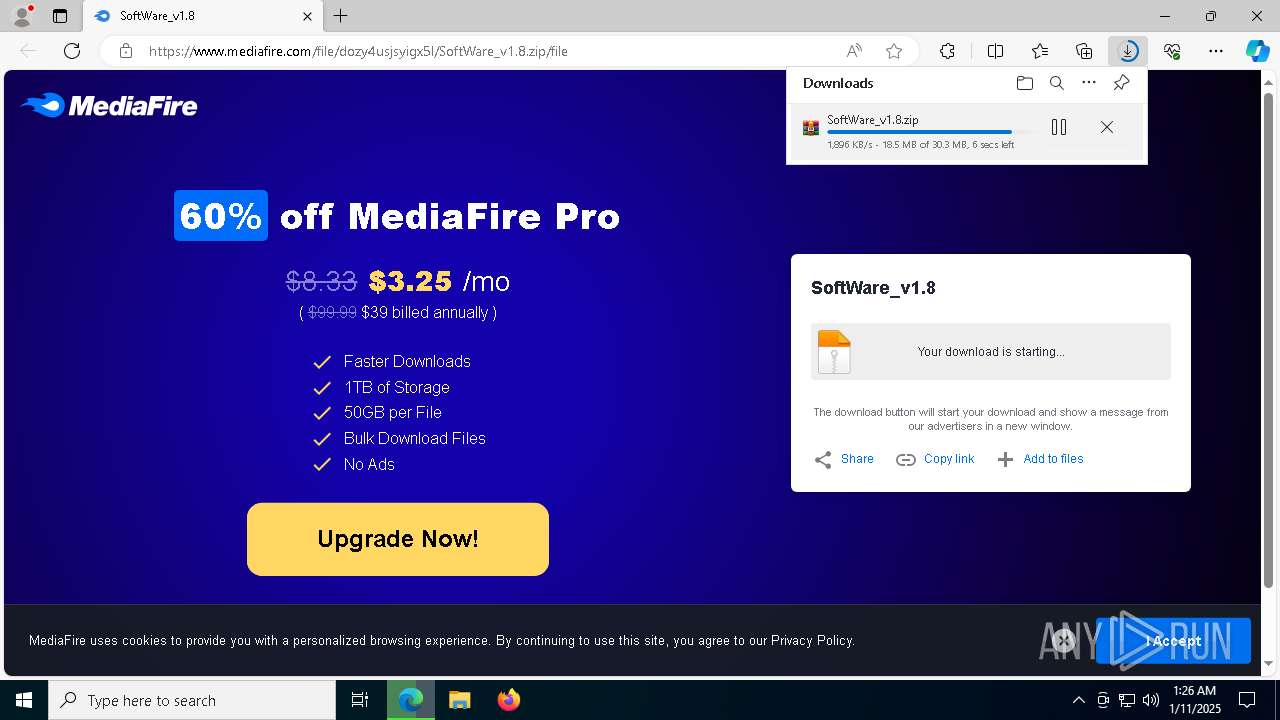
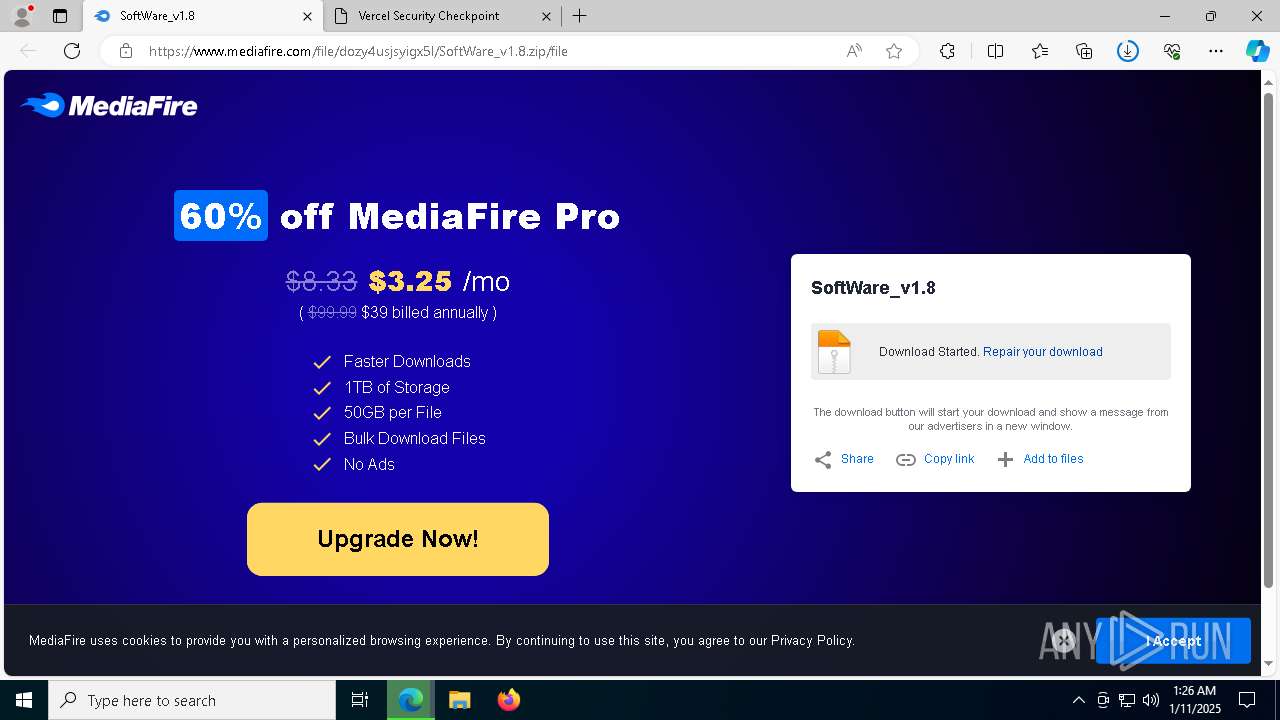
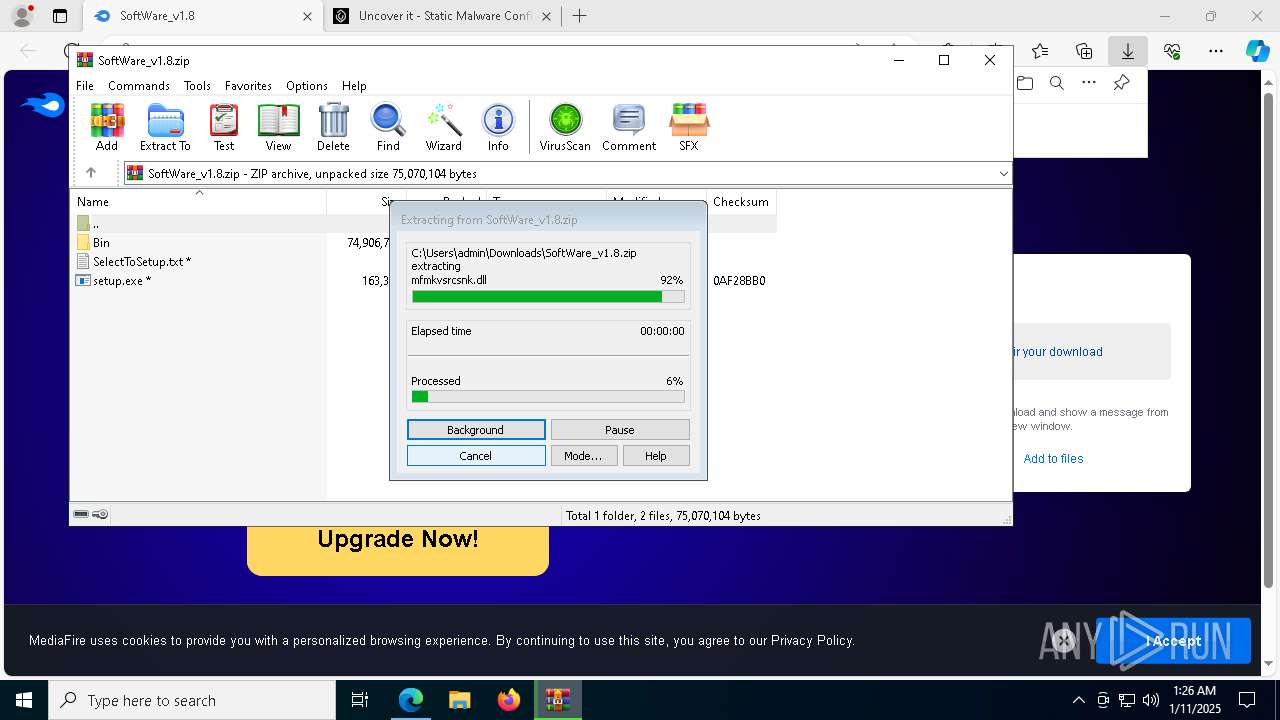
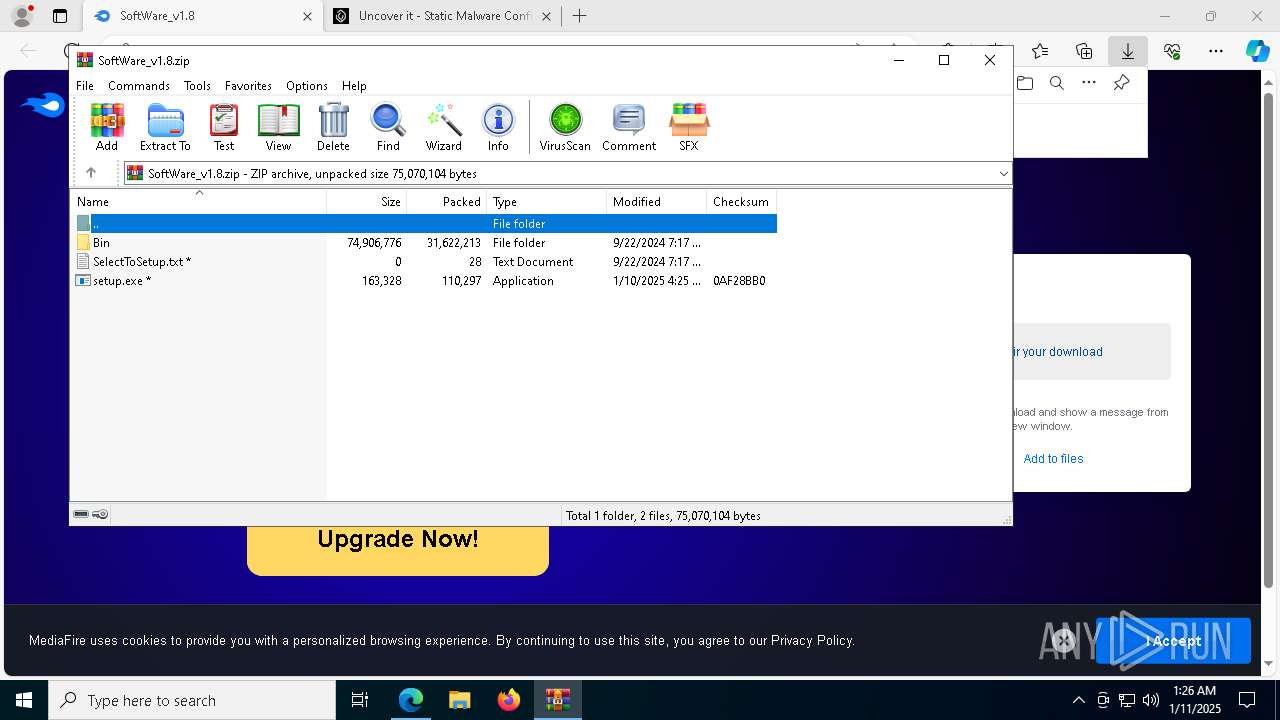
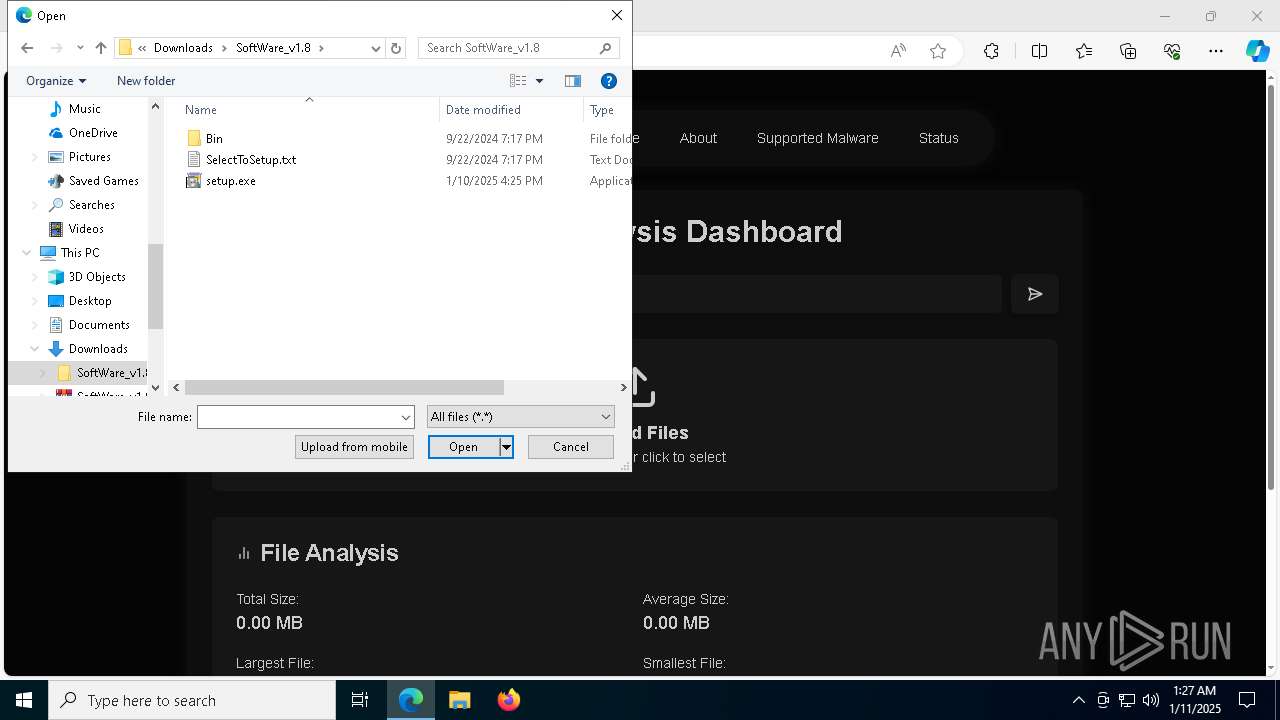
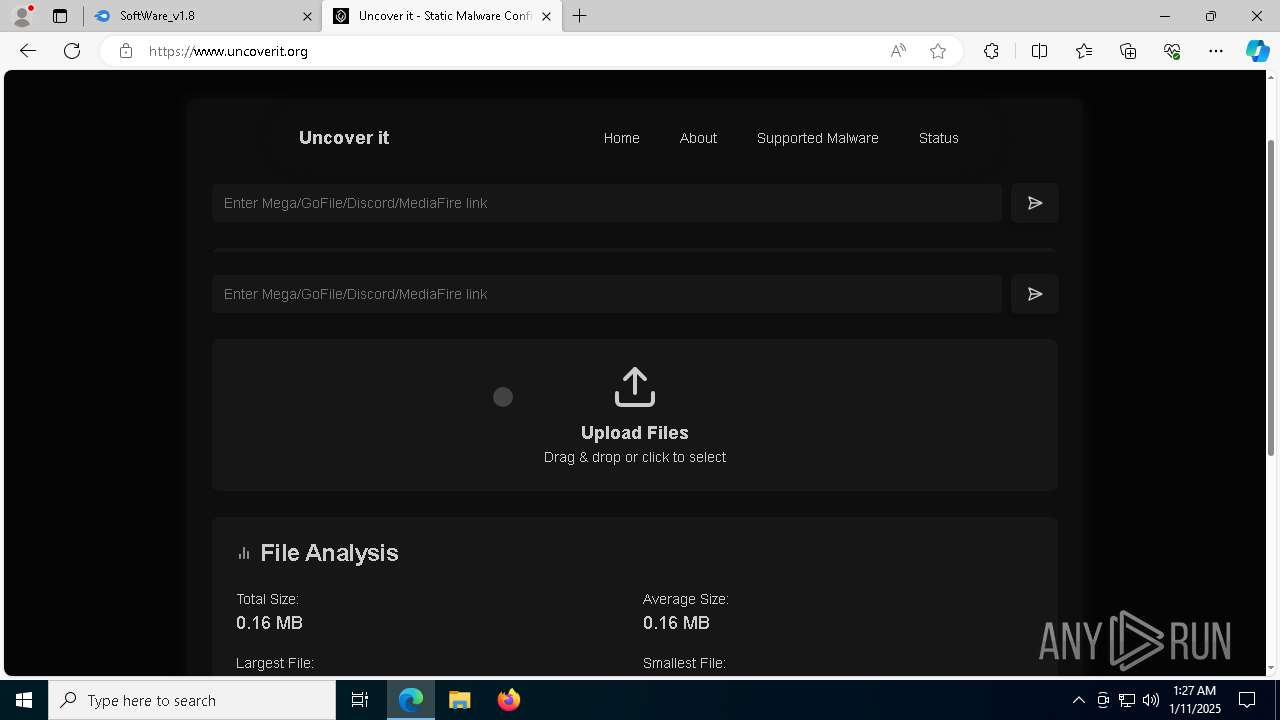
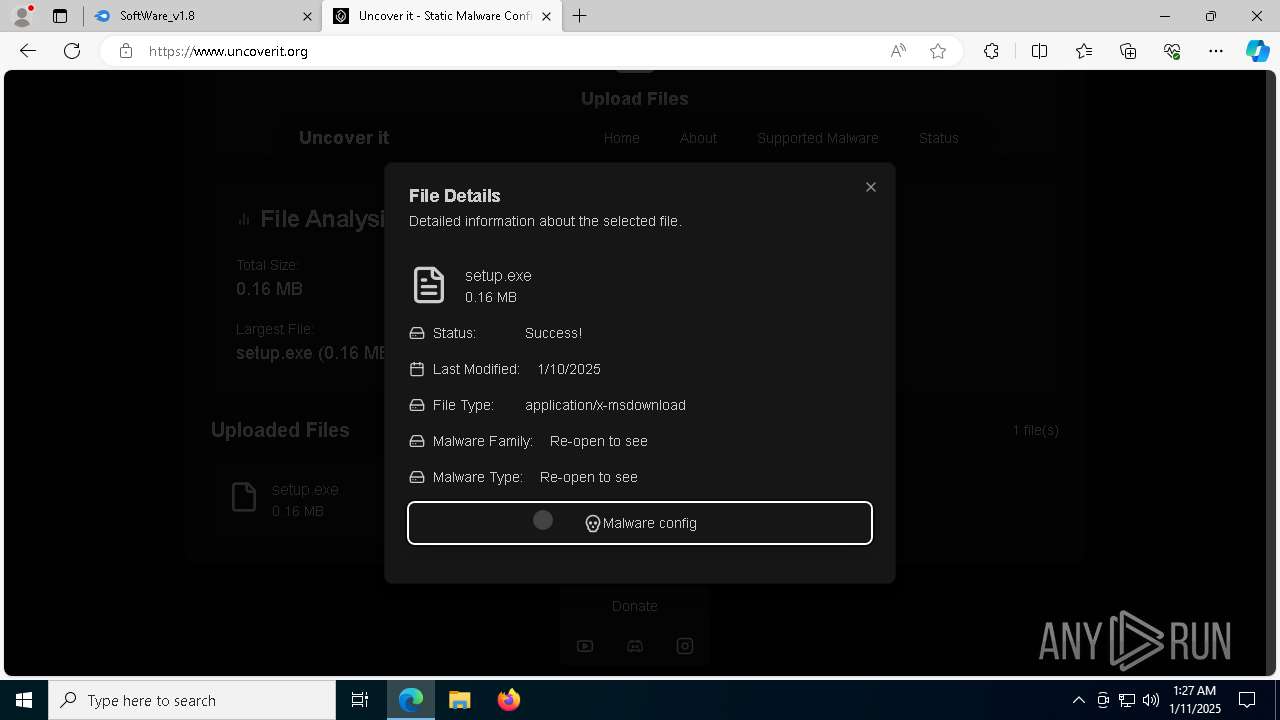
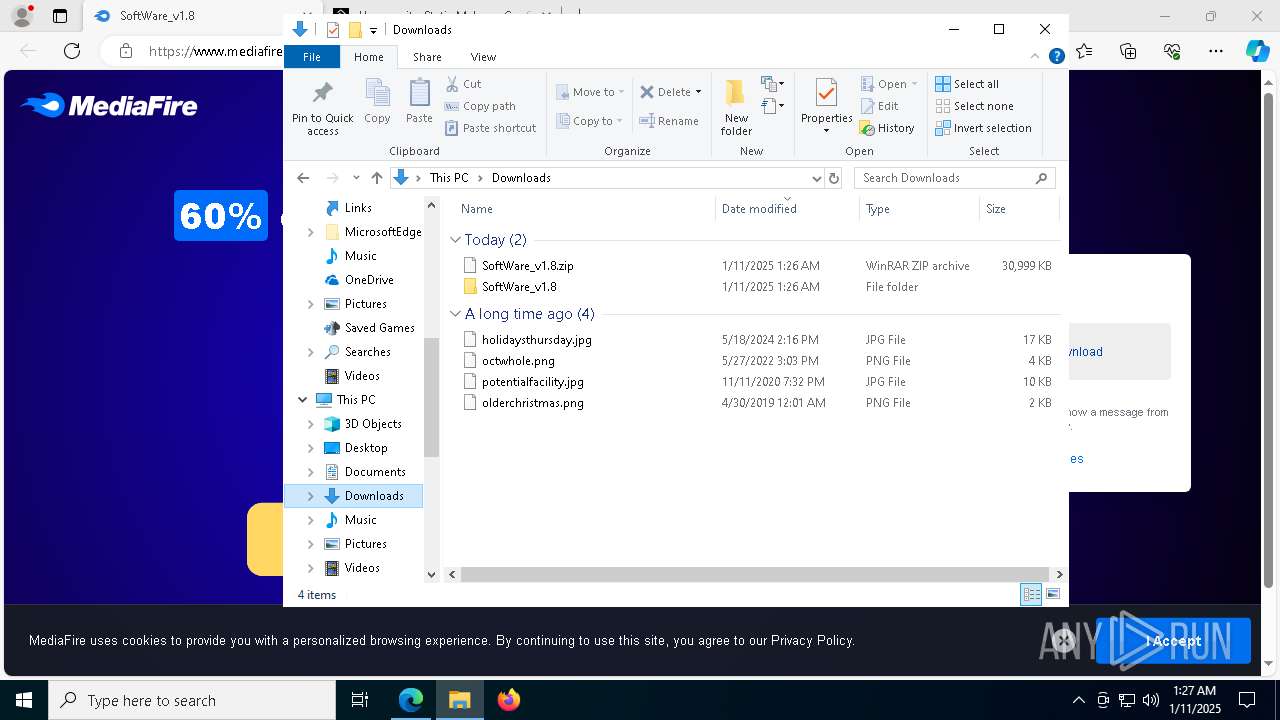
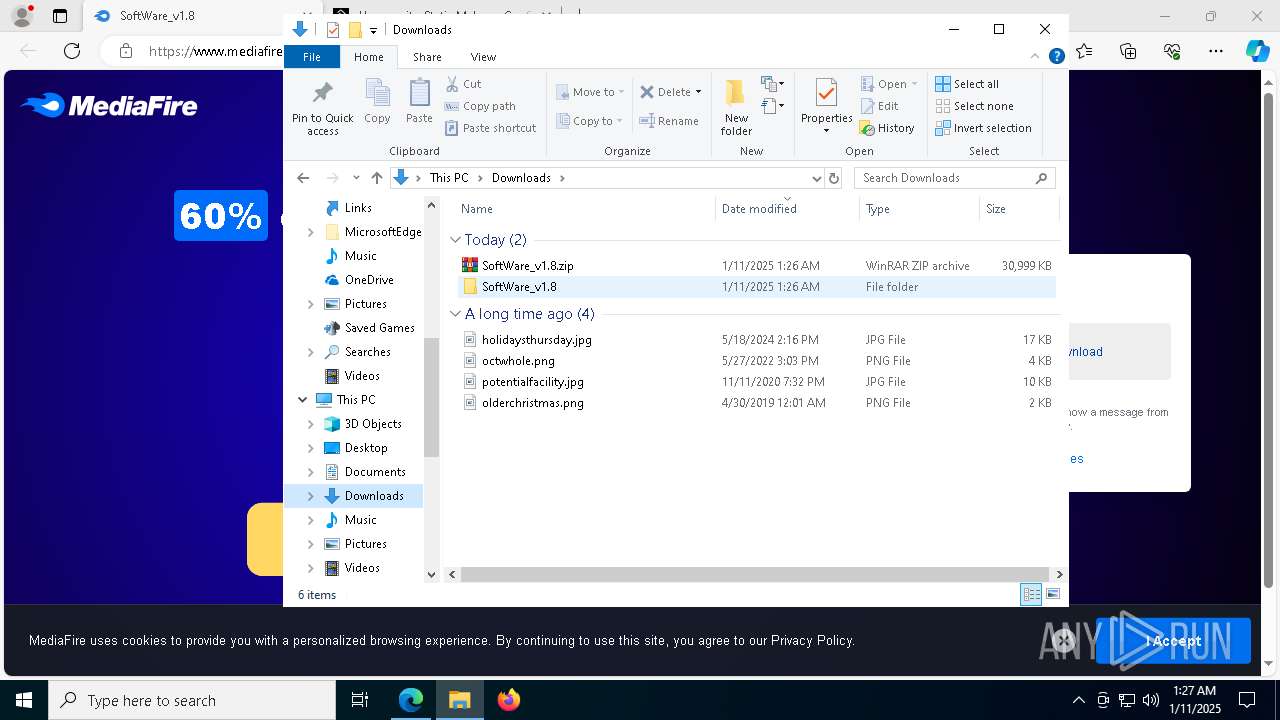
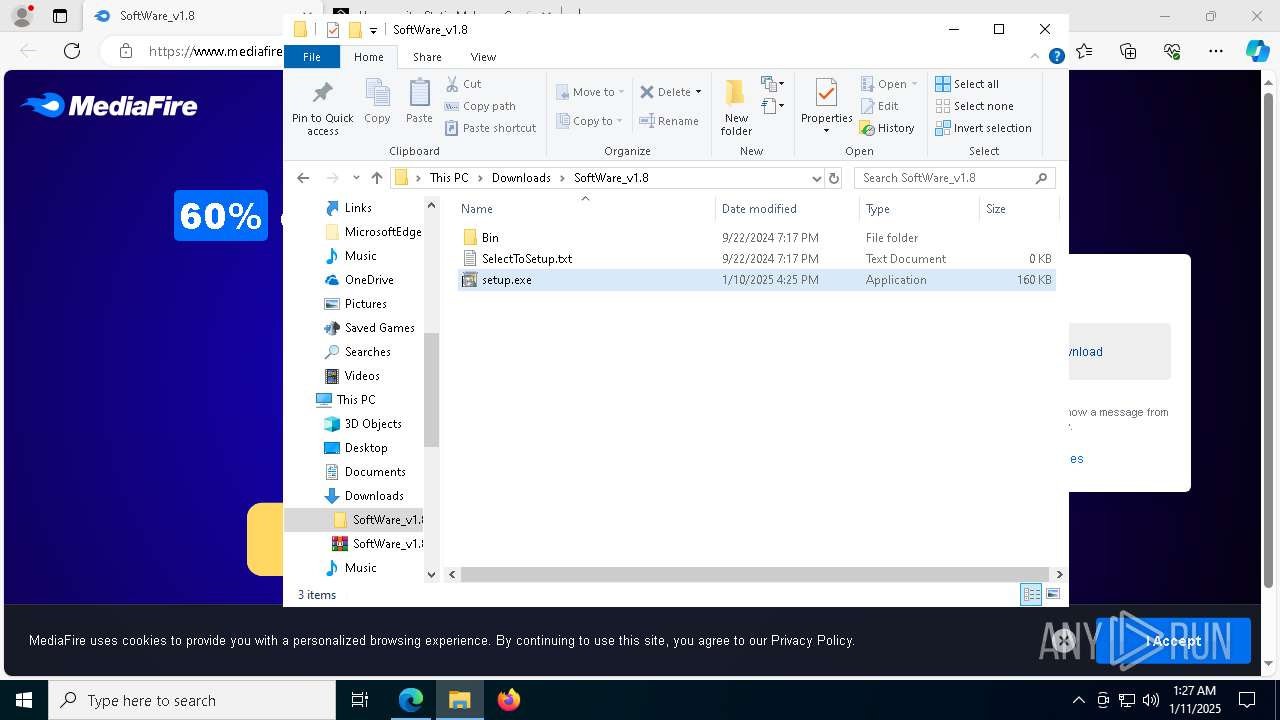
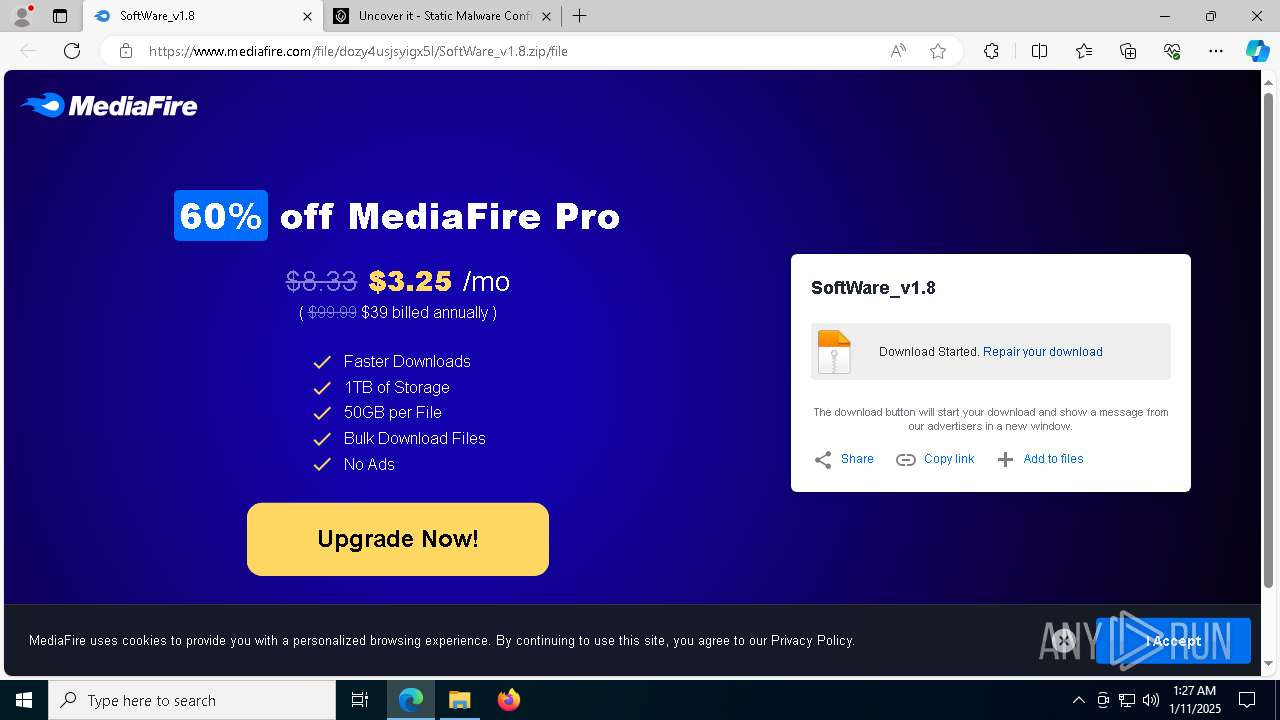
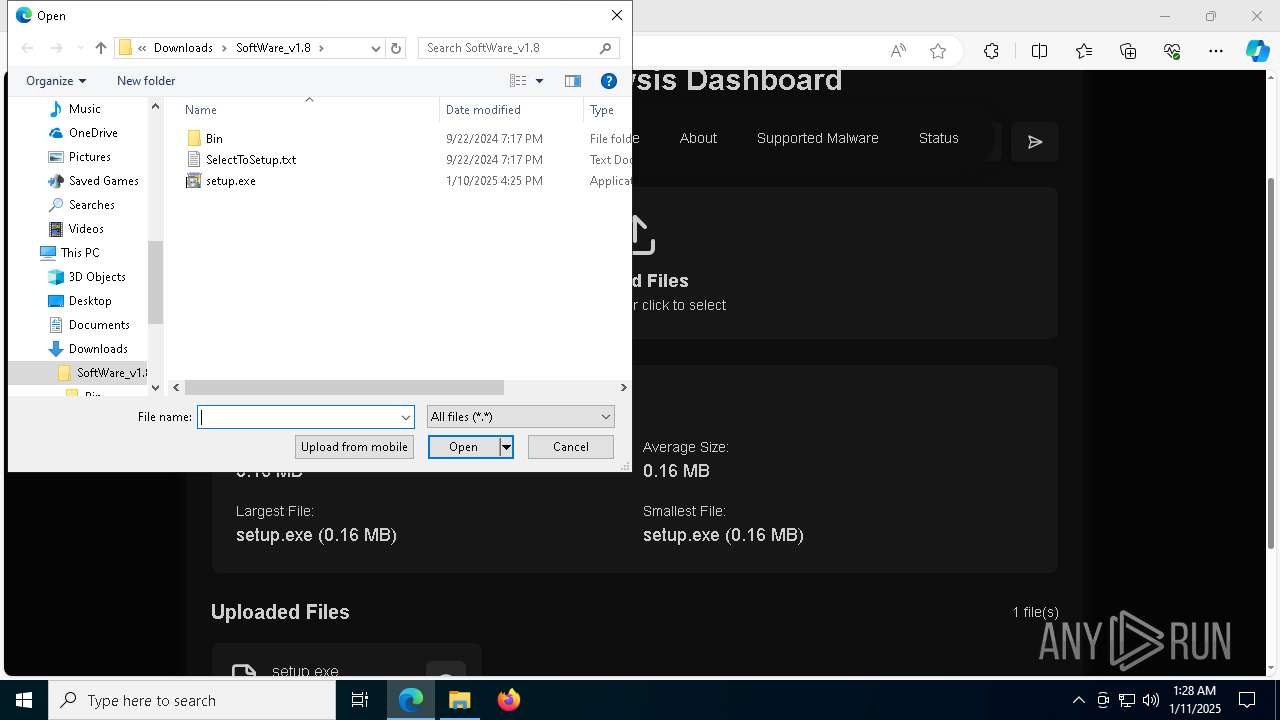
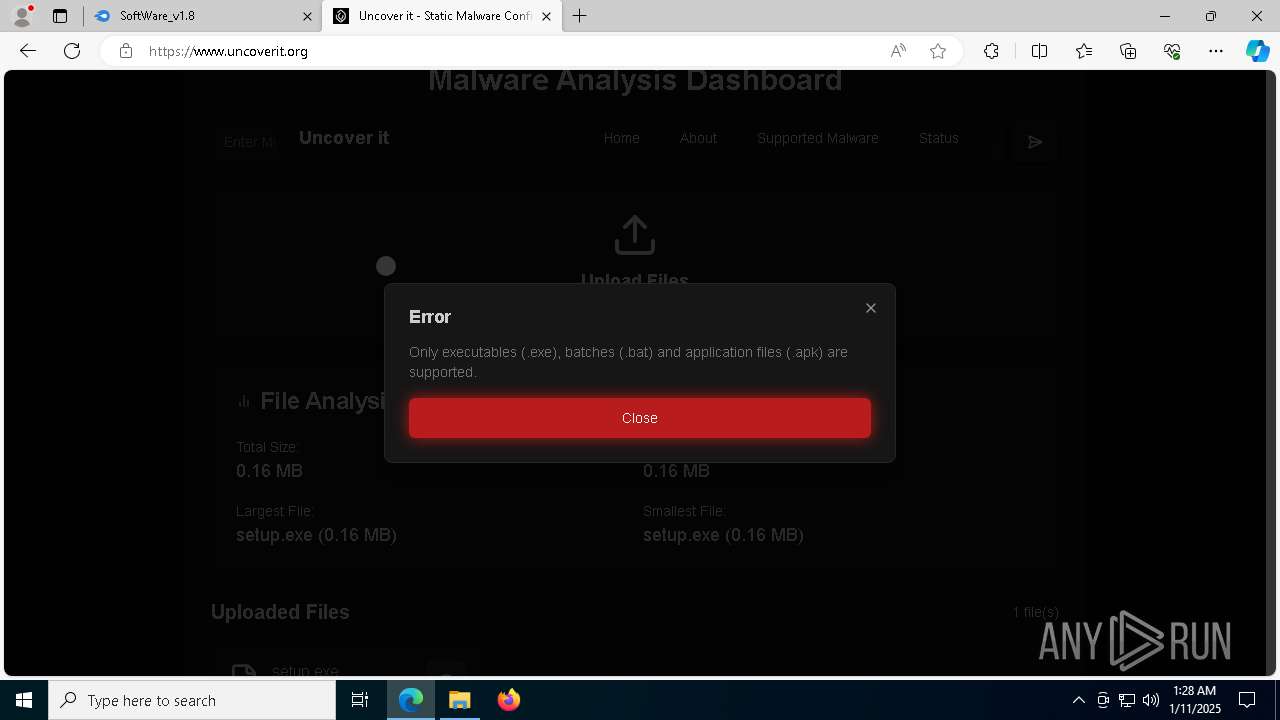
| URL: | https://www.mediafire.com/file/dozy4usjsyigx5l/SoftWare_v1.8.zip/file |
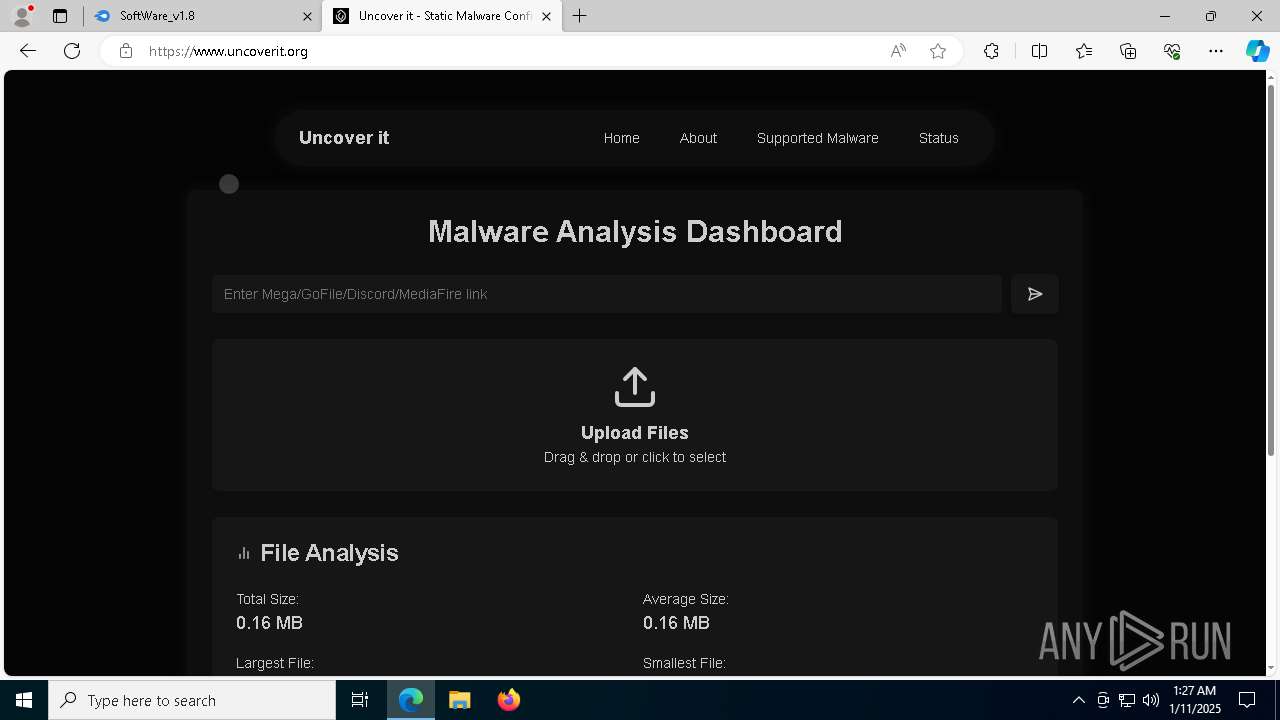
| Full analysis: | https://app.any.run/tasks/d1363067-467f-44a4-af22-ca2d9bb218e8 |
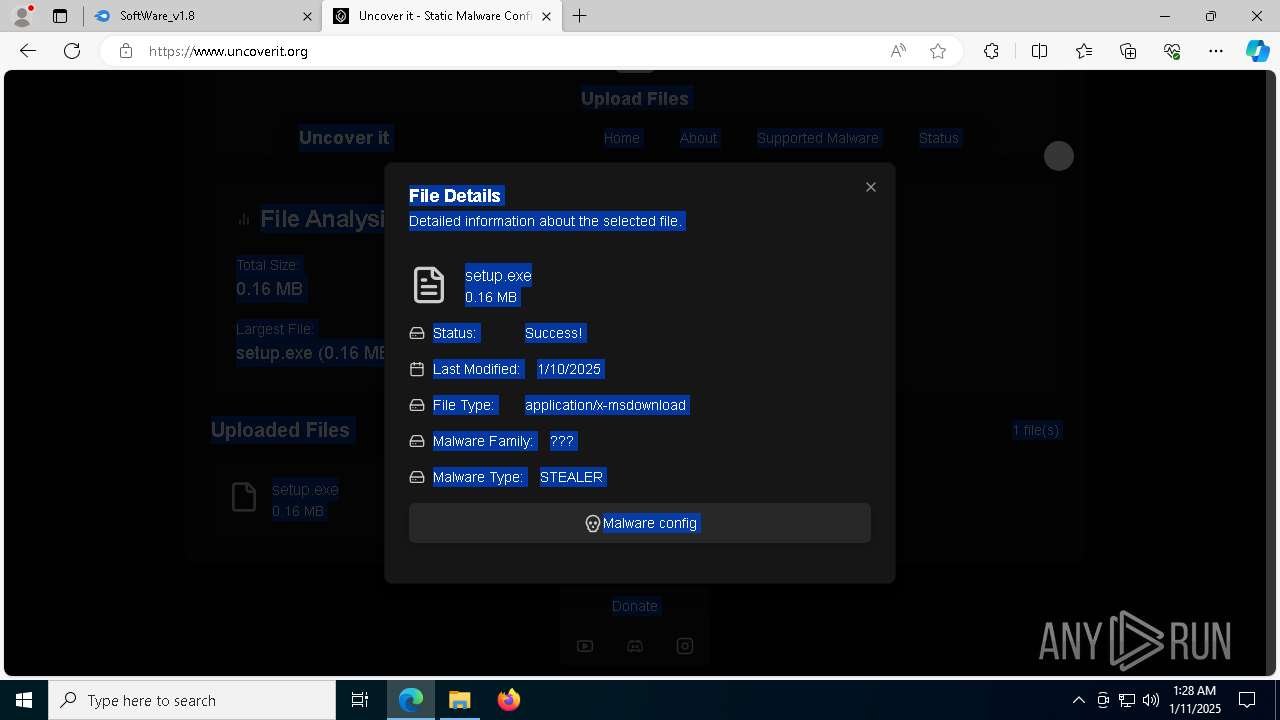
| Verdict: | Malicious activity |
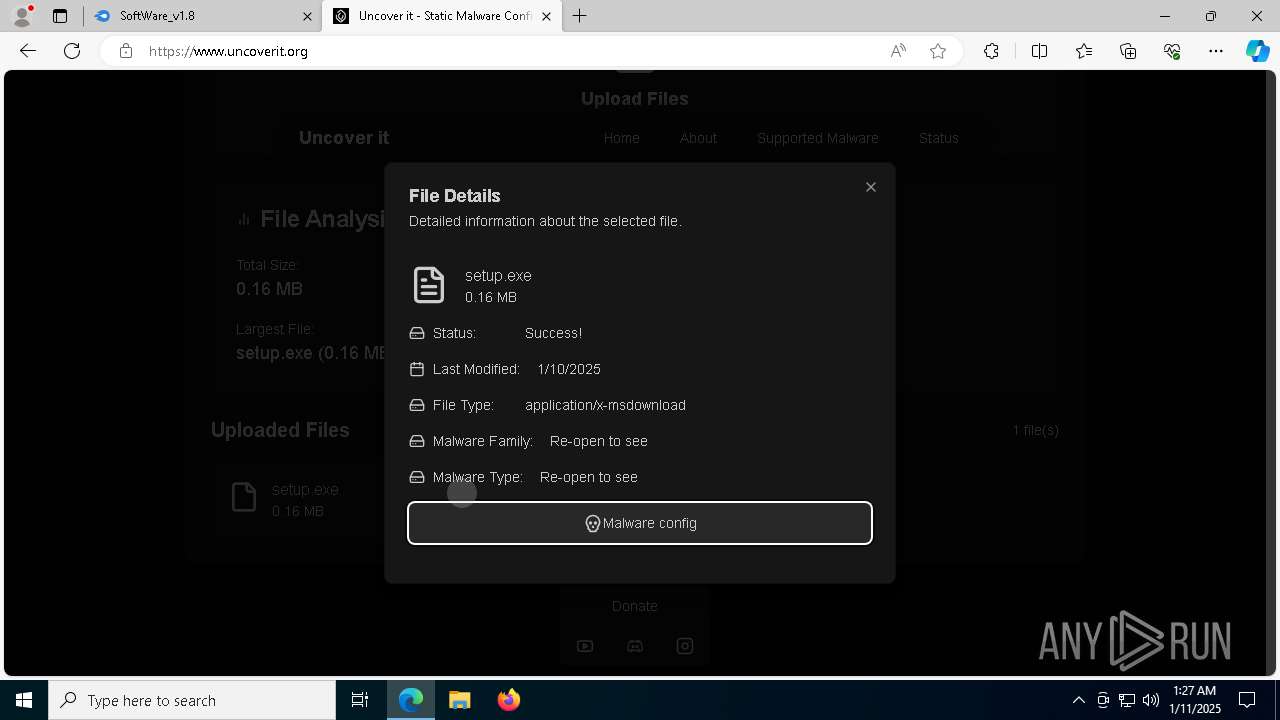
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
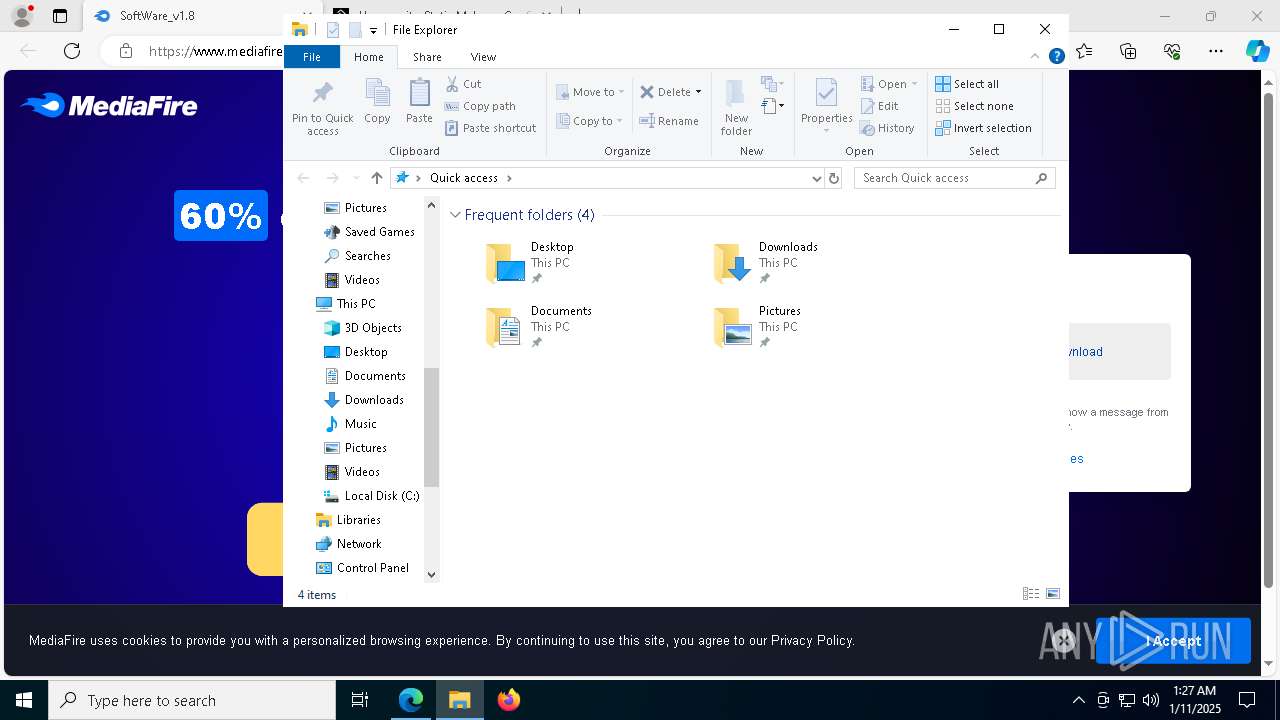
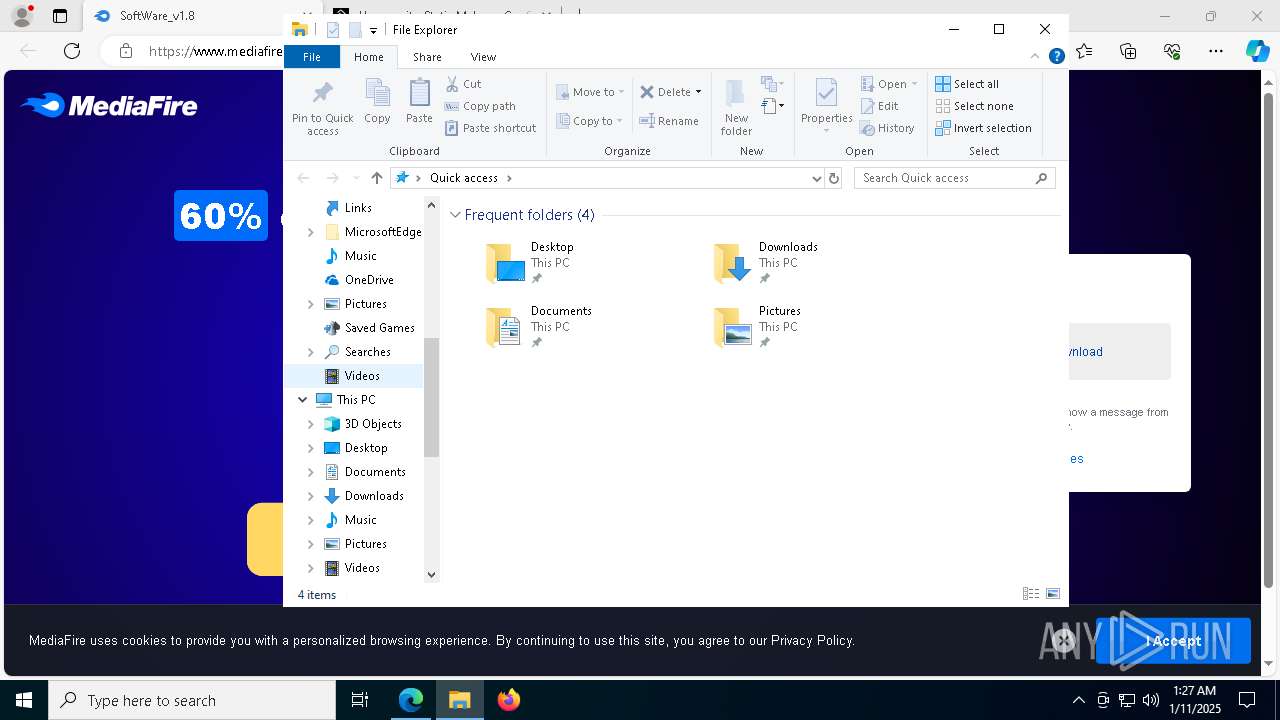
| Analysis date: | January 11, 2025, 01:26:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
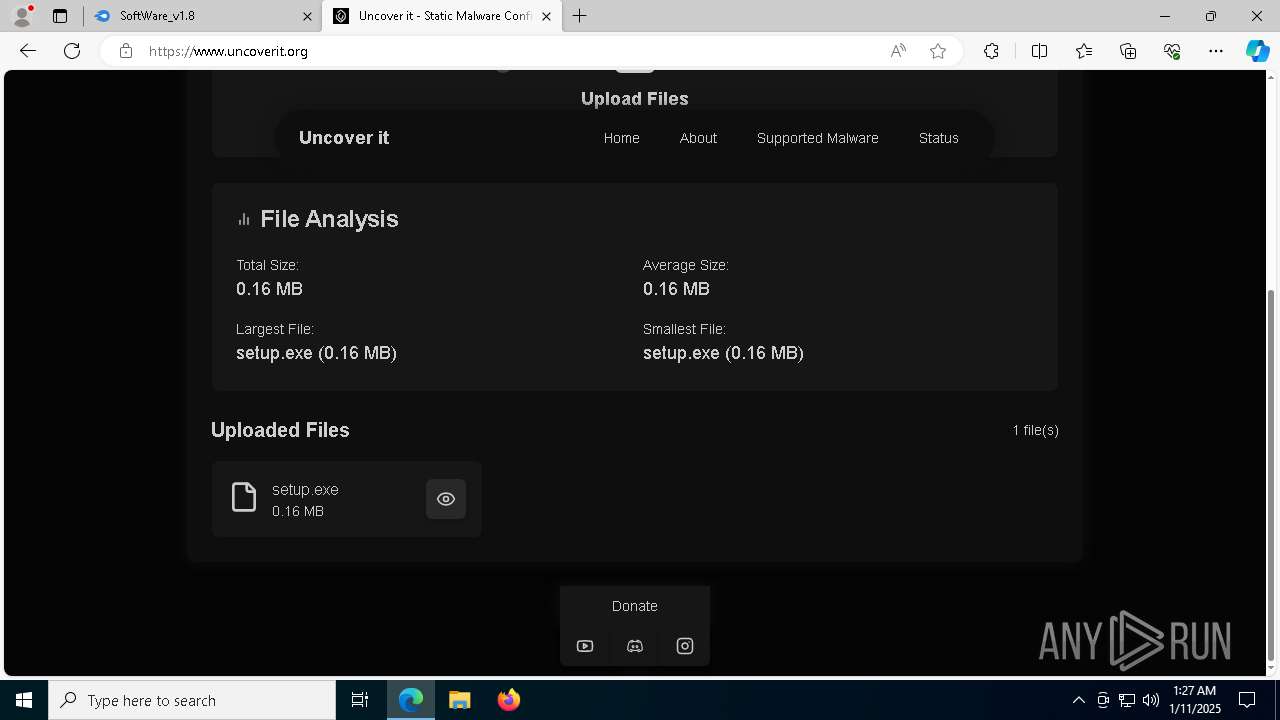
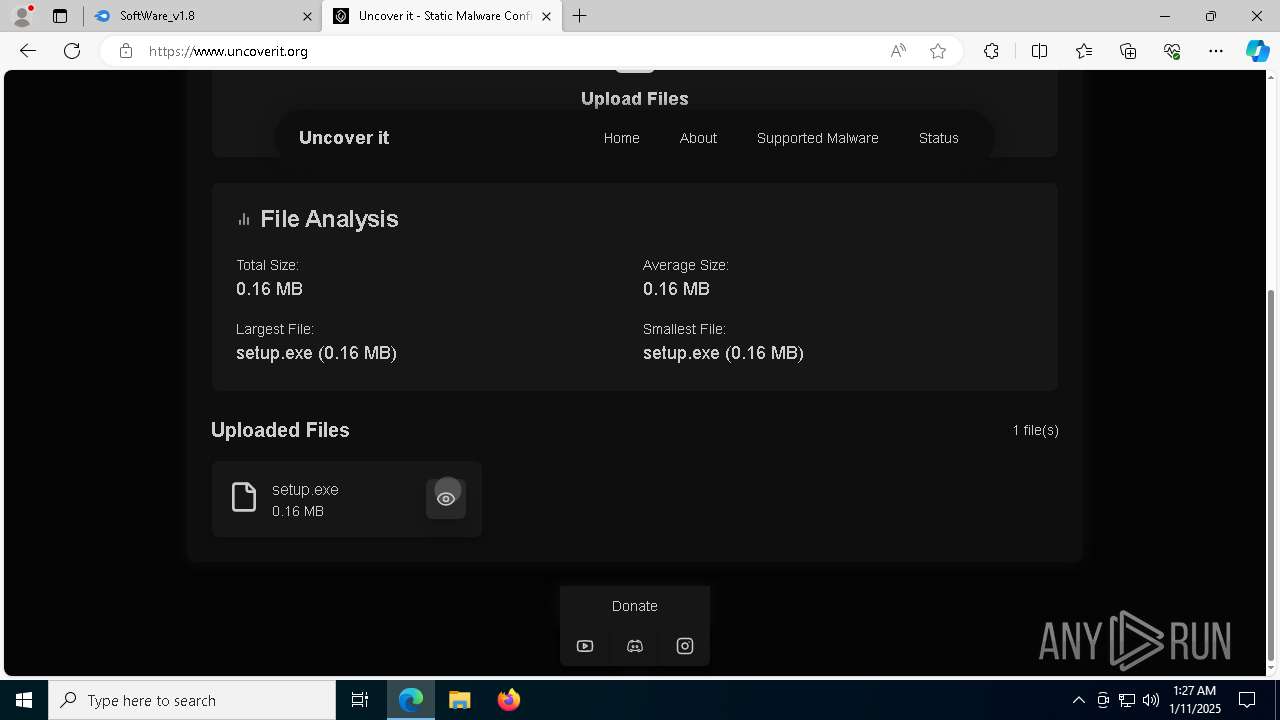
| MD5: | 00CE9D0ACB92C337C4BE64557AECF1A9 |
| SHA1: | 7D62AD51BF5C9F234E141F5A2FA64074E8F26B39 |
