| File name: | phobos.exe |
| Full analysis: | https://app.any.run/tasks/fb8fa7fb-0c1b-4470-9cbf-65486f4f90fd |
| Verdict: | Malicious activity |
| Threats: | Phobos is a ransomware that locks or encrypts files to demand a ransom. It uses AES encryption with different extensions, which leaves no chance to recover the infected files. |
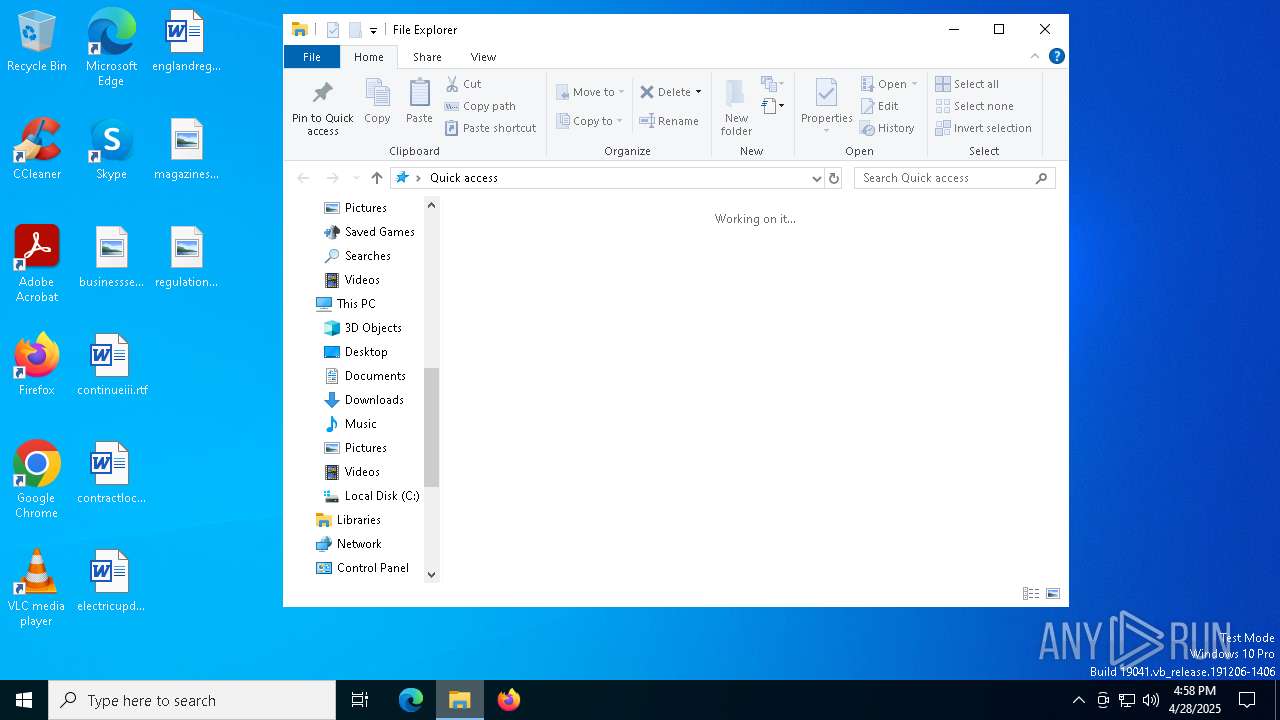
| Analysis date: | April 28, 2025, 16:57:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 4E93C194B641D9B849F270531EC14D20 |
| SHA1: | 8B5A21254A0C10E3CA2570EEBA490755197B544E |
| SHA256: | 43F846C12C24A078EBE33F71E8EA3B4F75107AEB275E2C3CD9DC61617C9757FC |
| SSDEEP: | 1536:kymNrLwC/WPYQ3CUXeXx35/bj3xLmPGDM3Q8wUx:kymdw49Q3teHDjhLmeDQNj |
MALICIOUS
PHOBOS mutex has been found
- phobos.exe (PID: 6436)
- phobos.exe (PID: 2096)
- phobos.exe (PID: 4696)
Changes the autorun value in the registry
- phobos.exe (PID: 2096)
- phobos.exe (PID: 6436)
Create files in the Startup directory
- phobos.exe (PID: 2096)
Deletes shadow copies
- cmd.exe (PID: 5960)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 5960)
PHOBOS has been detected
- phobos.exe (PID: 2096)
Renames files like ransomware
- phobos.exe (PID: 2096)
SUSPICIOUS
Application launched itself
- phobos.exe (PID: 4696)
- phobos.exe (PID: 6436)
Reads security settings of Internet Explorer
- phobos.exe (PID: 4696)
Starts CMD.EXE for commands execution
- phobos.exe (PID: 2096)
Executable content was dropped or overwritten
- phobos.exe (PID: 2096)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 516)
Executes as Windows Service
- VSSVC.exe (PID: 1660)
- vds.exe (PID: 4464)
- wbengine.exe (PID: 6632)
The process creates files with name similar to system file names
- phobos.exe (PID: 2096)
Process drops legitimate windows executable
- phobos.exe (PID: 2096)
INFO
Checks supported languages
- phobos.exe (PID: 6436)
- phobos.exe (PID: 4696)
- phobos.exe (PID: 2096)
Process checks computer location settings
- phobos.exe (PID: 4696)
Reads the computer name
- phobos.exe (PID: 4696)
- phobos.exe (PID: 2096)
- phobos.exe (PID: 6436)
Creates files or folders in the user directory
- phobos.exe (PID: 2096)
The sample compiled with english language support
- phobos.exe (PID: 2096)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 5056)
Creates files in the program directory
- phobos.exe (PID: 2096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:31 14:17:25+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 34304 |
| InitializedDataSize: | 15872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2fa7 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
20
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | phobos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | netsh advfirewall set currentprofile state off | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\phobos.exe" | C:\Users\admin\AppData\Local\Temp\phobos.exe | phobos.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 4424 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4464 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 144
Read events
2 106
Write events
20
Delete events
18
Modification events
| (PID) Process: | (2096) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | phobos |
Value: C:\Users\admin\AppData\Local\phobos.exe | |||
| (PID) Process: | (2096) phobos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | phobos |
Value: C:\Users\admin\AppData\Local\phobos.exe | |||
| (PID) Process: | (6436) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | phobos |
Value: C:\Users\admin\AppData\Local\phobos.exe | |||
| (PID) Process: | (6436) phobos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | phobos |
Value: C:\Users\admin\AppData\Local\phobos.exe | |||
| (PID) Process: | (680) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (680) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (680) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (680) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (680) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (680) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
Executable files
37
Suspicious files
1 313
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2096 | phobos.exe | C:\$WinREAgent\Backup\Winre.wim.id[26B799FA-2822].[frankmoffit@aol.com].eight | — | |
MD5:— | SHA256:— | |||
| 2096 | phobos.exe | C:\$WinREAgent\Scratch\update.wim.id[26B799FA-2822].[frankmoffit@aol.com].eight | — | |
MD5:— | SHA256:— | |||
| 2096 | phobos.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-500\desktop.ini.id[26B799FA-2822].[frankmoffit@aol.com].eight | binary | |
MD5:EA7045633D4F5C74522BC194827DF421 | SHA256:876367BE406DC009C044FC0DC1B5D8CA6949FD743201F889963DEAF23ACAFCFE | |||
| 2096 | phobos.exe | C:\$Recycle.Bin\S-1-5-18\desktop.ini.id[26B799FA-2822].[frankmoffit@aol.com].eight | binary | |
MD5:AE6CB89B83416B2EF228484C5960BDEE | SHA256:39C75F73EFCCB443357D2528E19E0BCF1B6C8DB38D2735743D2D1B0DC43B1741 | |||
| 2096 | phobos.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\phobos.exe | executable | |
MD5:4E93C194B641D9B849F270531EC14D20 | SHA256:43F846C12C24A078EBE33F71E8EA3B4F75107AEB275E2C3CD9DC61617C9757FC | |||
| 2096 | phobos.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini.id[26B799FA-2822].[frankmoffit@aol.com].eight | binary | |
MD5:1C1FD5A84AE4E0D942F546D3125145C4 | SHA256:D4ED7DB8FB7BA4BC7EAF4CB9757031B4C8597B49BDAB81F4FBAAF2132262BABE | |||
| 2096 | phobos.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\phobos.exe | executable | |
MD5:4E93C194B641D9B849F270531EC14D20 | SHA256:43F846C12C24A078EBE33F71E8EA3B4F75107AEB275E2C3CD9DC61617C9757FC | |||
| 2096 | phobos.exe | C:\Users\admin\AppData\Local\phobos.exe | executable | |
MD5:4E93C194B641D9B849F270531EC14D20 | SHA256:43F846C12C24A078EBE33F71E8EA3B4F75107AEB275E2C3CD9DC61617C9757FC | |||
| 2096 | phobos.exe | C:\$WinREAgent\Backup\location.txt.id[26B799FA-2822].[frankmoffit@aol.com].eight | binary | |
MD5:F9302DA58CA5EE75C7D038FD2AA9DA52 | SHA256:7B0B9B6AC6461174D07048A9AD88CBEE7B68CB58C4D8B9EF8A6FDB3CF4C93F5F | |||
| 2096 | phobos.exe | C:\BOOTNXT.id[26B799FA-2822].[frankmoffit@aol.com].eight | binary | |
MD5:ED3F8C00A2EFAF96C142C463C86A1F72 | SHA256:FE6C13BABD340B7AC3D174B488E0CA6FDFB795231F408D22F746E52C3CBF1D62 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7228 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7228 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2292 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
3812 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |