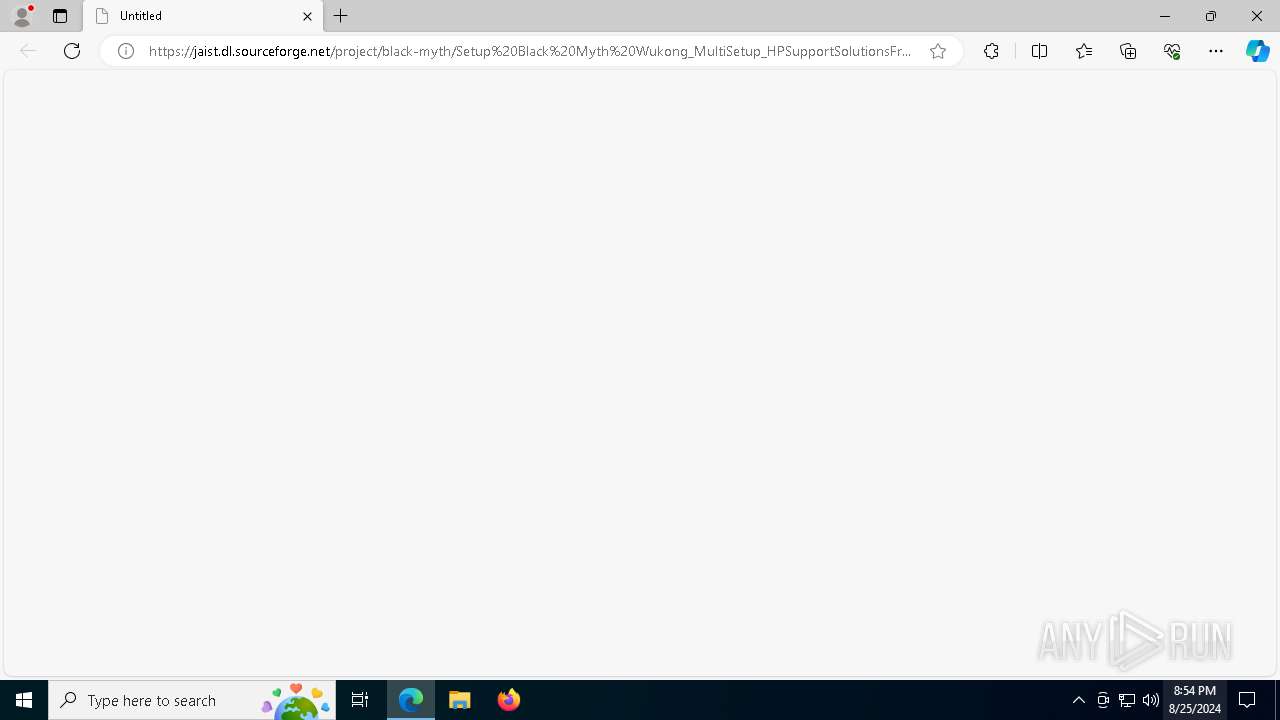
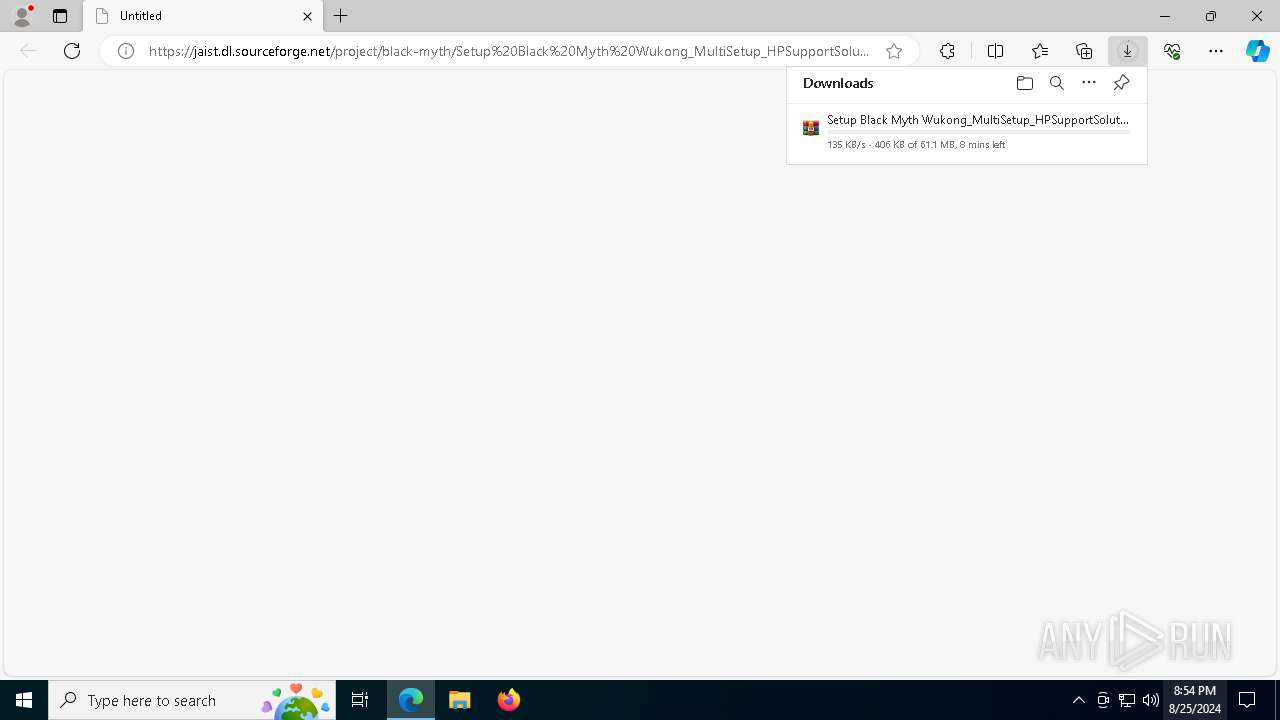
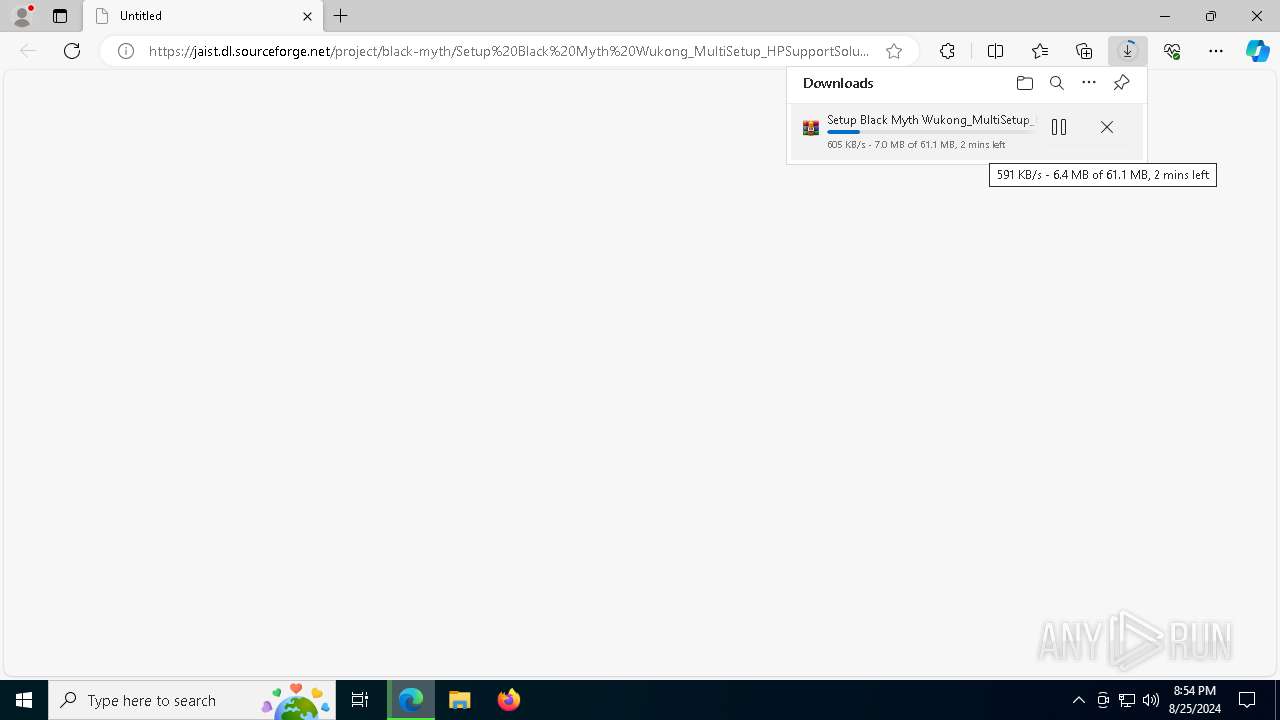
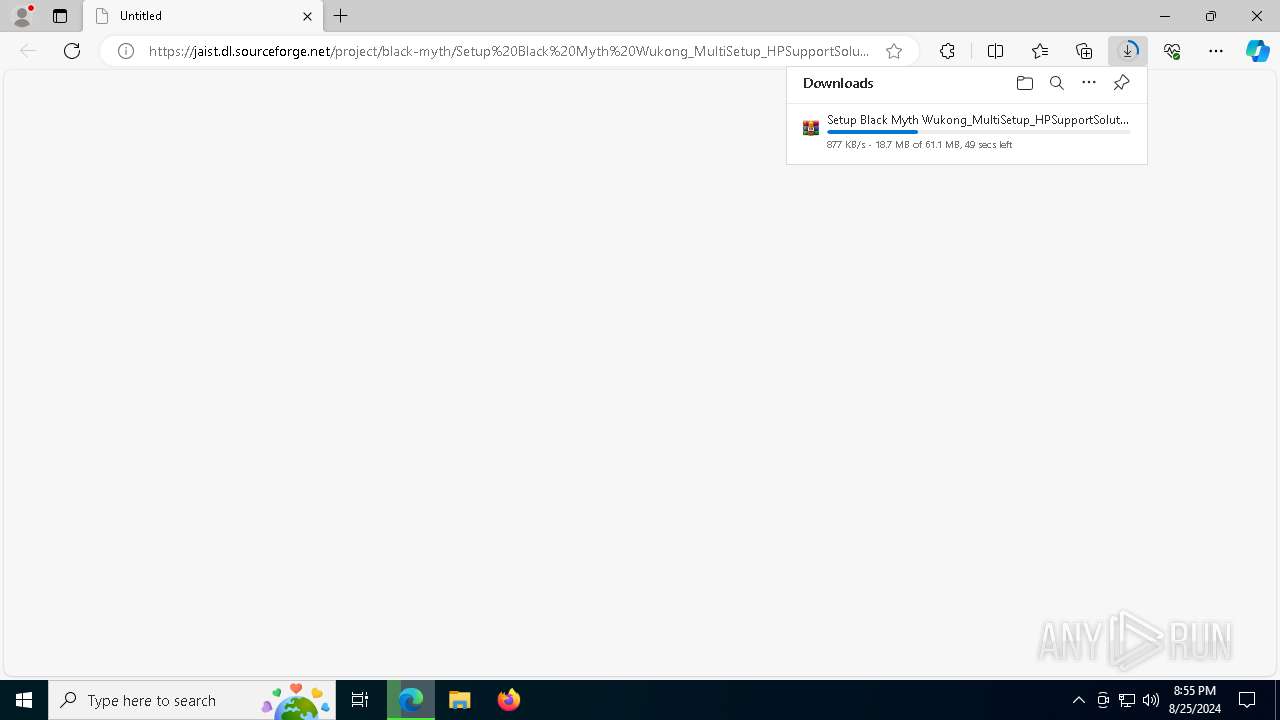
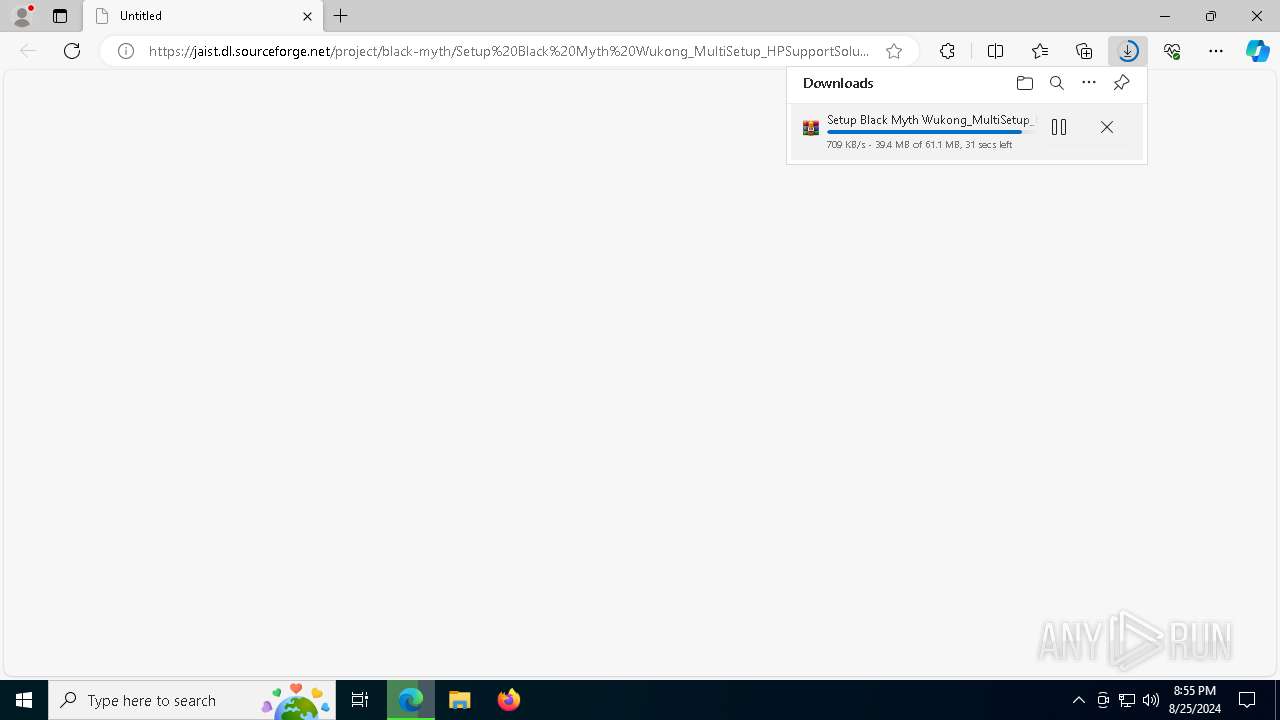
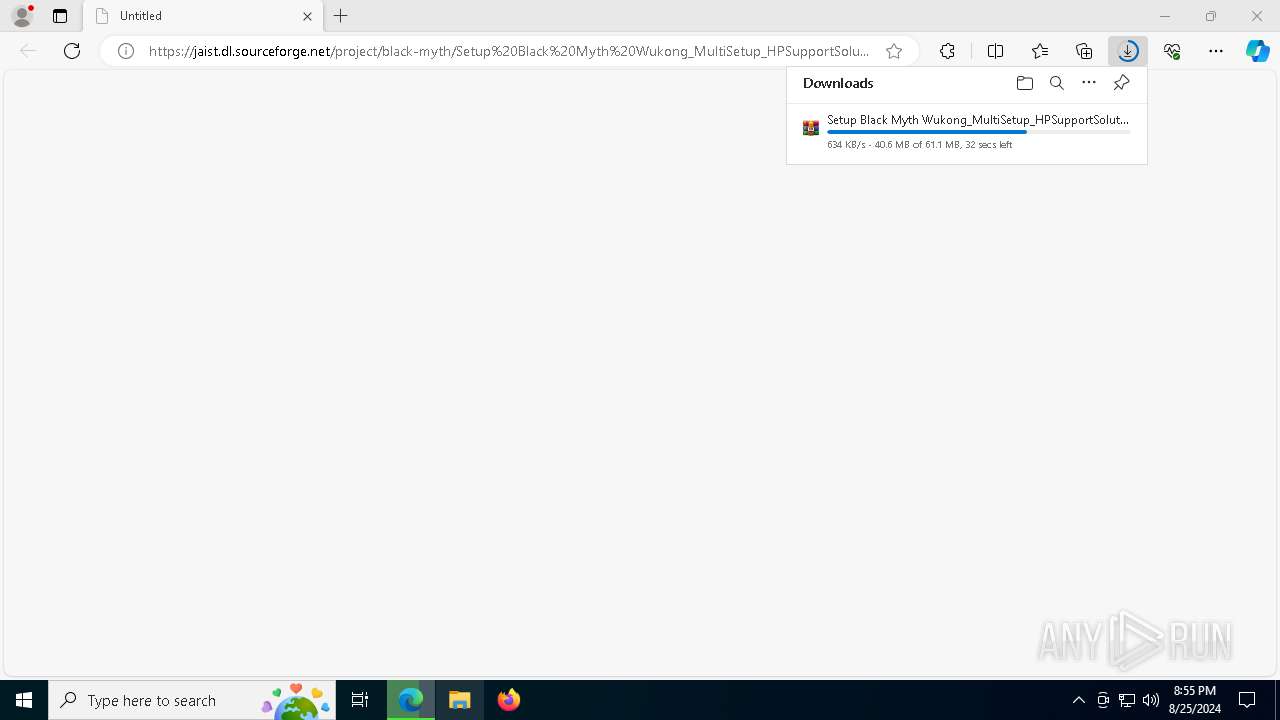
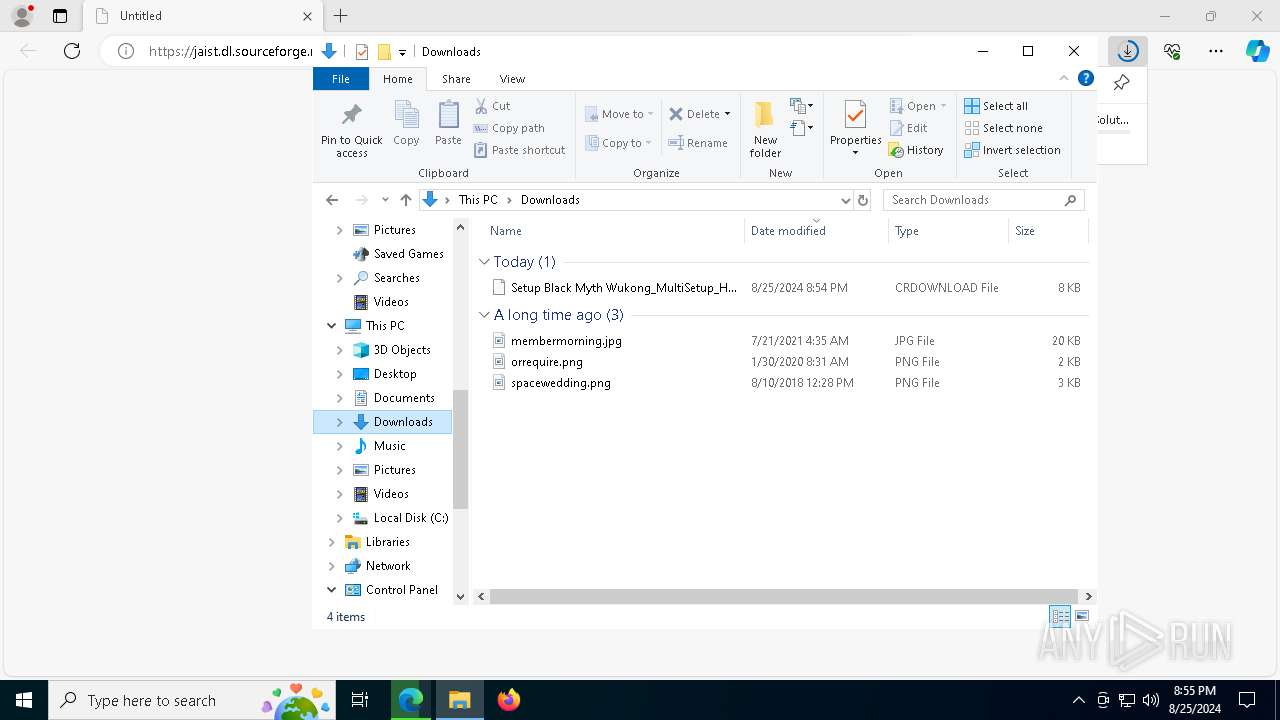
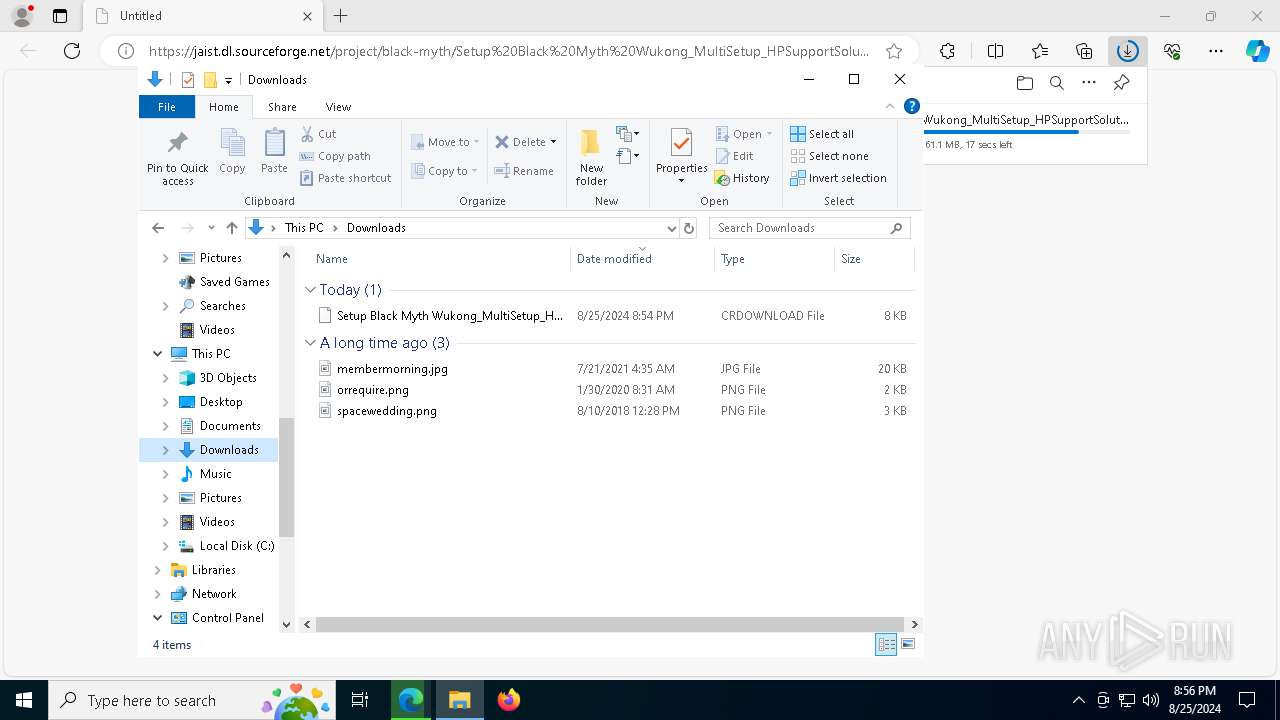
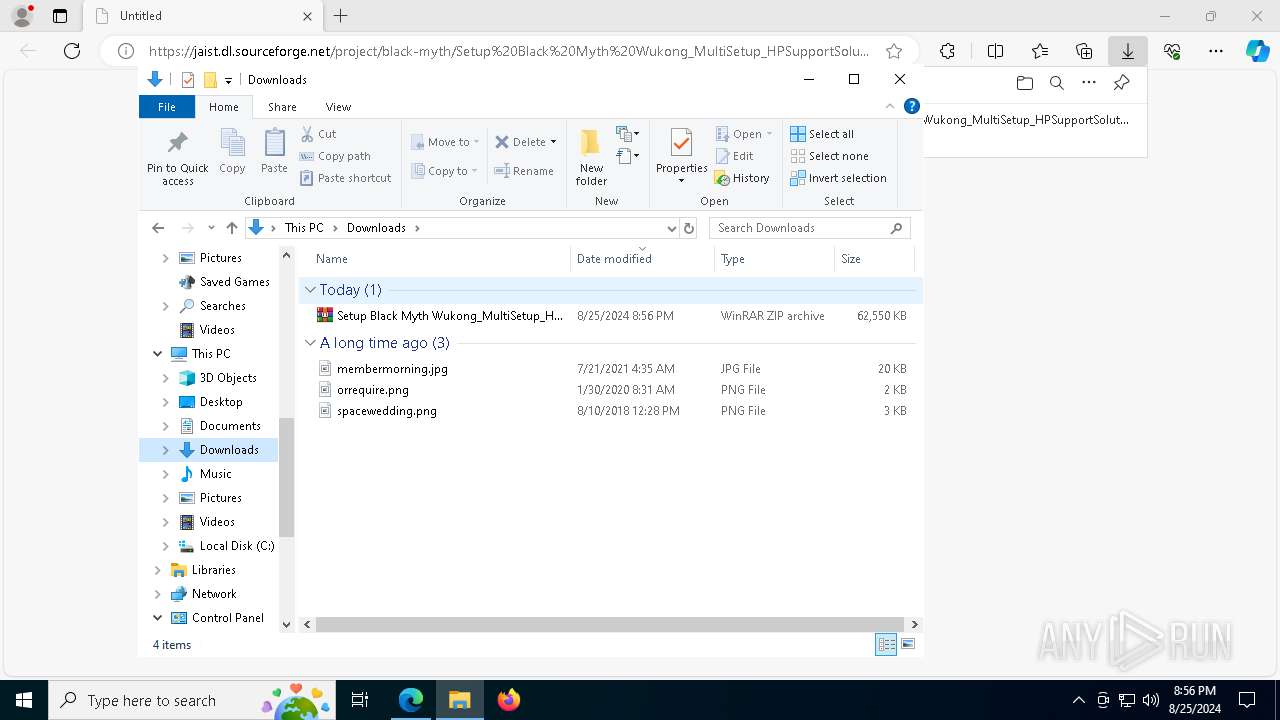
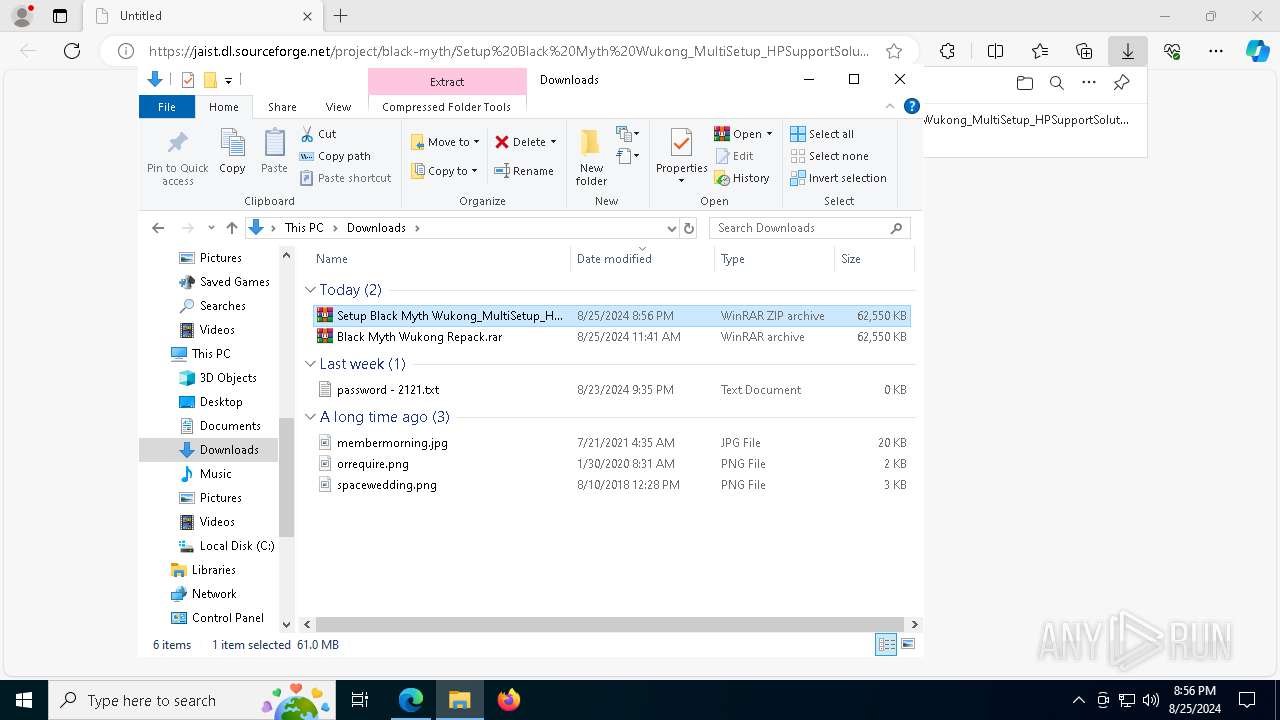
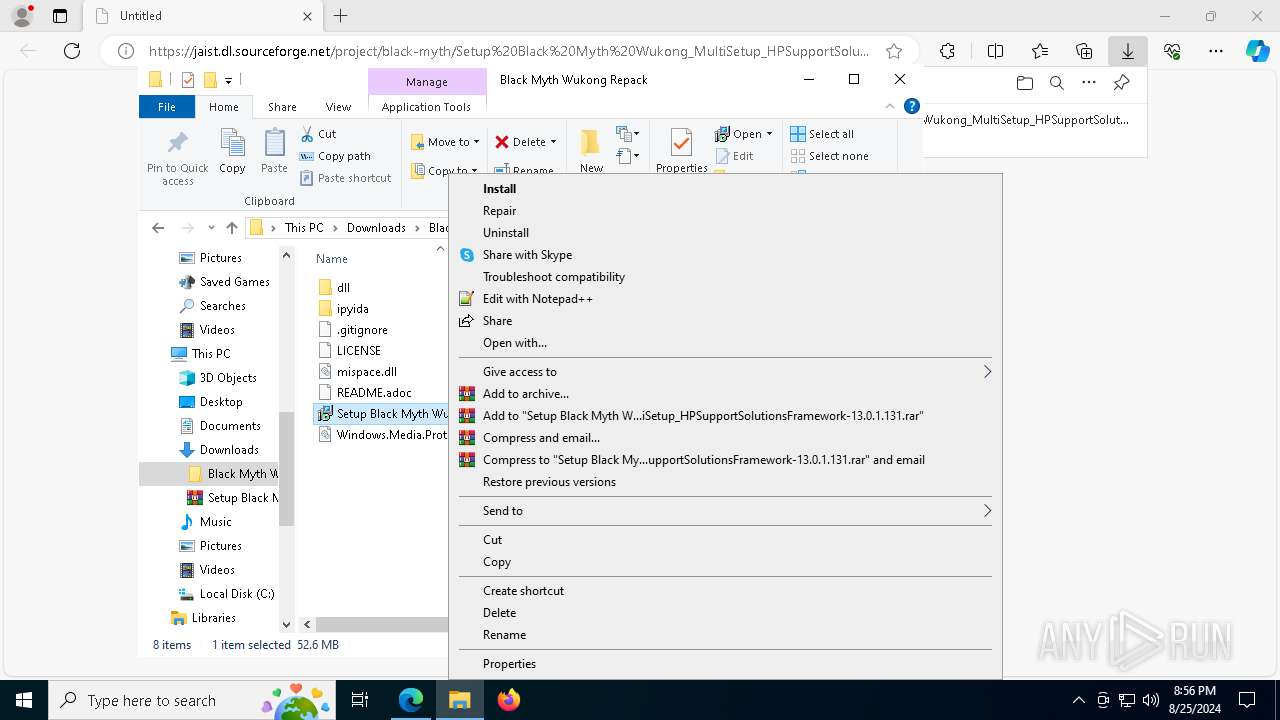
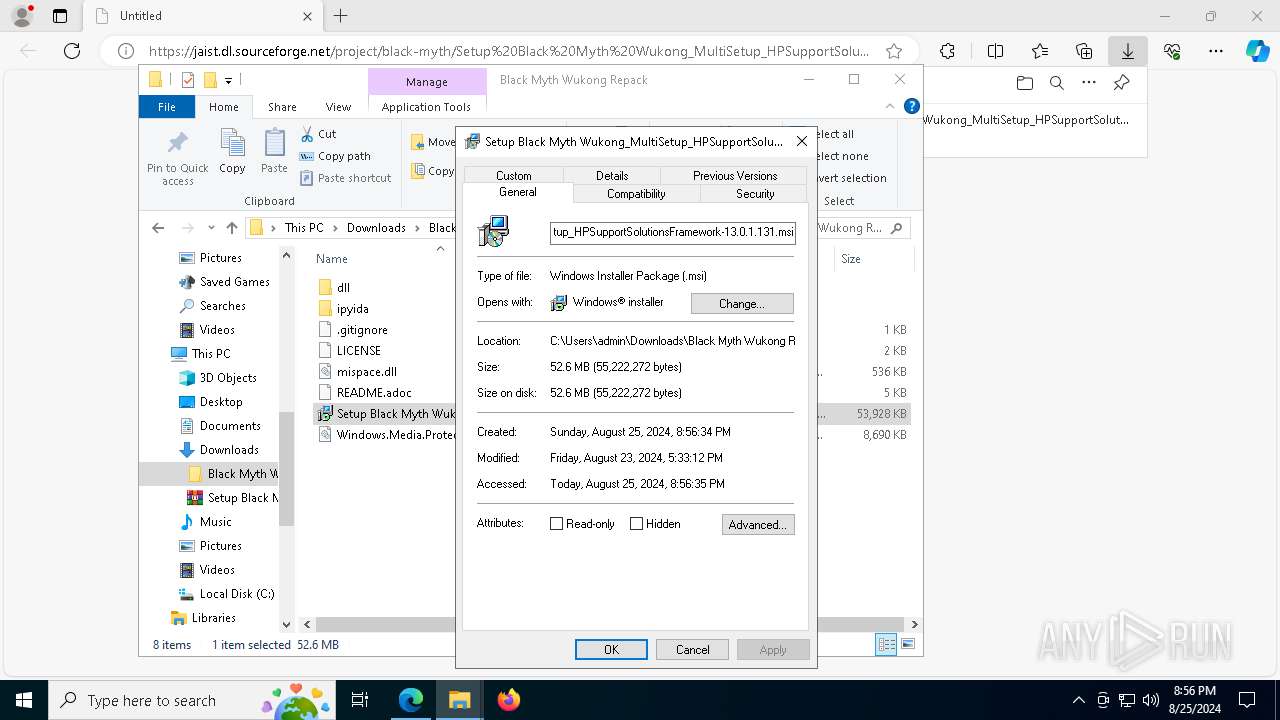
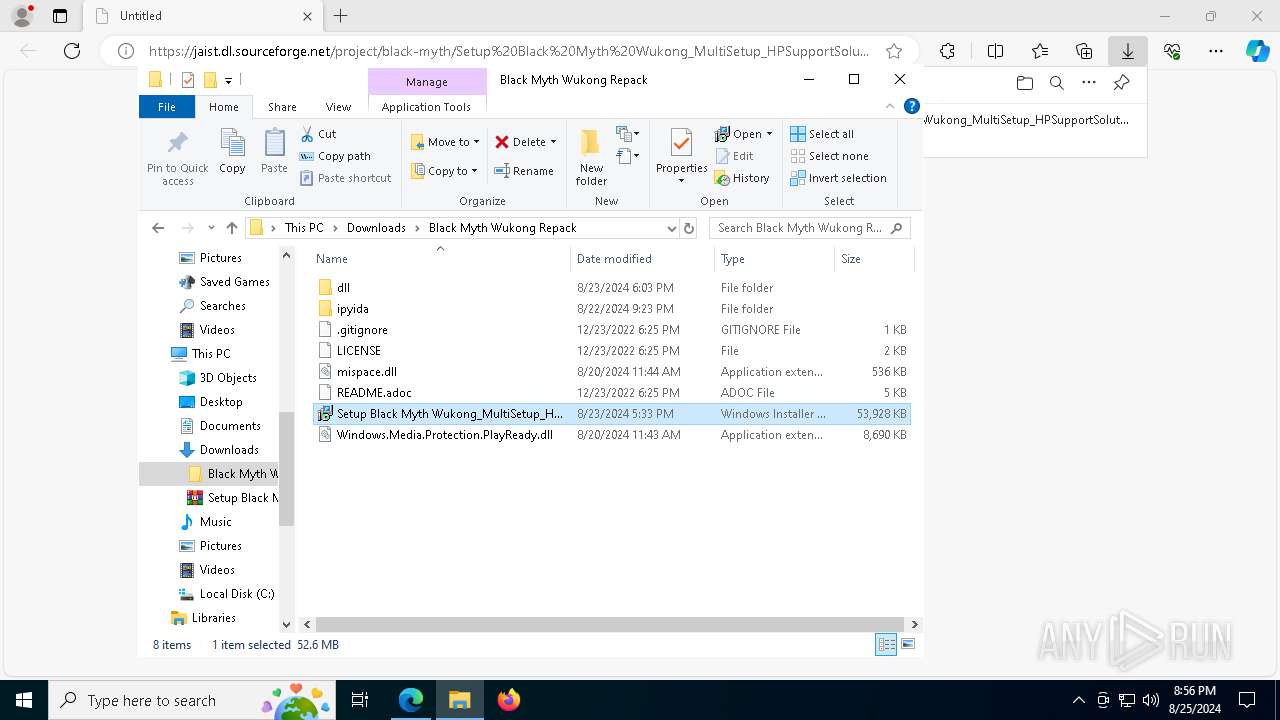
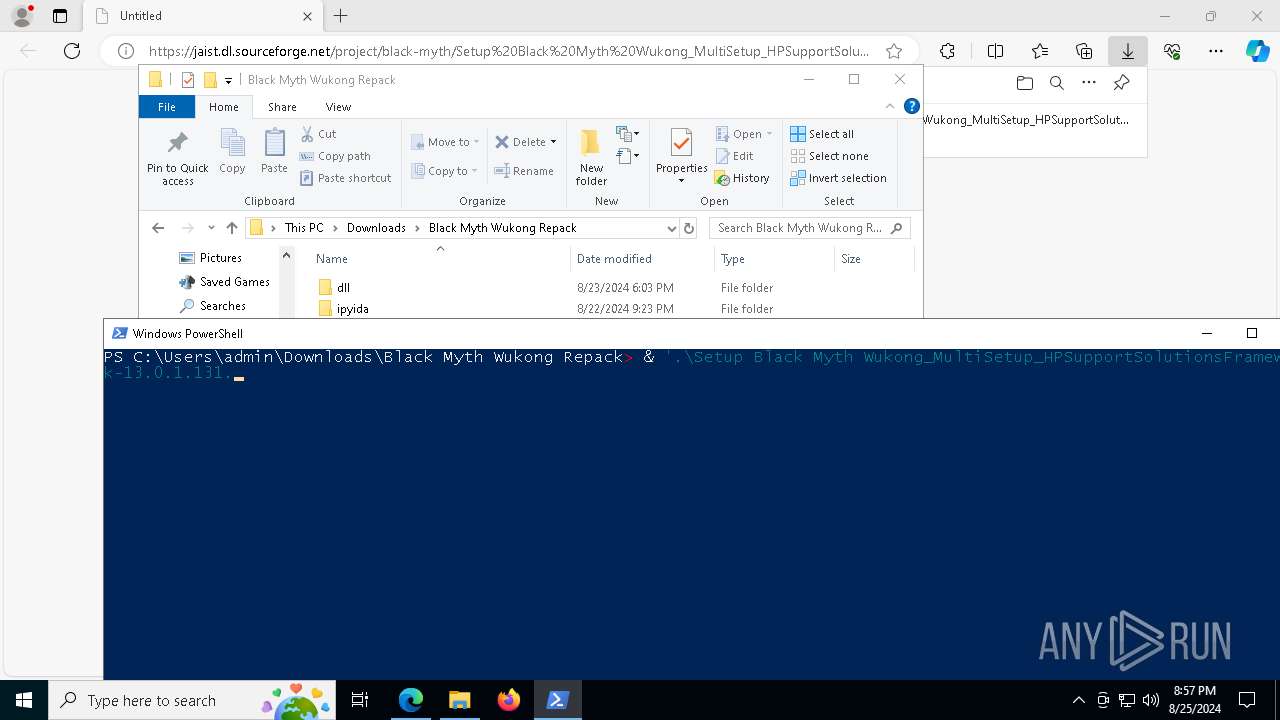
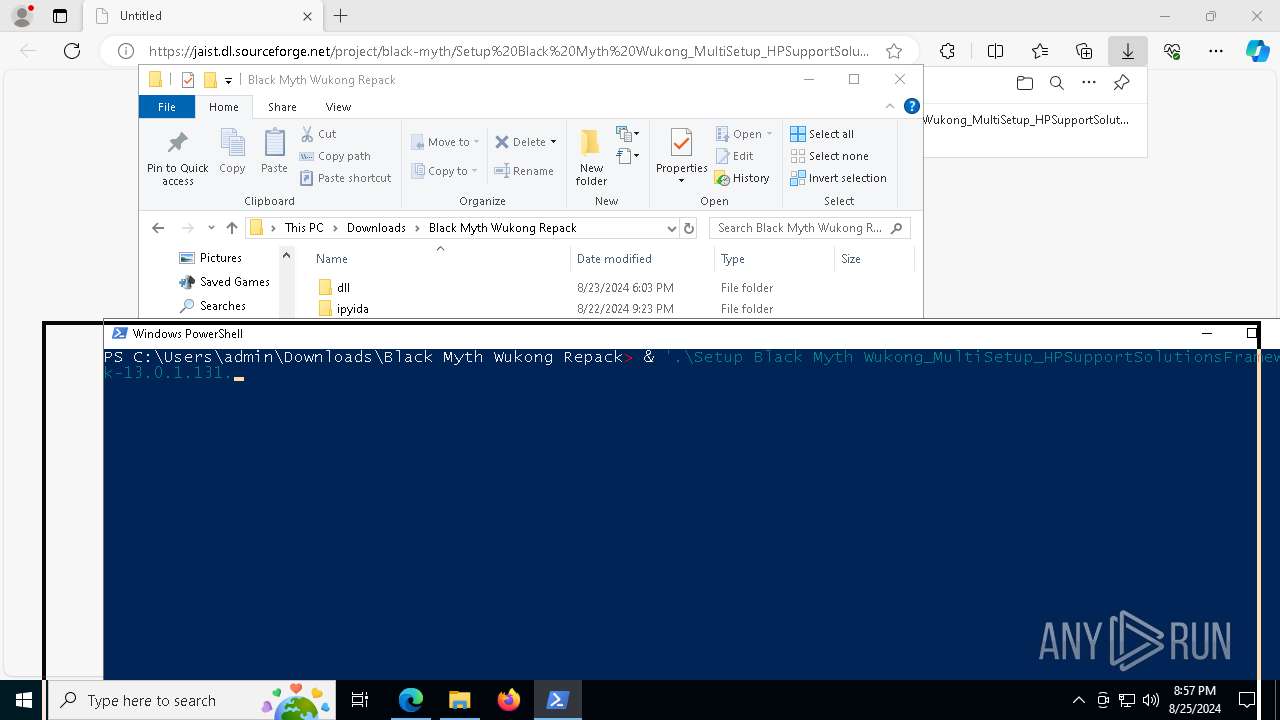
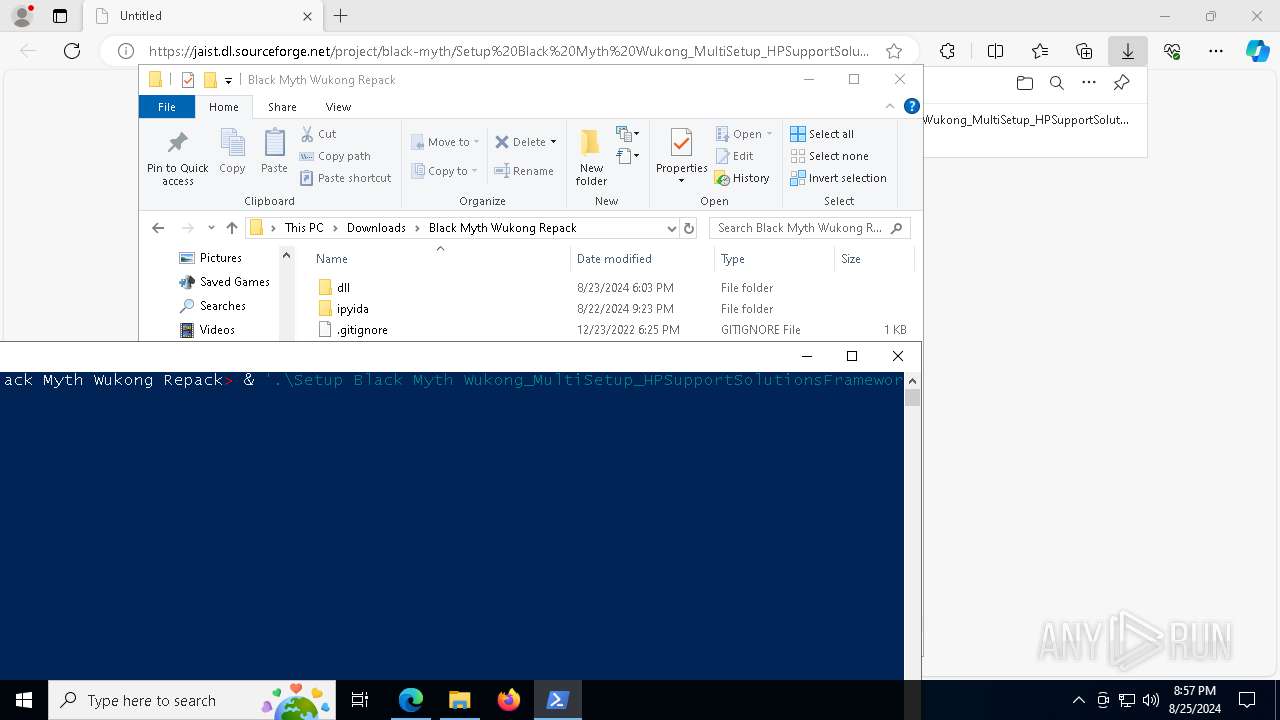
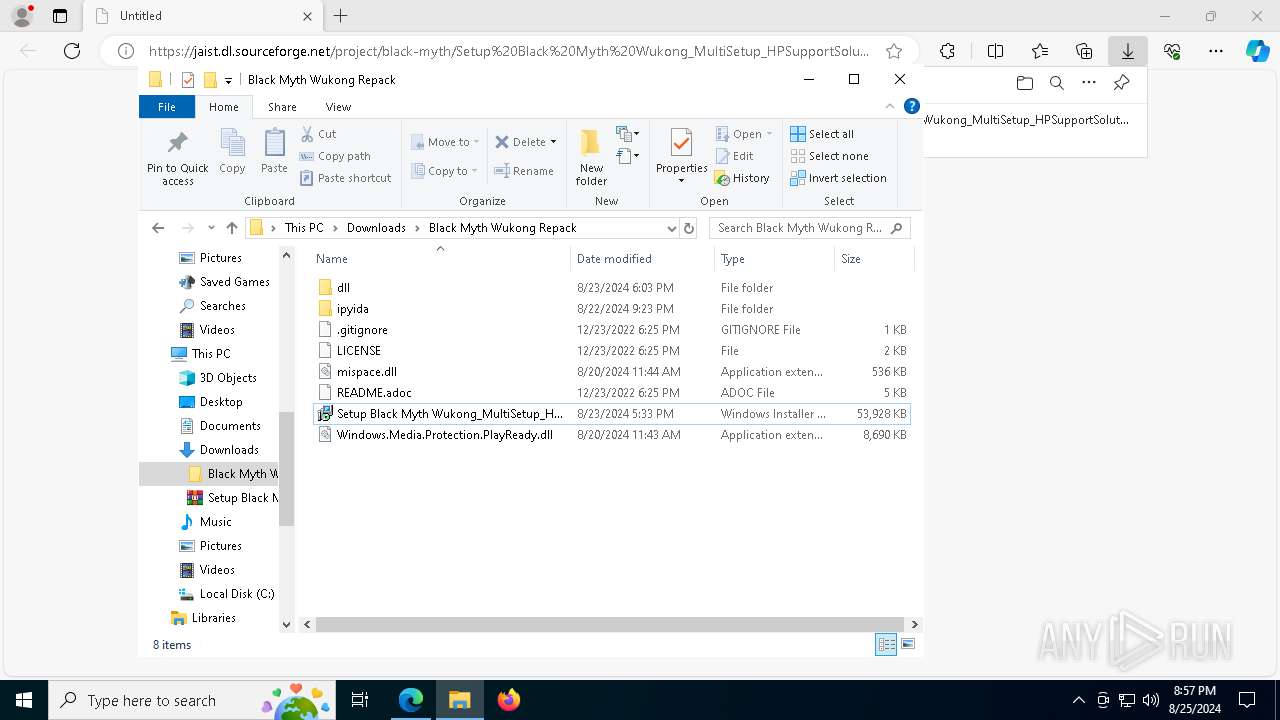
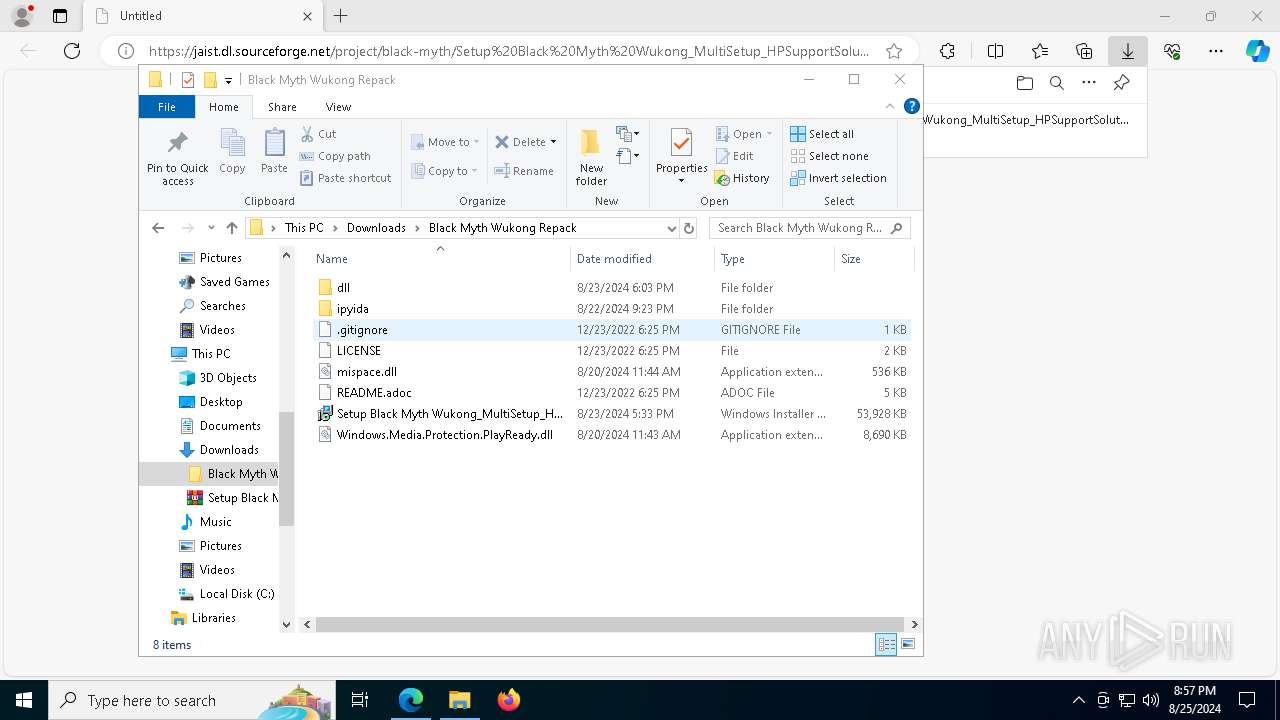
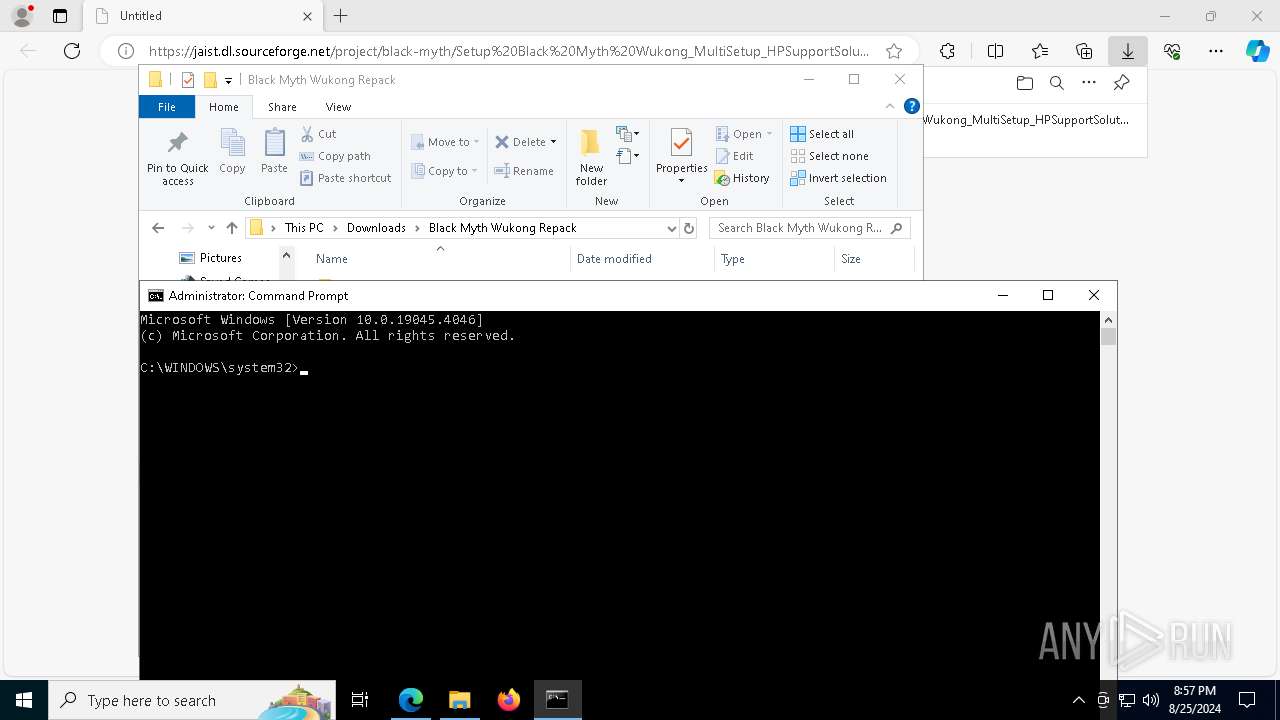
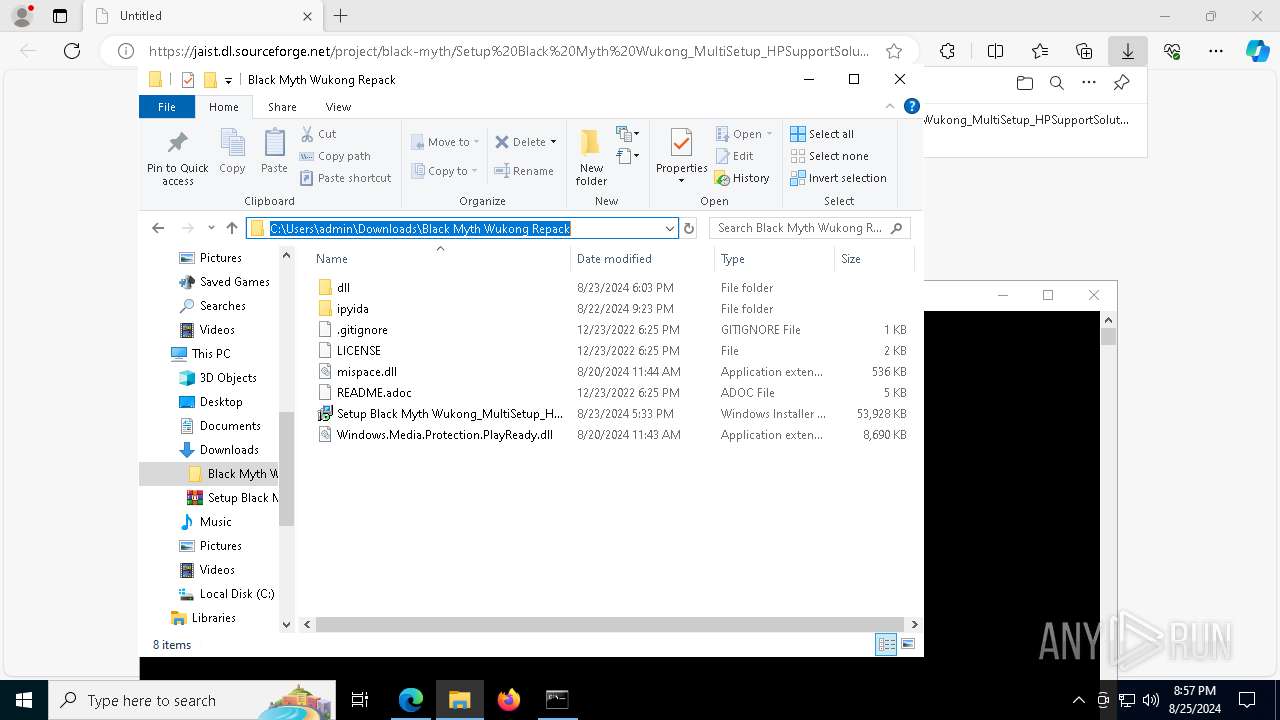
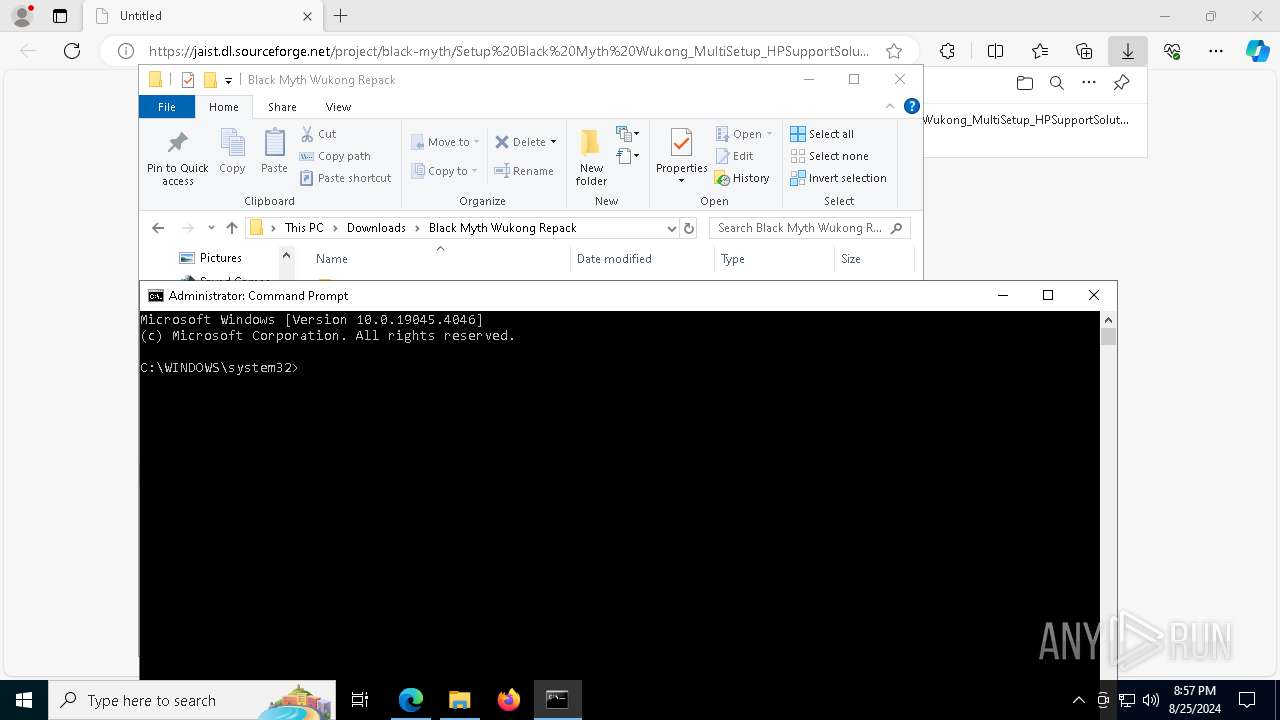
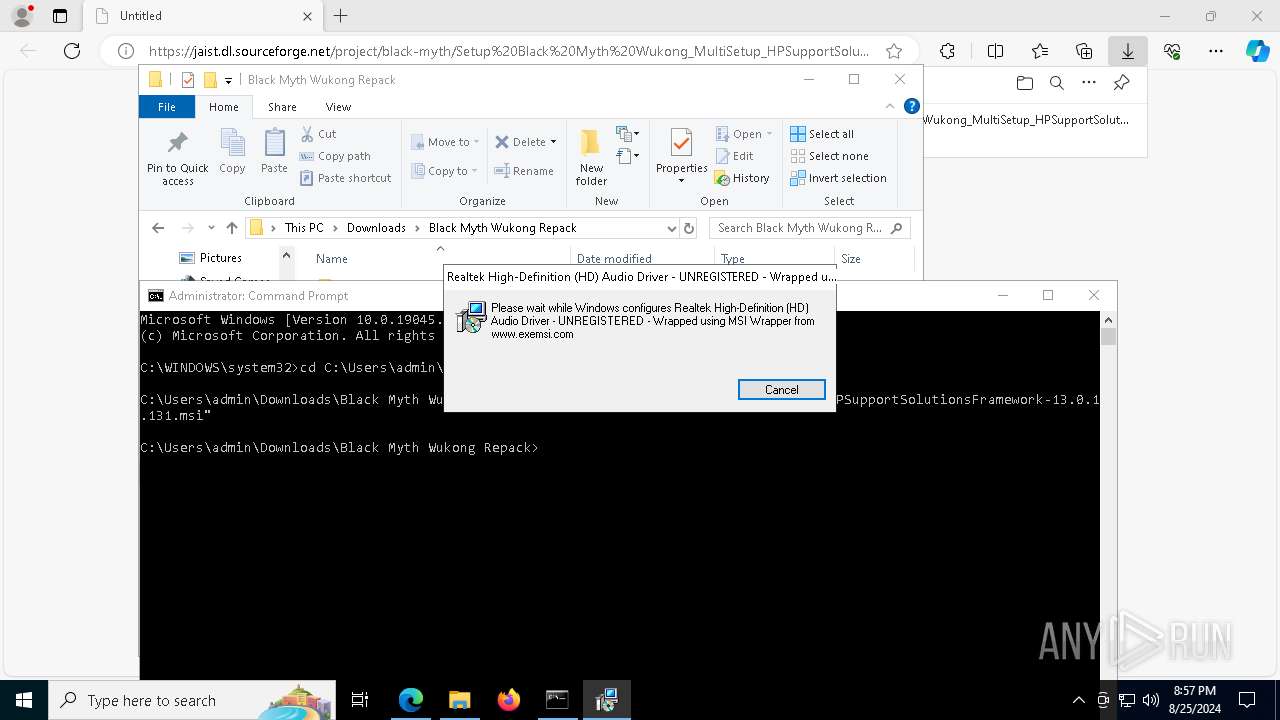
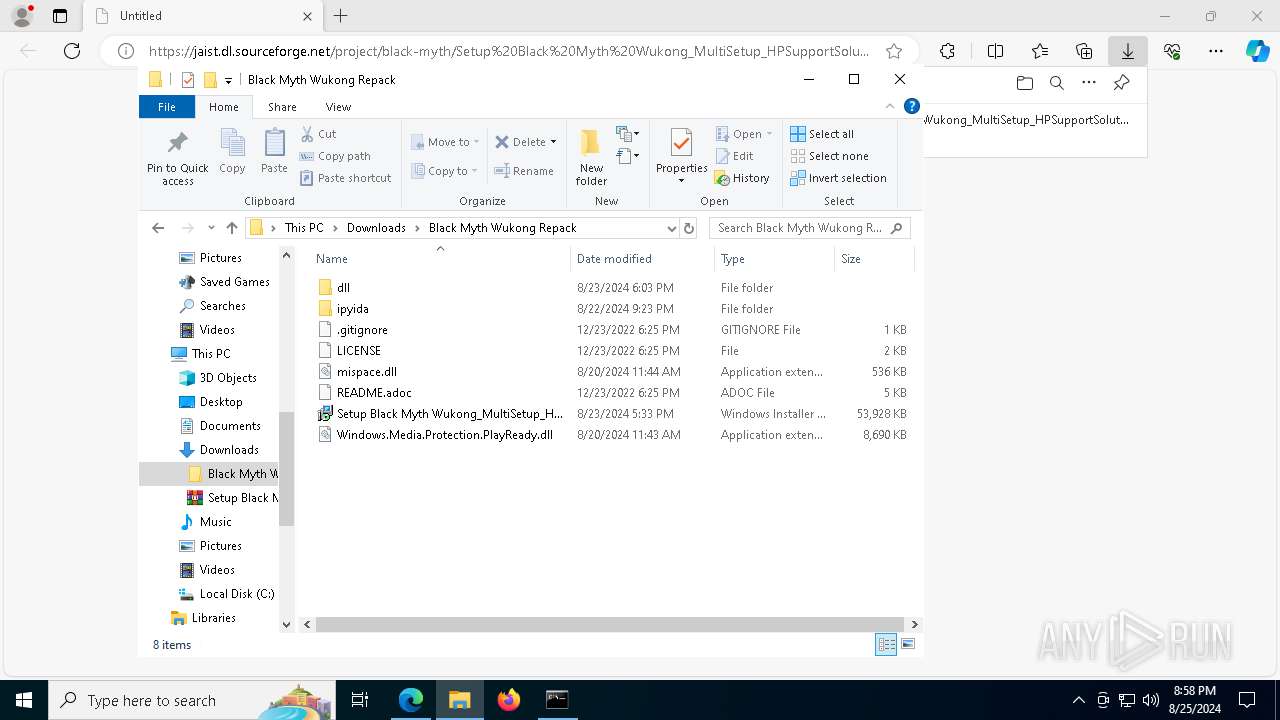
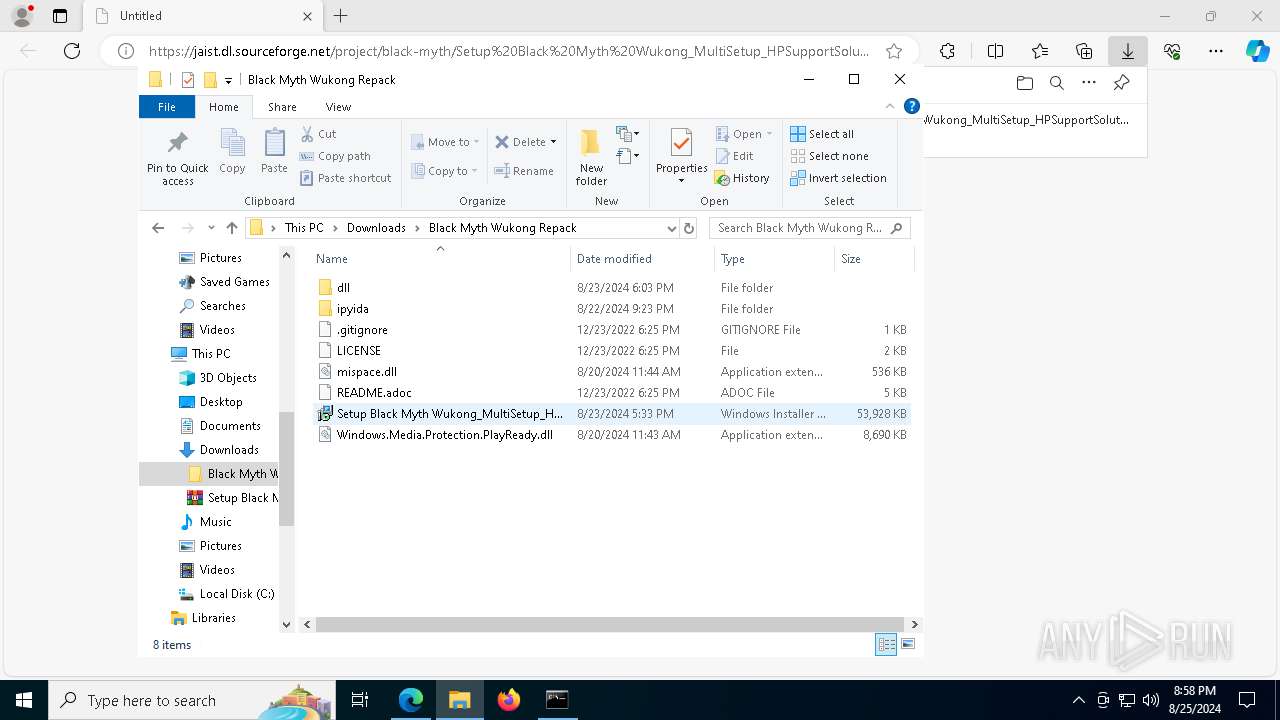
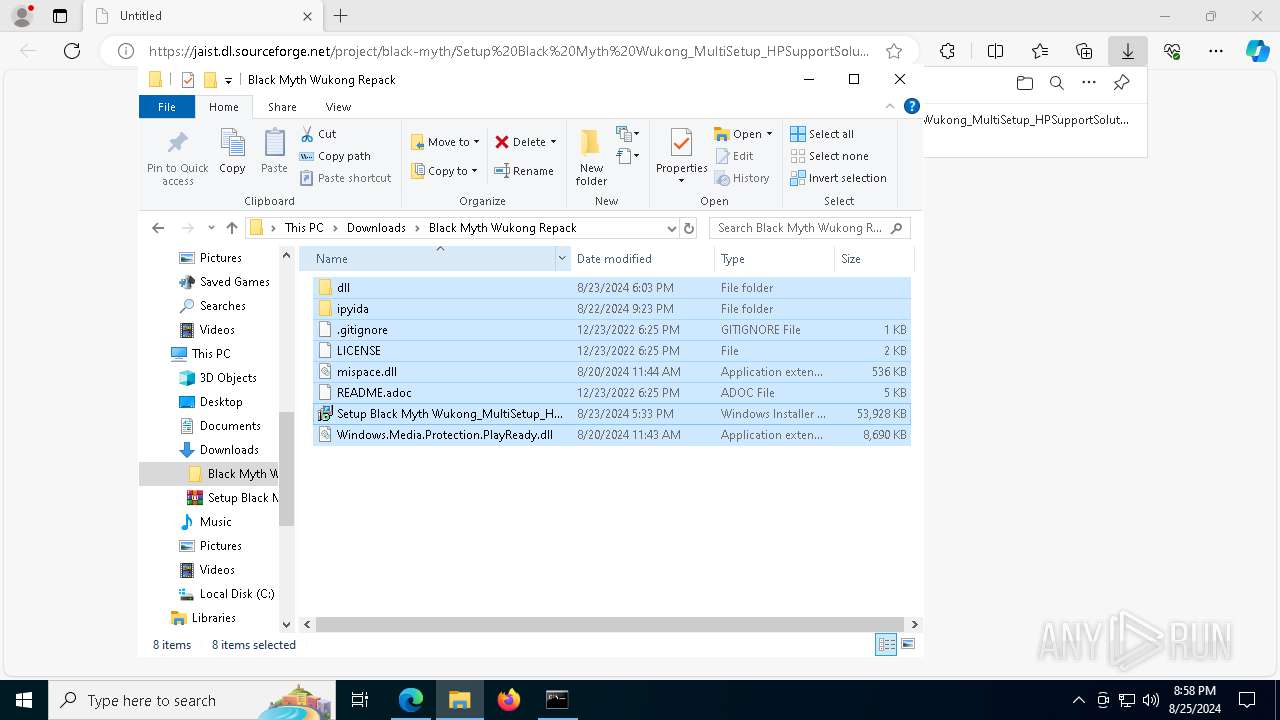
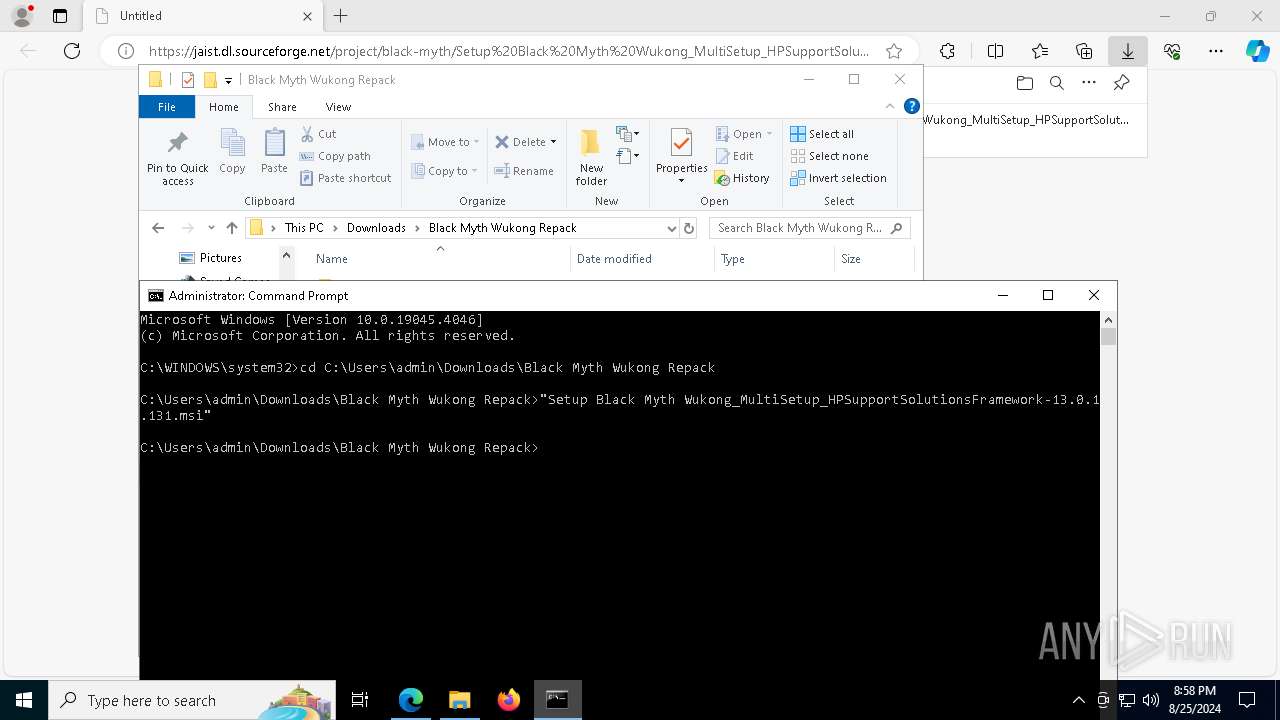
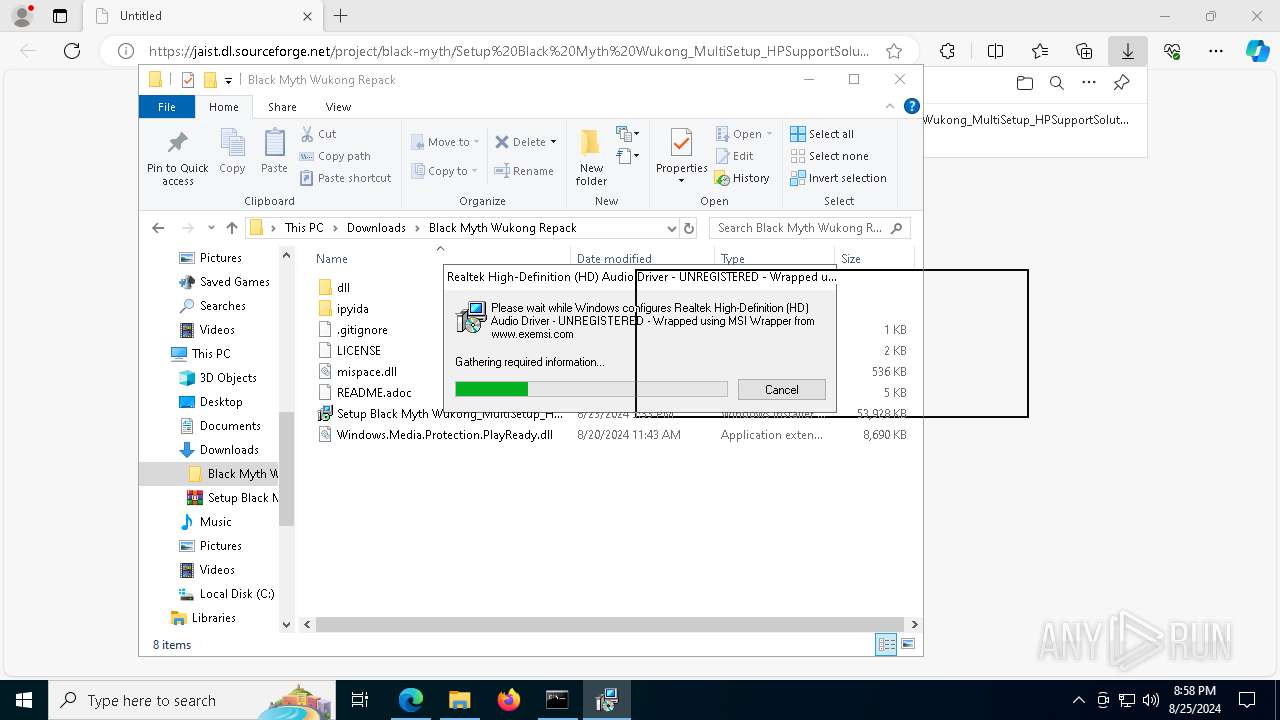
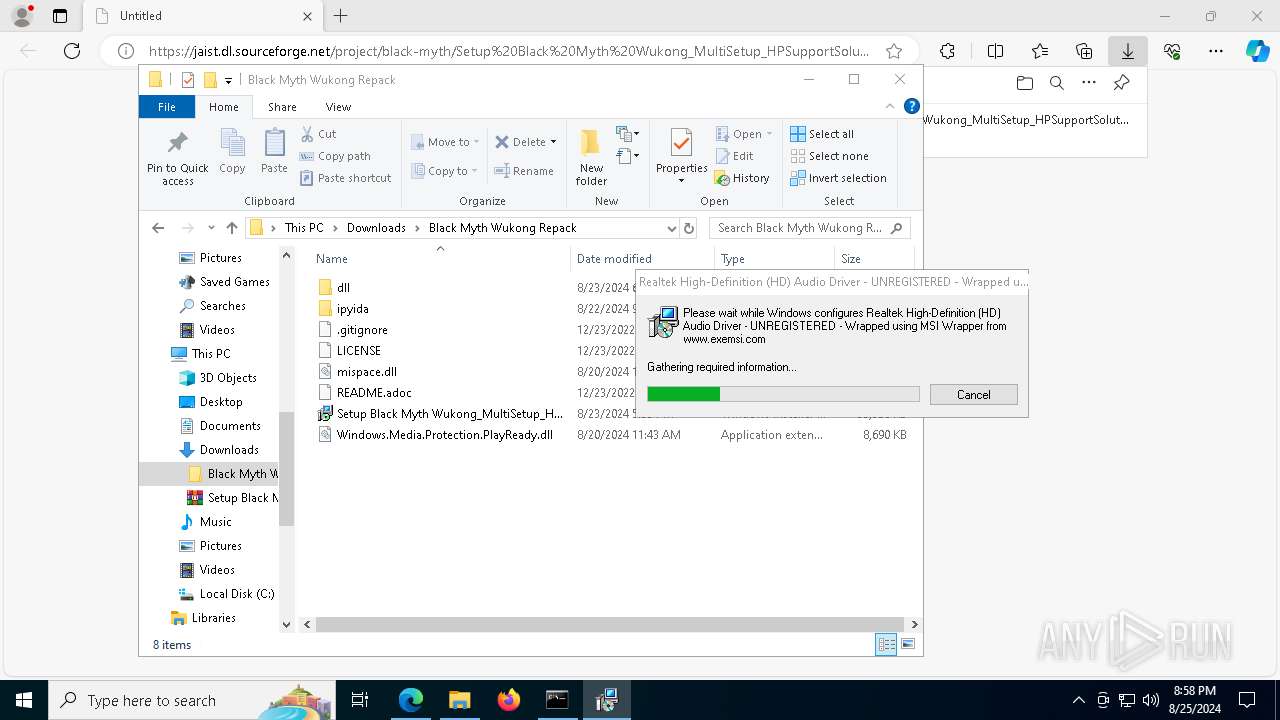
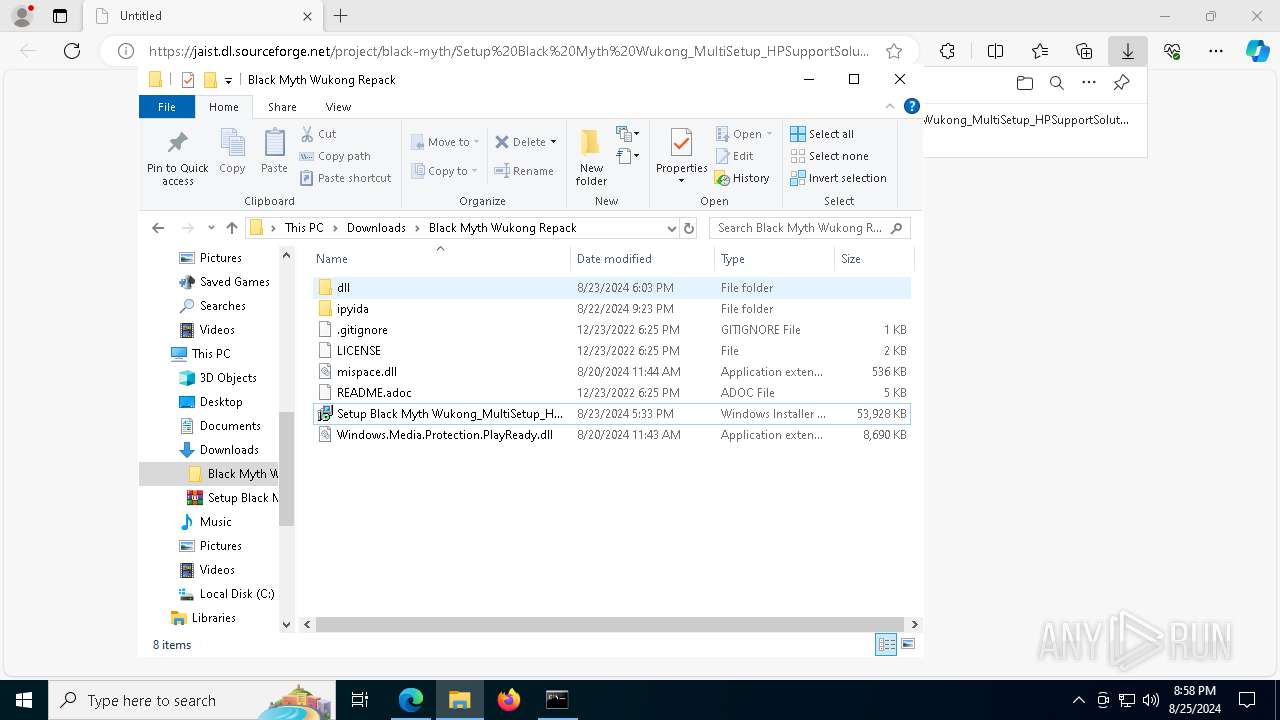
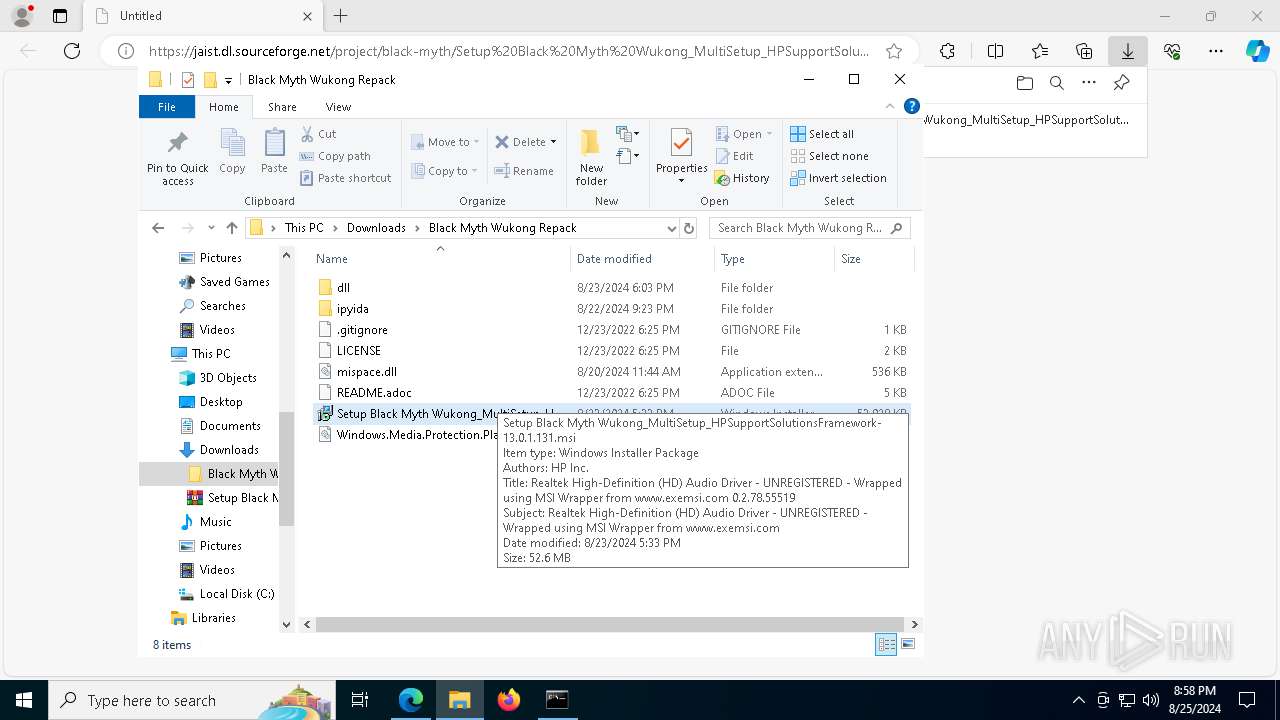
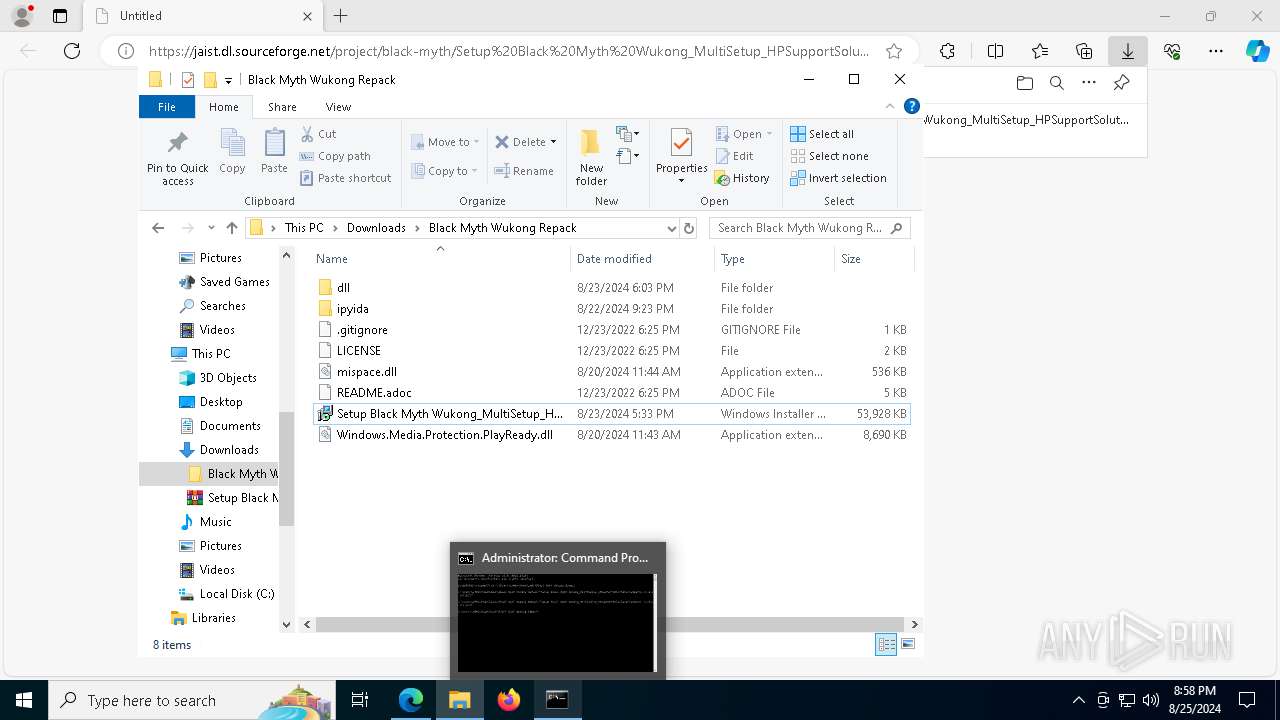
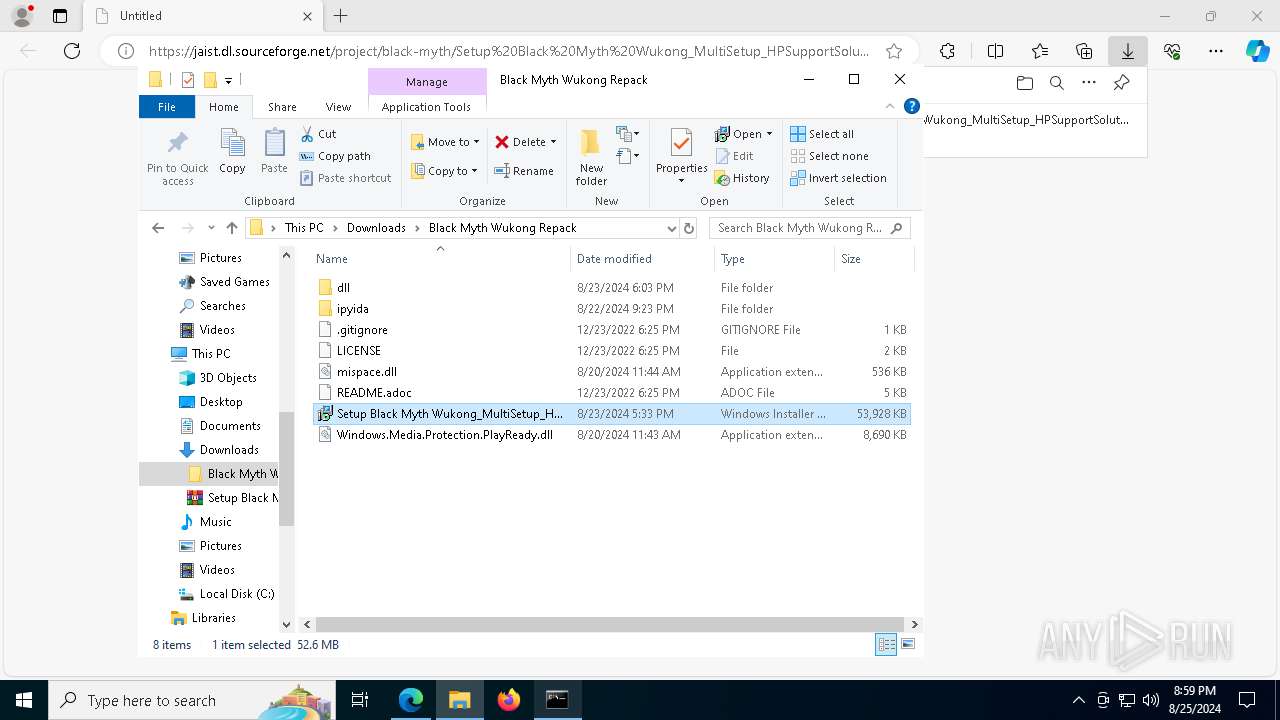
| URL: | https://jaist.dl.sourceforge.net/project/black-myth/Setup%20Black%20Myth%20Wukong_MultiSetup_HPSupportSolutionsFramework-13.0.1.131.zip?viasf=1 |