| SHA256: | 47F9346D12198A0A4FA88AD43185A41B6BB6A0DE49663C1D9AFD4A19F06984C8 |
| SSDEEP: | 3:N8DSLw3eGUoyWTMeQEtDU/1r:2OLw3eGWIMPgUJ |
MALICIOUS
LUMMA has been detected (SURICATA)
- msedge.exe (PID: 6456)
Run PowerShell with an invisible window
- powershell.exe (PID: 7536)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7508)
Stego campaign has been detected
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Changes powershell execution policy
- wscript.exe (PID: 3080)
- powershell.exe (PID: 7536)
- wscript.exe (PID: 2800)
- powershell.exe (PID: 6256)
- wscript.exe (PID: 2220)
- powershell.exe (PID: 7996)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
LUMMA mutex has been found
- MSBuild.exe (PID: 6672)
- MSBuild.exe (PID: 6956)
- MSBuild.exe (PID: 7624)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 6956)
- MSBuild.exe (PID: 6672)
- MSBuild.exe (PID: 7624)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 6672)
- MSBuild.exe (PID: 6956)
- MSBuild.exe (PID: 7624)
SUSPICIOUS
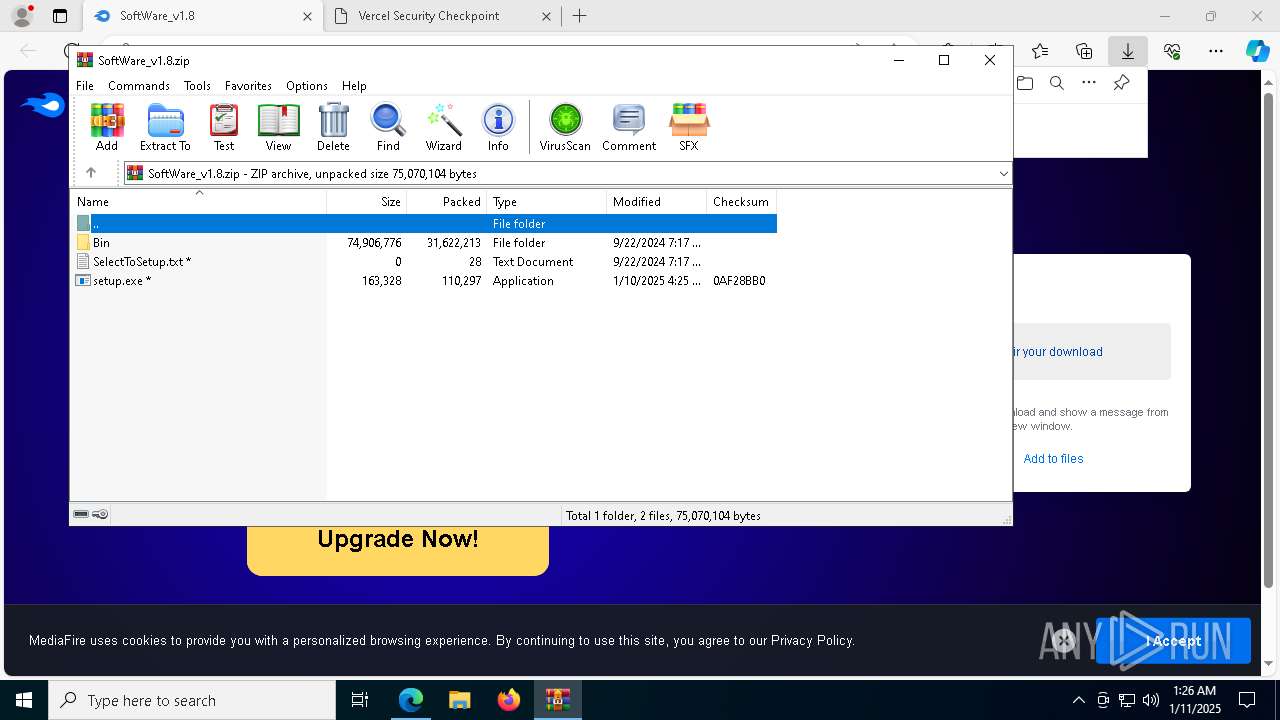
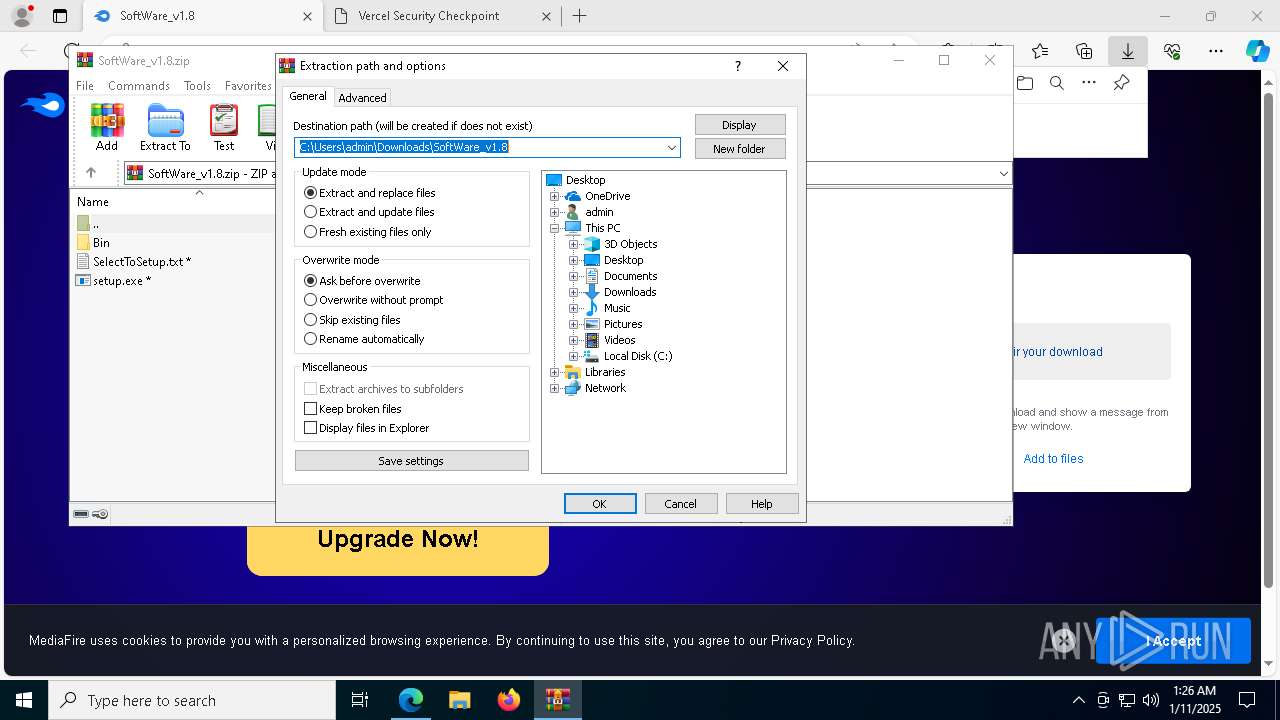
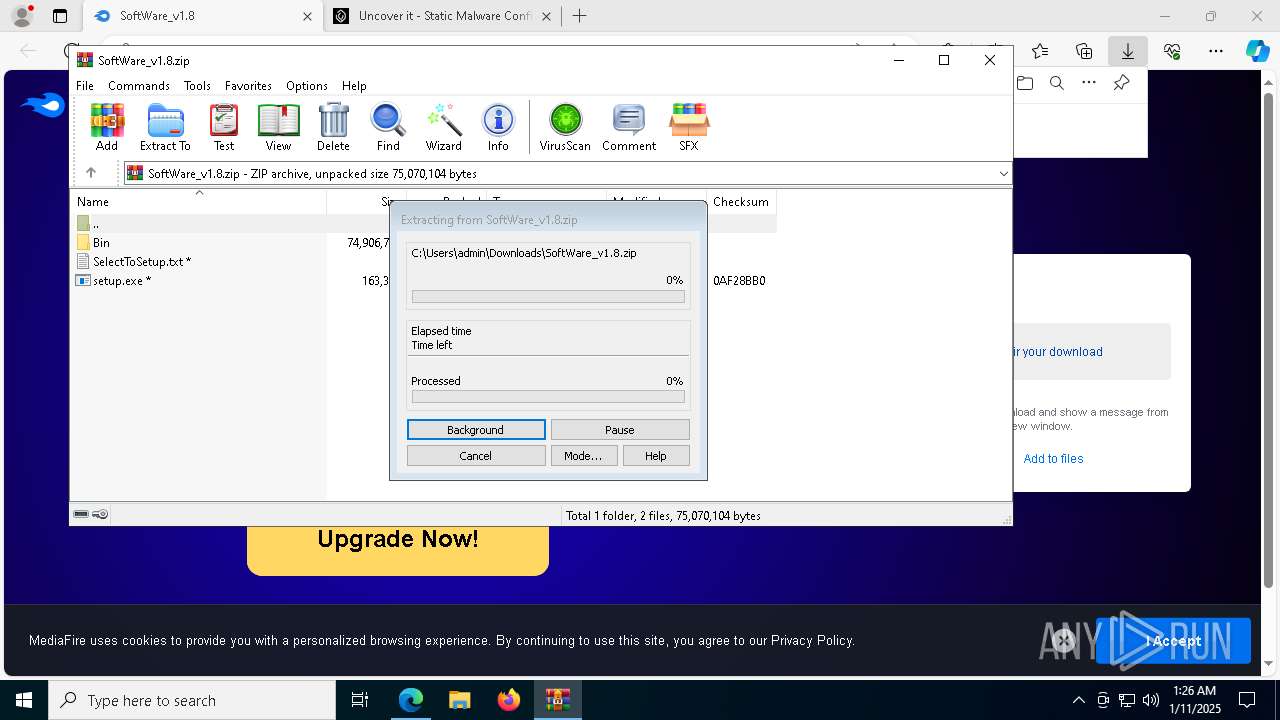
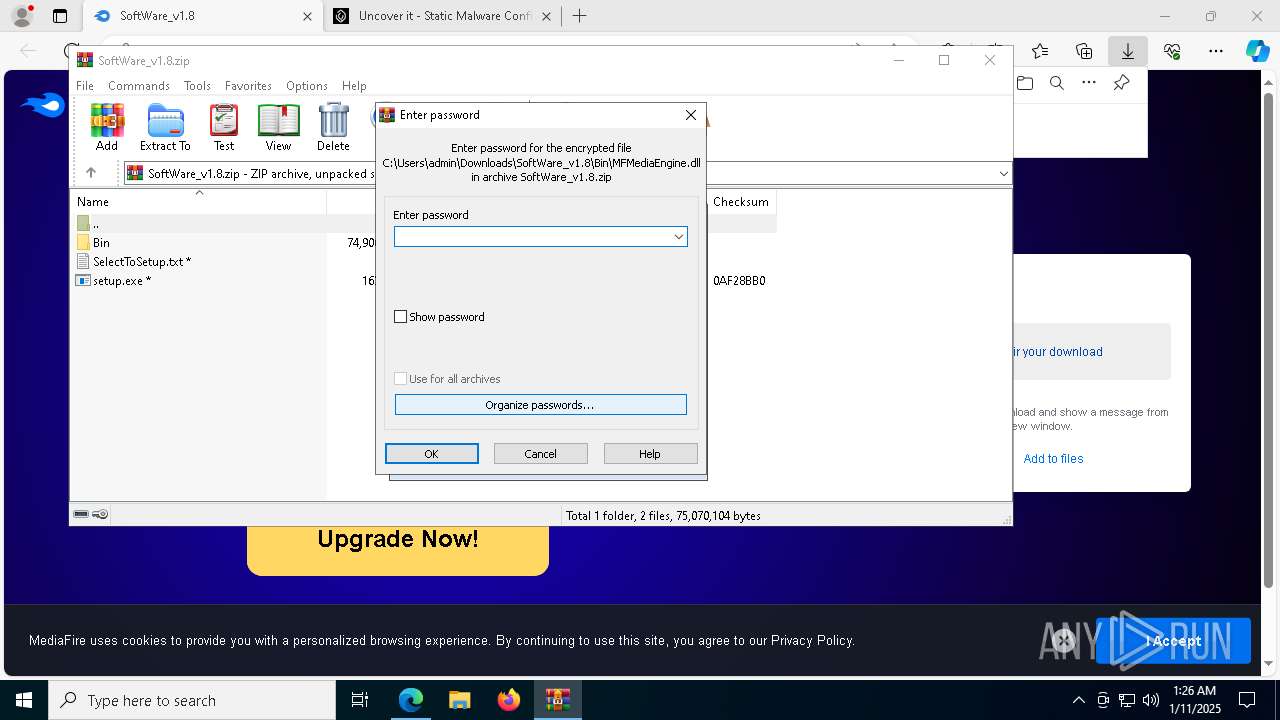
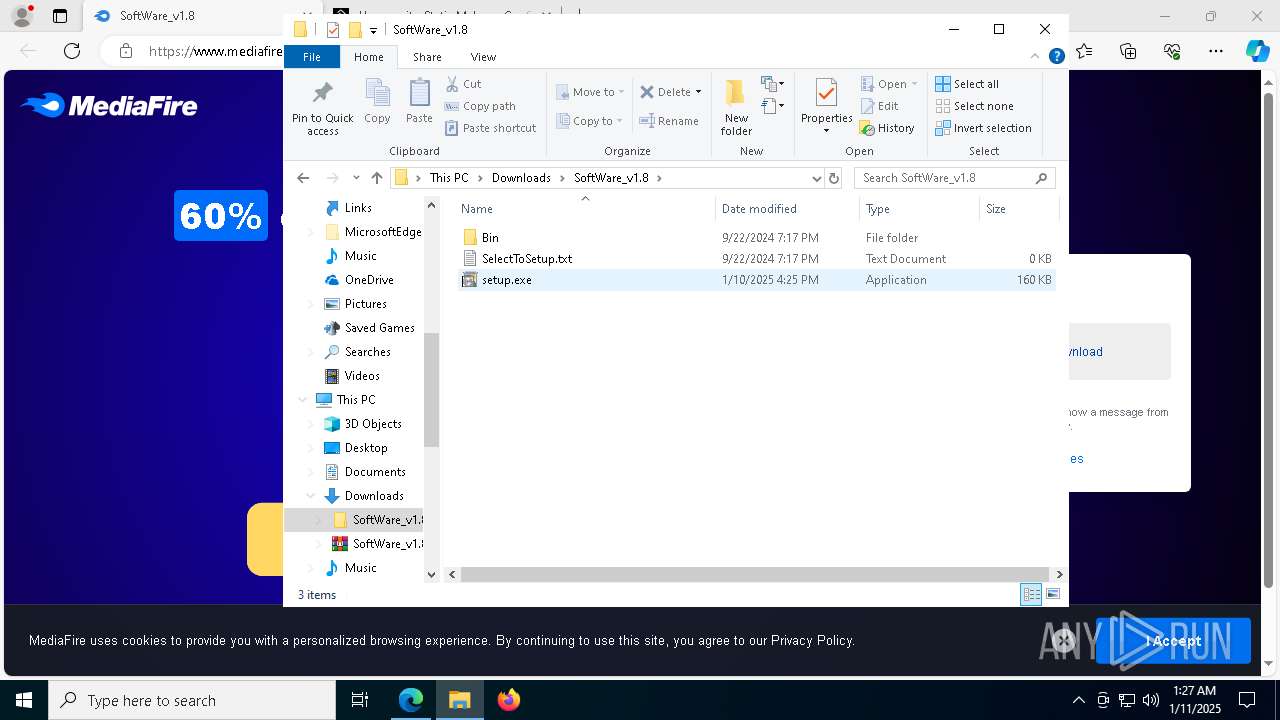
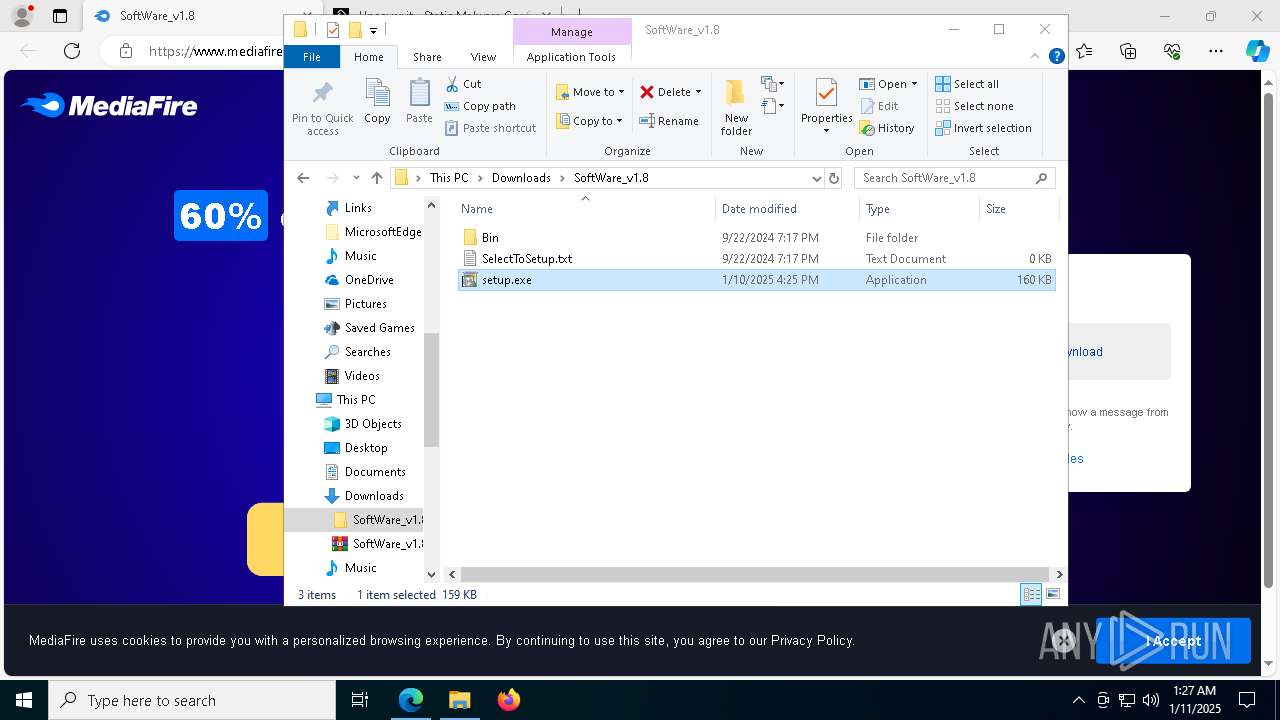
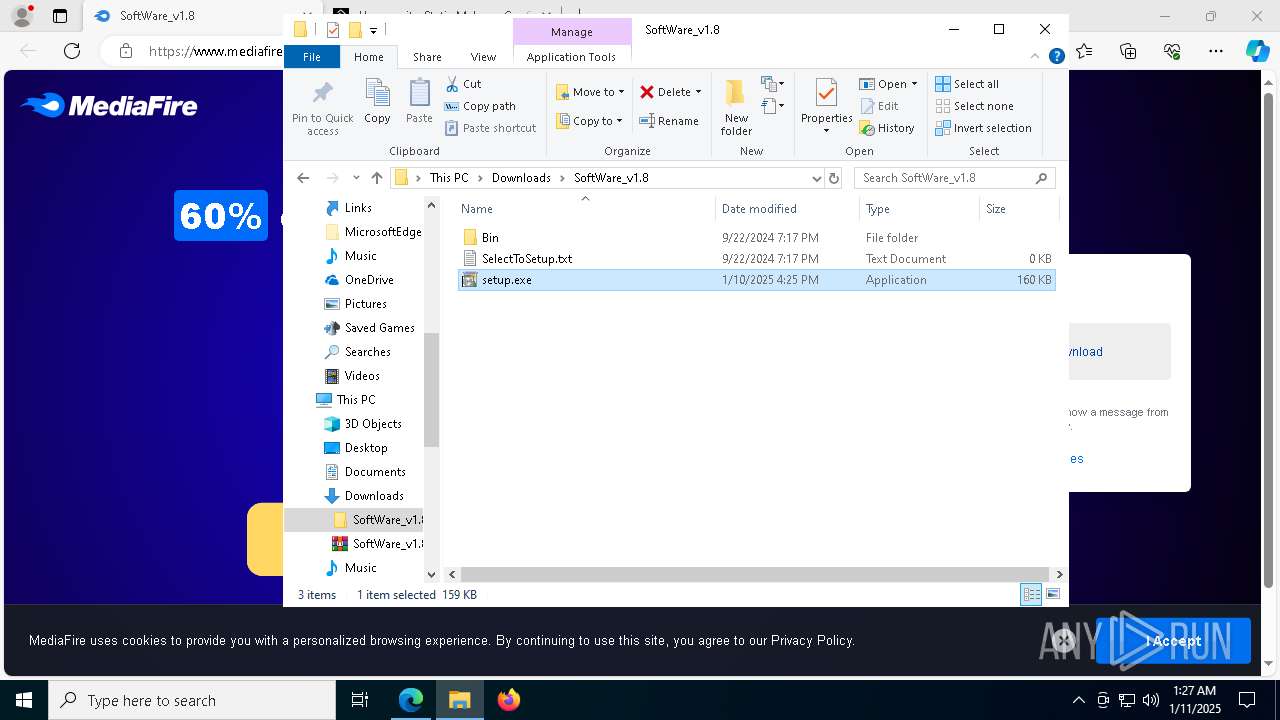
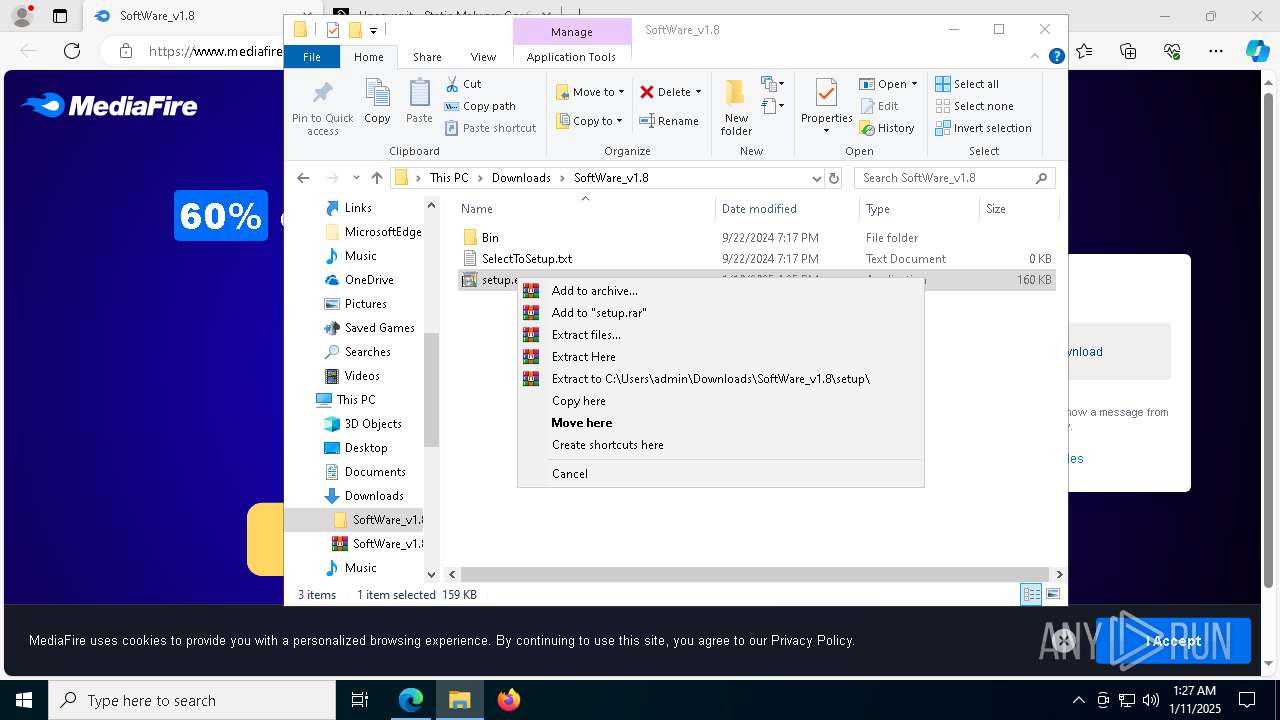
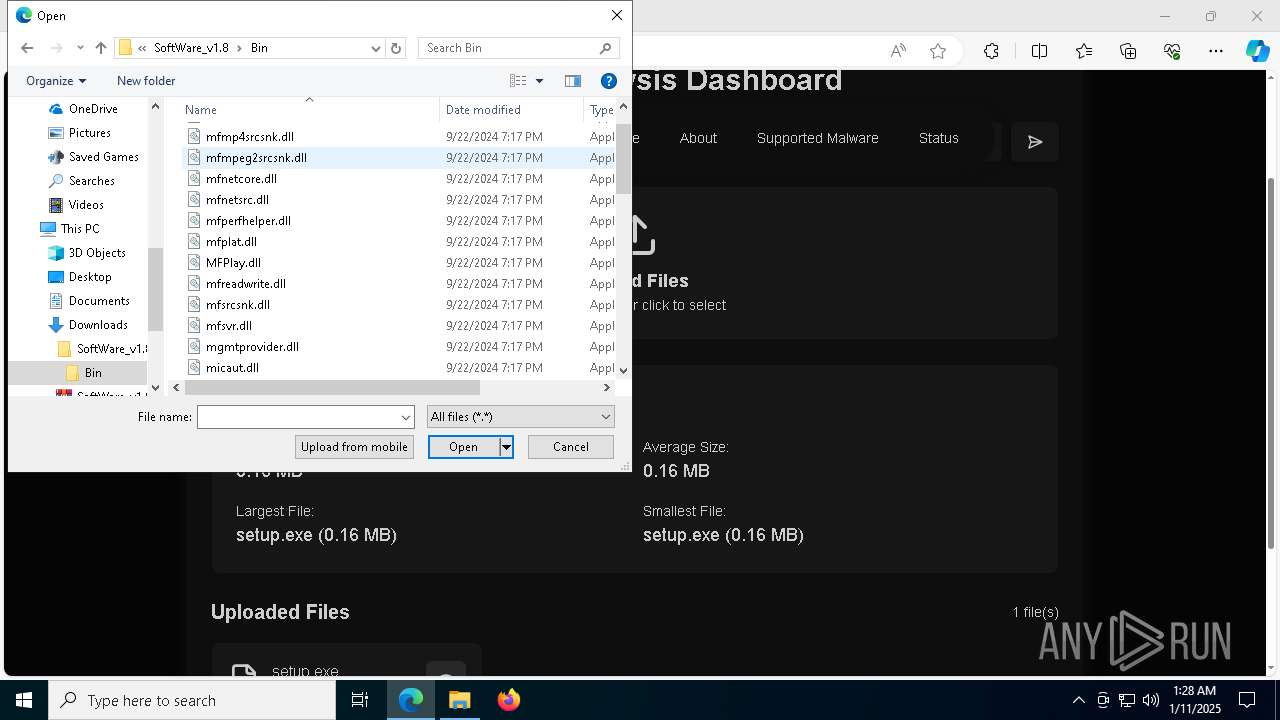
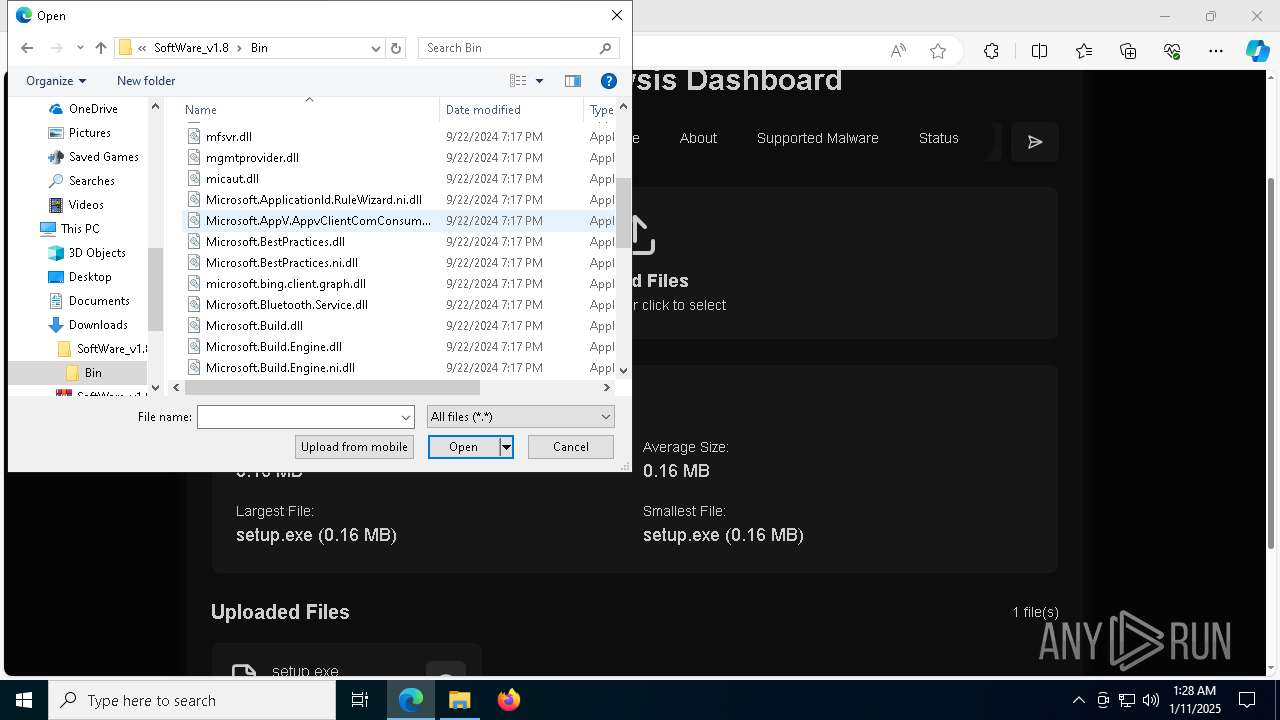
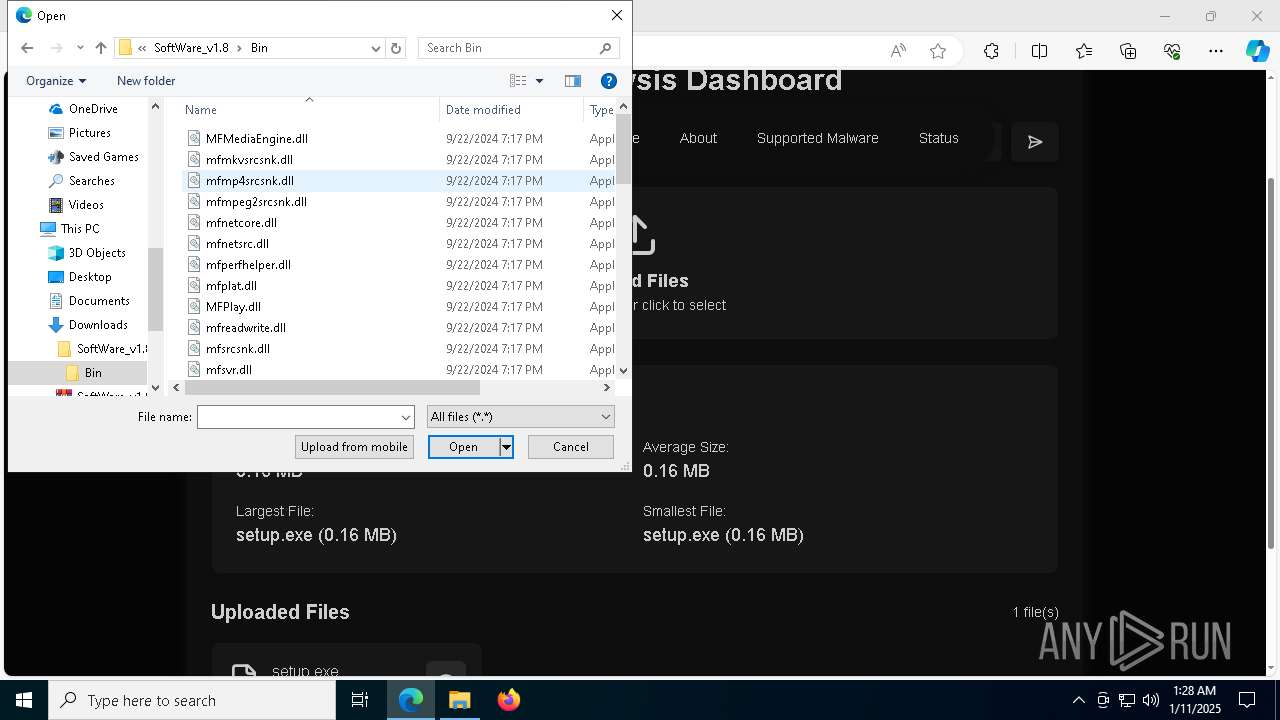
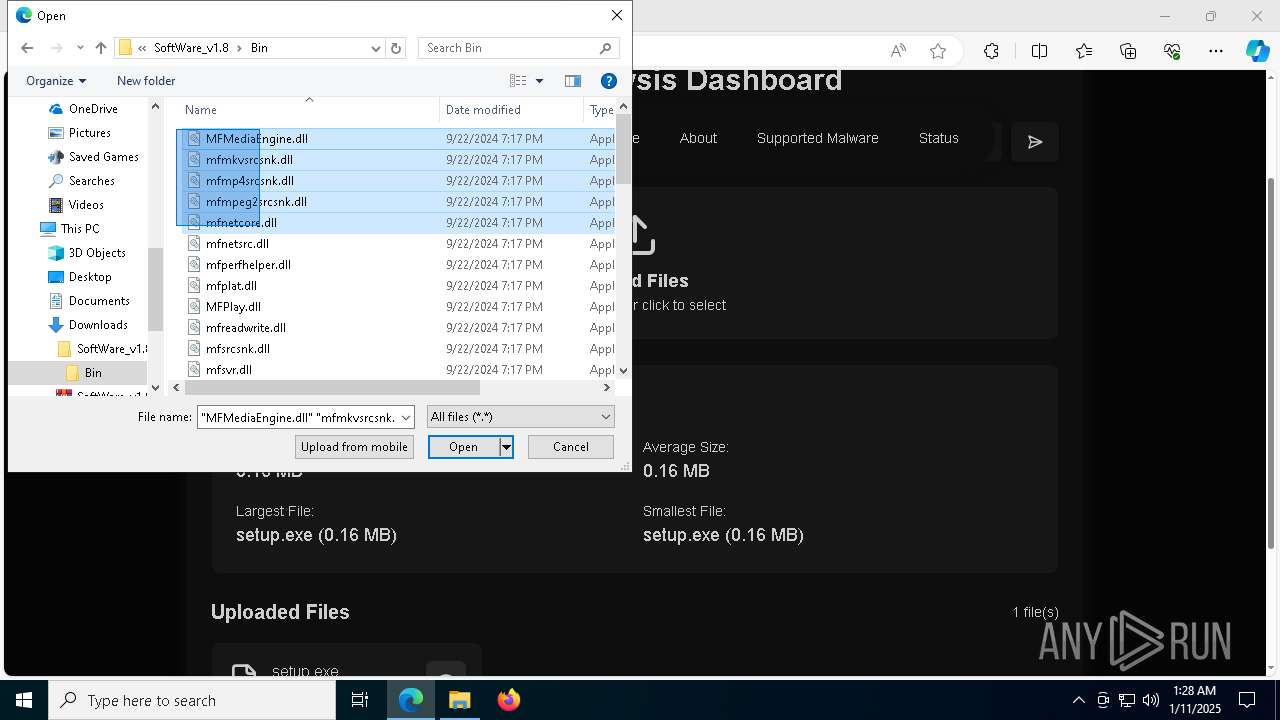
Process drops legitimate windows executable
- WinRAR.exe (PID: 3092)
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 6456)
Starts CMD.EXE for commands execution
- setup.exe (PID: 7620)
- setup.exe (PID: 7484)
- setup.exe (PID: 7060)
The process executes VB scripts
- cmd.exe (PID: 5076)
- cmd.exe (PID: 1540)
- cmd.exe (PID: 7048)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3080)
- wscript.exe (PID: 2800)
- wscript.exe (PID: 2220)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 3080)
- wscript.exe (PID: 2800)
- wscript.exe (PID: 2220)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 3080)
- wscript.exe (PID: 2800)
- wscript.exe (PID: 2220)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 3080)
- powershell.exe (PID: 7536)
- wscript.exe (PID: 2800)
- powershell.exe (PID: 6256)
- wscript.exe (PID: 2220)
- powershell.exe (PID: 7996)
Probably download files using WebClient
- powershell.exe (PID: 7536)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 7996)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7508)
Application launched itself
- powershell.exe (PID: 7536)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 7996)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
INFO
Reads the computer name
- identity_helper.exe (PID: 7876)
- setup.exe (PID: 7620)
- setup.exe (PID: 7484)
- MSBuild.exe (PID: 6672)
- MSBuild.exe (PID: 6956)
- setup.exe (PID: 7060)
- MSBuild.exe (PID: 7624)
The process uses the downloaded file
- WinRAR.exe (PID: 3092)
- msedge.exe (PID: 3840)
- msedge.exe (PID: 7996)
- cmd.exe (PID: 5076)
- wscript.exe (PID: 3080)
- cmd.exe (PID: 1540)
- wscript.exe (PID: 2800)
- cmd.exe (PID: 7048)
- wscript.exe (PID: 2220)
Checks supported languages
- identity_helper.exe (PID: 7876)
- setup.exe (PID: 7620)
- setup.exe (PID: 7484)
- MSBuild.exe (PID: 6672)
- MSBuild.exe (PID: 6956)
- setup.exe (PID: 7060)
- MSBuild.exe (PID: 7624)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3092)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3840)
The sample compiled with english language support
- WinRAR.exe (PID: 3092)
Reads Environment values
- identity_helper.exe (PID: 7876)
The sample compiled with russian language support
- WinRAR.exe (PID: 3092)
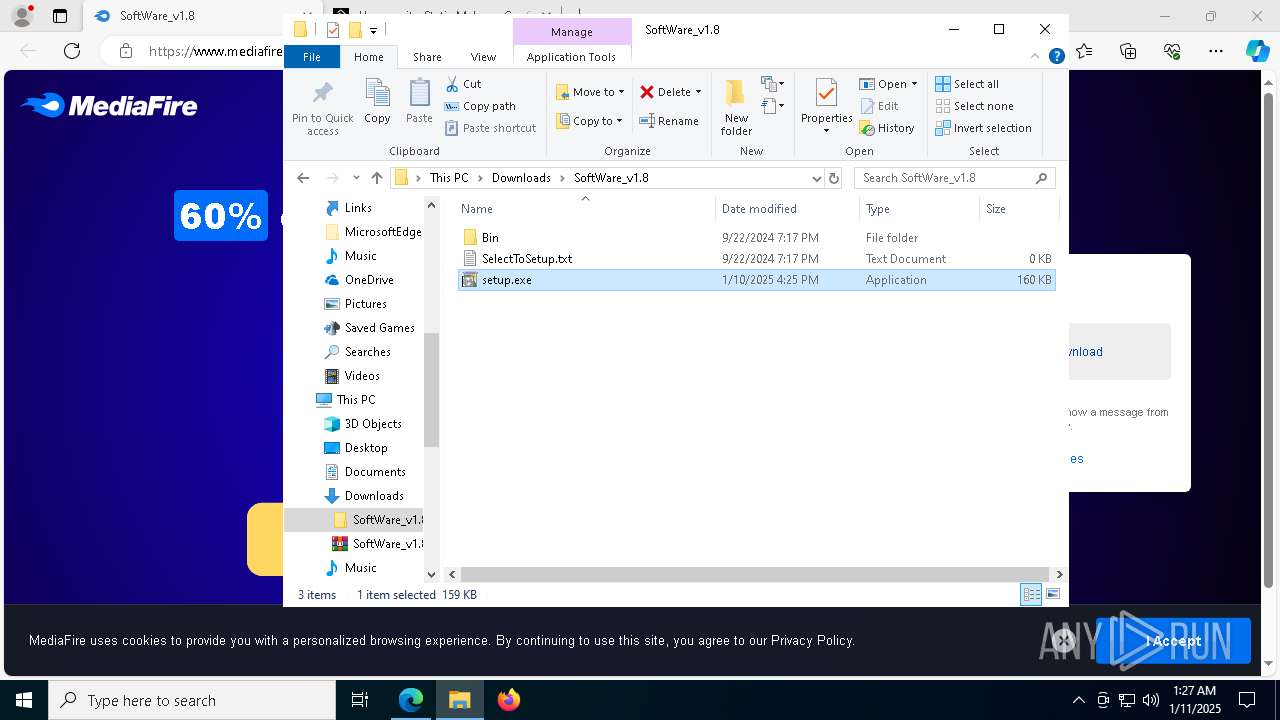
Manual execution by a user
- setup.exe (PID: 7620)
- setup.exe (PID: 7484)
- setup.exe (PID: 7060)
Create files in a temporary directory
- setup.exe (PID: 7620)
- setup.exe (PID: 7484)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- setup.exe (PID: 7060)
- powershell.exe (PID: 7508)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 7996)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 7996)
Reads security settings of Internet Explorer
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 7996)
Application launched itself
- msedge.exe (PID: 3840)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Checks proxy server information
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Disables trace logs
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Reads the software policy settings
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- MSBuild.exe (PID: 6672)
- MSBuild.exe (PID: 6956)
- powershell.exe (PID: 7508)
- MSBuild.exe (PID: 7624)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7864)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
214
Monitored processes
82
Malicious processes
20
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5080 --field-trial-handle=2376,i,6346901677913980205,240811632932688904,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5936 --field-trial-handle=2376,i,6346901677913980205,240811632932688904,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4228 --field-trial-handle=2376,i,6346901677913980205,240811632932688904,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1540 | cmd.exe /c 678165f2922ef.vbs | C:\Windows\System32\cmd.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5504 --field-trial-handle=2376,i,6346901677913980205,240811632932688904,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5752 --field-trial-handle=2376,i,6346901677913980205,240811632932688904,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2220 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\IXP001.TMP\678165f2922ef.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2800 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\678165f2922ef.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
53 870
Read events
53 619
Write events
231
Delete events
20
Modification events
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 639F0961FA892F00 | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 95671361FA892F00 | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C95E8DF-FB50-42C0-9C7E-D22A0D67D5AC} | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F8325C3D-31D3-4966-94D2-38377AF797D2} | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6B07DE61-5D4E-47E9-B327-9F7D4C5AEEFB} | |||
| (PID) Process: | (3840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E876097B-2370-4494-9475-4080EF094535} | |||
Executable files
83
Suspicious files
913
Text files
158
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1351bd.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1351bd.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1351cd.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1351cd.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1351dc.TMP | — | |
MD5:— | SHA256:— | |||
| 3840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
172
DNS requests
189
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1736939537&P2=404&P3=2&P4=a7CDcc6Okzi7EWTx5V1GlYikSJAUVaAqBbzjozTPMKBuIC979D1Z0x4NFTYr2mqrfSaCmL1PaerwRa5Upm4q3Q%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1736939537&P2=404&P3=2&P4=a7CDcc6Okzi7EWTx5V1GlYikSJAUVaAqBbzjozTPMKBuIC979D1Z0x4NFTYr2mqrfSaCmL1PaerwRa5Upm4q3Q%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1736939537&P2=404&P3=2&P4=a7CDcc6Okzi7EWTx5V1GlYikSJAUVaAqBbzjozTPMKBuIC979D1Z0x4NFTYr2mqrfSaCmL1PaerwRa5Upm4q3Q%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1736939537&P2=404&P3=2&P4=QkRXpP9hWQP7HnvKpsob5IqgDJVQ7v5X3UGe80l%2b%2bZBQaVCjbaWZjgR0lUXlL5wvEKtgdE6r8a1IhClKskqwFQ%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1736939537&P2=404&P3=2&P4=a7CDcc6Okzi7EWTx5V1GlYikSJAUVaAqBbzjozTPMKBuIC979D1Z0x4NFTYr2mqrfSaCmL1PaerwRa5Upm4q3Q%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1736939537&P2=404&P3=2&P4=QkRXpP9hWQP7HnvKpsob5IqgDJVQ7v5X3UGe80l%2b%2bZBQaVCjbaWZjgR0lUXlL5wvEKtgdE6r8a1IhClKskqwFQ%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8008 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1736939537&P2=404&P3=2&P4=a7CDcc6Okzi7EWTx5V1GlYikSJAUVaAqBbzjozTPMKBuIC979D1Z0x4NFTYr2mqrfSaCmL1PaerwRa5Upm4q3Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3508 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6456 | msedge.exe | 104.17.151.117:443 | www.mediafire.com | — | — | shared |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6456 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6456 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6456 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6456 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
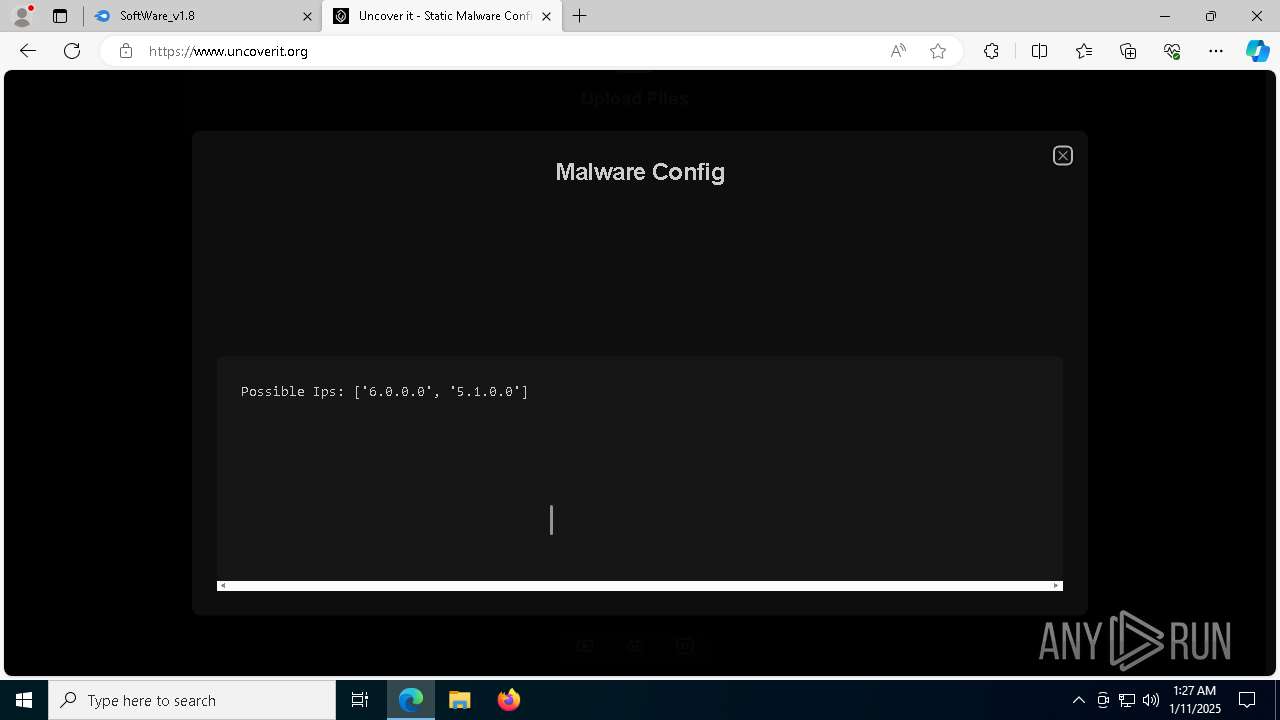
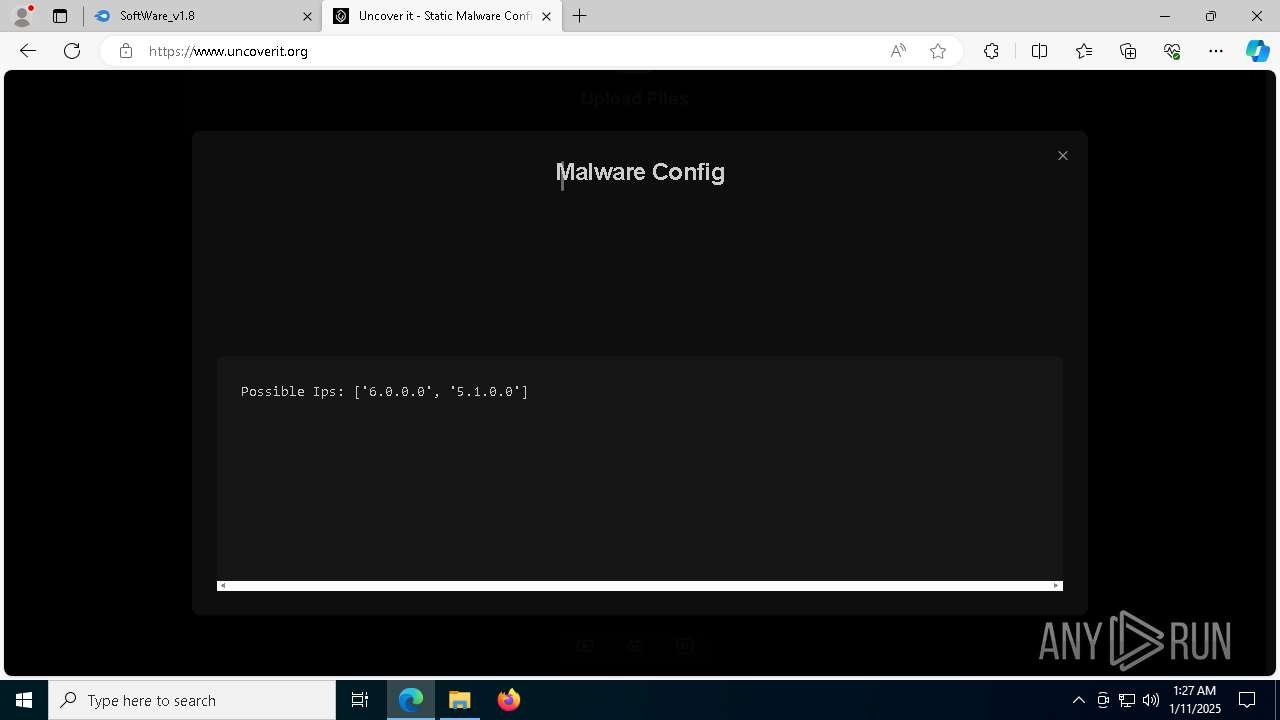
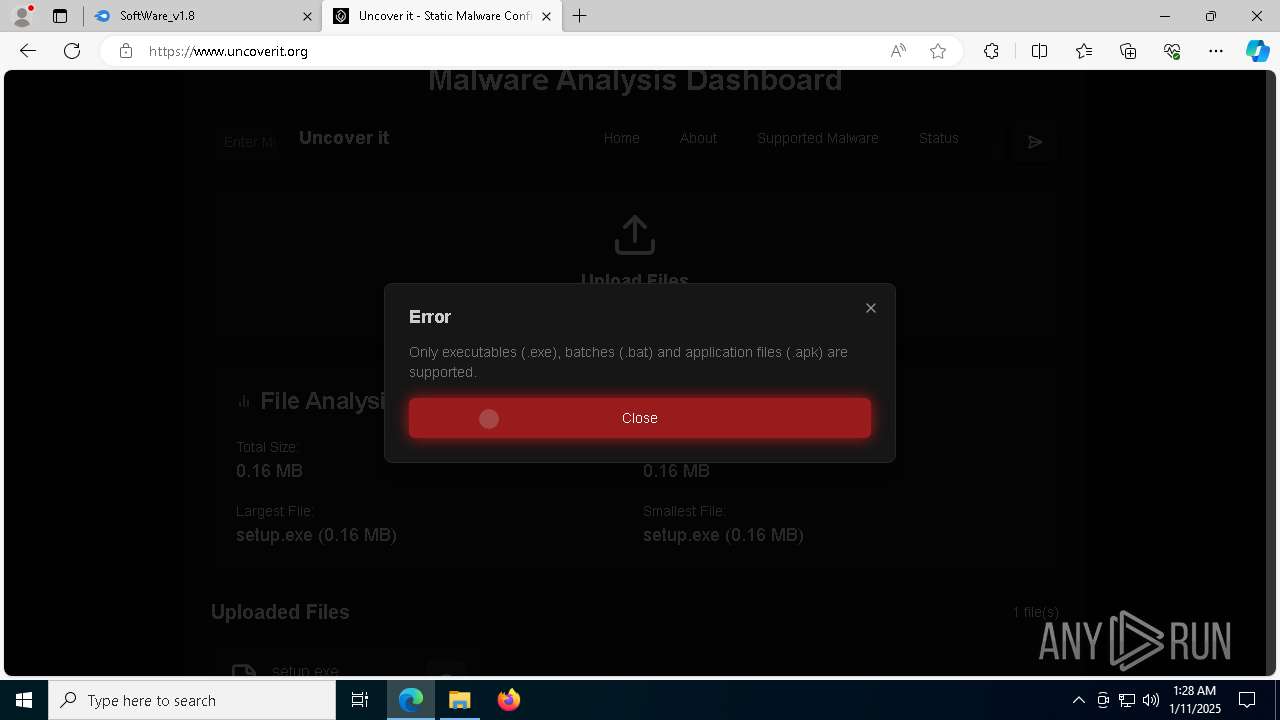
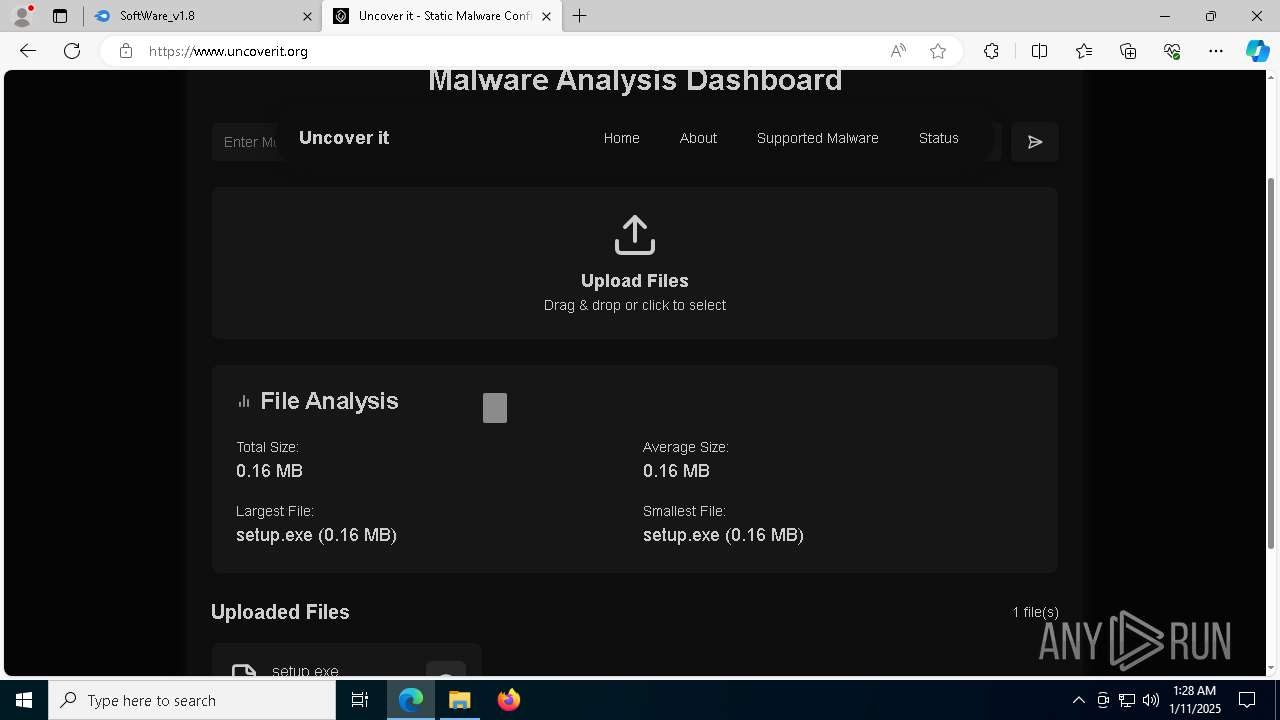
6456 | msedge.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (uncoverit .org) |
6456 | msedge.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (uncoverit .org) |
6456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |