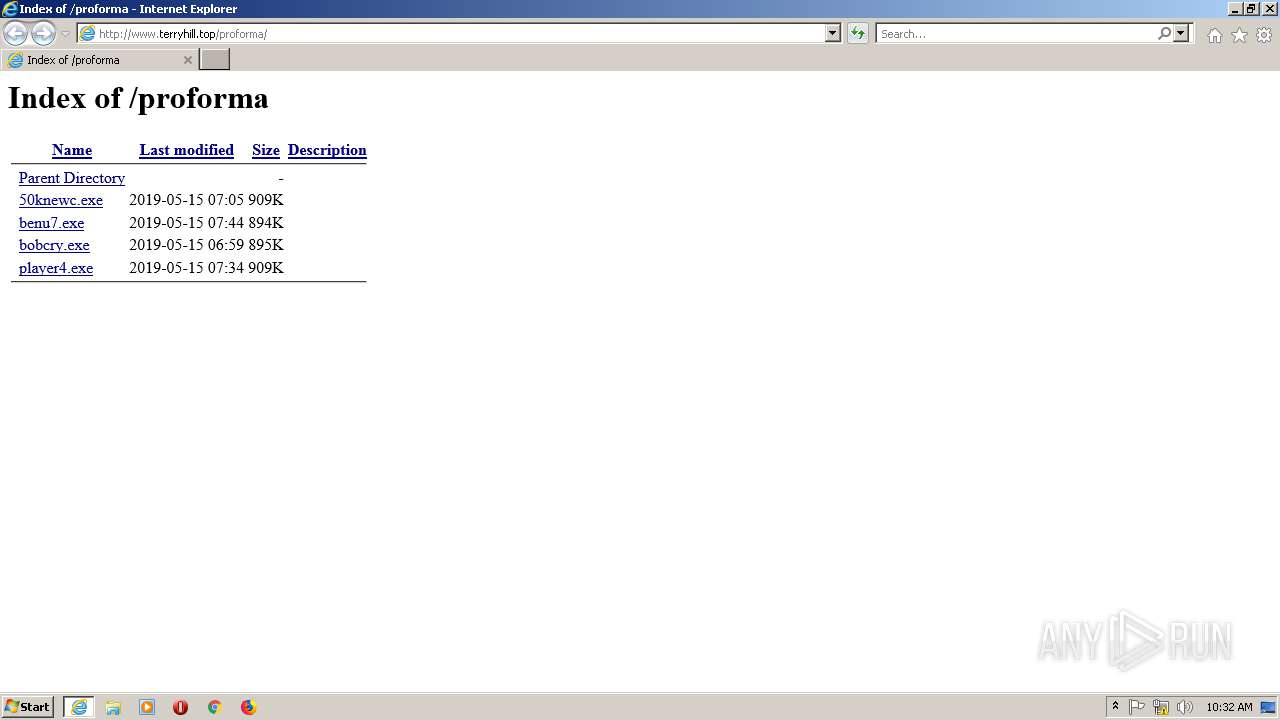
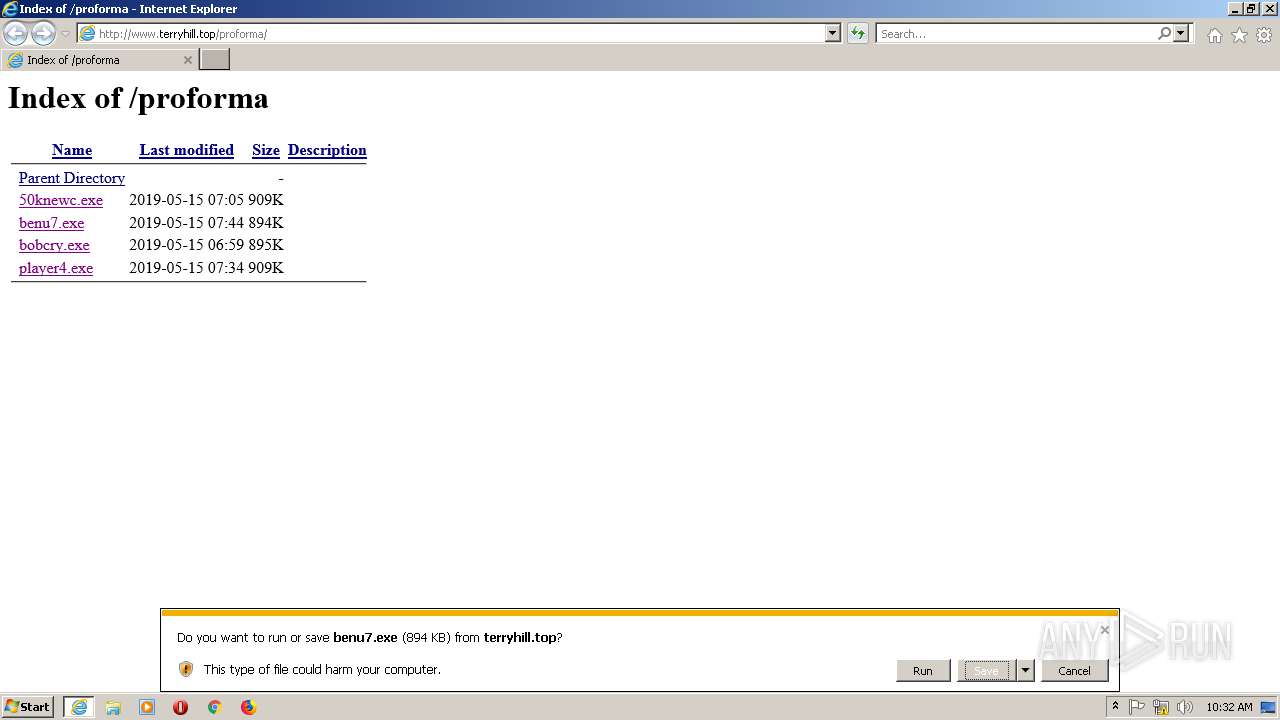
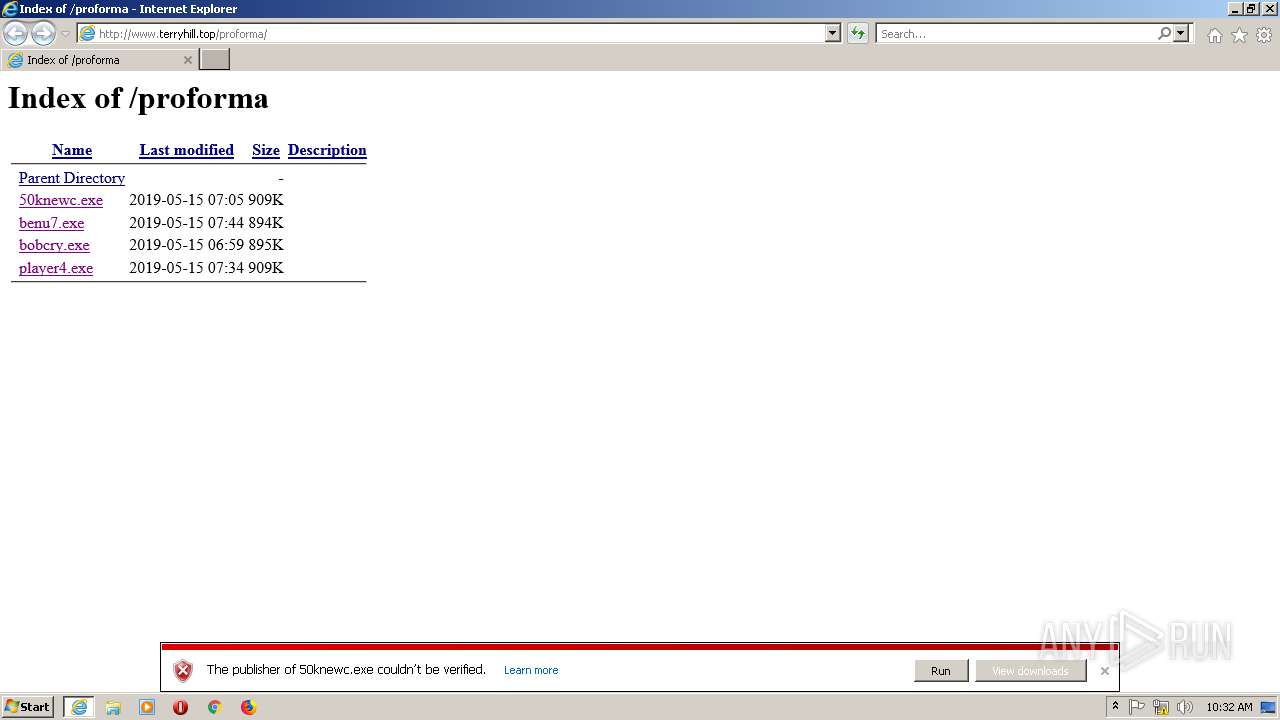
| URL: | http://www.terryhill.top/proforma/ |
| Full analysis: | https://app.any.run/tasks/3e1a0995-f4f6-4b0b-bdad-263b19c28eb8 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | May 15, 2019, 10:31:53 |
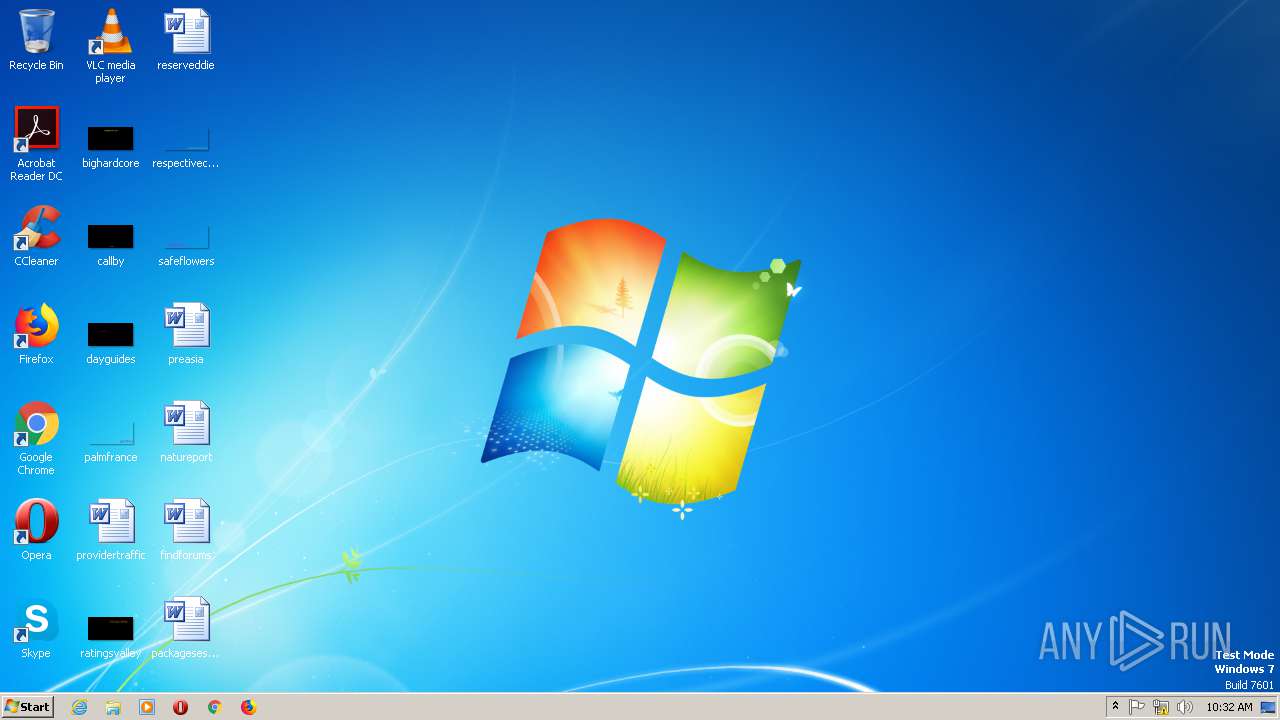
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3A7DE59B8BD73B64B19D716674CA3E19 |
| SHA1: | 80638C4AAD05385295BF870CAA166786EECCC7D4 |
| SHA256: | 4732CBB36F2E3F31E49233F6DAEB7280A724F421F91C29920C172883294A7656 |
| SSDEEP: | 3:N1KJS4S80L5Ij:Cc4S8pj |
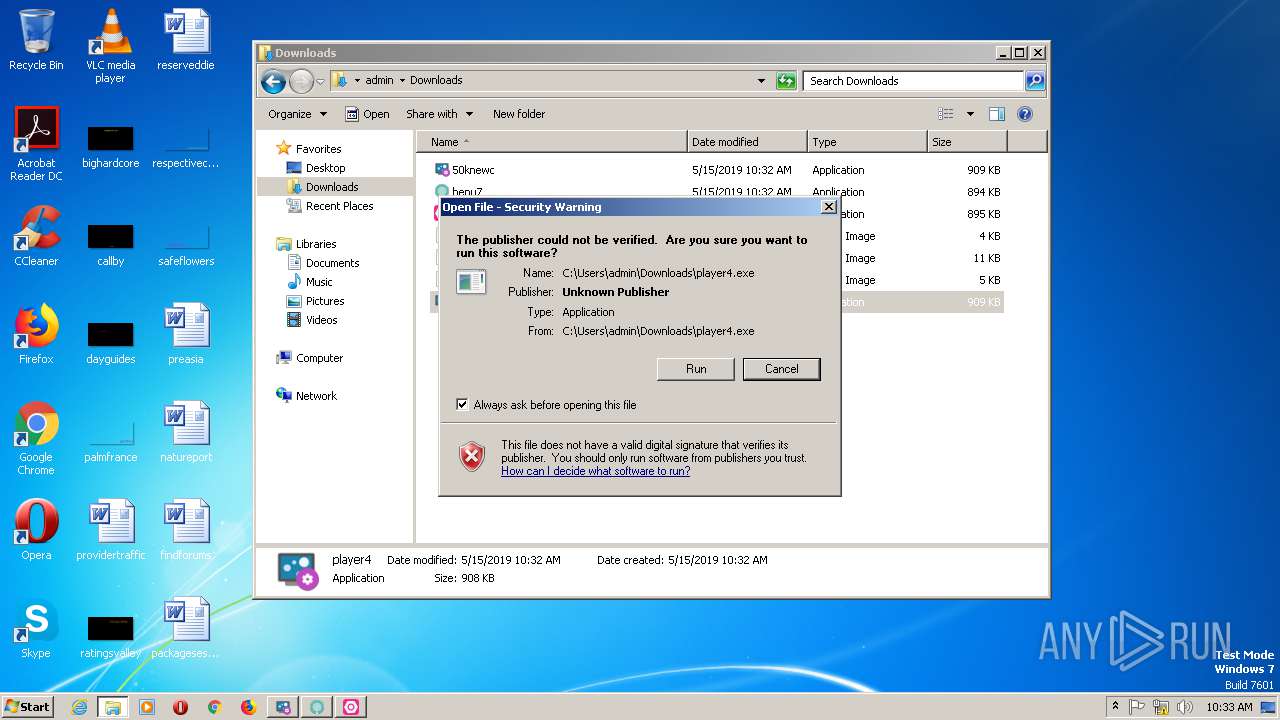
MALICIOUS
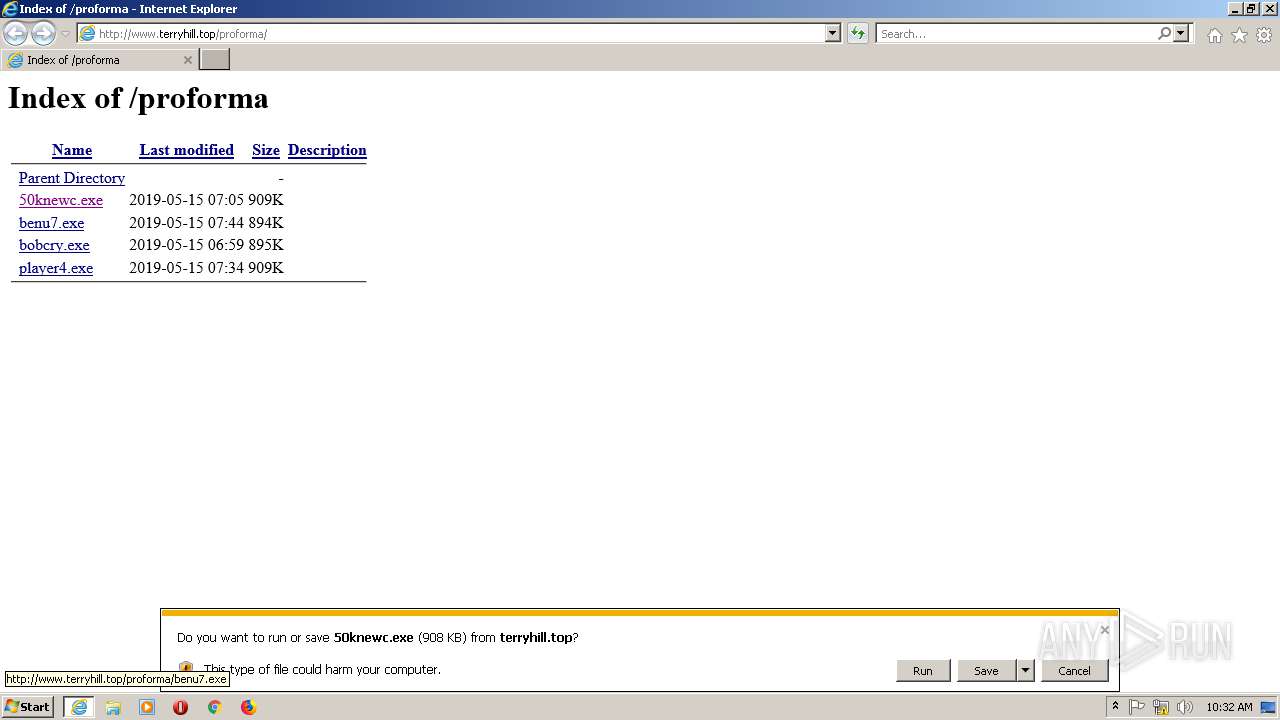
Downloads executable files from the Internet
- IEXPLORE.EXE (PID: 2816)
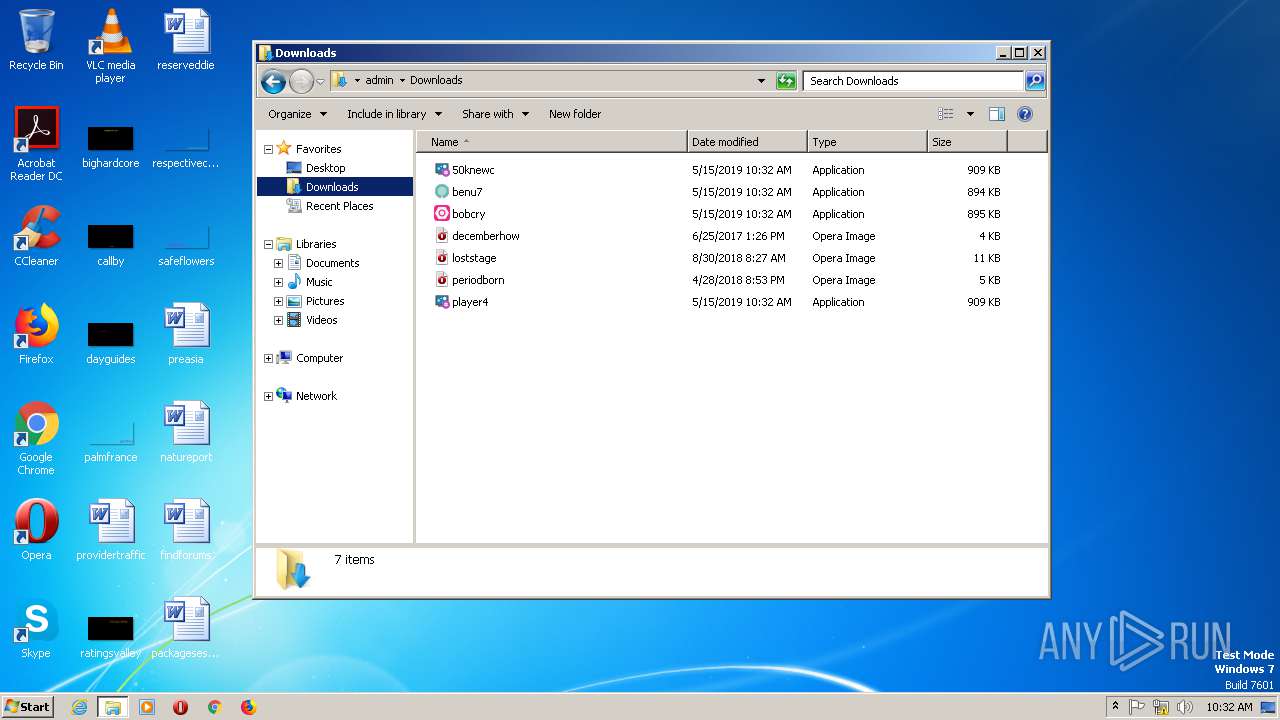
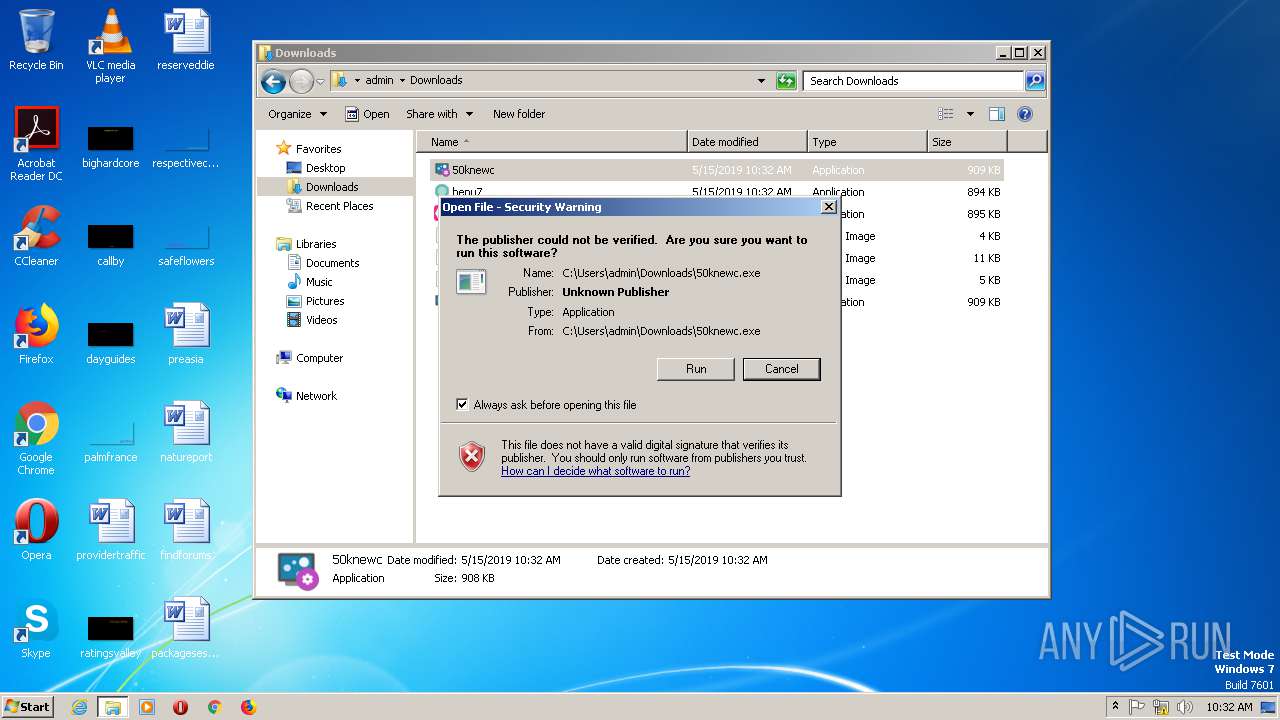
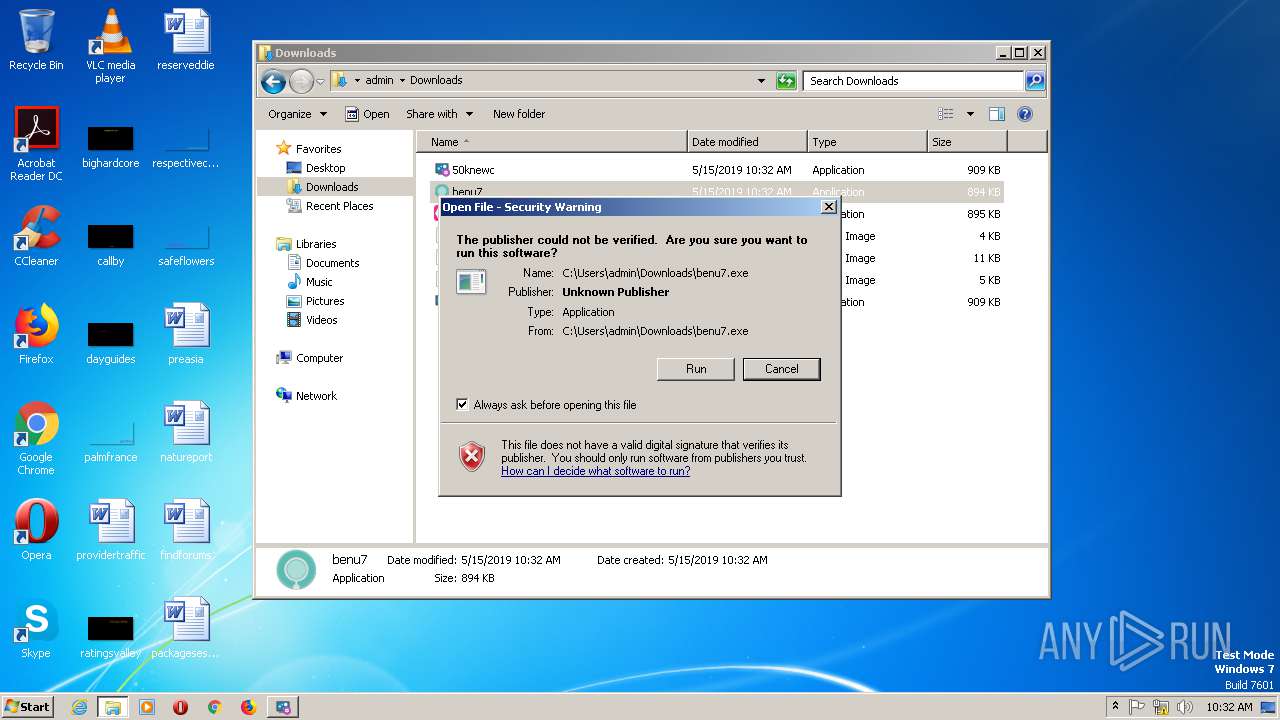
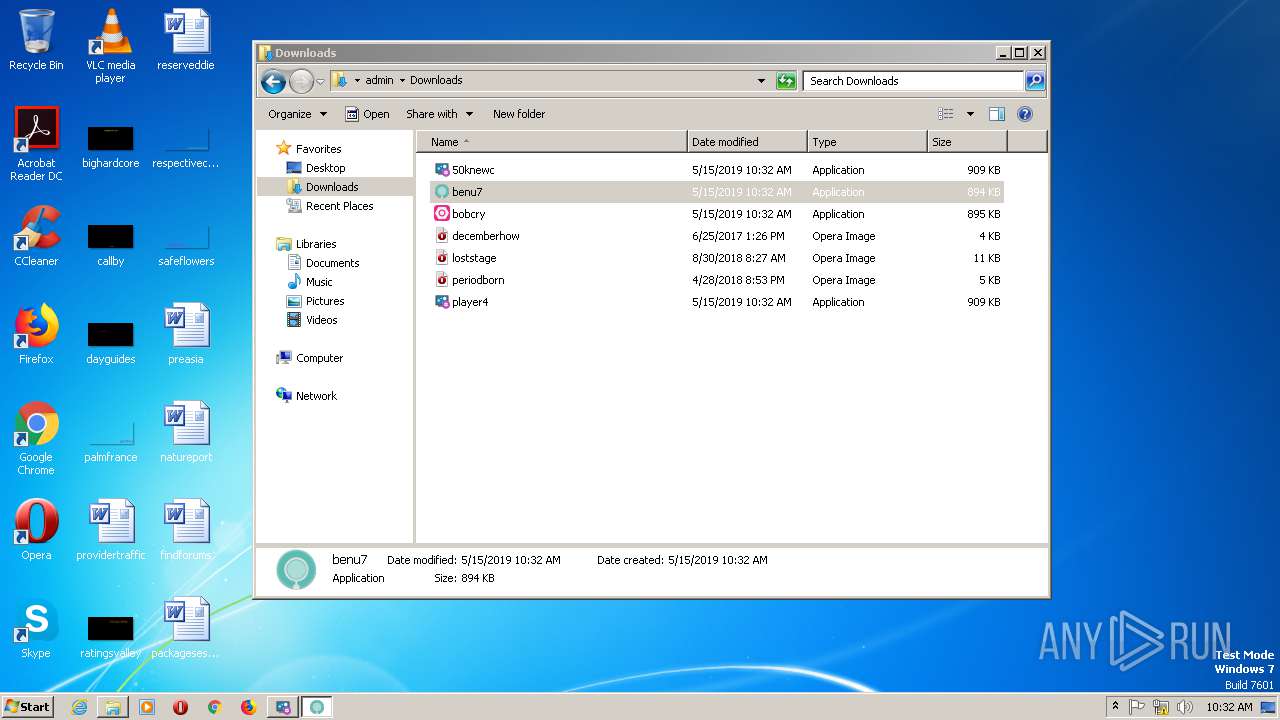
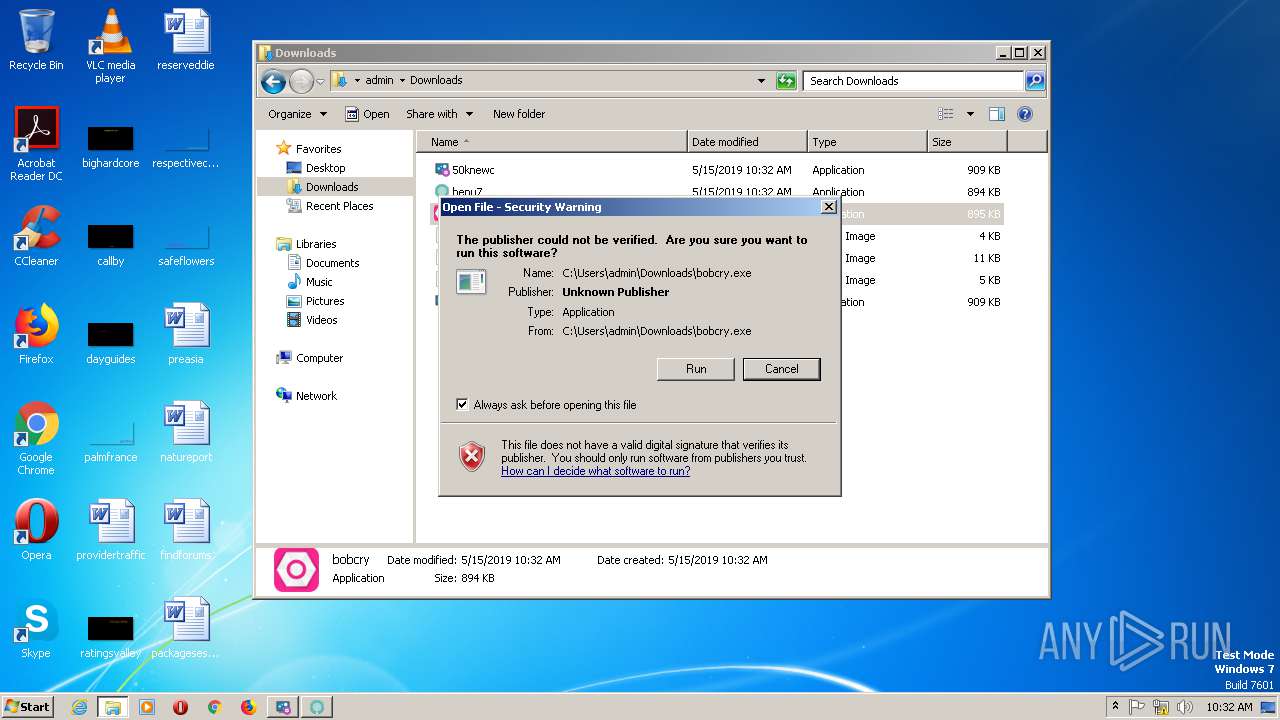
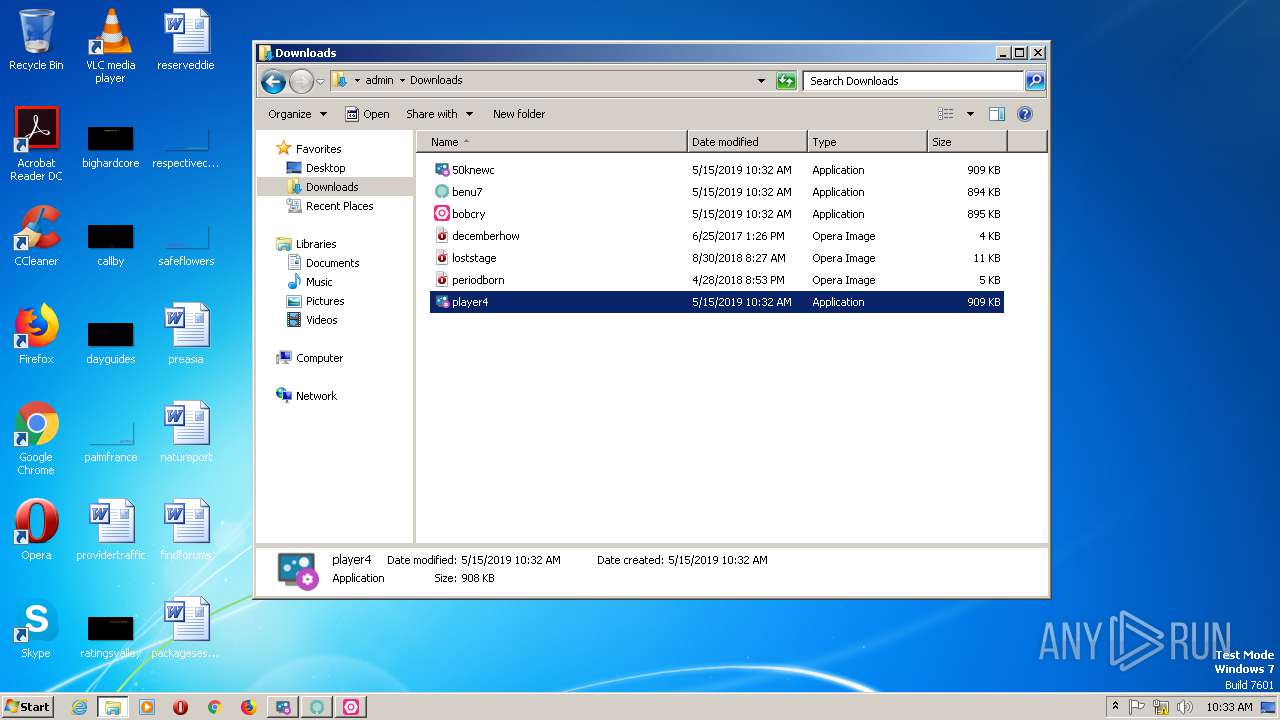
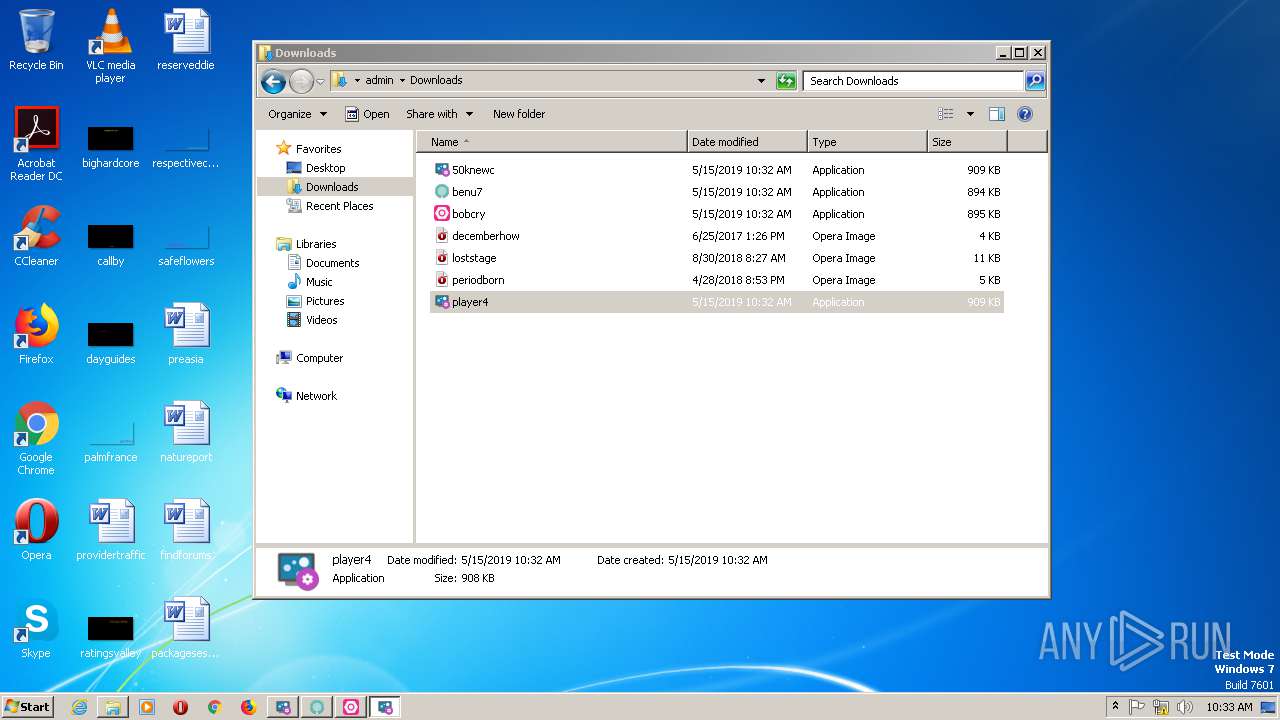
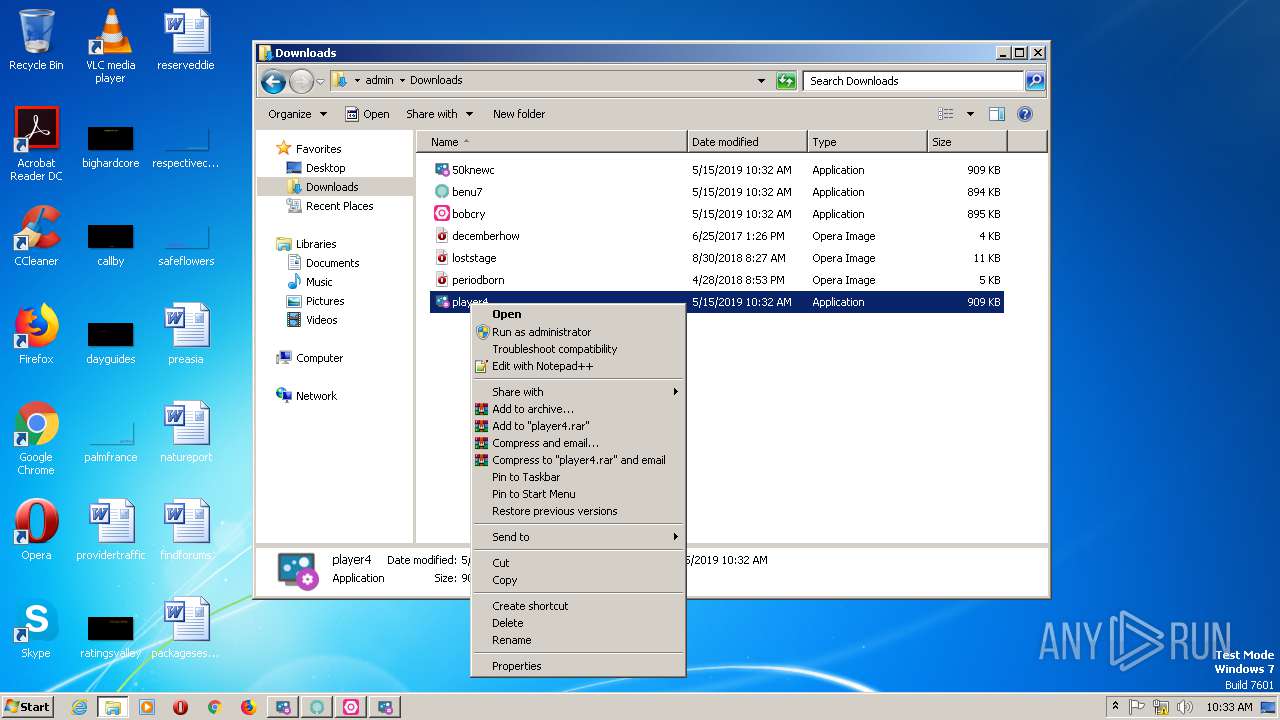
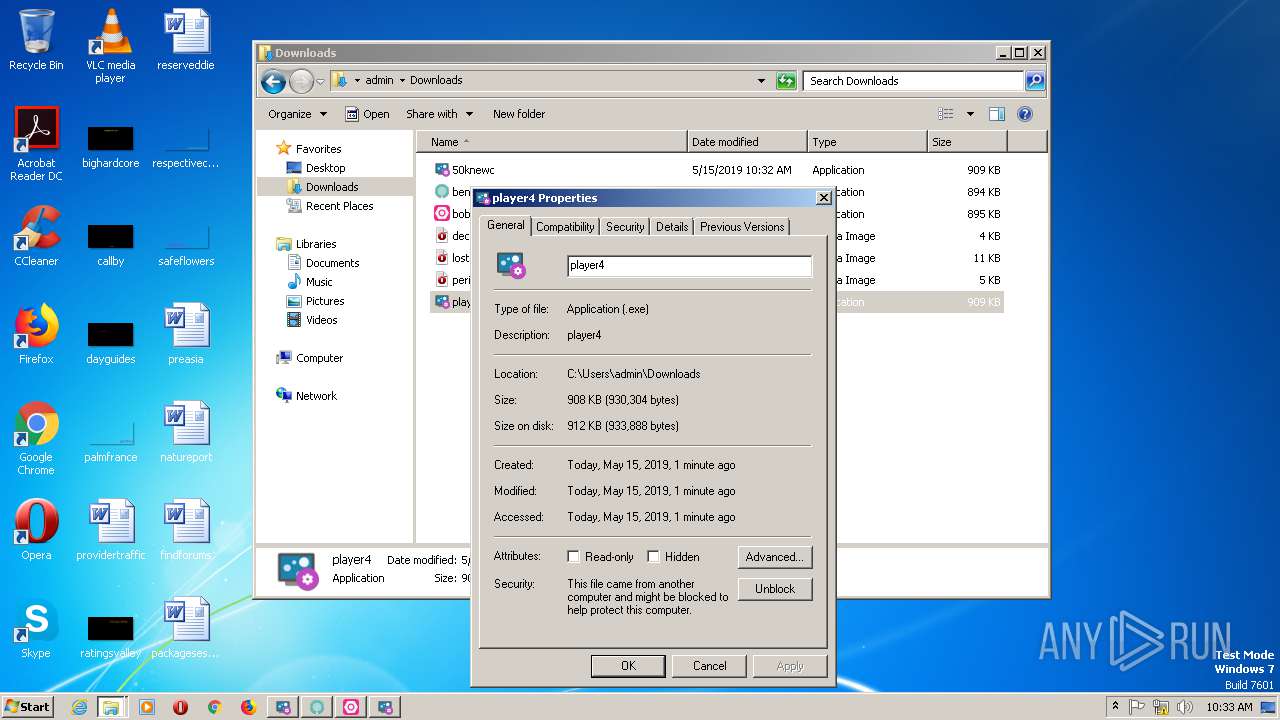
