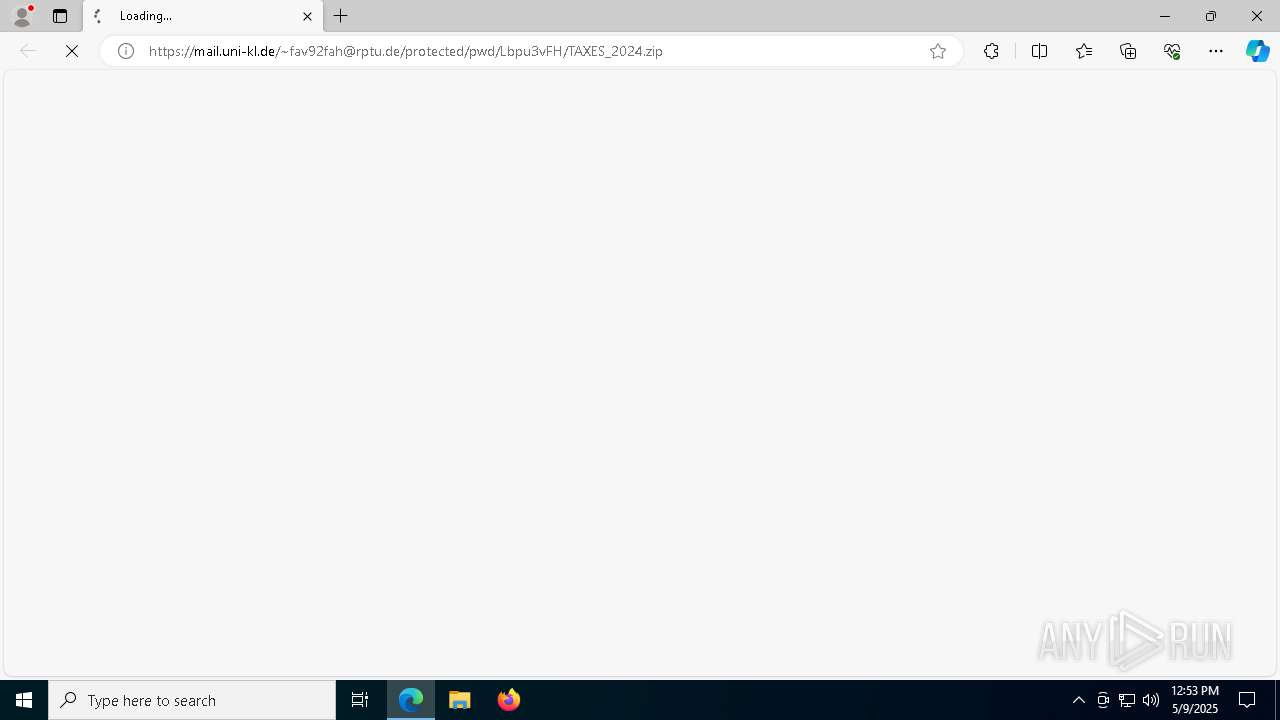
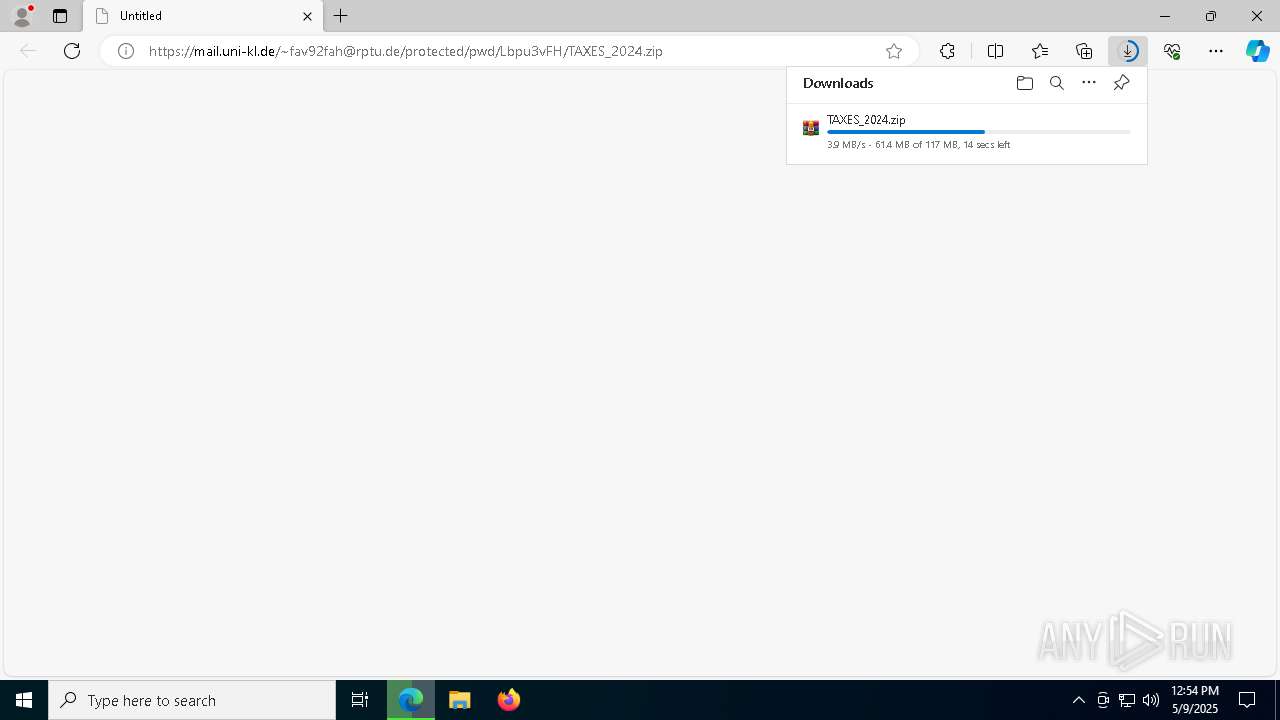
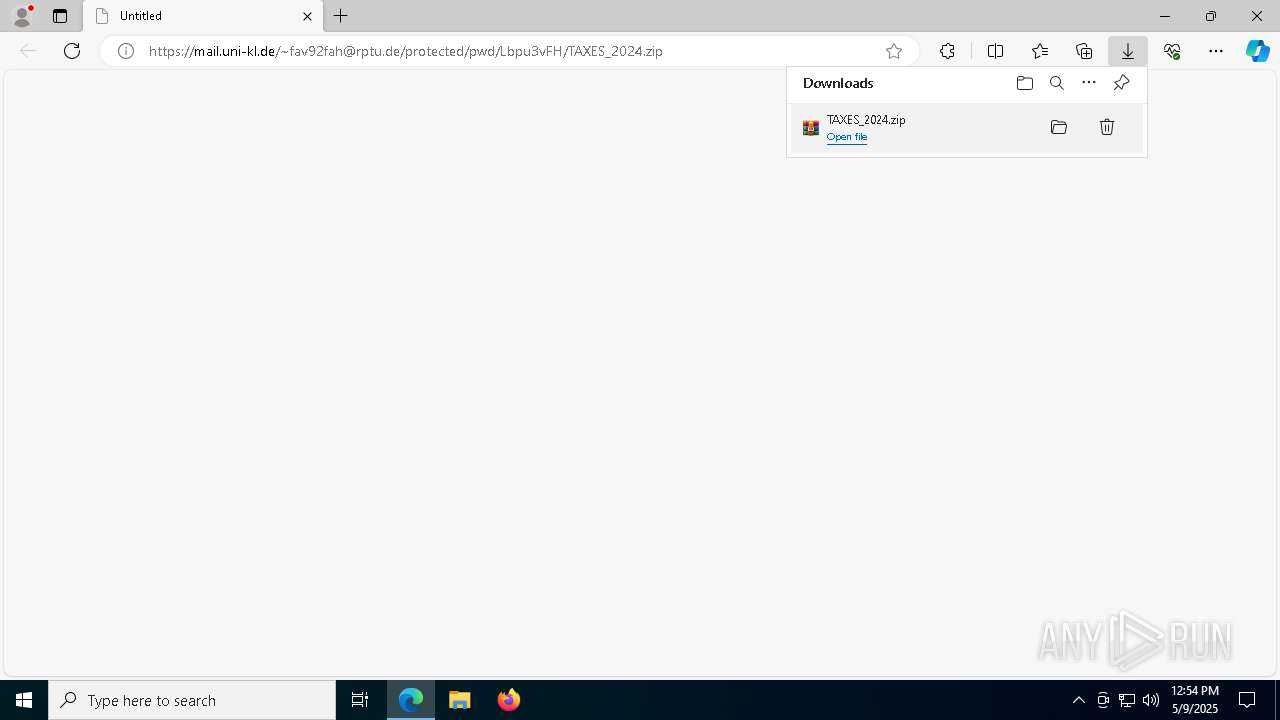
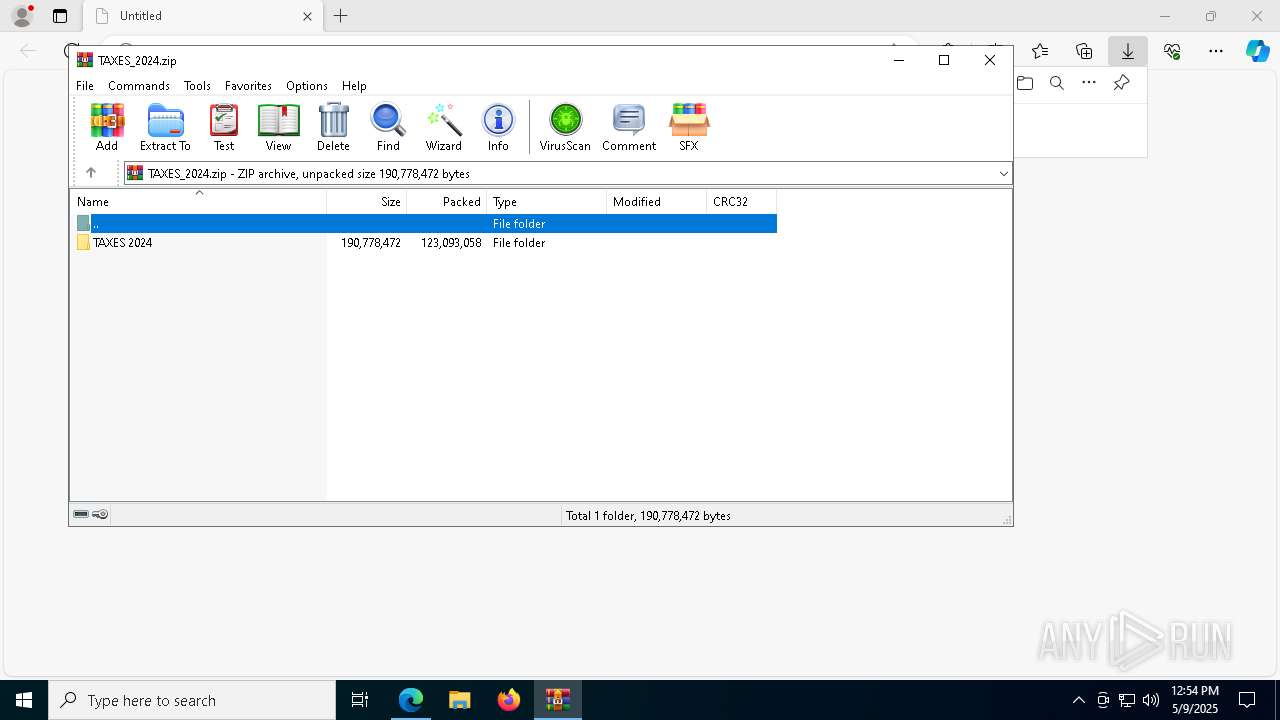
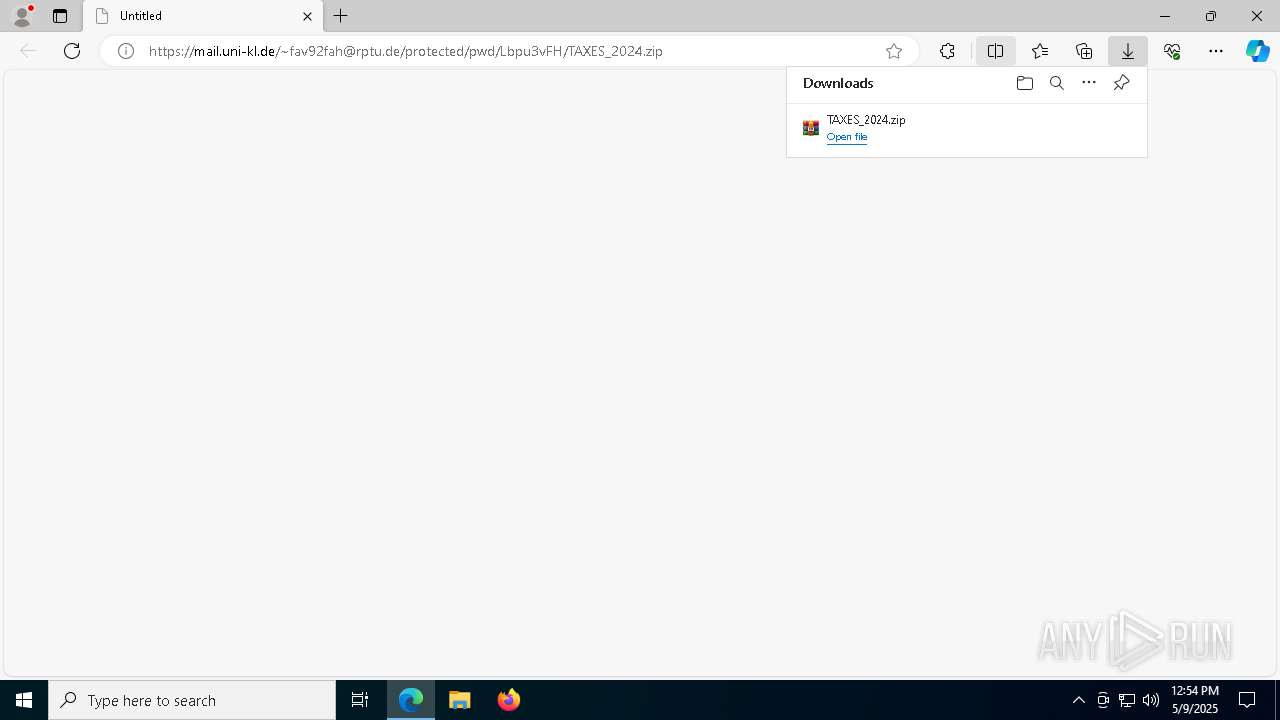
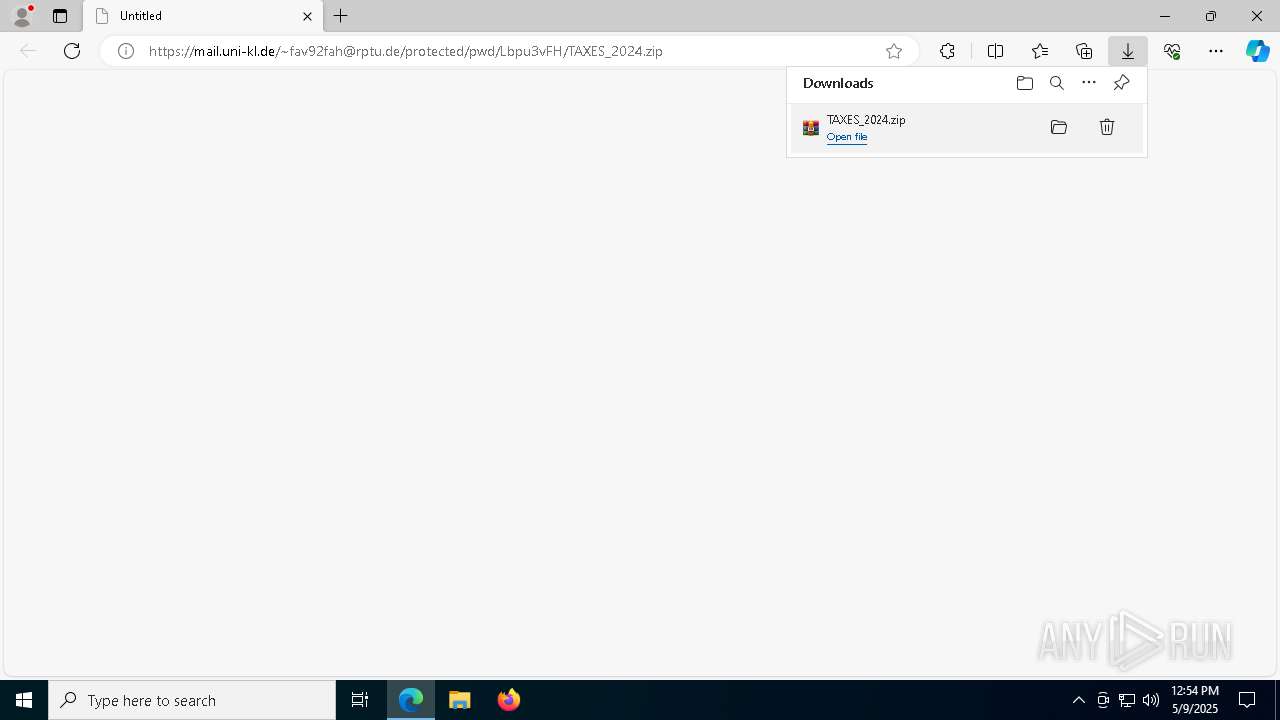
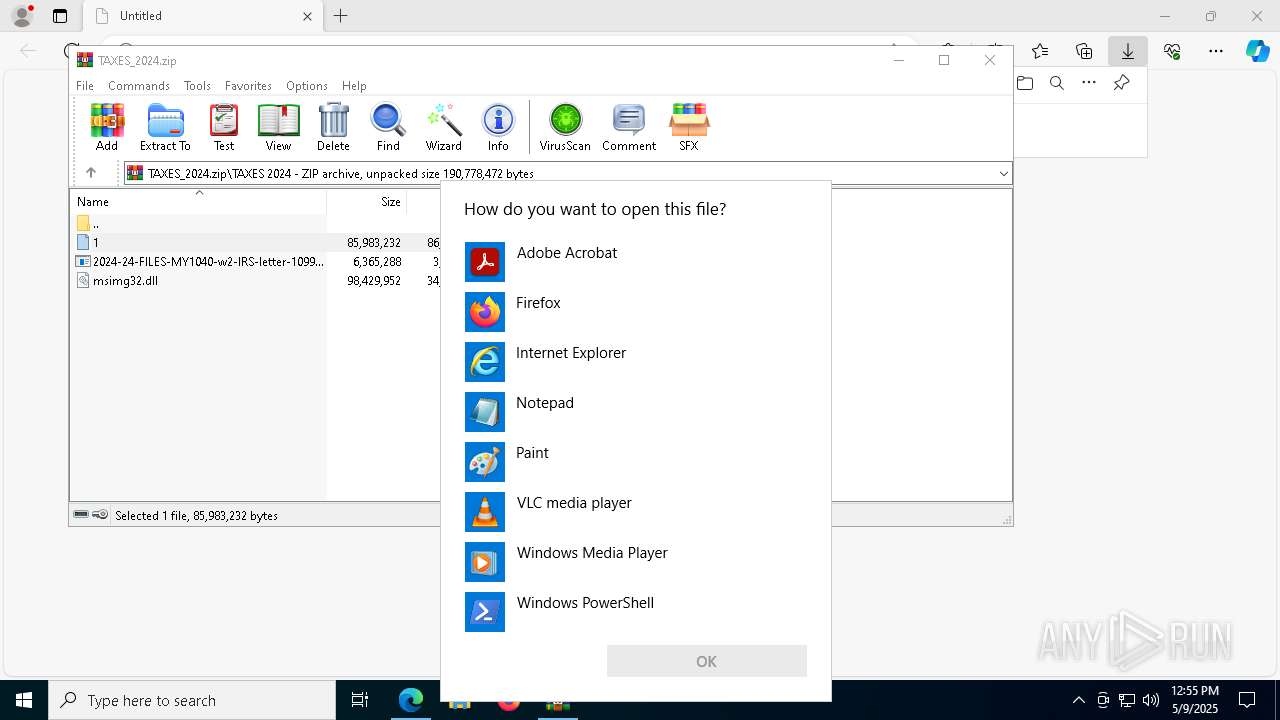
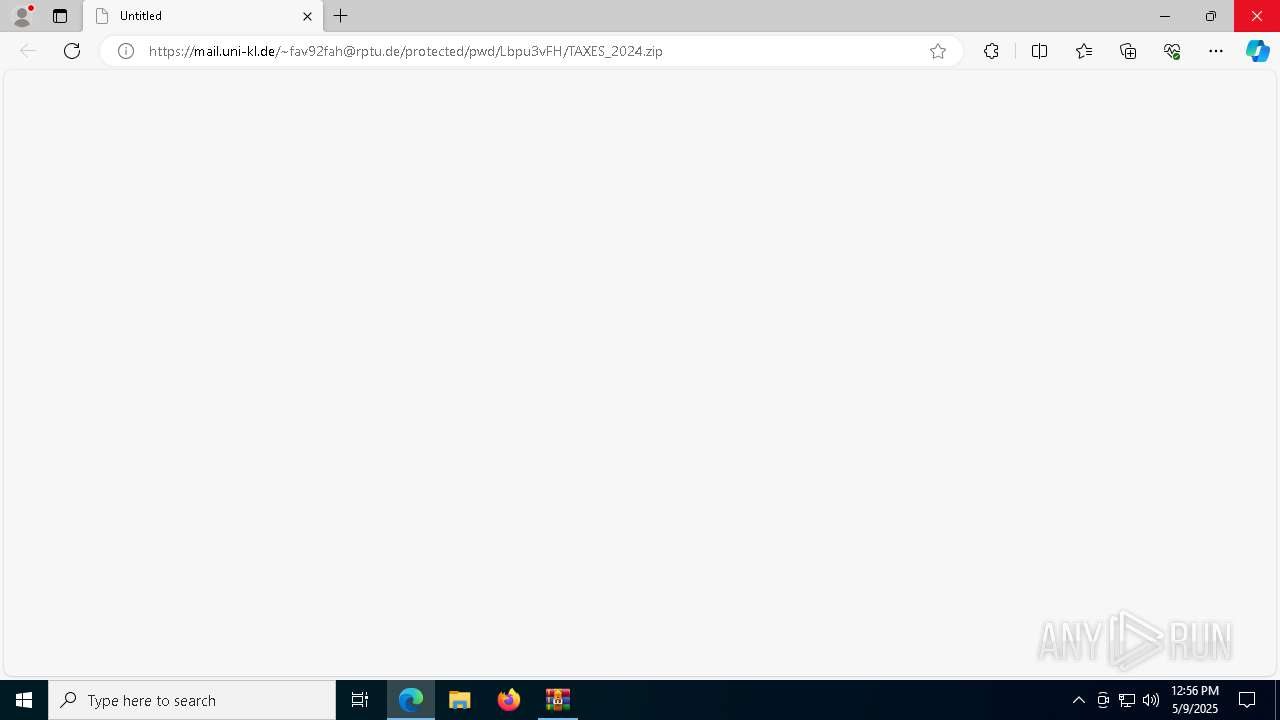
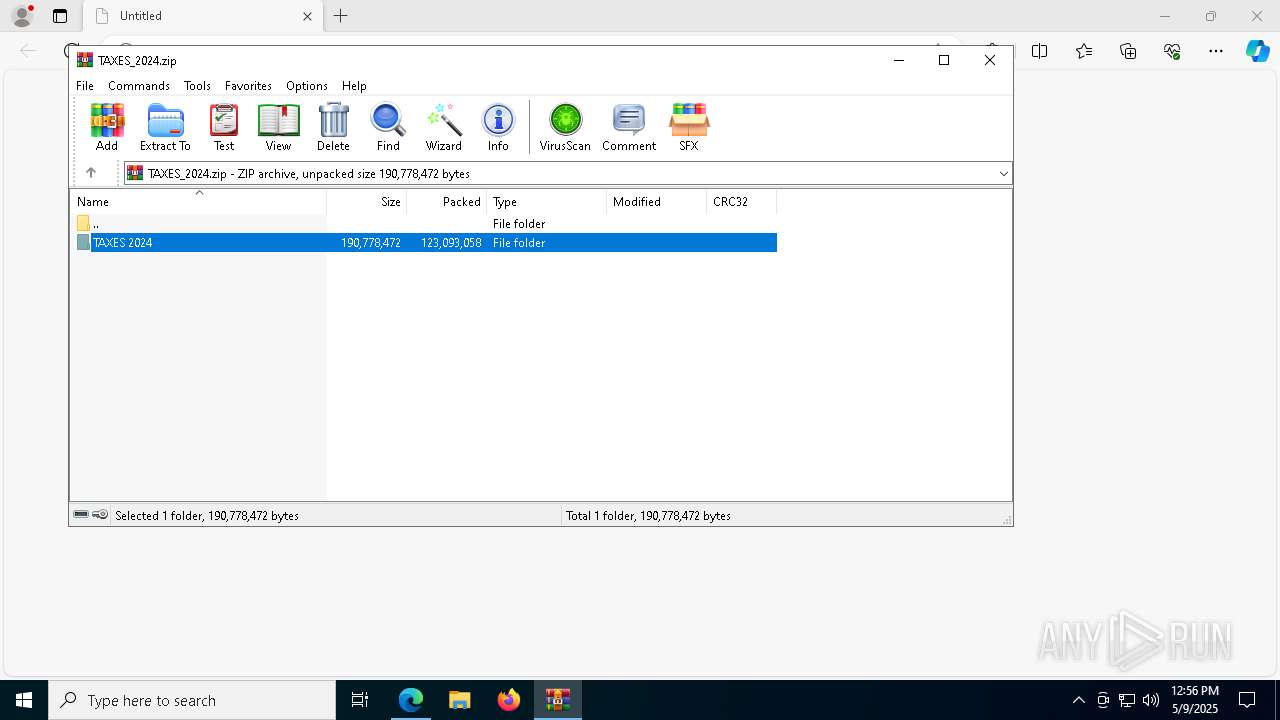
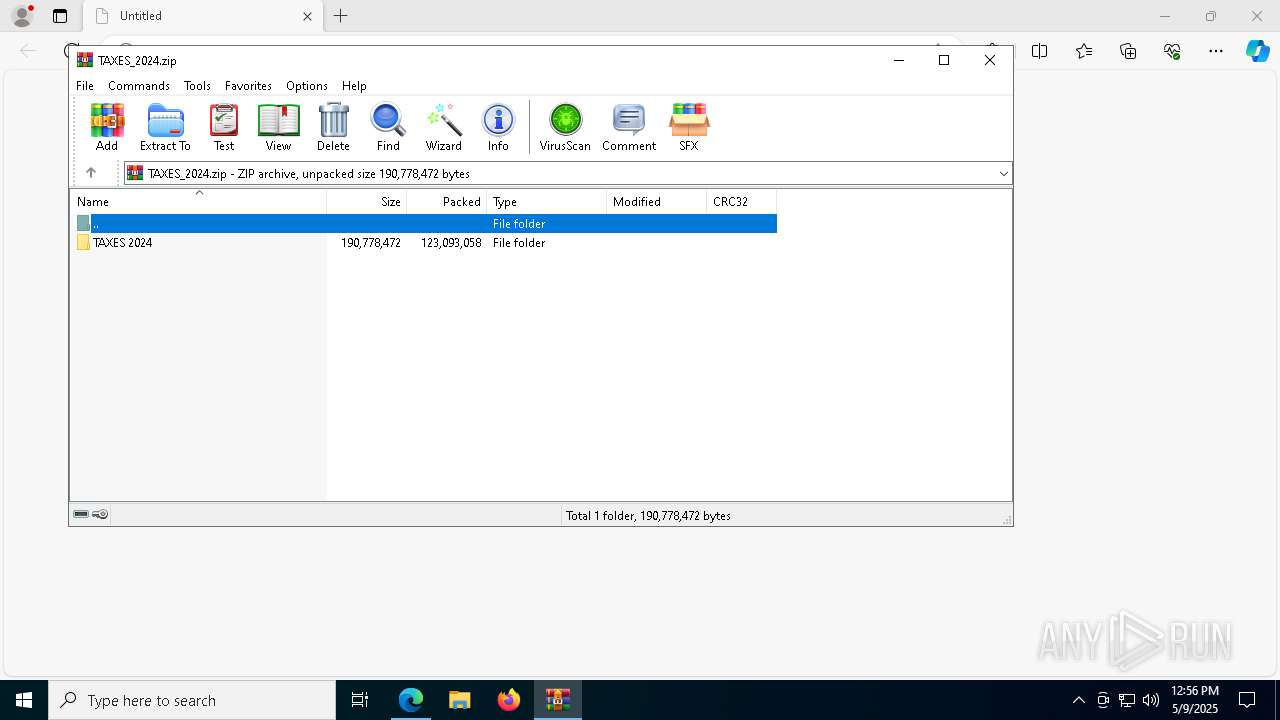
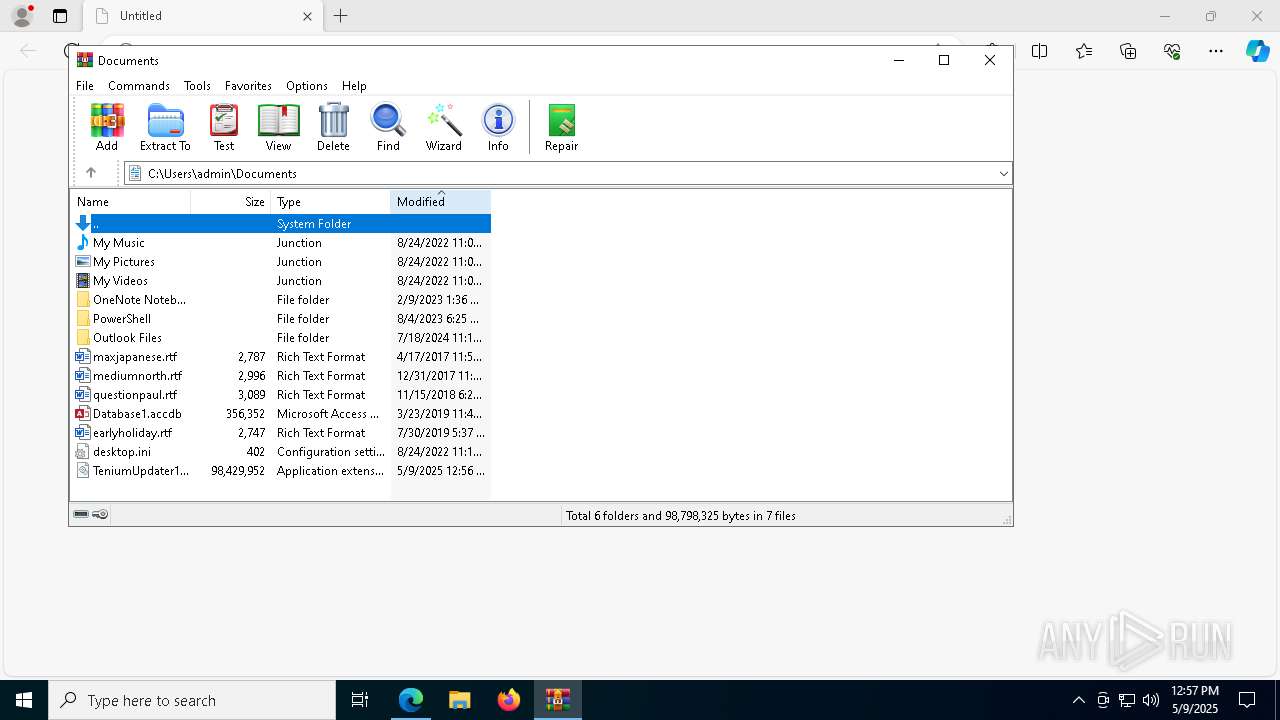
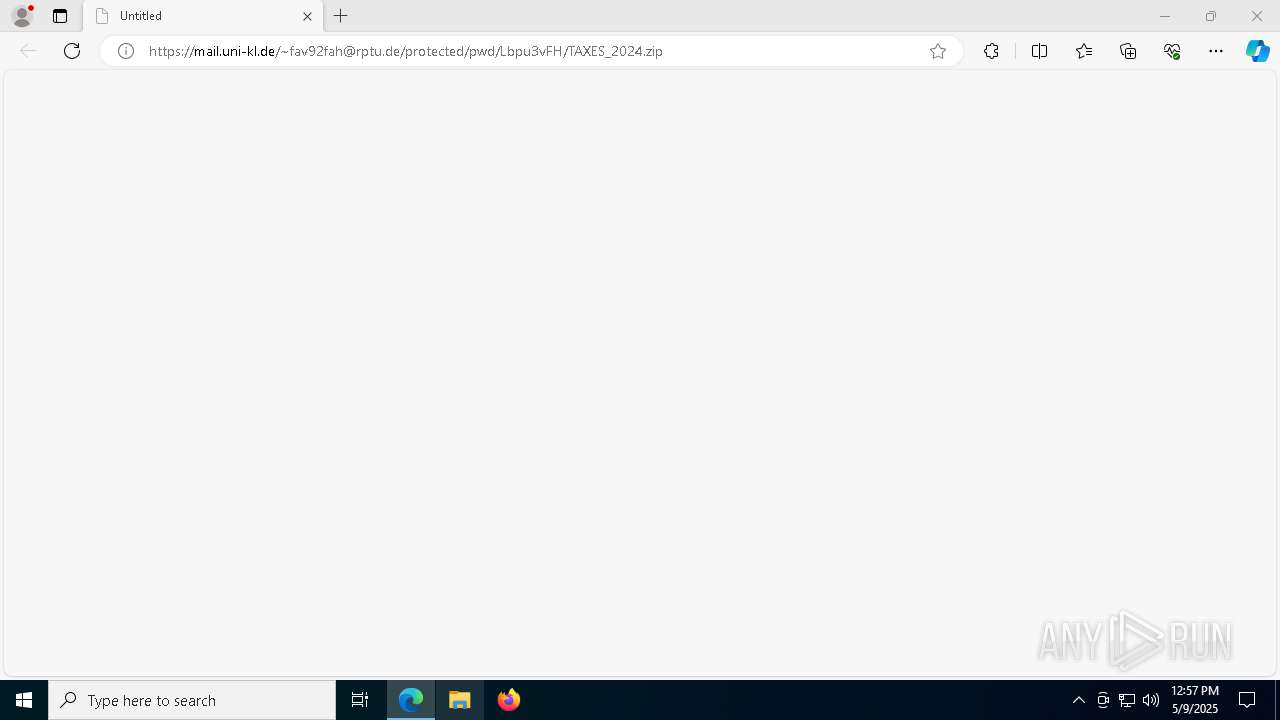
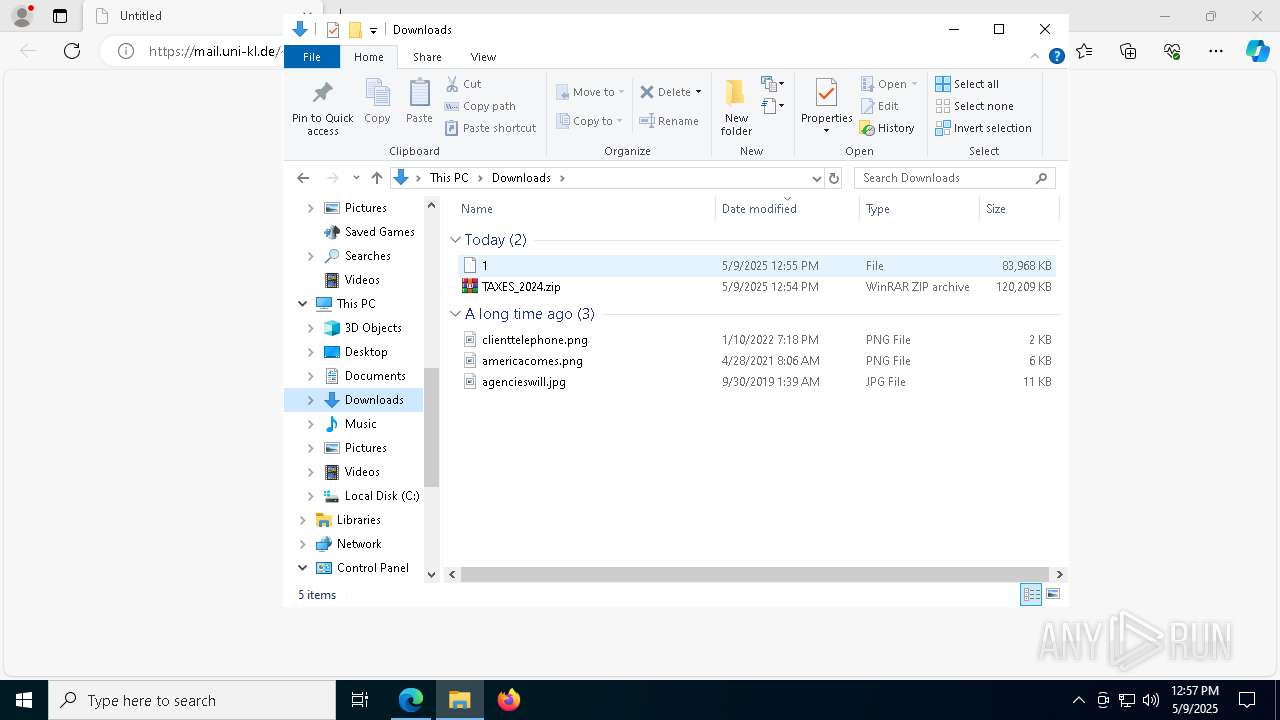
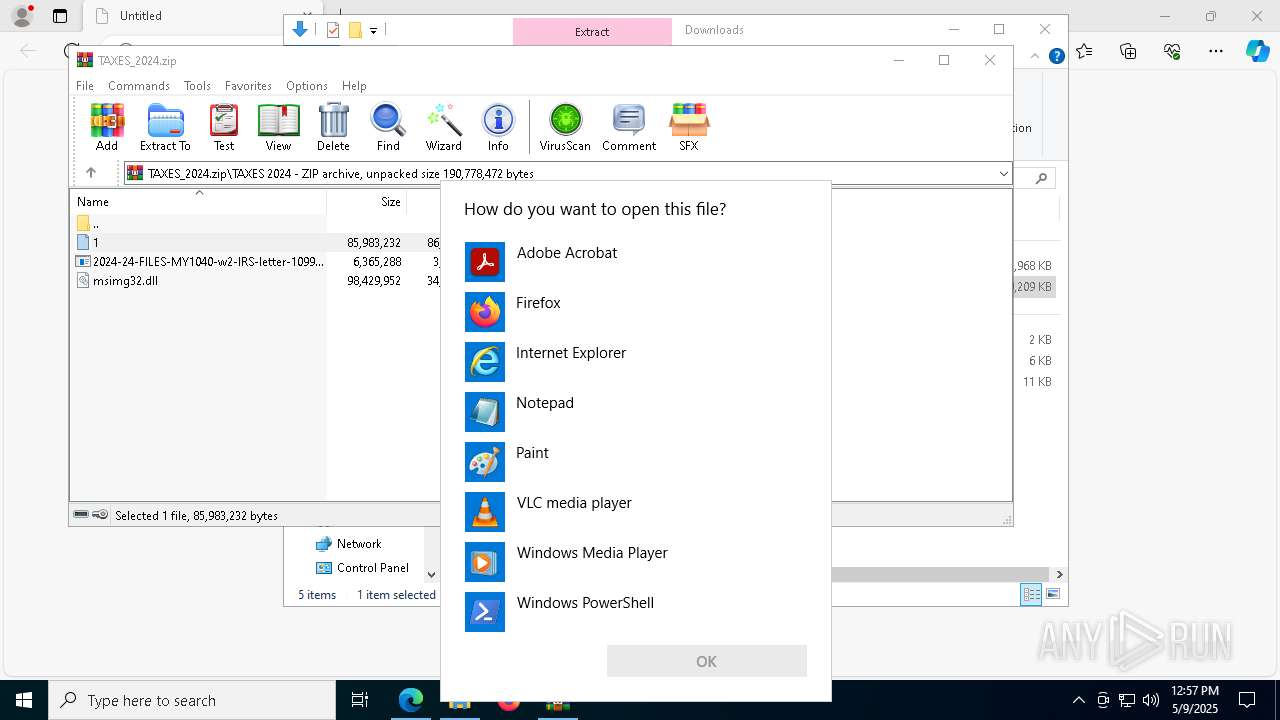
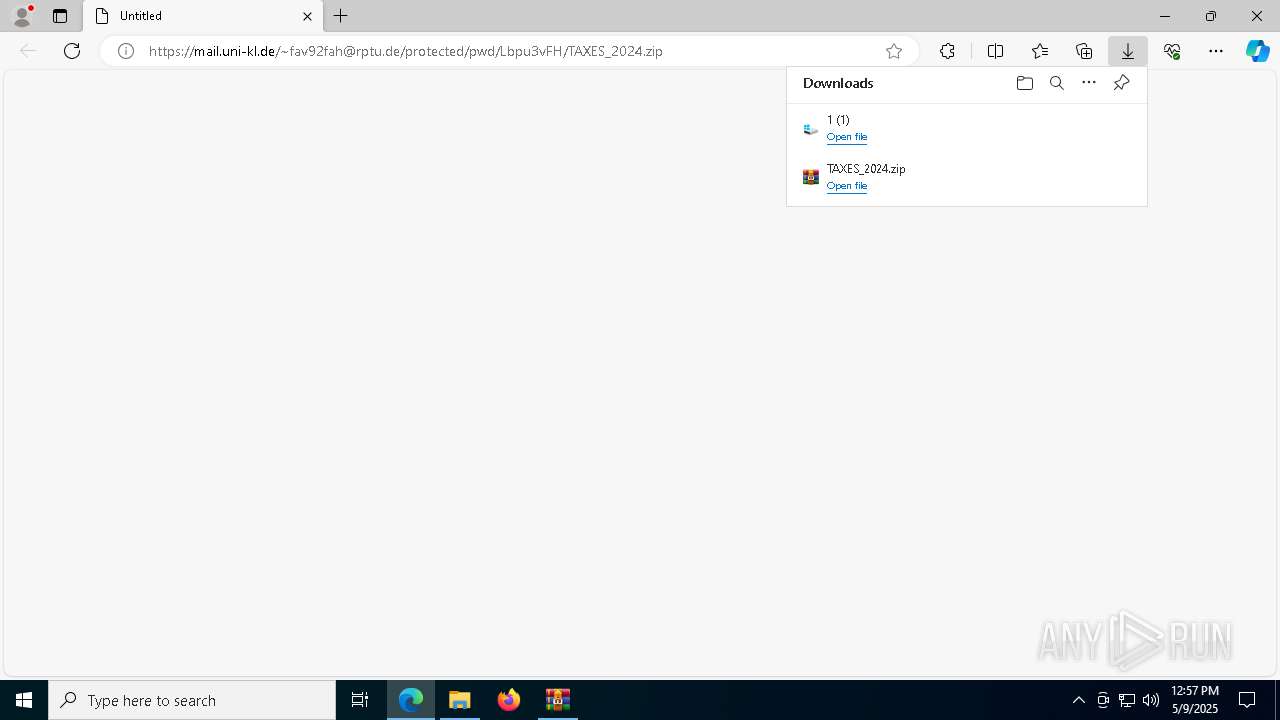
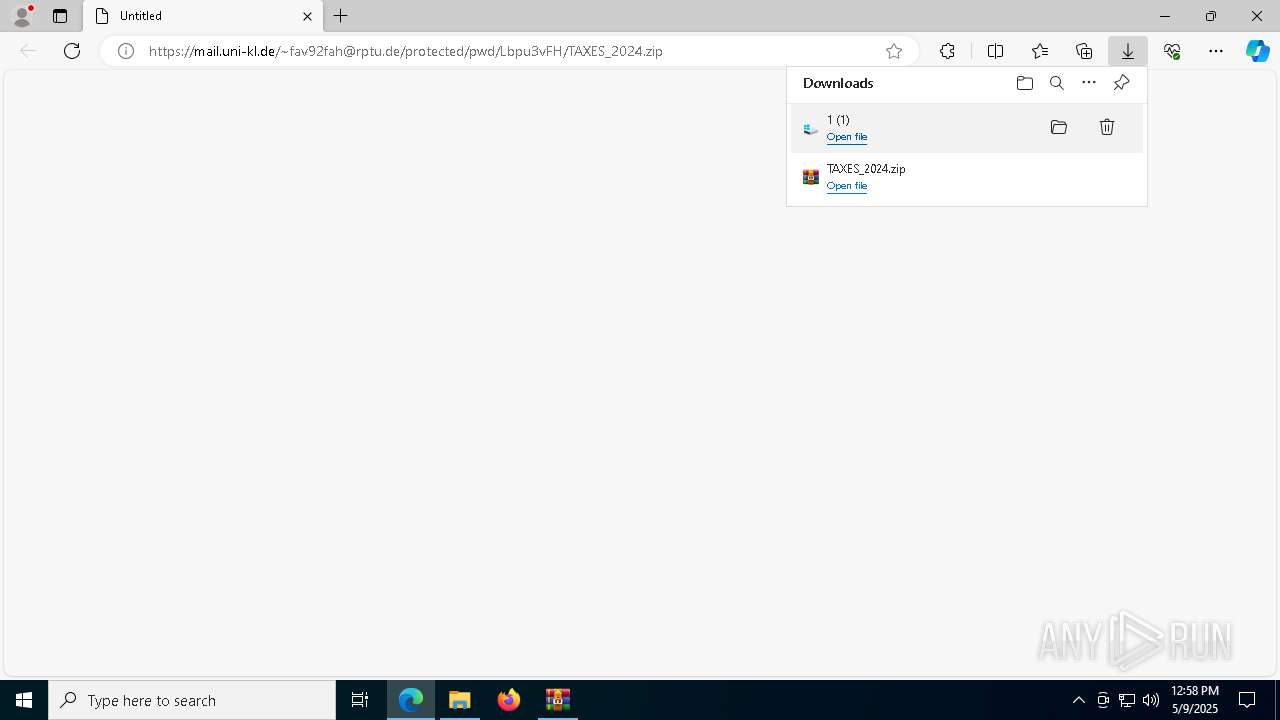
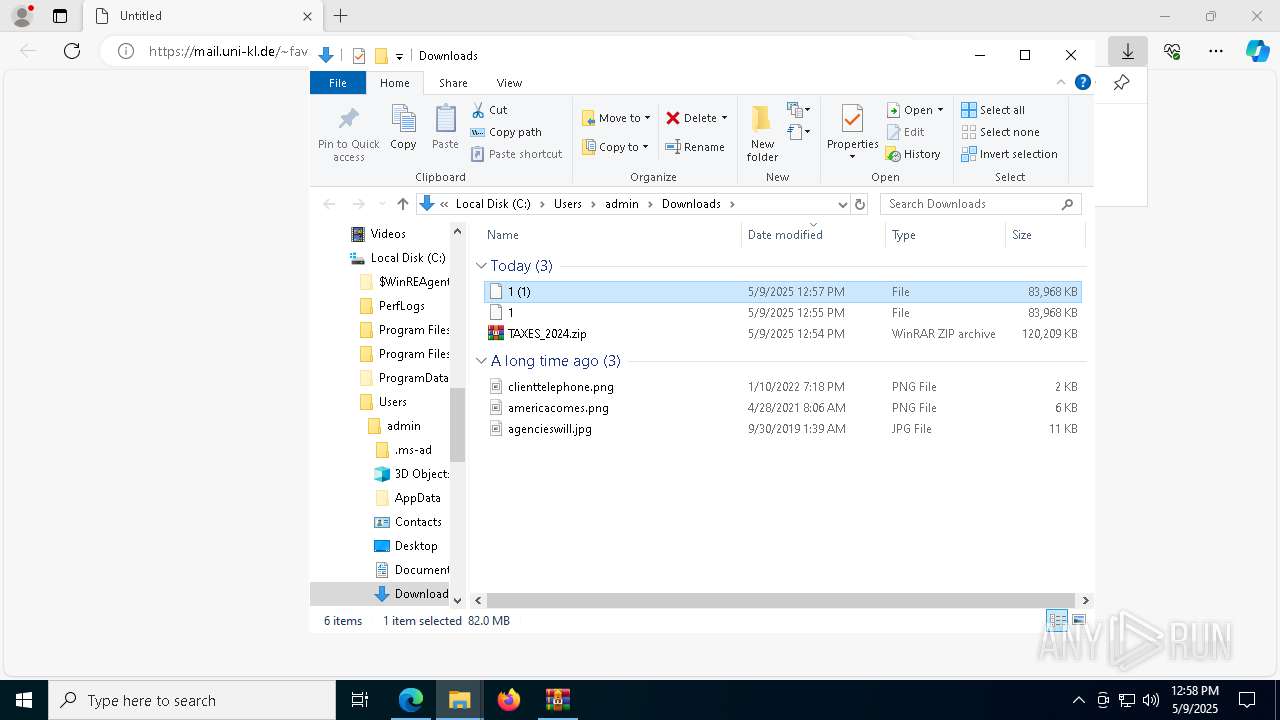
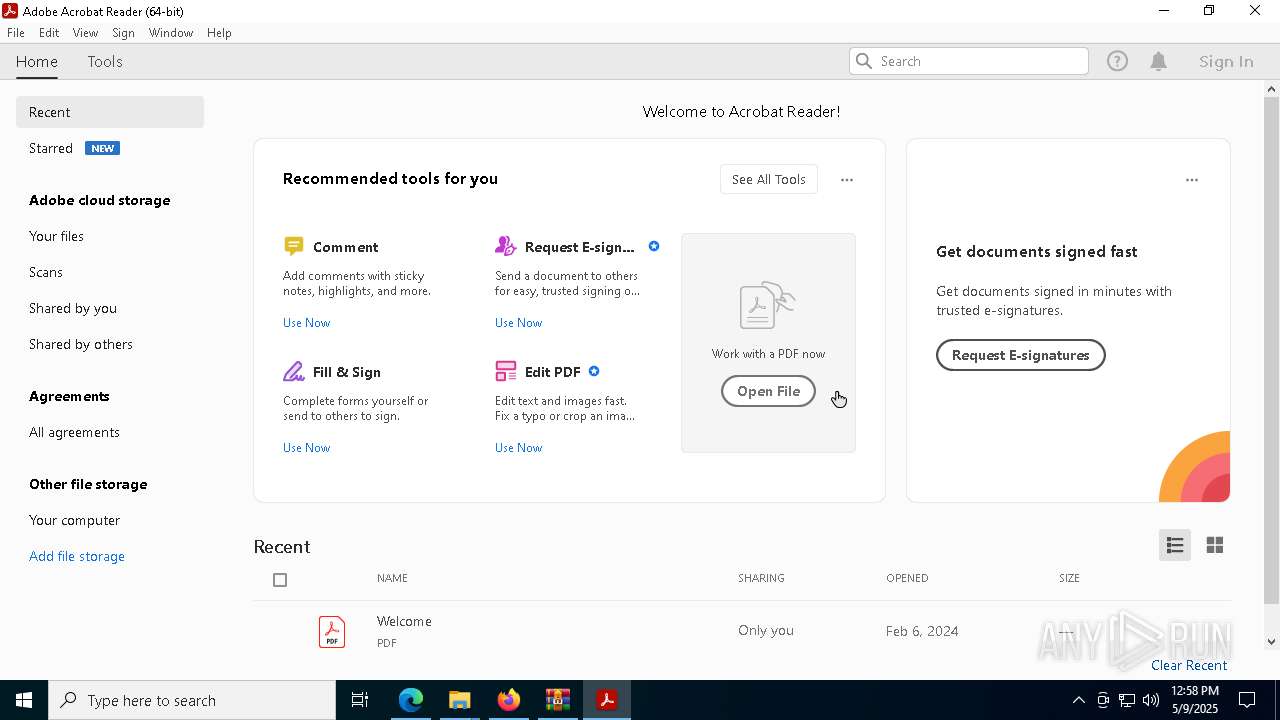
| URL: | https://mail.uni-kl.de/~fav92fah@rptu.de/protected/pwd/Lbpu3vFH/TAXES_2024.zip |
| Full analysis: | https://app.any.run/tasks/ace616ca-a0f8-491a-bdb2-5cf4515ed88f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 09, 2025, 12:53:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
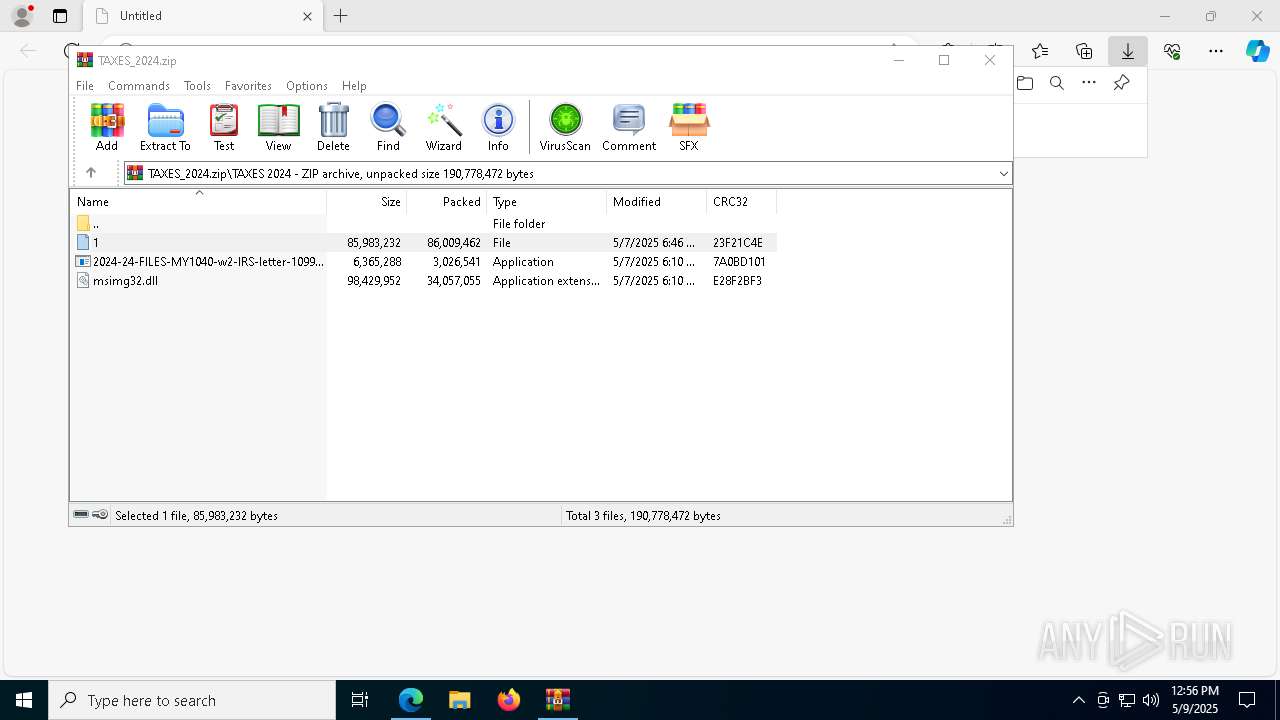
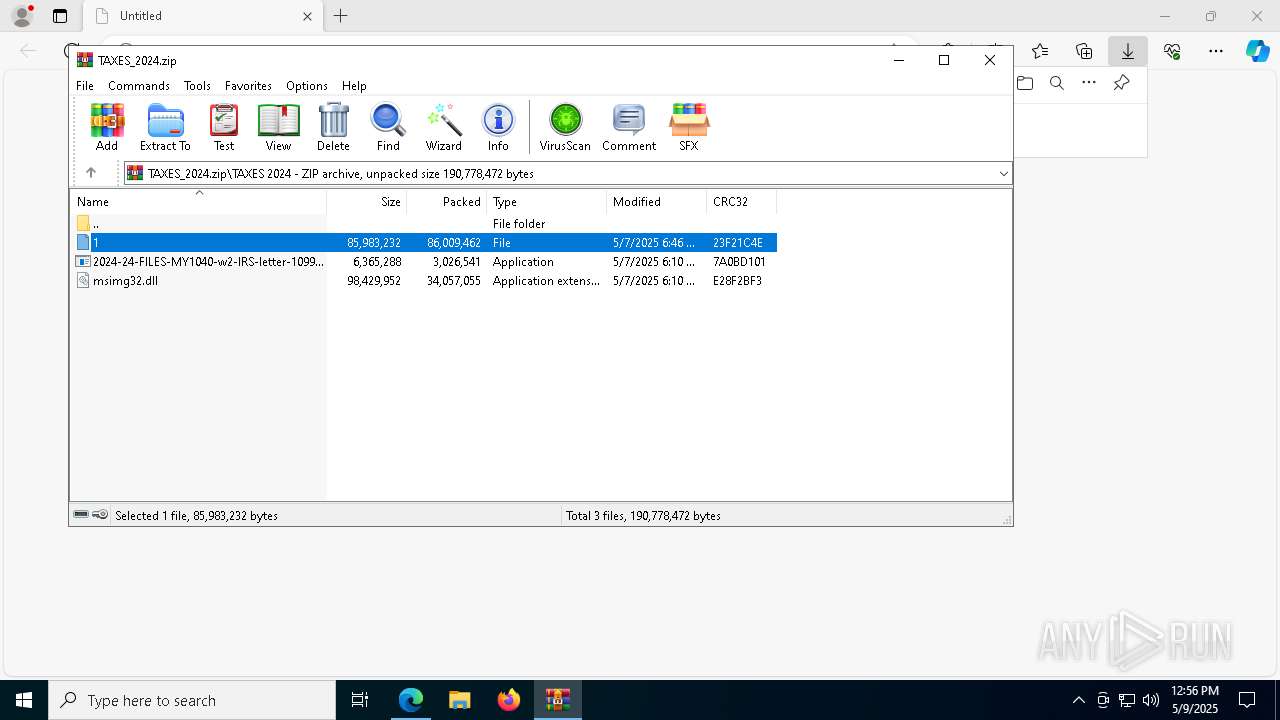
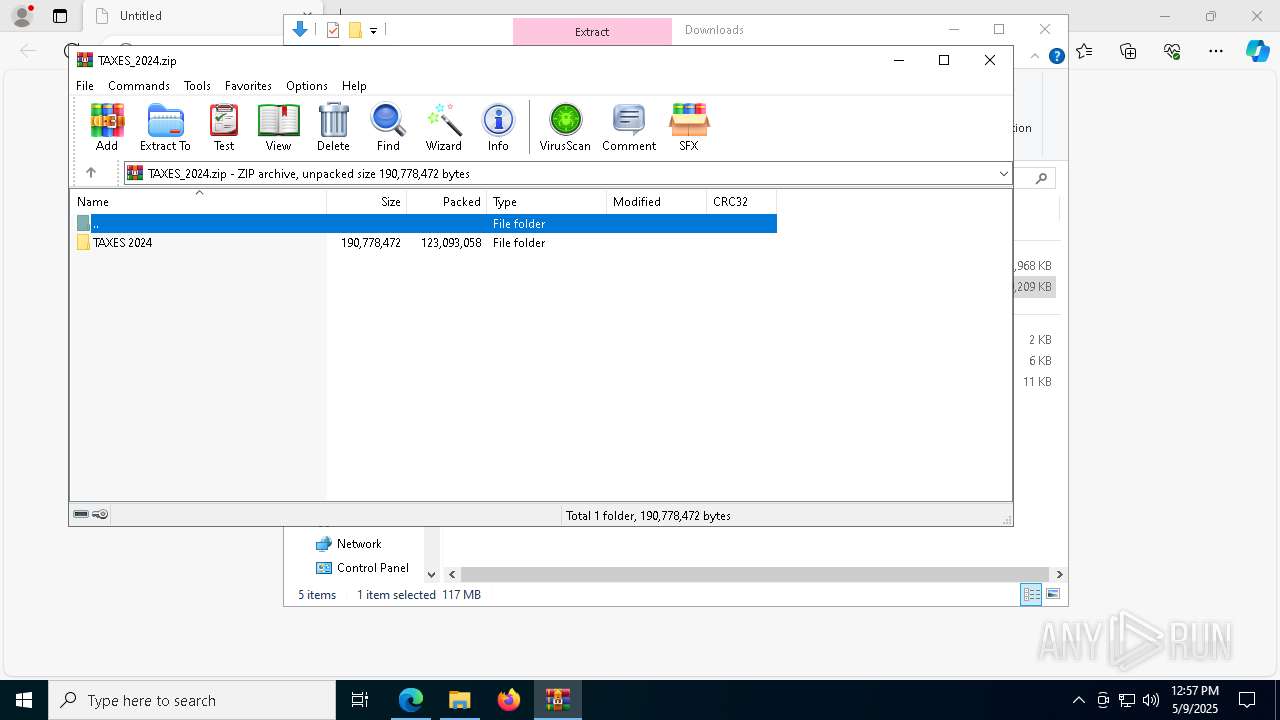
| MD5: | 0CA6C885B925A0EDFE9F0341DA3C296A |
| SHA1: | 011B2518BFAB05C5F4D5ED8721D54A4AA0C0D863 |
| SHA256: | 442157DA23E864F261E4D8BBD94699CB39302C108A7B360507652EFEE0250661 |
| SSDEEP: | 3:N8LLJm1AK60ENNCaX8IC2+qn:2LFmRYNNr8ICCn |
MALICIOUS
PUREHVNC has been detected (YARA)
- csc.exe (PID: 7796)
- csc.exe (PID: 924)
Actions looks like stealing of personal data
- csc.exe (PID: 7796)
Changes the autorun value in the registry
- reg.exe (PID: 924)
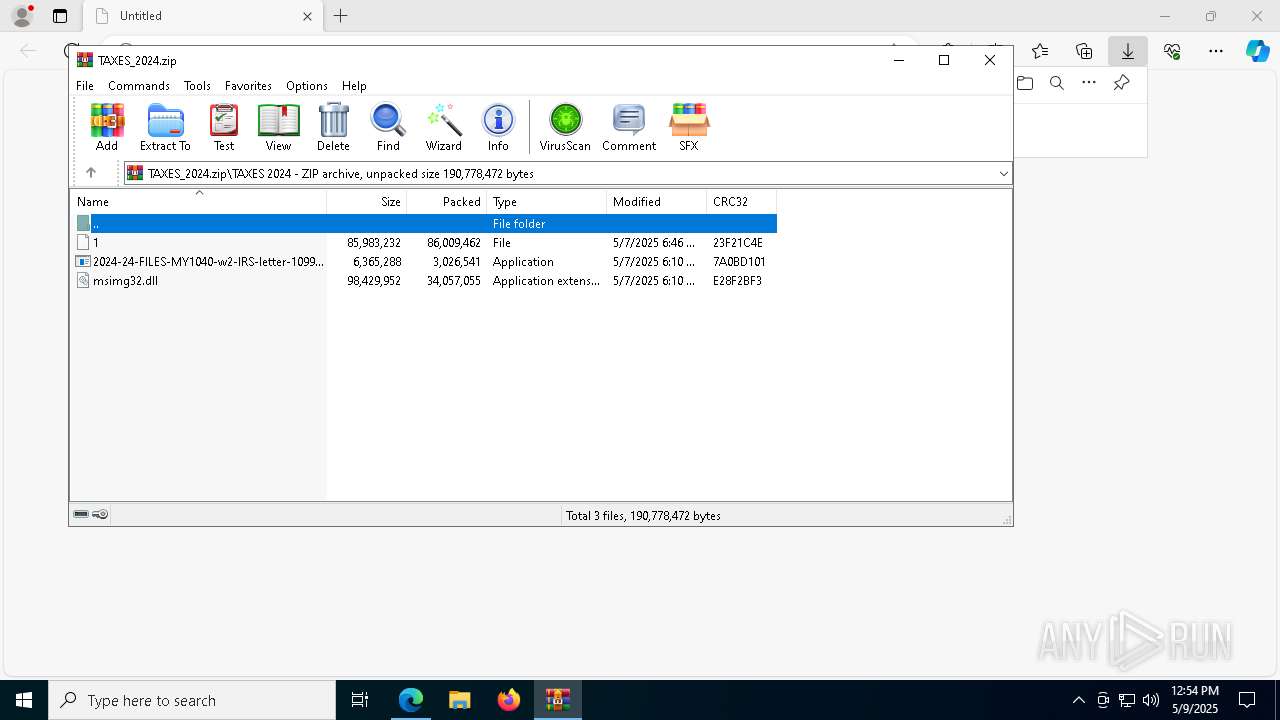
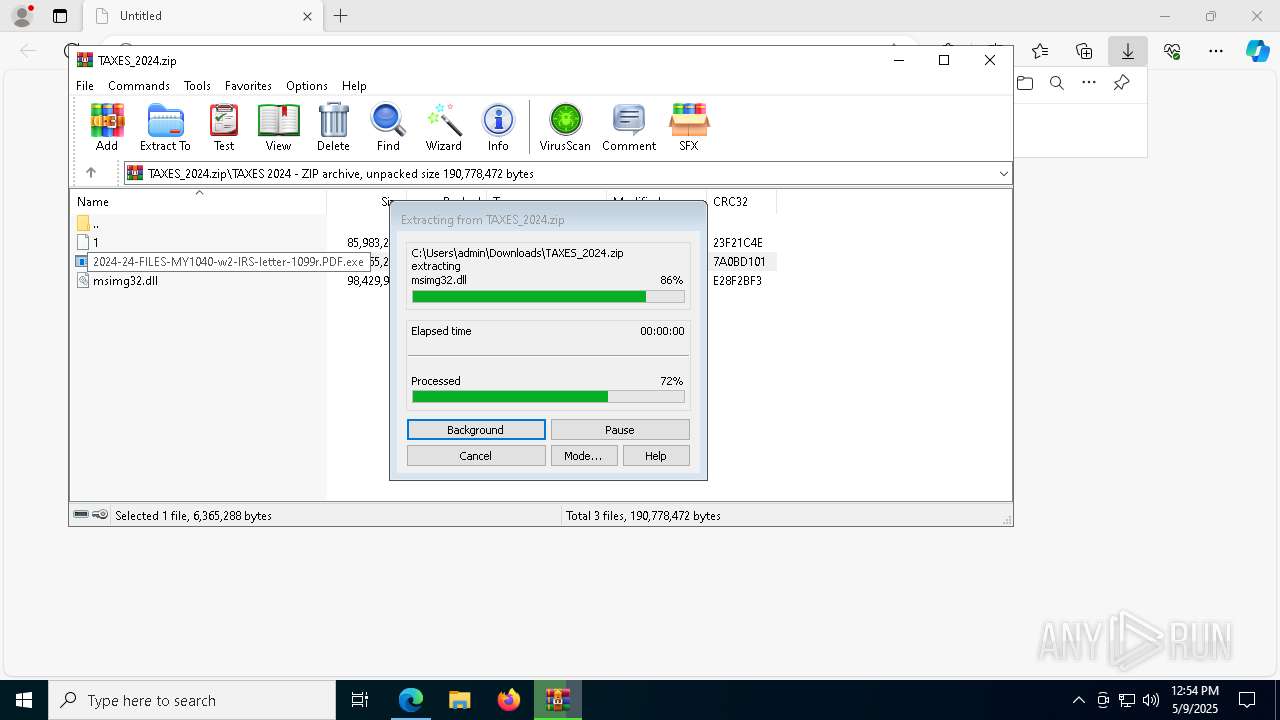
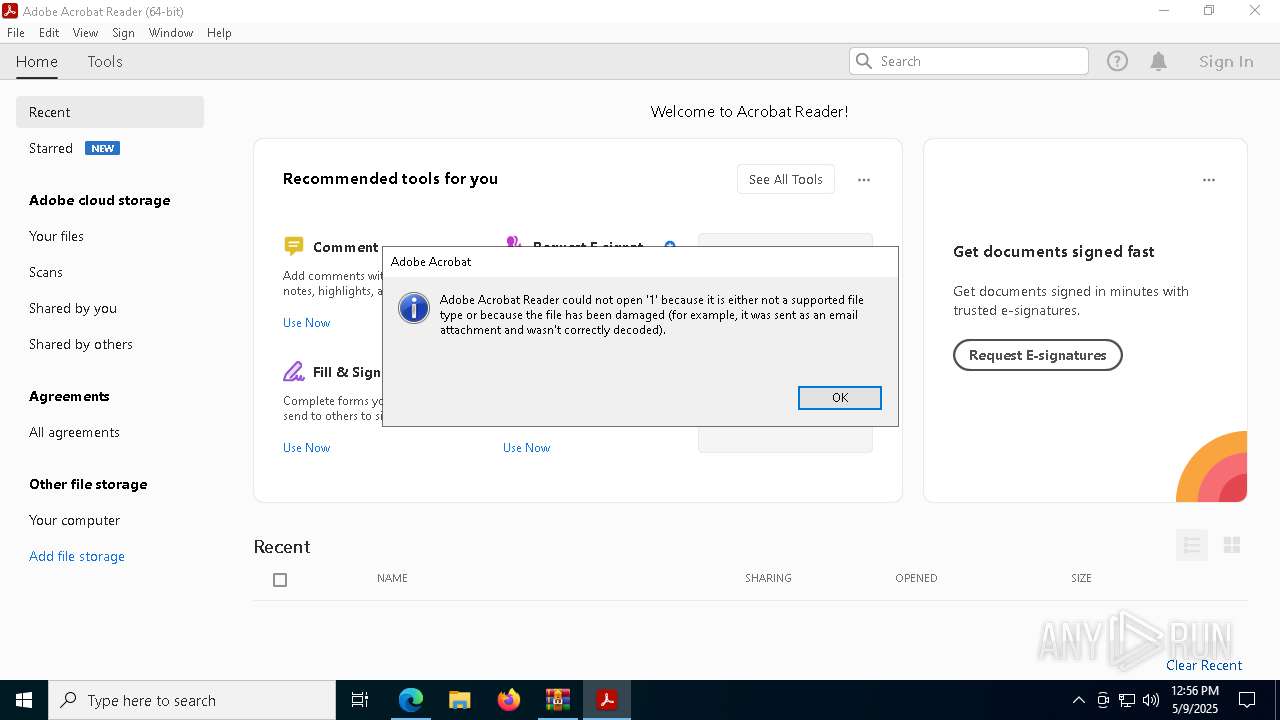
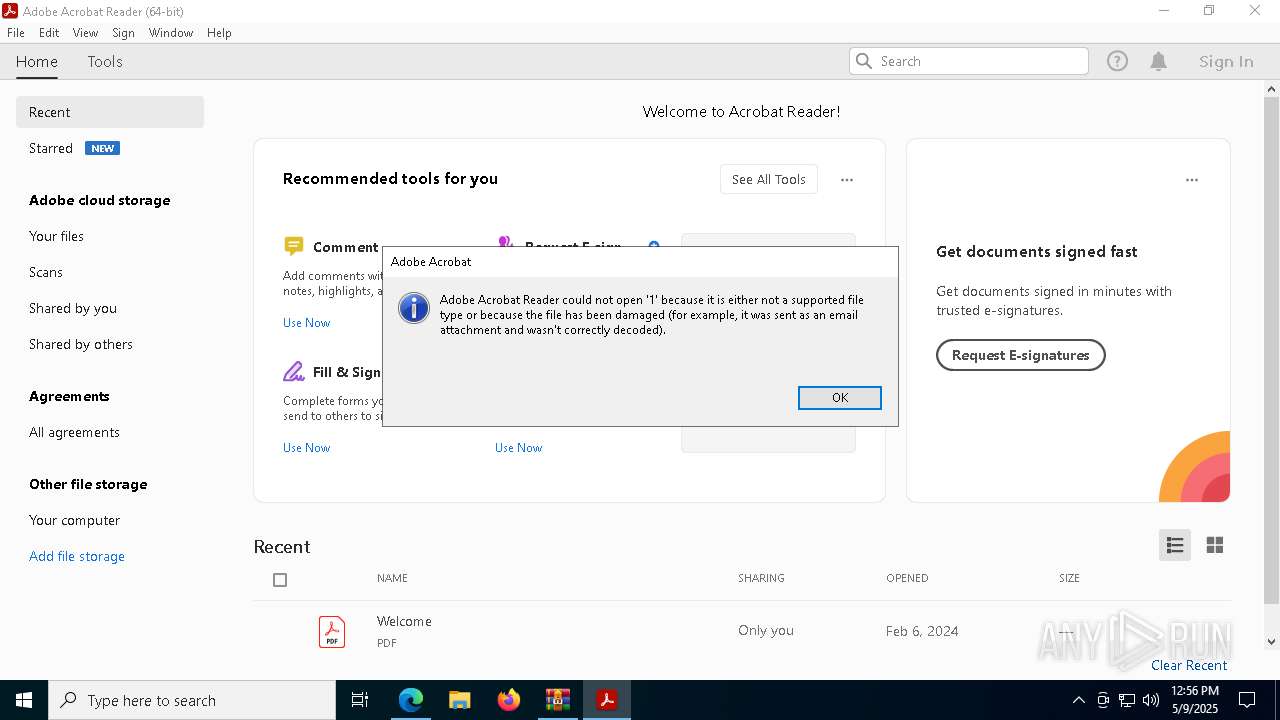
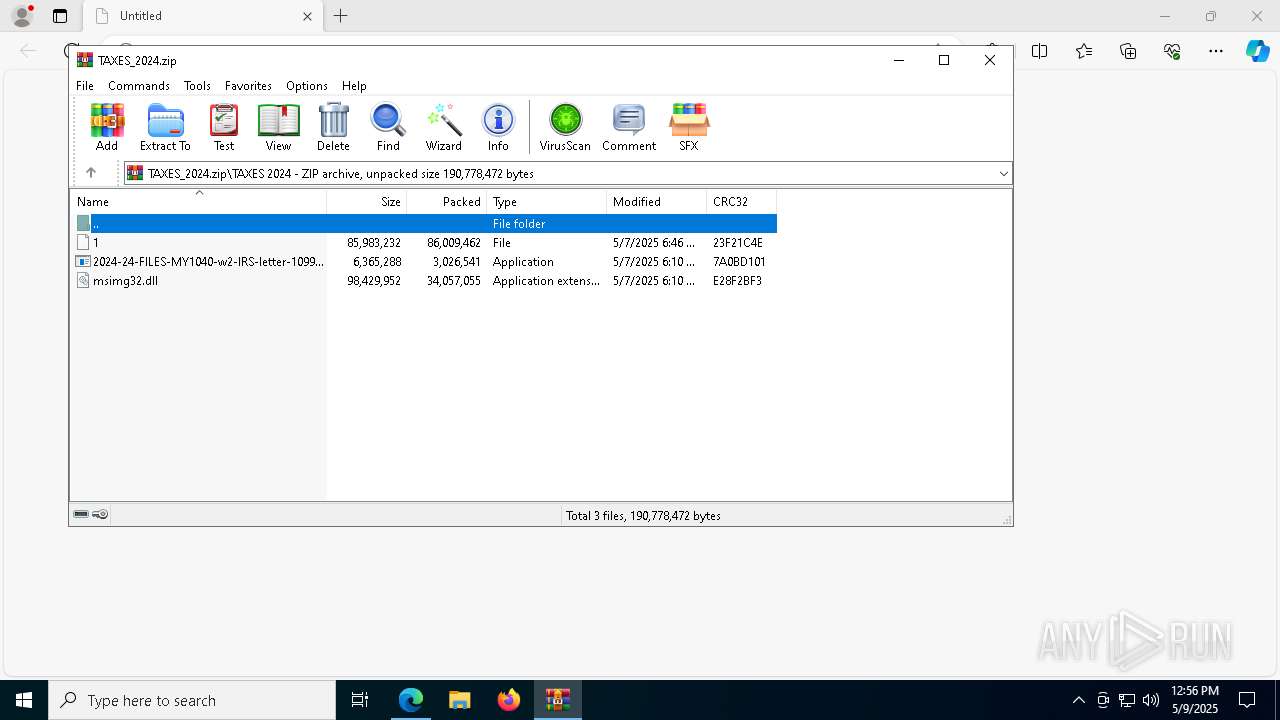
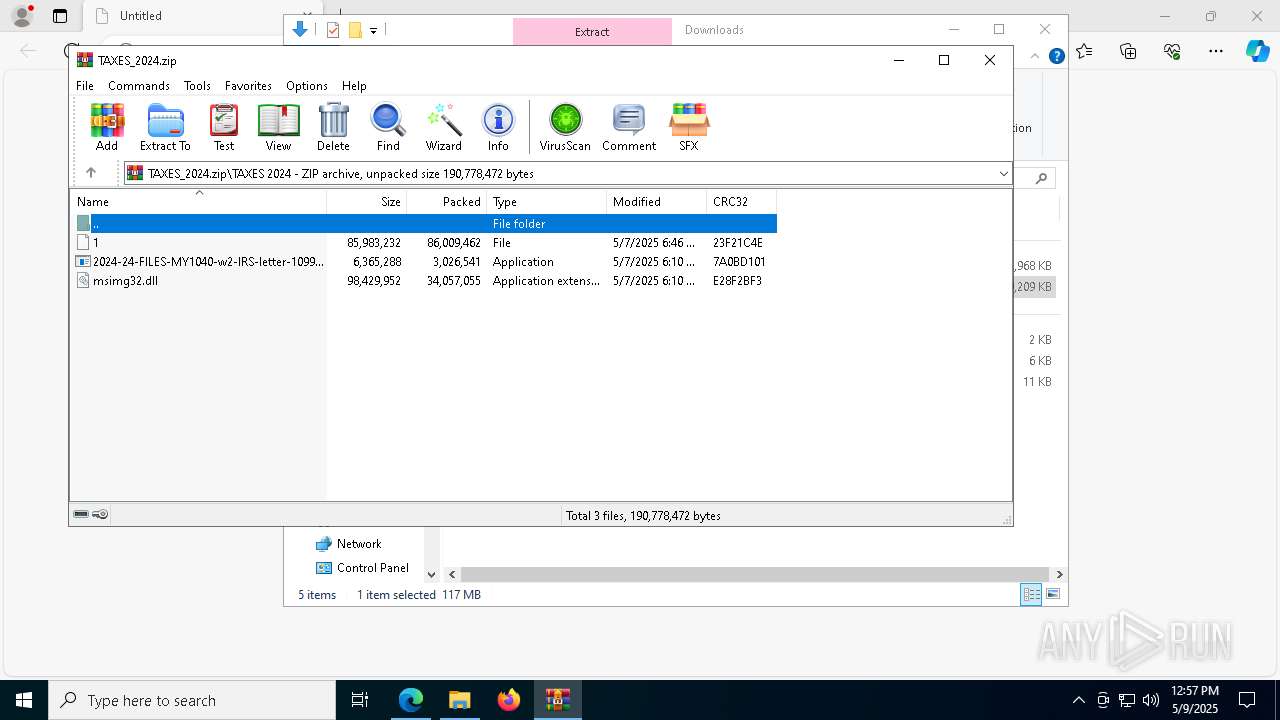
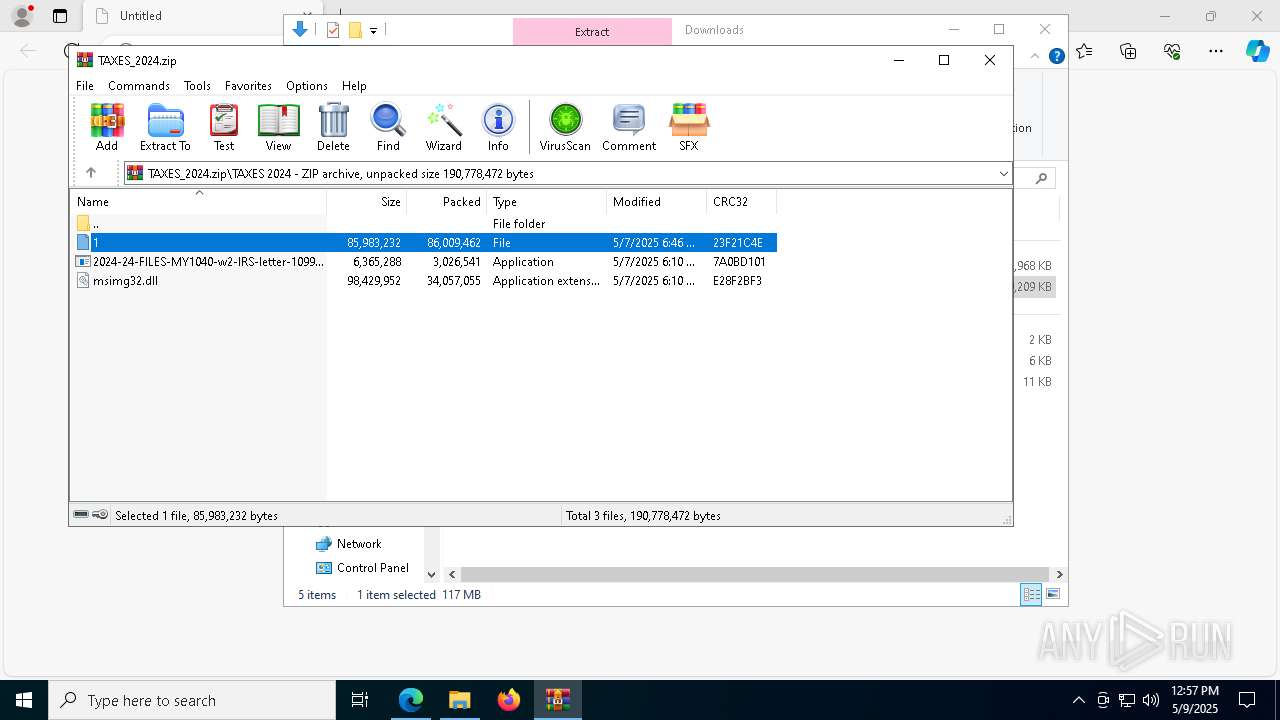
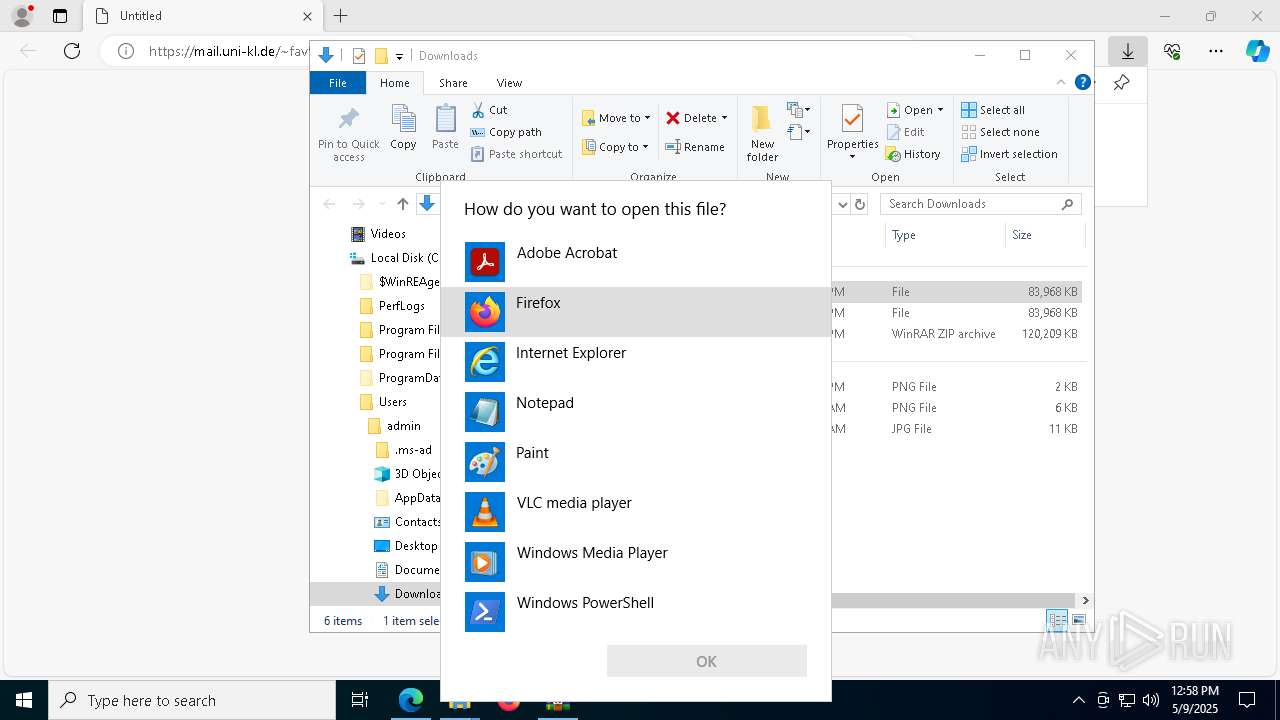
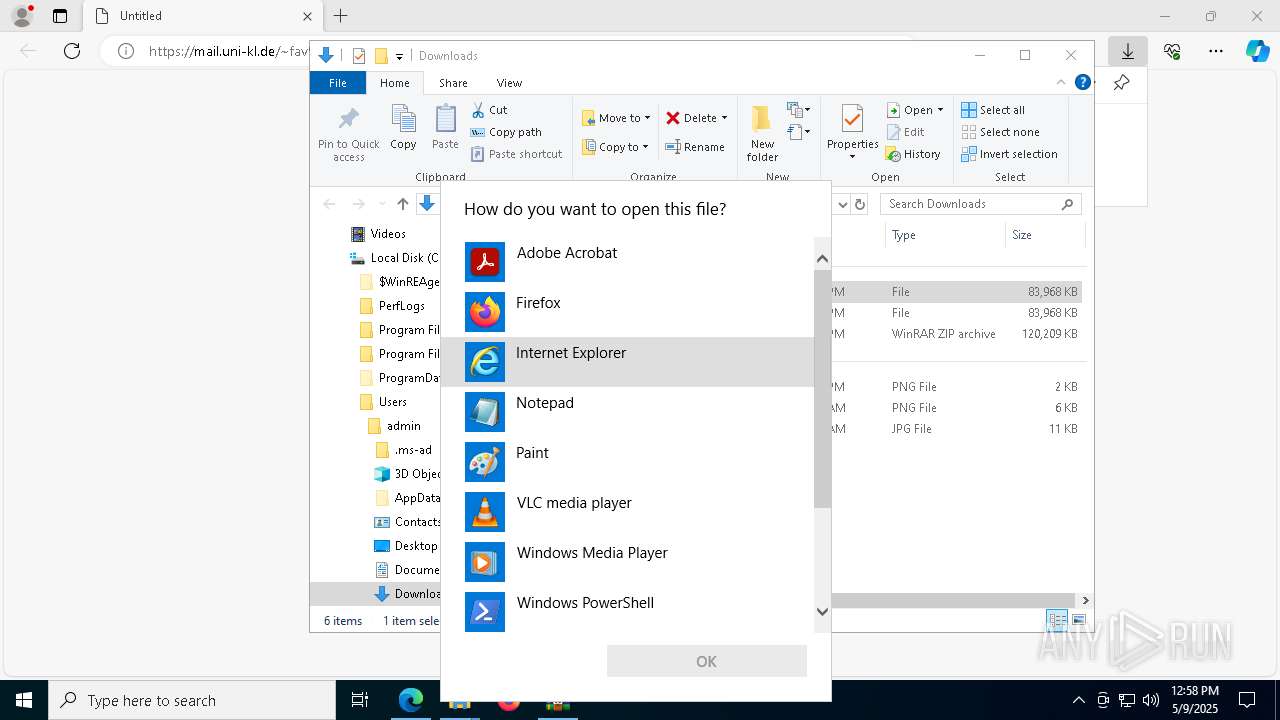
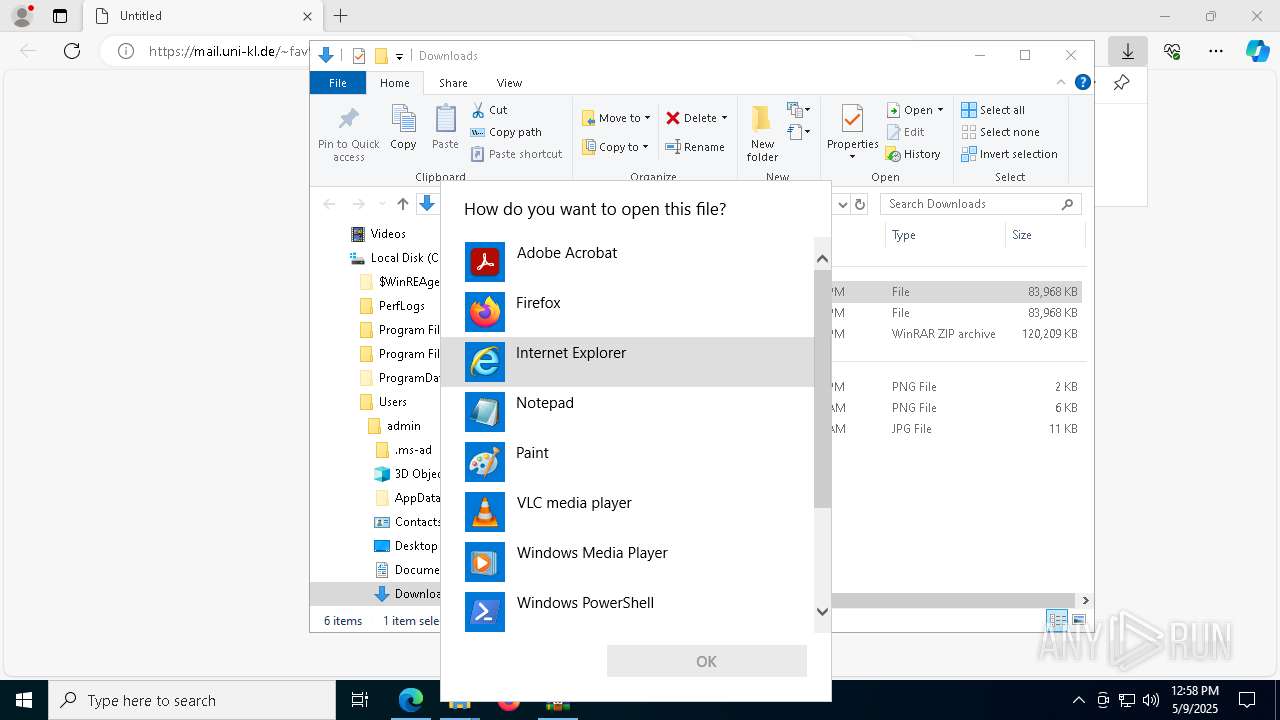
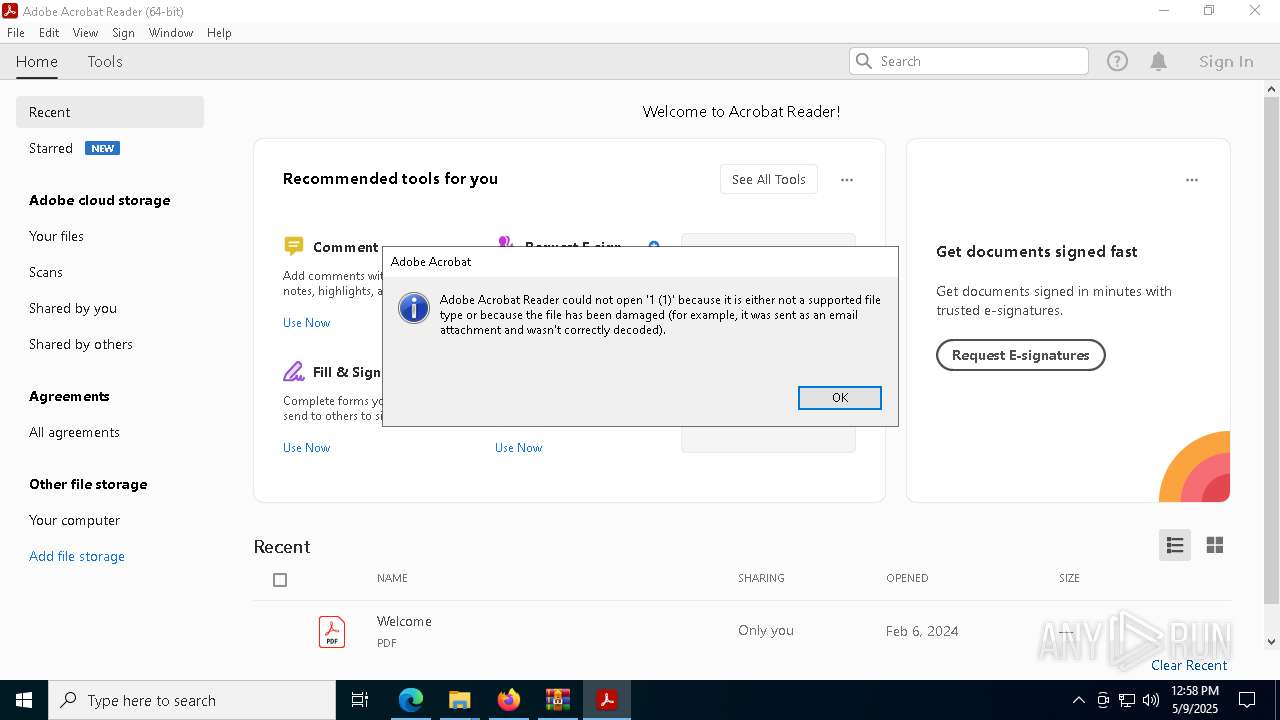
Starts Visual C# compiler
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 6272)
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 660)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 7796)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 660)
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 6272)
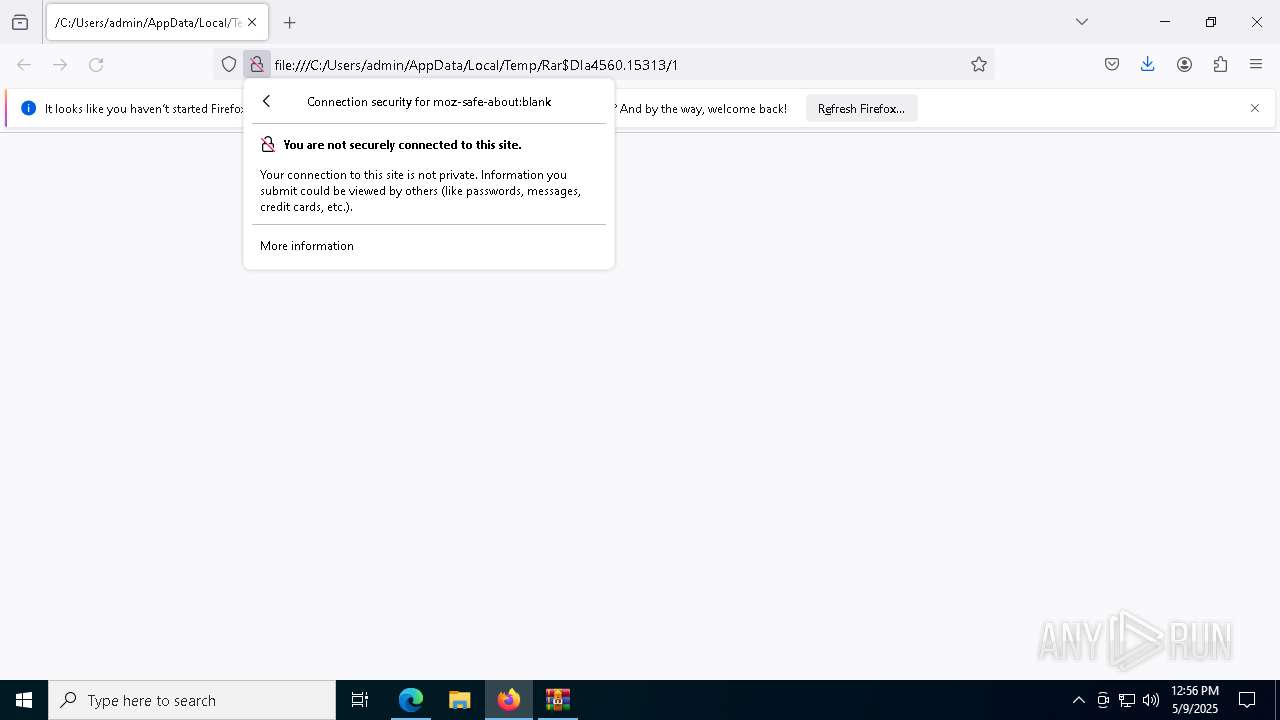
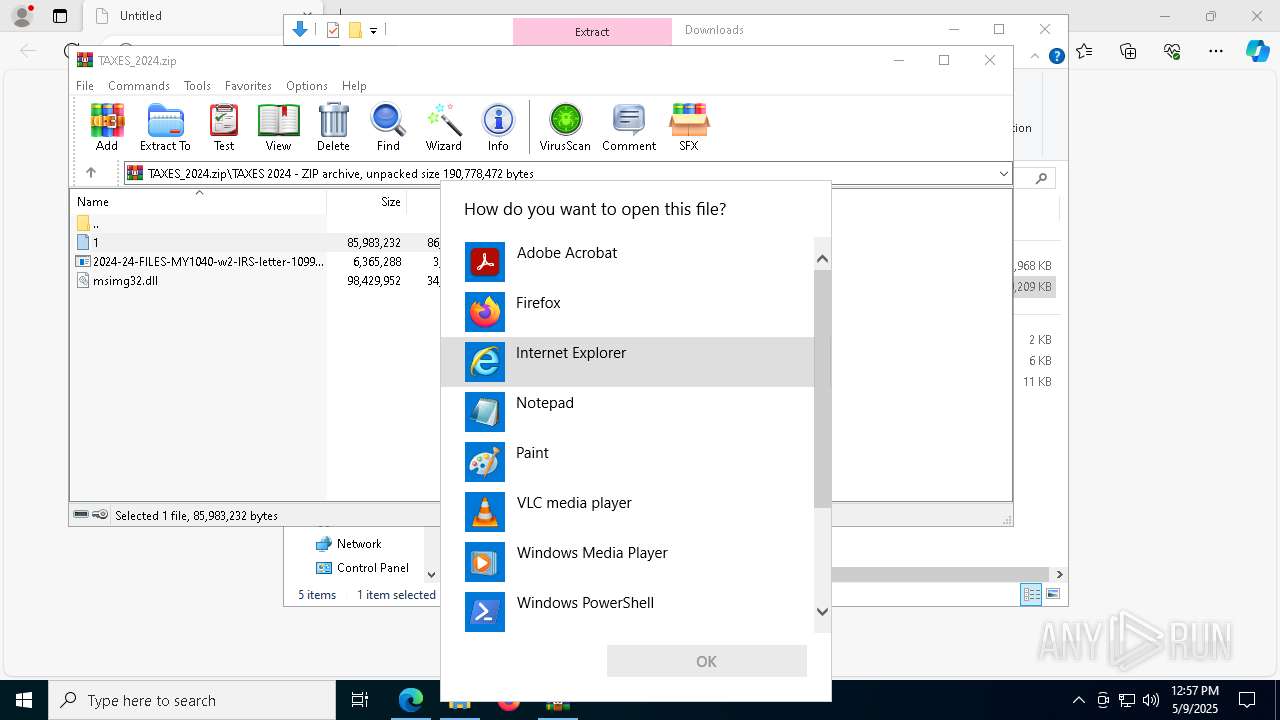
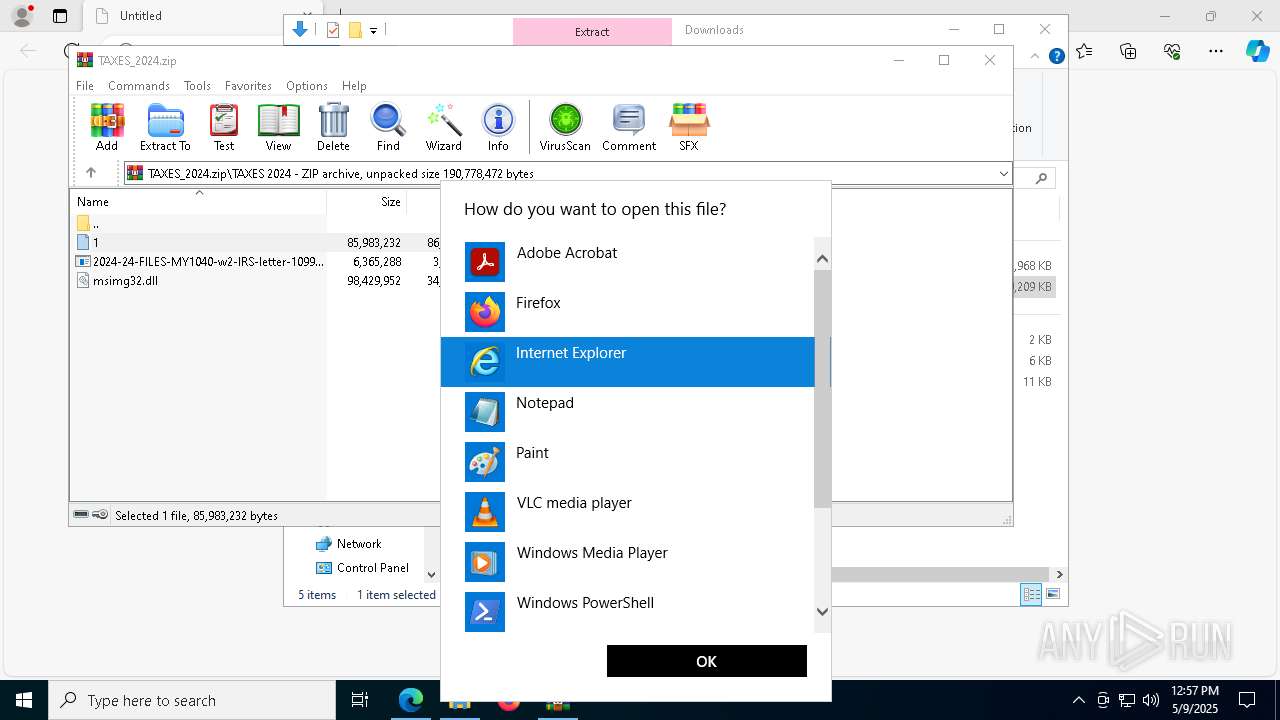
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4448)
- WinRAR.exe (PID: 4560)
Connects to unusual port
- csc.exe (PID: 7796)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 7796)
Multiple wallet extension IDs have been found
- csc.exe (PID: 7796)
- csc.exe (PID: 924)
Starts CMD.EXE for commands execution
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 660)
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 6272)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5256)
- cmd.exe (PID: 7944)
INFO
Reads the computer name
- identity_helper.exe (PID: 6872)
- csc.exe (PID: 7796)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6700)
- OpenWith.exe (PID: 5436)
- OpenWith.exe (PID: 7960)
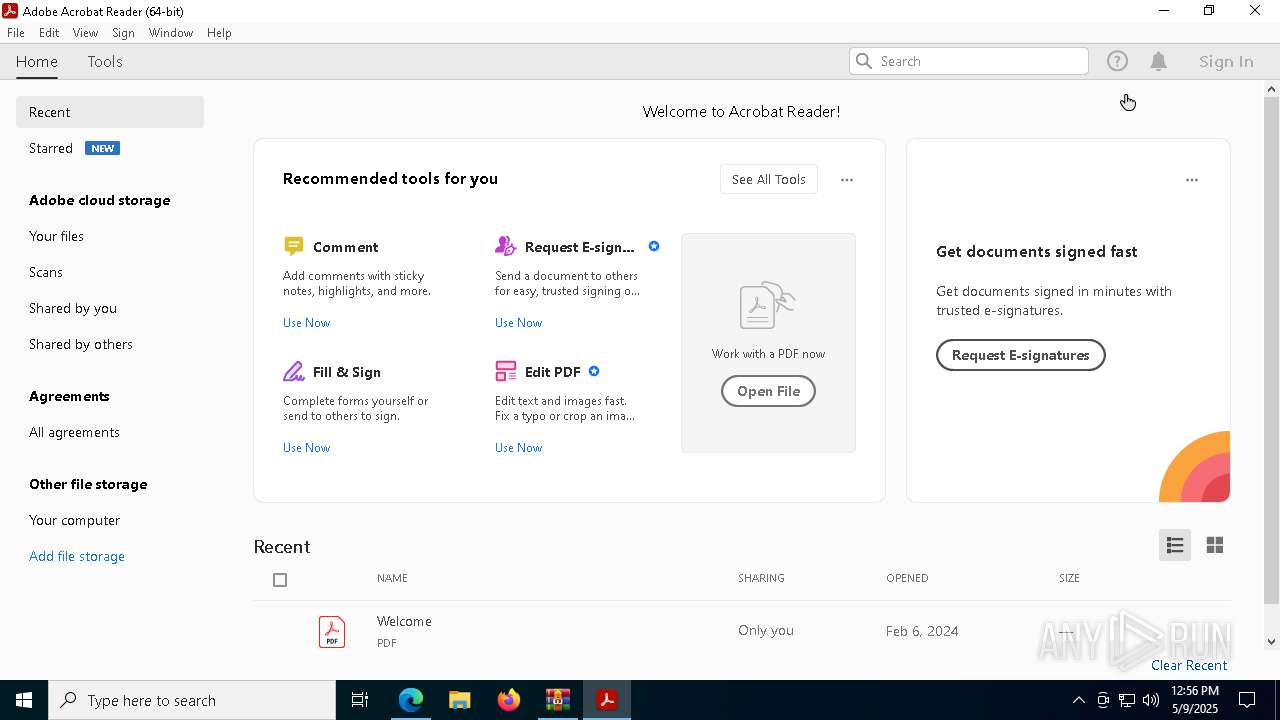
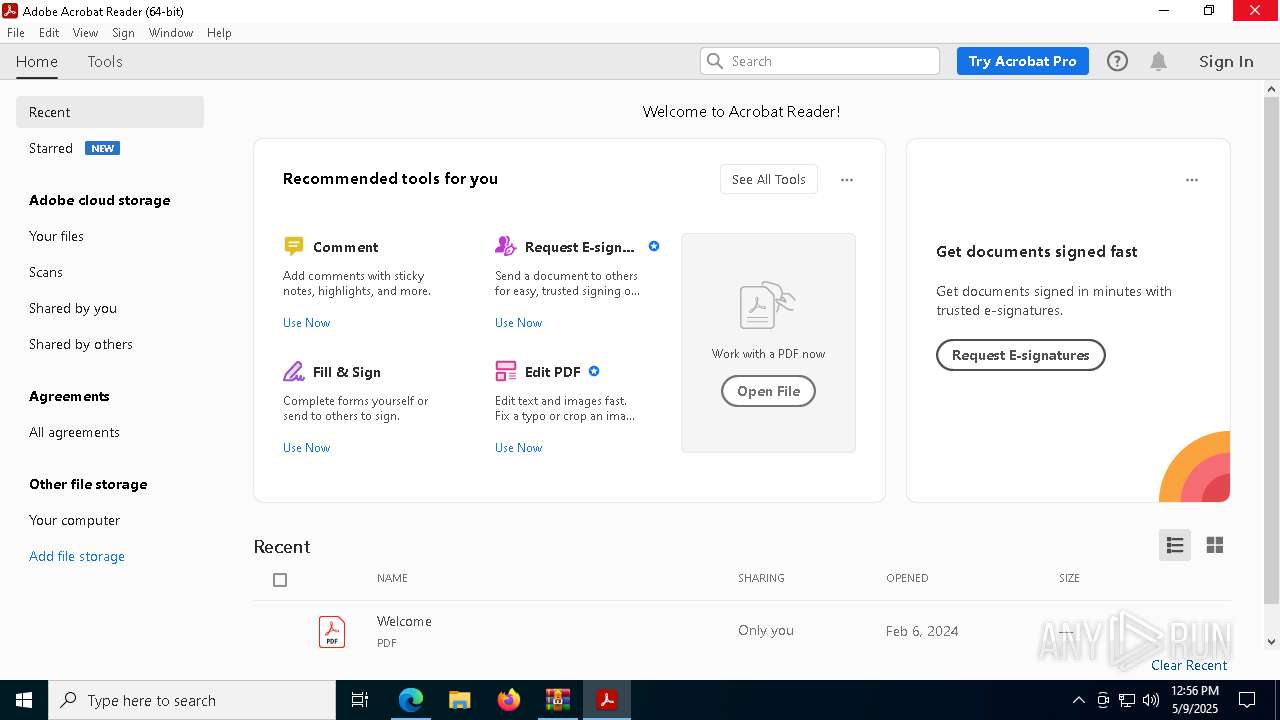
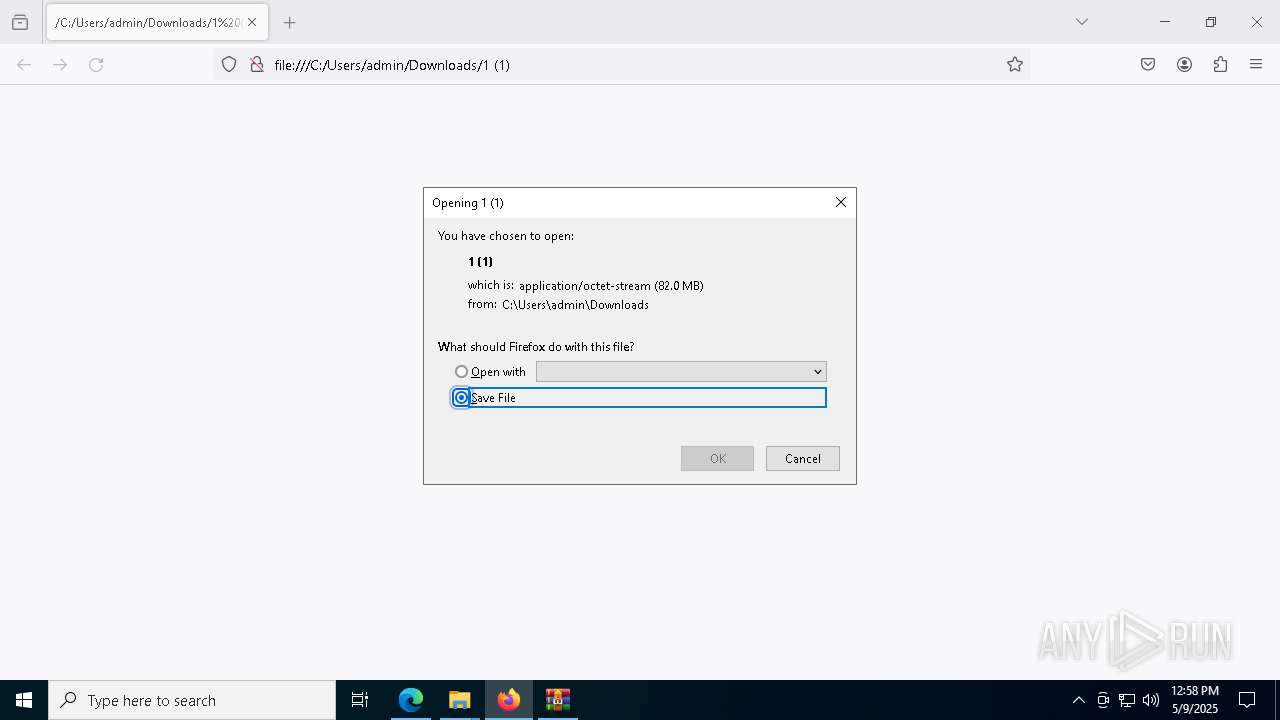
Application launched itself
- msedge.exe (PID: 6700)
- firefox.exe (PID: 8000)
- firefox.exe (PID: 6712)
- Acrobat.exe (PID: 4016)
- AcroCEF.exe (PID: 4348)
- firefox.exe (PID: 780)
- firefox.exe (PID: 2192)
- Acrobat.exe (PID: 7968)
- AcroCEF.exe (PID: 1096)
Reads Environment values
- identity_helper.exe (PID: 6872)
Checks supported languages
- identity_helper.exe (PID: 6872)
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 6272)
- 2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe (PID: 660)
- csc.exe (PID: 7796)
Reads the software policy settings
- slui.exe (PID: 1812)
- slui.exe (PID: 2420)
- csc.exe (PID: 7796)
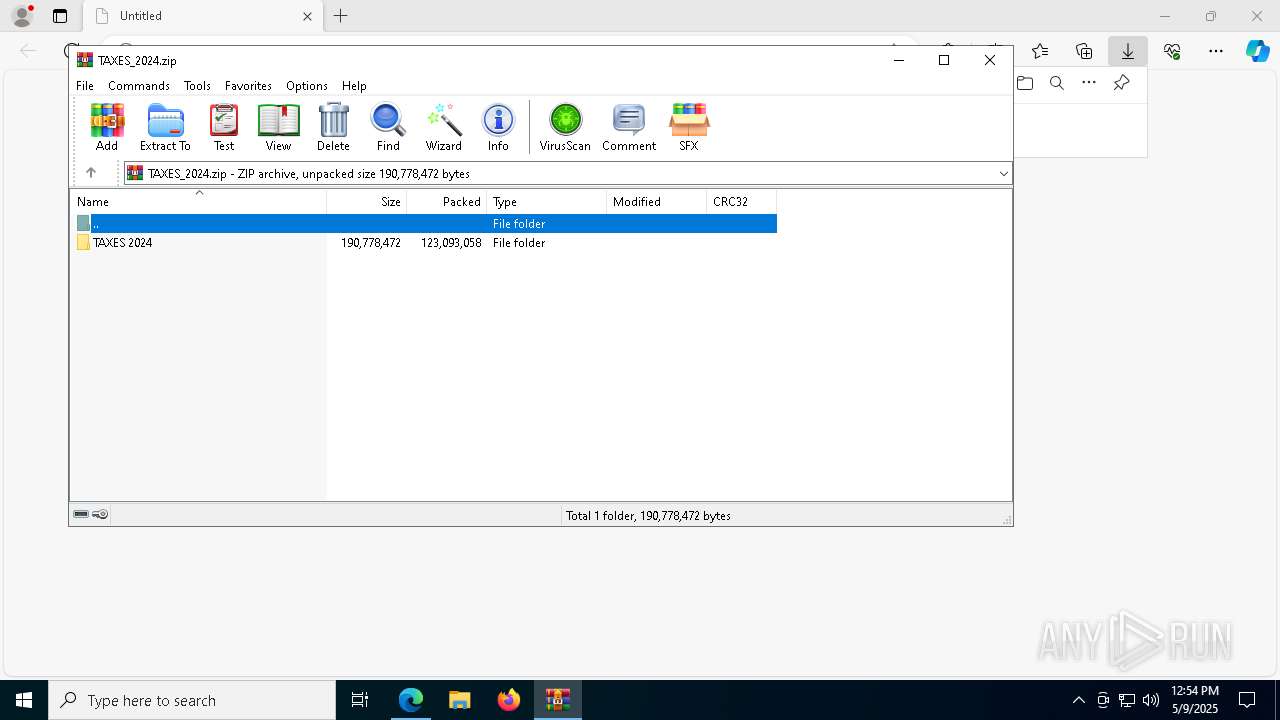
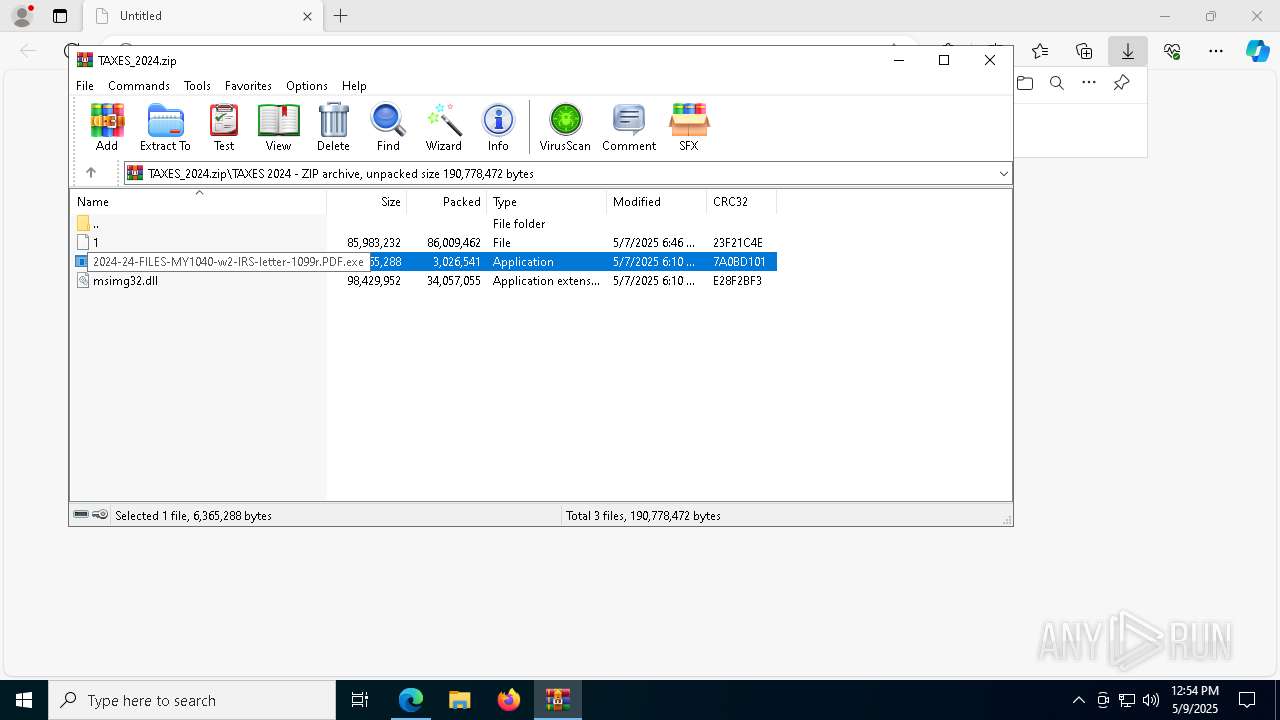
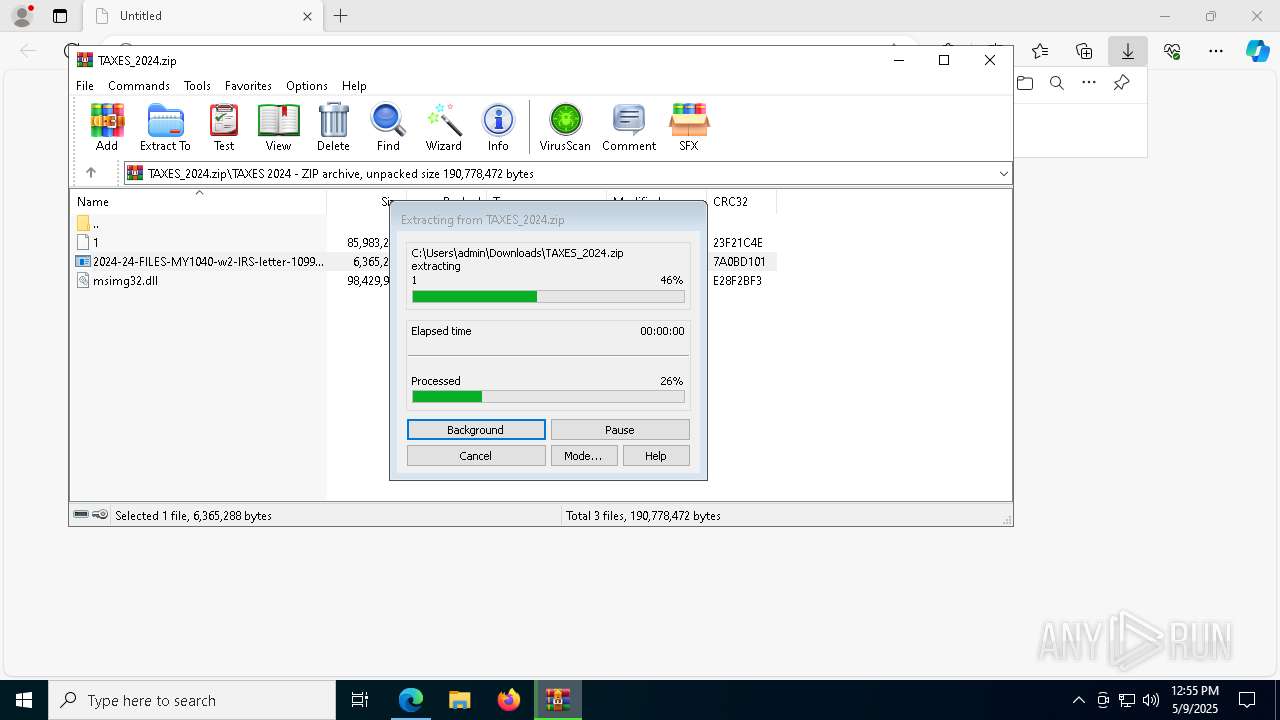
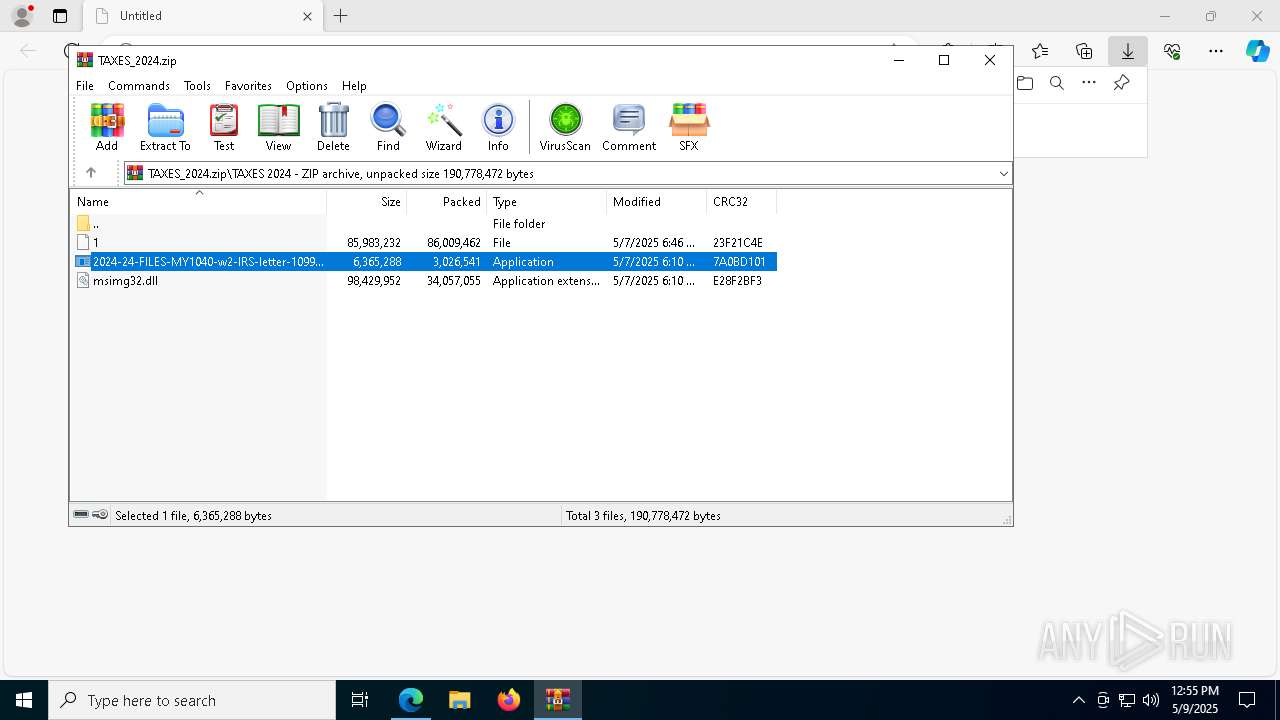
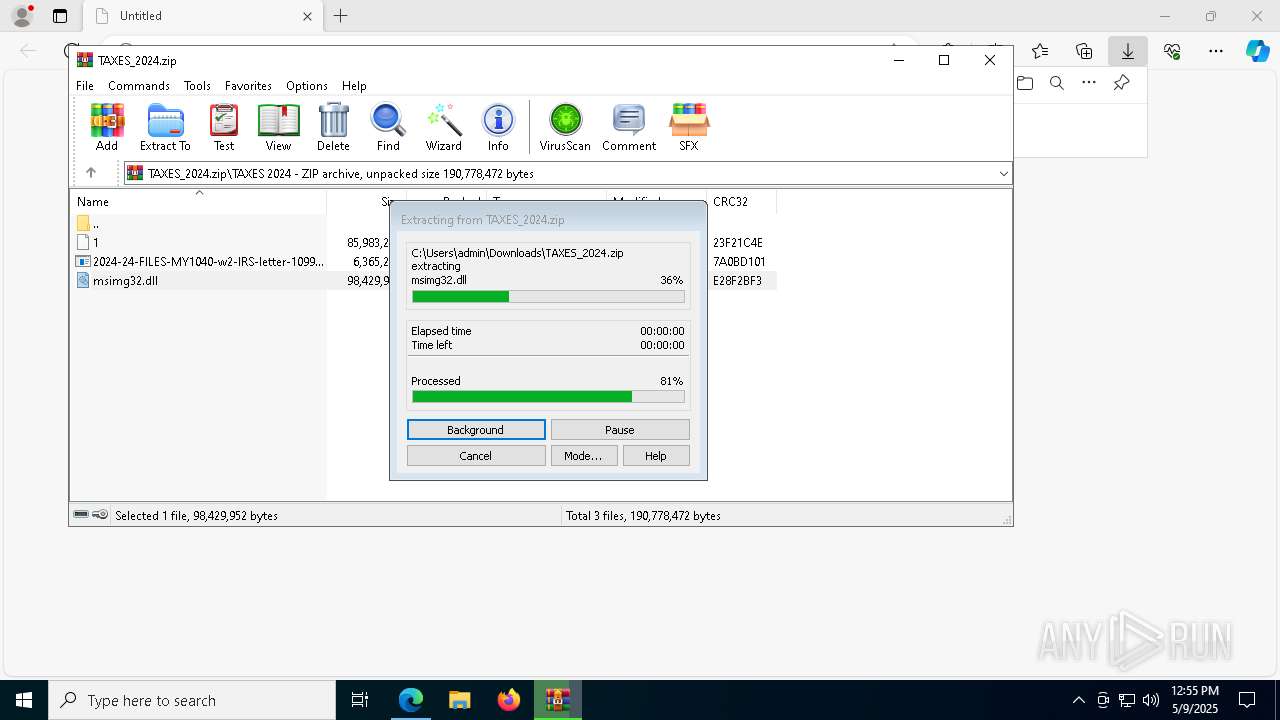
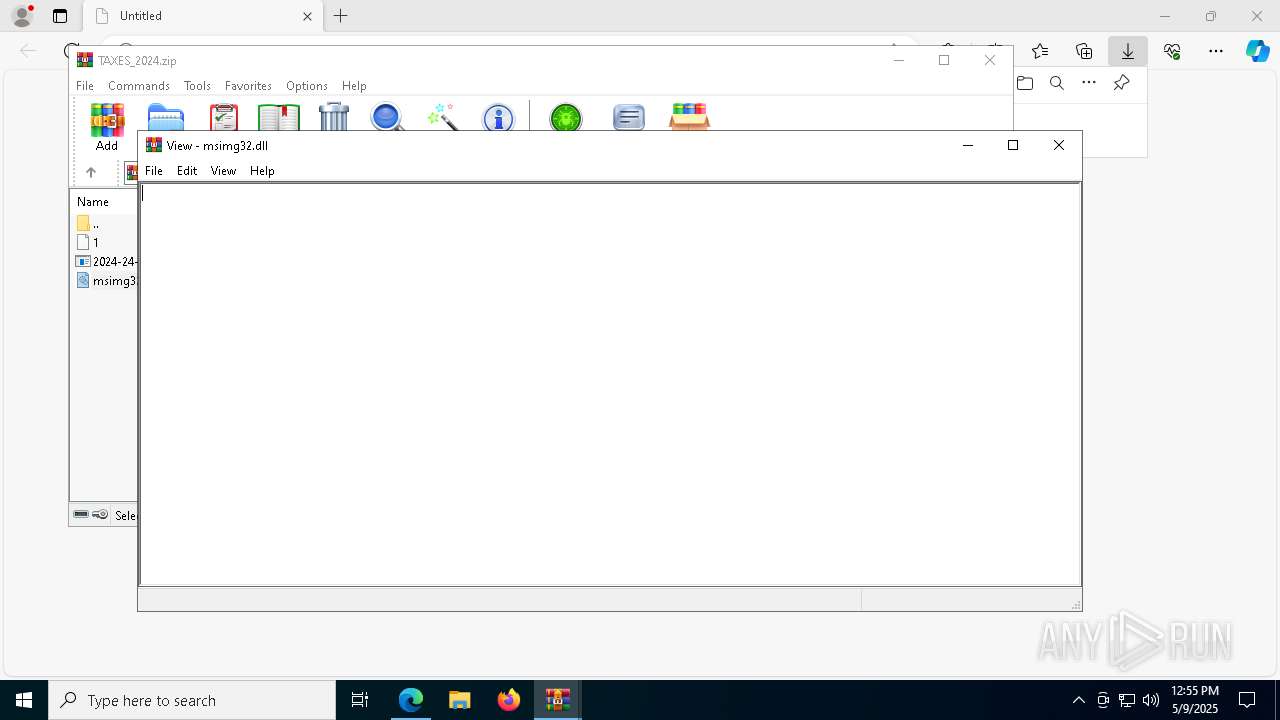
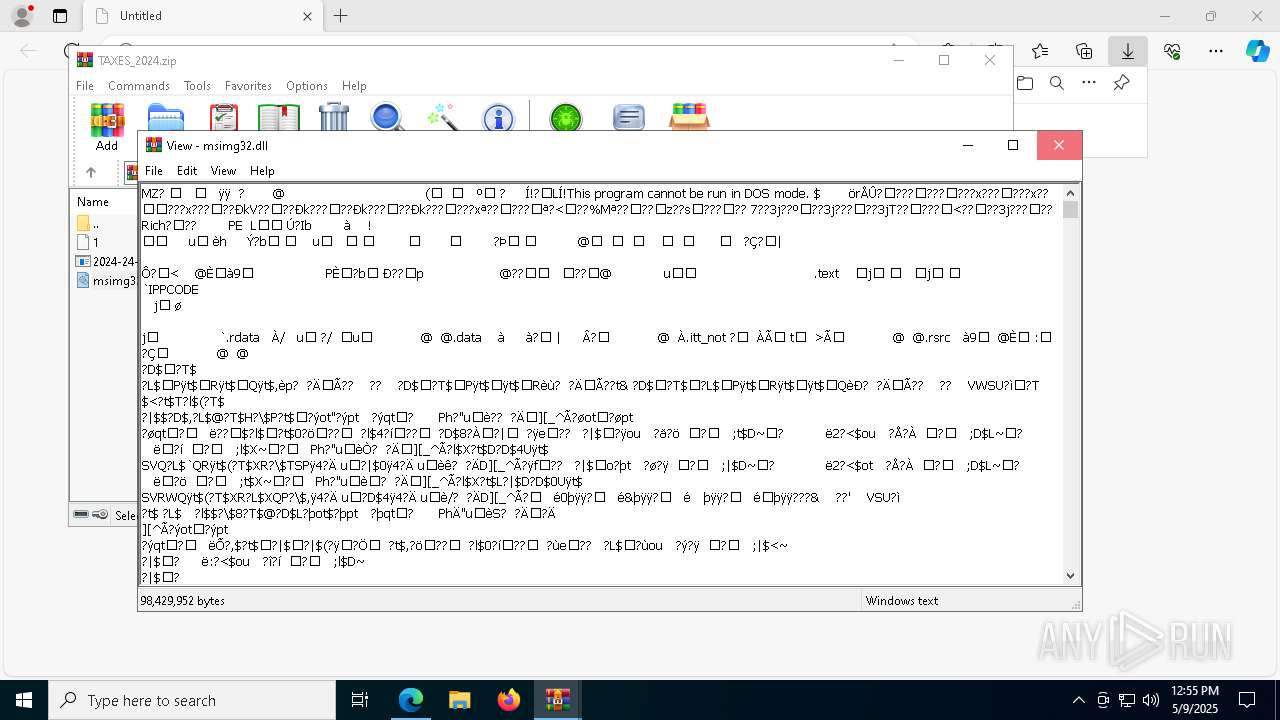
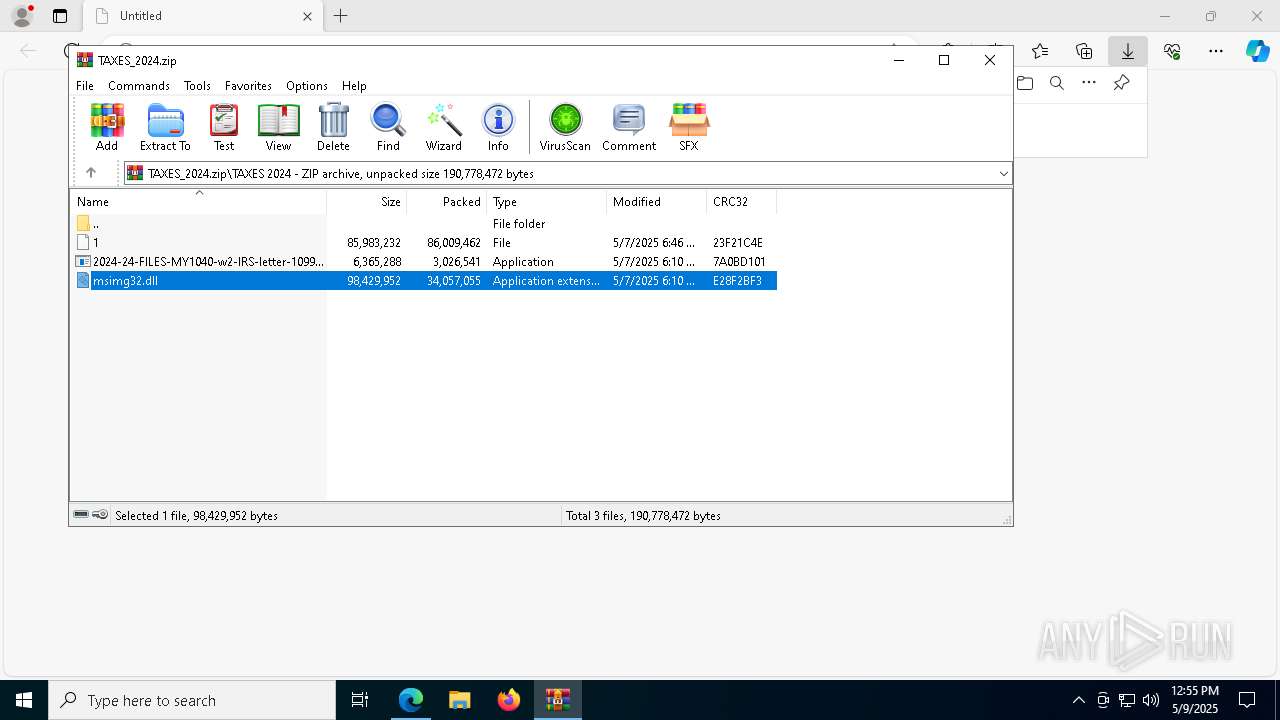
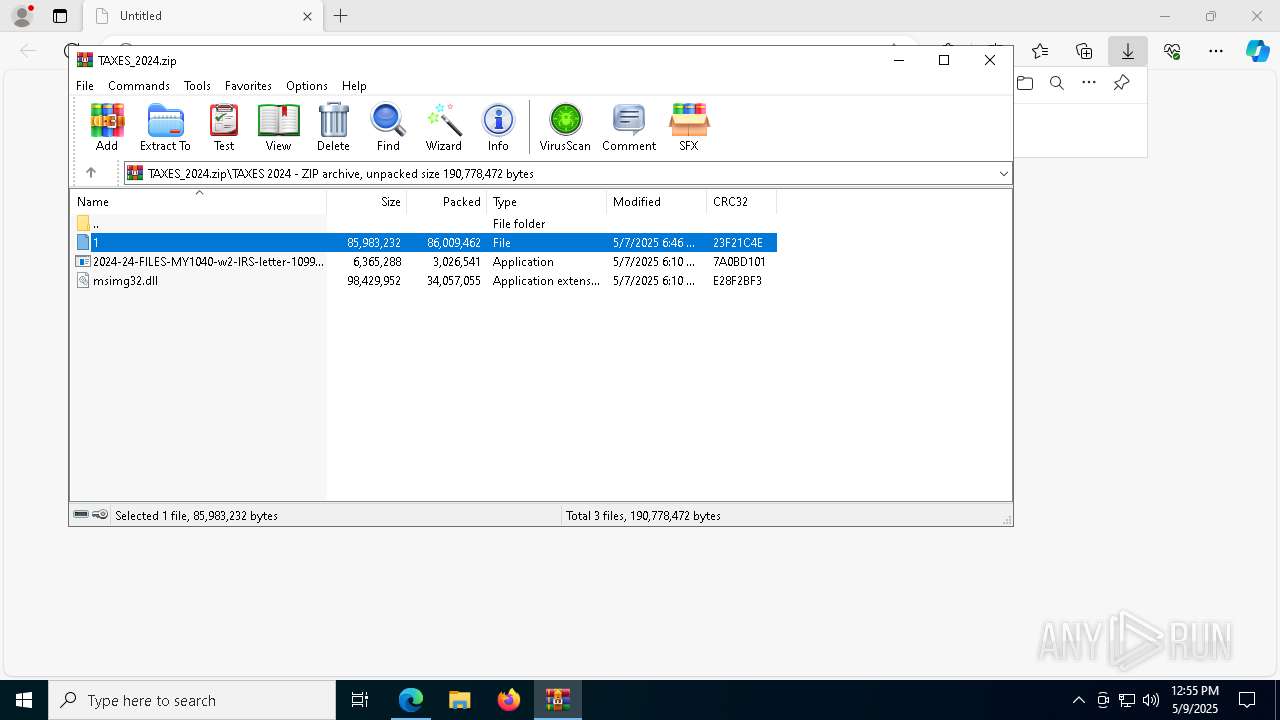
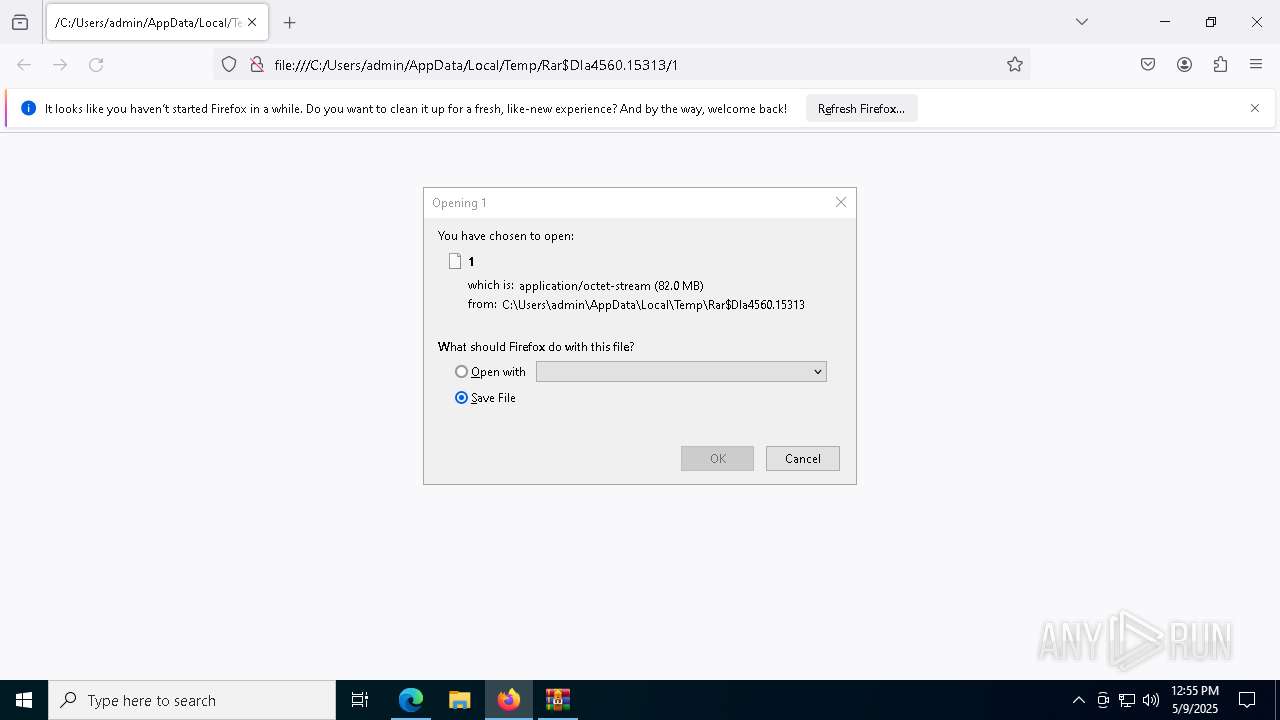
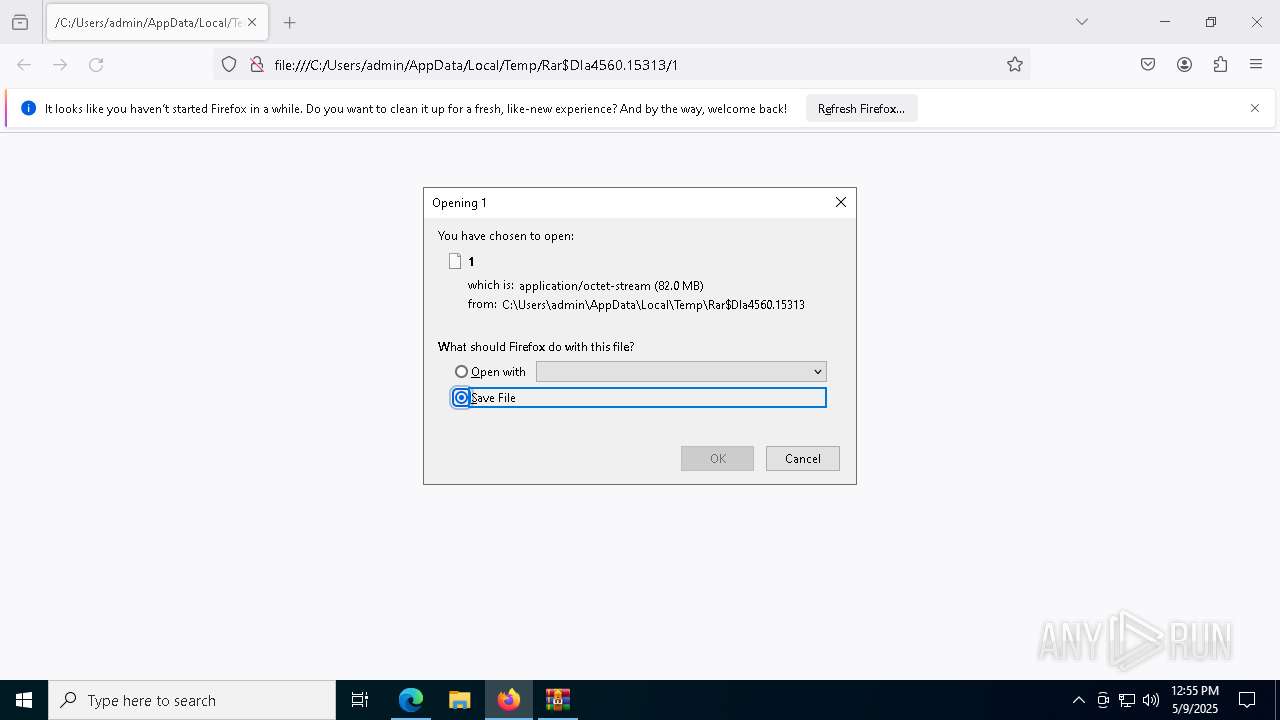
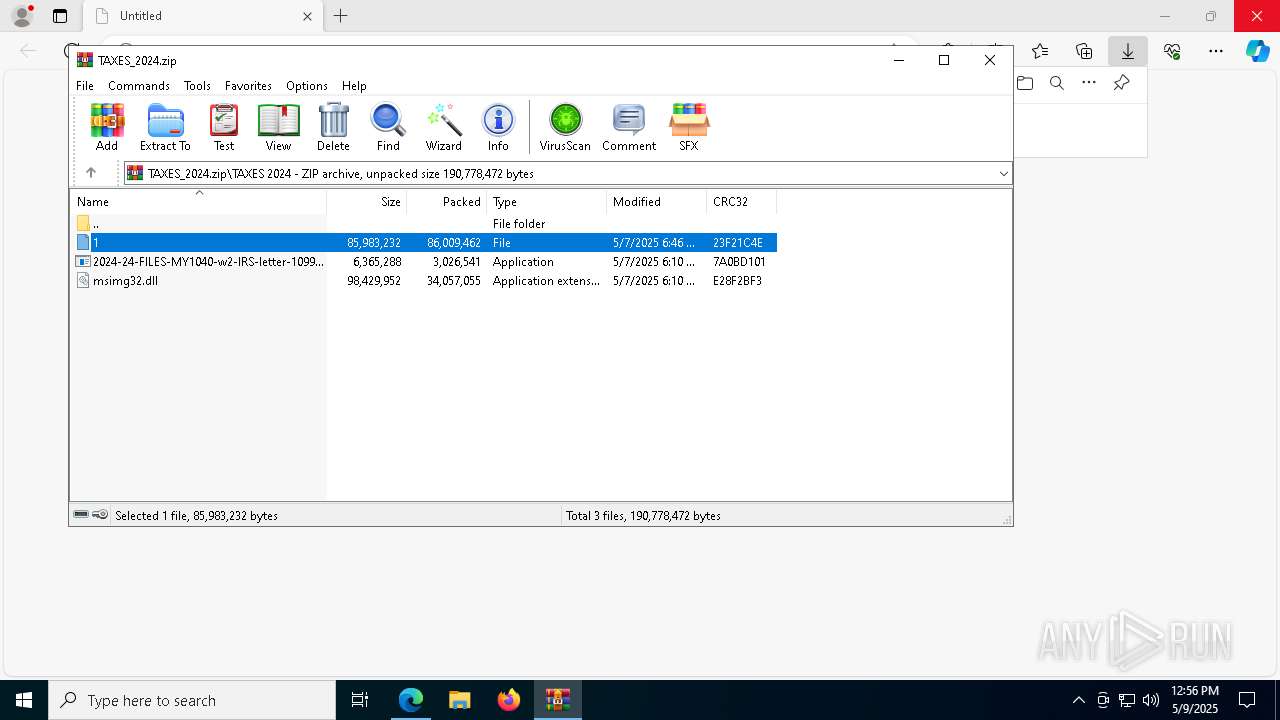
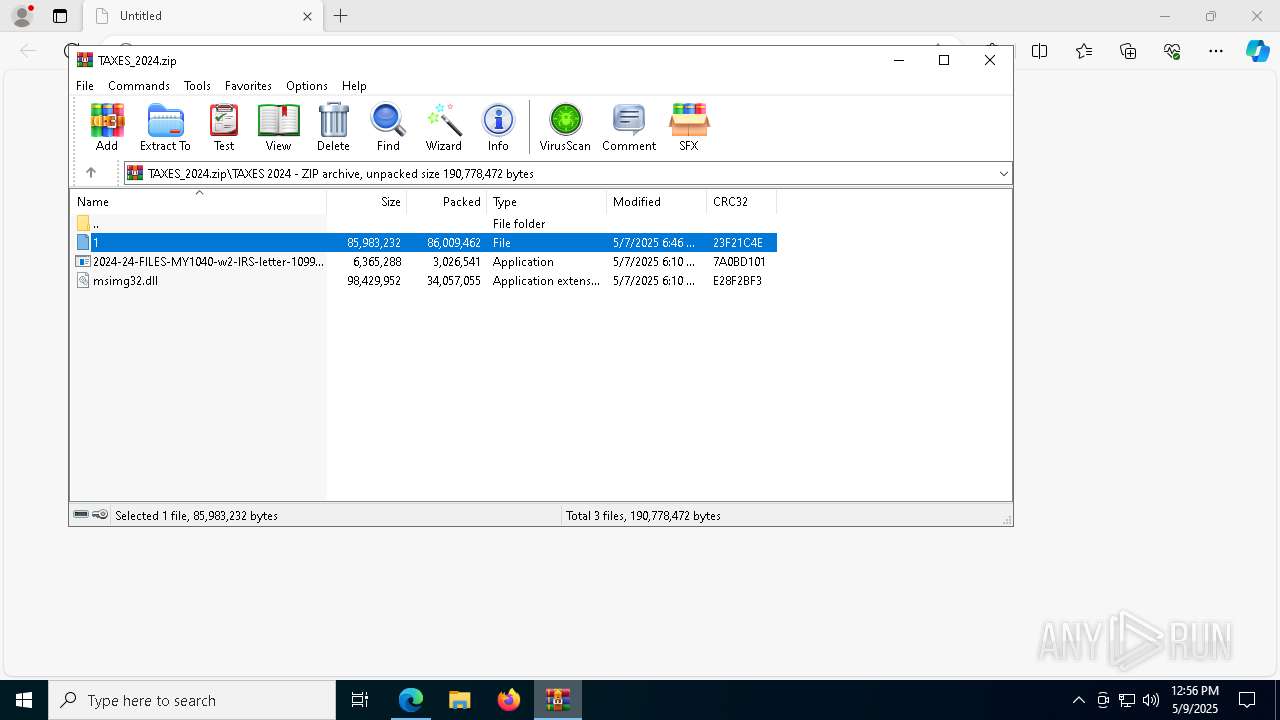
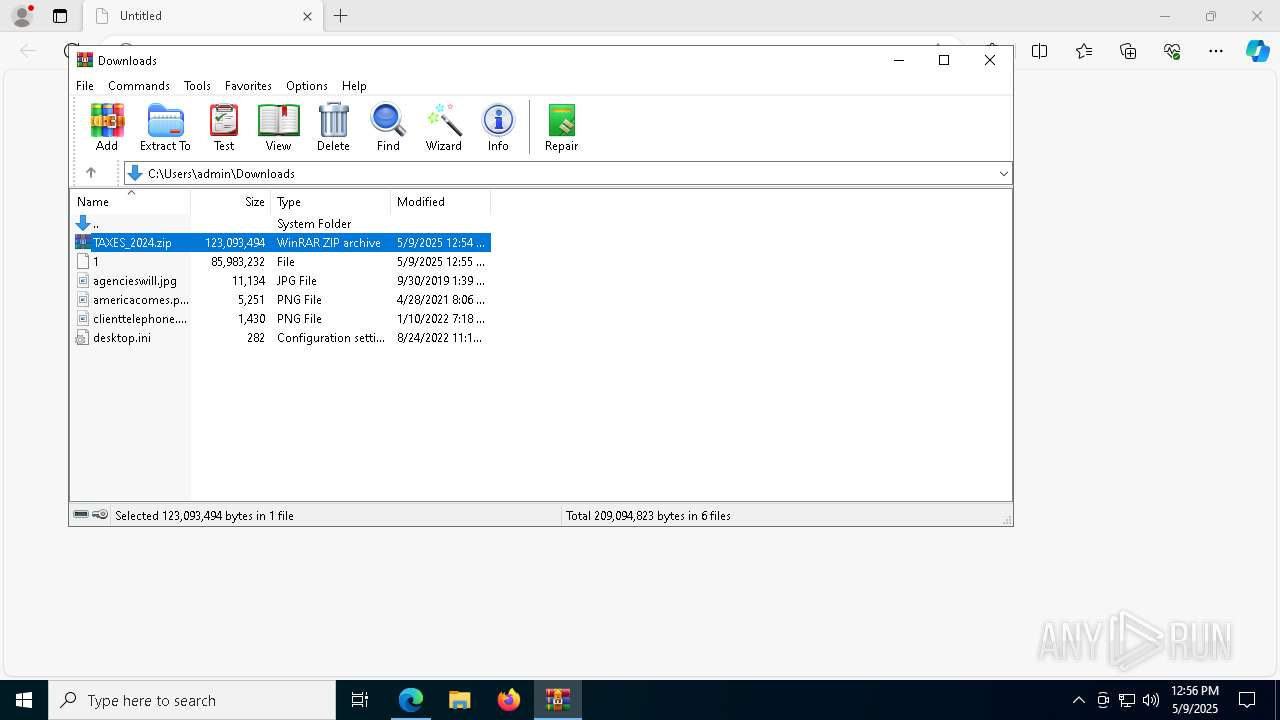
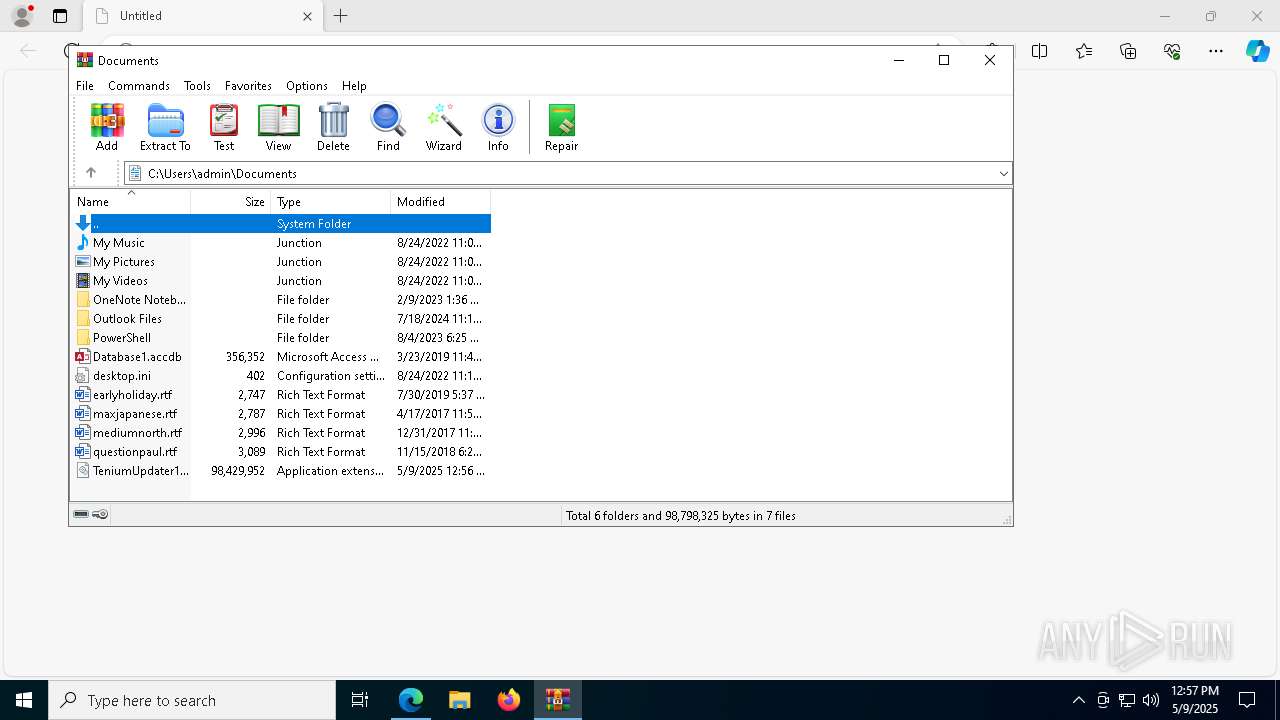
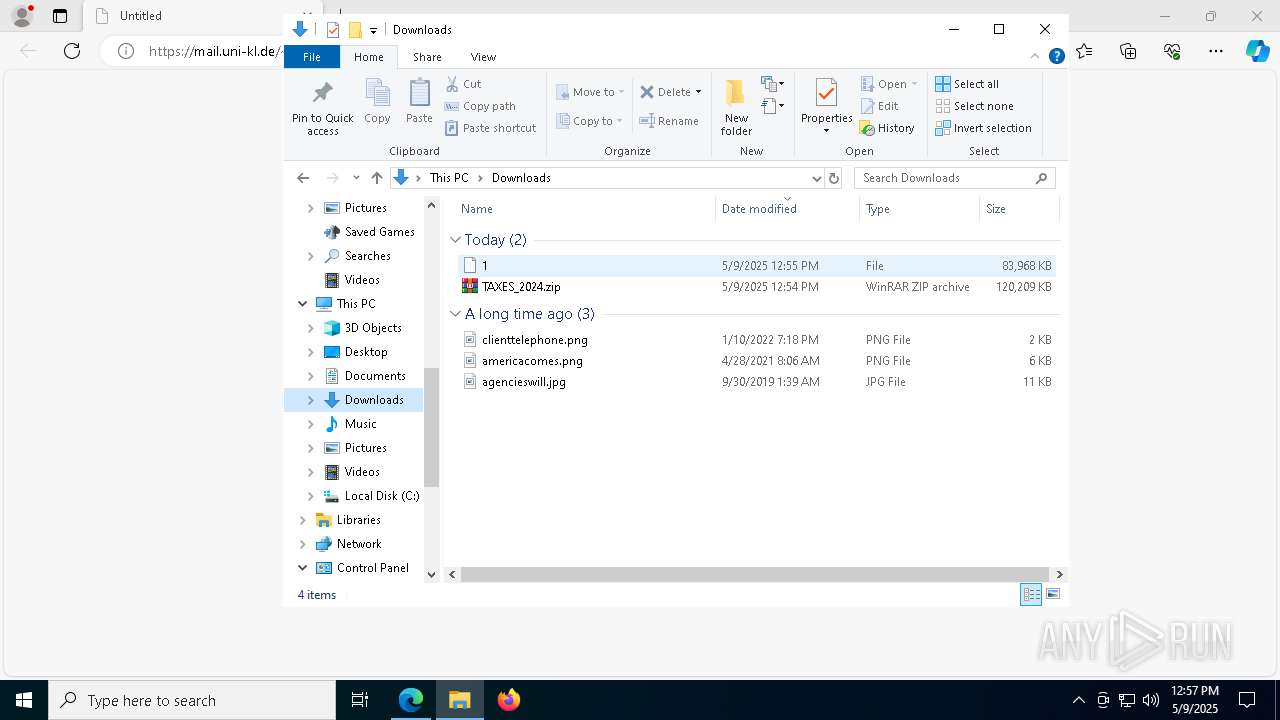
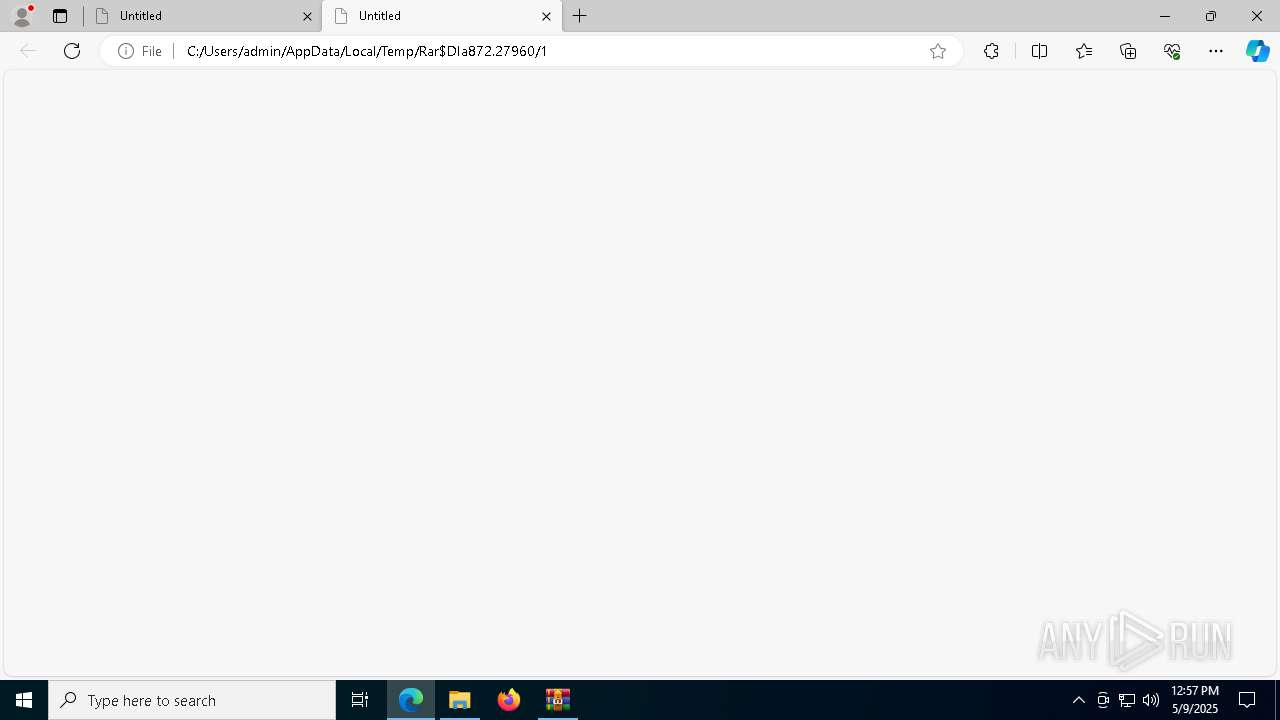
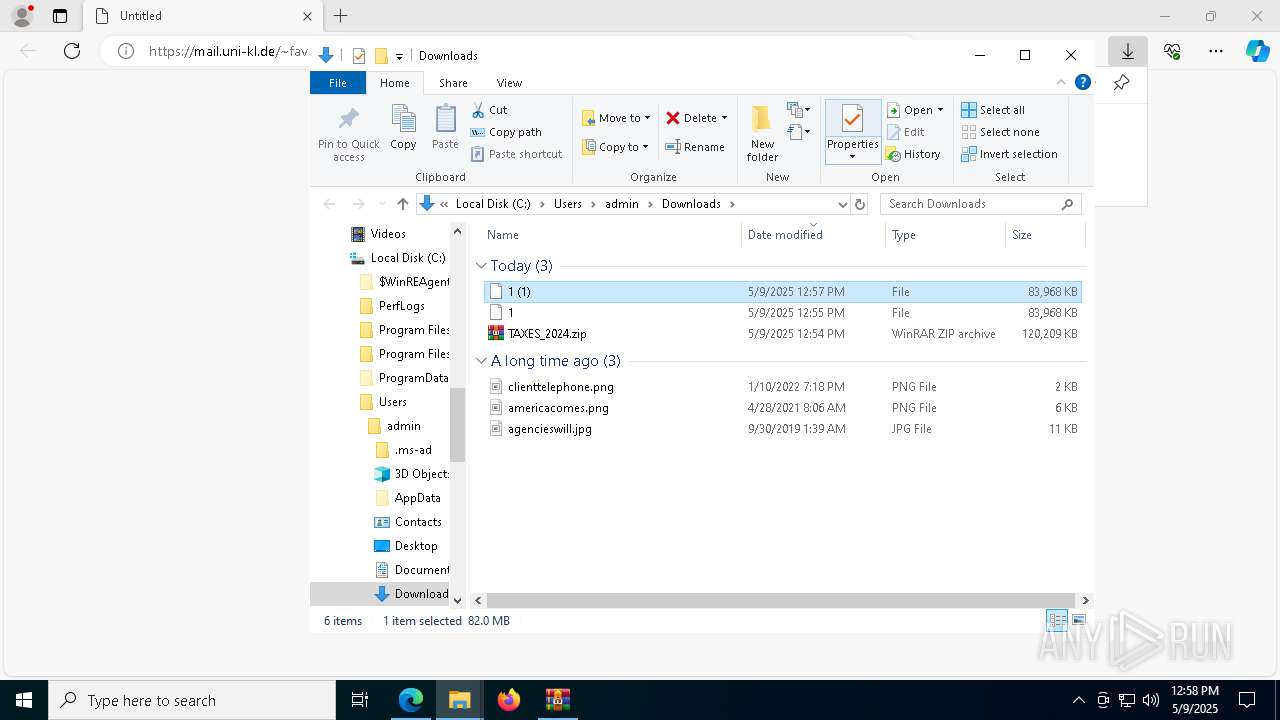
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4560)
- msedge.exe (PID: 3828)
The sample compiled with english language support
- WinRAR.exe (PID: 4560)
- msedge.exe (PID: 3828)
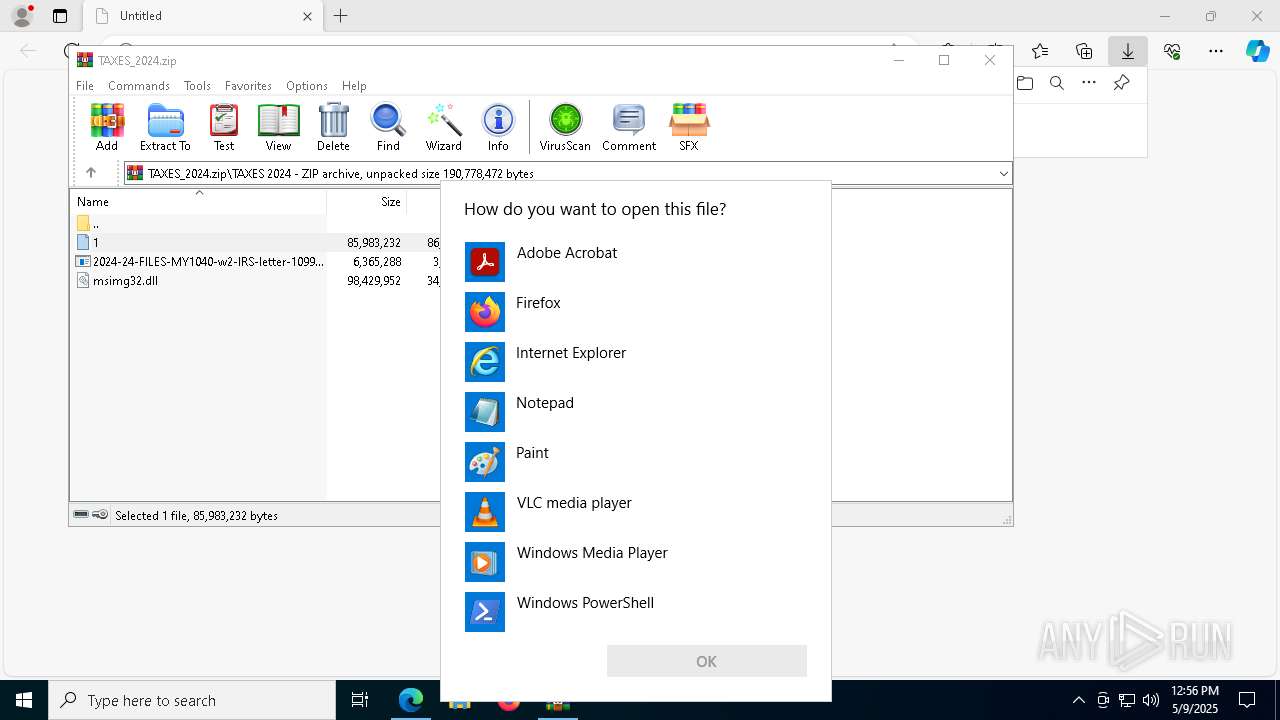
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 5436)
- OpenWith.exe (PID: 7960)
Checks proxy server information
- slui.exe (PID: 2420)
Reads the machine GUID from the registry
- csc.exe (PID: 7796)
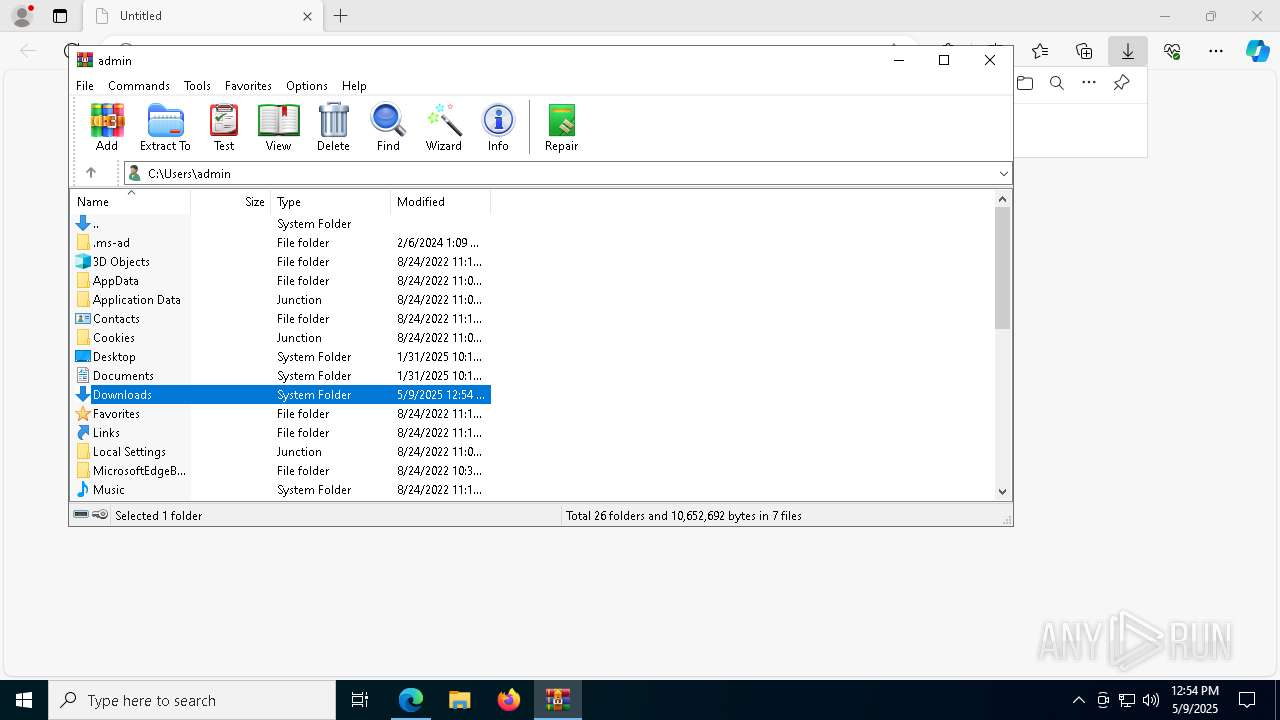
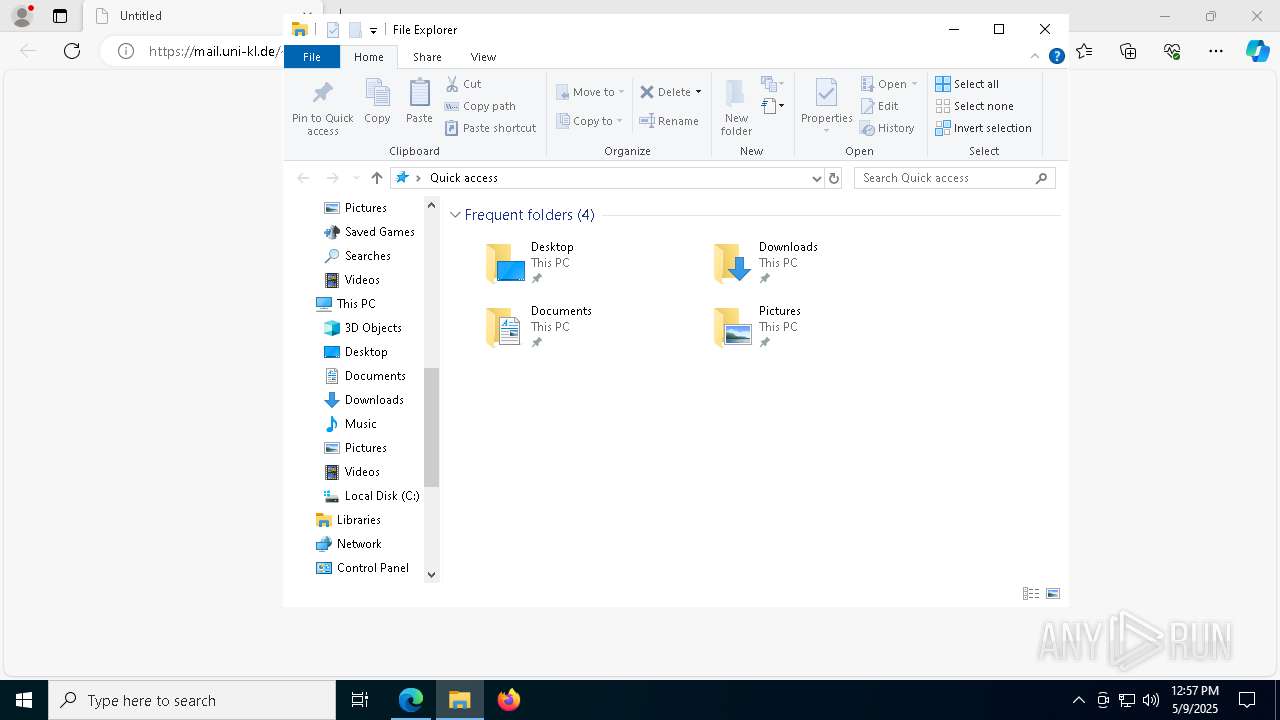
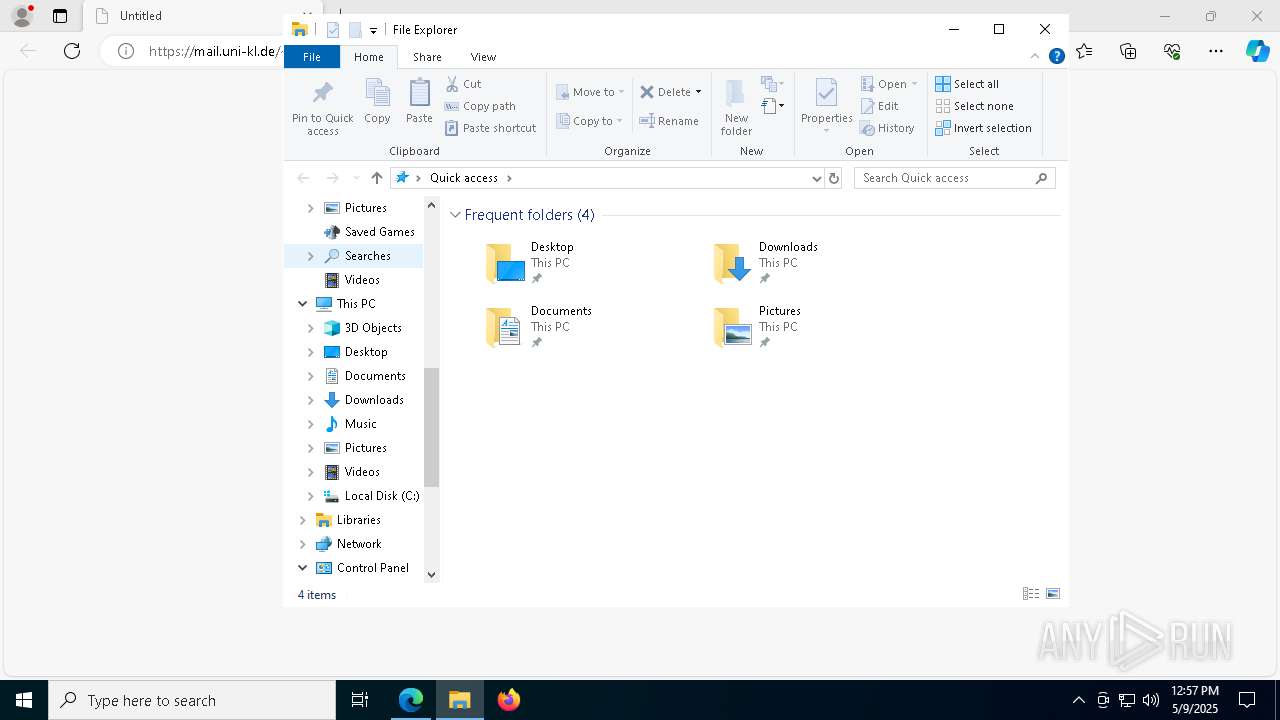
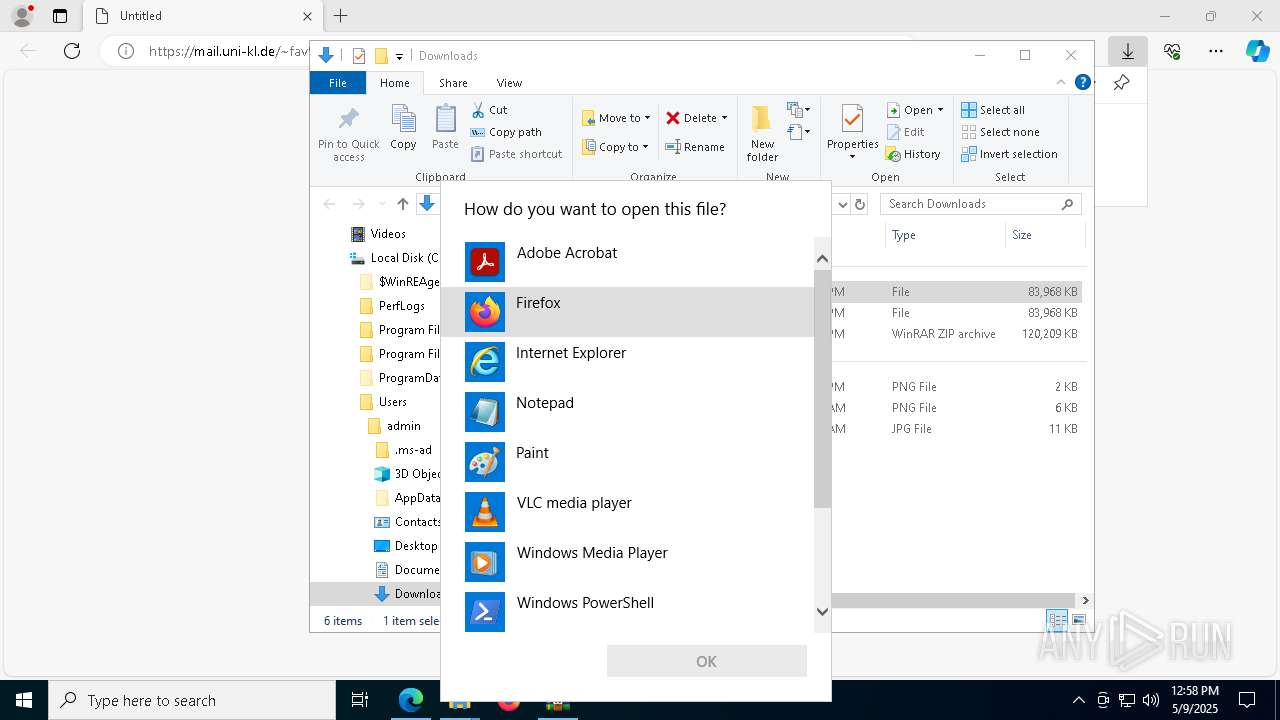
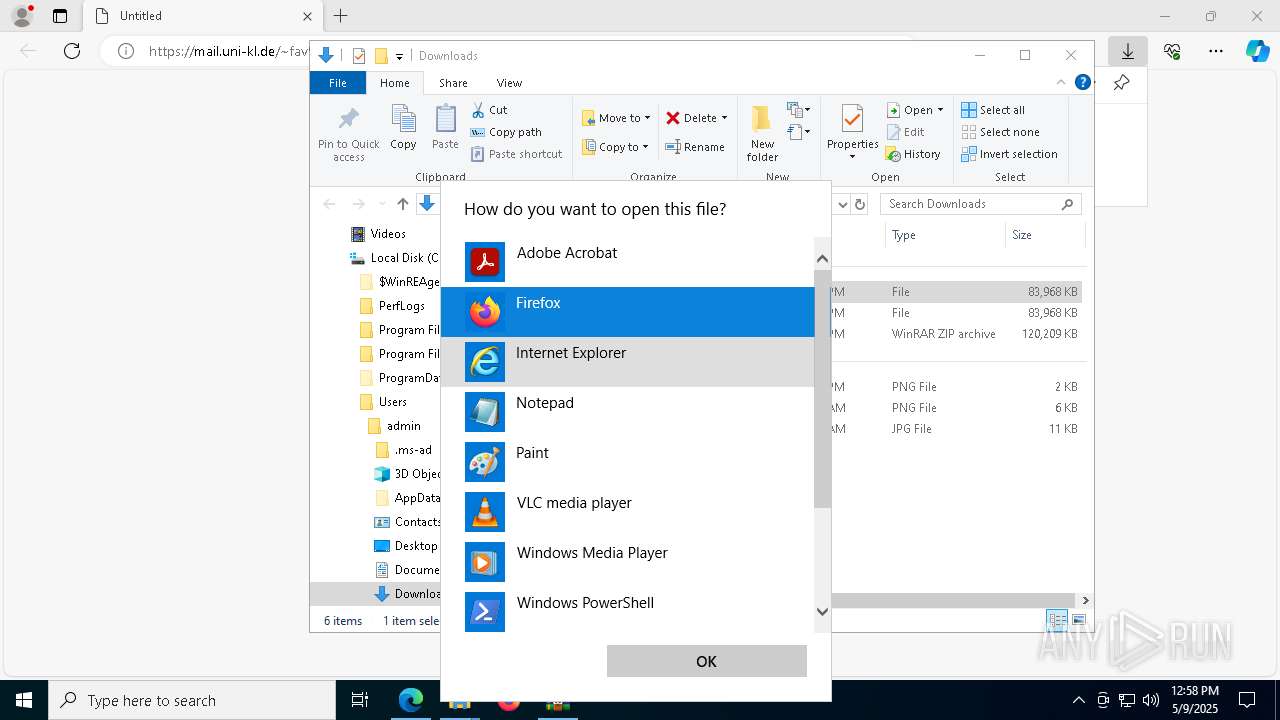
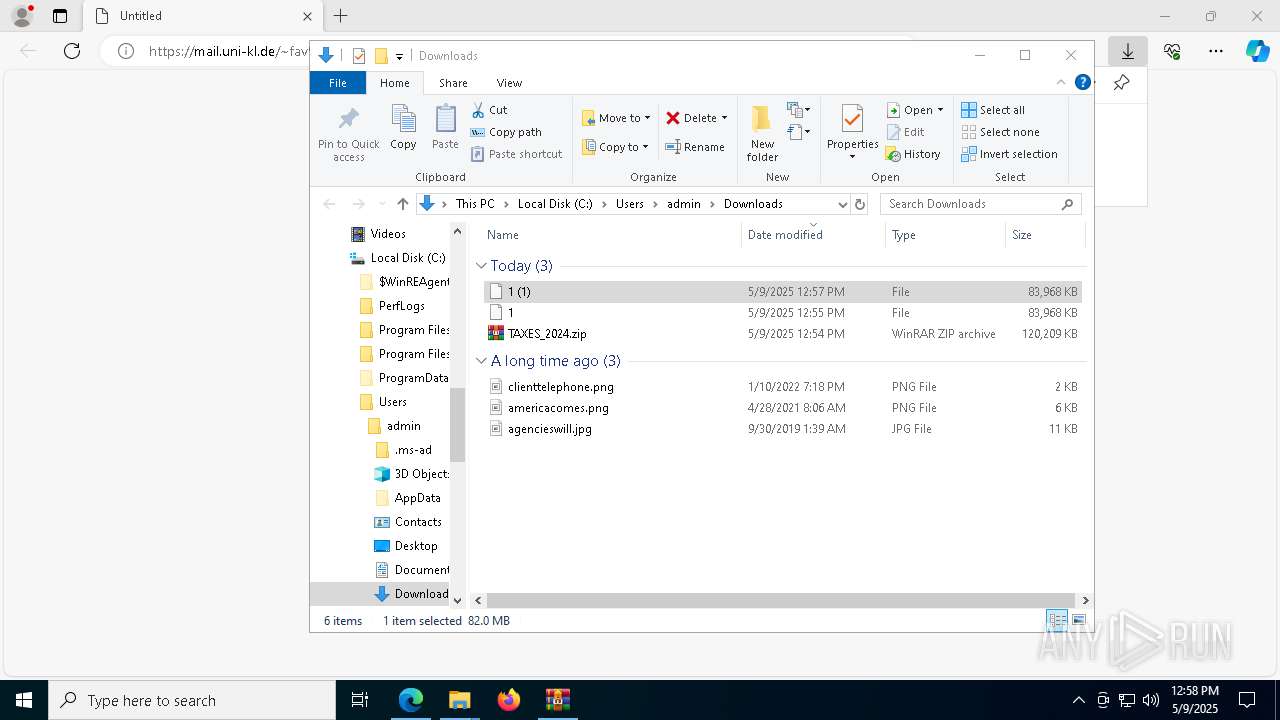
Manual execution by a user
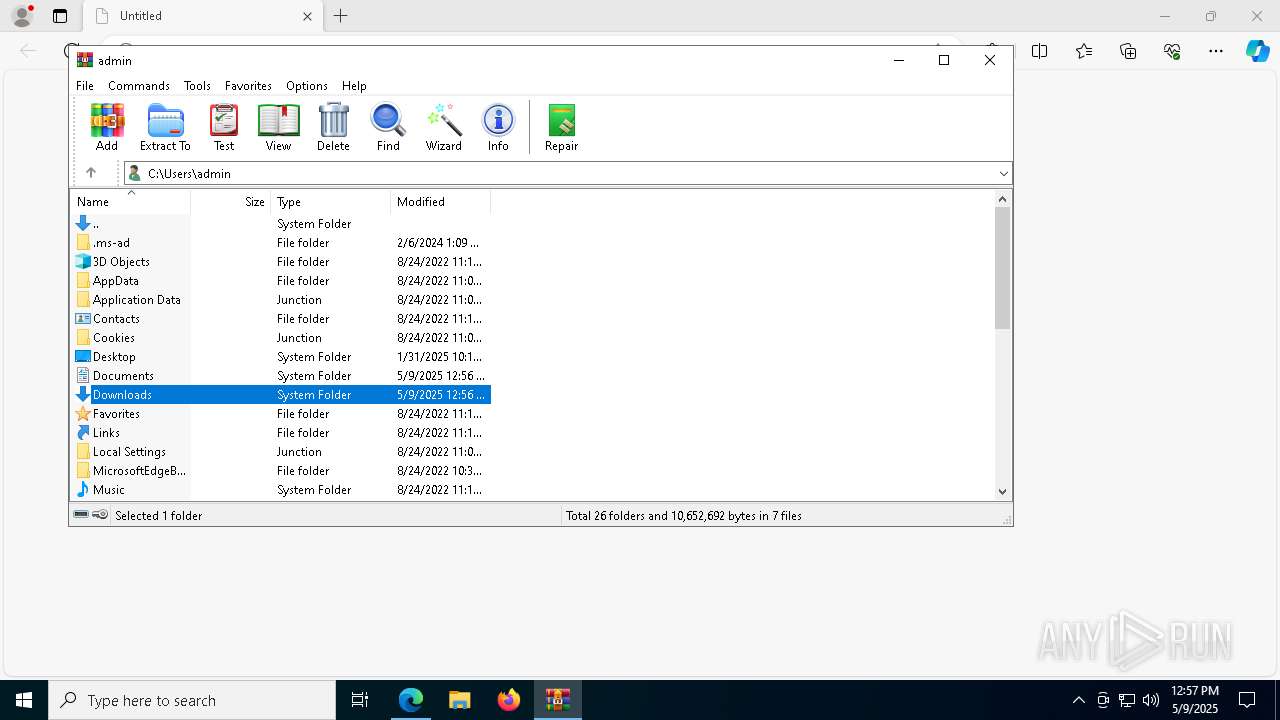
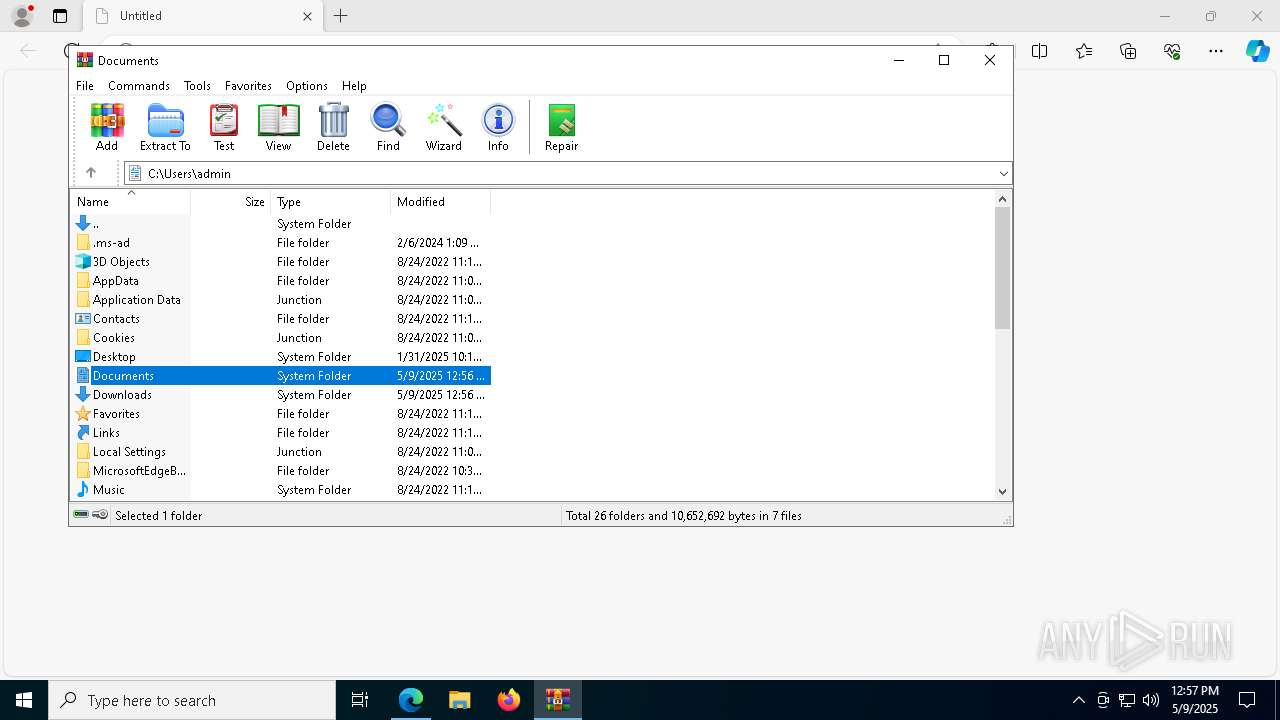
- WinRAR.exe (PID: 872)
- Acrobat.exe (PID: 7968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
117
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 "C:\Users\admin\AppData\Local\Temp\Rar$DIa4560.19615\1" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Exit code: 1 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7616 --field-trial-handle=2280,i,4180159752017941085,11788480616730471004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6584 --field-trial-handle=2280,i,4180159752017941085,11788480616730471004,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4560.10413\TAXES 2024\2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4560.10413\TAXES 2024\2024-24-FILES-MY1040-w2-IRS-letter-1099r.PDF.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Haihaisoft Limited Integrity Level: MEDIUM Description: Haihaisoft PDF Reader Exit code: 2510698164 Version: 1.5.7.0 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2168 -parentBuildID 20240213221259 -prefsHandle 2160 -prefMapHandle 2148 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2d8a2718-1ba8-464c-85a2-ab3a93822457} 6712 "\\.\pipe\gecko-crash-server-pipe.6712" 16888180f10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 684 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1520 --field-trial-handle=1652,i,8681363748867233509,15370357016387602010,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=3852 -childID 5 -isForBrowser -prefsHandle 5448 -prefMapHandle 5452 -prefsLen 31198 -prefMapSize 244583 -jsInitHandle 1484 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5879e018-9347-43e6-a506-9a9ba733d1c3} 6712 "\\.\pipe\gecko-crash-server-pipe.6712" 1689dfe2150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=utility --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2136 --field-trial-handle=1652,i,8681363748867233509,15370357016387602010,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
Total events
63 287
Read events
63 008
Write events
259
Delete events
20
Modification events
| (PID) Process: | (6700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (6700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (6700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524998 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D2730176-9FFD-408A-AF49-F303190E547A} | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000082E5CE7EE1C0DB01 | |||
| (PID) Process: | (6700) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
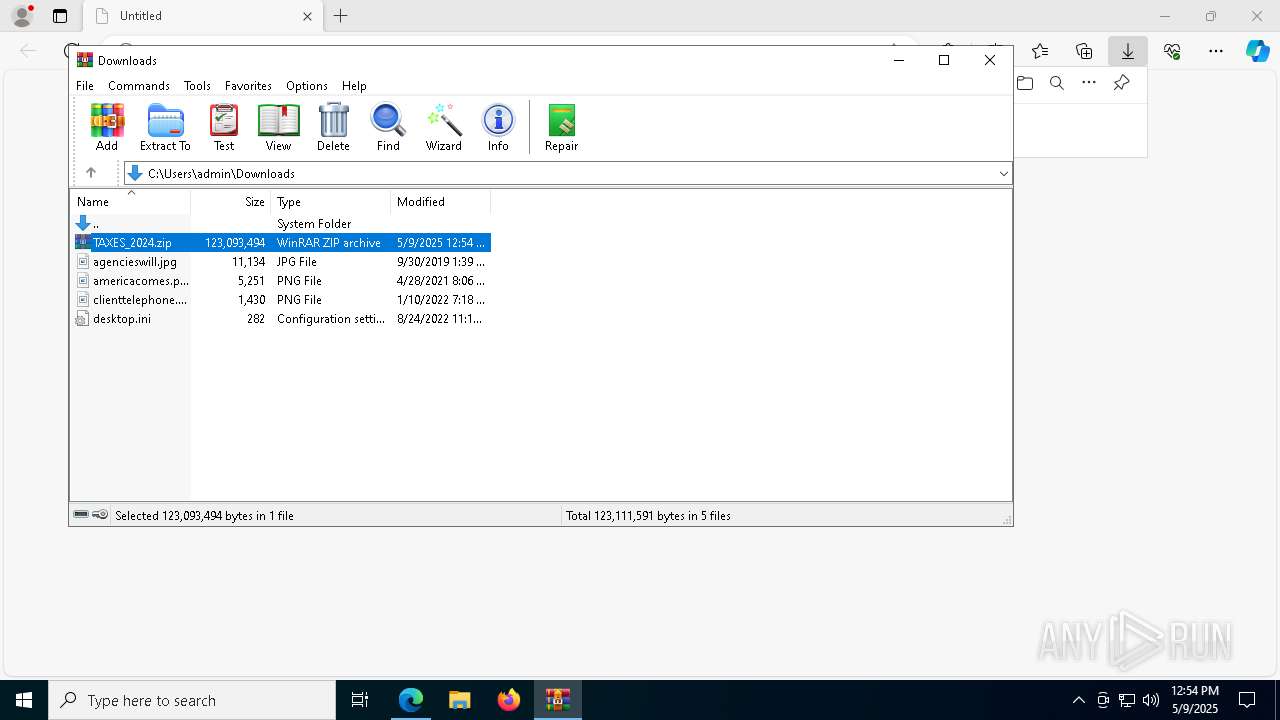
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
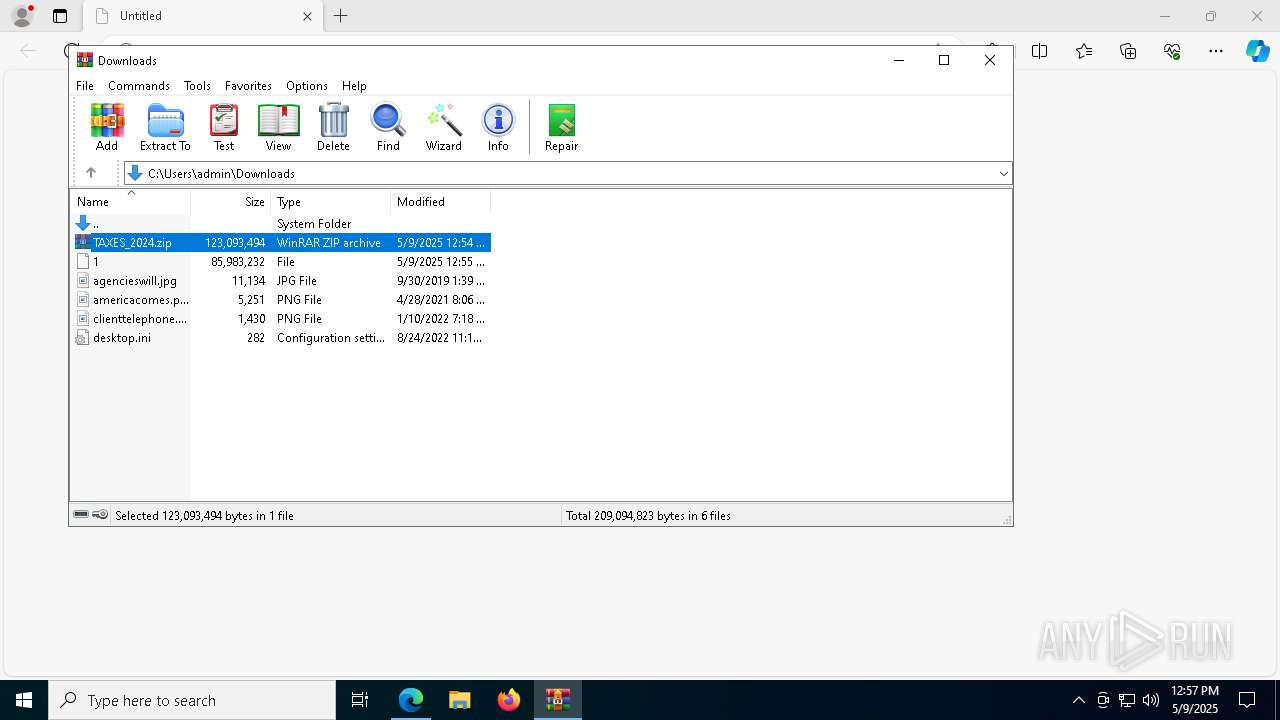
Value: C:\Users\admin\Downloads\TAXES_2024.zip | |||
Executable files
16
Suspicious files
861
Text files
147
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b661.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b661.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6a0.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b690.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b661.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
78
TCP/UDP connections
111
DNS requests
174
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6668 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747344461&P2=404&P3=2&P4=WEt7ILIacdfS8PWo0Mdb1JVxHeXA7HJbuFU91ketWojwjPalBu5%2bk1eAoGHQuAt11lBcDz8UKjDASczSxLMPUw%3d%3d | unknown | — | — | whitelisted |
6668 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747344461&P2=404&P3=2&P4=WEt7ILIacdfS8PWo0Mdb1JVxHeXA7HJbuFU91ketWojwjPalBu5%2bk1eAoGHQuAt11lBcDz8UKjDASczSxLMPUw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mail.uni-kl.de |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
7796 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
7796 | csc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |