| File name: | 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe |
| Full analysis: | https://app.any.run/tasks/e494387a-689a-4624-9502-4092f0505370 |
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | September 17, 2025, 09:33:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 0498723F7FFABDFA37B378795DCED76D |
| SHA1: | E55E8BA0EC7547E30589D479B2114D0ED0FDA8B6 |
| SHA256: | 44315F473653B7758DF7197C79D75CB6597F08F57E1509C33495074B5BC49B3C |
| SSDEEP: | 98304:ZDQPyP8hyW4xw83jvm481gRejHZBdeh26oQcmE61oWPRwlZhnx1E/gcew7FZVPpt:1eL9UVTj |
MALICIOUS
Changes the autorun value in the registry
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
Known privilege escalation attack
- dllhost.exe (PID: 6452)
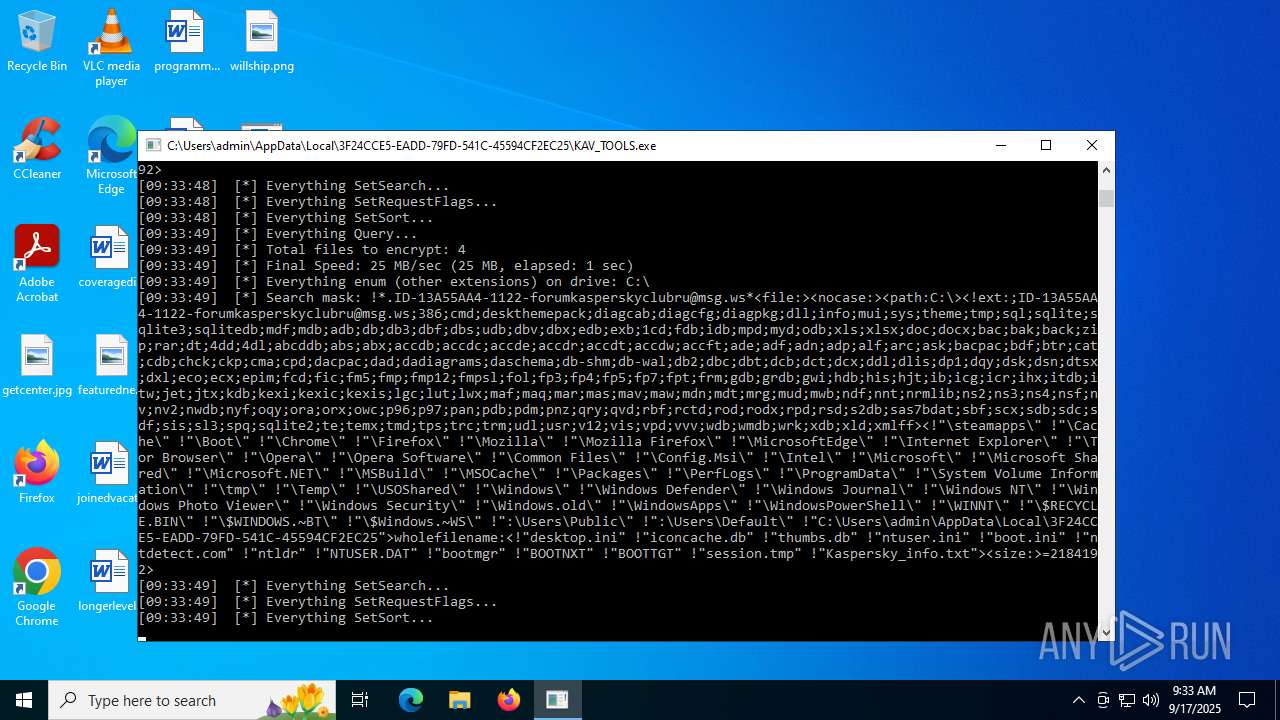
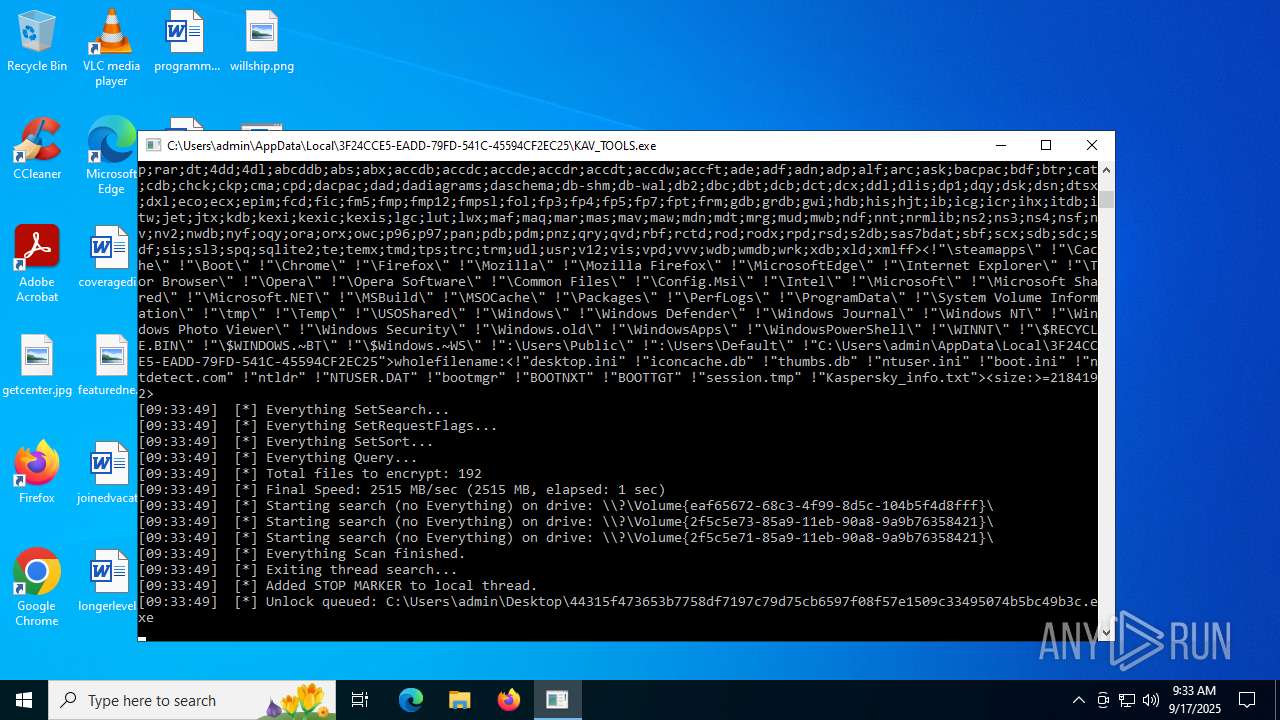
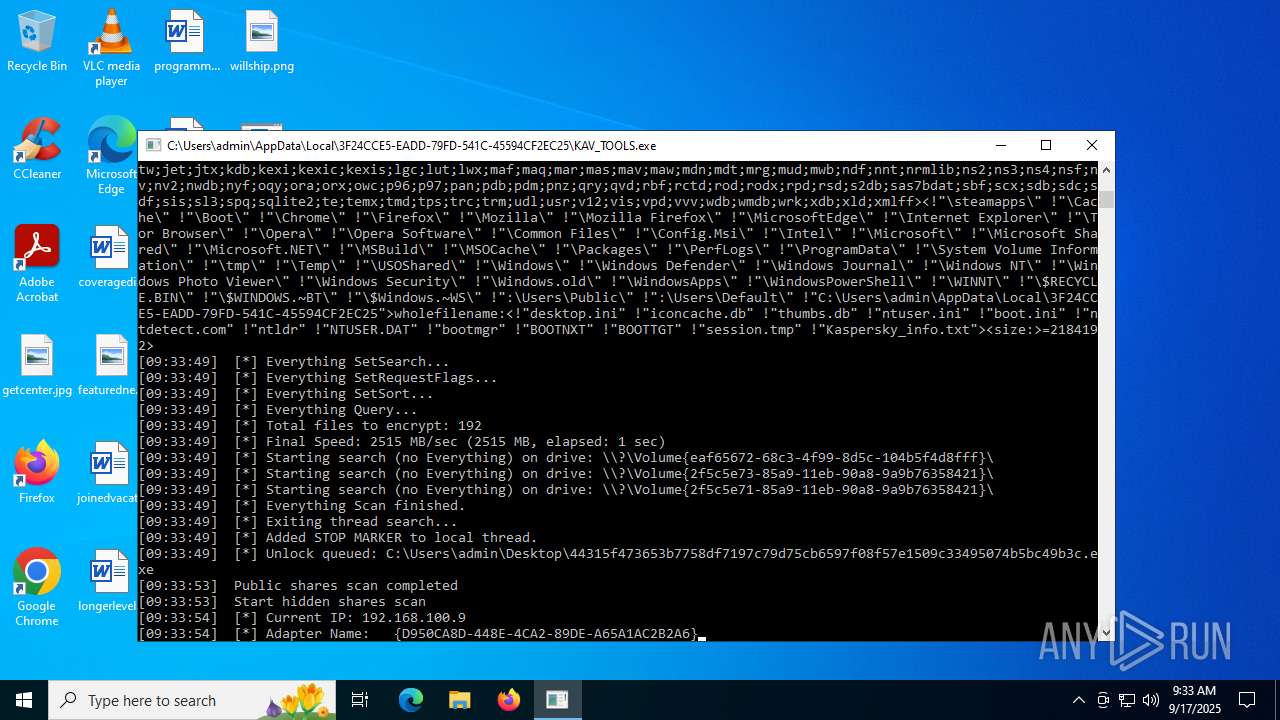
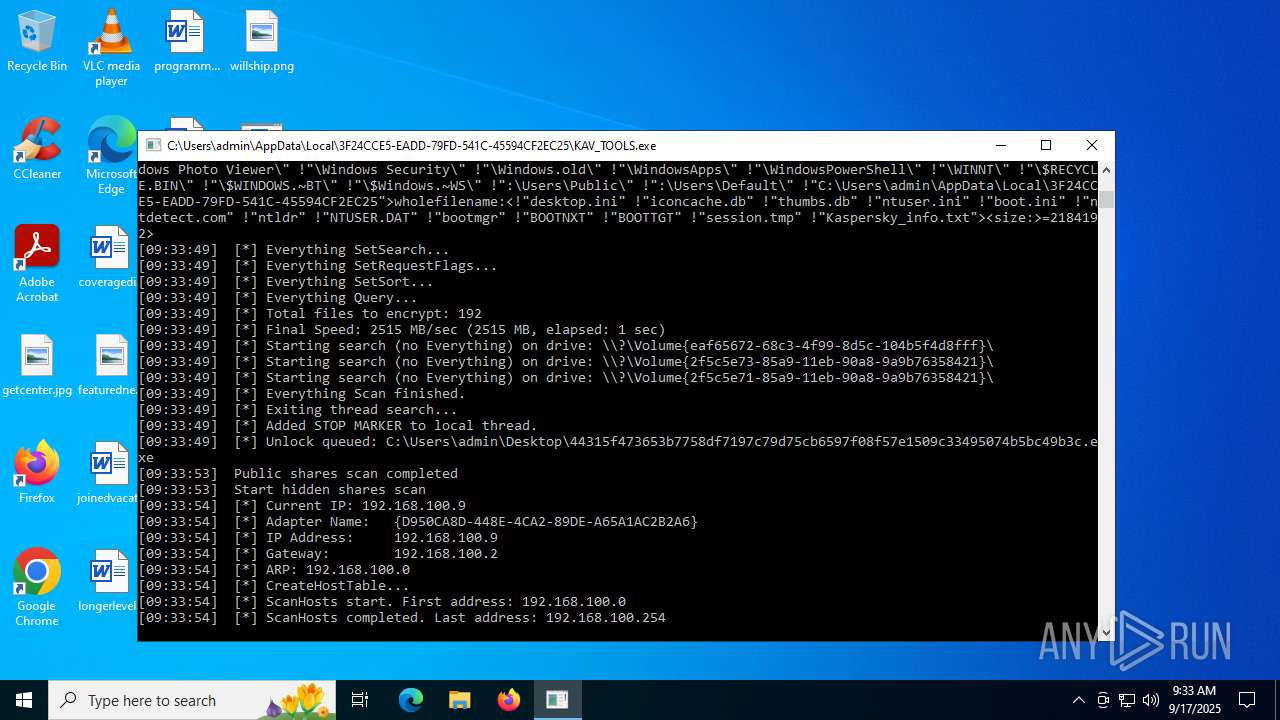
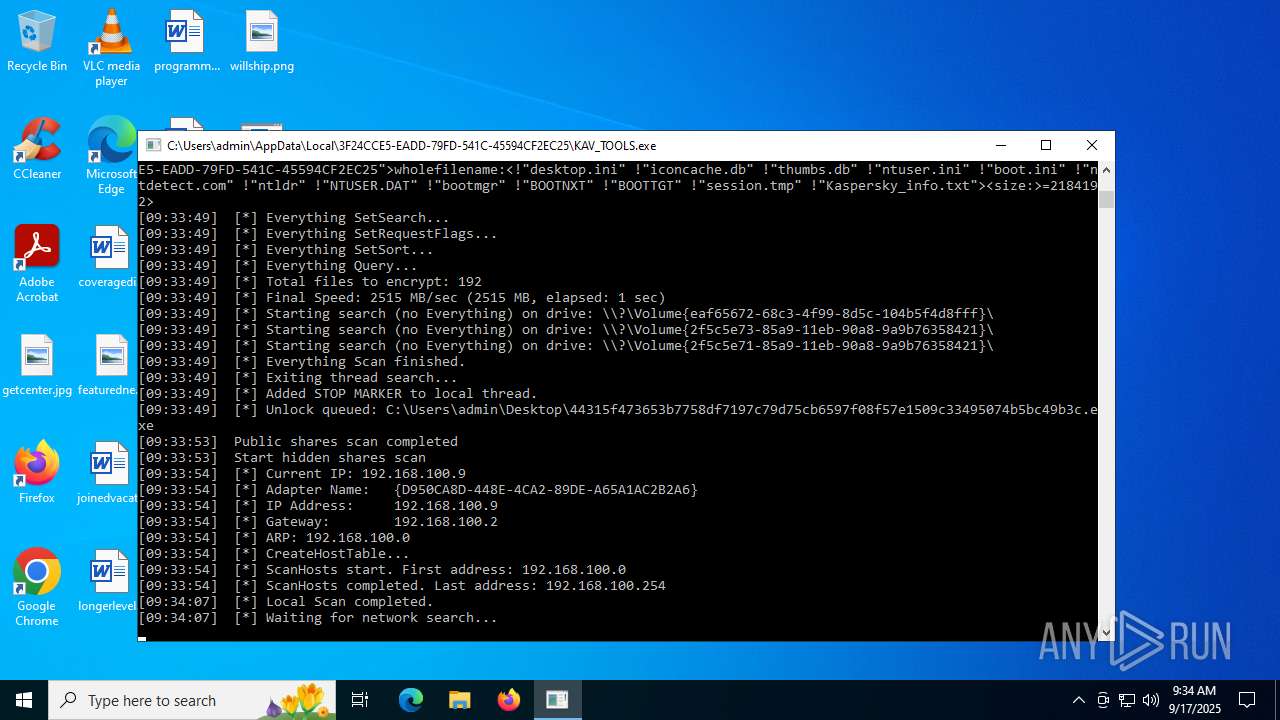
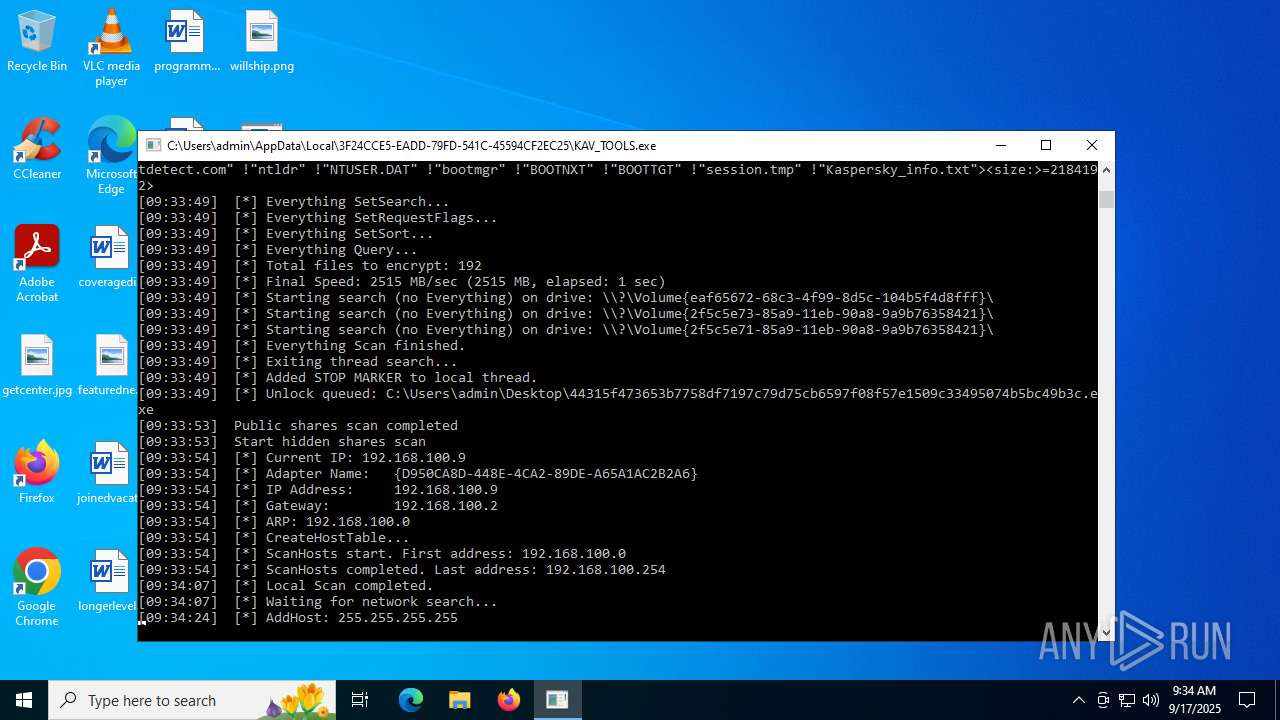
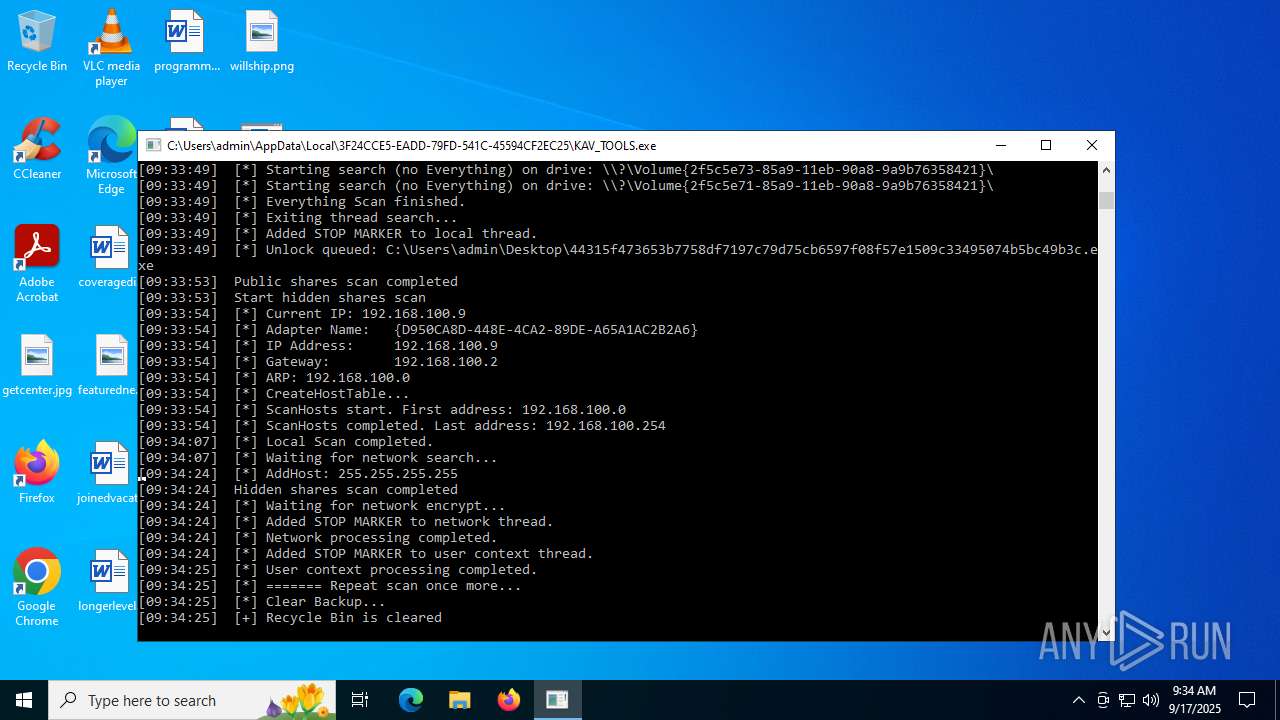
MIMIC mutex has been found
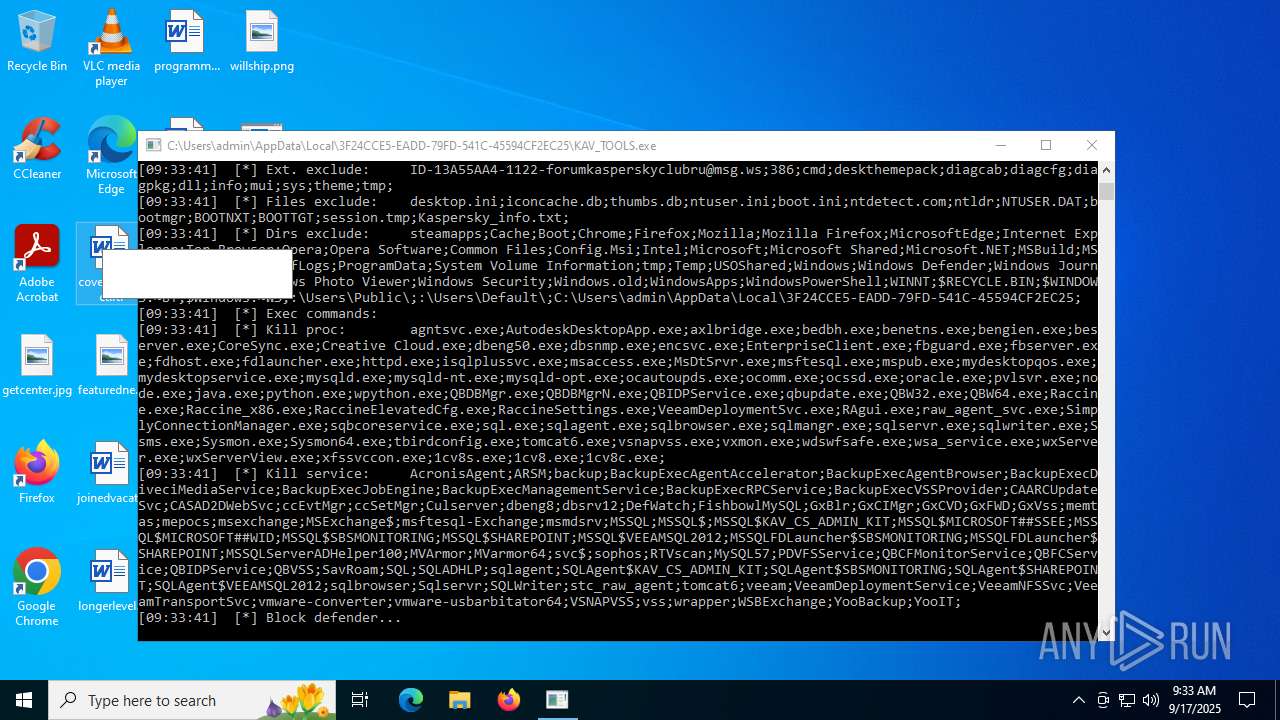
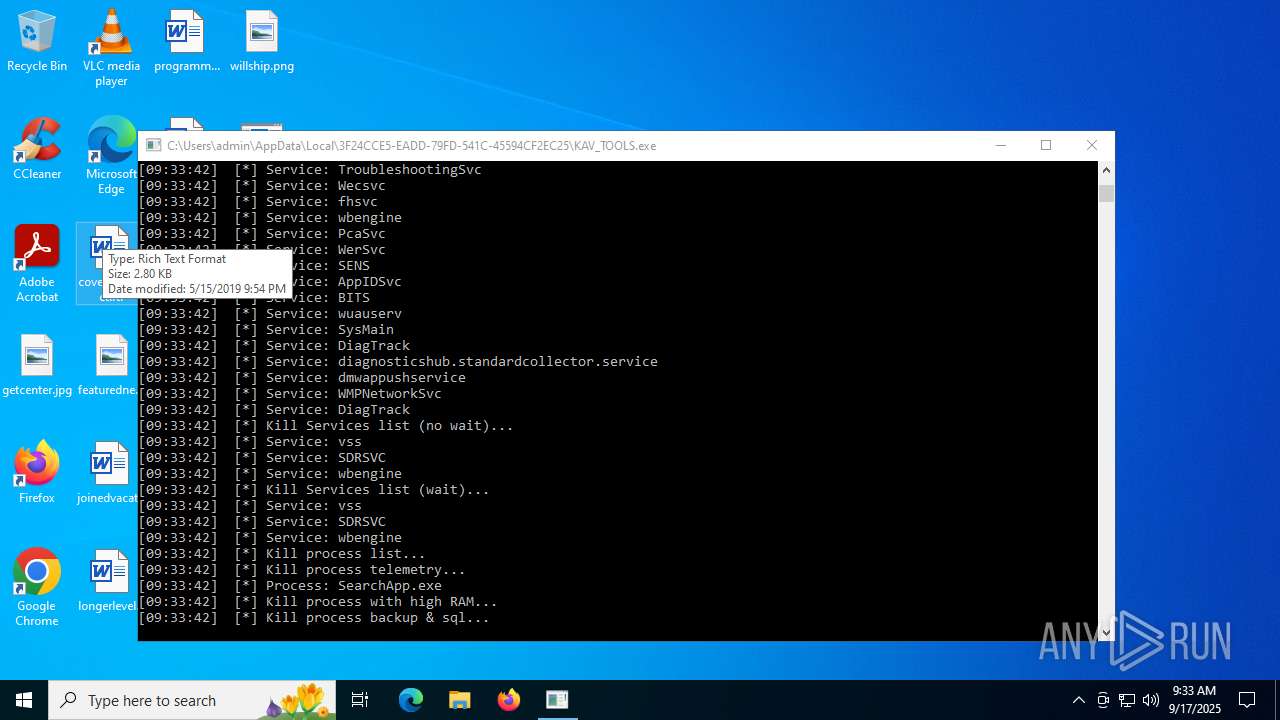
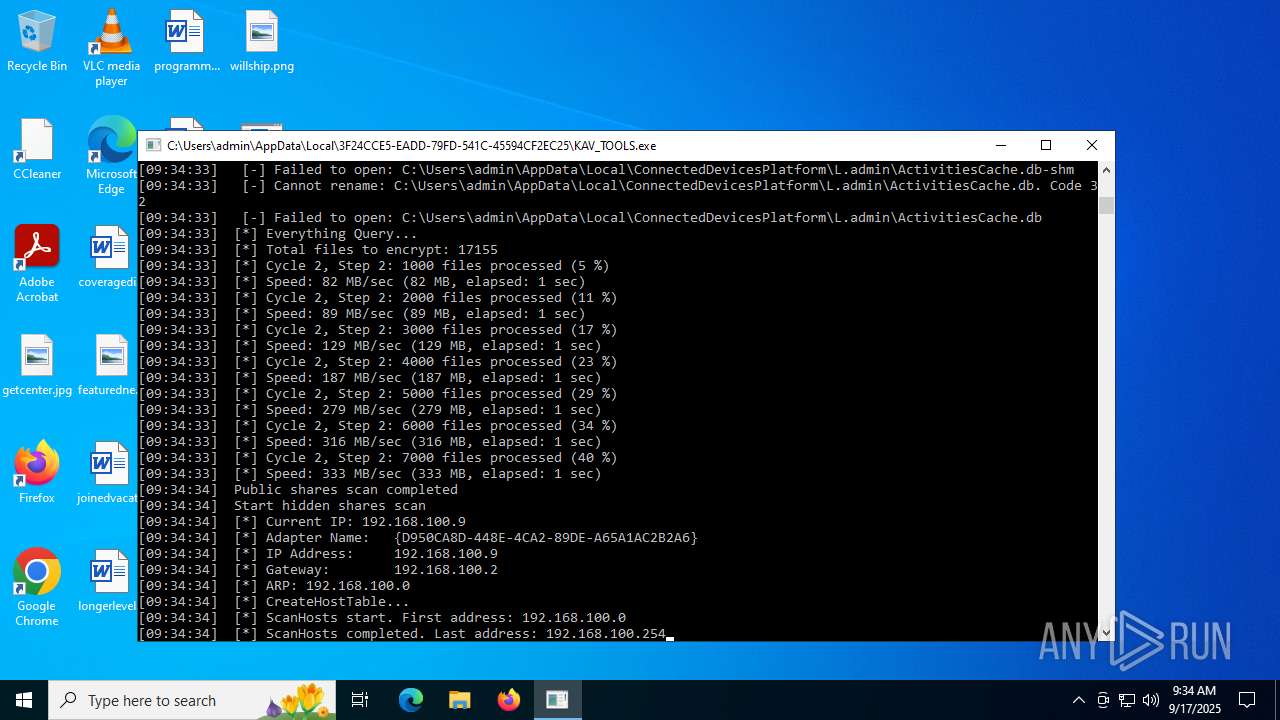
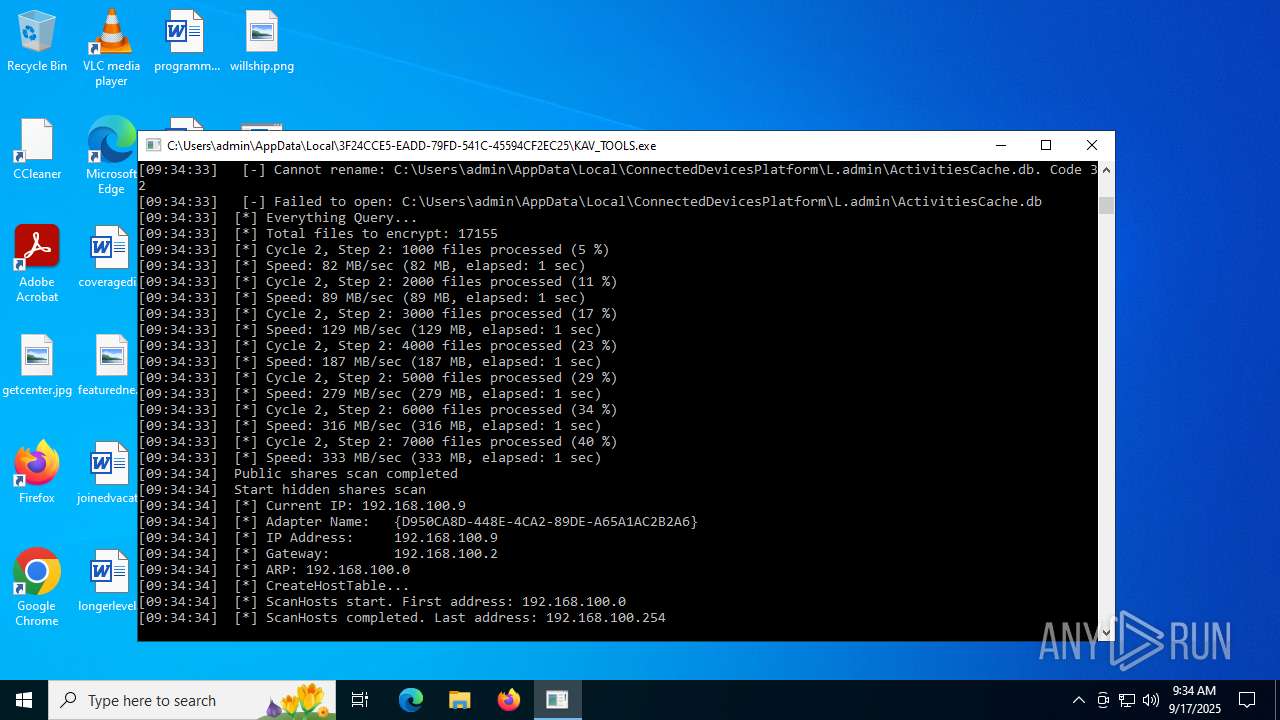
- KAV_TOOLS.exe (PID: 1644)
- KAV_TOOLS.exe (PID: 4836)
- KAV_TOOLS.exe (PID: 3644)
Changes image file execution options
- KAV_TOOLS.exe (PID: 1644)
Executing a file with an untrusted certificate
- DC.exe (PID: 6408)
- DC.exe (PID: 7764)
- DC.exe (PID: 8052)
Disables Windows Defender
- DC.exe (PID: 6408)
- DC.exe (PID: 7764)
- DC.exe (PID: 8052)
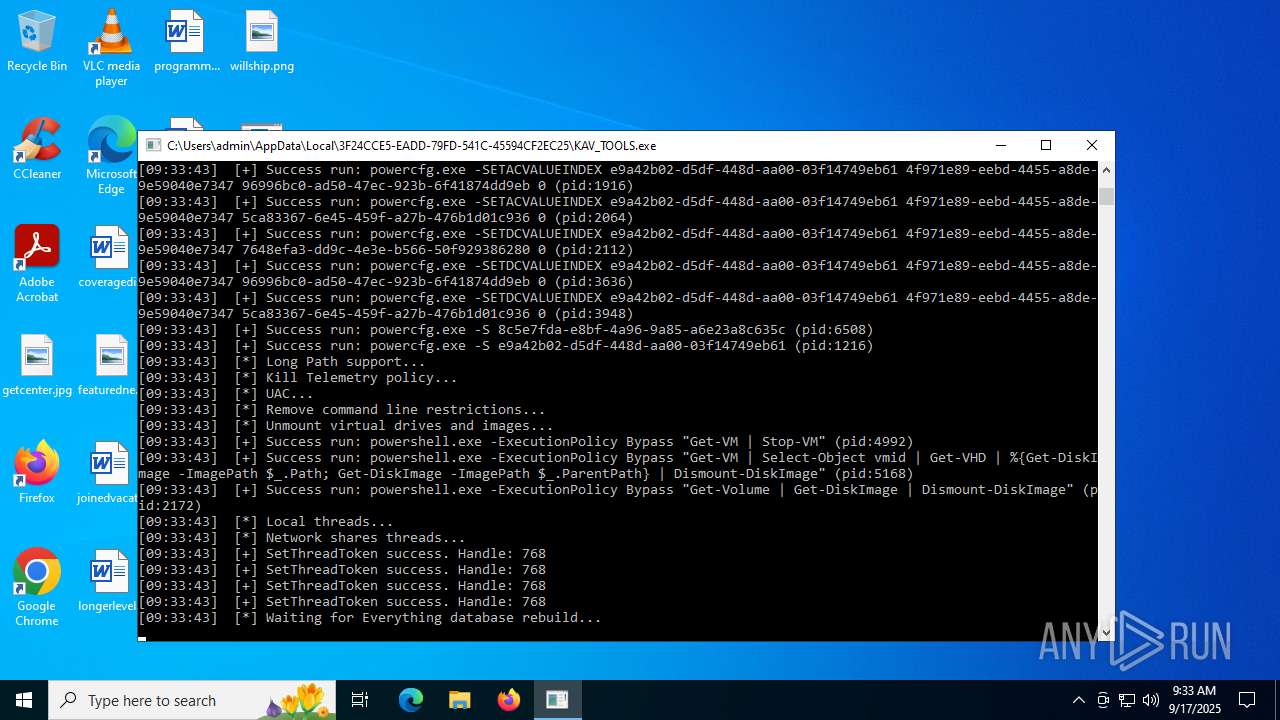
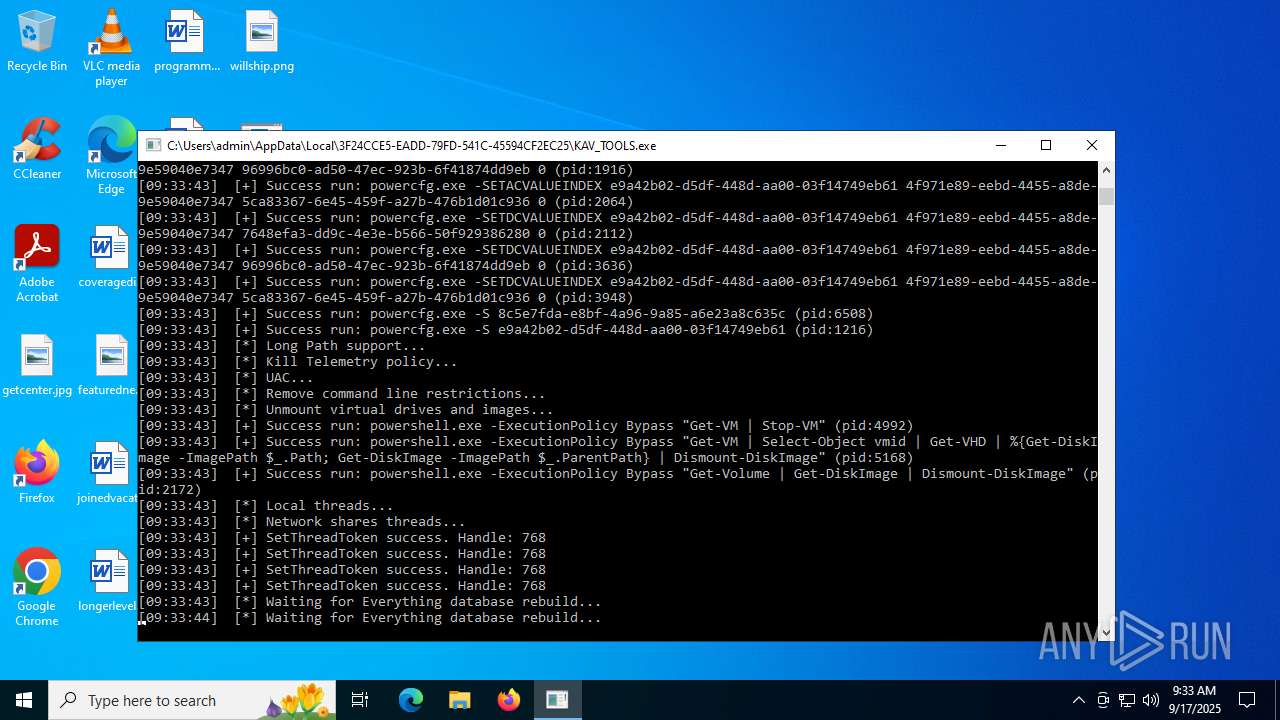
Bypass execution policy to execute commands
- powershell.exe (PID: 4992)
- powershell.exe (PID: 5168)
- powershell.exe (PID: 2172)
Disables the Shutdown in the Start menu
- KAV_TOOLS.exe (PID: 1644)
Changes powershell execution policy (Bypass)
- KAV_TOOLS.exe (PID: 1644)
Creates or modifies Windows services
- DC.exe (PID: 8052)
XORed URL has been found (YARA)
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
- KAV_TOOLS.exe (PID: 1644)
- KAV_TOOLS.exe (PID: 6232)
- KAV_TOOLS.exe (PID: 4836)
- KAV_TOOLS.exe (PID: 3644)
MIMIC has been detected (YARA)
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
- KAV_TOOLS.exe (PID: 1644)
- KAV_TOOLS.exe (PID: 6232)
- KAV_TOOLS.exe (PID: 4836)
- KAV_TOOLS.exe (PID: 3644)
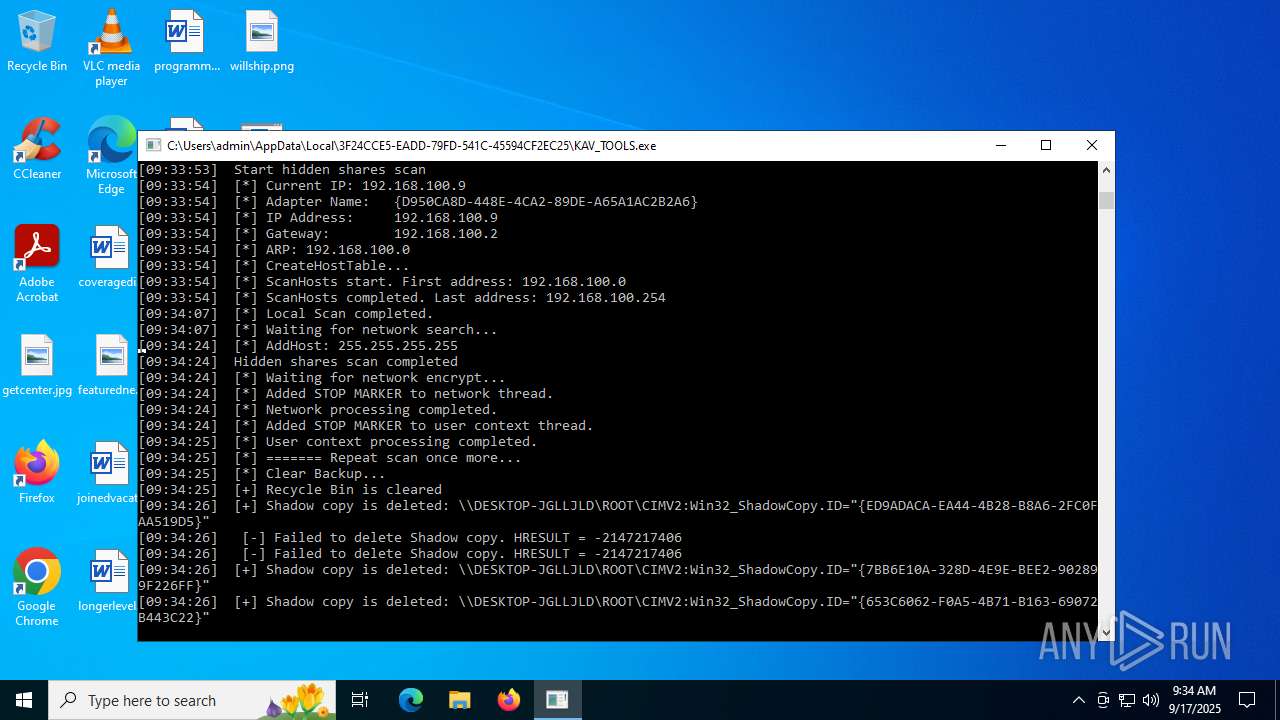
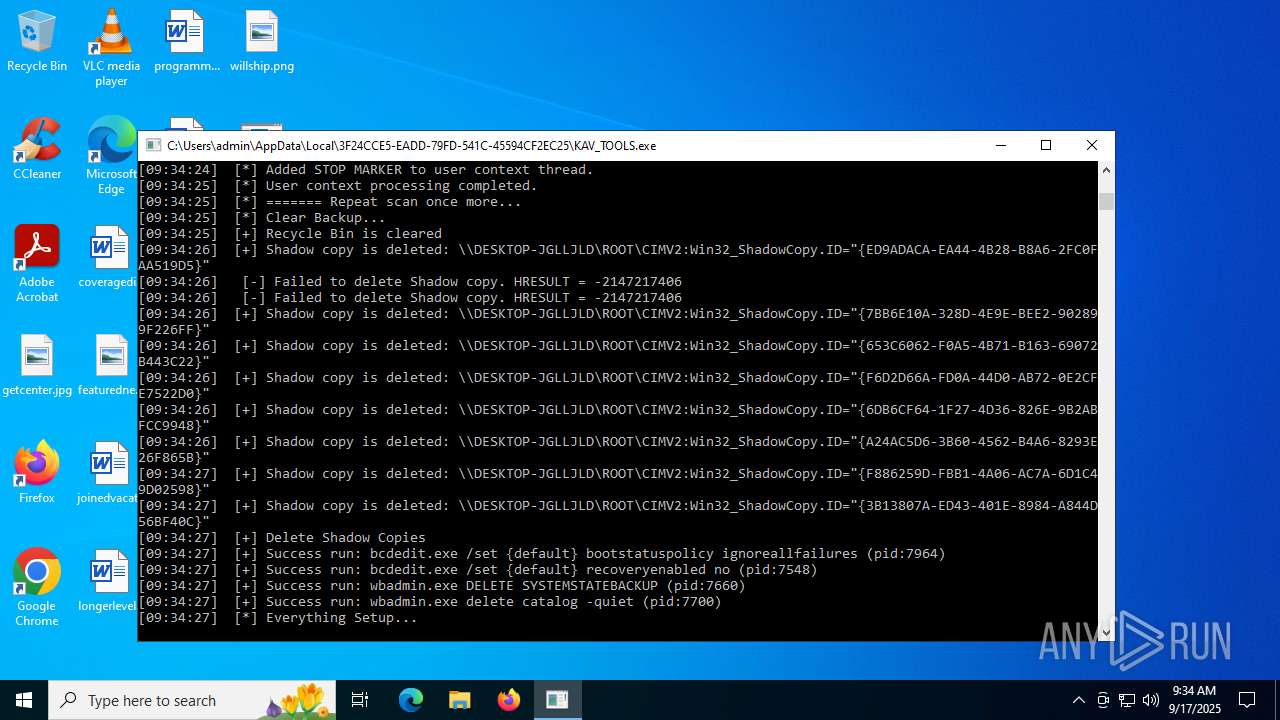
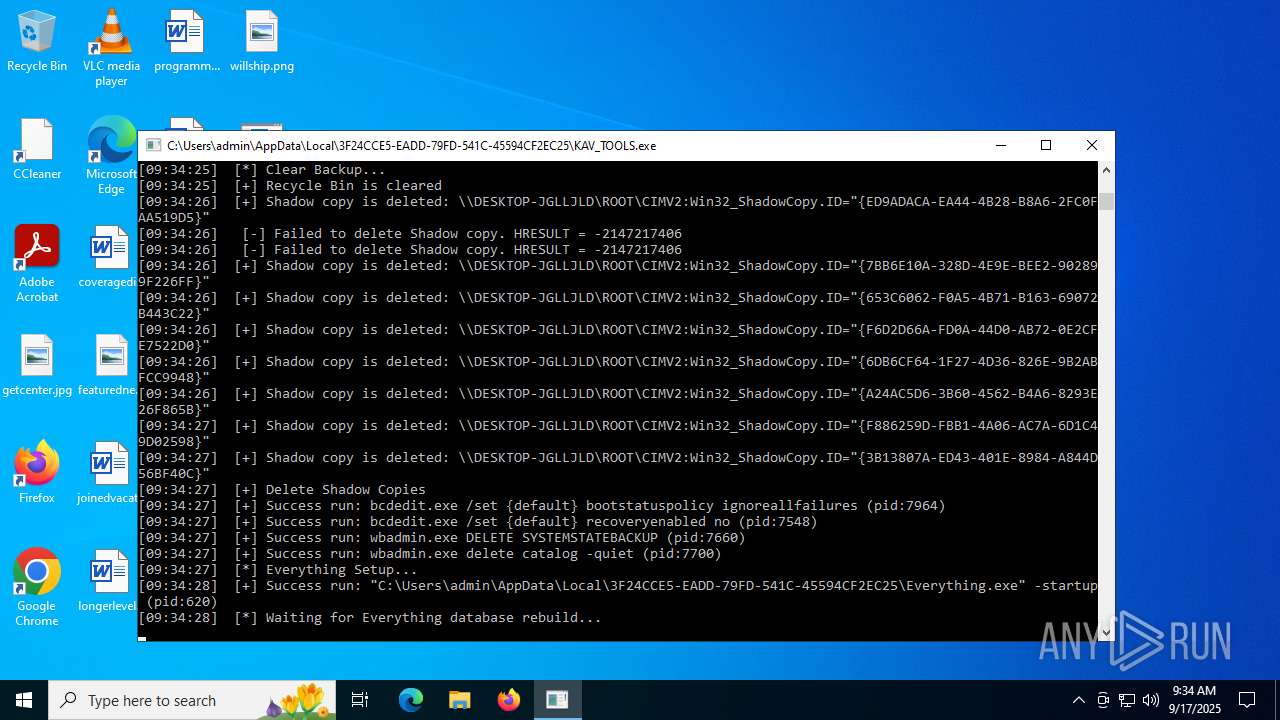
Deletes shadow copies
- KAV_TOOLS.exe (PID: 1644)
Deleting the backup catalog via wbadmin
- KAV_TOOLS.exe (PID: 1644)
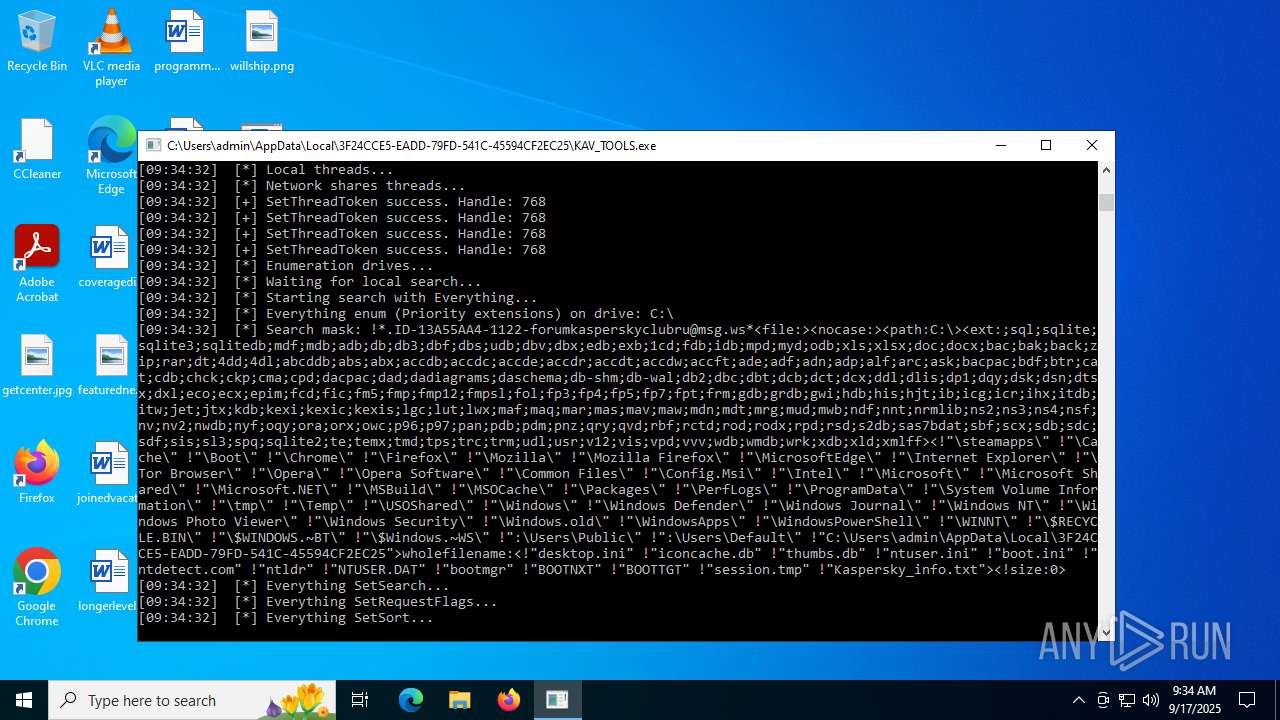
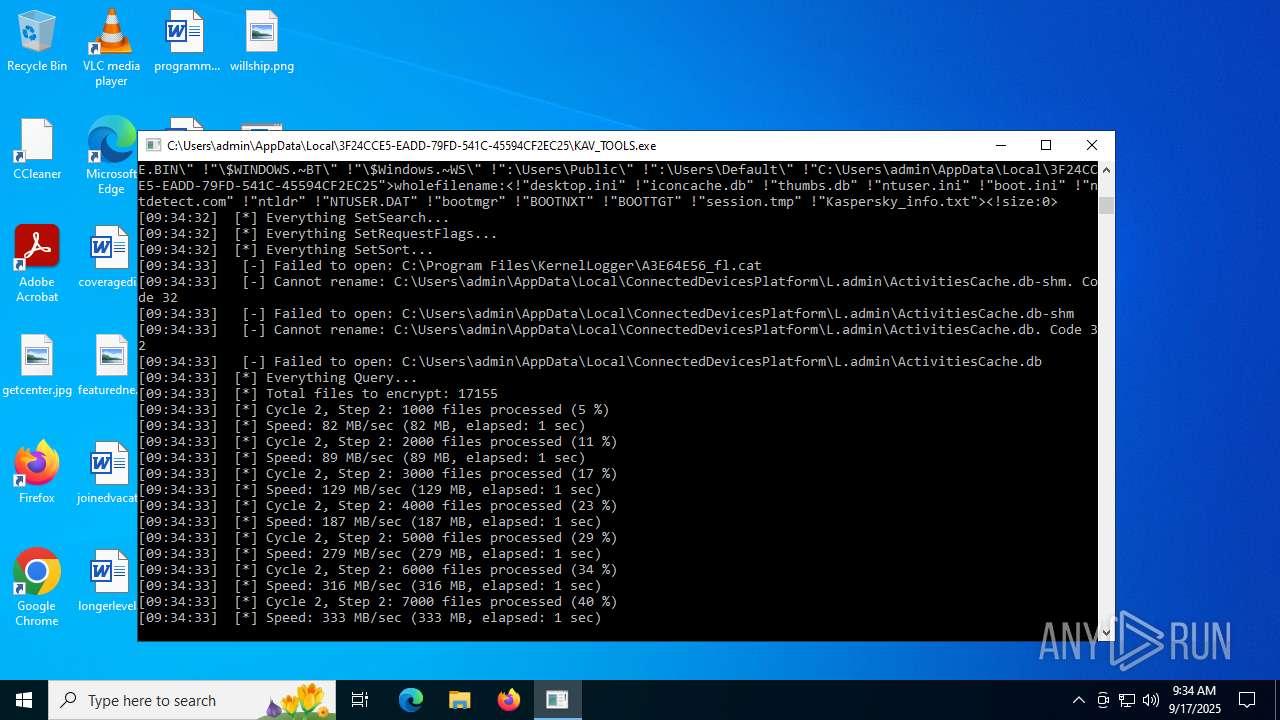
Renames files like ransomware
- KAV_TOOLS.exe (PID: 1644)
Using BCDEDIT.EXE to modify recovery options
- KAV_TOOLS.exe (PID: 1644)
SUSPICIOUS
Executable content was dropped or overwritten
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
- 7za.exe (PID: 5904)
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
