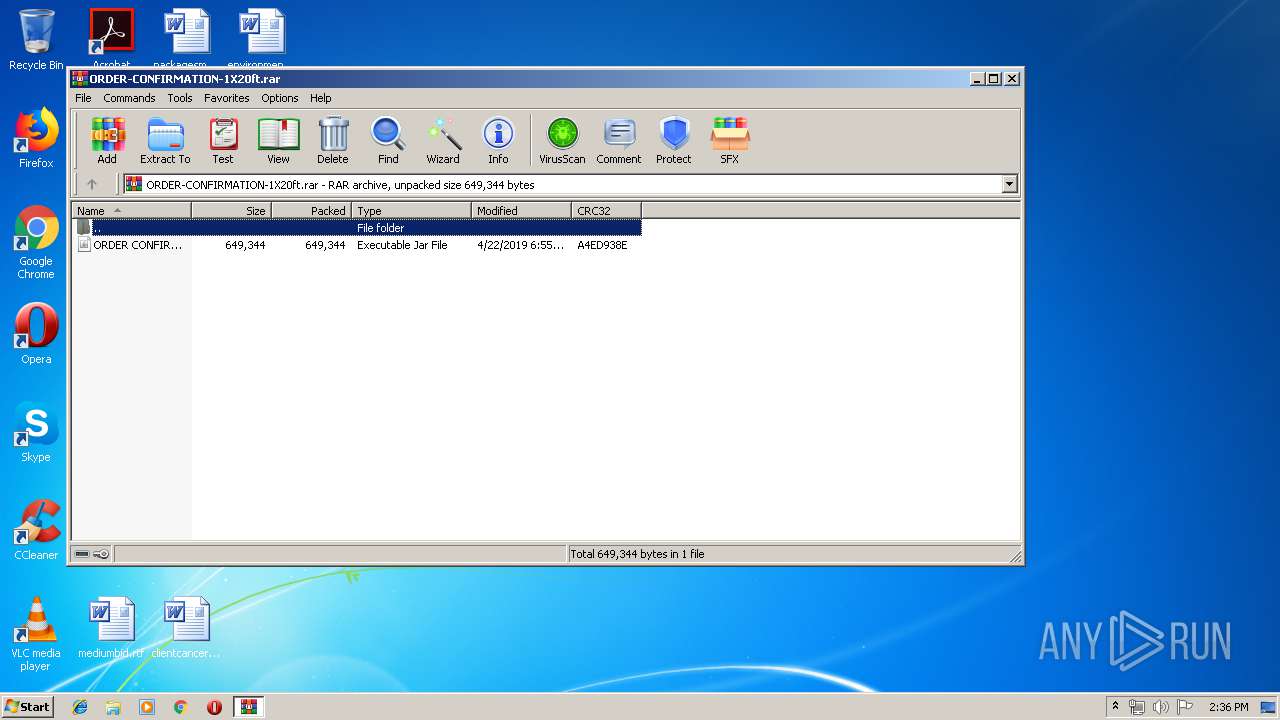
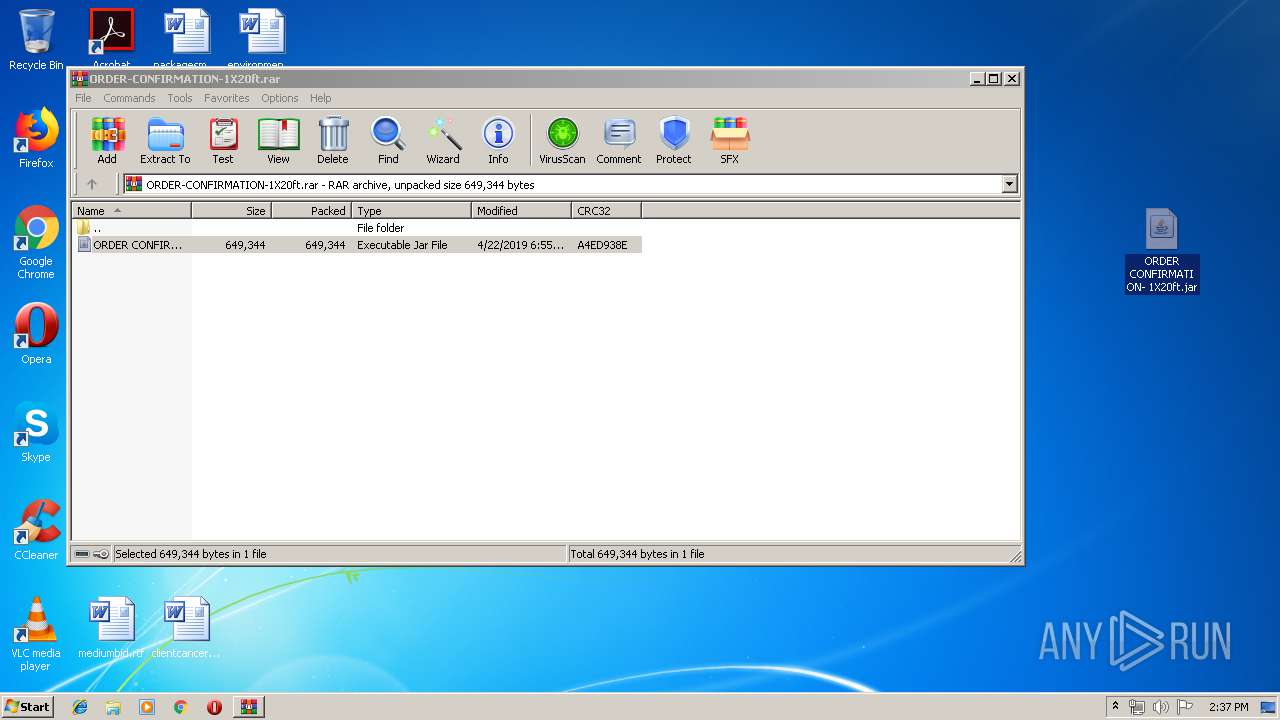
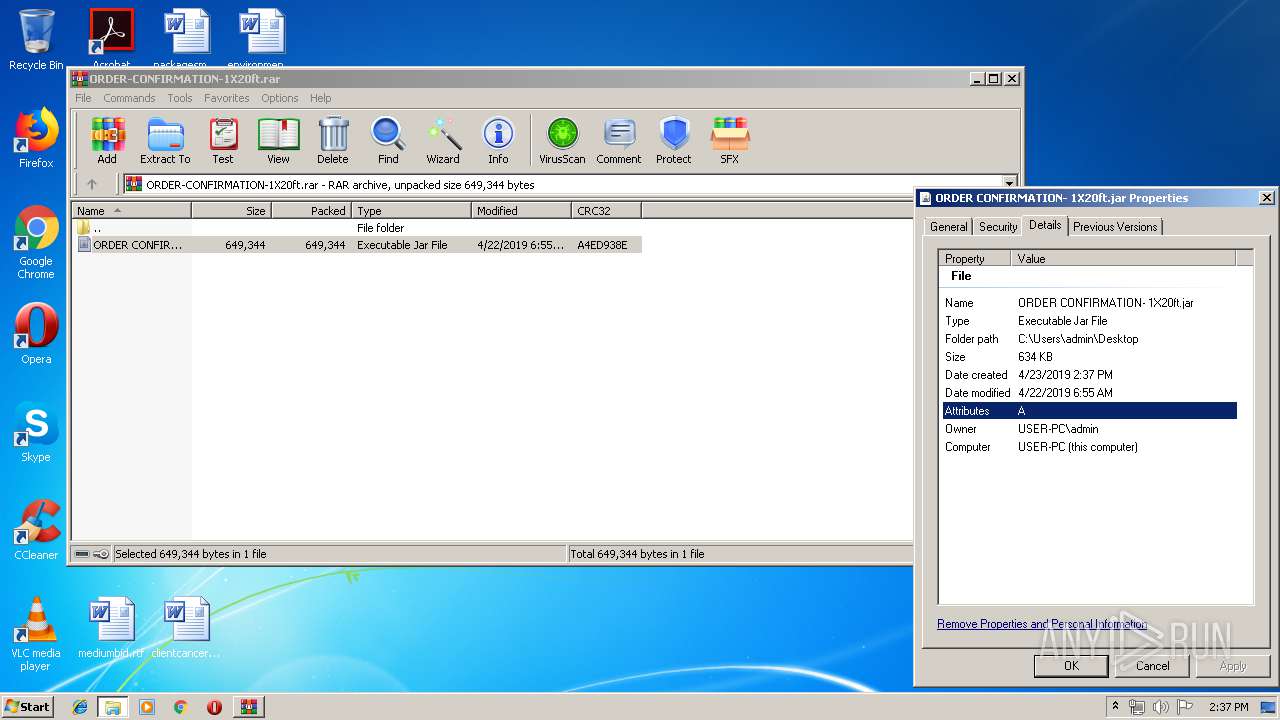
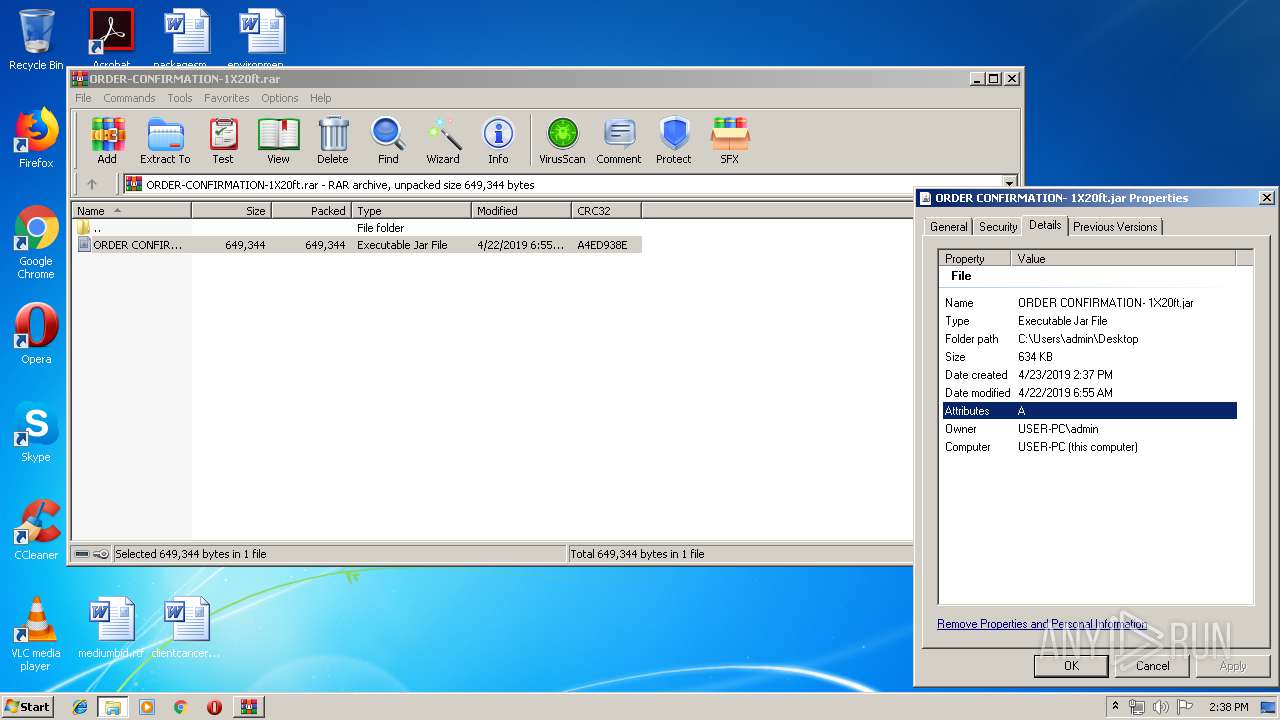
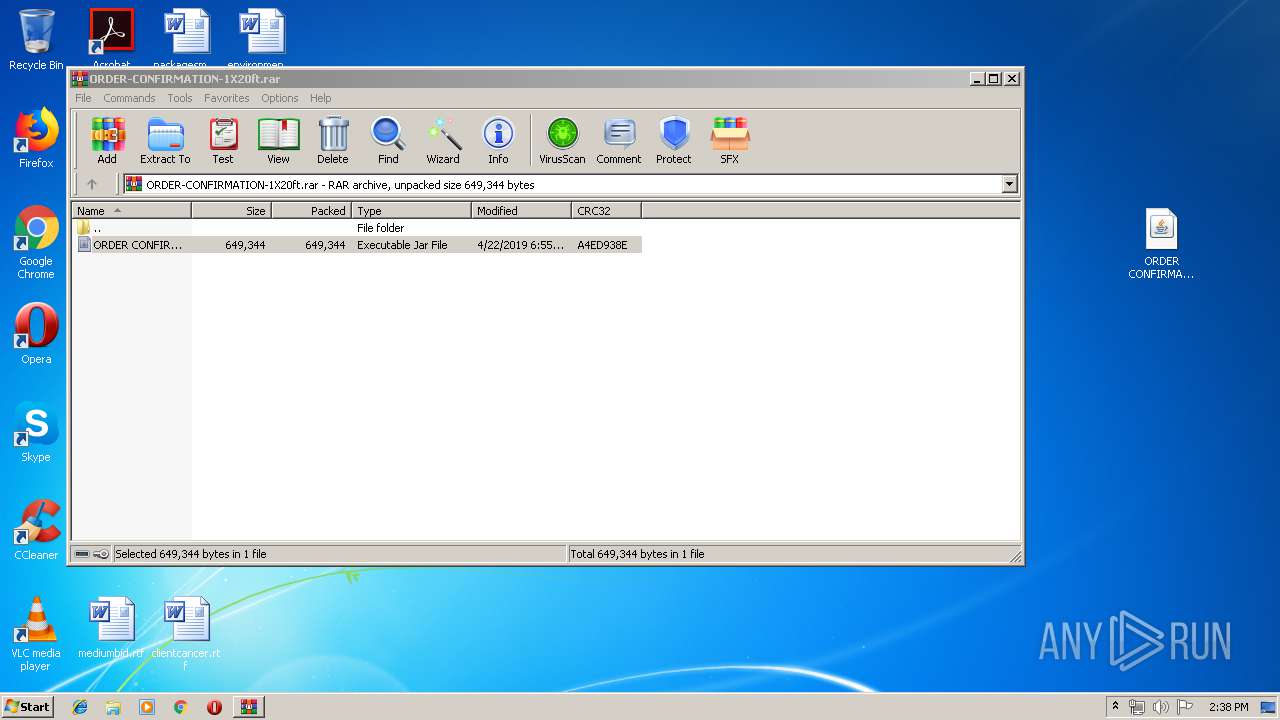
| File name: | ORDER-CONFIRMATION-1X20ft.rar |
| Full analysis: | https://app.any.run/tasks/bf362679-e3de-4d0d-9d58-1f580a28e0f5 |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | April 23, 2019, 13:36:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6167787A58C6EF5B9830C76BE2D64788 |
| SHA1: | 1C83E6EBCAF8121830DFD952D4A21F5A67813C57 |
| SHA256: | 482A7AFC18199E76DBFF9132CFE5DFA13C256BE34E41696DBE11473E31D0E624 |
| SSDEEP: | 12288:3uSnTTdBOMAipYHho5umXg0fn7iE8aYULPX2a1Gdl4tvoc+hXZtVX99c:39T+MANHho5umQ0fuE3xPX2aEdCr+hy |
MALICIOUS
Uses Task Scheduler to run other applications
- WScript.exe (PID: 2472)
Writes to a start menu file
- WScript.exe (PID: 2472)
AdWind was detected
- java.exe (PID: 2052)
- java.exe (PID: 460)
Changes the autorun value in the registry
- WScript.exe (PID: 2472)
- reg.exe (PID: 1260)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2112)
Loads dropped or rewritten executable
- wscript.exe (PID: 1892)
- java.exe (PID: 2052)
- javaw.exe (PID: 3516)
- explorer.exe (PID: 2044)
- svchost.exe (PID: 820)
- javaw.exe (PID: 3156)
- javaw.exe (PID: 1040)
- java.exe (PID: 460)
Application was dropped or rewritten from another process
- javaw.exe (PID: 3156)
- javaw.exe (PID: 3516)
- java.exe (PID: 2052)
- java.exe (PID: 460)
- javaw.exe (PID: 1040)
Uses TASKKILL.EXE to kill security tools
- javaw.exe (PID: 1040)
Turns off system restore
- regedit.exe (PID: 1440)
Changes Image File Execution Options
- regedit.exe (PID: 1440)
SUSPICIOUS
Executes JAVA applets
- explorer.exe (PID: 2044)
- wscript.exe (PID: 1892)
- javaw.exe (PID: 3516)
Executes scripts
- wscript.exe (PID: 1892)
- javaw.exe (PID: 3156)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 4076)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 2684)
- cmd.exe (PID: 1860)
- cmd.exe (PID: 836)
- cmd.exe (PID: 3860)
- cmd.exe (PID: 712)
Application launched itself
- wscript.exe (PID: 1892)
Creates files in the user directory
- wscript.exe (PID: 1892)
- javaw.exe (PID: 3516)
- WScript.exe (PID: 2472)
- xcopy.exe (PID: 2832)
- explorer.exe (PID: 2044)
Starts CMD.EXE for commands execution
- java.exe (PID: 2052)
- javaw.exe (PID: 3516)
- javaw.exe (PID: 1040)
- java.exe (PID: 460)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 3516)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3516)
Starts itself from another location
- javaw.exe (PID: 3516)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2832)
Reads Internet Cache Settings
- explorer.exe (PID: 2044)
Uses TASKKILL.EXE to kill process
- javaw.exe (PID: 1040)
INFO
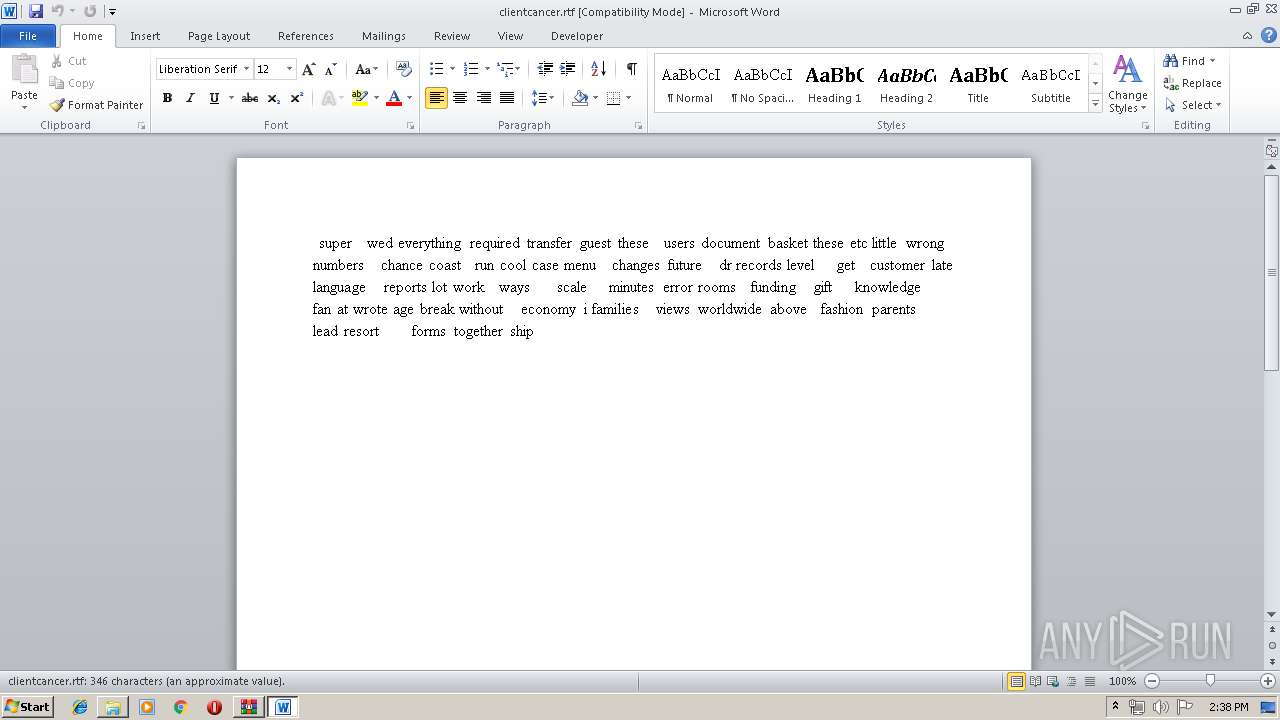
Starts Microsoft Office Application
- explorer.exe (PID: 2044)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2556)
Creates files in the user directory
- WINWORD.EXE (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
392
Monitored processes
189
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | taskkill /IM K7CrvSvc.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | taskkill /IM freshclam.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | taskkill /IM V3Svc.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 320 | taskkill /IM K7EmlPxy.EXE /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | taskkill /IM SASCore64.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 344 | taskkill /IM FPAVServer.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 368 | "C:\Windows\regedit.exe" /s C:\Users\admin\AppData\Local\Temp\lkUHuIcfeG620836796440885840.reg | C:\Windows\regedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | taskkill /IM PSUAMain.exe /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 460 | C:\Users\admin\AppData\Roaming\Oracle\bin\java.exe -jar C:\Users\admin\AppData\Local\Temp\_0.78071017881389898125763587183344232.class | C:\Users\admin\AppData\Roaming\Oracle\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 480 | taskkill /IM VIEWTCP.EXE /T /F | C:\Windows\system32\taskkill.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 242
Read events
5 878
Write events
353
Delete events
11
Modification events
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ORDER-CONFIRMATION-1X20ft.rar | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3872) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
110
Suspicious files
12
Text files
82
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
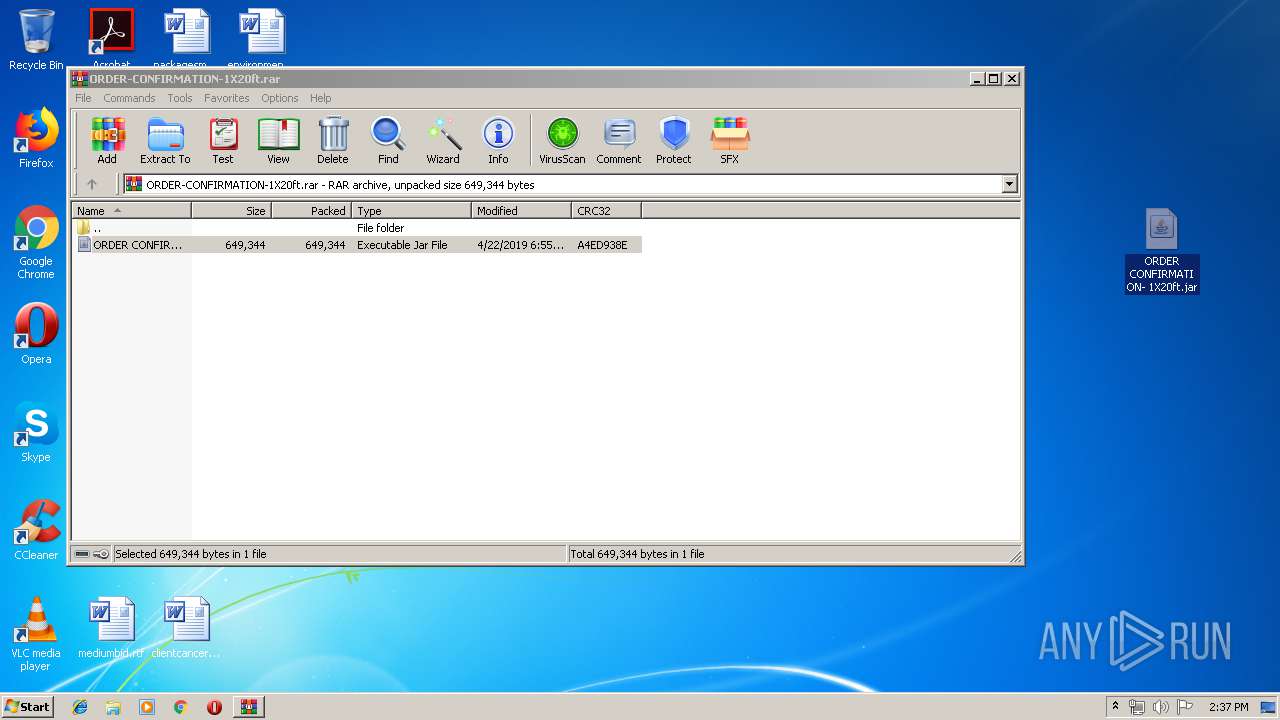
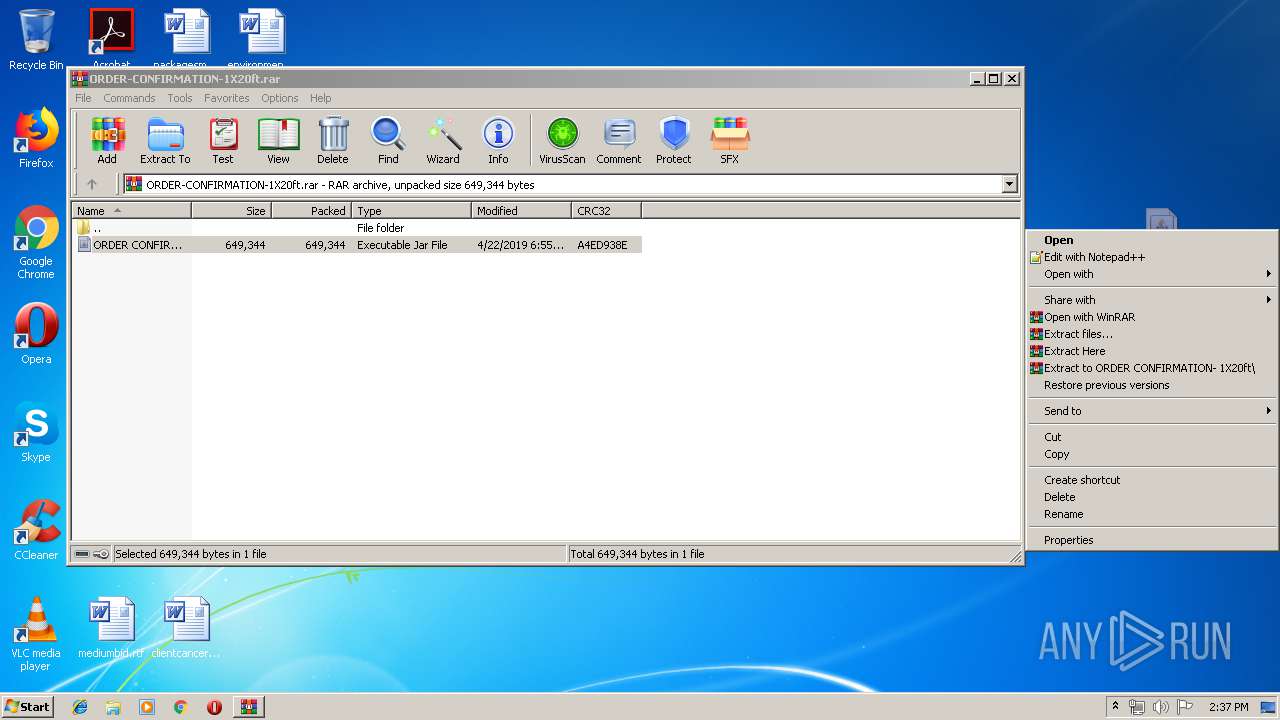
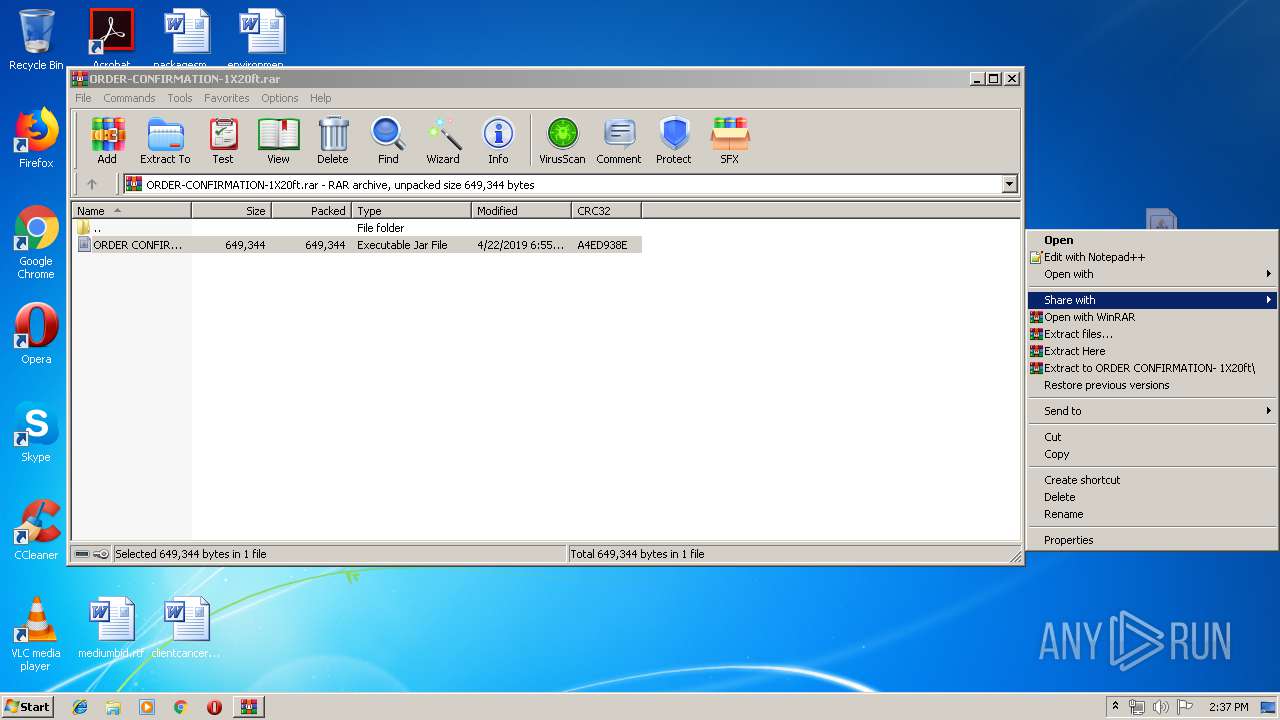
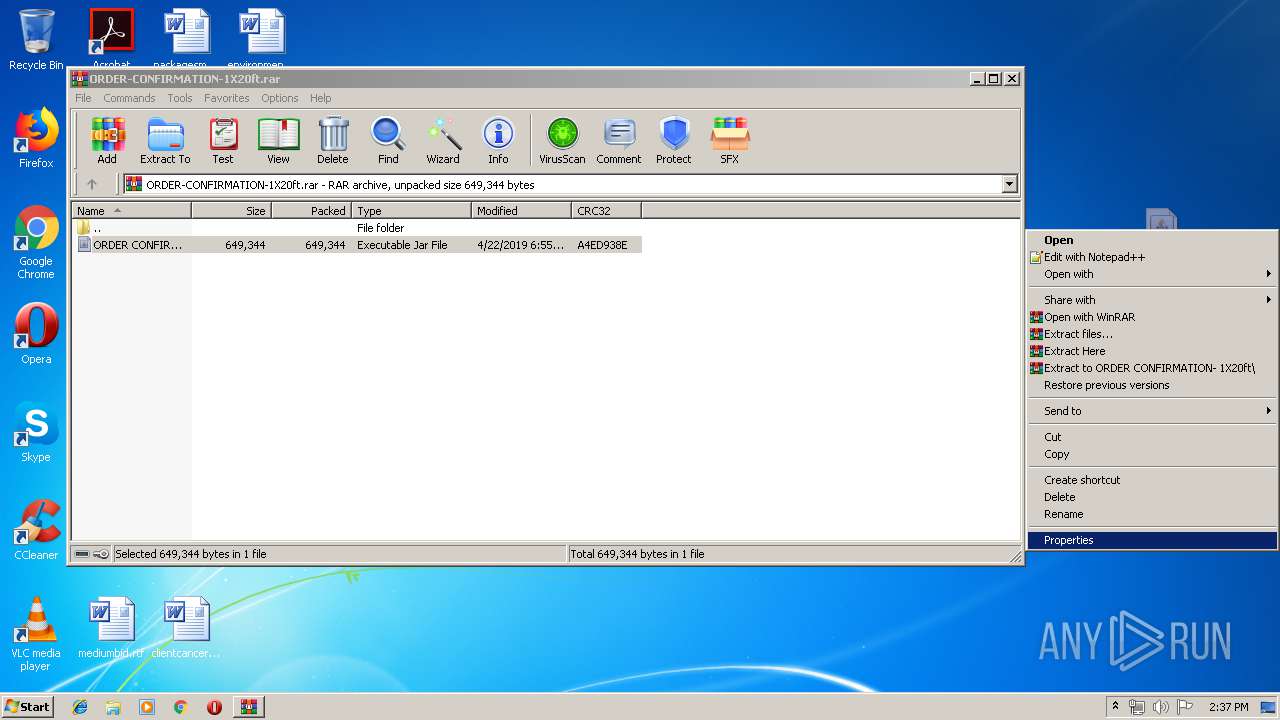
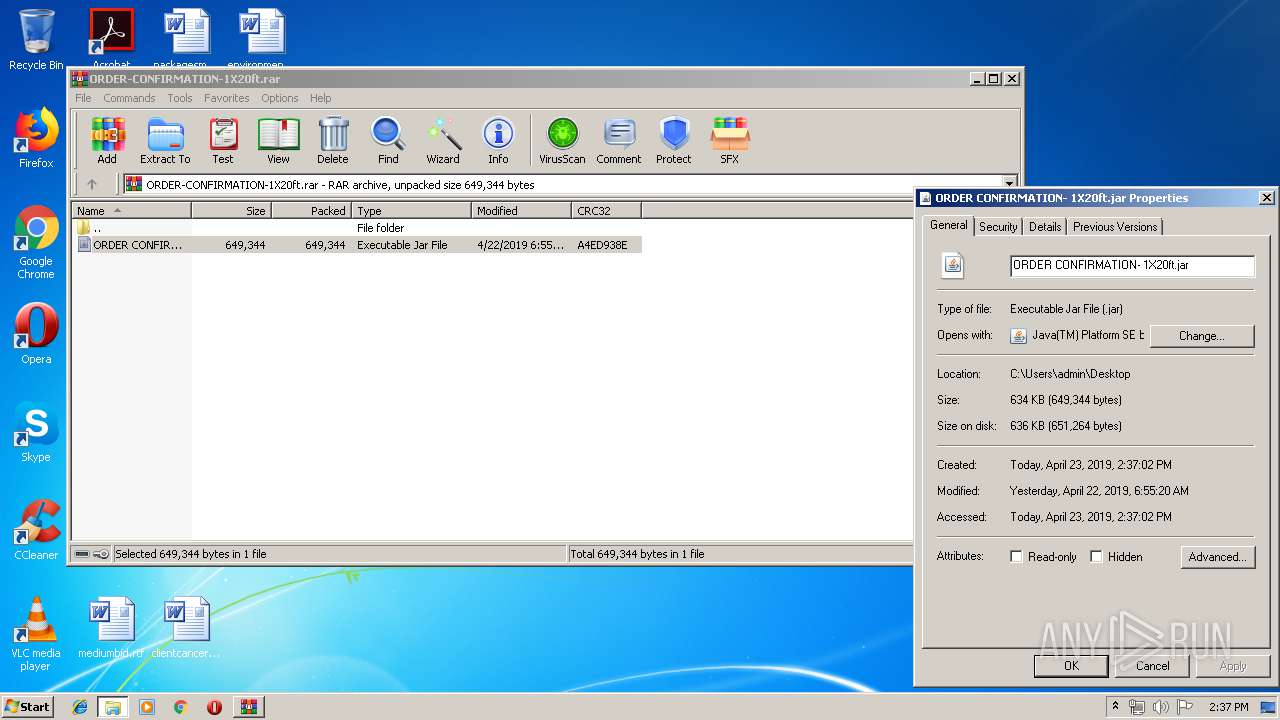
| 2044 | explorer.exe | C:\Users\admin\Desktop\ORDER CONFIRMATION- 1X20ft.jar | compressed | |
MD5:— | SHA256:— | |||
| 3156 | javaw.exe | C:\Users\admin\ahofotehjw.js | text | |
MD5:— | SHA256:— | |||
| 2052 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2472 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\dKQJdKjHMk.js | text | |
MD5:— | SHA256:— | |||
| 3156 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3516 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 1892 | wscript.exe | C:\Users\admin\AppData\Roaming\dKQJdKjHMk.js | text | |
MD5:— | SHA256:— | |||
| 1892 | wscript.exe | C:\Users\admin\AppData\Roaming\konbsy.txt | java | |
MD5:— | SHA256:— | |||
| 3872 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3872.12360\ORDER CONFIRMATION- 1X20ft.jar | compressed | |
MD5:— | SHA256:— | |||
| 3516 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
41
DNS requests
4
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2472 | WScript.exe | 194.5.98.8:7755 | unknownsoft.duckdns.org | — | FR | malicious |
1040 | javaw.exe | 91.192.100.30:6496 | emacomplex.duckdns.org | SOFTplus Entwicklungen GmbH | CH | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
unknownsoft.duckdns.org |
| malicious |
emacomplex.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |