| File name: | Maersk COVID -19 update.xlsx |
| Full analysis: | https://app.any.run/tasks/50fefae3-86a8-463f-b73f-30b4578255fb |
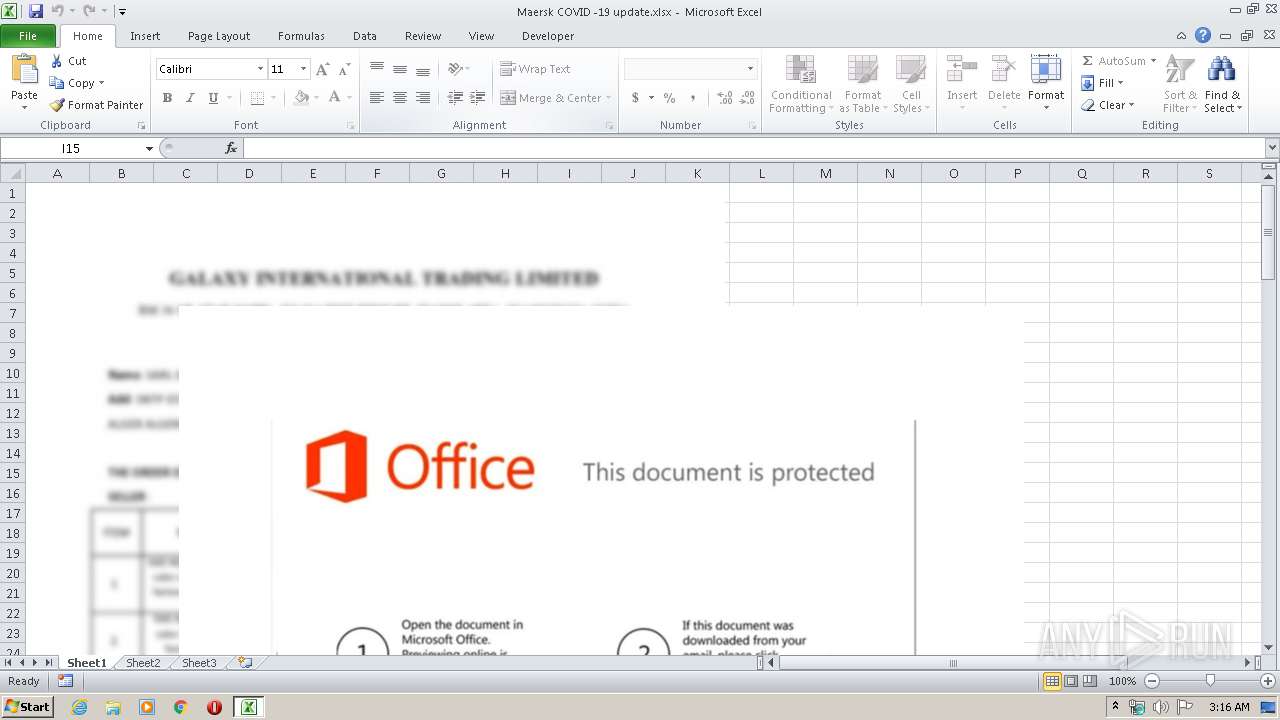
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | March 31, 2020, 02:16:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | D35271297FB00127721091FF9346FA4C |
| SHA1: | F274A972D5B3B20824DDA70089AFCE0E059BA500 |
| SHA256: | 479BFB01CD7BBD71CD2CE16CFDB25CF03F205A29CDE830F68D16D6A5994E107F |
| SSDEEP: | 12288:K10mlPrj3Dlp6szuispU1plzJrfSgEV3Ms4C4dJy0mky8nCNLRx8SE5uS4vw:rC/zlp6U/lagEV34HdJy0mPeV9uS4vw |
MALICIOUS
Application was dropped or rewritten from another process
- vbc.exe (PID: 608)
- vbc.exe (PID: 3624)
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 2420)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2420)
Actions looks like stealing of personal data
- vbc.exe (PID: 3624)
AGENTTESLA was detected
- vbc.exe (PID: 3624)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 2420)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 2420)
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 2420)
Creates files in the user directory
- EQNEDT32.EXE (PID: 2420)
- vbc.exe (PID: 3624)
Application launched itself
- vbc.exe (PID: 608)
Reads the cookies of Google Chrome
- vbc.exe (PID: 3624)
Reads the cookies of Mozilla Firefox
- vbc.exe (PID: 3624)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Users\admin\AppData\Roaming\vbc.exe" | C:\Users\admin\AppData\Roaming\vbc.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Appointment Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3624 | "{path}" | C:\Users\admin\AppData\Roaming\vbc.exe | vbc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Appointment Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
973
Read events
910
Write events
52
Delete events
11
Modification events
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | =`0 |
Value: 3D603000DC090000010000000000000000000000 | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2524) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C8D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3624 | vbc.exe | C:\Users\admin\AppData\Roaming\haa05ofe.fe2\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 3624 | vbc.exe | C:\Users\admin\AppData\Roaming\haa05ofe.fe2\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 2420 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\vbc[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2420 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\vbc.exe | executable | |
MD5:— | SHA256:— | |||
| 3624 | vbc.exe | C:\Users\admin\AppData\Roaming\haa05ofe.fe2.zip | compressed | |
MD5:— | SHA256:— | |||
| 2524 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1AA11974.emf | emf | |
MD5:9DBC4E90F367DF7508C707F6806E8DCA | SHA256:78C2466C6539C3C9AECC57DD4B2EA6303724EEAEF9925FC568C6DA8FC6EFDE19 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2420 | EQNEDT32.EXE | GET | 200 | 109.169.89.118:80 | http://easydatatransfercleansystemprofessional.duckdns.org/intel/vbc.exe | GB | executable | 434 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3624 | vbc.exe | 208.91.199.224:587 | smtp.kushpetroleurn.net | PDR | US | shared |
2420 | EQNEDT32.EXE | 109.169.89.118:80 | easydatatransfercleansystemprofessional.duckdns.org | iomart Cloud Services Limited. | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
easydatatransfercleansystemprofessional.duckdns.org |
| malicious |
smtp.kushpetroleurn.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2420 | EQNEDT32.EXE | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2420 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3624 | vbc.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3624 | vbc.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
3624 | vbc.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla SMTP Activity |
3624 | vbc.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
3624 | vbc.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3624 | vbc.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
3624 | vbc.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla SMTP Activity |
4 ETPRO signatures available at the full report