| File name: | d9092704073f79c371d390d17a4e2f6a |
| Full analysis: | https://app.any.run/tasks/b88eeb79-2e43-45dd-a887-db1df23a6462 |
| Verdict: | Malicious activity |
| Threats: | Phobos is a ransomware that locks or encrypts files to demand a ransom. It uses AES encryption with different extensions, which leaves no chance to recover the infected files. |
| Analysis date: | March 31, 2020, 08:30:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D9092704073F79C371D390D17A4E2F6A |
| SHA1: | 671EB7FAC6A4084673B8AB6BDD48897010AFE3CF |
| SHA256: | 44ED625A3A05EF138E123DE5852232372B24A50C67E8F2F17F8AF4467F94EE10 |
| SSDEEP: | 768:IgZRUSqFU+qJck+fO+lJ8f9ICGjI4t1hg0v861NR/uWiuKBUnLz0JF+L7n58APYt:DRvoU+XfE9ICf4t1OwruWiyz0b+CJAO |
MALICIOUS
Runs app for hidden code execution
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
Turns off the firewall via NETSH.EXE
- cmd.exe (PID: 2844)
Writes to a start menu file
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
Changes the autorun value in the registry
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 3692)
PHOBOS was detected
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 3692)
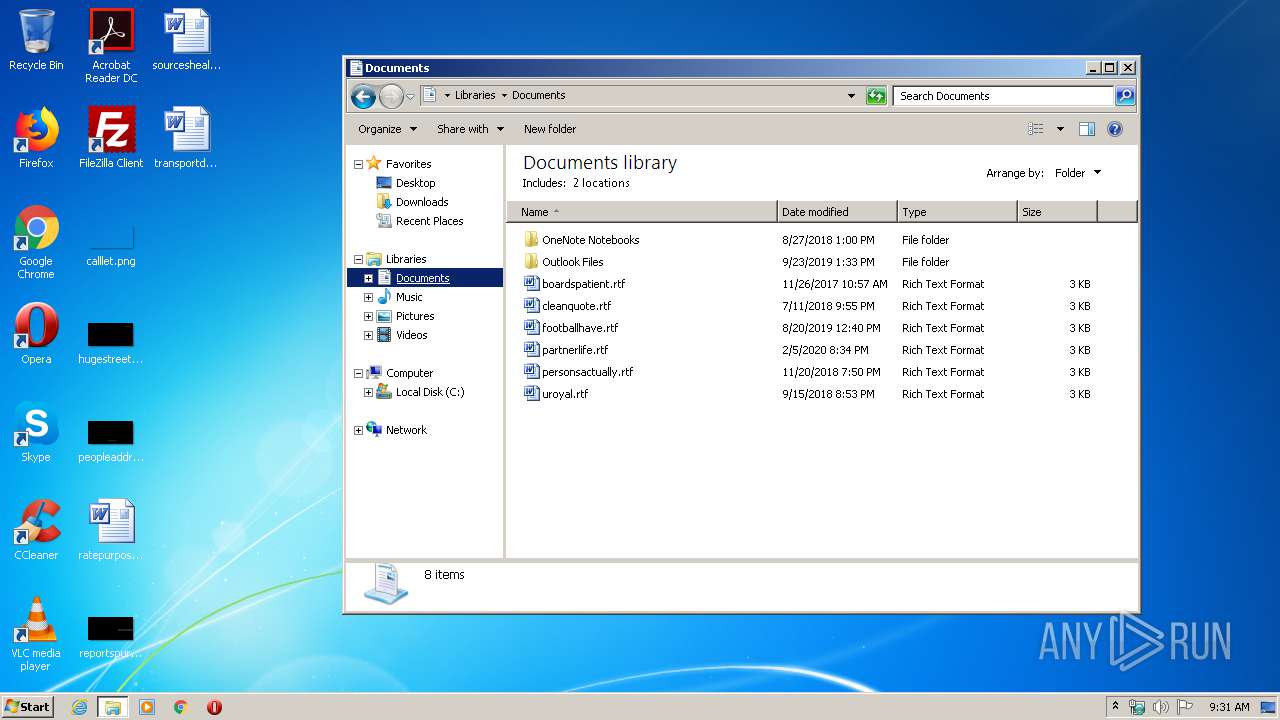
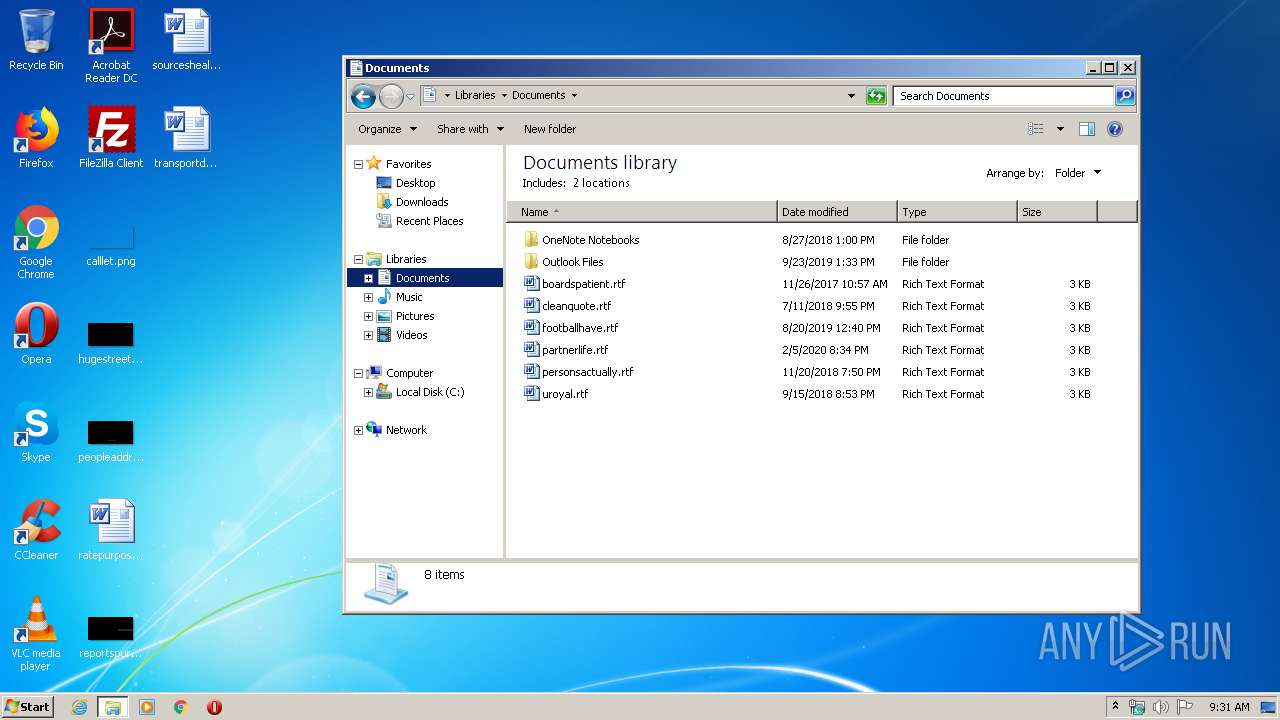
Actions looks like stealing of personal data
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
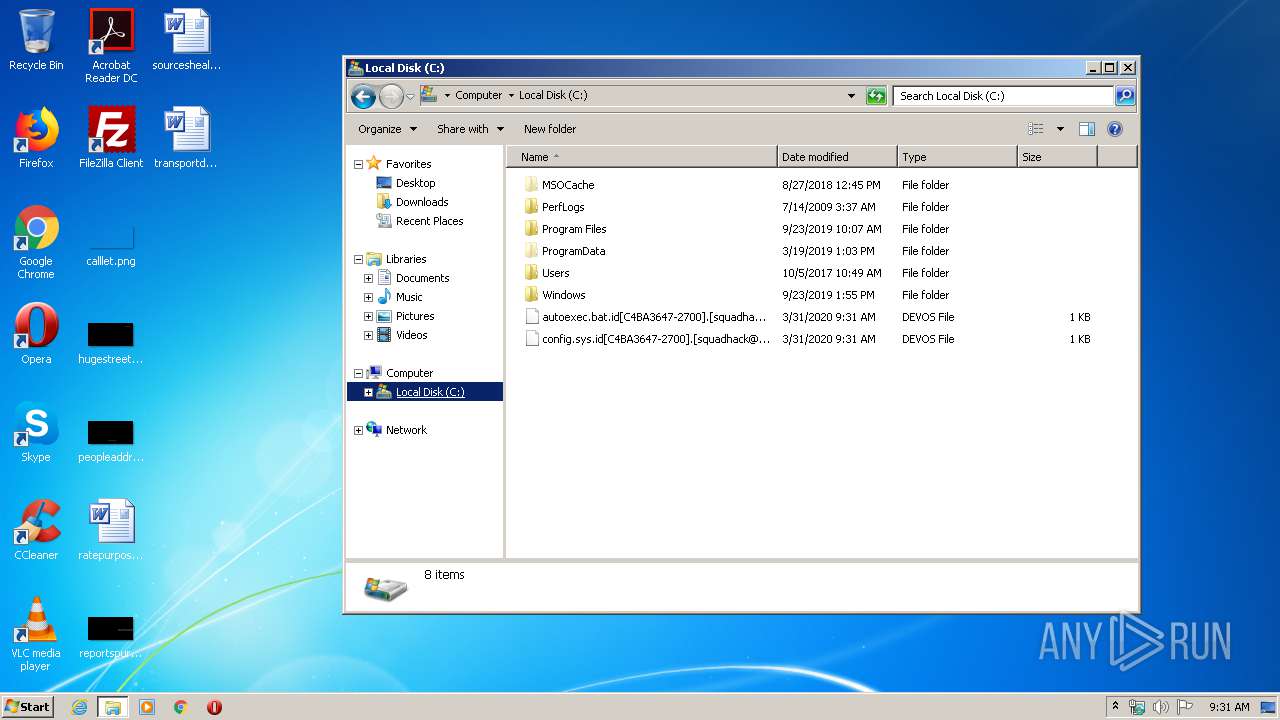
Renames files like Ransomware
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
SUSPICIOUS
Application launched itself
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 676)
Starts CMD.EXE for commands execution
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
Creates files in the user directory
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2844)
Executable content was dropped or overwritten
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 3692)
Reads the cookies of Mozilla Firefox
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
Writes to a desktop.ini file (may be used to cloak folders)
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
Creates files in the program directory
- d9092704073f79c371d390d17a4e2f6a.exe (PID: 2532)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:19 10:00:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 31744 |
| InitializedDataSize: | 15360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2518 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-2019 08:00:06 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Jun-2019 08:00:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007BB8 | 0x00007C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6211 |
.rdata | 0x00009000 | 0x00000C4A | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22085 |
.data | 0x0000A000 | 0x00002719 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.3965 |
.reloc | 0x0000D000 | 0x00000558 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.28469 |
.cdata | 0x0000E000 | 0x00002F2C | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.86908 |
Imports
ADVAPI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
SHELL32.dll |
USER32.dll |
WS2_32.dll |
ole32.dll |
Total processes
44
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | C:\Users\admin\AppData\Local\Temp\d9092704073f79c371d390d17a4e2f6a.exe | C:\Users\admin\AppData\Local\Temp\d9092704073f79c371d390d17a4e2f6a.exe | — | d9092704073f79c371d390d17a4e2f6a.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2128 | netsh firewall set opmode mode=disable | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Users\admin\AppData\Local\Temp\d9092704073f79c371d390d17a4e2f6a.exe" | C:\Users\admin\AppData\Local\Temp\d9092704073f79c371d390d17a4e2f6a.exe | d9092704073f79c371d390d17a4e2f6a.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2844 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | d9092704073f79c371d390d17a4e2f6a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\AppData\Local\Temp\d9092704073f79c371d390d17a4e2f6a.exe" | C:\Users\admin\AppData\Local\Temp\d9092704073f79c371d390d17a4e2f6a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3996 | netsh advfirewall set currentprofile state off | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
455
Read events
347
Write events
108
Delete events
0
Modification events
| (PID) Process: | (676) d9092704073f79c371d390d17a4e2f6a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (676) d9092704073f79c371d390d17a4e2f6a.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3996) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
Executable files
4
Suspicious files
739
Text files
5
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab.id[C4BA3647-2700].[squadhack@email.tg].Devos | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
| 2532 | d9092704073f79c371d390d17a4e2f6a.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab.id[C4BA3647-2700].[squadhack@email.tg].Devos | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report