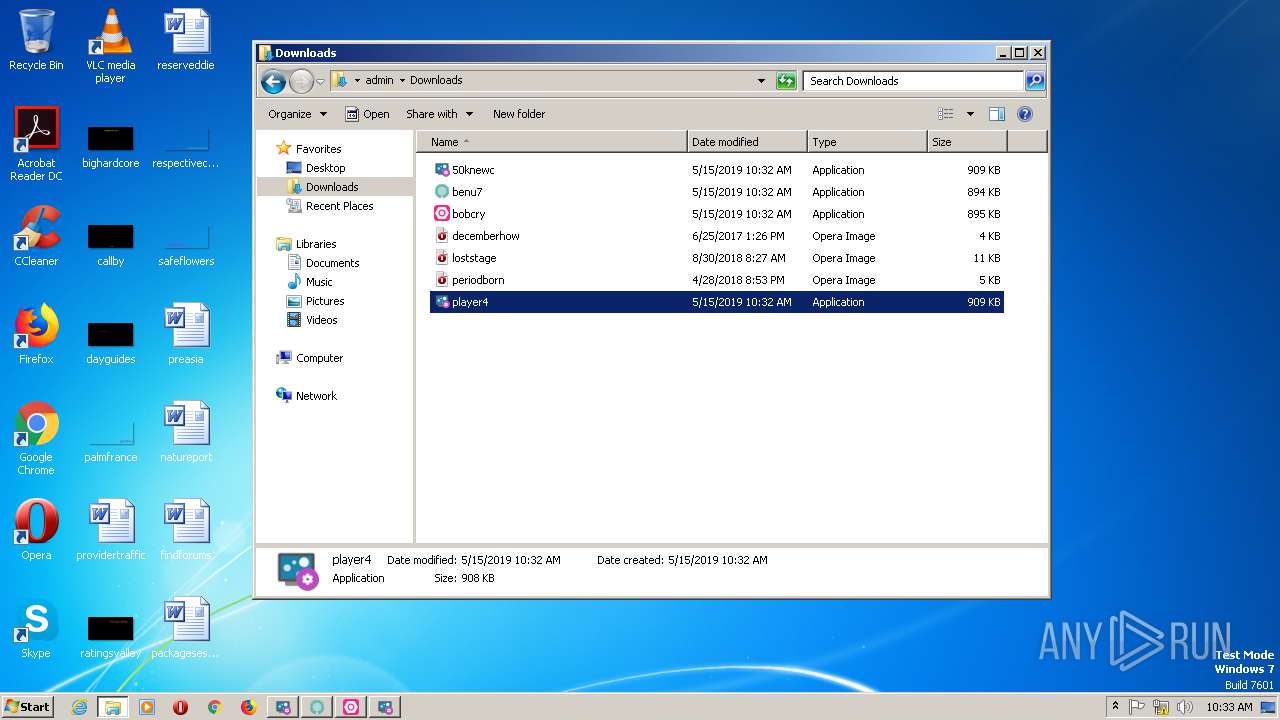
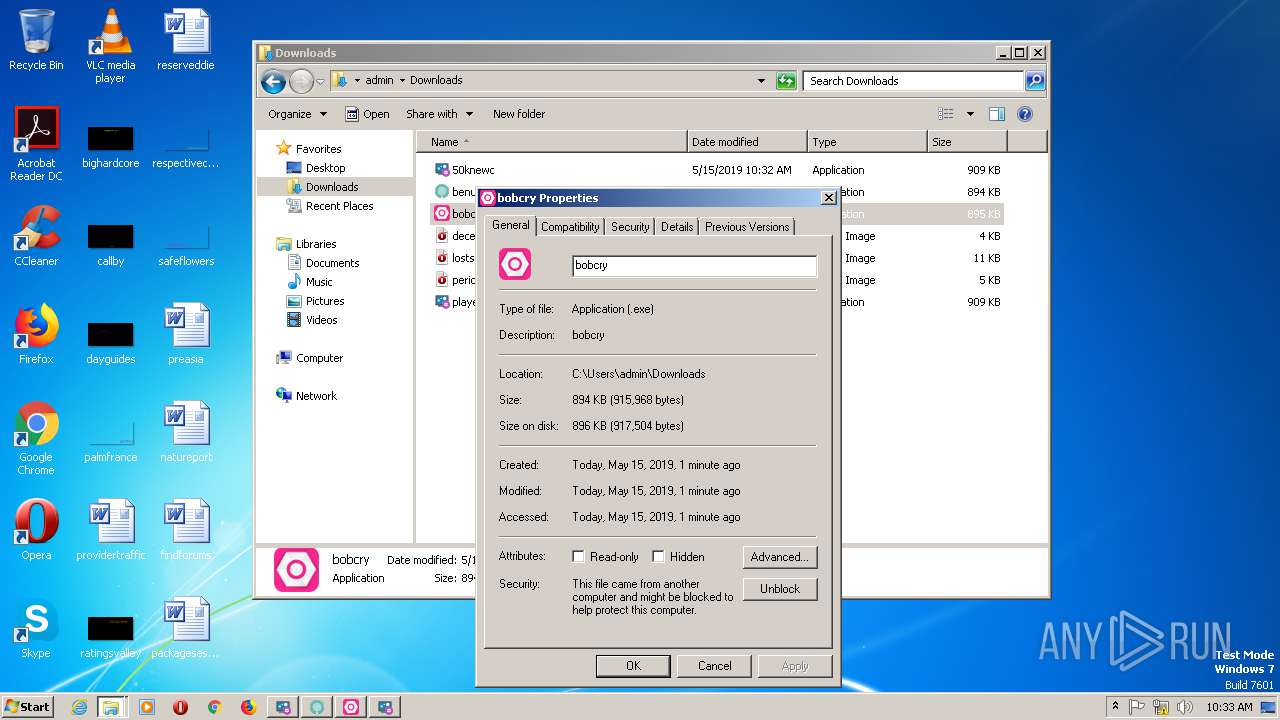
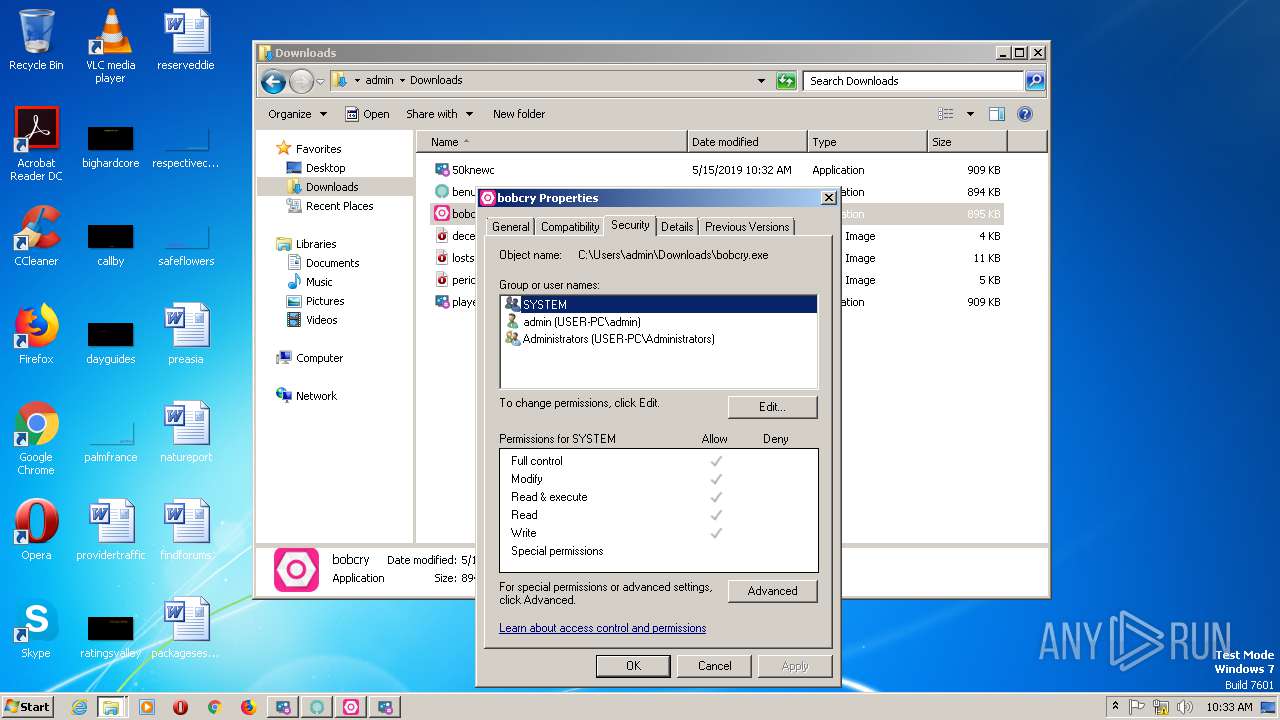
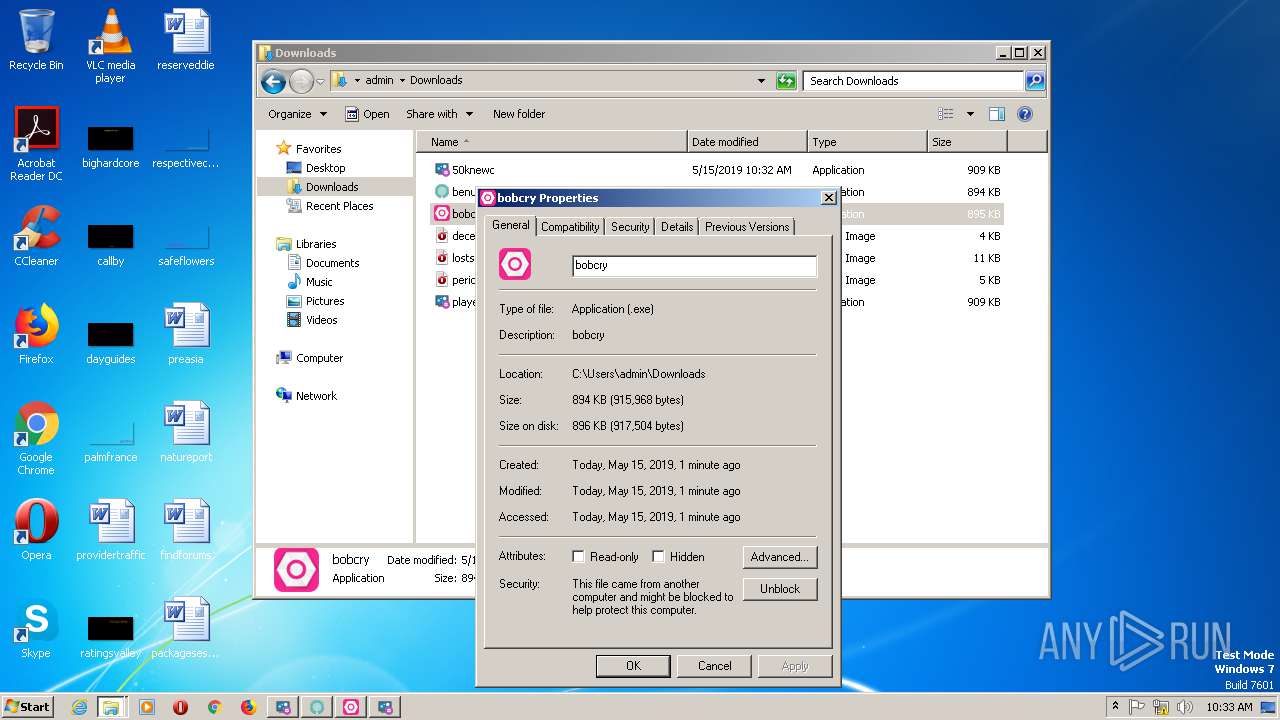
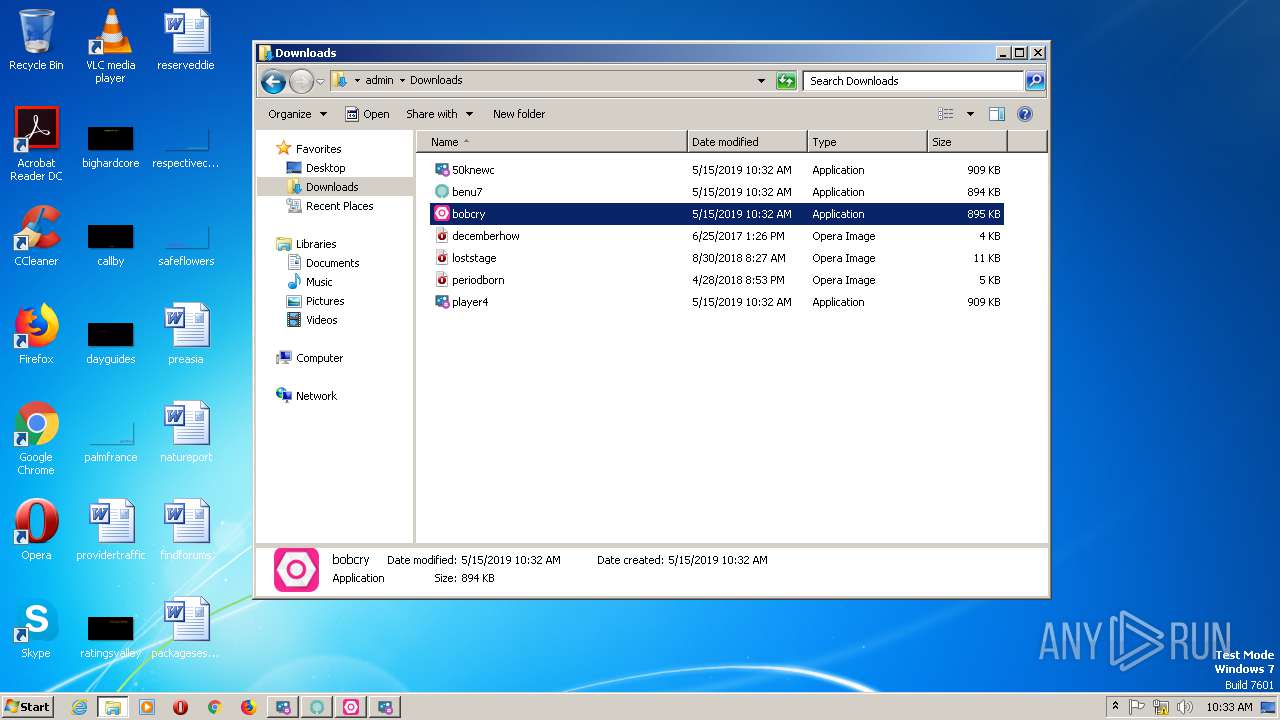
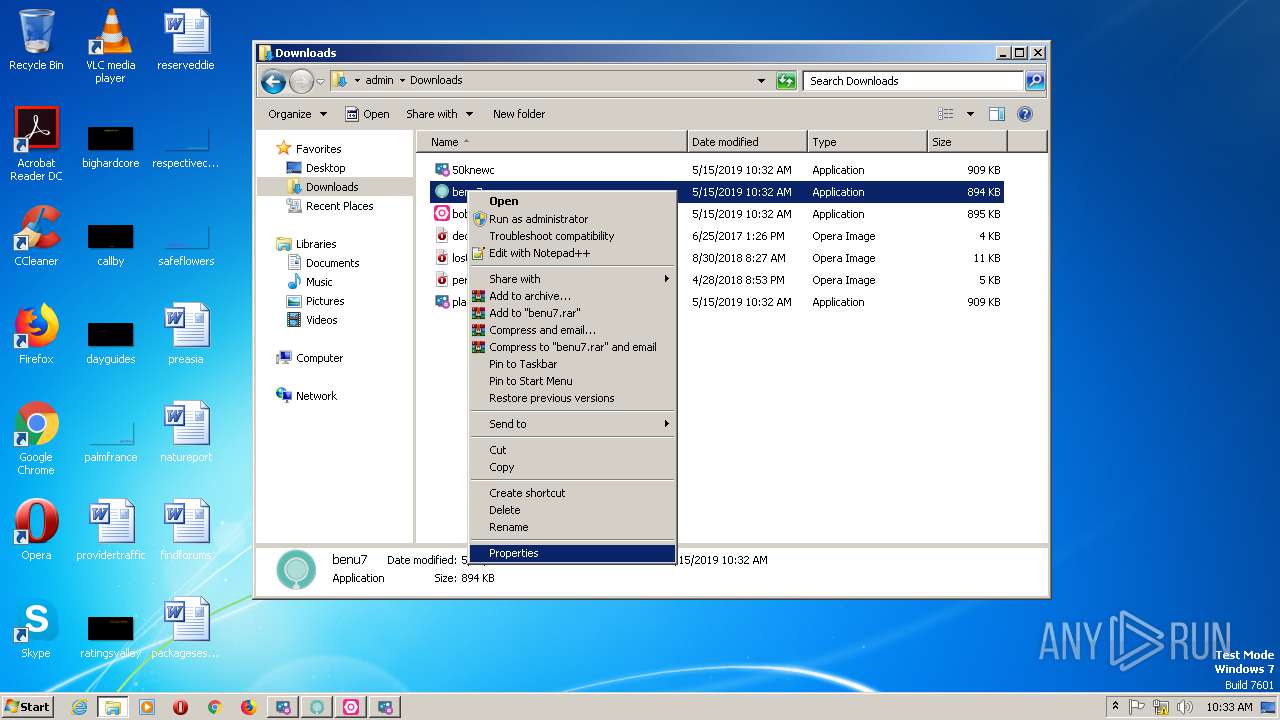
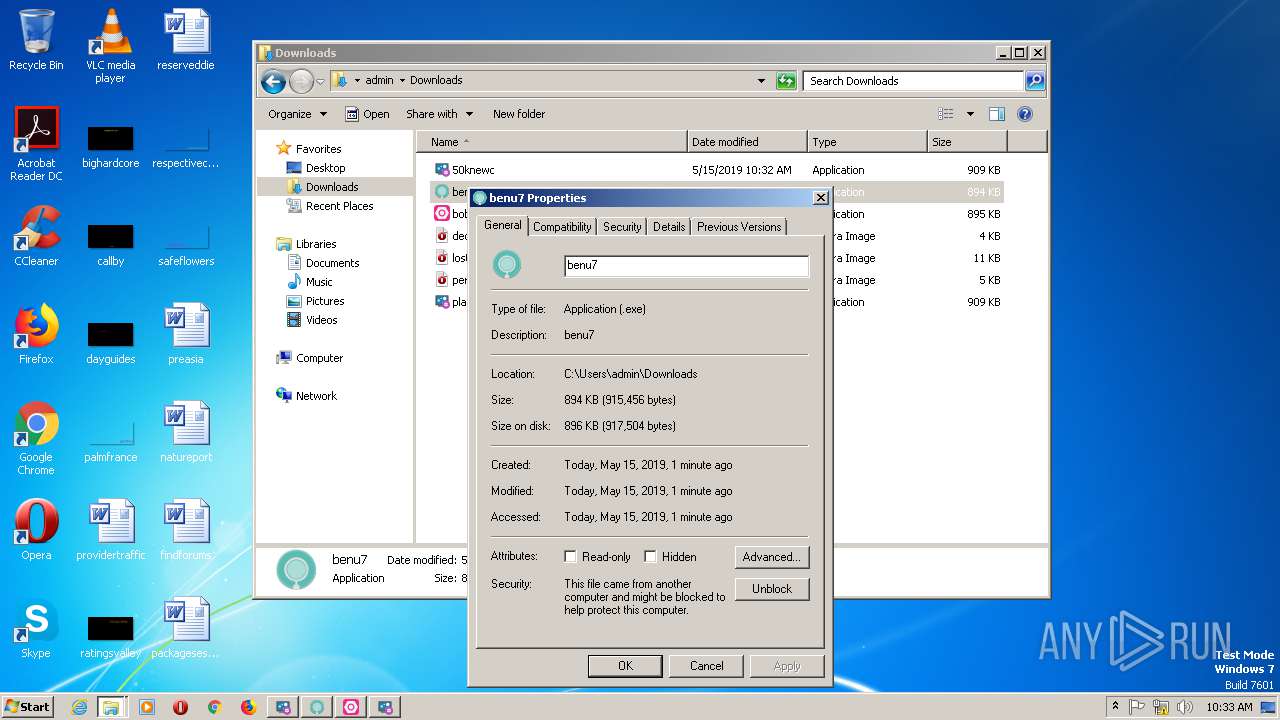
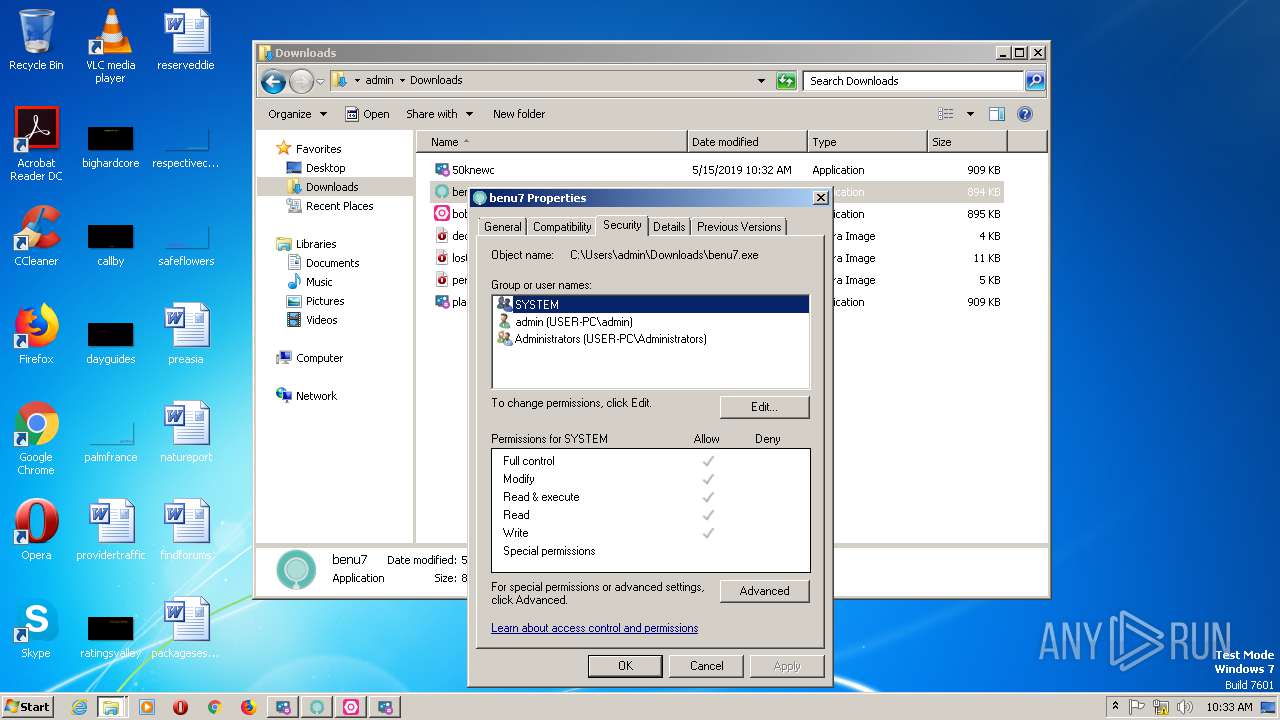
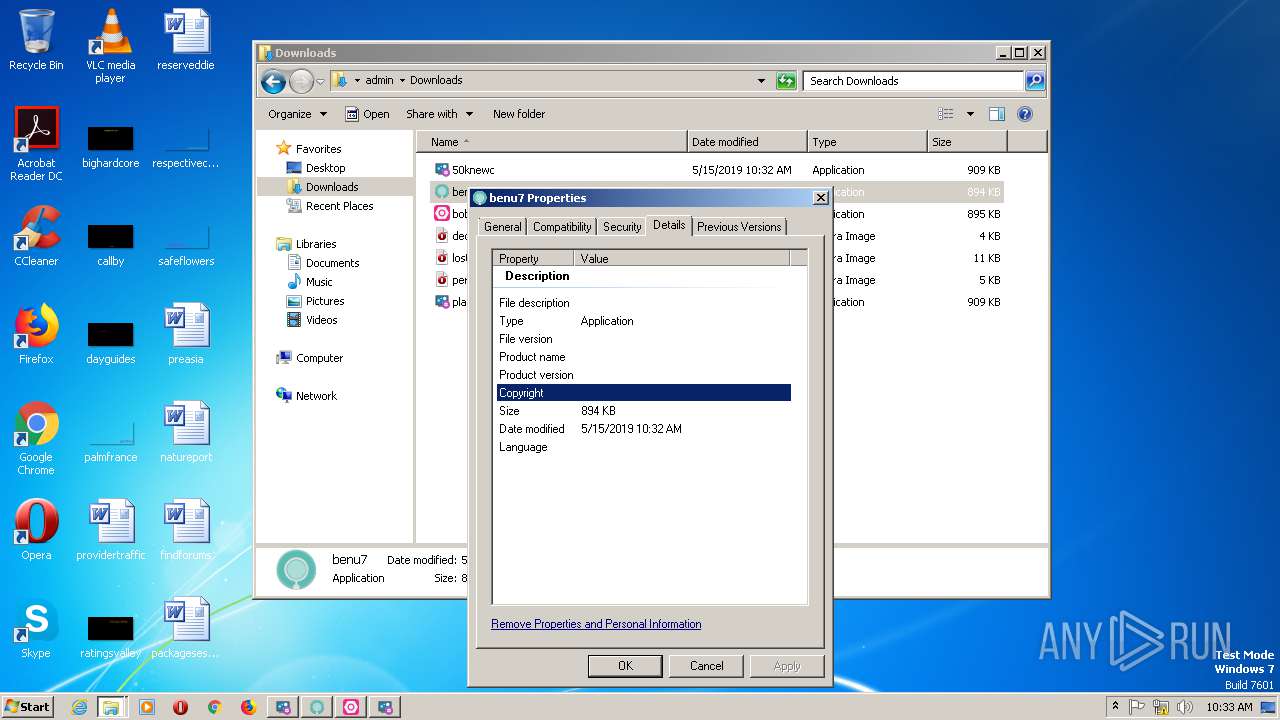
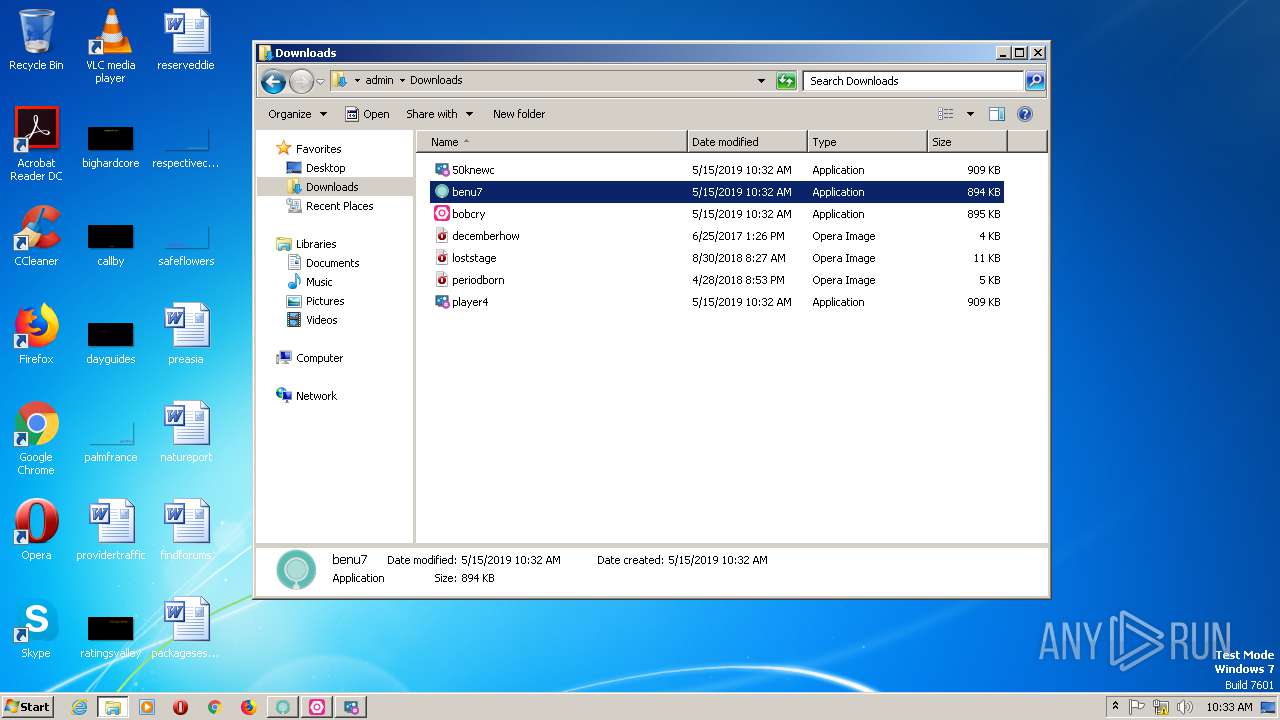
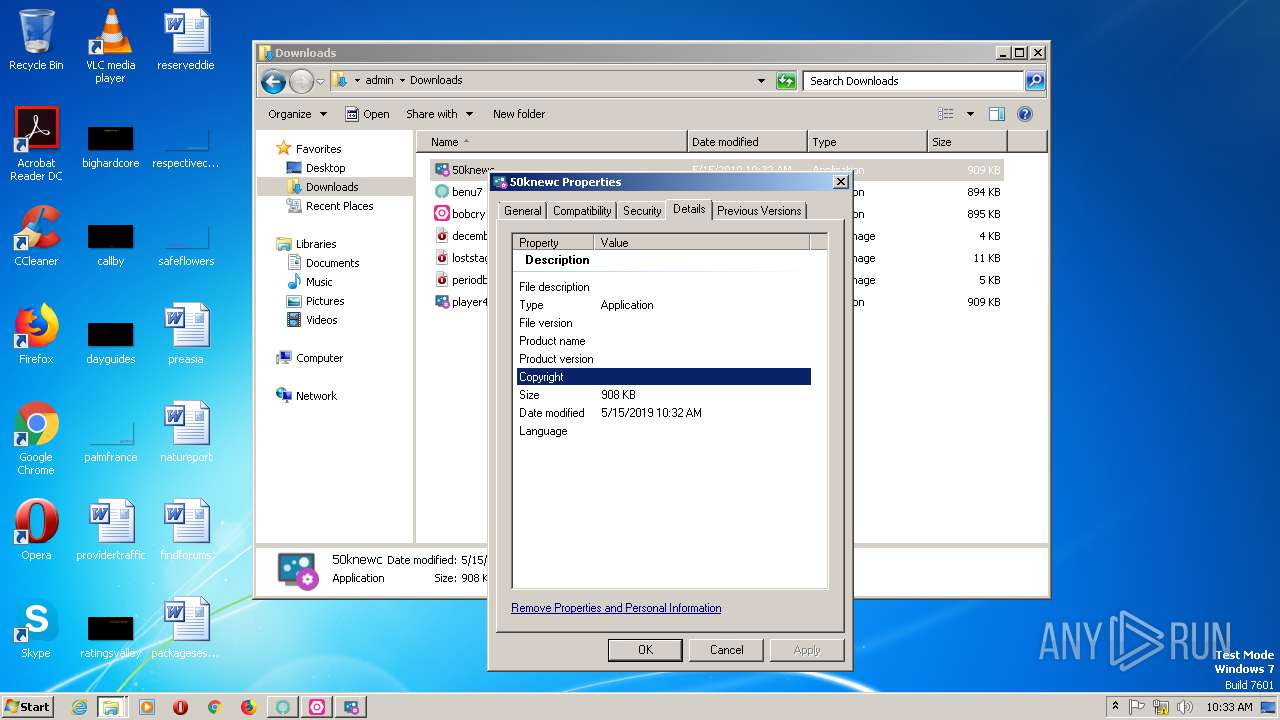
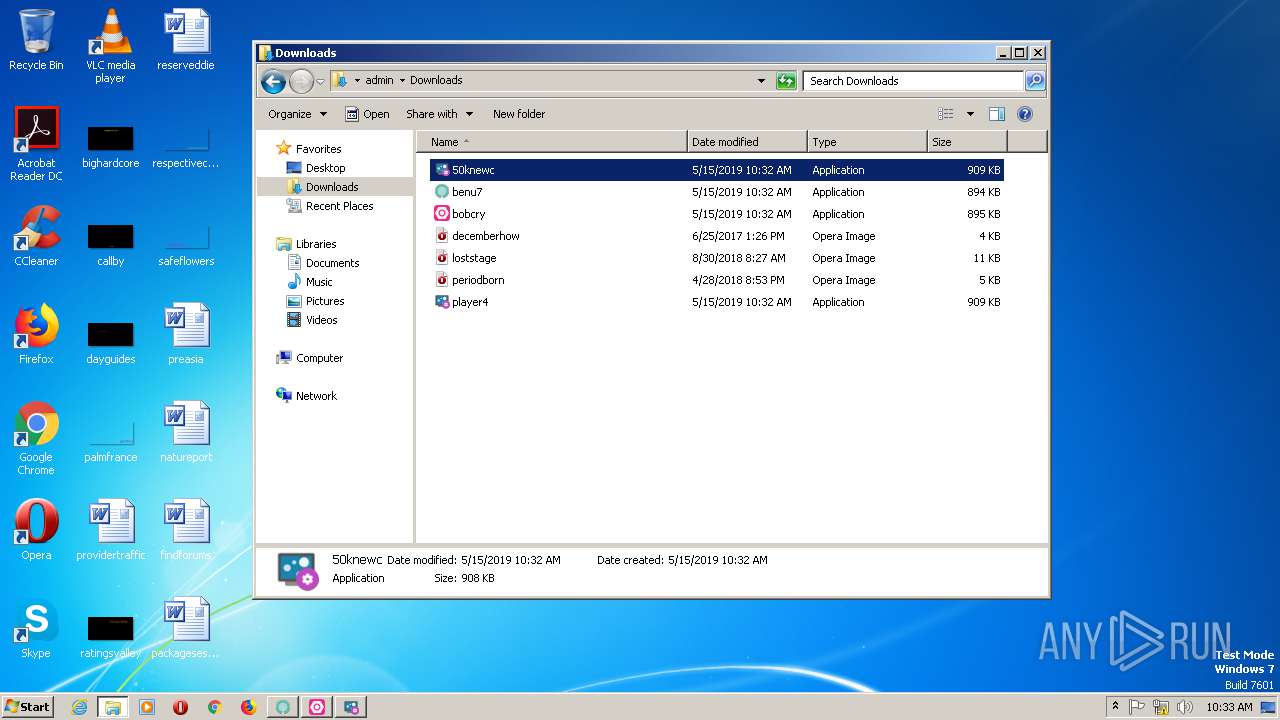
Application was dropped or rewritten from another process
- 50knewc.exe (PID: 372)
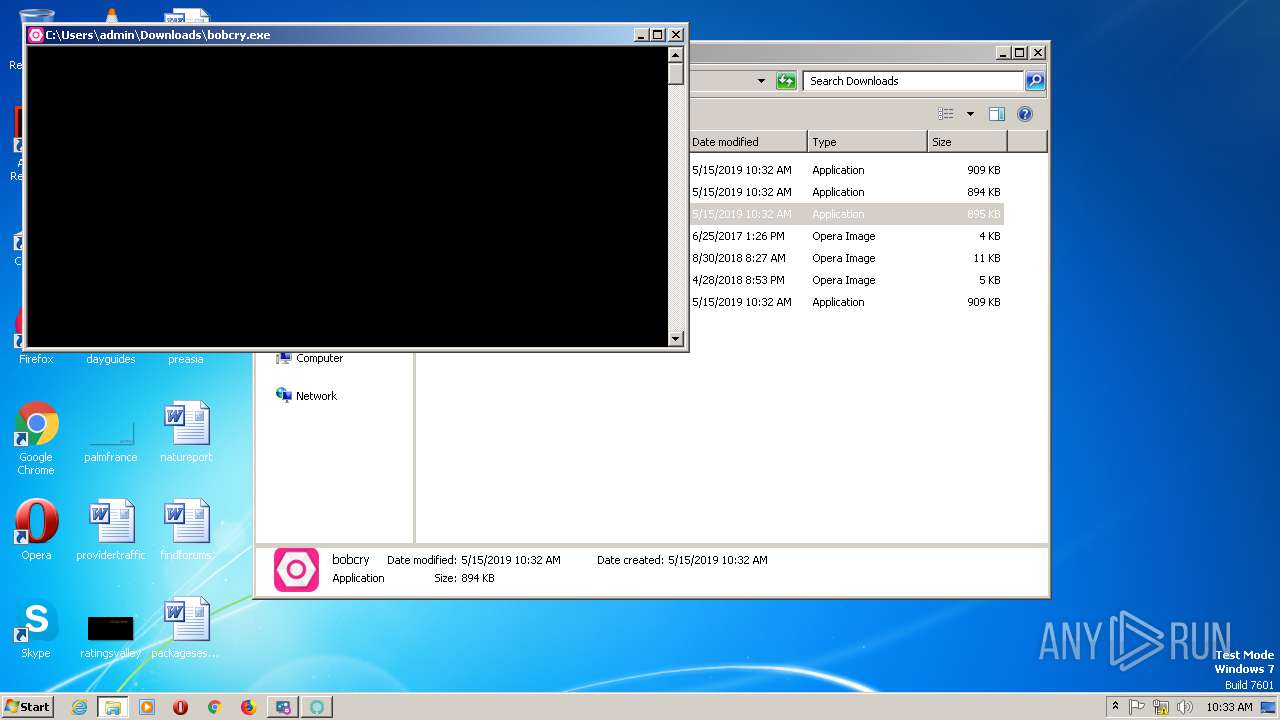
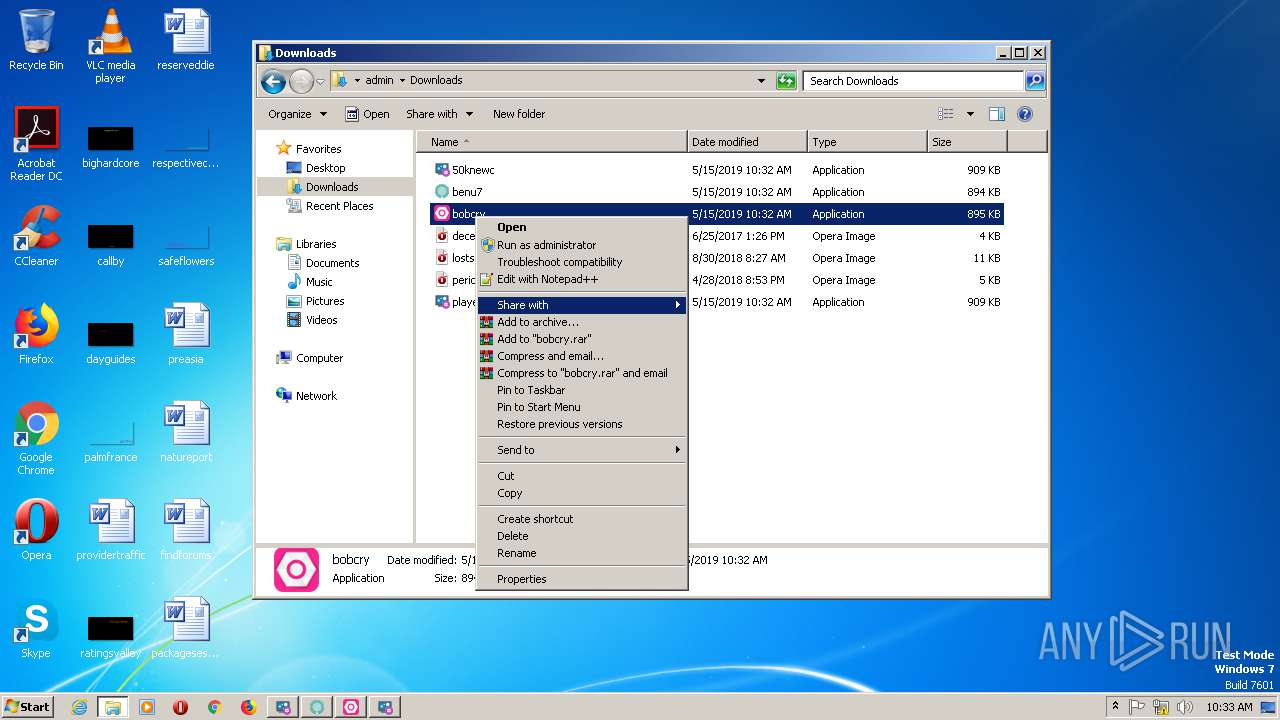
- bobcry.exe (PID: 2668)
- benu7.exe (PID: 2800)
- player4.exe (PID: 836)
Writes to a start menu file
- 50knewc.exe (PID: 372)
- benu7.exe (PID: 2800)
- bobcry.exe (PID: 2668)
- player4.exe (PID: 836)
Actions looks like stealing of personal data
- vbc.exe (PID: 2040)
- vbc.exe (PID: 2748)
- vbc.exe (PID: 2008)
- vbc.exe (PID: 2264)
- vbc.exe (PID: 1080)
- vbc.exe (PID: 2868)
- vbc.exe (PID: 2376)
- vbc.exe (PID: 2948)
Detected Hawkeye Keylogger
- RegAsm.exe (PID: 2068)
- RegAsm.exe (PID: 600)
- RegAsm.exe (PID: 1860)
- RegAsm.exe (PID: 2676)
Stealing of credential data
- vbc.exe (PID: 2040)
- vbc.exe (PID: 2748)
- vbc.exe (PID: 2008)
- vbc.exe (PID: 2264)
- vbc.exe (PID: 2868)
- vbc.exe (PID: 1080)
- vbc.exe (PID: 2376)
- vbc.exe (PID: 2948)
SUSPICIOUS
Executable content was dropped or overwritten
- IEXPLORE.EXE (PID: 2816)
- iexplore.exe (PID: 1736)
- benu7.exe (PID: 2800)
- 50knewc.exe (PID: 372)
- bobcry.exe (PID: 2668)
- player4.exe (PID: 836)
Creates files in the user directory
- 50knewc.exe (PID: 372)
- benu7.exe (PID: 2800)
- bobcry.exe (PID: 2668)
- player4.exe (PID: 836)
Executes scripts
- RegAsm.exe (PID: 2068)
- RegAsm.exe (PID: 600)
- RegAsm.exe (PID: 1860)
- RegAsm.exe (PID: 2676)
INFO
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2816)
Changes internet zones settings
- iexplore.exe (PID: 1736)
Reads settings of System Certificates
- iexplore.exe (PID: 1736)
Dropped object may contain Bitcoin addresses
- IEXPLORE.EXE (PID: 2816)
- iexplore.exe (PID: 1736)
- benu7.exe (PID: 2800)
Reads Internet Cache Settings
- iexplore.exe (PID: 1736)
Reads the machine GUID from the registry
- iexplore.exe (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
18
Malicious processes
12
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
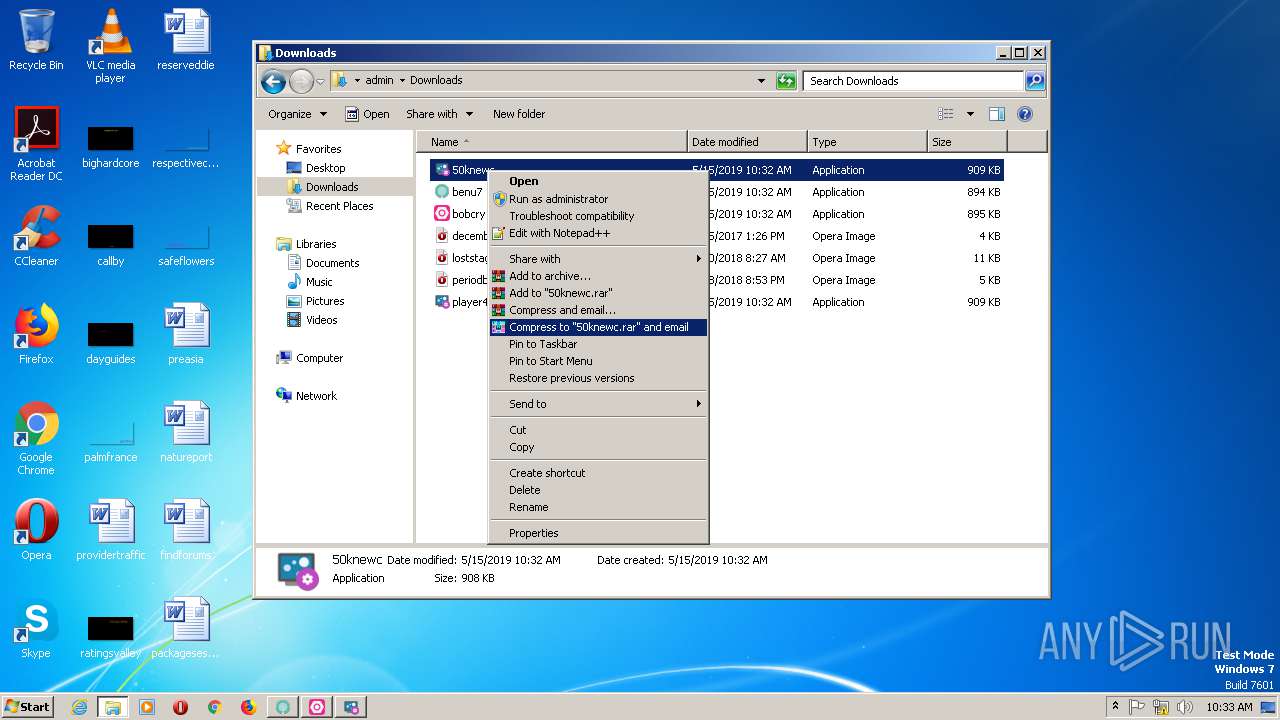
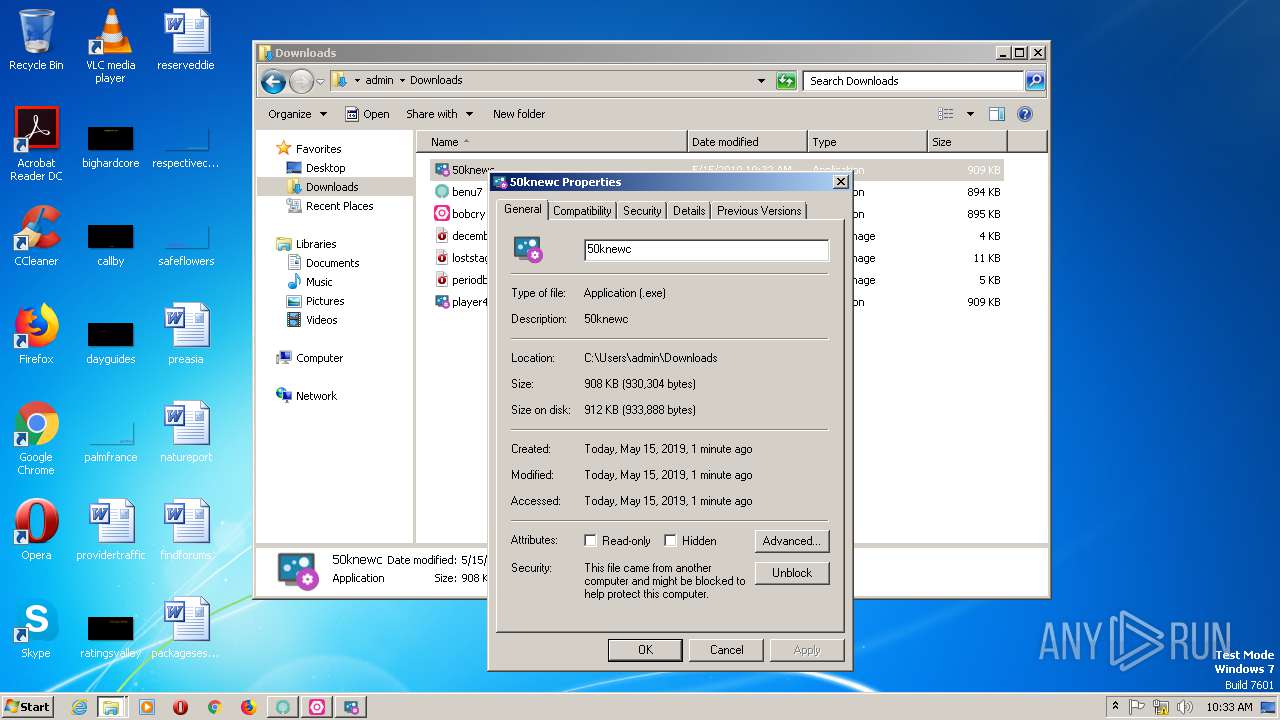
| 372 | "C:\Users\admin\Downloads\50knewc.exe" | C:\Users\admin\Downloads\50knewc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 600 | "C:\Users\admin\Downloads\bobcry.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | bobcry.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
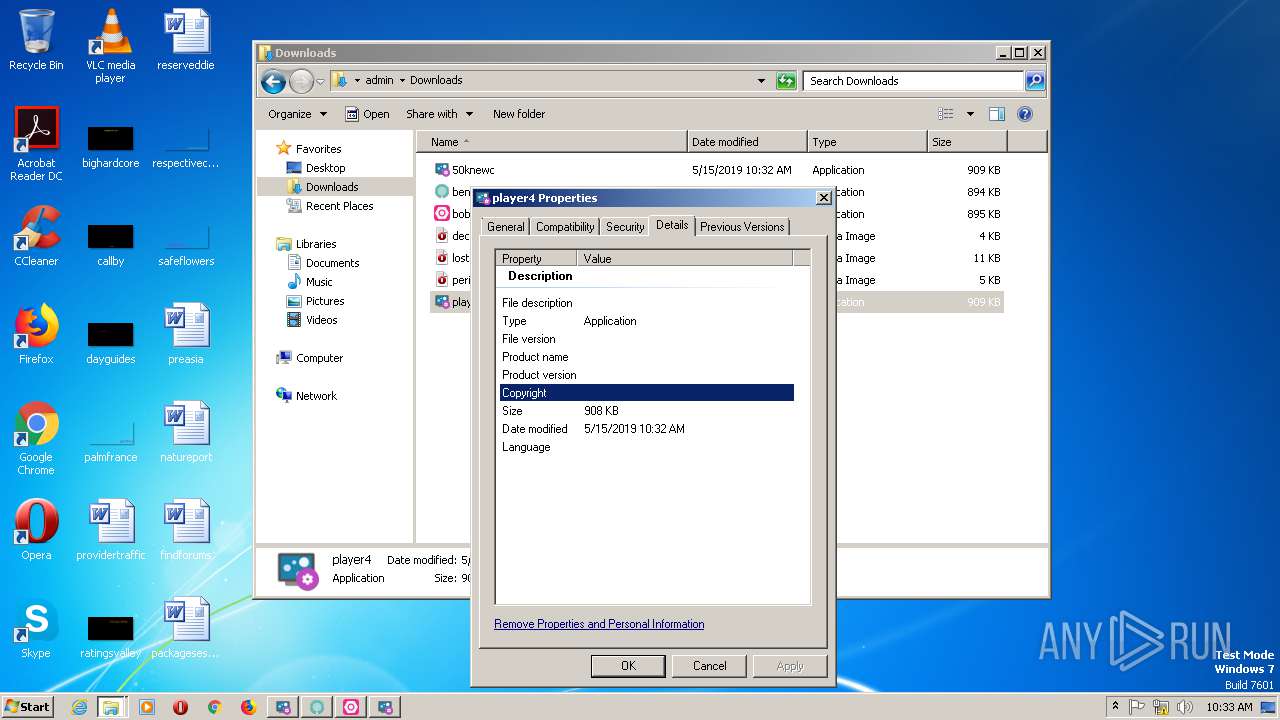
| 836 | "C:\Users\admin\Downloads\player4.exe" | C:\Users\admin\Downloads\player4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1080 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpD79C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.terryhill.top/proforma/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1860 | "C:\Users\admin\Downloads\benu7.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | benu7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2008 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpD3A3.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2040 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpA6C7.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\Downloads\50knewc.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | 50knewc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2264 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpD3B3.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | RegAsm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 Modules
| |||||||||||||||
Total events
1 199
Read events
1 080
Write events
118
Delete events
1
Modification events
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 2 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 1921451136 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30739209 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2221613636 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30739209 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
12
Suspicious files
10
Text files
17
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC8ACF041996C24CE.TMP | — | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\Downloads\player4.exe.e8hukn8.partial | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\Downloads\player4.exe.e8hukn8.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\Downloads\bobcry.exe.k09rwr2.partial | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\Downloads\bobcry.exe.k09rwr2.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\Downloads\benu7.exe.q9cfxxp.partial | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\Downloads\benu7.exe.q9cfxxp.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\Downloads\50knewc.exe.87byom0.partial | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\Downloads\50knewc.exe.87byom0.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
21
DNS requests
16
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1736 | iexplore.exe | GET | 304 | 152.199.19.161:443 | https://iecvlist.microsoft.com/ie11blocklist/1401746408/versionlistWin7.xml | US | — | — | whitelisted |
1736 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblocklist.bin | US | — | — | whitelisted |
2816 | IEXPLORE.EXE | GET | 200 | 54.36.212.206:80 | http://www.terryhill.top/proforma/player4.exe | FR | executable | 908 Kb | malicious |
2816 | IEXPLORE.EXE | GET | 200 | 54.36.212.206:80 | http://www.terryhill.top/proforma/ | FR | html | 1.29 Kb | malicious |
1736 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://iecvlist.microsoft.com/IE11/1479242656000/iecompatviewlist.xml | US | xml | 362 Kb | whitelisted |
1860 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 11 b | shared |
2816 | IEXPLORE.EXE | GET | 200 | 54.36.212.206:80 | http://www.terryhill.top/proforma/50knewc.exe | FR | executable | 908 Kb | malicious |
2676 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 11 b | shared |
2068 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 11 b | shared |
600 | RegAsm.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 11 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2816 | IEXPLORE.EXE | 54.36.212.206:80 | www.terryhill.top | OVH SAS | FR | malicious |
1736 | iexplore.exe | 54.36.212.206:80 | www.terryhill.top | OVH SAS | FR | malicious |
1736 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1736 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2068 | RegAsm.exe | 23.186.192.228:587 | mail.strutnfittings.com | — | — | unknown |
600 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
600 | RegAsm.exe | 69.46.29.186:587 | mail.renata-ltd.com | HIVELOCITY VENTURES CORP | US | malicious |
1860 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
1860 | RegAsm.exe | 192.185.84.68:587 | mail.jaguarline.com | CyrusOne LLC | US | unknown |
2676 | RegAsm.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.terryhill.top |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
bot.whatismyipaddress.com |
| shared |
mail.strutnfittings.com |
| unknown |
mail.renata-ltd.com |
| malicious |
mail.jaguarline.com |
| unknown |
mail.mwanzompya.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
320 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2816 | IEXPLORE.EXE | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2816 | IEXPLORE.EXE | Misc activity | ET INFO Packed Executable Download |
2816 | IEXPLORE.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2816 | IEXPLORE.EXE | Misc activity | ET INFO Possible EXE Download From Suspicious TLD |
2816 | IEXPLORE.EXE | Misc activity | ET INFO Packed Executable Download |
2816 | IEXPLORE.EXE | Misc activity | ET INFO Possible EXE Download From Suspicious TLD |
2068 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
2068 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
600 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |
50knewc.exe | User32.dll |