| Full analysis: | https://app.any.run/tasks/0c4823ae-73f3-49e7-8ced-7dcfa6665b0b |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 25, 2024, 20:54:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5CF7FEF670CE1EC8848C21BFADCBA545 |
| SHA1: | 29629C3A8AA767939DEE8CBBBD5011F888B6A1BC |
| SHA256: | 4490E8405F42CA206E280CD26316EE763C633579DB998C275235033B63F26690 |
| SSDEEP: | 3:N8/WRXC2SuLAuUt4PhpqdaIlbqbn/XQSET9J+LkUhExUn:2/WRXVnCt4P77IVWQ9JR01 |
MALICIOUS
Actions looks like stealing of personal data
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
Stealers network behavior
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
LUMMA has been detected (SURICATA)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
LUMMA has been detected (YARA)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
SUSPICIOUS
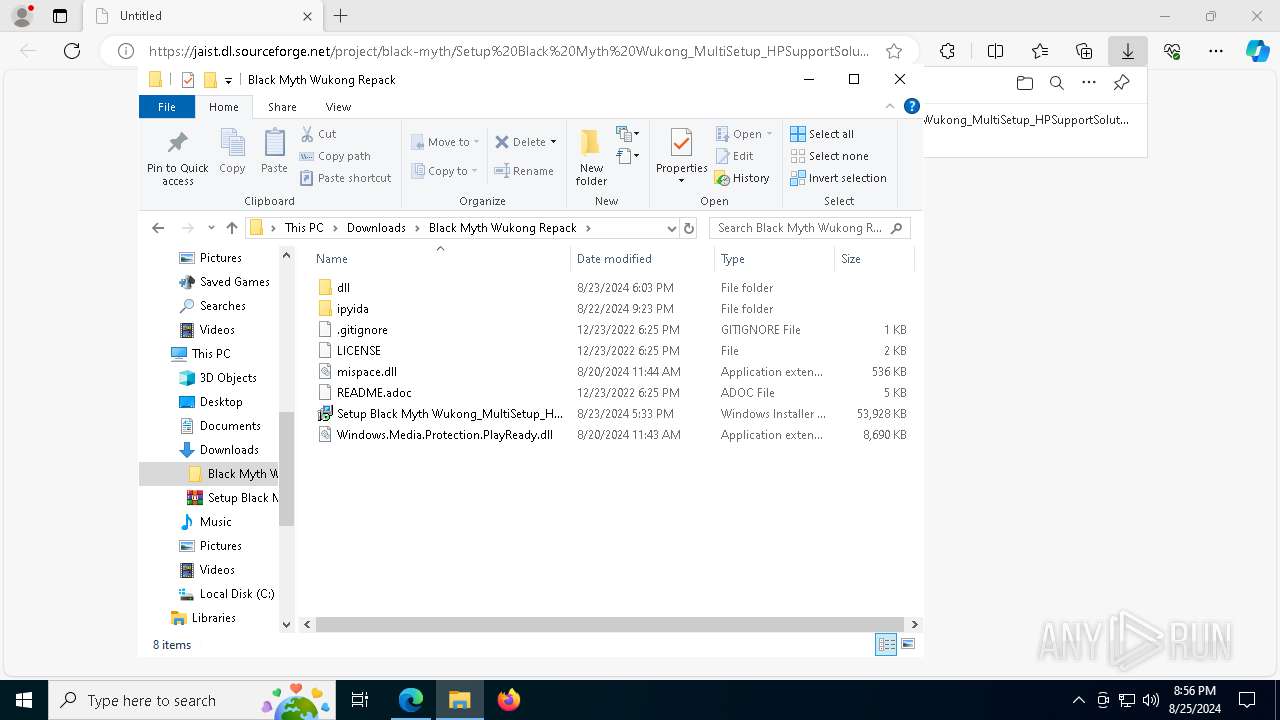
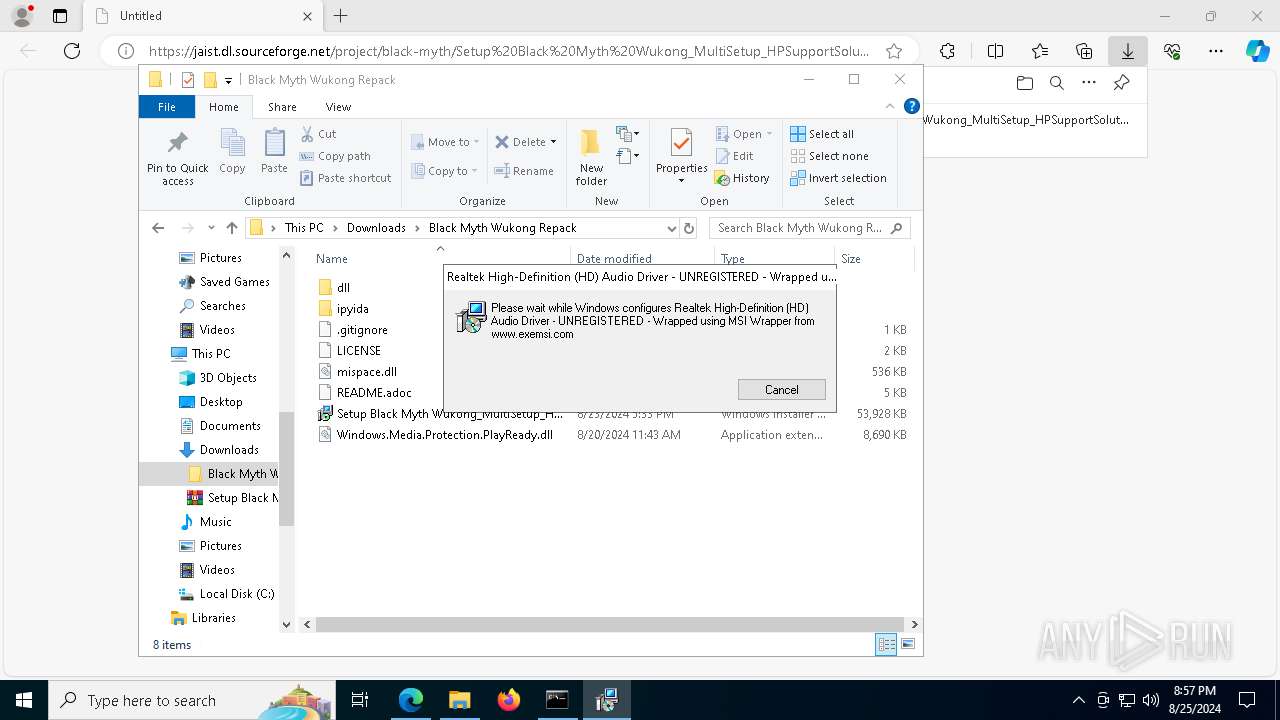
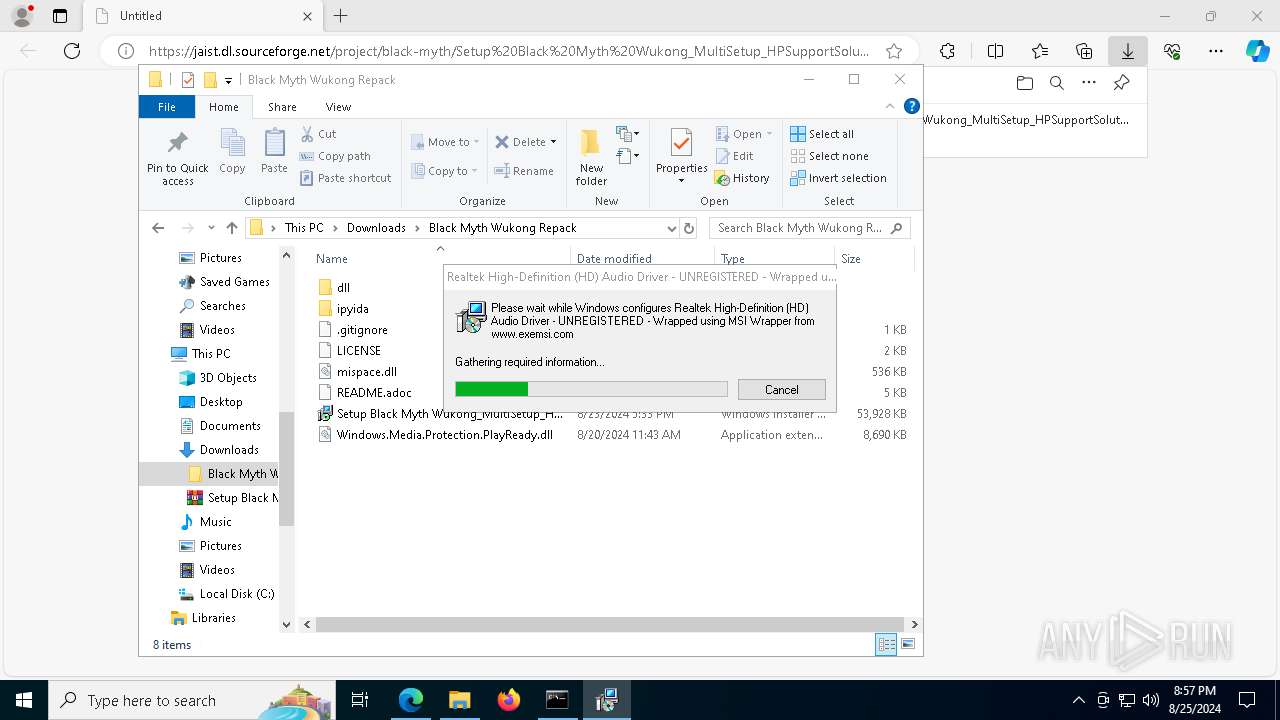
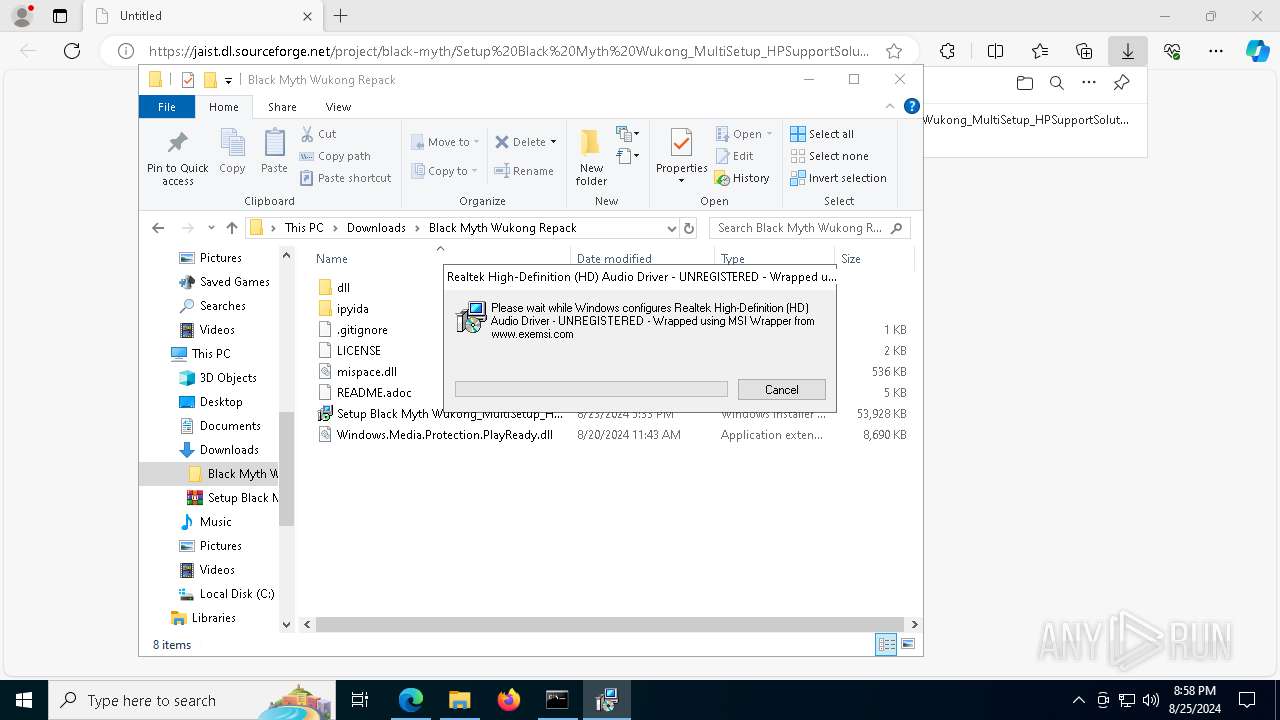
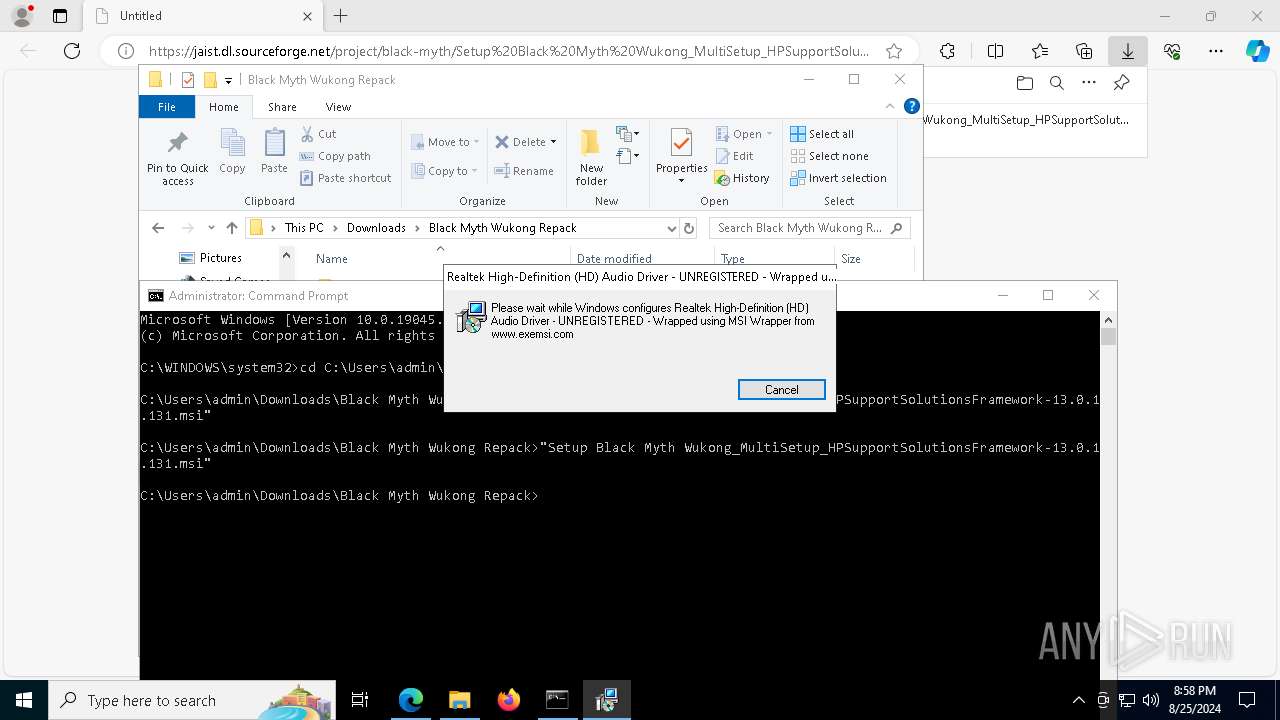
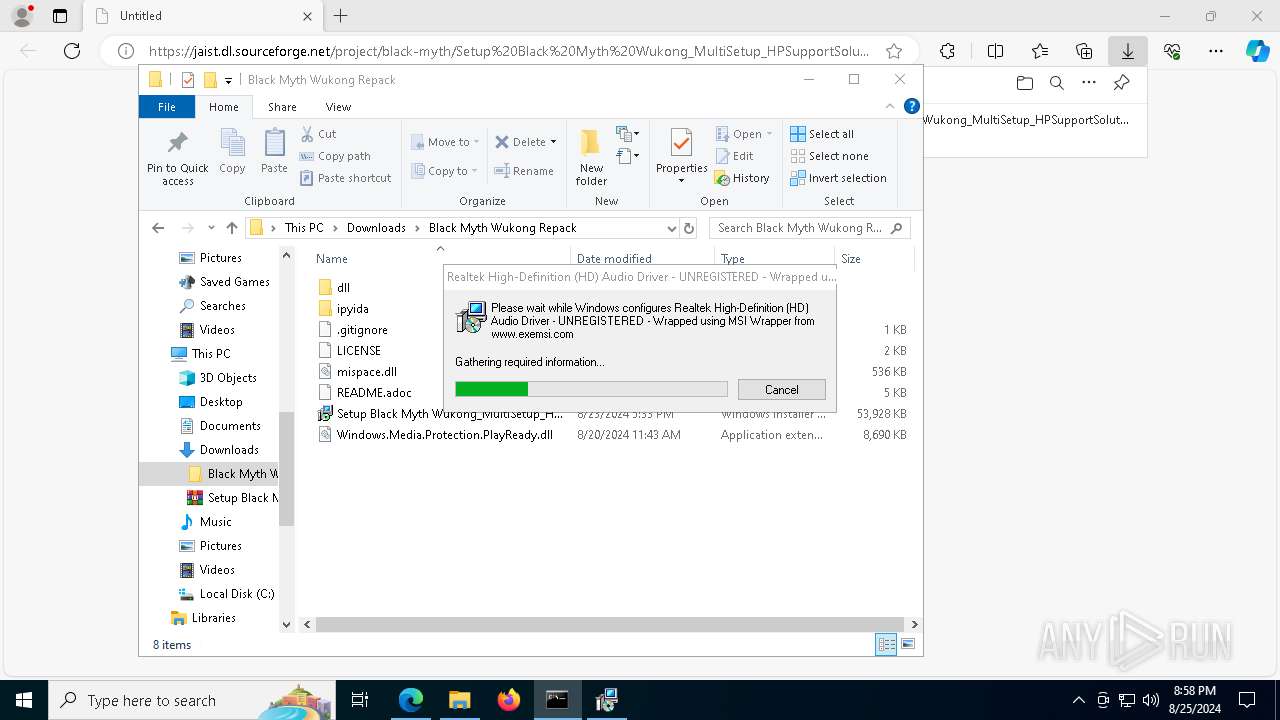
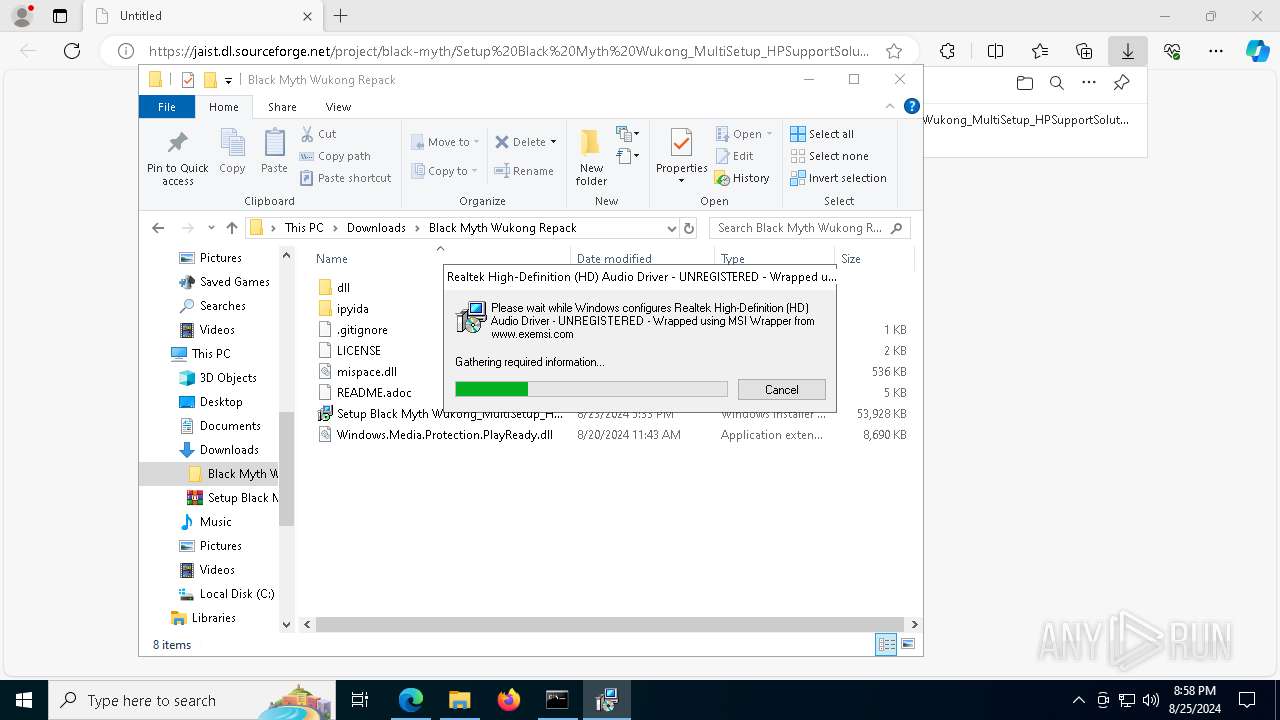
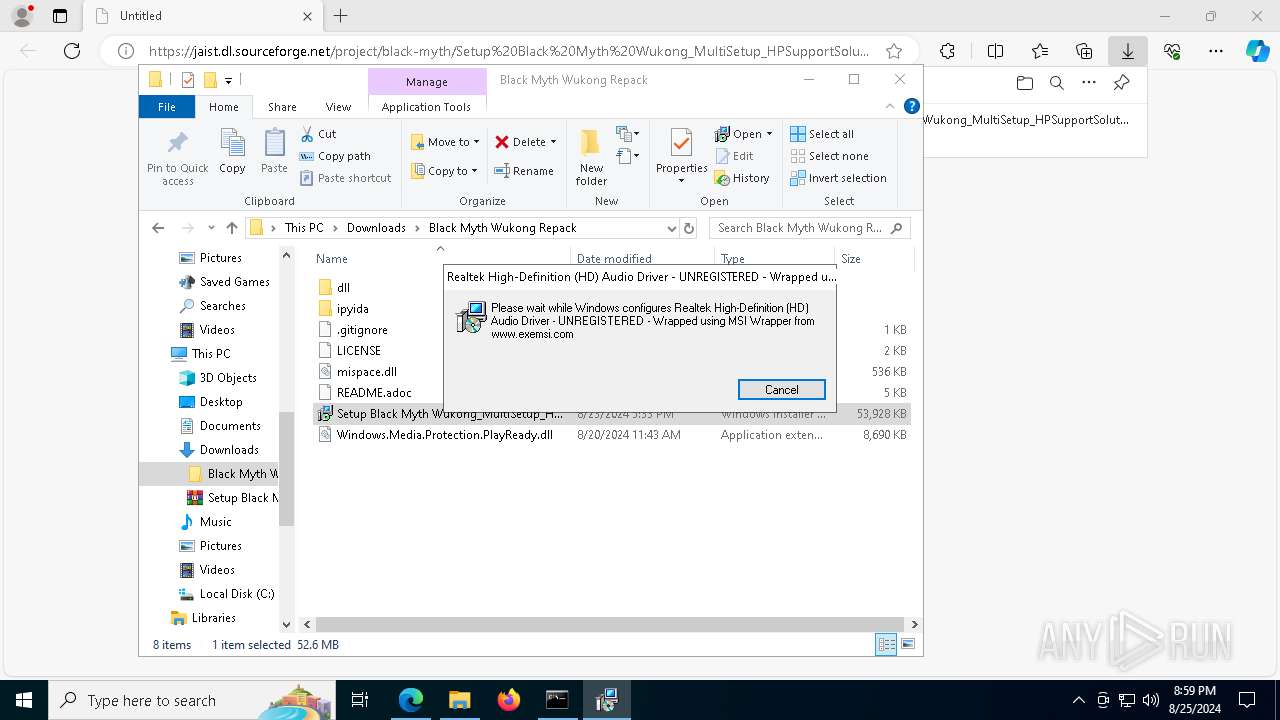
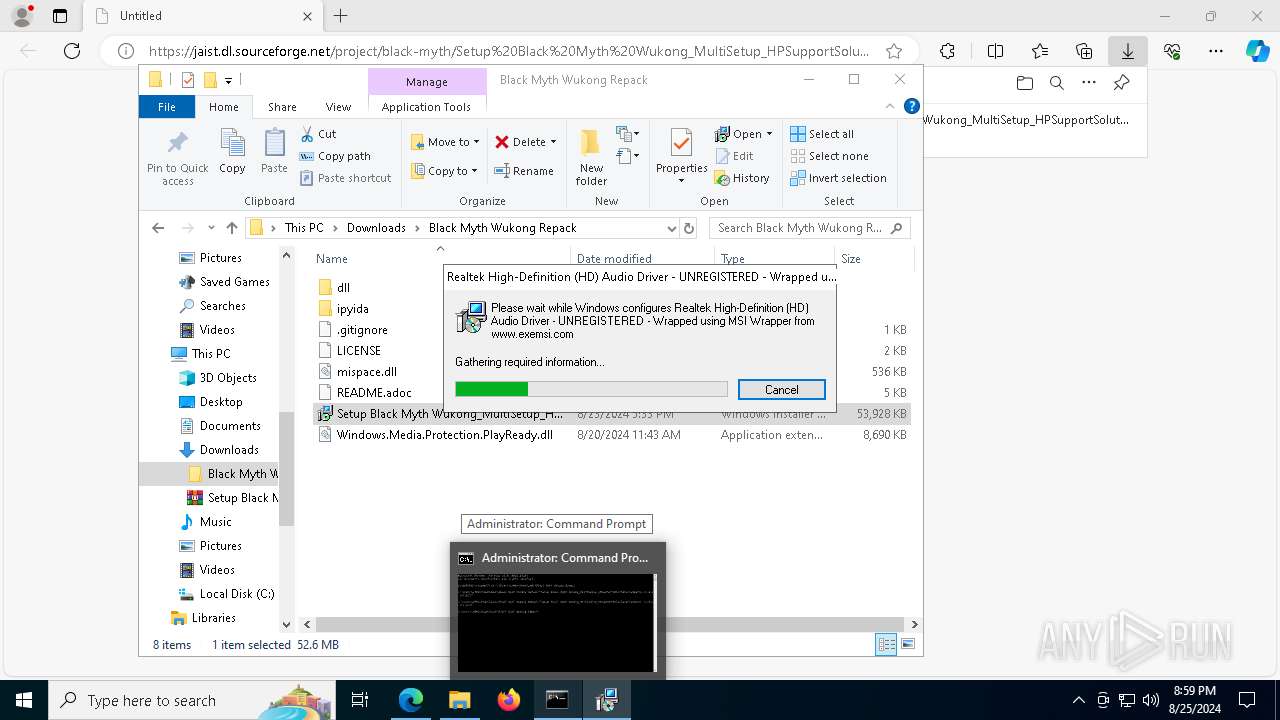
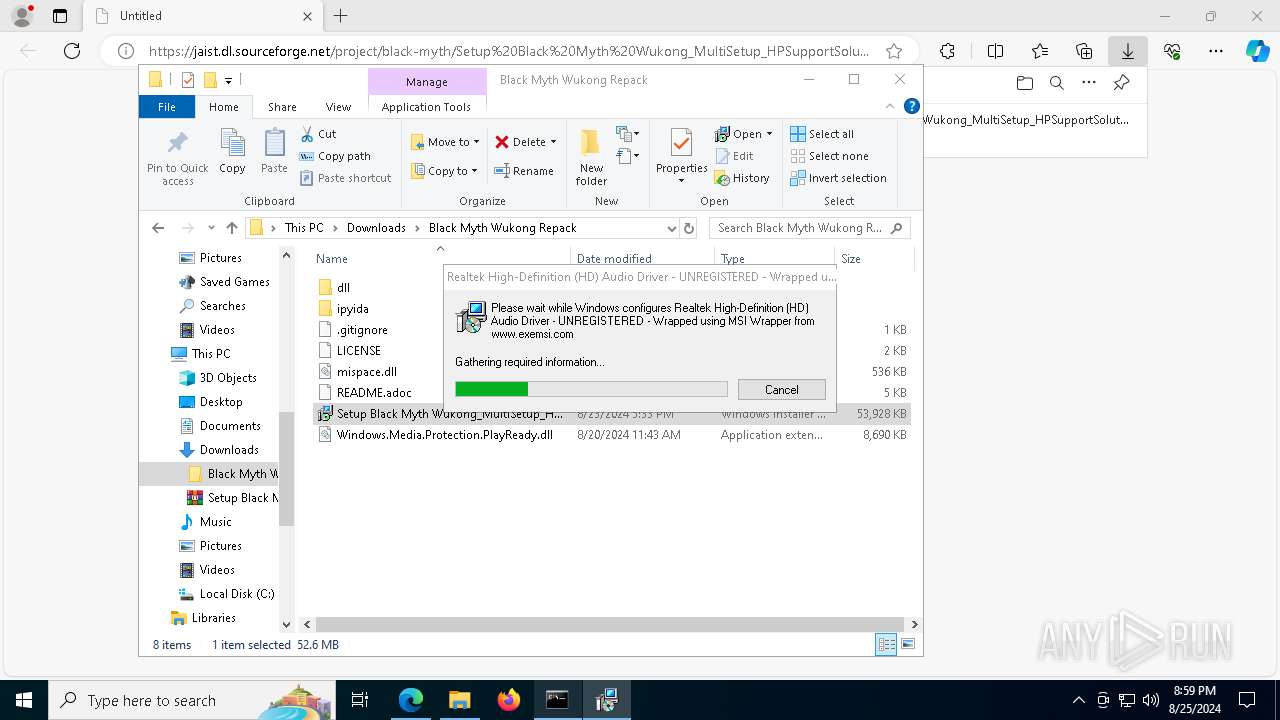
Process drops legitimate windows executable
- WinRAR.exe (PID: 8144)
Executes as Windows Service
