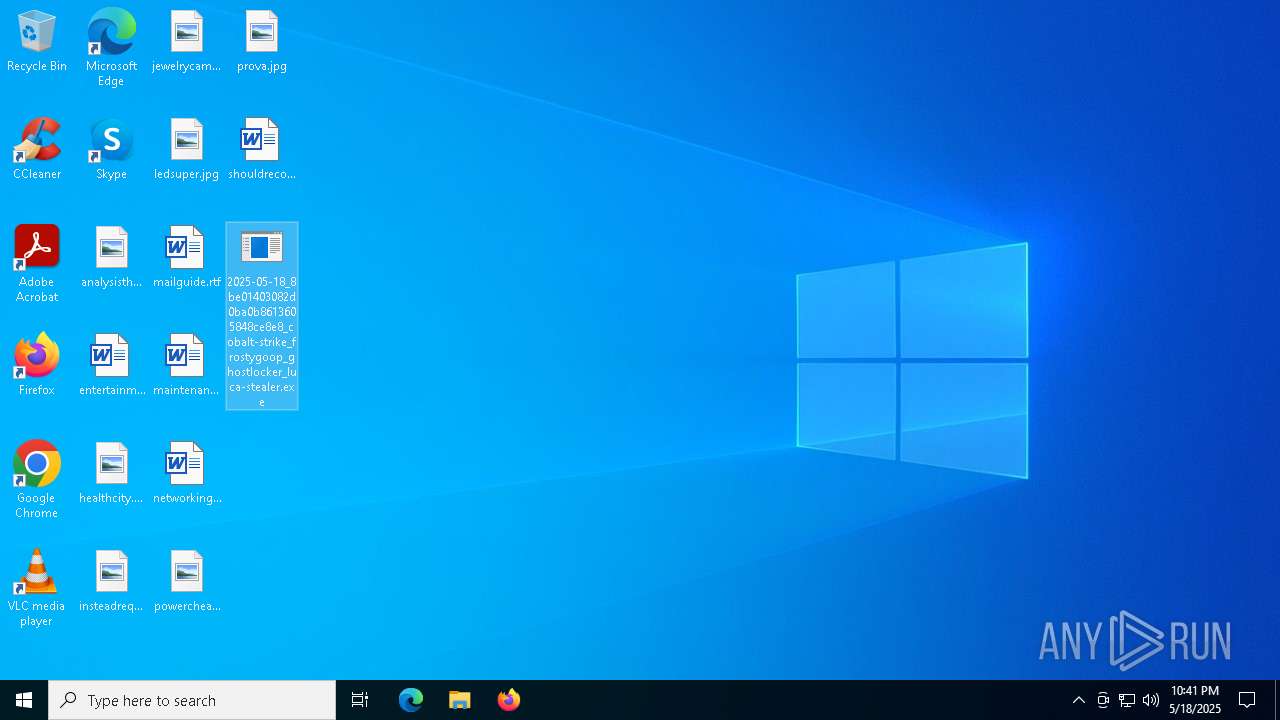
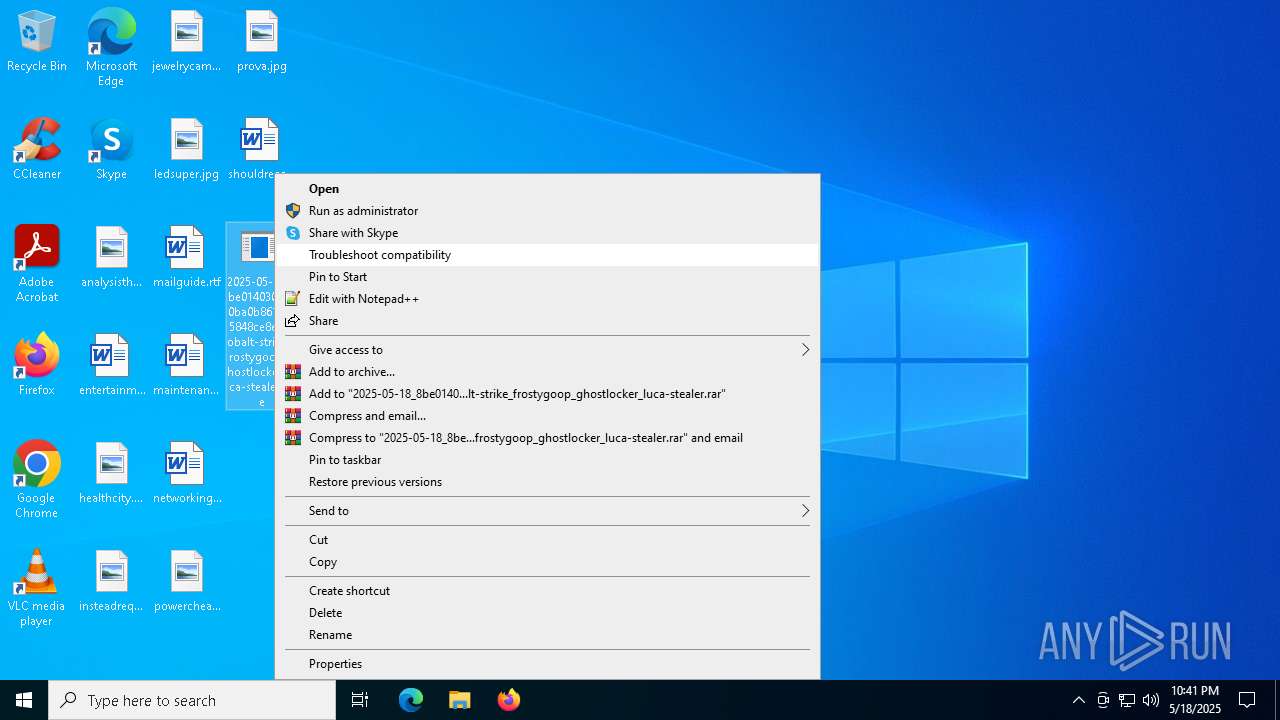
Manual execution by a user
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 7984)
Reads the computer name
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 2136)
- 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe (PID: 7984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
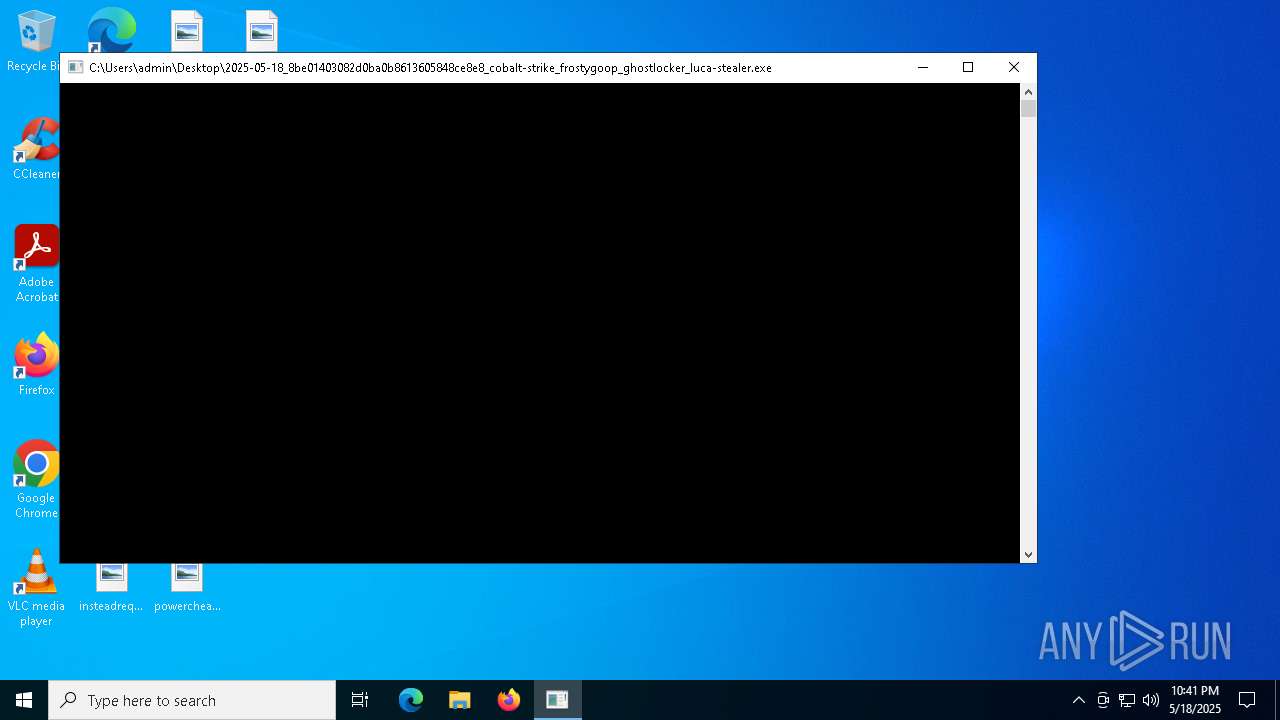
CobalStrike
(PID) Process(2136) 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe
C2192.168.70.129:80/jquery-3.3.2.slim.min.js
HeadersAccept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://code.jquery.com/
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 6.3; Trident/7.0; rv:11.0) like Gecko
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 599040 |
| InitializedDataSize: | 143360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5fde0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
Total processes
133
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2136 | "C:\Users\admin\Desktop\2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe" | C:\Users\admin\Desktop\2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
CobalStrike(PID) Process(2136) 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe C2192.168.70.129:80/jquery-3.3.2.slim.min.js HeadersAccept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://code.jquery.com/
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (Windows NT 6.3; Trident/7.0; rv:11.0) like Gecko | |||||||||||||||
| 2284 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7984 | "C:\Users\admin\Desktop\2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe" | C:\Users\admin\Desktop\2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
| 7996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
876
Read events
876
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7756 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7756 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2136 | 2025-05-18_8be01403082d0ba0b8613605848ce8e8_cobalt-strike_frostygoop_ghostlocker_luca-stealer.exe | 192.168.70.129:80 | — | — | — | unknown |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |