| File name: | EnterPoem.exe |
| Full analysis: | https://app.any.run/tasks/2933096b-9f39-478b-91e3-df1165608163 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 02, 2024, 16:26:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | D525FD714F5C8BDBDE9FB2F2D87F1A1A |
| SHA1: | 06892F112A319717312EFB86519E8A67D0671998 |
| SHA256: | 45C5C765C84272B599A28BB94F044F36D44266DDFEF13D0F6EF2A90283FC1410 |
| SSDEEP: | 49152:b/nsIJNd8NYvRySGx96qRFmryEbMJETrMIl5yYSTz58ekiCprfYP/Z6xxJckRyvz:bPsIJNd8mF2kW2TrMM5yYSh/CpEXZ6dO |
MALICIOUS
AutoIt loader has been detected (YARA)
- Trackback.pif (PID: 2588)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
Changes powershell execution policy (Bypass)
- Trackback.pif (PID: 2588)
Bypass execution policy to execute commands
- powershell.exe (PID: 6300)
Stealers network behavior
- svchost.exe (PID: 2172)
SUSPICIOUS
Executing commands from a ".bat" file
- EnterPoem.exe (PID: 6772)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6868)
- EnterPoem.exe (PID: 6772)
Reads security settings of Internet Explorer
- EnterPoem.exe (PID: 6772)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 6868)
The executable file from the user directory is run by the CMD process
- Trackback.pif (PID: 2588)
Get information on the list of running processes
- cmd.exe (PID: 6868)
Application launched itself
- cmd.exe (PID: 6868)
Executable content was dropped or overwritten
- cmd.exe (PID: 6868)
- AutoIt3.exe (PID: 6316)
- Trackback.pif (PID: 2588)
Starts application with an unusual extension
- cmd.exe (PID: 6868)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6868)
The process executes Powershell scripts
- Trackback.pif (PID: 2588)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2172)
Node.exe was dropped
- Trackback.pif (PID: 2588)
Starts POWERSHELL.EXE for commands execution
- Trackback.pif (PID: 2588)
INFO
Create files in a temporary directory
- EnterPoem.exe (PID: 6772)
Reads the computer name
- EnterPoem.exe (PID: 6772)
- Trackback.pif (PID: 2588)
Process checks computer location settings
- EnterPoem.exe (PID: 6772)
The process uses the downloaded file
- EnterPoem.exe (PID: 6772)
Creates a new folder
- cmd.exe (PID: 5168)
Checks supported languages
- Trackback.pif (PID: 2588)
- EnterPoem.exe (PID: 6772)
Reads mouse settings
- Trackback.pif (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:19:54+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28160 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3883 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.37.6.44883 |
| ProductVersionNumber: | 9.37.6.44883 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| LegalTrademarks: | SpectraFox is a trademark of ColorSync Dynamics |
| ProductName: | SpectraFox |
Total processes
192
Monitored processes
61
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
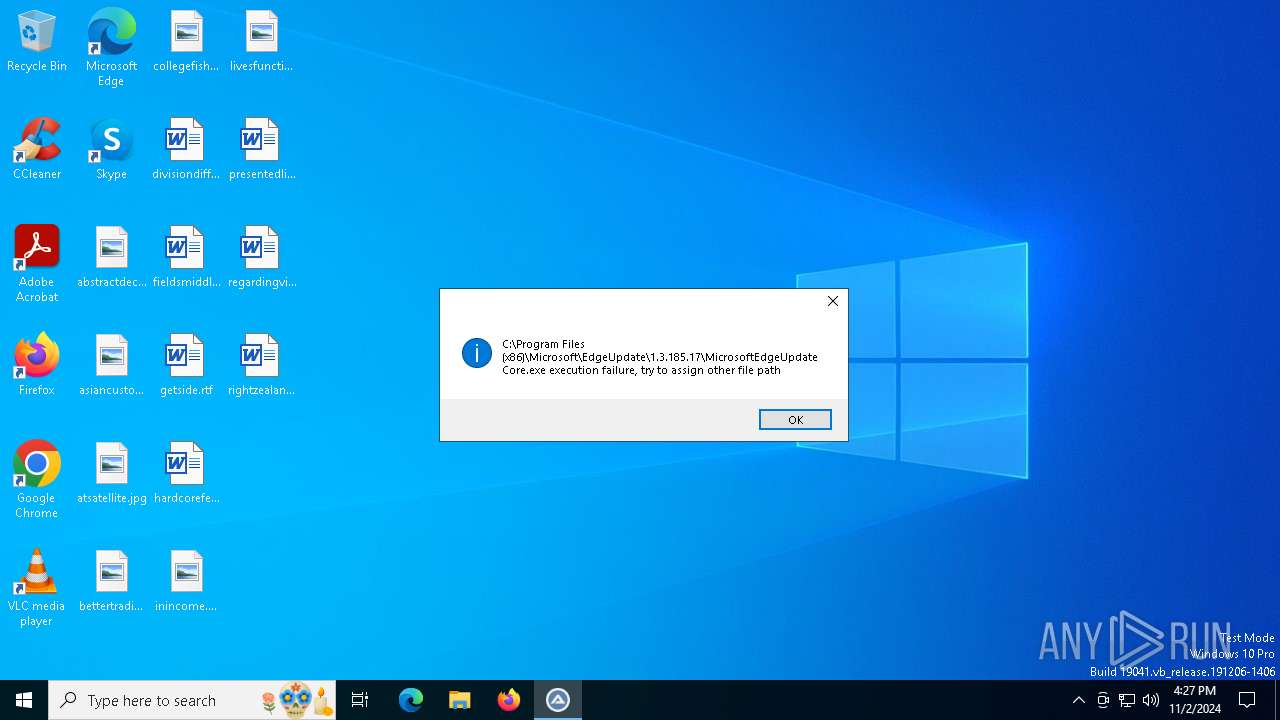
| 1008 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1048 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1084 | findstr /V "initiativemanufacturingborncached" Clip | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1112 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1252 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1568 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1744 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1748 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
Total events
5 765
Read events
5 764
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6316) AutoIt3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | ebhhaeg |
Value: "C:\hbcfbdf\AutoIt3.exe" C:\hbcfbdf\ebhhaeg.a3x | |||
Executable files
4
Suspicious files
15
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6772 | EnterPoem.exe | C:\Users\admin\AppData\Local\Temp\Manufacturers | binary | |
MD5:32B02CEB9CF2390B0BAA1287869B183C | SHA256:6E0A523A35FC0889B2CA967DF9E49F9BC24A757FD8DA15C10B376D5548C1F1E1 | |||
| 6772 | EnterPoem.exe | C:\Users\admin\AppData\Local\Temp\Clip | binary | |
MD5:A50EA9A47715B1EEBE76D0797A90A443 | SHA256:4E0FF3771ABF5525D183CA61934C27E315D18E060A2B14F15857A7820FC50915 | |||
| 6772 | EnterPoem.exe | C:\Users\admin\AppData\Local\Temp\Feeling | binary | |
MD5:BAB8BC88DC75E1876929B9C6E700A683 | SHA256:C5305A5807CB55ED1799ABC0A7215F6D5DA4F3E888FAE5F9E30FCBE0B8F26A7A | |||
| 6772 | EnterPoem.exe | C:\Users\admin\AppData\Local\Temp\Wound | binary | |
MD5:9EDAA1FD97302AF249ED4B1BEE766B89 | SHA256:DE372460E39B3598371EAA5D87A53821FA9CD09C1579CB196EB0CE8D84DD2F51 | |||
| 2588 | Trackback.pif | C:\Users\admin\AppData\Local\Temp\PJRQ35\Afflicted.a3x | — | |
MD5:— | SHA256:— | |||
| 6772 | EnterPoem.exe | C:\Users\admin\AppData\Local\Temp\Rely | text | |
MD5:F7189EA942DD1366B89B7B865F4D6227 | SHA256:5A1CF60FE4FB87911DD71467AA59740D11C9A5F13DB47801CD1A4AB7ECF89164 | |||
| 6316 | AutoIt3.exe | C:\hbcfbdf\ebhhaeg.a3x | — | |
MD5:— | SHA256:— | |||
| 2648 | 3JJU1WU5YIBZZQ5WBTO91E6.exe | C:\Users\admin\AppData\Local\Temp\826cc3f7 | image | |
MD5:E11362AB856AD40E432C9AA356EA7FB0 | SHA256:2EE91362BBE22AADA4D879FA18DFC5FDA57700BD8255B084789339C6950148A2 | |||
| 2588 | Trackback.pif | C:\Users\admin\AppData\Local\Temp\K9Q7WNRY7CA2HU3K60CO.ps1 | html | |
MD5:EE70E52441EC629D1708DFD3BBBFE7D7 | SHA256:4FF9EB9A44F8D55794854AC15DC70A4DE297478012582A21C7D4864202470903 | |||
| 6772 | EnterPoem.exe | C:\Users\admin\AppData\Local\Temp\Trim | binary | |
MD5:E810E55AF75FF79DFD1D8597E8101A43 | SHA256:0969399090A4F8710D84D4620DB829592C3A6E08B40C9702F7CDC45376018455 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
49
DNS requests
28
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6996 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6996 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2588 | Trackback.pif | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
4004 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7132 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2588 | Trackback.pif | GET | 200 | 172.217.18.3:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3524 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 92.123.104.65:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4004 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4004 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
780 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
eYOIVVhHJz.eYOIVVhHJz |
| unknown |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (creative-habitat .shop) |
2172 | svchost.exe | Misc activity | ET INFO Pastebin Service Domain in DNS Lookup (rentry .co) |
2588 | Trackback.pif | Misc activity | ET INFO Observed Pastebin Service Domain (rentry .co in TLS SNI) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (creative-habitat .shop) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (creative-habitat .shop) |