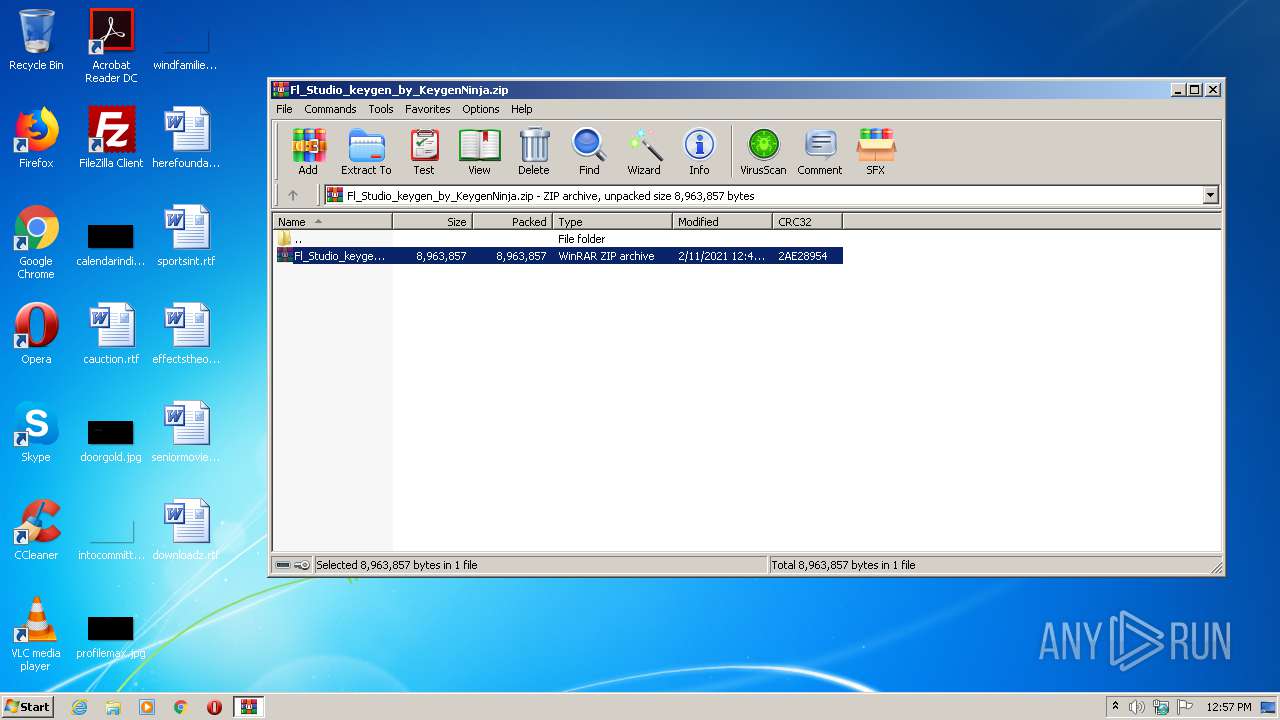
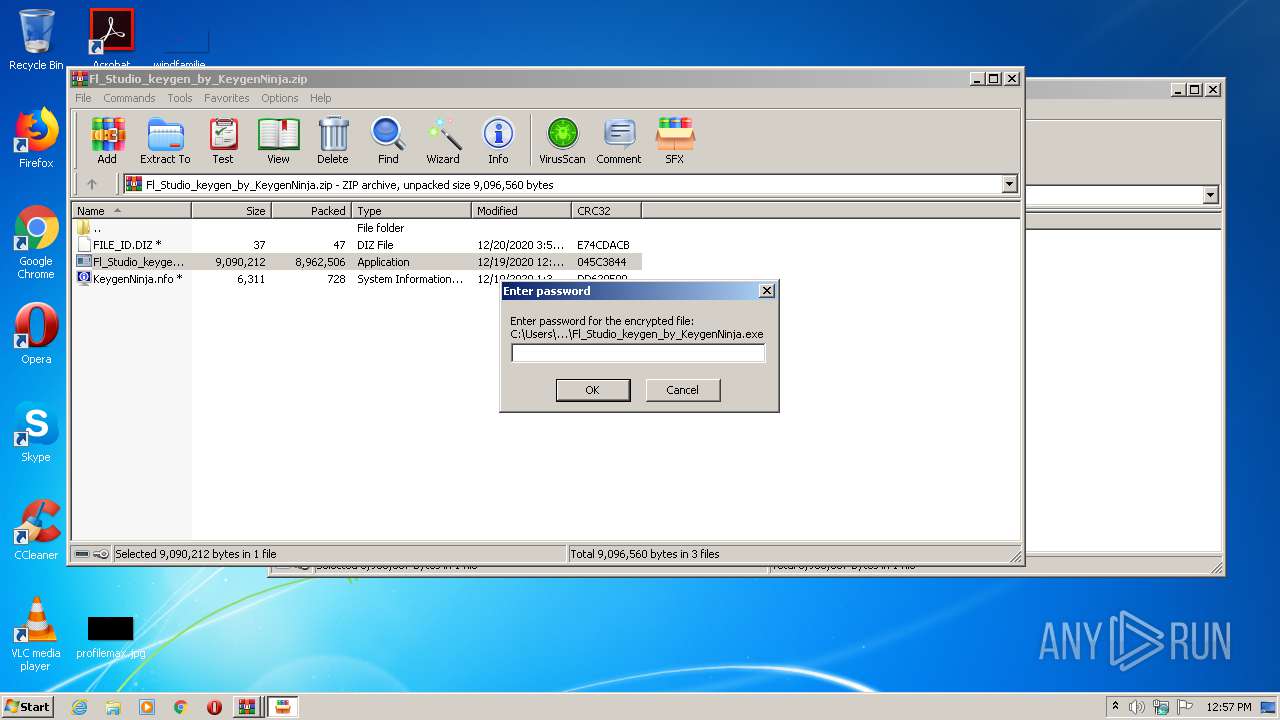
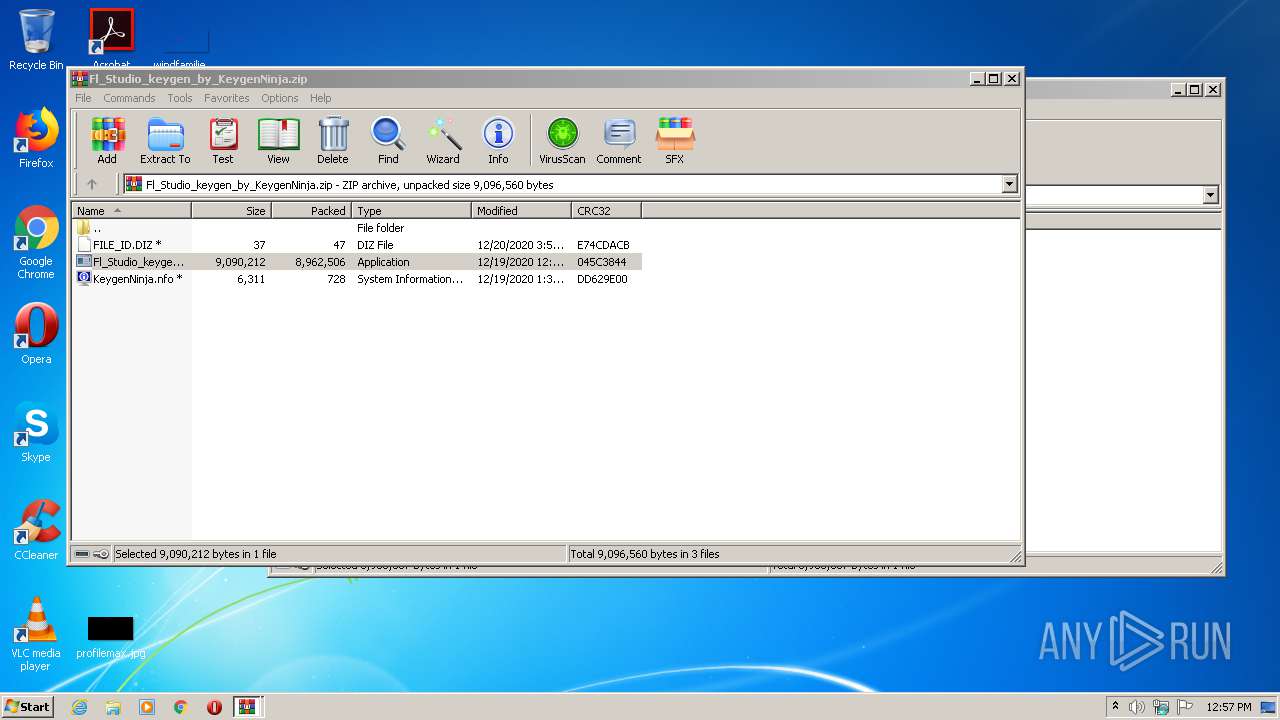
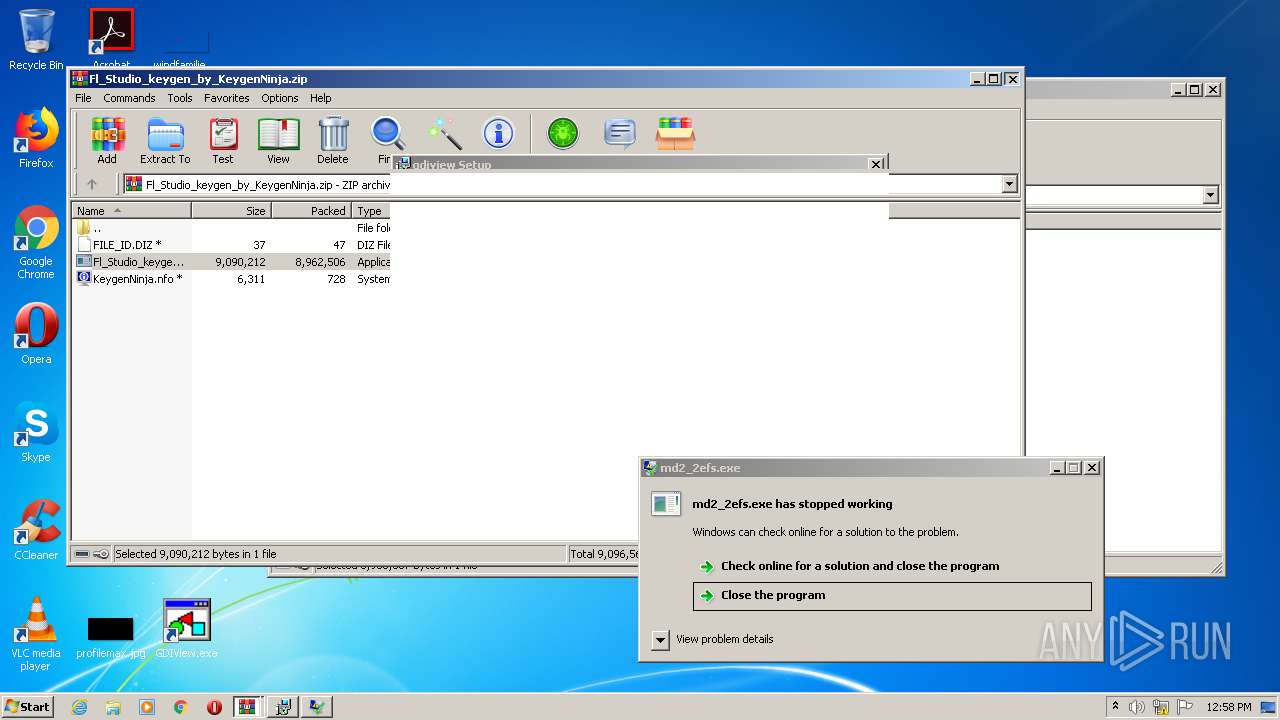
| File name: | Fl_Studio_keygen_by_KeygenNinja.zip |
| Full analysis: | https://app.any.run/tasks/371be46f-4817-4a4c-8eac-9e491bc93296 |
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | February 11, 2021, 12:56:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
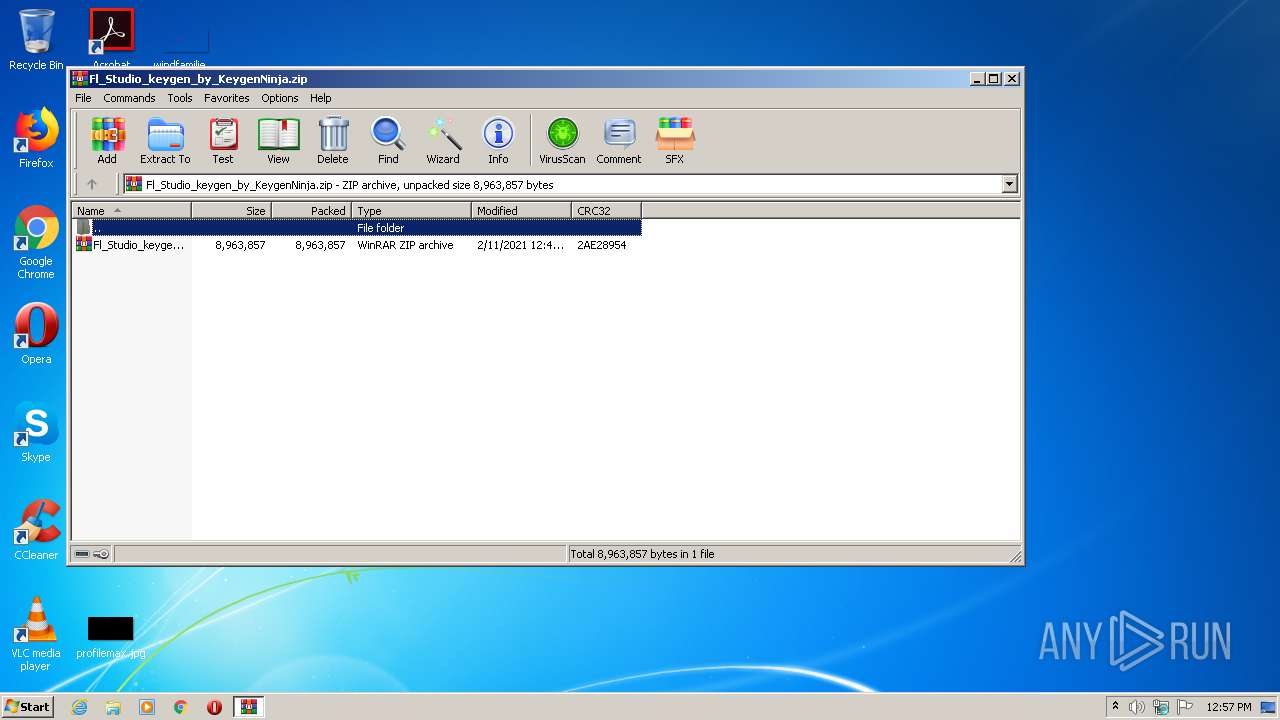
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | B8E1FF4717D44B9DCE6EC285380B906E |
| SHA1: | 20F35B68F2521CDB445278C52E2E1E7D06B5726B |
| SHA256: | 443251DADA6B299D6921D28AC949B955FDA03E834757E6CDC2A570BADC8DBF70 |
| SSDEEP: | 196608:w/2OFq4wxmF2MMglLNPTZXY0oKDT40bENkVmnGoek4n+Iysx9HX6:BcFoyXYQDThToGc4nrysvHX6 |
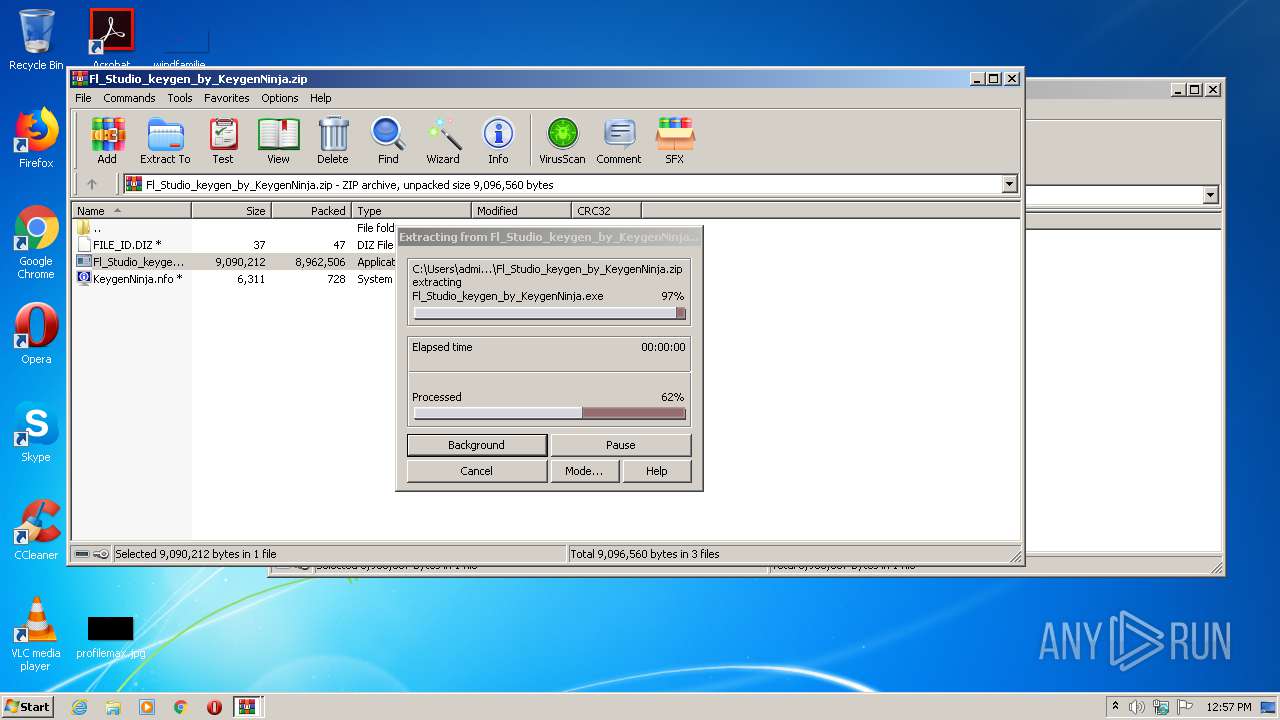
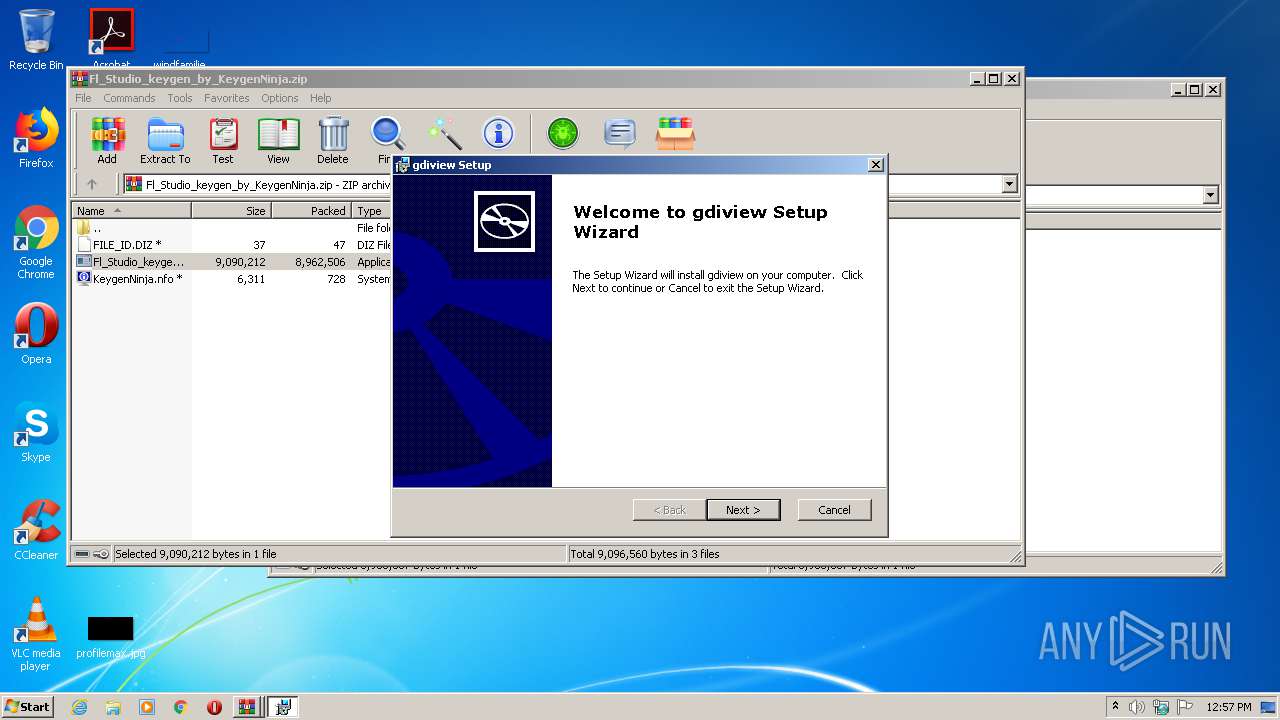
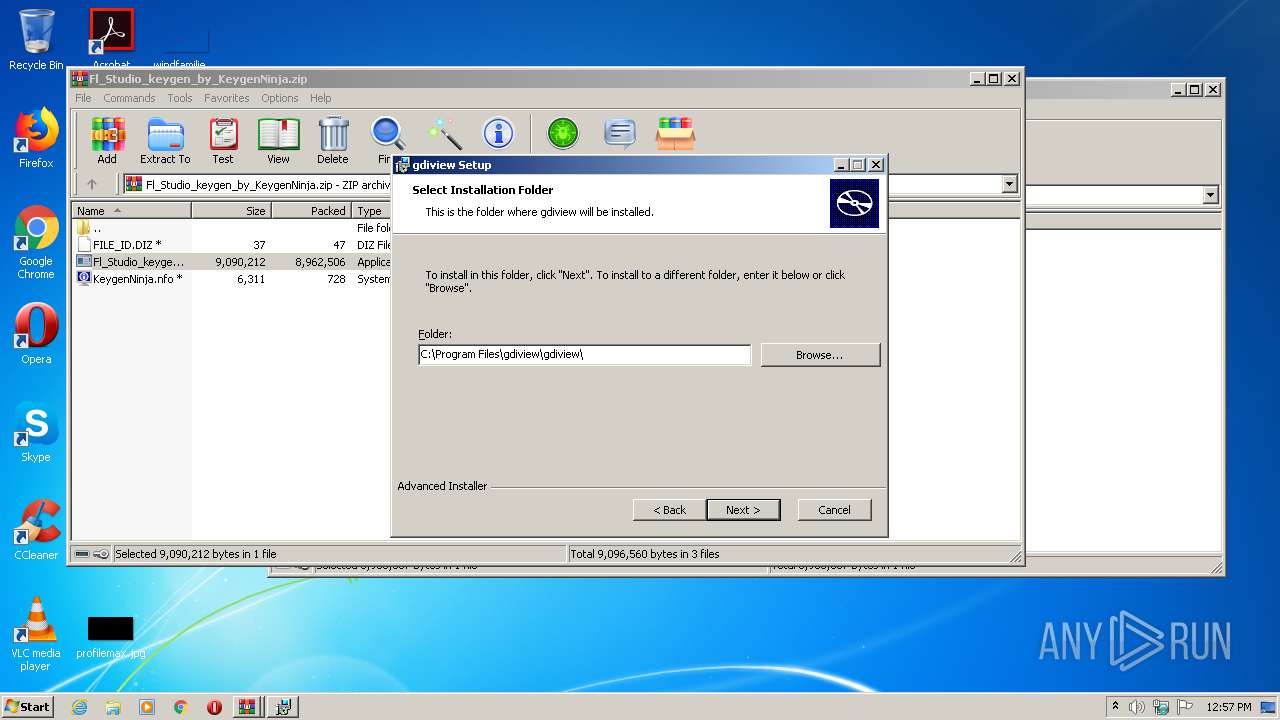
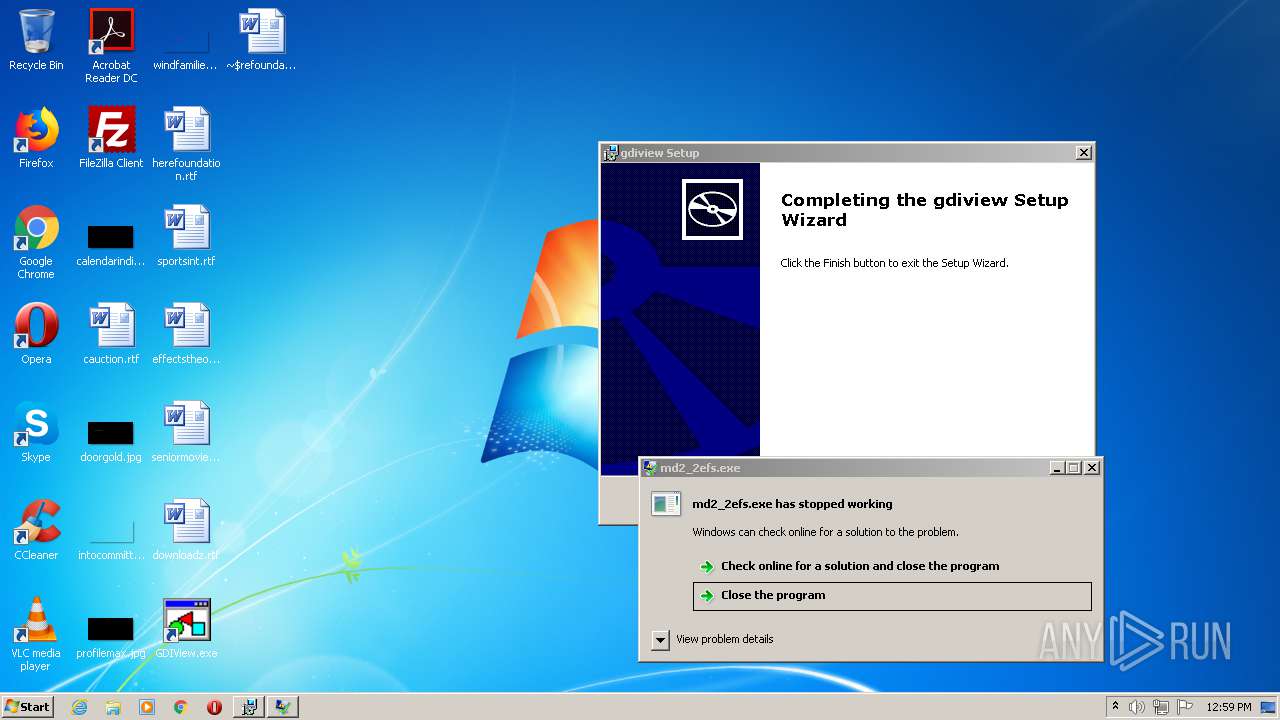
MALICIOUS
Drops executable file immediately after starts
- keygen-step-4.exe (PID: 3076)
- BTRSetp.exe (PID: 3872)
- gdrrr.exe (PID: 4020)
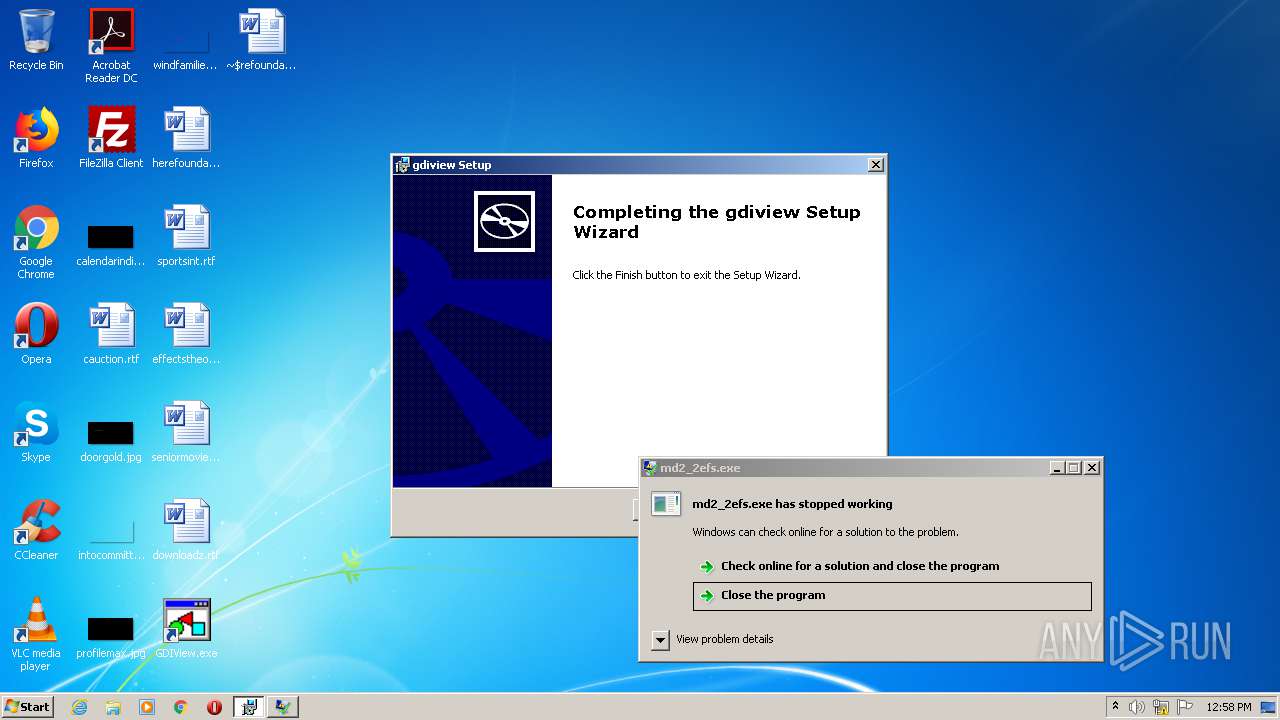
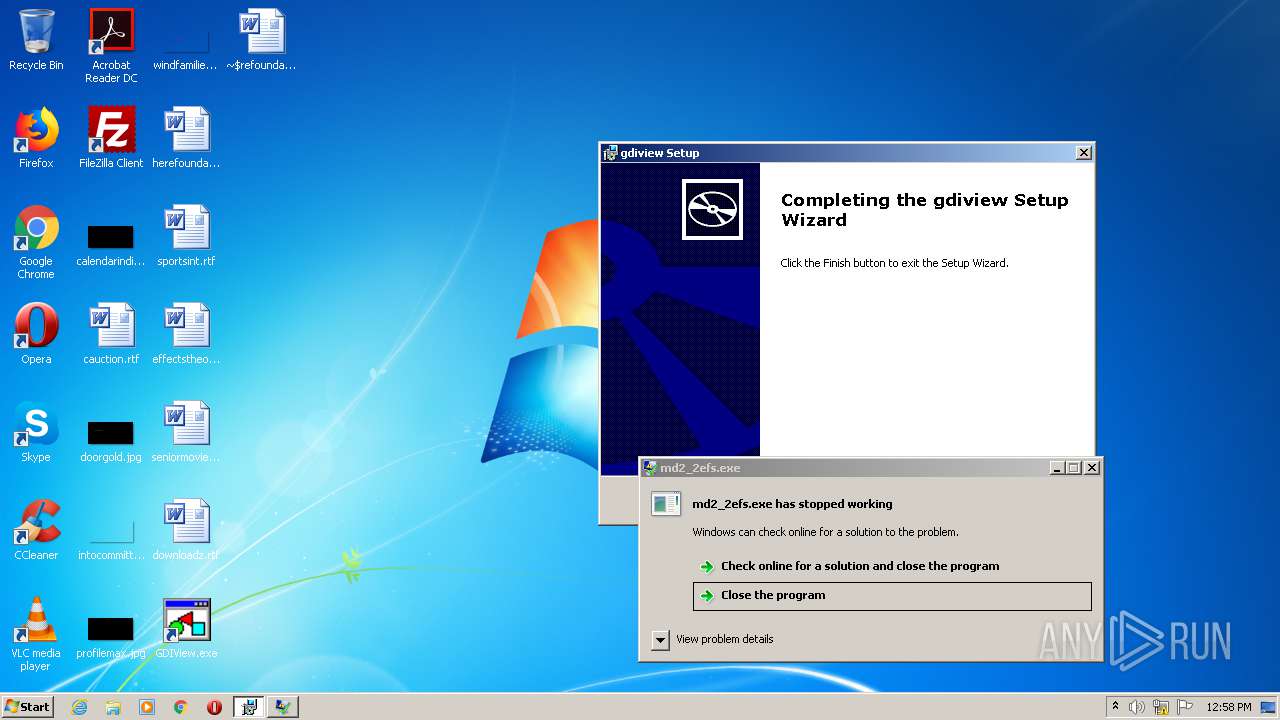
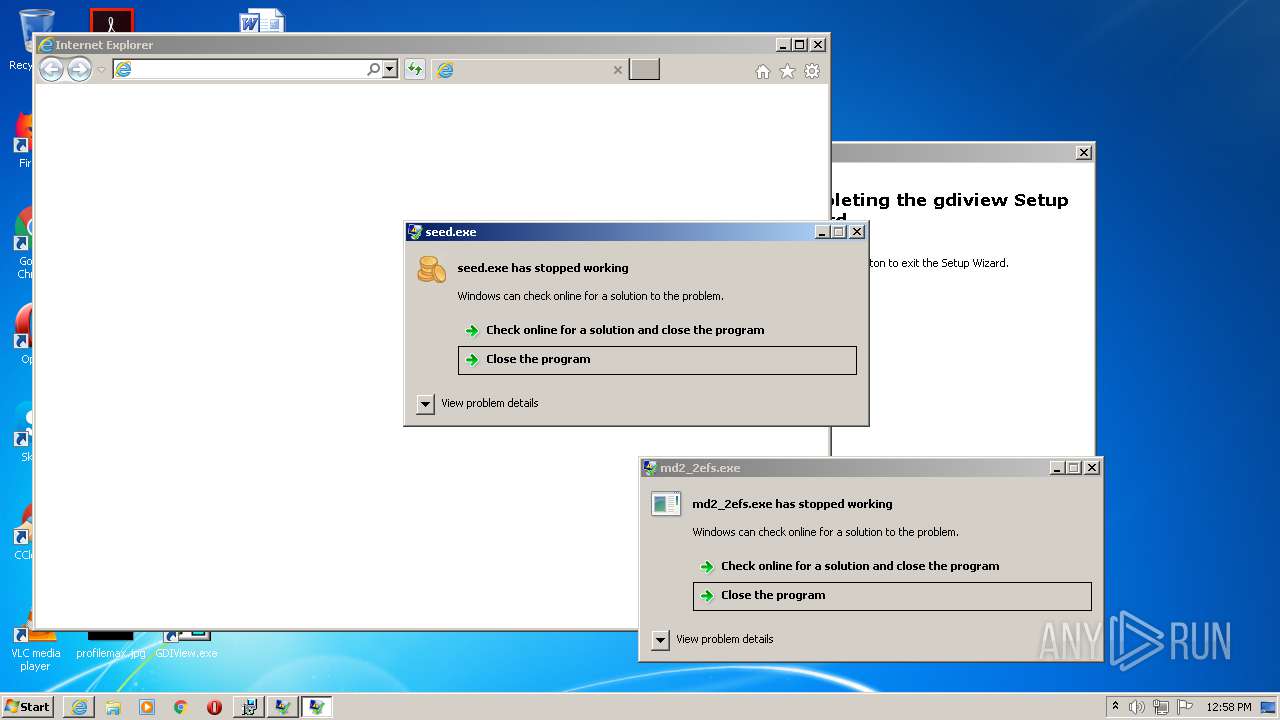
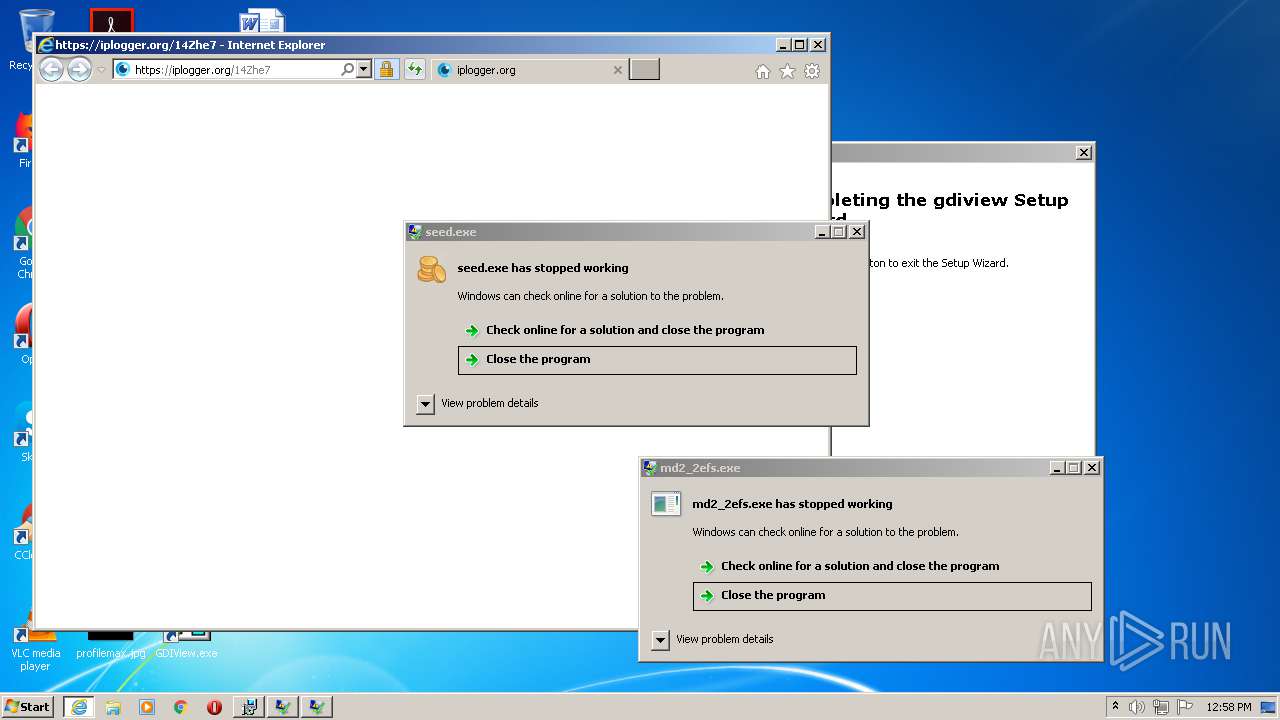
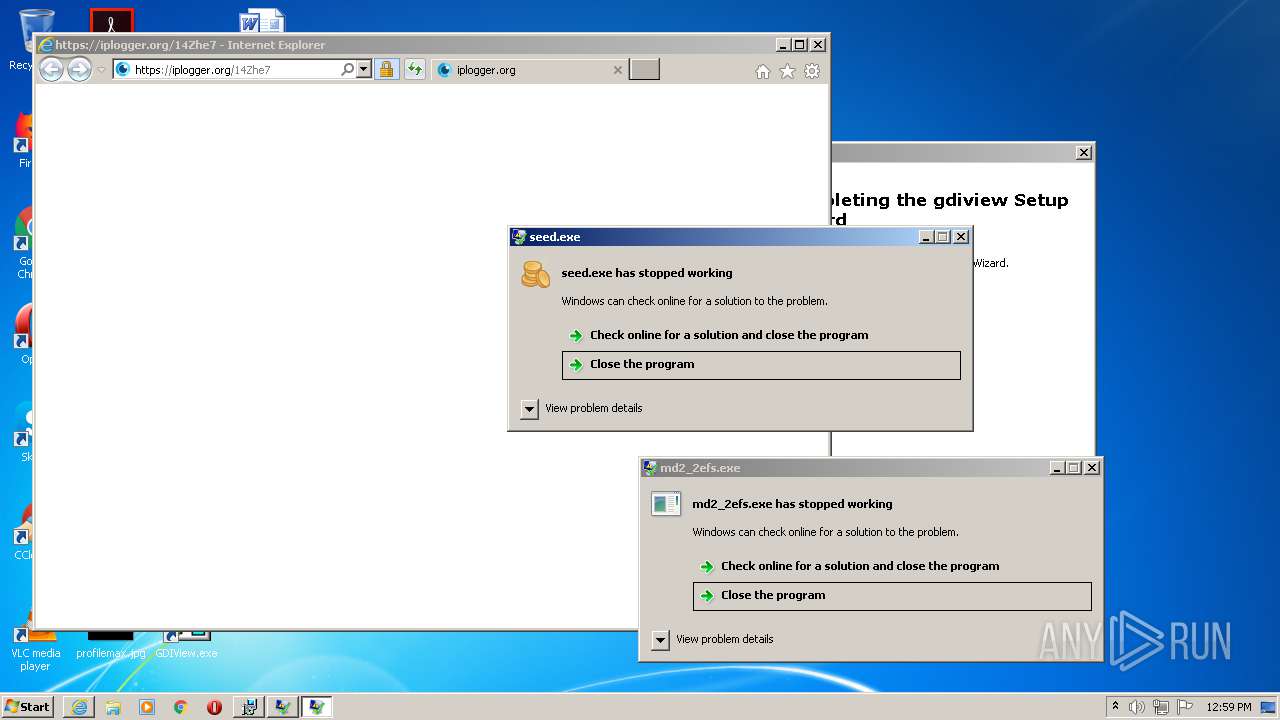
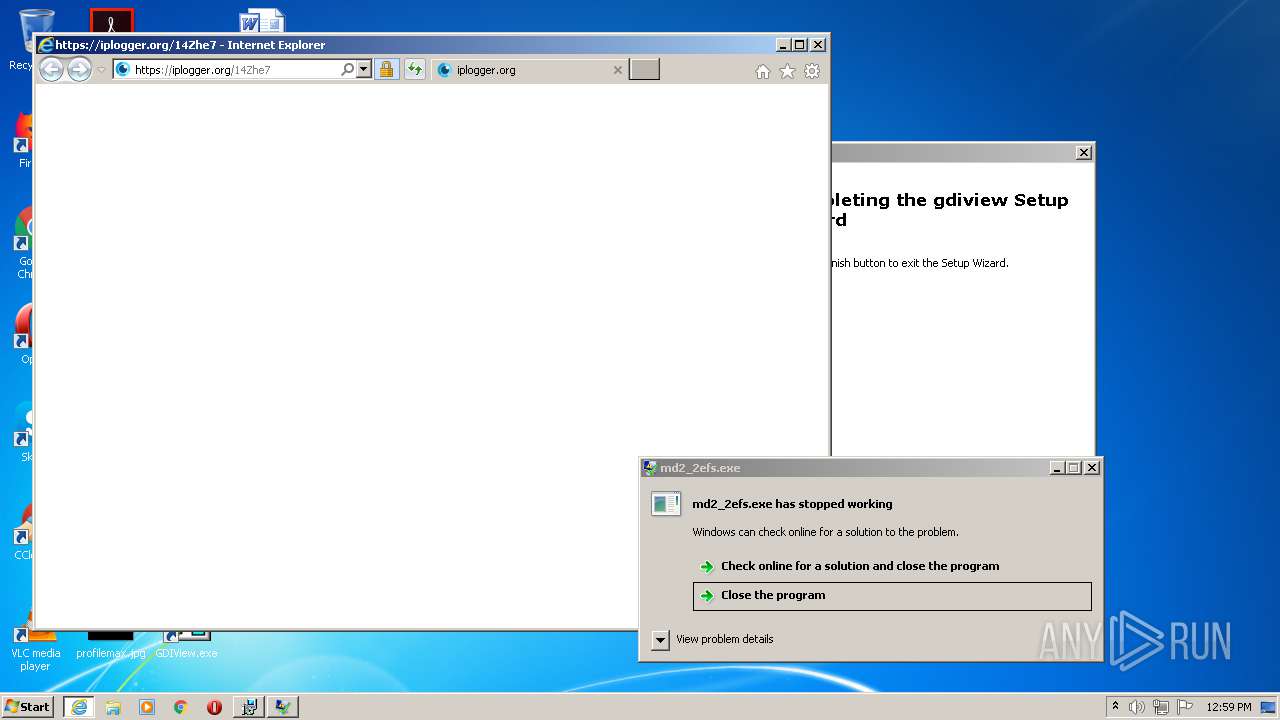
Actions looks like stealing of personal data
- keygen-step-4.exe (PID: 3076)
- 6489A2274AE24900.exe (PID: 3084)
- key.exe (PID: 1348)
- 6489A2274AE24900.exe (PID: 3584)
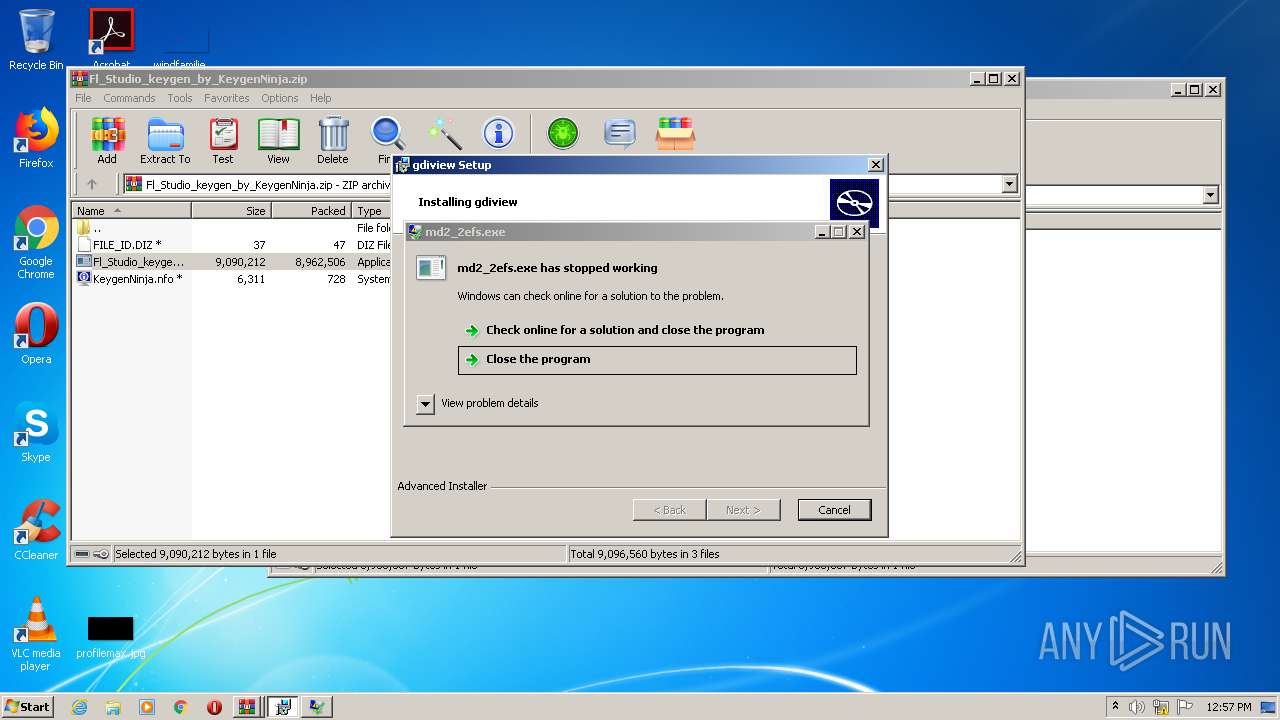
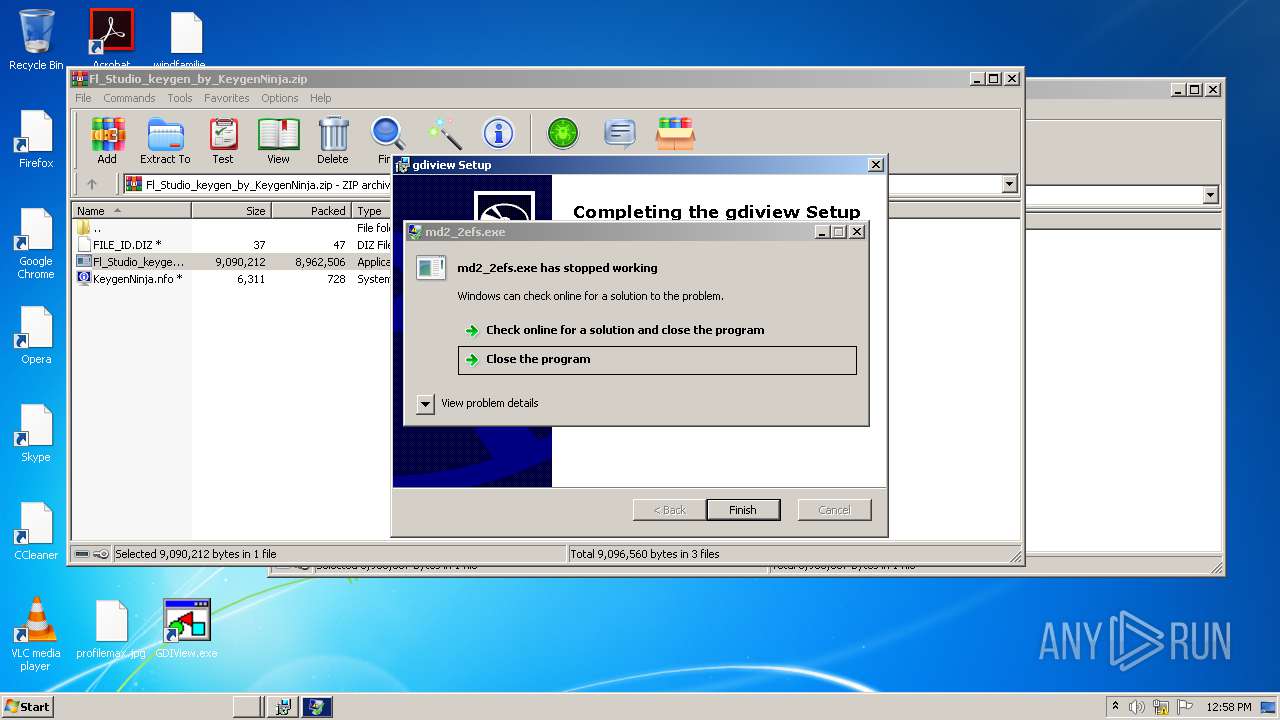
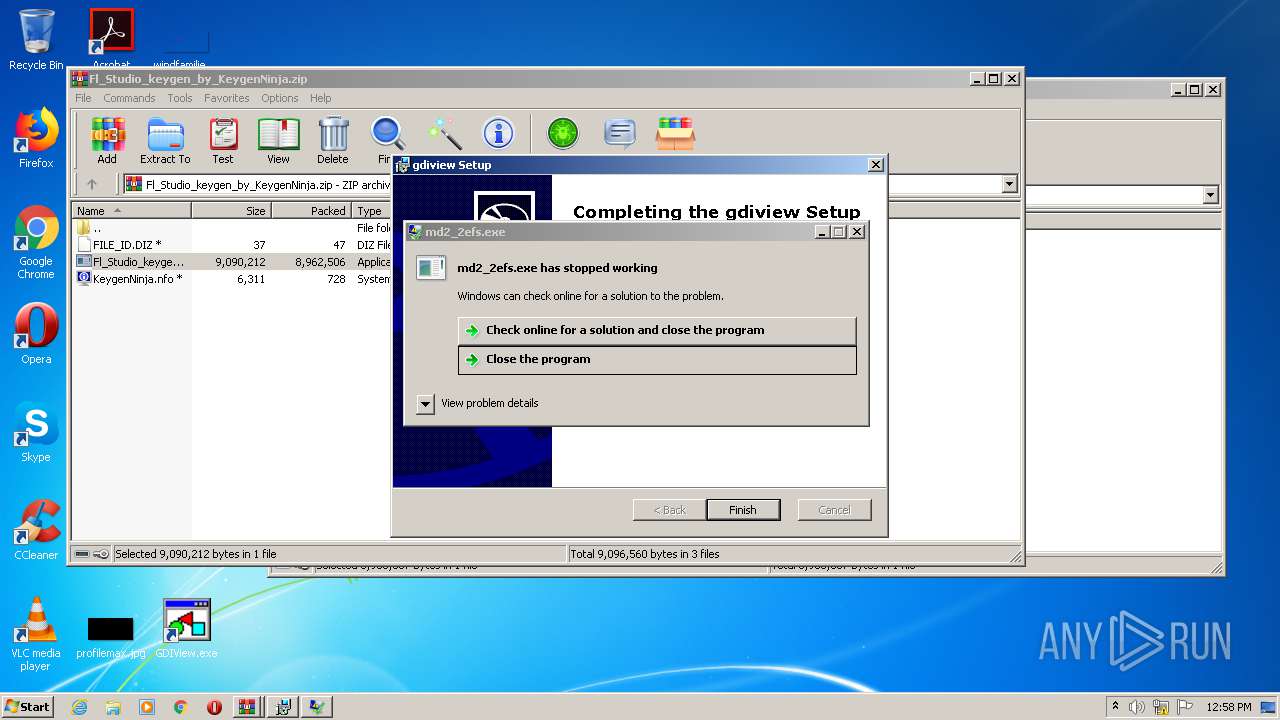
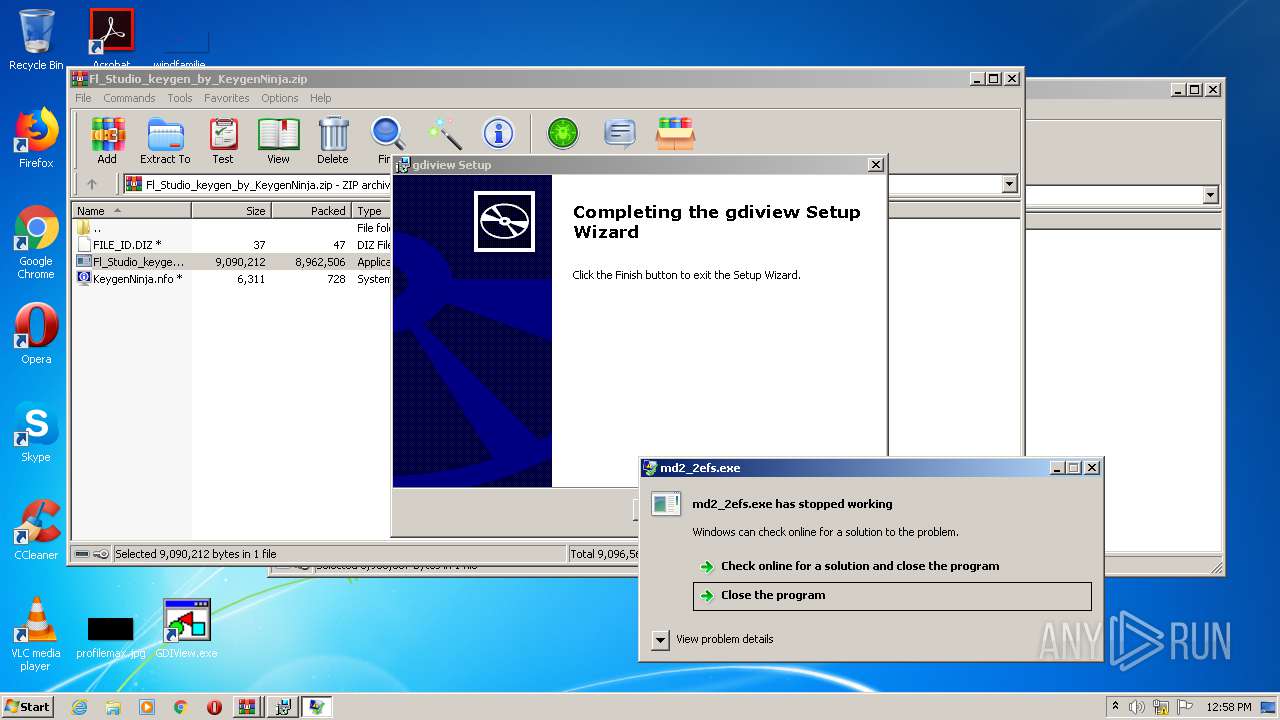
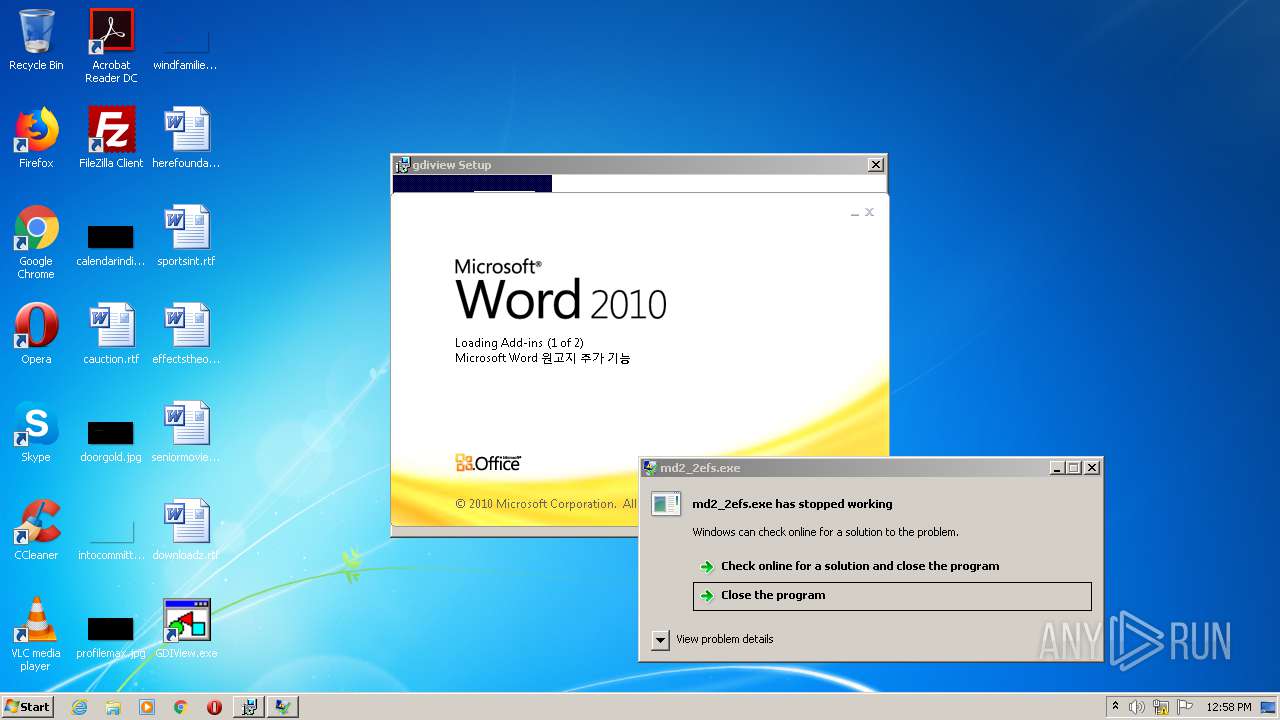
- md2_2efs.exe (PID: 2064)
- 576D.tmp.exe (PID: 2820)
- ubisoftinfo.exe (PID: 2404)
- 5226540.57 (PID: 2896)
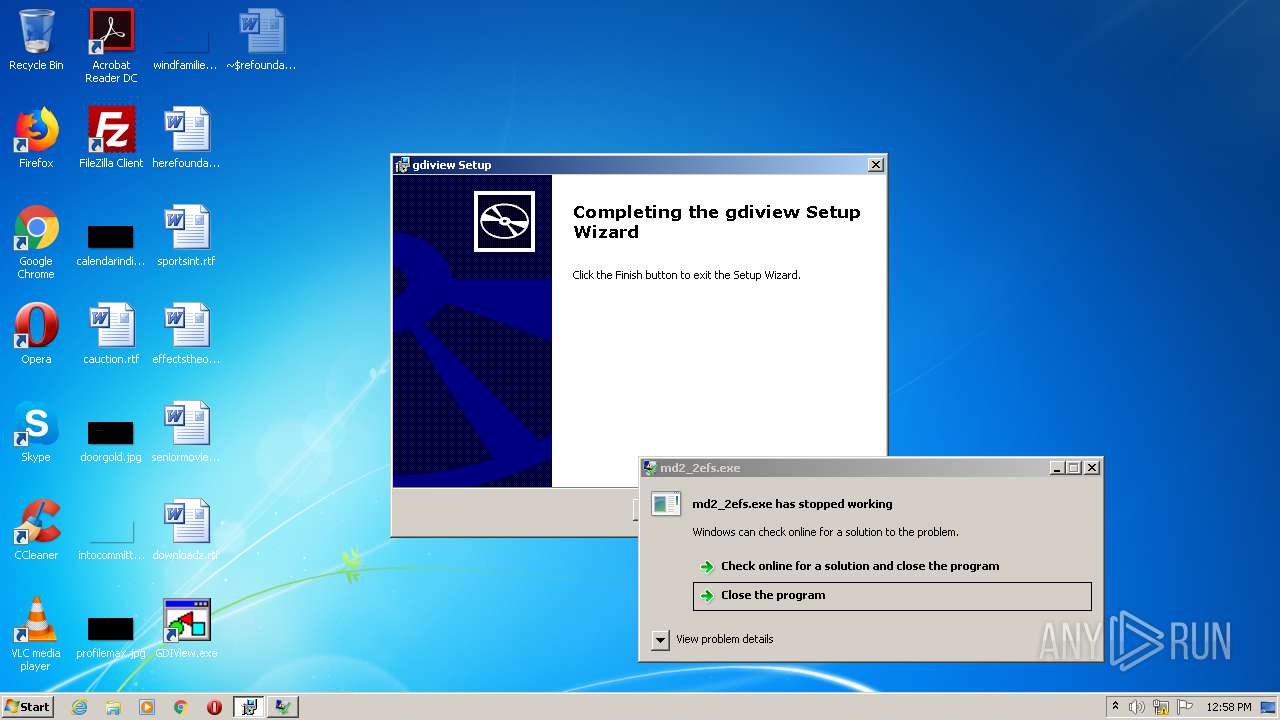
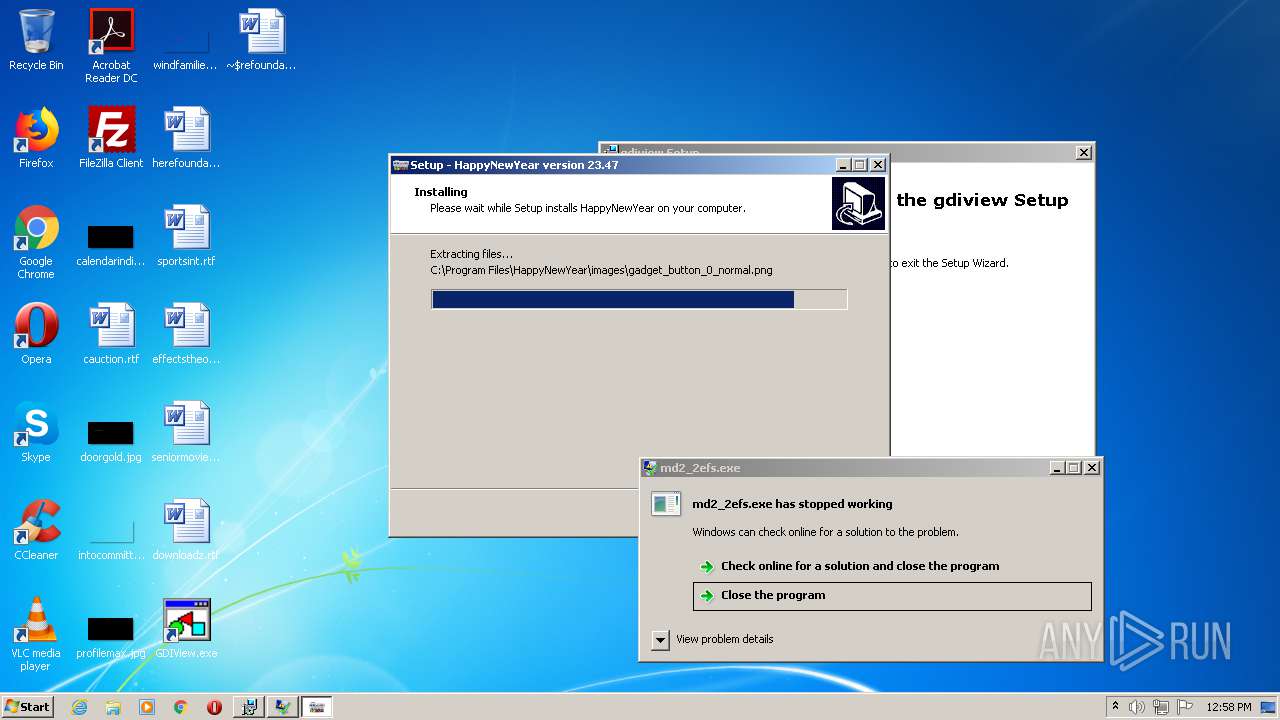
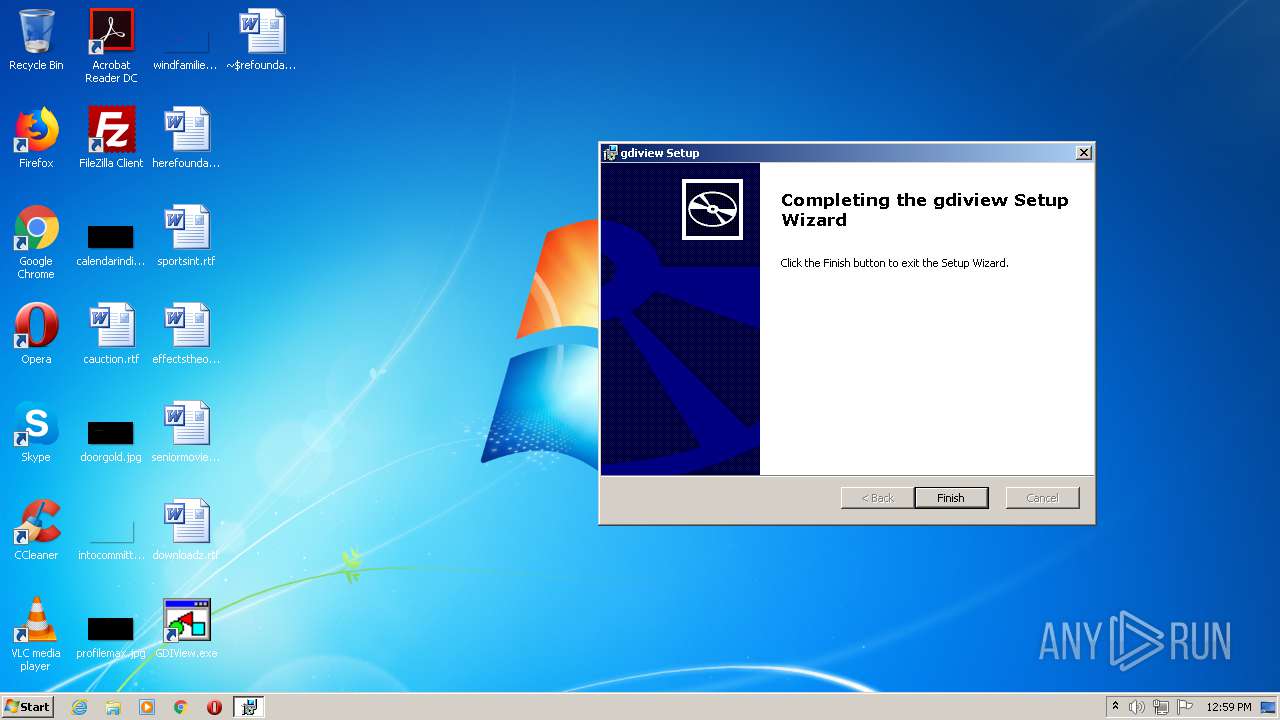
Application was dropped or rewritten from another process
- keygen-step-1.exe (PID: 2672)
- key.exe (PID: 1348)
- Fl_Studio_keygen_by_KeygenNinja.exe (PID: 1700)
- keygen-pr.exe (PID: 2564)
- key.exe (PID: 2508)
- Setup.exe (PID: 2316)
- keygen-step-4.exe (PID: 3076)
- Setup.exe (PID: 2200)
- 6489A2274AE24900.exe (PID: 3084)
- 6489A2274AE24900.exe (PID: 3584)
- md2_2efs.exe (PID: 2064)
- ThunderFW.exe (PID: 2196)
- MiniThunderPlatform.exe (PID: 3176)
- 23E04C4F32EF2158.exe (PID: 2080)
