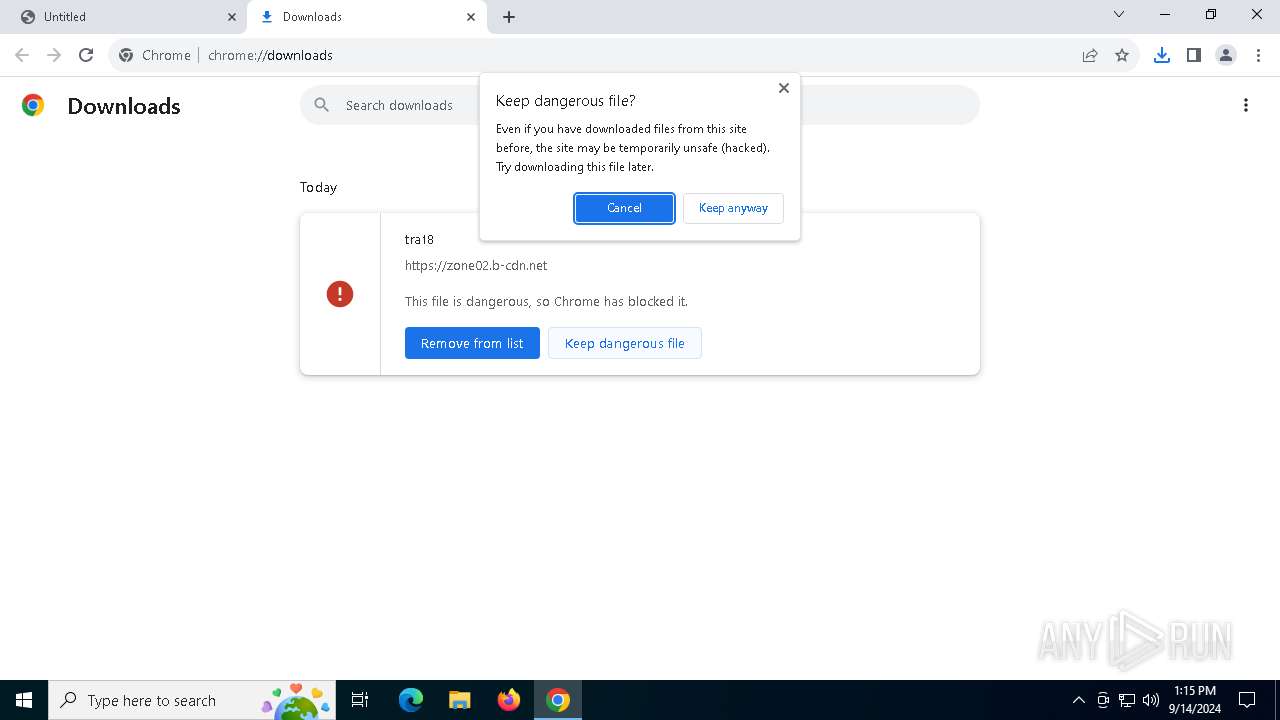
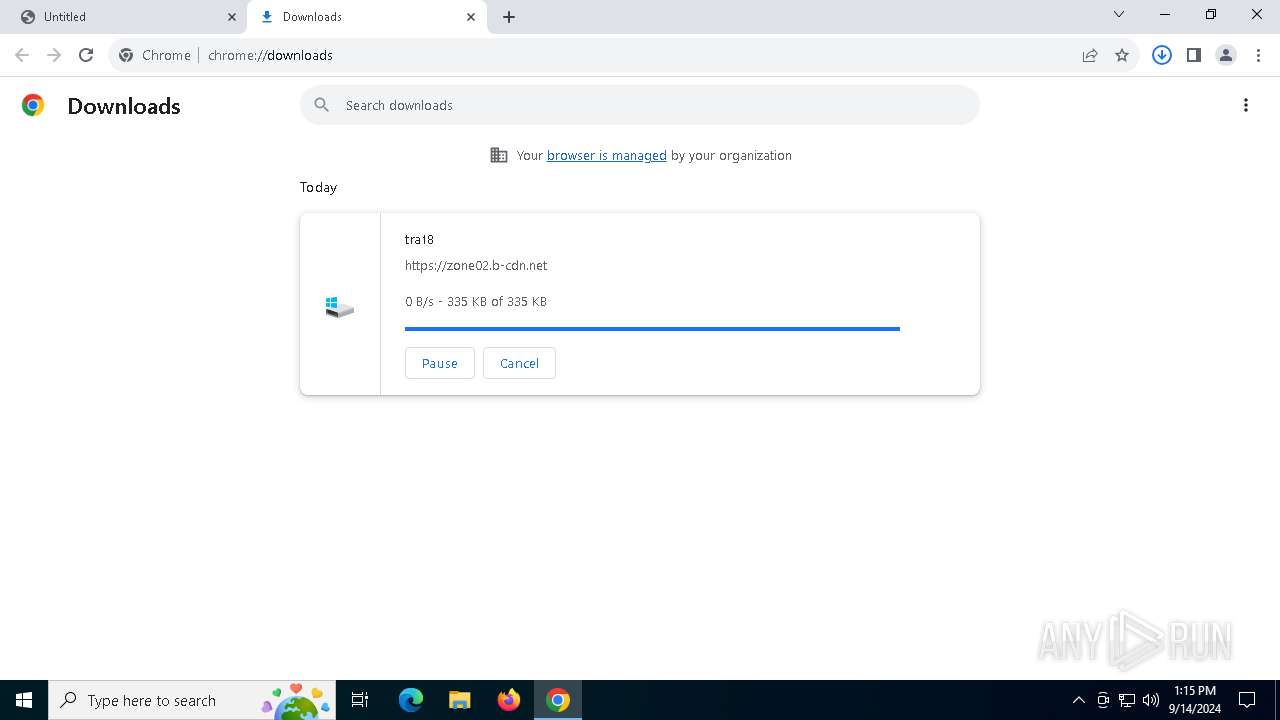
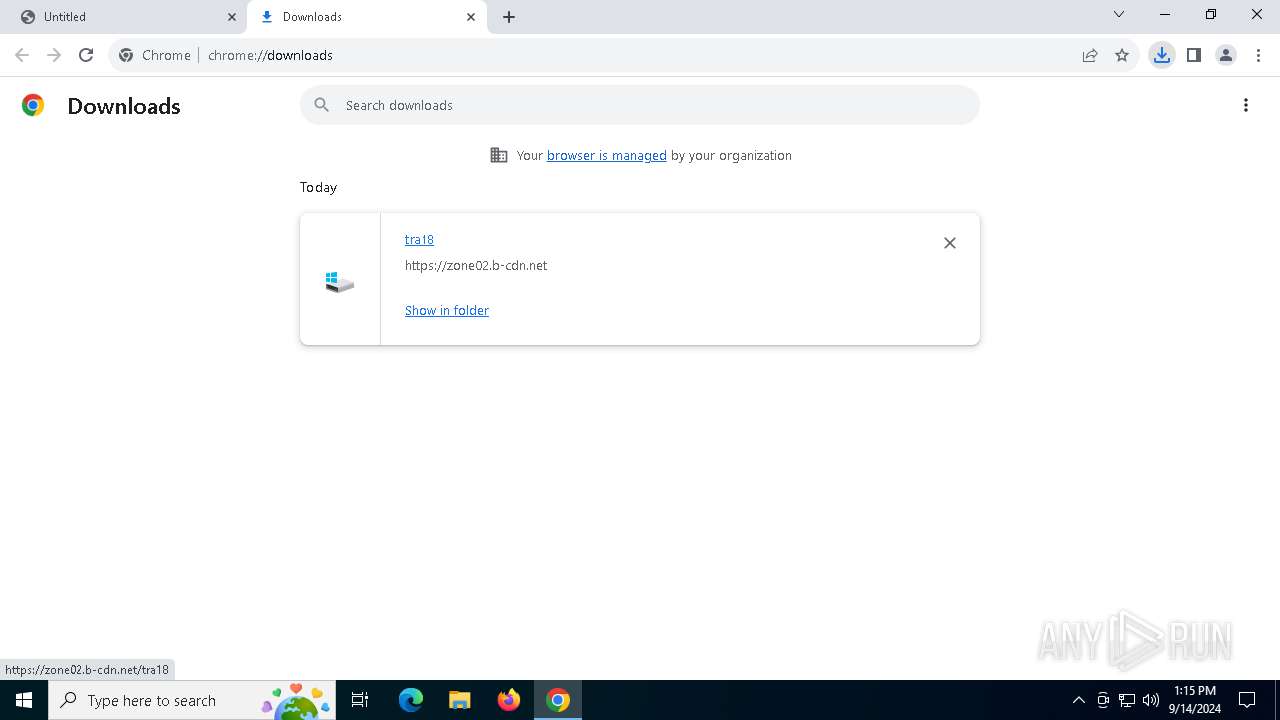
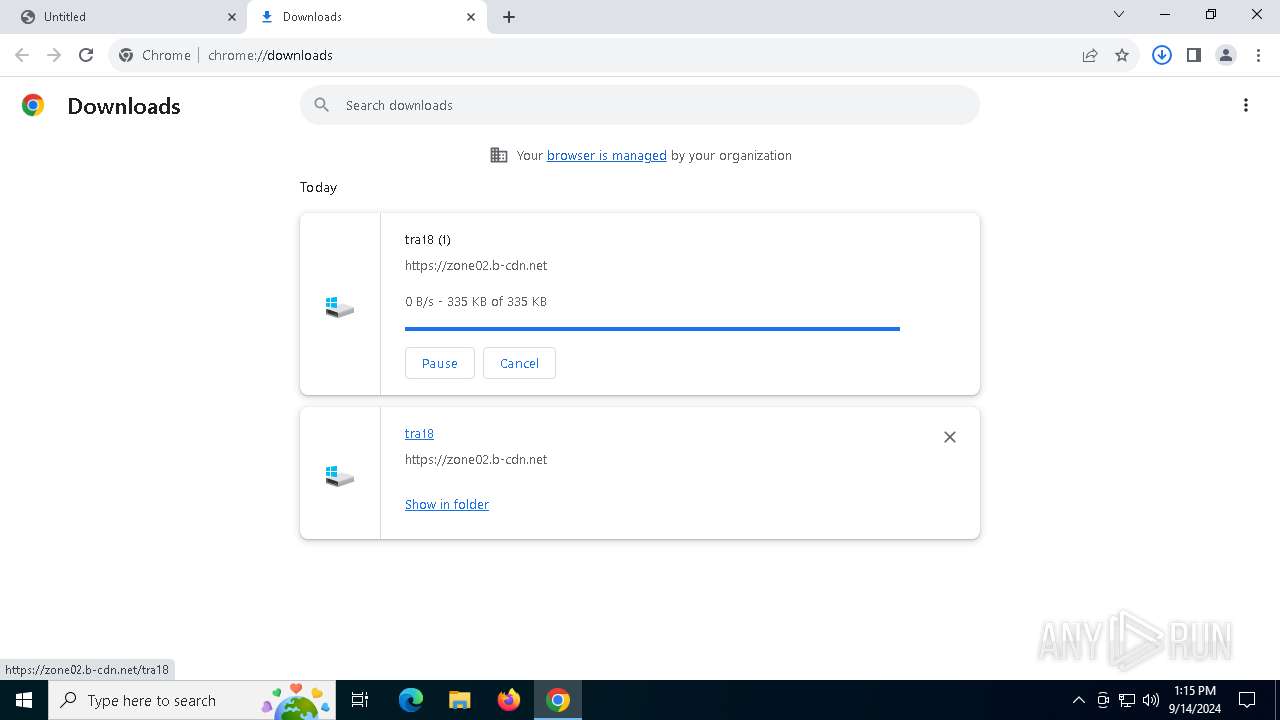
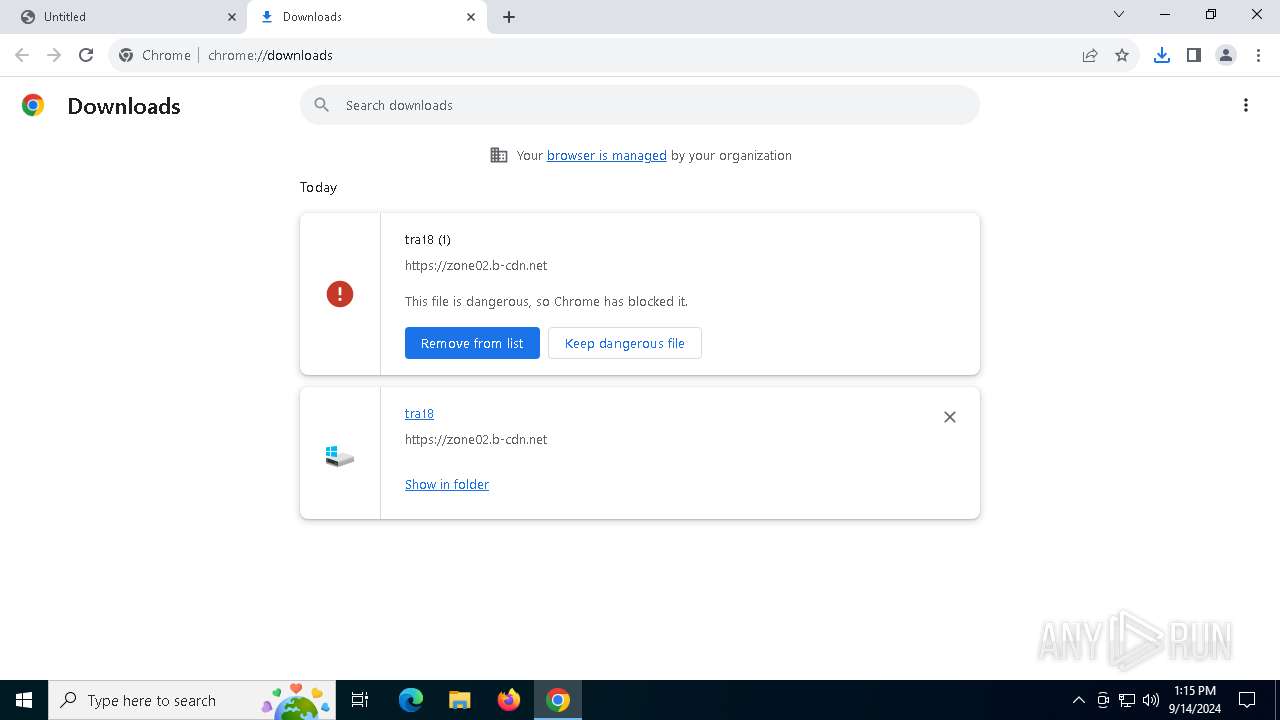
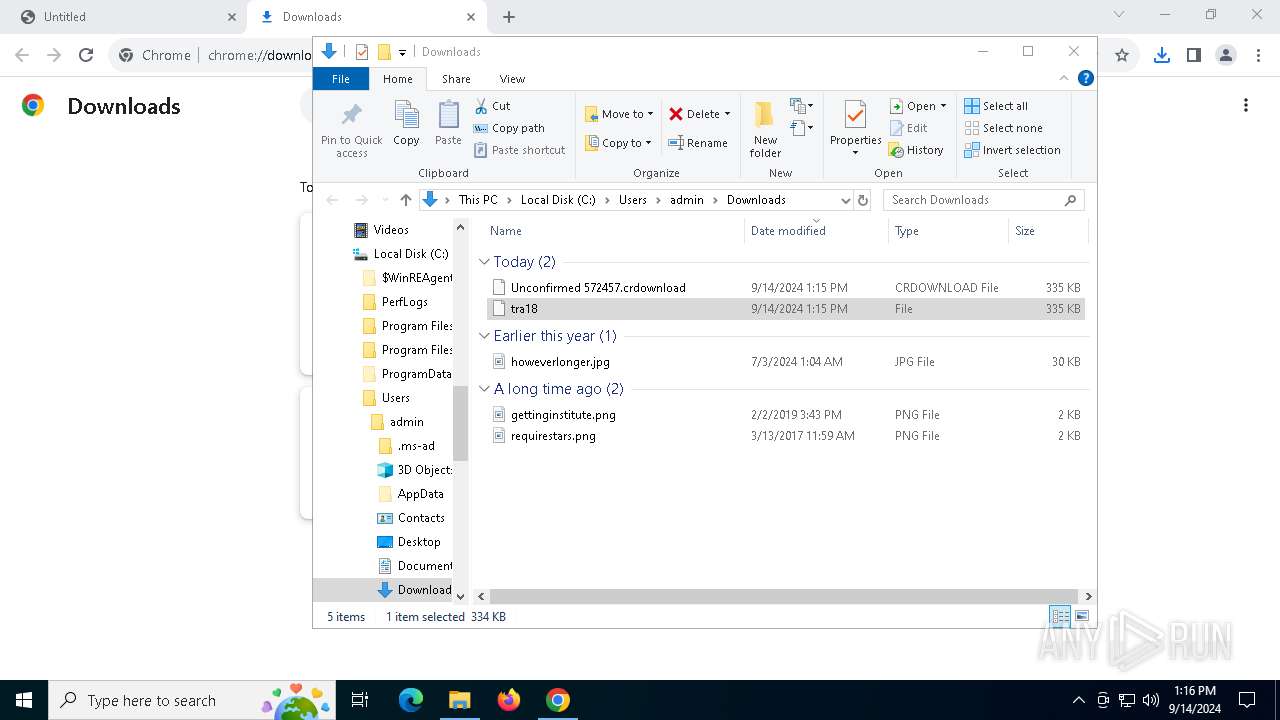
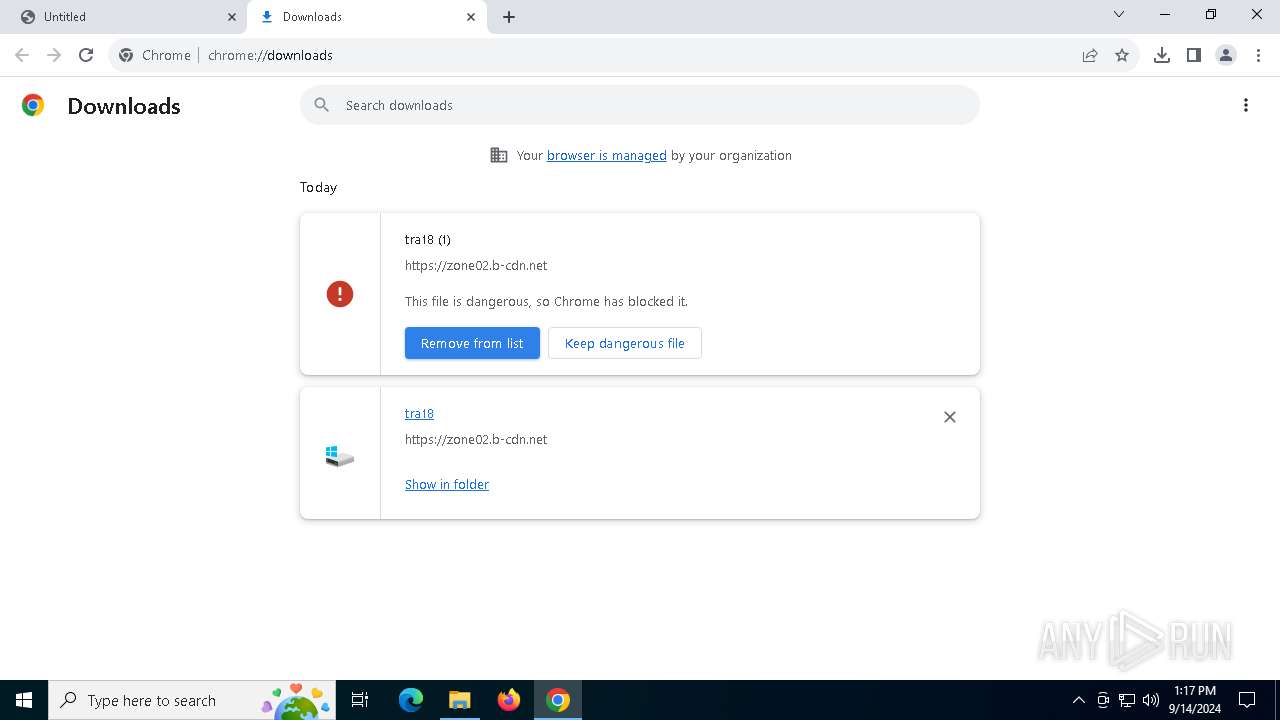
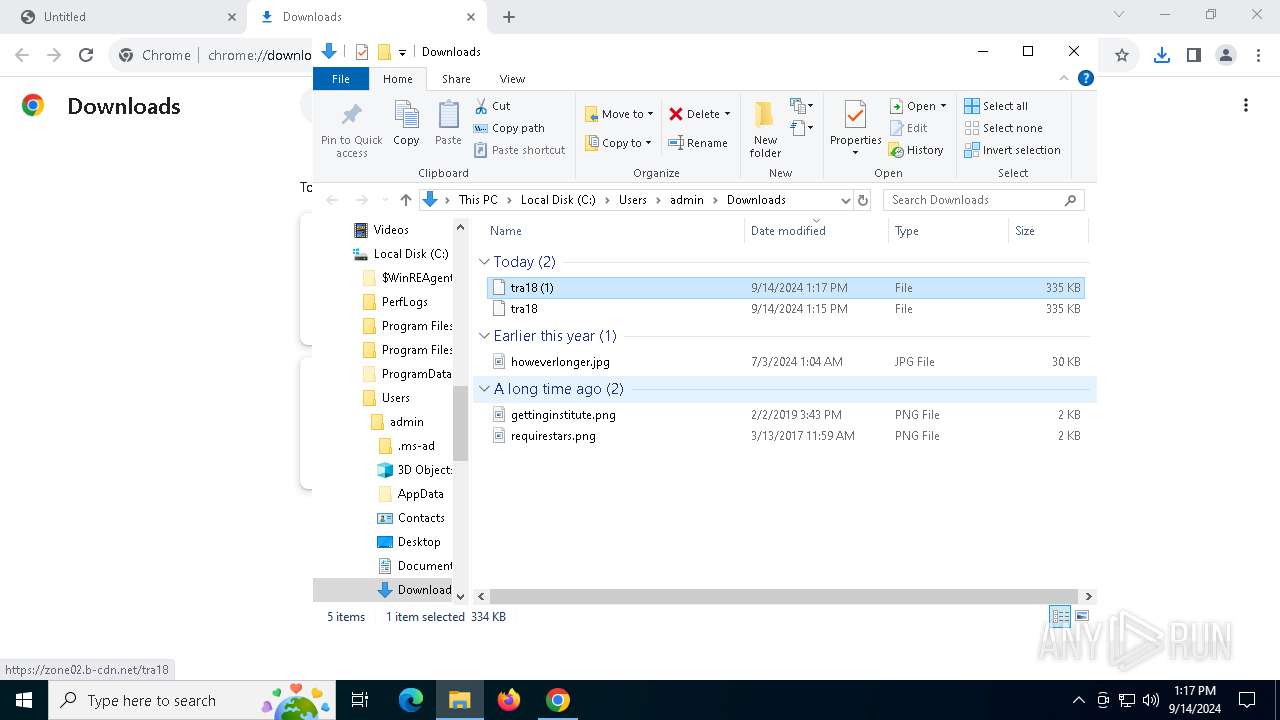
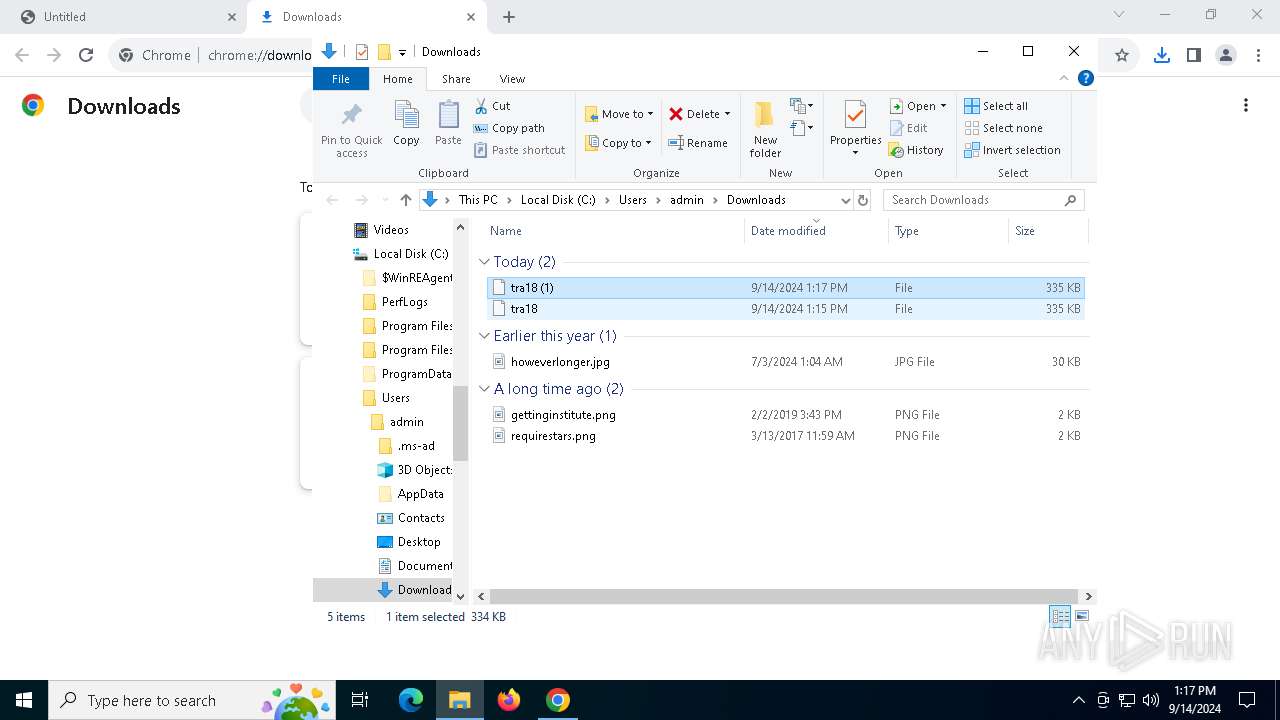
| URL: | https://zone02.b-cdn.net/tra18 |
| Full analysis: | https://app.any.run/tasks/05c5a8cd-1418-43a3-a9cd-b37c80663cd2 |
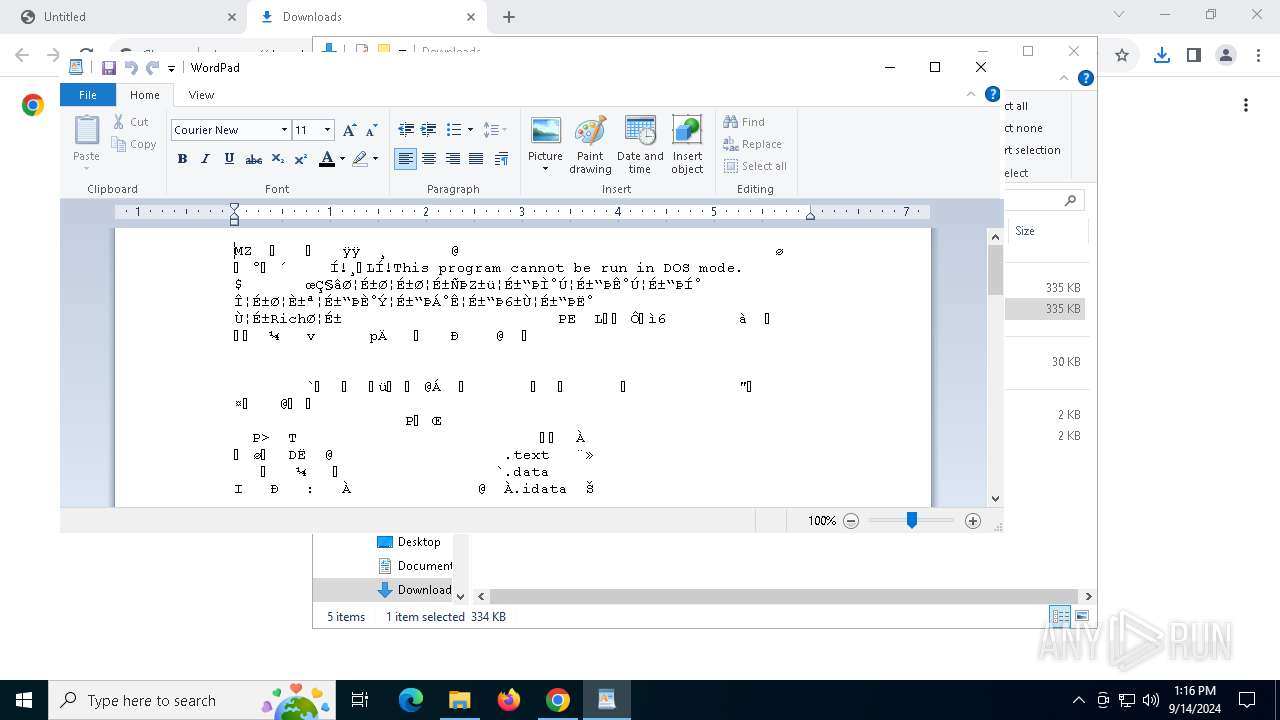
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 14, 2024, 13:15:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8FFF04442EEFF0BB8F9534D7751D9EFB |
| SHA1: | CE37B128767B9171B4F60FFE45F5E551B05DF40C |
| SHA256: | 479A680B19654A5C9D31F453F69A8875C1546706EDDC14471F581A92F190AE4C |
| SSDEEP: | 3:N87gMEUdn:27gFE |
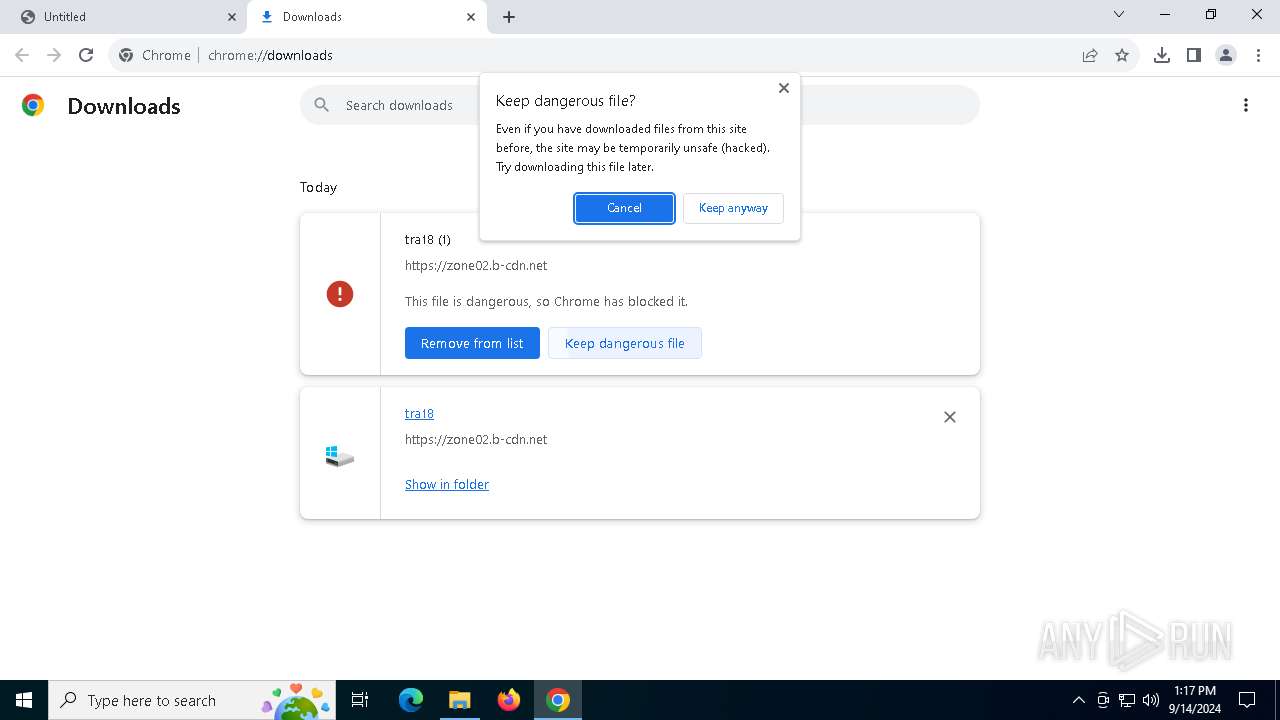
MALICIOUS
LUMMA has been detected (SURICATA)
- chrome.exe (PID: 5220)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- chrome.exe (PID: 5220)
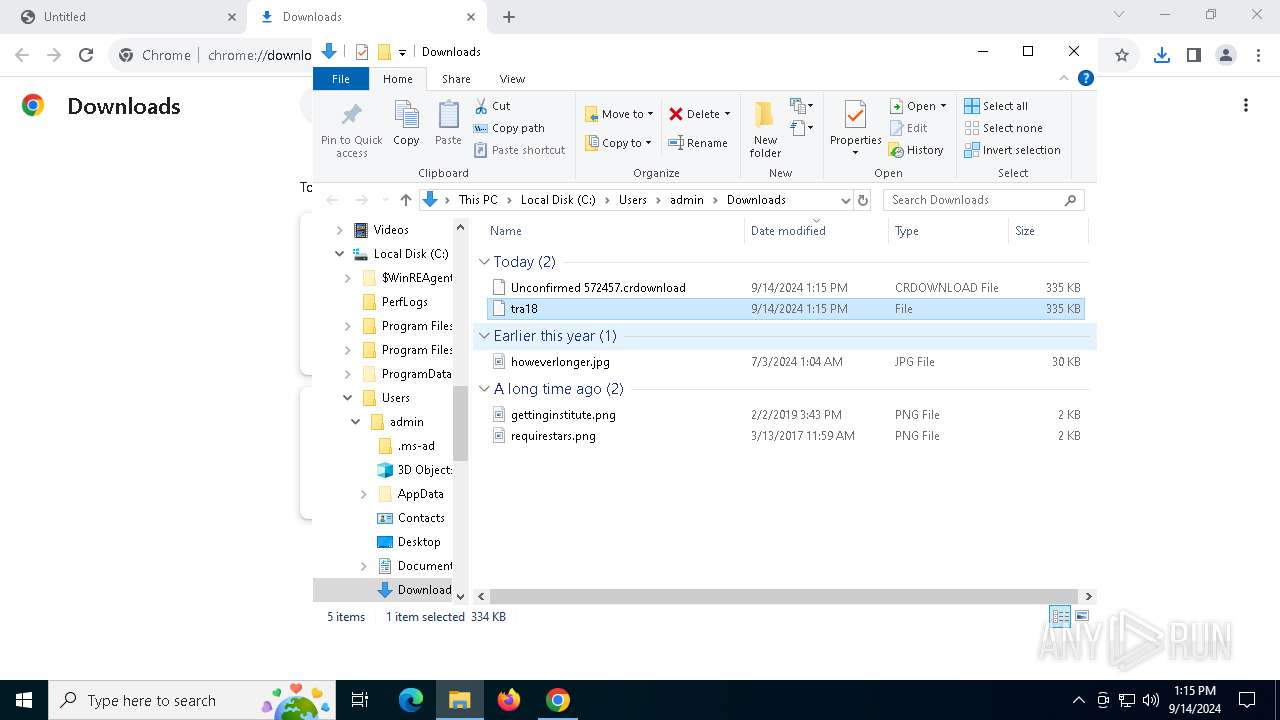
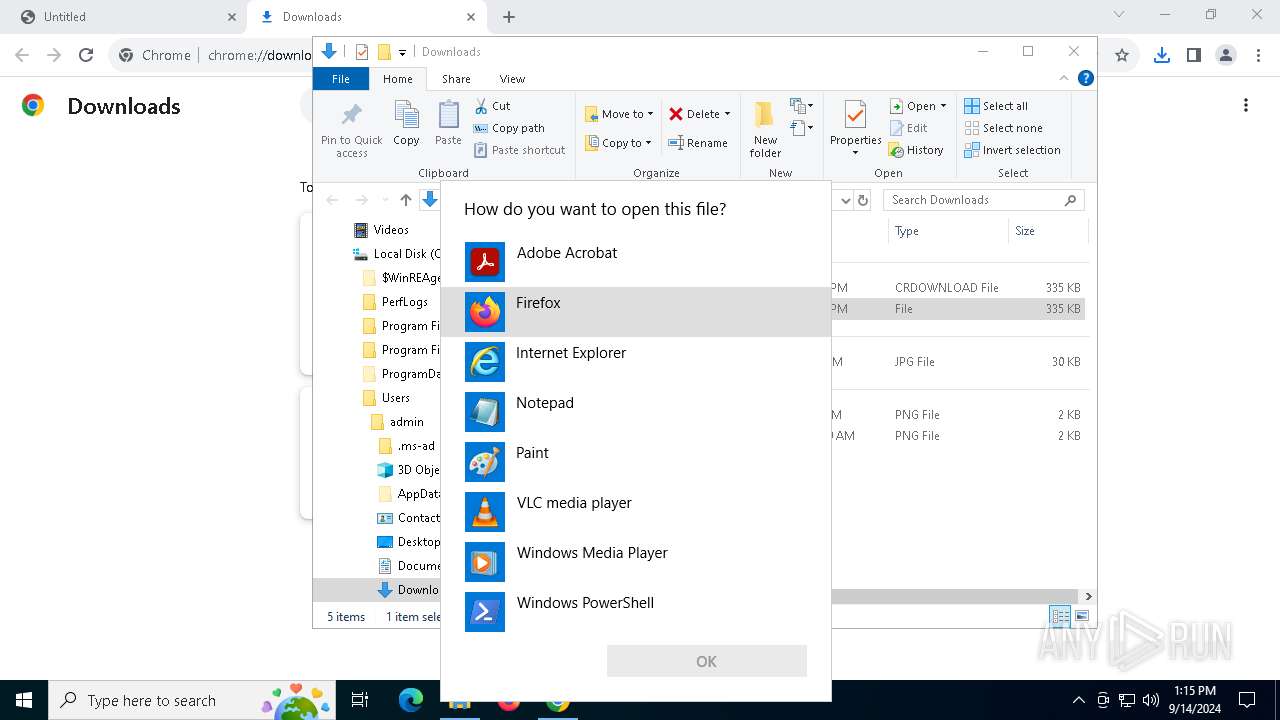
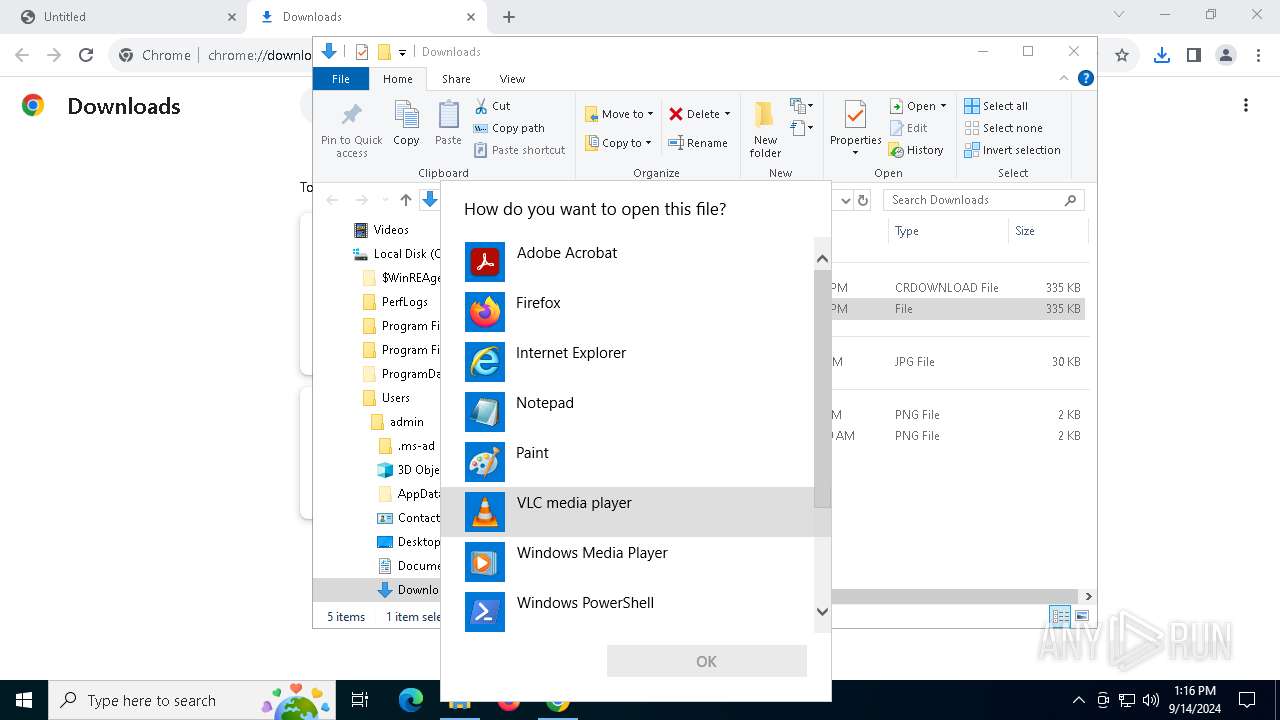
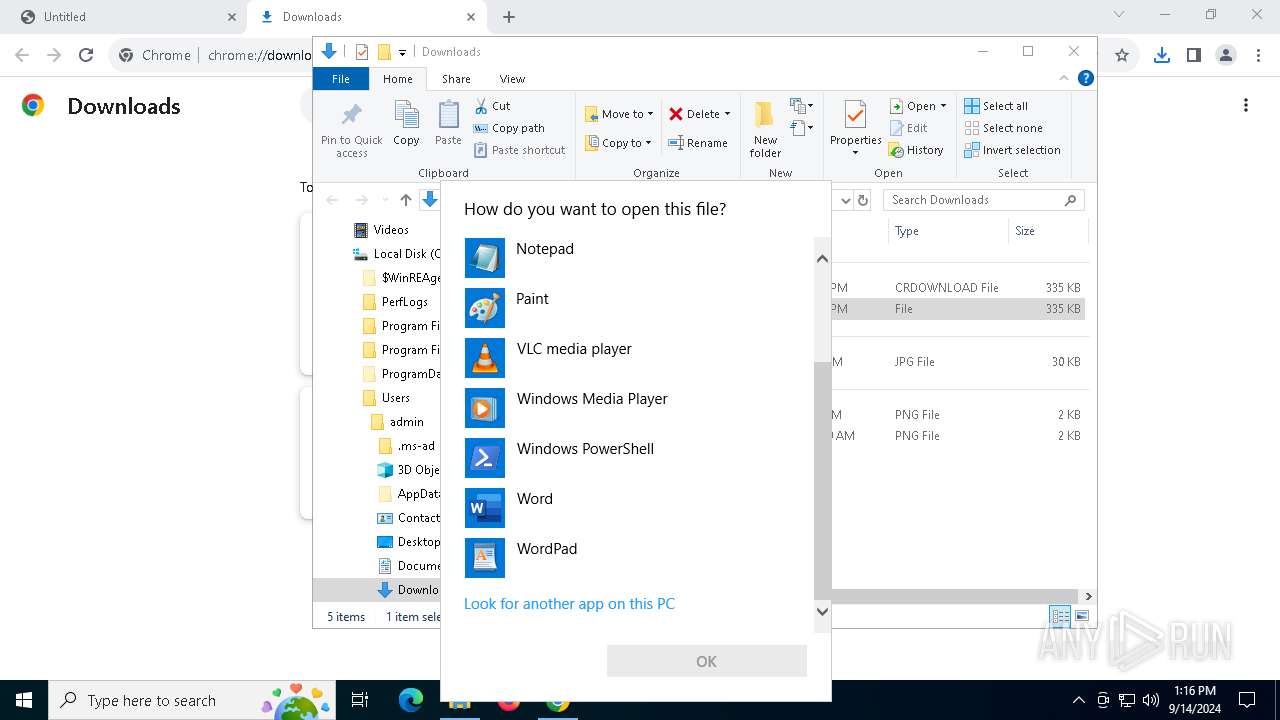
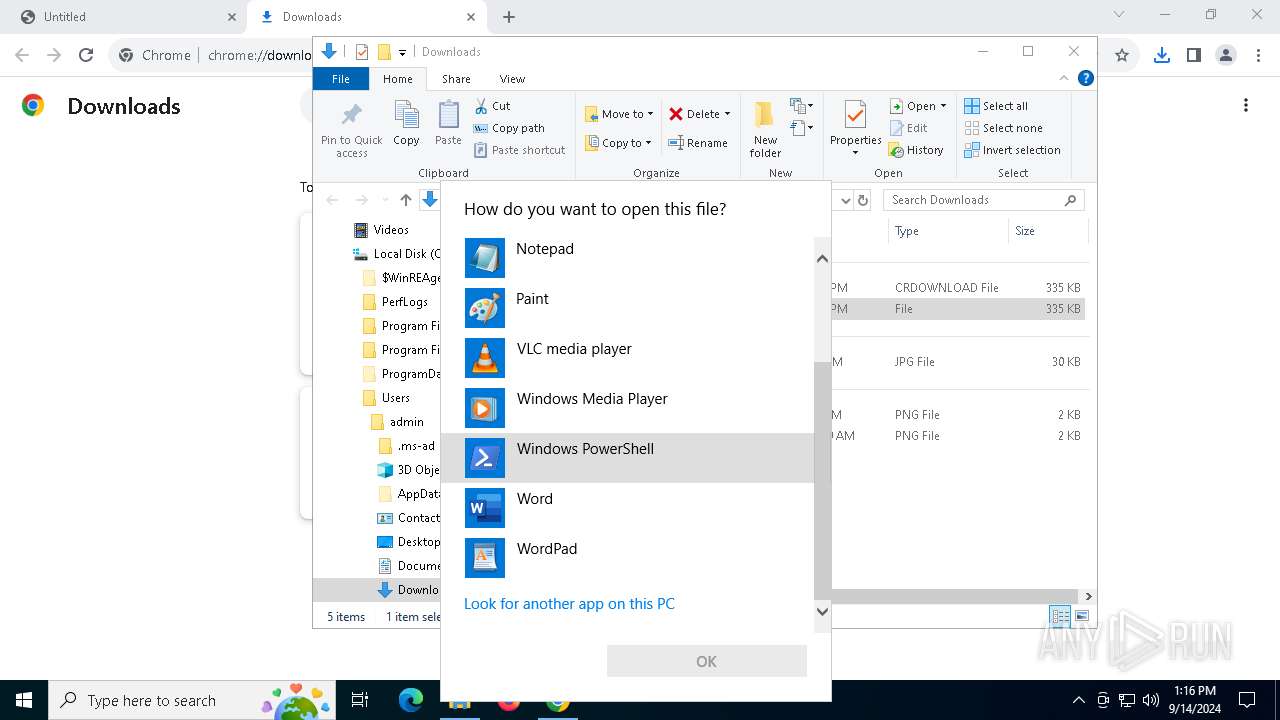
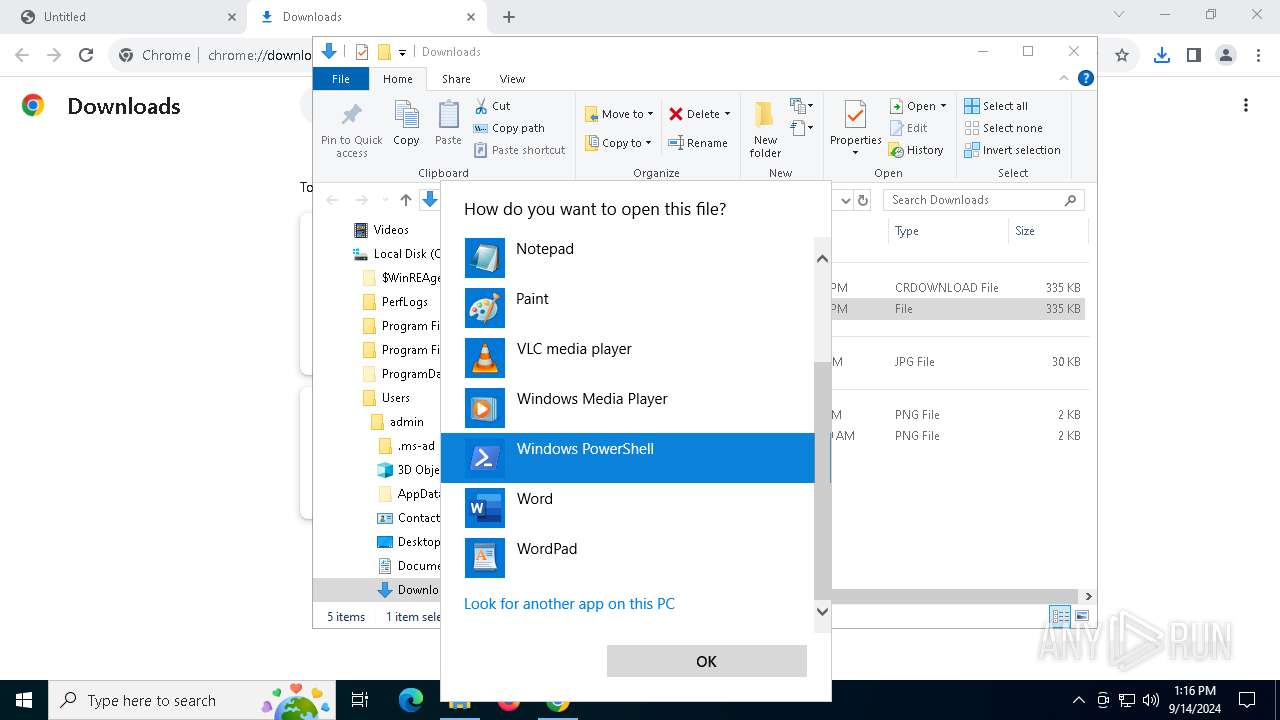
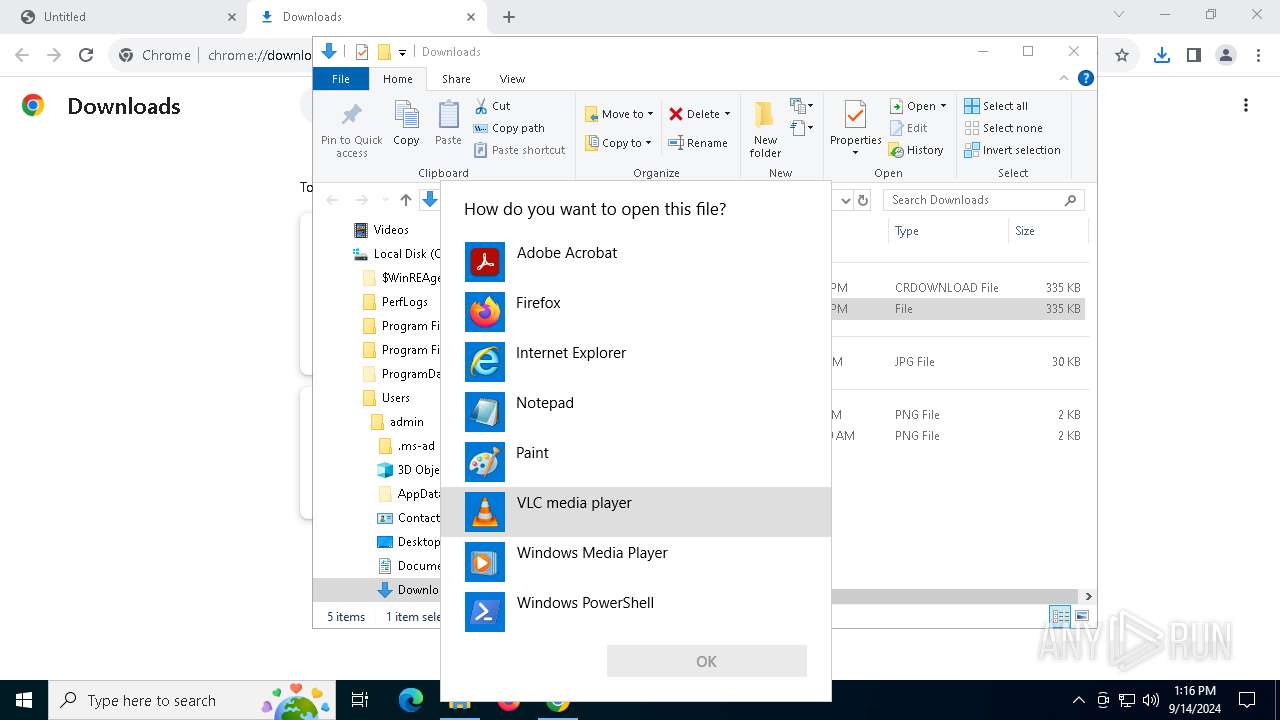
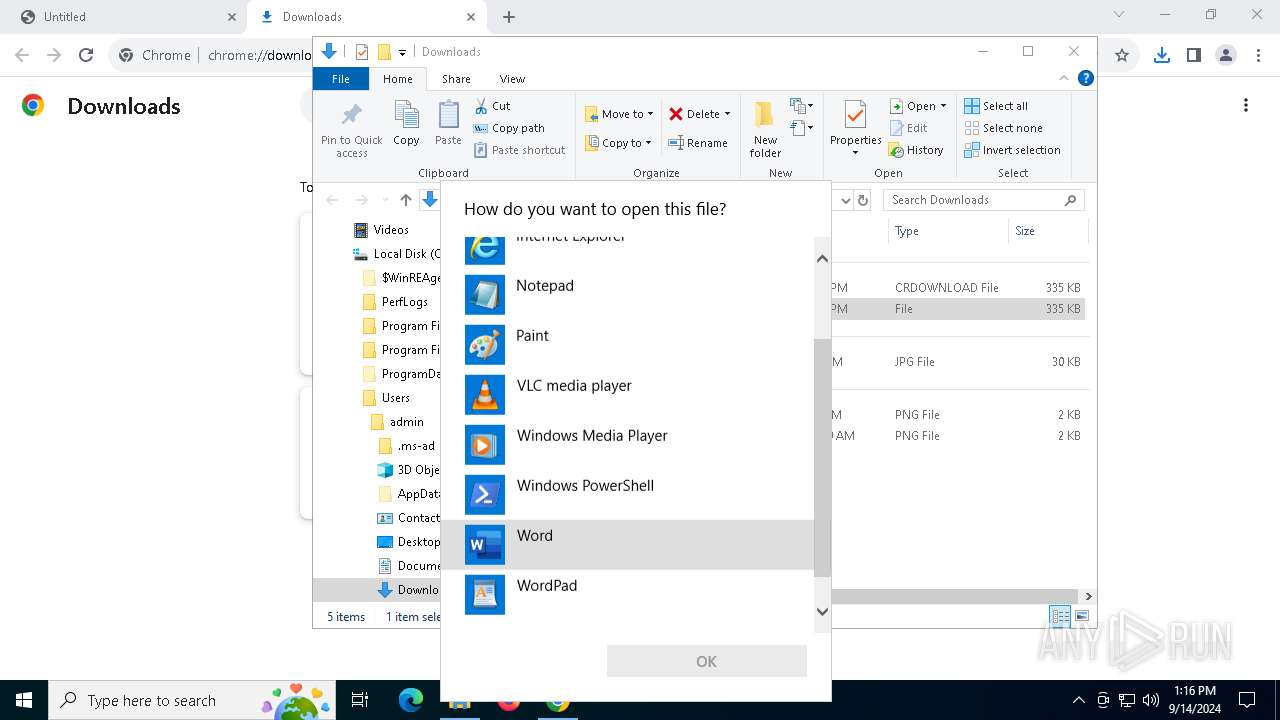
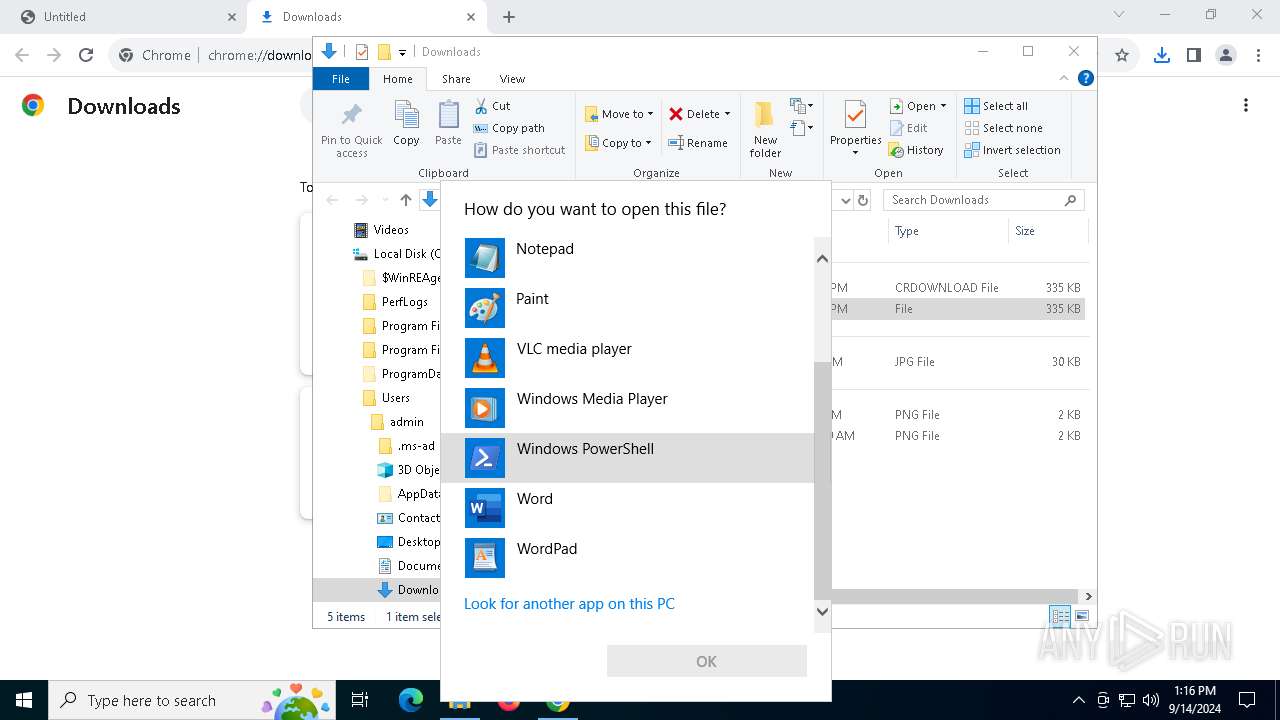
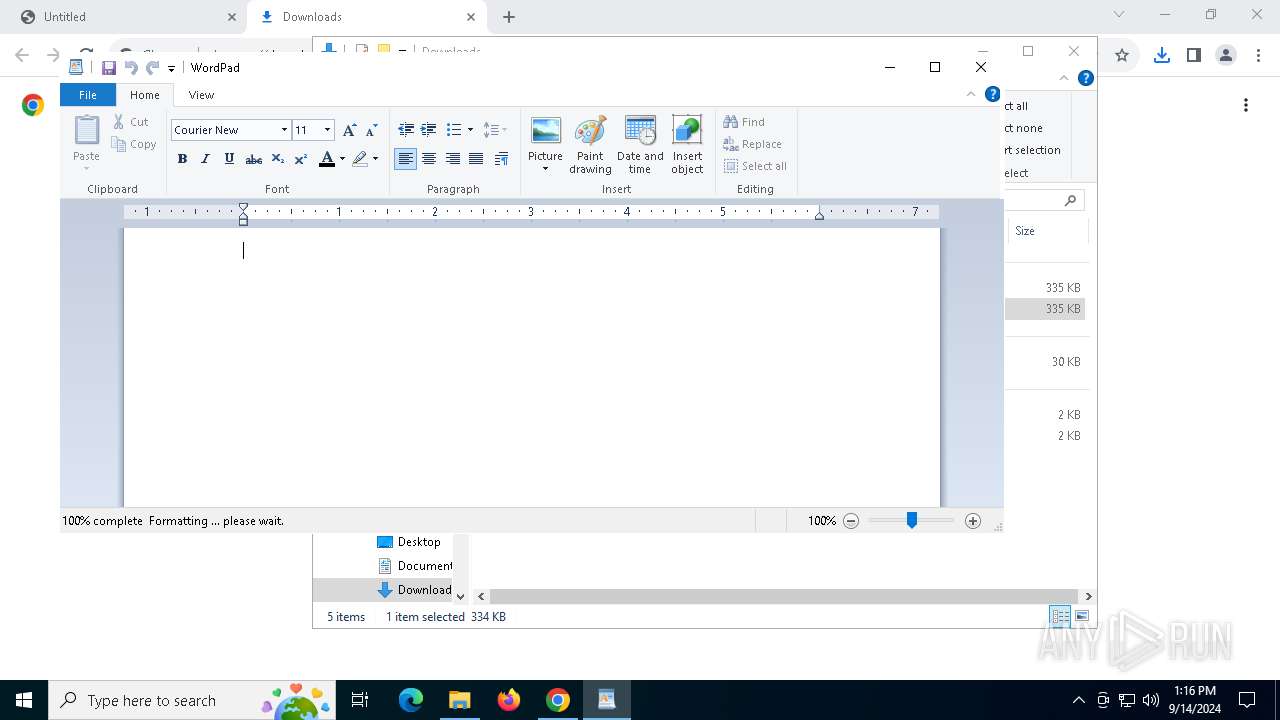
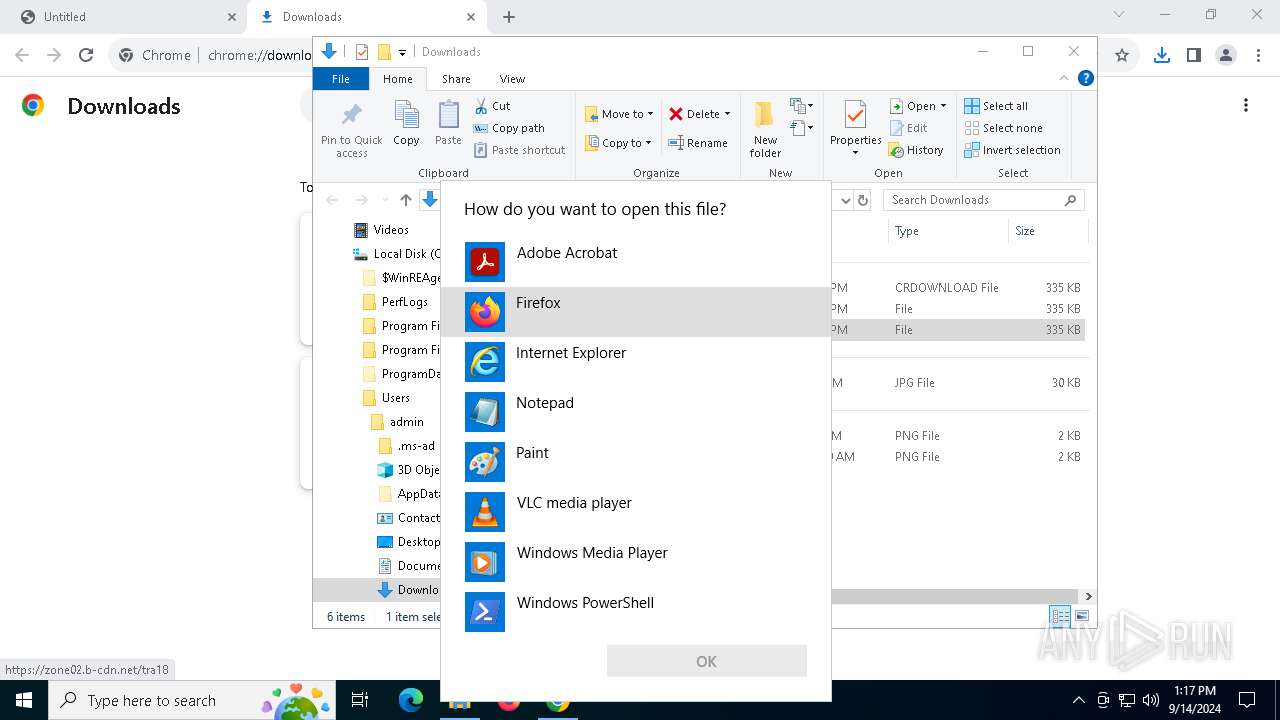
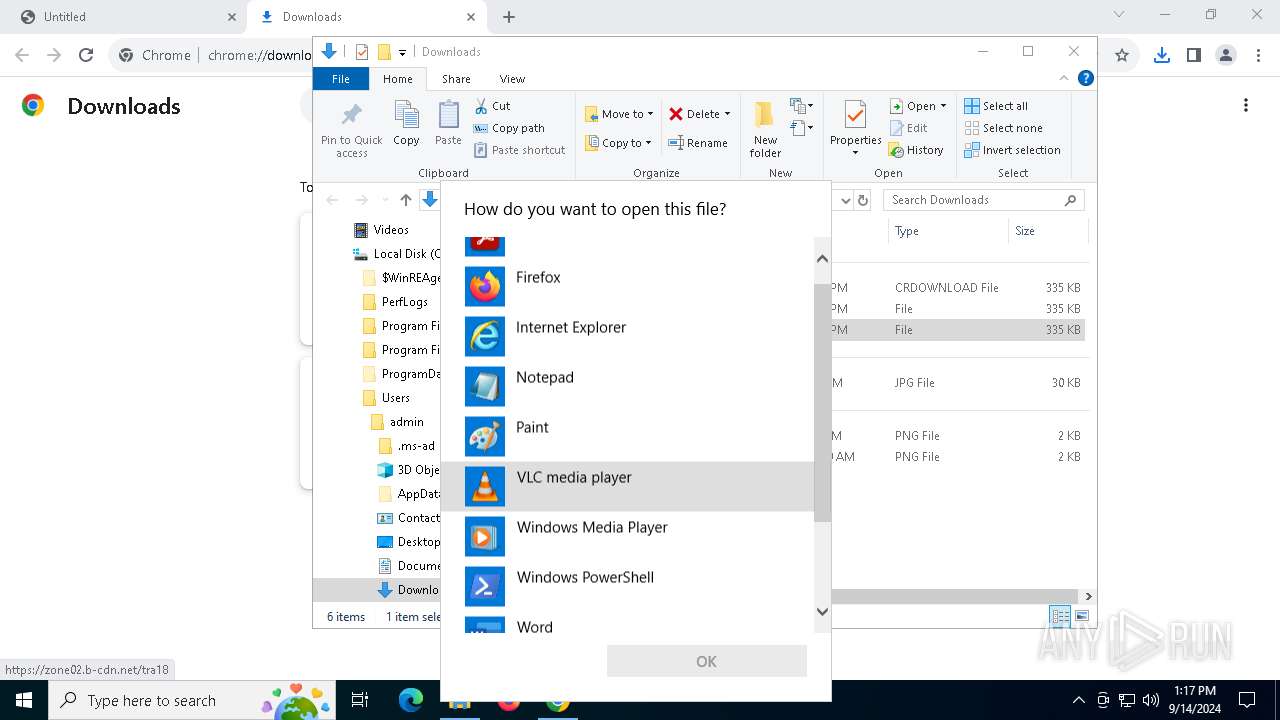
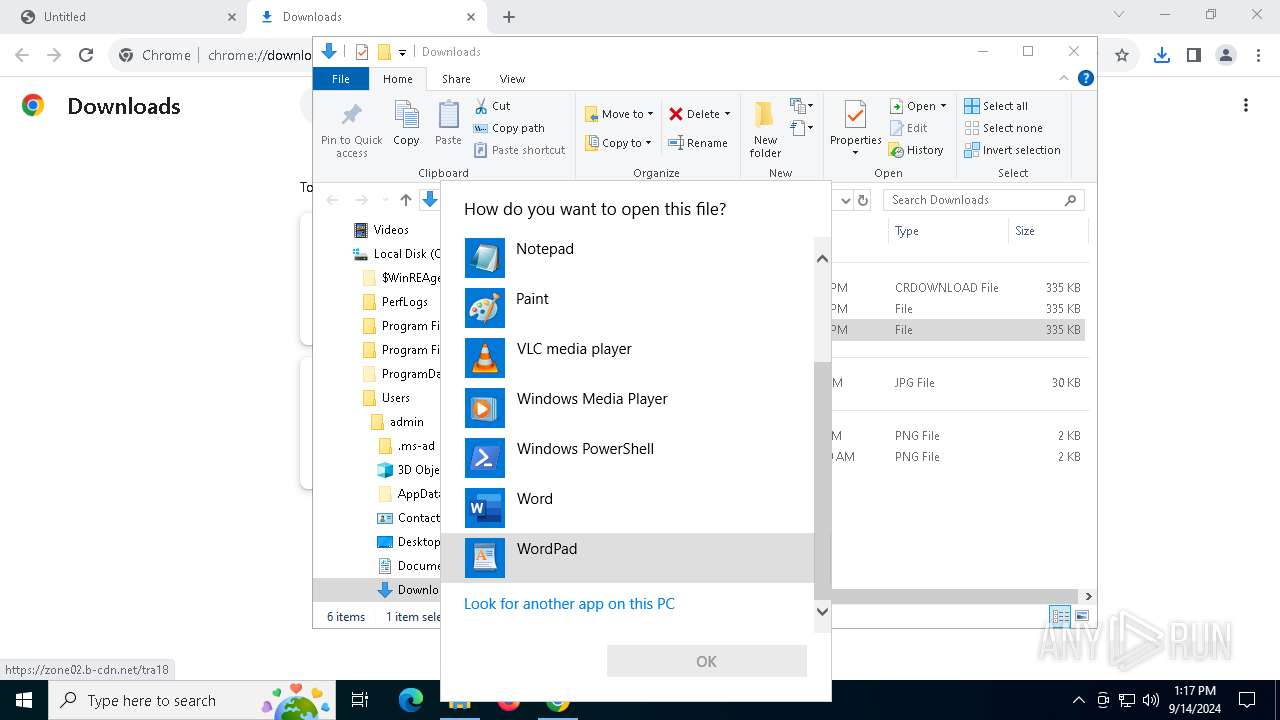
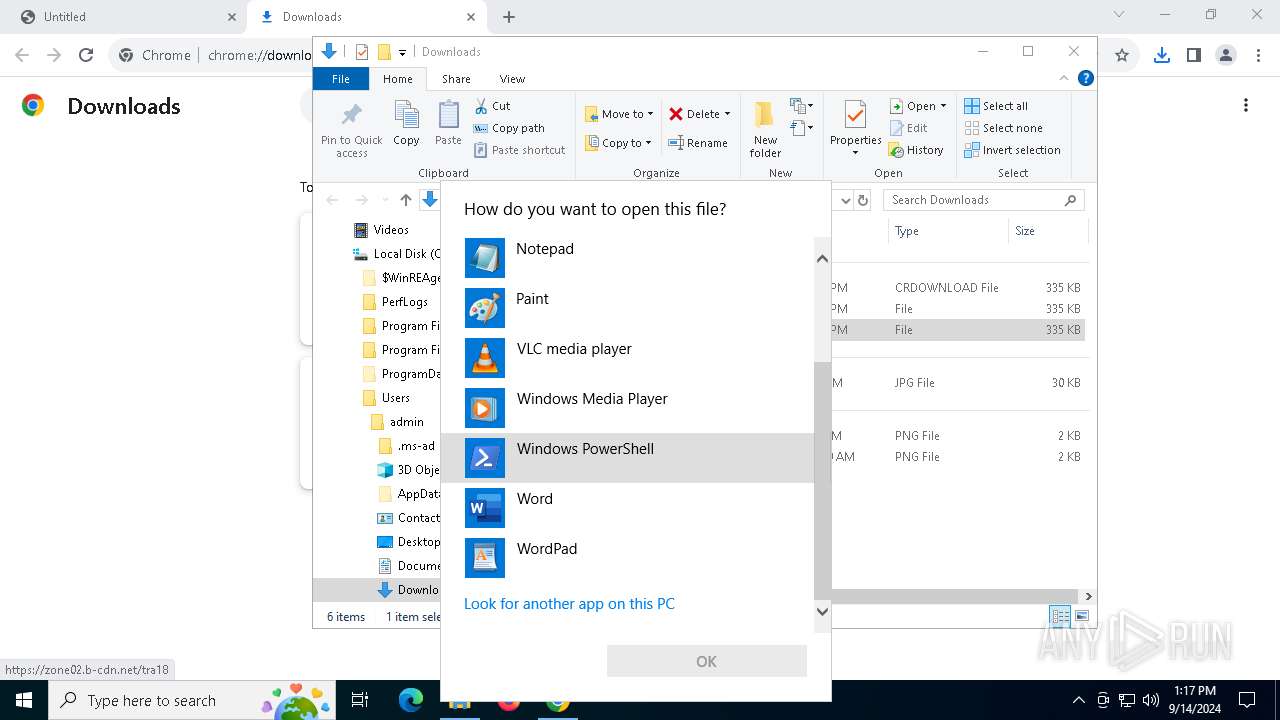
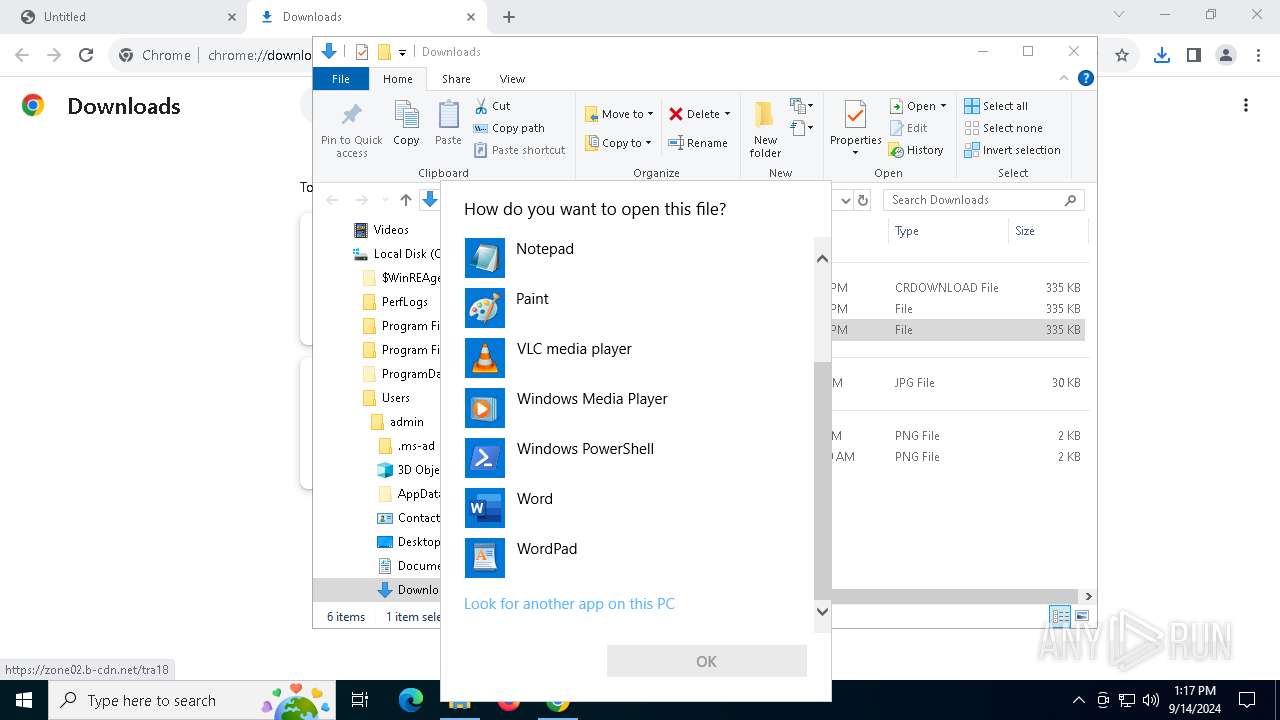
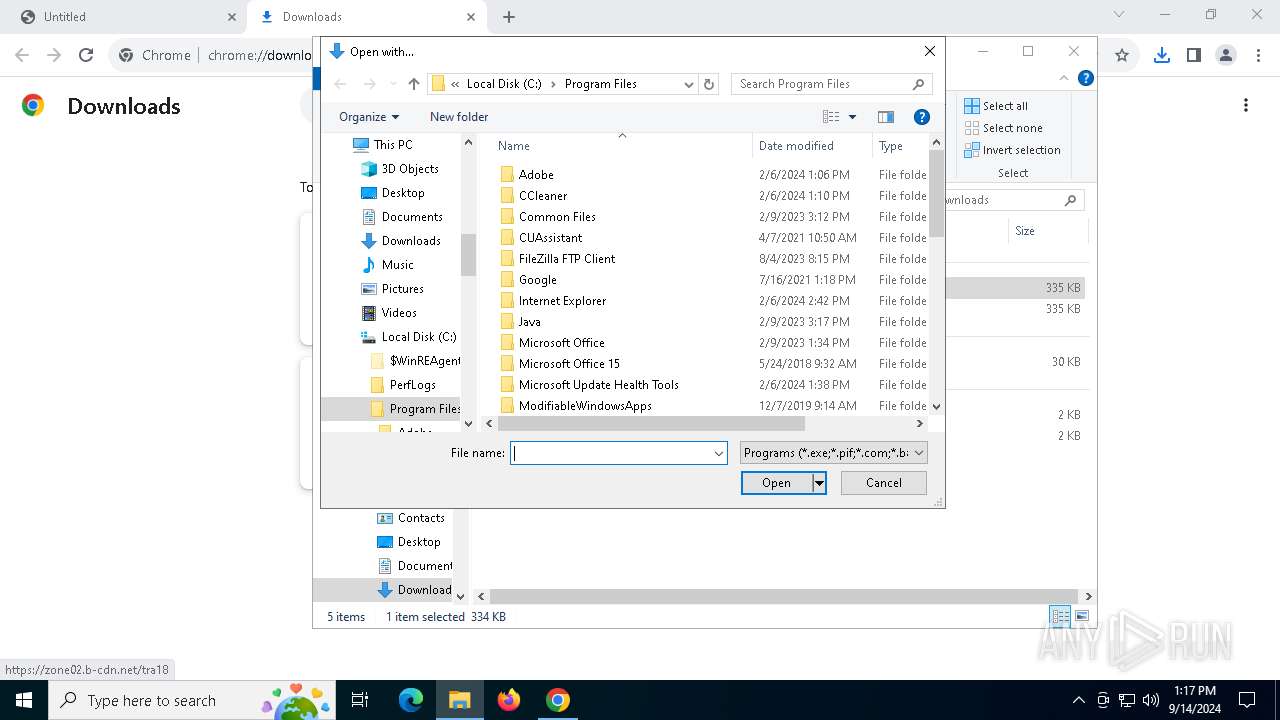
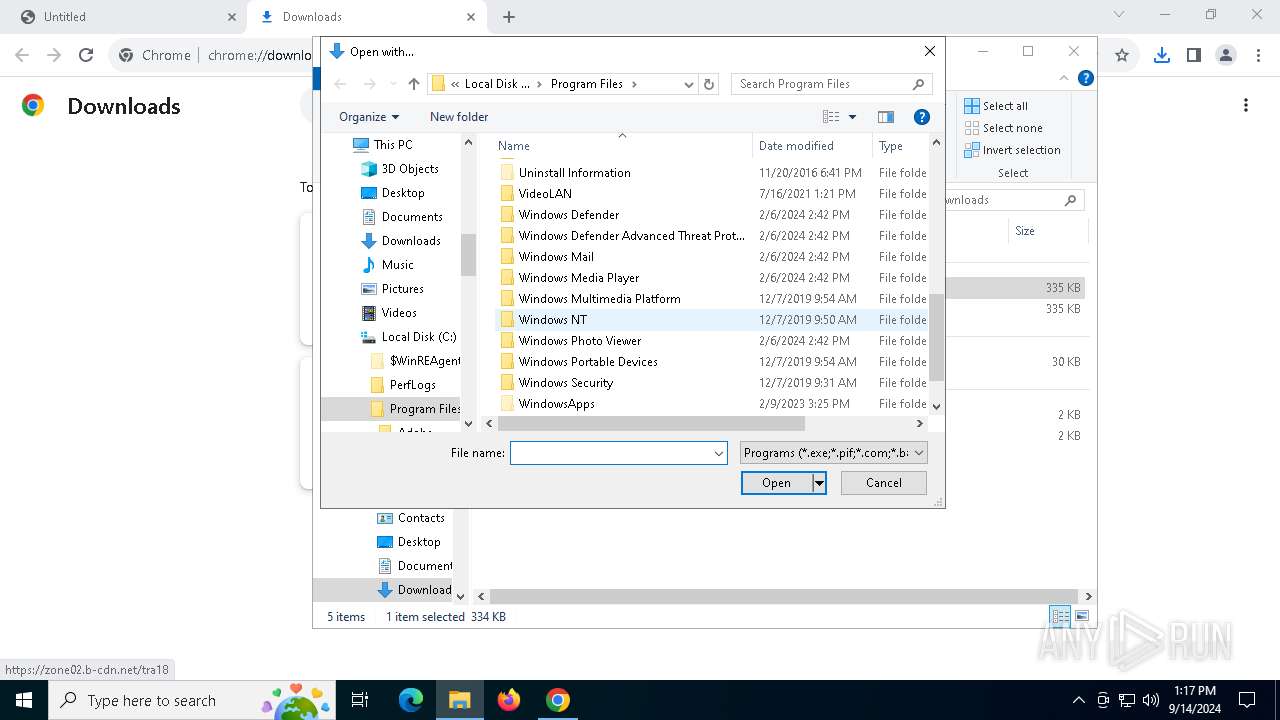
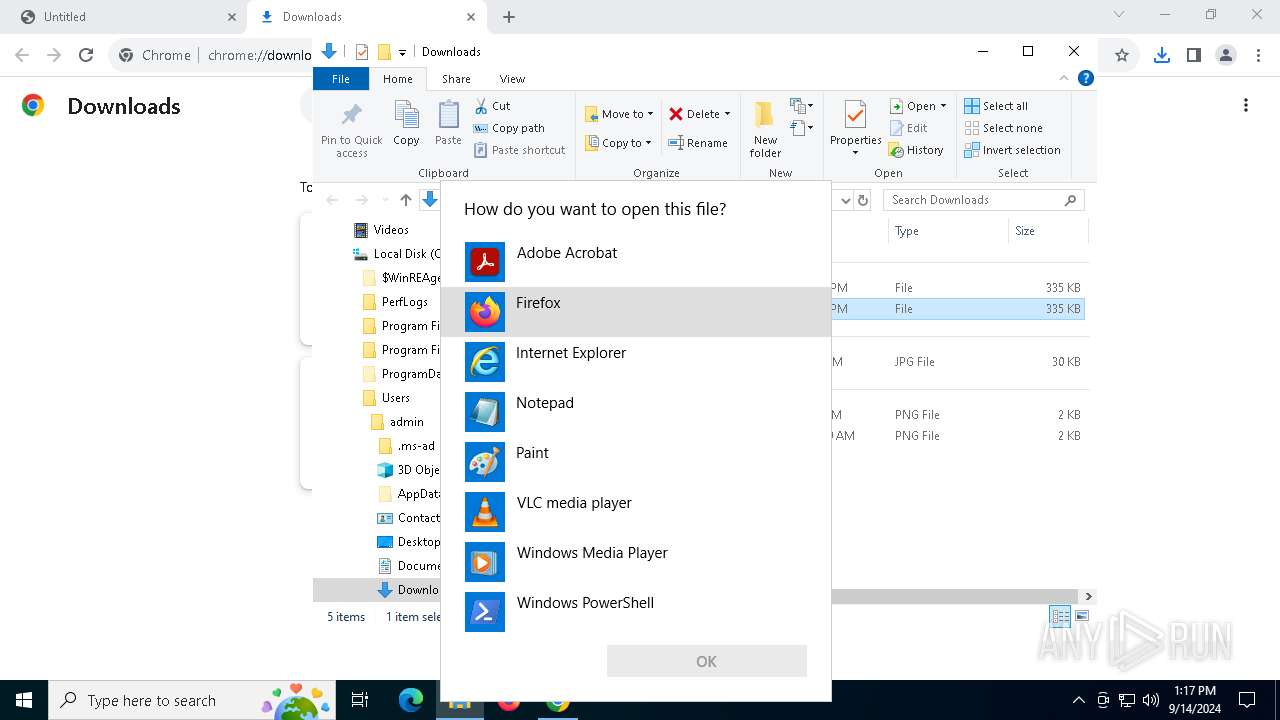
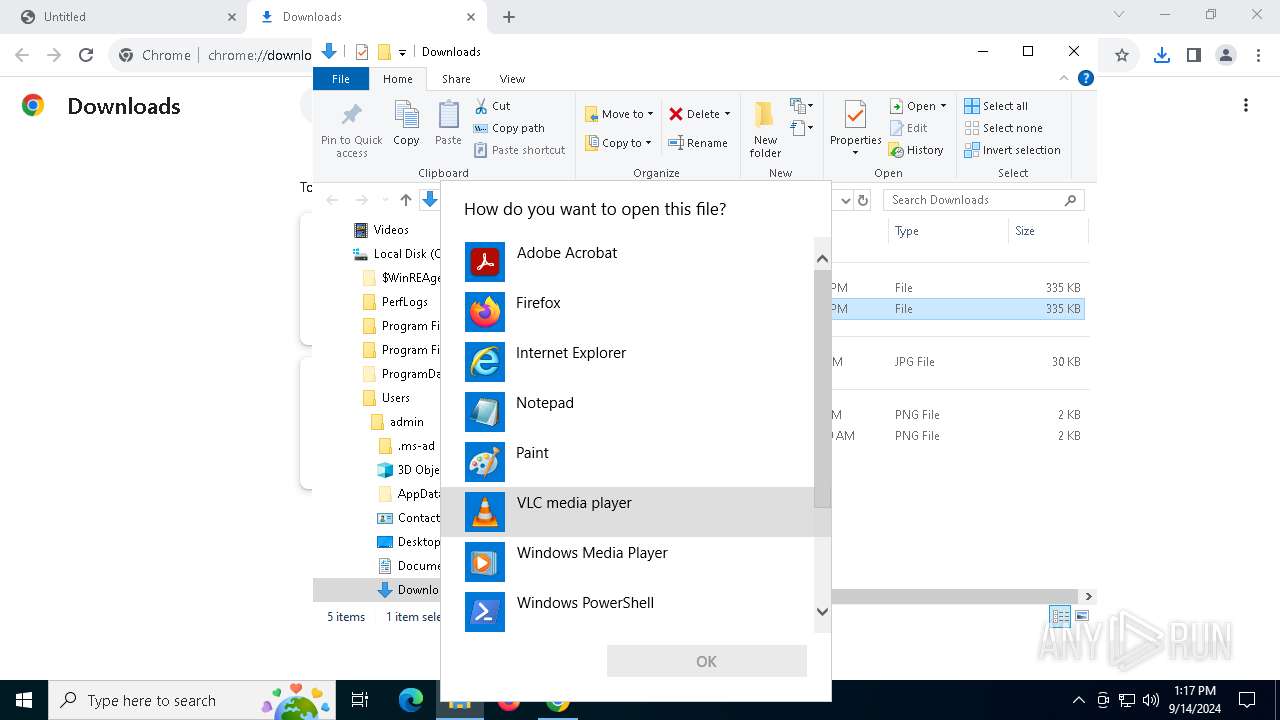
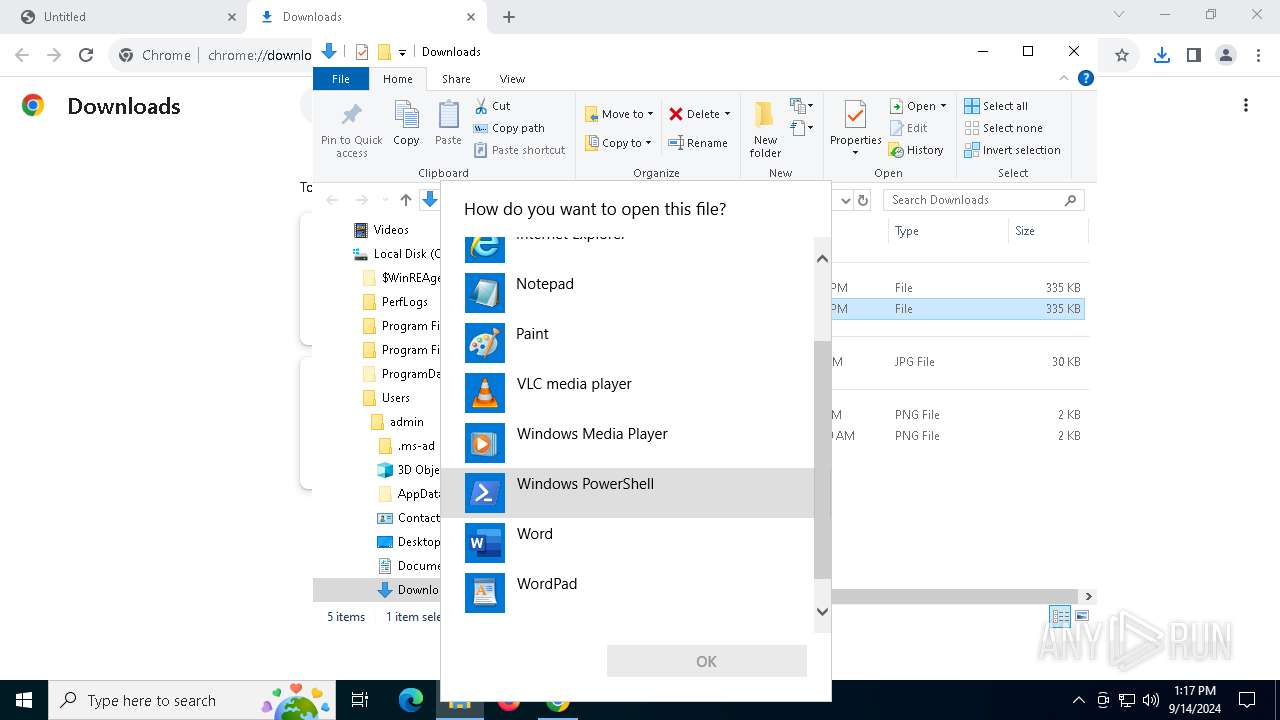
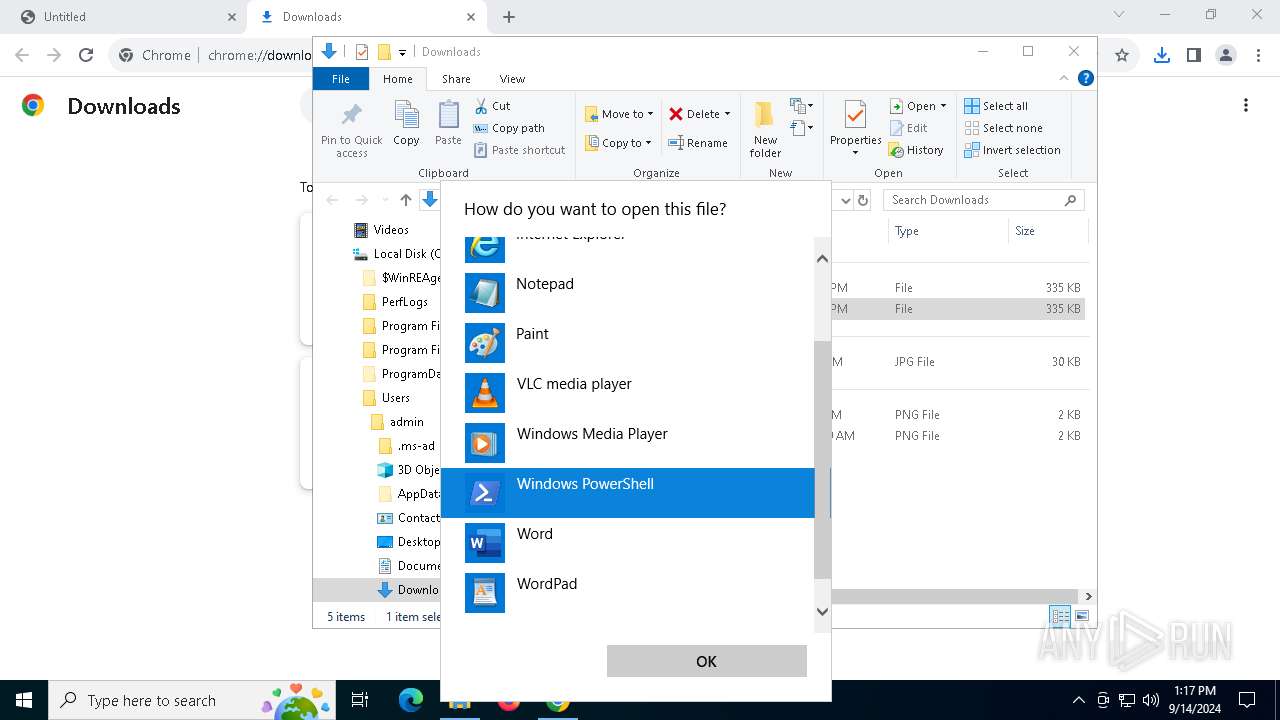
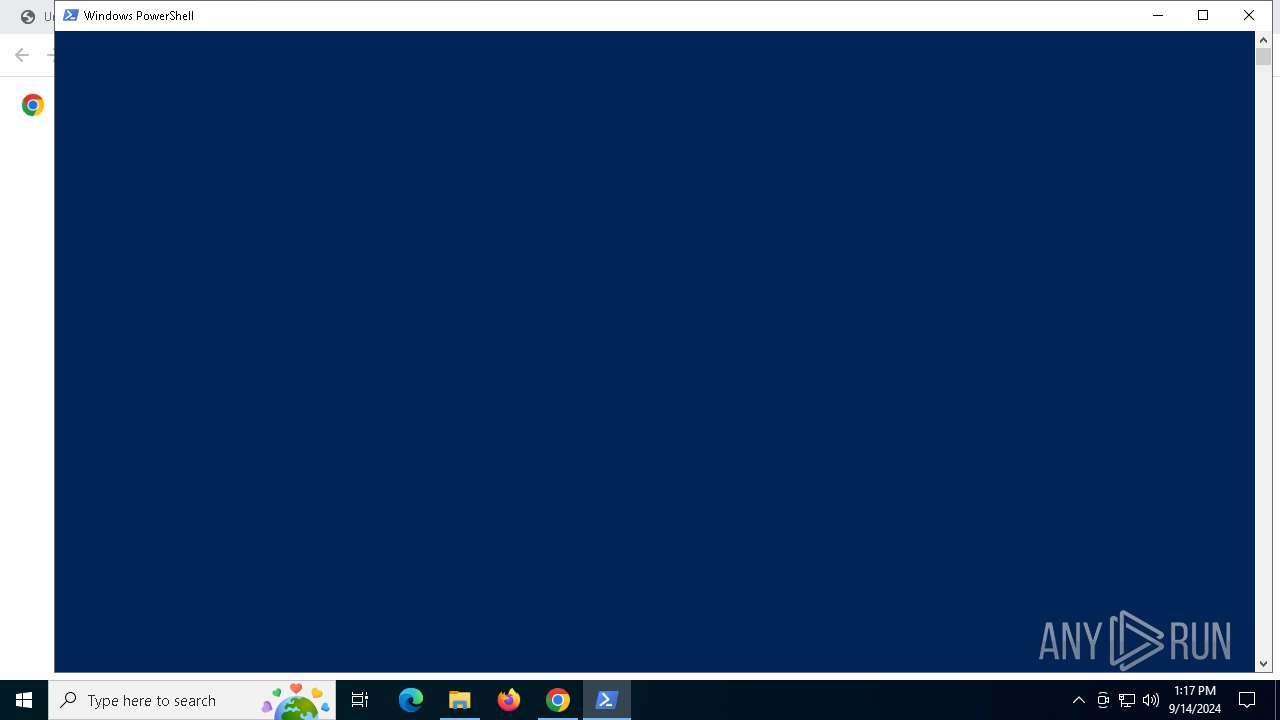
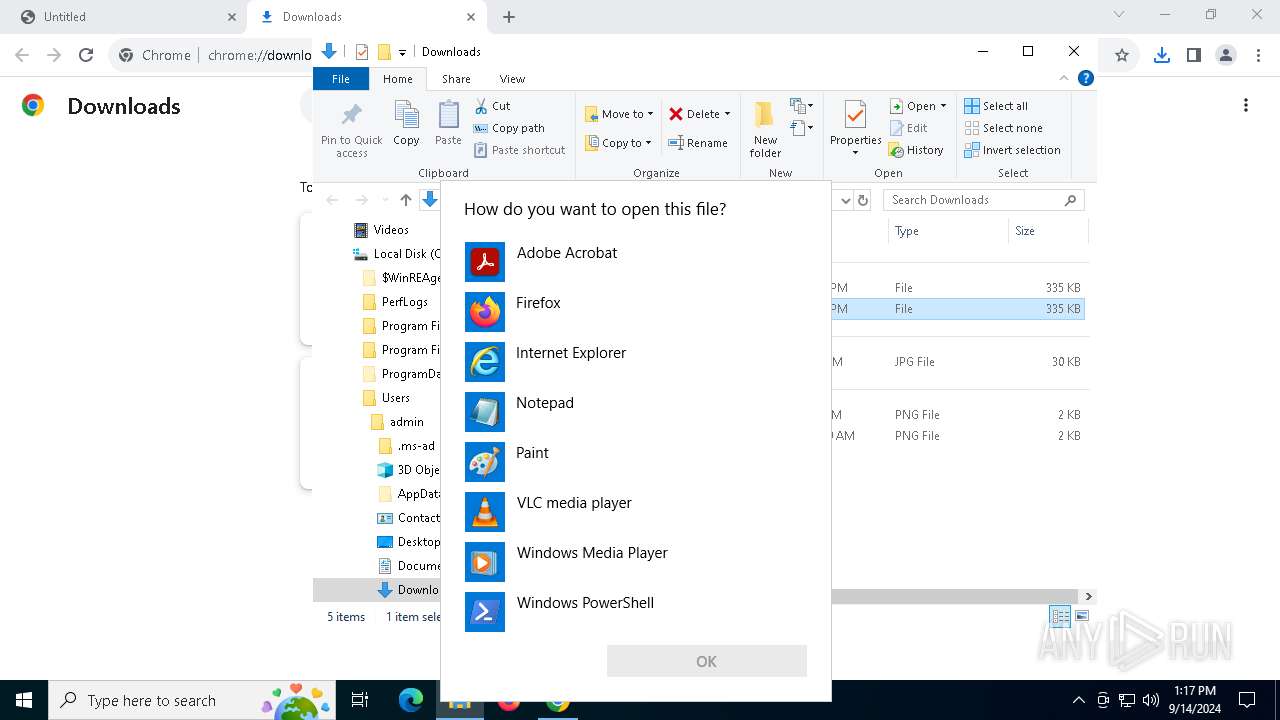
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 1360)
- OpenWith.exe (PID: 2400)
Reads security settings of Internet Explorer
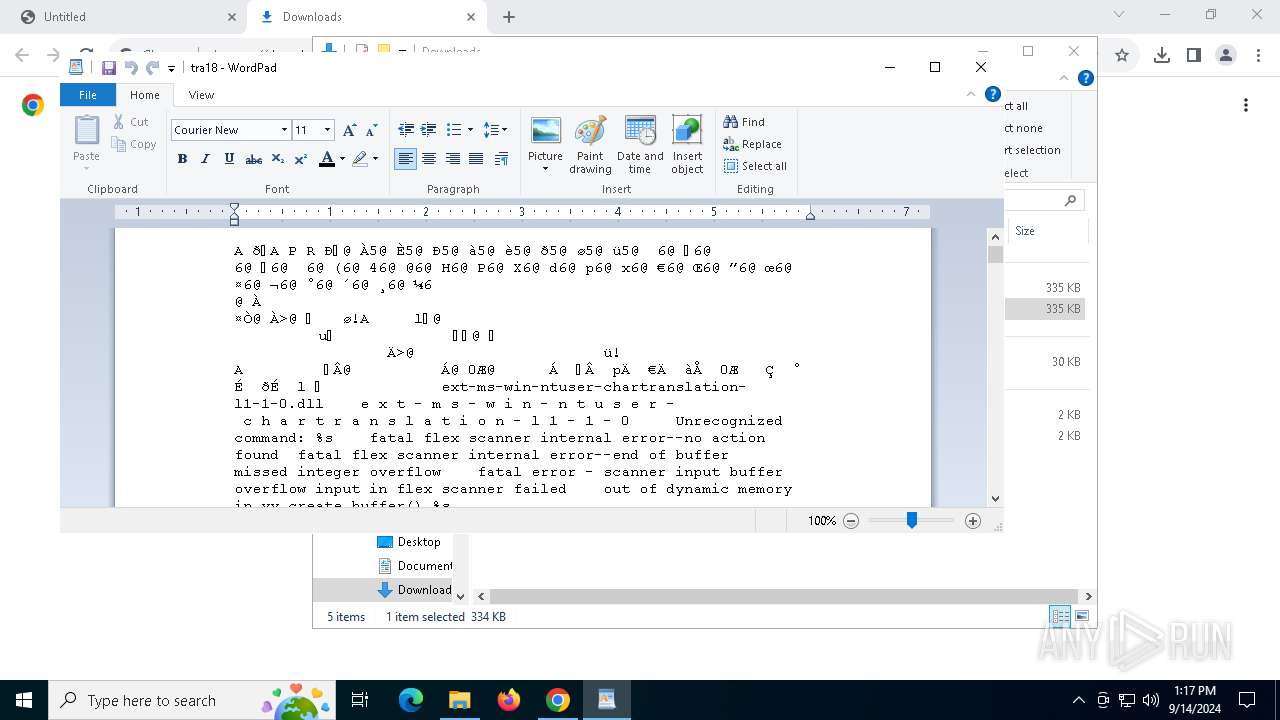
- wordpad.exe (PID: 5144)
Sets XML DOM element text (SCRIPT)
- wordpad.exe (PID: 5144)
Creates file in the systems drive root
- OpenWith.exe (PID: 300)
INFO
Application launched itself
- chrome.exe (PID: 4100)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 1360)
- OpenWith.exe (PID: 6268)
- OpenWith.exe (PID: 300)
- OpenWith.exe (PID: 2400)
- OpenWith.exe (PID: 2468)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 1360)
- OpenWith.exe (PID: 6268)
- OpenWith.exe (PID: 300)
- OpenWith.exe (PID: 2400)
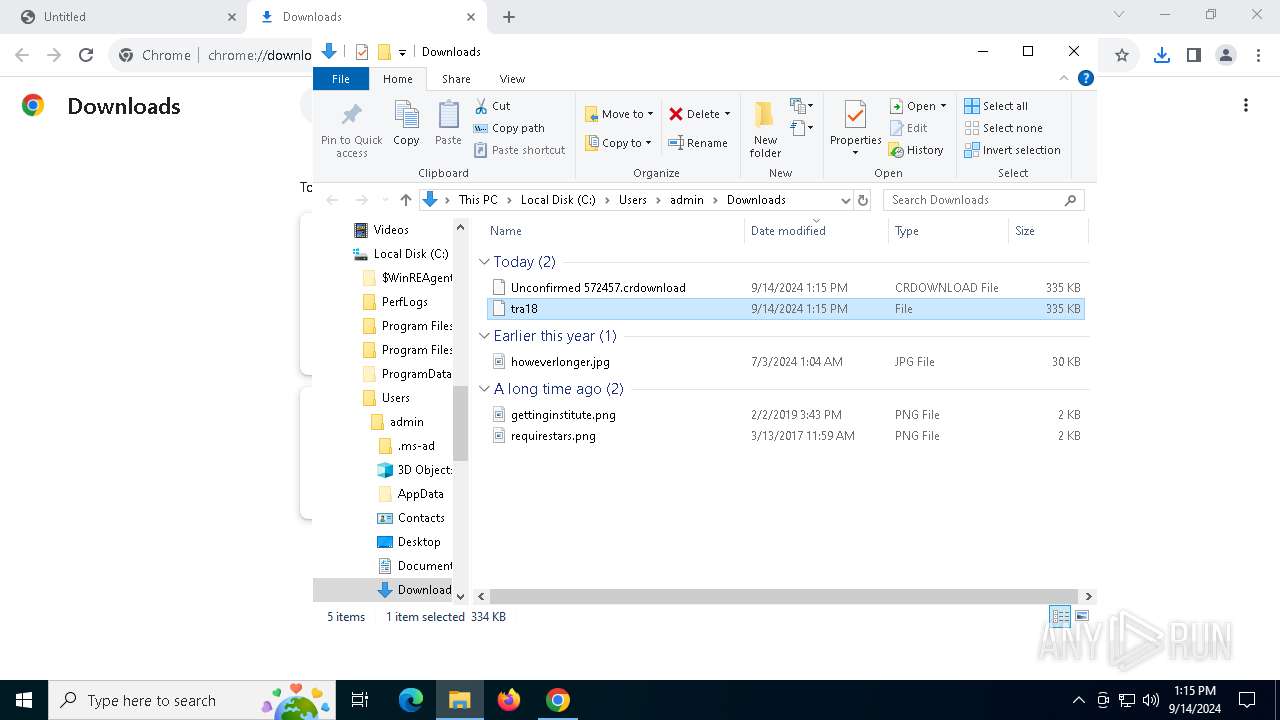
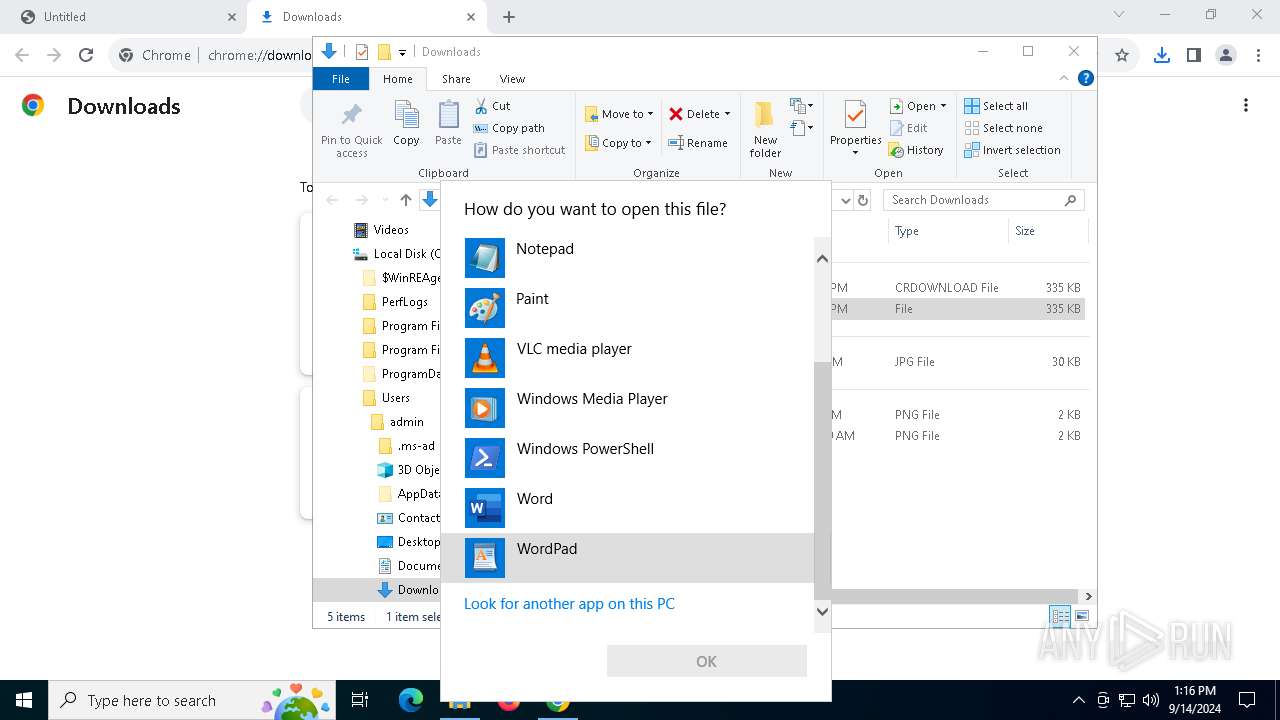
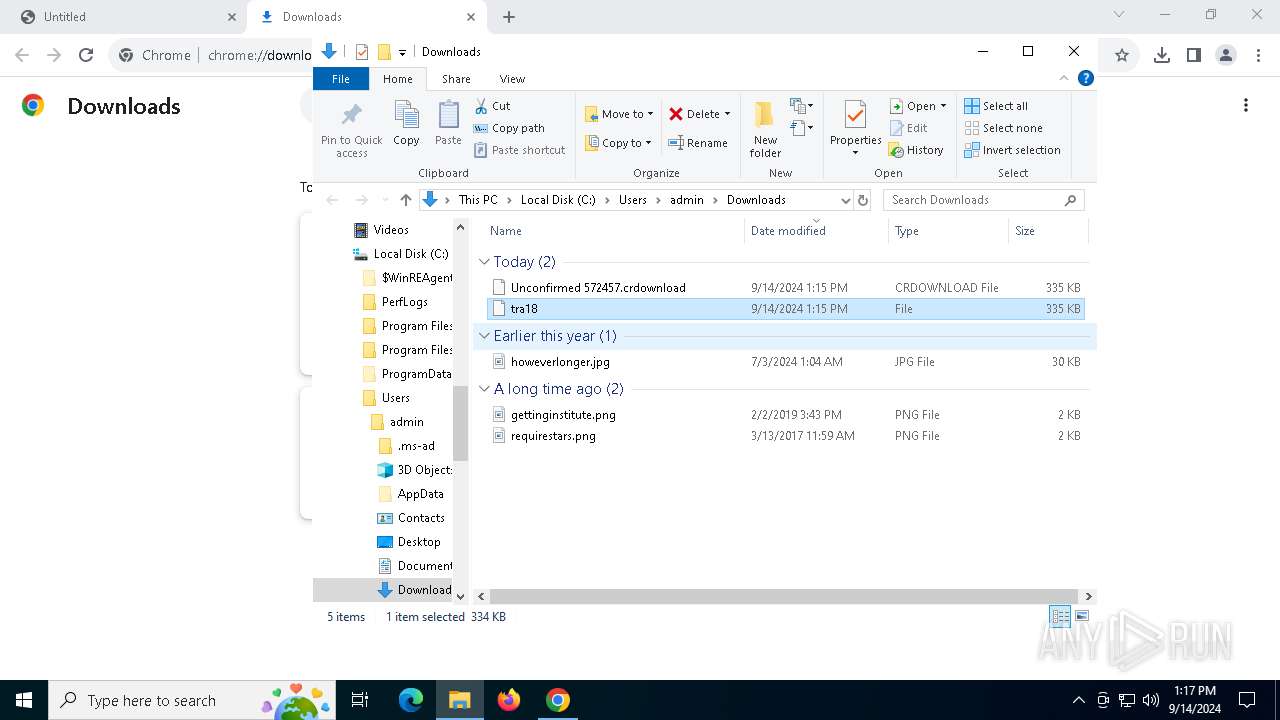
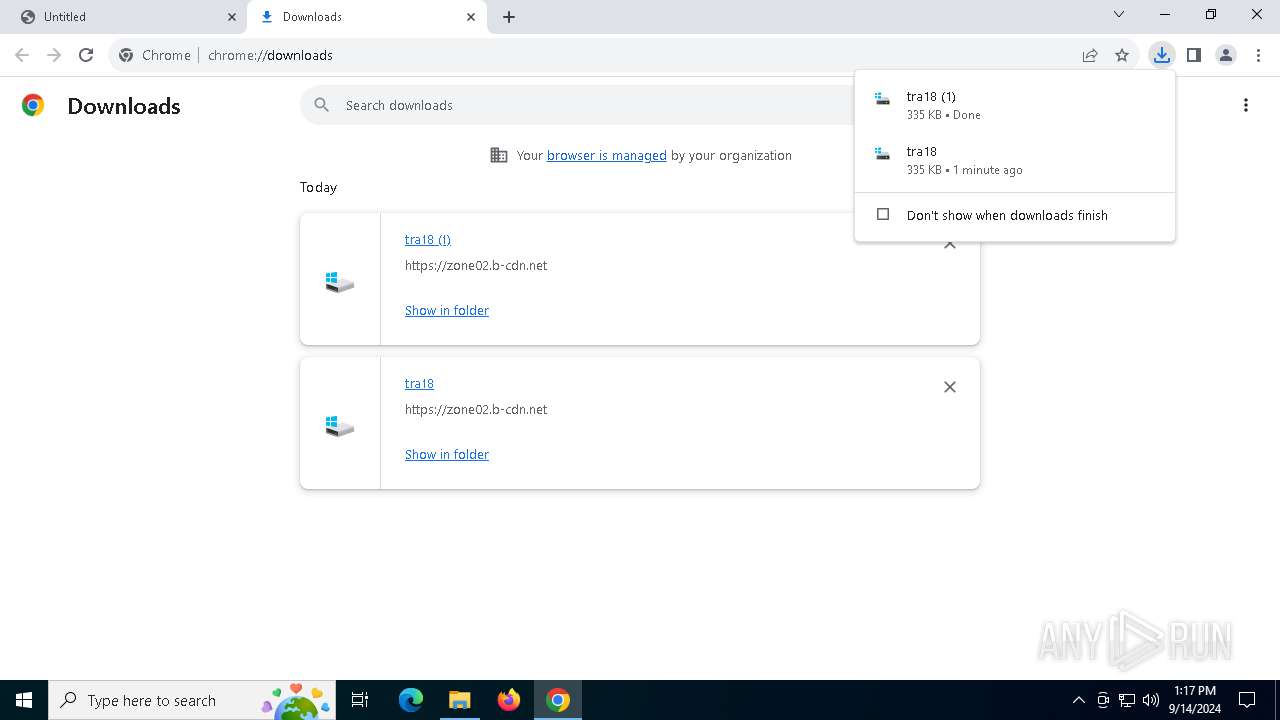
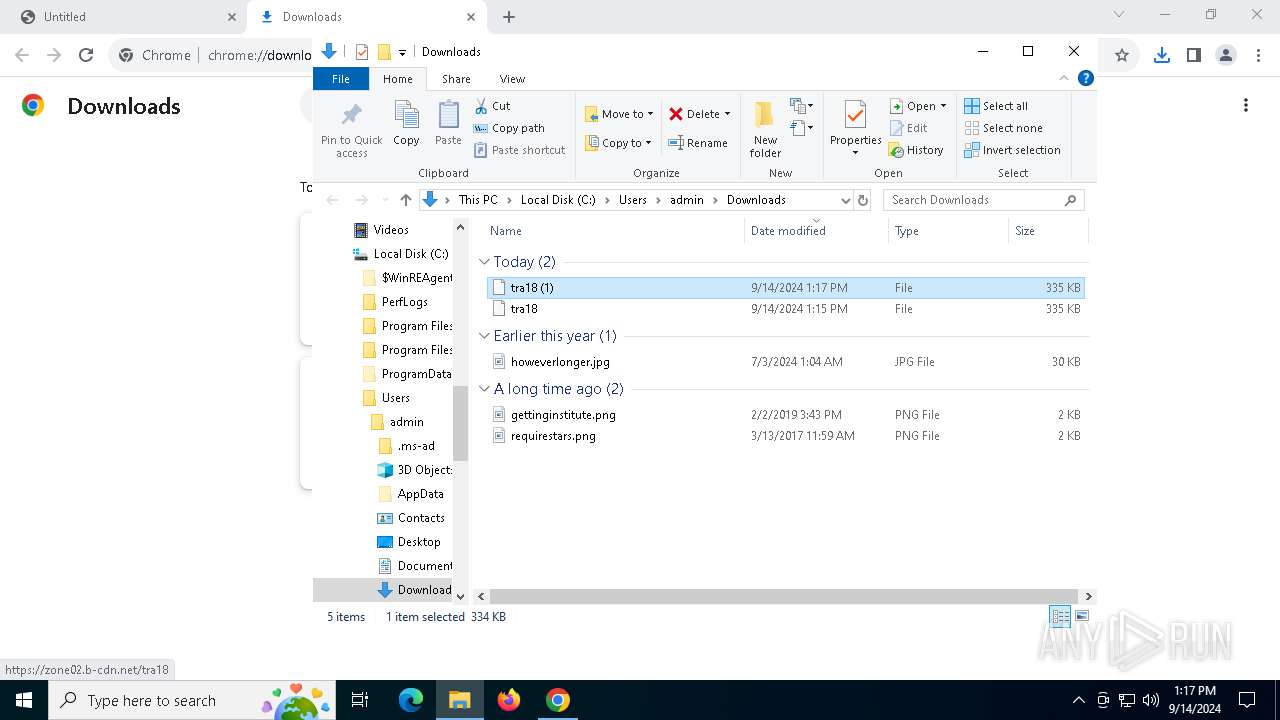
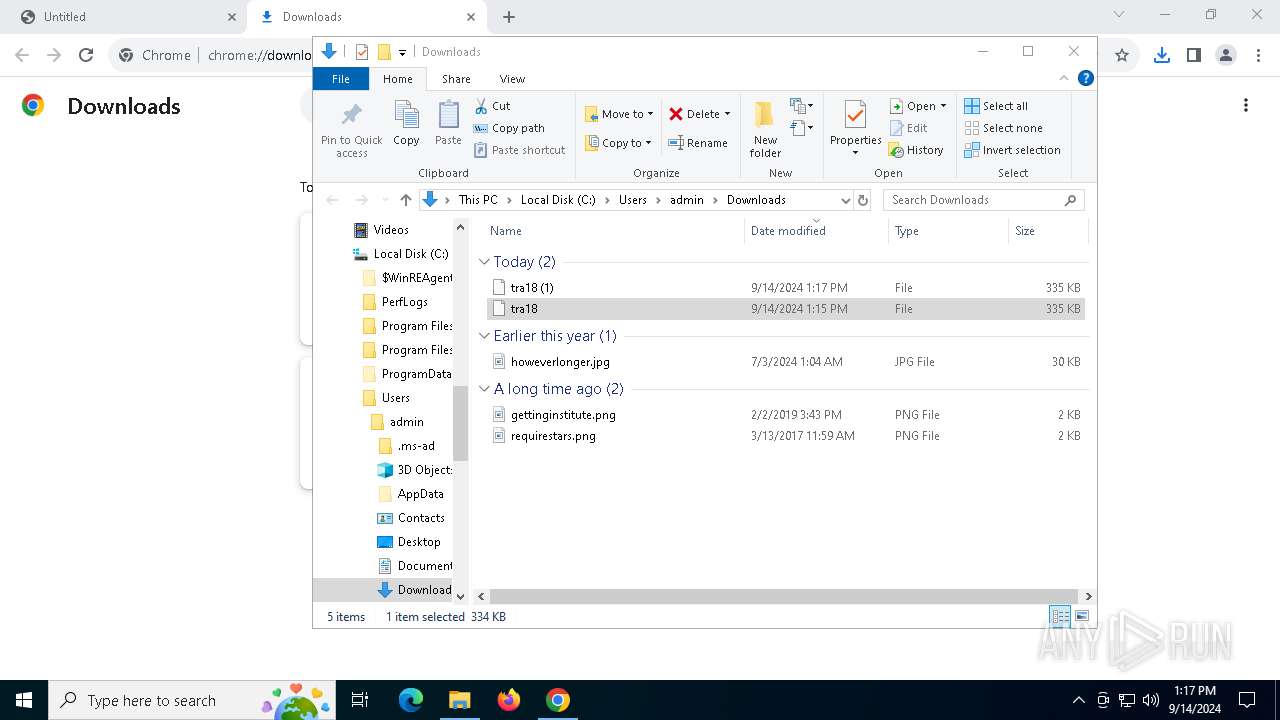
The process uses the downloaded file
- OpenWith.exe (PID: 1360)
- chrome.exe (PID: 1812)
- powershell.exe (PID: 5760)
- OpenWith.exe (PID: 6268)
- chrome.exe (PID: 6408)
- OpenWith.exe (PID: 2400)
- powershell.exe (PID: 2040)
Executable content was dropped or overwritten
- chrome.exe (PID: 4100)
Checks supported languages
- wordpad.exe (PID: 5144)
Reads the computer name
- wordpad.exe (PID: 5144)
Reads Environment values
- wordpad.exe (PID: 5144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
154
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1360 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5400 --field-trial-handle=1896,i,1140797878184338087,14690737820886249074,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4220 --field-trial-handle=1896,i,1140797878184338087,14690737820886249074,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4220 --field-trial-handle=1896,i,1140797878184338087,14690737820886249074,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
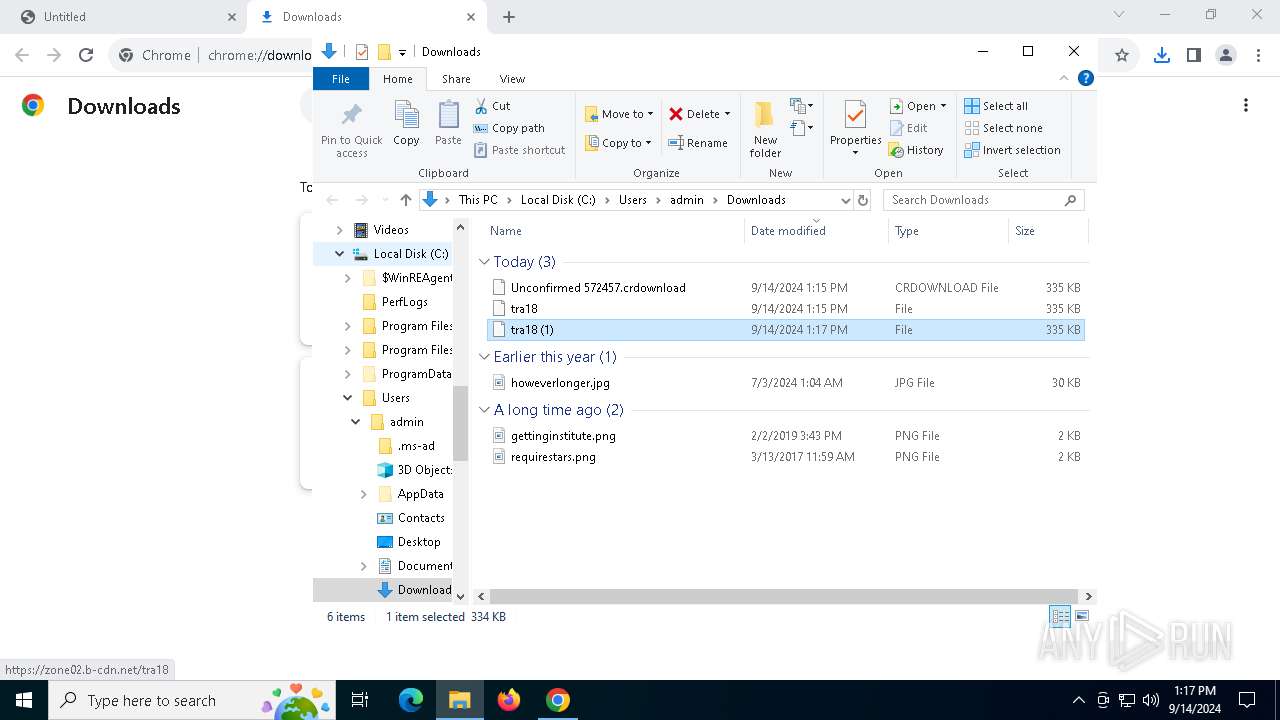
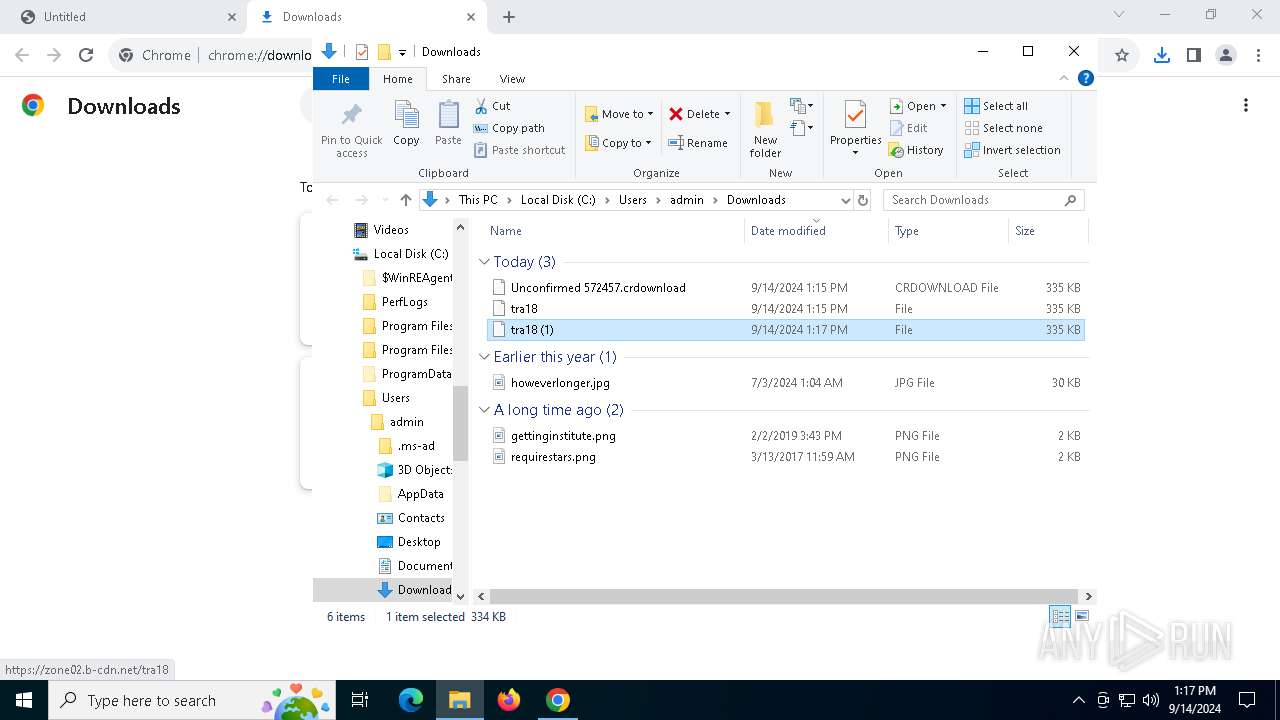
| 2040 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "C:\Users\admin\Downloads\tra18" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | OpenWith.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2400 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2468 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://zone02.b-cdn.net/tra18" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
23 981
Read events
23 913
Write events
60
Delete events
8
Modification events
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000003982C837A806DB01 | |||
| (PID) Process: | (5144) wordpad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wordpad.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: AA83130000000000 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (4100) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
Executable files
11
Suspicious files
99
Text files
28
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF12aef5.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF12af05.TMP | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\43797186-e920-4f90-a7a1-a81218b0ce52.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 4100 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
27
DNS requests
28
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6232 | svchost.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2128 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2128 | svchost.exe | HEAD | 200 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2128 | svchost.exe | GET | 206 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2128 | svchost.exe | GET | 206 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2128 | svchost.exe | GET | 206 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2128 | svchost.exe | GET | 206 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2128 | svchost.exe | GET | 206 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
2128 | svchost.exe | GET | 206 | 216.58.213.110:80 | http://dl.google.com/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6232 | svchost.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6232 | svchost.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.44.239.154:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5220 | chrome.exe | 185.59.220.198:443 | zone02.b-cdn.net | Datacamp Limited | DE | whitelisted |
4100 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5220 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
zone02.b-cdn.net |
| whitelisted |
accounts.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5220 | chrome.exe | Domain Observed Used for C2 Detected | ET MALWARE DNS Query to Lumma Stealer Domain (zone02 .b-cdn .net) |
5220 | chrome.exe | Domain Observed Used for C2 Detected | ET MALWARE DNS Query to Lumma Stealer Domain (zone02 .b-cdn .net) |
5220 | chrome.exe | Domain Observed Used for C2 Detected | ET MALWARE DNS Query to Lumma Stealer Domain (zone02 .b-cdn .net) |
5220 | chrome.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Domain (zone02 .b-cdn .net in TLS SNI) |