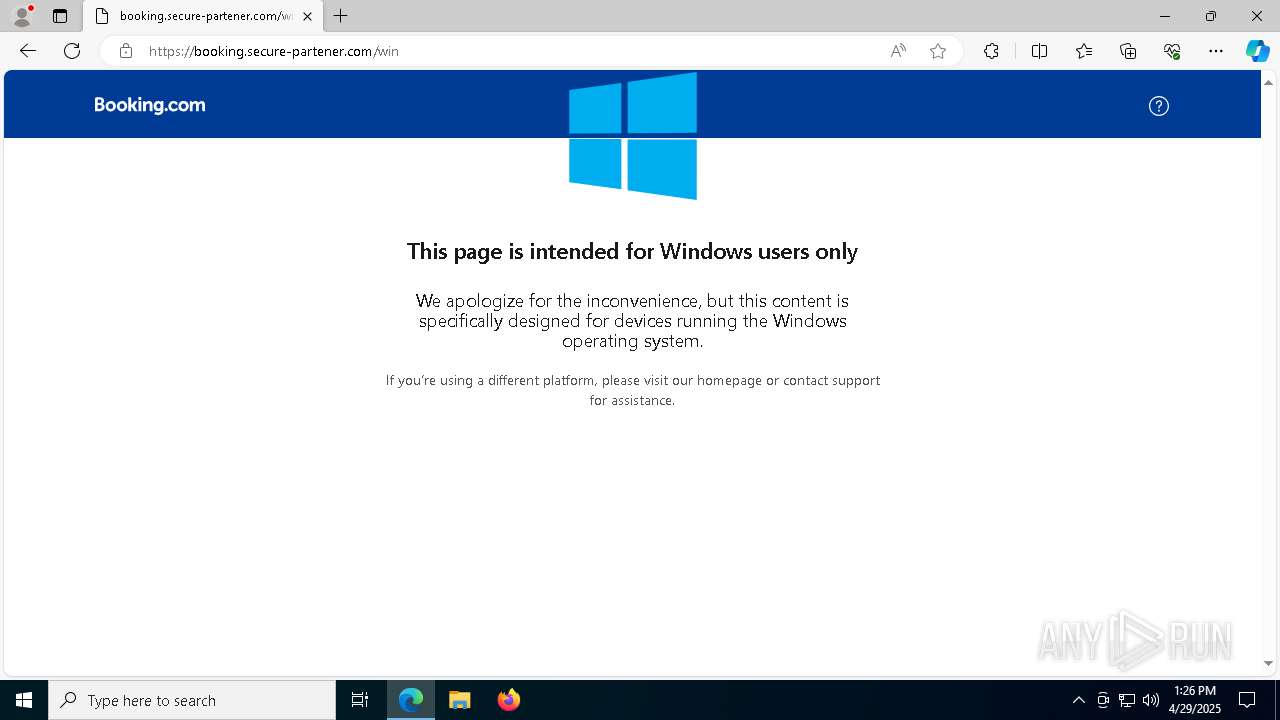
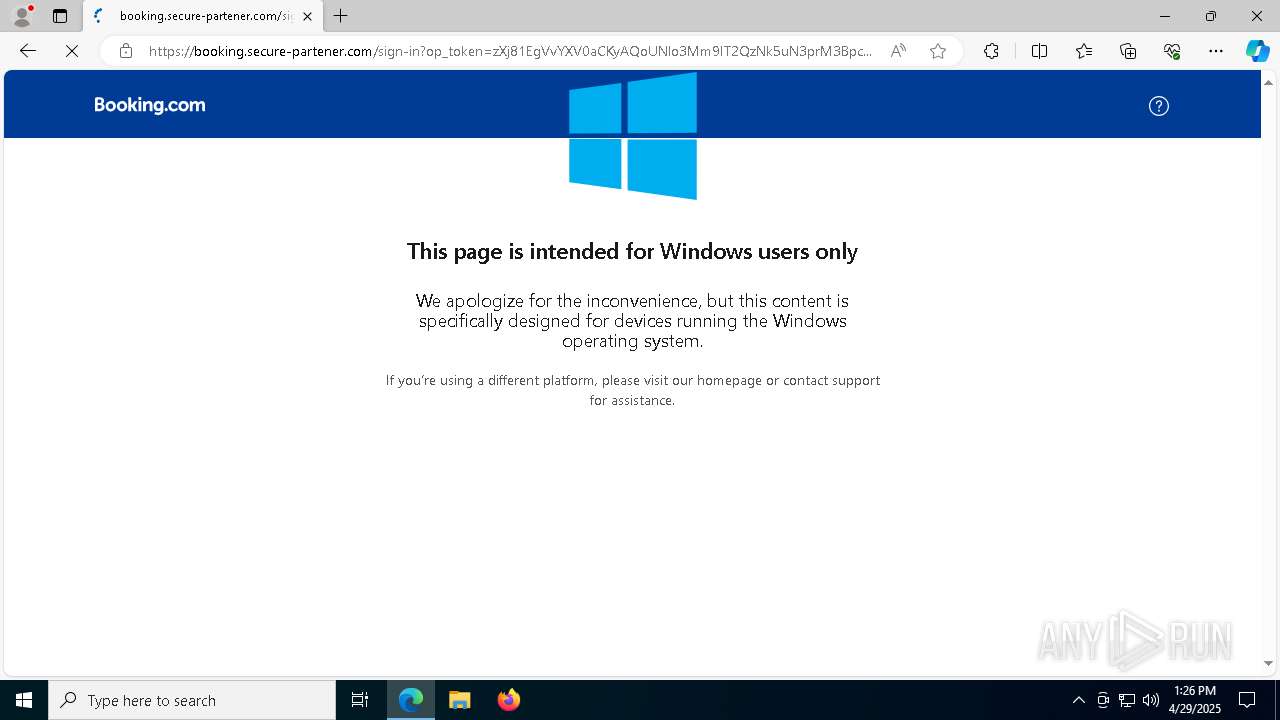
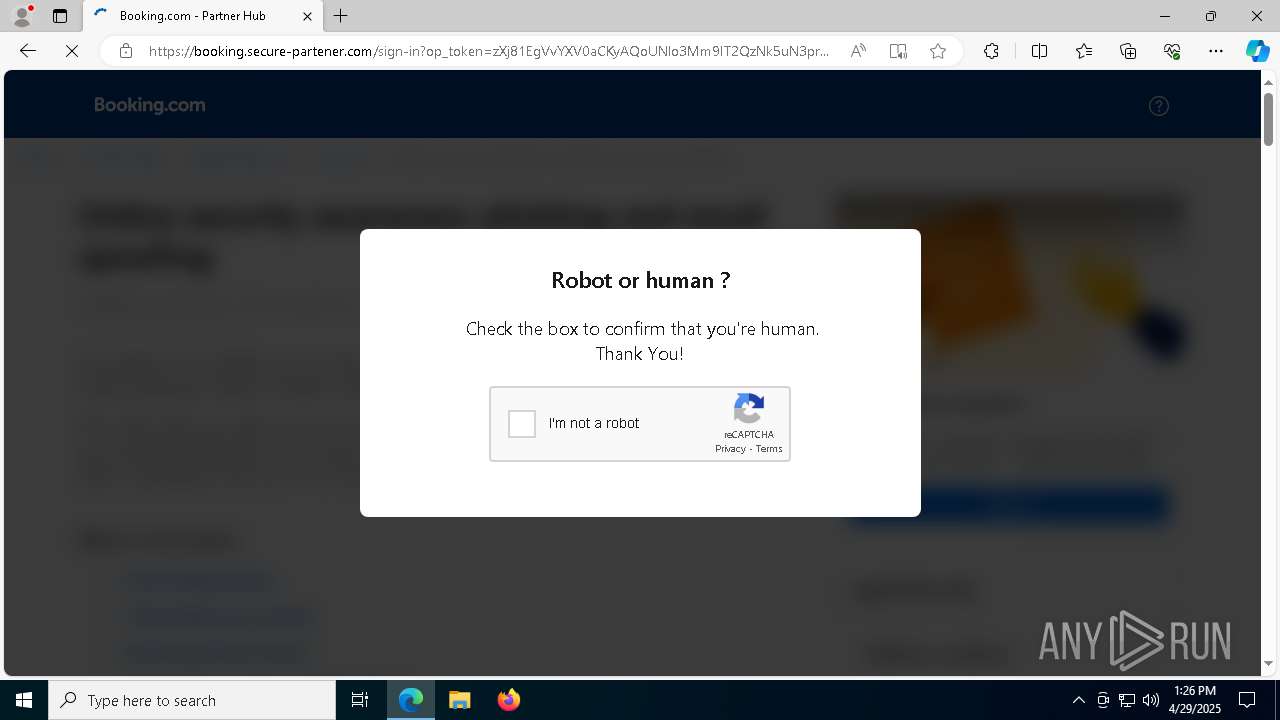
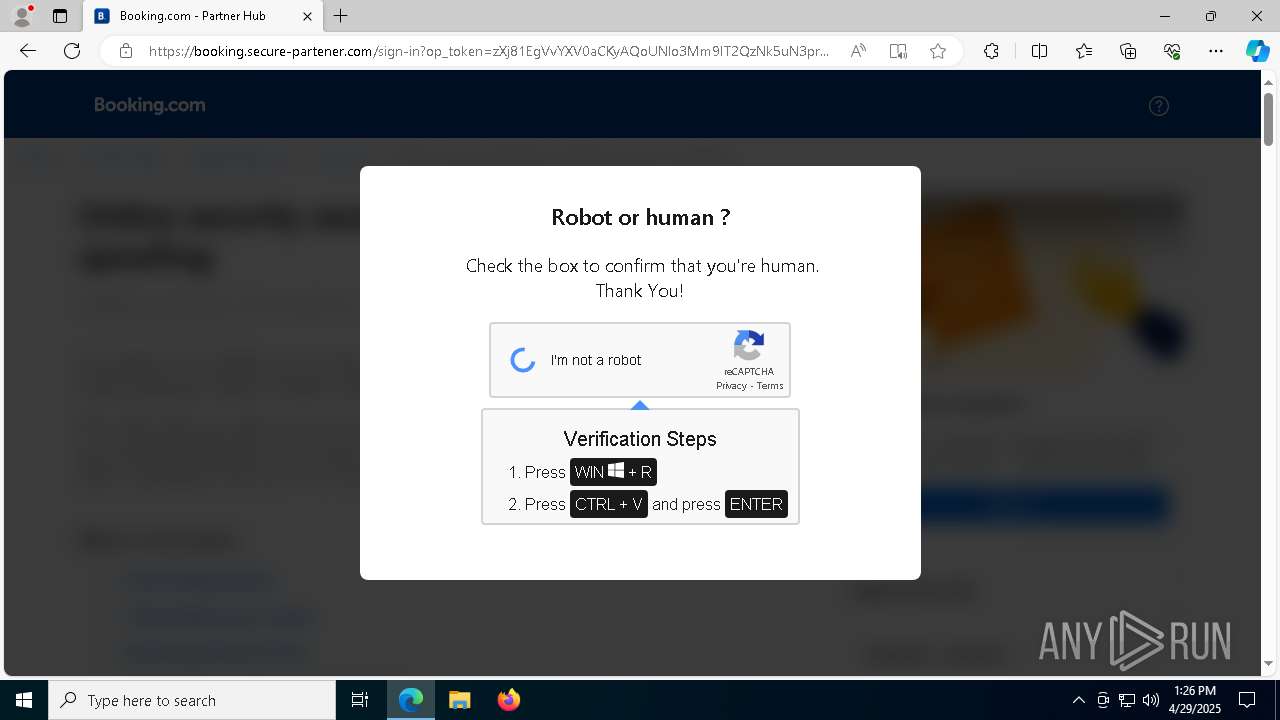
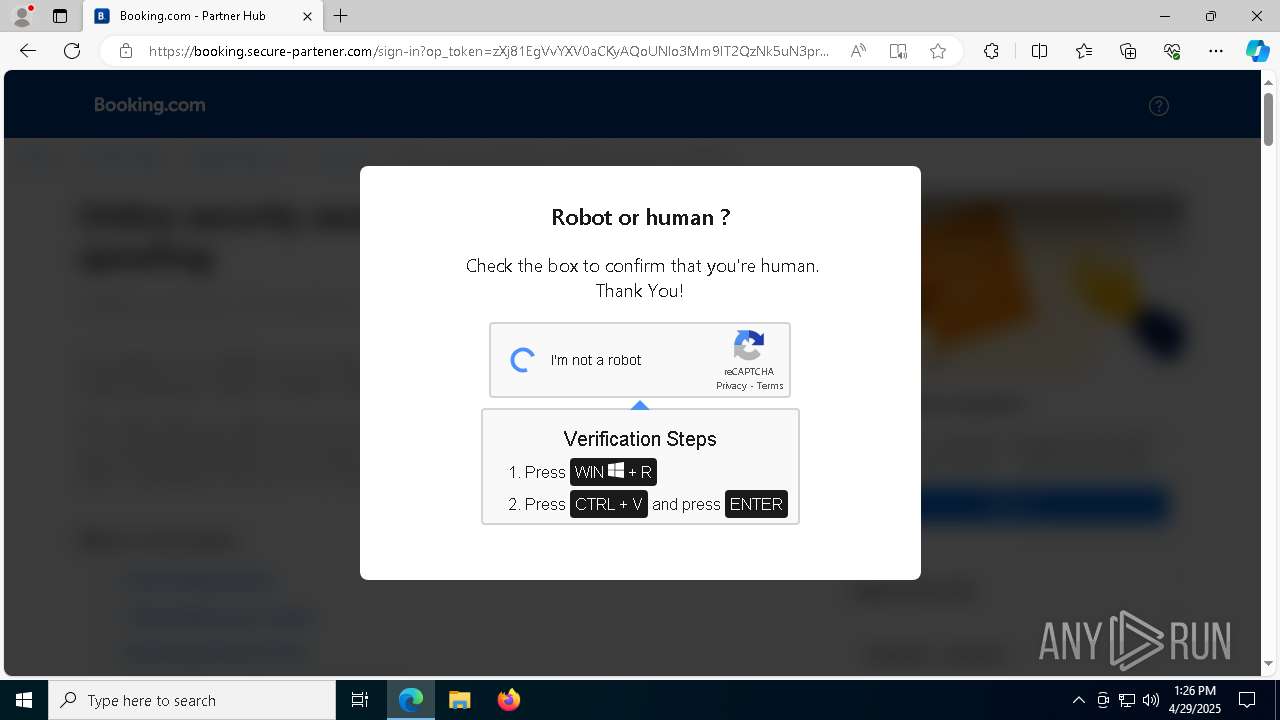
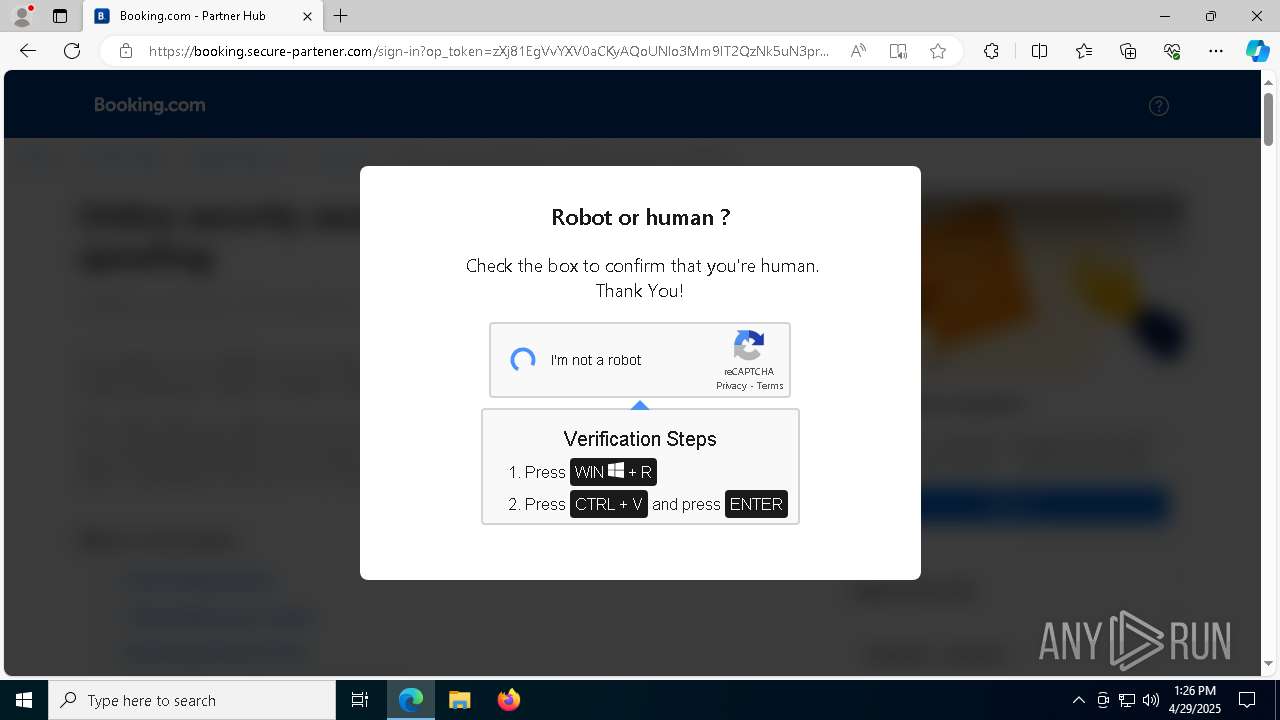
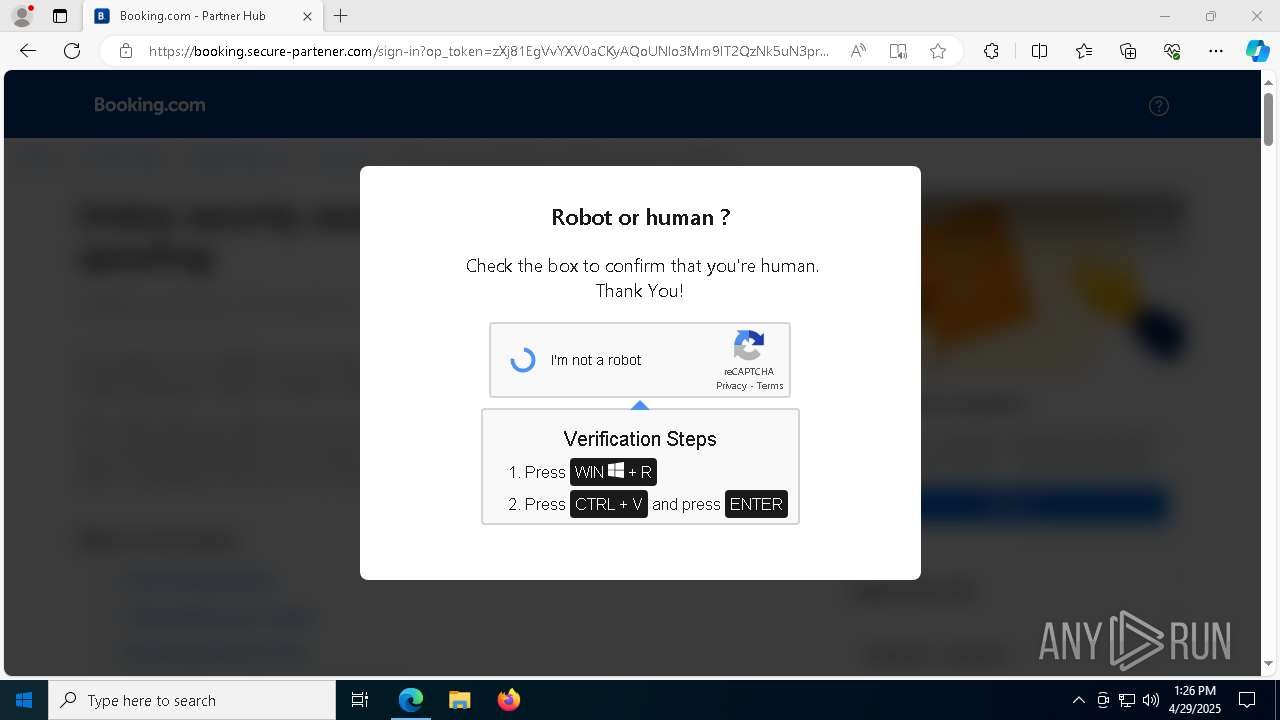
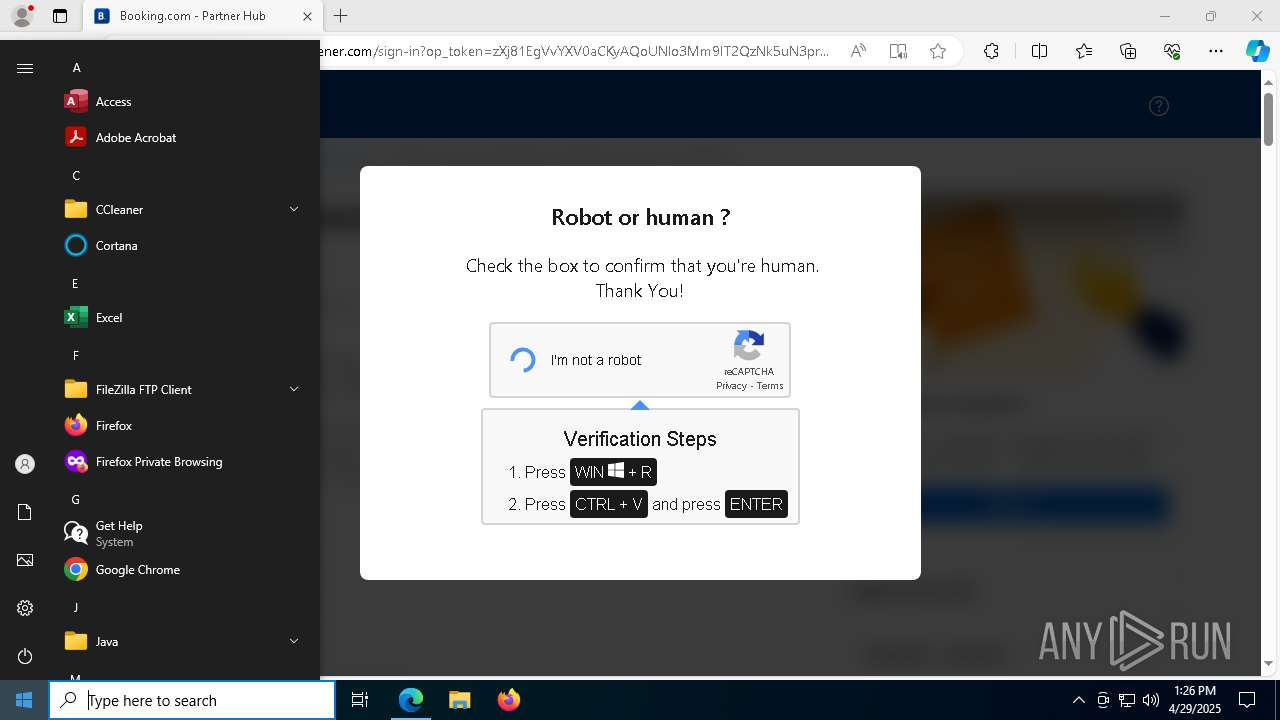
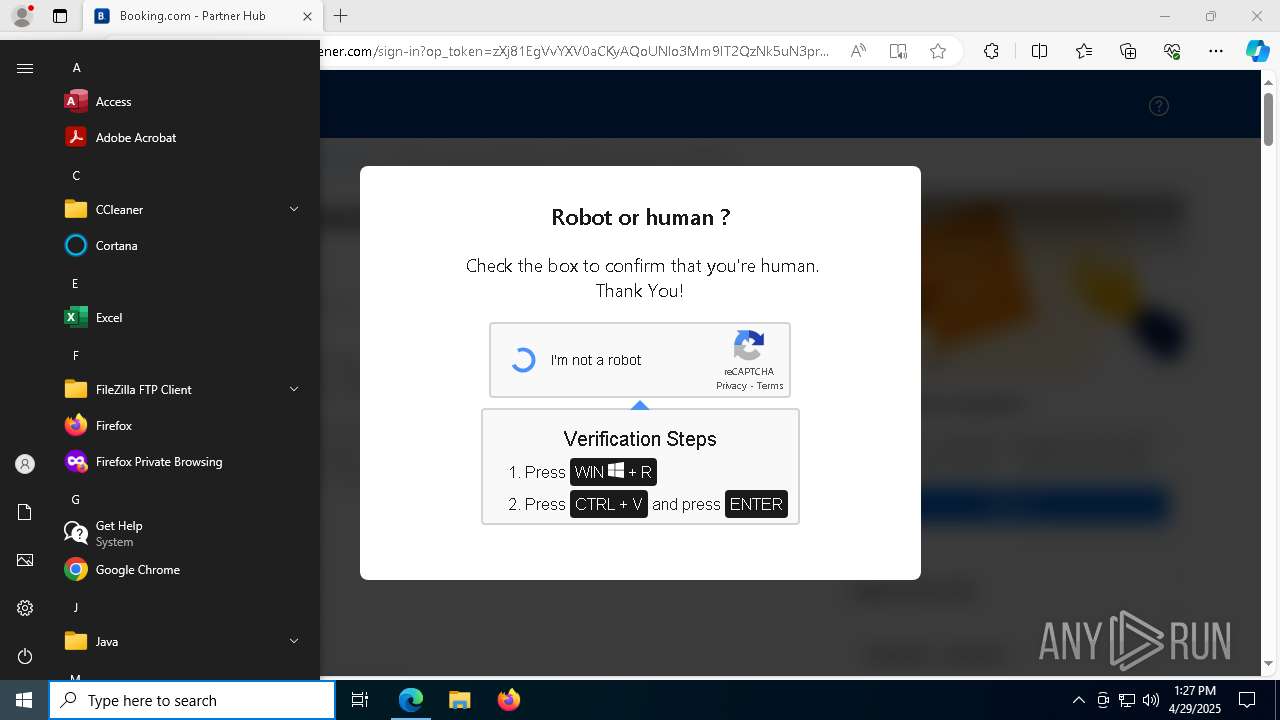
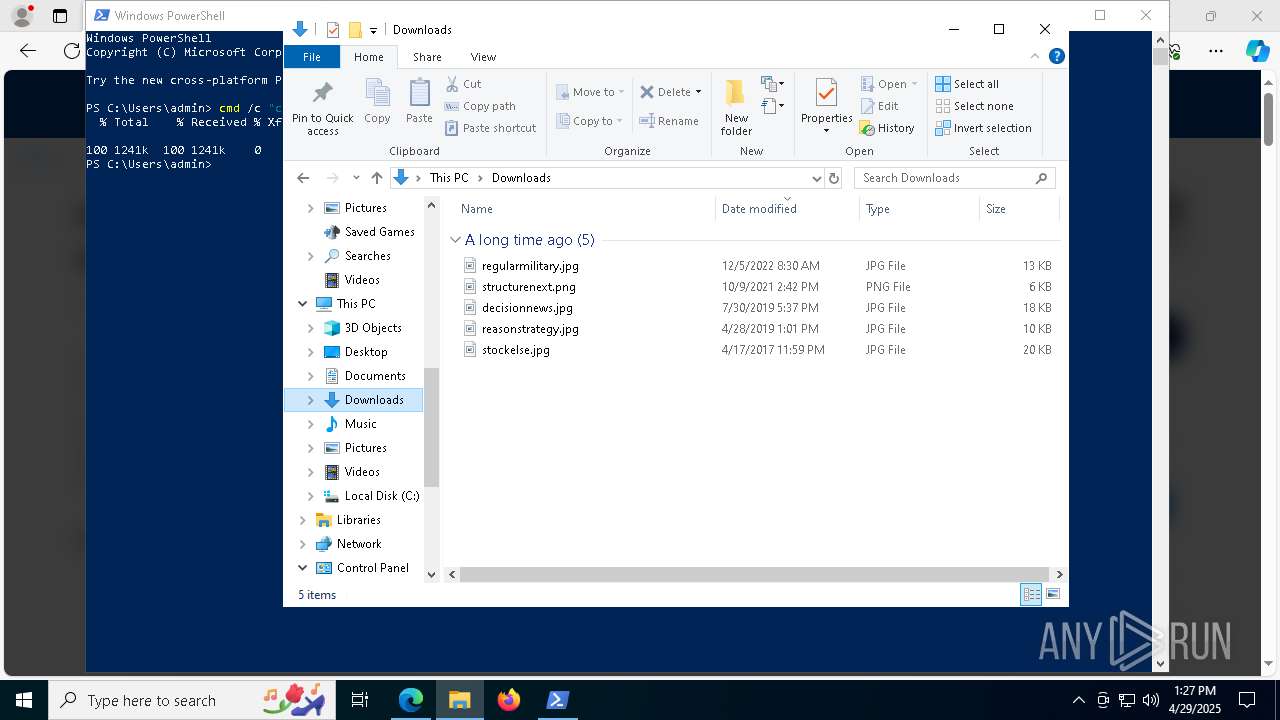
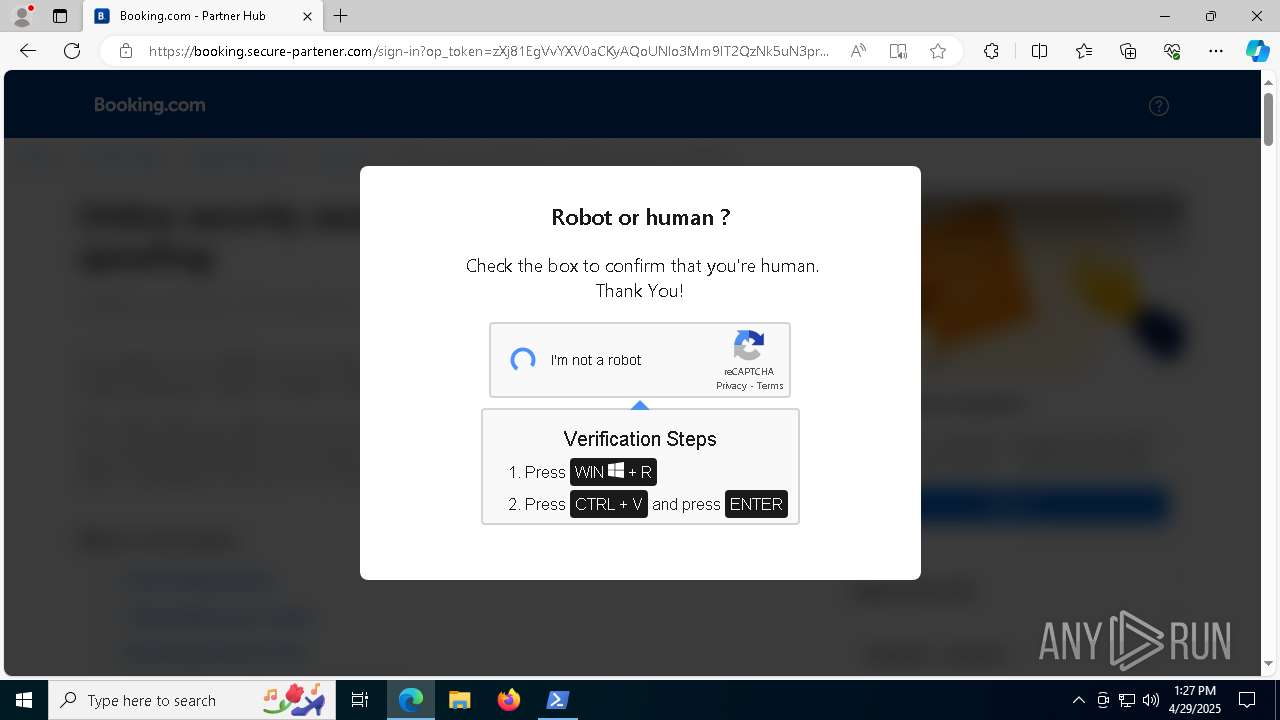
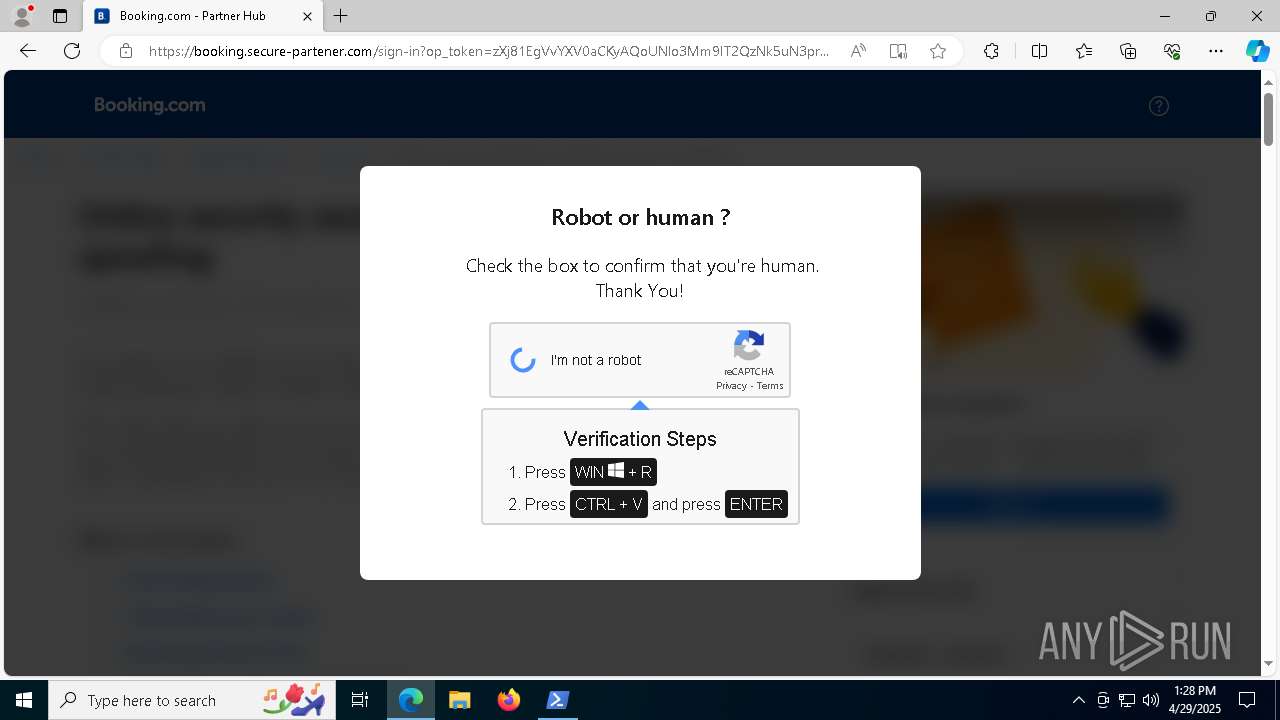
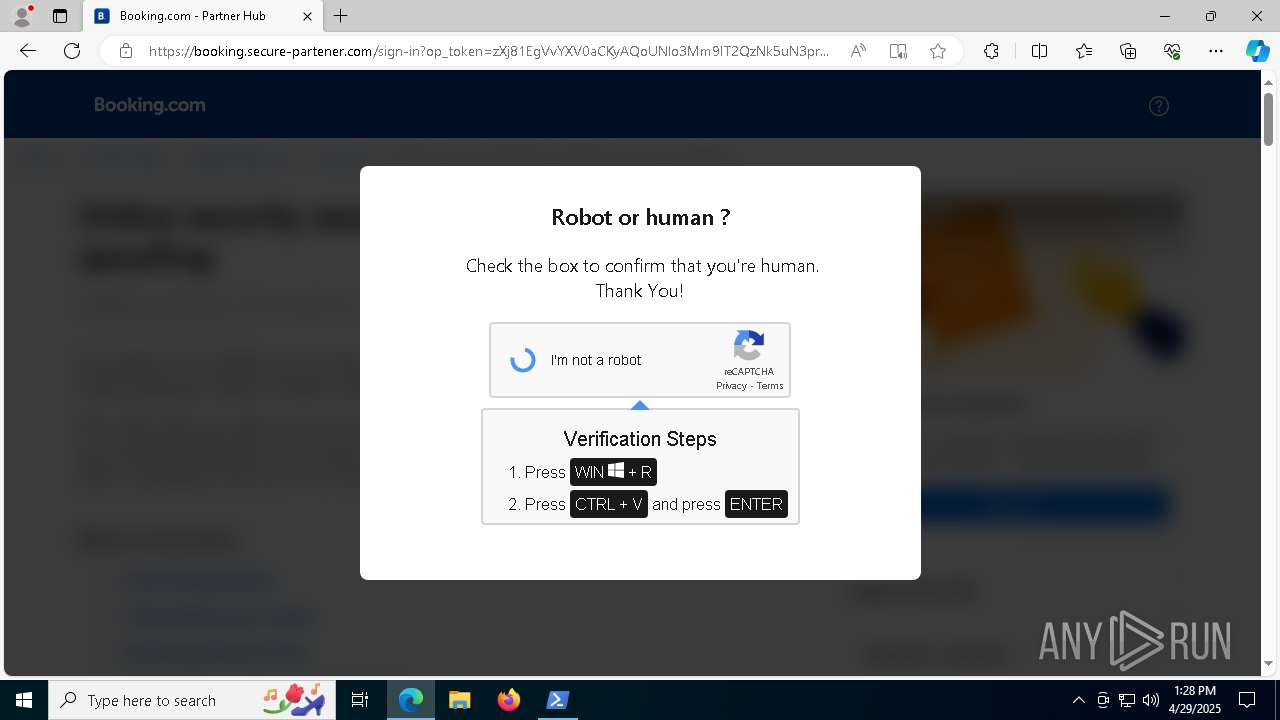
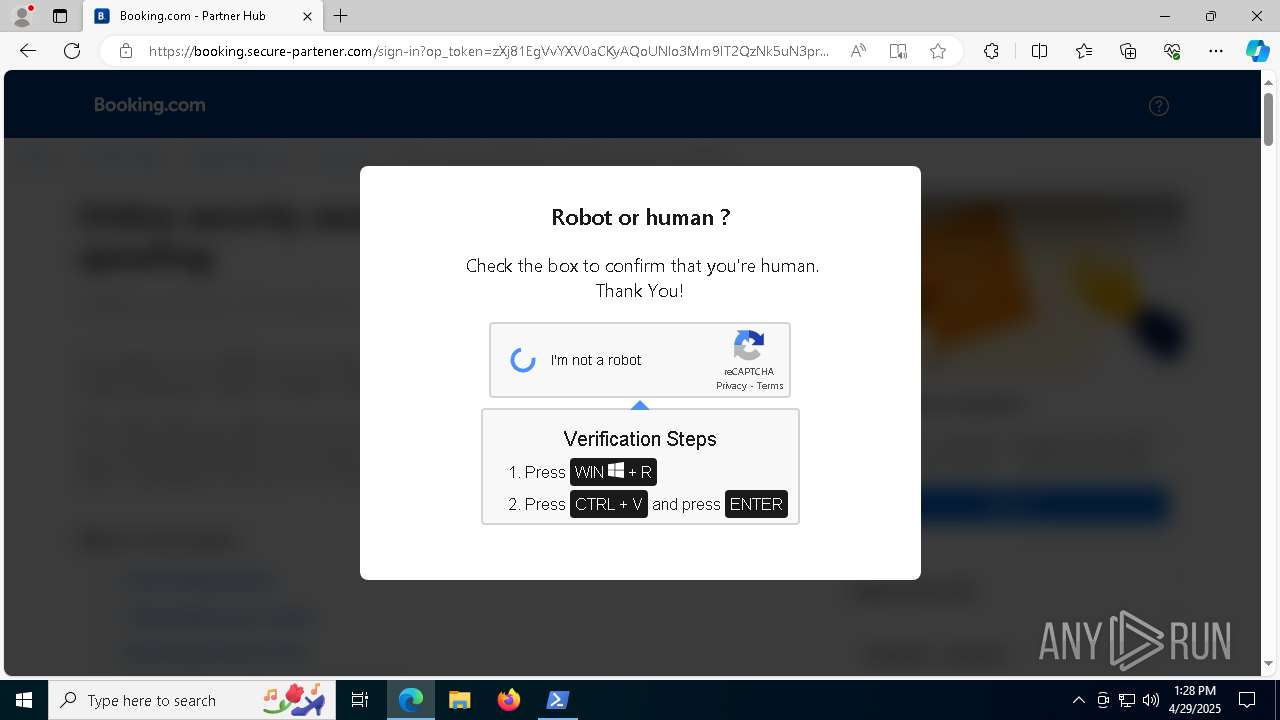
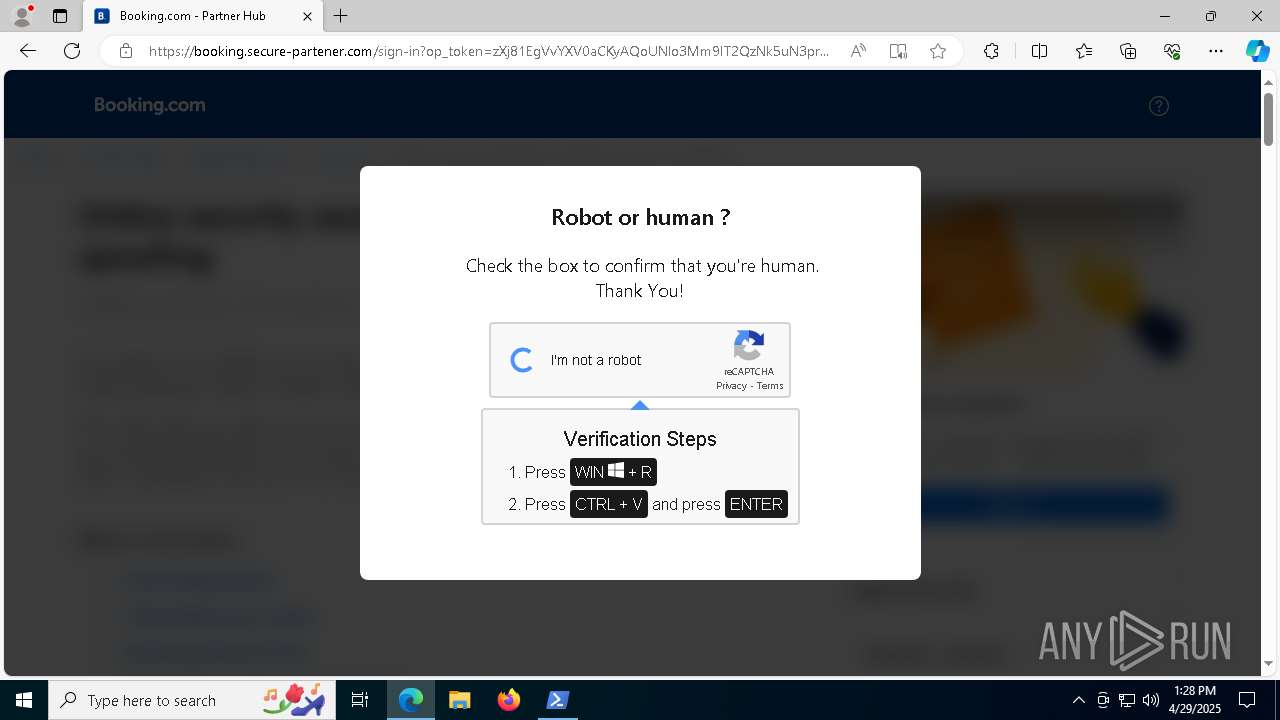
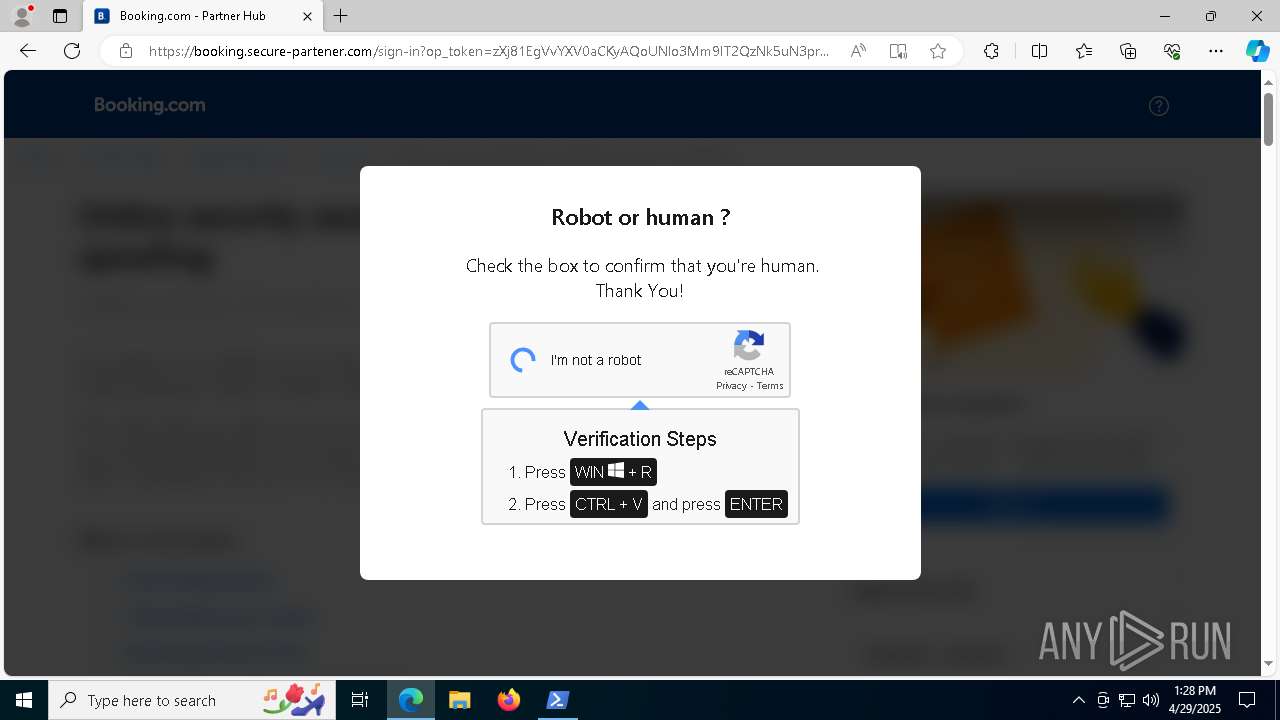
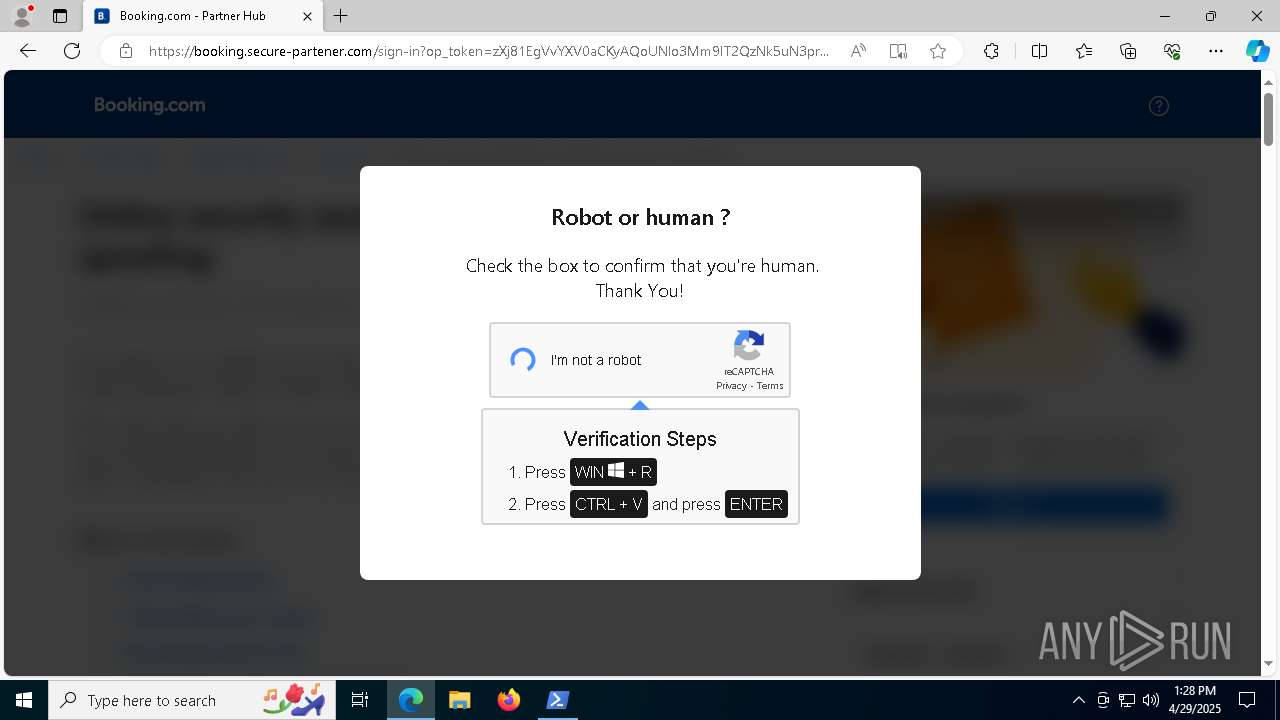
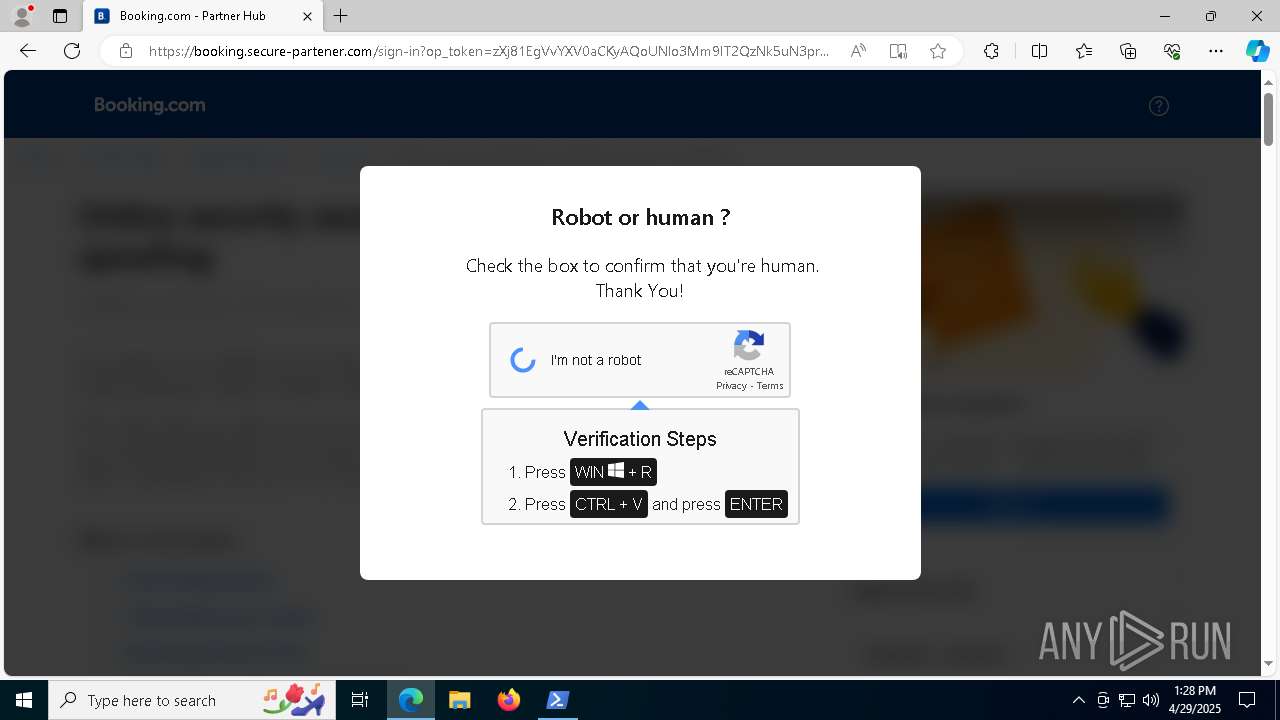
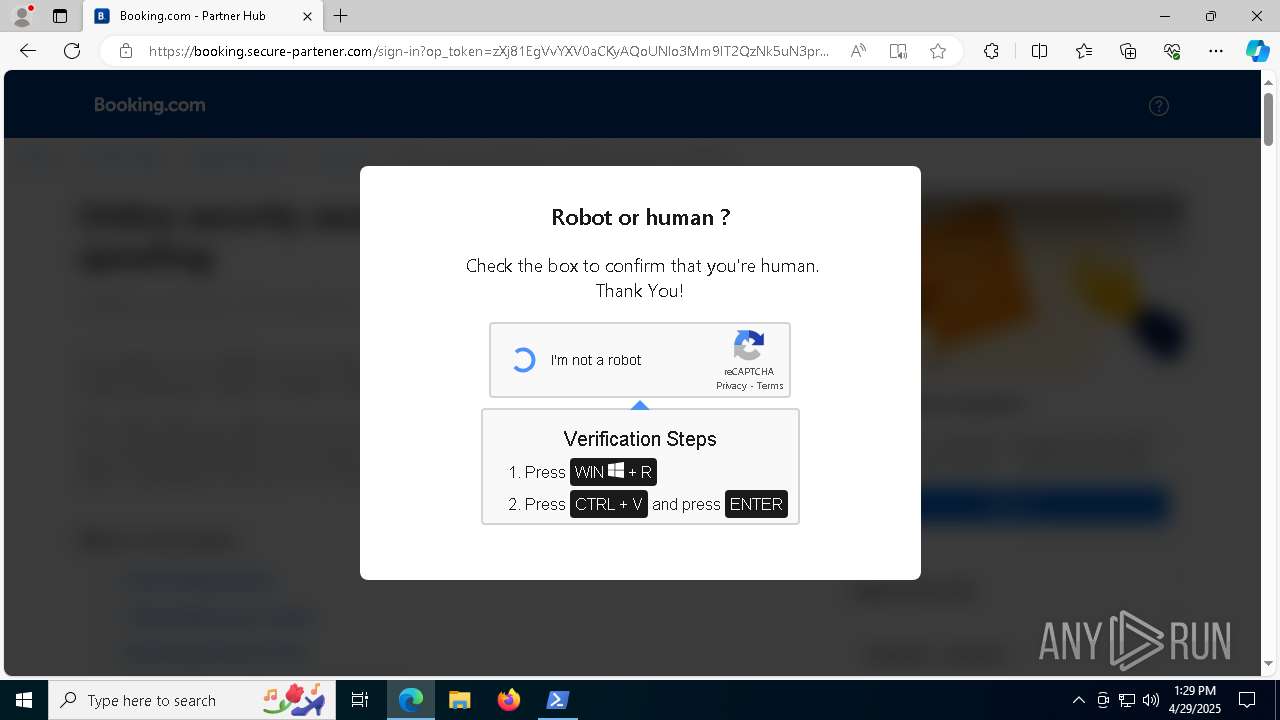
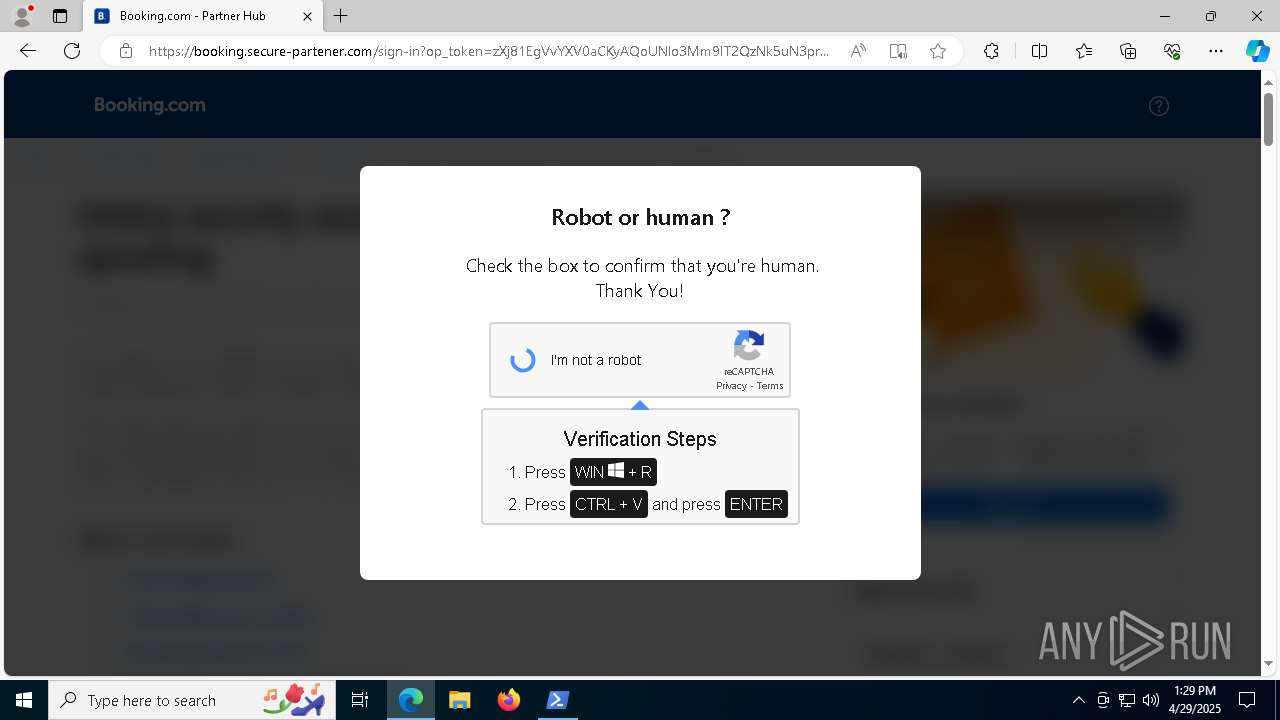
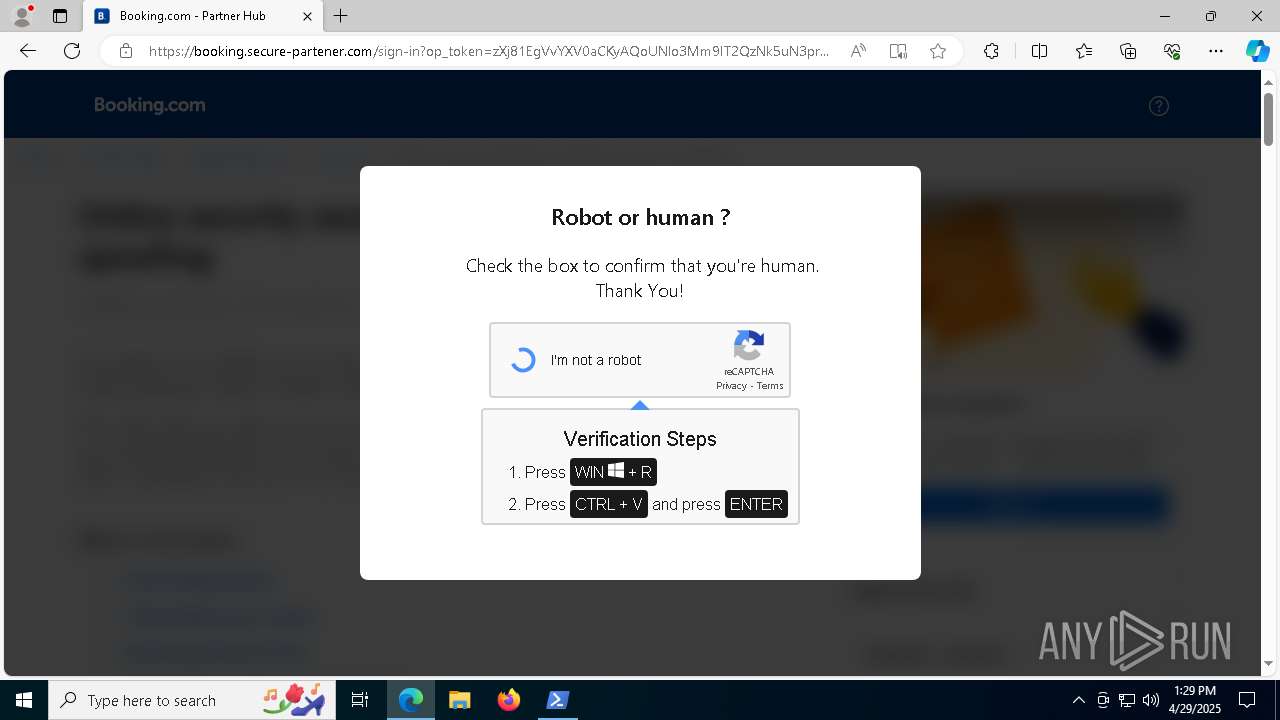
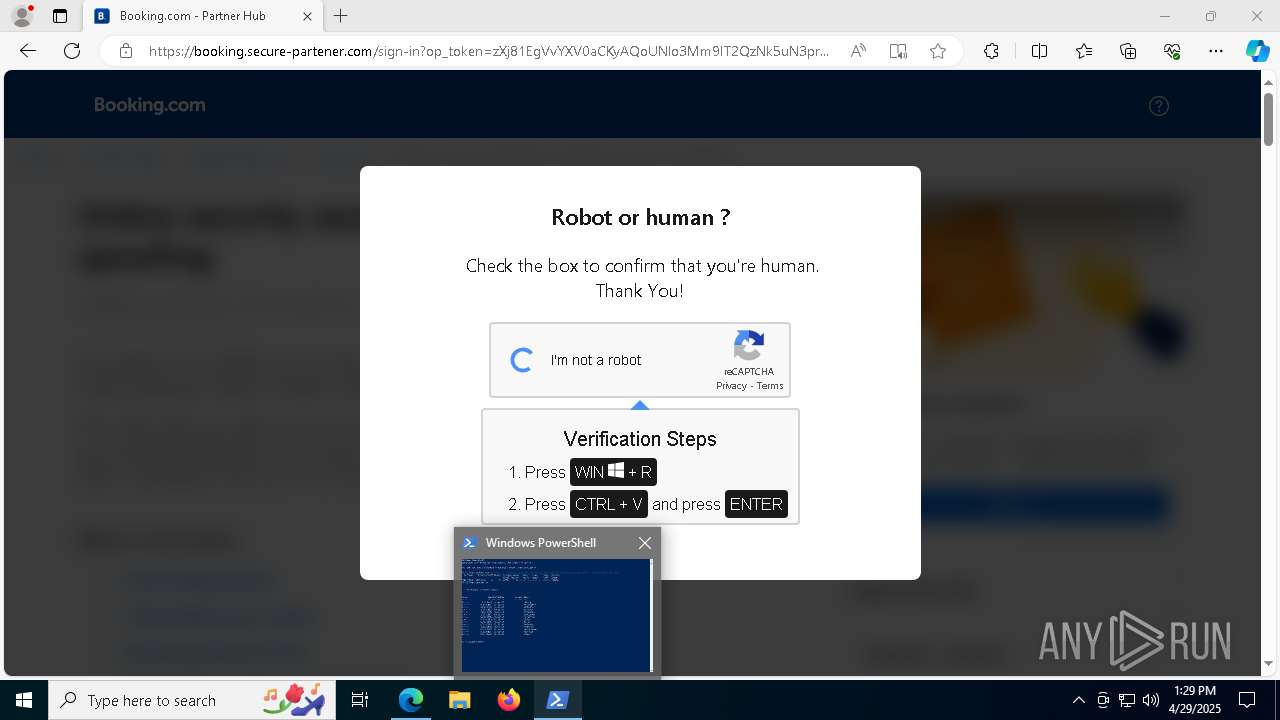
| URL: | https://booking.secure-partener.com/win |
| Full analysis: | https://app.any.run/tasks/20e535d0-a9e1-4384-b3f8-04e531aec55e |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 29, 2025, 13:26:10 |
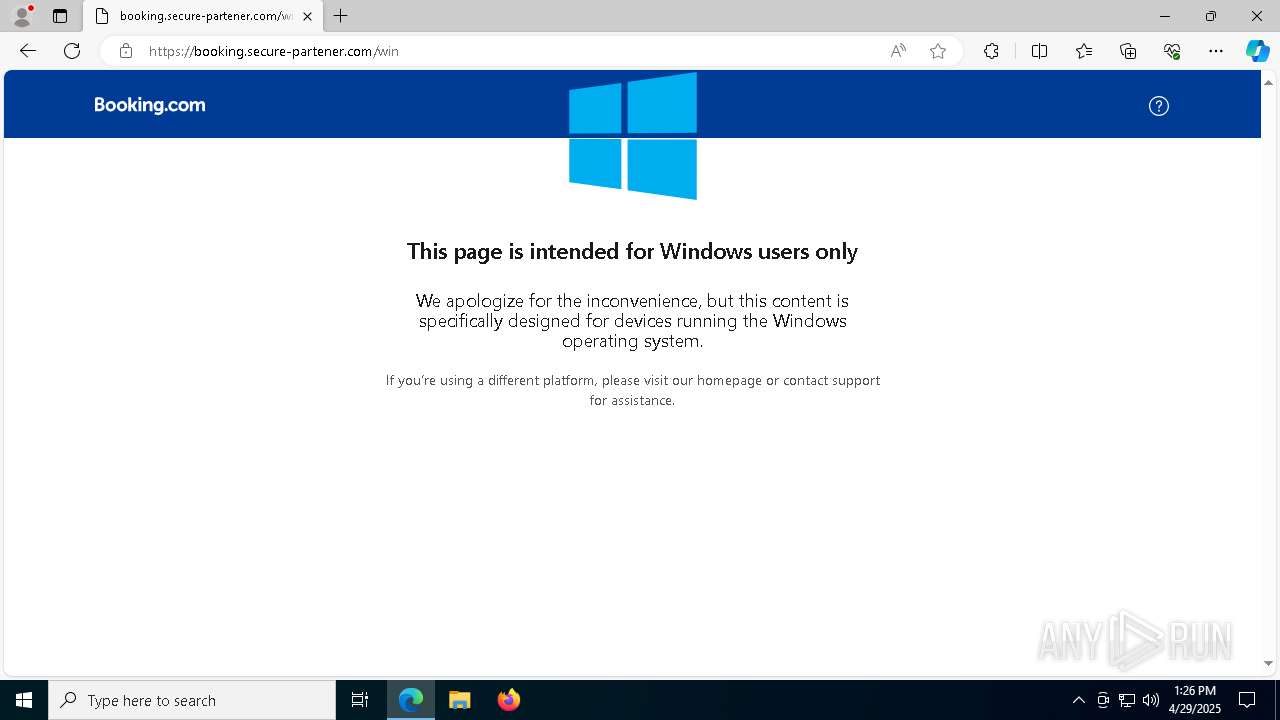
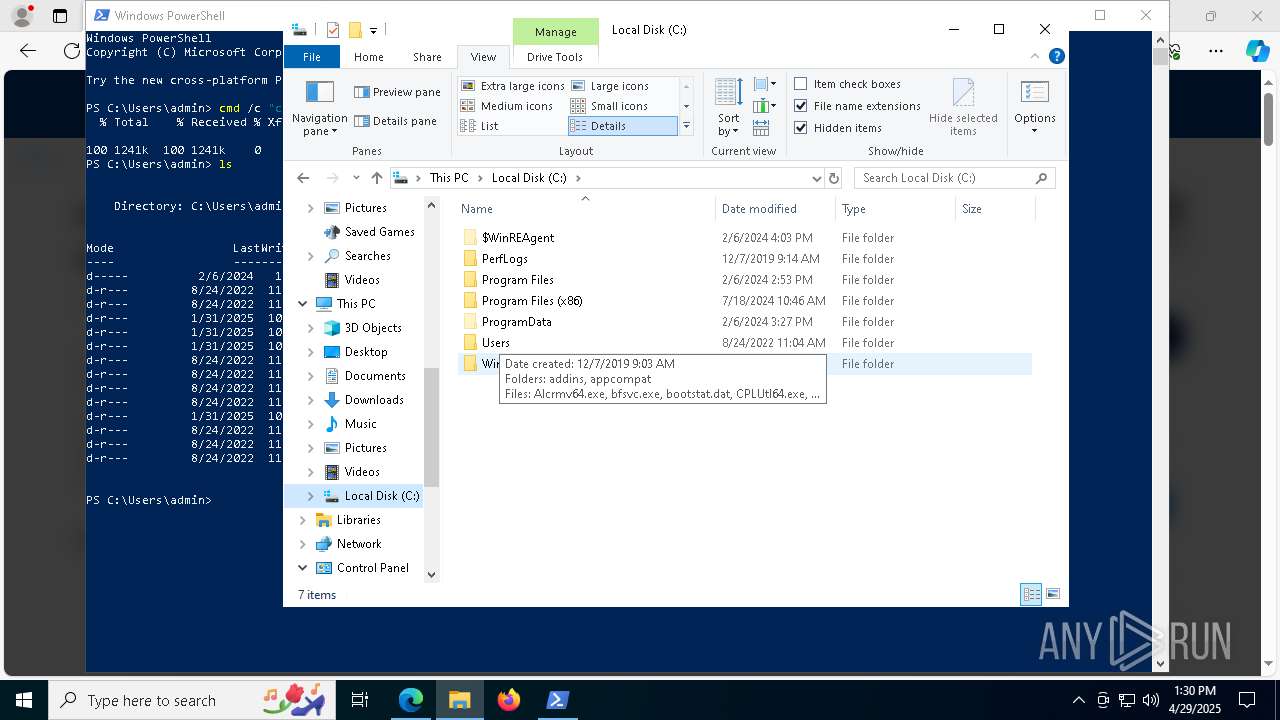
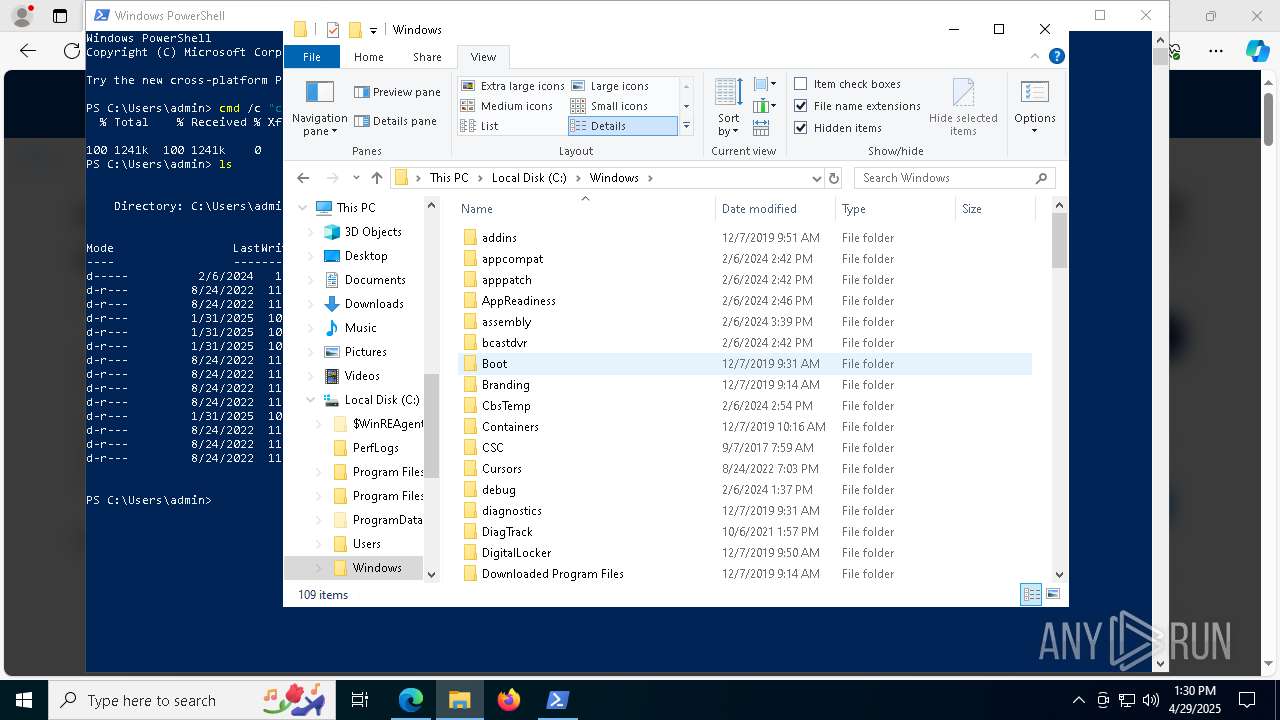
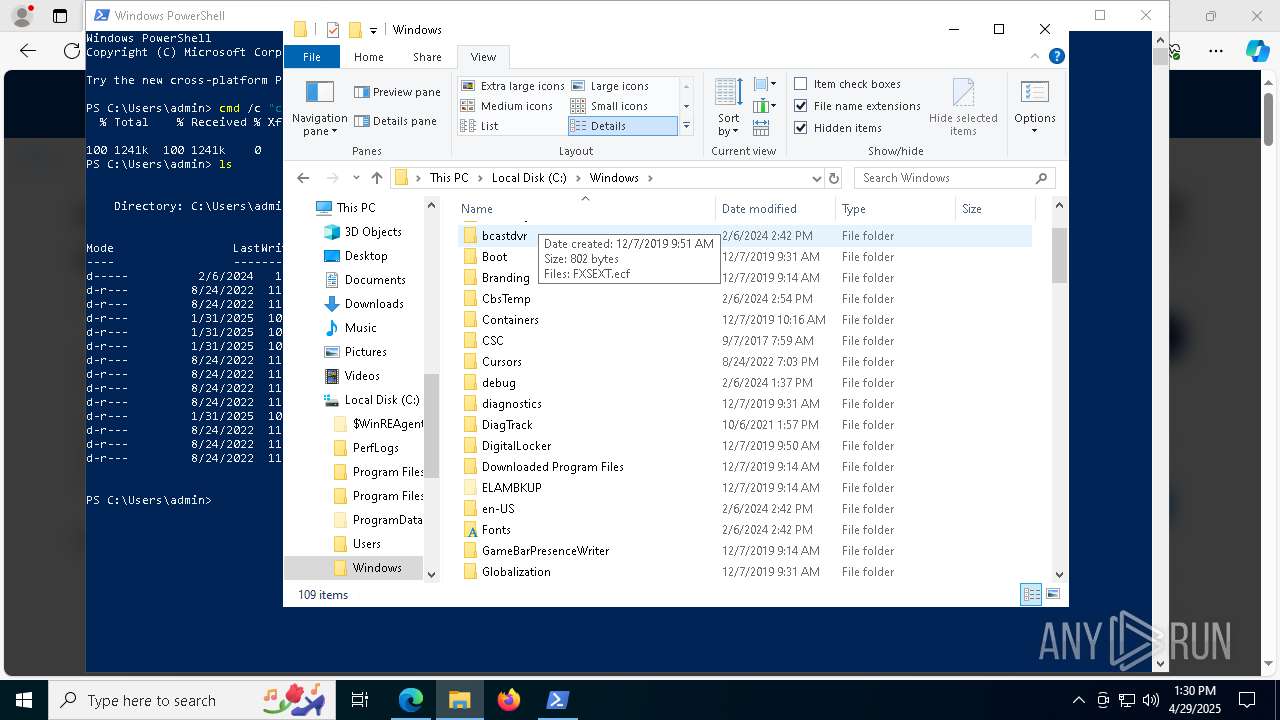
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2AEC5C64AB8DE853A635DD9829307B89 |
| SHA1: | 140A27A50BA56733B6E06273D5EE89C191430947 |
| SHA256: | 4681AAFE2D7CC7C703F755AC95510AE5A3571FE122D0282158AAF1FCEF0713EC |
| SSDEEP: | 3:N8ScsXty5L:2SG |
MALICIOUS
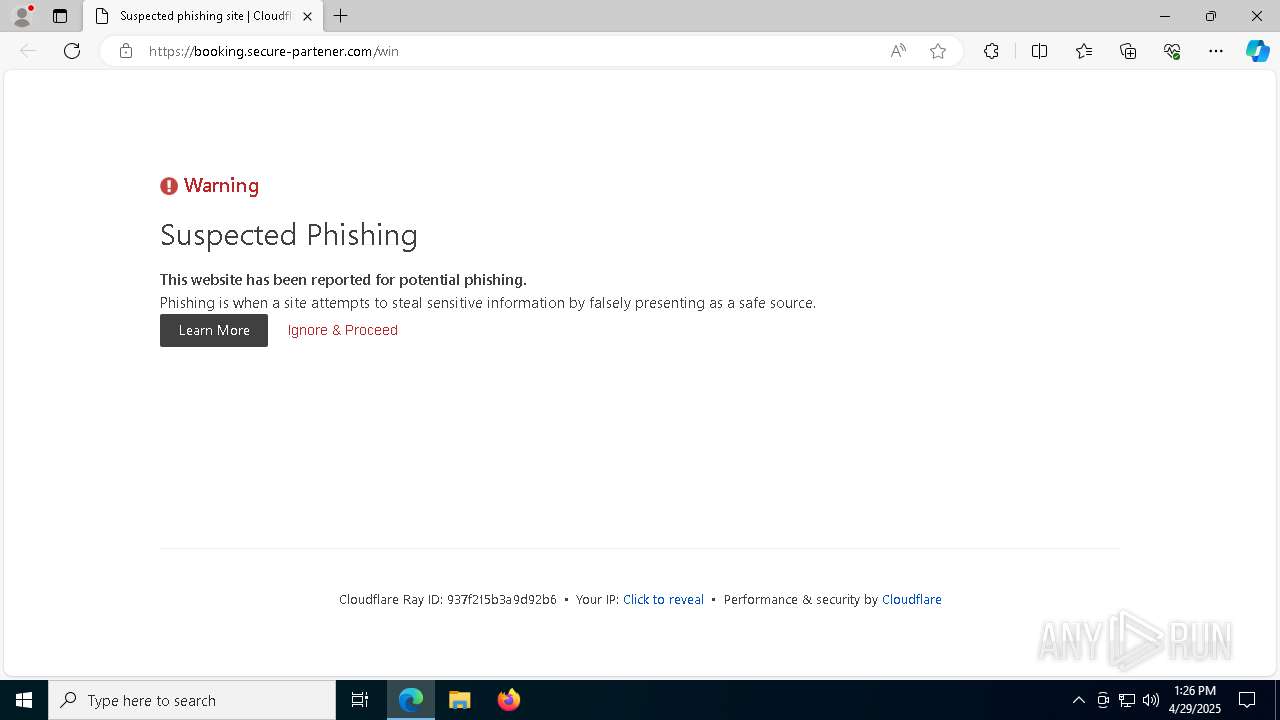
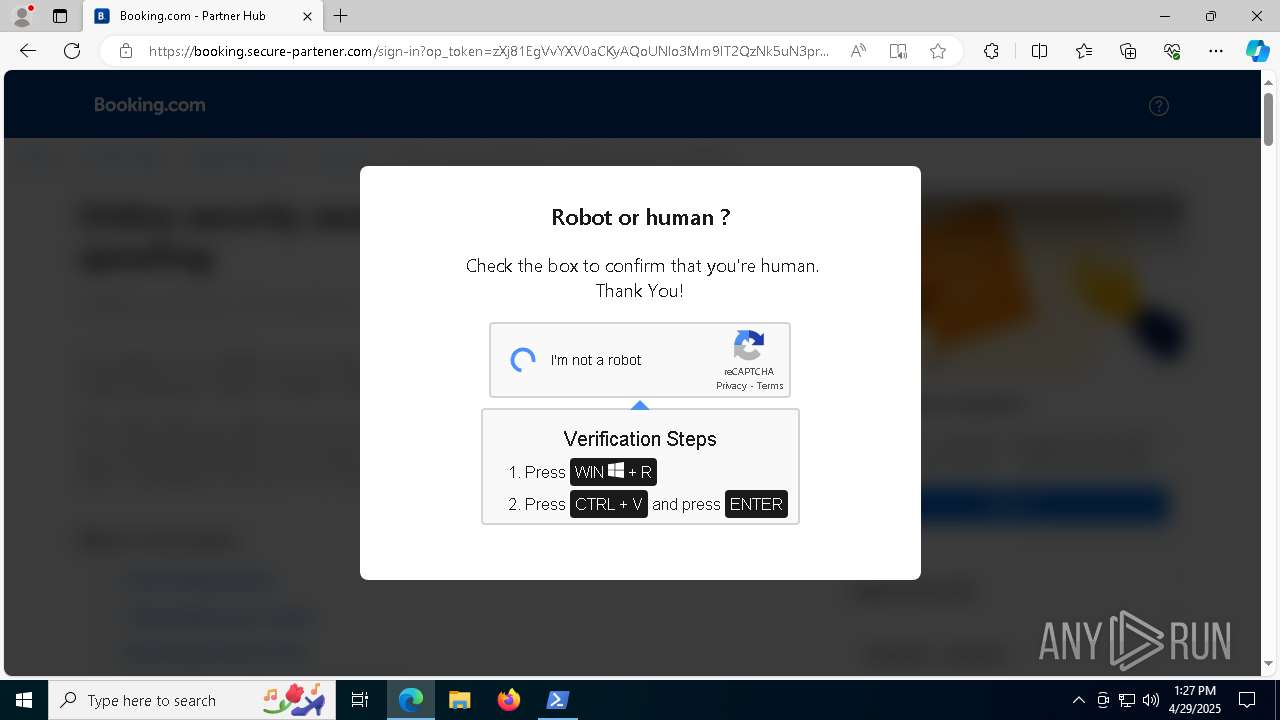
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7780)
Adds path to the Windows Defender exclusion list
- xSg.exe (PID: 8740)
Changes Windows Defender settings
- xSg.exe (PID: 8740)
RAT has been found (auto)
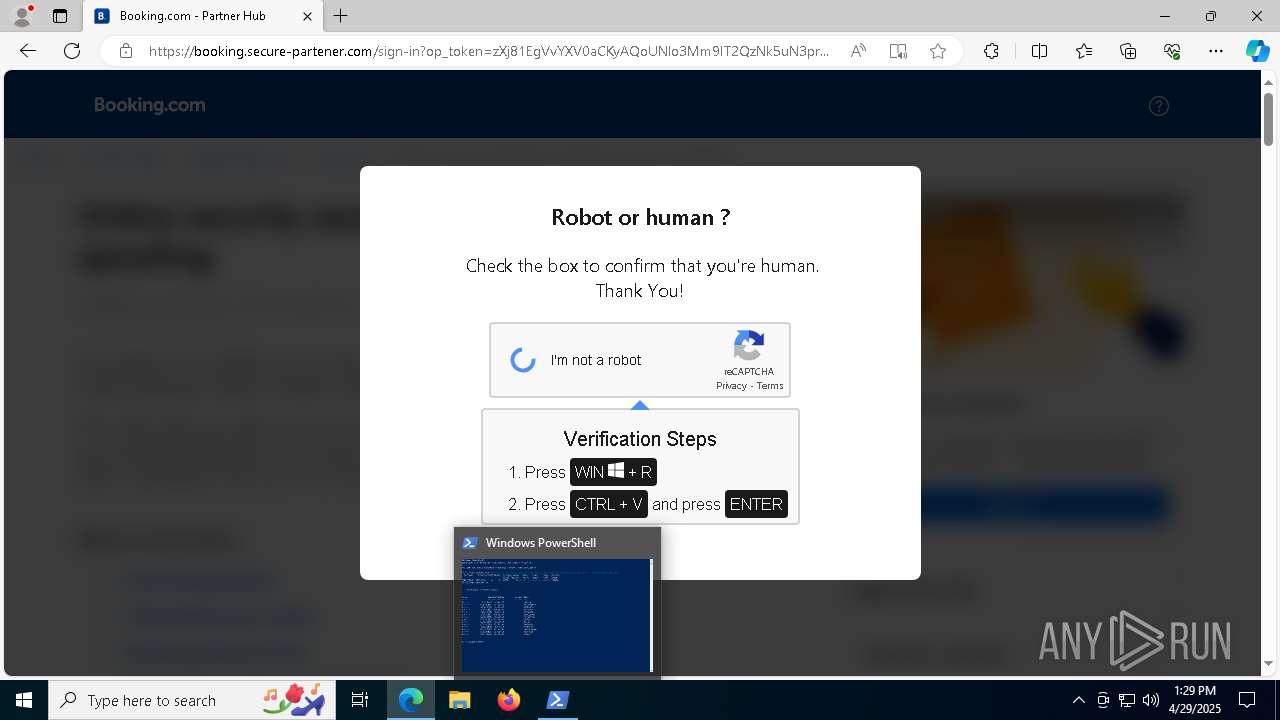
- powershell.exe (PID: 4200)
- rbcoa.exe (PID: 8512)
Executing a file with an untrusted certificate
- rbcoa.exe (PID: 8512)
ASYNCRAT has been detected (SURICATA)
- MSBuild.exe (PID: 1164)
ASYNCRAT has been detected (YARA)
- MSBuild.exe (PID: 1164)
SUSPICIOUS
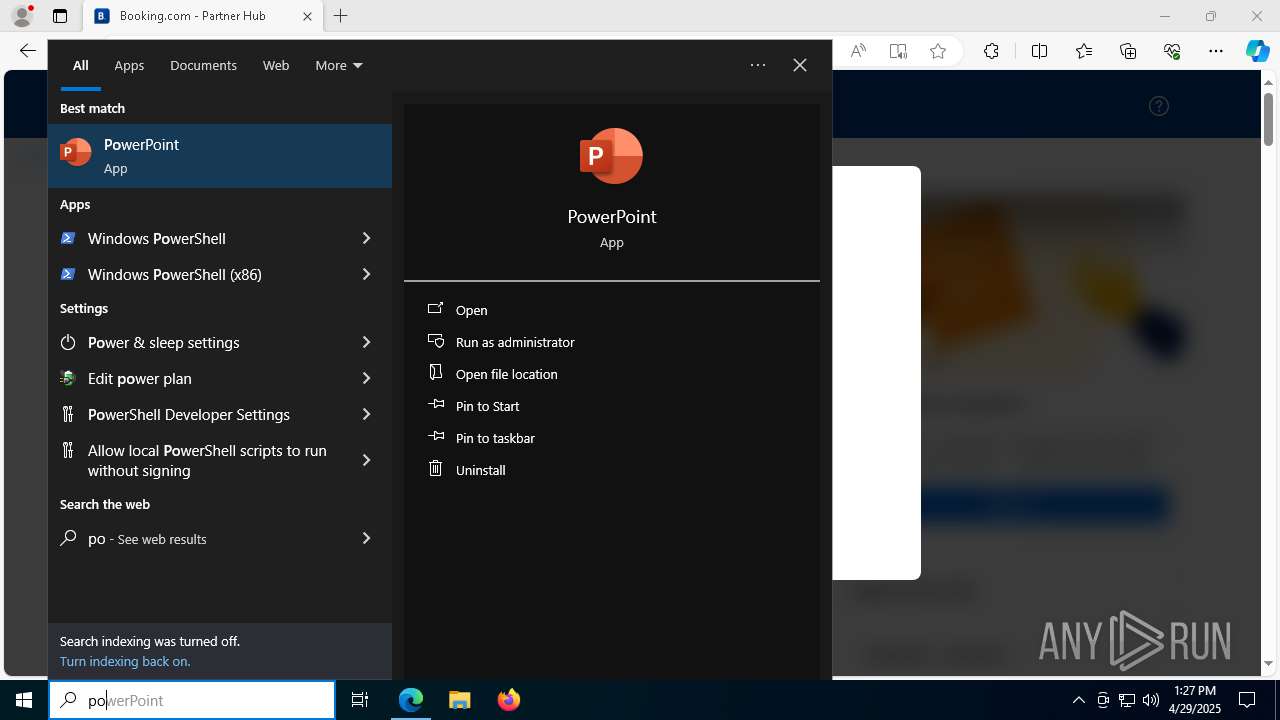
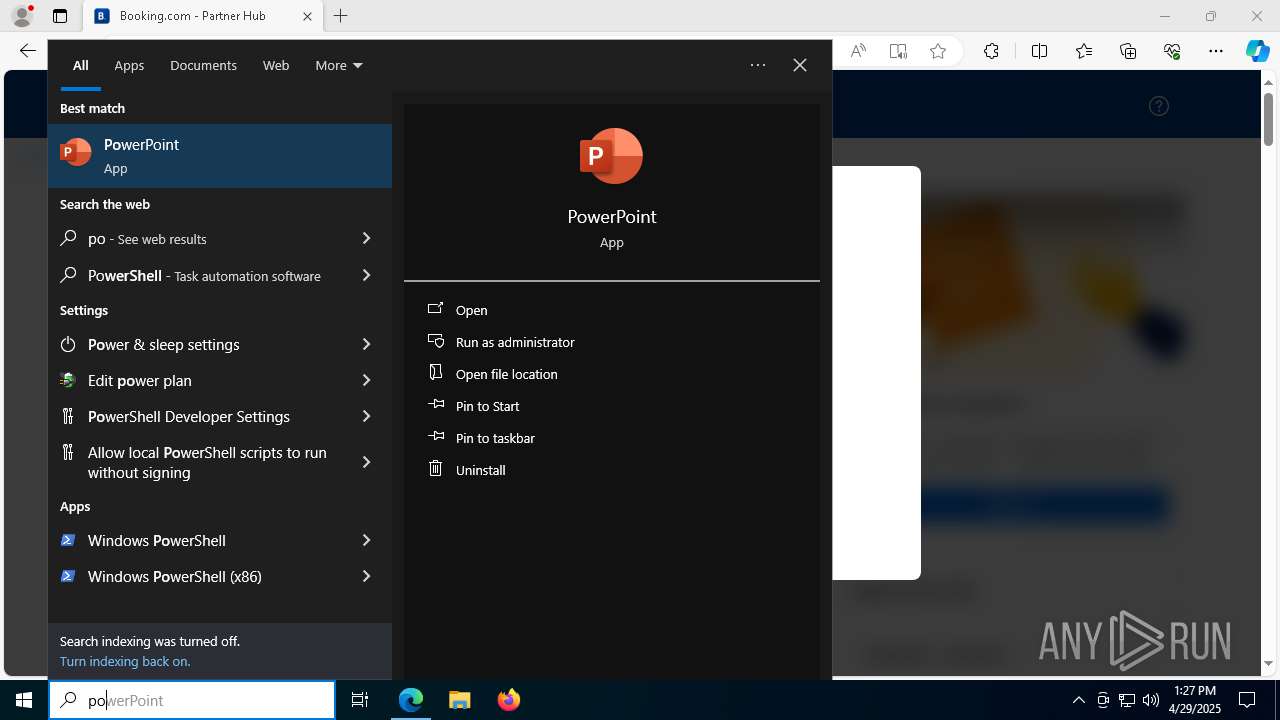
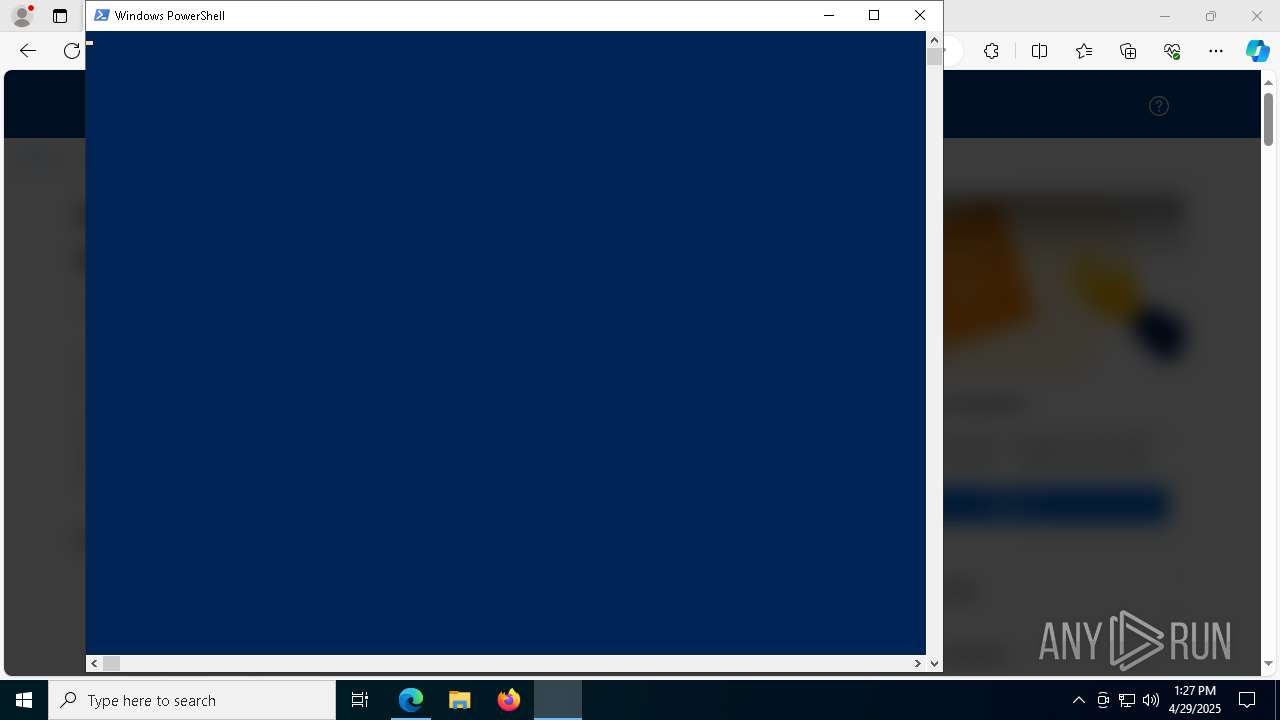
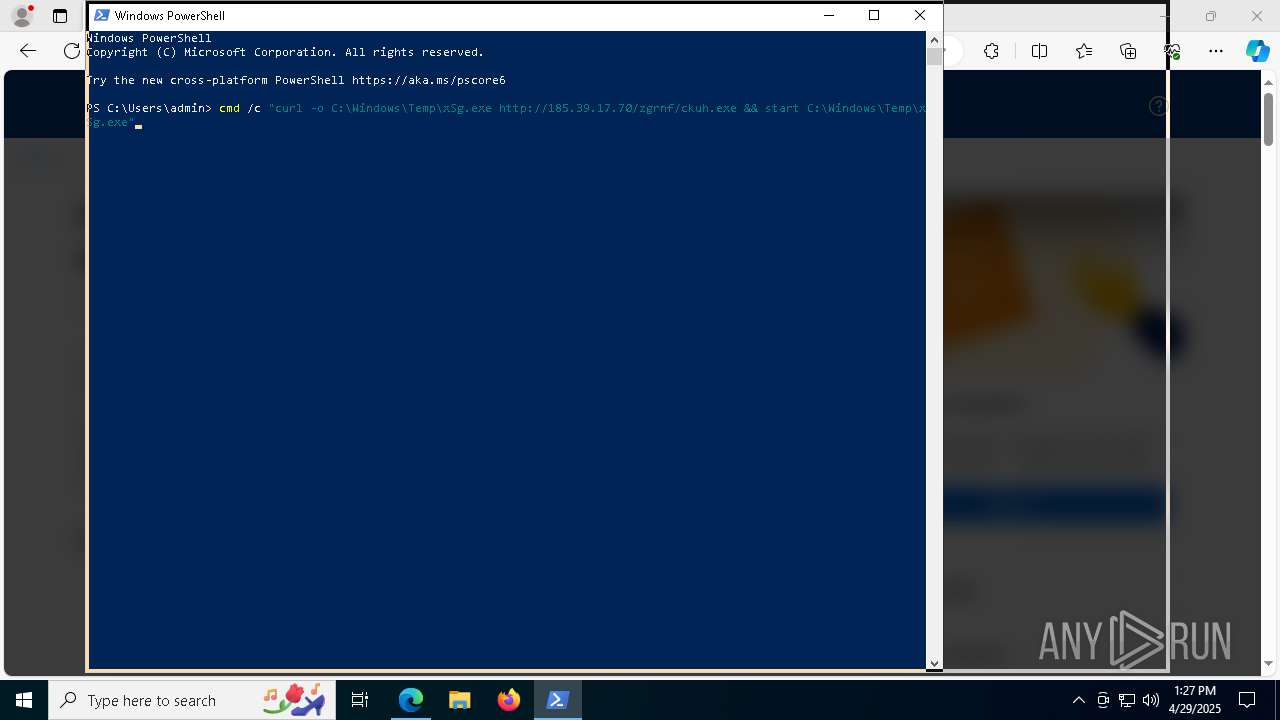
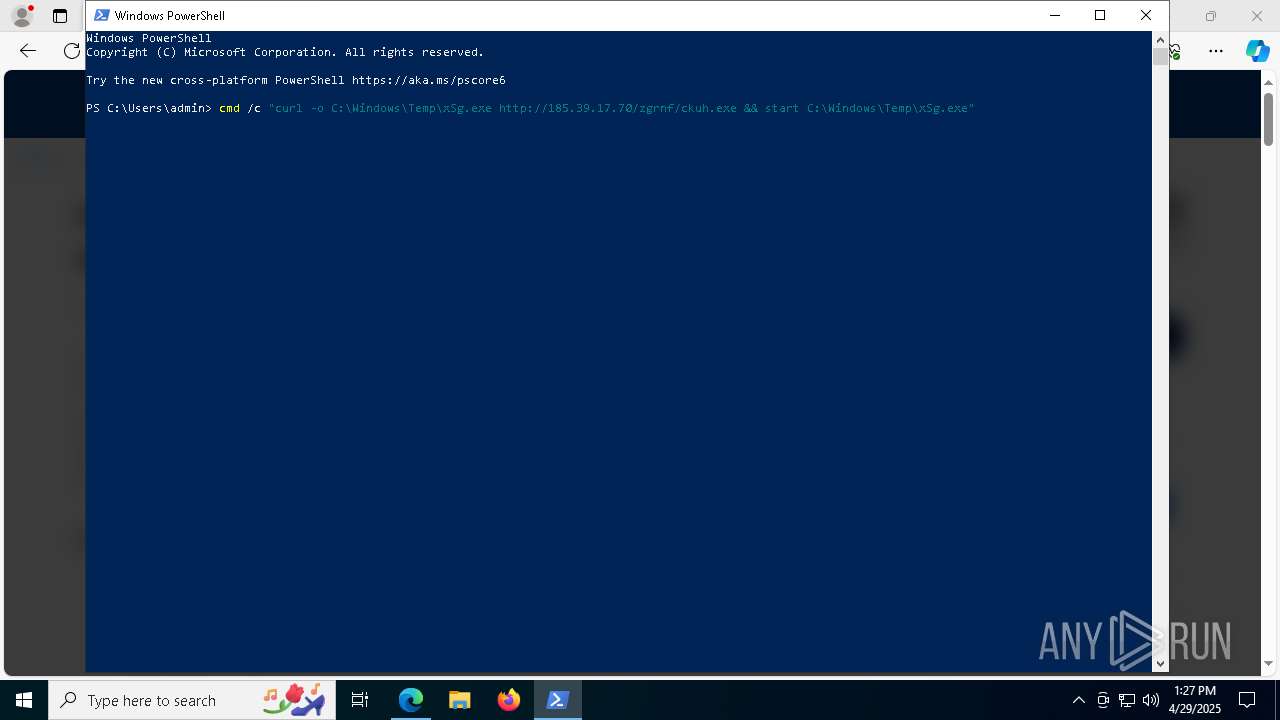
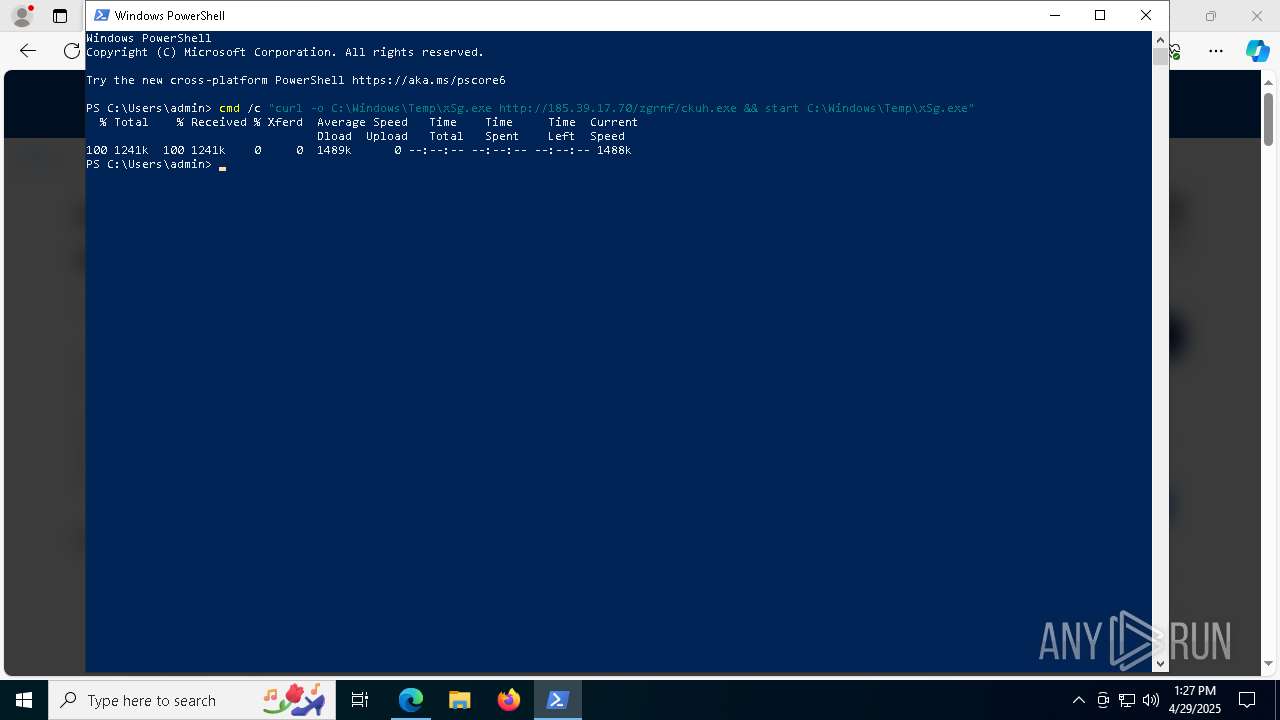
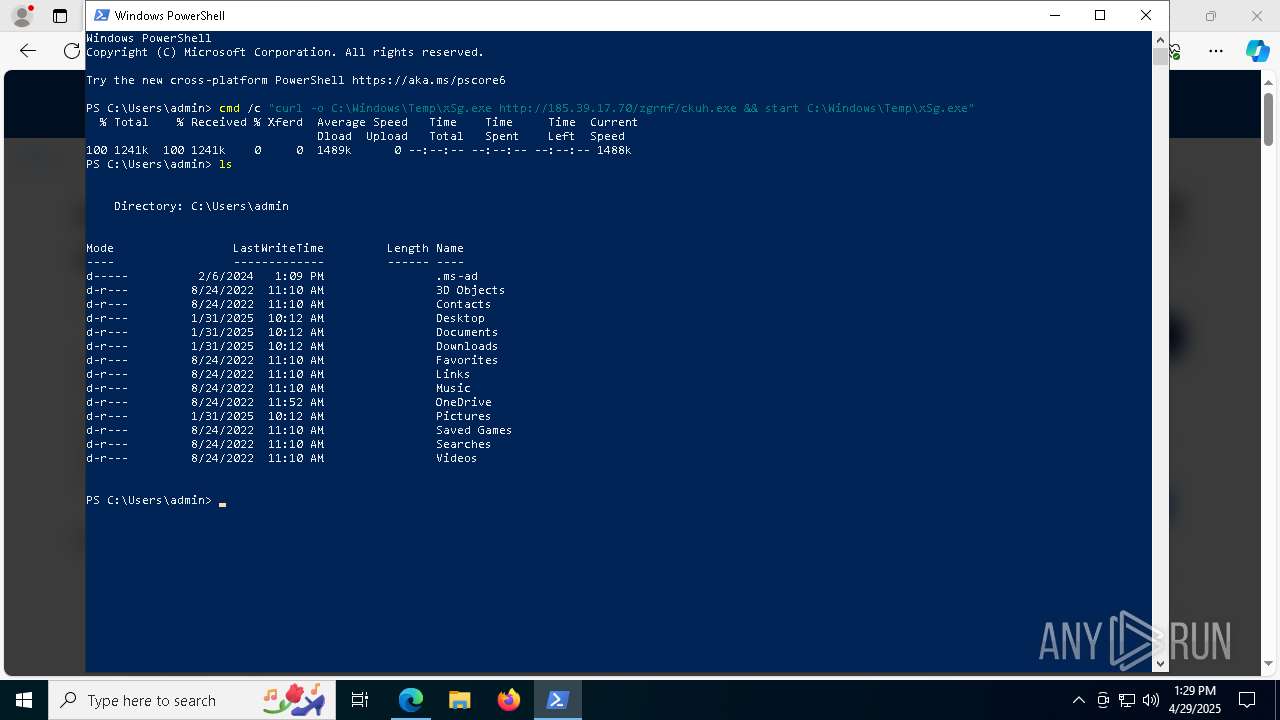
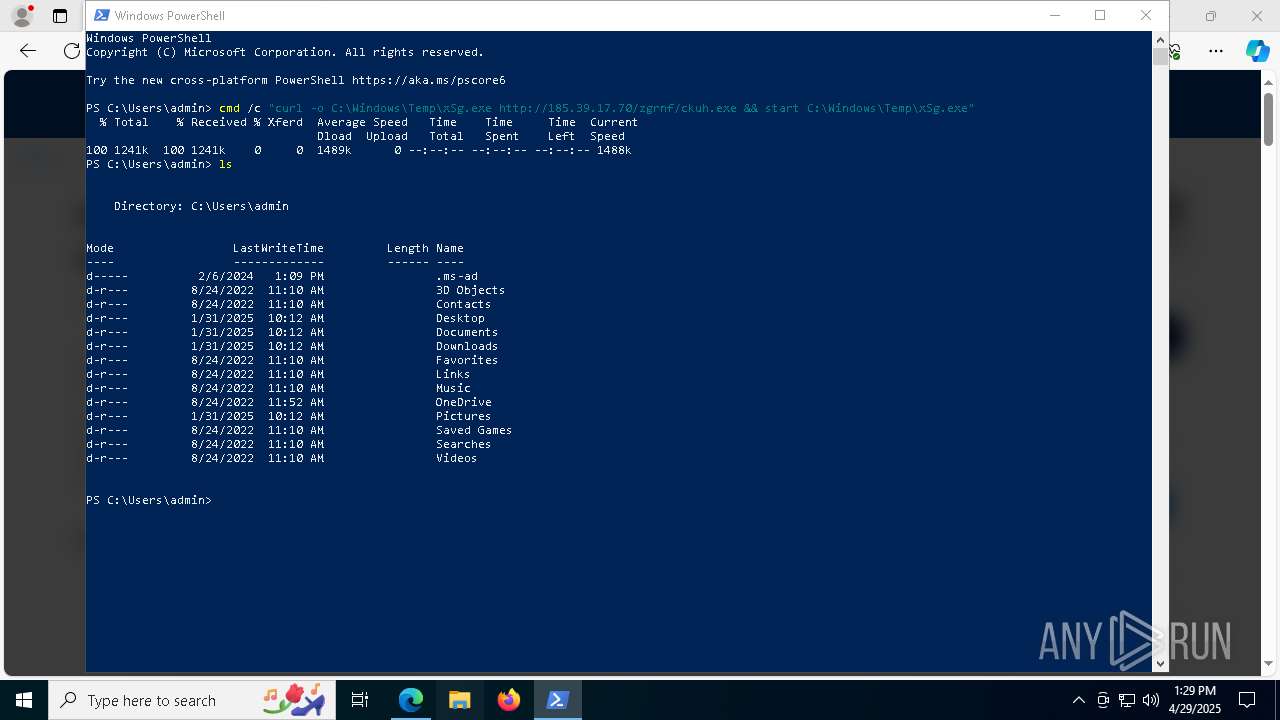
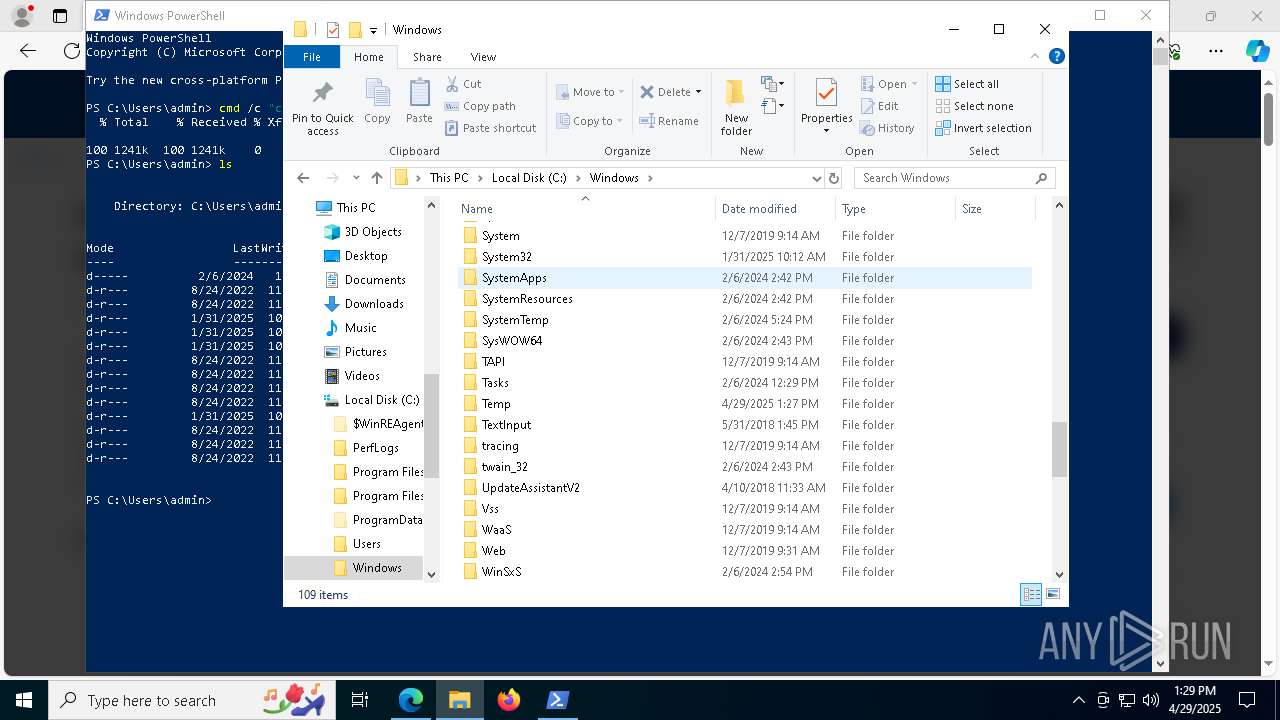
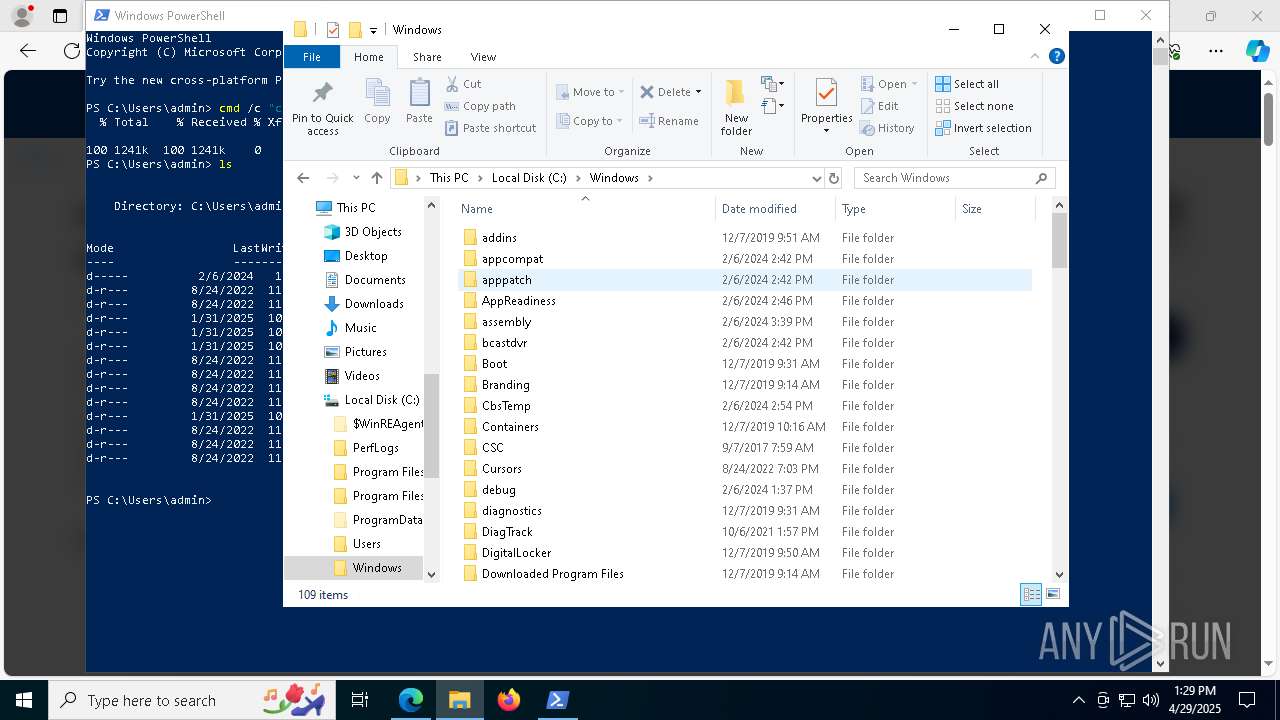
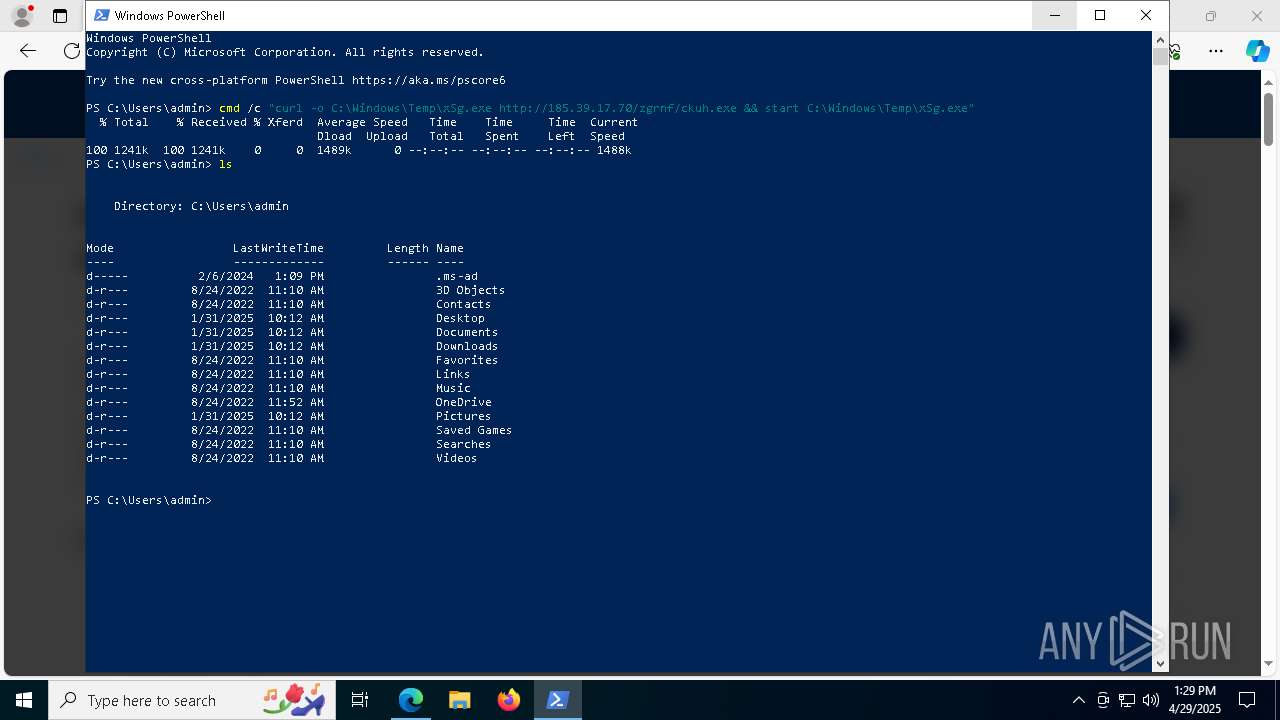
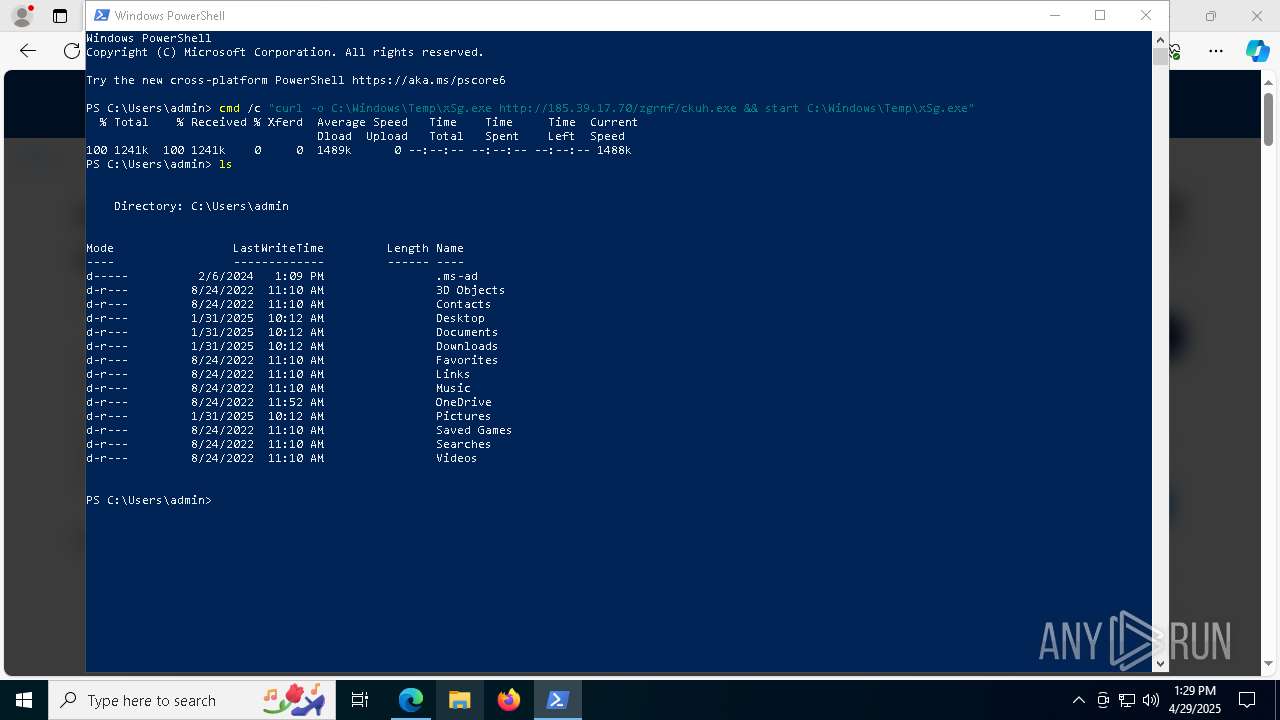
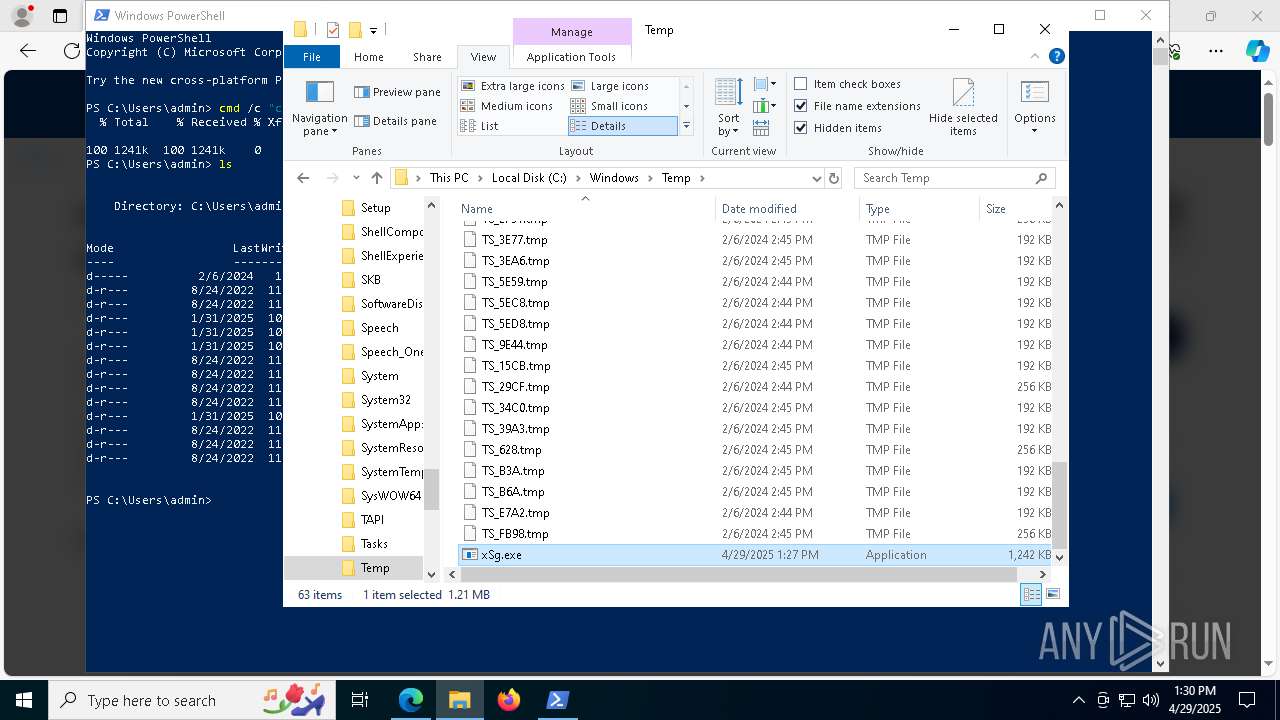
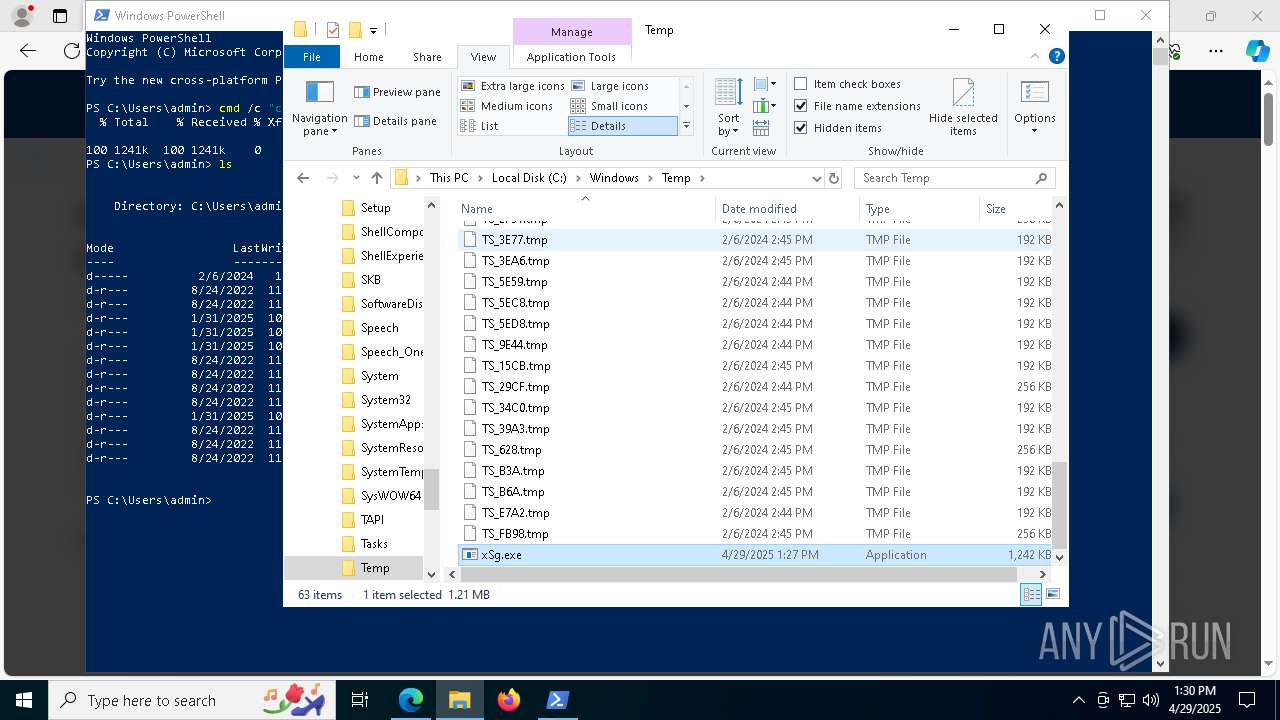
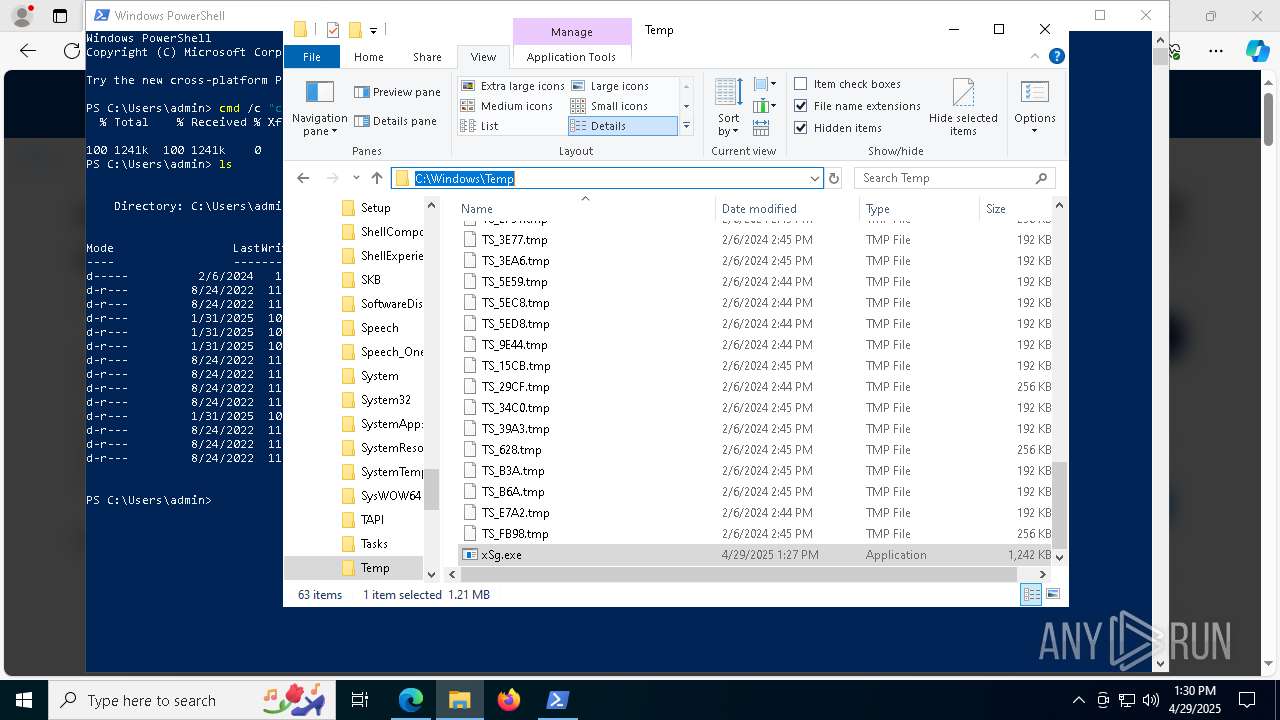
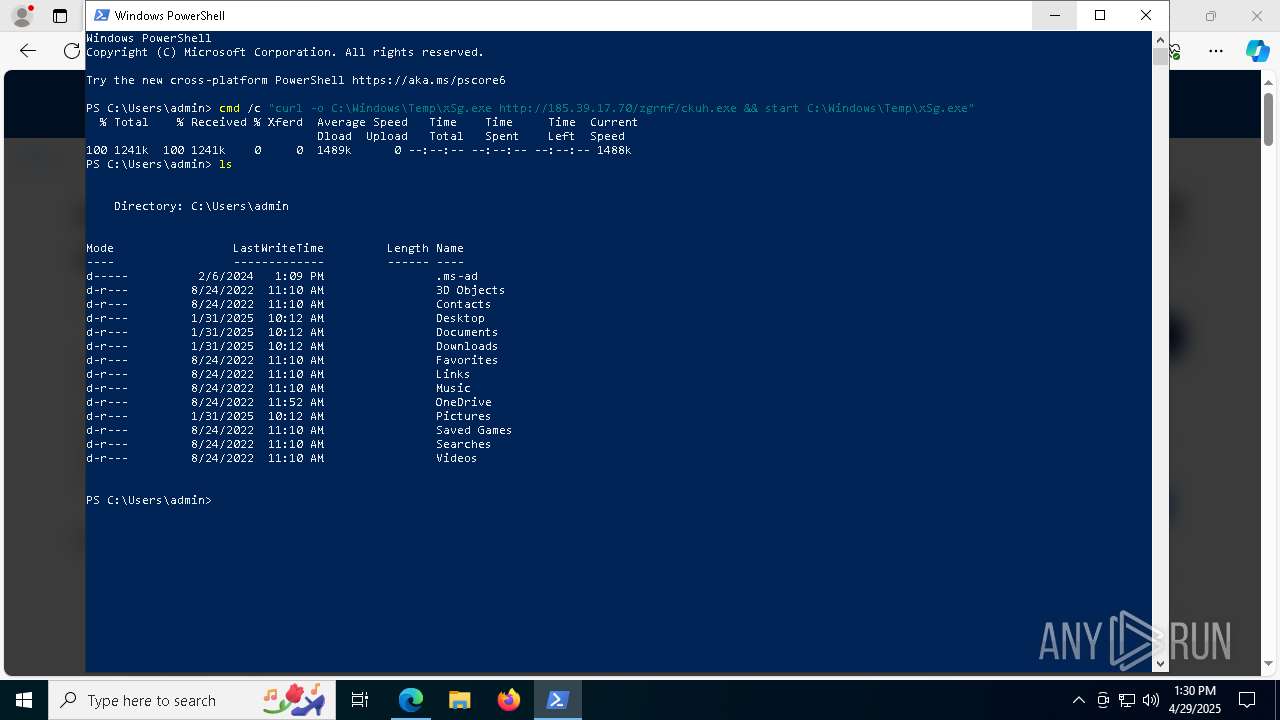
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4724)
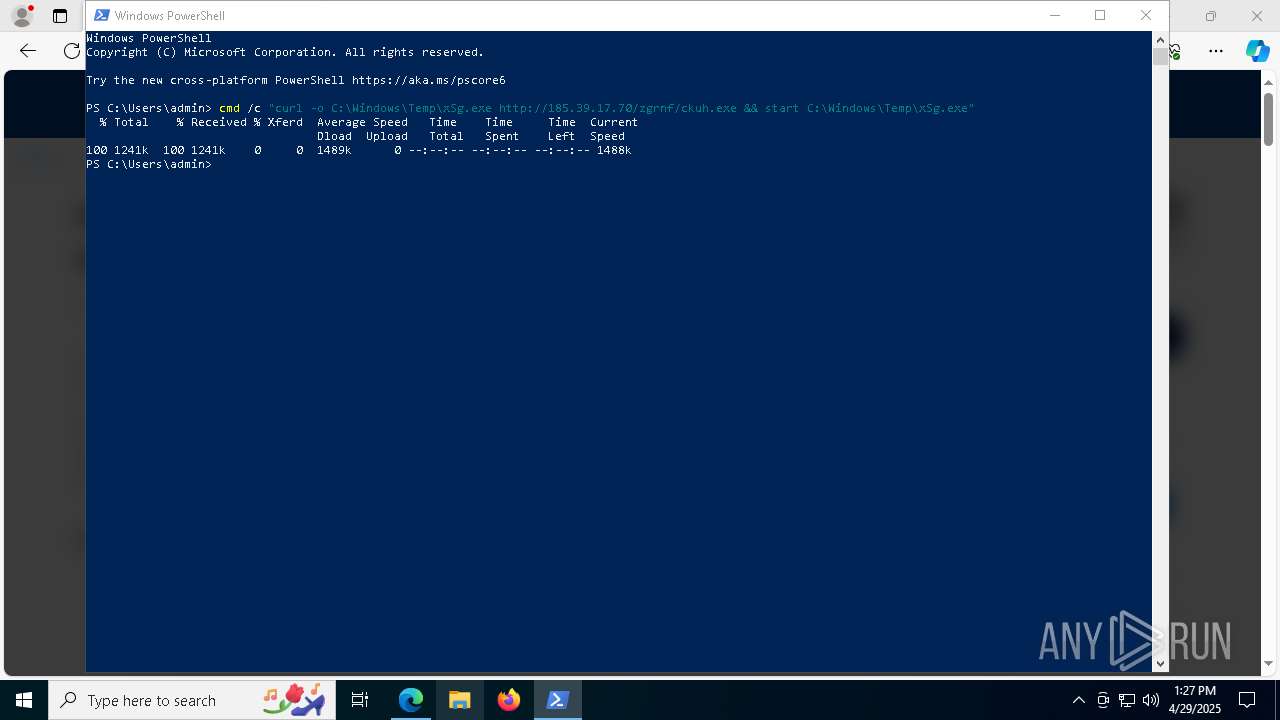
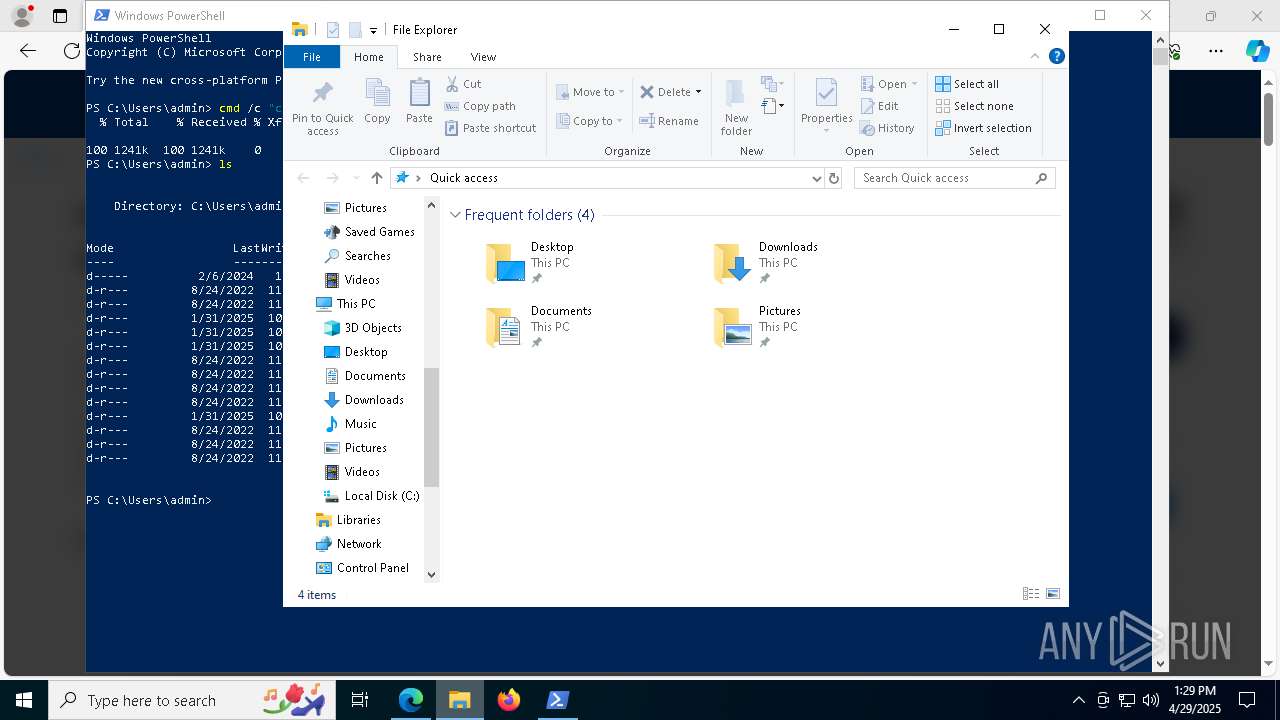
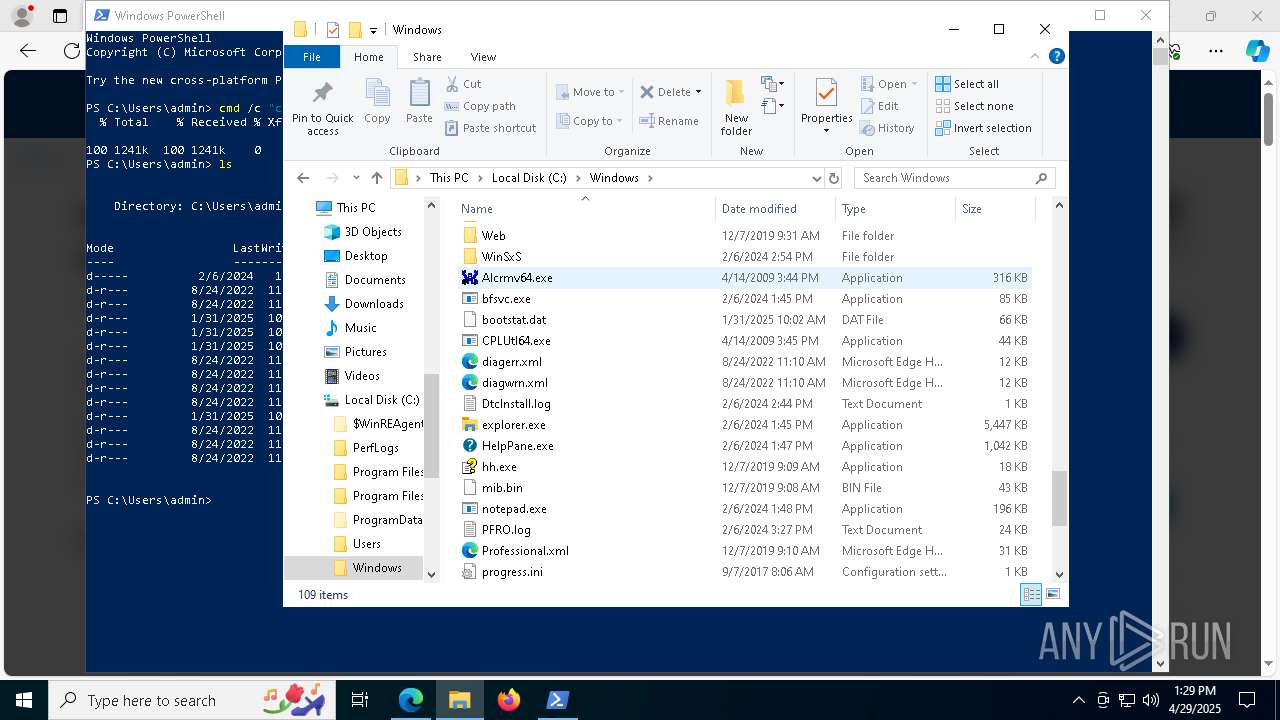
Executable content was dropped or overwritten
- curl.exe (PID: 8804)
- powershell.exe (PID: 4200)
- csc.exe (PID: 6456)
- rbcoa.exe (PID: 8512)
Process requests binary or script from the Internet
- curl.exe (PID: 8804)
- powershell.exe (PID: 4200)
Reads the date of Windows installation
- xSg.exe (PID: 8740)
Reads security settings of Internet Explorer
- xSg.exe (PID: 8740)
Execution of CURL command
- powershell.exe (PID: 4724)
Starts process via Powershell
- powershell.exe (PID: 4200)
Starts POWERSHELL.EXE for commands execution
- xSg.exe (PID: 8740)
Downloads file from URI via Powershell
- powershell.exe (PID: 4200)
Script adds exclusion path to Windows Defender
- xSg.exe (PID: 8740)
Found IP address in command line
- powershell.exe (PID: 4200)
Connects to the server without a host name
- powershell.exe (PID: 4200)
- curl.exe (PID: 8804)
Contacting a server suspected of hosting an CnC
- MSBuild.exe (PID: 1164)
Uses WMIC.EXE to obtain computer system information
- MSBuild.exe (PID: 1164)
Connects to unusual port
- MSBuild.exe (PID: 1164)
Potential Corporate Privacy Violation
- powershell.exe (PID: 4200)
- curl.exe (PID: 8804)
INFO
Checks supported languages
- identity_helper.exe (PID: 8944)
- xSg.exe (PID: 8740)
- curl.exe (PID: 8804)
Application launched itself
- msedge.exe (PID: 7500)
Reads the computer name
- xSg.exe (PID: 8740)
- identity_helper.exe (PID: 8944)
Reads Environment values
- identity_helper.exe (PID: 8944)
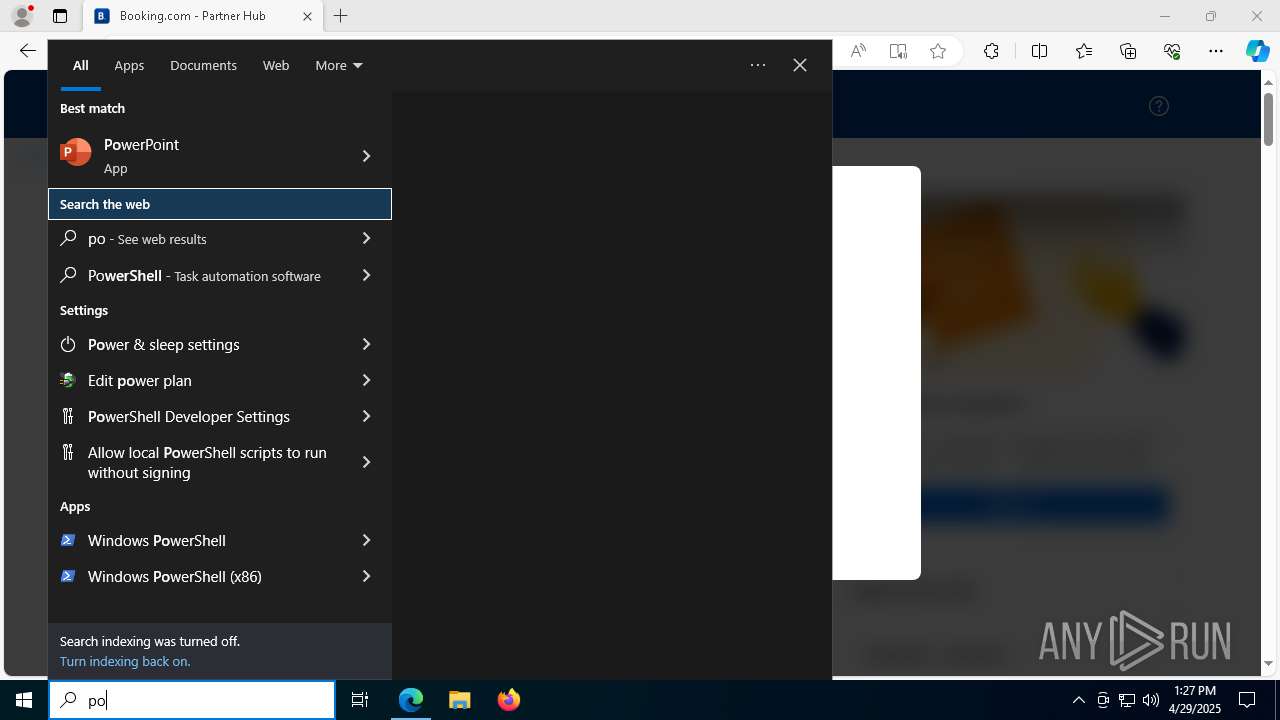
Manual execution by a user
- powershell.exe (PID: 4724)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4724)
Process checks computer location settings
- xSg.exe (PID: 8740)
Disables trace logs
- powershell.exe (PID: 4200)
Checks proxy server information
- powershell.exe (PID: 4200)
Executable content was dropped or overwritten
- msedge.exe (PID: 6808)
The sample compiled with english language support
- msedge.exe (PID: 6808)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8664)
Execution of CURL command
- cmd.exe (PID: 8776)
Reads the software policy settings
- slui.exe (PID: 8372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1164) MSBuild.exe
C2 (1)185.39.17.70
Ports (1)8848
VersionLoaderPanel
Options
AutoRunfalse
Mutexmjcdqgbpklgt
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAJHz+ah5/J2brULSjvSUc0iQ1oaHMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDYyMzE5MDc1MFoXDTM1MDQwMjE5MDc1MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignatureVYU3HkjTdmupf8sfvY5pEMO0/8noyMVeV0yz5jxGMUhWzUuupOWgq2wL5V2r42twsETUKLnqV9SYwqvT6XJv7xhz5pB/85fT0UoCReOgAHpFJ0so+WbBDfbpB/UzVXGoln8h2vH909hWHbCwL3+SAvPMWJx9IwIPkoMEs8mh4eg=
Keys
AESf74c3494998cde01f6f929d1ad131e3139264e2d9b70a7f185170bd2fbcbd120
SaltLoaderPanel
Total processes
224
Monitored processes
82
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6832 --field-trial-handle=2284,i,14163244569987368901,18129189153565344479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=3668 --field-trial-handle=2284,i,14163244569987368901,18129189153565344479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | rbcoa.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(1164) MSBuild.exe C2 (1)185.39.17.70 Ports (1)8848 VersionLoaderPanel Options AutoRunfalse Mutexmjcdqgbpklgt InstallFolder%AppData% Certificates Cert1MIICMDCCAZmgAwIBAgIVAJHz+ah5/J2brULSjvSUc0iQ1oaHMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDYyMzE5MDc1MFoXDTM1MDQwMjE5MDc1MFowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_SignatureVYU3HkjTdmupf8sfvY5pEMO0/8noyMVeV0yz5jxGMUhWzUuupOWgq2wL5V2r42twsETUKLnqV9SYwqvT6XJv7xhz5pB/85fT0UoCReOgAHpFJ0so+WbBDfbpB/UzVXGoln8h2vH909hWHbCwL3+SAvPMWJx9IwIPkoMEs8mh4eg= Keys AESf74c3494998cde01f6f929d1ad131e3139264e2d9b70a7f185170bd2fbcbd120 SaltLoaderPanel | |||||||||||||||
| 1324 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | rbcoa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4752 --field-trial-handle=2284,i,14163244569987368901,18129189153565344479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2148 | C:\WINDOWS\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4208 --field-trial-handle=2284,i,14163244569987368901,18129189153565344479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6808 --field-trial-handle=2284,i,14163244569987368901,18129189153565344479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4348 --field-trial-handle=2284,i,14163244569987368901,18129189153565344479,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
26 681
Read events
26 652
Write events
29
Delete events
0
Modification events
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 23B0590781922F00 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B774630781922F00 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197210 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A214066D-0F0E-4973-9966-0F7EF1BED7E3} | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 67688A0781922F00 | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197210 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {29922A7A-8344-4993-93BA-9364E2F1297A} | |||
| (PID) Process: | (7500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197210 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3329B3B2-37F3-41E7-BA4E-3C8017976119} | |||
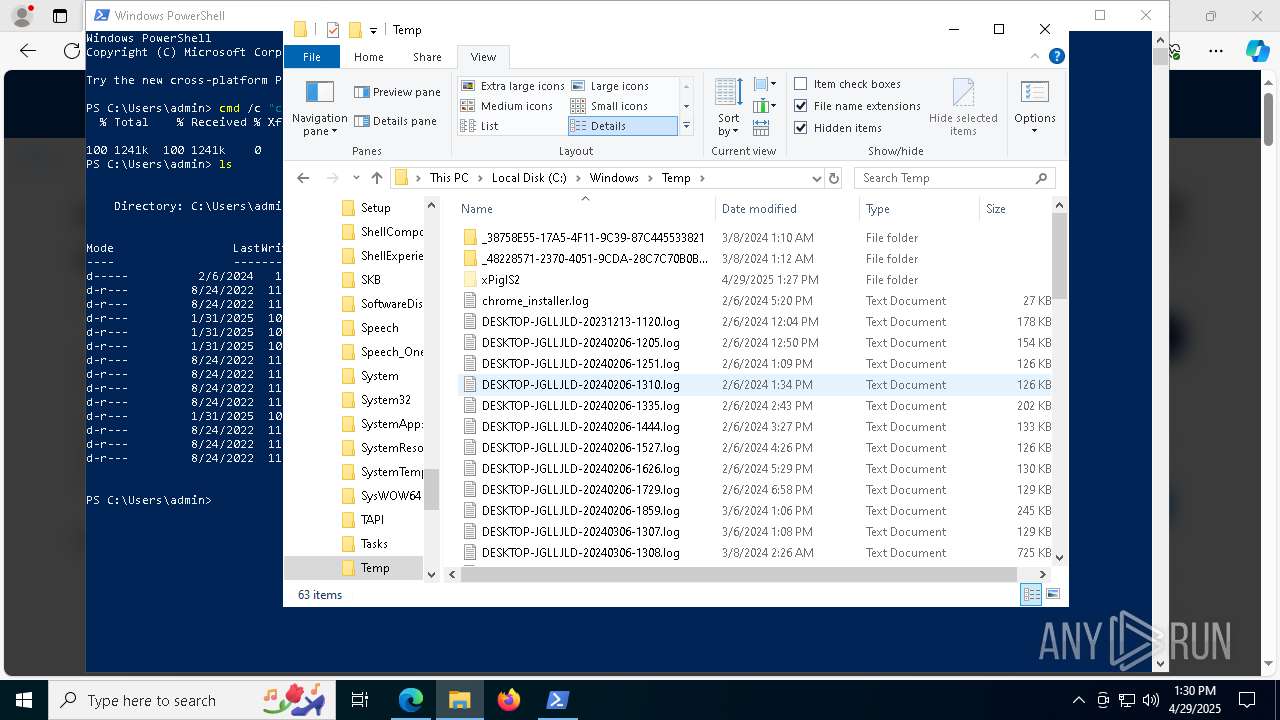
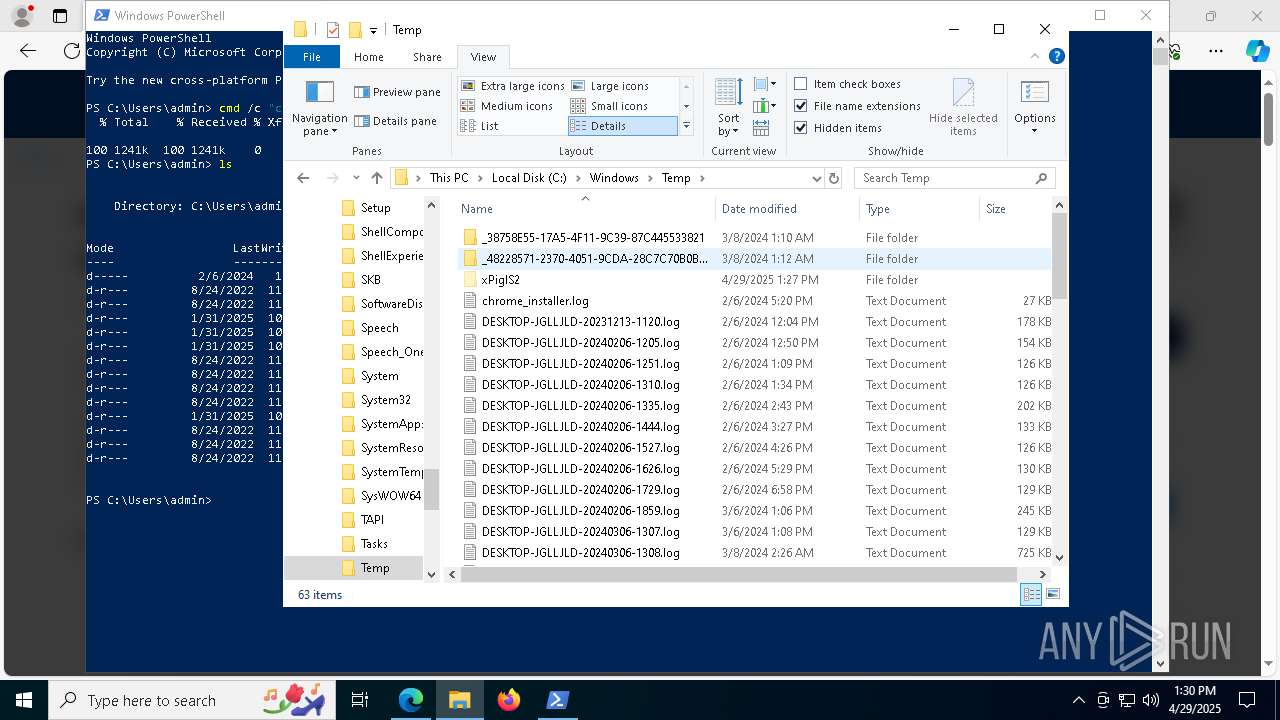
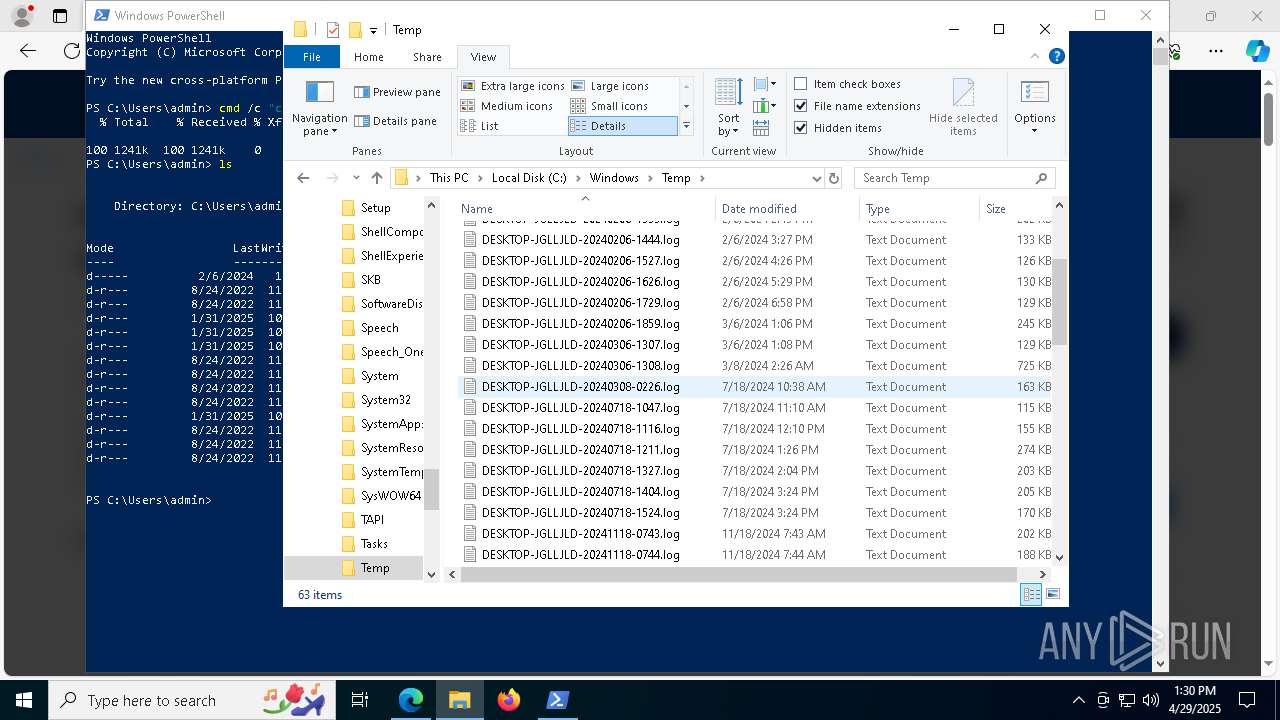
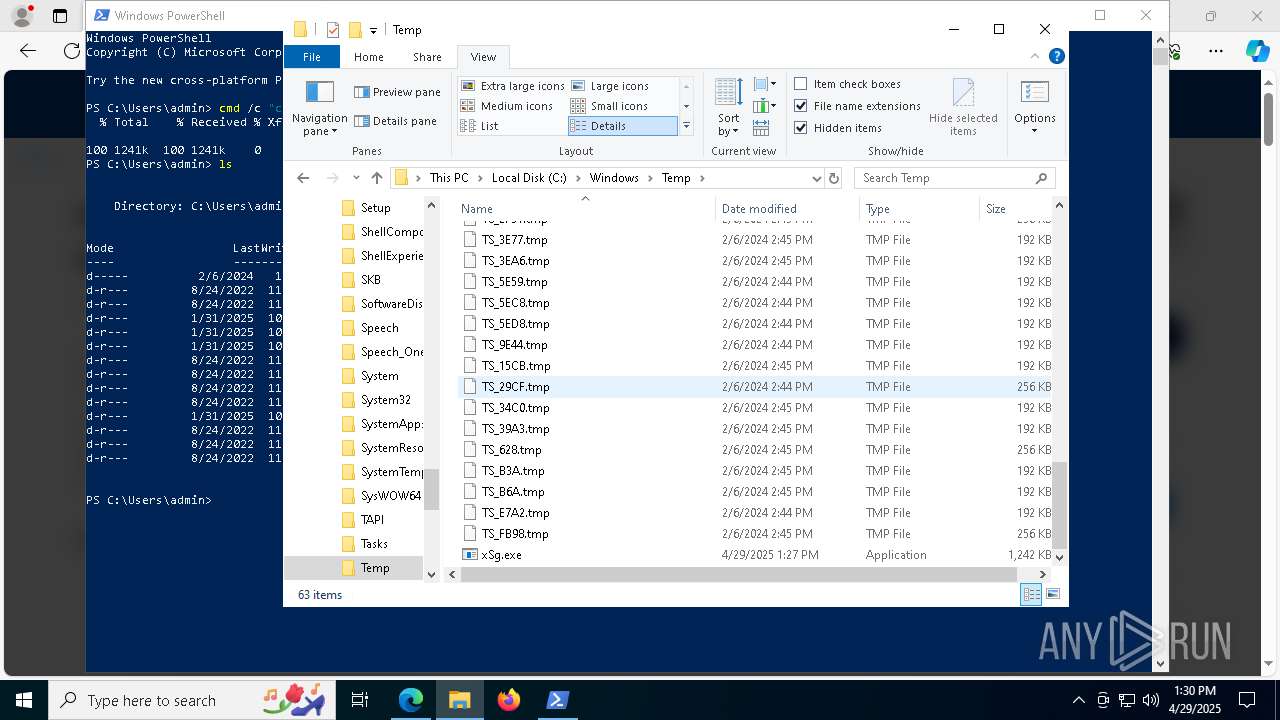
Executable files
17
Suspicious files
583
Text files
110
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ba88.TMP | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
98
DNS requests
108
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.16:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 868 b | whitelisted |
6576 | svchost.exe | HEAD | 200 | 23.48.23.47:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | DE | — | — | whitelisted |
6576 | svchost.exe | GET | 206 | 23.48.23.47:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | DE | binary | 1.09 Kb | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6576 | svchost.exe | GET | 206 | 23.48.23.47:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | DE | binary | 2.79 Kb | whitelisted |
6576 | svchost.exe | GET | 206 | 23.48.23.47:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/cf34b06a-2f53-4bd0-9d11-b58cf2e820a4?P1=1746407434&P2=404&P3=2&P4=cjfHSGDM899kcUHSiDbI70teC1zt4DIx8imbQCBRvnvlkx%2bSztBaNgdGmIHjwmIikGVhO3jFkfEnLBOtd9S%2bLg%3d%3d | DE | binary | 3.73 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.16:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7780 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7500 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7780 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7780 | msedge.exe | 104.21.80.1:443 | booking.secure-partener.com | CLOUDFLARENET | — | unknown |
7780 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
booking.secure-partener.com |
| unknown |
business.bing.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7780 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7780 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Booking Page |
7780 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Booking Page |