- VSSVC.exe (PID: 2324)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7060)
Drops the executable file immediately after the start
- msiexec.exe (PID: 7060)
- expand.exe (PID: 7396)
- expand.exe (PID: 508)
- expand.exe (PID: 7864)
Executable content was dropped or overwritten
- expand.exe (PID: 7396)
- expand.exe (PID: 508)
- expand.exe (PID: 7864)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2876)
- msiexec.exe (PID: 6516)
- msiexec.exe (PID: 7600)
Reads the date of Windows installation
- msiexec.exe (PID: 2876)
- msiexec.exe (PID: 6516)
- msiexec.exe (PID: 7600)
Unpacks CAB file
- expand.exe (PID: 7396)
- expand.exe (PID: 508)
- expand.exe (PID: 7864)
Uses ICACLS.EXE to modify access control lists
- msiexec.exe (PID: 2876)
- msiexec.exe (PID: 6516)
Searches for installed software
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
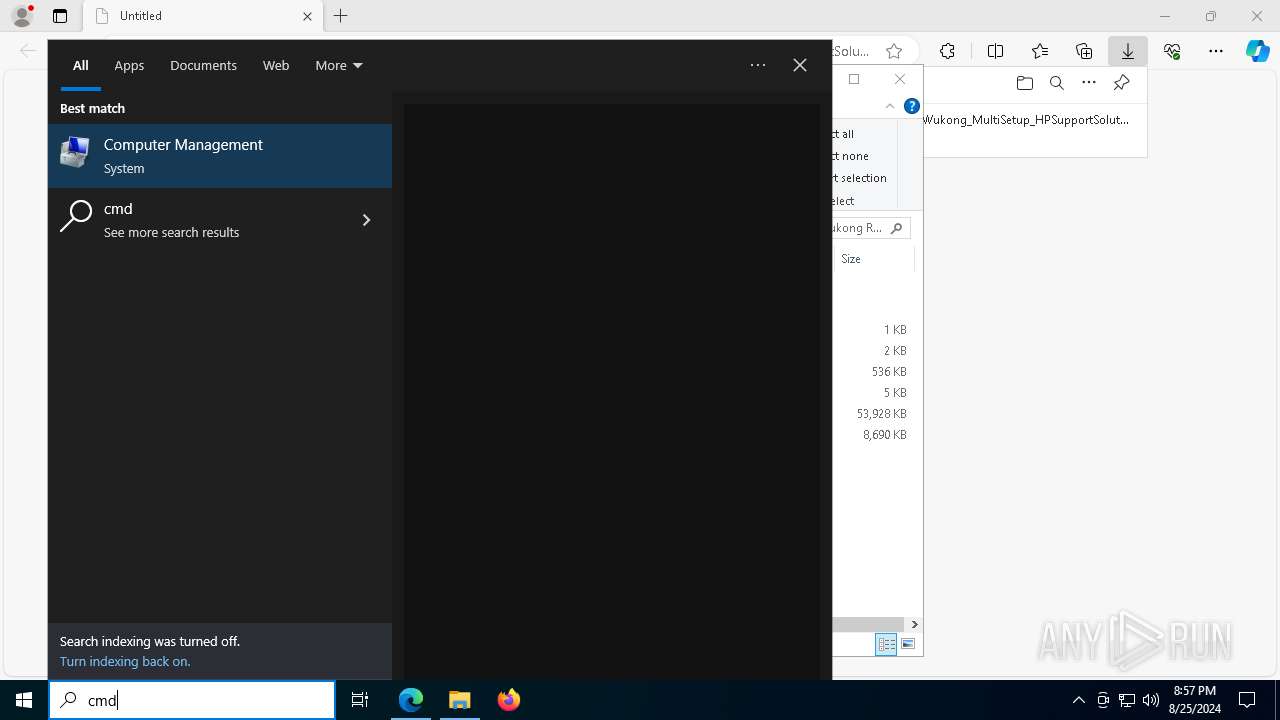
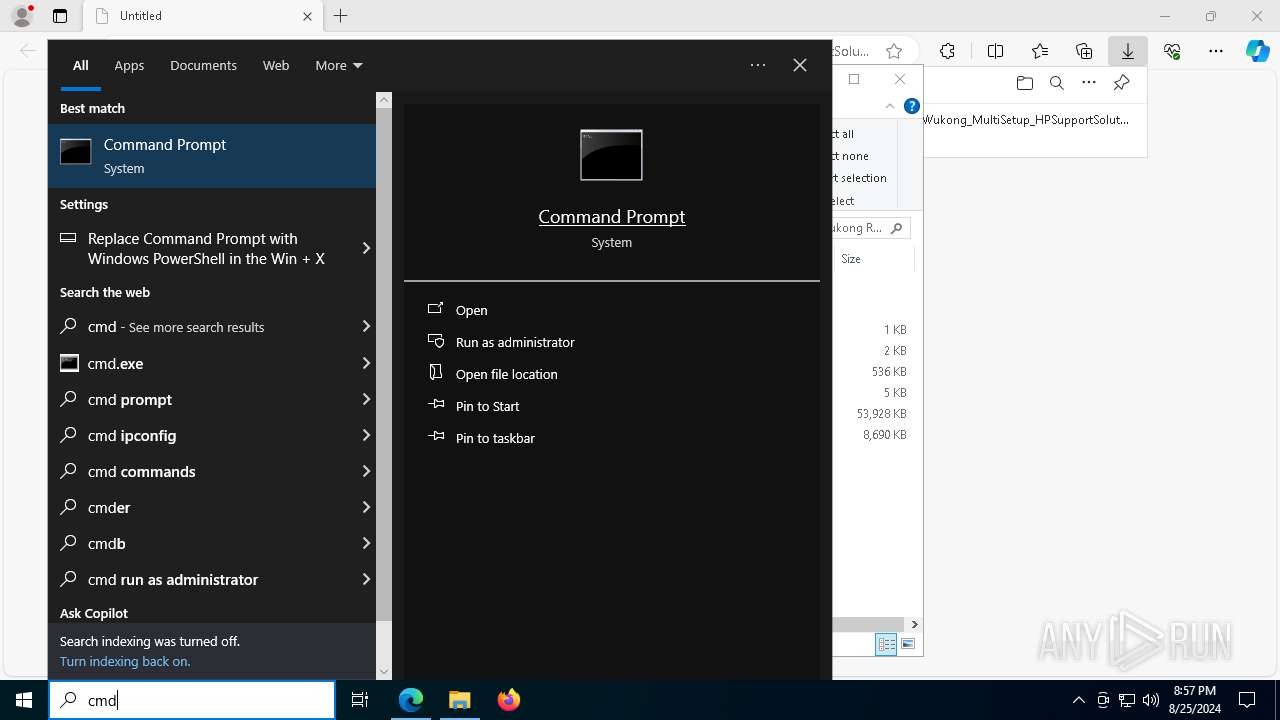
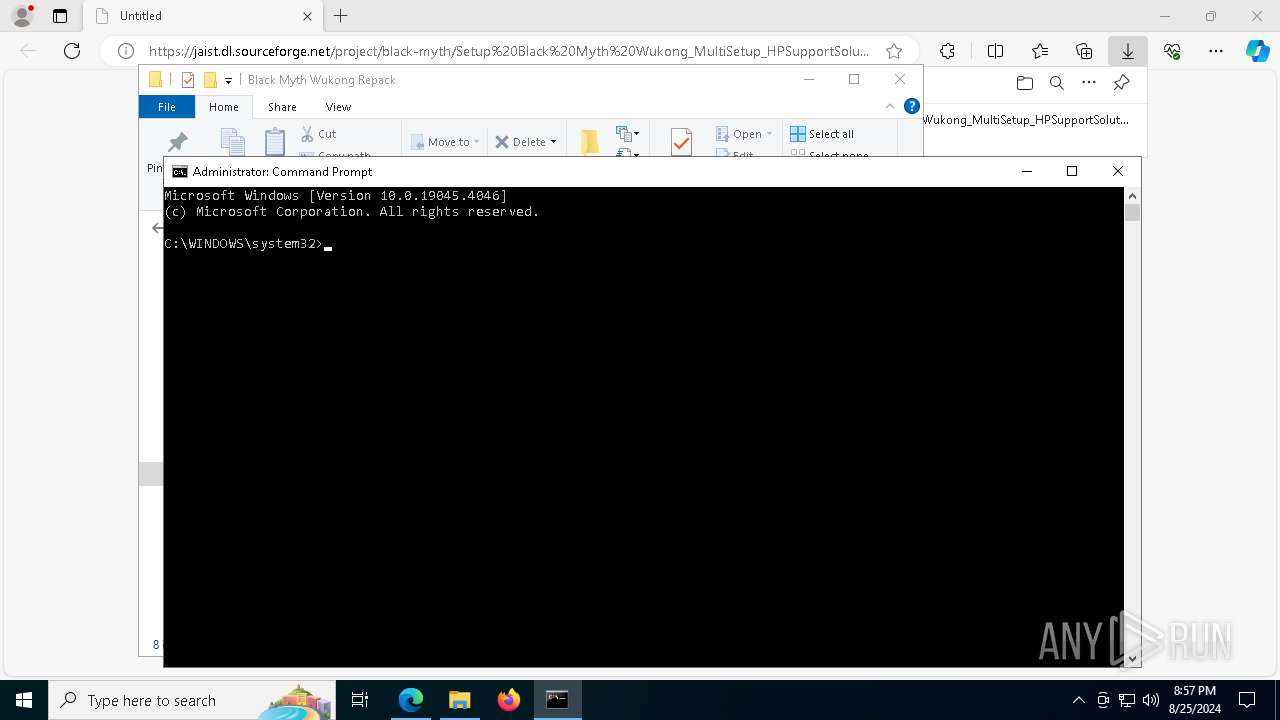
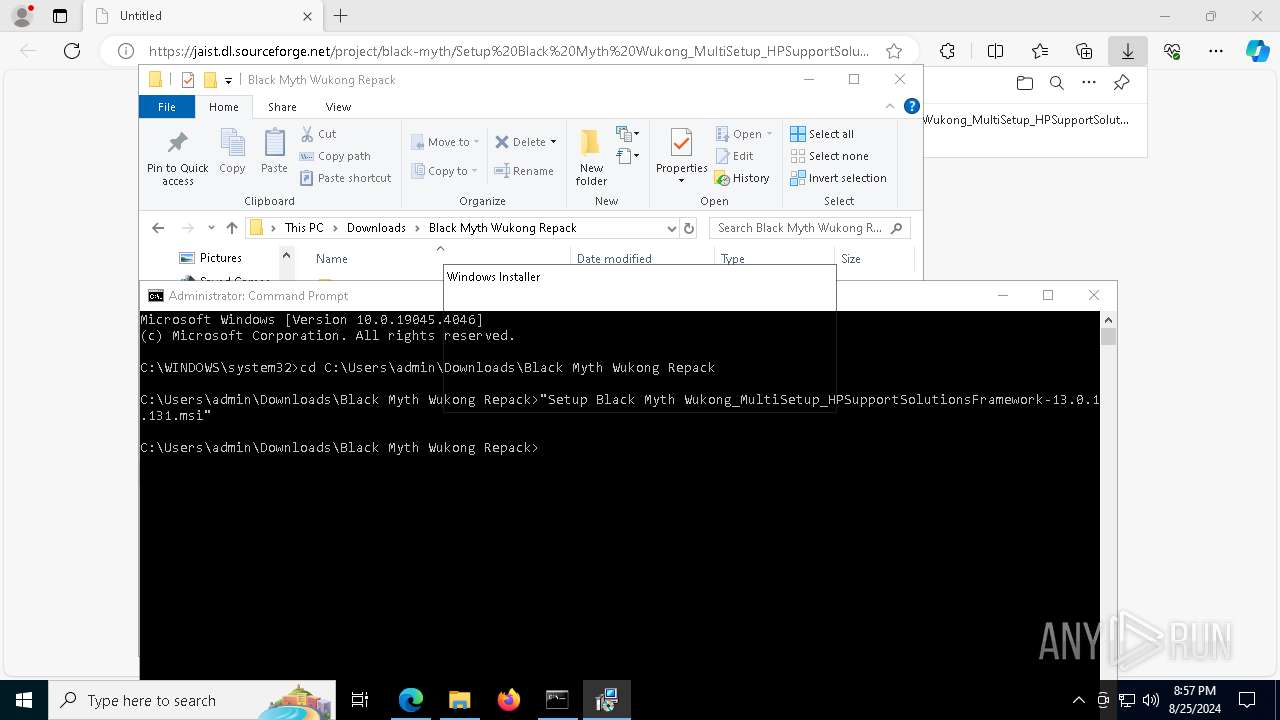
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 2876)
- msiexec.exe (PID: 6516)
- msiexec.exe (PID: 7600)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6548)
Application launched itself
- msedge.exe (PID: 6548)
Checks supported languages
- identity_helper.exe (PID: 7316)
- msiexec.exe (PID: 7060)
- msiexec.exe (PID: 2876)
- expand.exe (PID: 7396)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- expand.exe (PID: 508)
- msiexec.exe (PID: 6516)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- expand.exe (PID: 7864)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
- msiexec.exe (PID: 7600)
Reads Environment values
- identity_helper.exe (PID: 7316)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8144)
- msiexec.exe (PID: 7060)
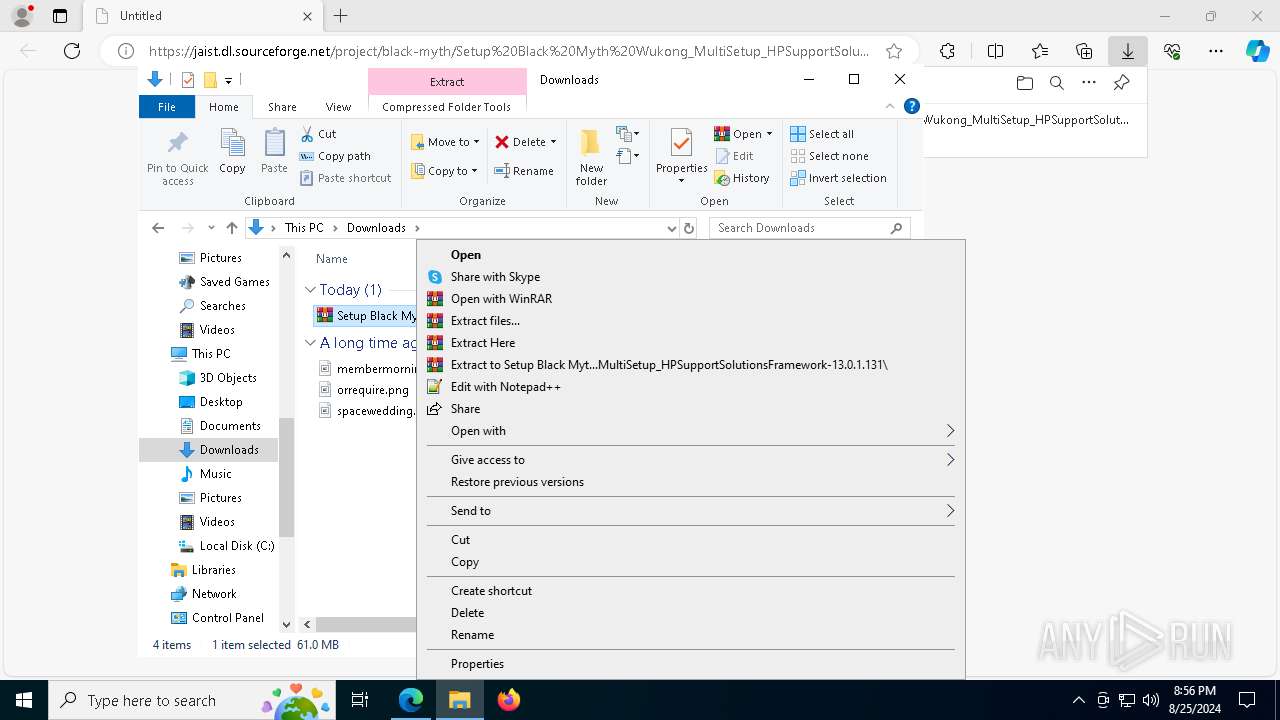
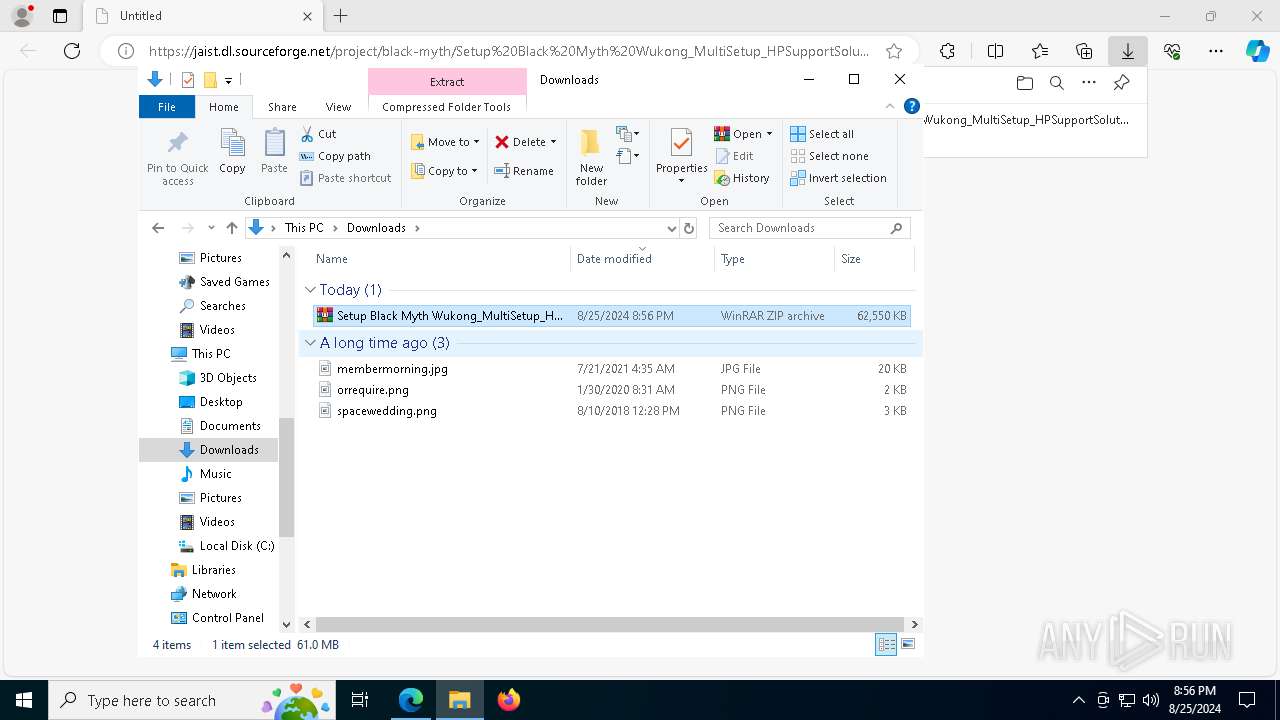
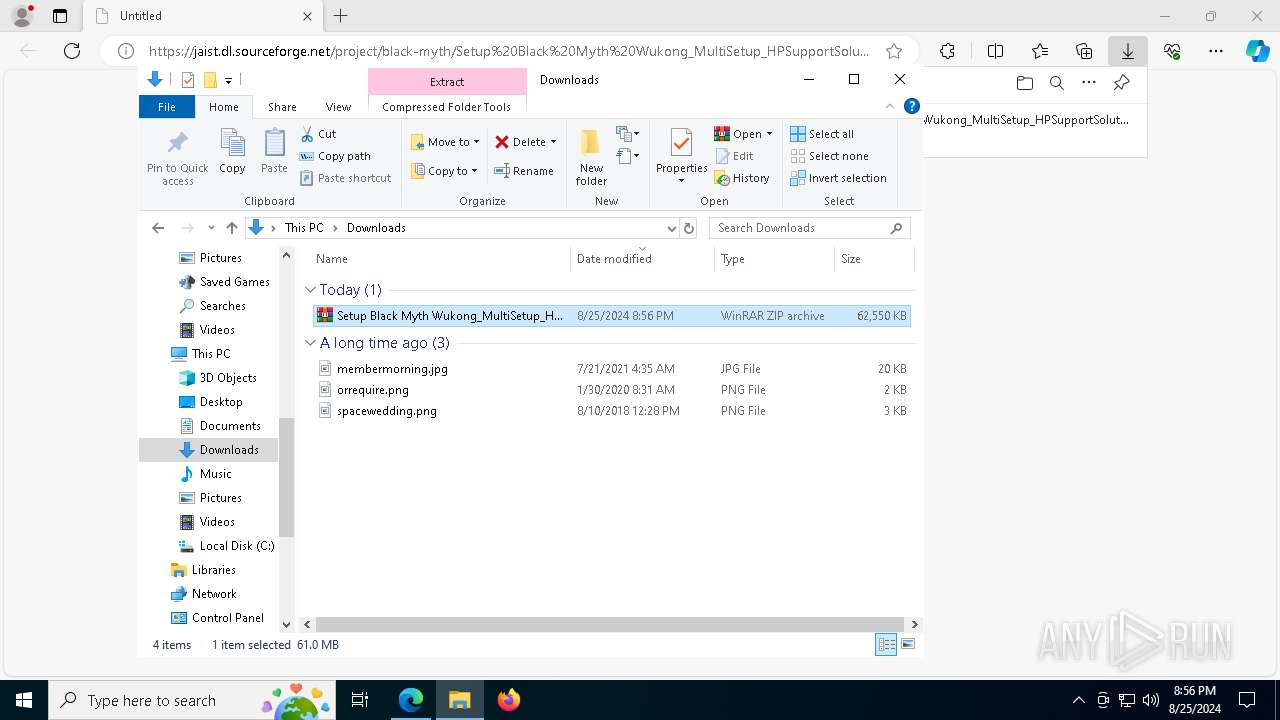
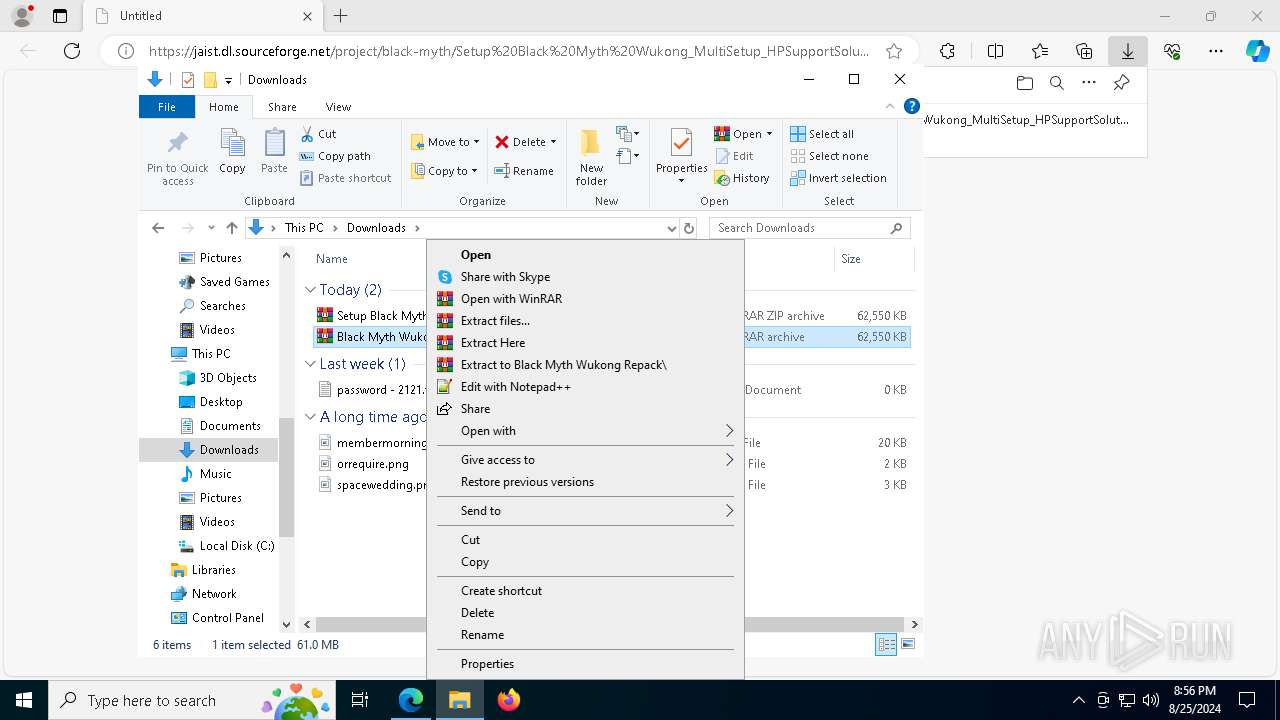
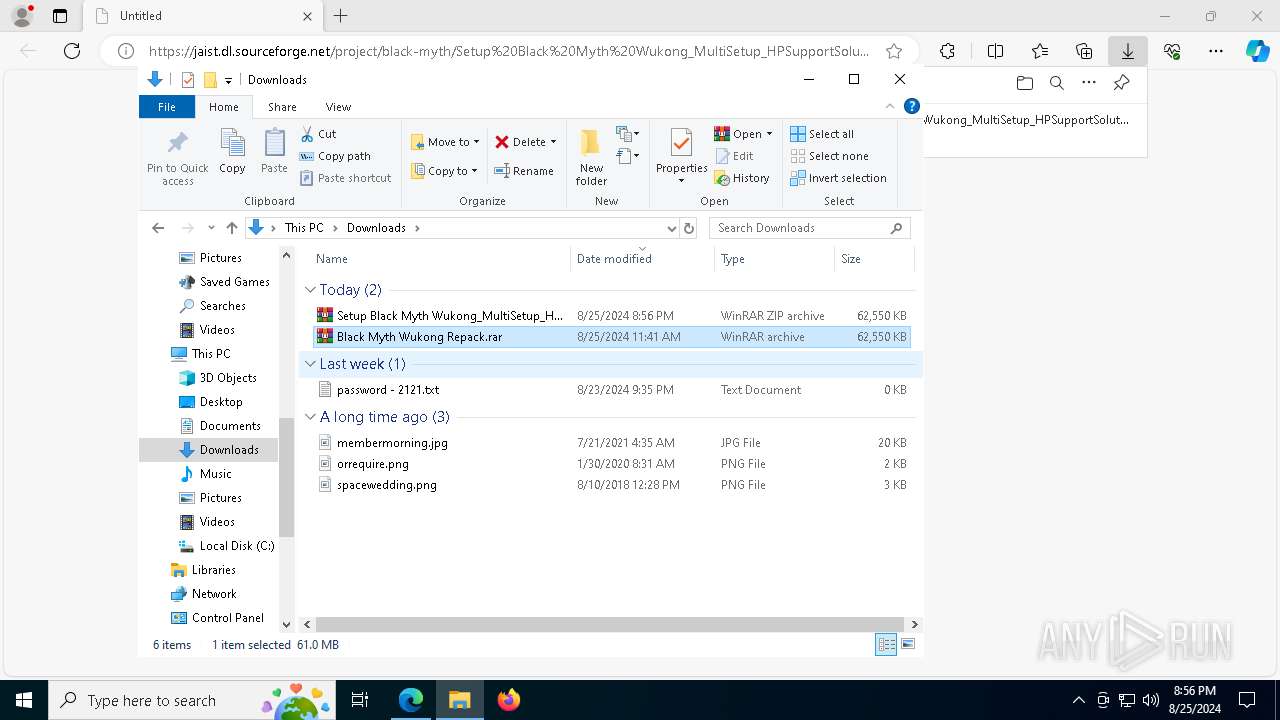
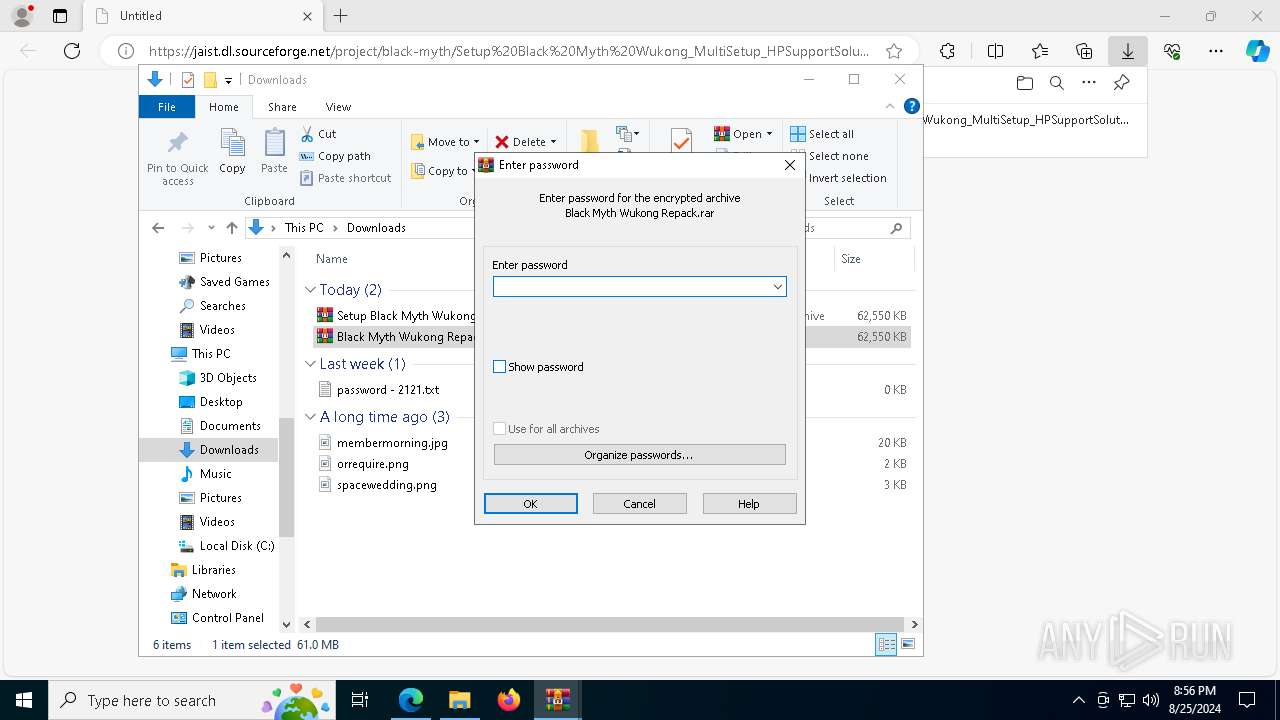
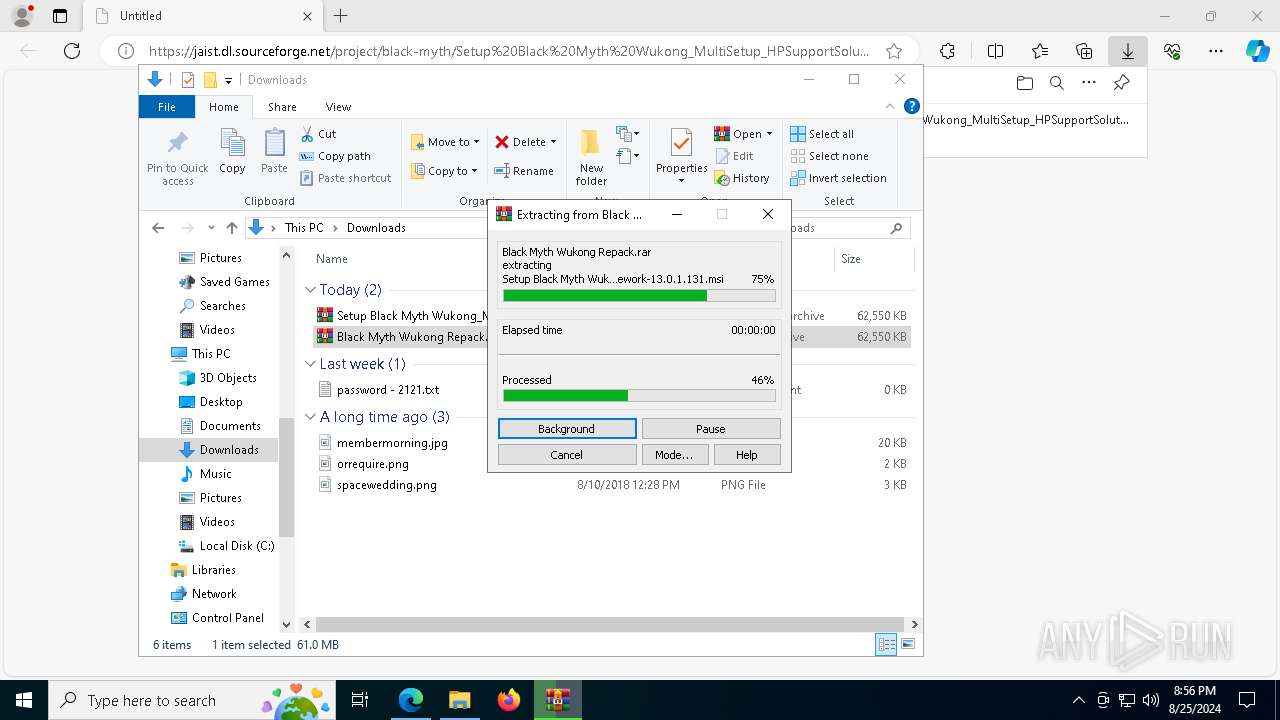
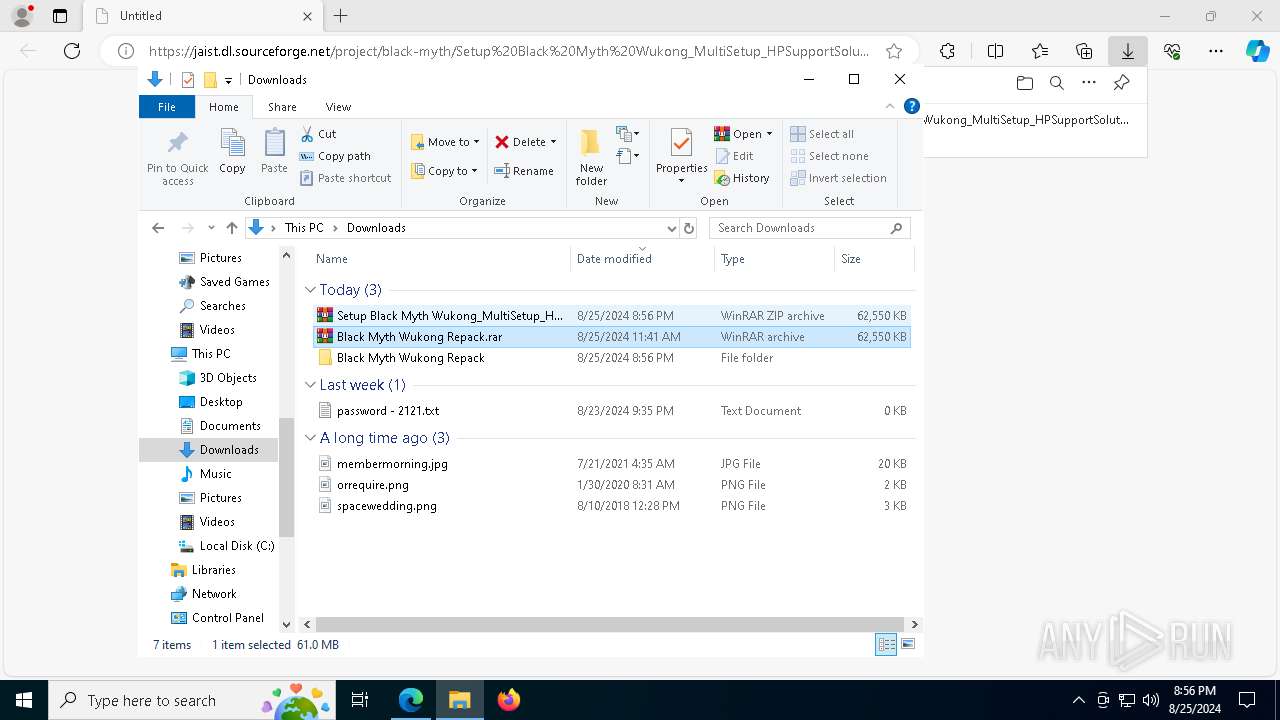
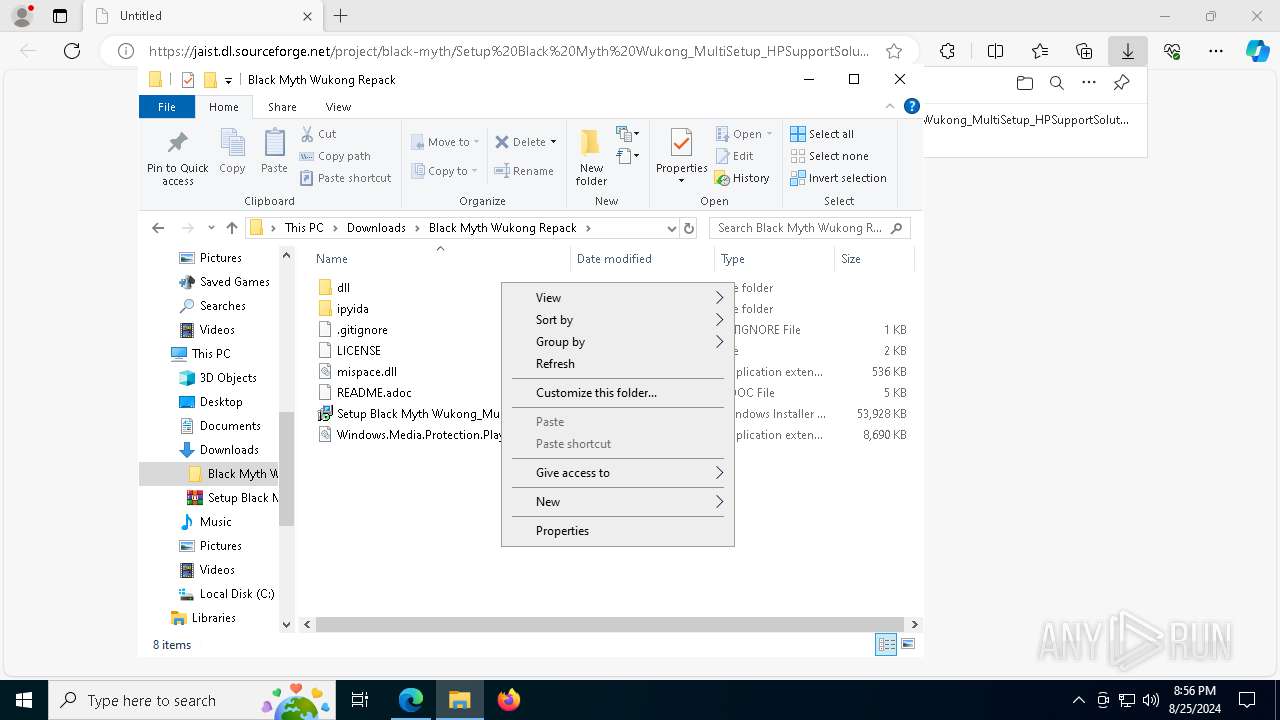
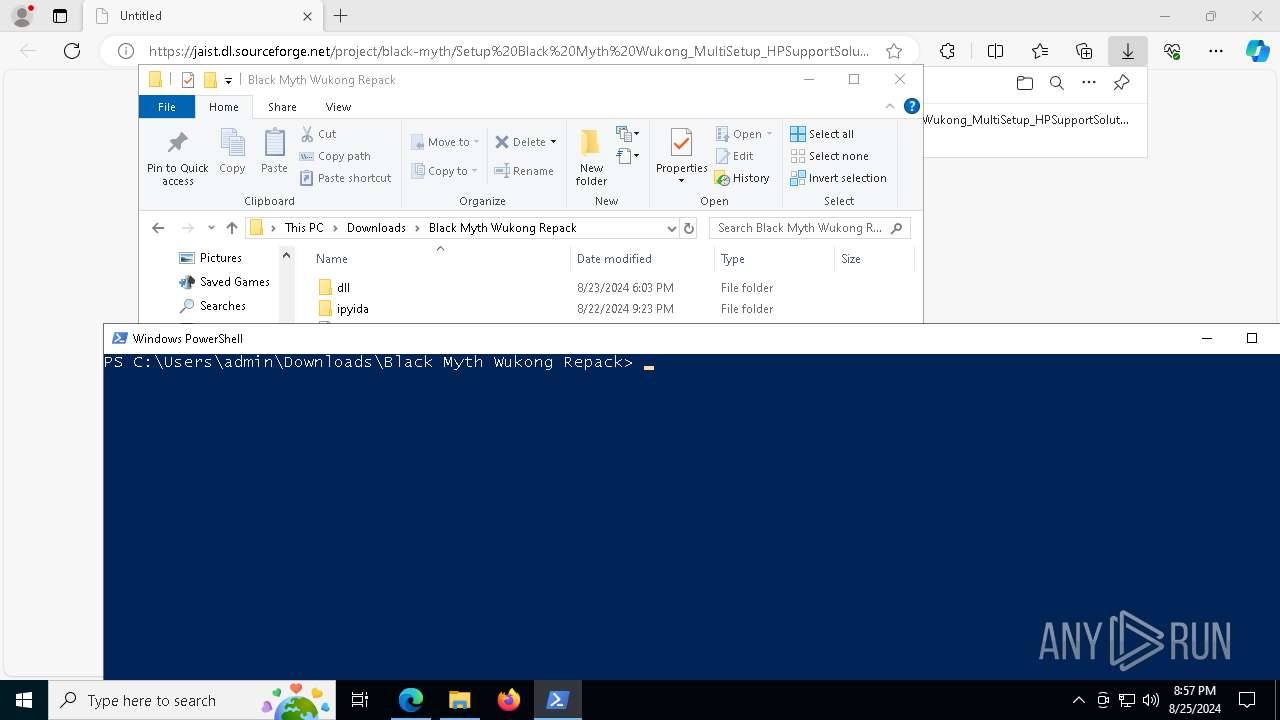
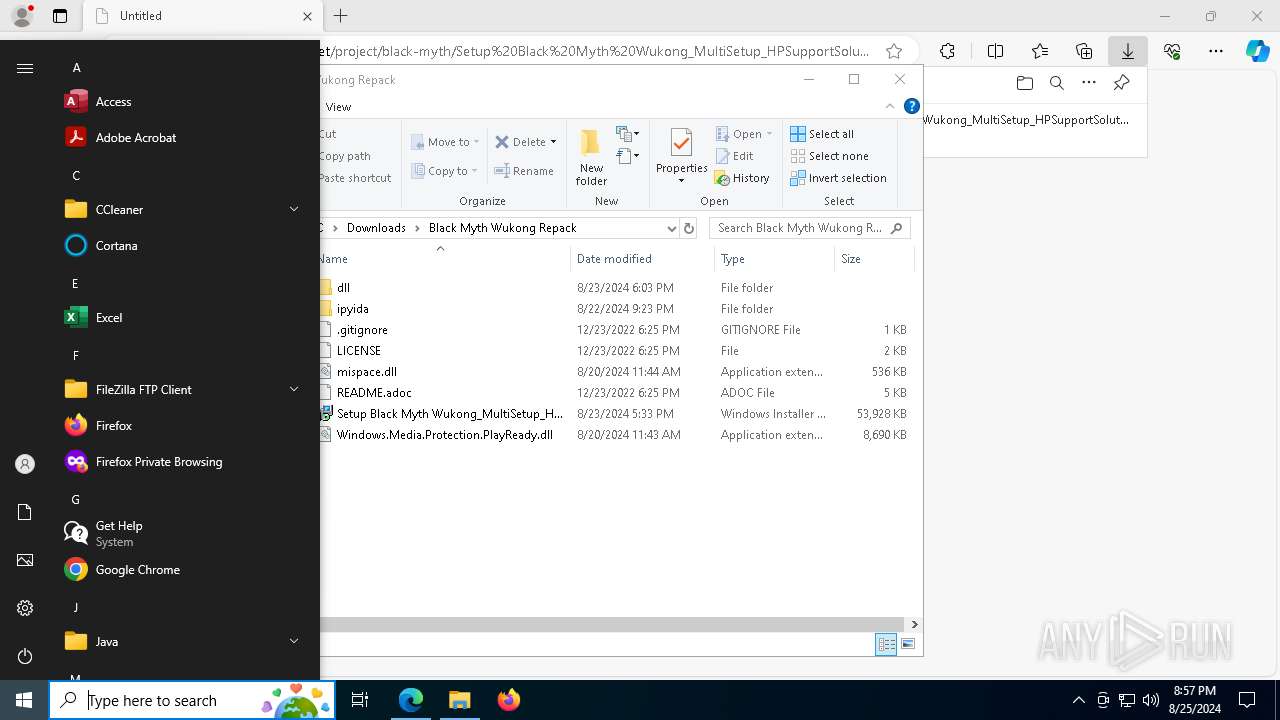
Manual execution by a user
- WinRAR.exe (PID: 5044)
- WinRAR.exe (PID: 8144)
- powershell.exe (PID: 6372)
- cmd.exe (PID: 4048)
- msiexec.exe (PID: 5508)
Reads the computer name
- identity_helper.exe (PID: 7316)
- msiexec.exe (PID: 7060)
- msiexec.exe (PID: 2876)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- msiexec.exe (PID: 6516)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- msiexec.exe (PID: 7600)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6372)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2876)
- expand.exe (PID: 7396)
- msiexec.exe (PID: 6516)
- expand.exe (PID: 508)