- seed.sfx.exe (PID: 3196)
- seed.exe (PID: 3540)
- file.exe (PID: 2908)
- 576D.tmp.exe (PID: 2820)
- BTRSetp.exe (PID: 3872)
- installer.exe (PID: 2904)
- installer.exe (PID: 2588)
- 2469876.27 (PID: 3800)
- 5226540.57 (PID: 2896)
- Windows Host.exe (PID: 2708)
- gdrrr.exe (PID: 3268)
- gdrrr.exe (PID: 4020)
- ubisoftinfo.exe (PID: 2404)
- 7610177.83 (PID: 2912)
- jfiag3g_gg.exe (PID: 2364)
AZORULT was detected
- keygen-step-1.exe (PID: 2672)
Loads the Task Scheduler COM API
- sppsvc.exe (PID: 3028)
- OSPPSVC.EXE (PID: 1644)
Connects to CnC server
- keygen-step-1.exe (PID: 2672)
- Setup.exe (PID: 2200)
- key.exe (PID: 1348)
- 6489A2274AE24900.exe (PID: 3084)
- MiniThunderPlatform.exe (PID: 3176)
- md2_2efs.exe (PID: 2064)
Changes settings of System certificates
- Setup.exe (PID: 2200)
- md2_2efs.exe (PID: 2064)
- 576D.tmp.exe (PID: 2820)
- installer.exe (PID: 2588)
- gdrrr.exe (PID: 4020)
COPPER was detected
- Setup.exe (PID: 2200)
- 6489A2274AE24900.exe (PID: 3084)
Steals credentials from Web Browsers
- key.exe (PID: 1348)
- 6489A2274AE24900.exe (PID: 3584)
- md2_2efs.exe (PID: 2064)
- 6489A2274AE24900.exe (PID: 3084)
- 576D.tmp.exe (PID: 2820)
- ubisoftinfo.exe (PID: 2404)
- 5226540.57 (PID: 2896)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1956)
- cmd.exe (PID: 1584)
- cmd.exe (PID: 2532)
Detected Pony/Fareit Trojan
- key.exe (PID: 1348)
PONY was detected
- key.exe (PID: 1348)
Modifies files in Chrome extension folder
- 6489A2274AE24900.exe (PID: 3584)
Loads dropped or rewritten executable
- MiniThunderPlatform.exe (PID: 3176)
- 6489A2274AE24900.exe (PID: 3084)
- ThunderFW.exe (PID: 2196)
- DllHost.exe (PID: 4076)
- svchost.exe (PID: 1828)
- seed.exe (PID: 3540)
- msiexec.exe (PID: 2936)
- WINWORD.EXE (PID: 1392)
- seed.sfx.exe (PID: 3196)
- conhost.exe (PID: 1464)
- key.exe (PID: 2508)
- WinRAR.exe (PID: 2188)
- keygen-step-1.exe (PID: 2672)
- conhost.exe (PID: 2356)
- keygen-pr.exe (PID: 2564)
- firefox.exe (PID: 4024)
- 6489A2274AE24900.exe (PID: 3584)
- WerFault.exe (PID: 2728)
- Fl_Studio_keygen_by_KeygenNinja.exe (PID: 1700)
- Setup.exe (PID: 2316)
- PING.EXE (PID: 3392)
- keygen-step-4.exe (PID: 3076)
- conhost.exe (PID: 2476)
- WinRAR.exe (PID: 2372)
- cmd.exe (PID: 1956)
- DllHost.exe (PID: 2264)
- sppsvc.exe (PID: 3028)
- cmd.exe (PID: 1584)
- PING.EXE (PID: 1904)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 1904)
- vssvc.exe (PID: 2724)
- conhost.exe (PID: 956)
- DllHost.exe (PID: 3060)
- taskkill.exe (PID: 3588)
- firefox.exe (PID: 2112)
- WerFault.exe (PID: 3784)
- key.exe (PID: 1348)
- consent.exe (PID: 1148)
- wmiprvse.exe (PID: 2620)
- wmiprvse.exe (PID: 4036)
- DllHost.exe (PID: 1812)
- cmd.exe (PID: 3592)
- md2_2efs.exe (PID: 2064)
- OSPPSVC.EXE (PID: 1644)
- conhost.exe (PID: 2500)
- 23E04C4F32EF2158.exe (PID: 2080)
- svchost.exe (PID: 1716)
- iexplore.exe (PID: 1720)
- conhost.exe (PID: 4056)
- iexplore.exe (PID: 1044)
- Setup.exe (PID: 2200)
- SearchProtocolHost.exe (PID: 1556)
- cmd.exe (PID: 2532)
- SearchFilterHost.exe (PID: 3716)
- IELowutil.exe (PID: 2980)
- PING.EXE (PID: 3284)
- 576D.tmp.exe (PID: 2820)
- file.exe (PID: 2908)
- cmd.exe (PID: 2952)
- conhost.exe (PID: 2688)
- PING.EXE (PID: 2224)
- BTRSetp.exe (PID: 3872)
- conhost.exe (PID: 3568)
- consent.exe (PID: 3560)
- installer.exe (PID: 2904)
- DllHost.exe (PID: 3564)
- installer.exe (PID: 2588)
- DllHost.exe (PID: 3420)
- 5226540.57 (PID: 2896)
- 2469876.27 (PID: 3800)
- 7610177.83 (PID: 2912)
- Windows Host.exe (PID: 2708)
- gdrrr.exe (PID: 3268)
- consent.exe (PID: 1592)
- DllHost.exe (PID: 1080)
- wmiprvse.exe (PID: 3840)
- DllHost.exe (PID: 2512)
- gdrrr.exe (PID: 4020)
- ubisoftinfo.exe (PID: 2404)
- conhost.exe (PID: 2800)
- jfiag3g_gg.exe (PID: 2364)
- timeout.exe (PID: 2632)
- cmd.exe (PID: 1876)
- iexplore.exe (PID: 2988)
- iexplore.exe (PID: 3044)
Stealing of credential data
- 576D.tmp.exe (PID: 2820)
- 5226540.57 (PID: 2896)
Changes the autorun value in the registry
- 2469876.27 (PID: 3800)
- gdrrr.exe (PID: 4020)
REDLINE was detected
- 7610177.83 (PID: 2912)
SUSPICIOUS
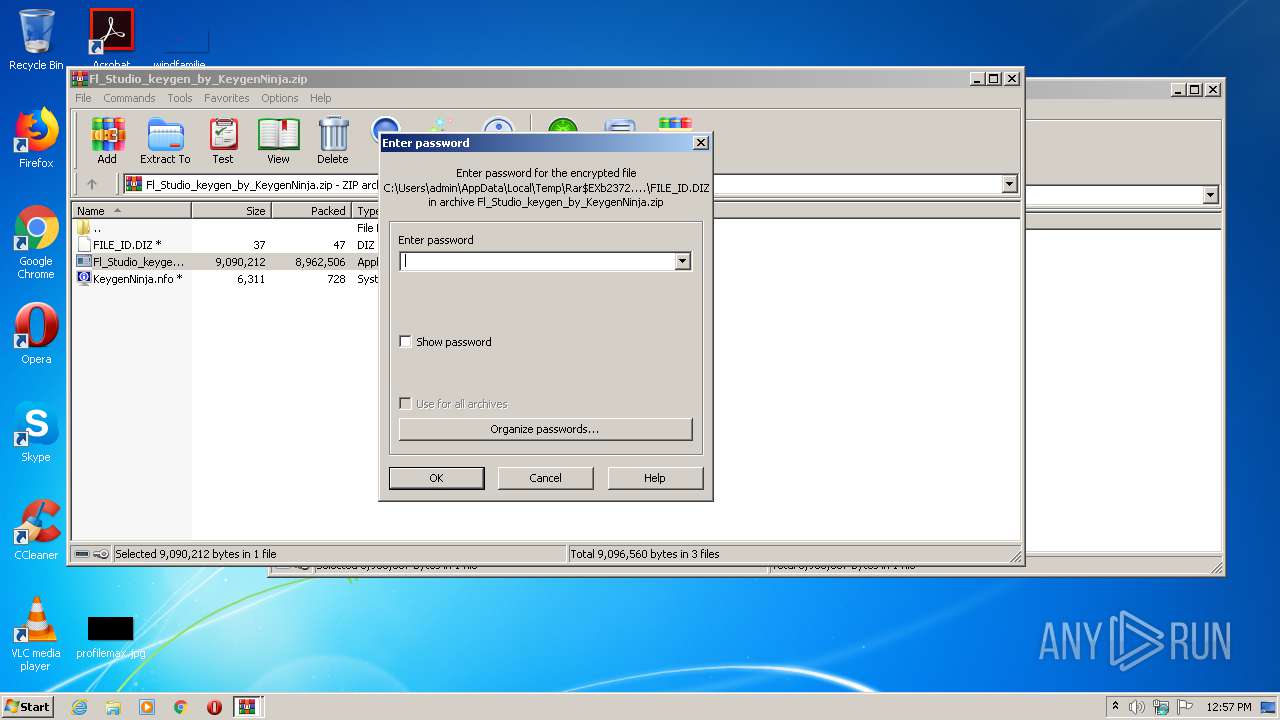
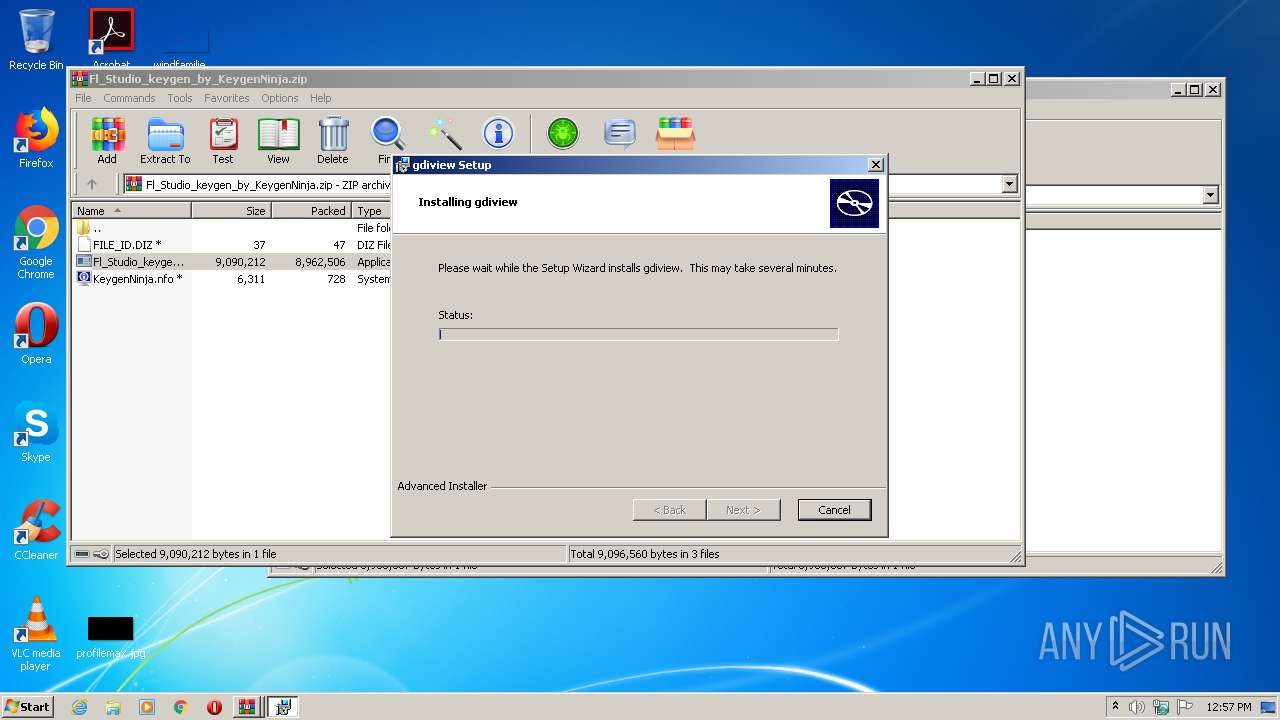
Executable content was dropped or overwritten
- Fl_Studio_keygen_by_KeygenNinja.exe (PID: 1700)
- keygen-pr.exe (PID: 2564)
- WinRAR.exe (PID: 2372)
- keygen-step-4.exe (PID: 3076)
- Setup.exe (PID: 2200)
- msiexec.exe (PID: 2936)
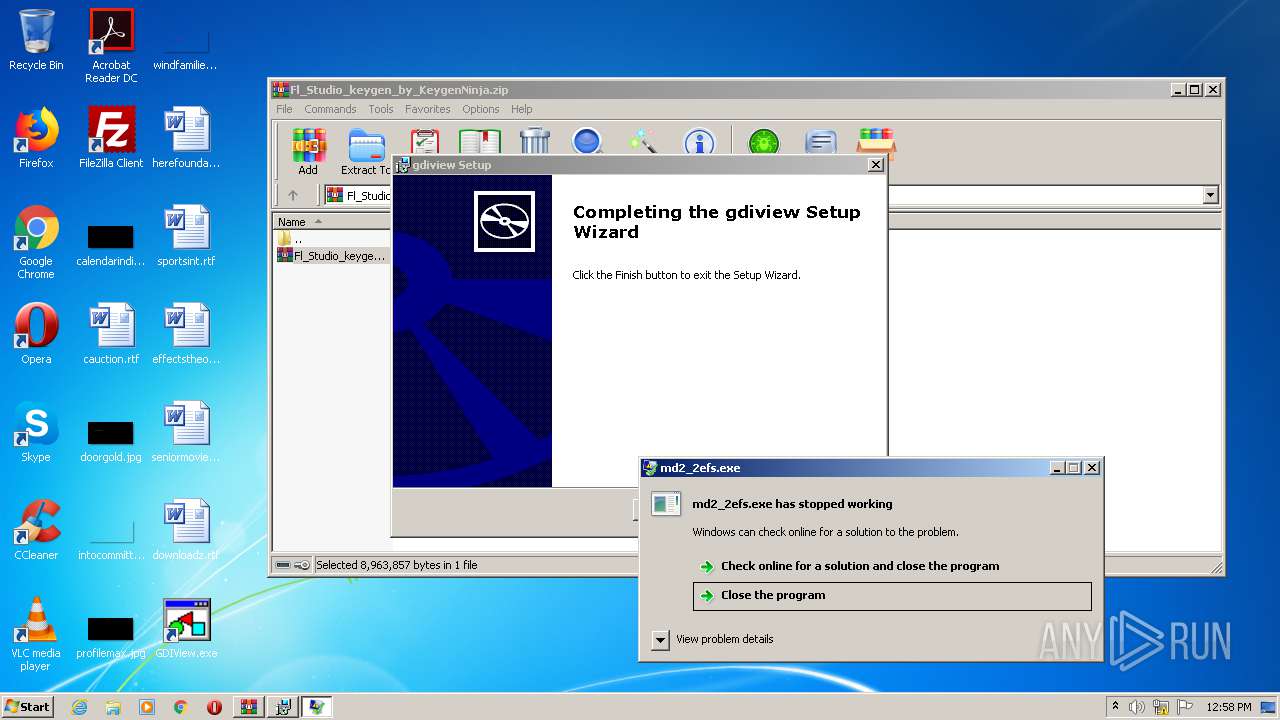
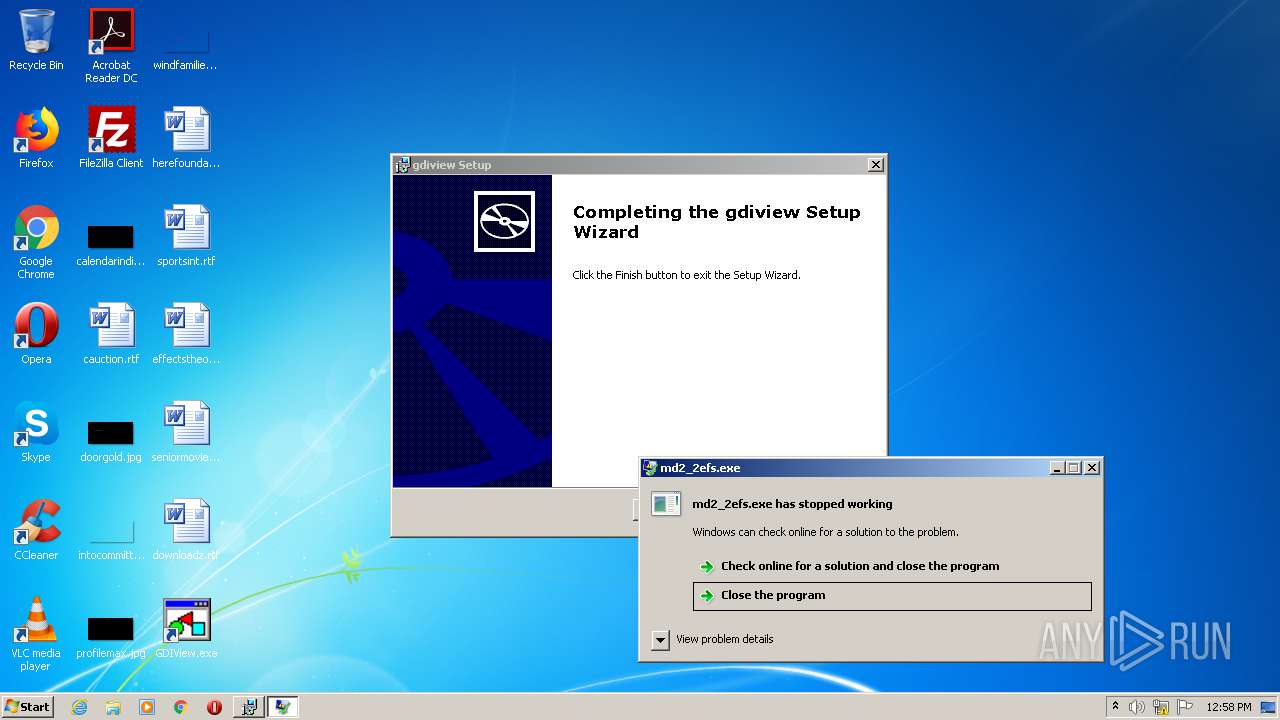
- md2_2efs.exe (PID: 2064)
- msiexec.exe (PID: 2760)
- MiniThunderPlatform.exe (PID: 3176)
- 6489A2274AE24900.exe (PID: 3084)
- 23E04C4F32EF2158.tmp (PID: 2788)
- seed.sfx.exe (PID: 3196)
- 23E04C4F32EF2158.exe (PID: 2080)
- seed.exe (PID: 3540)
- file.exe (PID: 2908)
- BTRSetp.exe (PID: 3872)
- 576D.tmp.exe (PID: 2820)
- installer.exe (PID: 2588)
- 2469876.27 (PID: 3800)
- 5226540.57 (PID: 2896)
- gdrrr.exe (PID: 4020)
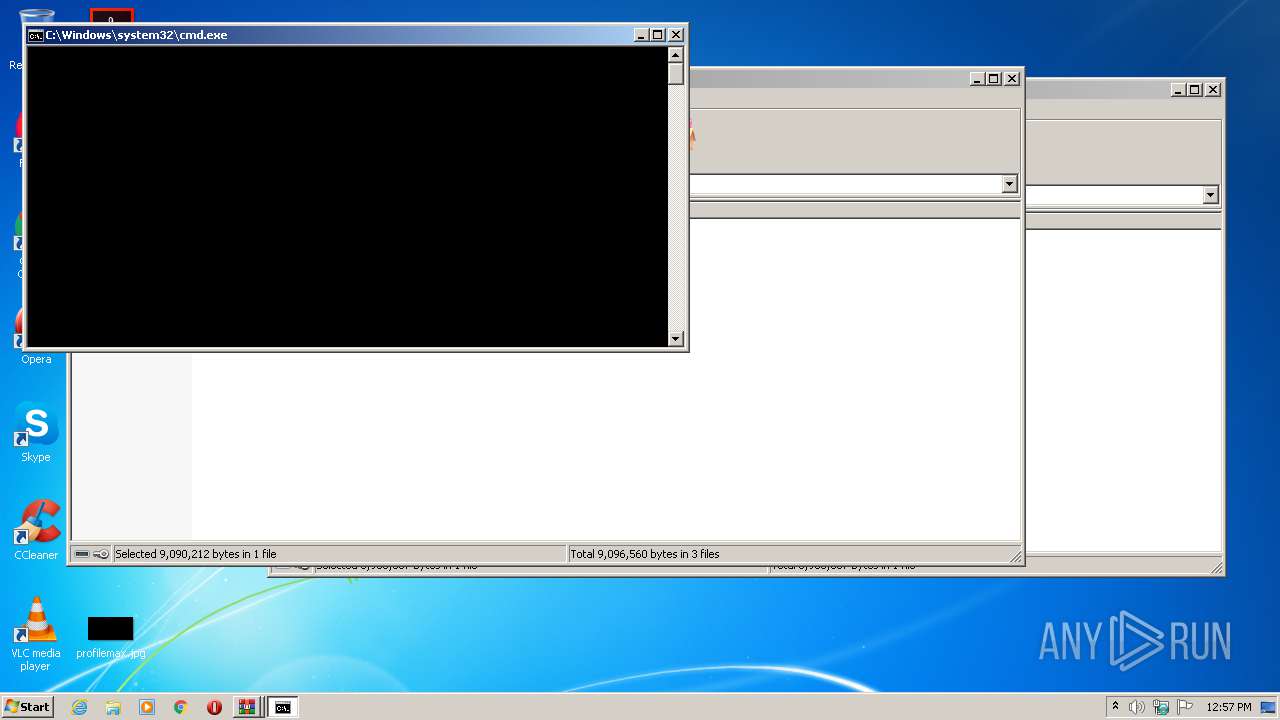
Starts CMD.EXE for commands execution
- Fl_Studio_keygen_by_KeygenNinja.exe (PID: 1700)
- Setup.exe (PID: 2200)
- 6489A2274AE24900.exe (PID: 3584)
- 23E04C4F32EF2158.tmp (PID: 2788)
- 6489A2274AE24900.exe (PID: 3084)
- file.exe (PID: 2908)
- 576D.tmp.exe (PID: 2820)
Application launched itself
- WinRAR.exe (PID: 2188)
- key.exe (PID: 1348)
- gdrrr.exe (PID: 3268)
Drops a file with too old compile date
- Fl_Studio_keygen_by_KeygenNinja.exe (PID: 1700)
- keygen-step-4.exe (PID: 3076)
- msiexec.exe (PID: 2936)
- Setup.exe (PID: 2200)
- 6489A2274AE24900.exe (PID: 3084)
- MiniThunderPlatform.exe (PID: 3176)
- 23E04C4F32EF2158.tmp (PID: 2788)
- 23E04C4F32EF2158.exe (PID: 2080)
- BTRSetp.exe (PID: 3872)
- 576D.tmp.exe (PID: 2820)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2372)
- keygen-step-4.exe (PID: 3076)
- Fl_Studio_keygen_by_KeygenNinja.exe (PID: 1700)
- Setup.exe (PID: 2200)
- msiexec.exe (PID: 2936)
- md2_2efs.exe (PID: 2064)
- msiexec.exe (PID: 2760)
- MiniThunderPlatform.exe (PID: 3176)
- 6489A2274AE24900.exe (PID: 3084)
- 23E04C4F32EF2158.tmp (PID: 2788)
- seed.exe (PID: 3540)
- 576D.tmp.exe (PID: 2820)
- BTRSetp.exe (PID: 3872)
- 5226540.57 (PID: 2896)
- gdrrr.exe (PID: 4020)
Creates files in the user directory
- keygen-step-1.exe (PID: 2672)
- key.exe (PID: 1348)
- 6489A2274AE24900.exe (PID: 3584)
- 6489A2274AE24900.exe (PID: 3084)
- msiexec.exe (PID: 2760)
- file.exe (PID: 2908)
Drops a file with a compile date too recent
- keygen-step-4.exe (PID: 3076)
- md2_2efs.exe (PID: 2064)
- file.exe (PID: 2908)
- BTRSetp.exe (PID: 3872)
- installer.exe (PID: 2588)
- 2469876.27 (PID: 3800)
- 576D.tmp.exe (PID: 2820)
- gdrrr.exe (PID: 4020)
Reads Environment values
- key.exe (PID: 2508)
Reads the Windows organization settings
- key.exe (PID: 2508)
Reads Windows owner or organization settings
- key.exe (PID: 2508)
Reads Windows Product ID
- key.exe (PID: 2508)
Low-level read access rights to disk partition
- Setup.exe (PID: 2200)
- 6489A2274AE24900.exe (PID: 3584)
- 6489A2274AE24900.exe (PID: 3084)
- MiniThunderPlatform.exe (PID: 3176)
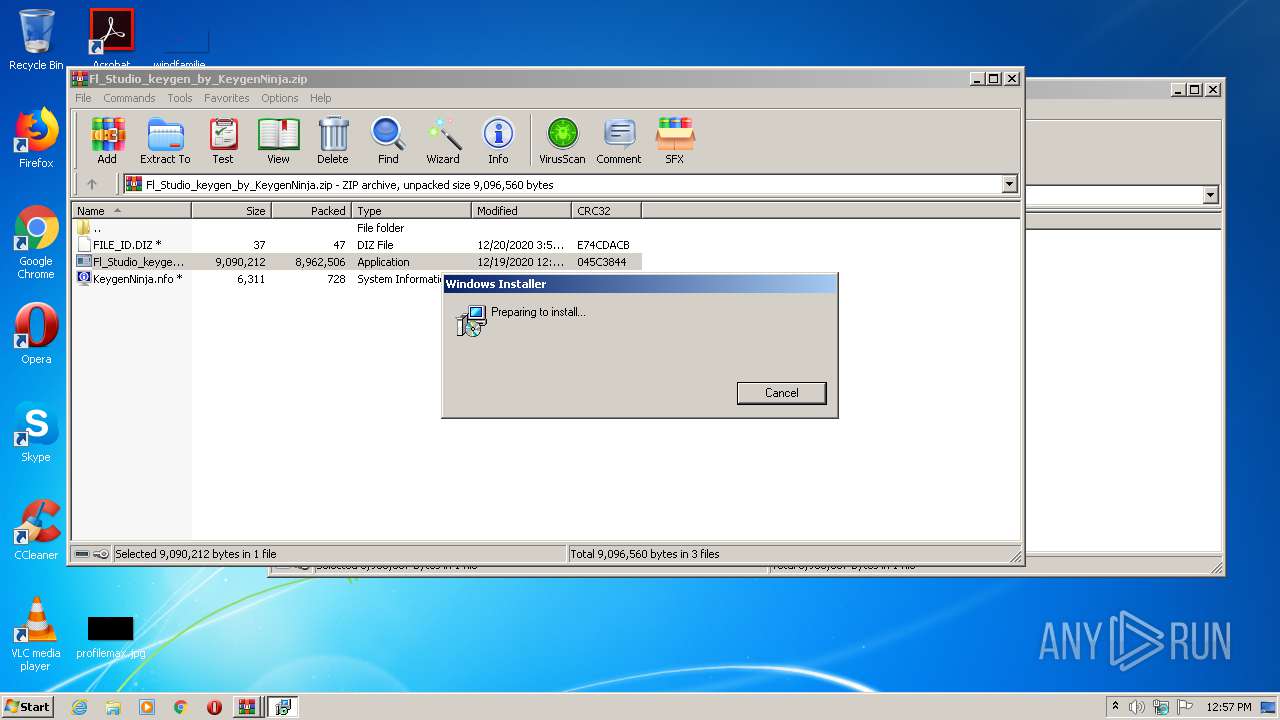
Starts Microsoft Installer
- Setup.exe (PID: 2200)
Loads DLL from Mozilla Firefox
- key.exe (PID: 1348)
Executed as Windows Service
- vssvc.exe (PID: 2724)
Starts itself from another location
- Setup.exe (PID: 2200)
- keygen-step-4.exe (PID: 3076)