- KAV_TOOLS.exe (PID: 1644)
Drops 7-zip archiver for unpacking
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
Reads security settings of Internet Explorer
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
Application launched itself
- KAV_TOOLS.exe (PID: 1644)
- DC.exe (PID: 6408)
- DC.exe (PID: 7764)
Creates or modifies Windows services
- KAV_TOOLS.exe (PID: 1644)
Uses powercfg.exe to modify the power settings
- KAV_TOOLS.exe (PID: 1644)
Starts POWERSHELL.EXE for commands execution
- KAV_TOOLS.exe (PID: 1644)
There is functionality for taking screenshot (YARA)
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
- Everything.exe (PID: 2148)
Process drops legitimate windows executable
- KAV_TOOLS.exe (PID: 1644)
Executes as Windows Service
- VSSVC.exe (PID: 3720)
- vds.exe (PID: 6096)
- wbengine.exe (PID: 3504)
INFO
The sample compiled with english language support
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
- 7za.exe (PID: 5904)
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
- KAV_TOOLS.exe (PID: 1644)
Create files in a temporary directory
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
- 7za.exe (PID: 5904)
- DC.exe (PID: 6408)
Checks supported languages
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
- 7za.exe (PID: 3000)
- 7za.exe (PID: 5904)
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
- KAV_TOOLS.exe (PID: 1644)
- Everything.exe (PID: 2148)
- KAV_TOOLS.exe (PID: 6232)
- KAV_TOOLS.exe (PID: 4836)
- KAV_TOOLS.exe (PID: 4120)
- KAV_TOOLS.exe (PID: 3644)
- DC.exe (PID: 6408)
- DC.exe (PID: 7764)
- DC.exe (PID: 8052)
- Everything.exe (PID: 620)
Process checks computer location settings
- 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe (PID: 2320)
Creates files or folders in the user directory
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
- KAV_TOOLS.exe (PID: 1644)
- Everything.exe (PID: 2148)
Launching a file from a Registry key
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 6452)
EVERYTHING mutex has been found
- Everything.exe (PID: 2148)
- Everything.exe (PID: 620)
Manual execution by a user
- KAV_TOOLS.exe (PID: 4120)
Reads mouse settings
- DC.exe (PID: 6408)
- DC.exe (PID: 7764)
- DC.exe (PID: 8052)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4992)
- powershell.exe (PID: 5168)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2172)
The sample compiled with japanese language support
- KAV_TOOLS.exe (PID: 1644)
Checks proxy server information
- slui.exe (PID: 7980)
Reads the software policy settings
- slui.exe (PID: 7980)
Reads the machine GUID from the registry
- forumkasperskyclubru@msg.ws.exe (PID: 5556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5556) forumkasperskyclubru@msg.ws.exe
Decrypted-URLs (1)https://t.me/forumkasperskyclubru
(PID) Process(1644) KAV_TOOLS.exe
Decrypted-URLs (1)https://t.me/forumkasperskyclubru
(PID) Process(6232) KAV_TOOLS.exe
Decrypted-URLs (1)https://t.me/forumkasperskyclubru
(PID) Process(4836) KAV_TOOLS.exe
Decrypted-URLs (1)https://t.me/forumkasperskyclubru
(PID) Process(3644) KAV_TOOLS.exe
Decrypted-URLs (1)https://t.me/forumkasperskyclubru
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 00:38:51+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 101888 |
| InitializedDataSize: | 19456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1942f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
233
Monitored processes
84
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | KAV_TOOLS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\Everything.exe" -startup | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\Everything.exe | — | KAV_TOOLS.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 628 | C:\WINDOWS\System32\Systray.exe "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\System32\systray.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Systray .exe stub Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | cmd.exe /c DC.exe /D | C:\Windows\SysWOW64\cmd.exe | — | KAV_TOOLS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | powercfg.exe -S e9a42b02-d5df-448d-aa00-03f14749eb61 | C:\Windows\System32\powercfg.exe | — | KAV_TOOLS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 896
Read events
24 751
Write events
125
Delete events
20
Modification events
| (PID) Process: | (5556) forumkasperskyclubru@msg.ws.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | KAV_TOOLS |
Value: "C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\KAV_TOOLS.exe" | |||
| (PID) Process: | (6452) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6408) DC.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe |
| Operation: | write | Name: | Debugger |
Value: C:\WINDOWS\System32\Systray.exe | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\tasklist.exe |
| Operation: | write | Name: | Debugger |
Value: C:\WINDOWS\System32\Systray.exe | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskkill.exe |
| Operation: | write | Name: | Debugger |
Value: C:\WINDOWS\System32\Systray.exe | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\perfmon.exe |
| Operation: | write | Name: | Debugger |
Value: C:\WINDOWS\System32\Systray.exe | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | HidePowerOptions |
Value: 1 | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | HidePowerOptions |
Value: 1 | |||
| (PID) Process: | (1644) KAV_TOOLS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | shutdownwithoutlogon |
Value: 0 | |||
Executable files
76
Suspicious files
822
Text files
57
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5904 | 7za.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Everything.ini | text | |
MD5:742C2400F2DE964D0CCE4A8DABADD708 | SHA256:2FEFB69E4B2310BE5E09D329E8CF1BEBD1F9E18884C8C2A38AF8D7EA46BD5E01 | |||
| 5904 | 7za.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\forumkasperskyclubru@msg.ws.exe | executable | |
MD5:C0CD51D66614B9EDBF46F74EDF60C22A | SHA256:0AD7E5B613EDD2309A323E14645C5C04503C9337F224948485593222B44ABDBA | |||
| 2320 | 44315f473653b7758df7197c79d75cb6597f08f57e1509c33495074b5bc49b3c.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Everything.exe | executable | |
MD5:C44487CE1827CE26AC4699432D15B42A | SHA256:4C83E46A29106AFBAF5279029D102B489D958781764289B61AB5B618A4307405 | |||
| 5556 | forumkasperskyclubru@msg.ws.exe | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\KAV_TOOLS.exe | executable | |
MD5:C0CD51D66614B9EDBF46F74EDF60C22A | SHA256:0AD7E5B613EDD2309A323E14645C5C04503C9337F224948485593222B44ABDBA | |||
| 5556 | forumkasperskyclubru@msg.ws.exe | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\Everything.exe | executable | |
MD5:C44487CE1827CE26AC4699432D15B42A | SHA256:4C83E46A29106AFBAF5279029D102B489D958781764289B61AB5B618A4307405 | |||
| 5556 | forumkasperskyclubru@msg.ws.exe | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\DC.exe | executable | |
MD5:AC34BA84A5054CD701EFAD5DD14645C9 | SHA256:C576F7F55C4C0304B290B15E70A638B037DF15C69577CD6263329C73416E490E | |||
| 5904 | 7za.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\xdel.exe | executable | |
MD5:803DF907D936E08FBBD06020C411BE93 | SHA256:E8EAA39E2ADFD49AB69D7BB8504CCB82A902C8B48FBC256472F36F41775E594C | |||
| 5556 | forumkasperskyclubru@msg.ws.exe | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\Everything32.dll | executable | |
MD5:3B03324537327811BBBAFF4AAFA4D75B | SHA256:8CAE8A9740D466E17F16481E68DE9CBD58265863C3924D66596048EDFD87E880 | |||
| 5556 | forumkasperskyclubru@msg.ws.exe | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\Everything2.ini | text | |
MD5:51014C0C06ACDD80F9AE4469E7D30A9E | SHA256:89AD2164717BD5F5F93FBB4CEBF0EFEB473097408FDDFC7FC7B924D790514DC5 | |||
| 5556 | forumkasperskyclubru@msg.ws.exe | C:\Users\admin\AppData\Local\3F24CCE5-EADD-79FD-541C-45594CF2EC25\7za.exe | executable | |
MD5:B93EB0A48C91A53BDA6A1A074A4B431E | SHA256:AB15A9B27EE2D69A8BC8C8D1F5F40F28CD568F5CBB28D36ED938110203F8D142 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
51
DNS requests
17
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 814 b | whitelisted |
472 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | QA | binary | 814 b | whitelisted |
— | — | POST | 400 | 20.190.160.20:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | unknown |
— | — | POST | 200 | 20.190.160.3:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | unknown |
— | — | POST | 400 | 20.190.160.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | unknown |
— | — | POST | 400 | 40.126.32.134:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | unknown |
— | — | POST | 400 | 20.190.160.66:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
472 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
472 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
1644 | KAV_TOOLS.exe | Not Suspicious Traffic | INFO [ANY.RUN] Possible SMB Connection Attempt |
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|