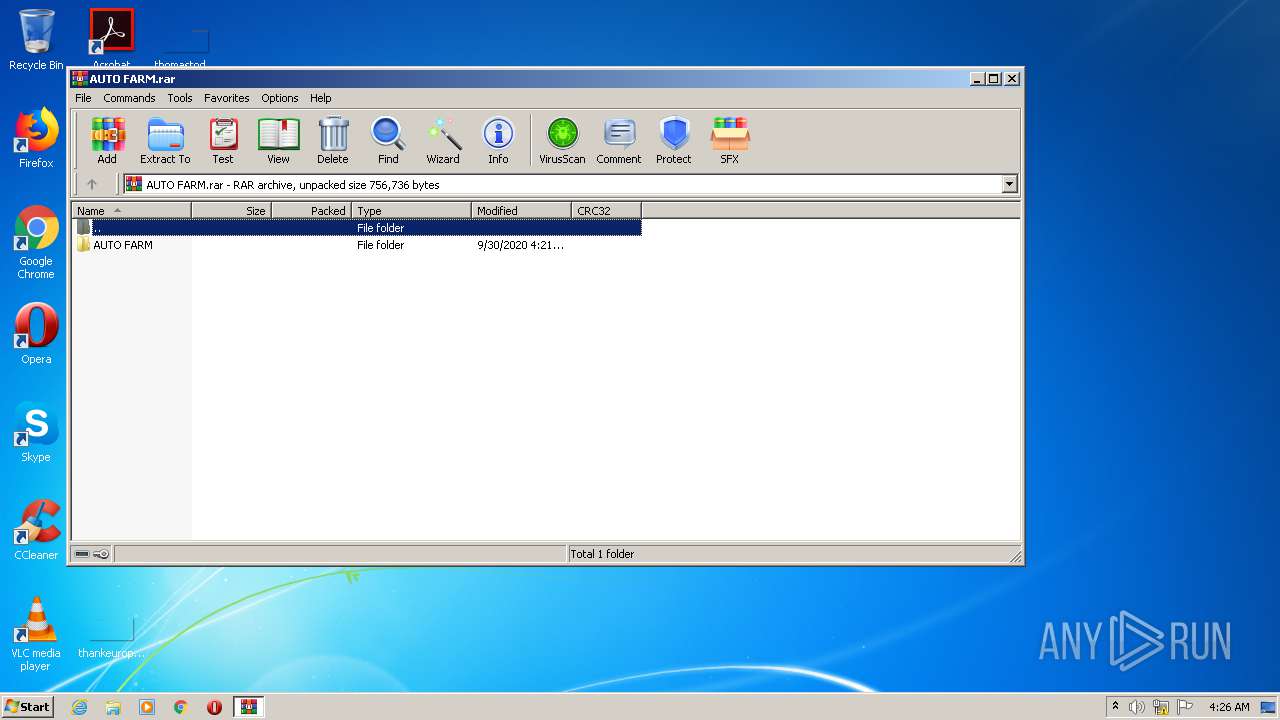
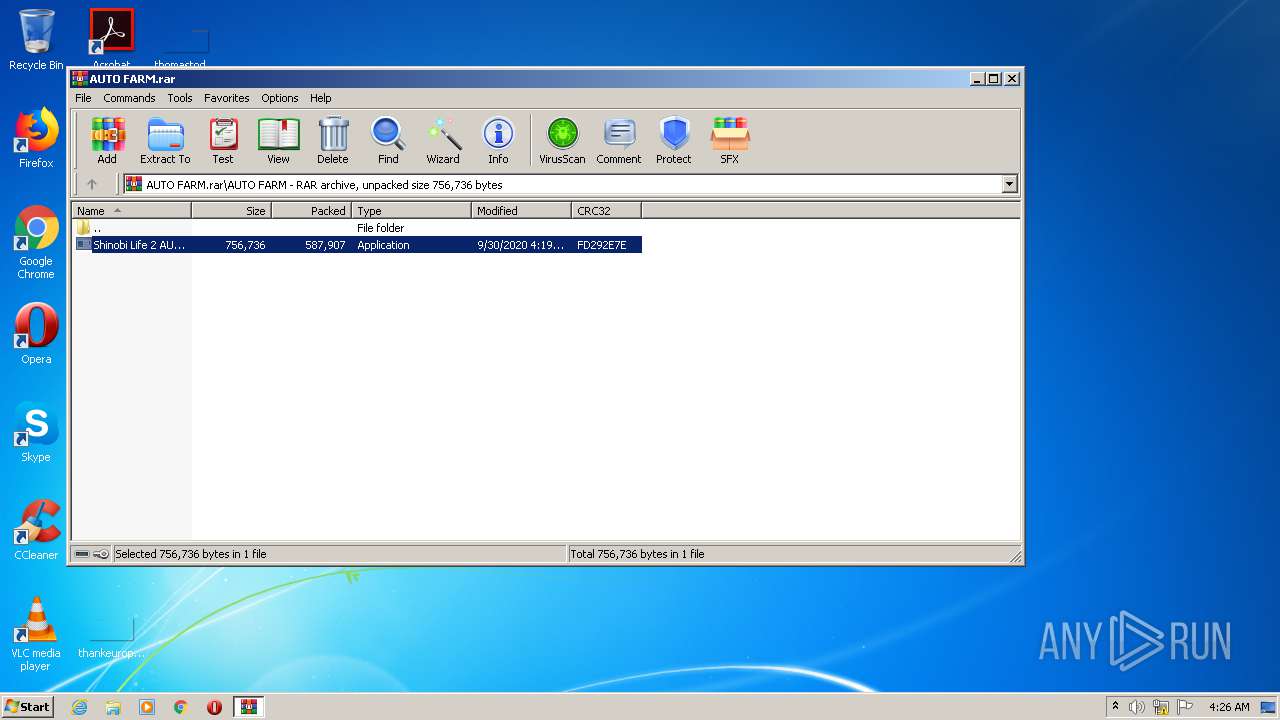
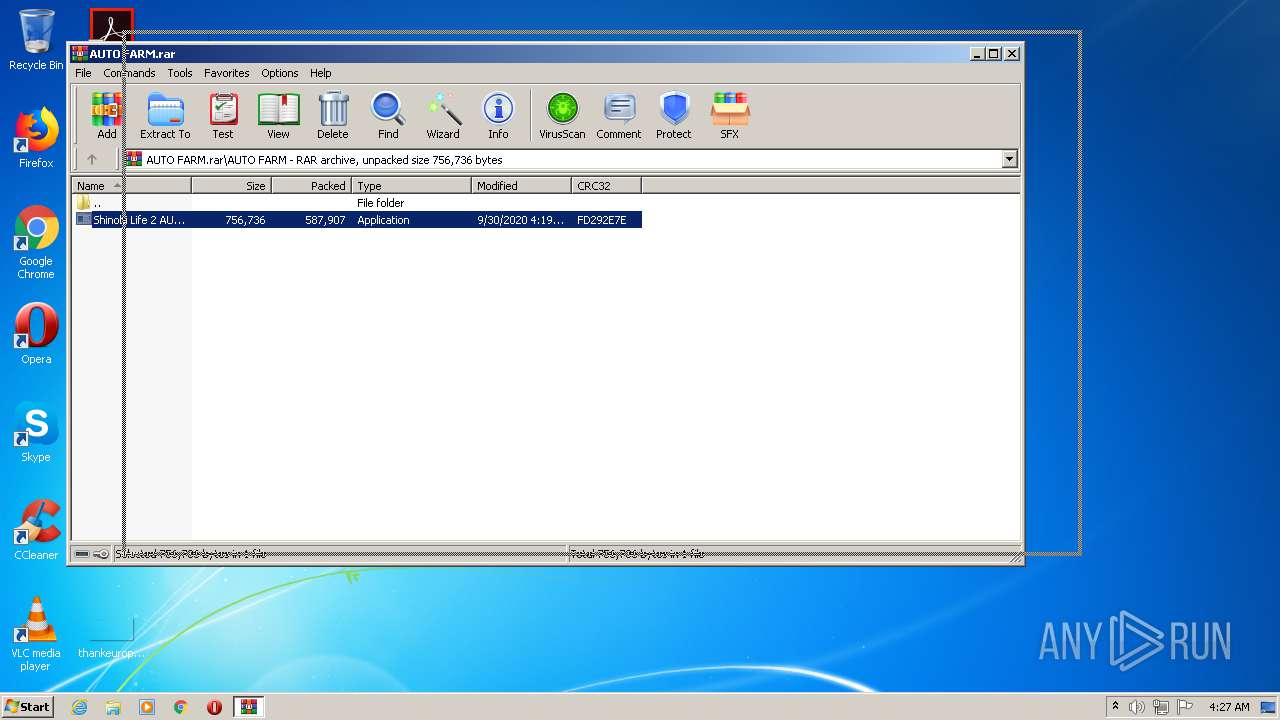
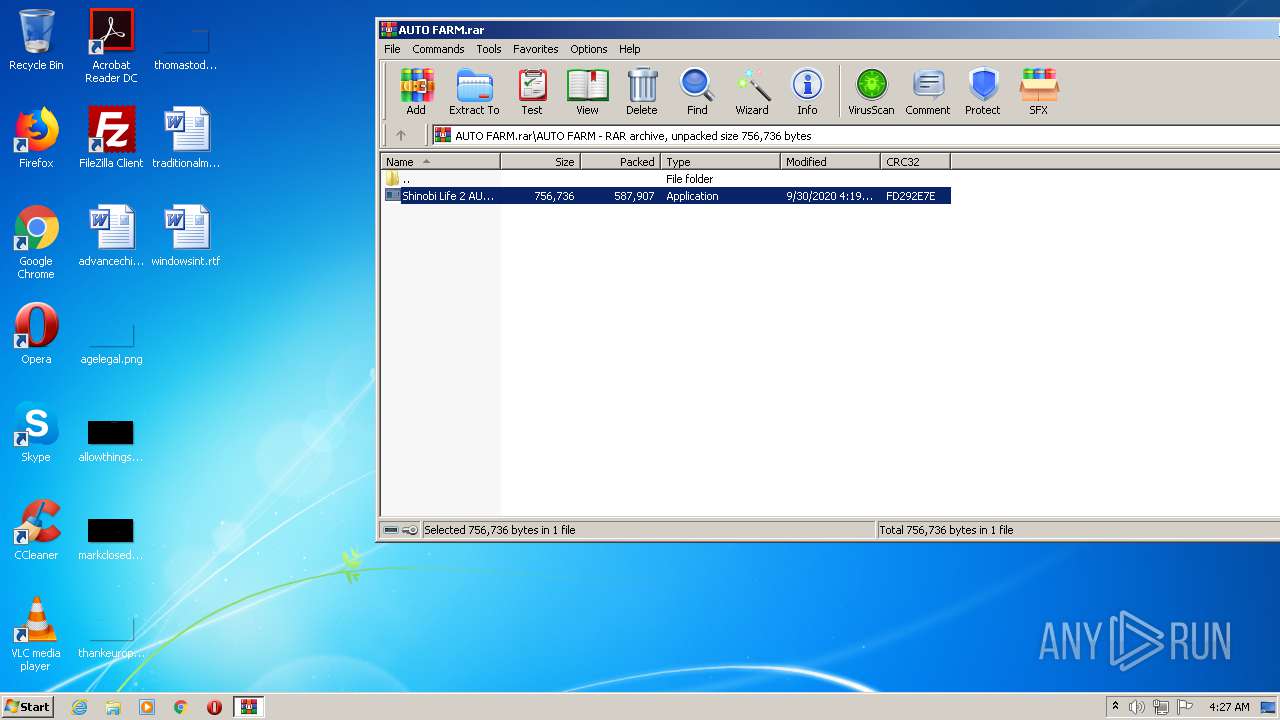
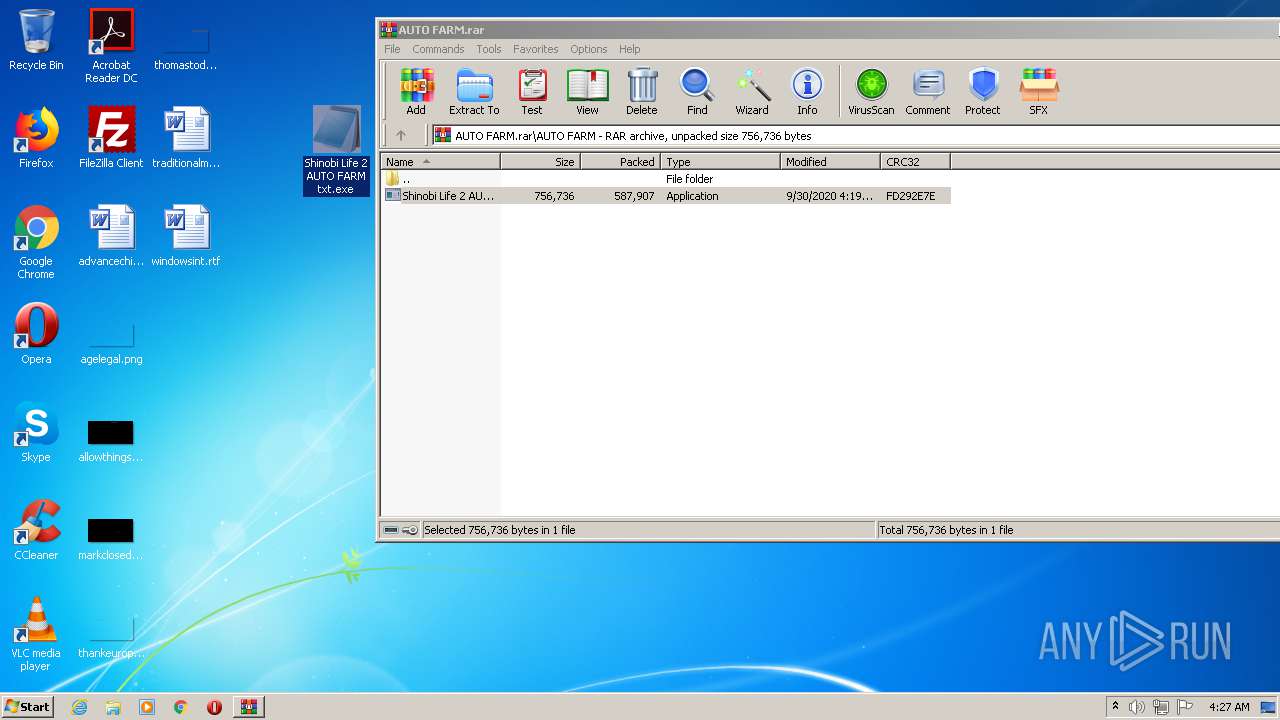
| File name: | AUTO FARM.rar |
| Full analysis: | https://app.any.run/tasks/b67183be-6e2d-4491-8688-21fbb95daf07 |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | September 30, 2020, 03:26:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0A41916E3C10F20F1A82F3FCCE83D514 |
| SHA1: | CD1D7CAD6063429242FCE8263EC1A696FE405B8B |
| SHA256: | 4699B9AD2F66650AF5769F90581A59947525ABA74C2C11EFB3AB7D5EA78810A1 |
| SSDEEP: | 12288:JPsQFNjAvFrCHpGoBqaBPDJK5cYu6Vhc+Ew3kdT0X/Cf0xZj2lW:+8NMFmptqUUWIOTO/d2Y |
MALICIOUS
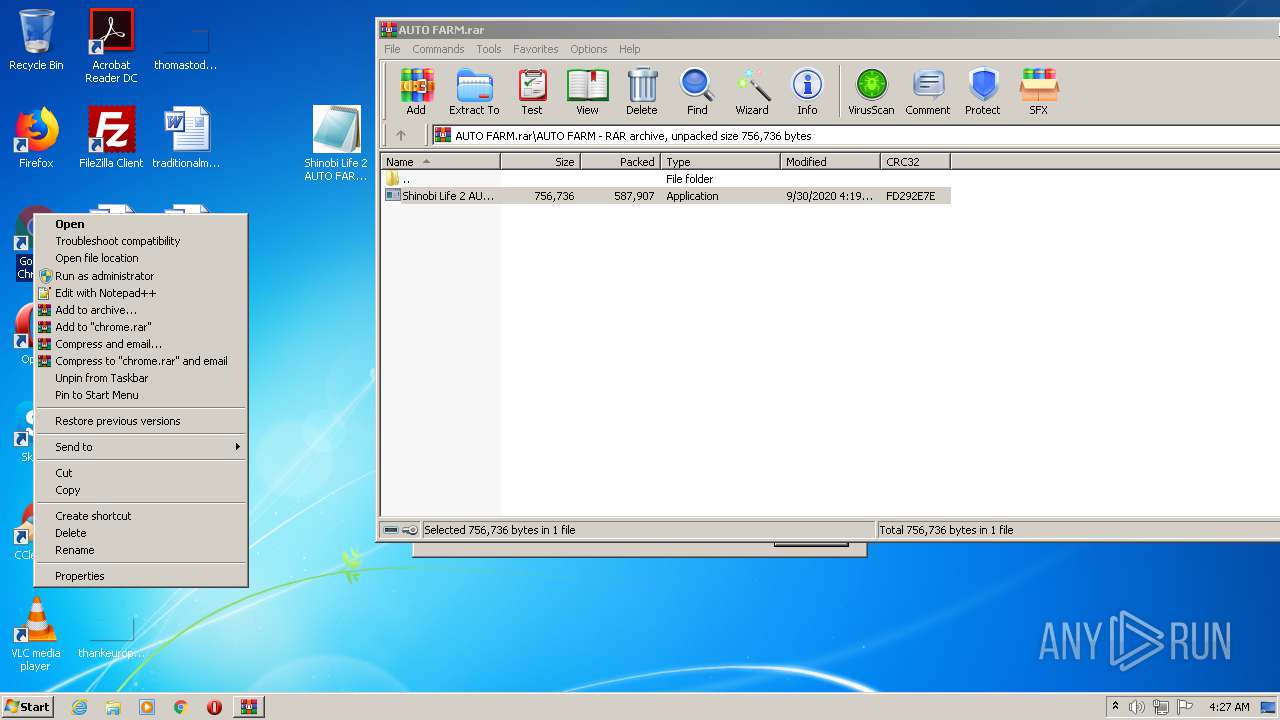
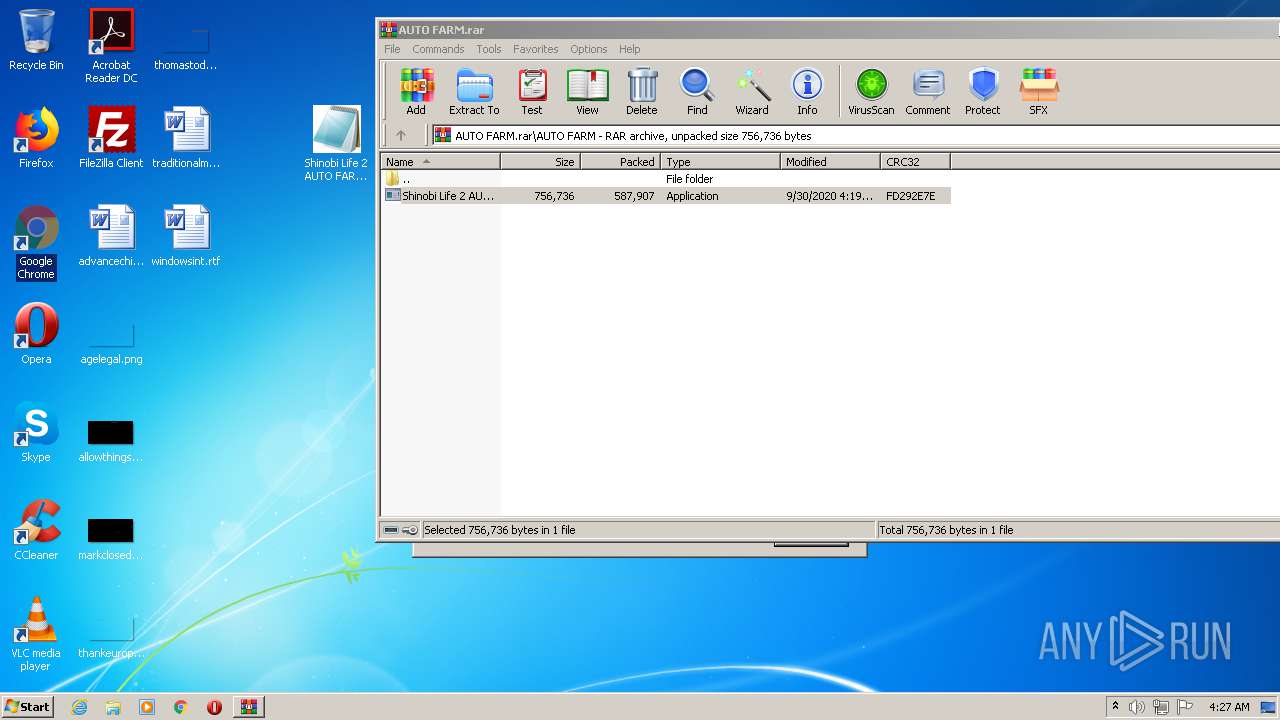
Application was dropped or rewritten from another process
- Shinobi Life 2 AUTO FARM txt.exe (PID: 3708)
- Shinobi Life 2 AUTO FARM txt.exe (PID: 3872)
- Windows Update.exe (PID: 2820)
HAWKEYE was detected
- Windows Update.exe (PID: 2820)
Changes settings of System certificates
- Windows Update.exe (PID: 2820)
Actions looks like stealing of personal data
- vbc.exe (PID: 3528)
- vbc.exe (PID: 3884)
SUSPICIOUS
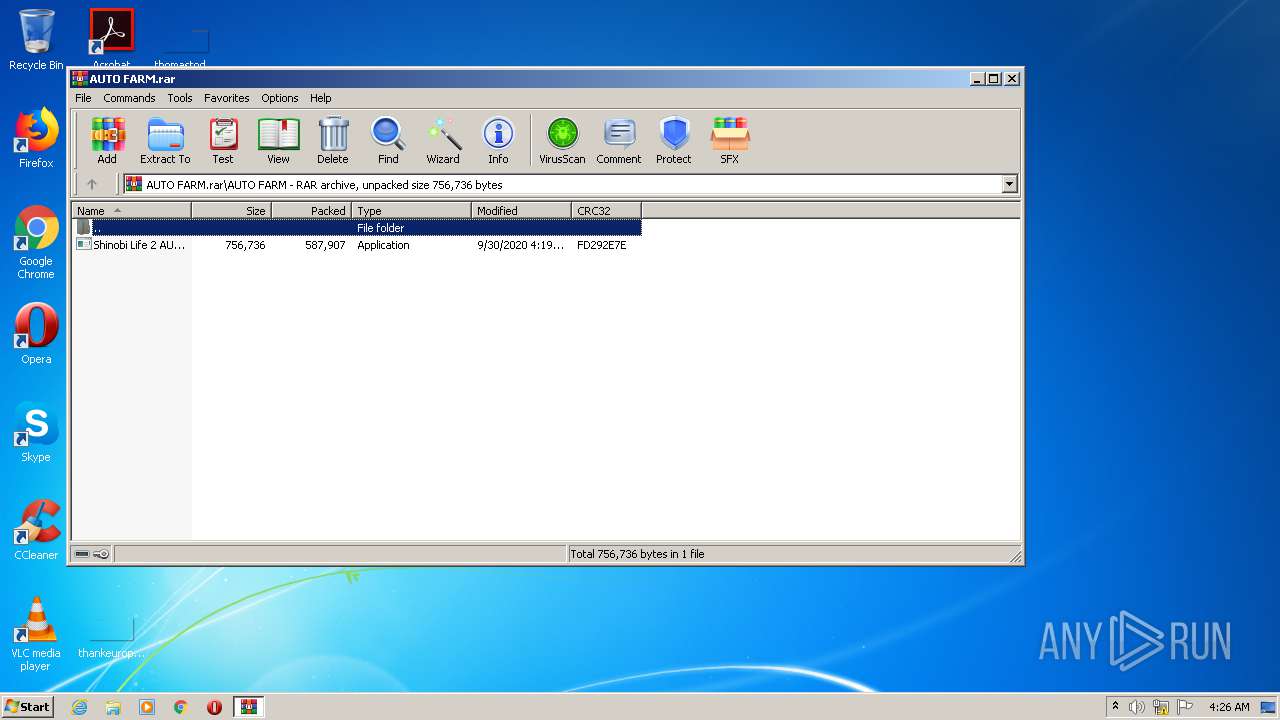
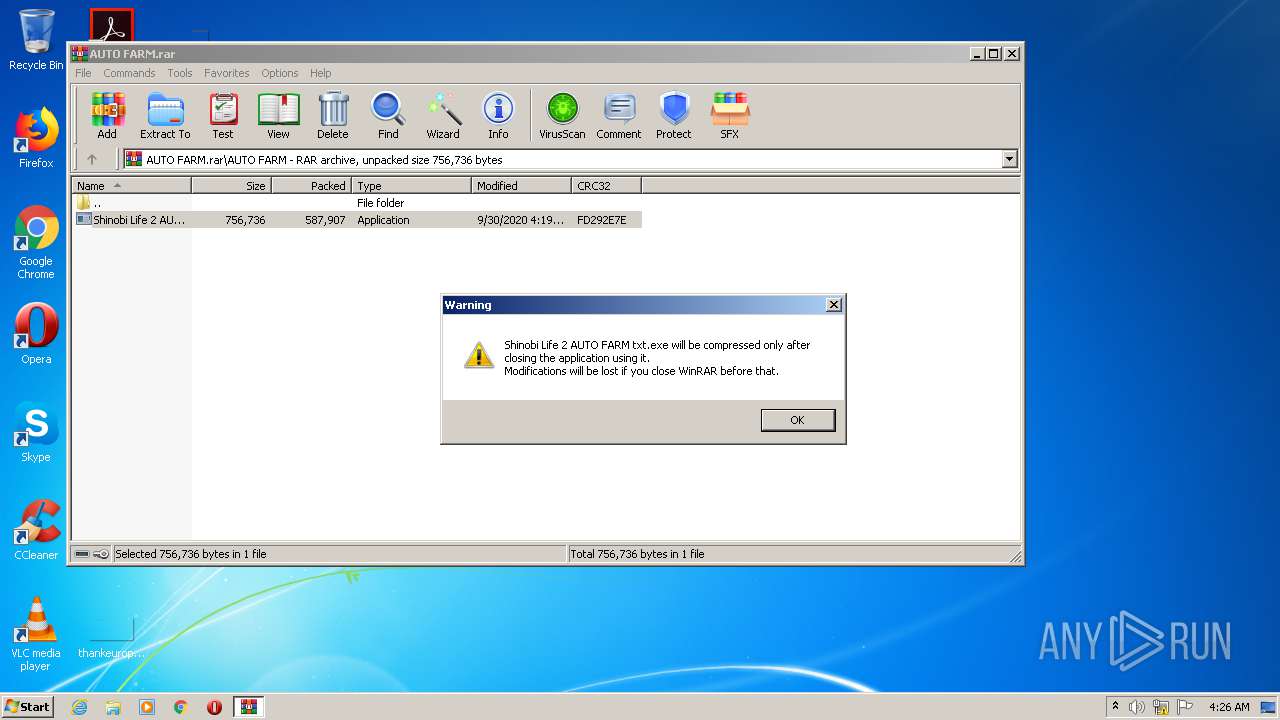
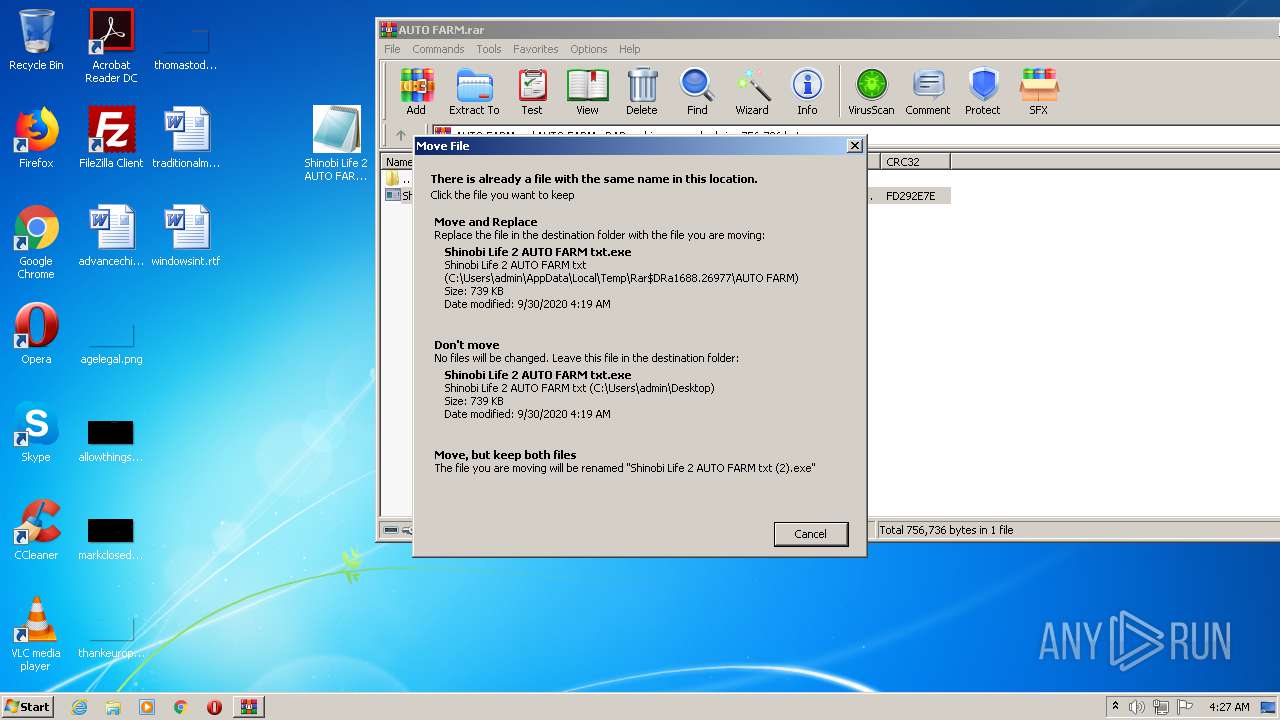
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1688)
- Shinobi Life 2 AUTO FARM txt.exe (PID: 3872)
Application launched itself
- Shinobi Life 2 AUTO FARM txt.exe (PID: 3708)
Starts itself from another location
- Shinobi Life 2 AUTO FARM txt.exe (PID: 3872)
Creates files in the user directory
- Shinobi Life 2 AUTO FARM txt.exe (PID: 3872)
- Windows Update.exe (PID: 2820)
Checks for external IP
- Windows Update.exe (PID: 2820)
Adds / modifies Windows certificates
- Windows Update.exe (PID: 2820)
Executes scripts
- Windows Update.exe (PID: 2820)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 3884)
INFO
Reads settings of System Certificates
- Windows Update.exe (PID: 2820)
- chrome.exe (PID: 2208)
Reads the hosts file
- chrome.exe (PID: 3152)
- chrome.exe (PID: 2208)
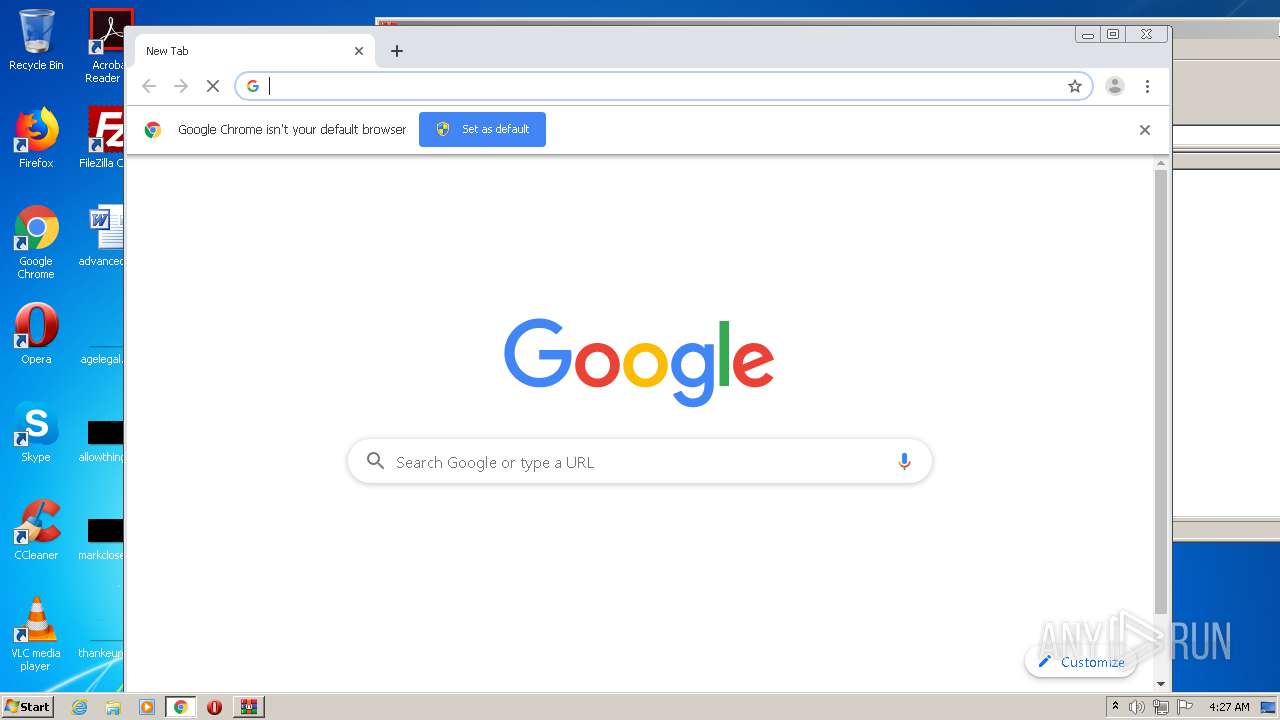
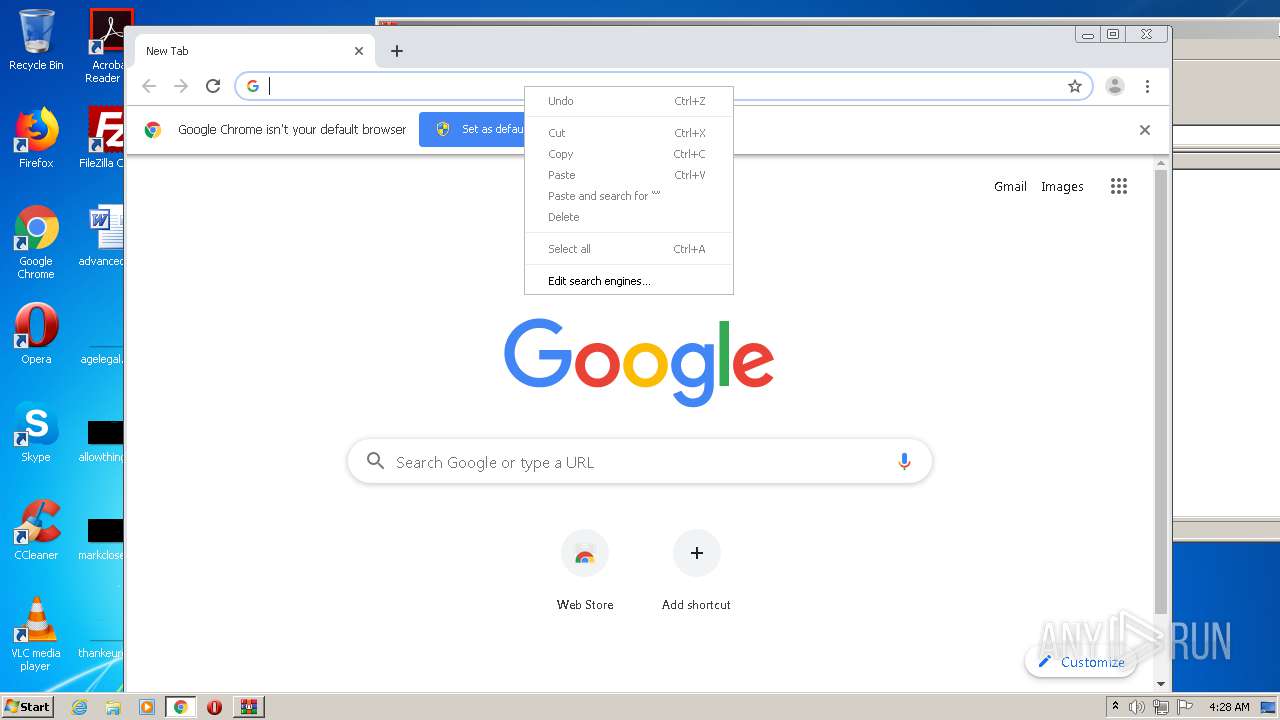
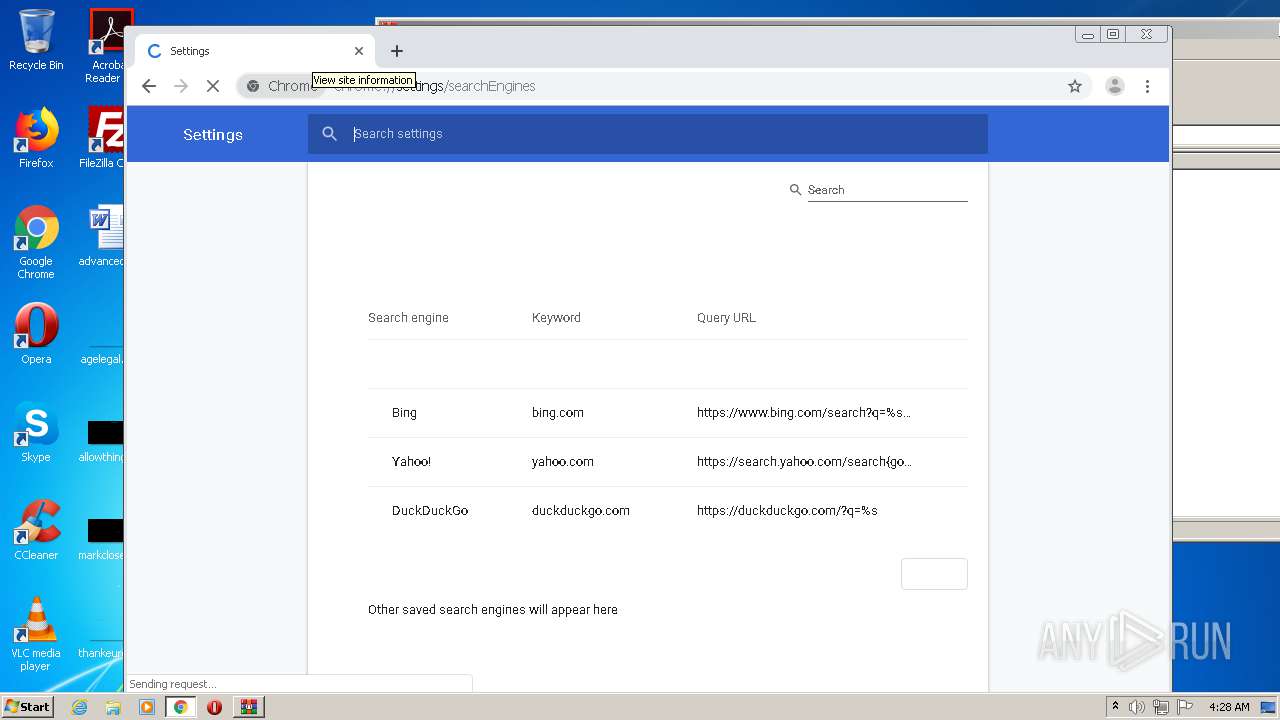
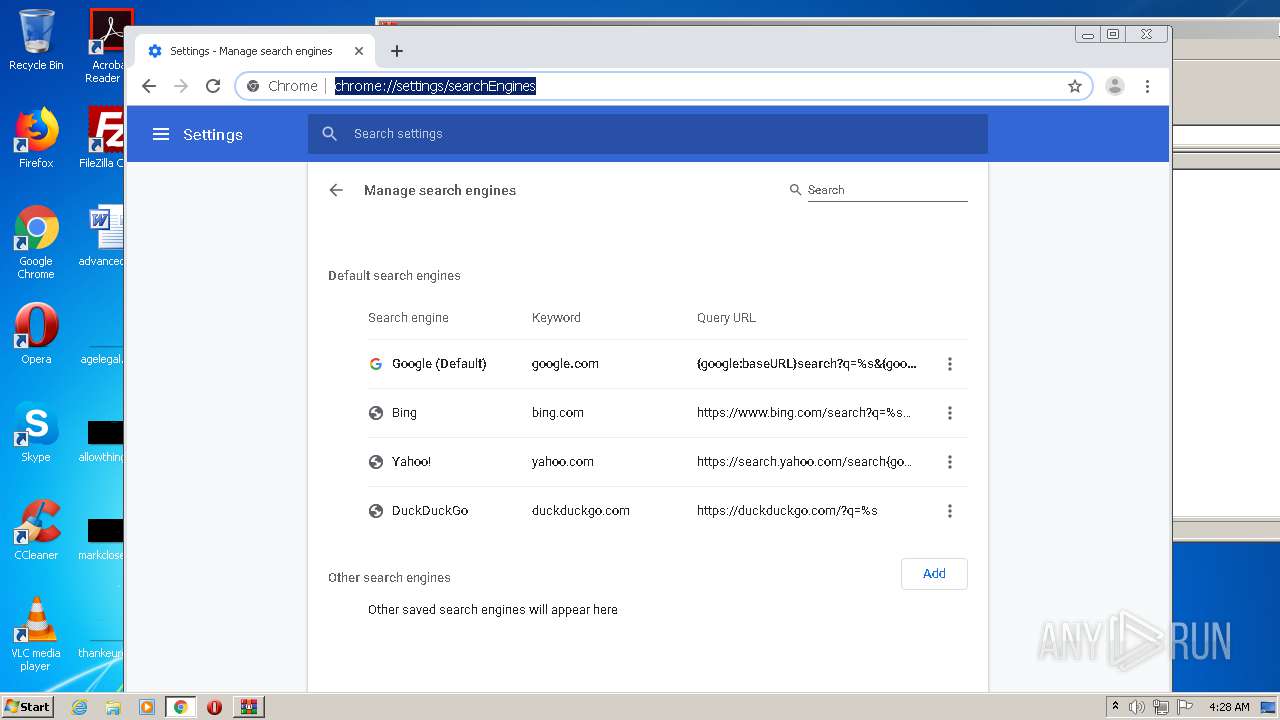
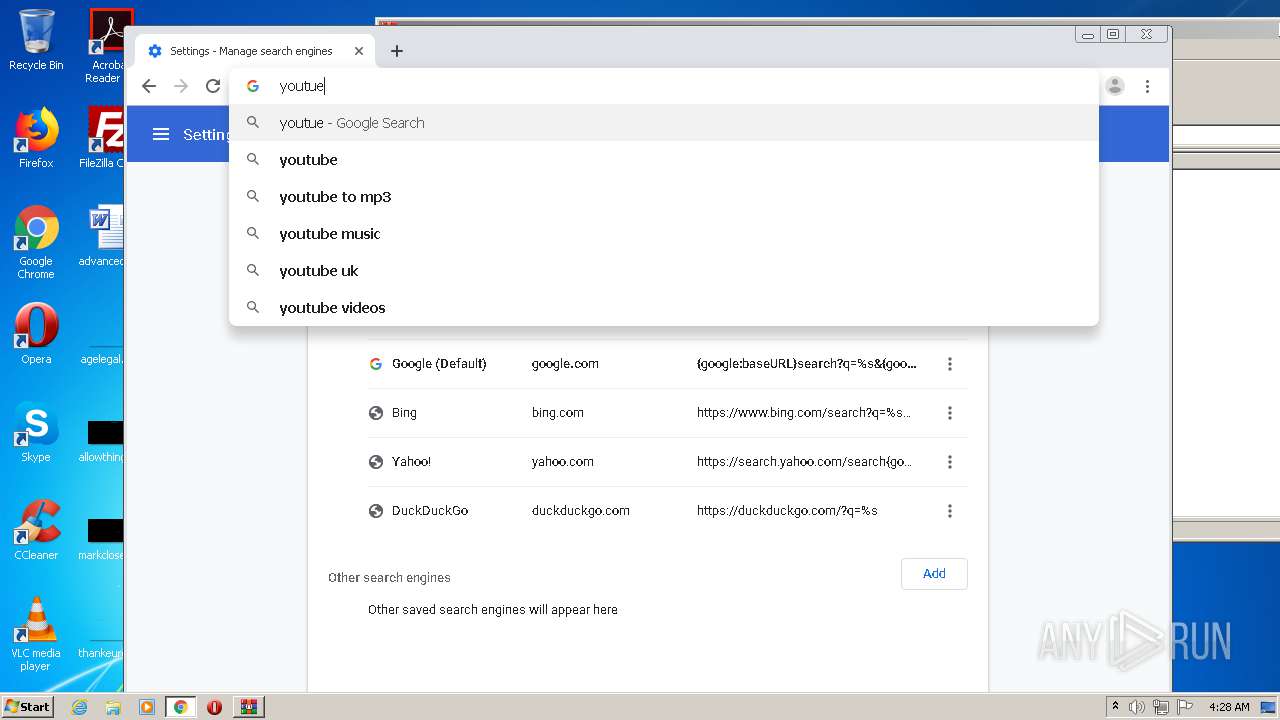
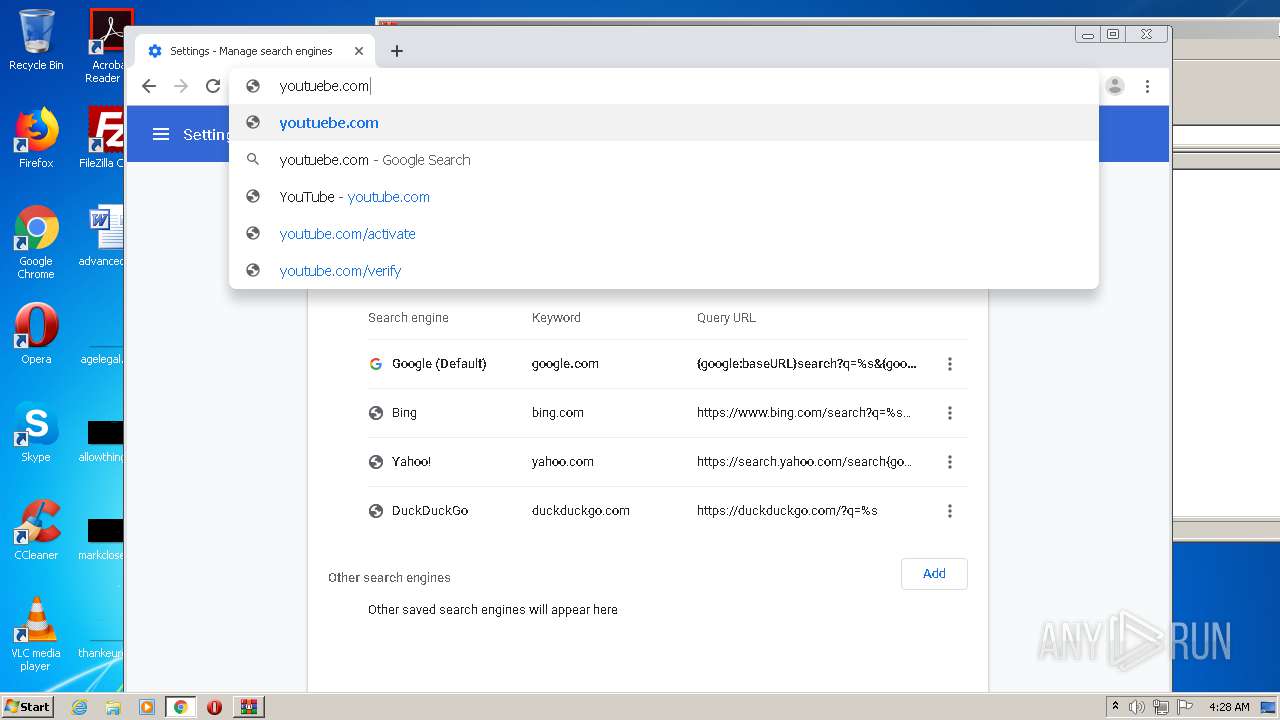
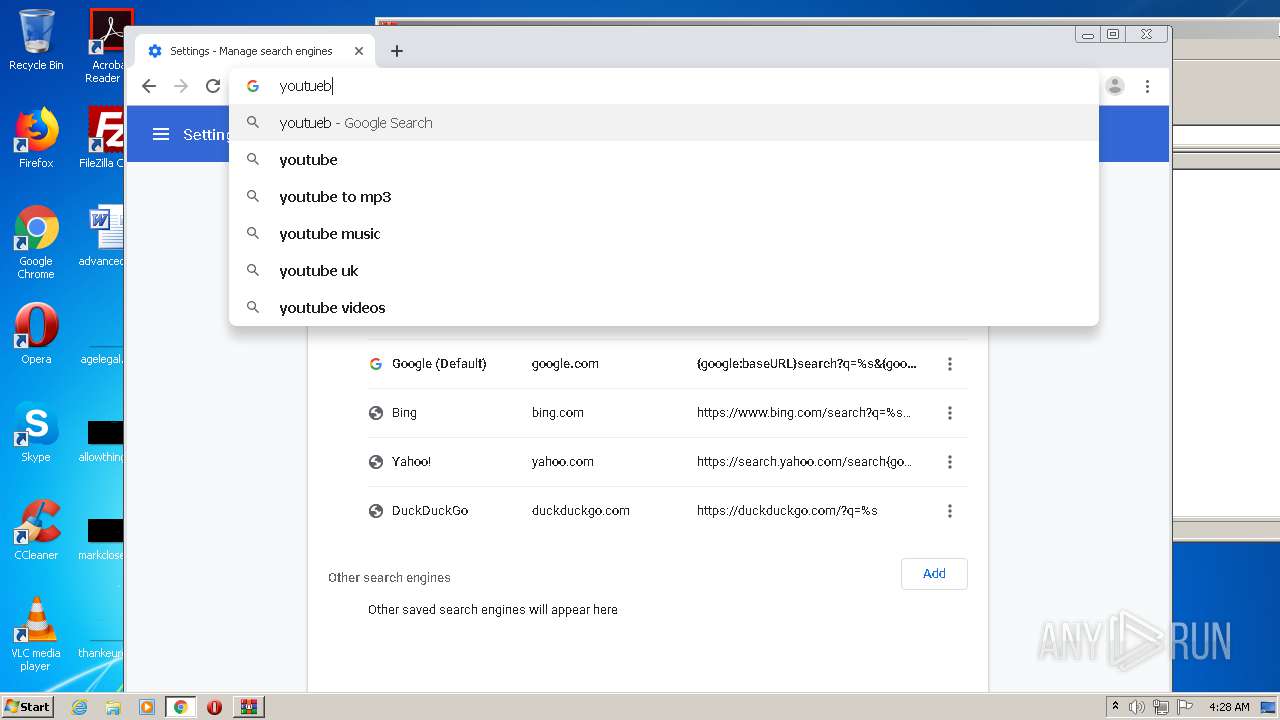
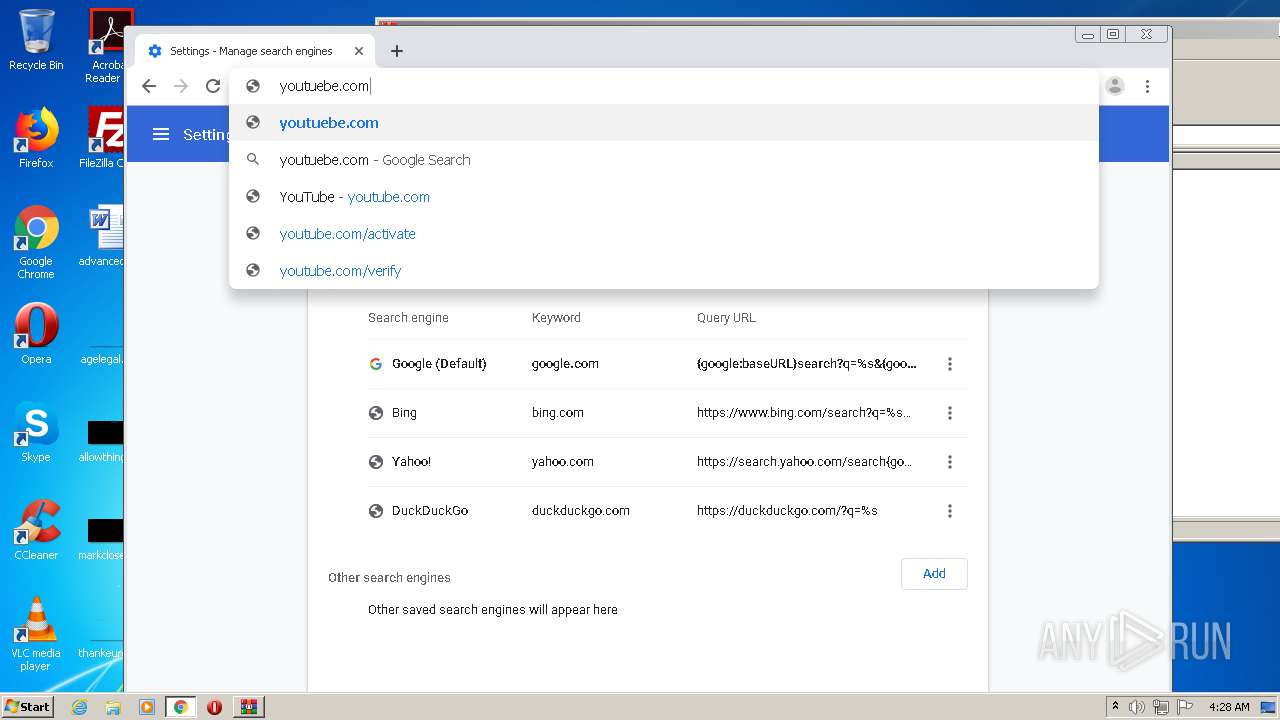
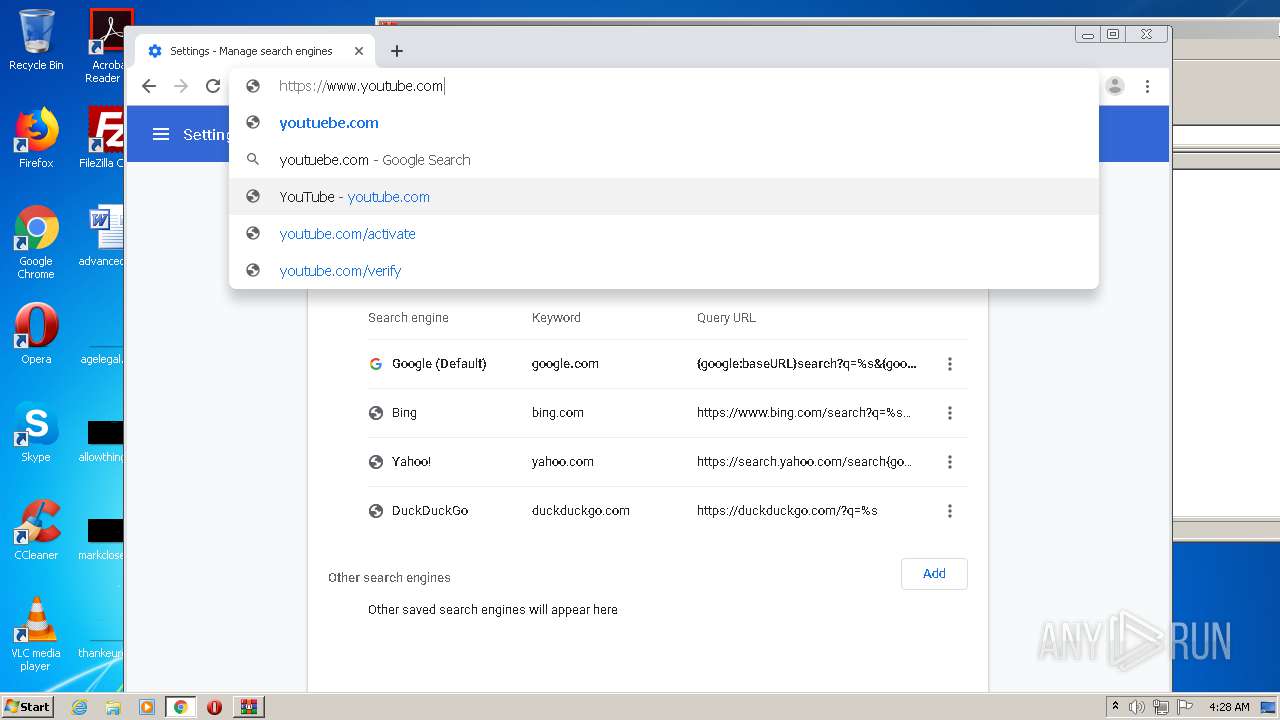
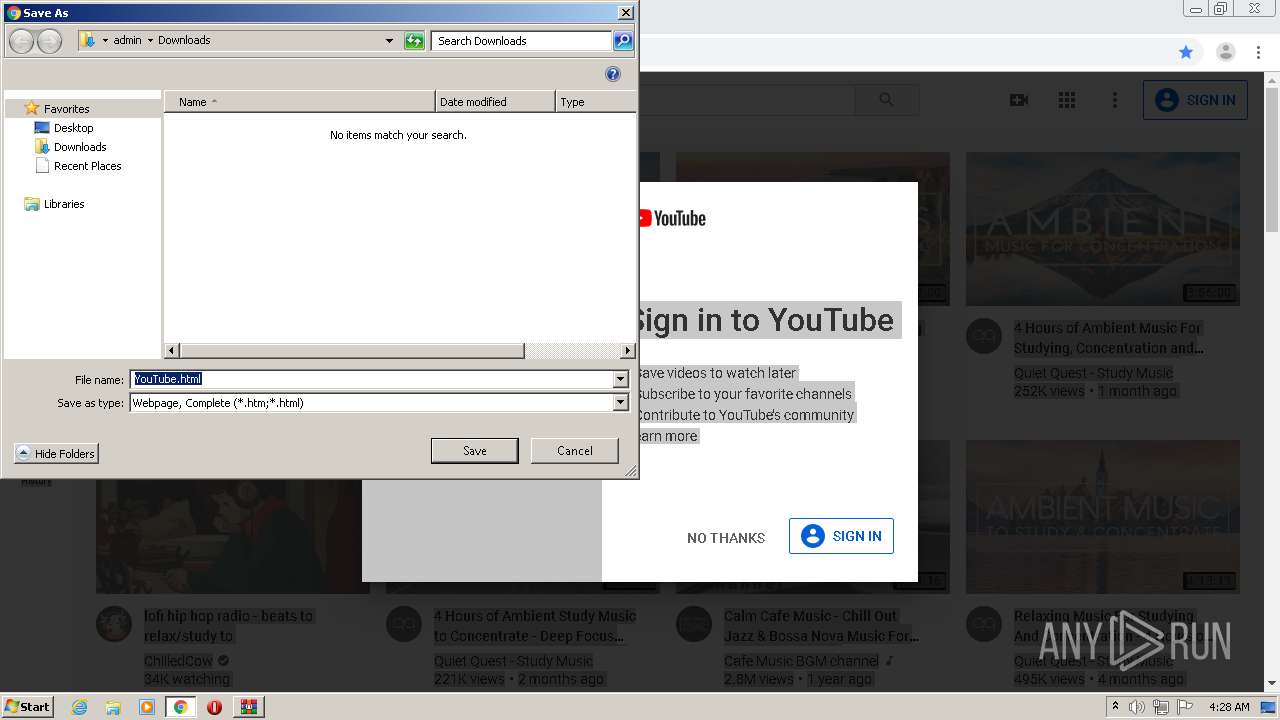
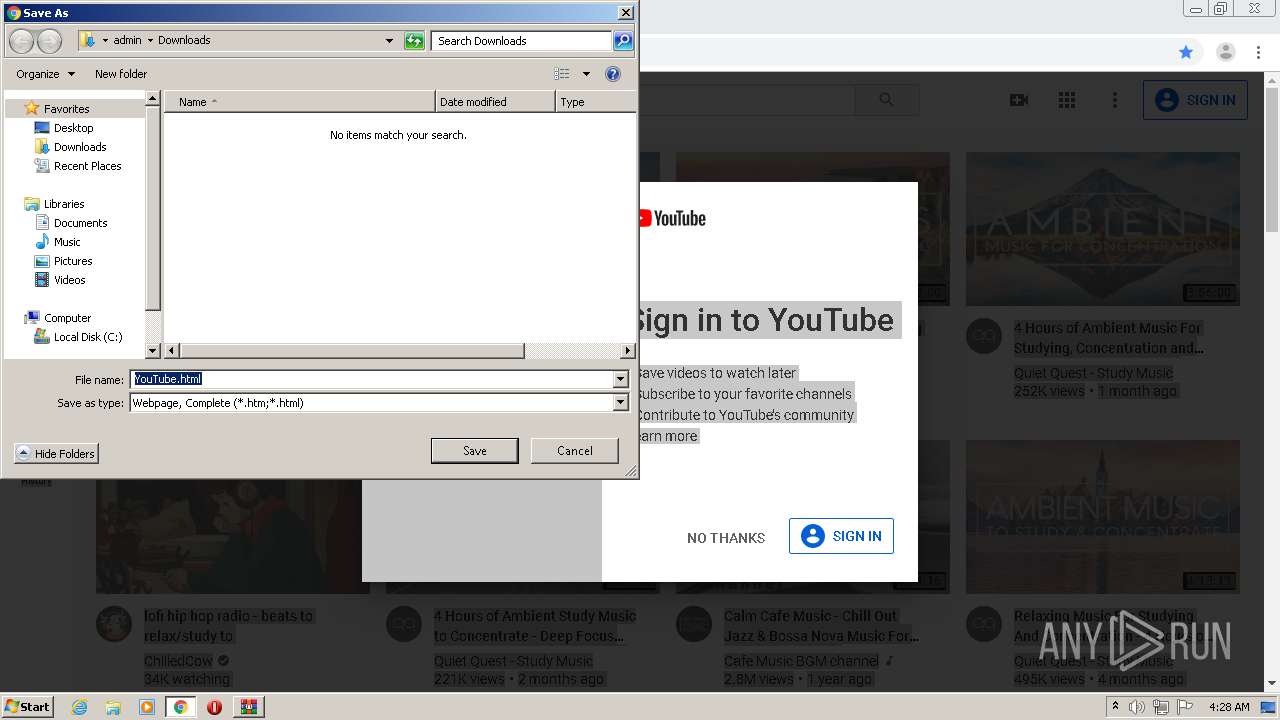
Manual execution by user
- chrome.exe (PID: 3152)
Application launched itself
- chrome.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
66
Monitored processes
26
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7825938563553389395 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c08a9d0,0x6c08a9e0,0x6c08a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4215208372564205462 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10544233604854065495 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10080348516549732056 --mojo-platform-channel-handle=732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AUTO FARM.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3697982137434548468 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3237505348815962996 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11100903214089467057 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,14100168038296890564,10049621811322472354,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12816303114478405869 --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 573
Read events
2 379
Write events
188
Delete events
6
Modification events
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AUTO FARM.rar | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
67
Text files
117
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 3884 | vbc.exe | C:\Users\admin\AppData\Local\Temp\bhvD89.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 1688 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1688.26926\AUTO FARM\Shinobi Life 2 AUTO FARM txt.exe | — | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F73FB1C-C50.pma | — | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\04a1870e-8556-4882-8328-3f671a65400c.tmp | — | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3872 | Shinobi Life 2 AUTO FARM txt.exe | C:\Users\admin\AppData\Local\Temp\SysInfo.txt | text | |
MD5:— | SHA256:— | |||
| 3152 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3872 | Shinobi Life 2 AUTO FARM txt.exe | C:\Users\admin\AppData\Roaming\Windows Update.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
27
DNS requests
20
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2820 | Windows Update.exe | GET | 301 | 104.16.154.36:80 | http://whatismyipaddress.com/ | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2820 | Windows Update.exe | 104.16.154.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
— | — | 104.16.154.36:443 | whatismyipaddress.com | Cloudflare Inc | US | shared |
2820 | Windows Update.exe | 108.177.119.108:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
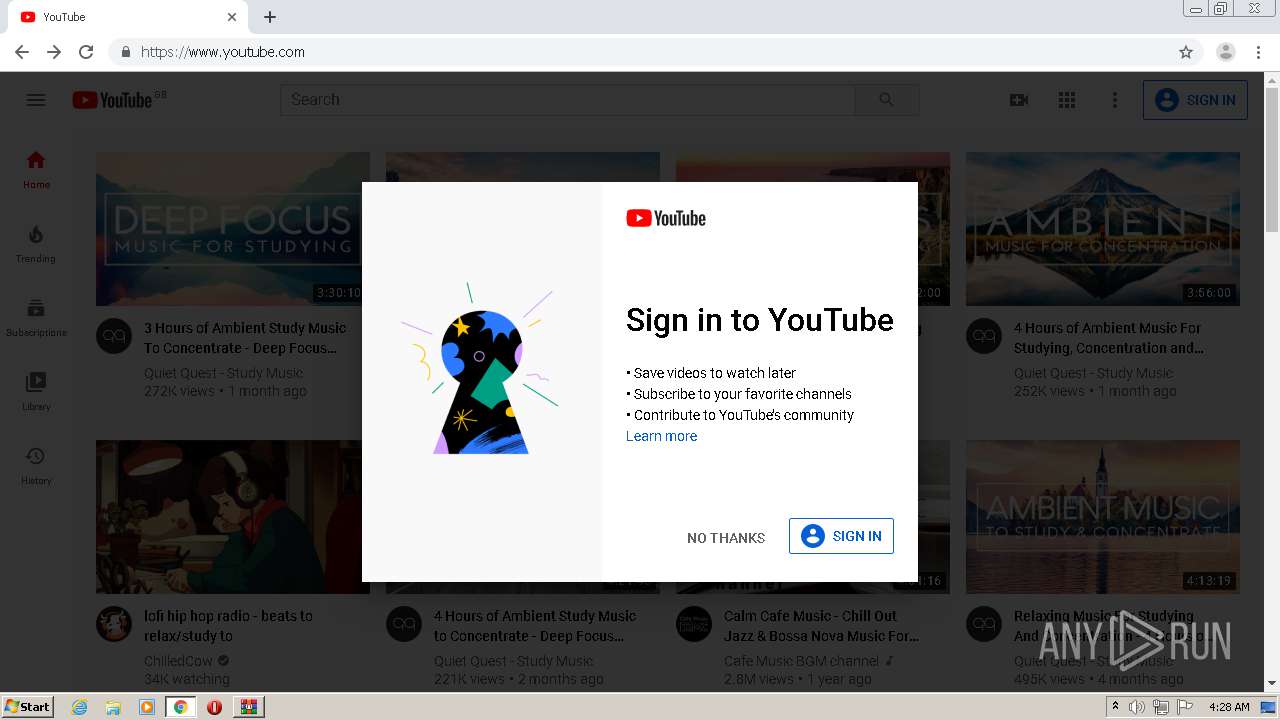
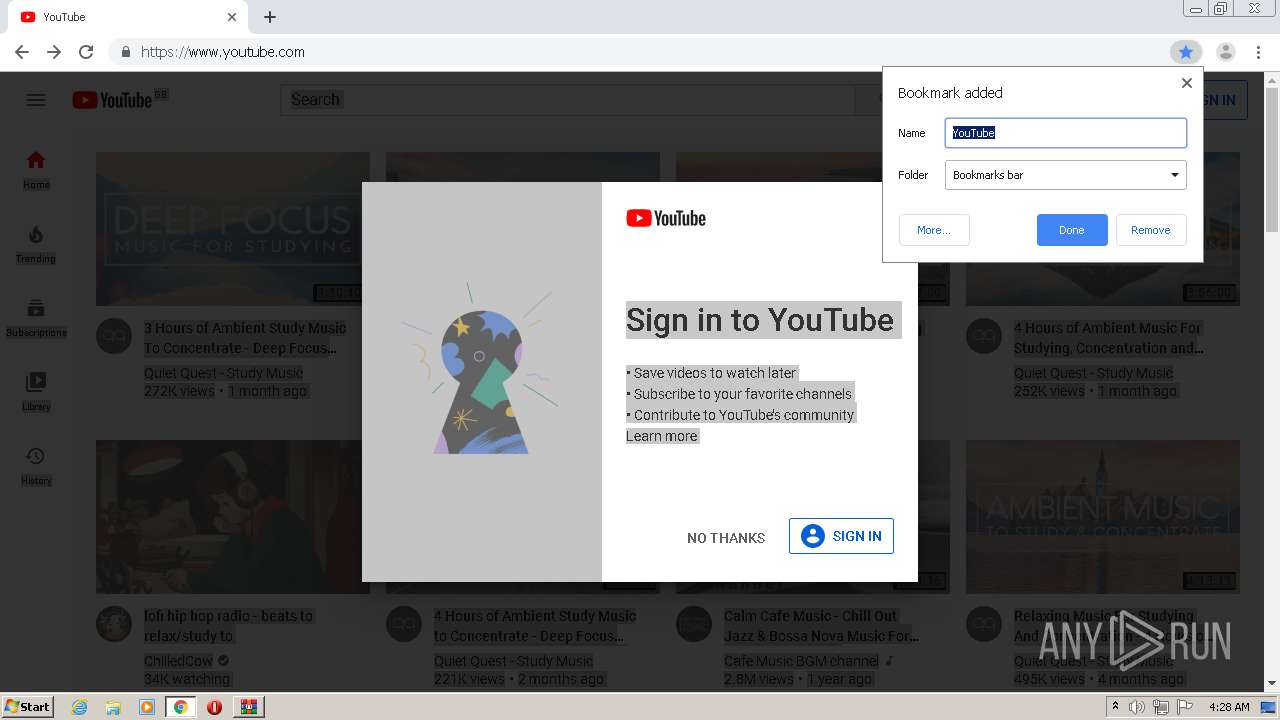
— | — | 216.58.212.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 216.58.212.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 216.58.206.22:443 | i.ytimg.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtp.gmail.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
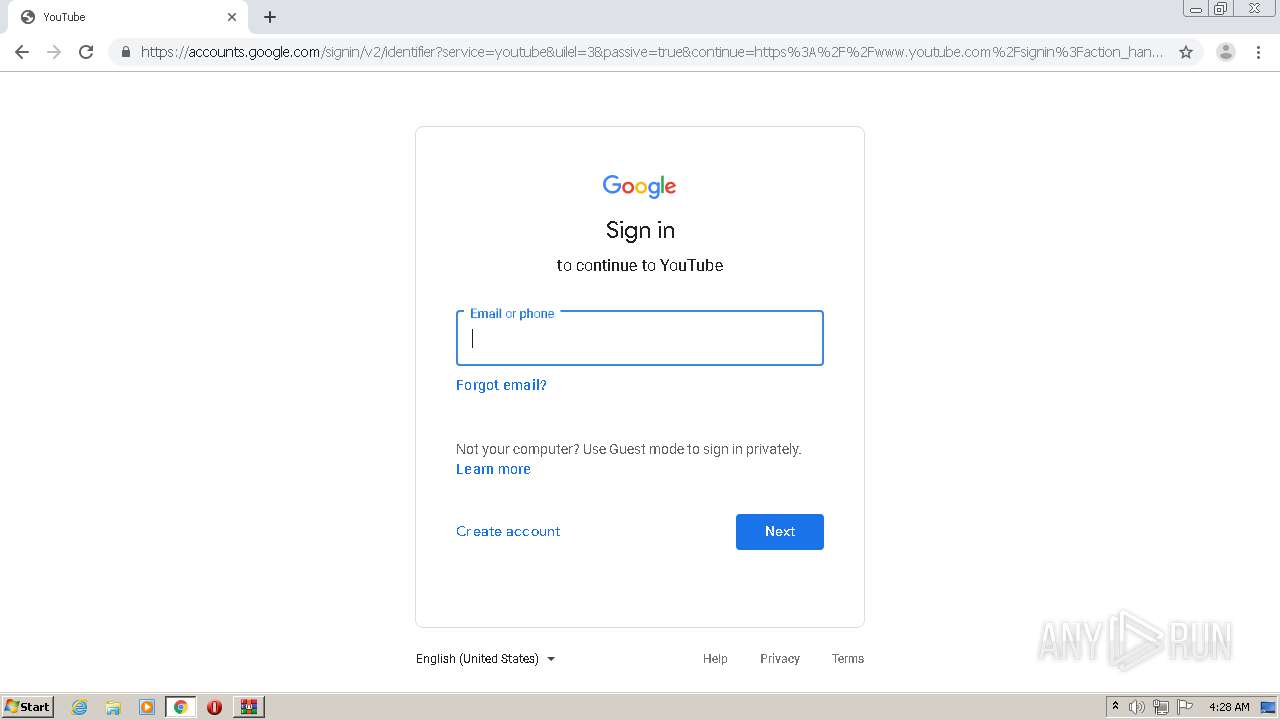
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2820 | Windows Update.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
2820 | Windows Update.exe | A Network Trojan was detected | SPYWARE [PTsecurity] HawkEye / Predator Pain (IP Chck) |
2820 | Windows Update.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
2820 | Windows Update.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2820 | Windows Update.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report