| File name: | v1.rar |
| Full analysis: | https://app.any.run/tasks/49ad223c-ed58-4e09-8b30-5ddaabb8031a |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | June 12, 2019, 06:26:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7E5E0F995E99430B6869D3B203EAACA9 |
| SHA1: | 66BDA2B87AB3C3882D1B68000CAE1063B99258B3 |
| SHA256: | 4458F344DBEA60736789CCACF4F04C72AFBECE1E9047253405C4639AA122B859 |
| SSDEEP: | 24576:gKC7FAdtmGC9vSyxUFeu0TDKNOjrirTGdW:FkA3mGC9F+0TDKNOjEP |
MALICIOUS
Application was dropped or rewritten from another process
- v3.exe (PID: 2712)
- 顾成城家.exe (PID: 1204)
- Skype.exe (PID: 1152)
- Skype.exe (PID: 3312)
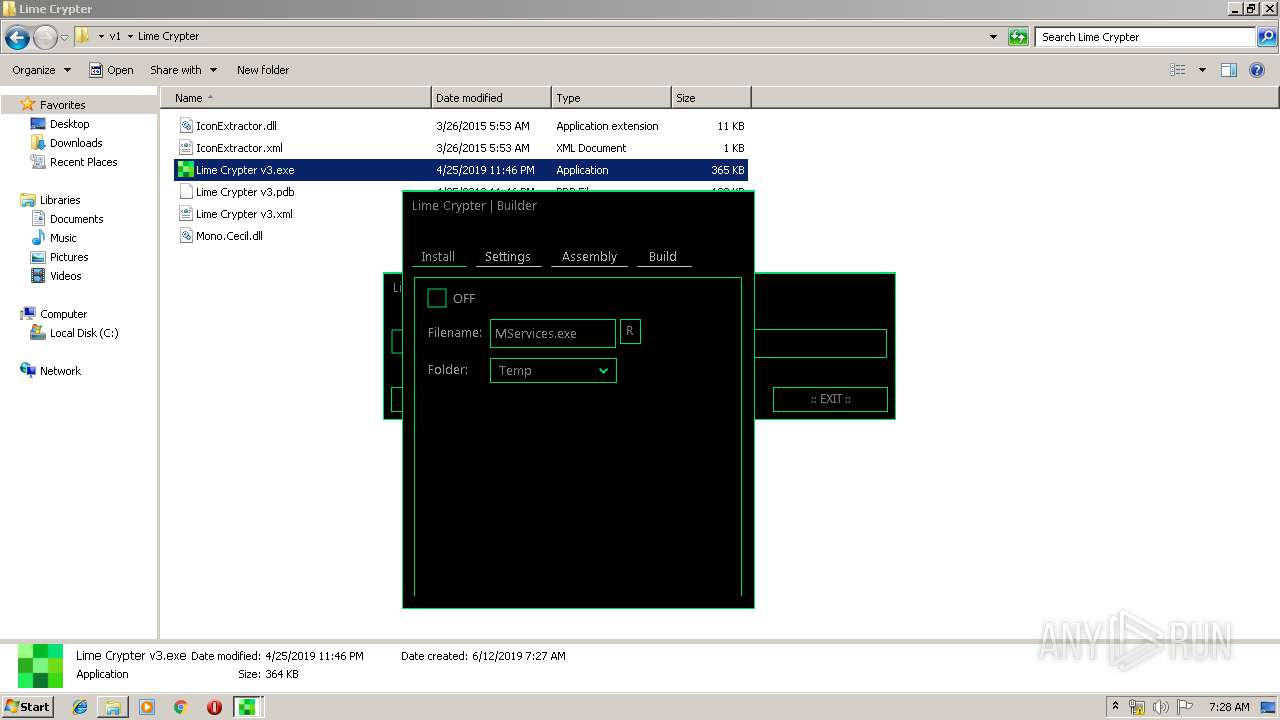
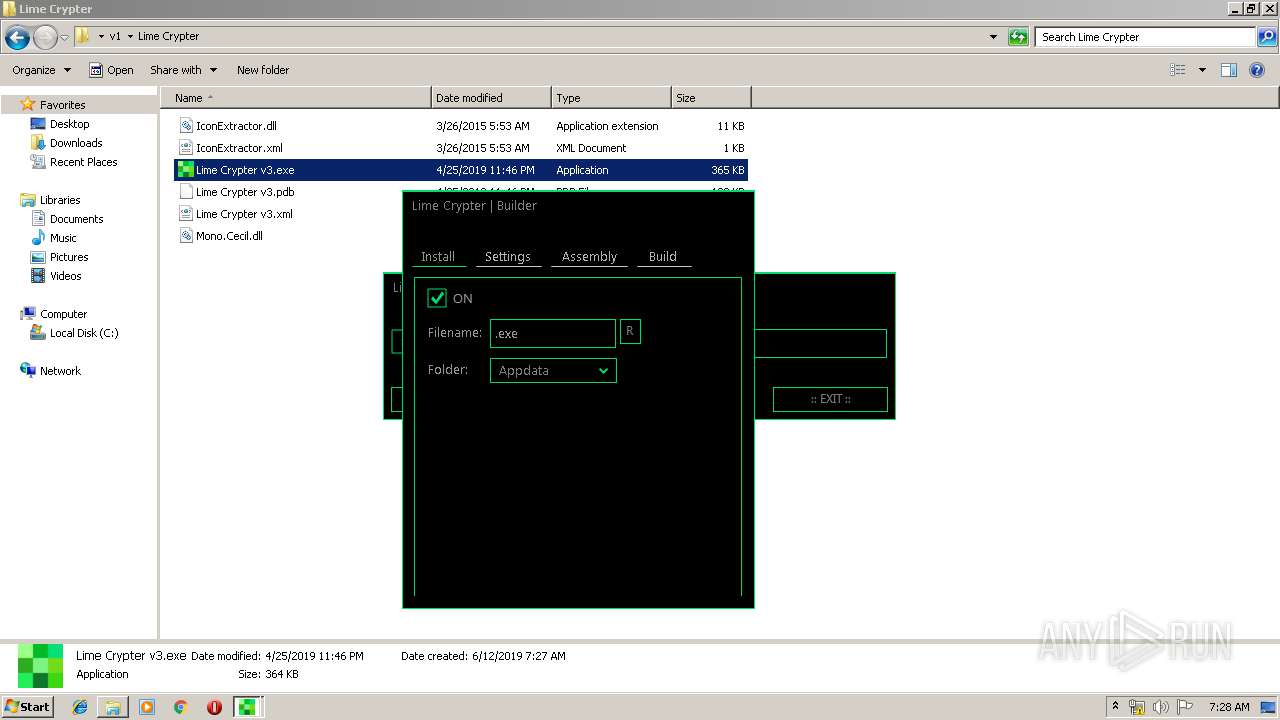
Changes the autorun value in the registry
- v3.exe (PID: 2712)
Orcus was detected
- Regasm.exe (PID: 3520)
Loads the Task Scheduler COM API
- Regasm.exe (PID: 3520)
Orcus RAT was detected
- Skype.exe (PID: 1152)
SUSPICIOUS
Executable content was dropped or overwritten
- vbc.exe (PID: 2572)
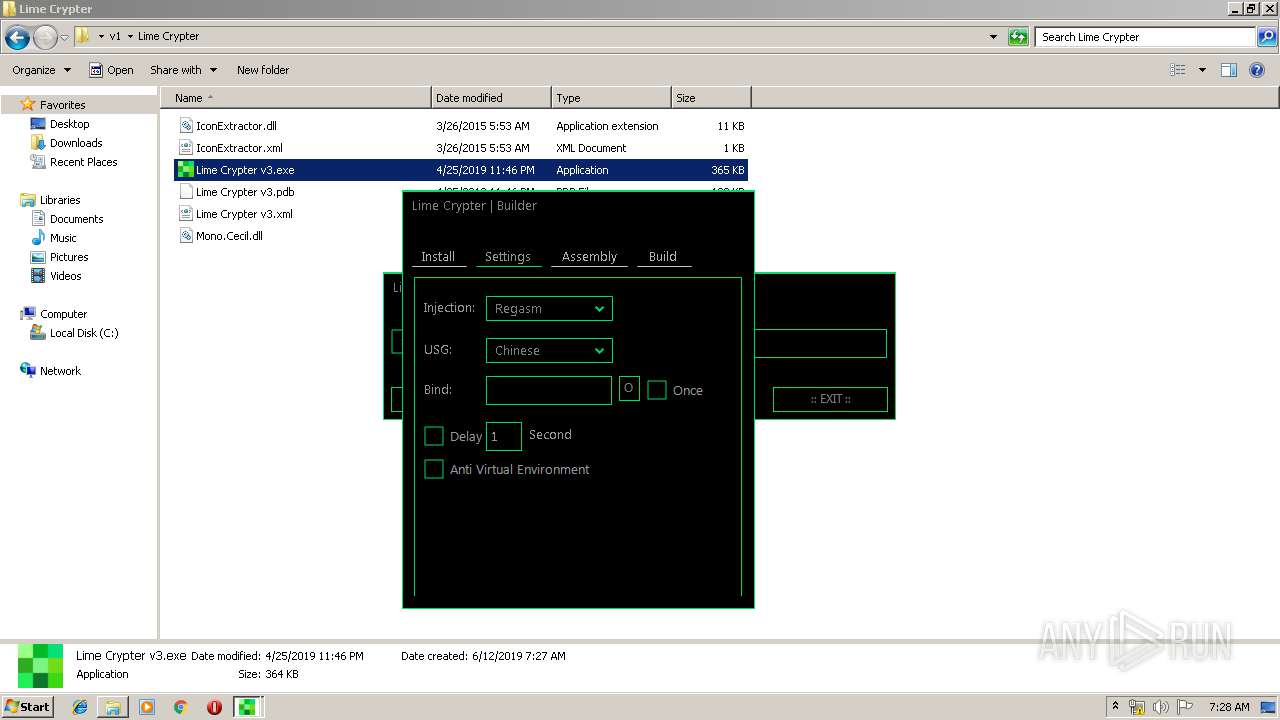
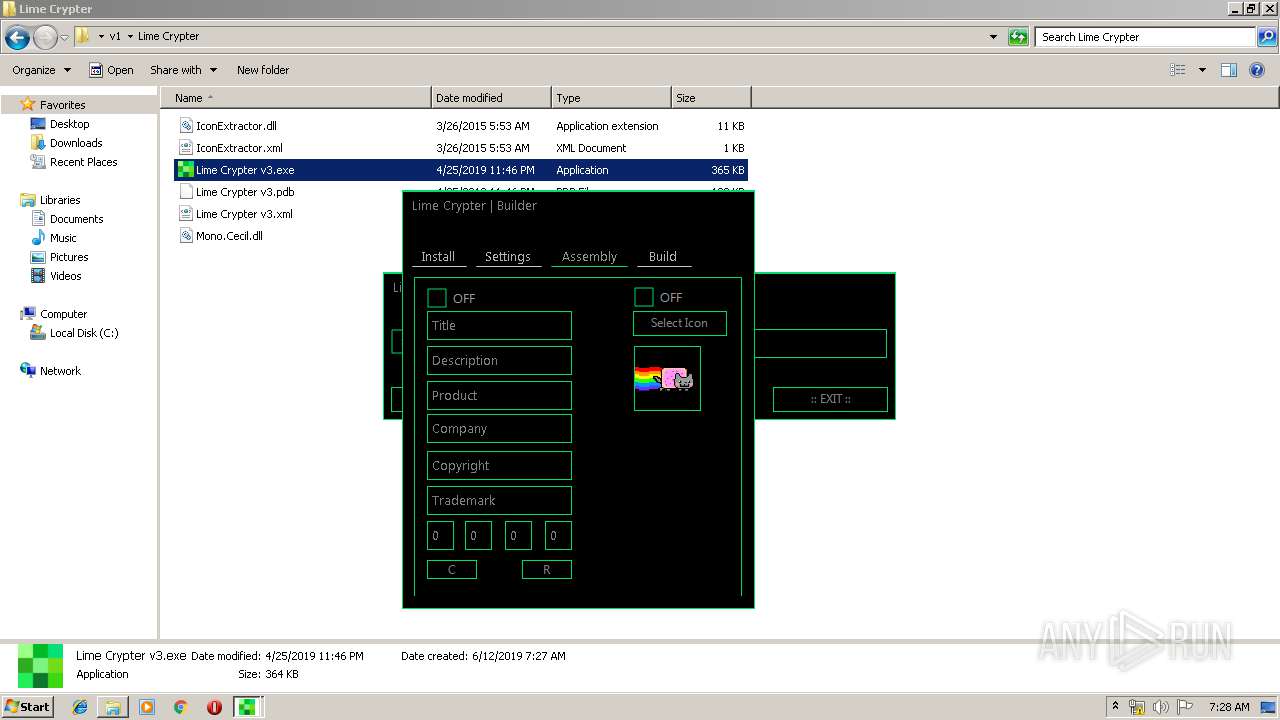
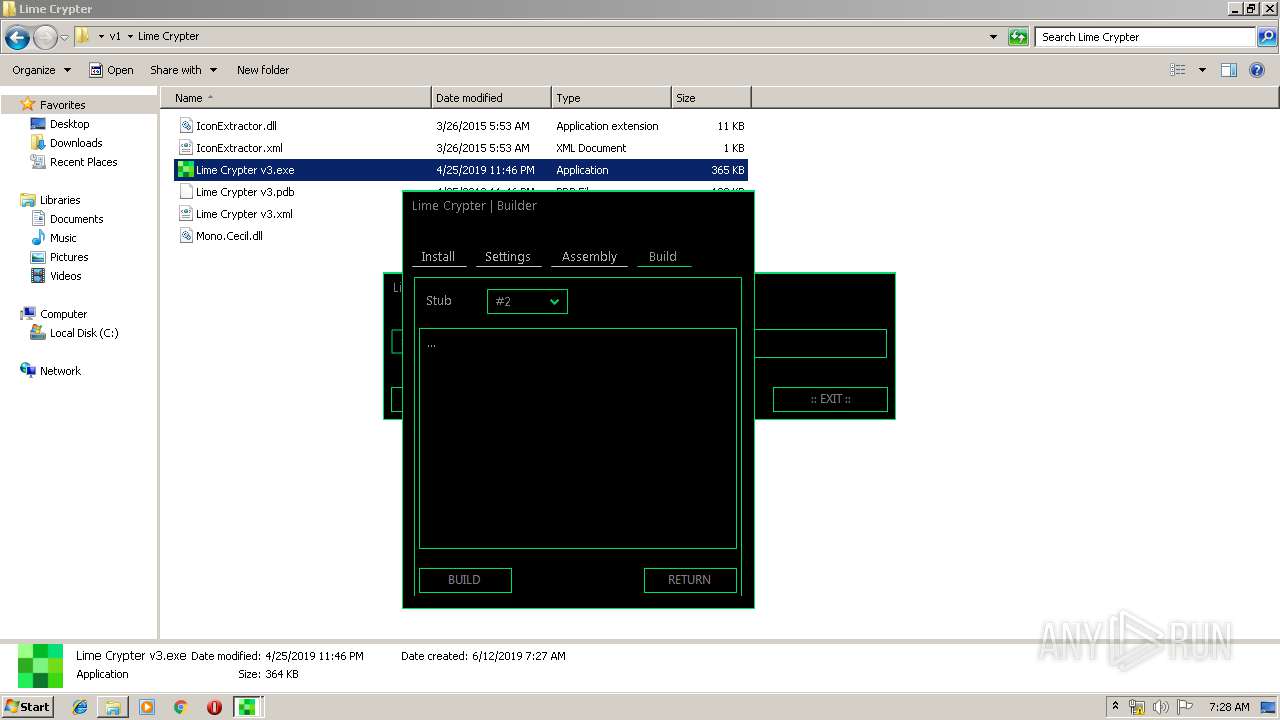
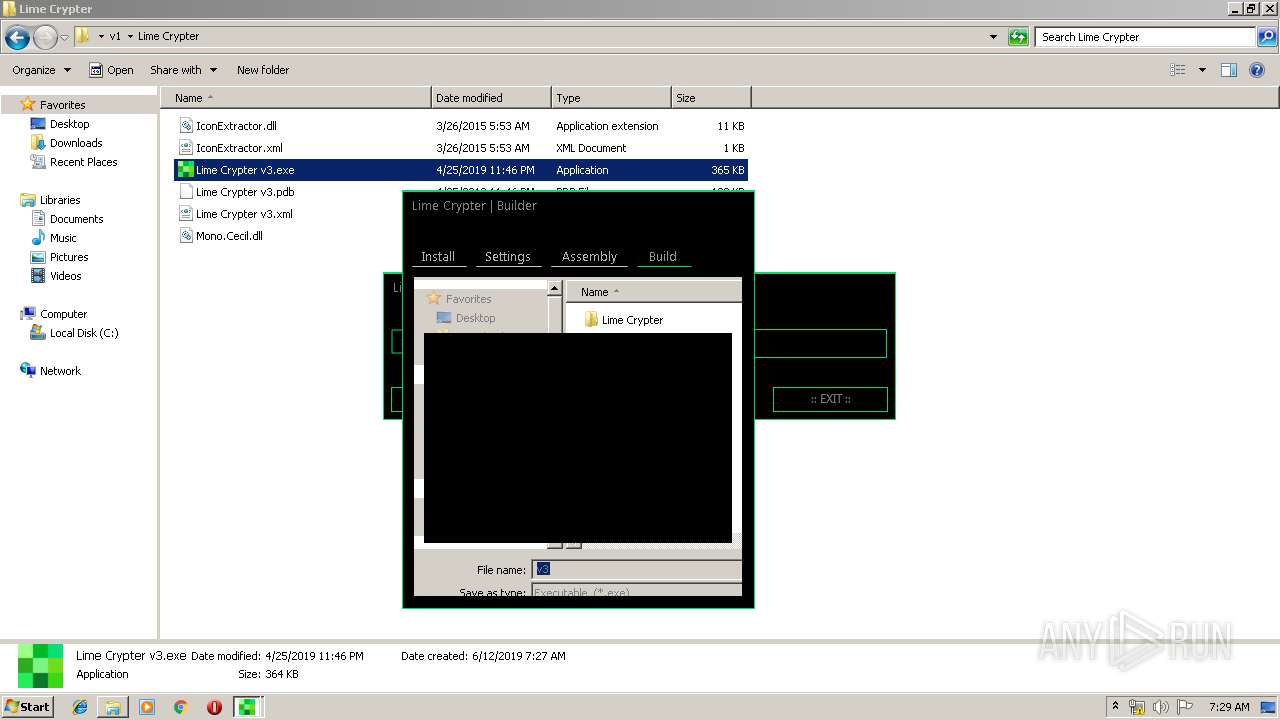
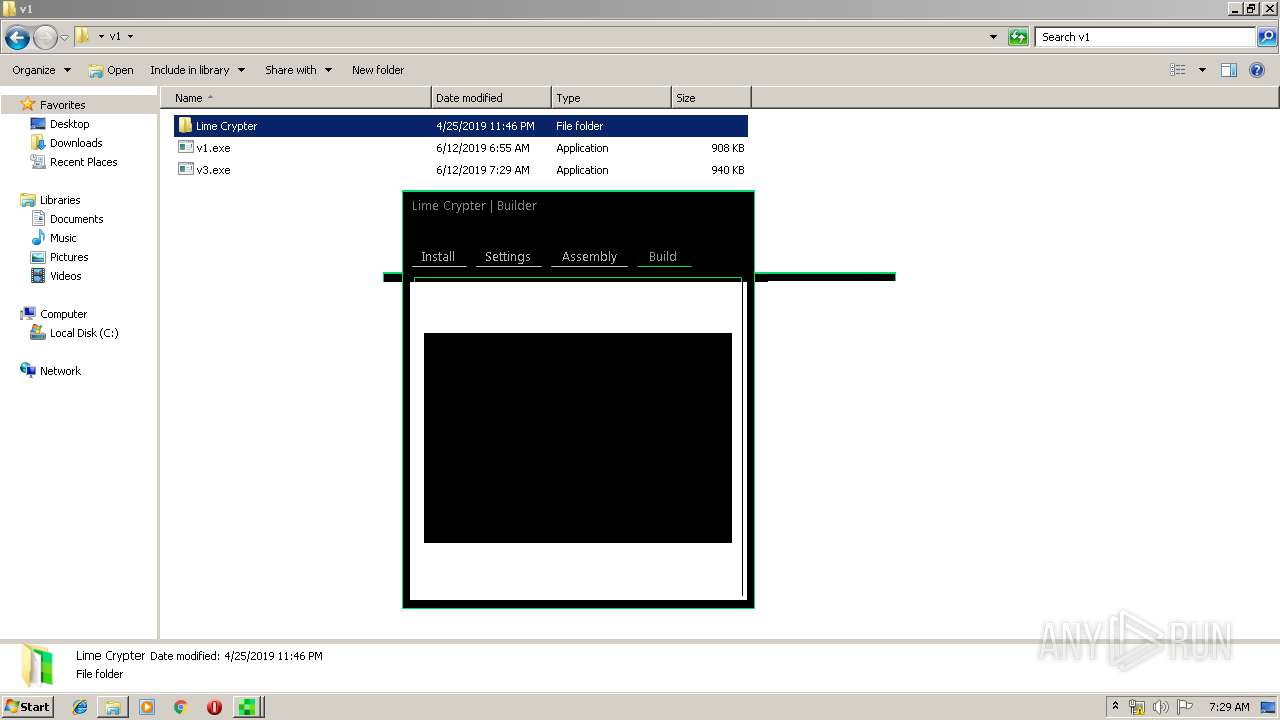
- Lime Crypter v3.exe (PID: 2836)
- v3.exe (PID: 2712)
- Regasm.exe (PID: 3520)
Executes scripts
- Lime Crypter v3.exe (PID: 2836)
Creates files in the user directory
- v3.exe (PID: 2712)
- Regasm.exe (PID: 3520)
Starts itself from another location
- v3.exe (PID: 2712)
Executed via Task Scheduler
- Regasm.exe (PID: 996)
Application launched itself
- Skype.exe (PID: 1152)
Reads Environment values
- Regasm.exe (PID: 3520)
INFO
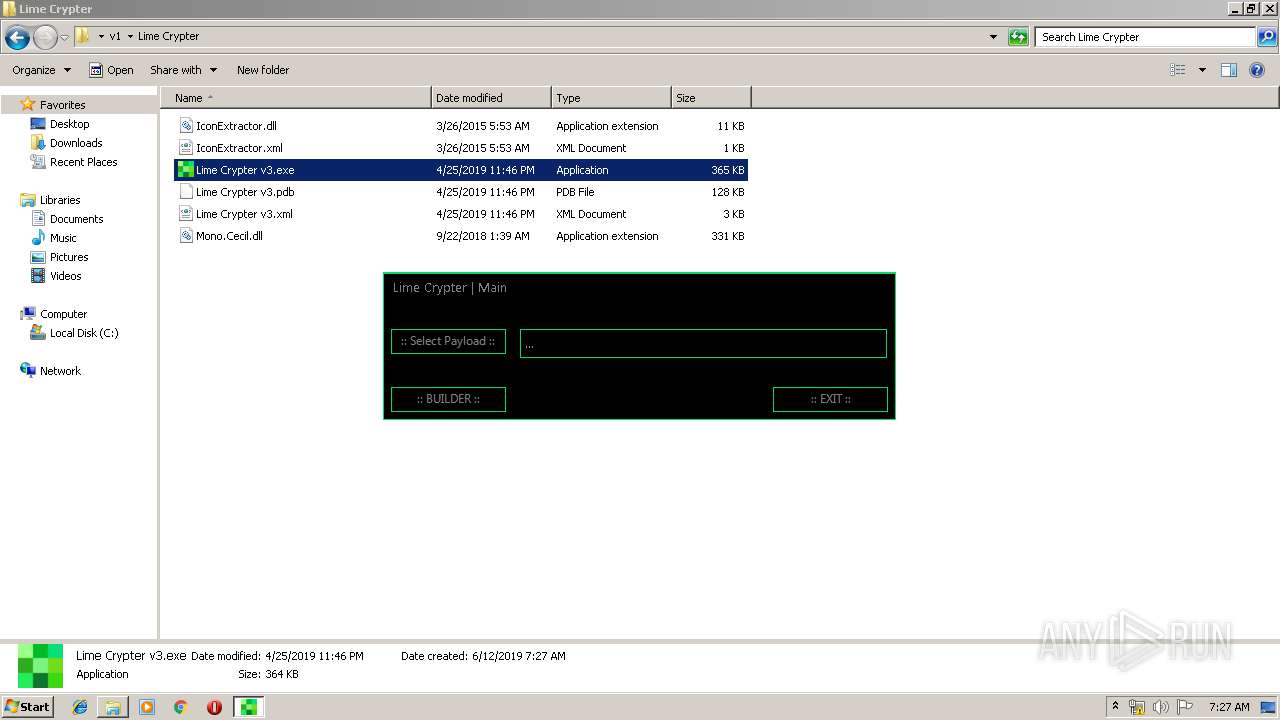
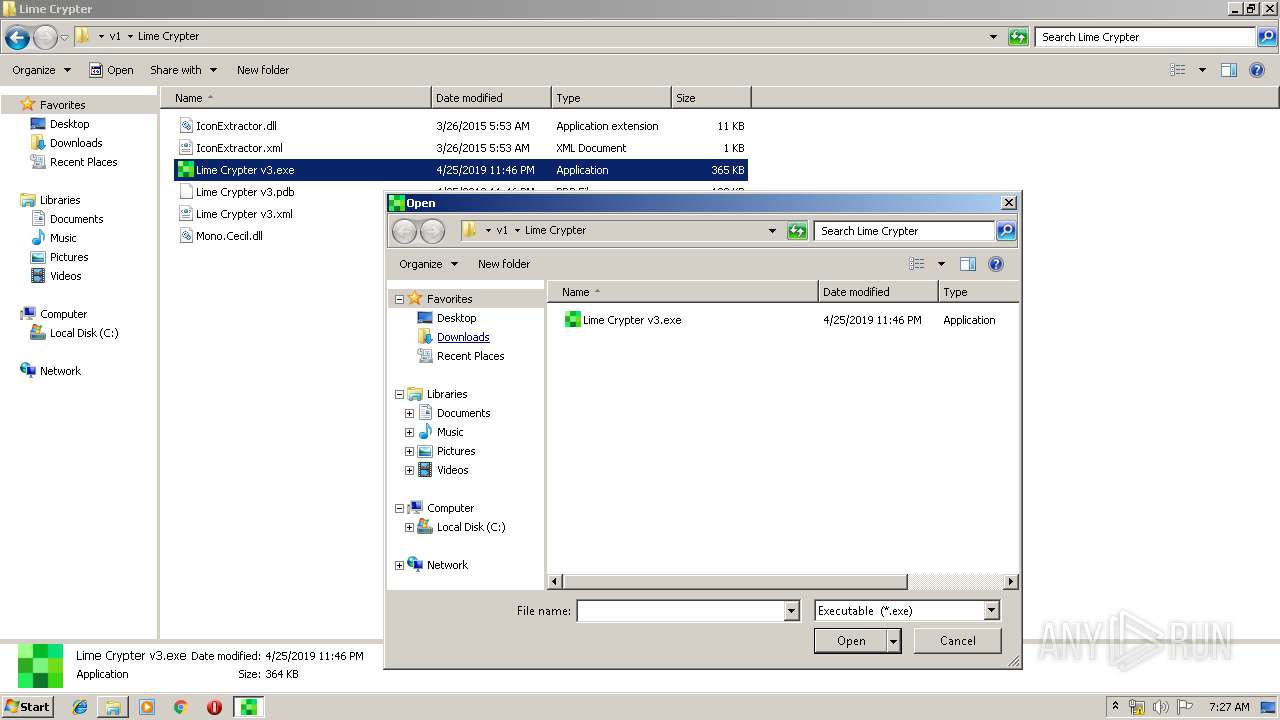
Manual execution by user
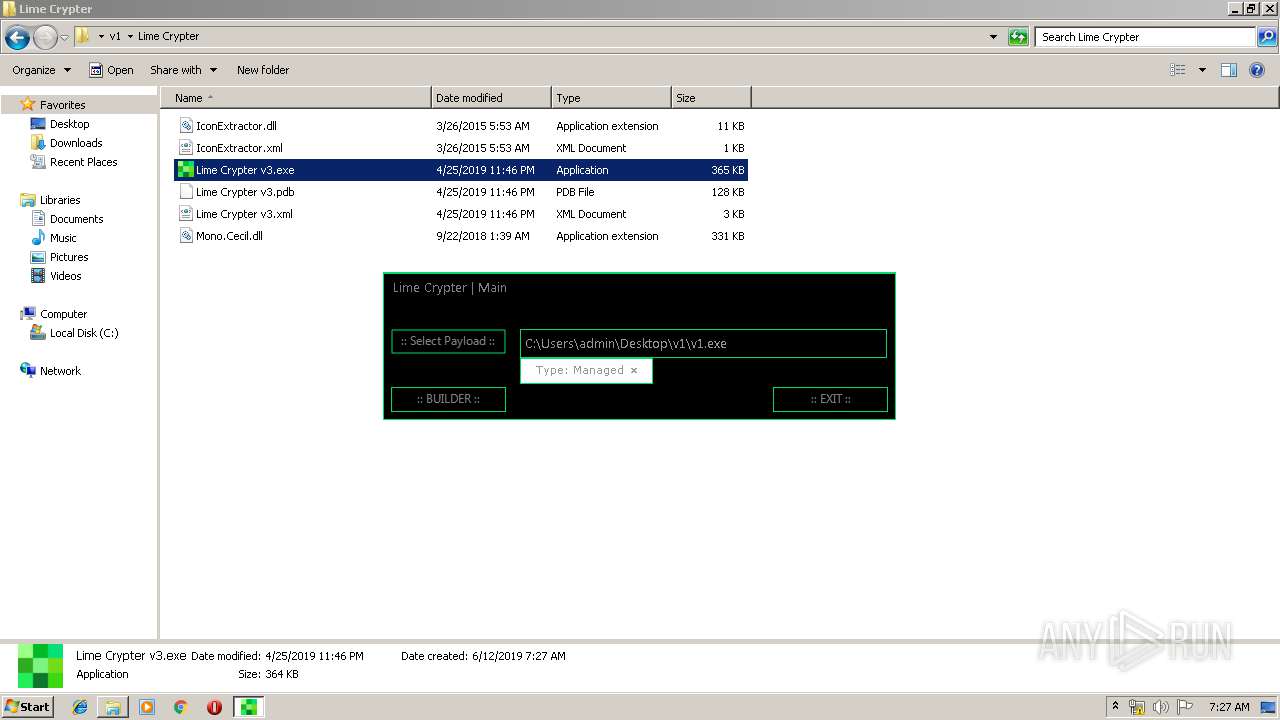
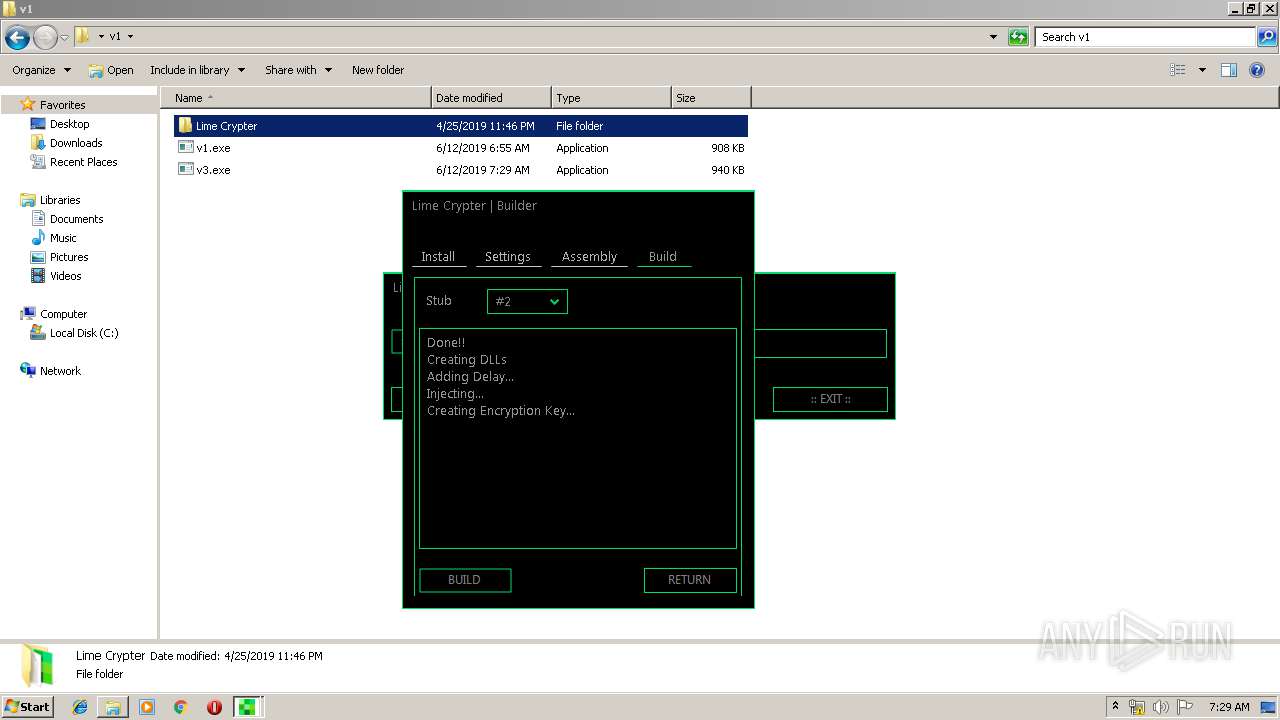
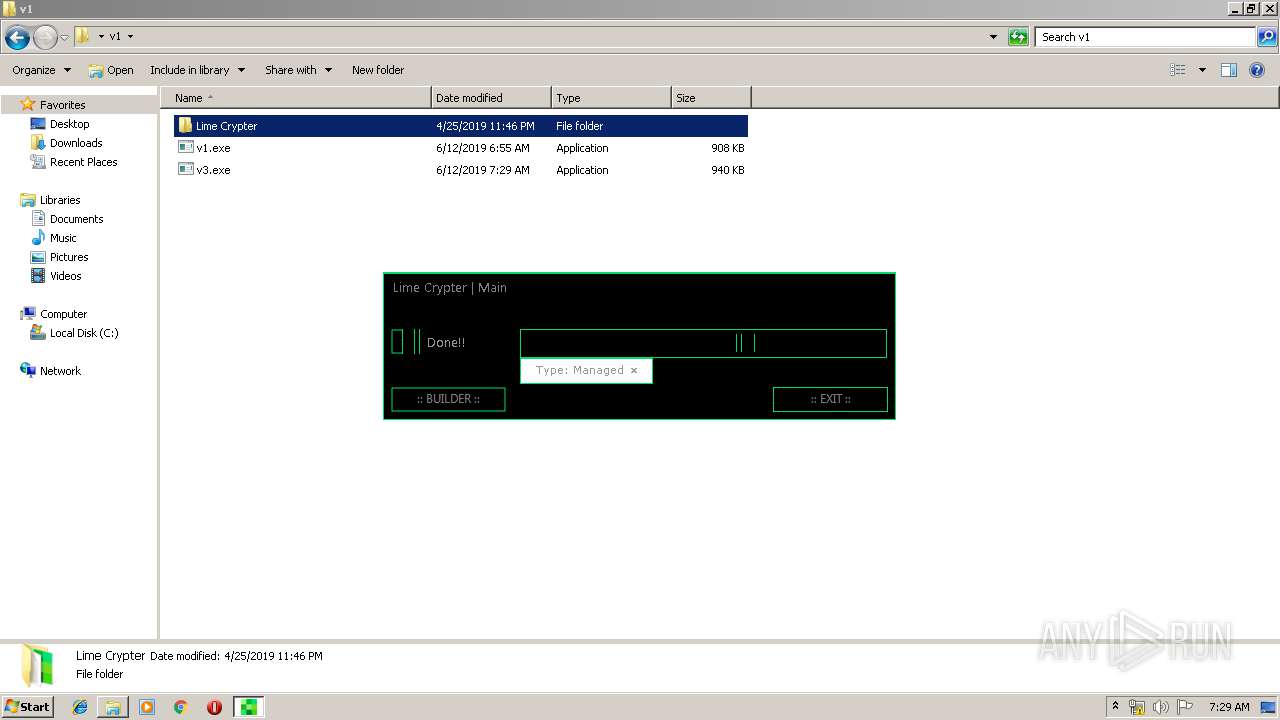
- Lime Crypter v3.exe (PID: 2836)
- v3.exe (PID: 2712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
49
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1152 | "C:\Users\admin\AppData\Roaming\Skype.exe" /launchSelfAndExit "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" 3520 /protectFile | C:\Users\admin\AppData\Roaming\Skype.exe | Regasm.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3312 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1204 | "C:\Users\admin\AppData\Roaming\顾成城家.exe" | C:\Users\admin\AppData\Roaming\顾成城家.exe | — | v3.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1516 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESBDF4.tmp" "C:\Users\admin\AppData\Local\Temp\vbc561F107E81AF4FF8B3C7F1AC8404FC3.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.52512.0 built by: VSWINSERVICING Modules
| |||||||||||||||
| 2572 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe" /noconfig @"C:\Users\admin\AppData\Local\Temp\mmfxij0x.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\vbc.exe | Lime Crypter v3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 14.0.1055.0 Modules
| |||||||||||||||
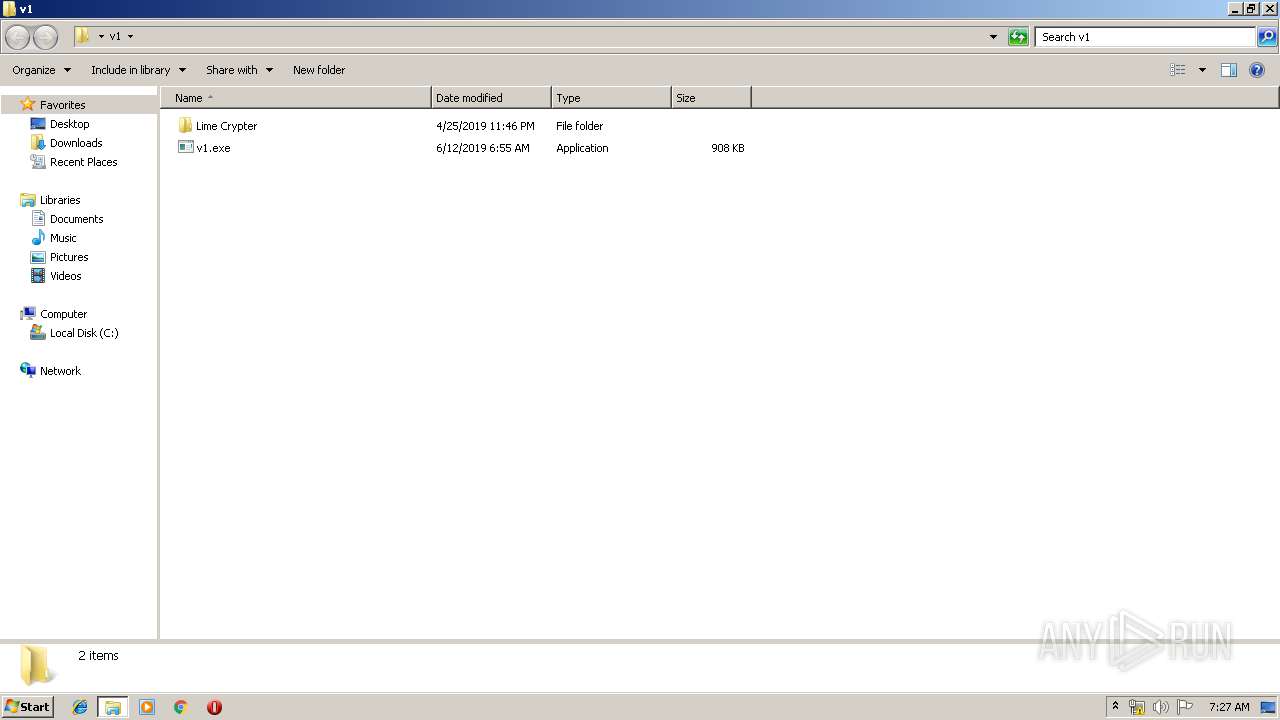
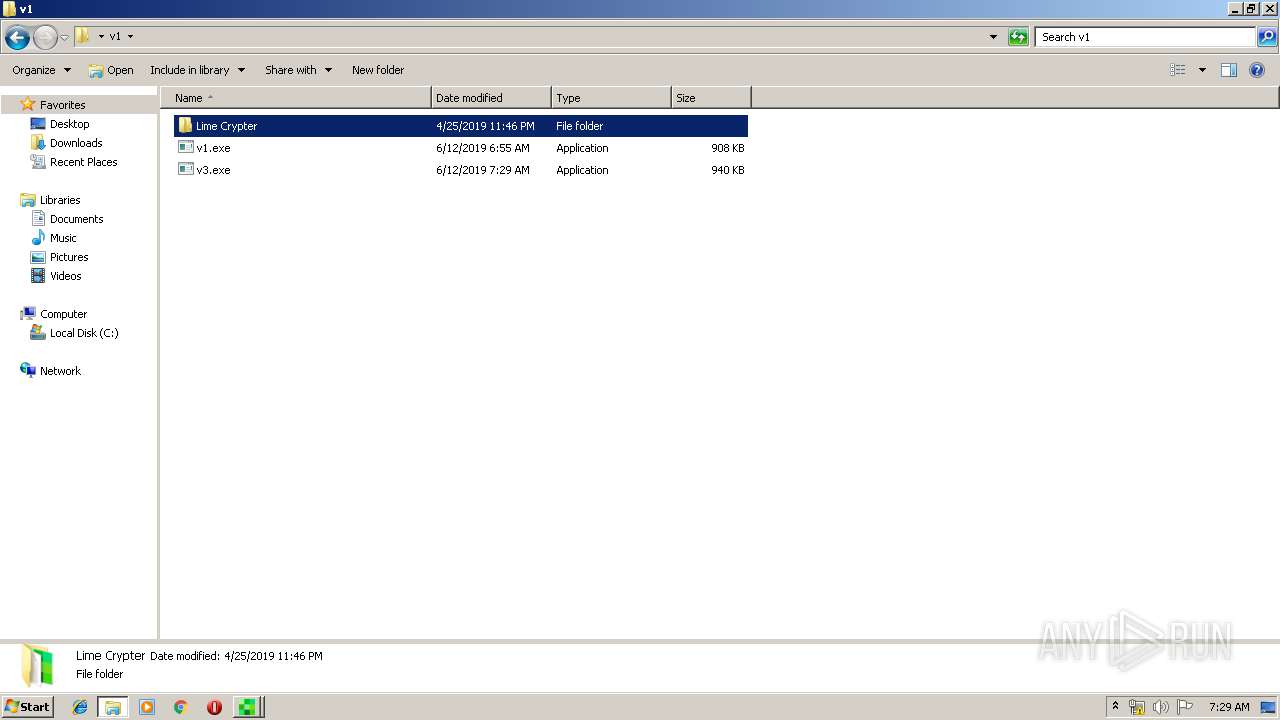
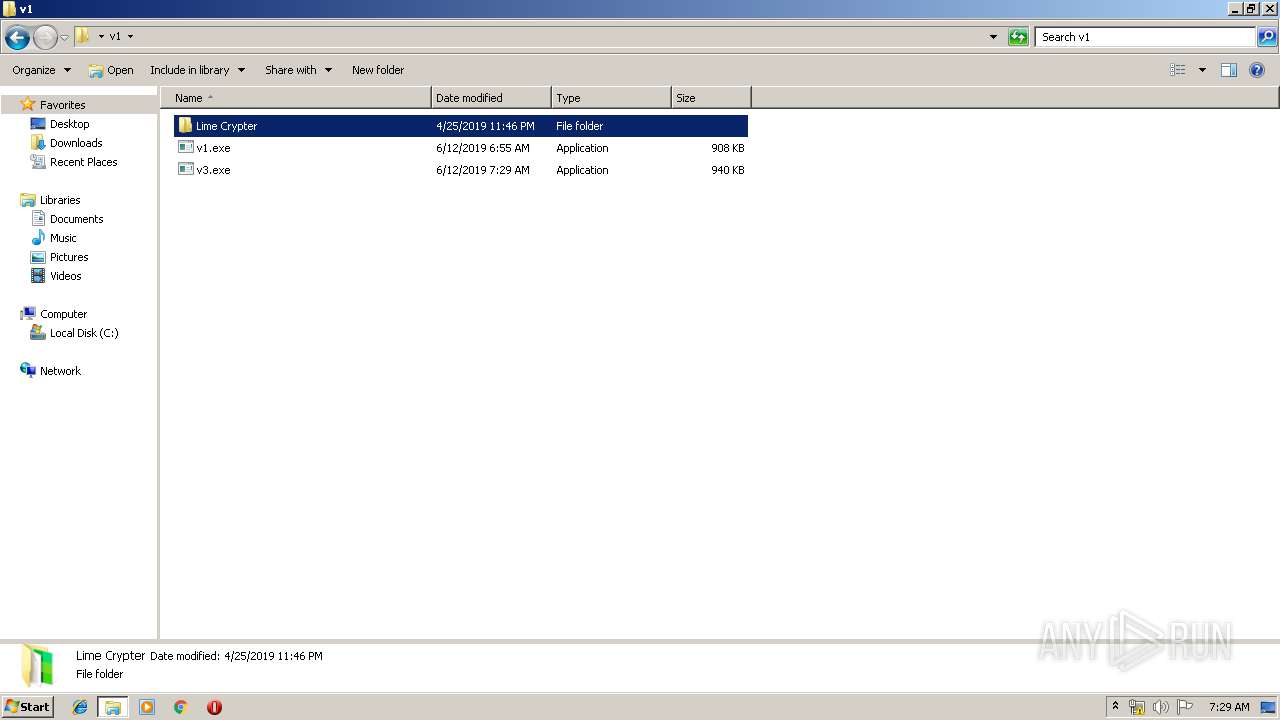
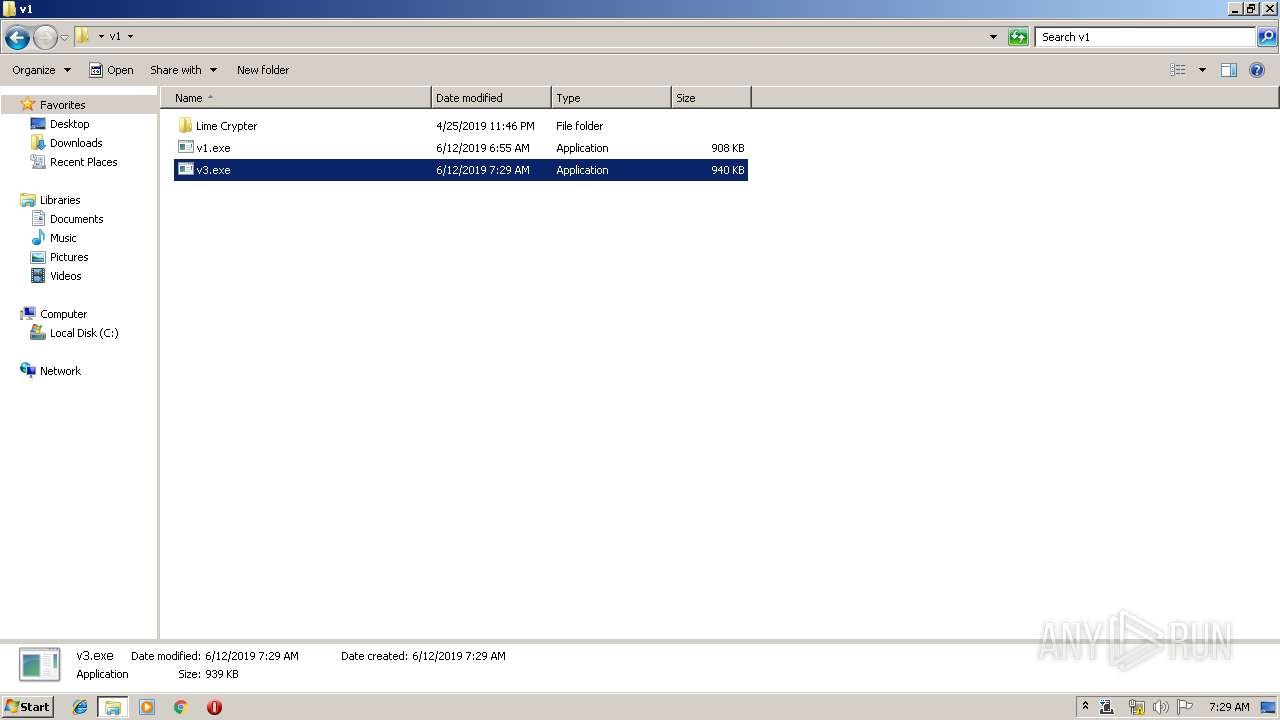
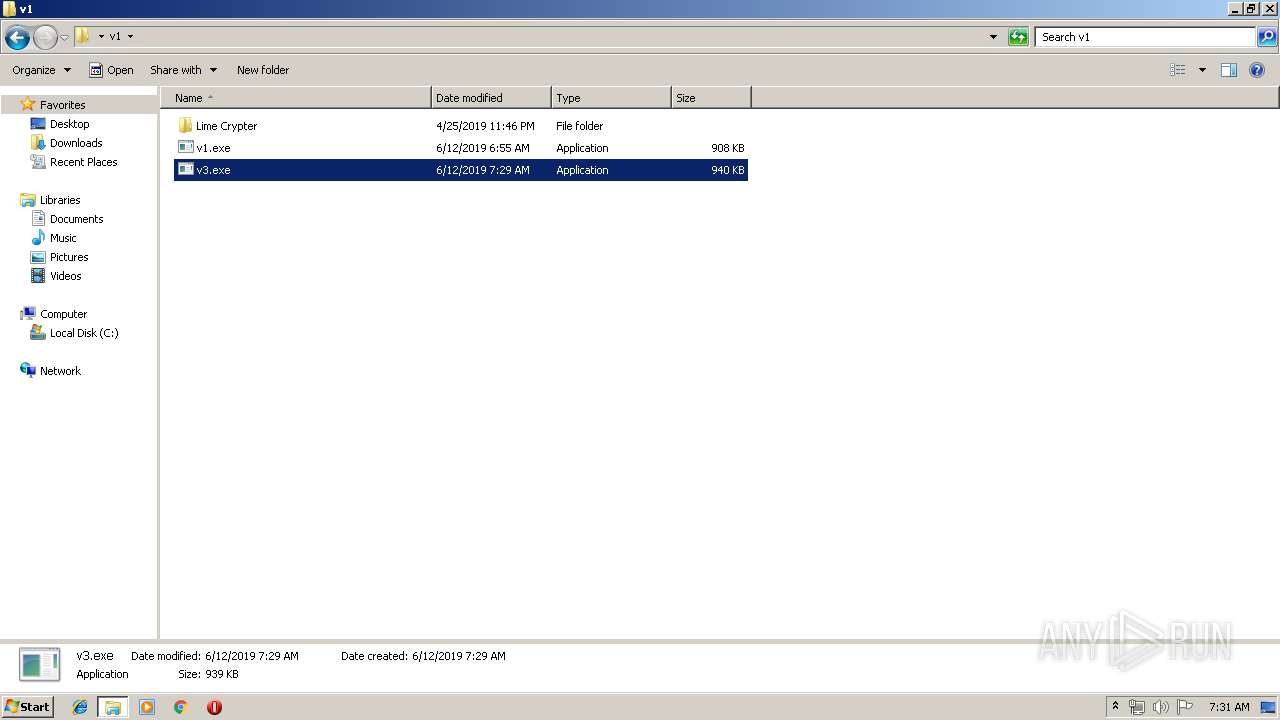
| 2712 | "C:\Users\admin\Desktop\v1\v3.exe" | C:\Users\admin\Desktop\v1\v3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
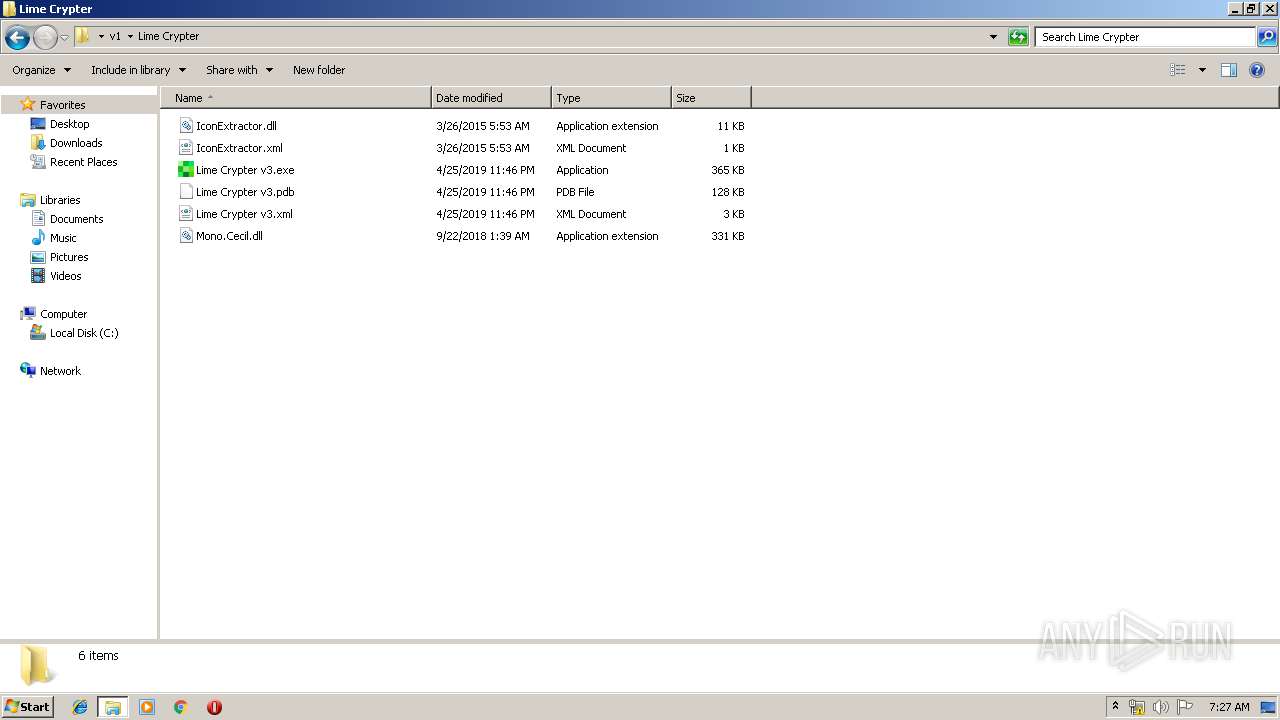
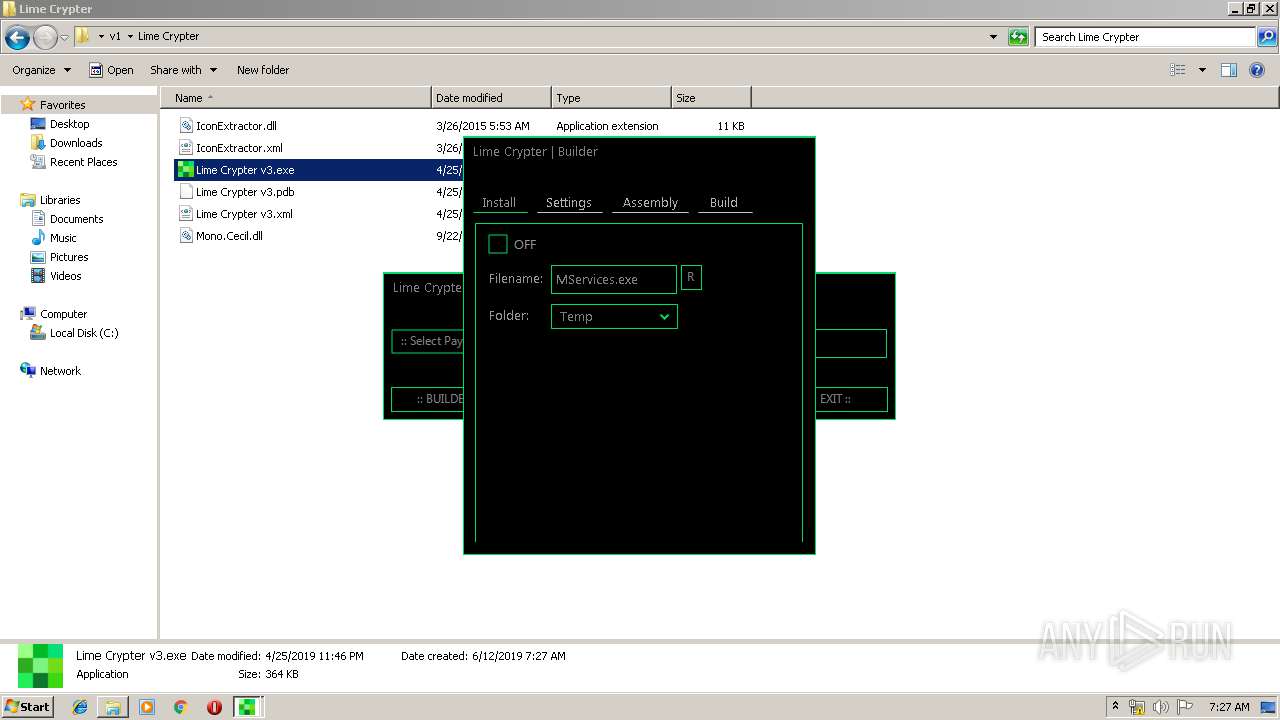
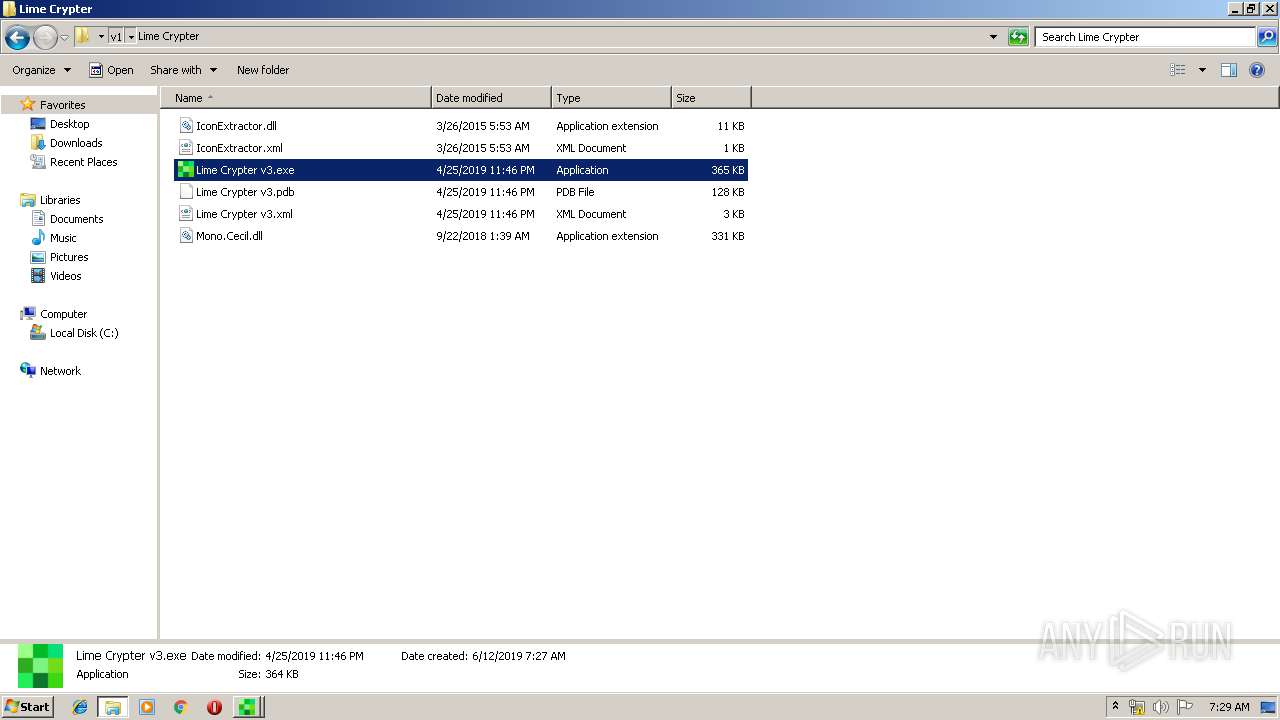
| 2836 | "C:\Users\admin\Desktop\v1\Lime Crypter\Lime Crypter v3.exe" | C:\Users\admin\Desktop\v1\Lime Crypter\Lime Crypter v3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\AppData\Roaming\Skype.exe" /watchProcess "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" 3520 "/protectFile" | C:\Users\admin\AppData\Roaming\Skype.exe | — | Skype.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
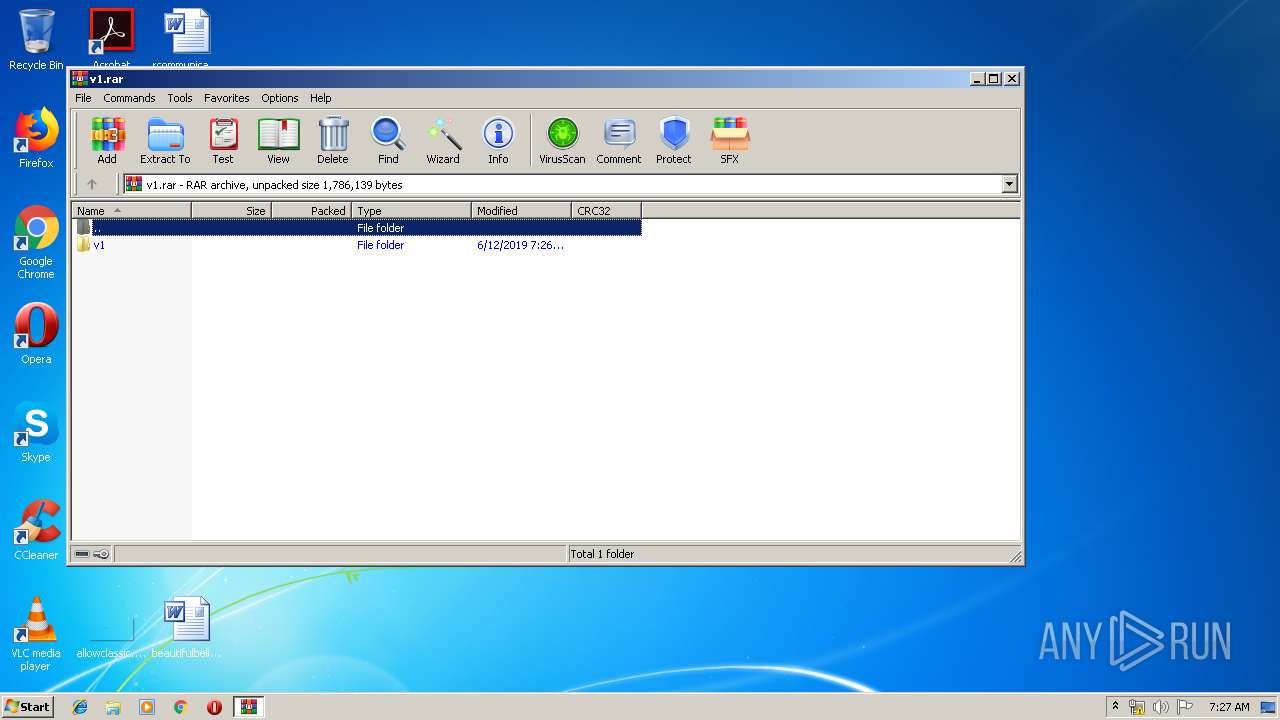
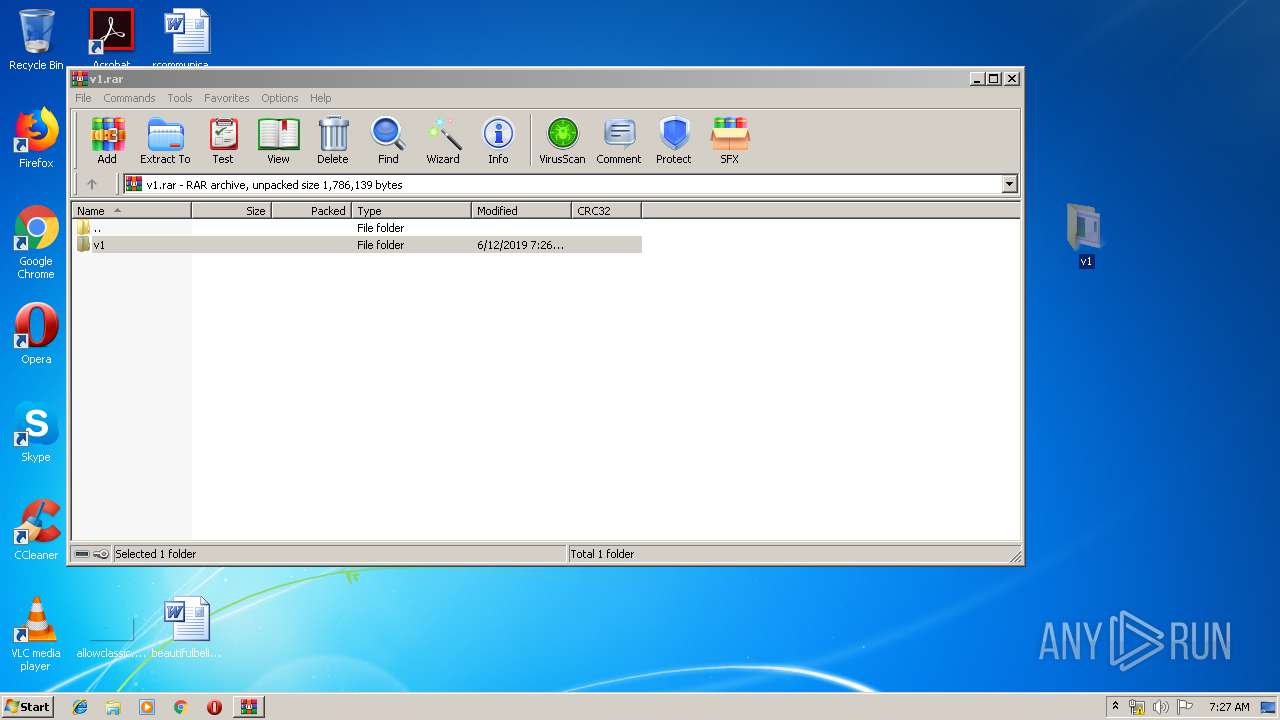
| 3464 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\v1.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3520 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\Regasm.exe | 顾成城家.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
2 240
Read events
2 097
Write events
137
Delete events
6
Modification events
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\v1.rar | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
5
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
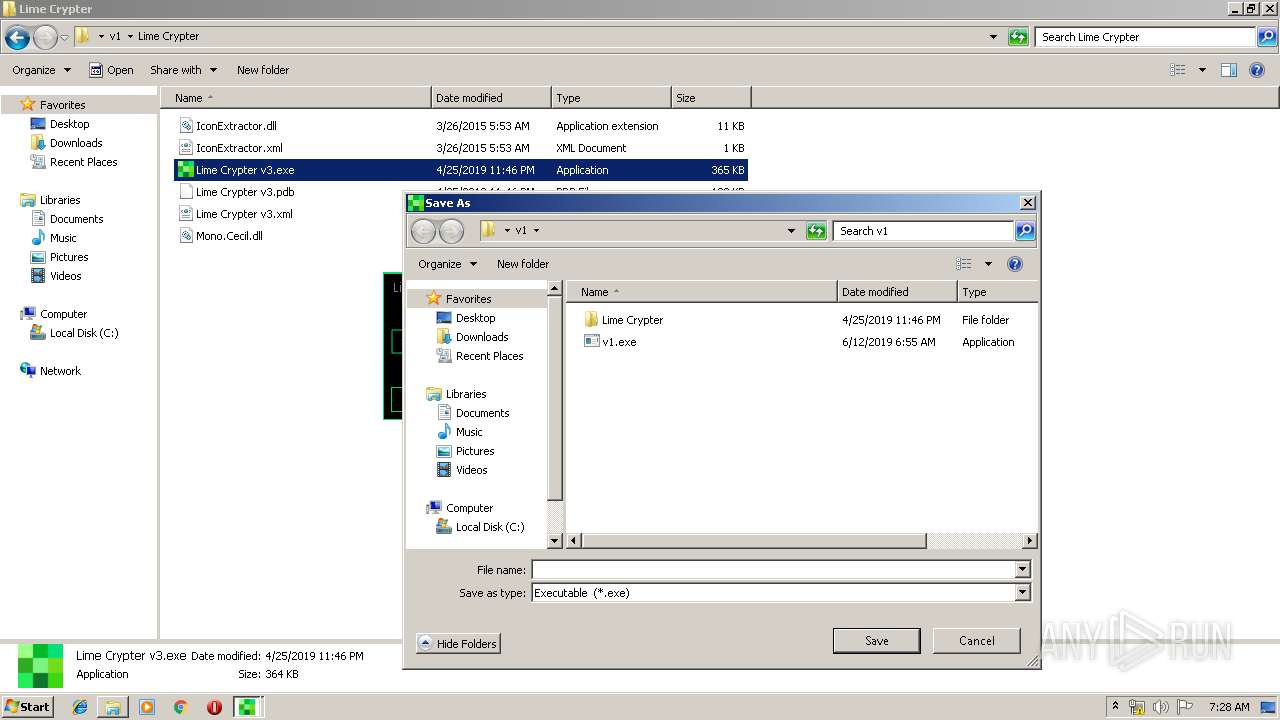
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\Lime Crypter\IconExtractor.dll | — | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\Lime Crypter\IconExtractor.xml | — | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\Lime Crypter\Lime Crypter v3.exe | — | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\Lime Crypter\Lime Crypter v3.pdb | — | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\Lime Crypter\Lime Crypter v3.xml | — | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\Lime Crypter\Mono.Cecil.dll | — | |
MD5:— | SHA256:— | |||
| 3464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3464.34989\v1\v1.exe | — | |
MD5:— | SHA256:— | |||
| 2836 | Lime Crypter v3.exe | C:\Users\admin\AppData\Local\Temp\tmpBBF0.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | vbc.exe | C:\Users\admin\AppData\Local\Temp\vbc561F107E81AF4FF8B3C7F1AC8404FC3.TMP | — | |
MD5:— | SHA256:— | |||
| 1516 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESBDF4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3520 | Regasm.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3520 | Regasm.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3520 | Regasm.exe | 199.195.250.222:9161 | — | FranTech Solutions | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3520 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
3520 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
3520 | Regasm.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) |
1 ETPRO signatures available at the full report