- 2469876.27 (PID: 3800)
Starts CMD.EXE for self-deleting
- Setup.exe (PID: 2200)
- 6489A2274AE24900.exe (PID: 3584)
- 6489A2274AE24900.exe (PID: 3084)
- file.exe (PID: 2908)
- 576D.tmp.exe (PID: 2820)
Searches for installed software
- key.exe (PID: 1348)
- key.exe (PID: 2508)
- 576D.tmp.exe (PID: 2820)
- 5226540.57 (PID: 2896)
Reads the cookies of Google Chrome
- 6489A2274AE24900.exe (PID: 3084)
- md2_2efs.exe (PID: 2064)
- 576D.tmp.exe (PID: 2820)
- ubisoftinfo.exe (PID: 2404)
- jfiag3g_gg.exe (PID: 2364)
- 5226540.57 (PID: 2896)
Adds / modifies Windows certificates
- md2_2efs.exe (PID: 2064)
- 576D.tmp.exe (PID: 2820)
- installer.exe (PID: 2588)
- gdrrr.exe (PID: 4020)
Reads the cookies of Mozilla Firefox
- 6489A2274AE24900.exe (PID: 3084)
- md2_2efs.exe (PID: 2064)
- 576D.tmp.exe (PID: 2820)
- 5226540.57 (PID: 2896)
- ubisoftinfo.exe (PID: 2404)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2928)
Creates a directory in Program Files
- msiexec.exe (PID: 2760)
- 23E04C4F32EF2158.tmp (PID: 2788)
- seed.sfx.exe (PID: 3196)
Creates files in the program directory
- MiniThunderPlatform.exe (PID: 3176)
- seed.sfx.exe (PID: 3196)
- WerFault.exe (PID: 2728)
- installer.exe (PID: 2588)
- 2469876.27 (PID: 3800)
- 5226540.57 (PID: 2896)
Starts Internet Explorer
- cmd.exe (PID: 3592)
Starts application with an unusual extension
- installer.exe (PID: 2588)
Executed via COM
- iexplore.exe (PID: 2988)
Checks for external IP
- gdrrr.exe (PID: 4020)
INFO
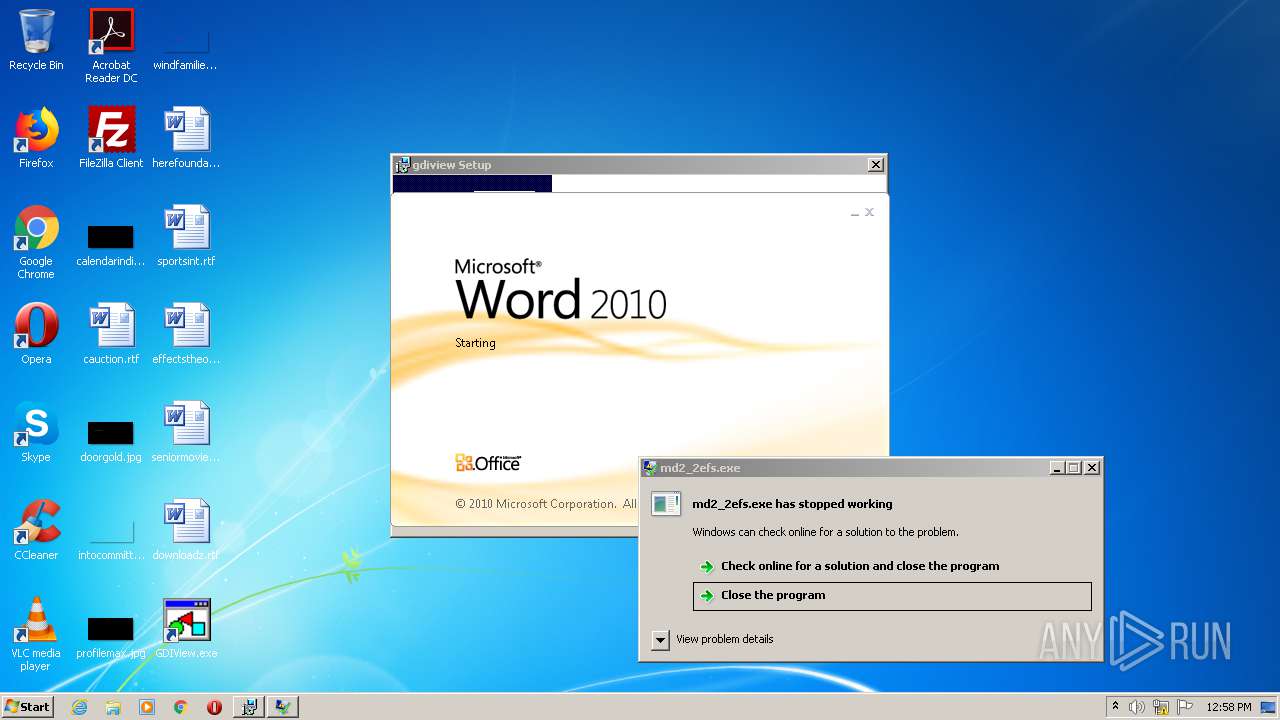
Reads Microsoft Office registry keys
- key.exe (PID: 2508)
- WINWORD.EXE (PID: 1392)
Application launched itself
- msiexec.exe (PID: 2760)
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 2988)
Searches for installed software
- msiexec.exe (PID: 2760)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2724)
Creates files in the program directory
- msiexec.exe (PID: 2760)
- 23E04C4F32EF2158.tmp (PID: 2788)
Creates a software uninstall entry
- msiexec.exe (PID: 2760)
- 23E04C4F32EF2158.tmp (PID: 2788)
Creates files in the user directory
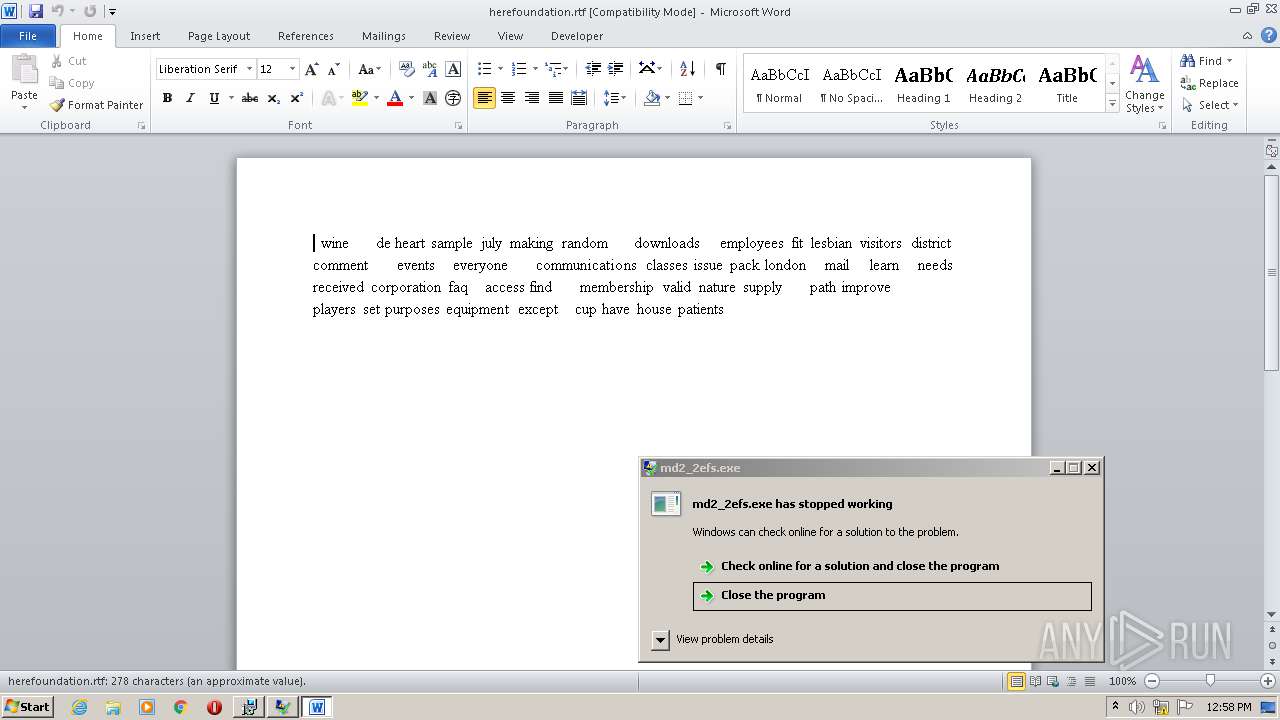
- WINWORD.EXE (PID: 1392)
- iexplore.exe (PID: 1044)
Manual execution by user
- WINWORD.EXE (PID: 1392)
Reads the hosts file
- MiniThunderPlatform.exe (PID: 3176)
Application was dropped or rewritten from another process
- 23E04C4F32EF2158.tmp (PID: 2788)
Changes internet zones settings
- iexplore.exe (PID: 1720)
- iexplore.exe (PID: 2988)
Loads dropped or rewritten executable
- 23E04C4F32EF2158.tmp (PID: 2788)
- MsiExec.exe (PID: 3792)
- msiexec.exe (PID: 2760)
Reads internet explorer settings
- iexplore.exe (PID: 1044)
Reads settings of System Certificates
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 1720)
Changes settings of System certificates
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 1720)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1044)
- iexplore.exe (PID: 1720)
Dropped object may contain Bitcoin addresses
- installer.exe (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:02:11 15:47:21 |
| ZipCRC: | 0x2ae28954 |
| ZipCompressedSize: | 8963857 |
| ZipUncompressedSize: | 8963857 |
| ZipFileName: | Fl_Studio_keygen_by_KeygenNinja.zip |
Total processes
122
Monitored processes
89
Malicious processes
31
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | \??\C:\Windows\system32\conhost.exe "-18403120821043115780-779267730508938222-12362349852004938504-15223331601138611207" | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1720 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1080 | C:\Windows\system32\DllHost.exe /Processid:{E10F6C3A-F1AE-4ADC-AA9D-2FE65525666E} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | consent.exe 872 384 0280AF38 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Temp\RarSFX2\key.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX2\key.exe | keygen-pr.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\herefoundation.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1464 | \??\C:\Windows\system32\conhost.exe "1304359394-2092935961-1724508401406775279894192010783740917-1887479004-1747642508" | C:\Windows\system32\conhost.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10003_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10003 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | cmd /c ping 127.0.0.1 -n 3 & del "C:\Users\admin\AppData\Local\Temp\6489A2274AE24900.exe" | C:\Windows\system32\cmd.exe | — | 6489A2274AE24900.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | consent.exe 872 384 0285AAF8 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 368
Read events
8 315
Write events
876
Delete events
177
Modification events
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Fl_Studio_keygen_by_KeygenNinja.zip | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2372) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
115
Suspicious files
42
Text files
109
Unknown types
40
Dropped files
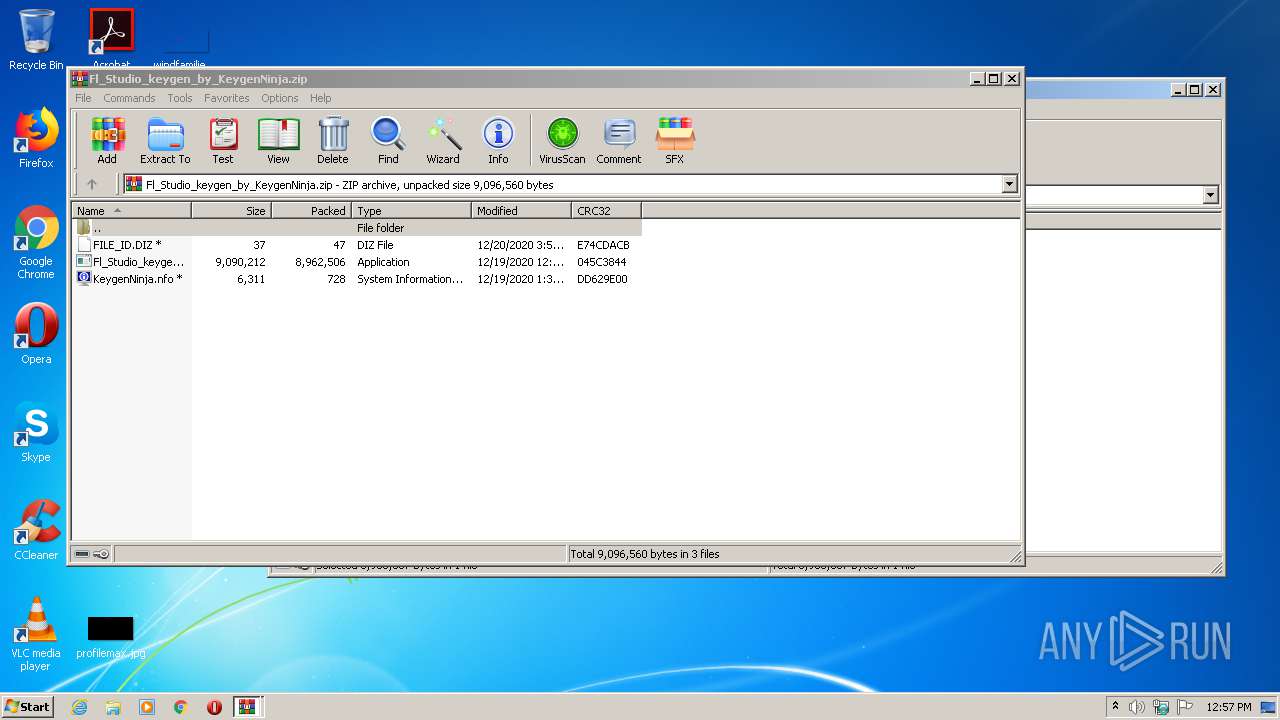
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2372 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2372.6472\KeygenNinja.nfo | text | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2188.5788\Fl_Studio_keygen_by_KeygenNinja.zip | compressed | |
MD5:— | SHA256:— | |||
| 1700 | Fl_Studio_keygen_by_KeygenNinja.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen.bat | text | |
MD5:— | SHA256:— | |||
| 2508 | key.exe | C:\Users\admin\AppData\Local\Temp\tmpE964.tmp | — | |
MD5:— | SHA256:— | |||
| 2372 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2372.6472\Fl_Studio_keygen_by_KeygenNinja.exe | executable | |
MD5:— | SHA256:— | |||
| 2372 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2372.6472\FILE_ID.DIZ | text | |
MD5:— | SHA256:— | |||
| 1700 | Fl_Studio_keygen_by_KeygenNinja.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen-step-4.exe | executable | |
MD5:— | SHA256:— | |||
| 3084 | 6489A2274AE24900.exe | C:\Users\admin\AppData\Local\Login Data1613048269452 | — | |
MD5:— | SHA256:— | |||
| 3084 | 6489A2274AE24900.exe | C:\Users\admin\AppData\Local\Cookies1613048269561 | — | |
MD5:— | SHA256:— | |||
| 2064 | md2_2efs.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\d | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
78
DNS requests
40
Threats
70
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1348 | key.exe | POST | 200 | 172.67.192.106:80 | http://oldhorse.info/a.php | US | — | — | malicious |
3584 | 6489A2274AE24900.exe | POST | 200 | 104.21.55.158:80 | http://bccb0fef593c34da.xyz/info_old/w | US | — | — | malicious |
3084 | 6489A2274AE24900.exe | POST | 200 | 104.21.55.158:80 | http://bccb0fef593c34da.xyz/info_old/w | US | — | — | malicious |
3584 | 6489A2274AE24900.exe | POST | 200 | 104.21.55.158:80 | http://bccb0fef593c34da.xyz/info_old/w | US | — | — | malicious |
1348 | key.exe | POST | — | 172.67.192.106:80 | http://www.oldhorse.info/ | US | — | — | malicious |
1348 | key.exe | POST | — | 172.67.192.106:80 | http://www.oldhorse.info/ | US | — | — | malicious |
1348 | key.exe | POST | — | 172.67.192.106:80 | http://www.oldhorse.info/ | US | — | — | malicious |
3176 | MiniThunderPlatform.exe | POST | 200 | 140.206.225.232:80 | http://140.206.225.232:80/ | CN | binary | 28 b | malicious |
3084 | 6489A2274AE24900.exe | GET | 200 | 104.21.55.158:80 | http://bccb0fef593c34da.xyz/info_old/r | US | text | 24 b | malicious |
3084 | 6489A2274AE24900.exe | POST | 200 | 104.21.55.158:80 | http://bccb0fef593c34da.xyz/info_old/a | US | text | 24 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.21.44.36:80 | kvaka.li | Cloudflare Inc | US | malicious |
2200 | Setup.exe | 104.21.55.158:80 | bccb0fef593c34da.xyz | Cloudflare Inc | US | malicious |
1348 | key.exe | 172.67.192.106:80 | oldhorse.info | — | US | malicious |
2064 | md2_2efs.exe | 101.36.107.74:80 | — | — | CN | malicious |
3584 | 6489A2274AE24900.exe | 104.21.55.158:80 | bccb0fef593c34da.xyz | Cloudflare Inc | US | malicious |
3084 | 6489A2274AE24900.exe | 104.21.55.158:80 | bccb0fef593c34da.xyz | Cloudflare Inc | US | malicious |
2064 | md2_2efs.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
3176 | MiniThunderPlatform.exe | 47.92.99.221:8000 | hub5pnc.hz.sandai.net | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
3084 | 6489A2274AE24900.exe | 172.67.171.167:80 | bccb0fef593c34da.xyz | — | US | malicious |
3176 | MiniThunderPlatform.exe | 47.97.7.140:80 | pmap.hz.sandai.net | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kvaka.li |
| malicious |
bccb0fef593c34da.xyz |
| malicious |
oldhorse.info |
| malicious |
www.oldhorse.info |
| malicious |
iplogger.org |
| shared |
BCCB0FEF593C34DA.xyz |
| malicious |
hub5pn.hz.sandai.net |
| unknown |
hub5pnc.hz.sandai.net |
| malicious |
hub5u.hz.sandai.net |
| unknown |
relay.phub.hz.sandai.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2672 | keygen-step-1.exe | A Network Trojan was detected | ET TROJAN Win32/AZORult V3.3 Client Checkin M2 |
2672 | keygen-step-1.exe | A Network Trojan was detected | AV TROJAN Azorult CnC Beacon |
2672 | keygen-step-1.exe | A Network Trojan was detected | STEALER [PTsecurity] AZORult v.3 |
2672 | keygen-step-1.exe | A Network Trojan was detected | STEALER [PTsecurity] AZORult |
2200 | Setup.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2200 | Setup.exe | A Network Trojan was detected | STEALER [PTsecurity] Cooper |
2200 | Setup.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2200 | Setup.exe | A Network Trojan was detected | STEALER [PTsecurity] Cooper |
2200 | Setup.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2200 | Setup.exe | A Network Trojan was detected | STEALER [PTsecurity] Cooper |
22 ETPRO signatures available at the full report