- msiexec.exe (PID: 7600)
- expand.exe (PID: 7864)
Create files in a temporary directory
- msiexec.exe (PID: 2876)
- expand.exe (PID: 7396)
- msiexec.exe (PID: 6516)
- expand.exe (PID: 508)
- msiexec.exe (PID: 7600)
- expand.exe (PID: 7864)
Process checks computer location settings
- msiexec.exe (PID: 2876)
- msiexec.exe (PID: 6516)
- msiexec.exe (PID: 7600)
Reads the software policy settings
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 8108)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 5700)
- HPSupportSolutionsFramework-13.0.1.131.exe (PID: 7700)
Creates a software uninstall entry
- msiexec.exe (PID: 7060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(5700) HPSupportSolutionsFramework-13.0.1.131.exe
C2 (9)condedqpwqm.shop
stagedchheiqwo.shop
traineiwnqo.shop
locatedblsoqp.shop
caffegclasiqwp.shop
evoliutwoqm.shop
reagoofydwqioo.shop
millyscroqwp.shop
stamppreewntnq.shop
Total processes
221
Monitored processes
83
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\WINDOWS\system32\ICACLS.EXE" "C:\Users\admin\AppData\Local\Temp\MW-67f31258-9603-41c5-96e4-7c0b9ec5f7e7\." /SETINTEGRITYLEVEL (CI)(OI)HIGH | C:\Windows\SysWOW64\icacls.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | "C:\WINDOWS\system32\EXPAND.EXE" -R files.cab -F:* files | C:\Windows\SysWOW64\expand.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: LZ Expansion Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\WINDOWS\system32\cmd.exe /c rd /s /q "C:\Users\admin\AppData\Local\Temp\MW-28c2ada6-687d-46fc-bf69-ae2b58382670\files" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1104 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5140 --field-trial-handle=2308,i,2988404027612443351,14526020082620732622,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1108 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2024 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6940 --field-trial-handle=2308,i,2988404027612443351,14526020082620732622,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2088 | "C:\WINDOWS\system32\ICACLS.EXE" "C:\Users\admin\AppData\Local\Temp\MW-e2ac503a-4bab-49a7-beac-0bb8229e2874\." /SETINTEGRITYLEVEL (CI)(OI)HIGH | C:\Windows\SysWOW64\icacls.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
50 798
Read events
50 317
Write events
438
Delete events
43
Modification events
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6548) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
26
Suspicious files
293
Text files
142
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11d994.TMP | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11d9a4.TMP | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11d9a4.TMP | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11d9a4.TMP | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11d9a4.TMP | — | |
MD5:— | SHA256:— | |||
| 6548 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
93
DNS requests
59
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8032 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/28c6f2f3-e00d-4d63-a9fd-479746481b21?P1=1725177250&P2=404&P3=2&P4=liZntPj9MsljT0yvk7prDKwTa5j%2bh9RT39eNwciHHHKkmGfX17yo46QrlhBjsd6a4601Sp6zvBbe9pstITNRwg%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2031e0a3-b9df-4382-8332-8406f15a9d48?P1=1725130429&P2=404&P3=2&P4=kuGaLDwzhoOI8pqSswBThtpUMHHr8V88h4NlqrzXY%2bfFpSLe7k2APR1dKMgQ4tgmguHxph4LIAatXglM06a0jA%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2031e0a3-b9df-4382-8332-8406f15a9d48?P1=1725130429&P2=404&P3=2&P4=kuGaLDwzhoOI8pqSswBThtpUMHHr8V88h4NlqrzXY%2bfFpSLe7k2APR1dKMgQ4tgmguHxph4LIAatXglM06a0jA%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1724992166&P2=404&P3=2&P4=UQyYT1qeiCPuKH5HnZ46o3N1BdvVFv%2f2KdRy0wXAC8vJDfZgC5hsotIxye0eaWyw7ZQmI1hbpdel7uBqlM5QnQ%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/34ab5090-f94b-4ad8-a820-46efdd30b975?P1=1724892515&P2=404&P3=2&P4=AFQycpfYH4zpyOqH6KBq4CY3TzhAS%2bPQe2dw8D1wVIvXq%2fu3UIWPsMsllrEK%2foQ4POn2L%2b7jBjdIiVvS9%2bl%2baQ%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1724992166&P2=404&P3=2&P4=UQyYT1qeiCPuKH5HnZ46o3N1BdvVFv%2f2KdRy0wXAC8vJDfZgC5hsotIxye0eaWyw7ZQmI1hbpdel7uBqlM5QnQ%3d%3d | unknown | — | — | whitelisted |
7488 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/34ab5090-f94b-4ad8-a820-46efdd30b975?P1=1724892515&P2=404&P3=2&P4=AFQycpfYH4zpyOqH6KBq4CY3TzhAS%2bPQe2dw8D1wVIvXq%2fu3UIWPsMsllrEK%2foQ4POn2L%2b7jBjdIiVvS9%2bl%2baQ%3d%3d | unknown | — | — | whitelisted |
1048 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/062b65bc-b6a4-4f5a-8413-7218292237fe?P1=1724892515&P2=404&P3=2&P4=f01JUJiucACEae1ySKtxiur8BHBDVIImB5%2f1x%2fMVQRX063u9hhEC%2fTb43gHDI%2fNylxUU6iwu7sLunKIFFm7bog%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4200 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5144 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6548 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6860 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6860 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6860 | msedge.exe | 150.65.7.130:443 | jaist.dl.sourceforge.net | Japan Advanced Institute of Science and Technology | JP | unknown |
6860 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6860 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
jaist.dl.sourceforge.net |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8108 | HPSupportSolutionsFramework-13.0.1.131.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
5700 | HPSupportSolutionsFramework-13.0.1.131.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
7700 | HPSupportSolutionsFramework-13.0.1.131.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |